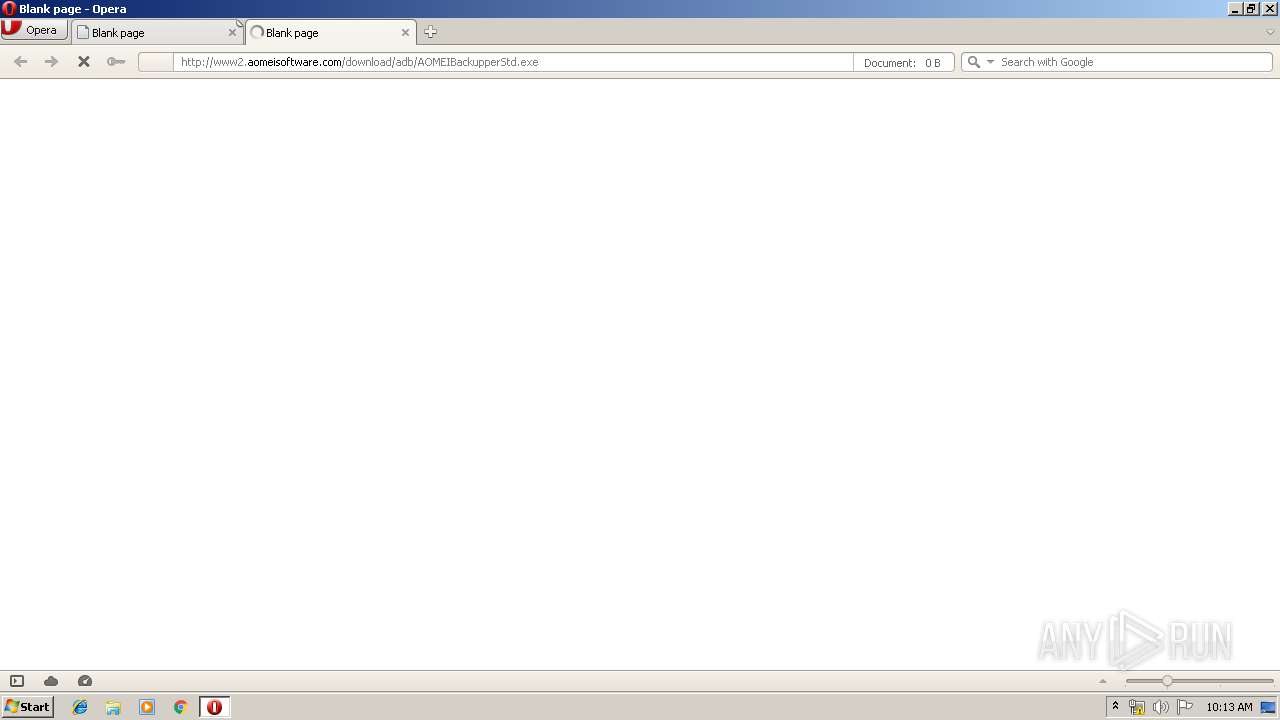
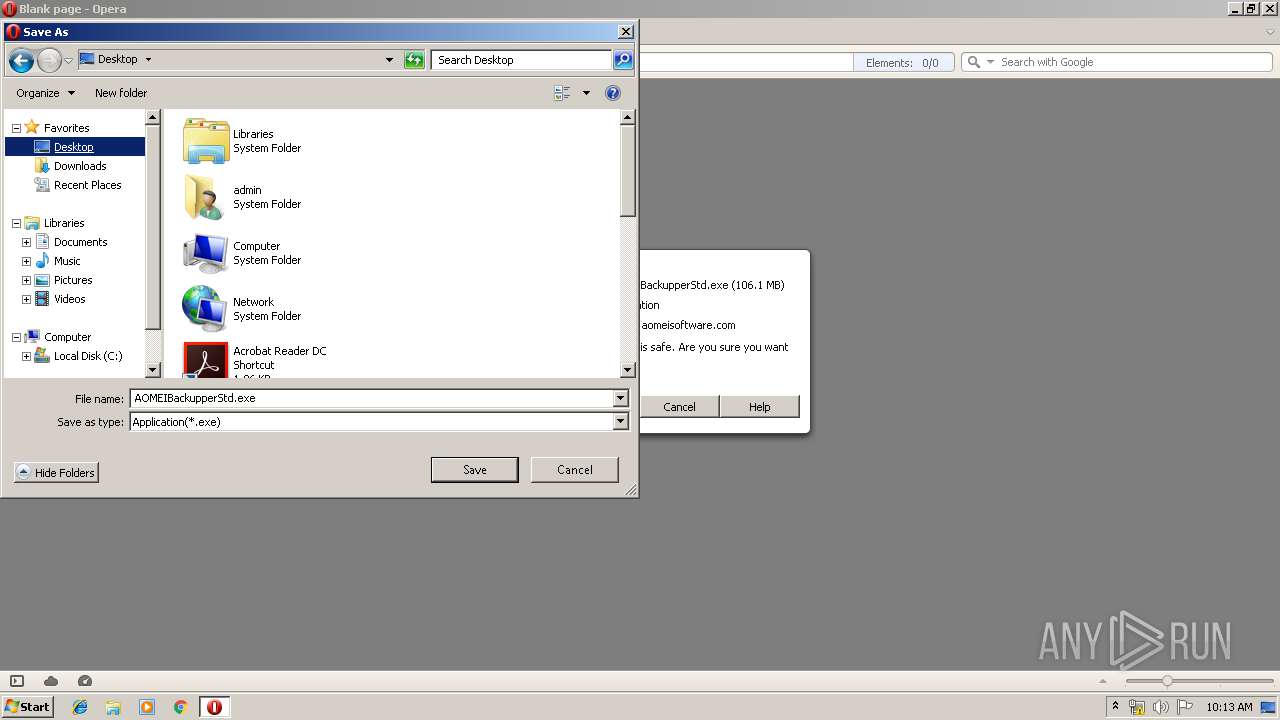
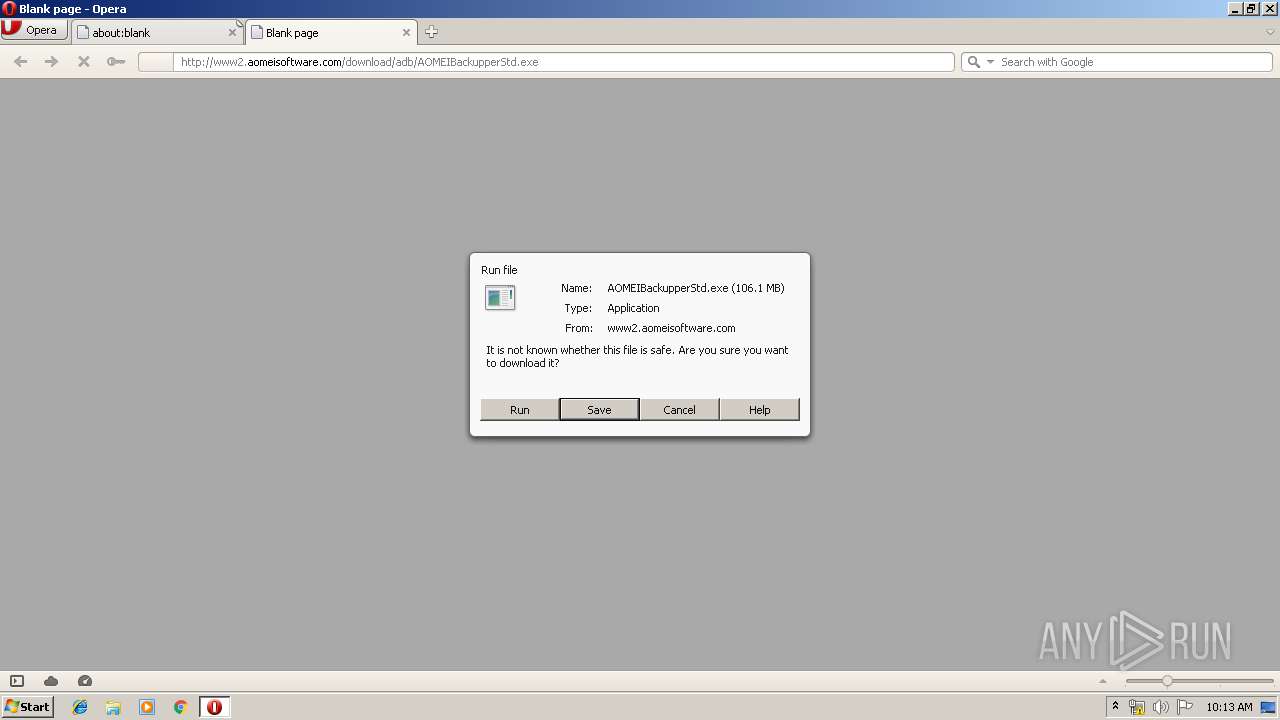
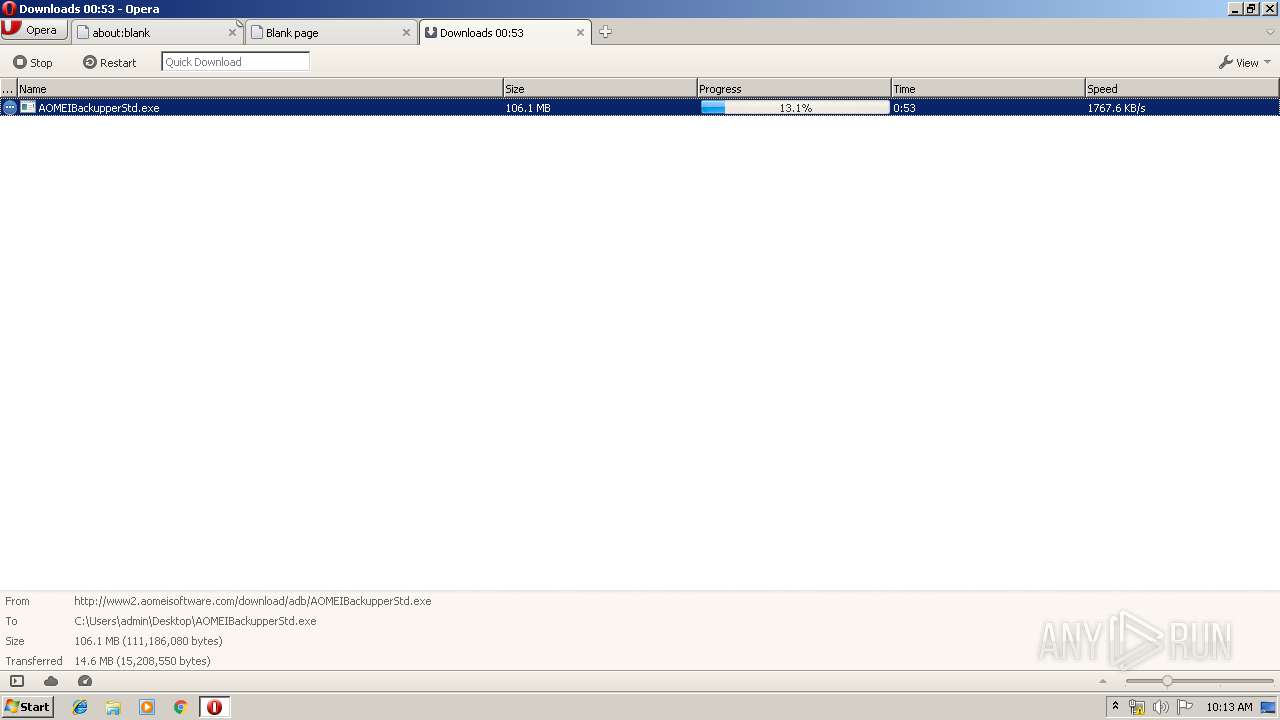
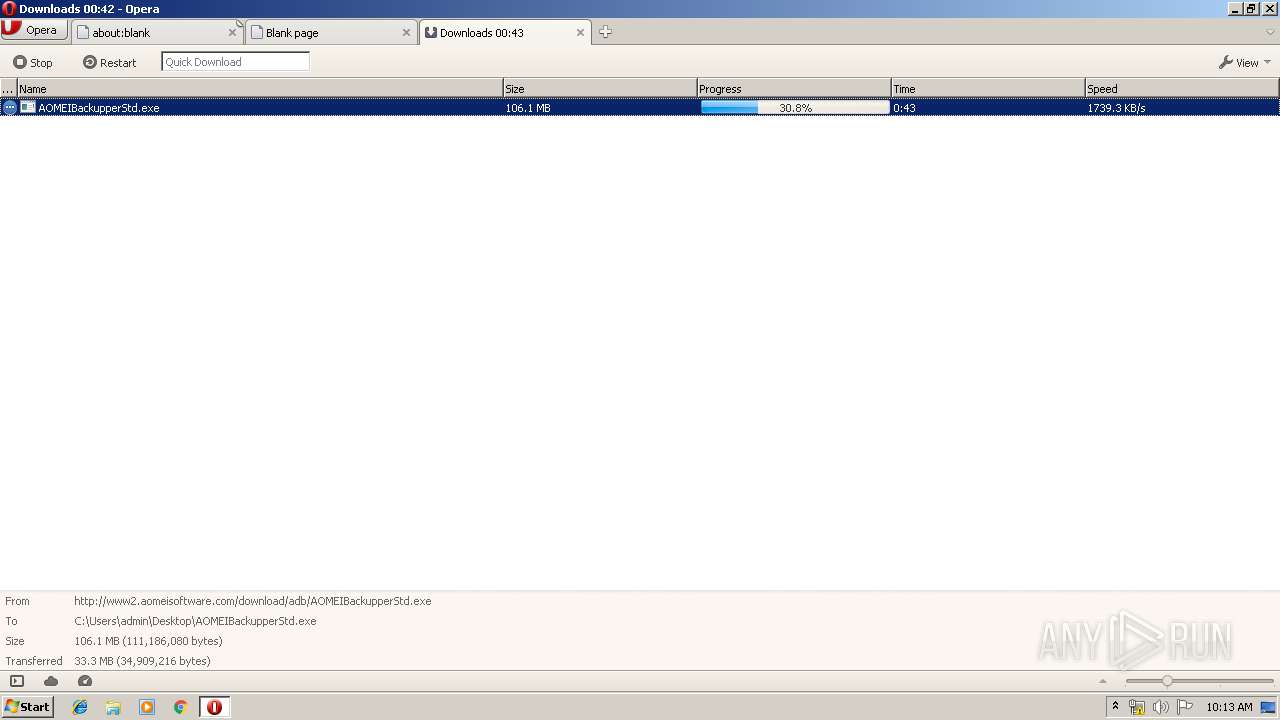
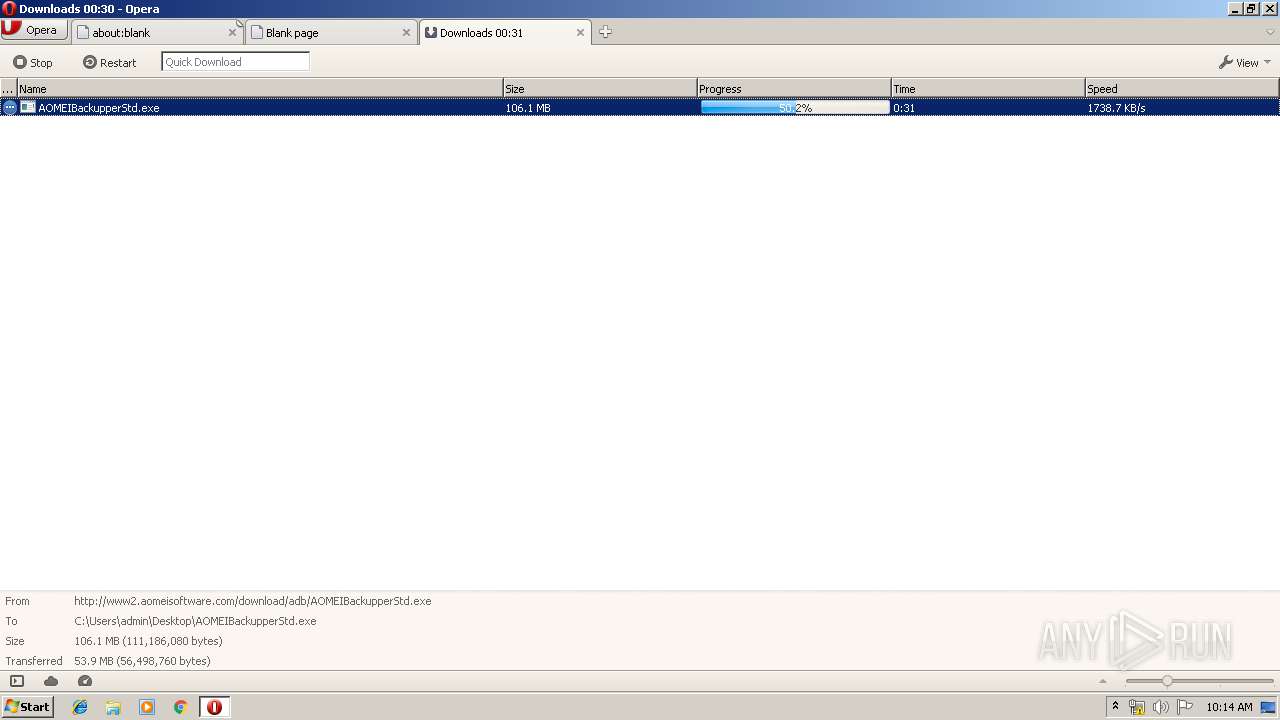
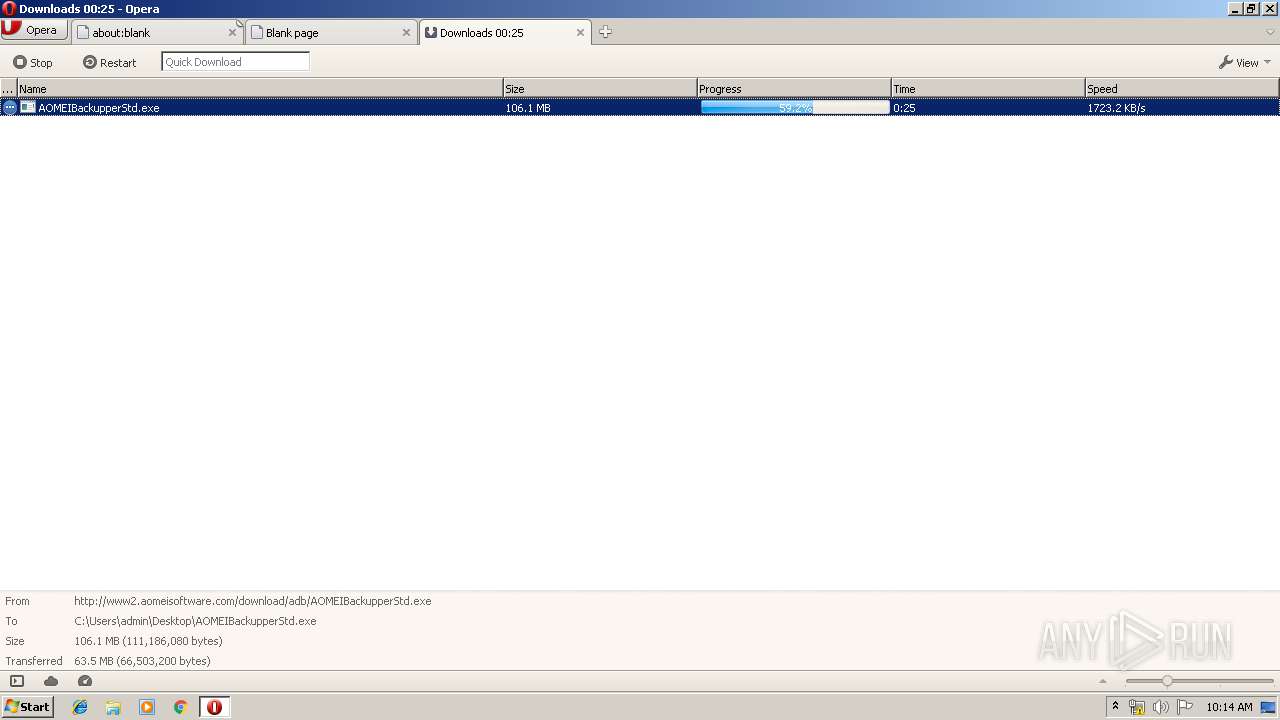
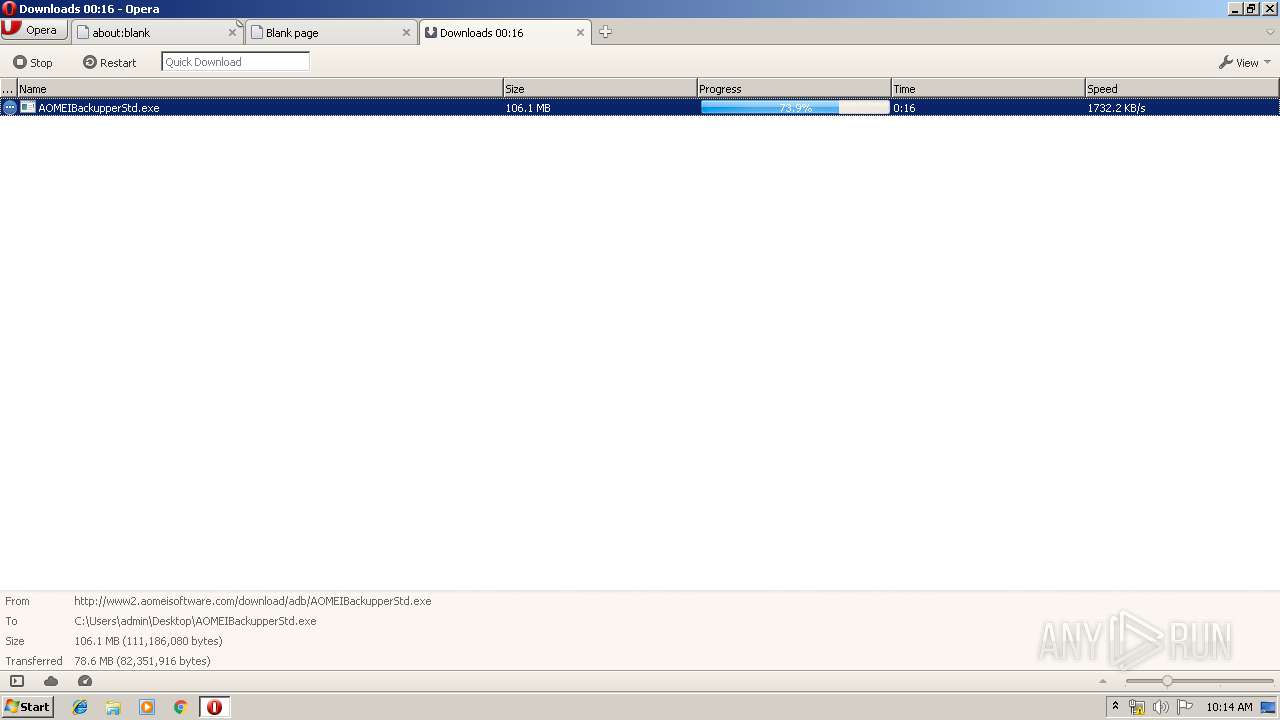
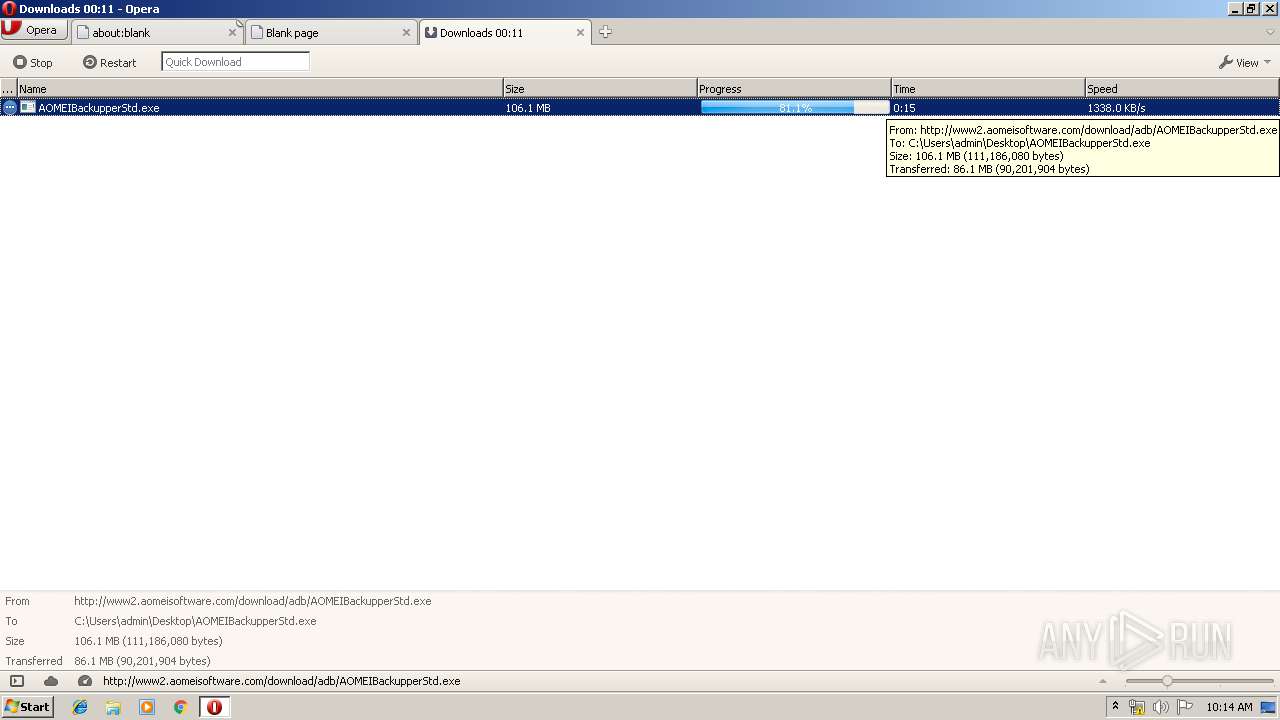
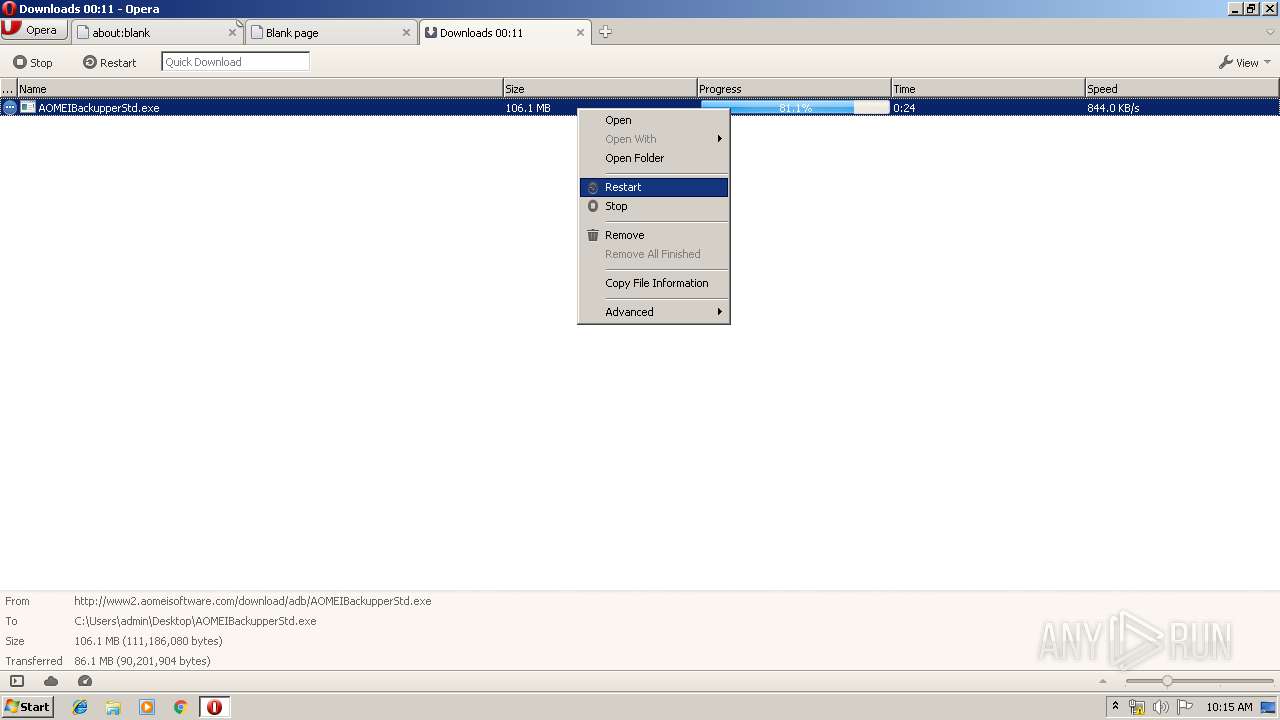
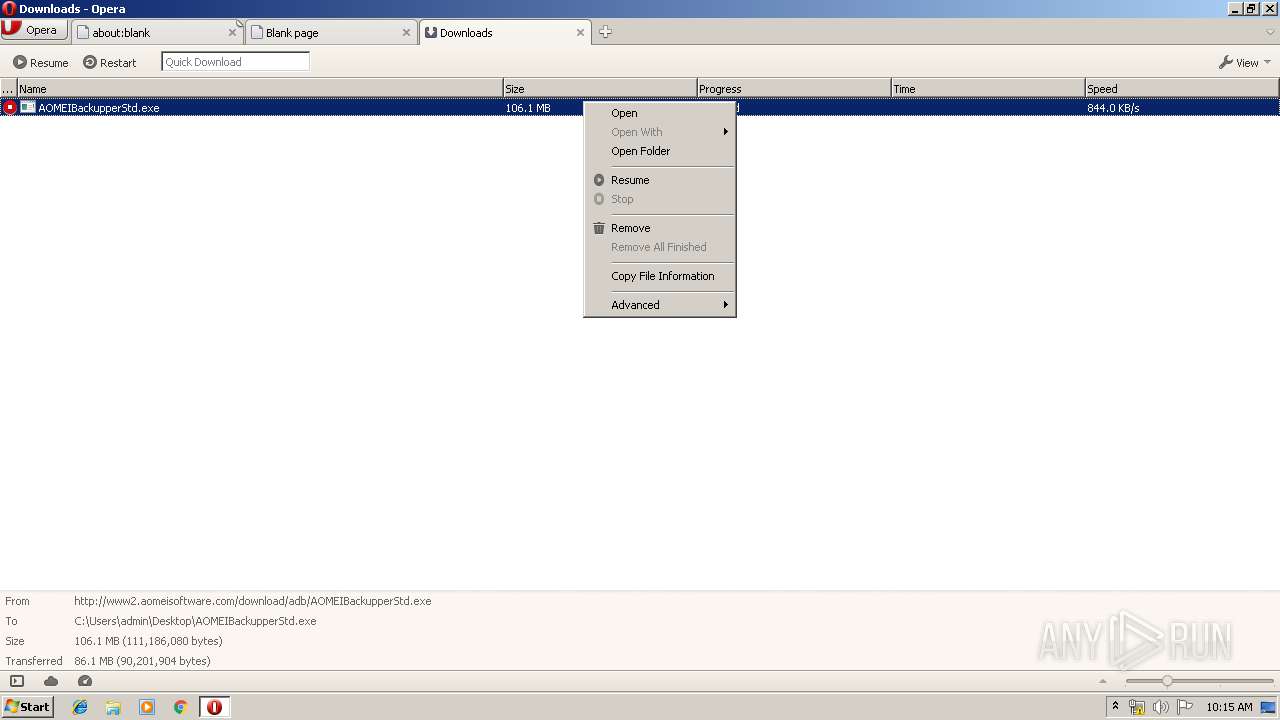
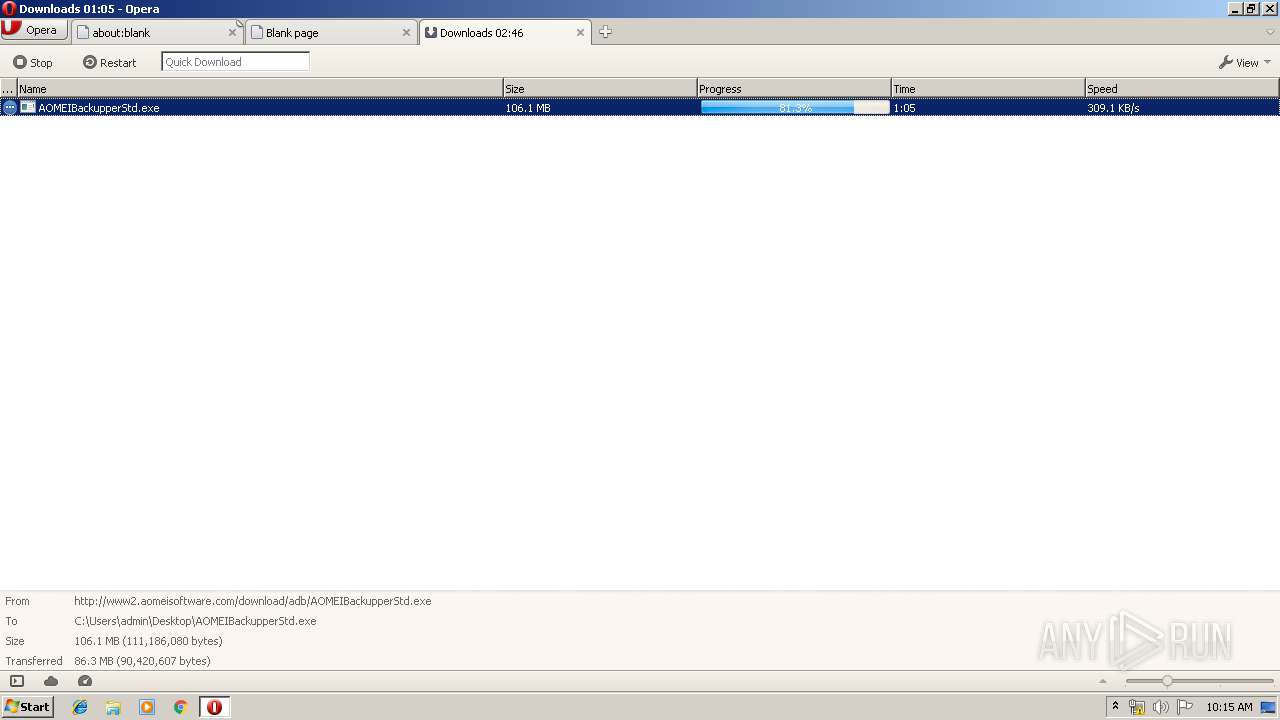
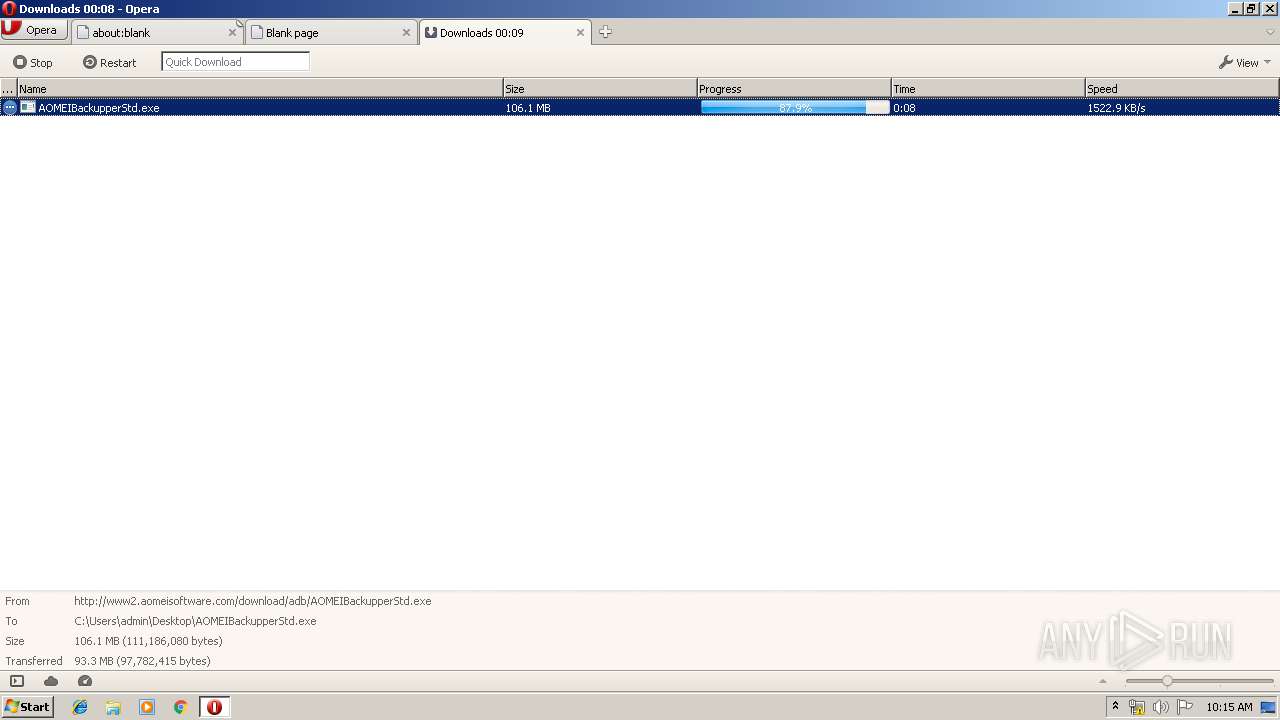
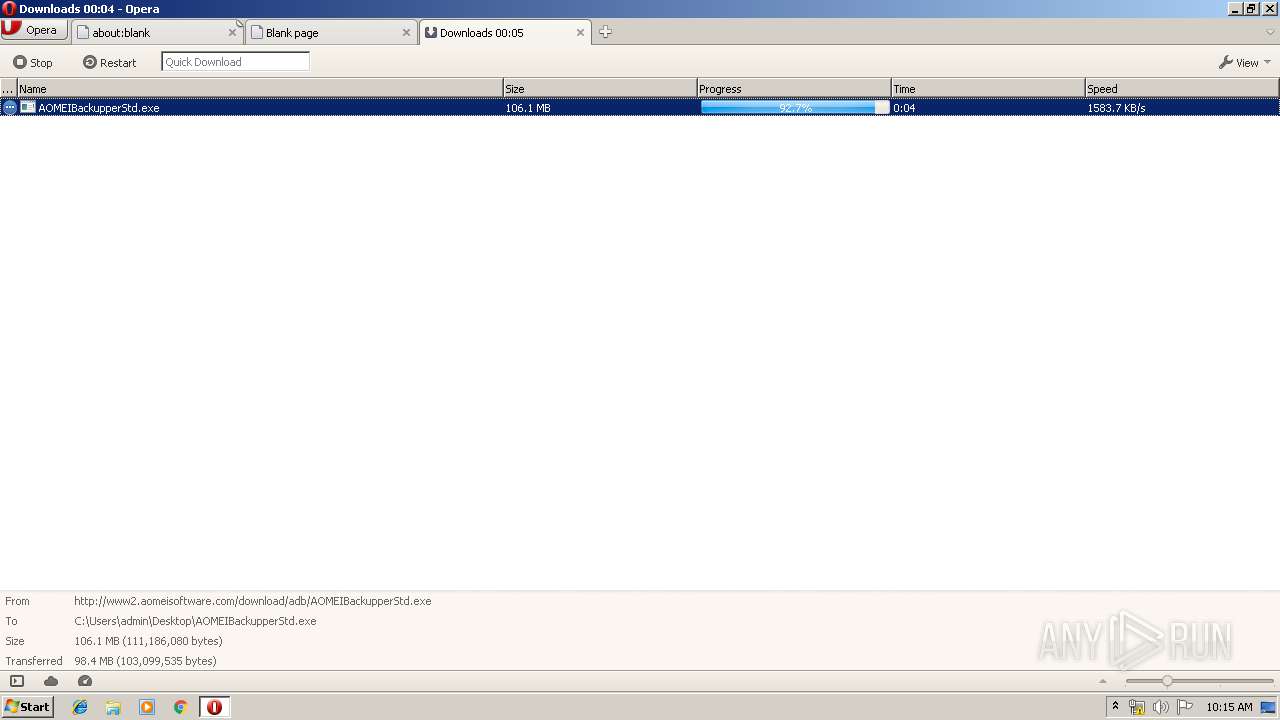
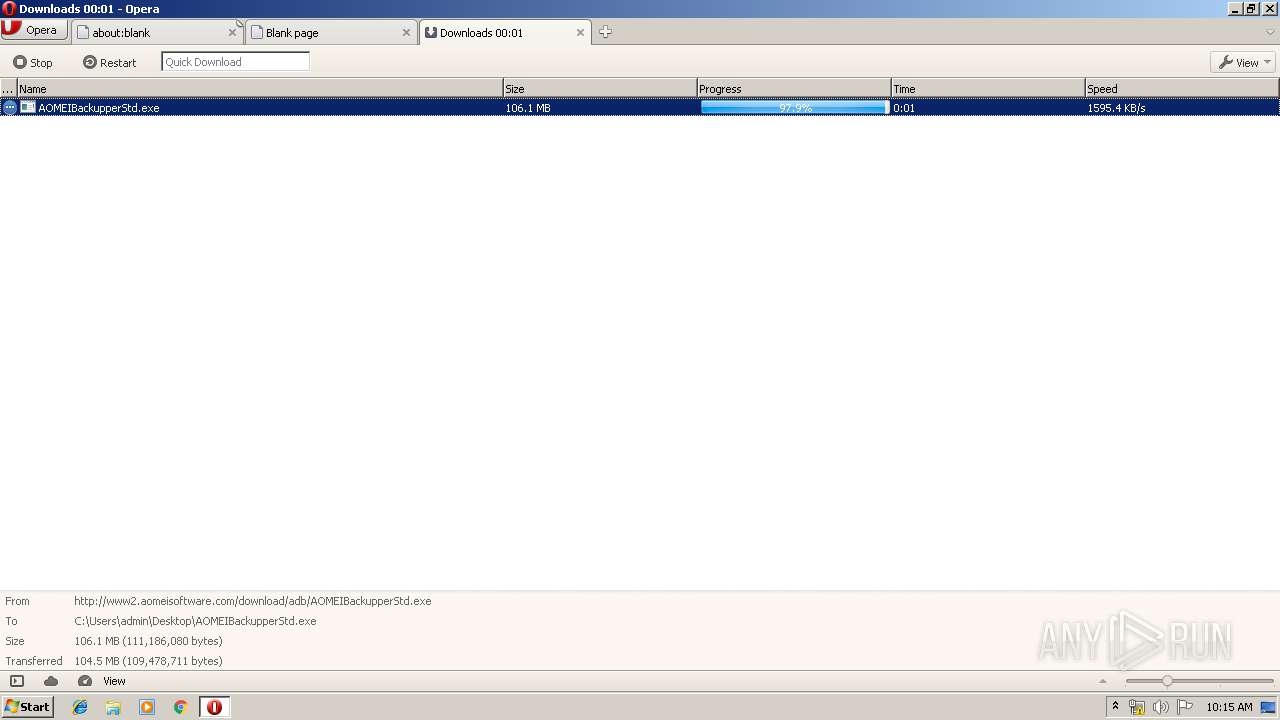
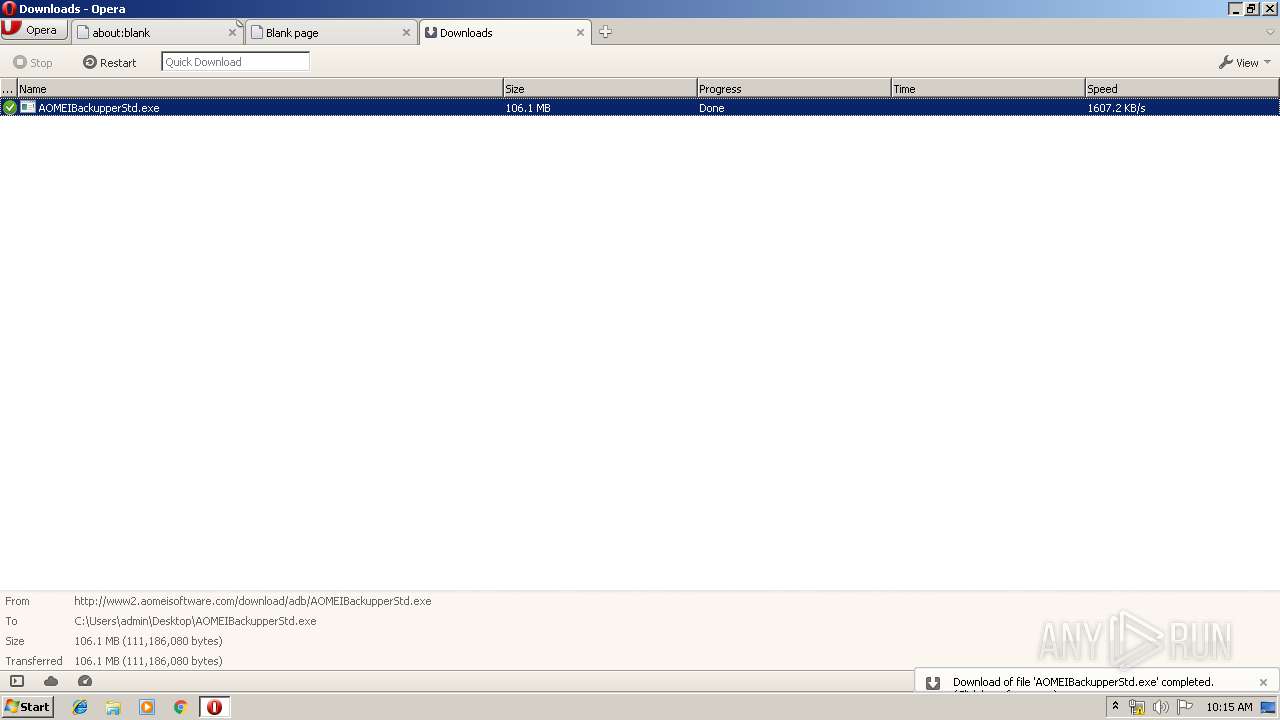
| URL: | http://www2.aomeisoftware.com/download/adb/AOMEIBackupperStd.exe |
| Full analysis: | https://app.any.run/tasks/d1c0e44f-0579-40df-a15c-b3e1e916df67 |
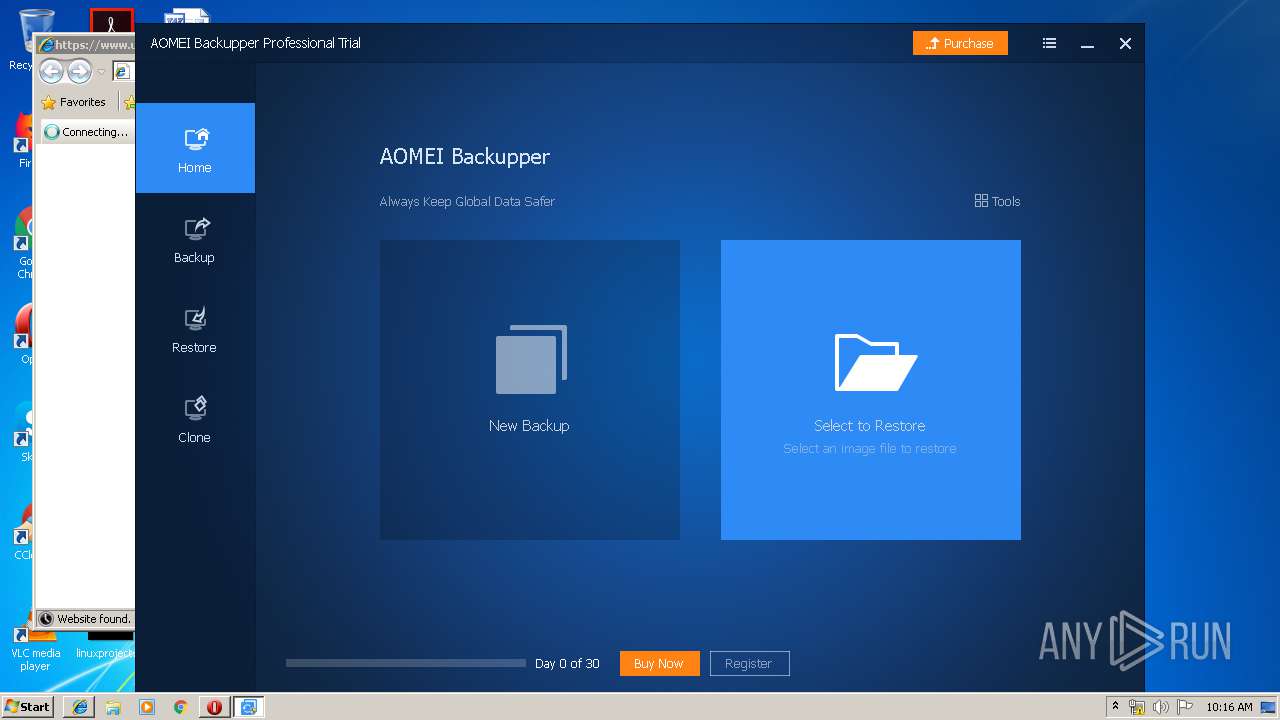
| Verdict: | Malicious activity |
| Analysis date: | September 27, 2019, 09:13:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5709000EDD896DB75BF5DD15997E025D |
| SHA1: | 62E992A542D2496A9C361F26E7E43E78DF0BE893 |
| SHA256: | 8BDB14C3DE33EAE15701AC50DBCA1F55F2D73B00C6C12530A4191B647713BFF1 |
| SSDEEP: | 3:N1KJSk/TxKLoq5TuVVAsN:Cck/ozTf0 |
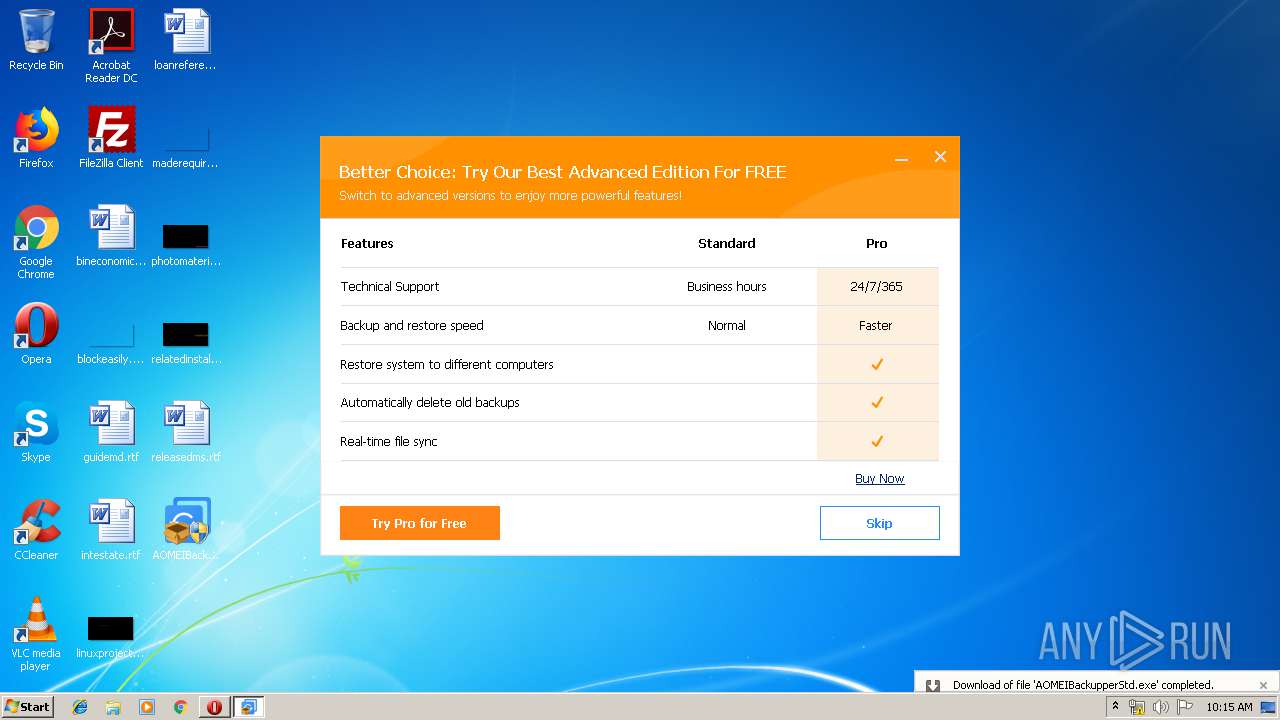
MALICIOUS
Application was dropped or rewritten from another process
- AOMEIBackupperStd.exe (PID: 2652)
- AOMEIBackupperStd.exe (PID: 3448)
- ABService.exe (PID: 3512)
- ABService.exe (PID: 2900)
- ValidCheck.exe (PID: 2224)
- Backupper.exe (PID: 3620)
- LoadDrv.exe (PID: 2440)
- ABService.exe (PID: 4064)
Loads dropped or rewritten executable
- ABService.exe (PID: 3512)
- ABService.exe (PID: 2900)
- Backupper.exe (PID: 3620)
- ABService.exe (PID: 4064)
Changes the autorun value in the registry
- ABService.exe (PID: 4064)
SUSPICIOUS
Executable content was dropped or overwritten
- opera.exe (PID: 2784)
- AOMEIBackupperStd.exe (PID: 3448)
- AOMEIBackupperStd.tmp (PID: 2200)
Reads Windows owner or organization settings
- AOMEIBackupperStd.tmp (PID: 2200)
Reads internet explorer settings
- AOMEIBackupperStd.tmp (PID: 2200)
Reads the Windows organization settings
- AOMEIBackupperStd.tmp (PID: 2200)
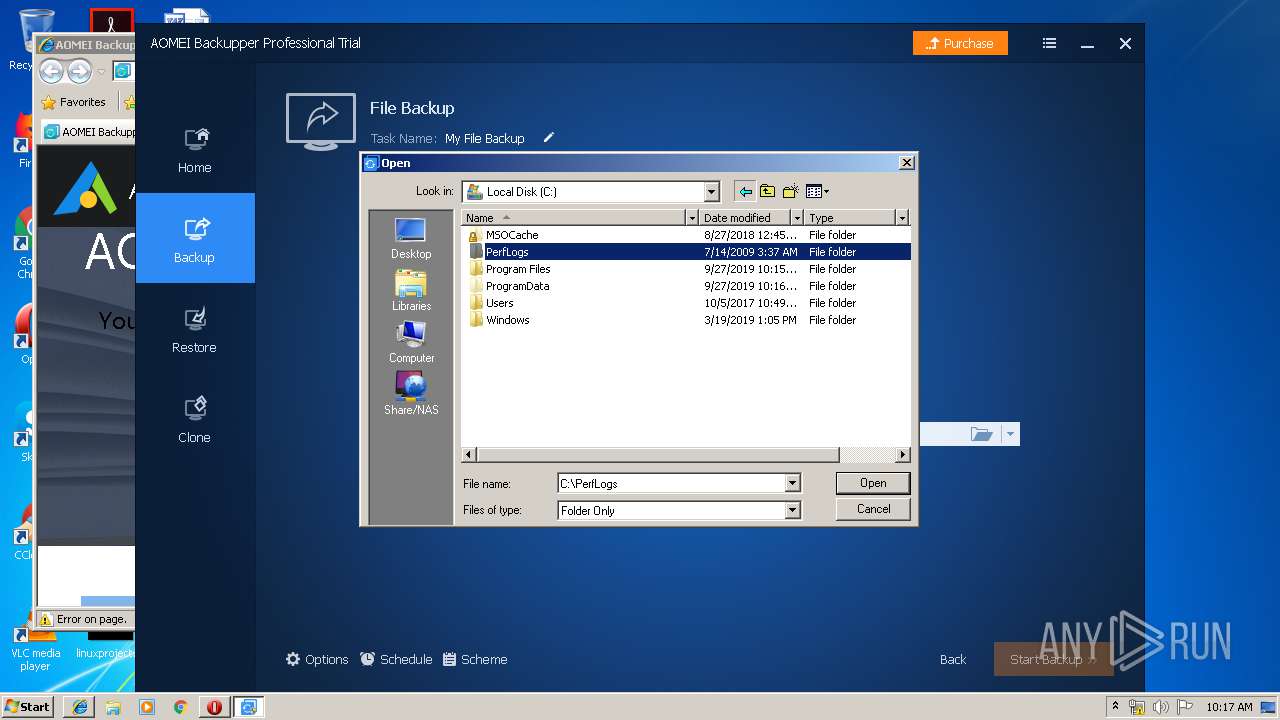
Creates files in the Windows directory
- AOMEIBackupperStd.tmp (PID: 2200)
- ValidCheck.exe (PID: 2224)
Reads Internet Cache Settings
- AOMEIBackupperStd.tmp (PID: 2200)
Creates files in the program directory
- ABService.exe (PID: 2900)
- ValidCheck.exe (PID: 2224)
- ABService.exe (PID: 4064)
- Backupper.exe (PID: 3620)
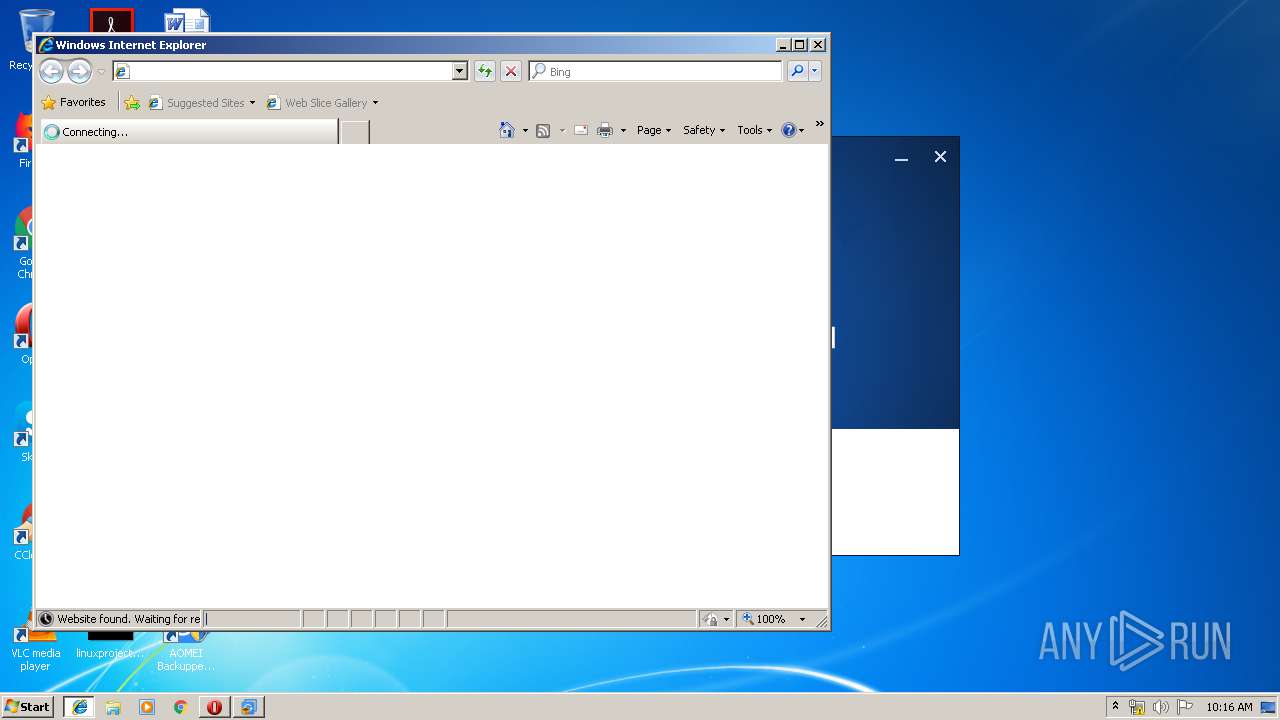
Starts Internet Explorer
- AOMEIBackupperStd.tmp (PID: 2200)
Executed as Windows Service
- ABService.exe (PID: 4064)
Searches for installed software
- AOMEIBackupperStd.tmp (PID: 2200)
Uses WMIC.EXE to obtain a system information
- ABService.exe (PID: 4064)
- Backupper.exe (PID: 3620)
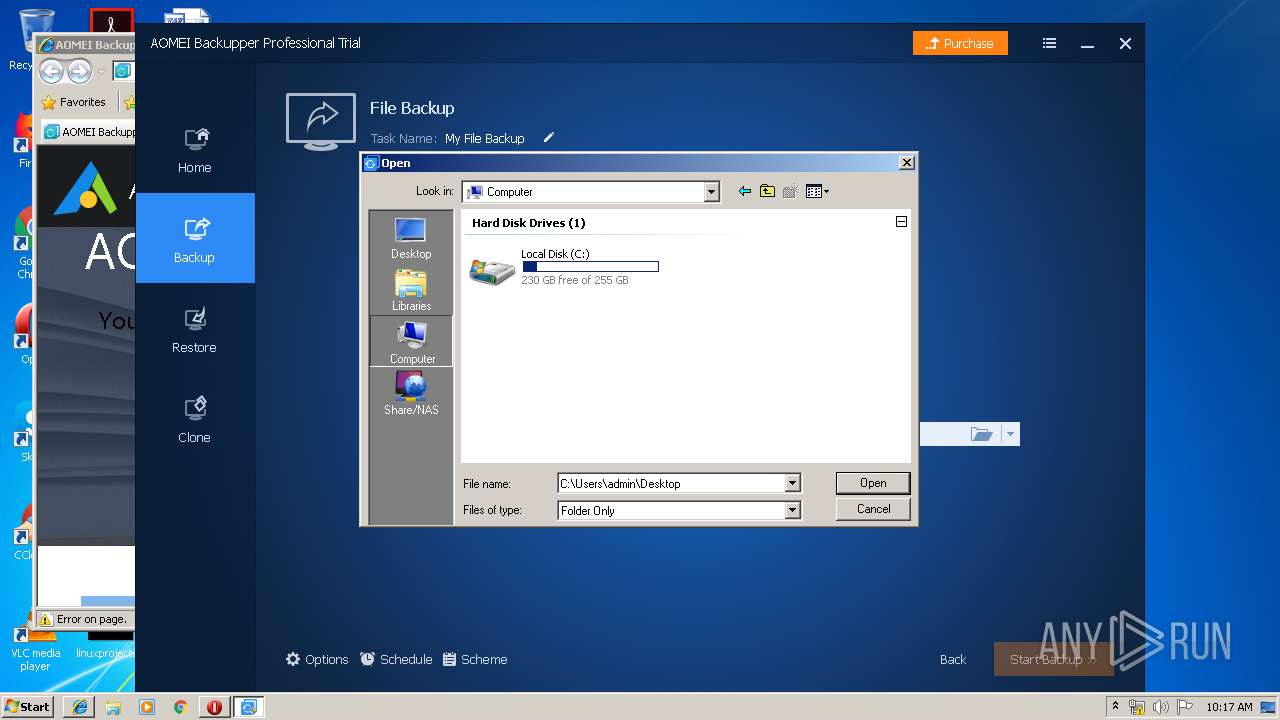
Low-level read access rights to disk partition
- Backupper.exe (PID: 3620)
- ABService.exe (PID: 4064)
INFO
Creates files in the user directory
- opera.exe (PID: 2784)
- iexplore.exe (PID: 2780)
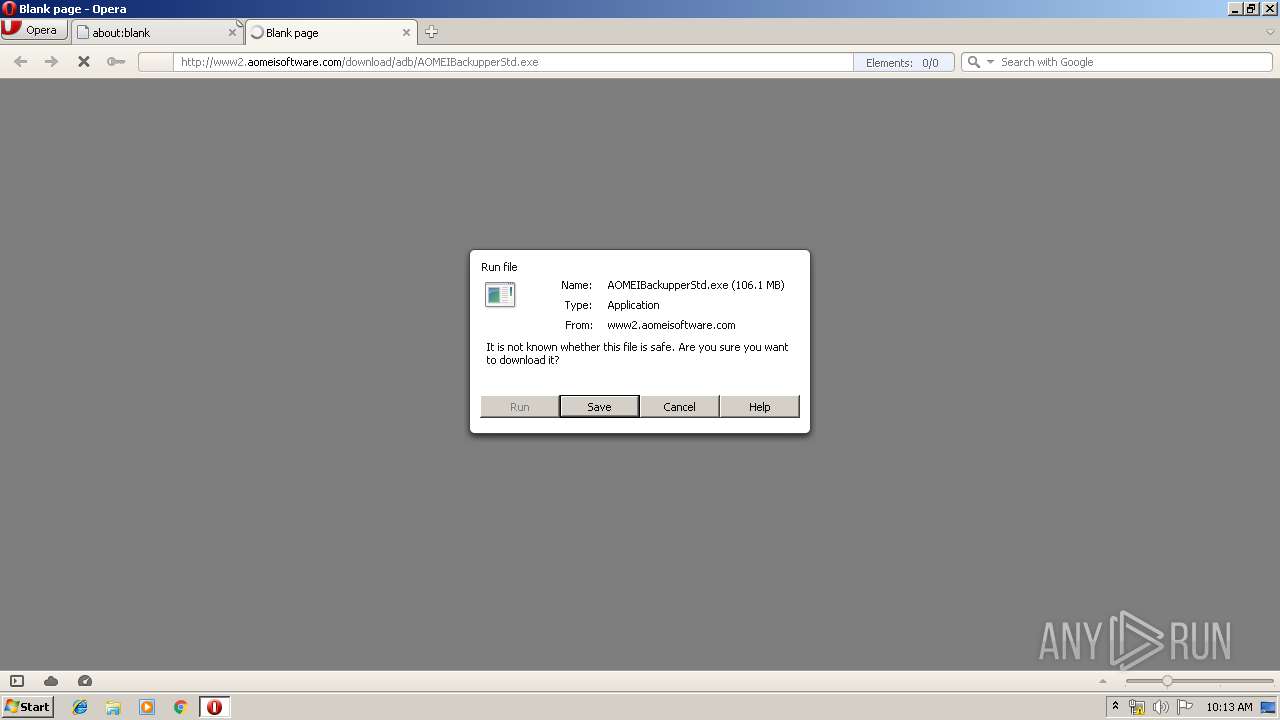
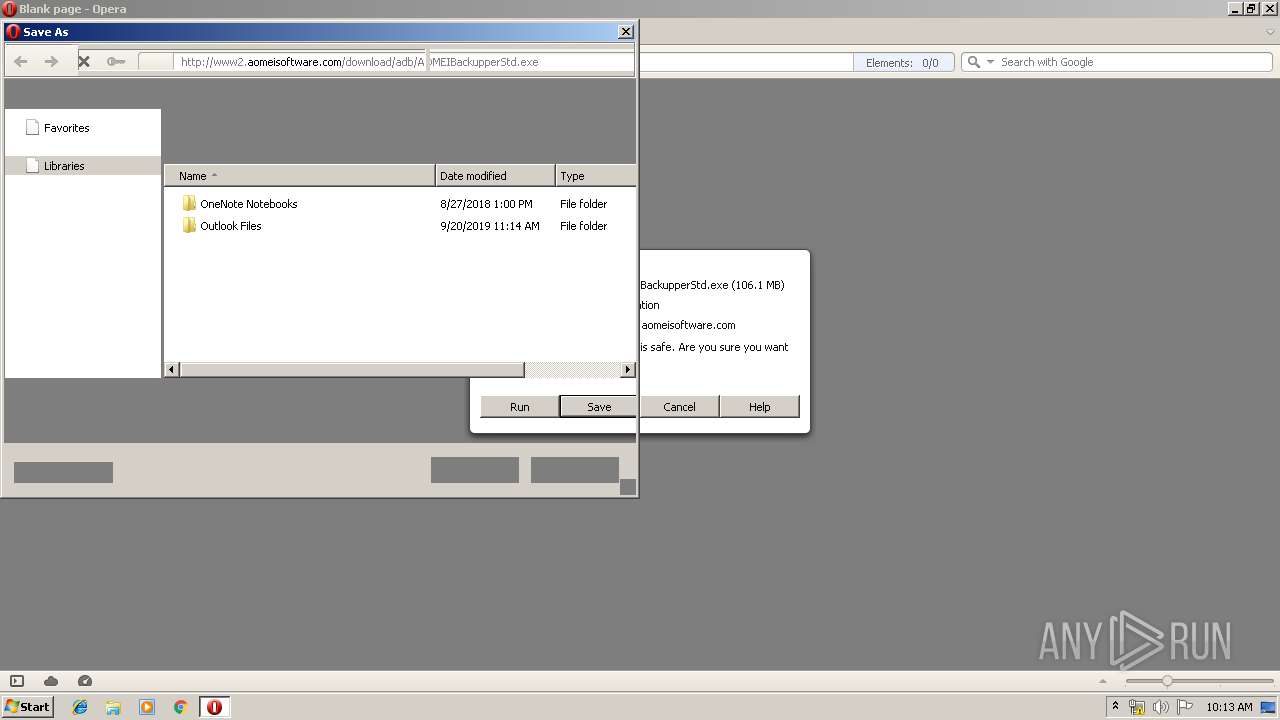
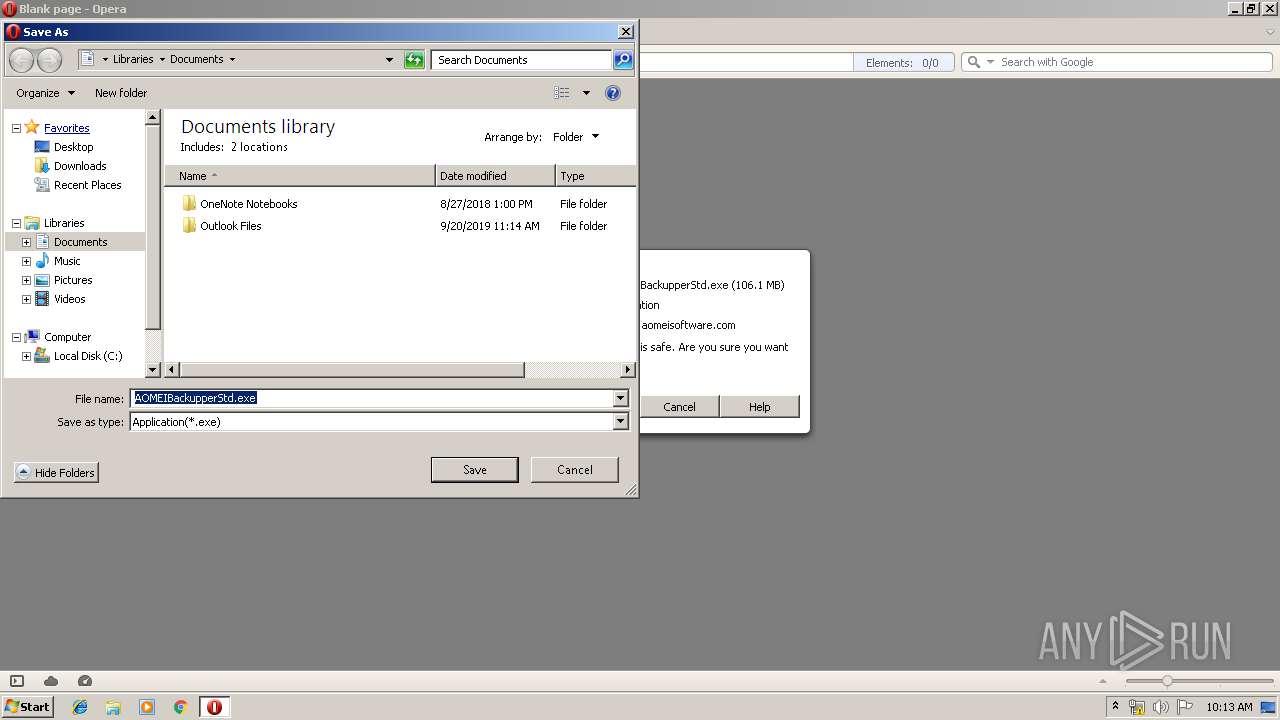
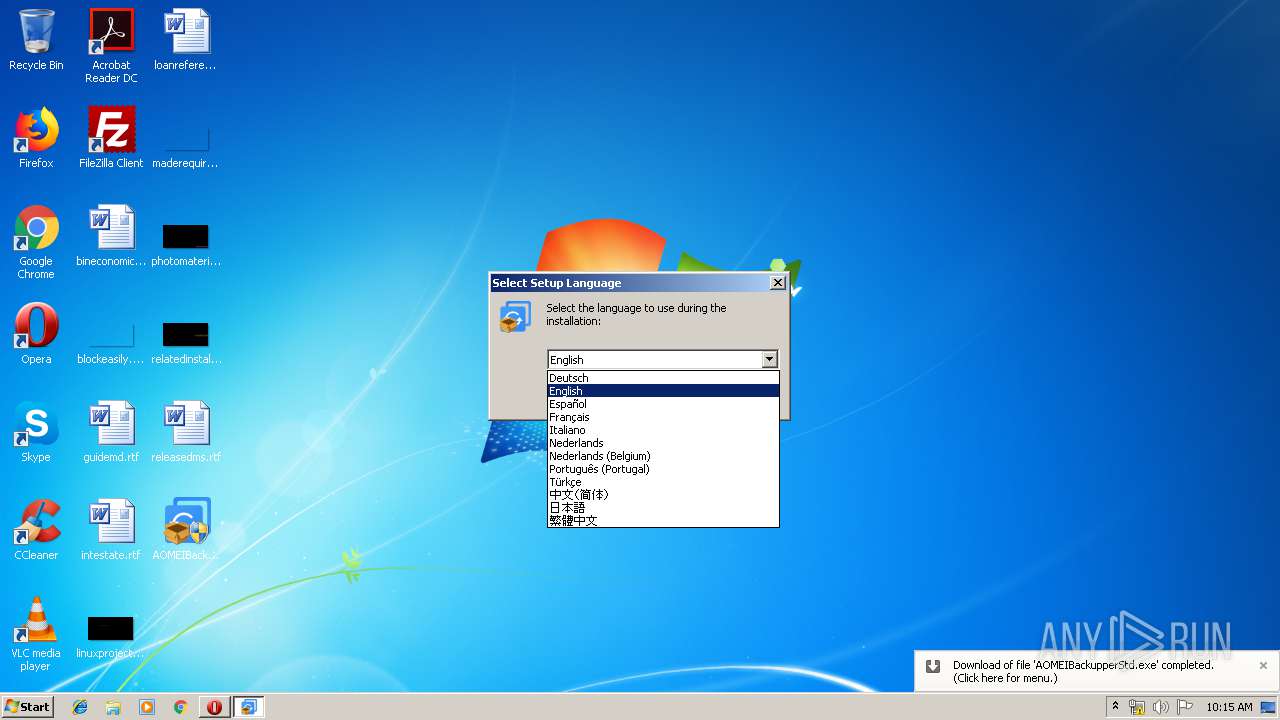
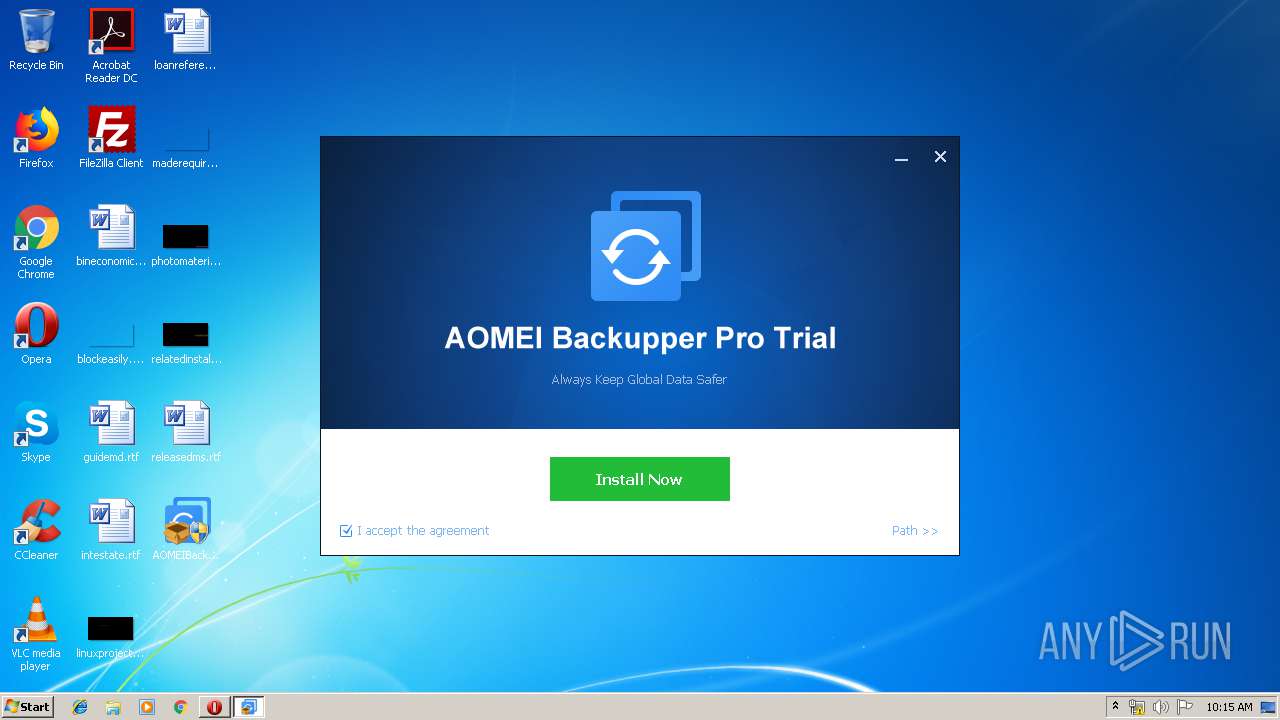
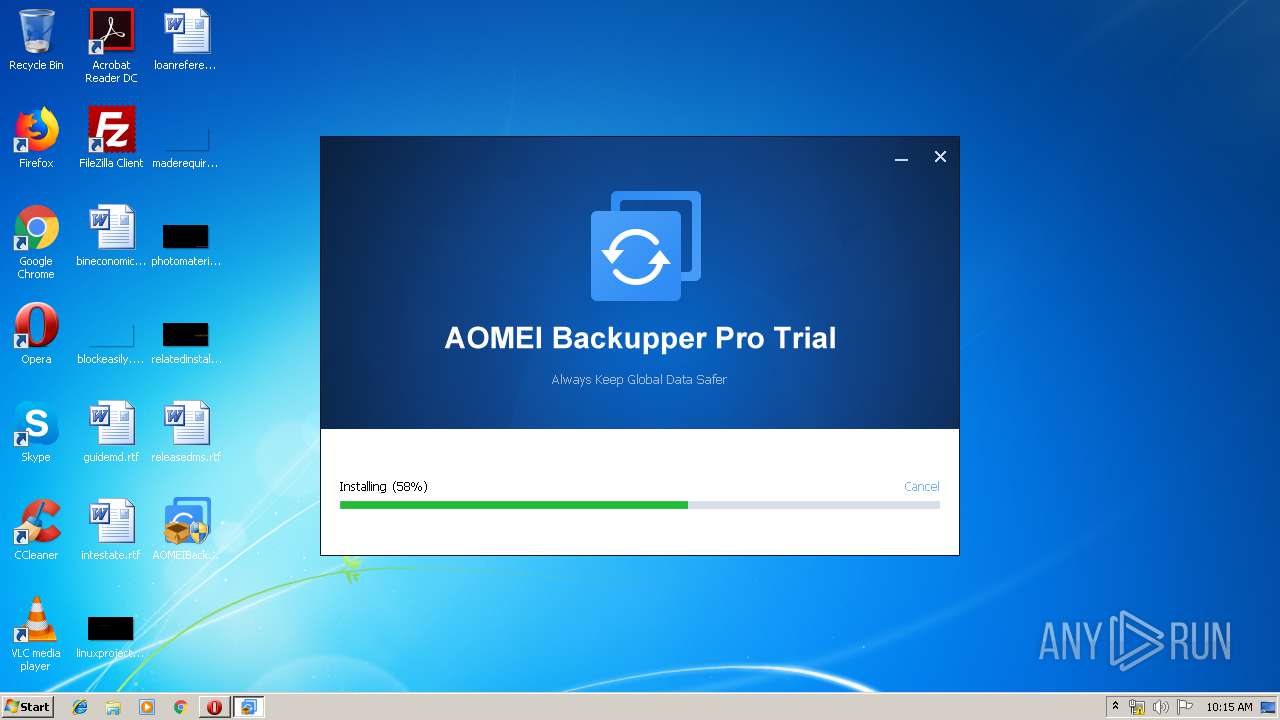
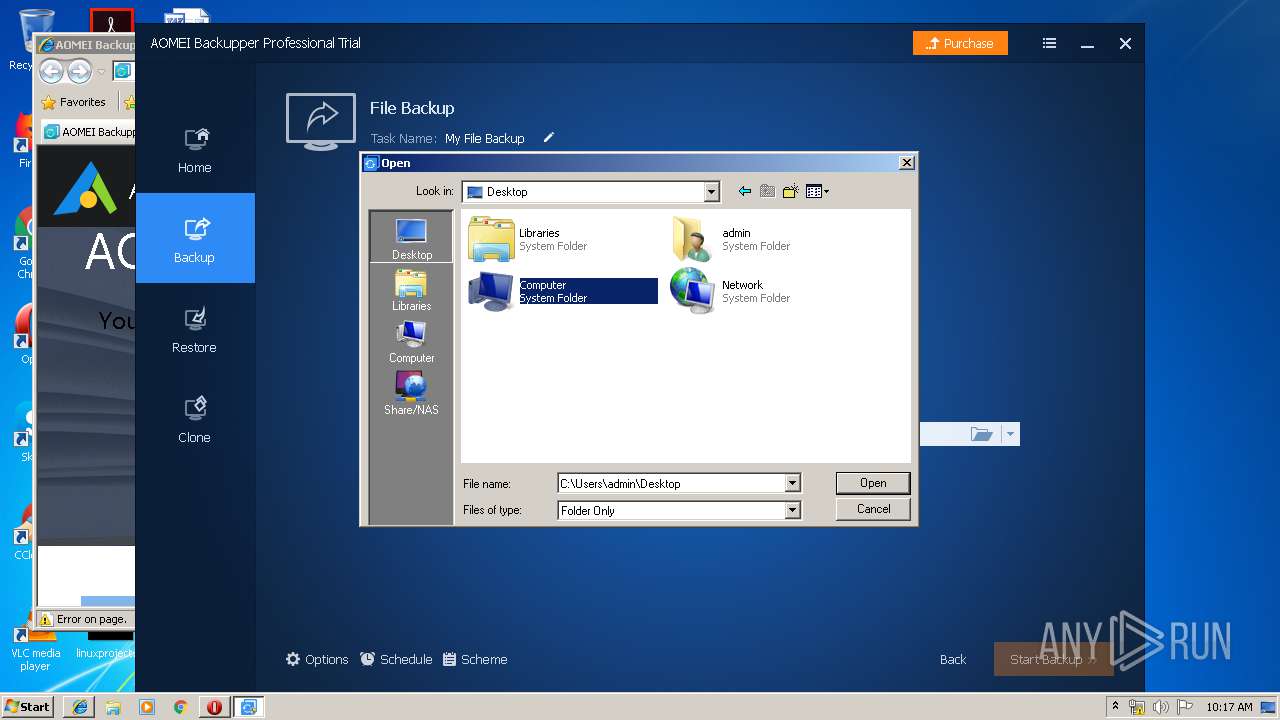
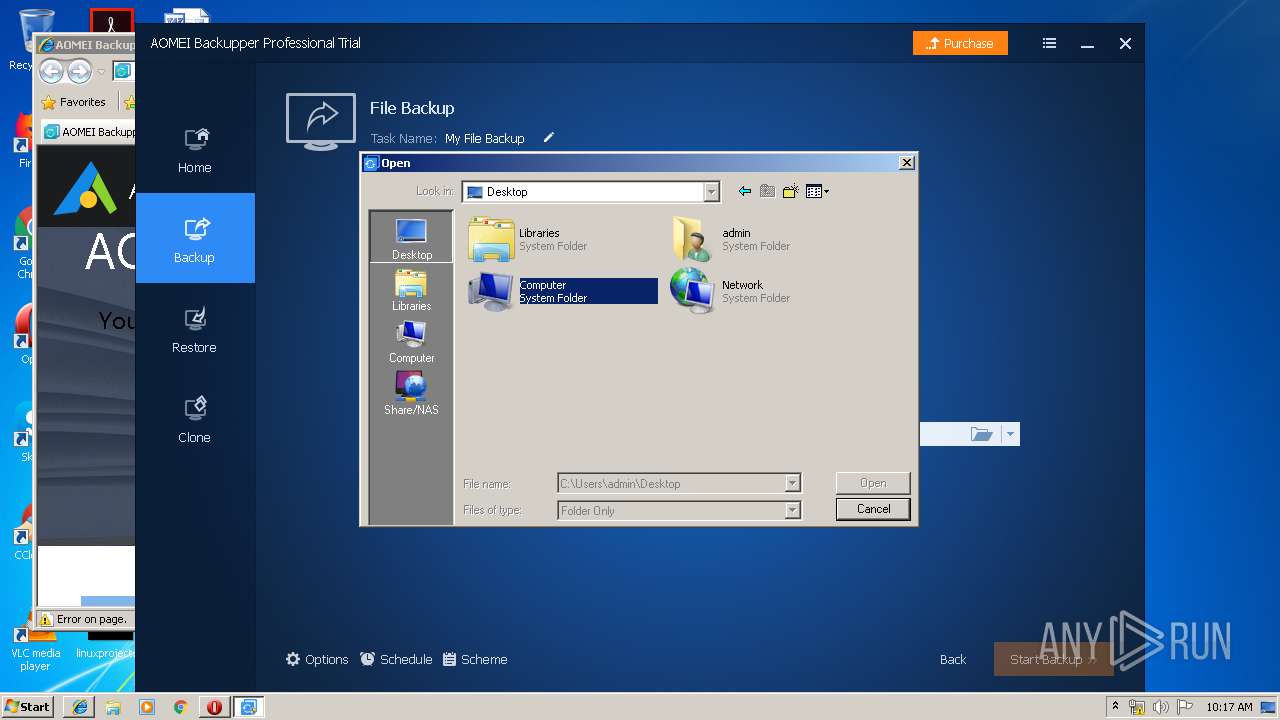
Manual execution by user
- AOMEIBackupperStd.exe (PID: 2652)
- AOMEIBackupperStd.exe (PID: 3448)
Loads dropped or rewritten executable
- AOMEIBackupperStd.tmp (PID: 2200)
Creates a software uninstall entry
- AOMEIBackupperStd.tmp (PID: 2200)
Reads Internet Cache Settings
- opera.exe (PID: 2784)
Dropped object may contain Bitcoin addresses
- AOMEIBackupperStd.tmp (PID: 2200)
Application was dropped or rewritten from another process
- AOMEIBackupperStd.tmp (PID: 2200)
- IUHelper.exe (PID: 2332)
Application launched itself
- iexplore.exe (PID: 3564)
Changes settings of System certificates
- iexplore.exe (PID: 2780)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2780)
Changes internet zones settings
- iexplore.exe (PID: 3564)
Creates files in the program directory
- IUHelper.exe (PID: 2332)
- AOMEIBackupperStd.tmp (PID: 2200)
Reads internet explorer settings
- iexplore.exe (PID: 2780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
16
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | wmic cpu get processorid | C:\Windows\System32\Wbem\wmic.exe | — | ABService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | "C:\Users\admin\AppData\Local\Temp\is-VPDEG.tmp\AOMEIBackupperStd.tmp" /SL5="$301C4,110585412,433664,C:\Users\admin\Desktop\AOMEIBackupperStd.exe" | C:\Users\admin\AppData\Local\Temp\is-VPDEG.tmp\AOMEIBackupperStd.tmp | AOMEIBackupperStd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\AOMEI Backupper\ValidCheck.exe" RegTestCode|666 | C:\Program Files\AOMEI Backupper\ValidCheck.exe | — | AOMEIBackupperStd.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2332 | "C:\Users\admin\AppData\Local\Temp\is-7JBF9.tmp\IUHelper.exe" UA-78416831-14 AB_Trial Install | C:\Users\admin\AppData\Local\Temp\is-7JBF9.tmp\IUHelper.exe | AOMEIBackupperStd.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\AOMEI Backupper\LoadDrv.exe" | C:\Program Files\AOMEI Backupper\LoadDrv.exe | AOMEIBackupperStd.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2652 | "C:\Users\admin\Desktop\AOMEIBackupperStd.exe" | C:\Users\admin\Desktop\AOMEIBackupperStd.exe | — | explorer.exe | |||||||||||
User: admin Company: AOMEI Technology Co., Ltd. Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: 5.2.0 Modules
| |||||||||||||||
| 2772 | wmic cpu get processorid | C:\Windows\System32\Wbem\wmic.exe | — | Backupper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3564 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Opera\opera.exe" "http://www2.aomeisoftware.com/download/adb/AOMEIBackupperStd.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2900 | "C:\Program Files\AOMEI Backupper\ABService.exe" | C:\Program Files\AOMEI Backupper\ABService.exe | AOMEIBackupperStd.tmp | ||||||||||||
User: admin Company: AOMEI Tech Co., Ltd. Integrity Level: HIGH Description: AOMEI Backupper Schedule task service Exit code: 0 Version: 5, 2, 0, 0 Modules
| |||||||||||||||
Total events
4 561
Read events
2 209
Write events
2 337
Delete events
15
Modification events
| (PID) Process: | (2784) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe "http://www2.aomeisoftware.com/download/adb/AOMEIBackupperStd.exe" | |||
| (PID) Process: | (2784) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2784) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2784) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000070000000100000009000000080000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2784) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2784) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2784) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2784) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (2784) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (2784) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | FFlags |
Value: 1092616257 | |||
Executable files
198
Suspicious files
45
Text files
177
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2784 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr4E65.tmp | — | |
MD5:— | SHA256:— | |||
| 2784 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr4E76.tmp | — | |
MD5:— | SHA256:— | |||
| 2784 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr4EB5.tmp | — | |
MD5:— | SHA256:— | |||
| 2784 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00002.tmp | — | |
MD5:— | SHA256:— | |||
| 2784 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\O8O8UH7KNX12P63OLRK0.temp | — | |
MD5:— | SHA256:— | |||
| 2784 | opera.exe | C:\Users\admin\Desktop\AOMEIBackupperStd.exe | — | |
MD5:— | SHA256:— | |||
| 2784 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 2784 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2784 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opcacrt6.dat | binary | |
MD5:59761E989F564F76A3A4B778DB7ABCF1 | SHA256:AF879942D234D85C0CE75921DBDDA50E2F6D135BD961F259106131751359052B | |||
| 2784 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\optrust.dat | binary | |
MD5:1AA8644C9261DC10F7247F6A145C1DD2 | SHA256:58A8933F65361633C6AB194000D312DC9D566F717B1A16814A0DBEE24A60EBE3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
21
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2784 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 528 b | whitelisted |
2784 | opera.exe | GET | 206 | 104.28.8.219:80 | http://www2.aomeisoftware.com/download/adb/AOMEIBackupperStd.exe | US | binary | 20.0 Mb | suspicious |
3564 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2784 | opera.exe | GET | — | 107.167.110.216:80 | http://sitecheck2.opera.com/?host=www2.aomeisoftware.com&hdn=%2BH9VgGwo/eqgs4na7uwiuw== | US | — | — | whitelisted |
2780 | iexplore.exe | GET | 301 | 104.24.5.19:80 | http://www.backup-utility.com/help/index.html | US | — | — | shared |
2784 | opera.exe | GET | — | 104.28.8.219:80 | http://www2.aomeisoftware.com/download/adb/AOMEIBackupperStd.exe | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2784 | opera.exe | 104.28.8.219:80 | www2.aomeisoftware.com | Cloudflare Inc | US | shared |
2784 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2780 | iexplore.exe | 104.24.5.19:80 | www.backup-utility.com | Cloudflare Inc | US | shared |
2784 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2332 | IUHelper.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3564 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 104.25.132.107:80 | www.aomeitech.com | Cloudflare Inc | US | shared |
2780 | iexplore.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2780 | iexplore.exe | 64.233.167.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2784 | opera.exe | 107.167.110.216:80 | sitecheck2.opera.com | Opera Software Americas LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www2.aomeisoftware.com |
| suspicious |
sitecheck2.opera.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
www.backup-utility.com |
| unknown |
www.bing.com |
| whitelisted |
www.ubackup.com |
| suspicious |
www.google-analytics.com |
| whitelisted |
www.aomeitech.com |
| suspicious |
stats.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2784 | opera.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
ABService.exe | [0 ]::GetFileAttributesA(sCurPath)!=INVALID_FILE_ATTRIBUTES return code: 0x0103100B, NetworkMgr.cpp(259).
|
LoadDrv.exe | ------------Install AMPA Drive-----------------
|
LoadDrv.exe | OpenSCManager() ok !
|
LoadDrv.exe | CrateService() ok !
|
LoadDrv.exe | OpenSCManager() ok !
|
LoadDrv.exe | CrateService() ok !
|
LoadDrv.exe | OpenSCManager() ok !
|
LoadDrv.exe | CrateService() ok !
|
LoadDrv.exe | ==============CurrentVersion=============== |
LoadDrv.exe | 6.1 |