| File name: | Dati 522337.doc |
| Full analysis: | https://app.any.run/tasks/2ab8d7f2-bd9c-48e0-81d0-4e7a351f4fcc |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 25, 2019, 10:46:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
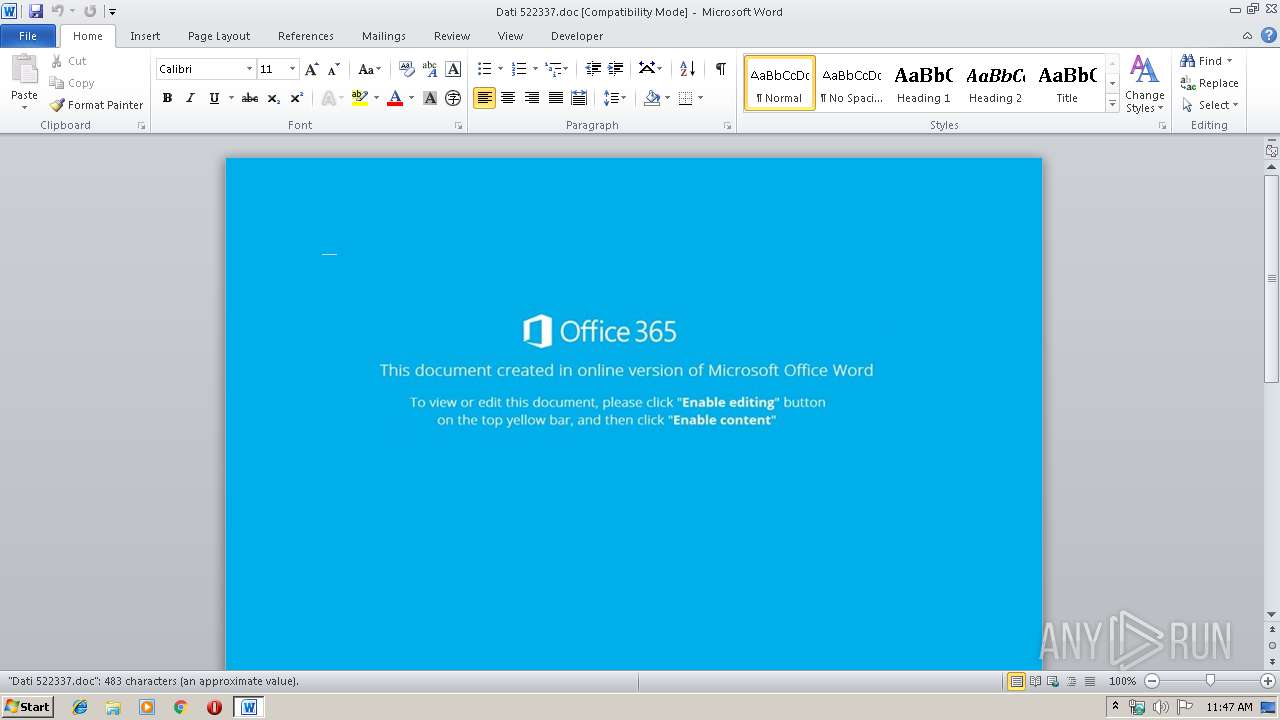
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Daria Wnuk, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Oct 25 10:40:00 2019, Last Saved Time/Date: Fri Oct 25 10:40:00 2019, Number of Pages: 1, Number of Words: 87, Number of Characters: 499, Security: 0 |
| MD5: | F9E6FFF7F705A662B7839E5E260BE235 |
| SHA1: | 6D6B63932D5CE98D6C15157E198B7F6596B5B2DB |
| SHA256: | 8BD55564450B6BA955132F489990ED88ACD91146745FF19B1CB8B625B3B9F32C |
| SSDEEP: | 3072:NZEYFLDPhMu5xsdt84eOY5CTsdAPi2vLOhrN9ty6bzvDD:NZEYFLDPhMu5xsd+TbAi2sh9tySzv |
MALICIOUS
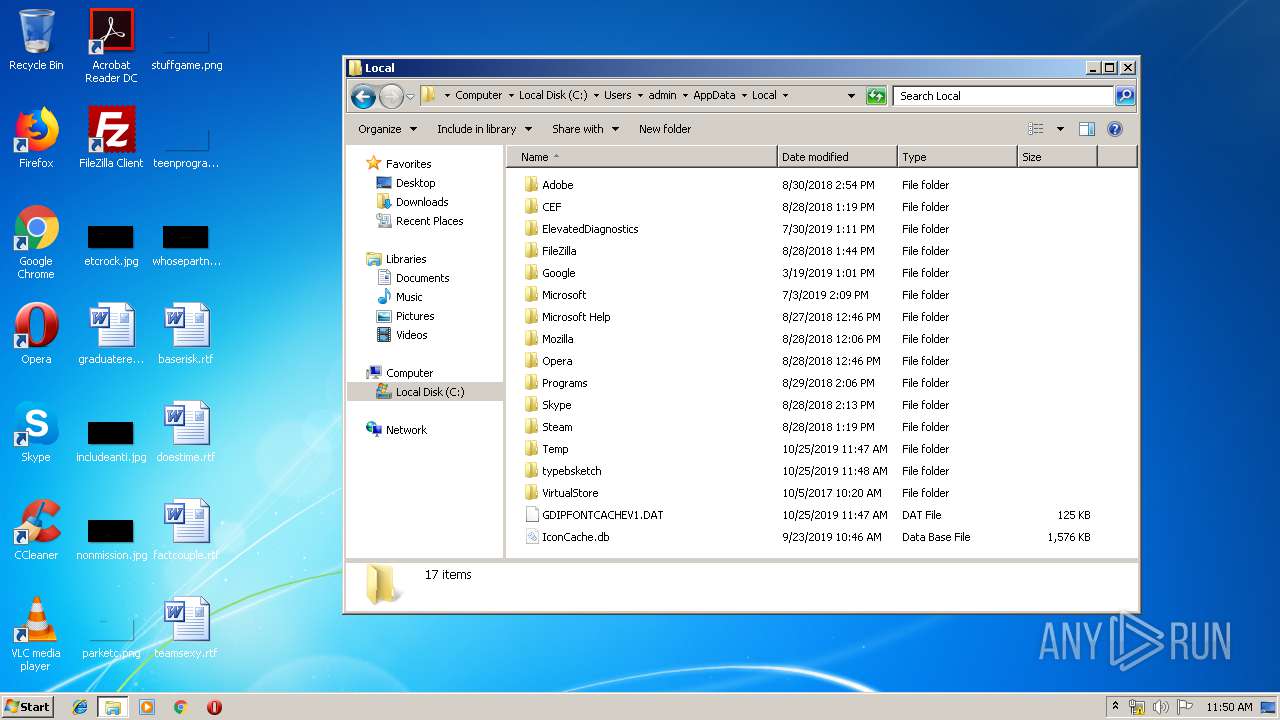
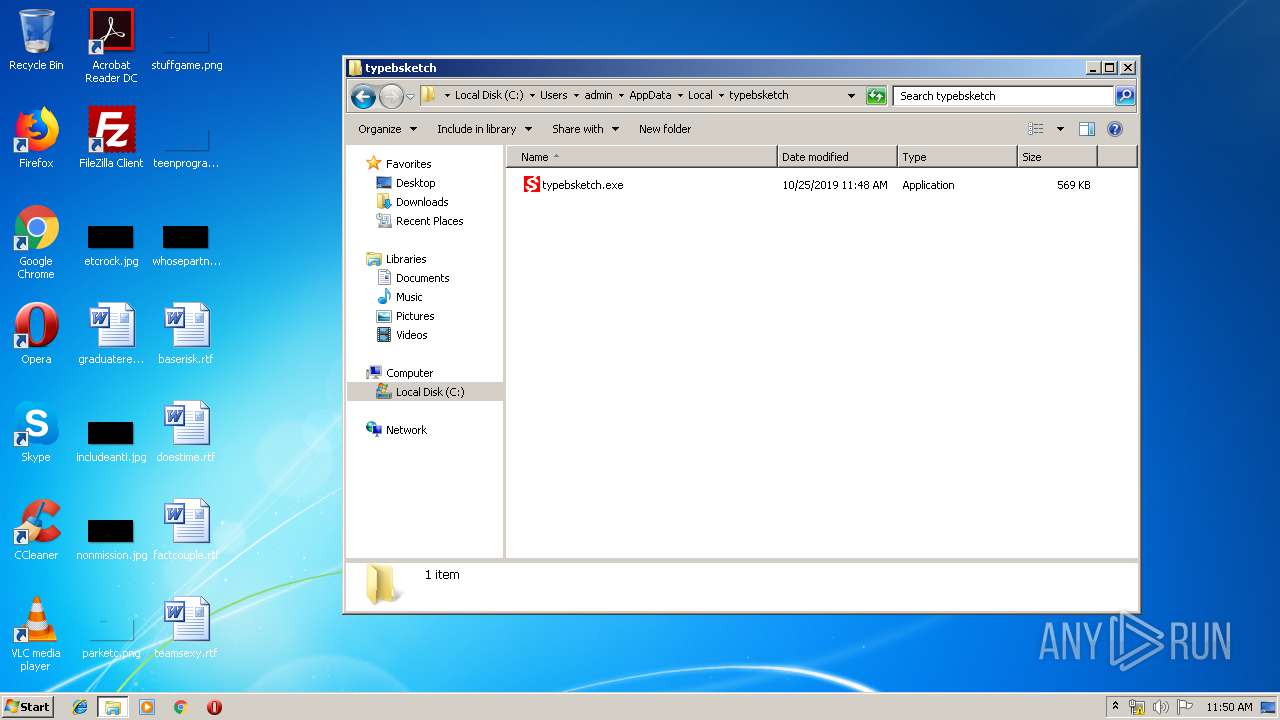
Application was dropped or rewritten from another process
- 196.exe (PID: 3920)
- typebsketch.exe (PID: 2436)
- 196.exe (PID: 2600)
- typebsketch.exe (PID: 3548)
- typebsketch.exe (PID: 2500)
- typebsketch.exe (PID: 2204)
Emotet process was detected
- 196.exe (PID: 2600)
EMOTET was detected
- typebsketch.exe (PID: 3548)
- typebsketch.exe (PID: 2204)
Changes the autorun value in the registry
- typebsketch.exe (PID: 3548)
Connects to CnC server
- typebsketch.exe (PID: 3548)
- typebsketch.exe (PID: 2204)
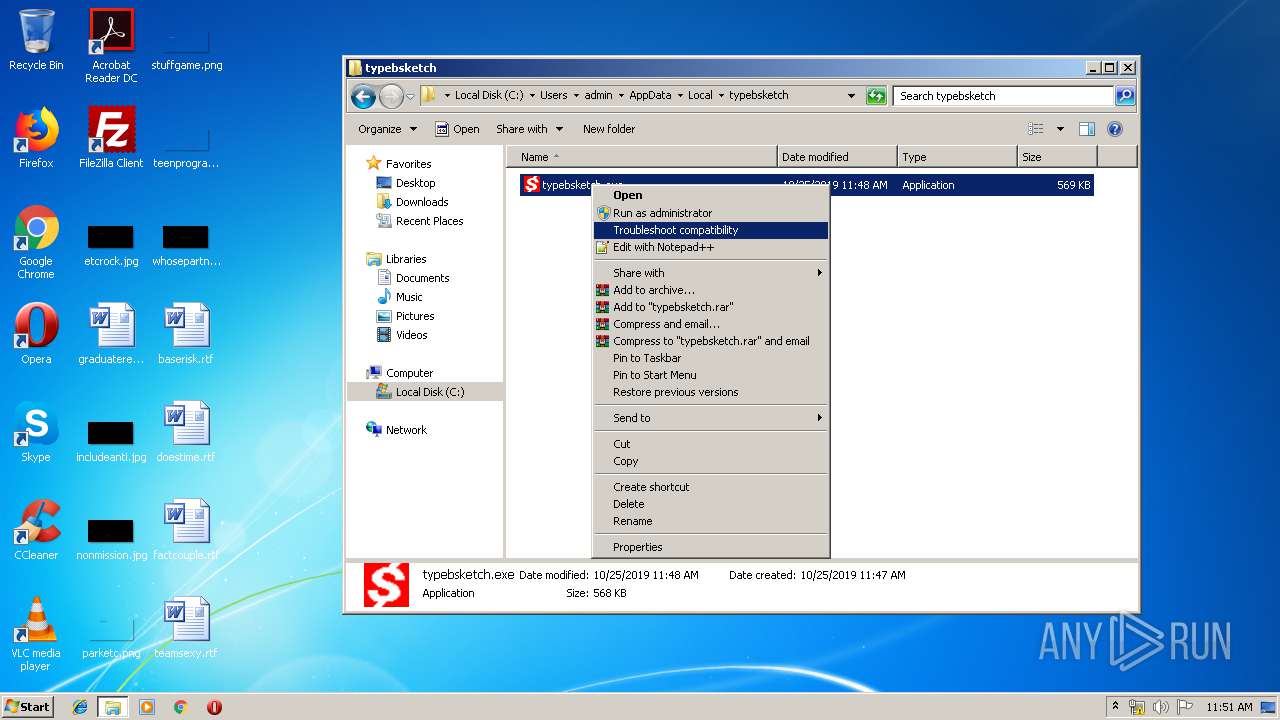
Starts Visual C# compiler
- sdiagnhost.exe (PID: 3836)
SUSPICIOUS
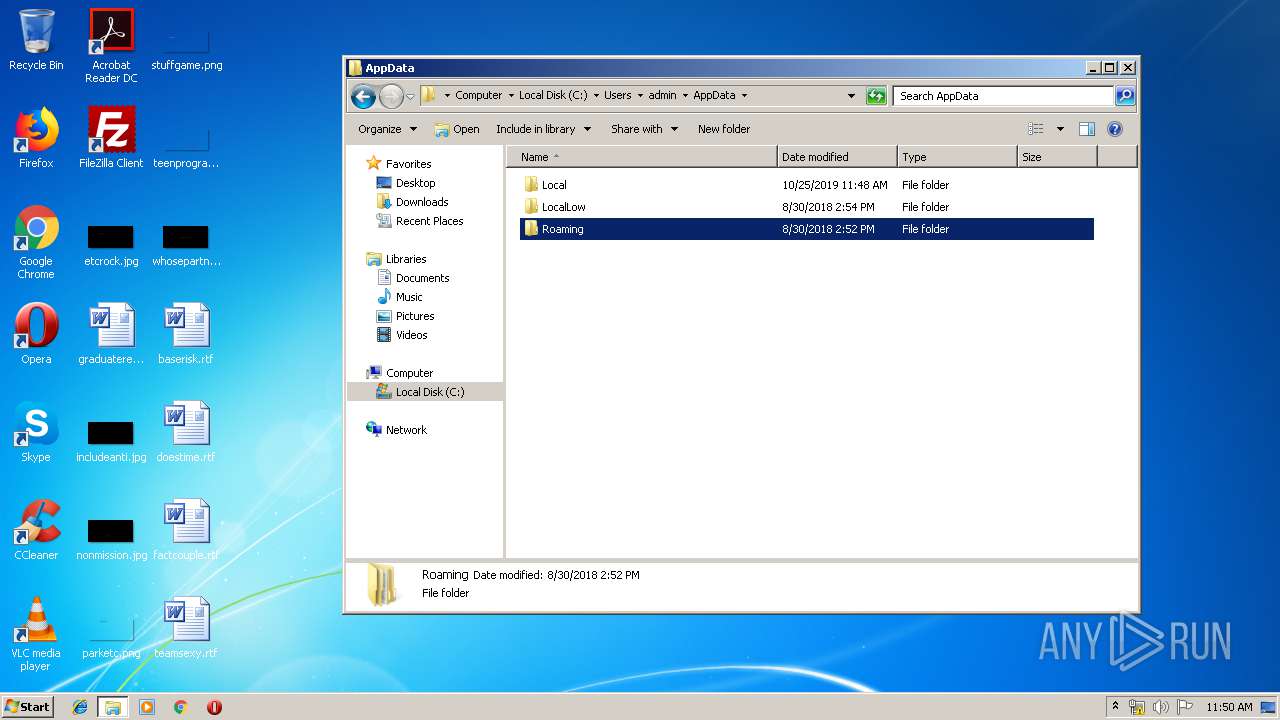
Creates files in the user directory
- powershell.exe (PID: 3764)
Executed via WMI
- powershell.exe (PID: 3764)
PowerShell script executed
- powershell.exe (PID: 3764)
Executable content was dropped or overwritten
- powershell.exe (PID: 3764)
- 196.exe (PID: 2600)
- msdt.exe (PID: 392)
Starts itself from another location
- 196.exe (PID: 2600)
Connects to server without host name
- typebsketch.exe (PID: 3548)
- typebsketch.exe (PID: 2204)
Application launched itself
- typebsketch.exe (PID: 2500)
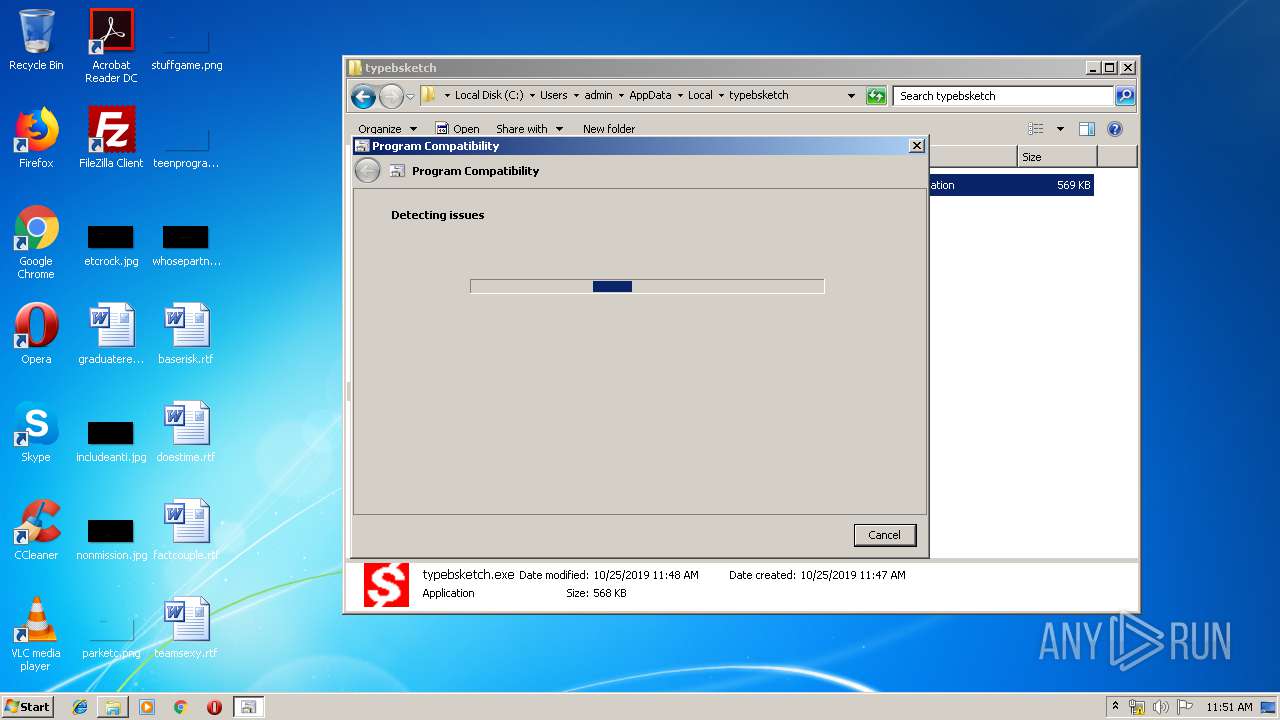
Executed via COM
- sdiagnhost.exe (PID: 3836)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1704)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1704)
Reads settings of System Certificates
- powershell.exe (PID: 3764)
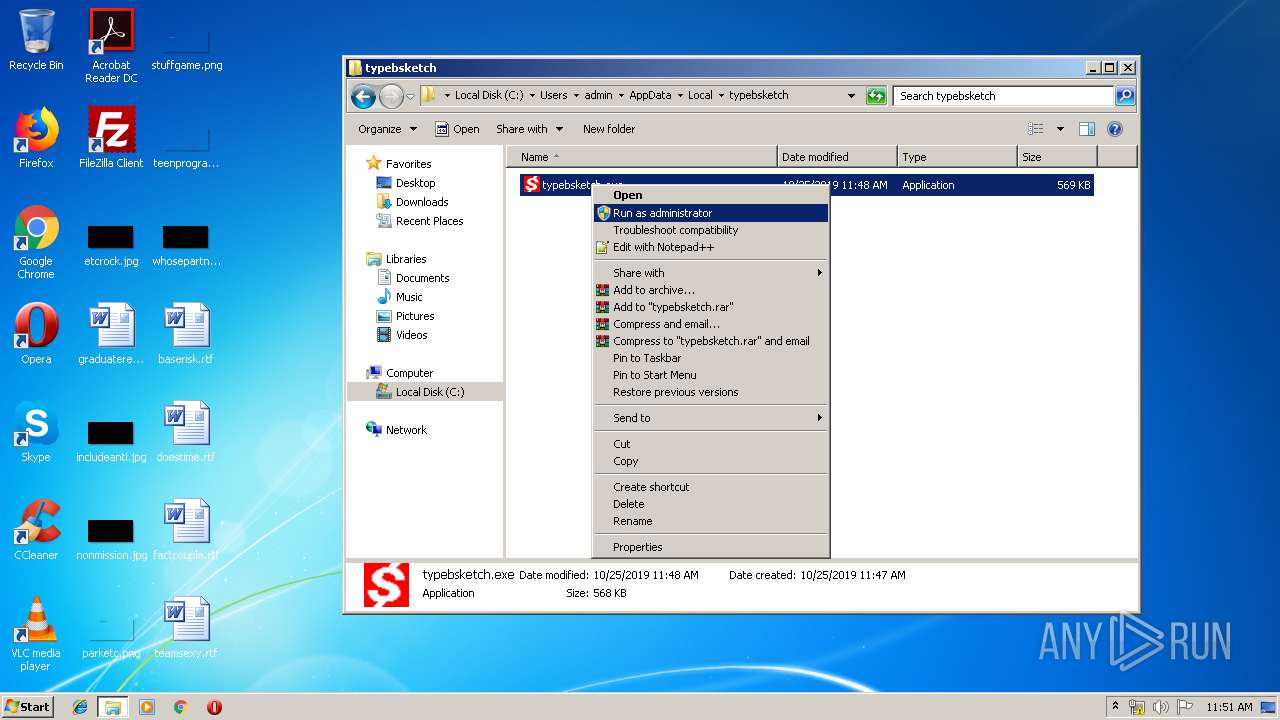
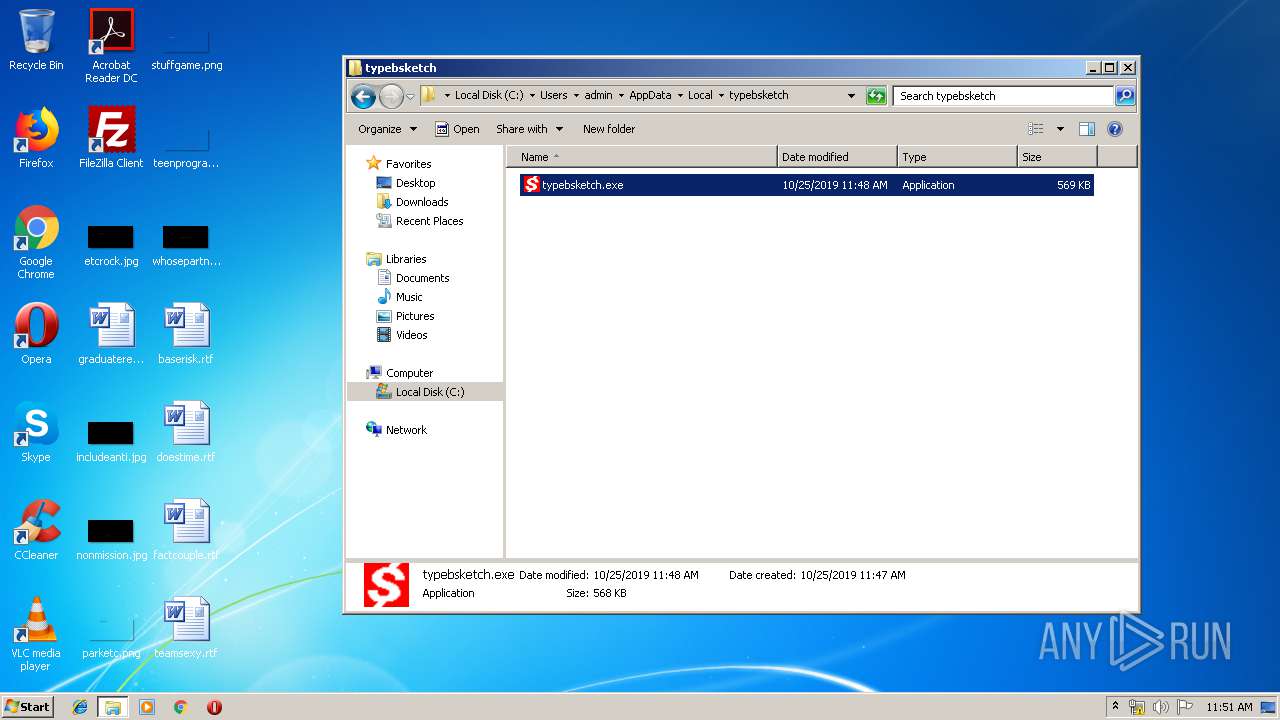
Manual execution by user
- typebsketch.exe (PID: 2500)
- explorer.exe (PID: 3452)
- pcwrun.exe (PID: 2456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Daria Wnuk |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:25 09:40:00 |
| ModifyDate: | 2019:10:25 09:40:00 |
| Pages: | 1 |
| Words: | 87 |
| Characters: | 499 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Kasperek - Cichon |
| Lines: | 4 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 585 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
57
Monitored processes
18
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | C:\Windows\System32\msdt.exe -path C:\Windows\diagnostics\index\PCWDiagnostic.xml -af C:\Users\admin\AppData\Local\Temp\PCW1E3D.xml /skip TRUE | C:\Windows\System32\msdt.exe | pcwrun.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Dati 522337.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2192 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES24C6.tmp" "c:\Users\admin\AppData\Local\Temp\CSC24C5.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2204 | --b583abe8 | C:\Users\admin\AppData\Local\typebsketch\typebsketch.exe | typebsketch.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2436 | "C:\Users\admin\AppData\Local\typebsketch\typebsketch.exe" | C:\Users\admin\AppData\Local\typebsketch\typebsketch.exe | — | 196.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2456 | C:\Windows\system32\pcwrun.exe "C:\Users\admin\AppData\Local\typebsketch\typebsketch.exe" | C:\Windows\system32\pcwrun.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Troubleshooter Invoker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2500 | "C:\Users\admin\AppData\Local\typebsketch\typebsketch.exe" | C:\Users\admin\AppData\Local\typebsketch\typebsketch.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2600 | --deae836c | C:\Users\admin\196.exe | 196.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2736 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES22A3.tmp" "c:\Users\admin\AppData\Local\Temp\CSC22A2.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3164 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES239D.tmp" "c:\Users\admin\AppData\Local\Temp\CSC239C.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
2 530
Read events
1 656
Write events
739
Delete events
135
Modification events
| (PID) Process: | (1704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | >8c |
Value: 3E386300A8060000010000000000000000000000 | |||
| (PID) Process: | (1704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1704) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1331232830 | |||
Executable files
4
Suspicious files
3
Text files
17
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA89E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\586762E9.wmf | — | |
MD5:— | SHA256:— | |||
| 1704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5769DBD6.wmf | — | |
MD5:— | SHA256:— | |||
| 1704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\15DD6DDF.wmf | — | |
MD5:— | SHA256:— | |||
| 1704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\10CC6E54.wmf | — | |
MD5:— | SHA256:— | |||
| 1704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\148B1245.wmf | — | |
MD5:— | SHA256:— | |||
| 1704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3D146B82.wmf | — | |
MD5:— | SHA256:— | |||
| 1704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BC91419B.wmf | — | |
MD5:— | SHA256:— | |||
| 1704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DBA716E0.wmf | — | |
MD5:— | SHA256:— | |||
| 1704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F6796961.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
8
DNS requests
3
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3548 | typebsketch.exe | POST | — | 201.213.32.59:80 | http://201.213.32.59/entries/forced/add/merge/ | AR | — | — | malicious |
3764 | powershell.exe | GET | 301 | 34.209.166.206:80 | http://wp.zumbly.com/wp-content/plugins/cmb2/xrj846/ | US | html | 194 b | unknown |
3548 | typebsketch.exe | POST | 200 | 46.29.183.211:8080 | http://46.29.183.211:8080/codec/ | LU | binary | 132 b | malicious |
2204 | typebsketch.exe | POST | — | 201.213.32.59:80 | http://201.213.32.59/glitch/stubs/ | AR | — | — | malicious |
2204 | typebsketch.exe | POST | 200 | 46.29.183.211:8080 | http://46.29.183.211:8080/chunk/splash/add/ | LU | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3764 | powershell.exe | 34.209.166.206:80 | wp.zumbly.com | Amazon.com, Inc. | US | unknown |
3764 | powershell.exe | 34.209.166.206:443 | wp.zumbly.com | Amazon.com, Inc. | US | unknown |
3548 | typebsketch.exe | 201.213.32.59:80 | — | Prima S.A. | AR | malicious |
3548 | typebsketch.exe | 187.155.95.26:50000 | — | Uninet S.A. de C.V. | MX | malicious |
2204 | typebsketch.exe | 46.29.183.211:8080 | — | voipGATE S.A. | LU | malicious |
2204 | typebsketch.exe | 201.213.32.59:80 | — | Prima S.A. | AR | malicious |
3548 | typebsketch.exe | 46.29.183.211:8080 | — | voipGATE S.A. | LU | malicious |
2204 | typebsketch.exe | 187.155.95.26:50000 | — | Uninet S.A. de C.V. | MX | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wp.zumbly.com |
| unknown |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3548 | typebsketch.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
3548 | typebsketch.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3548 | typebsketch.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 19 |
3548 | typebsketch.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2204 | typebsketch.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2204 | typebsketch.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
6 ETPRO signatures available at the full report
Process | Message |
|---|---|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cppĒ |
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|