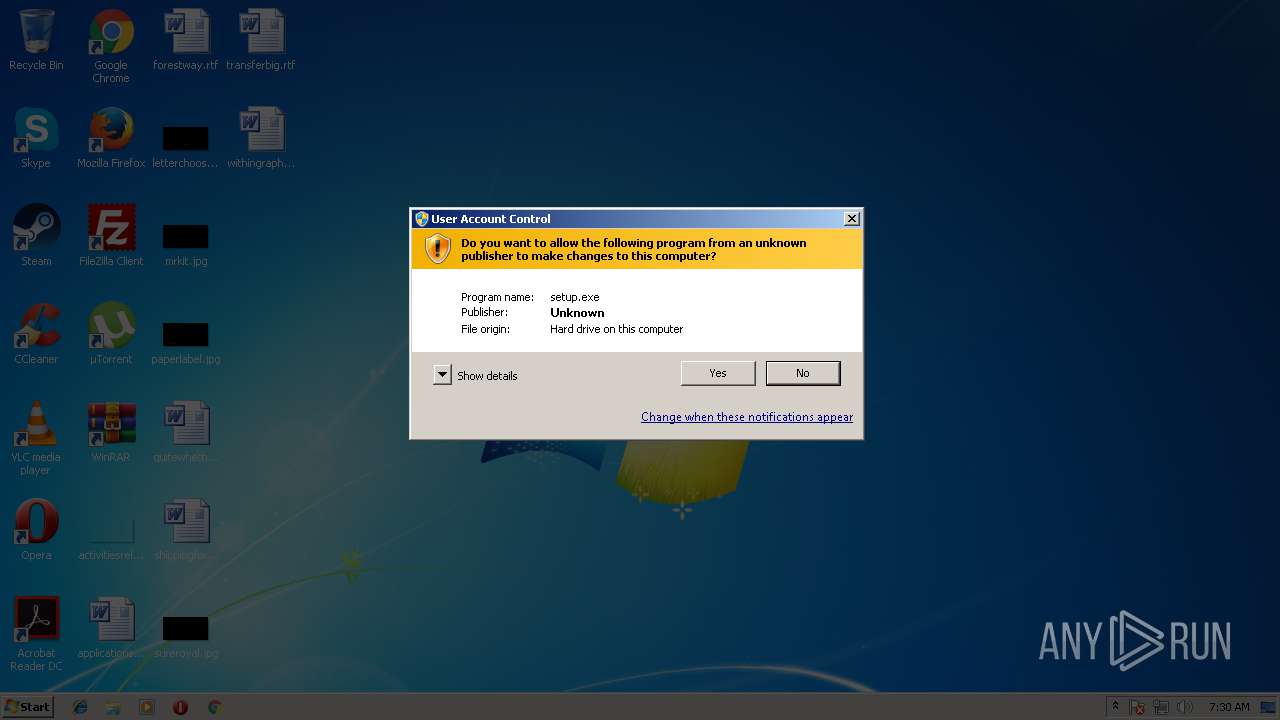
| download: | setup.exe |
| Full analysis: | https://app.any.run/tasks/944e0715-3815-470d-89a3-7e13ec54268e |
| Verdict: | Malicious activity |
| Analysis date: | August 21, 2018, 06:29:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 68A65A4EA1D8B741111E524F19B94870 |
| SHA1: | 1DD2A11061243D8EF449636B135748162EF64AB2 |
| SHA256: | 8BDC6C01E916F587D9264E906442A0B09965BD38DB19003412E9182653B05A3A |
| SSDEEP: | 786432:SDbLXvj1nbyxrSsFbdIpIAl3UtE2VH2b3BKC7:y/RbyJSkd7XVWb38C |
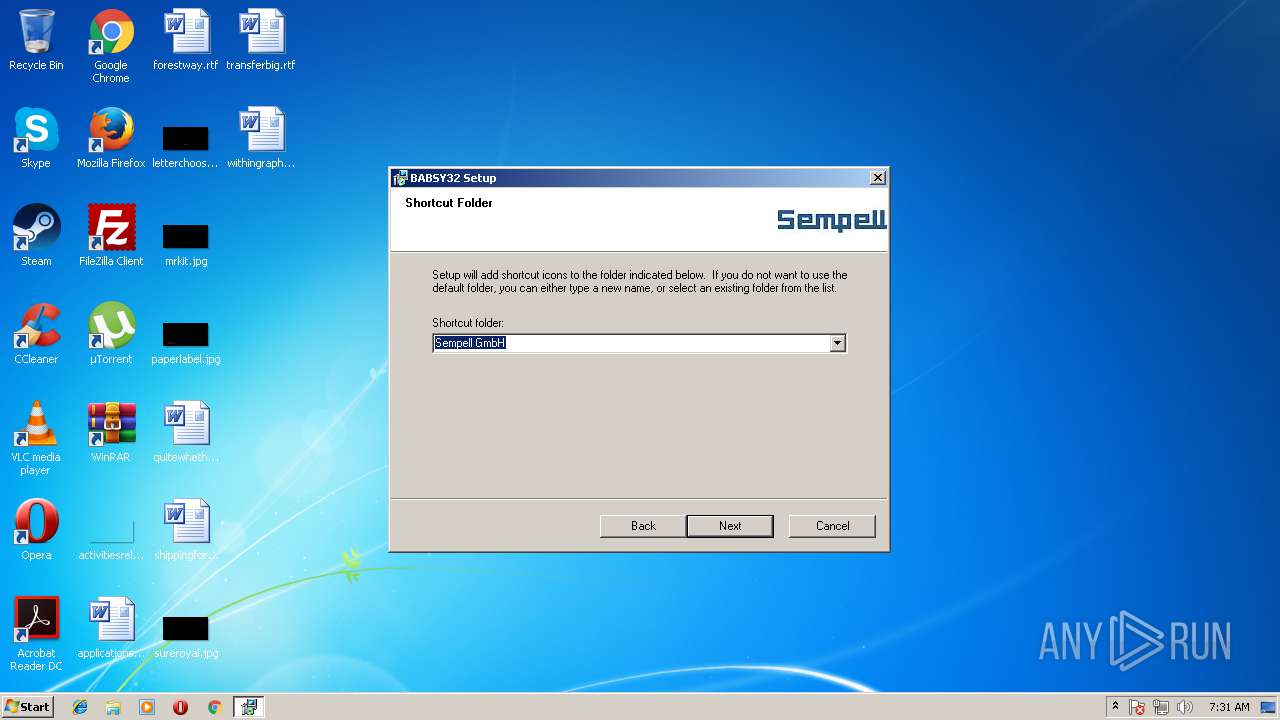
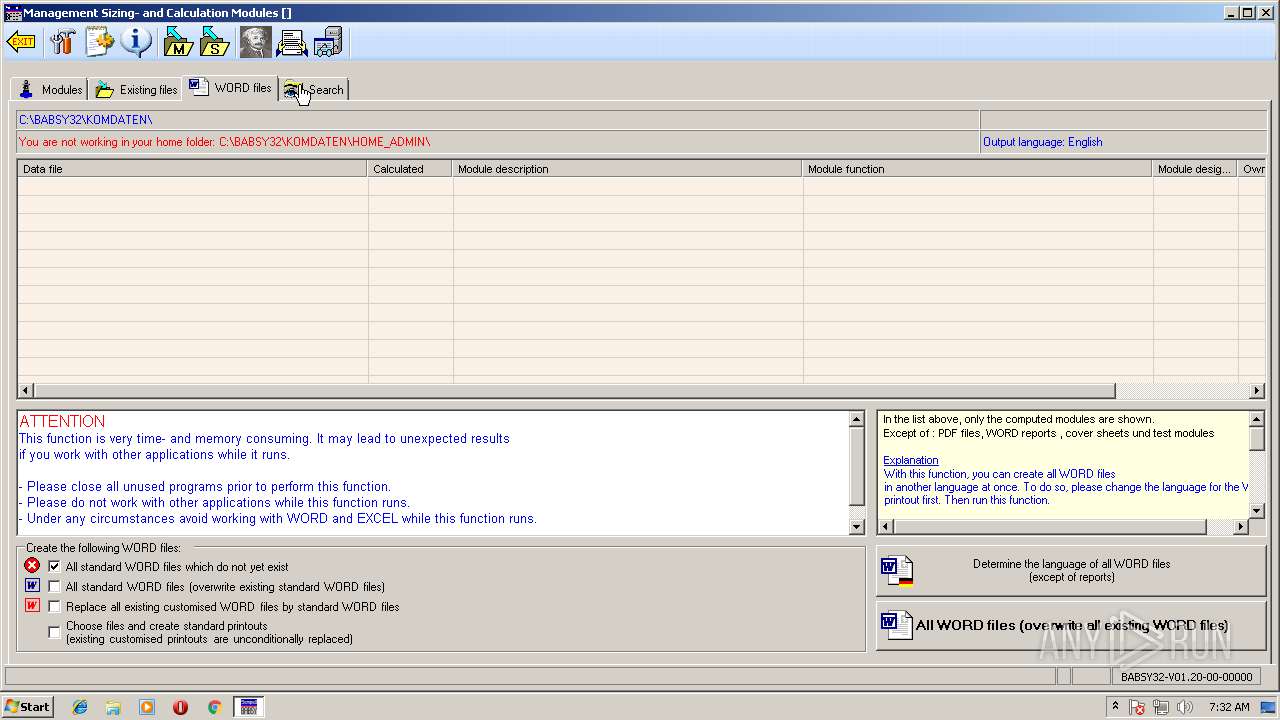
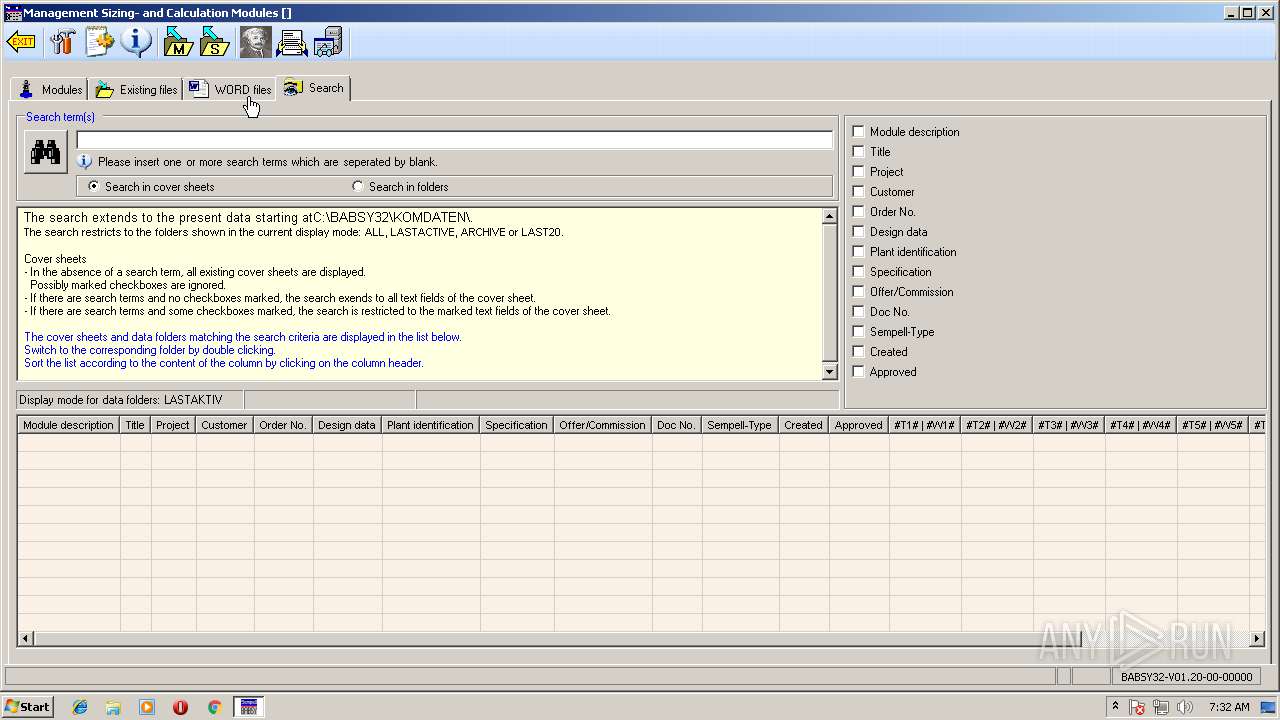
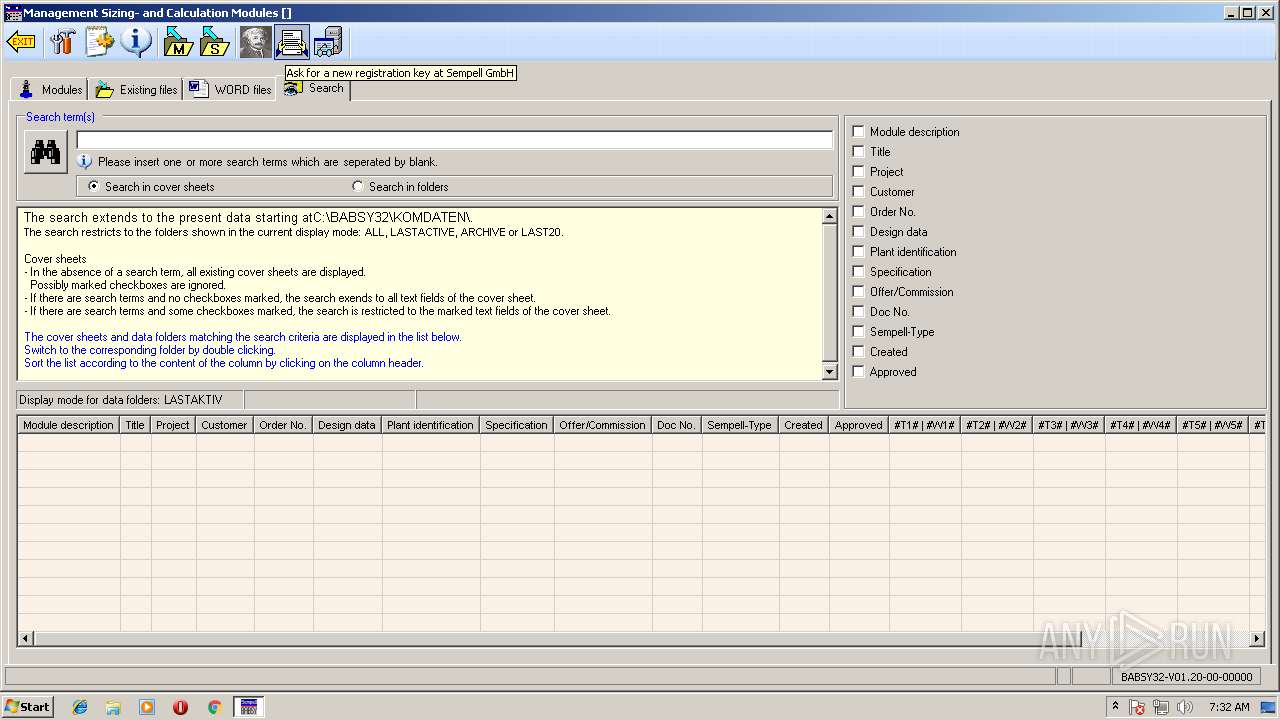
MALICIOUS
Application was dropped or rewritten from another process
- irsetup.exe (PID: 3348)
- BABSY32.EXE (PID: 1932)
Loads dropped or rewritten executable
- BABSY32.EXE (PID: 1932)
SUSPICIOUS
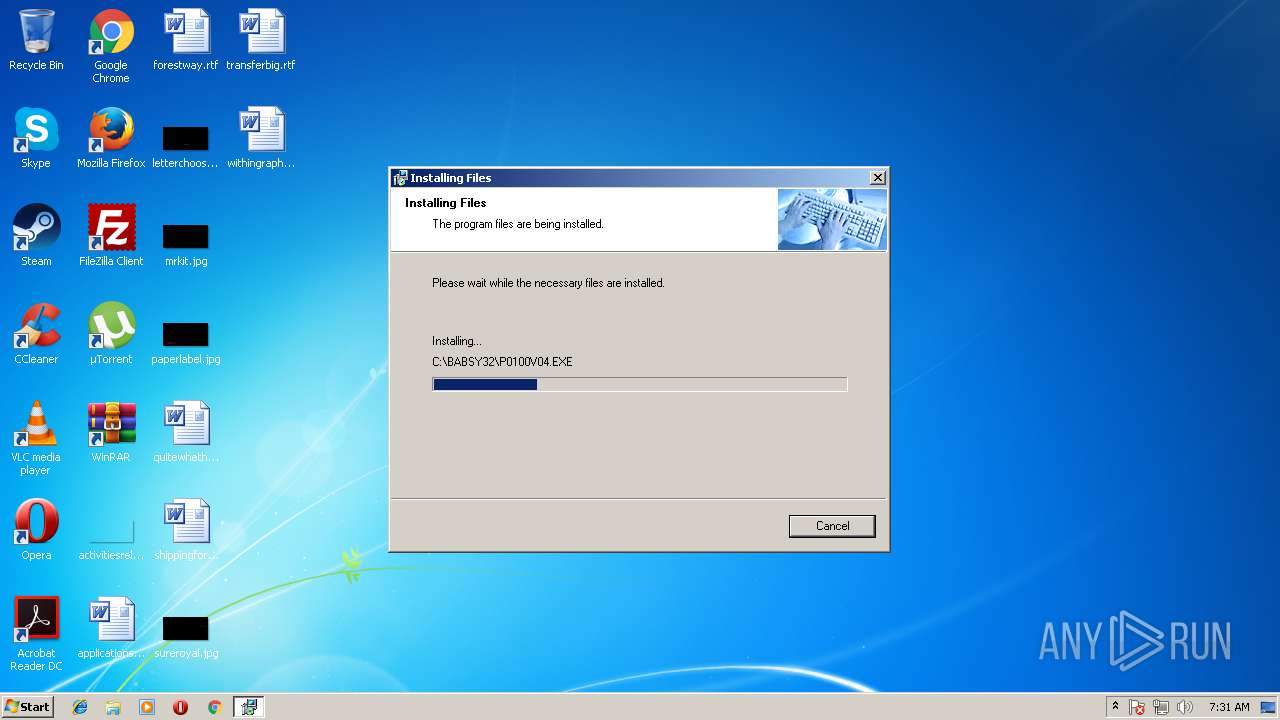
Executable content was dropped or overwritten
- setup.exe (PID: 3836)
- irsetup.exe (PID: 3348)
Creates files in the Windows directory
- irsetup.exe (PID: 3348)
Creates a software uninstall entry
- irsetup.exe (PID: 3348)
Creates files in the program directory
- irsetup.exe (PID: 3348)
INFO
Dropped object may contain Bitcoin addresses
- setup.exe (PID: 3836)
- irsetup.exe (PID: 3348)
Dropped object may contain URL's
- setup.exe (PID: 3836)
- BABSY32.EXE (PID: 1932)
- irsetup.exe (PID: 3348)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2452)
- BABSY32.EXE (PID: 1932)
- EXCEL.EXE (PID: 2824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (35.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (27) |
| .exe | | | Win64 Executable (generic) (23.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:09:23 21:04:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 20480 |
| InitializedDataSize: | 53248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2821 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.1.2 |
| ProductVersionNumber: | 6.0.1.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | This setup code is the property of Indigo Rose Corporation |
| CompanyName: | Indigo Rose Corporation http://www.indigorose.com |
| FileDescription: | Setup Factory 6.0 Setup Launcher |
| FileVersion: | 6.0.1.2 |
| InternalName: | setup |
| LegalCopyright: | Copyright © 2001 - 2002 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFileName: | setup.exe |
| PrivateBuild: | - |
| ProductName: | setup |
| ProductVersion: | 6.0.1.2 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Sep-2002 19:04:04 |
| Detected languages: |
|
| Comments: | This setup code is the property of Indigo Rose Corporation |
| CompanyName: | Indigo Rose Corporation http://www.indigorose.com |
| FileDescription: | Setup Factory 6.0 Setup Launcher |
| FileVersion: | 6.0.1.2 |
| InternalName: | setup |
| LegalCopyright: | Copyright © 2001 - 2002 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFilename: | setup.exe |
| PrivateBuild: | - |
| ProductName: | setup |
| ProductVersion: | 6.0.1.2 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 23-Sep-2002 19:04:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004065 | 0x00005000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.72103 |
.rdata | 0x00006000 | 0x00000C9C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.51368 |
.data | 0x00007000 | 0x00001E58 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.78384 |
.rsrc | 0x00009000 | 0x00009708 | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.86066 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.41904 | 1204 | UNKNOWN | English - United States | RT_VERSION |
101 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
102 | 2.40764 | 35336 | UNKNOWN | English - United States | RT_BITMAP |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
43
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
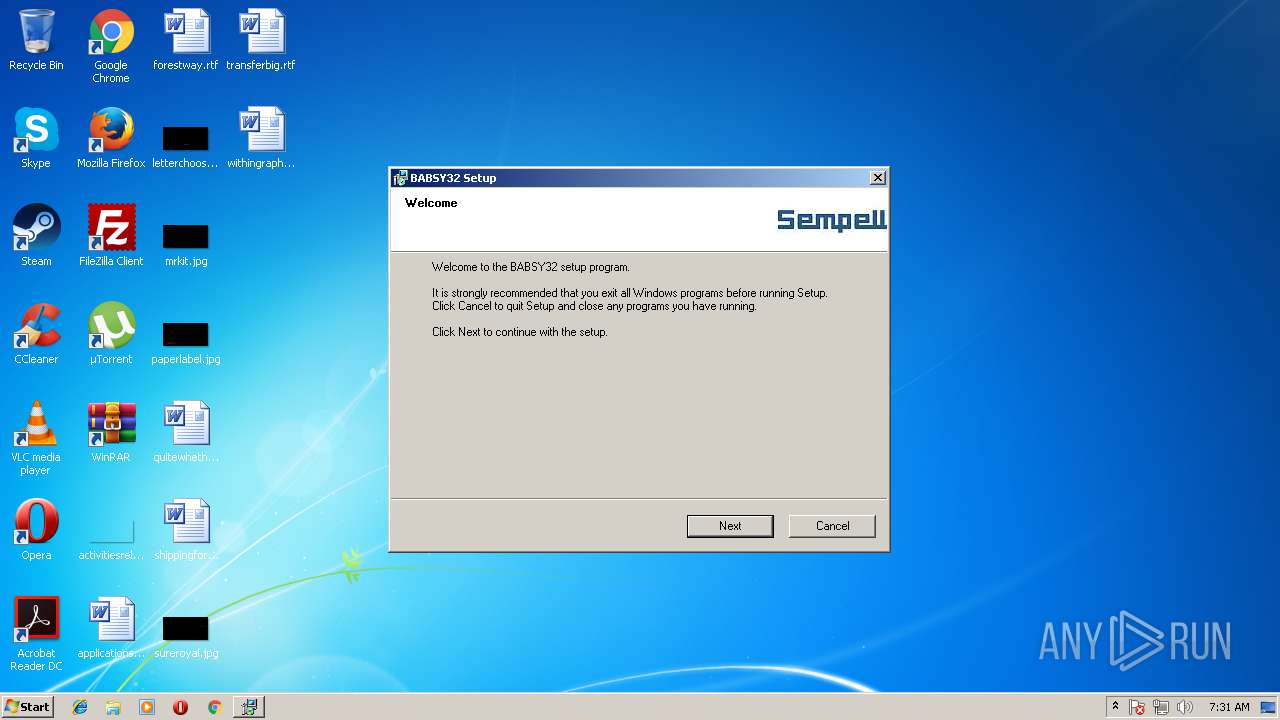
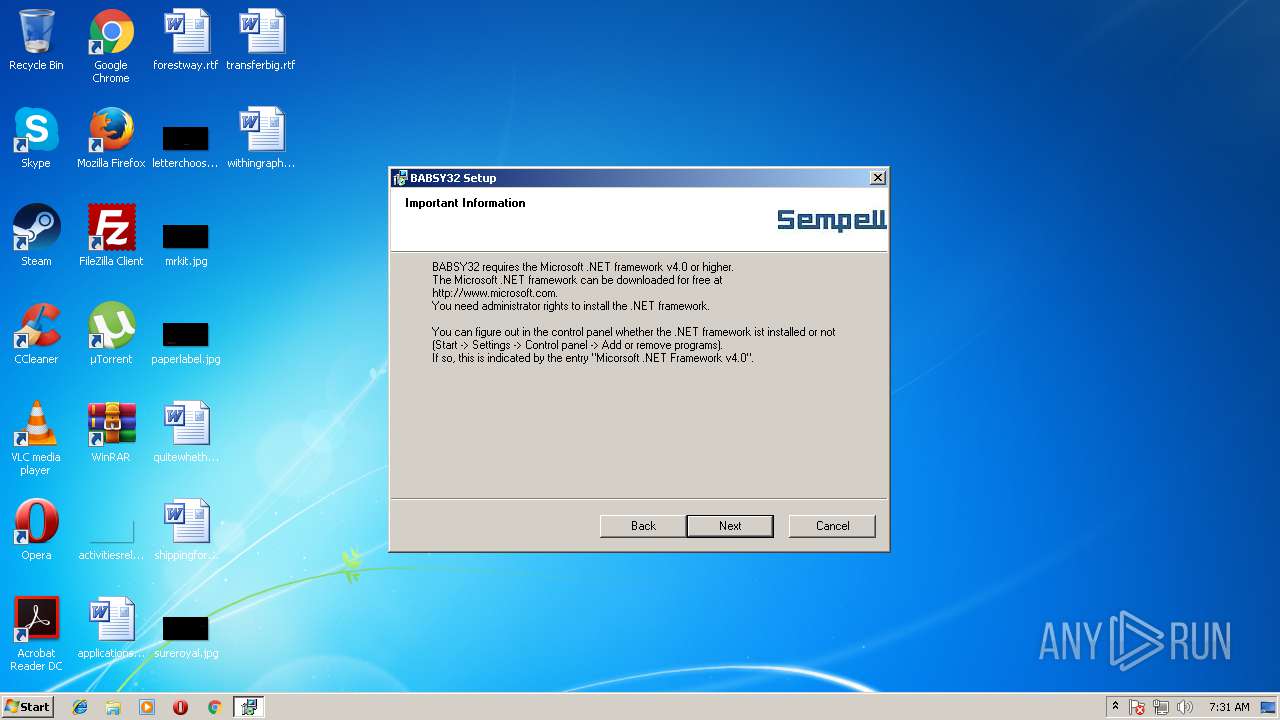
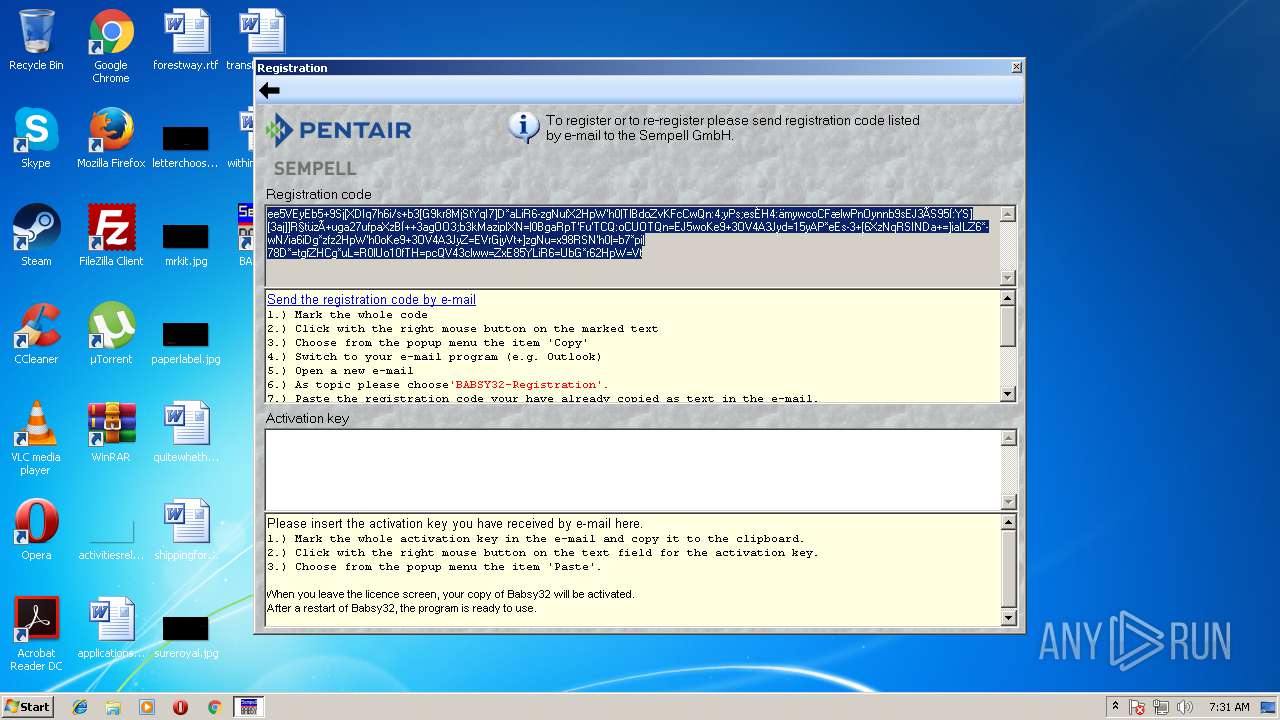
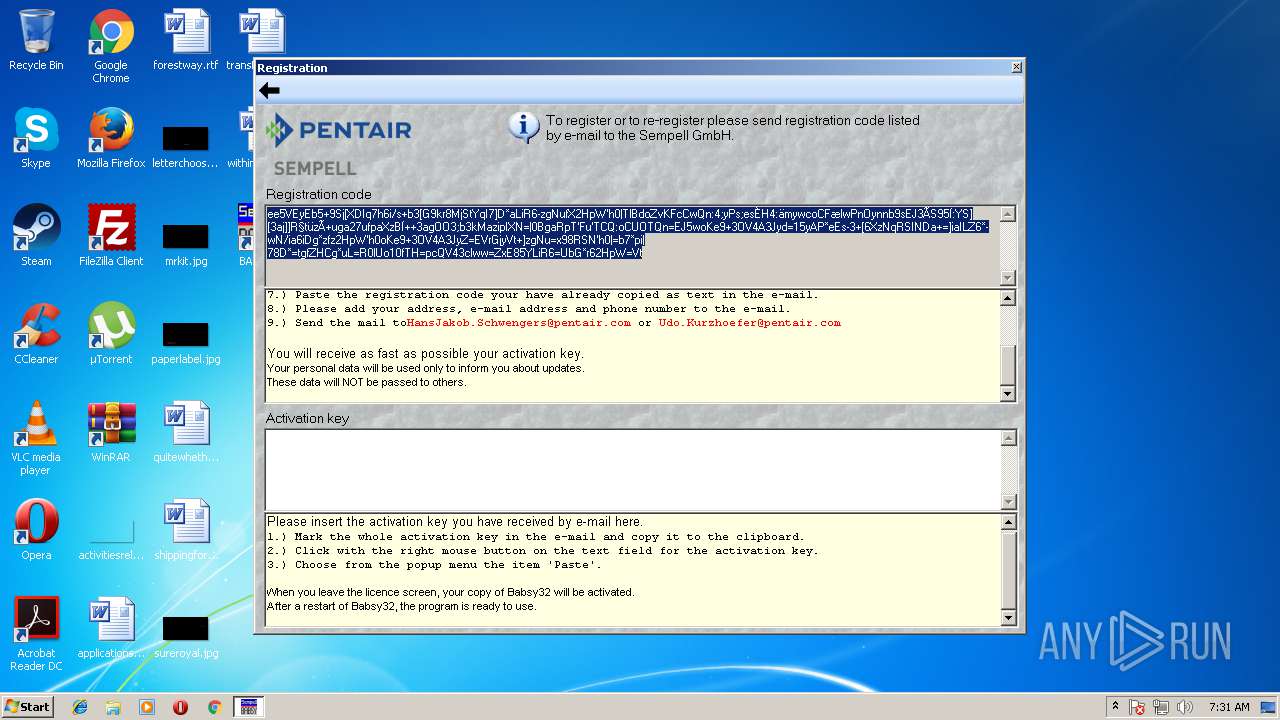
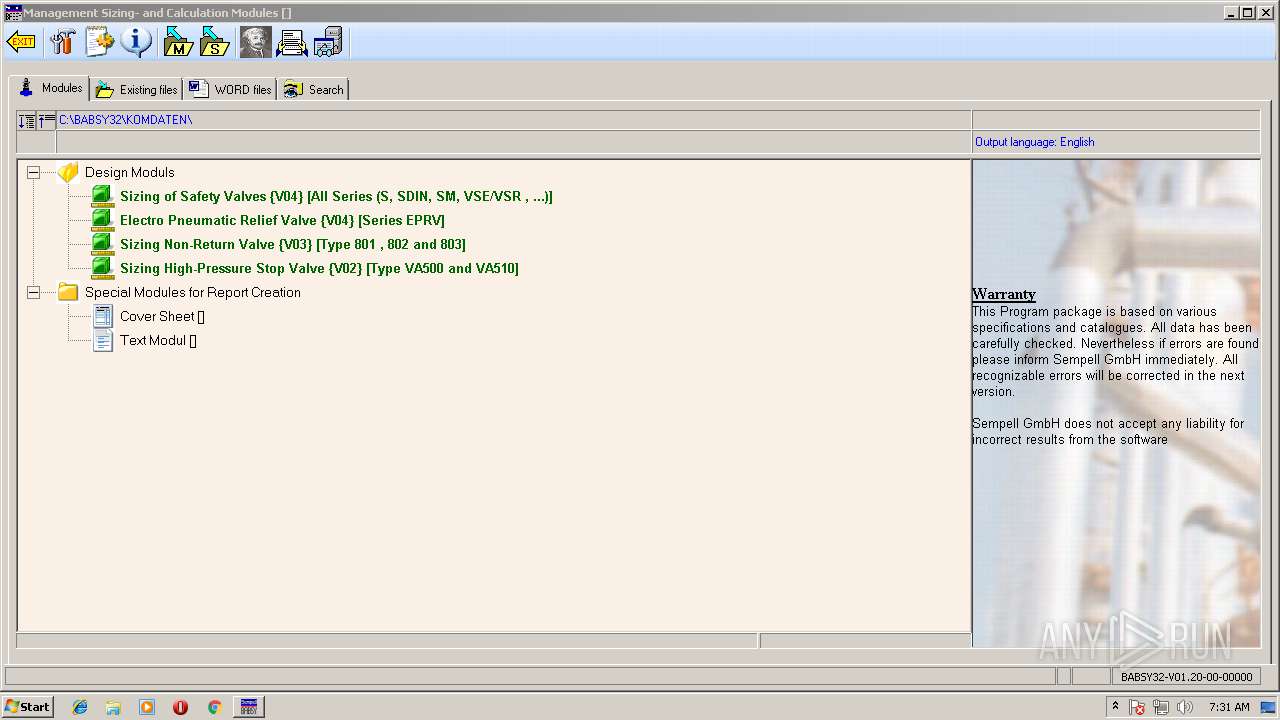
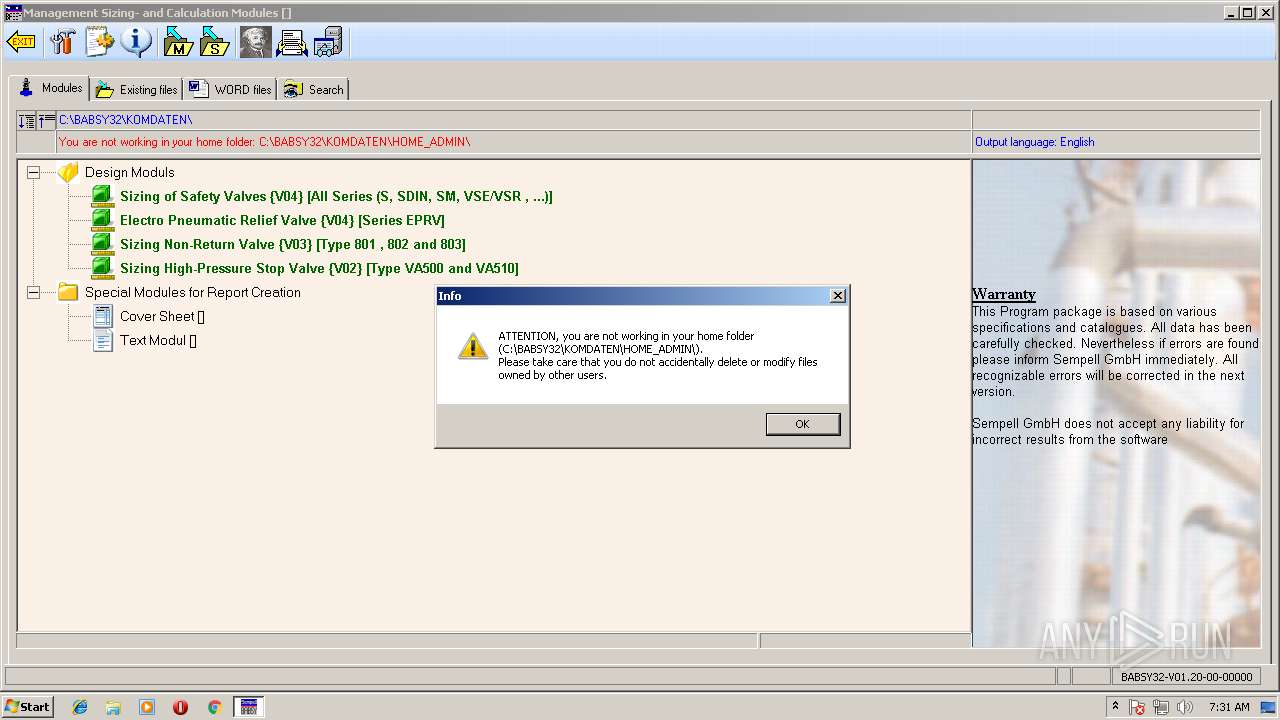
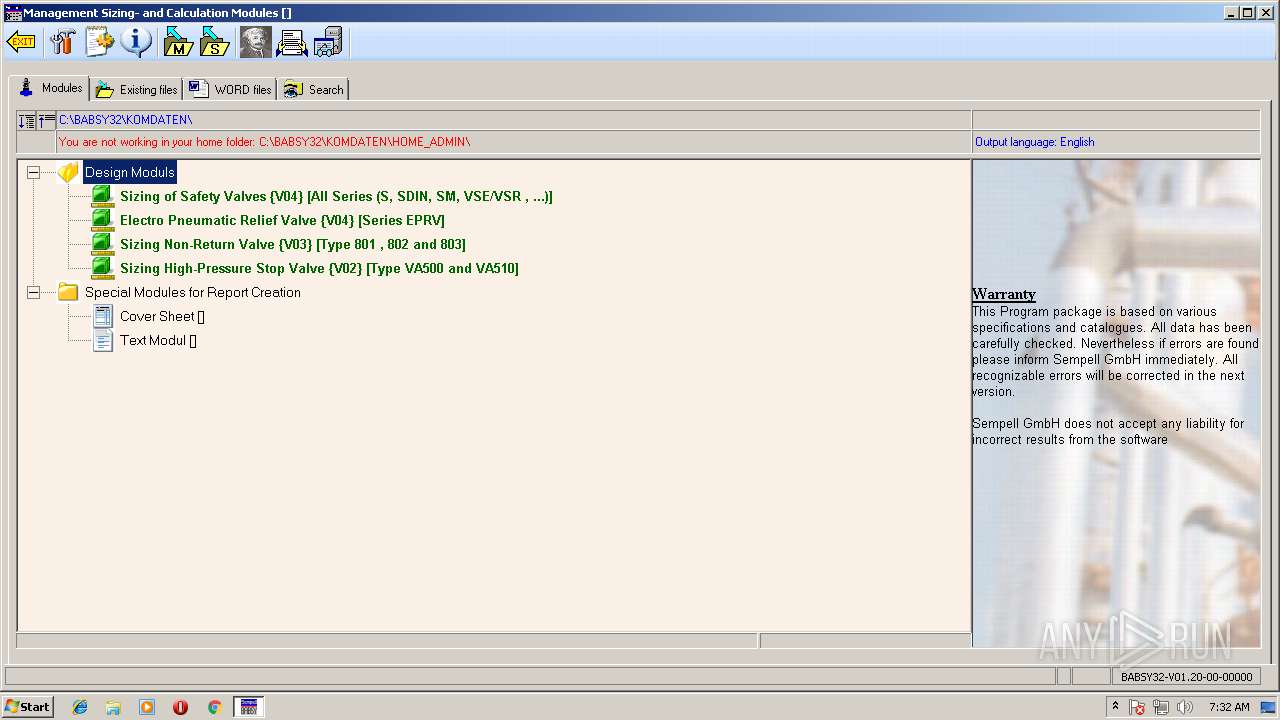
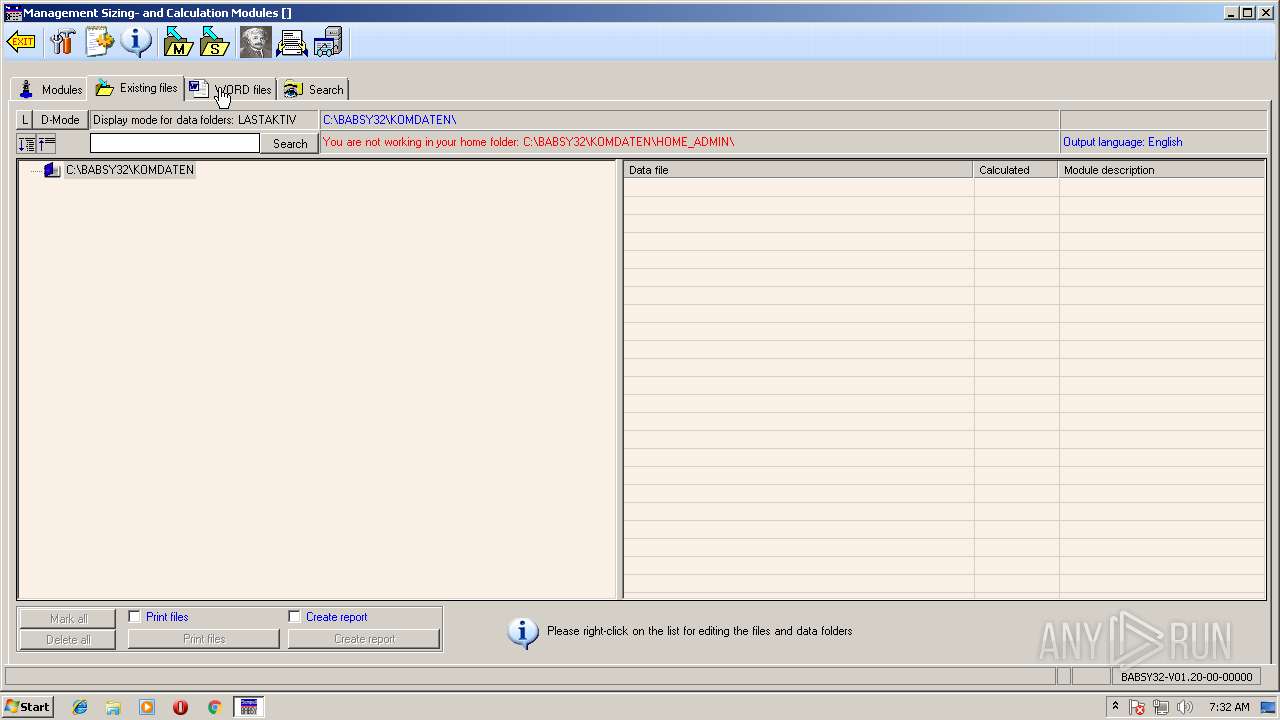
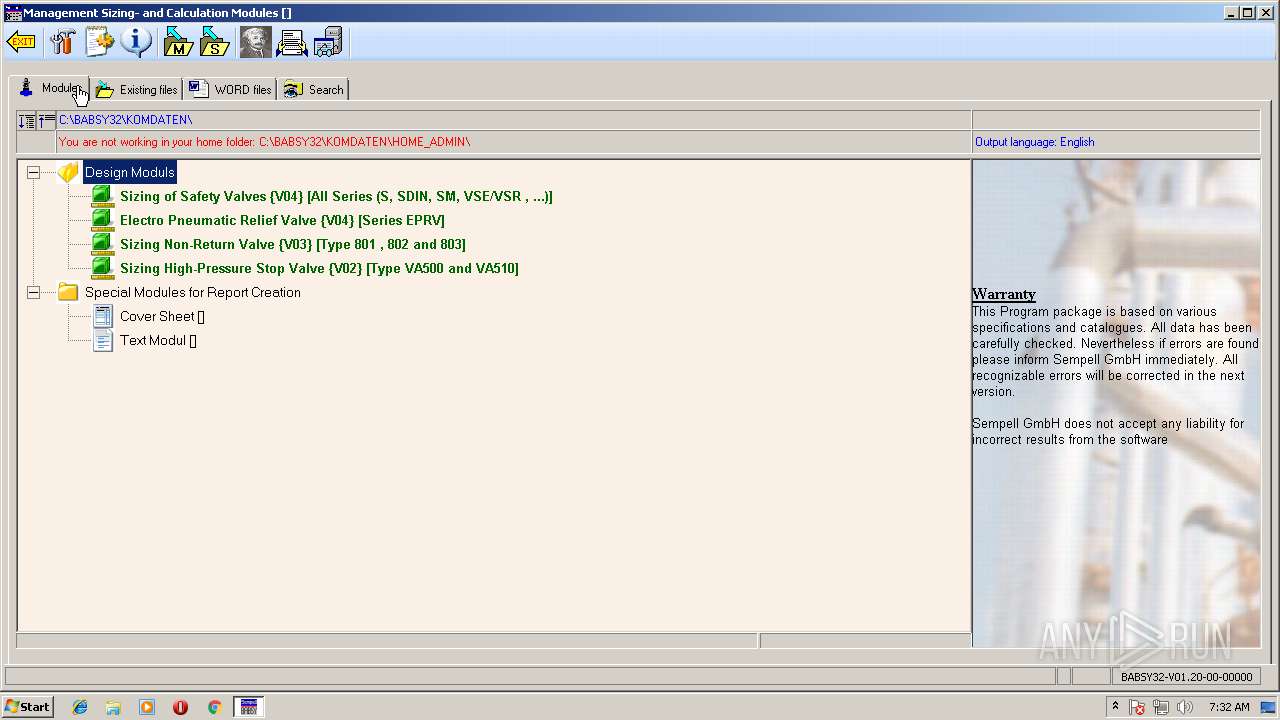
| 1932 | "C:\BABSY32\BABSY32.EXE" | C:\BABSY32\BABSY32.EXE | explorer.exe | ||||||||||||
User: admin Company: Sempell GmbH Integrity Level: MEDIUM Description: BABSY32-Verwaltung Auslegungs- und Berechnungsmodule Exit code: 0 Version: 01.20.004.0000 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Automation -Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /automation -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3348 | "C:\Users\admin\AppData\Local\Temp\irsetup.exe" | C:\Users\admin\AppData\Local\Temp\irsetup.exe | setup.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: HIGH Description: SUF60Runtime Exit code: 0 Version: 6.0.1.2 Modules
| |||||||||||||||
| 3676 | "C:\Users\admin\Downloads\setup.exe" | C:\Users\admin\Downloads\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Indigo Rose Corporation http://www.indigorose.com Integrity Level: MEDIUM Description: Setup Factory 6.0 Setup Launcher Exit code: 3221226540 Version: 6.0.1.2 Modules
| |||||||||||||||
| 3836 | "C:\Users\admin\Downloads\setup.exe" | C:\Users\admin\Downloads\setup.exe | explorer.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation http://www.indigorose.com Integrity Level: HIGH Description: Setup Factory 6.0 Setup Launcher Exit code: 0 Version: 6.0.1.2 Modules
| |||||||||||||||
Total events
1 258
Read events
1 007
Write events
242
Delete events
9
Modification events
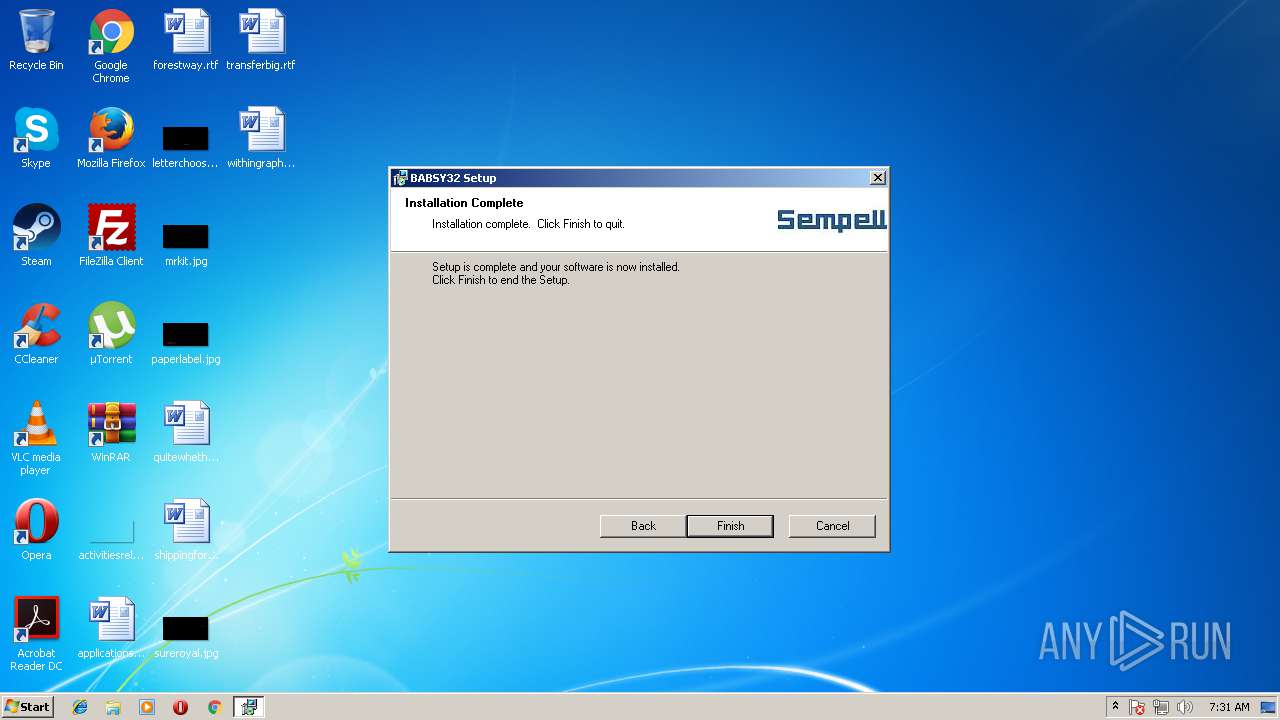
| (PID) Process: | (3348) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Product_Name |
| Operation: | write | Name: | DisplayName |
Value: BABSY32 | |||
| (PID) Process: | (3348) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Product_Name |
| Operation: | write | Name: | UninstallString |
Value: C:\Windows\iun6002.exe "C:\BABSY32\irunin.ini" | |||
| (PID) Process: | (3348) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\SempellAG_BABSY32.INI\INIT |
| Operation: | write | Name: | LastInstall |
Value: 2018-08-21 | |||
| (PID) Process: | (3348) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\DEL5068.tmp | |||
| (PID) Process: | (3348) irsetup.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-500\Software\VB and VBA Program Settings\SempellAG_BABSY32.INI\INIT |
| Operation: | write | Name: | LastInstall |
Value: 2018-08-21 | |||
| (PID) Process: | (1932) BABSY32.EXE | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\SempellAG_BABSY32.INI\INIT |
| Operation: | write | Name: | FLAGXXXX |
Value: /9j/4AAQSkZJRgABAQAAAQABAAD/2wBDAAsICAoIBwsKCQoNDAsNERwSEQ8PESIZGhQcKSQrKigkJyct | |||
| (PID) Process: | (1932) BABSY32.EXE | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\SempellAG_BABSY32.INI\INIT |
| Operation: | write | Name: | FLAGWWWW |
Value: zz/SgDY/4TbQ/wDn4n/8A5v/AIipIPF+j3NxFBFPMZJXCKDaygEk4HJXA/GsP+wD/wA8/wBKnstEMV9b | |||
| (PID) Process: | (1932) BABSY32.EXE | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\SempellAG_BABSY32.INI\INIT |
| Operation: | write | Name: | FLAGYYYY |
Value: | |||
| (PID) Process: | (1932) BABSY32.EXE | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\SempellAG_BABSY32.INI\INIT |
| Operation: | write | Name: | FLAGZZZZ |
Value: | |||
| (PID) Process: | (1932) BABSY32.EXE | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\SempellAG_BABSY32.INI\INIT |
| Operation: | write | Name: | FLAG0000 |
Value: MkA3LTA9MCcnOEw5PUNFSElIKzZPVU5GVEBHSEX/2wBDAQwNDREPESESEiFFLicuRUVFRUVFRUVFRUVF | |||
Executable files
27
Suspicious files
123
Text files
316
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3836 | setup.exe | C:\Users\admin\AppData\Local\Temp\irsetup.ini | text | |
MD5:— | SHA256:— | |||
| 3836 | setup.exe | C:\Users\admin\AppData\Local\Temp\irsetup.exe | executable | |
MD5:9433D5AC20EDCF7D39C454FE2F67B43D | SHA256:3687A458EA72DF00E771A62C3EFF33849631C662F62C9BB4FA3C735CC2B51B39 | |||
| 3836 | setup.exe | C:\Users\admin\AppData\Local\Temp\irsetup.dat | binary | |
MD5:6EF68332FDF0BEB2B4F7C7FFA1E2ED13 | SHA256:D90A0FF8B70360EDACB5B716BA2617CA846B200C773DF712A06F03FBA525D97D | |||
| 3836 | setup.exe | C:\Users\admin\AppData\Local\Temp\IRIMG3.BMP | image | |
MD5:95145F4CEAD2C4BD2EC219BC87D83F1D | SHA256:0542CB1D3E6B50F78DC63EA1ABEC6C518CFD4EA203649DF3EF3834309EA66CAD | |||
| 3836 | setup.exe | C:\Users\admin\AppData\Local\Temp\suf6lng.9 | text | |
MD5:CEDFFA2264D312A7CA515E64FF34B814 | SHA256:B13B8D36A80294FB22F2E166A307F6DAB26CEF2B7F4BE3067571731D7CDF424A | |||
| 3836 | setup.exe | C:\Users\admin\AppData\Local\Temp\suf6lng.7 | text | |
MD5:2C51F17926ECCCF856C1D6C9EE81167A | SHA256:45C56EB1A2B3D749B38CD395BE87A30D583EBE0B0DD295A795AB4C1BB5E78C33 | |||
| 3348 | irsetup.exe | C:\BABSY32\ADLABELEX.DLL | executable | |
MD5:AAFD92793428C759800268B9A15FD071 | SHA256:C825C8E12CDA3E03544DB73F5DBBA411FFD41B8B7340B4DCC18B8EB86EE911CA | |||
| 3348 | irsetup.exe | C:\BABSY32\CSHEETV01.EXE | executable | |
MD5:7D4397BC4D358CE678356816F652EAC4 | SHA256:E3B97AD1D051C4CA1E8499B2E503F570F1A0D1E75D7E55950FDFE7F9427D1ACF | |||
| 3348 | irsetup.exe | C:\BABSY32\BABSY32.EXE | executable | |
MD5:4470FBE7AFD0D18E31E4523E41BA5CC5 | SHA256:37AC0D5EA983E98B3D8FB4CF2DEC424D7C0A59C9896C58C27A01528874386207 | |||
| 3348 | irsetup.exe | C:\BABSY32\BITFUNKTIONEN.DLL | executable | |
MD5:7083EFDBCEF17F90531A9CA679157848 | SHA256:2C7AD0EDEFE0B028C936E58A8FD4BD4505BFAD35D85EA7C5D416B2AE869BF43A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1932 | BABSY32.EXE | GET | 301 | 212.227.247.145:80 | http://docs.sempell.com/DOWNLOADS/BABSY/SETUP.EXE | DE | html | 257 b | unknown |
1932 | BABSY32.EXE | GET | 301 | 212.227.247.145:80 | http://docs.sempell.com/DOWNLOADS/BABSY/SETUP.EXE | DE | html | 257 b | unknown |
1932 | BABSY32.EXE | GET | — | 212.227.247.145:80 | http://docs.sempell.com/downloads/babsy/Setup.exe | DE | — | — | unknown |
1932 | BABSY32.EXE | GET | 301 | 212.227.247.145:80 | http://docs.sempell.com/downloads/babsy/SETUP.EXE | DE | html | 257 b | unknown |
1932 | BABSY32.EXE | GET | 301 | 212.227.247.145:80 | http://docs.sempell.com/downloads/BABSY/SETUP.EXE | DE | html | 257 b | unknown |
1932 | BABSY32.EXE | GET | — | 212.227.247.145:80 | http://docs.sempell.com/downloads/babsy/Setup.exe | DE | — | — | unknown |
1932 | BABSY32.EXE | GET | 301 | 212.227.247.145:80 | http://docs.sempell.com/downloads/babsy/SETUP.EXE | DE | html | 257 b | unknown |
1932 | BABSY32.EXE | GET | 301 | 212.227.247.145:80 | http://docs.sempell.com/downloads/BABSY/SETUP.EXE | DE | html | 257 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1932 | BABSY32.EXE | 212.227.247.145:80 | docs.sempell.com | 1&1 Internet SE | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
DEKORFP01.PENTAIR.PVT |
| unknown |
DEKORFP01.DOMAIN.PVT |
| unknown |
docs.sempell.com |
| unknown |