| File name: | Xenos.exe |
| Full analysis: | https://app.any.run/tasks/324060ed-a2f6-4825-9b09-e9e8ea187f9b |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2019, 23:59:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 216C3EAE24901482BFD26CB9DCA1A833 |
| SHA1: | F6000CC06CBC9F0E748B81CFAC77EB2598F71E69 |
| SHA256: | 8BDB3CE10DEE7A3249A186050D7F804BCA19859F292DDAD7AE8C5AFBB649A07B |
| SSDEEP: | 24576:gwTJ6A1eP1Pm9zhTaUe0K9XXVYFEjd6/Gr+AK9hhEfSVgPCS3tMrMyj3F9hIF1SR:r5ra0K9ndjd6/GXKvhISVE3tMx3FE1Sr |
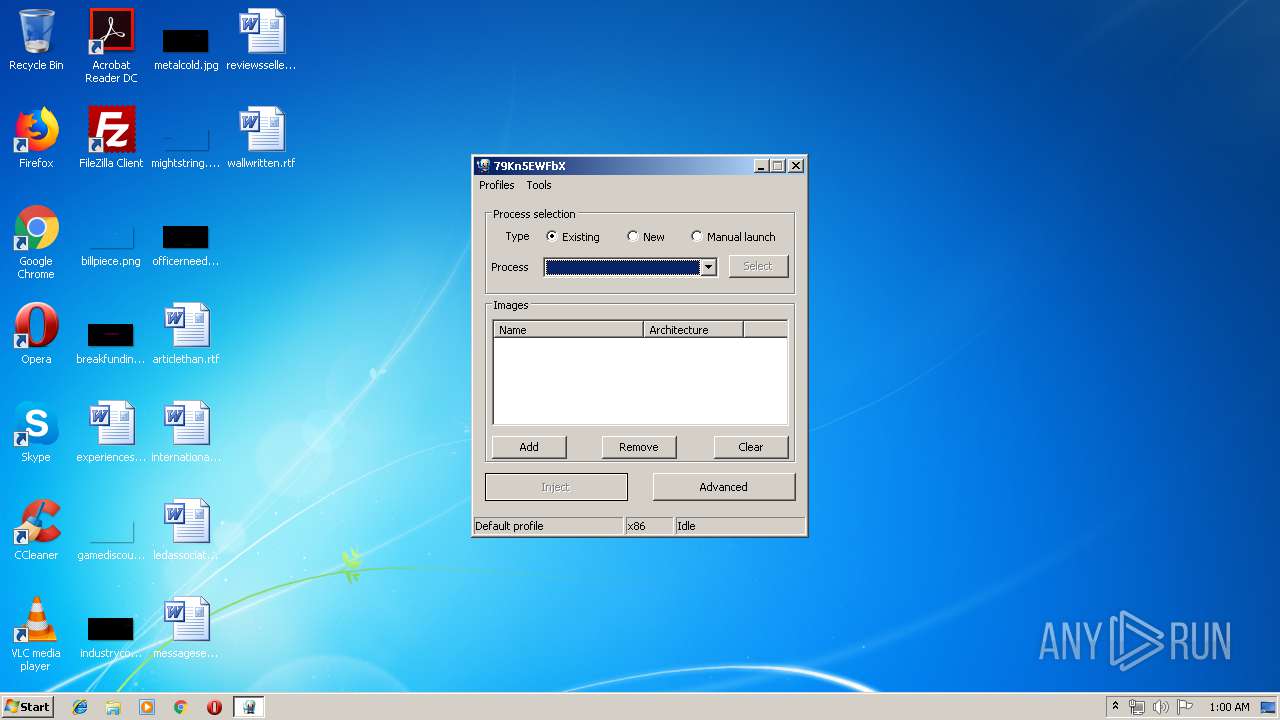
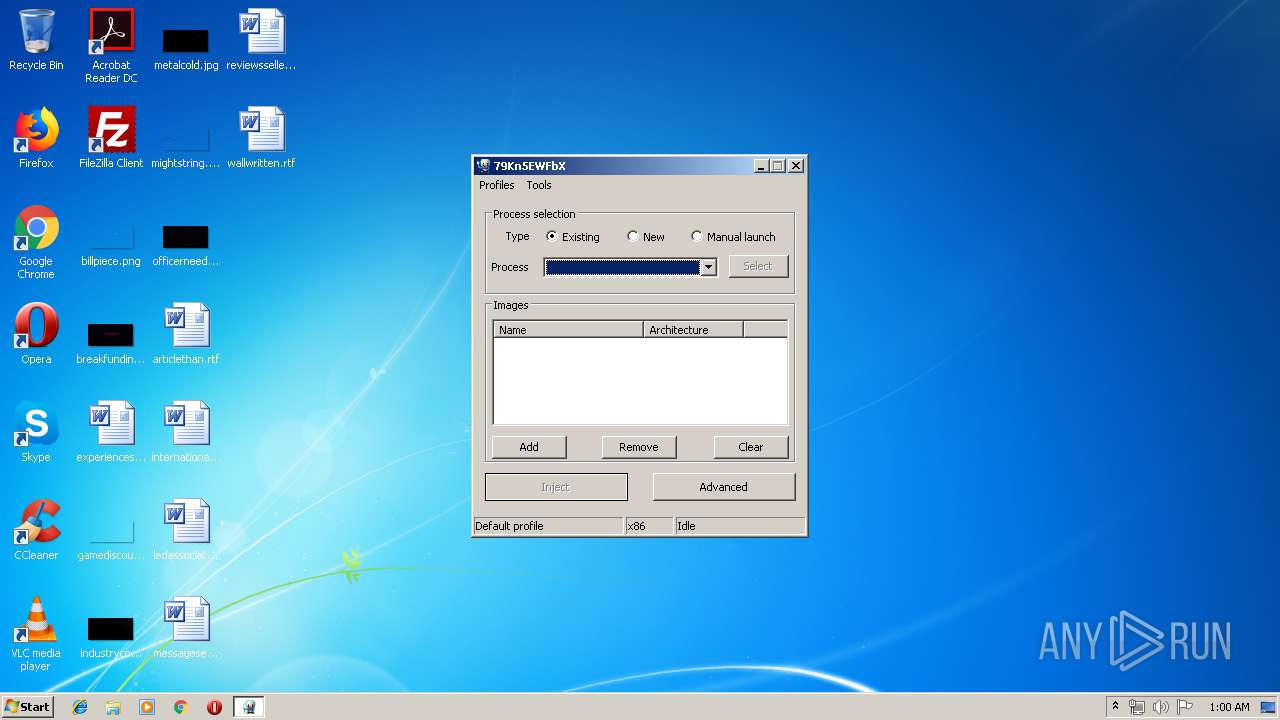
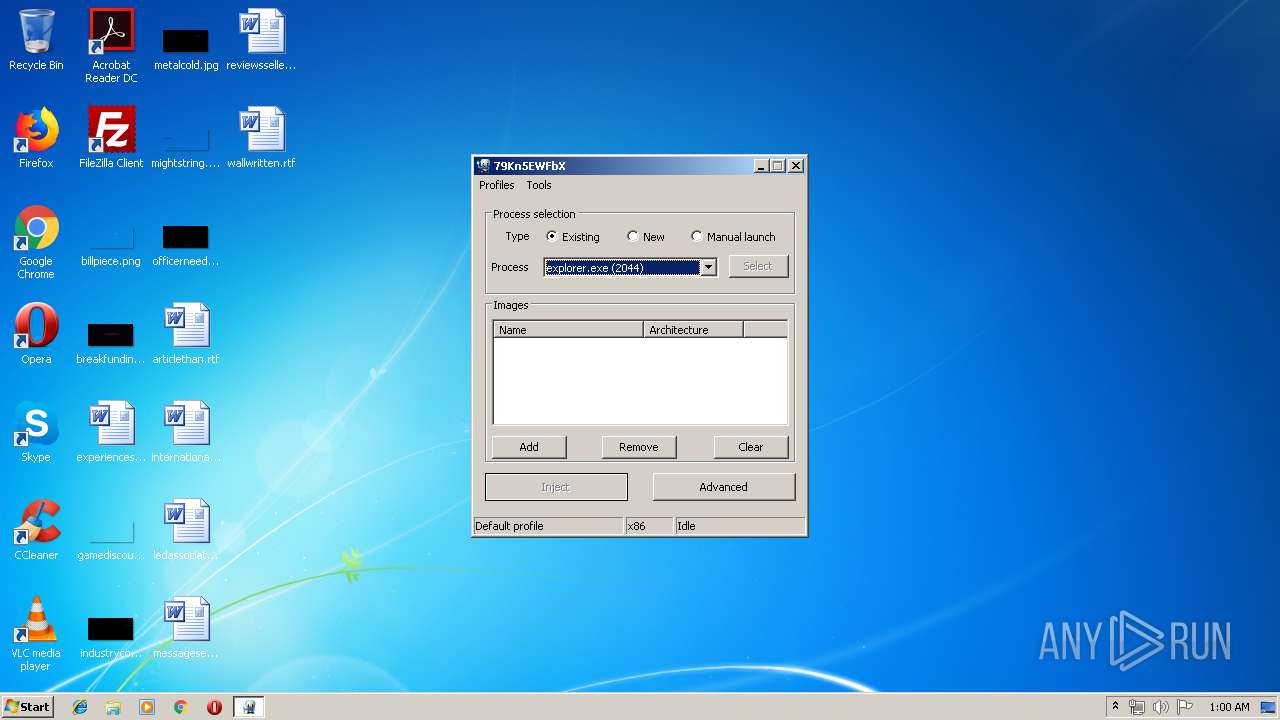
MALICIOUS
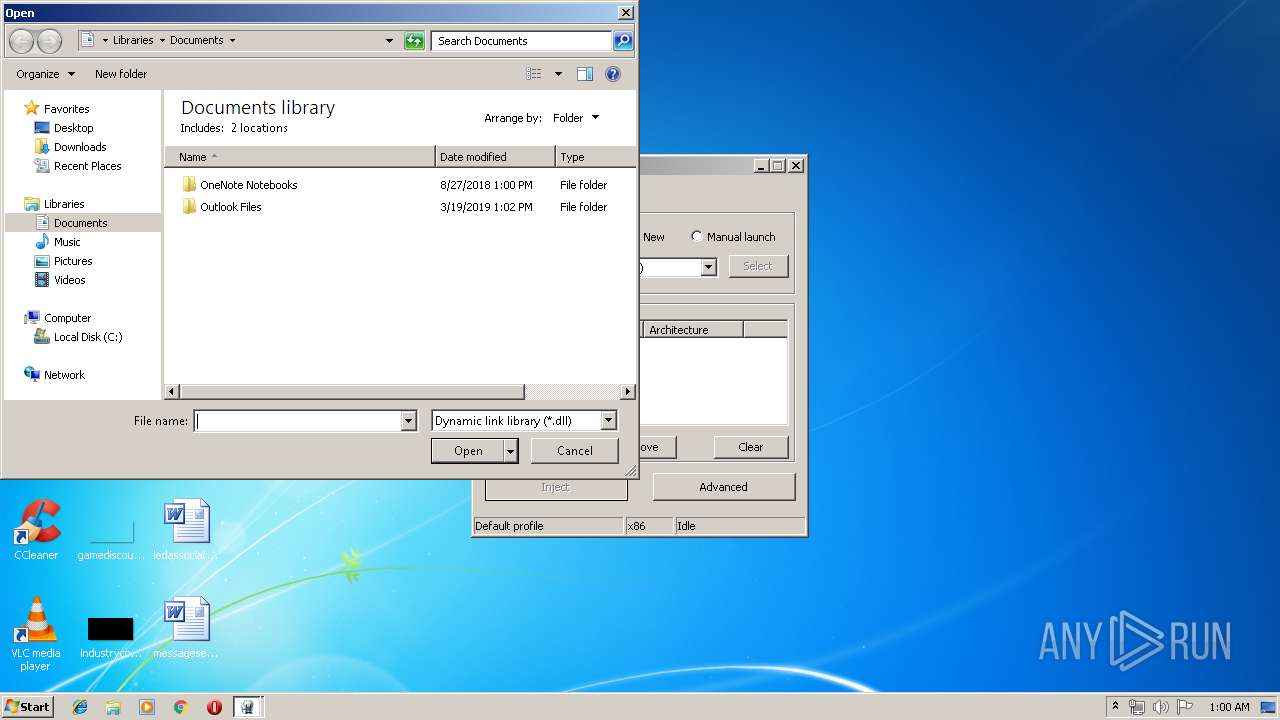
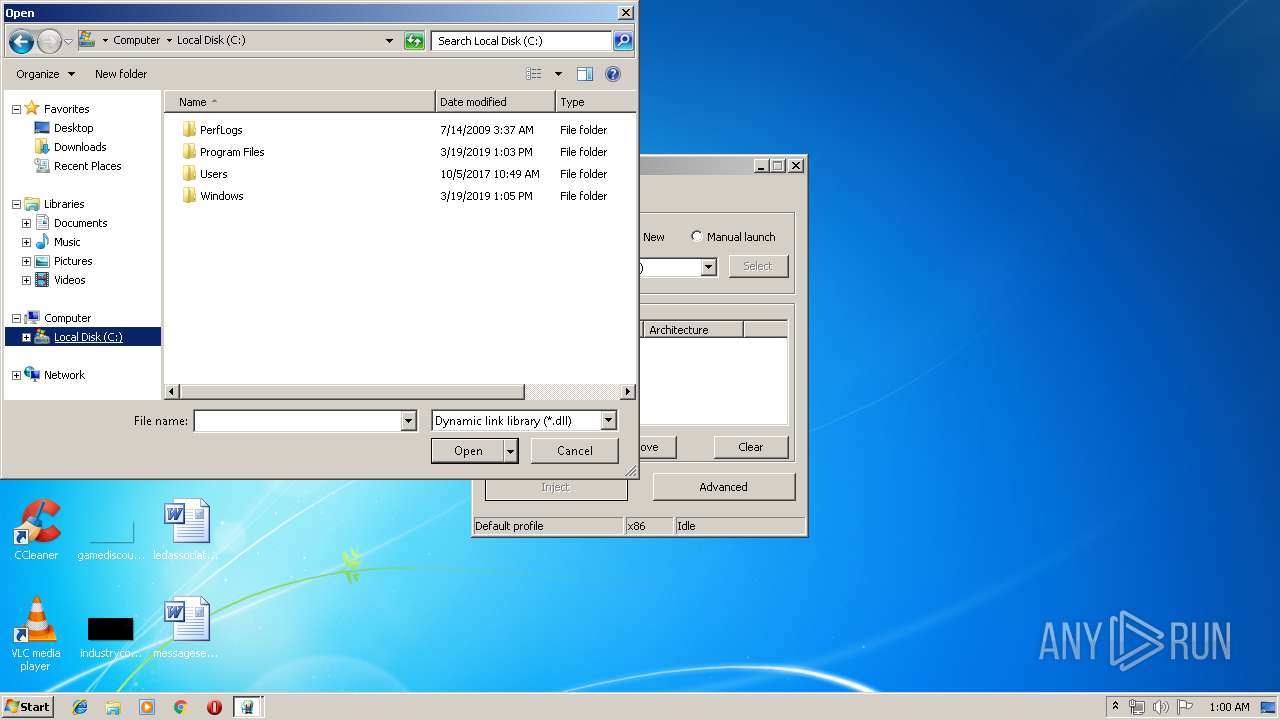
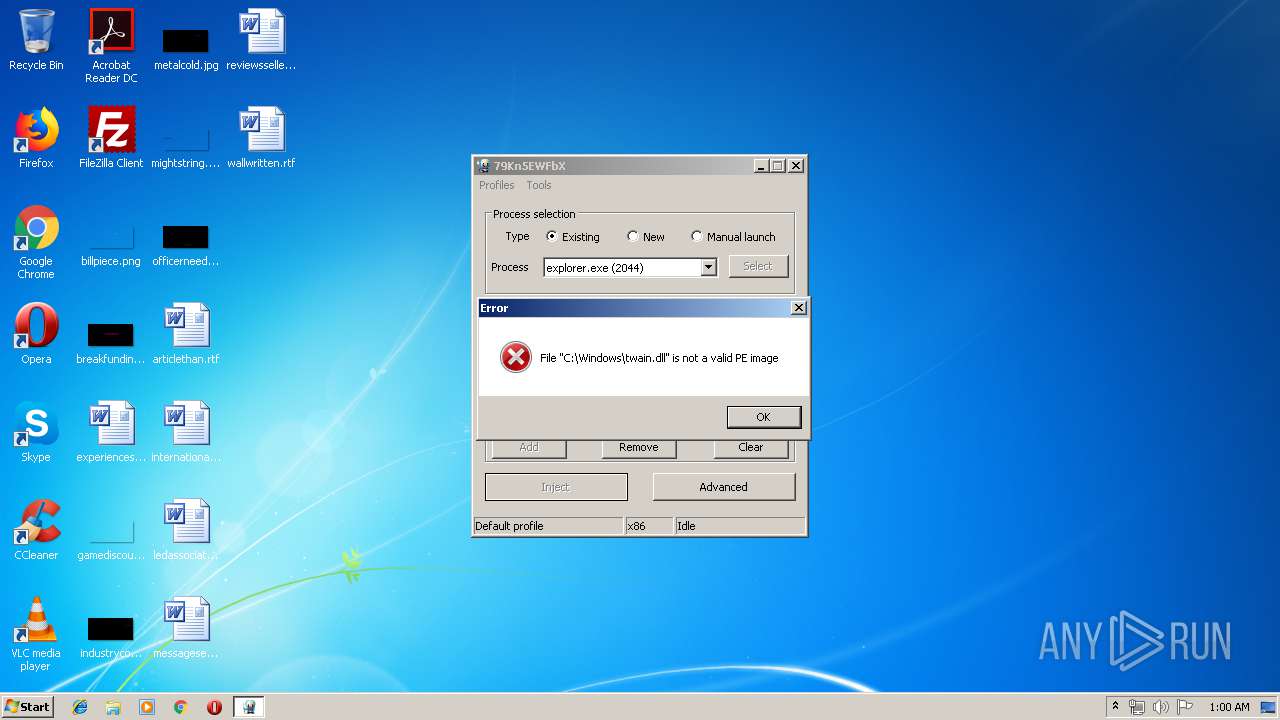
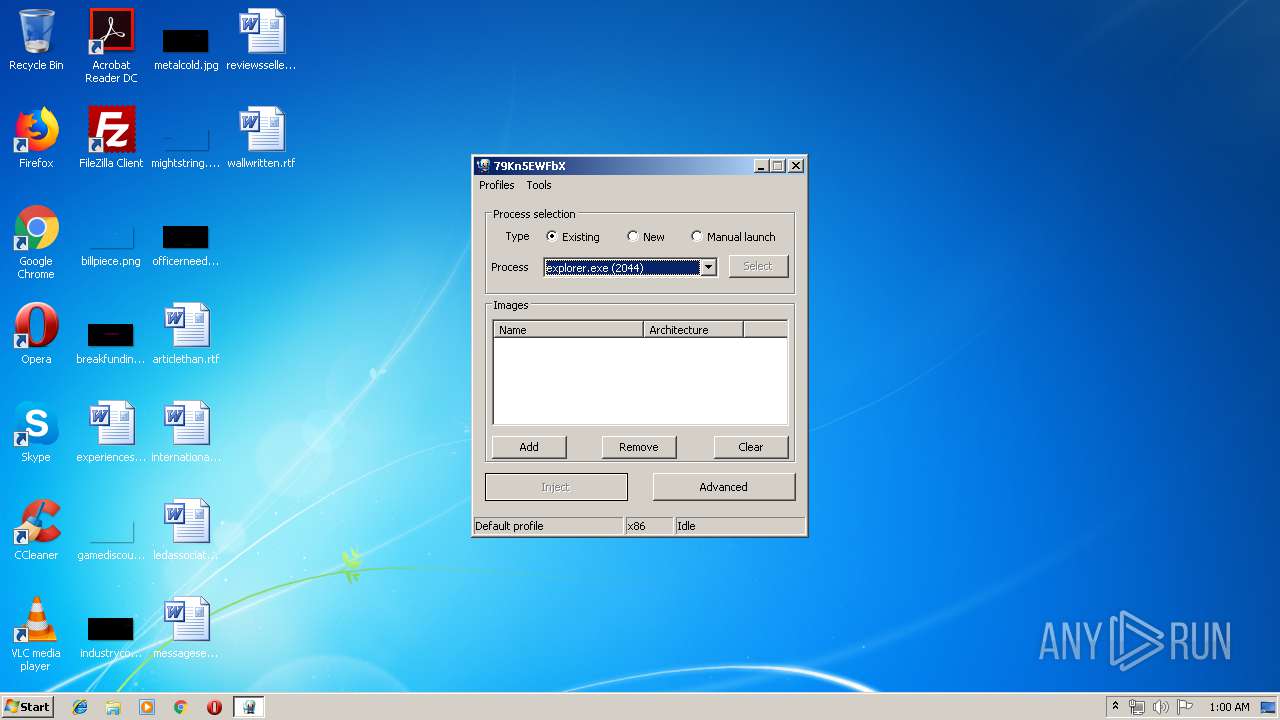
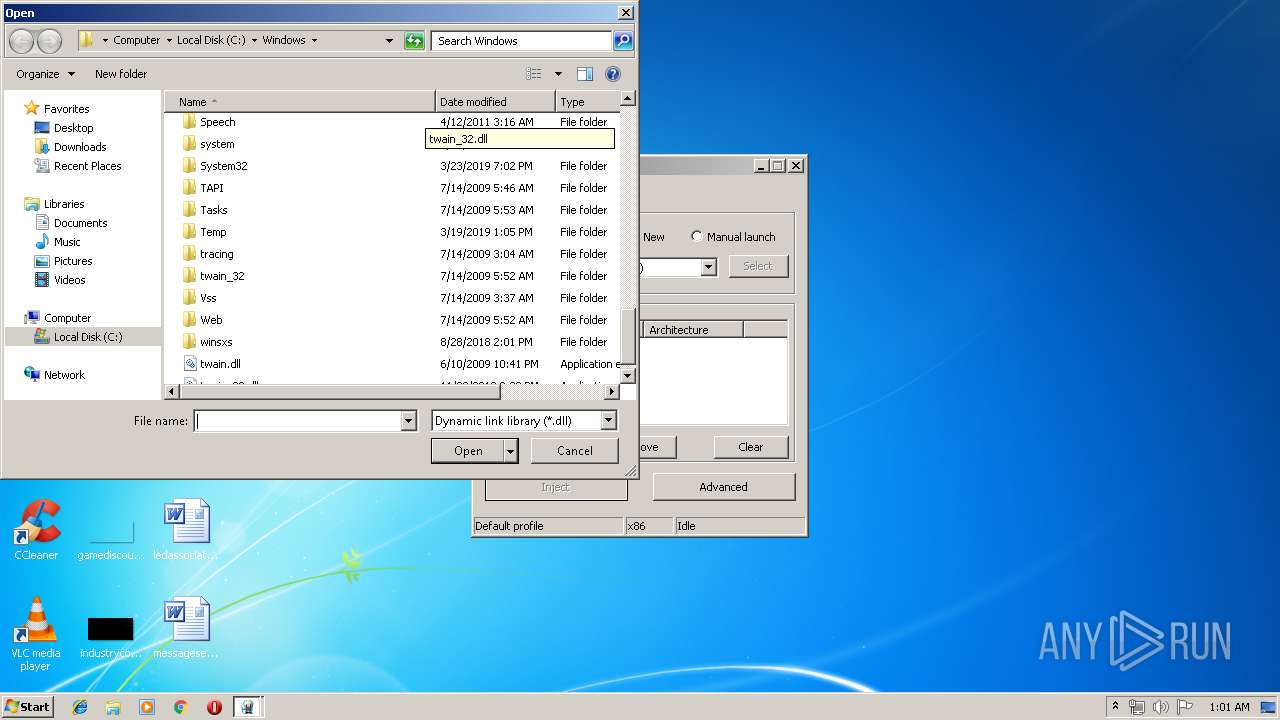
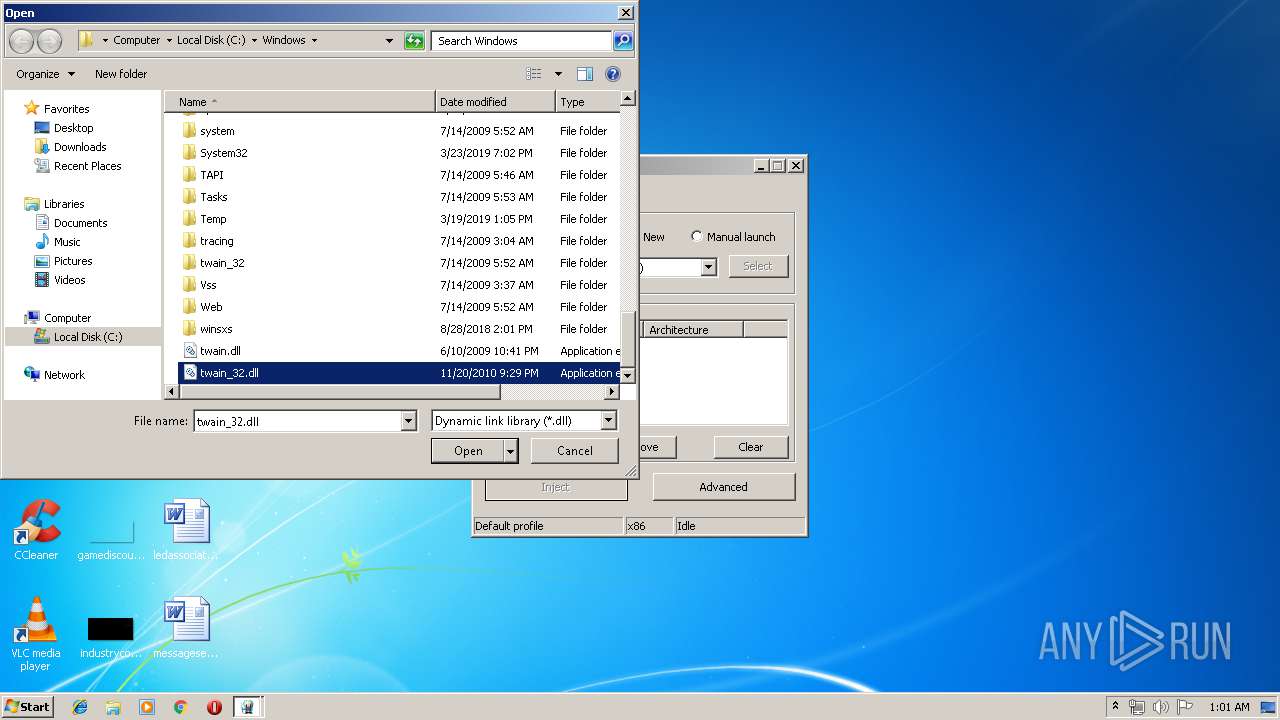
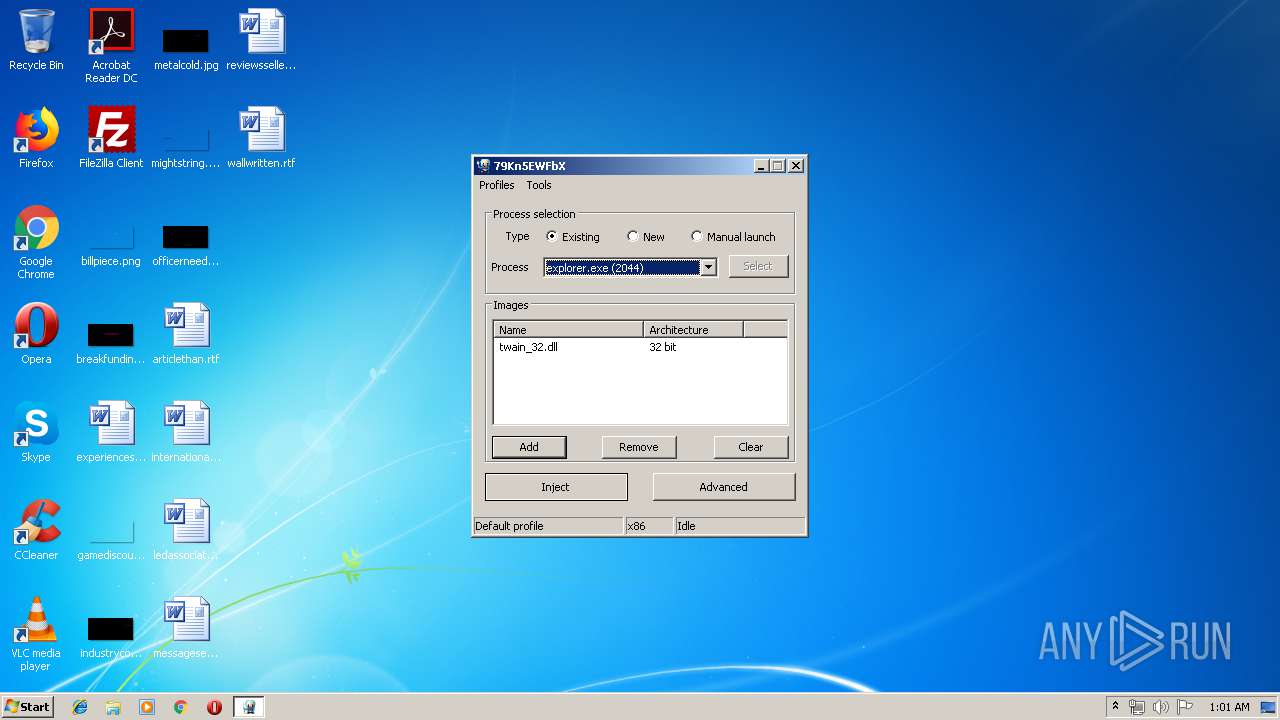
Application was injected by another process
- explorer.exe (PID: 2044)
Runs injected code in another process
- Xenos.exe (PID: 3008)
SUSPICIOUS
Creates files in the user directory
- explorer.exe (PID: 2044)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:03 17:51:55+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.14 |
| CodeSize: | 652800 |
| InitializedDataSize: | 529408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5f486 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.2.0 |
| ProductVersionNumber: | 2.3.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Process default |
| CharacterSet: | Unicode |
| FileDescription: | PE injector |
| FileVersion: | 2.3.2.0 |
| InternalName: | Xenos.exe |
| LegalCopyright: | Copyright (C) 2017 |
| OriginalFileName: | Xenos.exe |
| ProductName: | Xenos |
| ProductVersion: | 2.3.2.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jun-2018 15:51:55 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileDescription: | PE injector |
| FileVersion: | 2.3.2.0 |
| InternalName: | Xenos.exe |
| LegalCopyright: | Copyright (C) 2017 |
| OriginalFilename: | Xenos.exe |
| ProductName: | Xenos |
| ProductVersion: | 2.3.2.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 03-Jun-2018 15:51:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0009F4CB | 0x0009F600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60668 |
.rdata | 0x000A1000 | 0x0002C366 | 0x0002C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.78599 |
.data | 0x000CE000 | 0x000049D0 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.75139 |
.rsrc | 0x000D3000 | 0x00050590 | 0x00050600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.16186 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05508 | 649 | UNKNOWN | English - United States | RT_MANIFEST |
129 | 3.24872 | 774 | UNKNOWN | Process Default Language | RT_DIALOG |
135 | 1.98048 | 20 | UNKNOWN | Process Default Language | RT_GROUP_ICON |
137 | 3.0888 | 236 | UNKNOWN | Process Default Language | RT_DIALOG |
138 | 3.21441 | 174 | UNKNOWN | Process Default Language | RT_MENU |
139 | 3.12361 | 236 | UNKNOWN | Process Default Language | RT_DIALOG |
140 | 3.39845 | 2214 | UNKNOWN | Process Default Language | RT_DIALOG |
141 | 2.375 | 16 | UNKNOWN | Process Default Language | RT_ACCELERATOR |
142 | 6.37578 | 64936 | UNKNOWN | Process Default Language | DRIVER |
147 | 6.41236 | 62352 | UNKNOWN | Process Default Language | DRIVER |
Imports
ADVAPI32.dll |
COMDLG32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
dbghelp.dll |
ole32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
??0Assembler@asmjit@@QAE@PAURuntime@1@@Z | 1 | 0x00048F90 |
??0CodeGen@asmjit@@QAE@PAURuntime@1@@Z | 2 | 0x00056570 |
??0HostRuntime@asmjit@@QAE@XZ | 3 | 0x0004ED80 |
??0JitRuntime@asmjit@@QAE@XZ | 4 | 0x0004EF00 |
??0Runtime@asmjit@@QAE@XZ | 5 | 0x0004ED40 |
??0StaticRuntime@asmjit@@QAE@PAXI@Z | 6 | 0x0004EE30 |
??0VMemMgr@asmjit@@QAE@PAX@Z | 7 | 0x0003E770 |
??0X86Assembler@asmjit@@QAE@PAURuntime@1@I@Z | 8 | 0x0004F2C0 |
??0Zone@asmjit@@QAE@I@Z | 9 | 0x00056860 |
??1Assembler@asmjit@@UAE@XZ | 10 | 0x00049030 |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2044 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
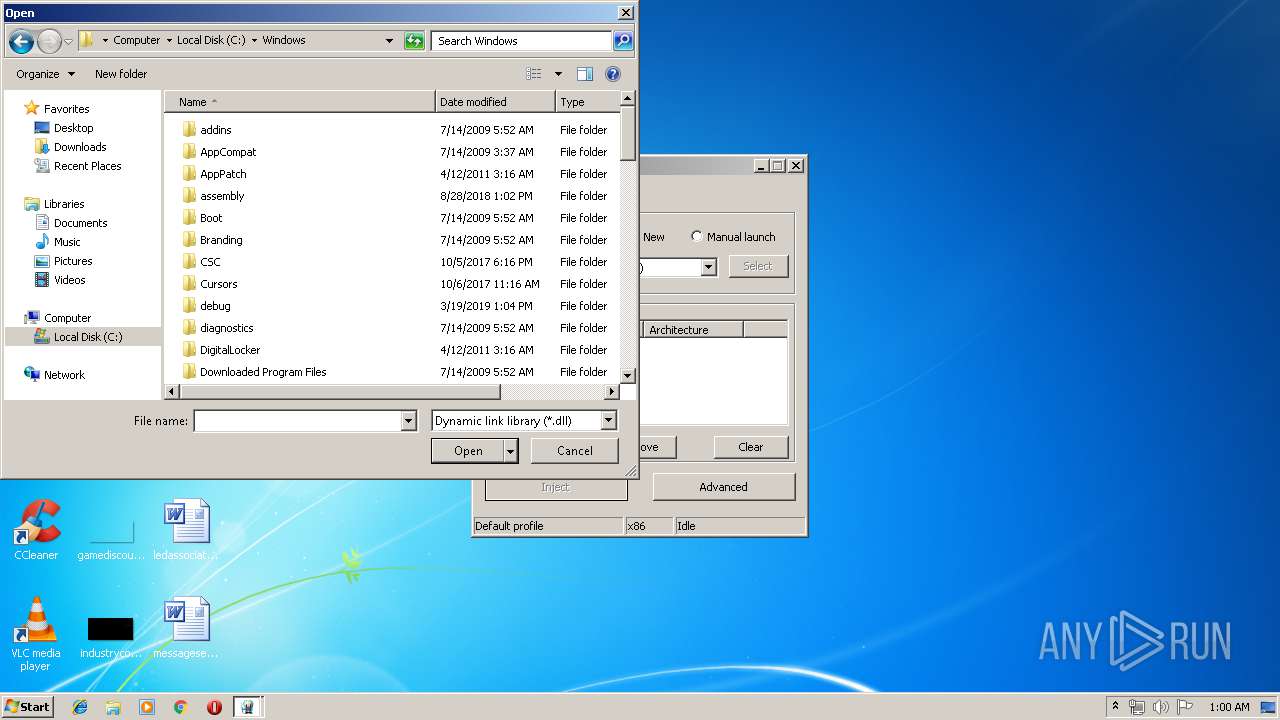
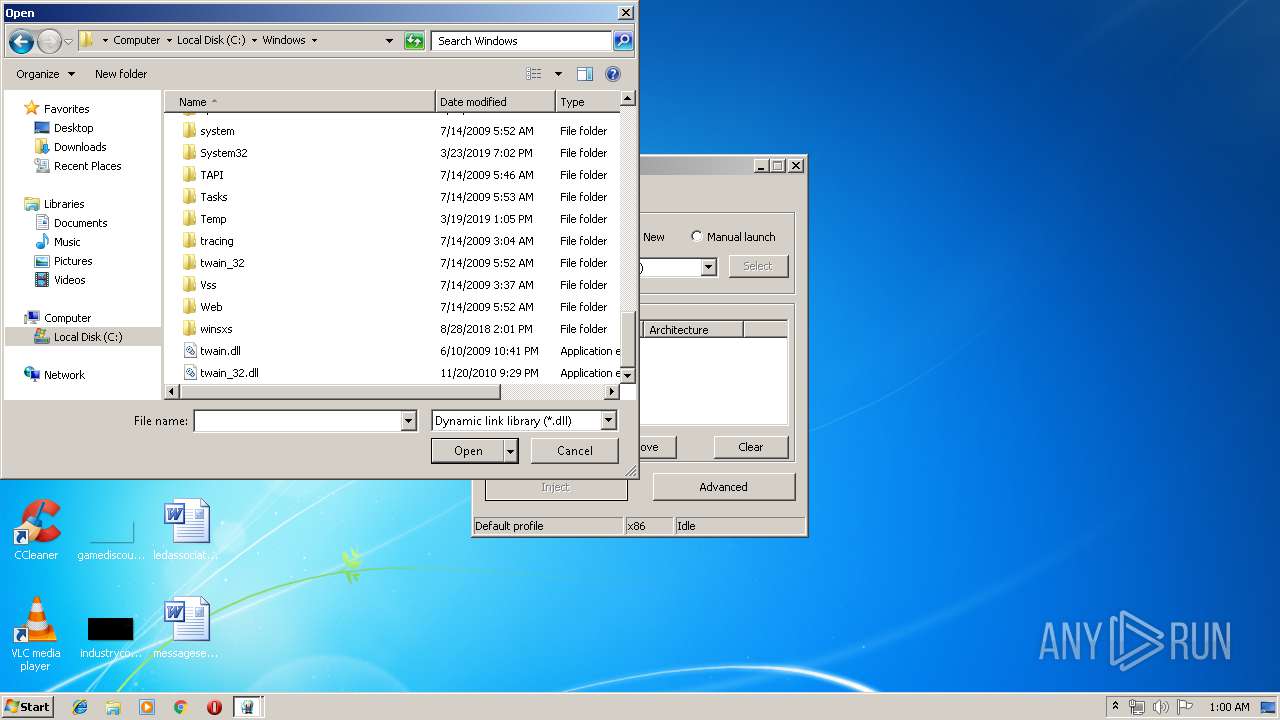
| 3008 | "C:\Users\admin\AppData\Local\Temp\Xenos.exe" | C:\Users\admin\AppData\Local\Temp\Xenos.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: PE injector Exit code: 0 Version: 2.3.2.0 Modules
| |||||||||||||||
| 3576 | "C:\Users\admin\AppData\Local\Temp\Xenos.exe" | C:\Users\admin\AppData\Local\Temp\Xenos.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PE injector Exit code: 3221226540 Version: 2.3.2.0 Modules
| |||||||||||||||
Total events
854
Read events
650
Write events
198
Delete events
6
Modification events
| (PID) Process: | (3008) Xenos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.xpr |
| Operation: | write | Name: | |
Value: XenosProfile | |||
| (PID) Process: | (3008) Xenos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.xpr |
| Operation: | write | Name: | Content Type |
Value: Application/xml | |||
| (PID) Process: | (3008) Xenos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\XenosProfile |
| Operation: | write | Name: | |
Value: Xenos injection profile | |||
| (PID) Process: | (3008) Xenos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\XenosProfile\shell |
| Operation: | write | Name: | |
Value: Run | |||
| (PID) Process: | (3008) Xenos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\XenosProfile\shell\Edit\command |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp\Xenos.exe --load %1 | |||
| (PID) Process: | (3008) Xenos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\XenosProfile\shell\Run\command |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp\Xenos.exe --run %1 | |||
| (PID) Process: | (3008) Xenos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\XenosProfile\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp\Xenos.exe,-135 | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\Krabf.rkr |
Value: 000000000000000000000000CB7D0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000500000005000000D76001000300000003000000BD6800004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000360200000000BCE8360201000000000000000000577690E836027CE636025E7CFB76BCE83602787CFB76030000008A018C01AC413400ACE63602F77CFB760100000090E83602847CFB76FCE63602F0E6360208E73602000000000000000000000000F8E6360290E8360200000000000000000000000030E8360230E836020000000001000000BCE8360230E83602B2FEFB76F270FB7685FCFB7695B635759A7CFA76AC413400A27EFA7674E83602180000004CFA3602006FFA7600000000000000005CE836023C003E00BCE83602C34E5200FCE6360200000000D8462B000000360258E7360244EA360200000088C8000000C8000000C8000000C8000000E20201000000000000008168B8F35703010600400000000030EA3602105381687FEB51762000000011000000B8452C00B0452C000000000044EA360200000000E4E70000630E855B94E7360282918075E4E7360298E736022795807500000000B45DE702C0E73602CD948075B45DE7026CE836022859E702E1948075000000002859E7026CE83602C8E736020300000003000000BD6800004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000360200000000BCE8360201000000000000000000577690E836027CE636025E7CFB76BCE83602787CFB76030000008A018C01AC413400ACE63602F77CFB760100000090E83602847CFB76FCE63602F0E6360208E73602000000000000000000000000F8E6360290E8360200000000000000000000000030E8360230E836020000000001000000BCE8360230E83602B2FEFB76F270FB7685FCFB7695B635759A7CFA76AC413400A27EFA7674E83602180000004CFA3602006FFA7600000000000000005CE836023C003E00BCE83602C34E5200FCE6360200000000D8462B000000360258E7360244EA360200000088C8000000C8000000C8000000C8000000E20201000000000000008168B8F35703010600400000000030EA3602105381687FEB51762000000011000000B8452C00B0452C000000000044EA360200000000E4E70000630E855B94E7360282918075E4E7360298E736022795807500000000B45DE702C0E73602CD948075B45DE7026CE836022859E702E1948075000000002859E7026CE83602C8E736020300000003000000BD6800004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000360200000000BCE8360201000000000000000000577690E836027CE636025E7CFB76BCE83602787CFB76030000008A018C01AC413400ACE63602F77CFB760100000090E83602847CFB76FCE63602F0E6360208E73602000000000000000000000000F8E6360290E8360200000000000000000000000030E8360230E836020000000001000000BCE8360230E83602B2FEFB76F270FB7685FCFB7695B635759A7CFA76AC413400A27EFA7674E83602180000004CFA3602006FFA7600000000000000005CE836023C003E00BCE83602C34E5200FCE6360200000000D8462B000000360258E7360244EA360200000088C8000000C8000000C8000000C8000000E20201000000000000008168B8F35703010600400000000030EA3602105381687FEB51762000000011000000B8452C00B0452C000000000044EA360200000000E4E70000630E855B94E7360282918075E4E7360298E736022795807500000000B45DE702C0E73602CD948075B45DE7026CE836022859E702E1948075000000002859E7026CE83602C8E73602 | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\Krabf.rkr |
Value: 000000000000000001000000CB7D0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
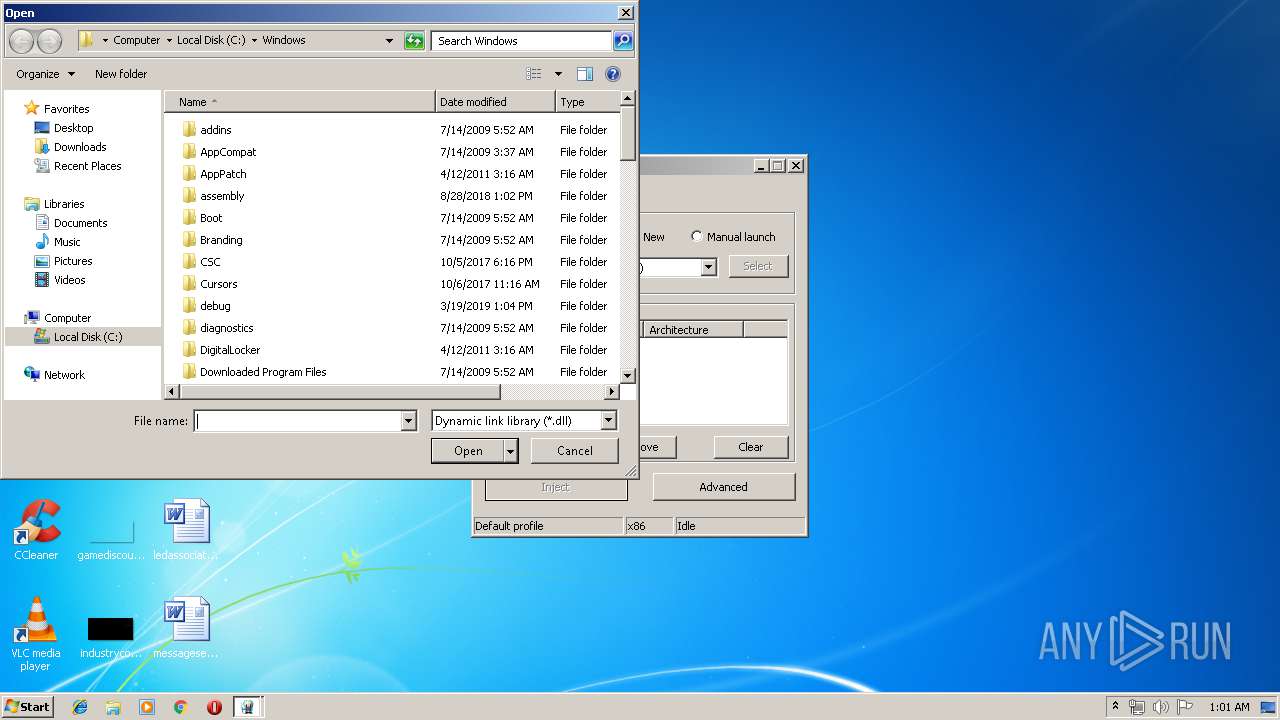
| 2044 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\Windows.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Twain001.Mtx | binary | |
MD5:6D5ABABB65E9FF214B73E891B4AFE6E8 | SHA256:913DA1F8DF6F8FD47593840D533BA0458CC9873996BF310460ABB495B34C232A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report