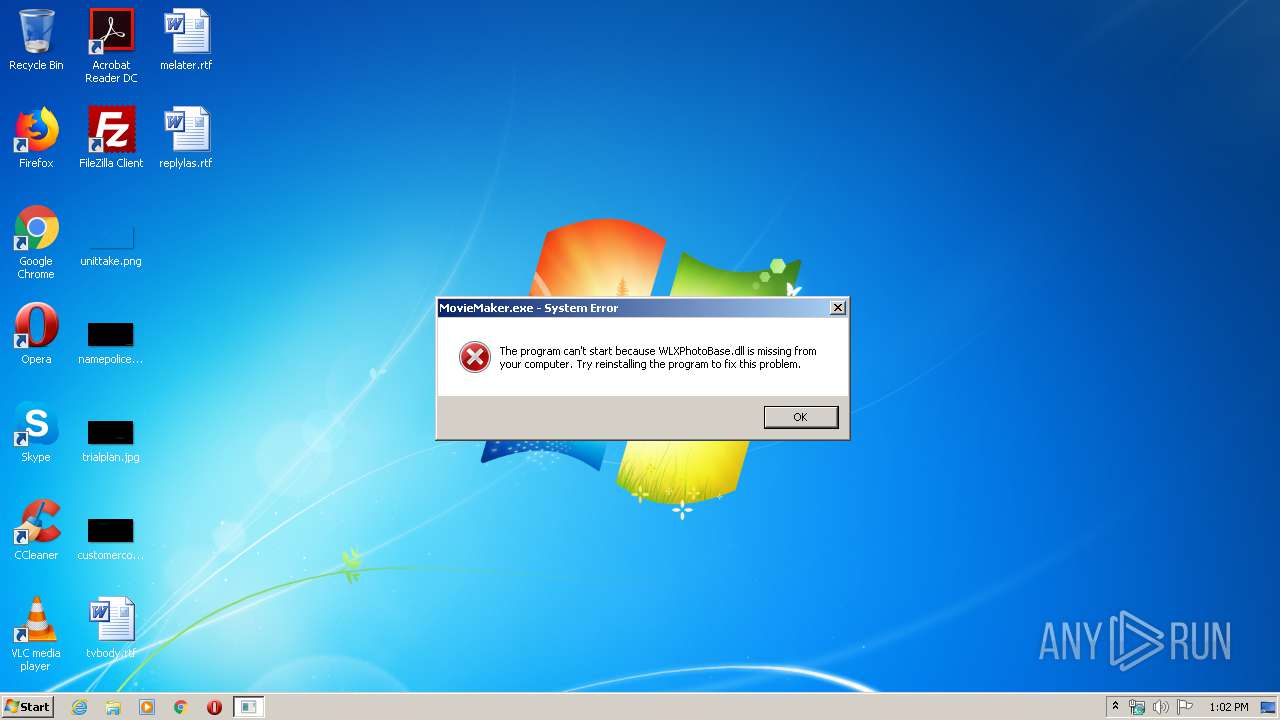
| File name: | MovieMaker.exe |
| Full analysis: | https://app.any.run/tasks/65186f02-6478-45ec-9636-ce7bfb477b77 |
| Verdict: | Malicious activity |
| Analysis date: | March 16, 2020, 13:02:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1649995FB7ED076AEE67CC7EA9826DCC |
| SHA1: | A4BD8A5209F81DE771E0A0E232A9F831F6608C23 |
| SHA256: | 8BDCC9AC2BA891A2EF962A714982DD5FB8B75E4FEF850CFF2C2E219B71456030 |
| SSDEEP: | 1536:XSNHvkDmgInw68SsY/49MML9KbmyjMVdfvghL2UHHEGK5G1nMXN+8jwTeV:i3g7lYw9MMCTYPfaq5G14N+80TeV |
MALICIOUS
Application was dropped or rewritten from another process
- LMI_Rescue_srv.exe (PID: 620)
- LMI_Rescue.exe (PID: 2576)
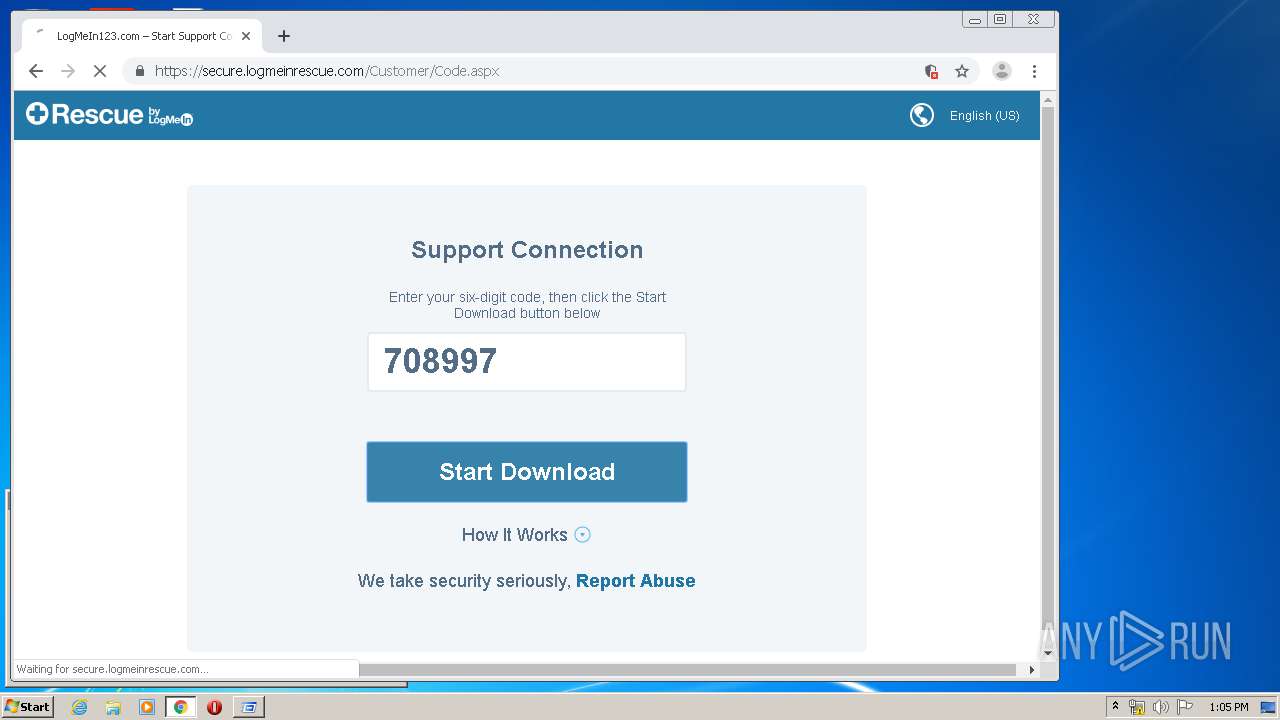
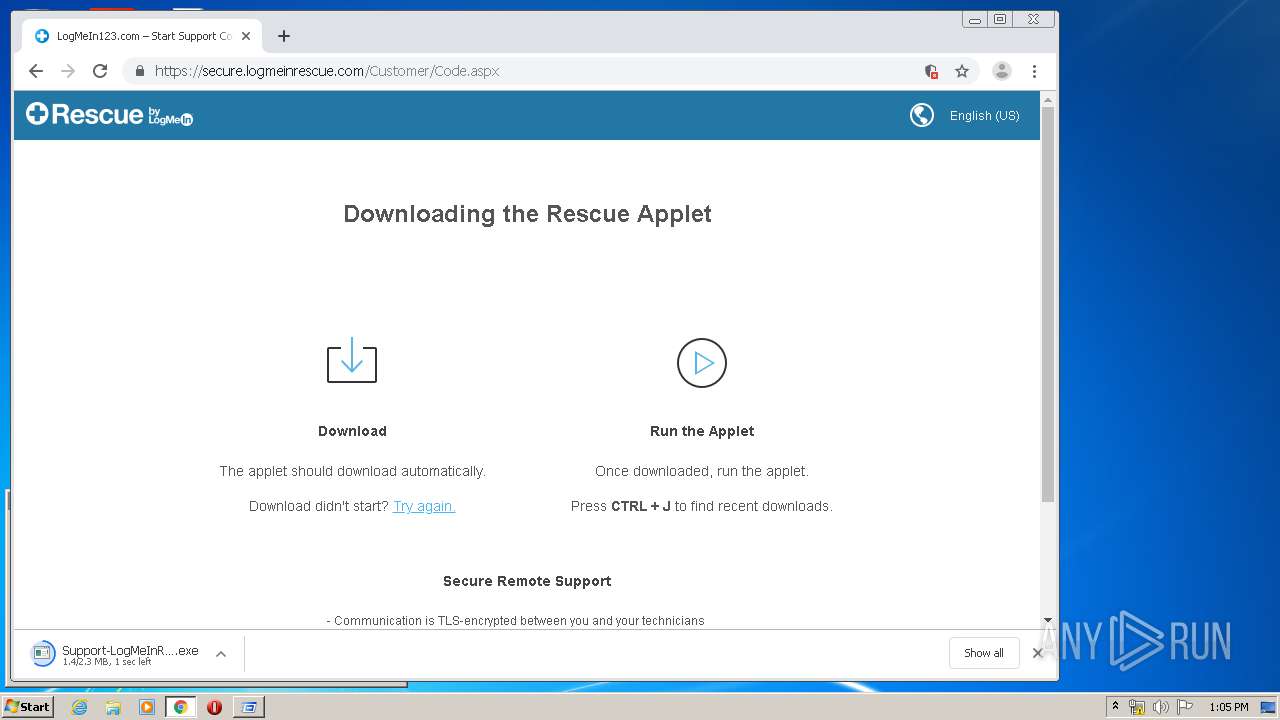
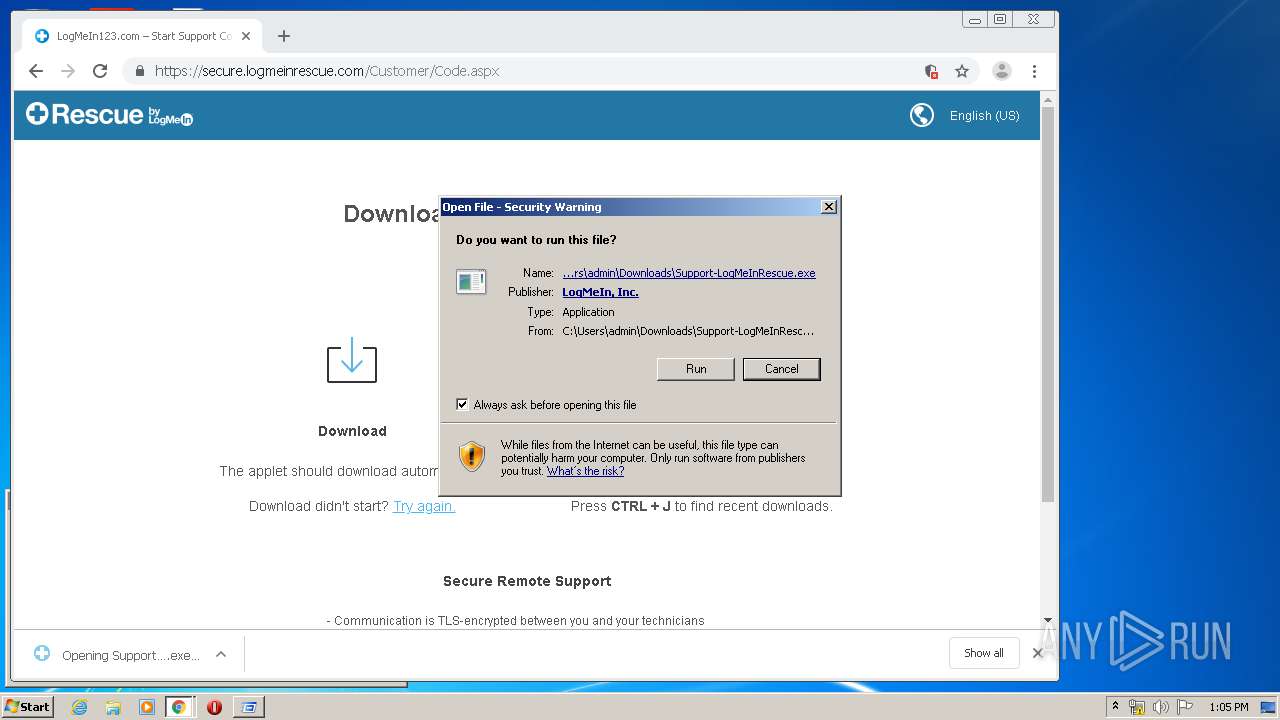
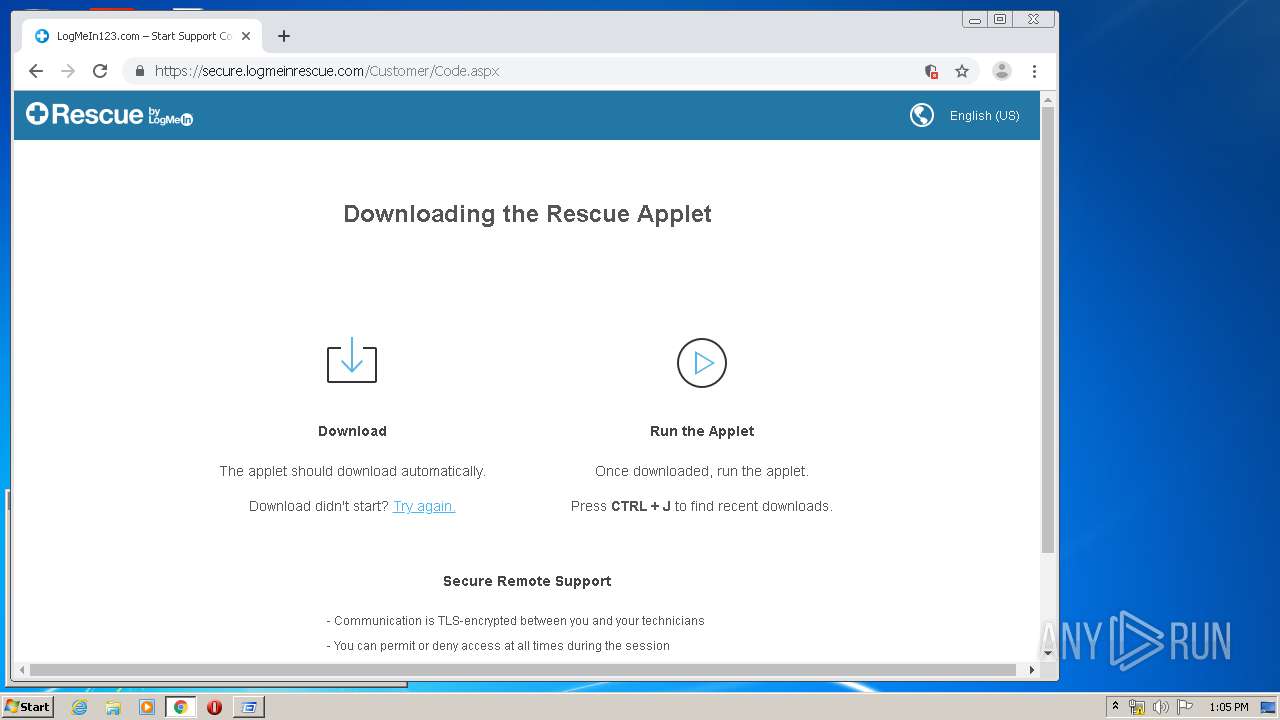
- Support-LogMeInRescue.exe (PID: 1544)
- LMI_Rescue_srv.exe (PID: 2564)
- LMI_Rescue_srv.exe (PID: 1084)
- LMI_RescueRC.exe (PID: 3300)
- LMI_RescueRC.exe (PID: 2972)
- LMI_RescueRC.exe (PID: 1712)
- LMI_Rescue_srv.exe (PID: 1888)
Loads dropped or rewritten executable
- ctfmon.exe (PID: 652)
- explorer.exe (PID: 372)
- LMI_Rescue.exe (PID: 2576)
- LMI_RescueRC.exe (PID: 1712)
- chrome.exe (PID: 1872)
Application was injected by another process
- lsm.exe (PID: 492)
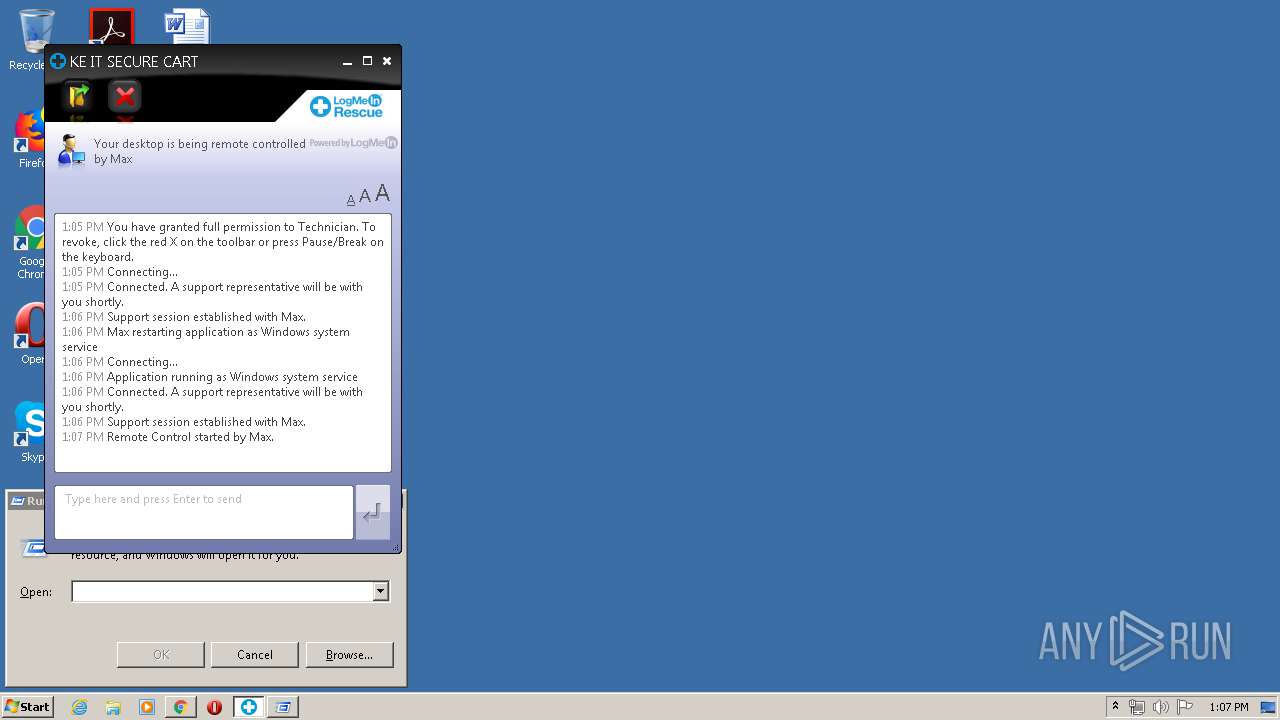
Runs injected code in another process
- LMI_Rescue_srv.exe (PID: 1084)
Changes the autorun value in the registry
- LMI_Rescue_srv.exe (PID: 620)
Changes settings of System certificates
- LMI_Rescue_srv.exe (PID: 1084)
SUSPICIOUS
Reads Internet Cache Settings
- LMI_Rescue_srv.exe (PID: 620)
- LMI_Rescue.exe (PID: 2576)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1872)
Executable content was dropped or overwritten
- chrome.exe (PID: 1872)
- LMI_Rescue_srv.exe (PID: 620)
- LMI_Rescue_srv.exe (PID: 2564)
- LMI_RescueRC.exe (PID: 1712)
- chrome.exe (PID: 2192)
- Support-LogMeInRescue.exe (PID: 1544)
Application launched itself
- LMI_Rescue_srv.exe (PID: 620)
- LMI_Rescue_srv.exe (PID: 1084)
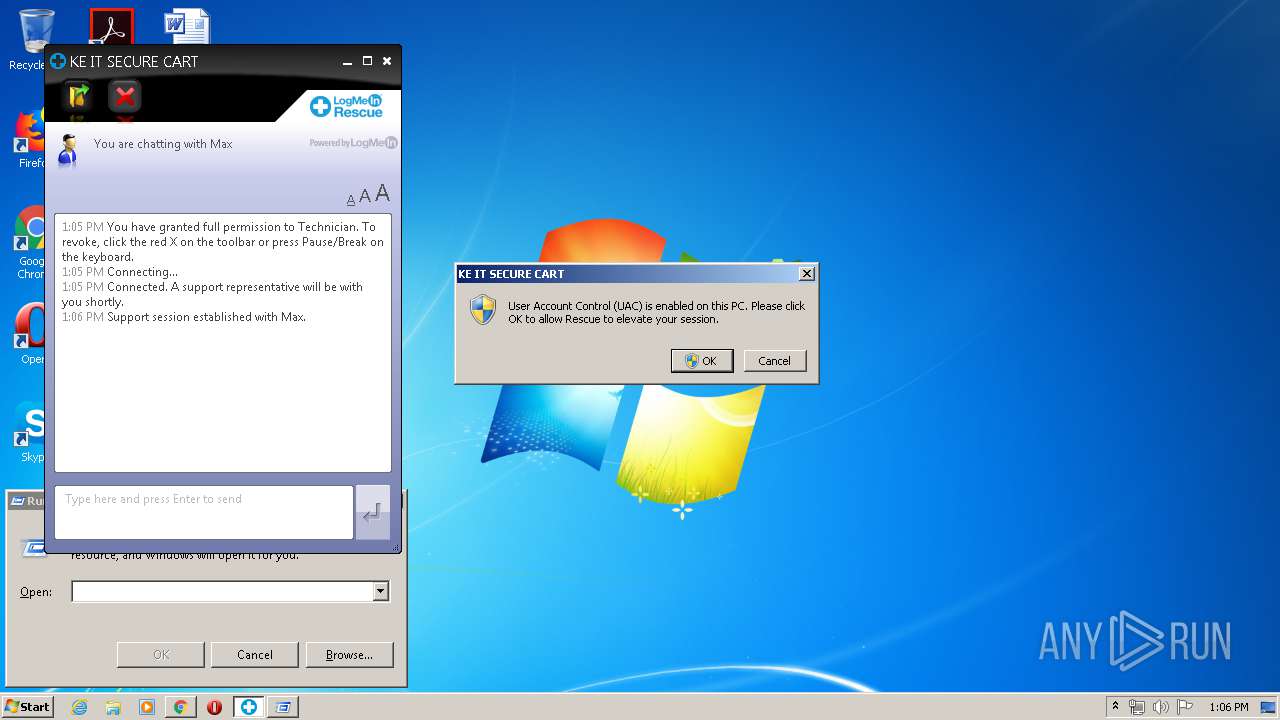
Executed as Windows Service
- LMI_Rescue_srv.exe (PID: 1084)
Creates files in the program directory
- LMI_RescueRC.exe (PID: 1712)
Adds / modifies Windows certificates
- LMI_Rescue_srv.exe (PID: 1084)
INFO
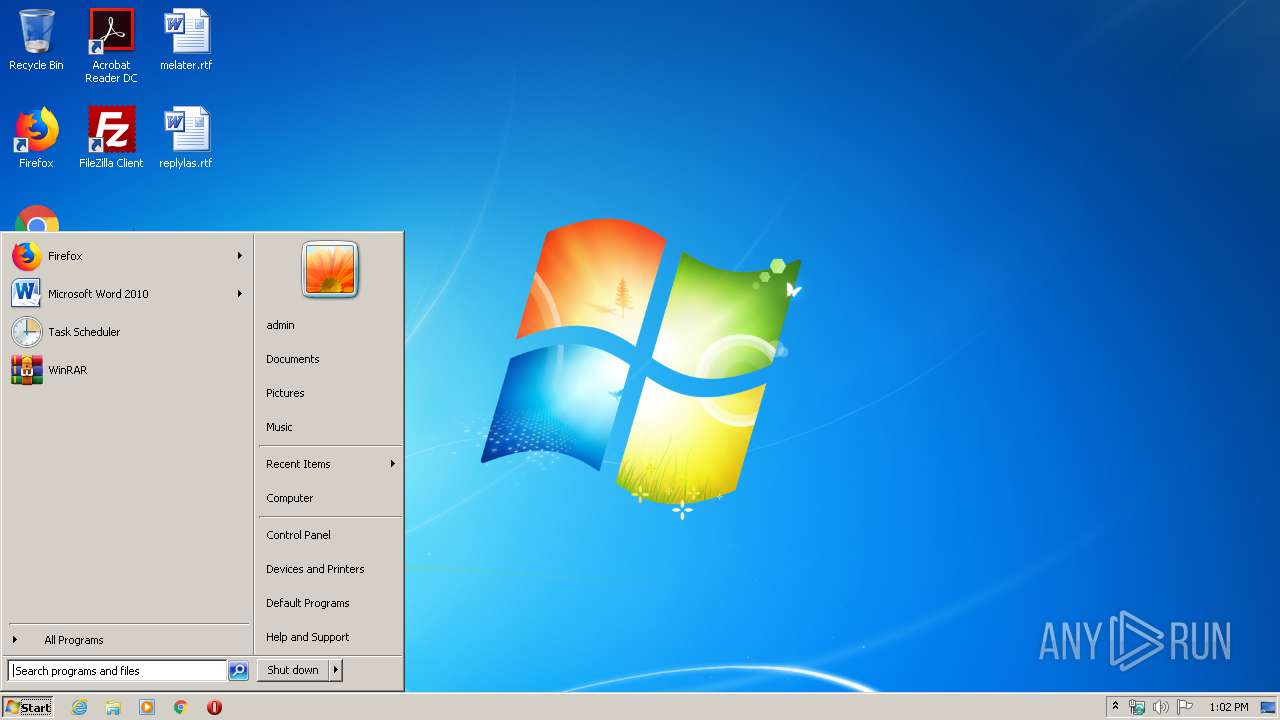
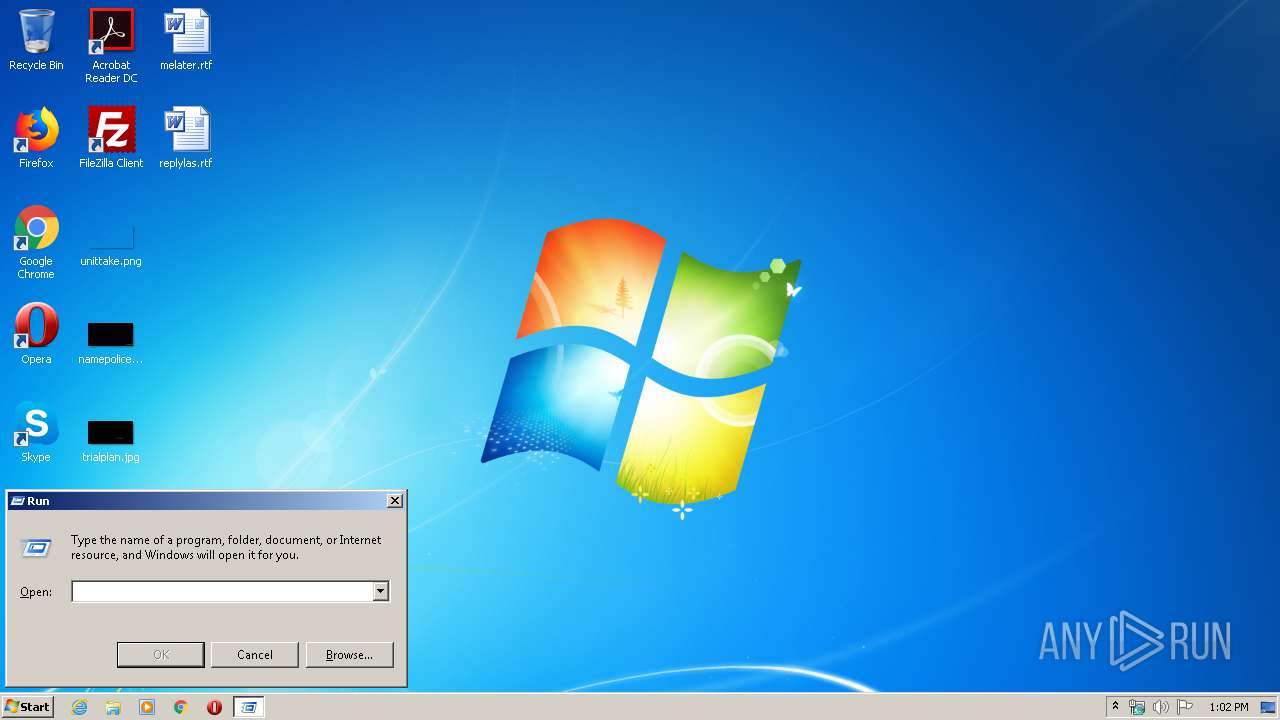
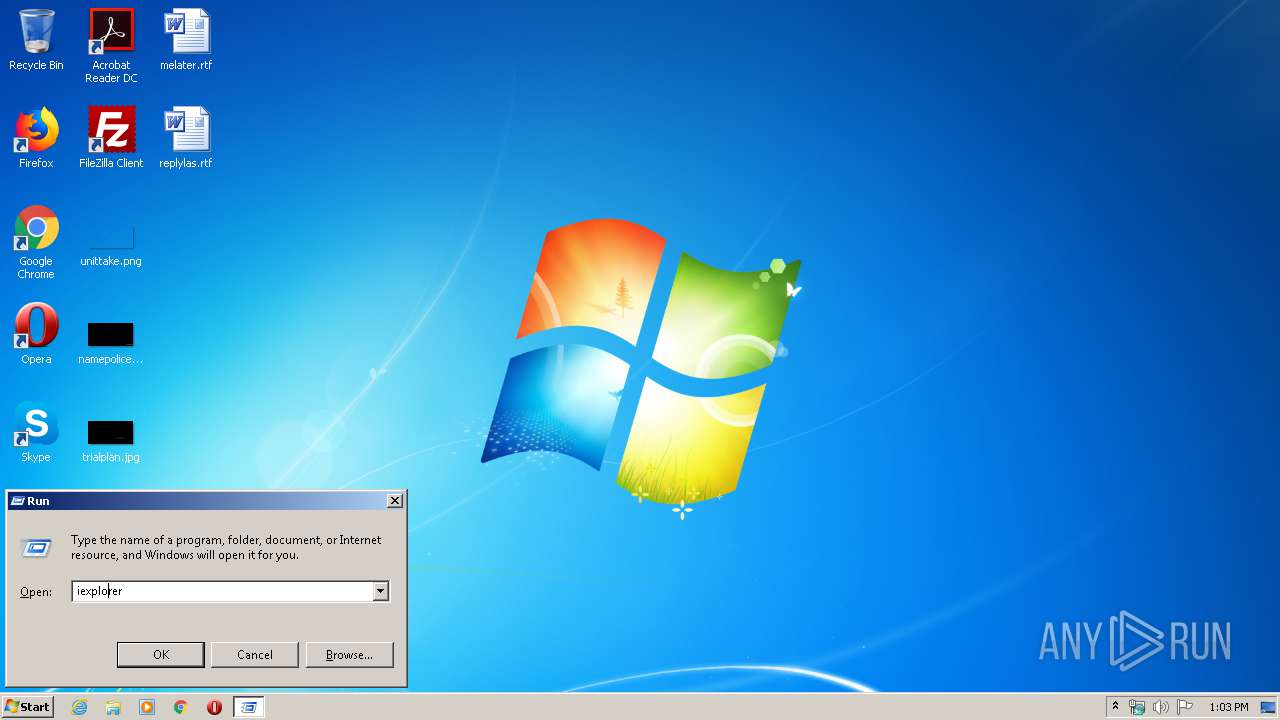
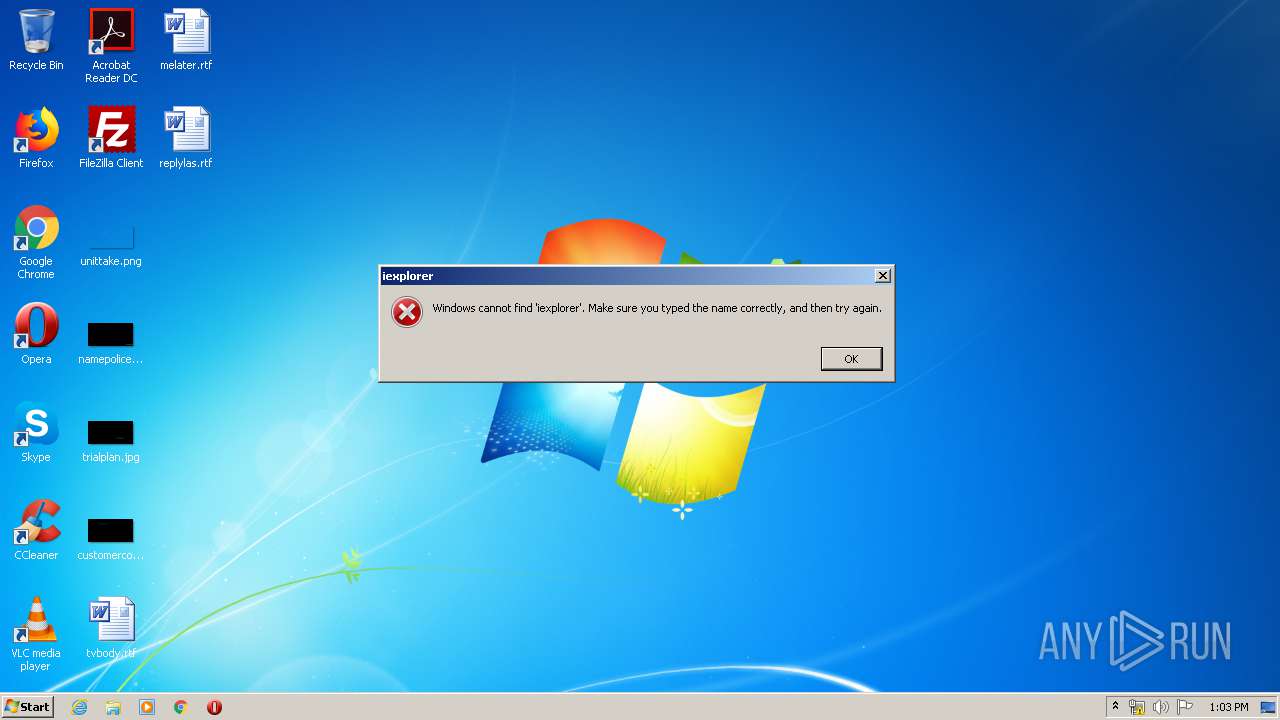
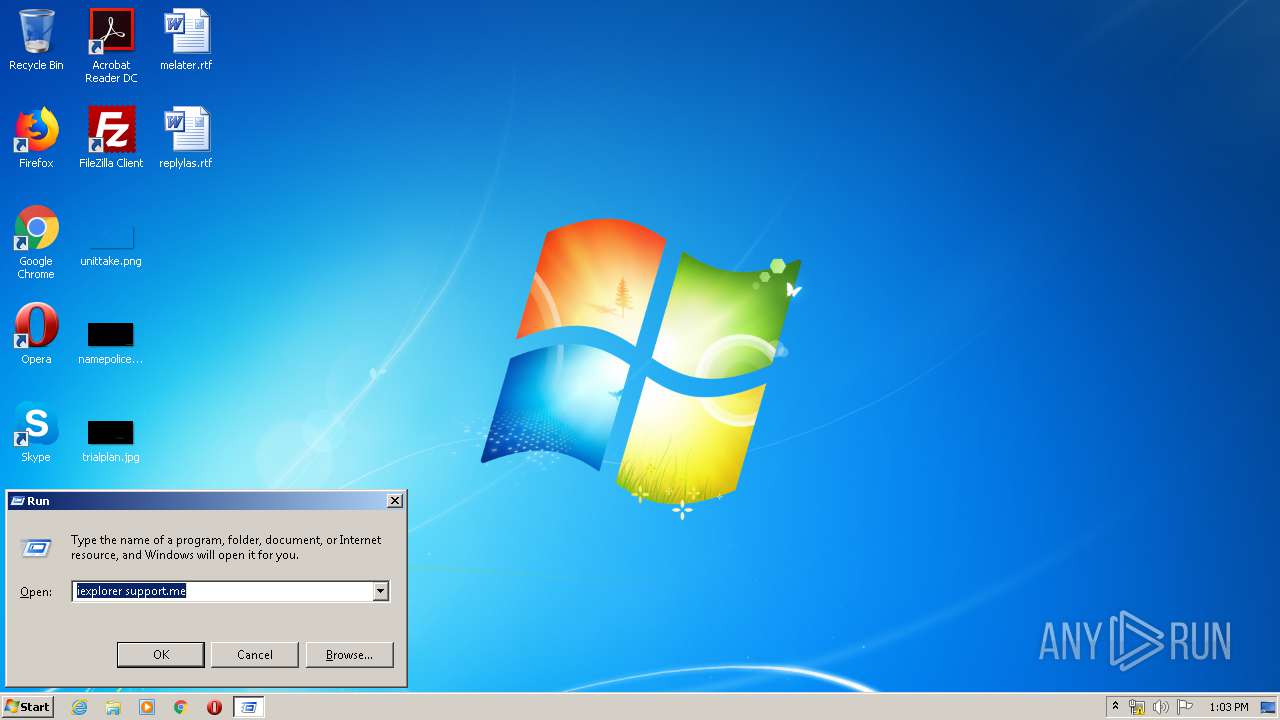
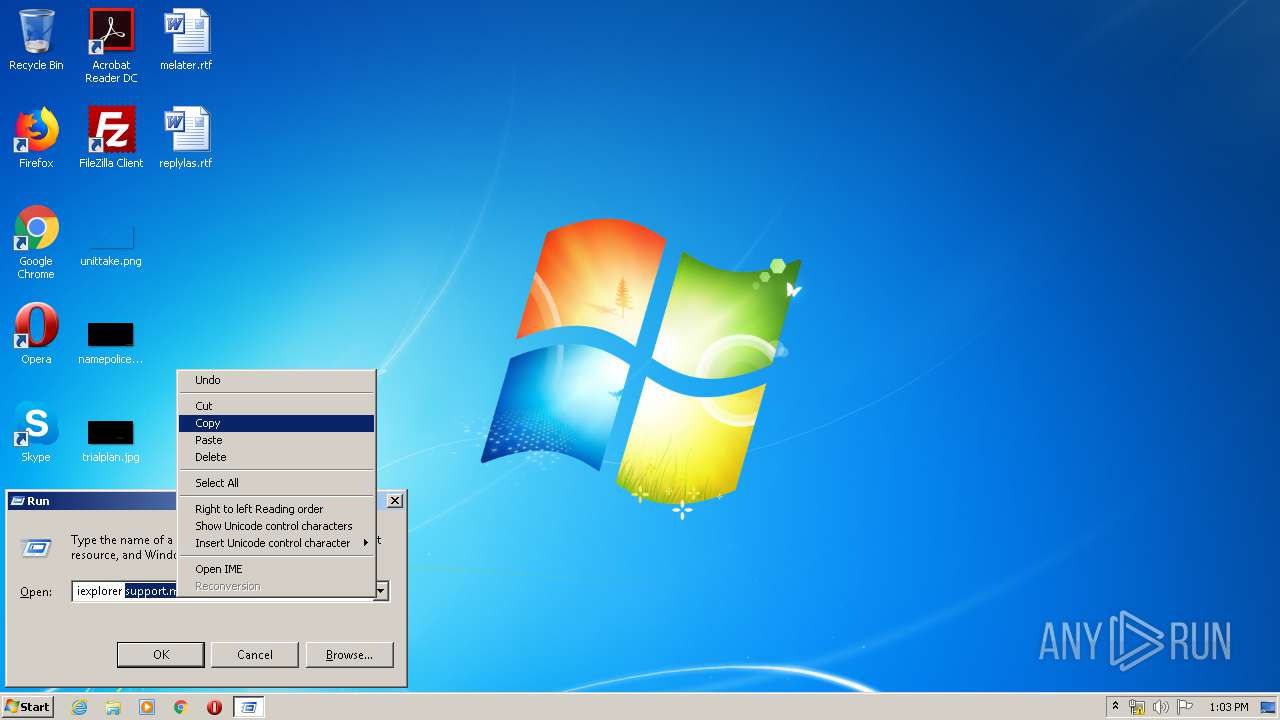
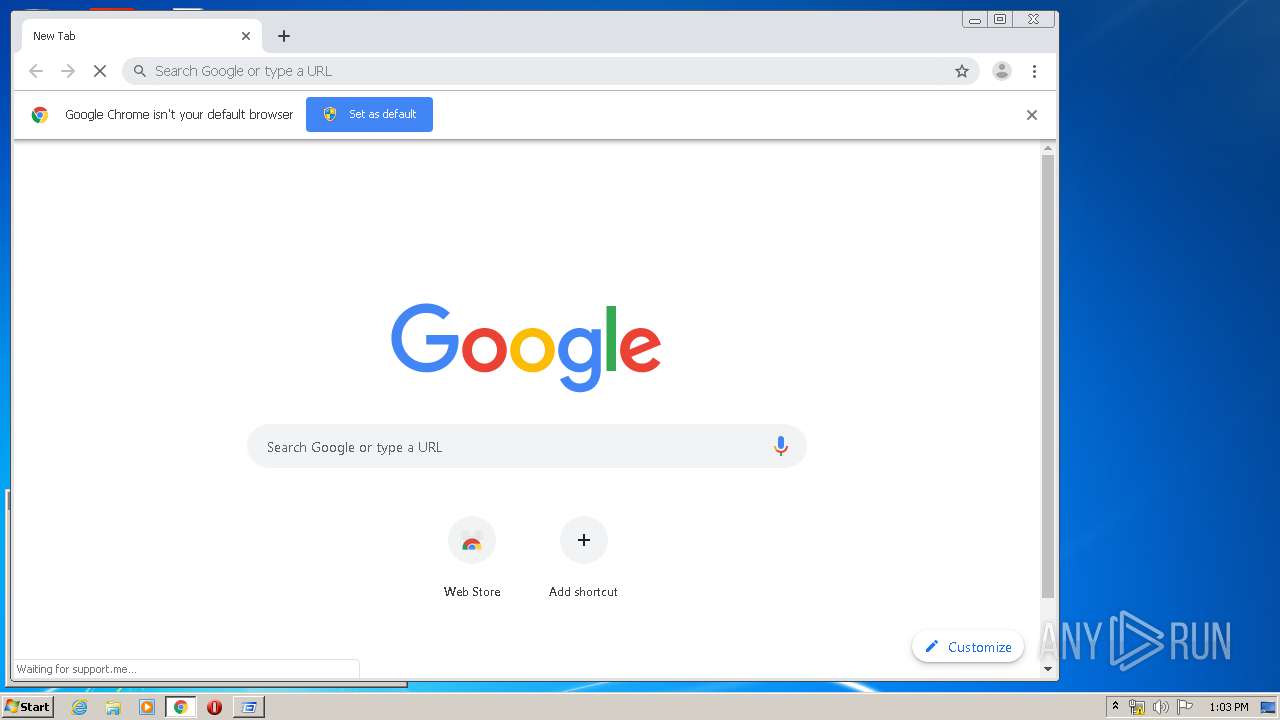
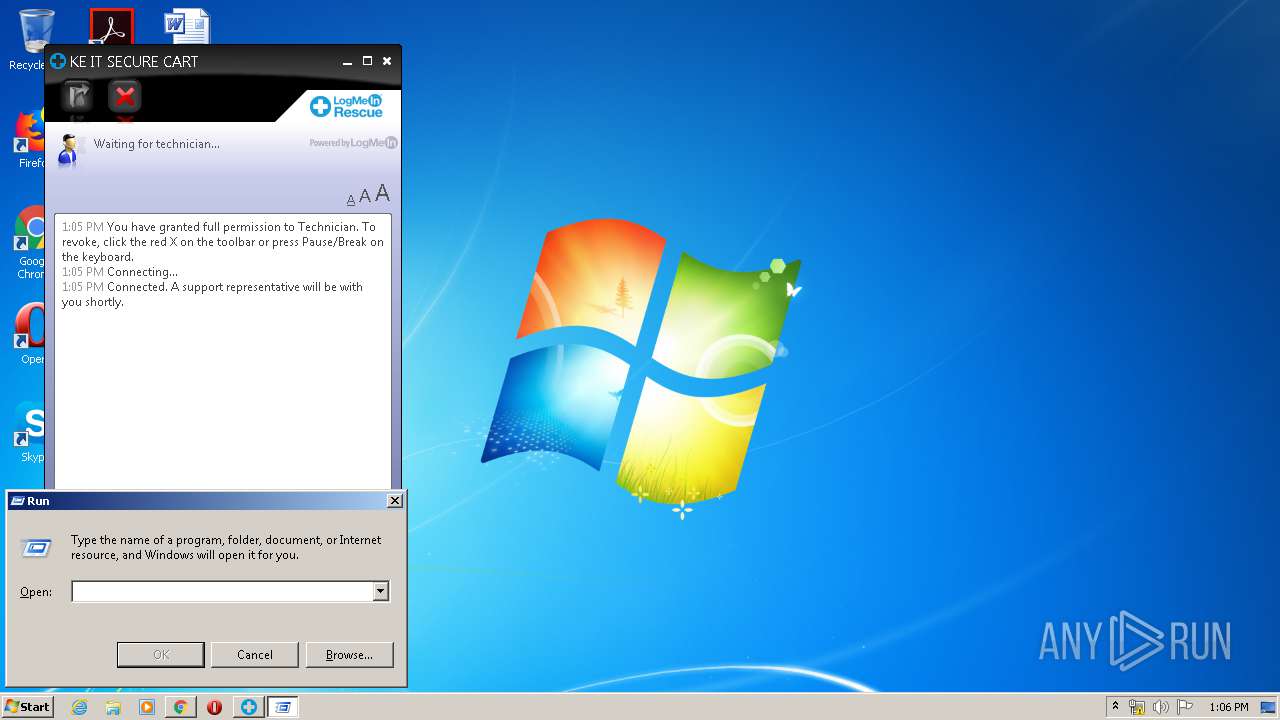
Manual execution by user
- chrome.exe (PID: 1872)
Reads the hosts file
- chrome.exe (PID: 1872)
- chrome.exe (PID: 2192)
Reads settings of System Certificates
- chrome.exe (PID: 2192)
- LMI_Rescue_srv.exe (PID: 620)
- LMI_Rescue_srv.exe (PID: 1084)
- chrome.exe (PID: 1872)
Reads Internet Cache Settings
- chrome.exe (PID: 1872)
Application launched itself
- chrome.exe (PID: 1872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:04:01 06:27:07+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 5120 |
| InitializedDataSize: | 100352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x152f |
| OSVersion: | 6.2 |
| ImageVersion: | 6.2 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.4.3528.331 |
| ProductVersionNumber: | 16.4.3528.331 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Movie Maker |
| FileVersion: | 16.4.3528.0331_ship.client.main.w5m4 (ship) |
| InternalName: | Movie Maker |
| LegalCopyright: | © 2012 Microsoft Corporation. All rights reserved. |
| OriginalFileName: | MovieMaker.EXE |
| ProductName: | Movie Maker |
| ProductVersion: | 16.4.3528.0331 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Apr-2014 04:27:07 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Movie Maker |
| FileVersion: | 16.4.3528.0331_ship.client.main.w5m4 (ship) |
| InternalName: | Movie Maker |
| LegalCopyright: | © 2012 Microsoft Corporation. All rights reserved. |
| OriginalFilename: | MovieMaker.EXE |
| ProductName: | Movie Maker |
| ProductVersion: | 16.4.3528.0331 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 01-Apr-2014 04:27:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000012F0 | 0x00001400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.74263 |
.data | 0x00003000 | 0x00000398 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.364514 |
.rsrc | 0x00004000 | 0x00017D60 | 0x00017E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.41585 |
.reloc | 0x0001C000 | 0x0000057A | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.24203 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07176 | 1203 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.59788 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 4.09517 | 1736 | UNKNOWN | English - United States | RT_ICON |
4 | 3.45441 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 7.96976 | 68162 | UNKNOWN | English - United States | RT_ICON |
6 | 5.23281 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 5.46711 | 4264 | UNKNOWN | English - United States | RT_ICON |
8 | 5.53081 | 2440 | UNKNOWN | English - United States | RT_ICON |
9 | 5.5061 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.8825 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
MSVCR110.dll |
MovieMakerCore.dll (delay-loaded) |
WLXPhotoBase.dll |
Total processes
84
Monitored processes
46
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,6715642771058305427,812780373404974156,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13066695988998910164 --mojo-platform-channel-handle=3312 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,6715642771058305427,812780373404974156,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=580946655128952189 --mojo-platform-channel-handle=4088 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,6715642771058305427,812780373404974156,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8881713081215694460 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 492 | C:\Windows\system32\lsm.exe | C:\Windows\System32\lsm.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Session Manager Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,6715642771058305427,812780373404974156,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1335907415985887674 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
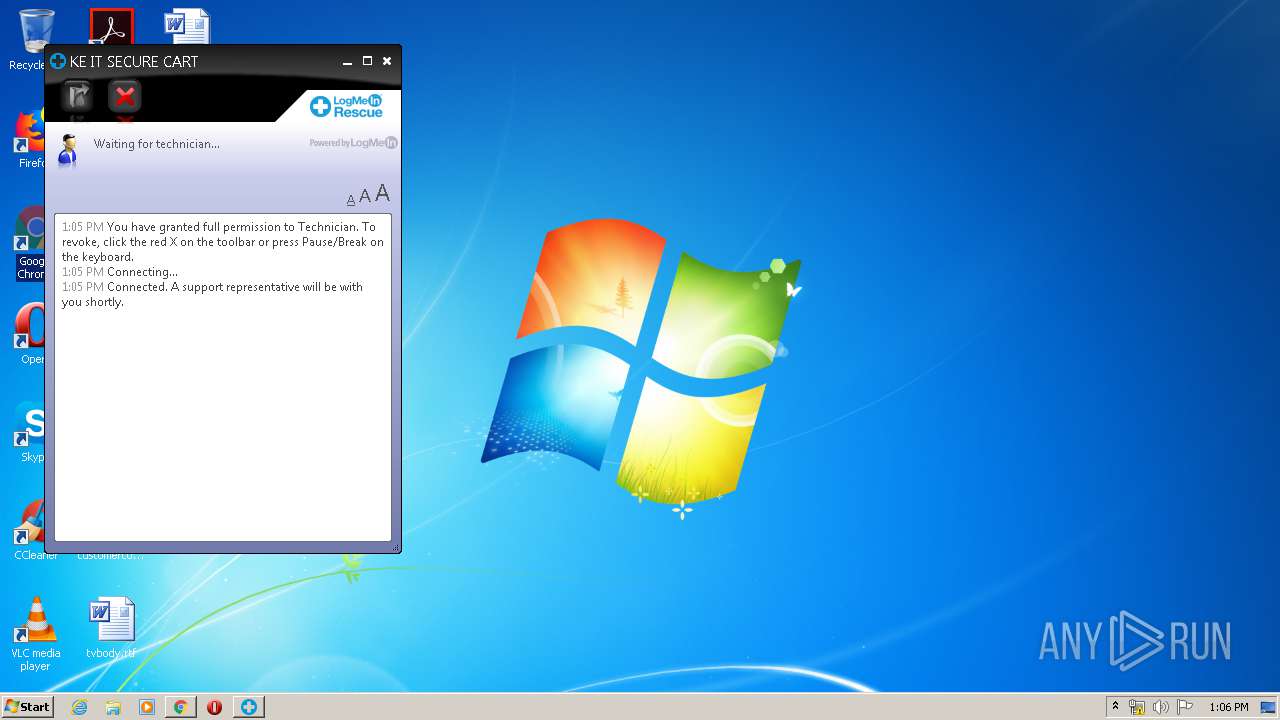
| 620 | "C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0B82C001.tmp\LMI_Rescue_srv.exe" -wd "C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0B82C001.tmp" | C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0B82C001.tmp\LMI_Rescue_srv.exe | LMI_Rescue.exe | ||||||||||||
User: admin Company: LogMeIn, Inc. Integrity Level: MEDIUM Description: LogMeIn Rescue Exit code: 1 Version: 7.14.420 Modules
| |||||||||||||||
| 652 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1084 | "C:\Program Files\LogMeIn Rescue Applet\LMIR0B85D001.tmp\LMI_Rescue_srv.exe" -service -sid 0a5f238b-8991-7fcf-6579-ef903c894c63 -wd "C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0B82C001.tmp\\" | C:\Program Files\LogMeIn Rescue Applet\LMIR0B85D001.tmp\LMI_Rescue_srv.exe | services.exe | ||||||||||||
User: SYSTEM Company: LogMeIn, Inc. Integrity Level: SYSTEM Description: LogMeIn Rescue Exit code: 0 Version: 7.14.420 Modules
| |||||||||||||||
| 1544 | "C:\Users\admin\Downloads\Support-LogMeInRescue.exe" | C:\Users\admin\Downloads\Support-LogMeInRescue.exe | chrome.exe | ||||||||||||
User: admin Company: LogMeIn, Inc. Integrity Level: MEDIUM Description: LogMeIn Rescue Exit code: 0 Version: 7.14.420 Modules
| |||||||||||||||
Total events
3 957
Read events
1 581
Write events
2 370
Delete events
6
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @"%windir%\System32\ie4uinit.exe",-738 |
Value: Start Internet Explorer without ActiveX controls or browser extensions. | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%windir%\explorer.exe,-7003 |
Value: Opens a program, folder, document, or web site. | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.lnk\OpenWithProgids |
| Operation: | write | Name: | lnkfile |
Value: | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Zvpebfbsg.Jvaqbjf.Furyy.EhaQvnybt |
Value: 0000000000000000000000006BE30000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003F0000004F000000C89626000A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED01 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Zvpebfbsg.Jvaqbjf.Furyy.EhaQvnybt |
Value: 0000000000000000010000006BE30000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003F00000050000000C89626000A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED01 | |||
| (PID) Process: | (1872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
27
Suspicious files
236
Text files
299
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E6F7935-750.pma | — | |
MD5:— | SHA256:— | |||
| 1872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d80076ed-5078-4e93-80e9-834cfd01bf13.tmp | — | |
MD5:— | SHA256:— | |||
| 1872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 372 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 1872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa7c8b2.TMP | text | |
MD5:— | SHA256:— | |||
| 1872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa7c8b2.TMP | text | |
MD5:— | SHA256:— | |||
| 1872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
64
DNS requests
35
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3320 | consent.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | US | der | 471 b | whitelisted |
2192 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
2192 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3320 | consent.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAd33SHPXcnceFrLrioCuyY%3D | US | der | 471 b | whitelisted |
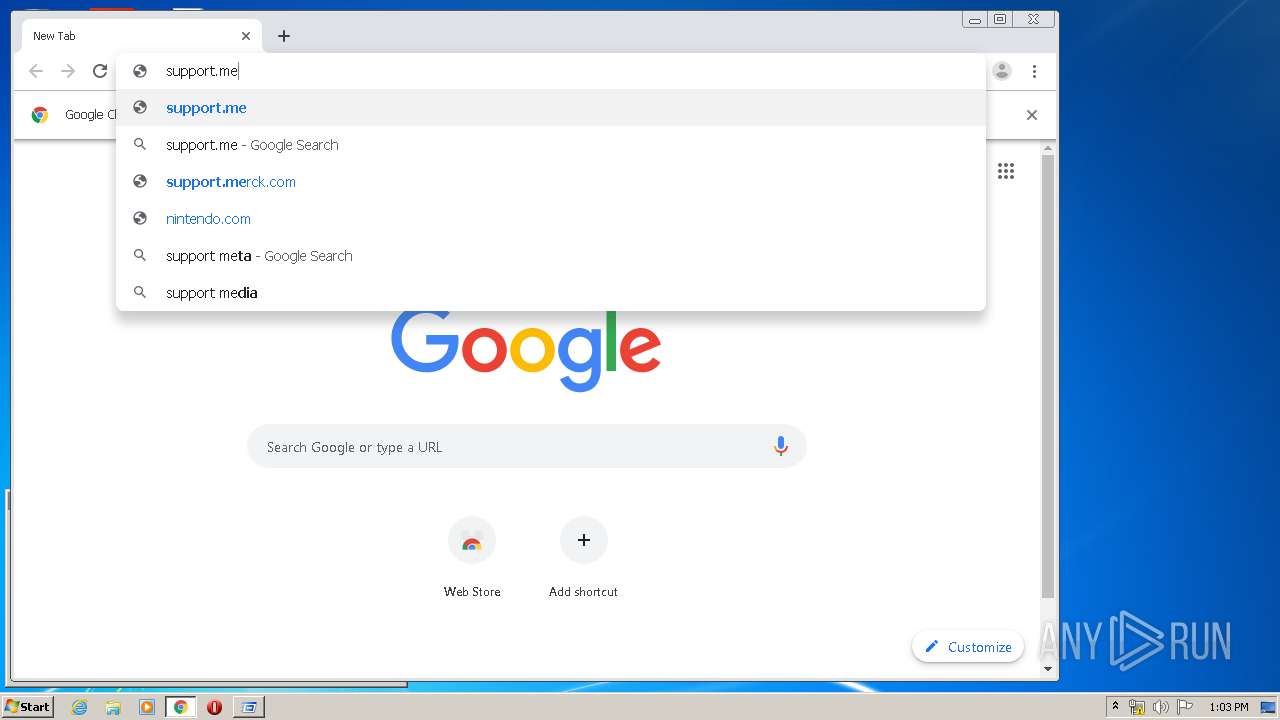
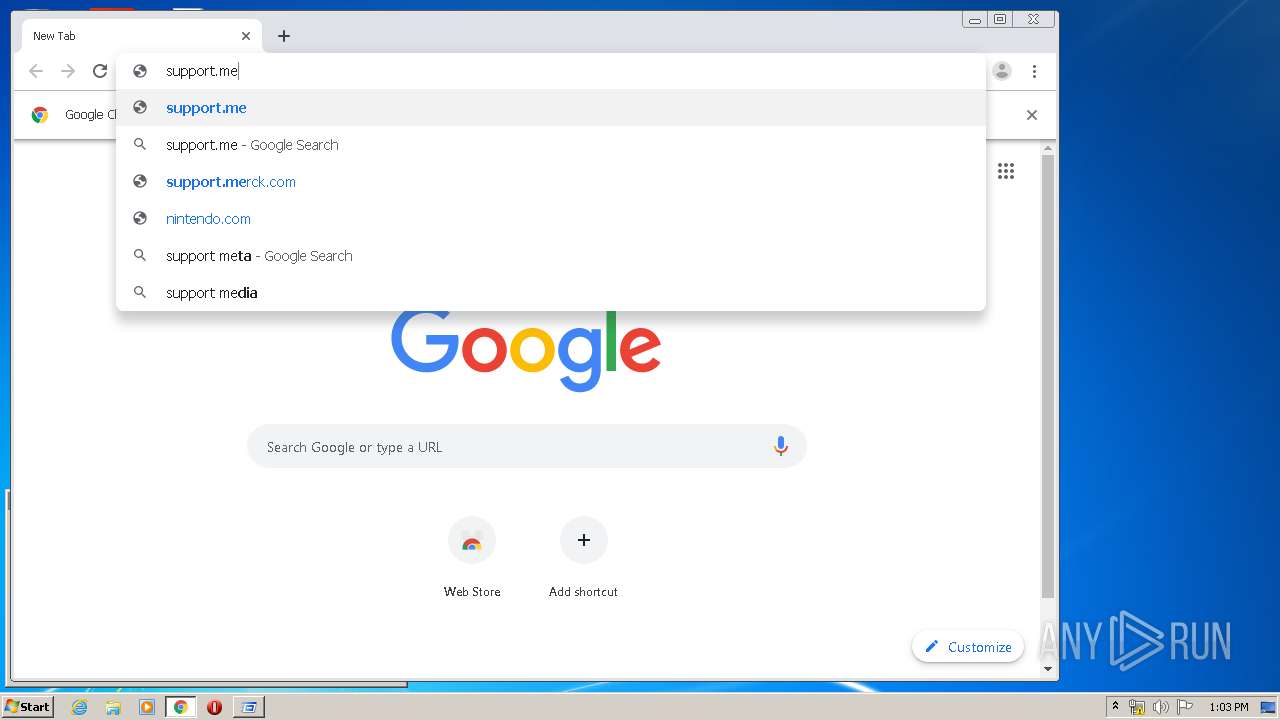
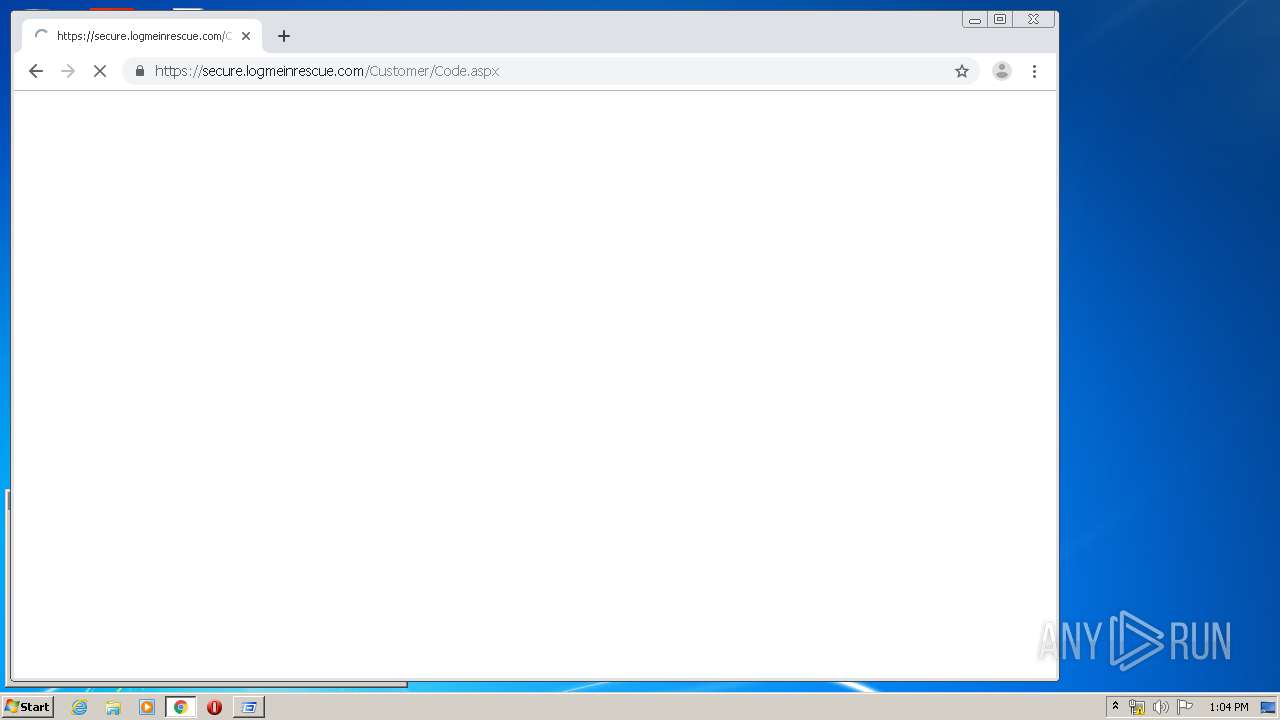
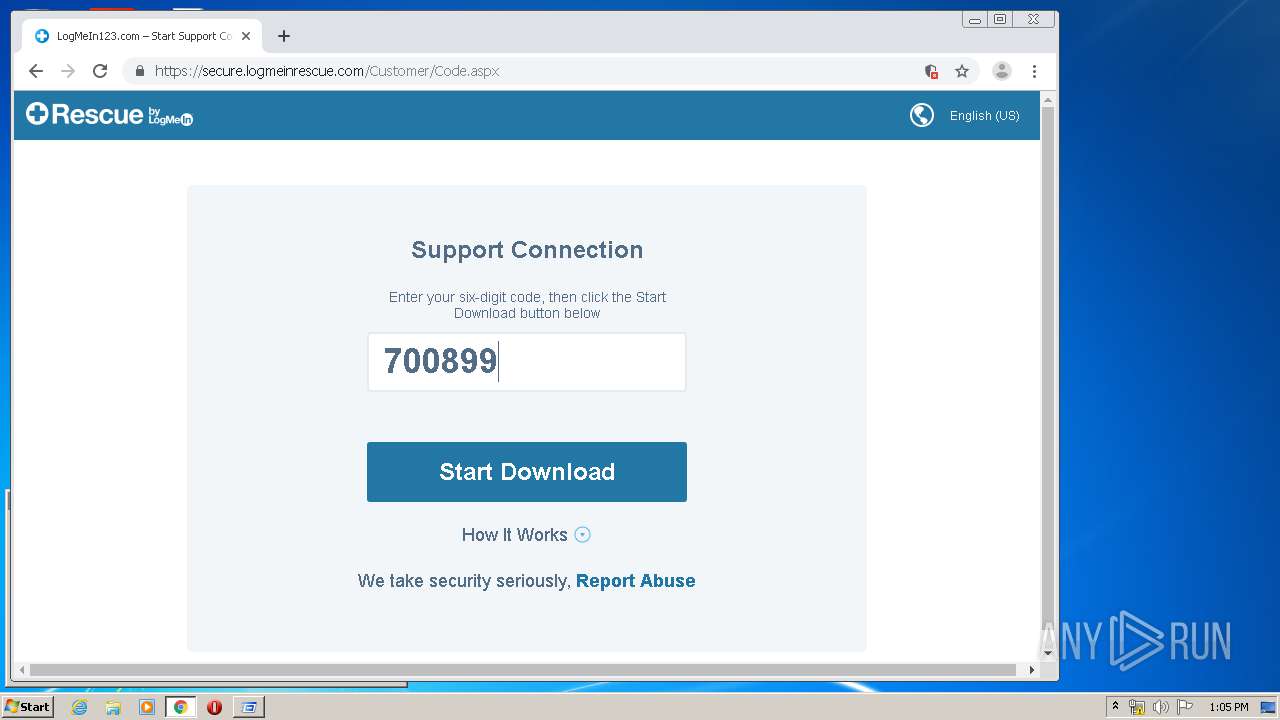
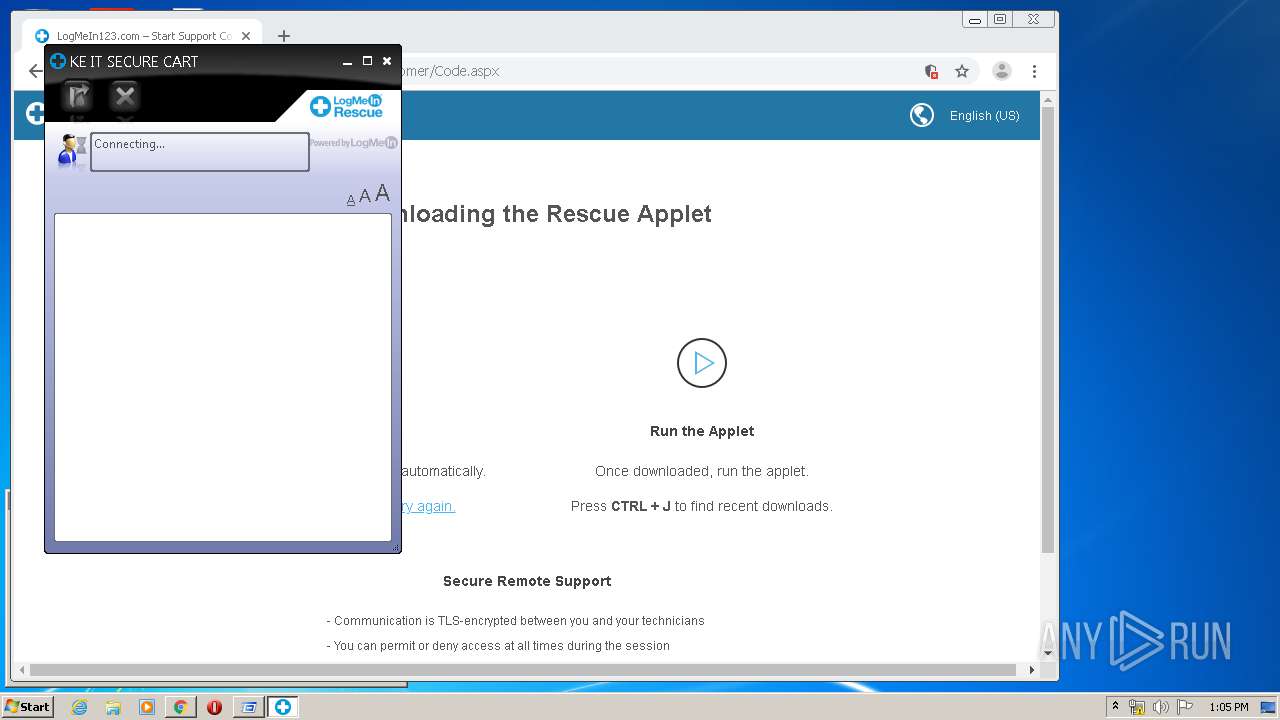
2192 | chrome.exe | GET | 301 | 40.68.205.178:80 | http://support.me/ | NL | html | 142 b | whitelisted |
2192 | chrome.exe | GET | 200 | 173.194.182.136:80 | http://r3---sn-hpa7znsz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=82.102.21.136&mm=28&mn=sn-hpa7znsz&ms=nvh&mt=1584363799&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2192 | chrome.exe | GET | 200 | 74.125.99.91:80 | http://r5---sn-hpa7kn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=82.102.21.136&mm=28&mn=sn-hpa7kn7s&ms=nvh&mt=1584363737&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2192 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2192 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2192 | chrome.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2192 | chrome.exe | 172.217.22.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2192 | chrome.exe | 172.217.23.142:443 | apis.google.com | Google Inc. | US | whitelisted |
2192 | chrome.exe | 172.217.18.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2192 | chrome.exe | 172.217.21.238:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
— | — | 172.217.21.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2192 | chrome.exe | 40.68.205.178:80 | support.me | Microsoft Corporation | NL | unknown |
2192 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
support.me |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
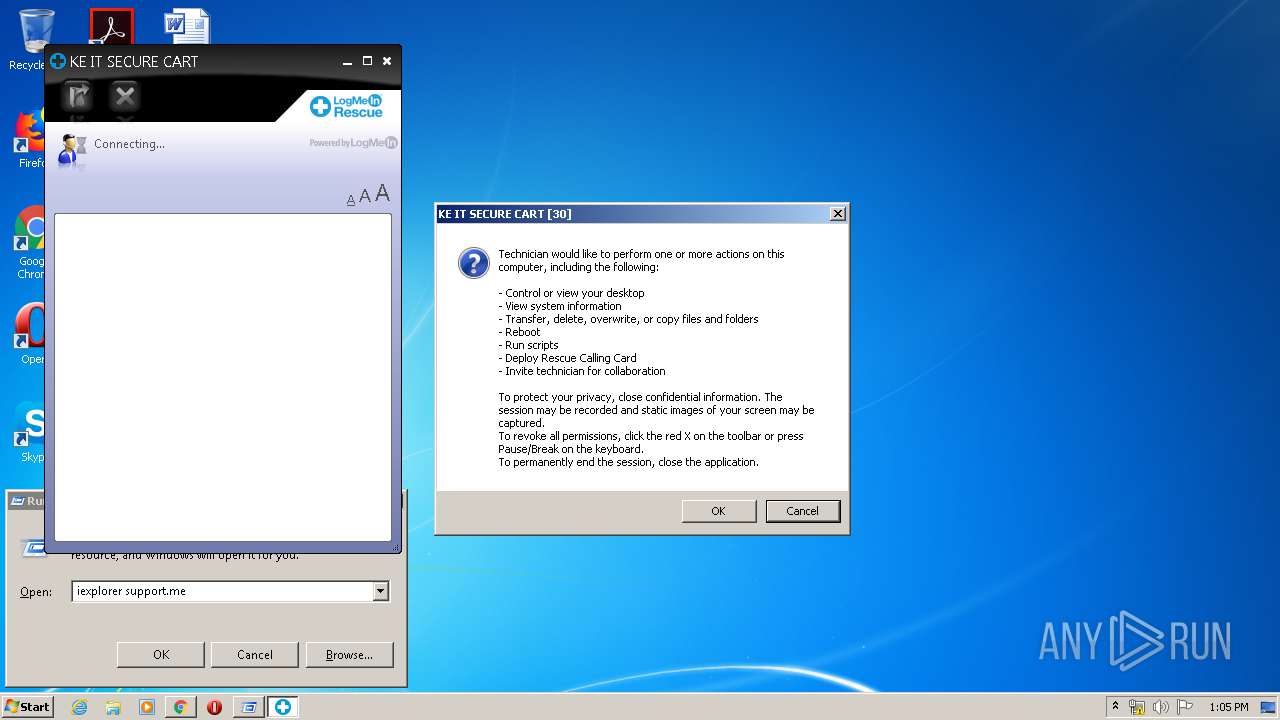
620 | LMI_Rescue_srv.exe | Potential Corporate Privacy Violation | ET POLICY Logmein.com/Join.me SSL Remote Control Access |
620 | LMI_Rescue_srv.exe | Potential Corporate Privacy Violation | ET POLICY Logmein.com/Join.me SSL Remote Control Access |
620 | LMI_Rescue_srv.exe | Potential Corporate Privacy Violation | ET POLICY Logmein.com/Join.me SSL Remote Control Access |
620 | LMI_Rescue_srv.exe | Potential Corporate Privacy Violation | ET POLICY Logmein.com/Join.me SSL Remote Control Access |
620 | LMI_Rescue_srv.exe | Potential Corporate Privacy Violation | ET POLICY Logmein.com/Join.me SSL Remote Control Access |
620 | LMI_Rescue_srv.exe | Potential Corporate Privacy Violation | ET POLICY Logmein.com/Join.me SSL Remote Control Access |
1084 | LMI_Rescue_srv.exe | Potential Corporate Privacy Violation | ET POLICY Logmein.com/Join.me SSL Remote Control Access |
1084 | LMI_Rescue_srv.exe | Potential Corporate Privacy Violation | ET POLICY Logmein.com/Join.me SSL Remote Control Access |
1084 | LMI_Rescue_srv.exe | Potential Corporate Privacy Violation | ET POLICY Logmein.com/Join.me SSL Remote Control Access |
1084 | LMI_Rescue_srv.exe | Potential Corporate Privacy Violation | ET POLICY Logmein.com/Join.me SSL Remote Control Access |
Process | Message |
|---|---|
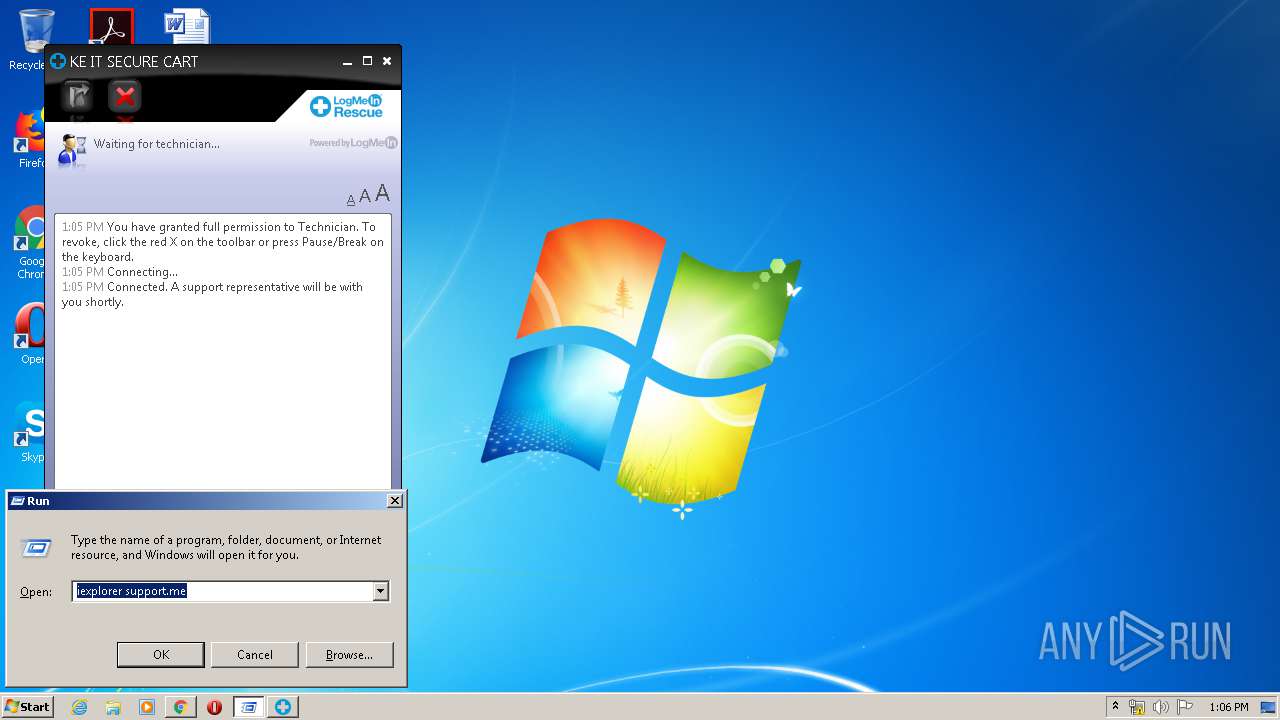
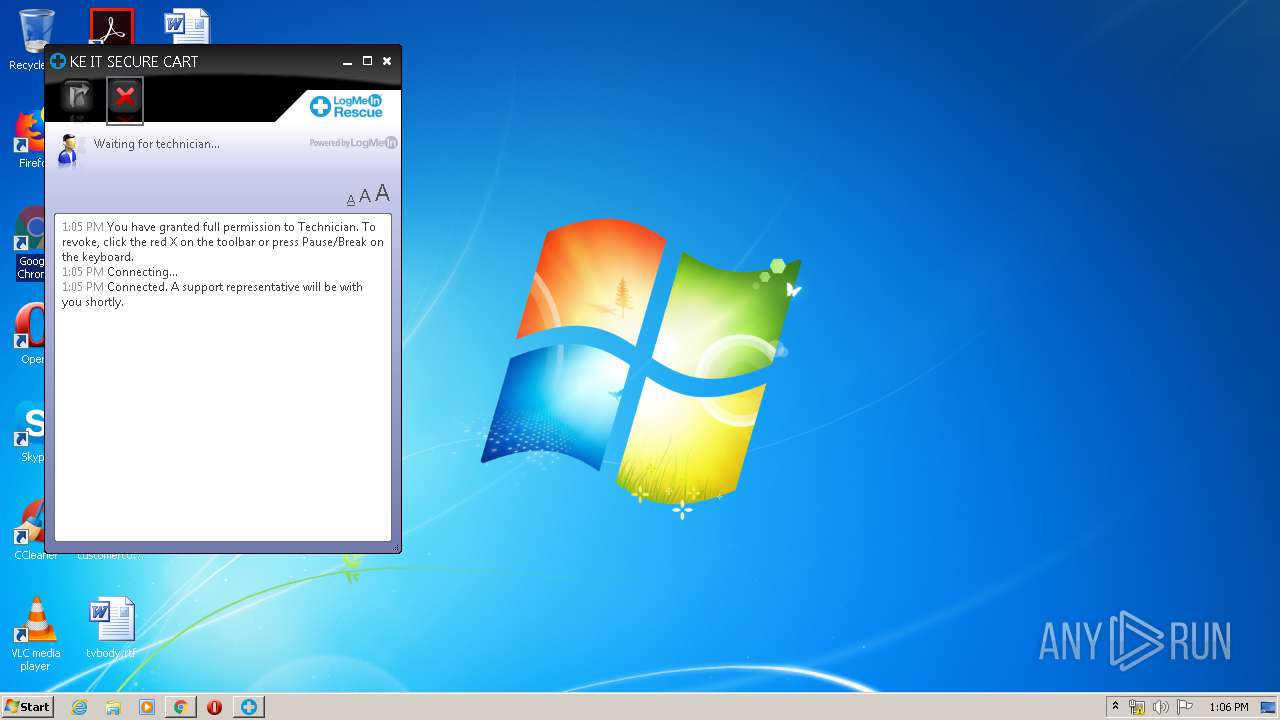
LMI_Rescue.exe | 2020-03-16 13:05:49.655 - Info - GUI:0A10 - Main - [0x00000fb4] Main - ======== STARTED 7.14.420.2233 ========
|
LMI_Rescue.exe | 2020-03-16 13:05:49.655 - Info - GUI:0A10 - Main - [0x00000fb4] Main - WritePath: C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0B82C001.tmp\
|
LMI_Rescue.exe | 2020-03-16 13:05:49.655 - Info - GUI:0A10 - Main - [0x00000fb4] Main - Binary: C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0B82C001.tmp\LMI_Rescue.exe
|
LMI_Rescue.exe | 2020-03-16 13:05:49.671 - Info - GUI:0A10 - InitUserInfo - [0x00000fb4] Main - Name: admin; Domain: USER-PC
|
LMI_Rescue.exe | 2020-03-16 13:05:49.671 - Error - GUI:0A10 - Main - [0x00000fb4] Main - SetProcessShutdownParameters failed. The operation completed successfully. (0)
|
LMI_Rescue.exe | 2020-03-16 13:05:49.671 - Info - GUI:0A10 - Main - [0x00000fb4] Main - IPC connection ID: (0a5f238b89917fcf6579ef903c894c63)
|
LMI_Rescue.exe | 2020-03-16 13:05:49.816 - Info - GUI:0A10 - Proxy - [0x00000fb4] Main - Initialization: Use OS settings
|
LMI_Rescue.exe | 2020-03-16 13:05:49.815 - Info - GUI:0A10 - CreateSecurityDescriptor - [0x00000fb4] Main - Set privilege fail.
|
LMI_Rescue.exe | 2020-03-16 13:05:49.815 - Info - GUI:0A10 - CreateSecurityDescriptor - [0x00000fb4] Main - Set privilege fail.
|
LMI_Rescue.exe | 2020-03-16 13:05:49.816 - Info - GUI:0A10 - Proxy - [0x00000fb4] Main - Initialization: First
|