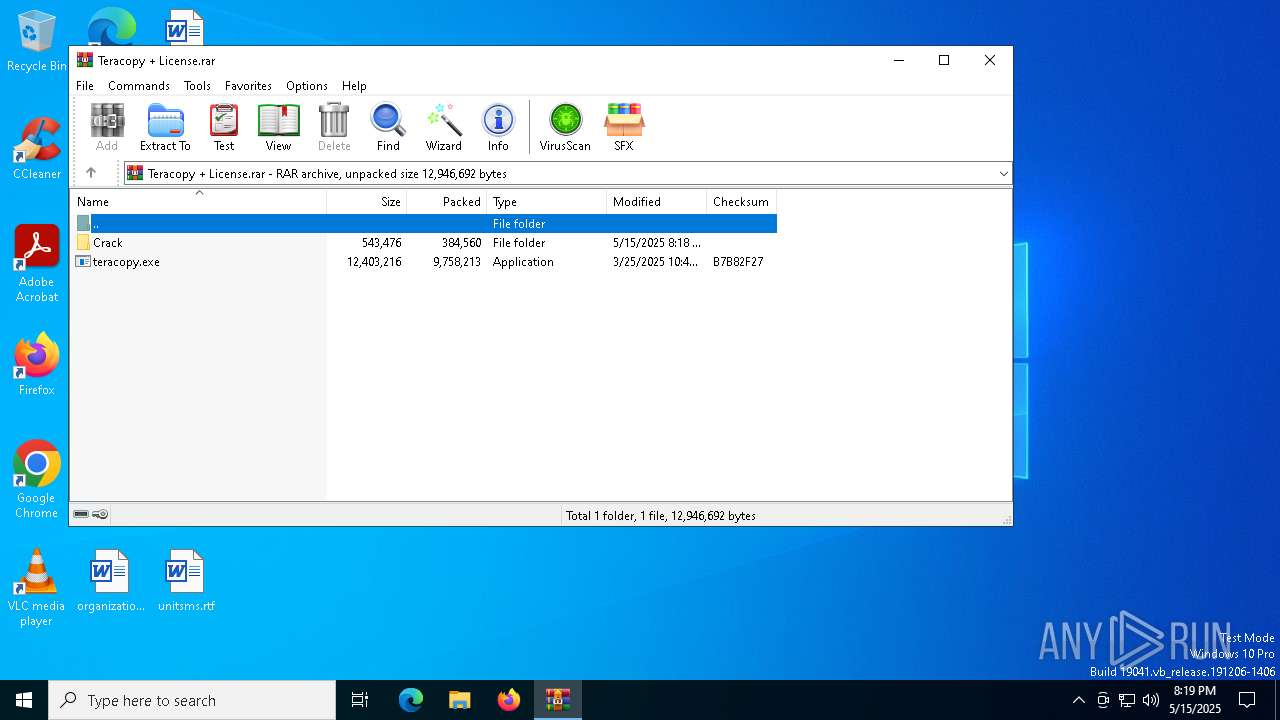
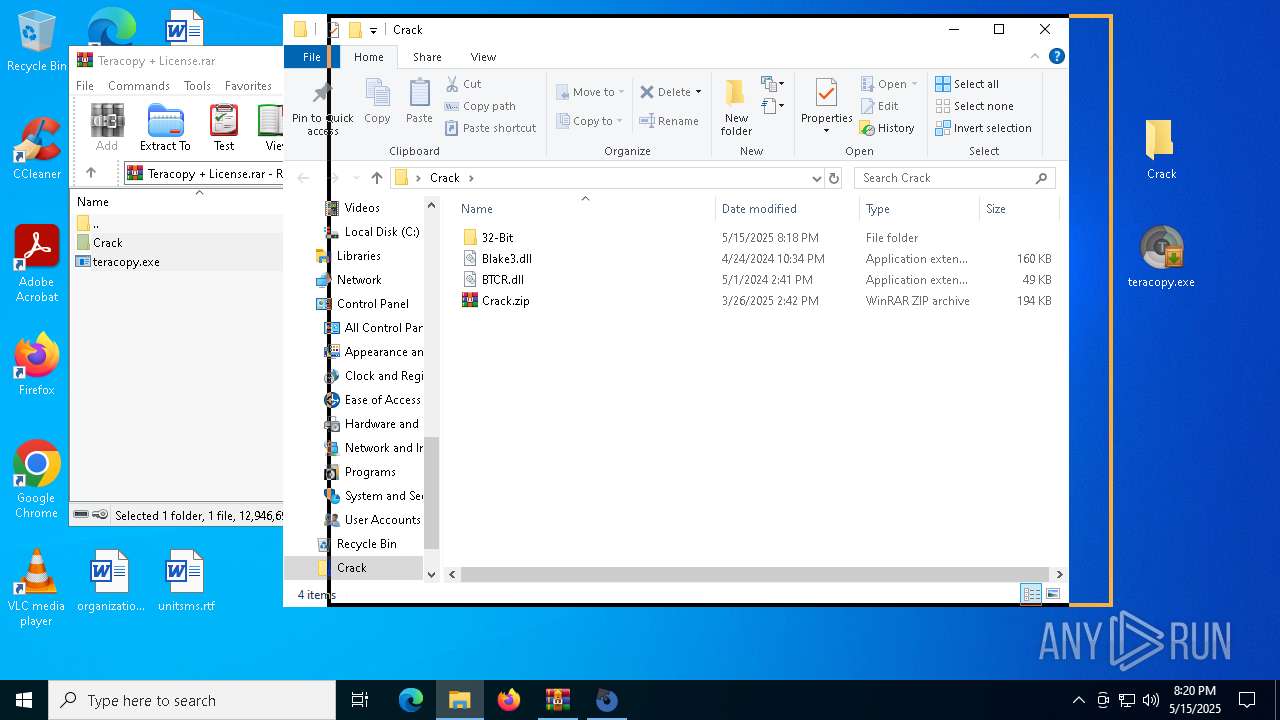
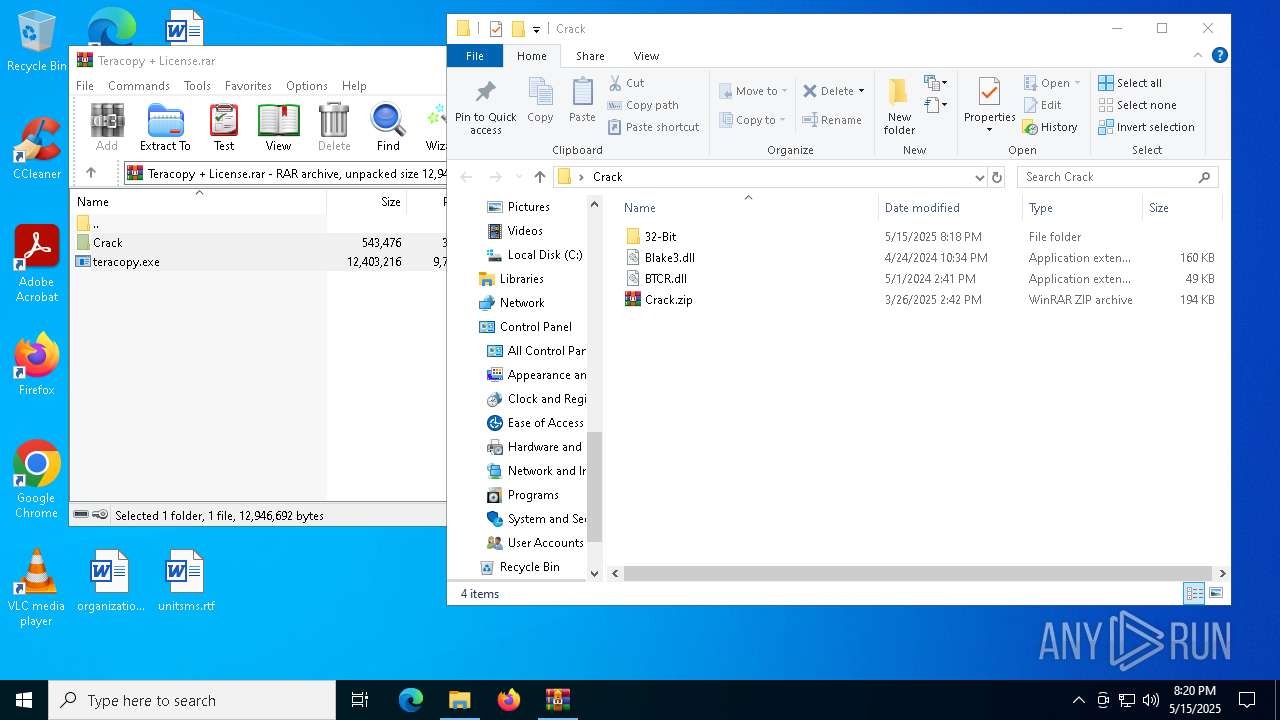
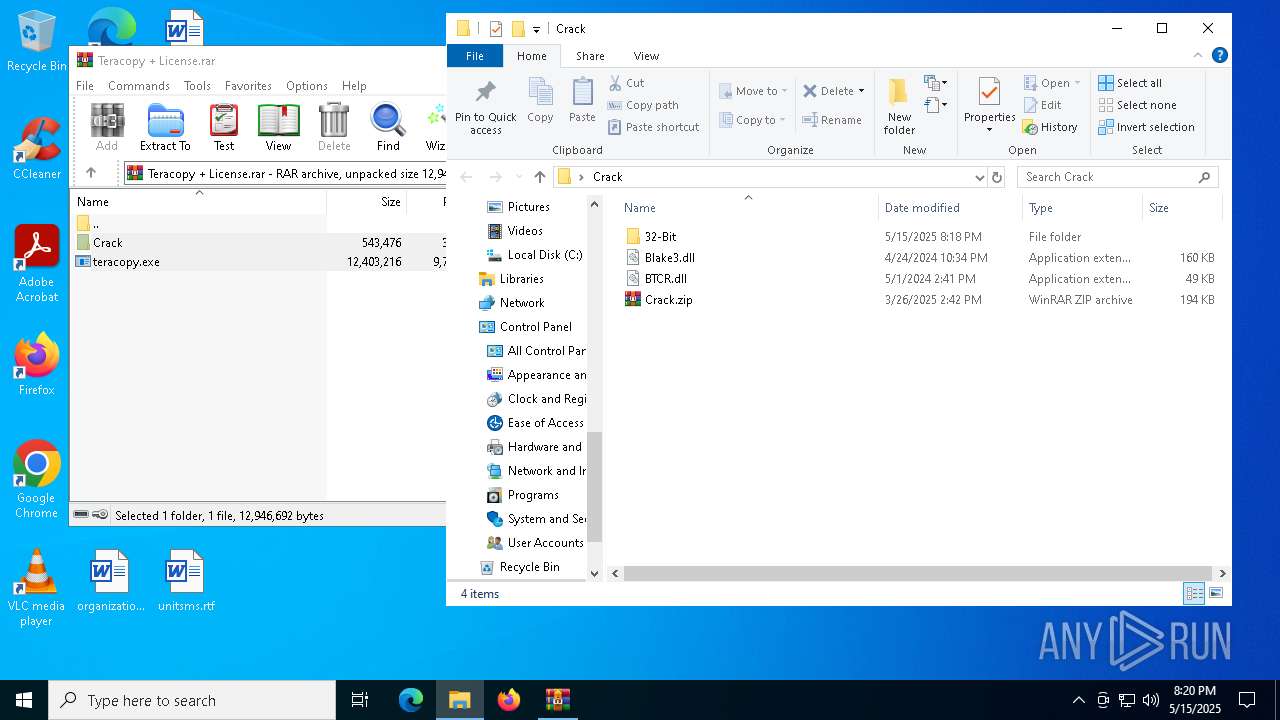
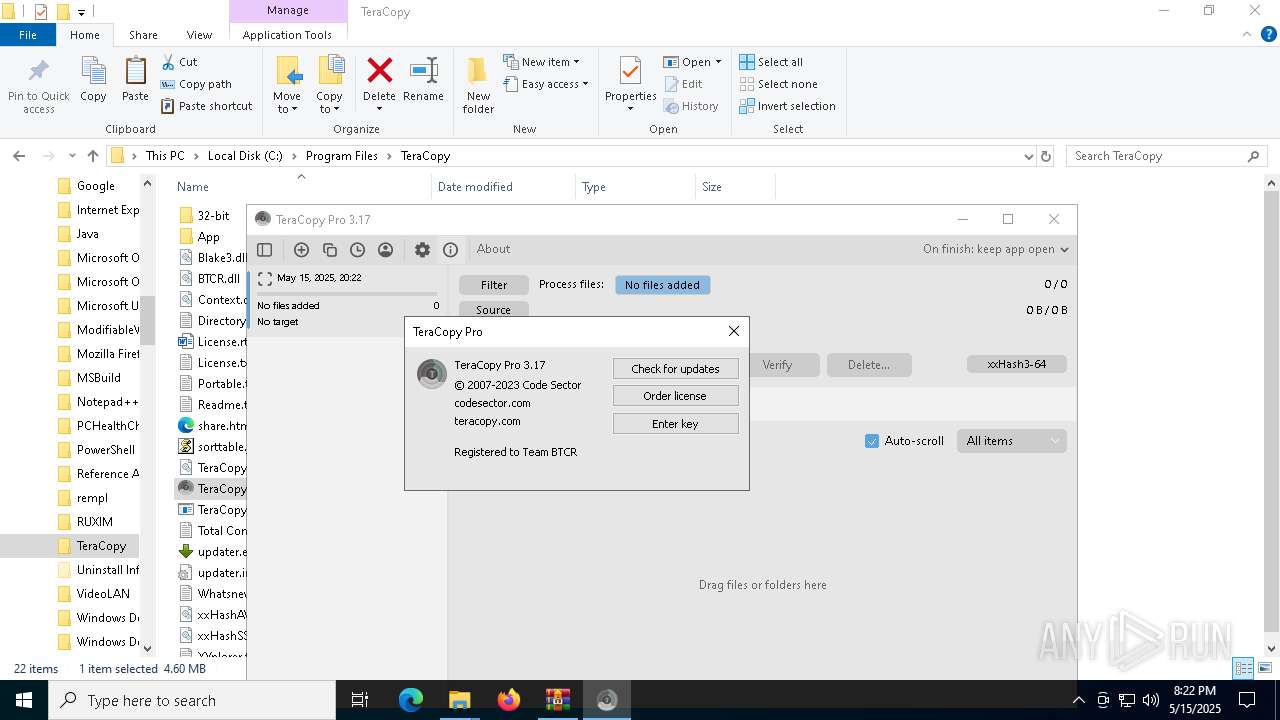
| File name: | Teracopy + License.rar |
| Full analysis: | https://app.any.run/tasks/37118cbe-95ad-44f3-833f-b51be3b2cb83 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 20:19:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 43E82998462E4CB2F4C4EC3AC9165EBF |
| SHA1: | 281F20A9E06F00F8ACA7368FACB5087E76E4214C |
| SHA256: | 8BD508170B6584F0184CF773D316422731A0DBBD685667B113DBAF66EE1E5C49 |
| SSDEEP: | 98304:XUt4hzqezdGMDBUeqYZJZTO934GfW7Ry1U9Scsl3iUiVjSccQt7guWXcL98IkbPI:b4bR82Pl33uNMi+h0tX+bc |
MALICIOUS
No malicious indicators.SUSPICIOUS
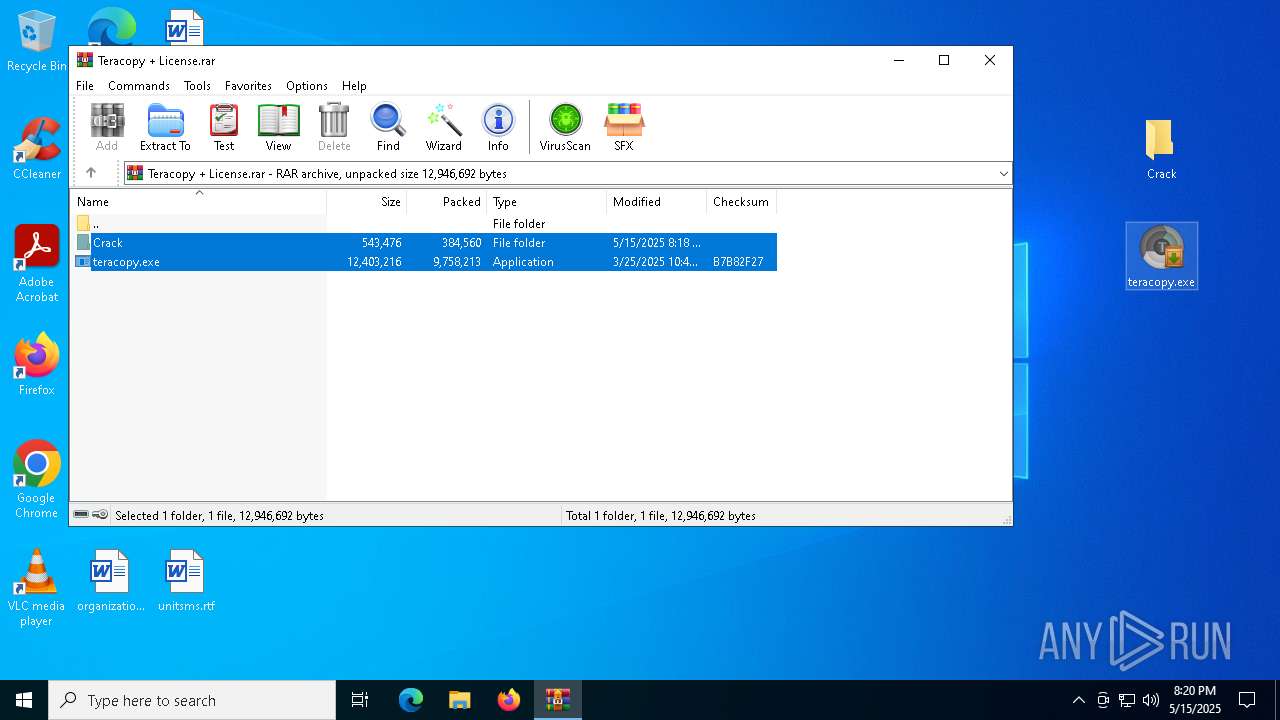
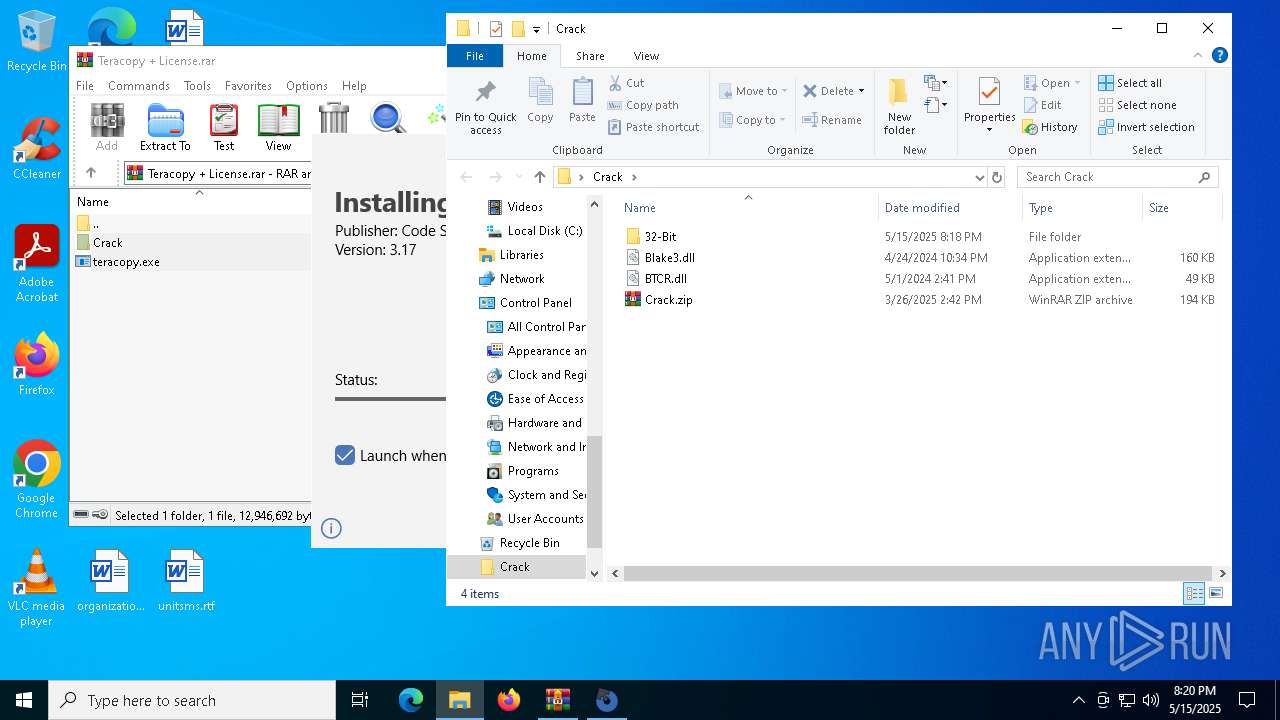
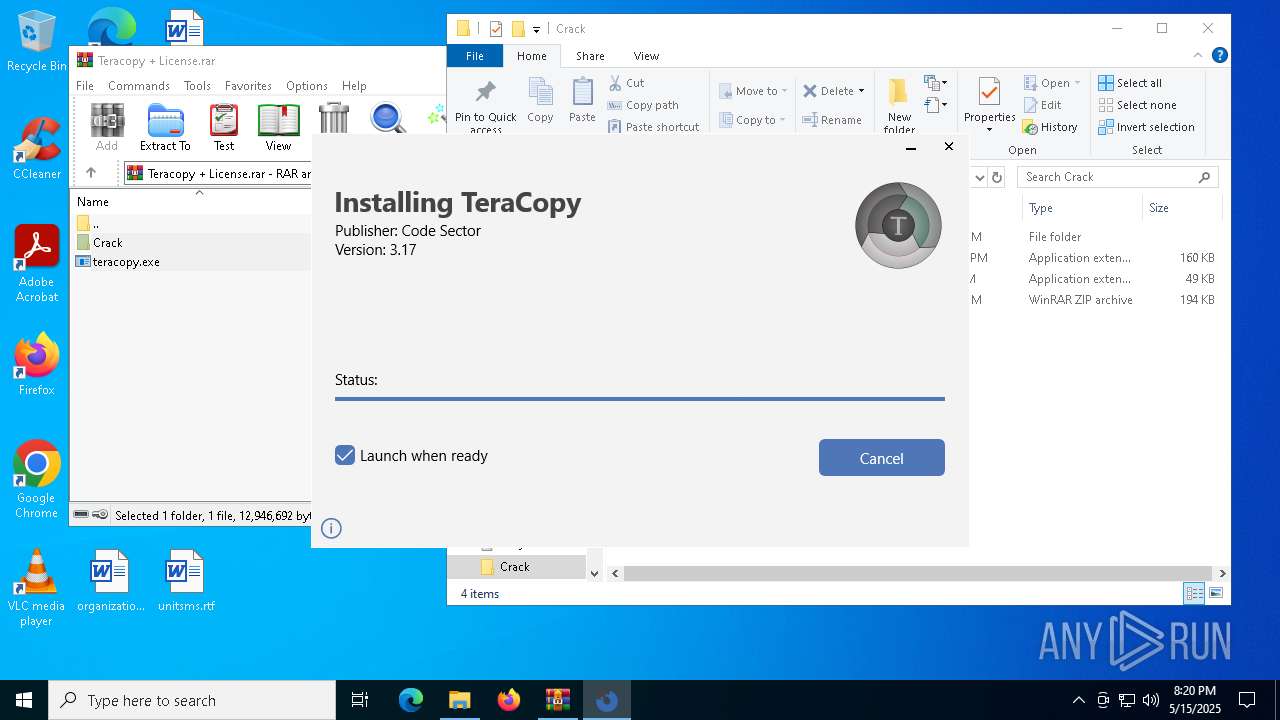
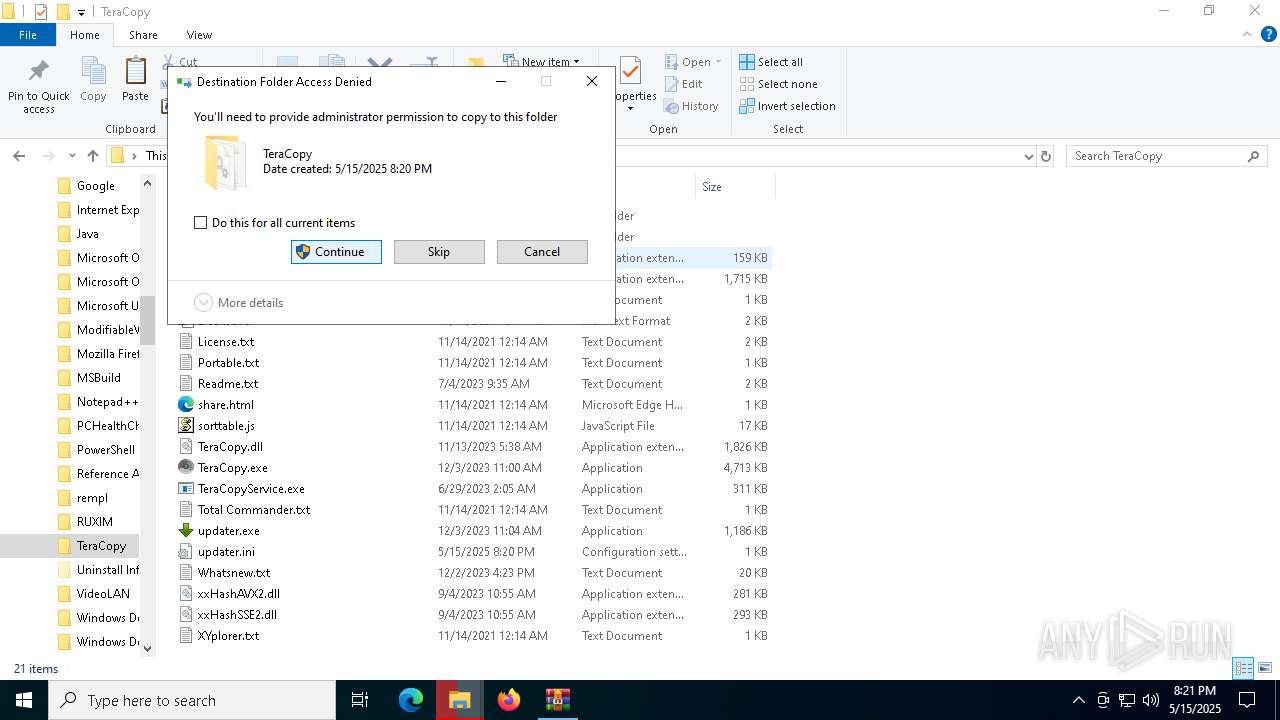
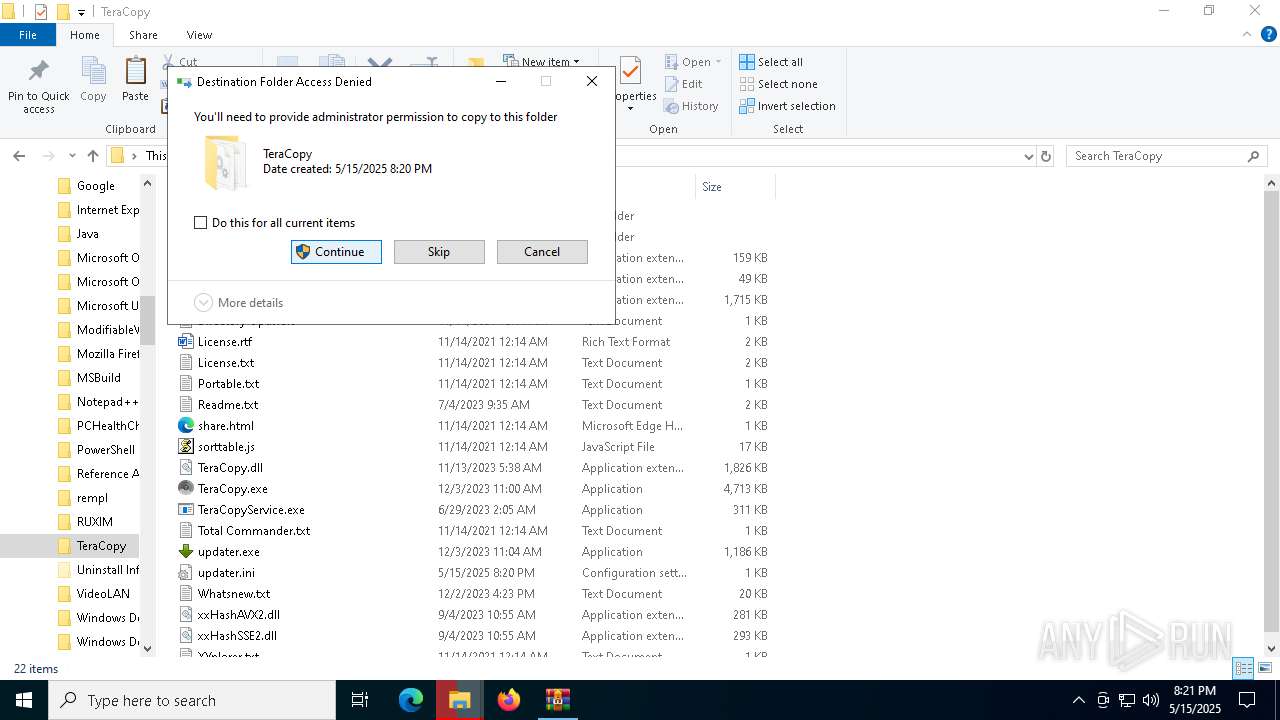
Process drops legitimate windows executable
- teracopy.exe (PID: 5972)
- teracopy.exe (PID: 5304)
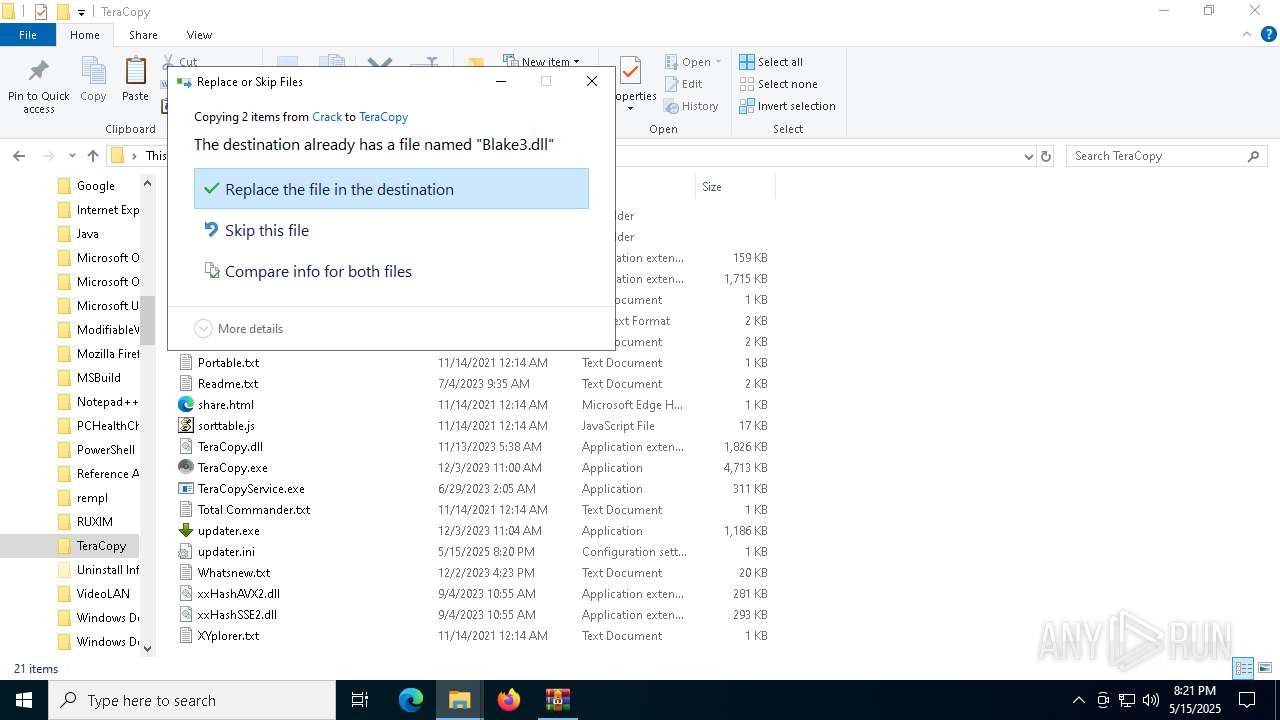
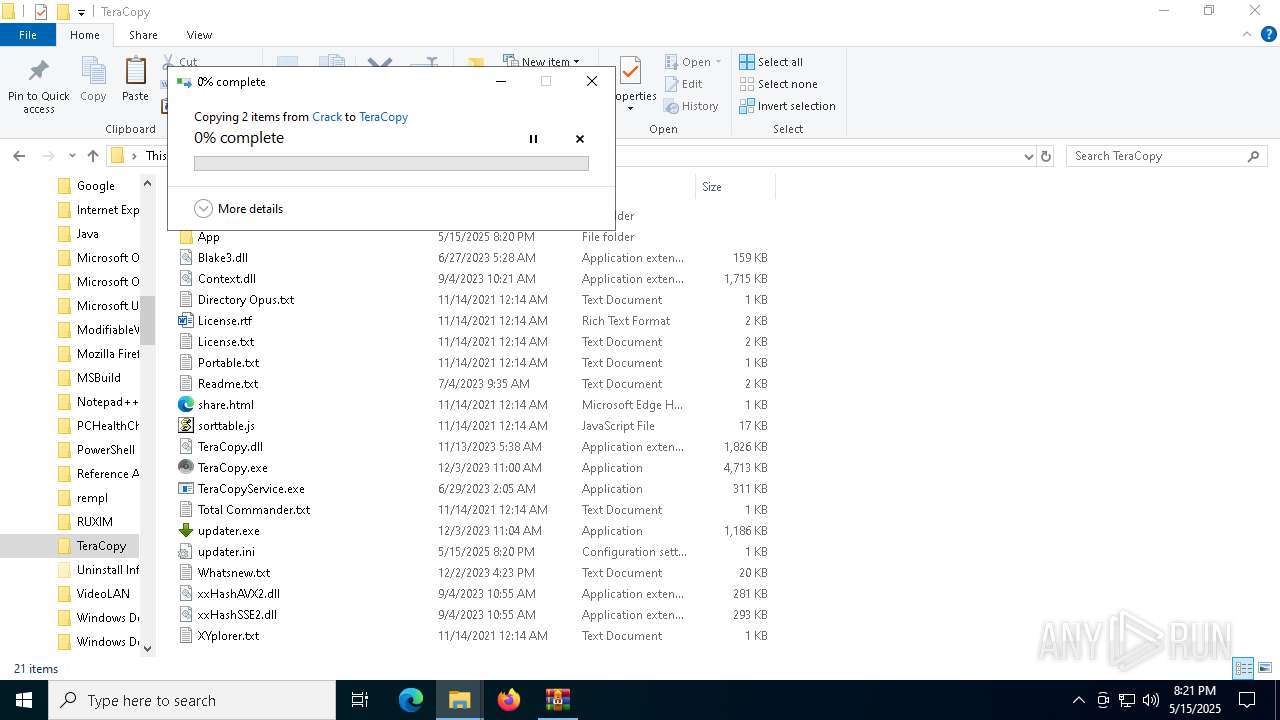
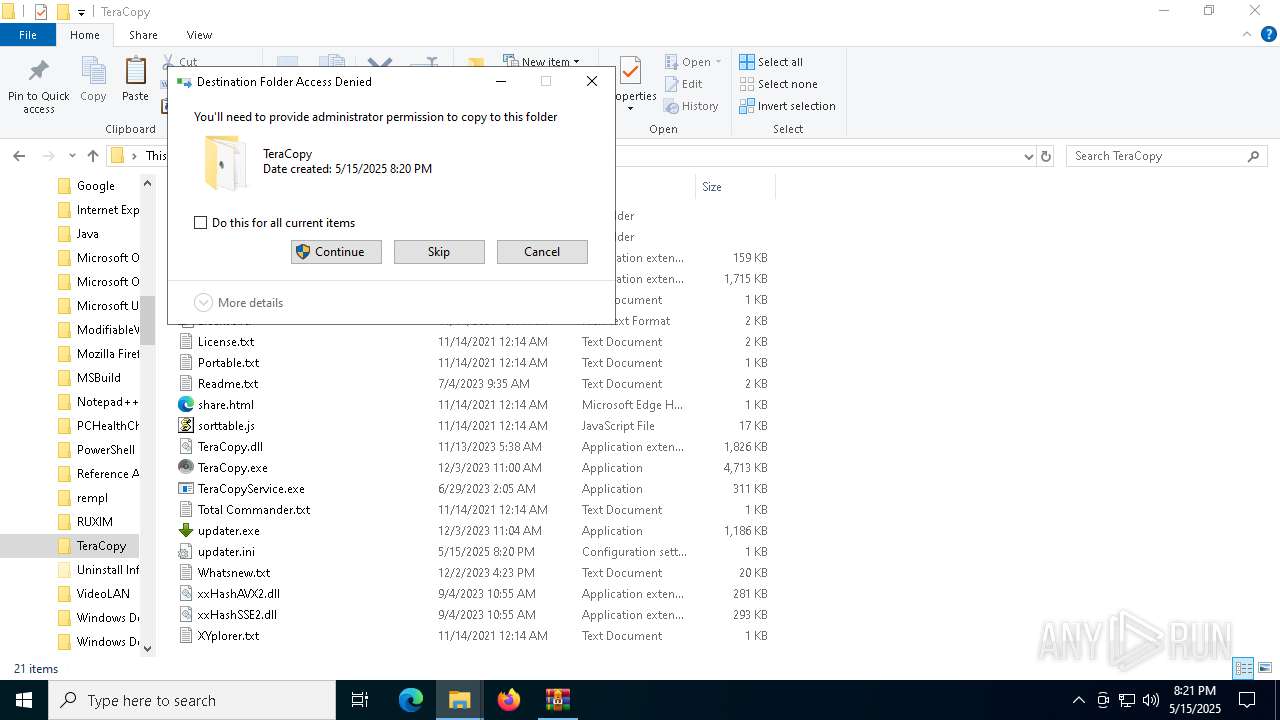
Executable content was dropped or overwritten
- teracopy.exe (PID: 5972)
- dllhost.exe (PID: 4120)
- teracopy.exe (PID: 5304)
Reads the Windows owner or organization settings
- teracopy.exe (PID: 5972)
- teracopy.exe (PID: 5304)
ADVANCEDINSTALLER mutex has been found
- teracopy.exe (PID: 5972)
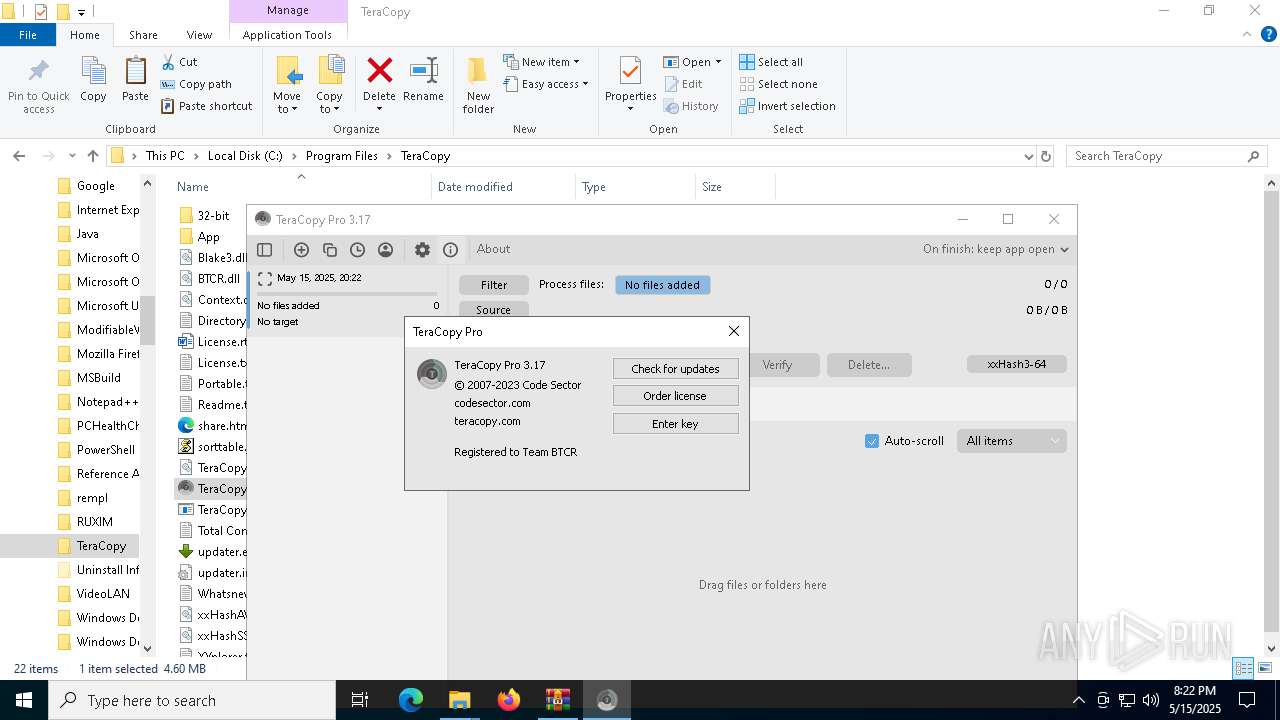
Adds/modifies Windows certificates
- teracopy.exe (PID: 5304)
Reads security settings of Internet Explorer
- teracopy.exe (PID: 5304)
- teracopy.exe (PID: 5972)
Application launched itself
- teracopy.exe (PID: 5972)
- msiexec.exe (PID: 5204)
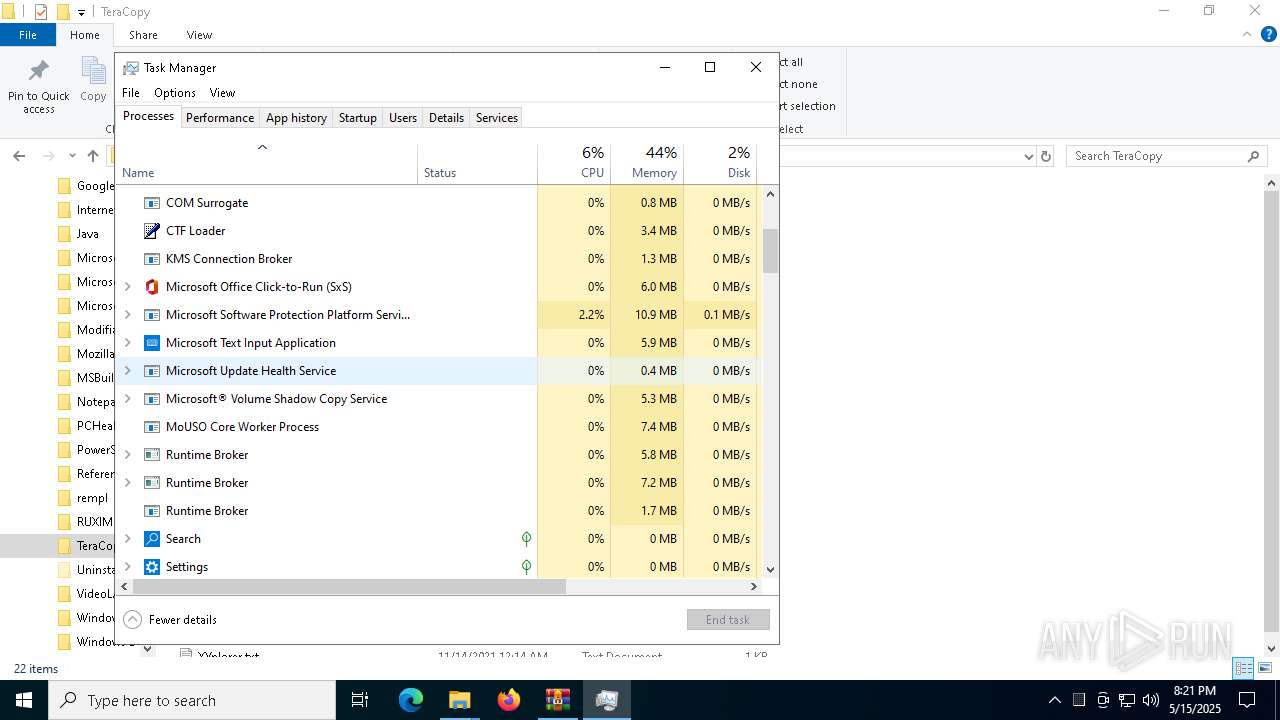
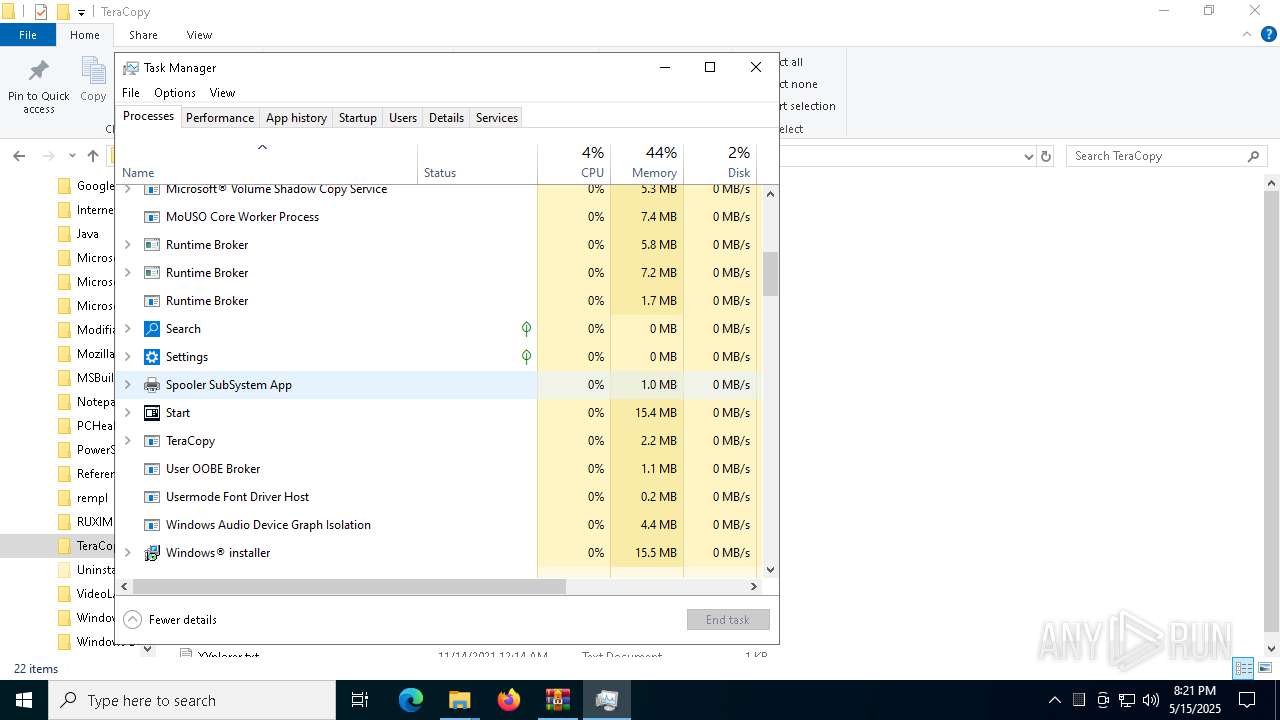
Executes as Windows Service
- VSSVC.exe (PID: 6036)
- TeraCopyService.exe (PID: 4284)
There is functionality for taking screenshot (YARA)
- teracopy.exe (PID: 5972)
Detects AdvancedInstaller (YARA)
- teracopy.exe (PID: 5972)
- msiexec.exe (PID: 5204)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 4652)
- teracopy.exe (PID: 5972)
- msiexec.exe (PID: 5204)
- teracopy.exe (PID: 5304)
Executable content was dropped or overwritten
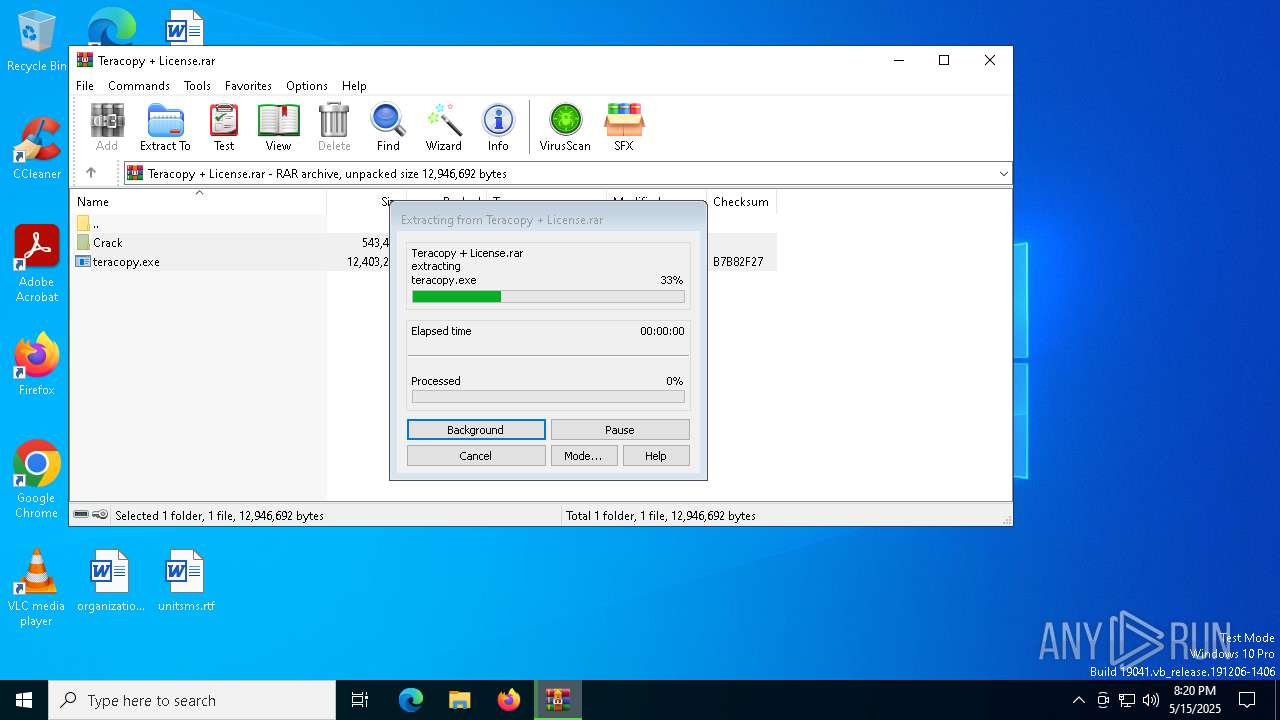
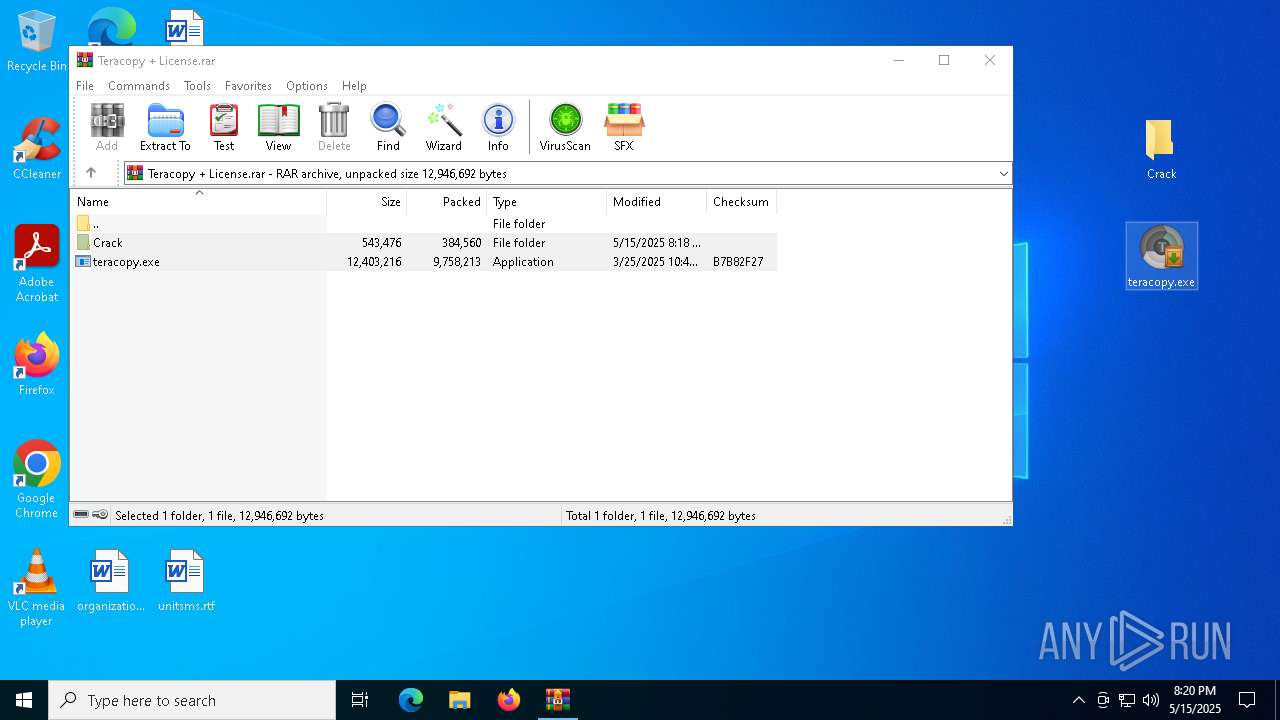
- WinRAR.exe (PID: 4652)
- msiexec.exe (PID: 5204)
Checks supported languages
- msiexec.exe (PID: 5204)
- msiexec.exe (PID: 6068)
- teracopy.exe (PID: 5304)
- teracopy.exe (PID: 5972)
Reads Environment values
- teracopy.exe (PID: 5972)
- msiexec.exe (PID: 6068)
- teracopy.exe (PID: 5304)
Create files in a temporary directory
- teracopy.exe (PID: 5972)
- teracopy.exe (PID: 5304)
Reads the computer name
- msiexec.exe (PID: 5204)
- msiexec.exe (PID: 6068)
- teracopy.exe (PID: 5972)
- teracopy.exe (PID: 5304)
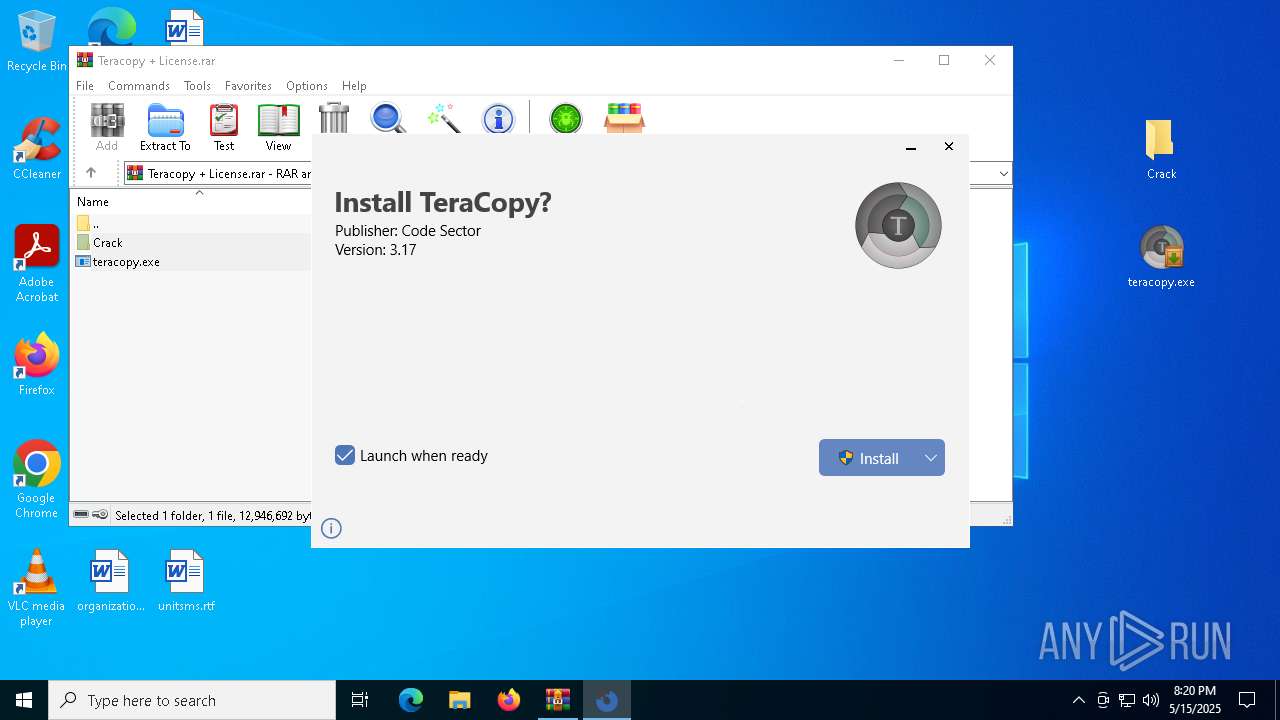
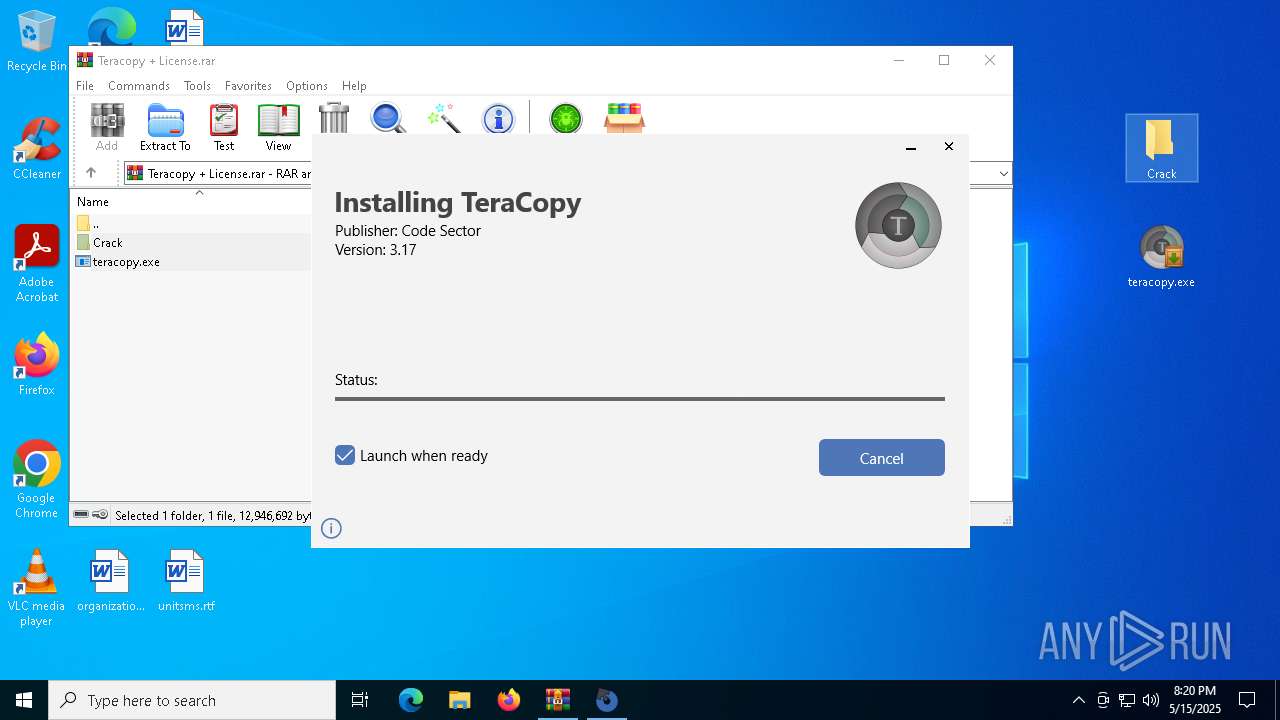
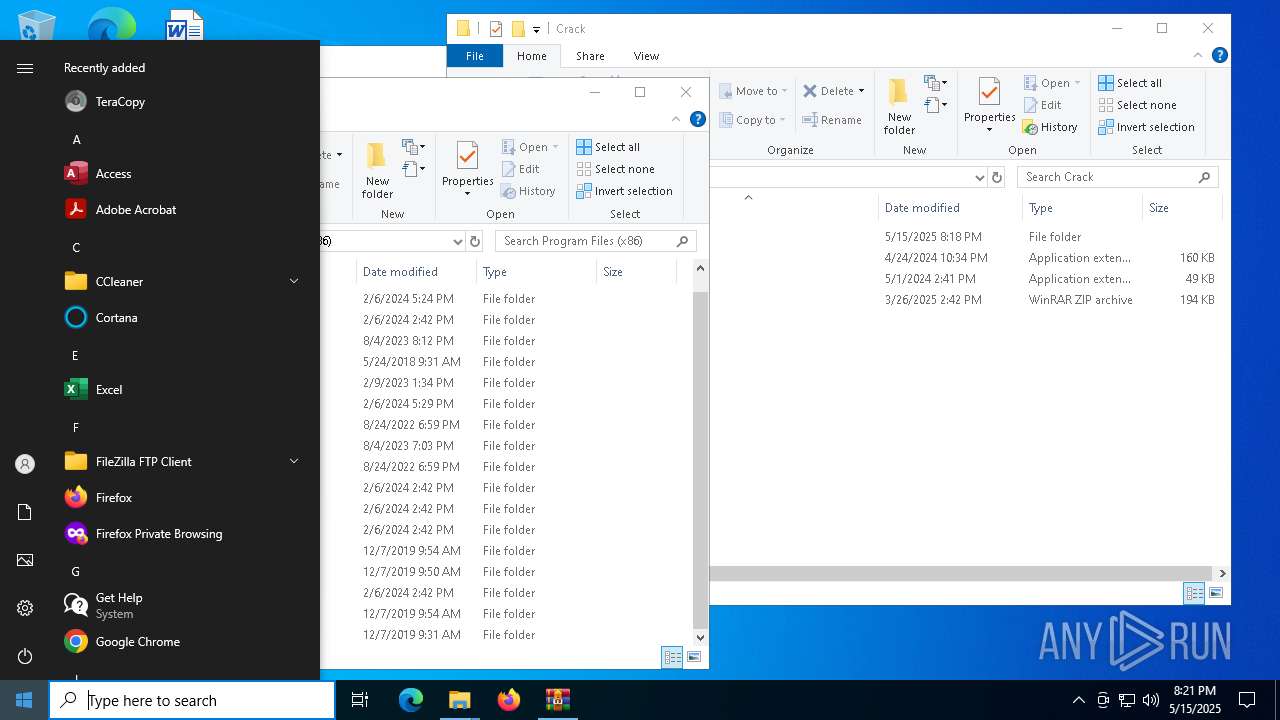
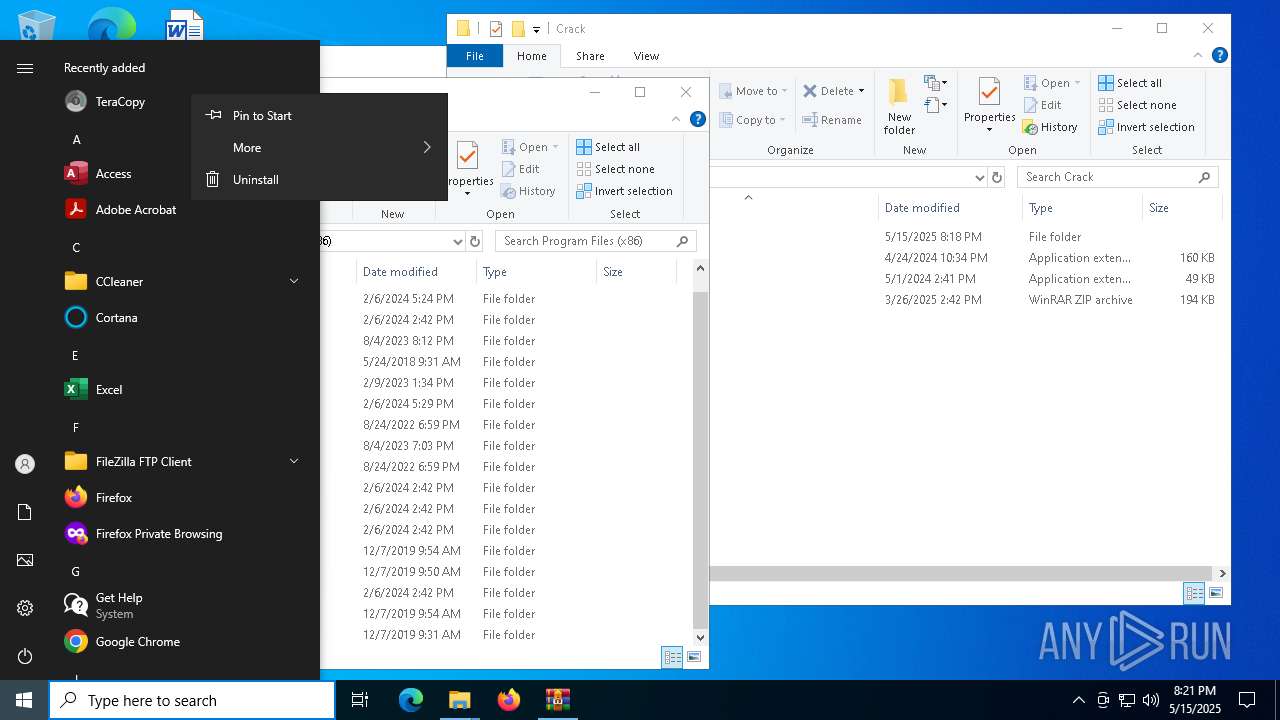
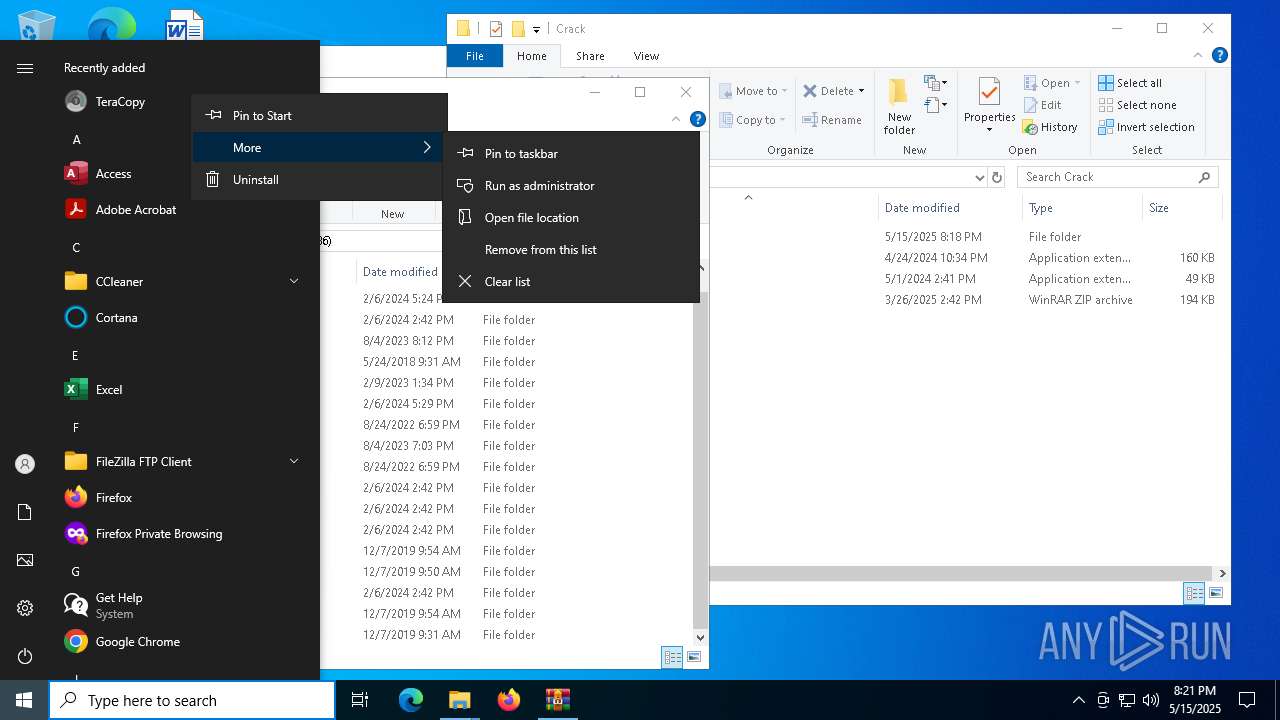
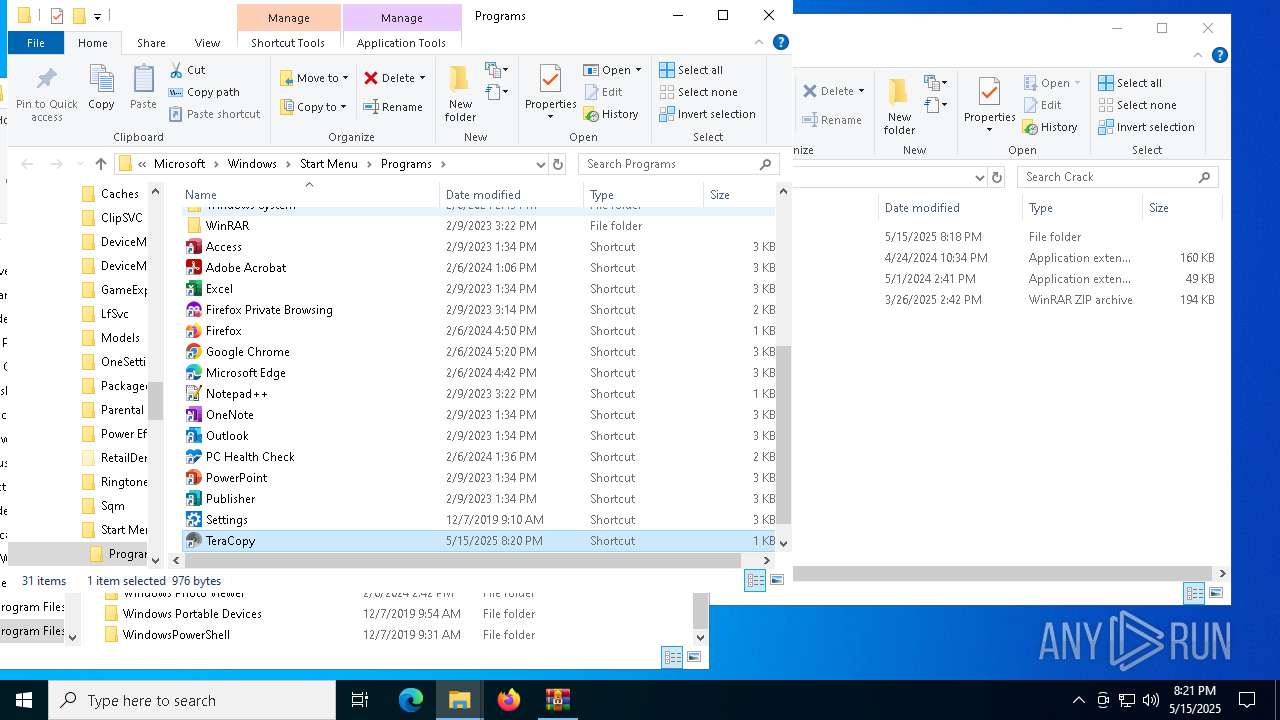
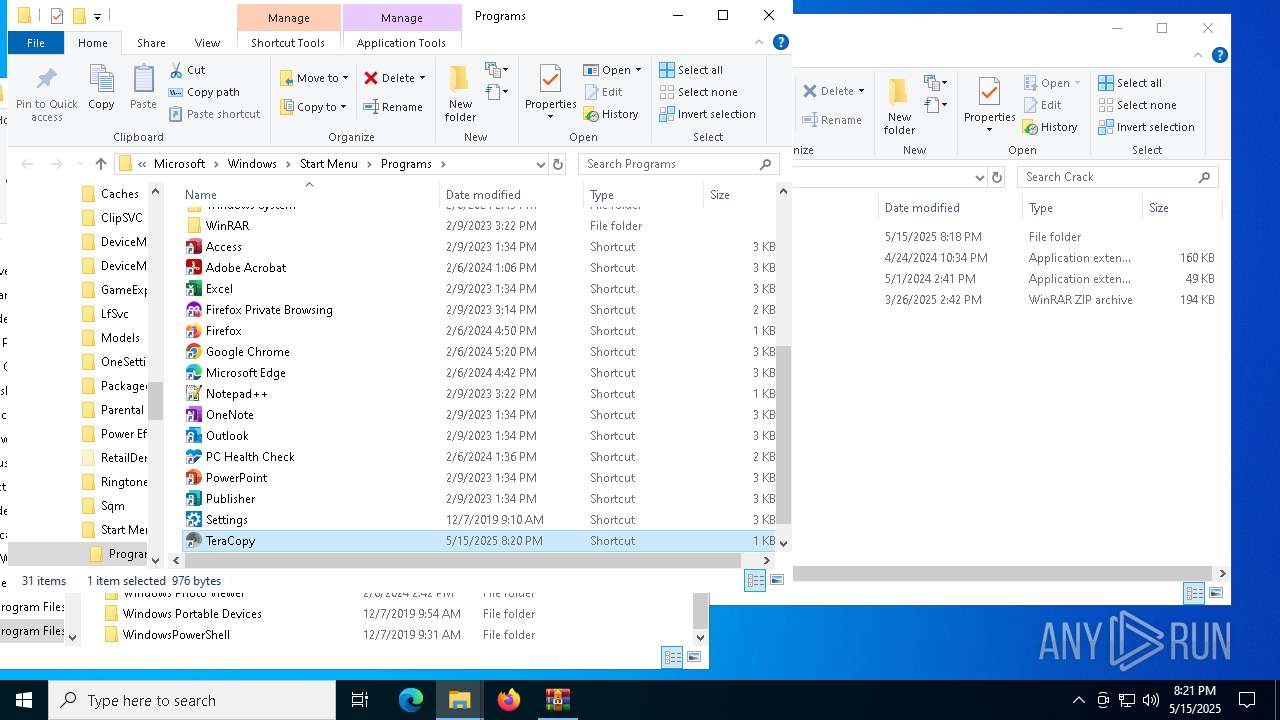
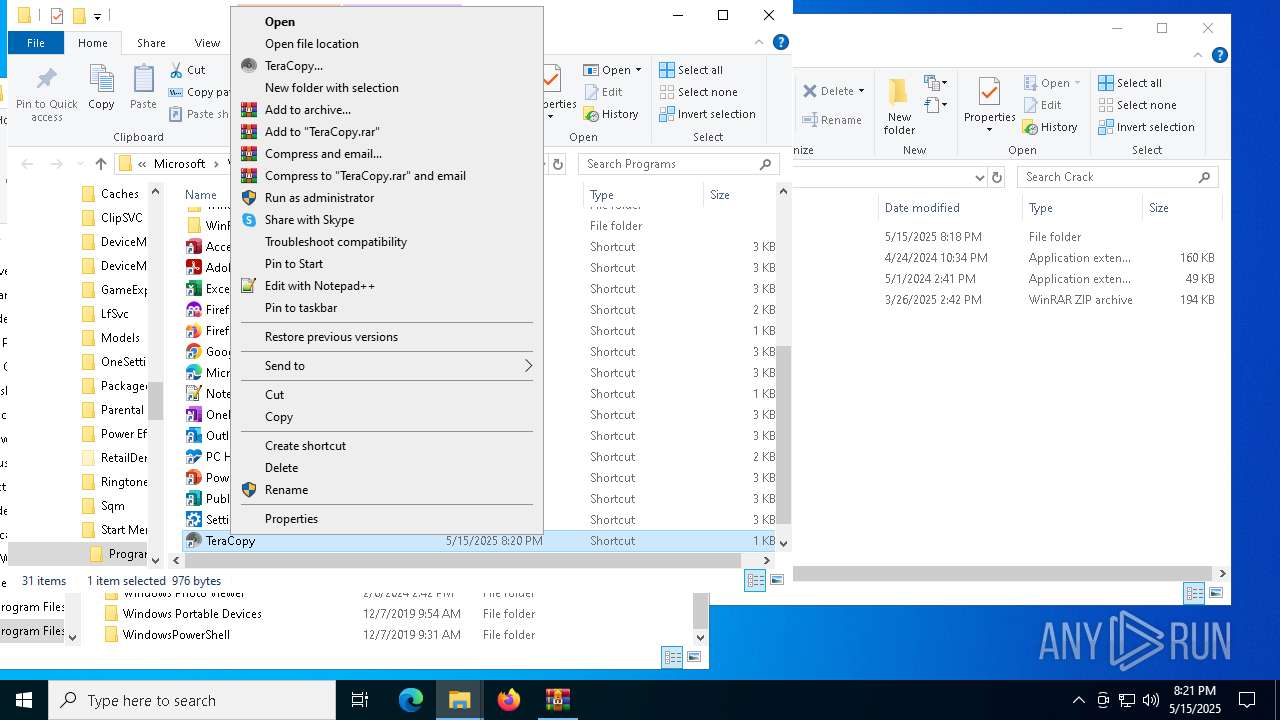
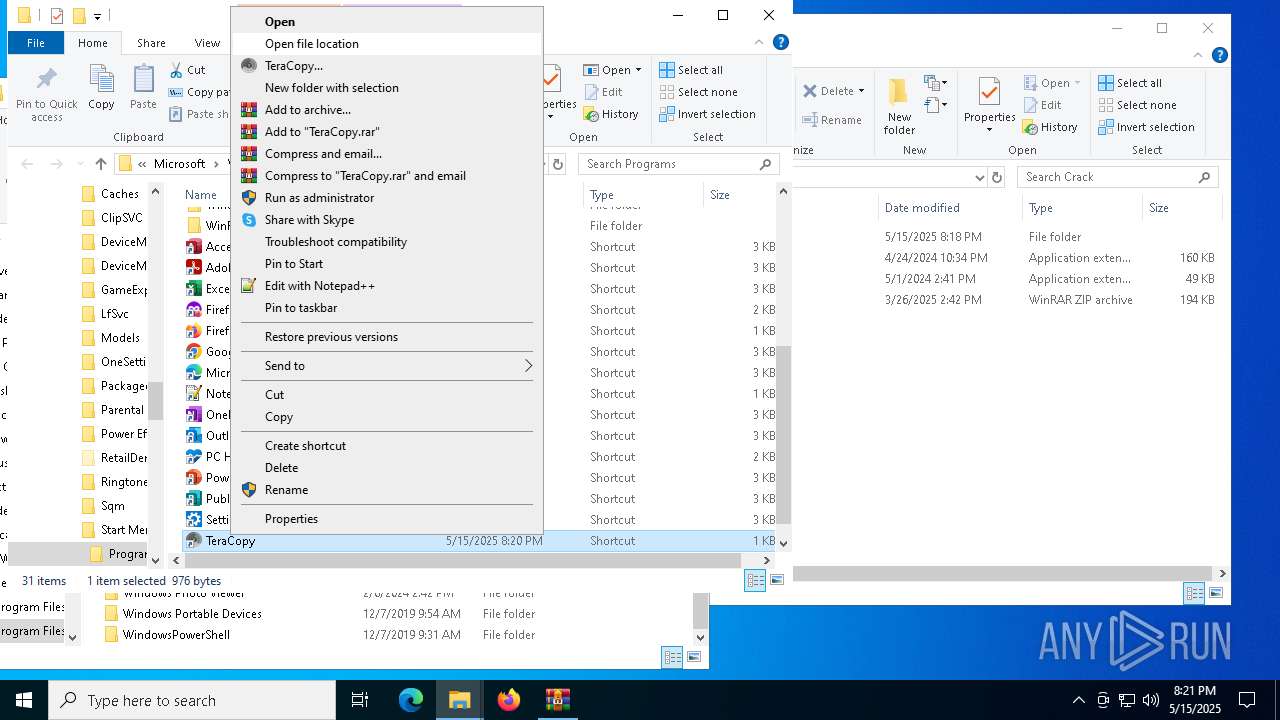
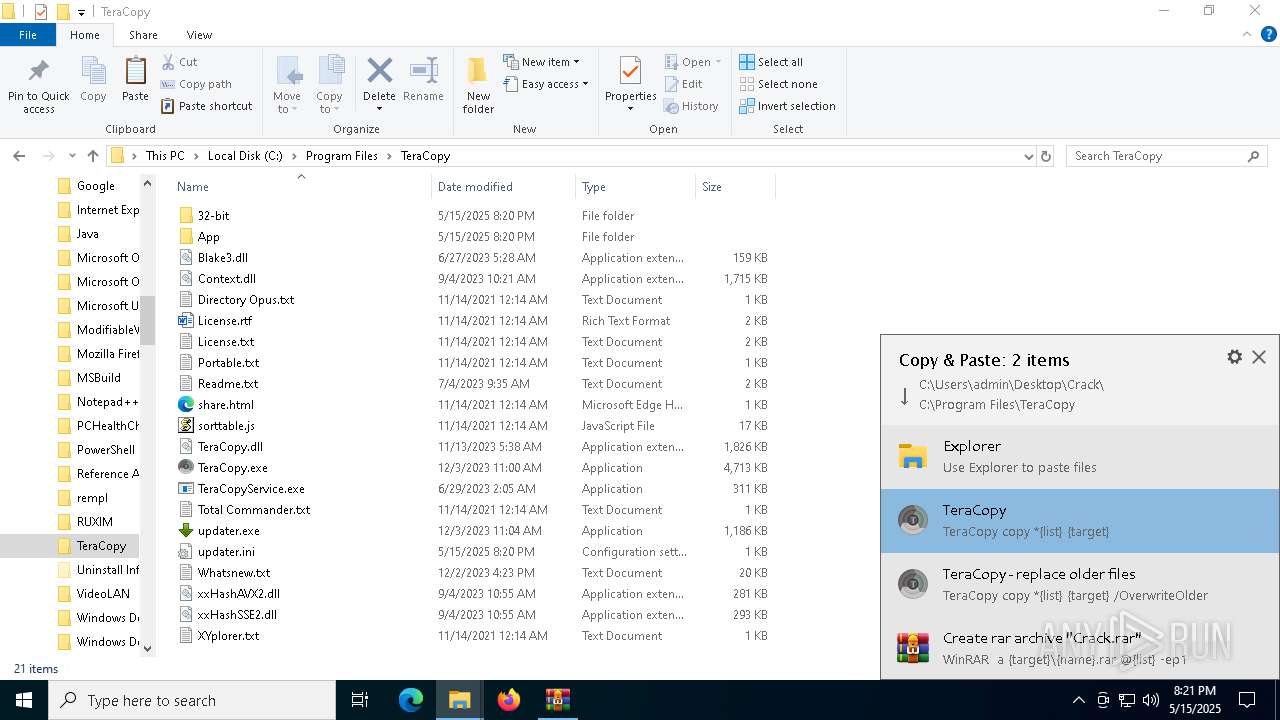
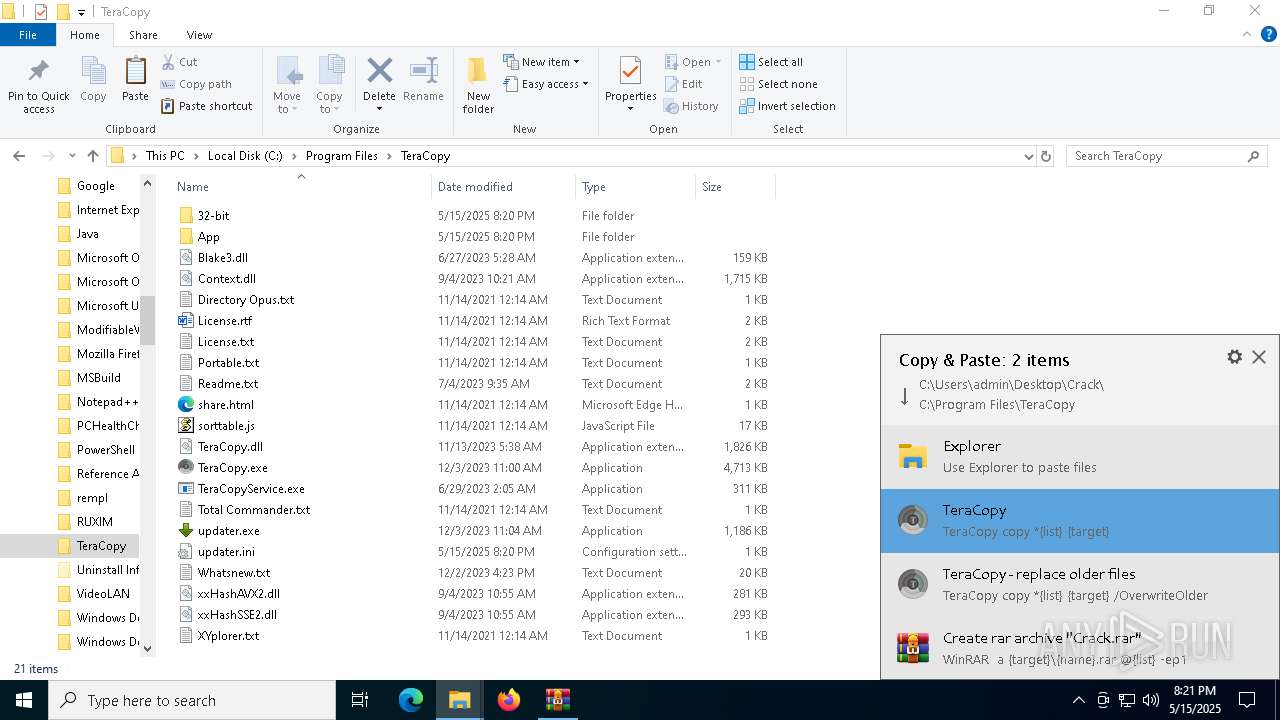
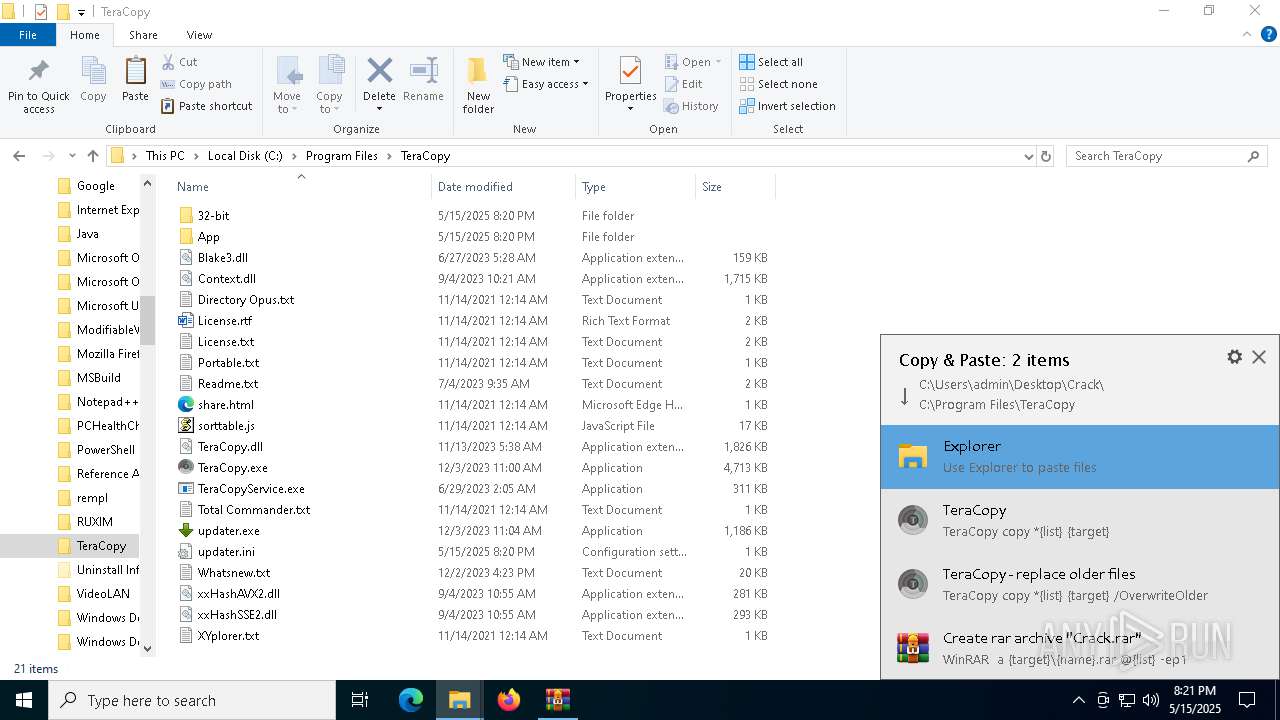
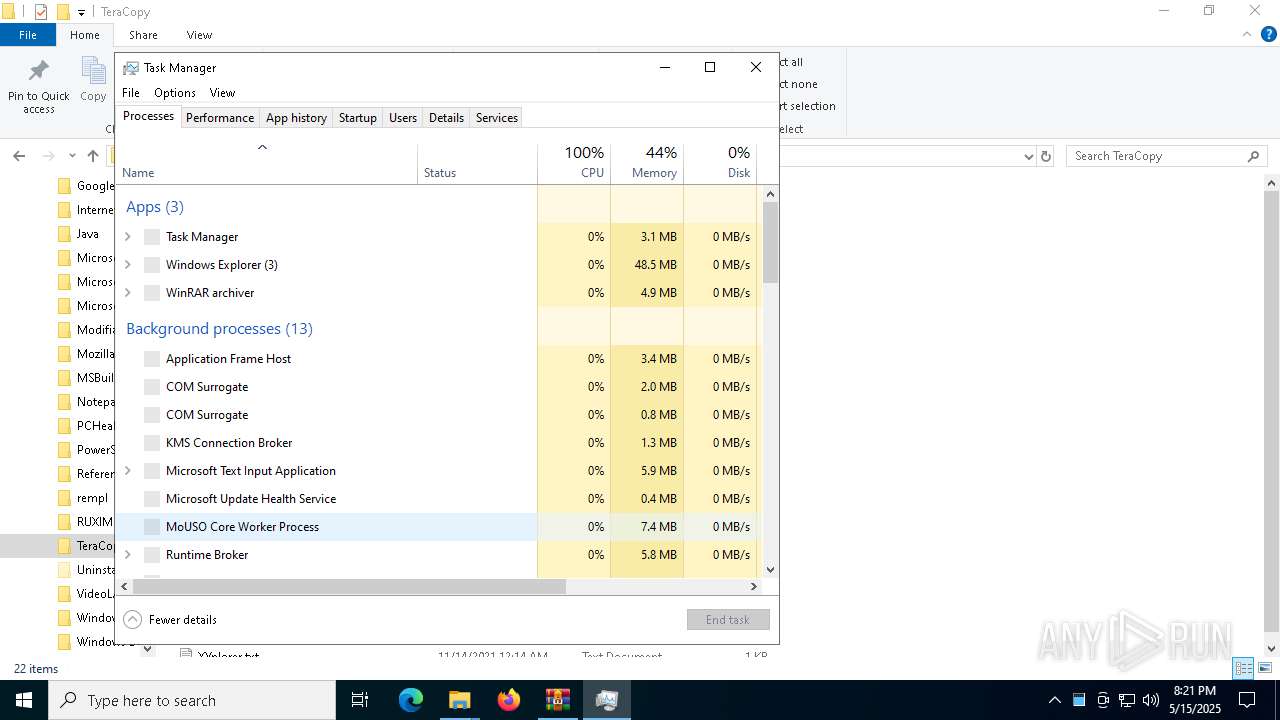
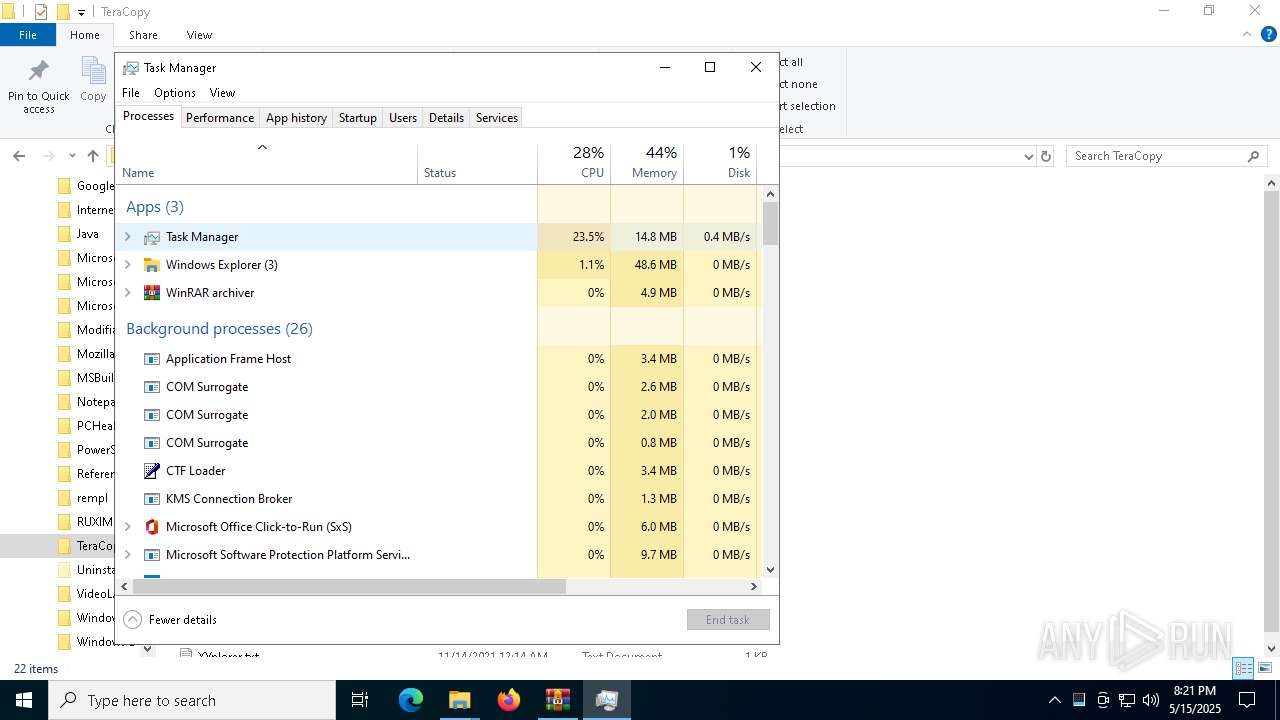
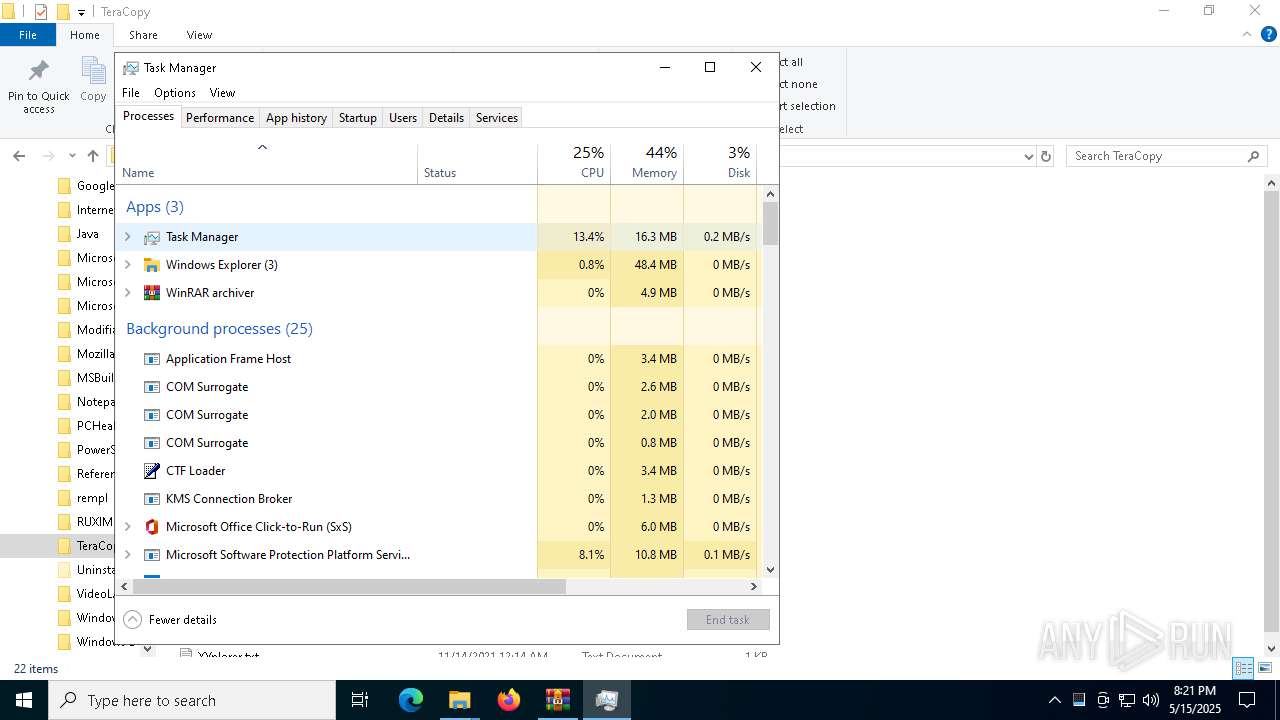
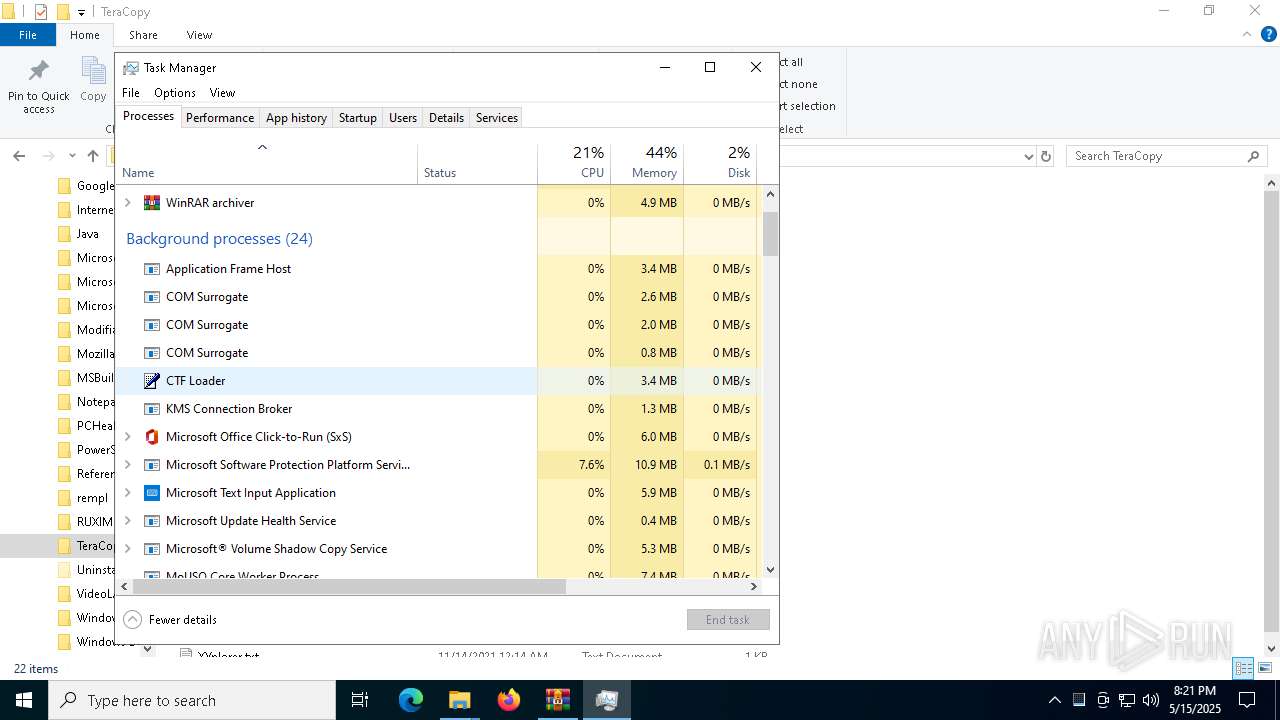
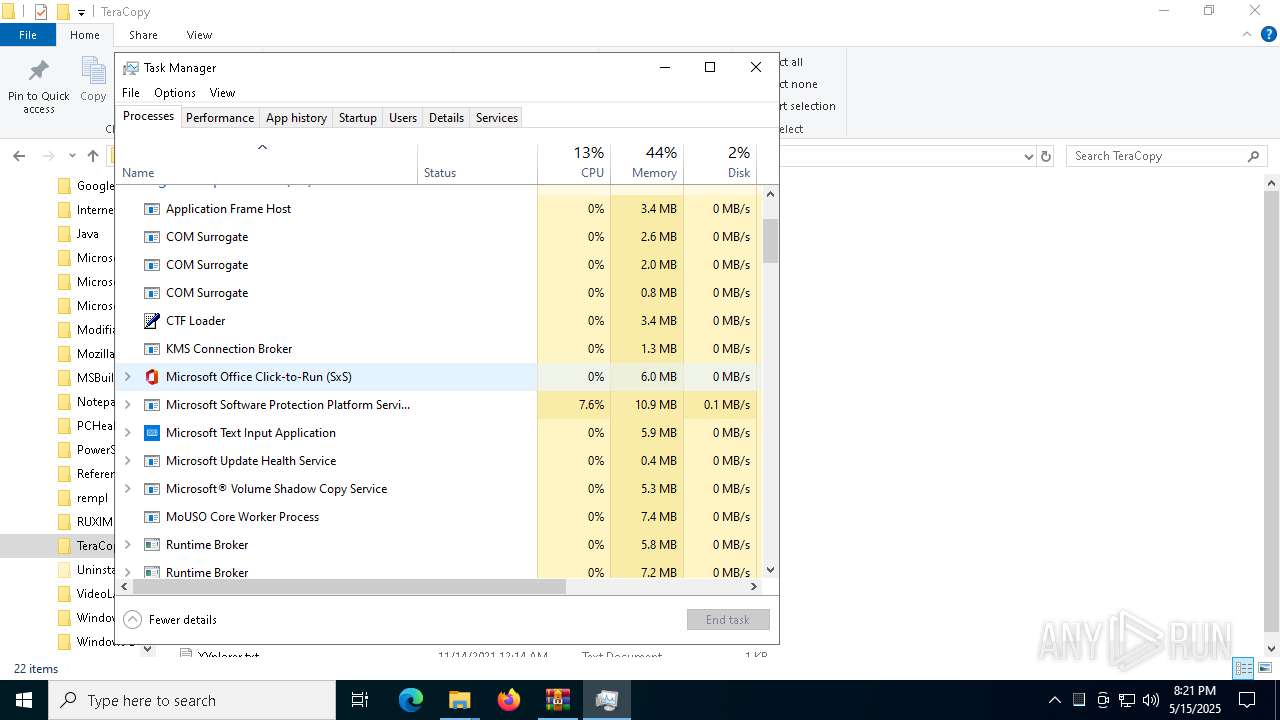
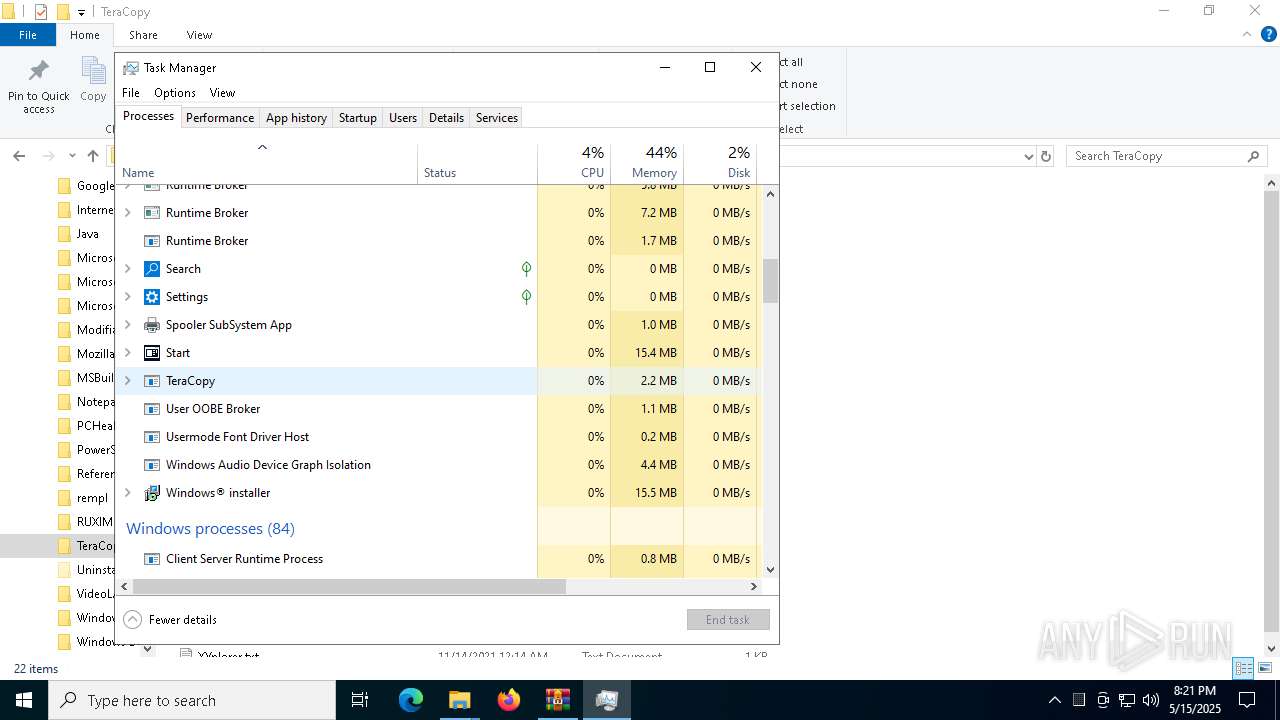
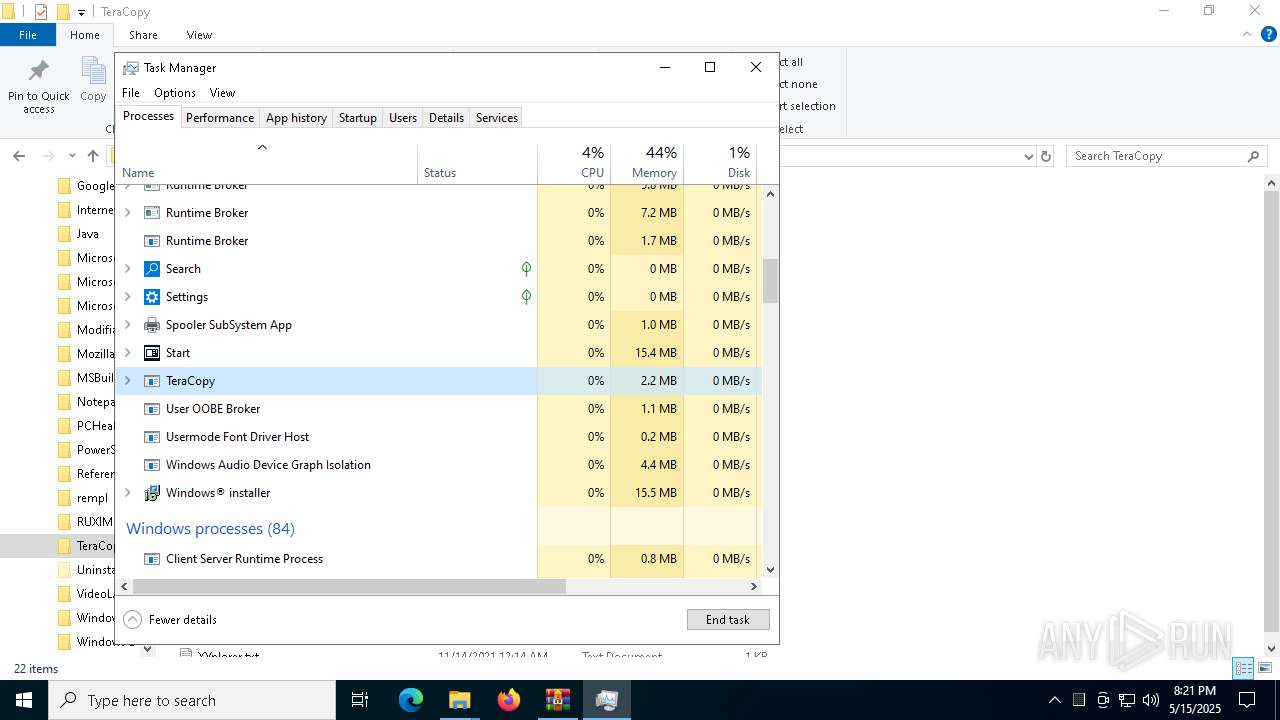
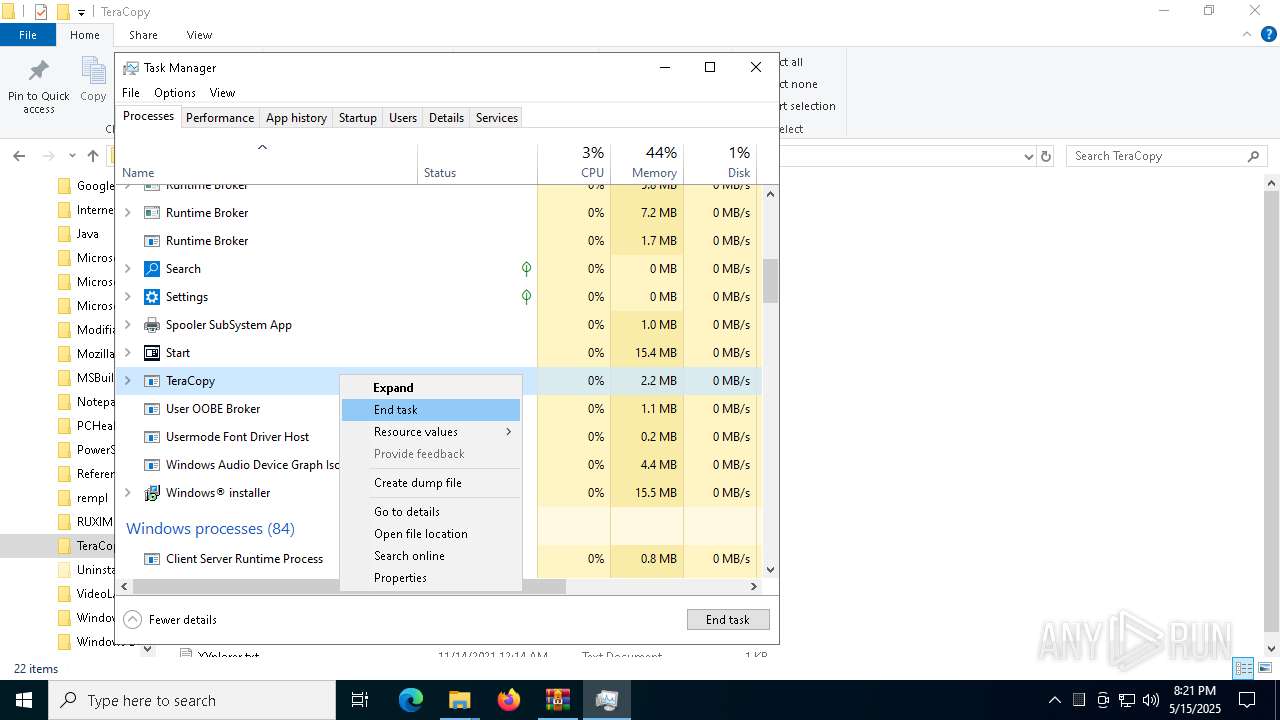
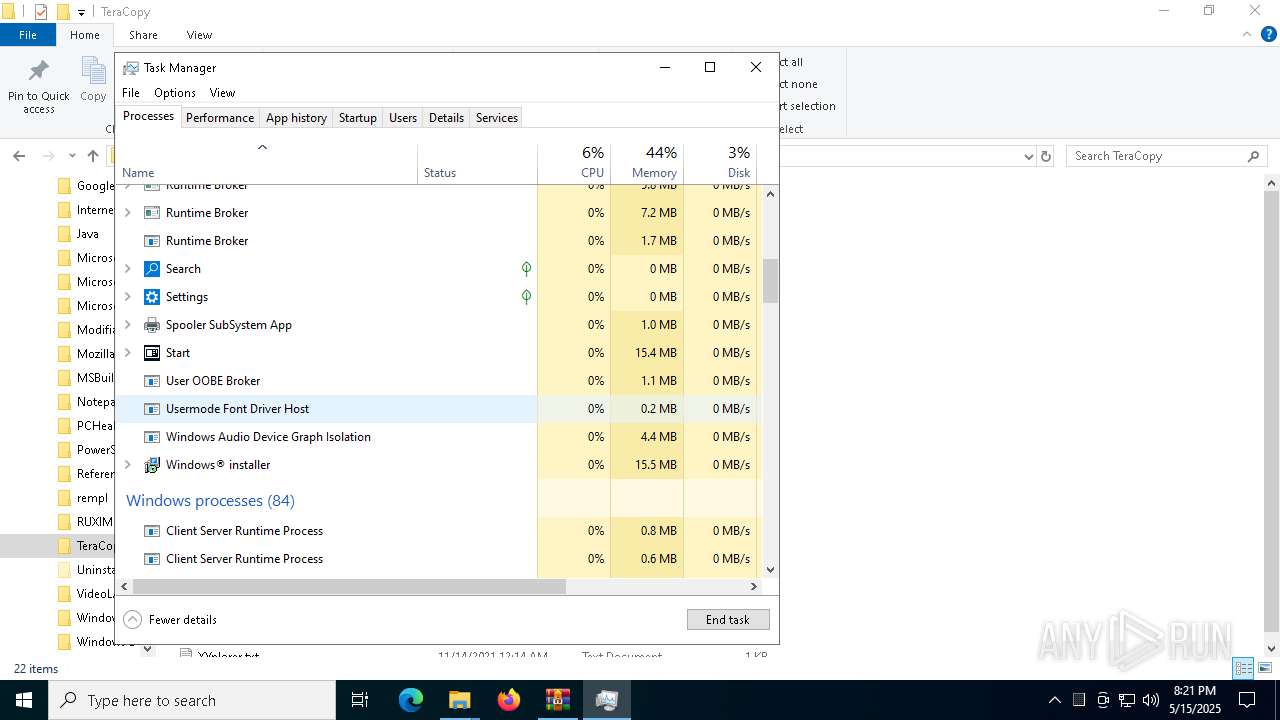
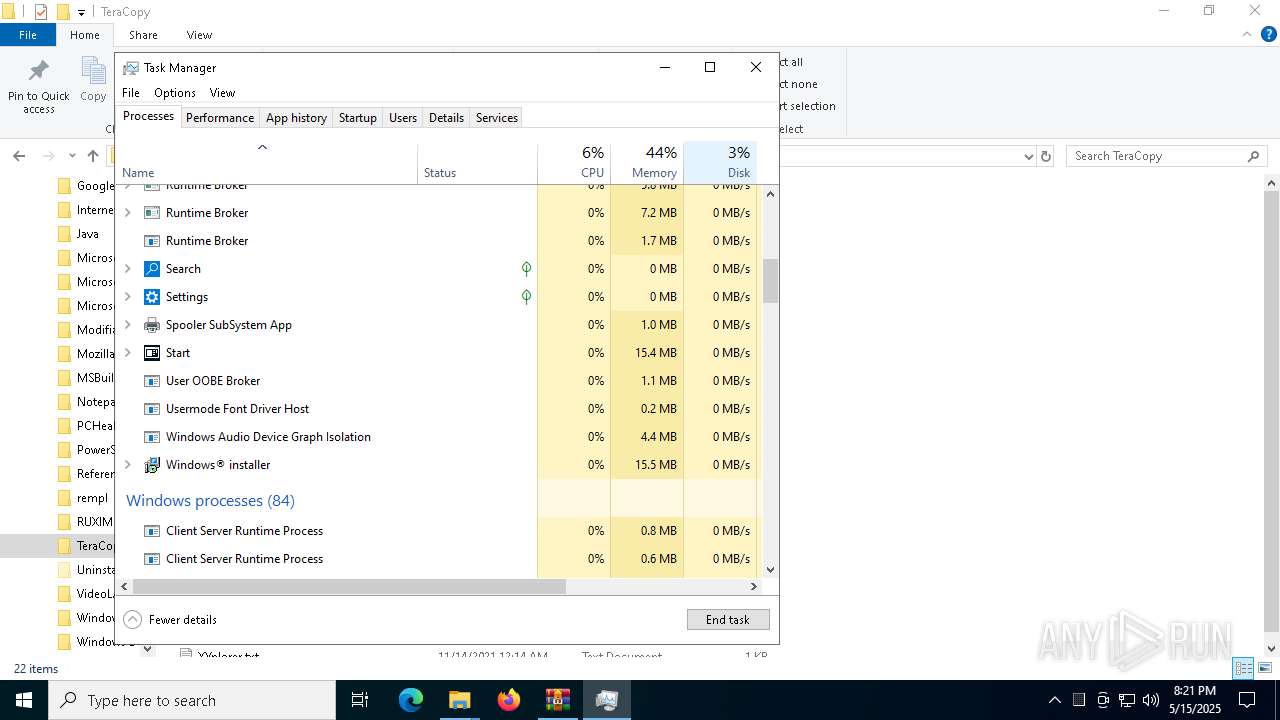
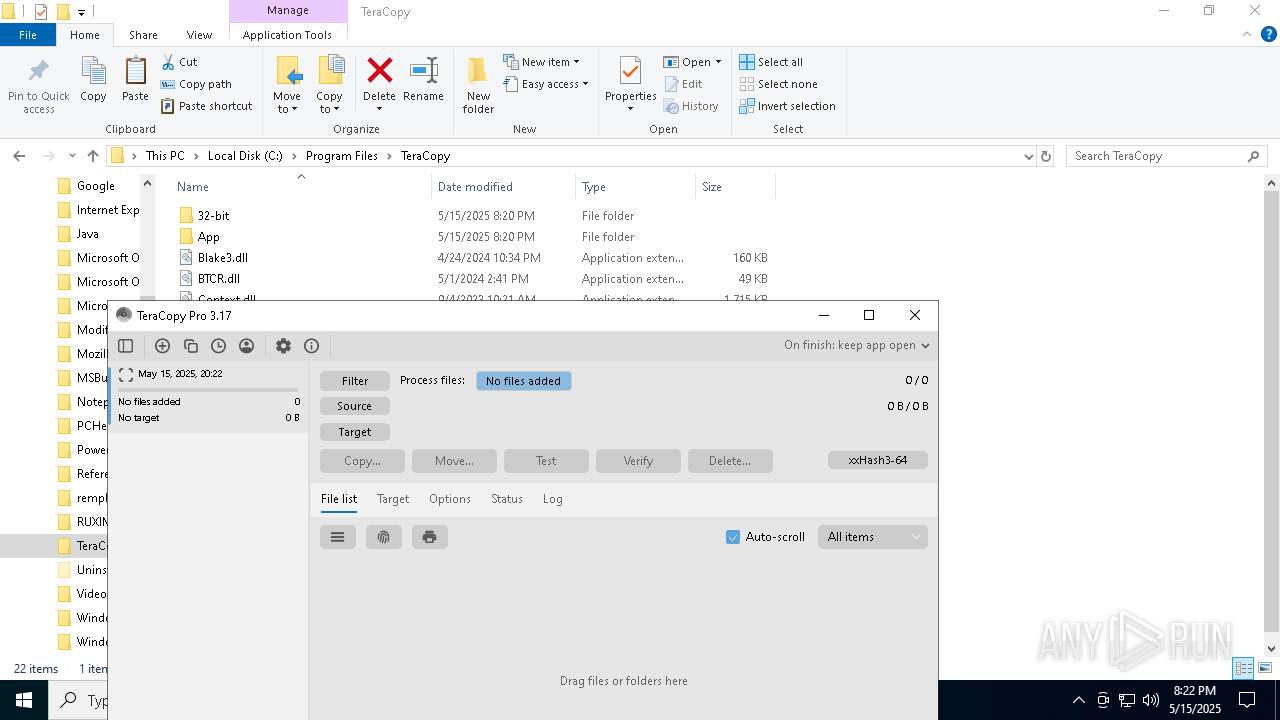
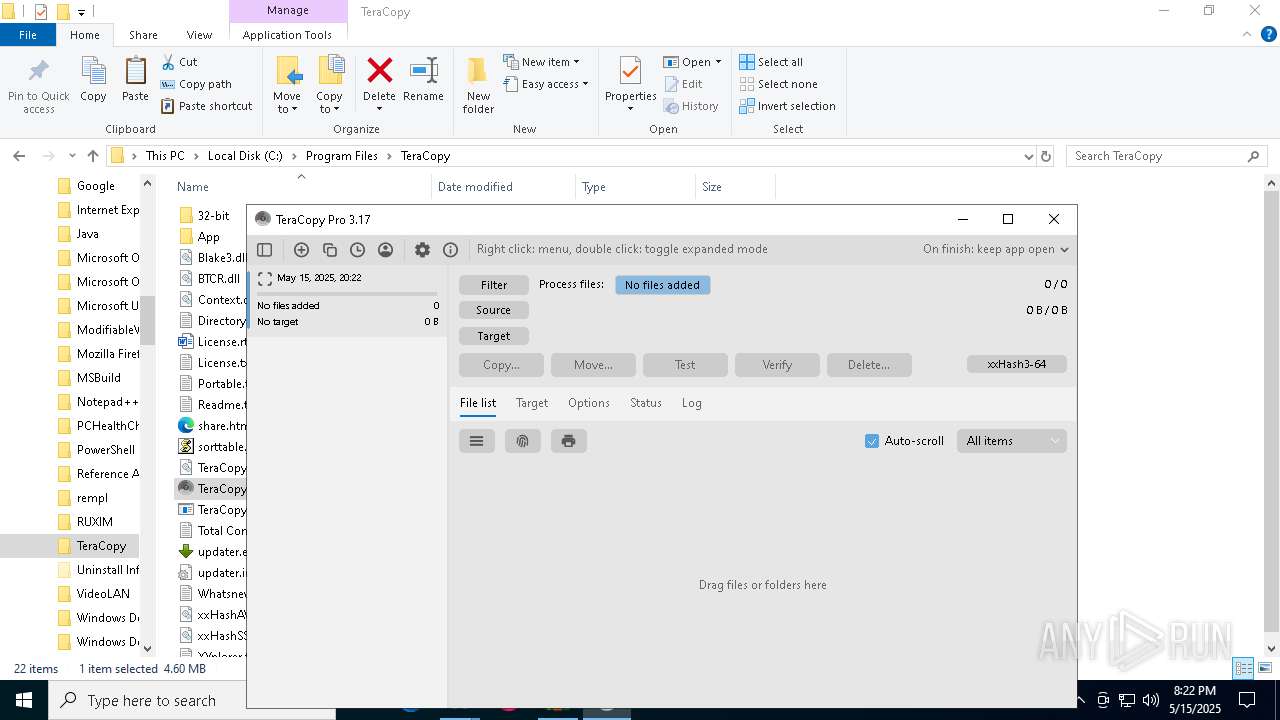
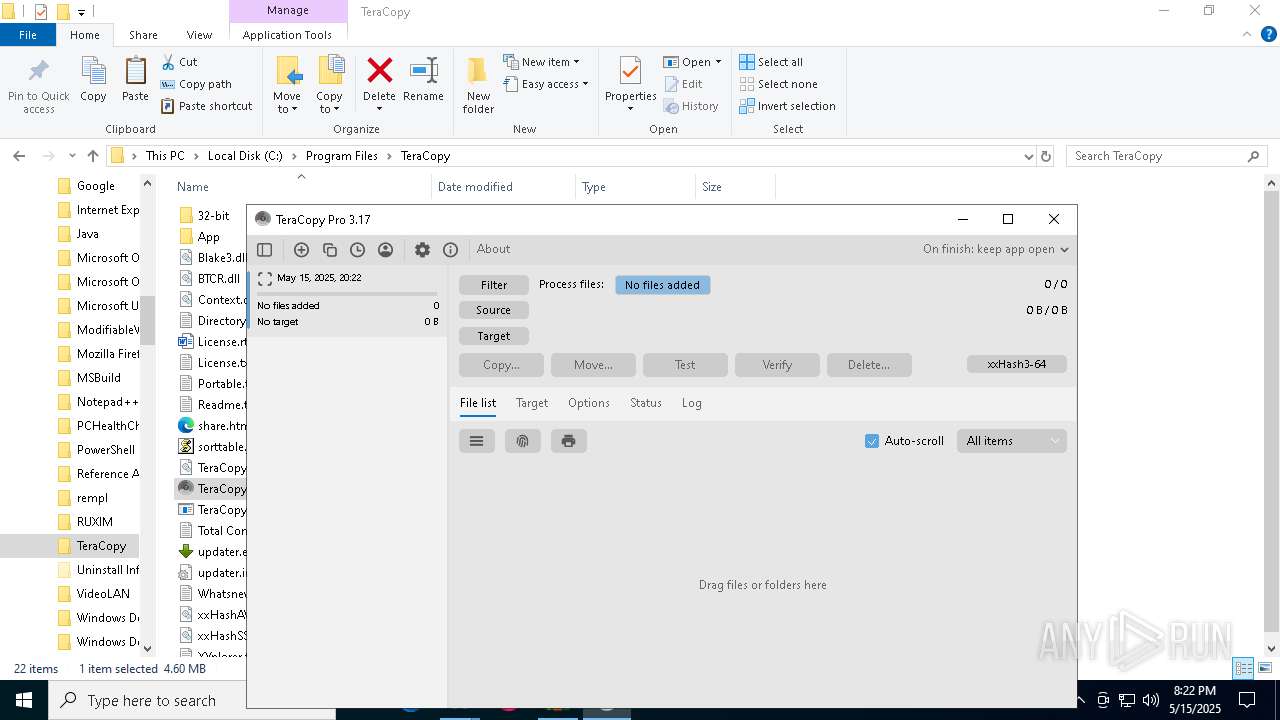
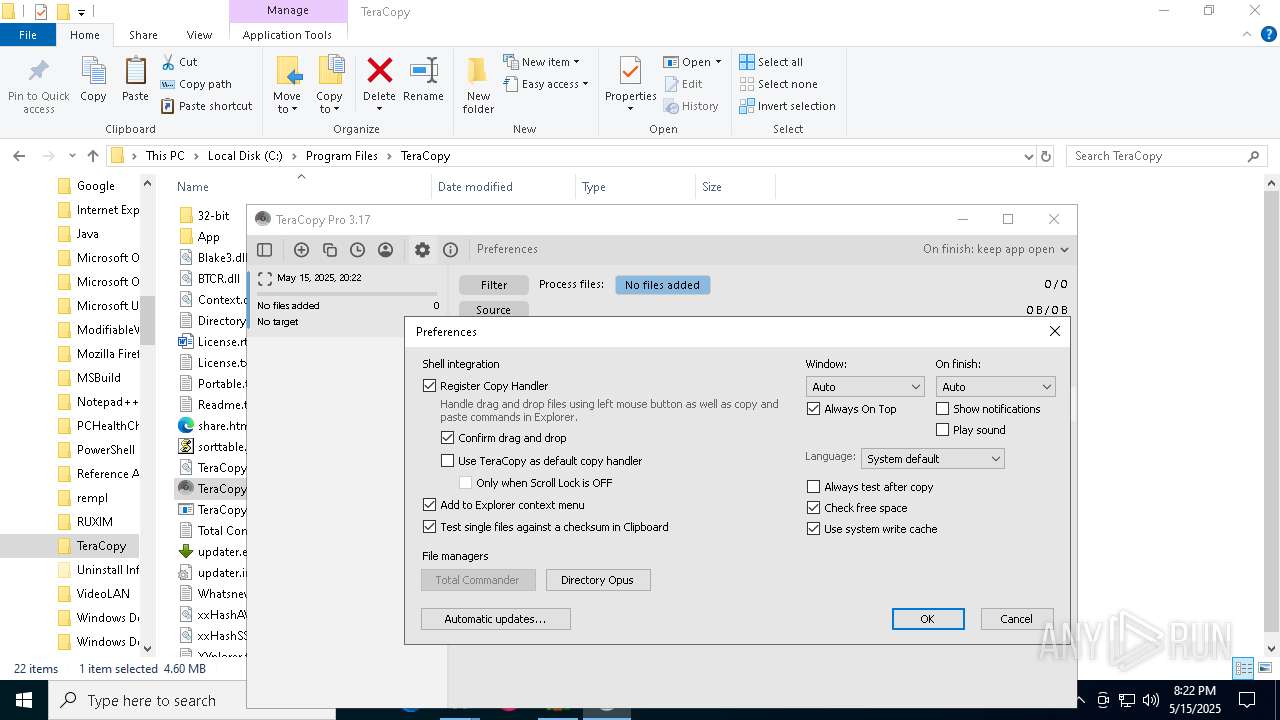
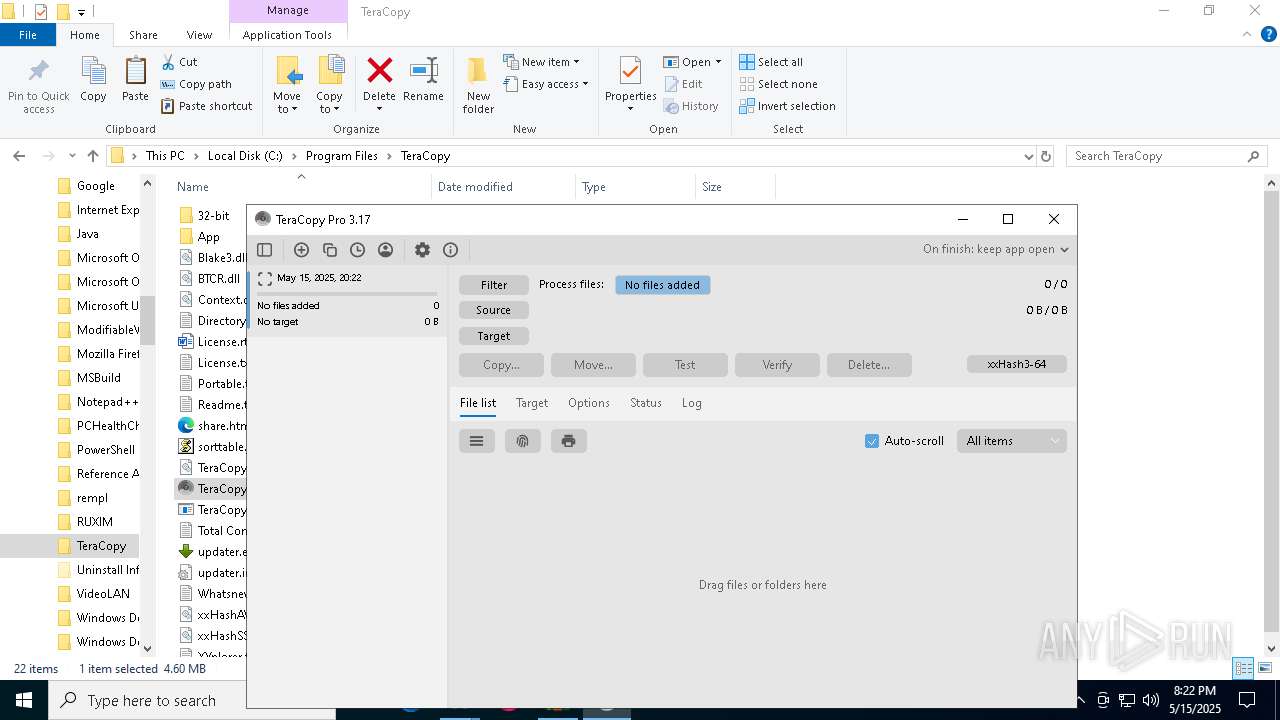
Manual execution by a user
- teracopy.exe (PID: 5972)
- Taskmgr.exe (PID: 5416)
- Taskmgr.exe (PID: 5400)
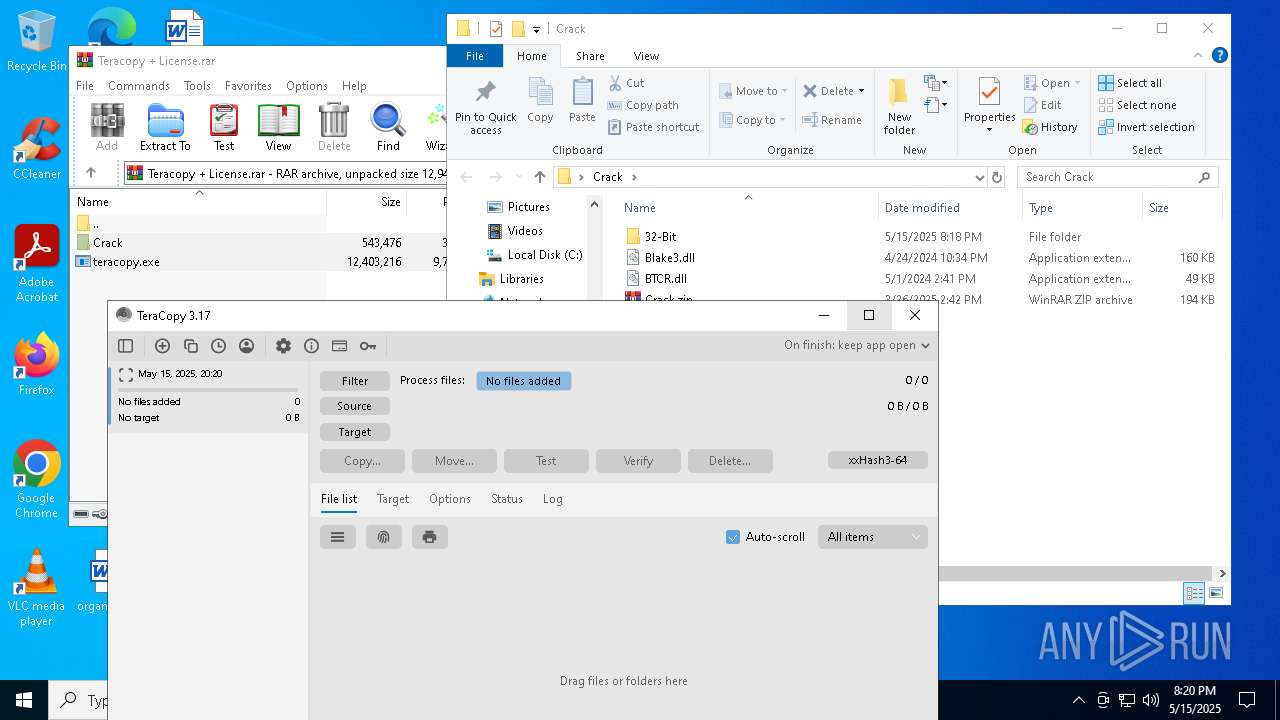
- TeraCopy.exe (PID: 5740)
Process checks computer location settings
- teracopy.exe (PID: 5972)
Reads the machine GUID from the registry
- teracopy.exe (PID: 5304)
- teracopy.exe (PID: 5972)
Reads the software policy settings
- teracopy.exe (PID: 5304)
- teracopy.exe (PID: 5972)
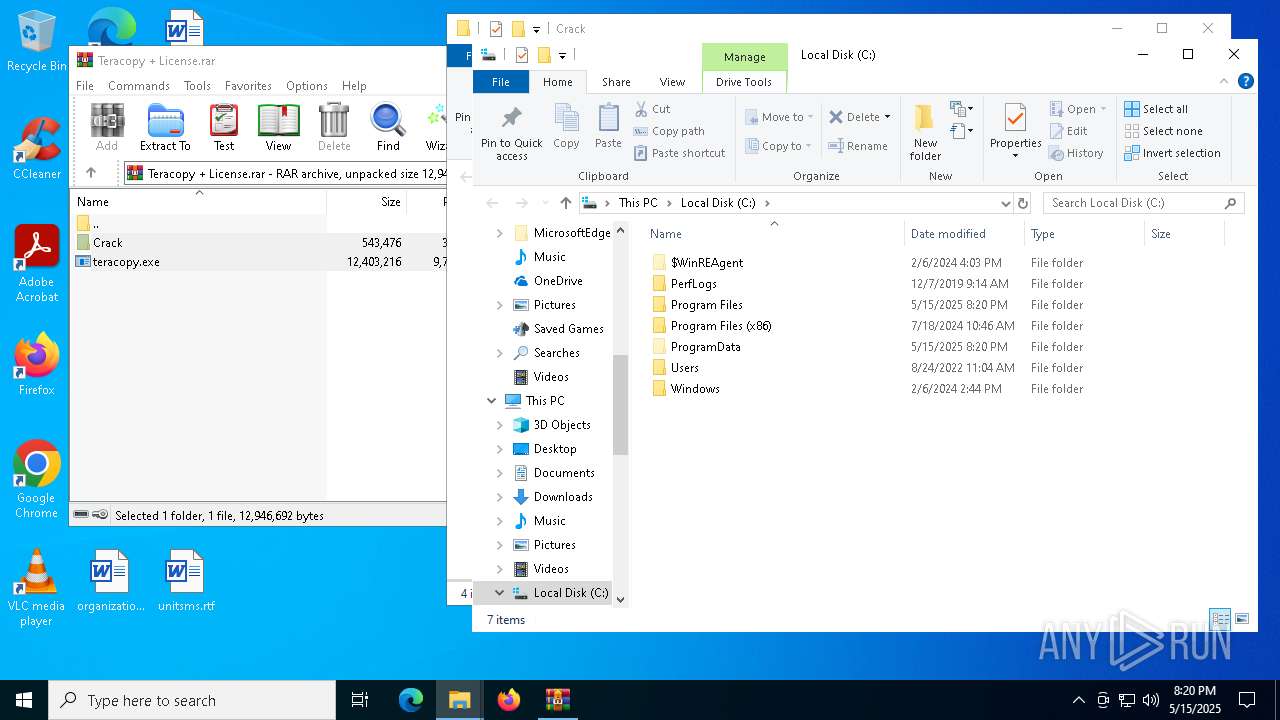
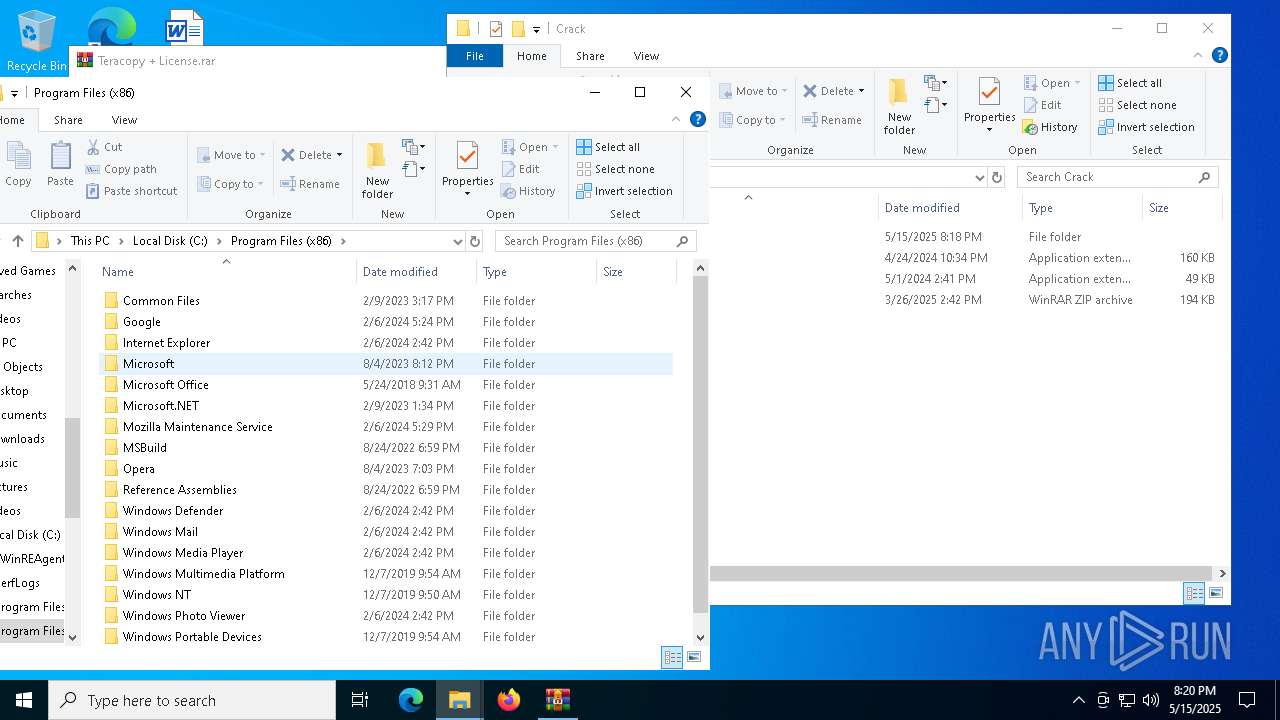
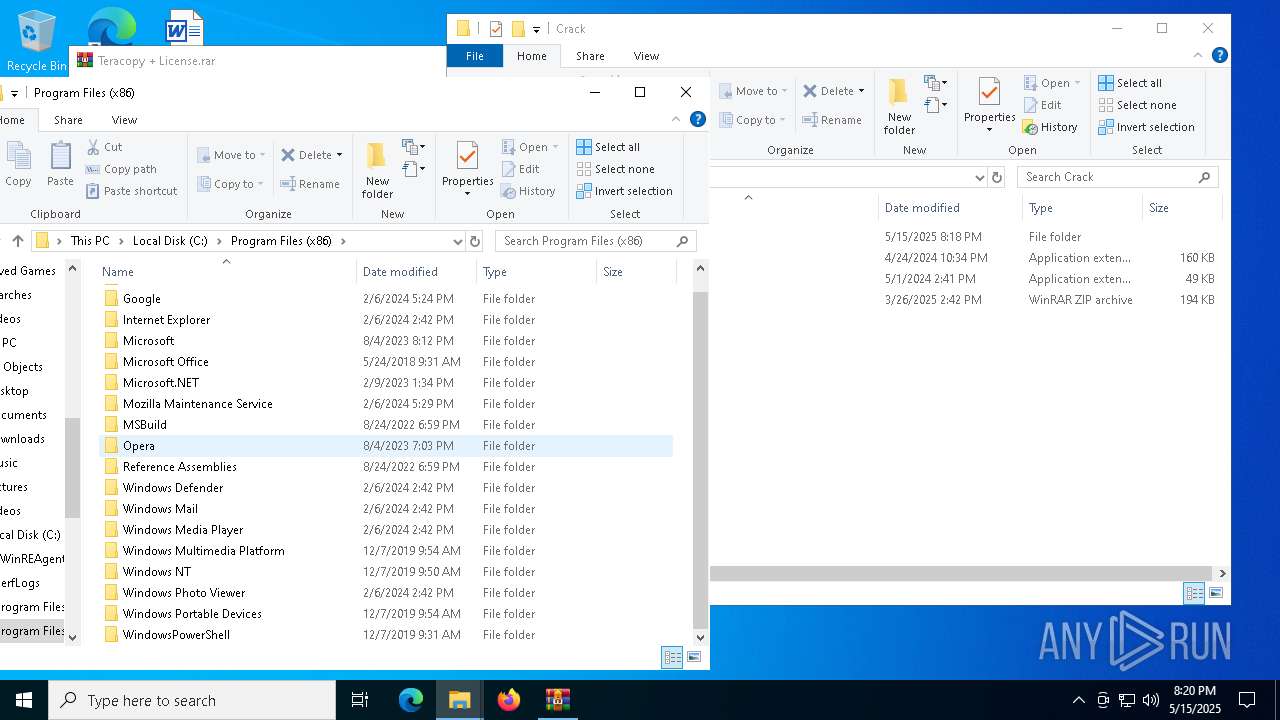
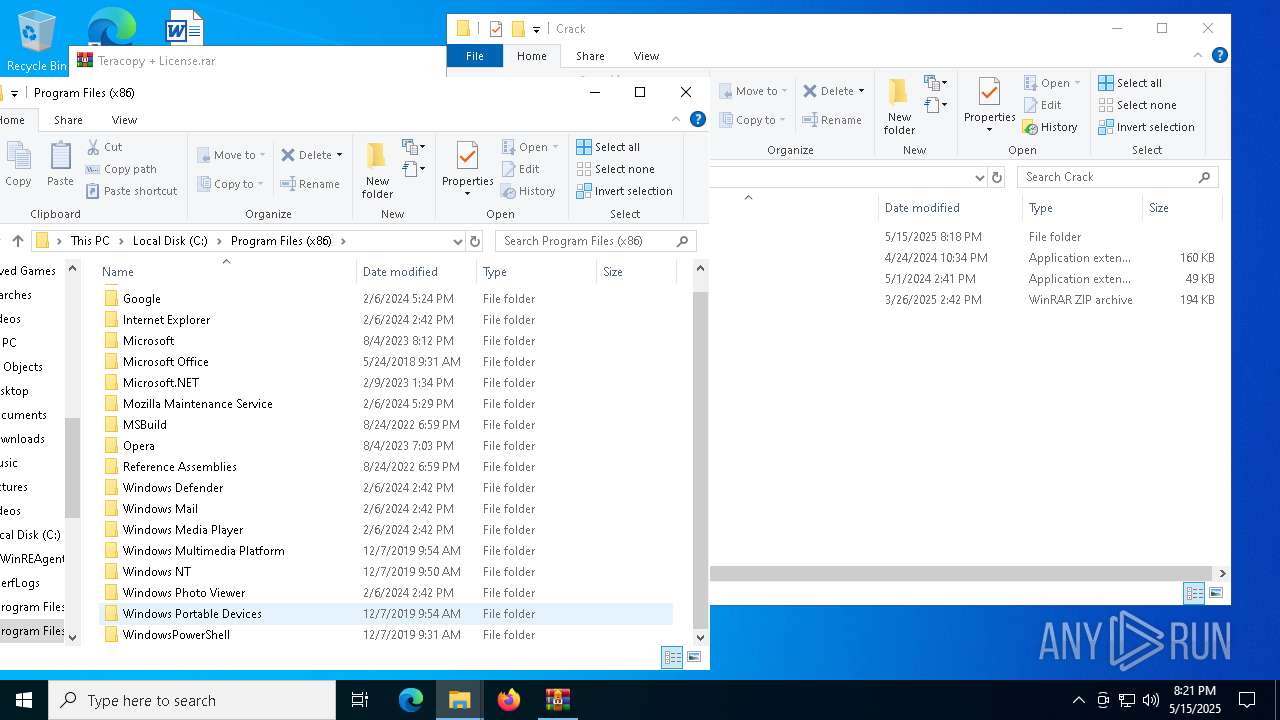
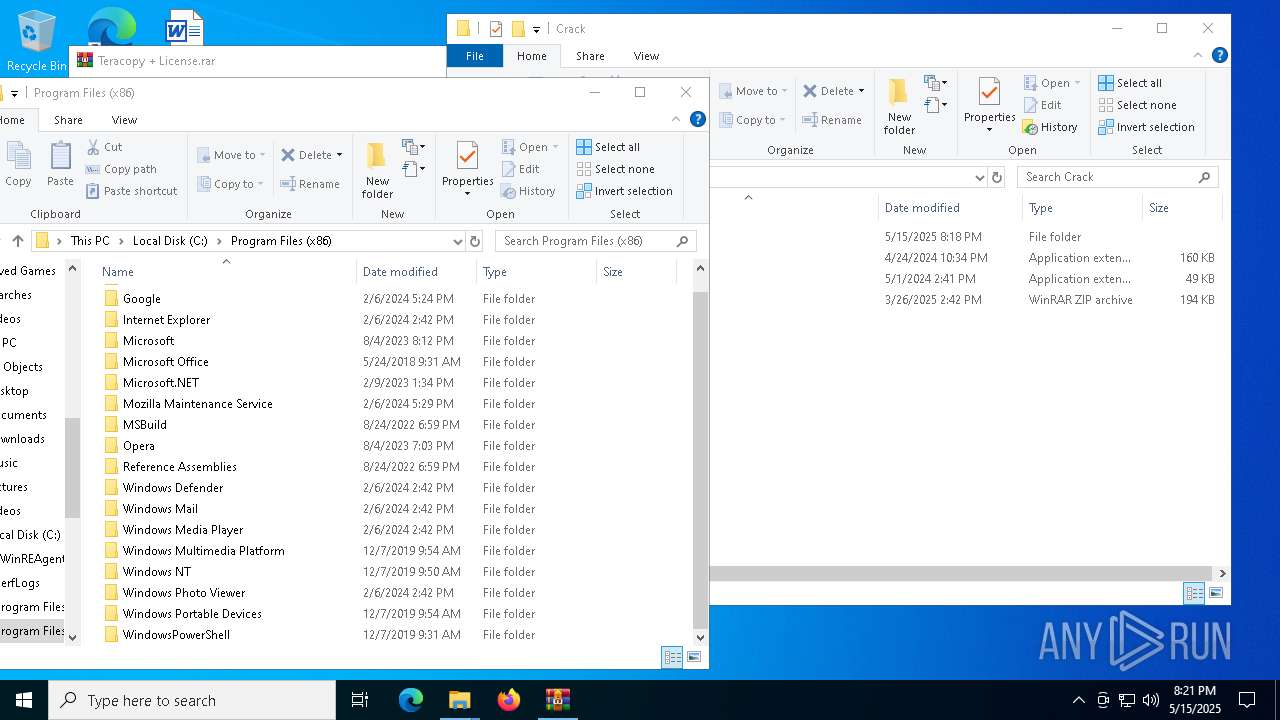
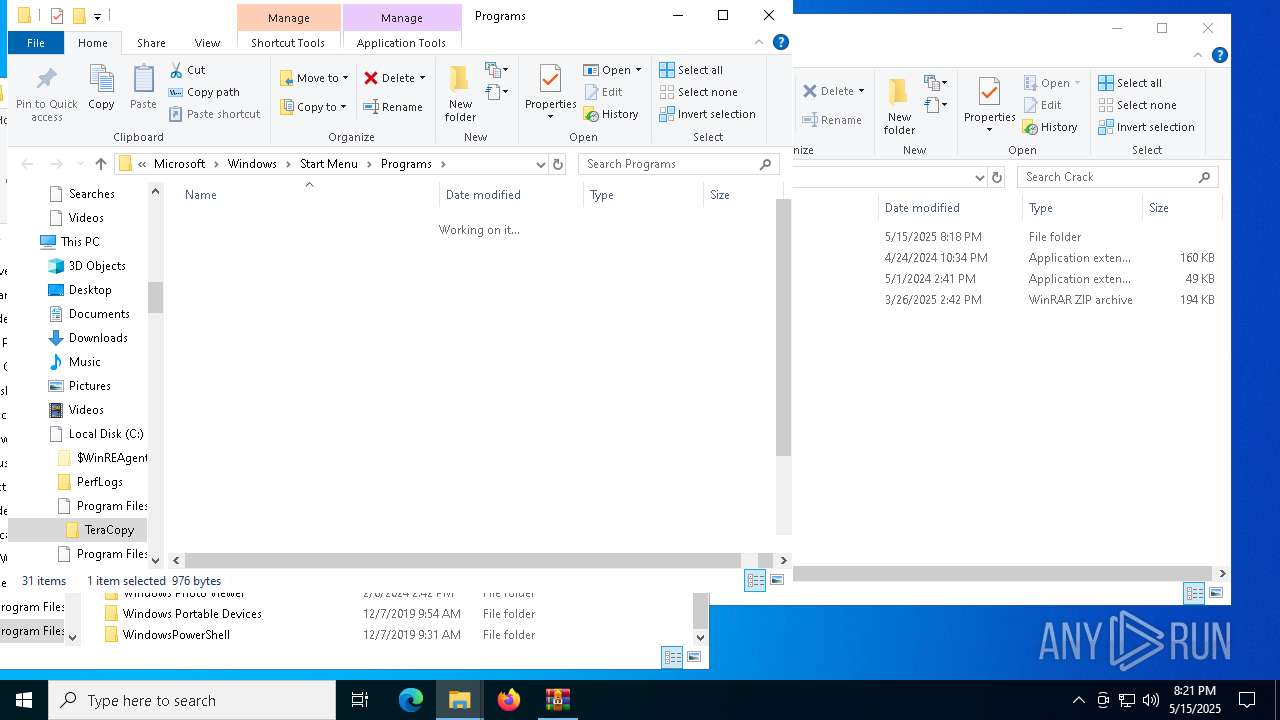
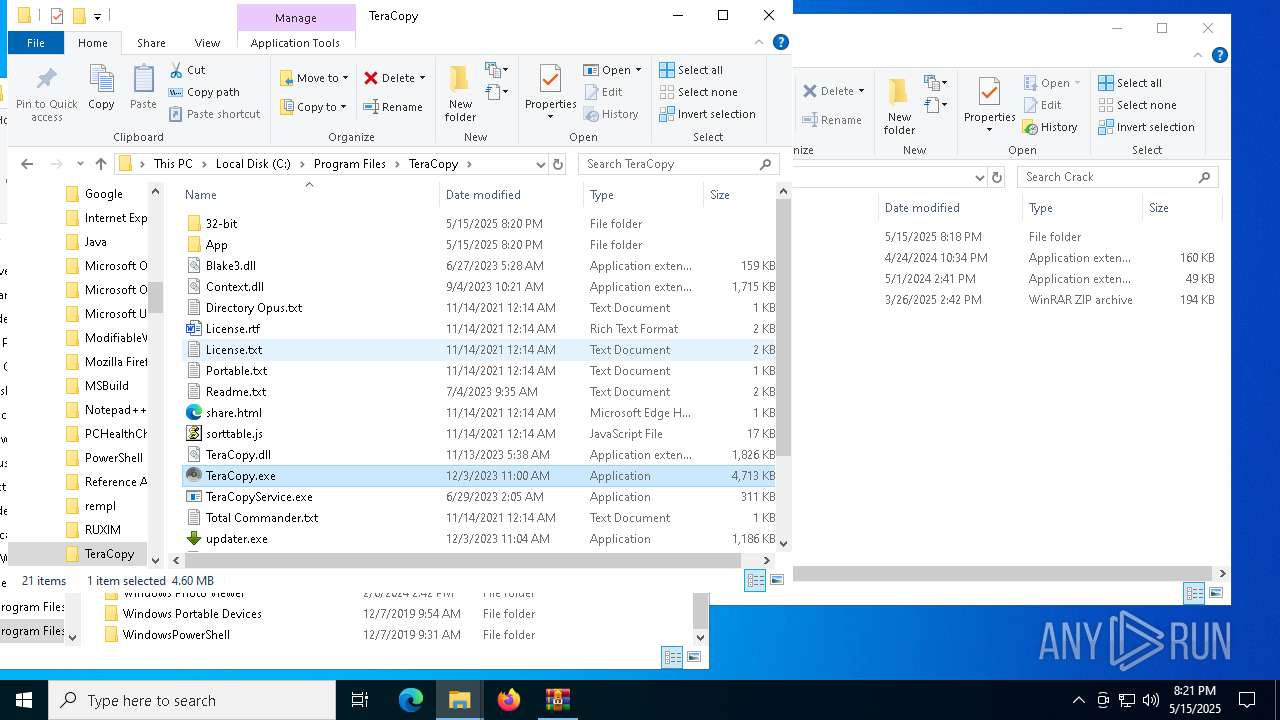
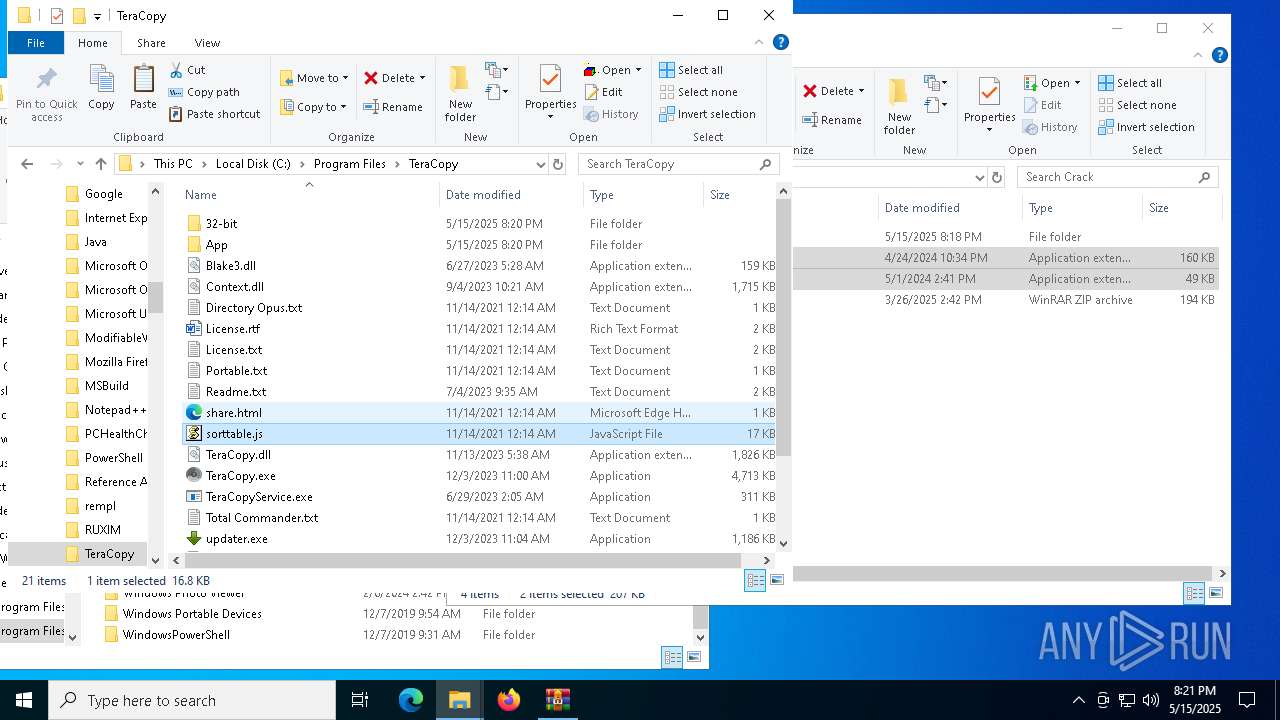
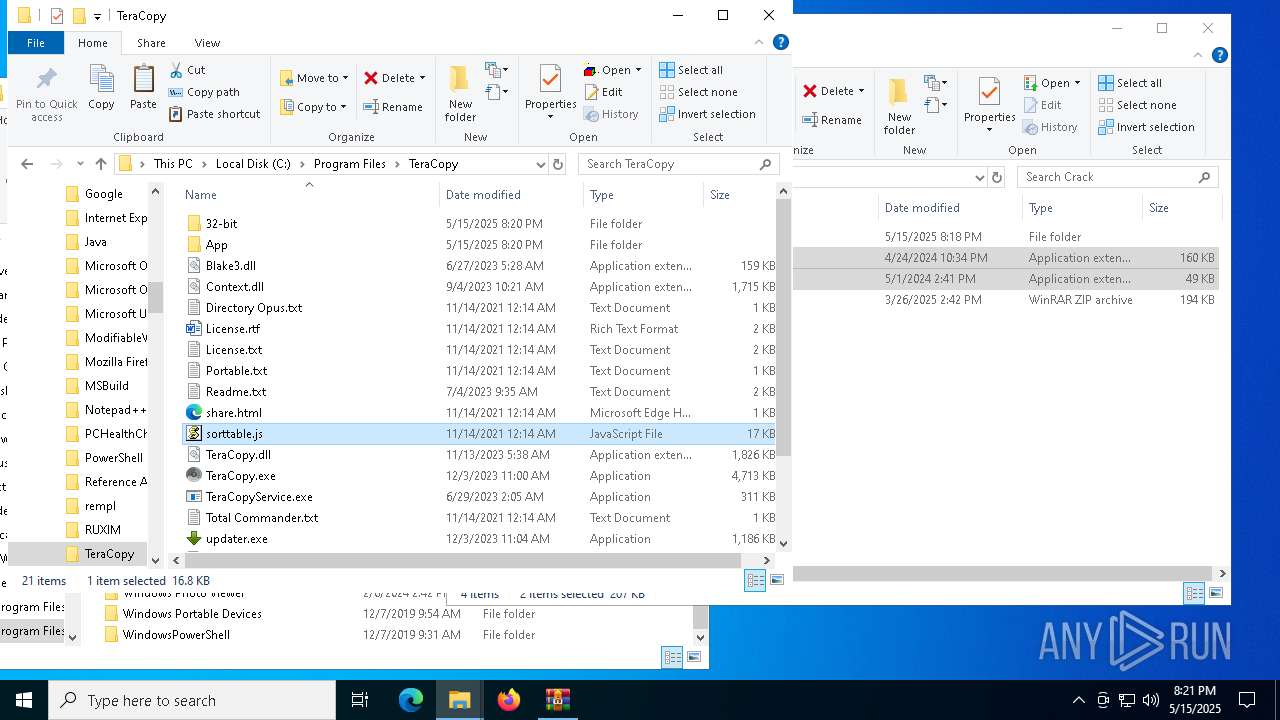
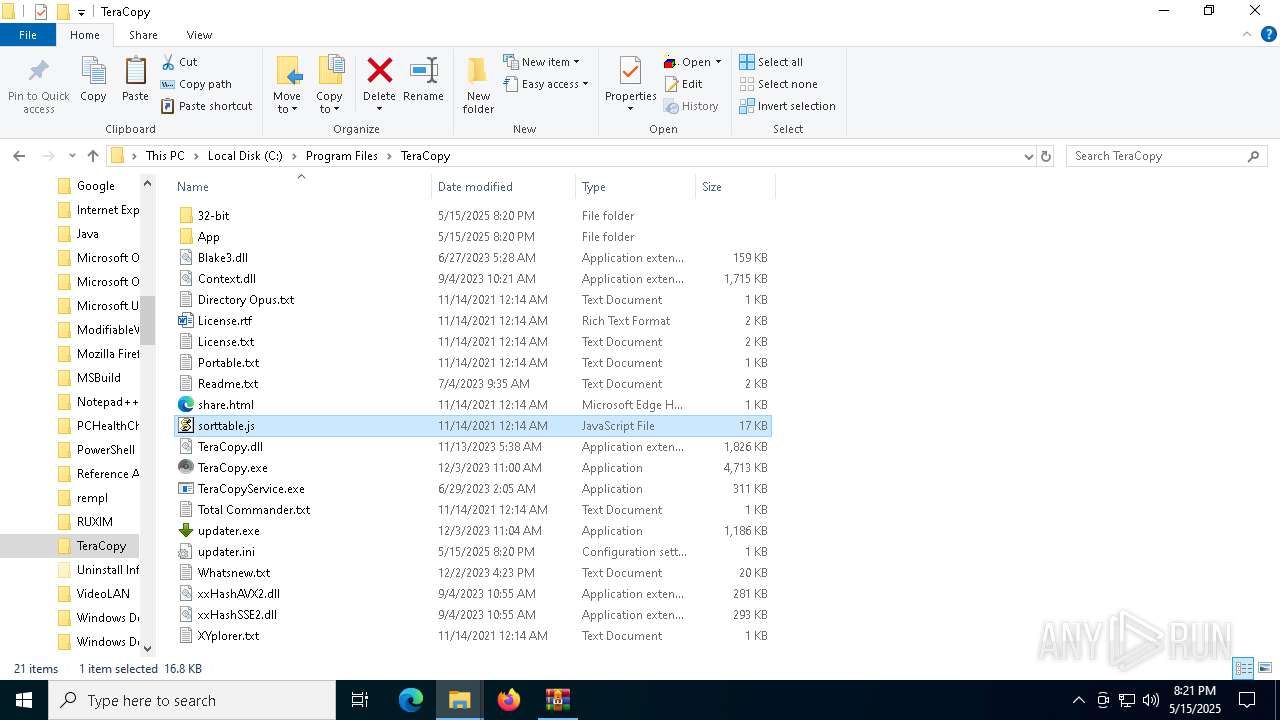
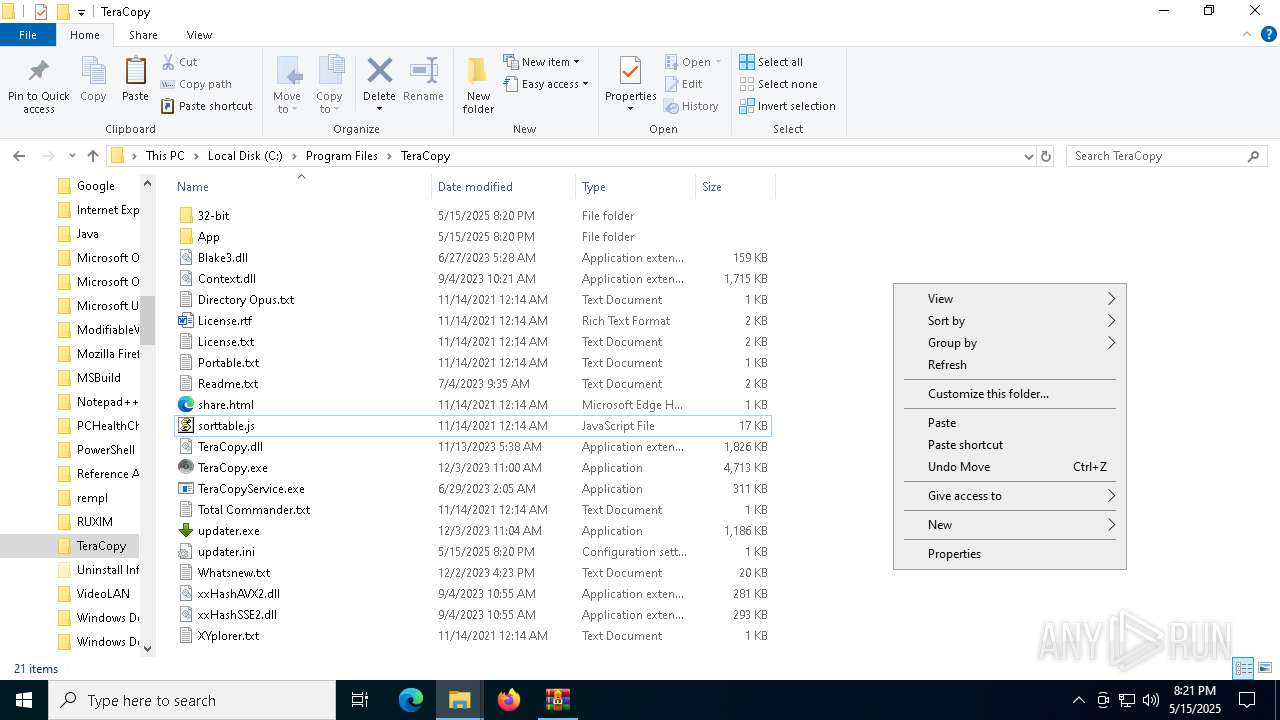
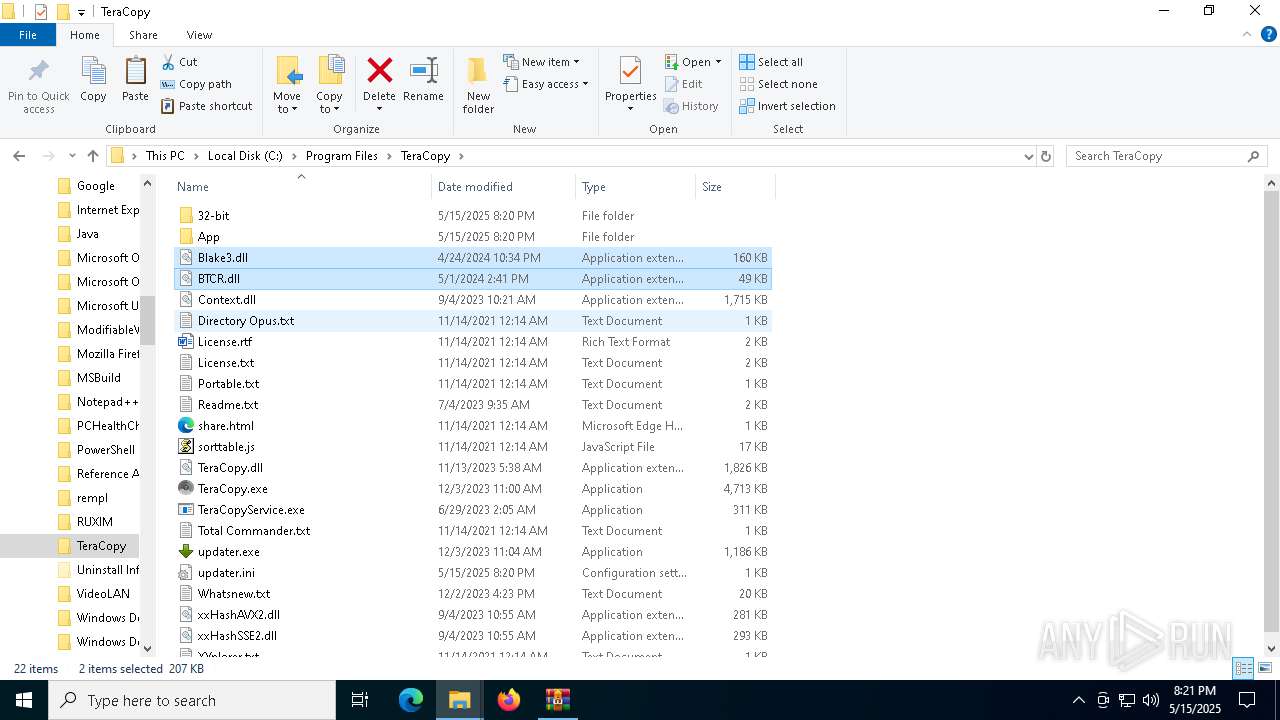
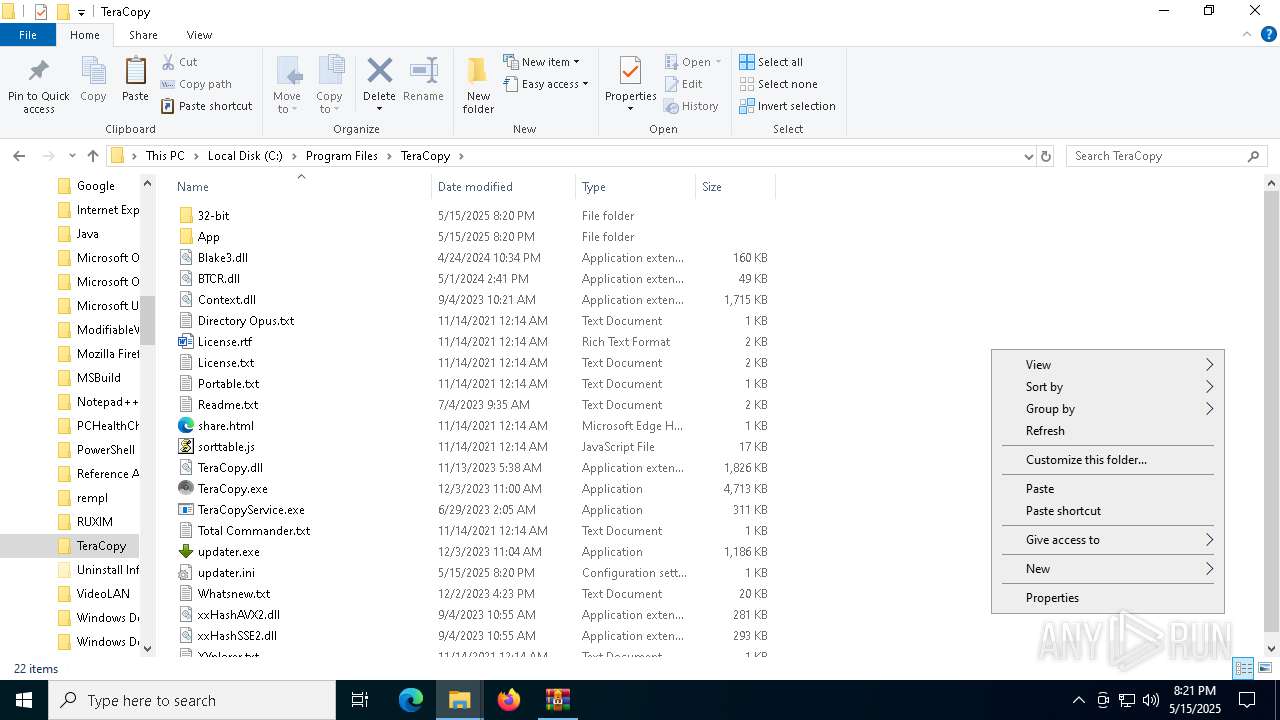
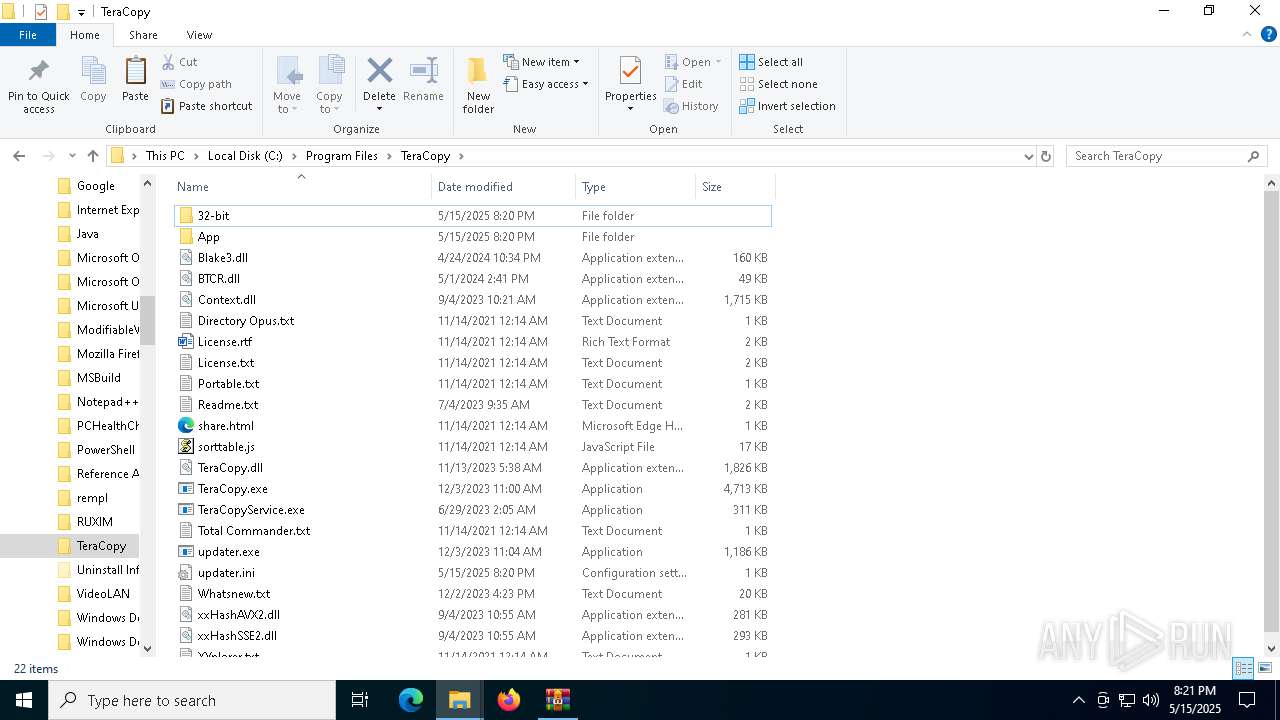
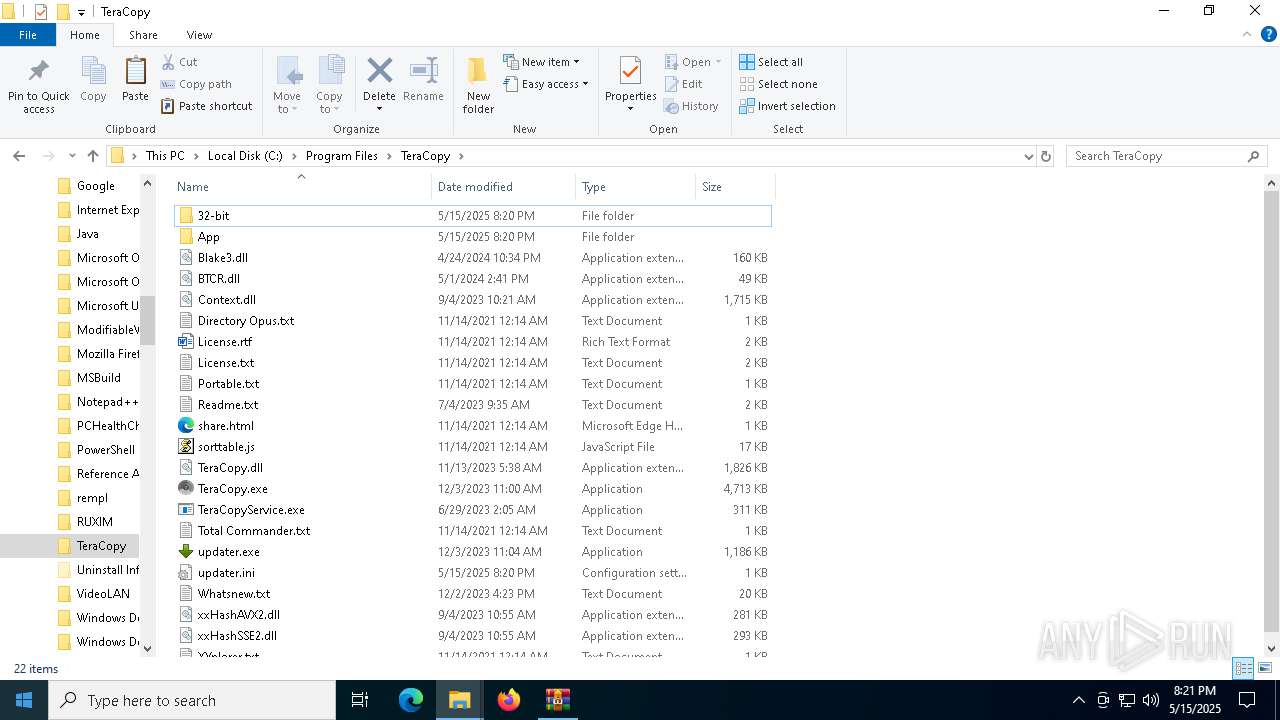
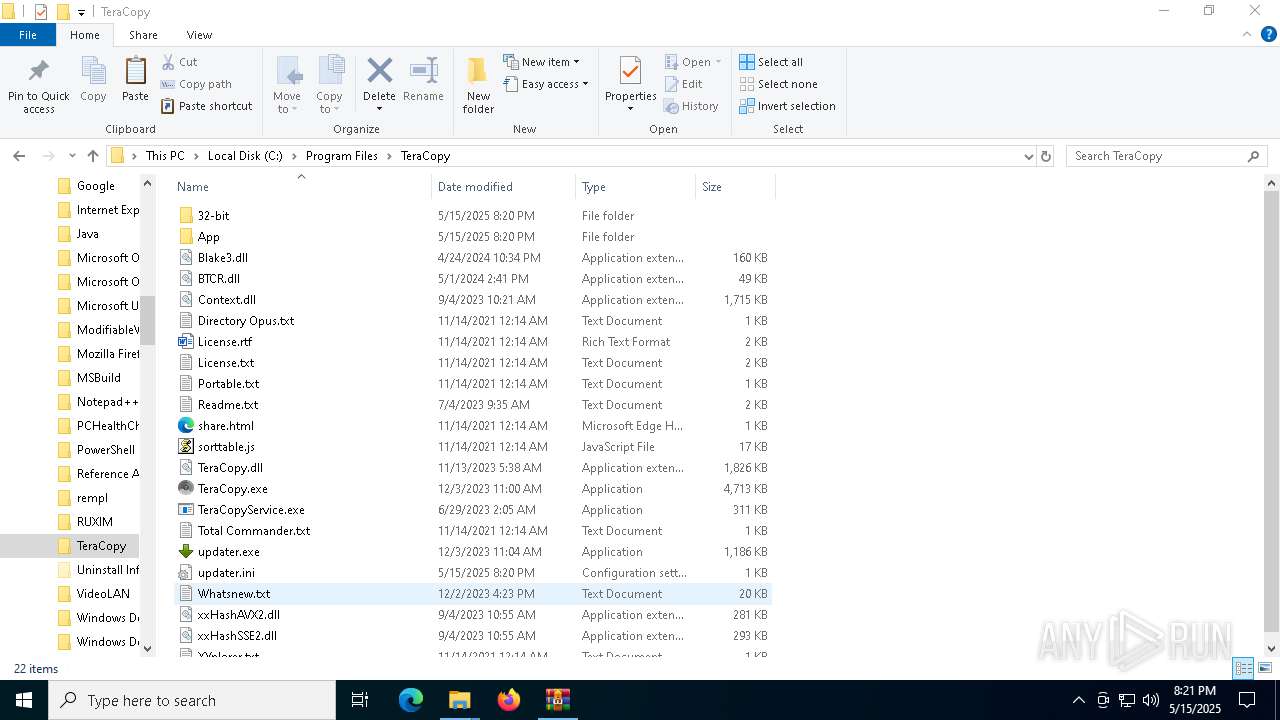
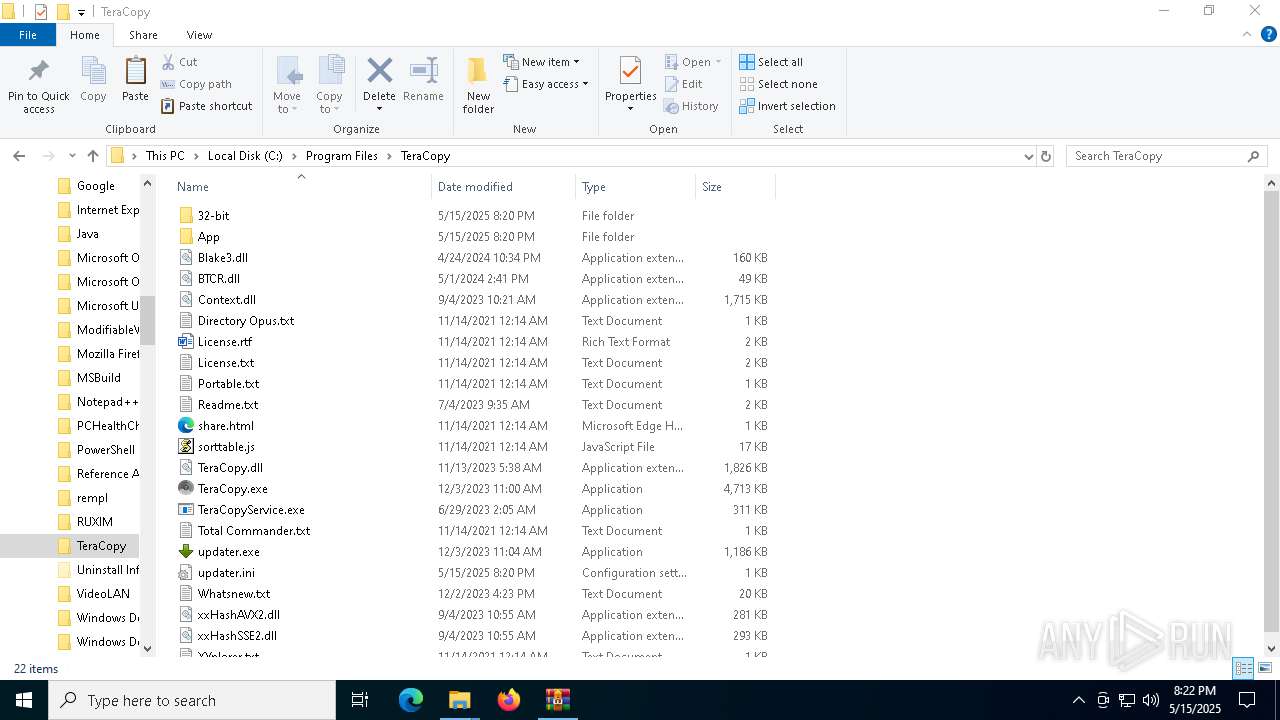
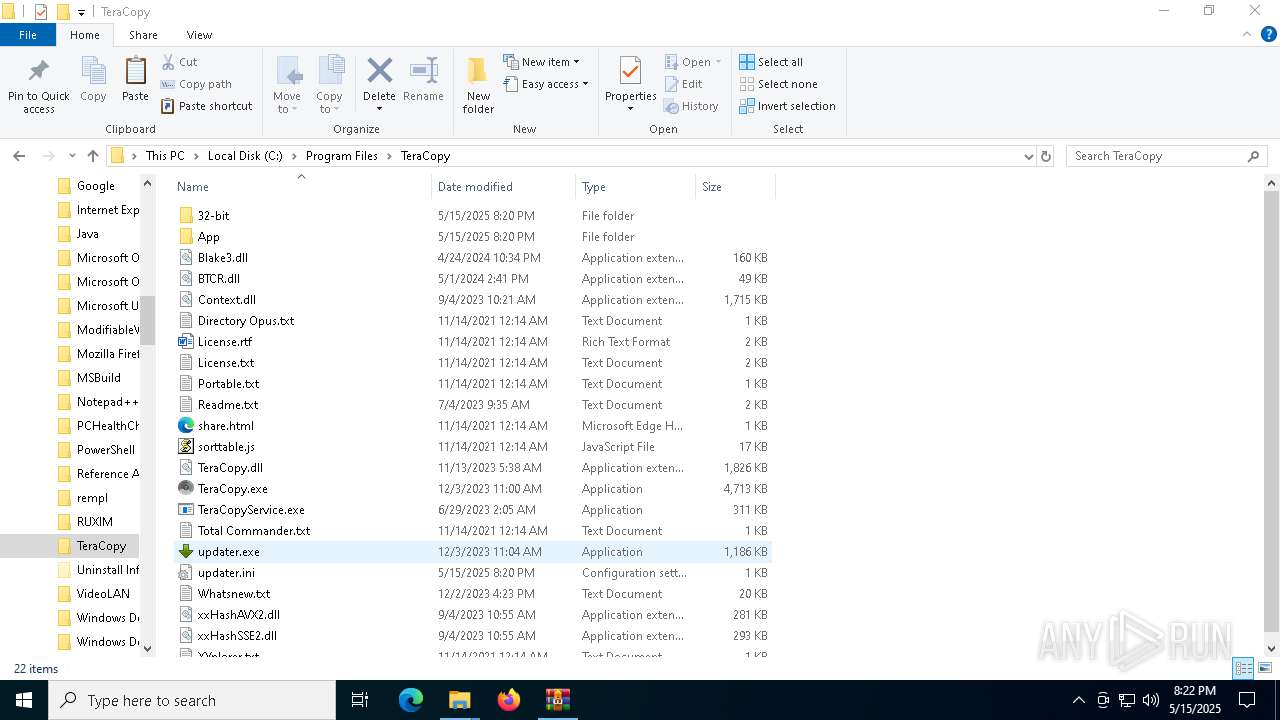
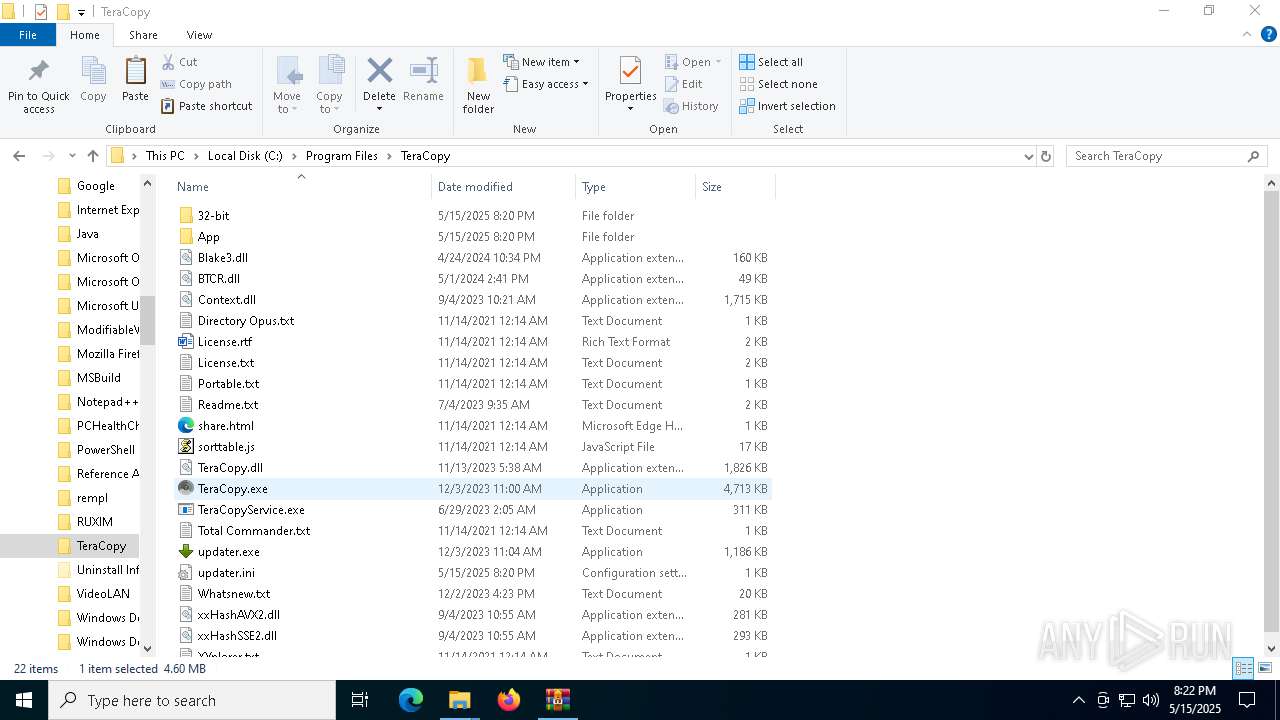
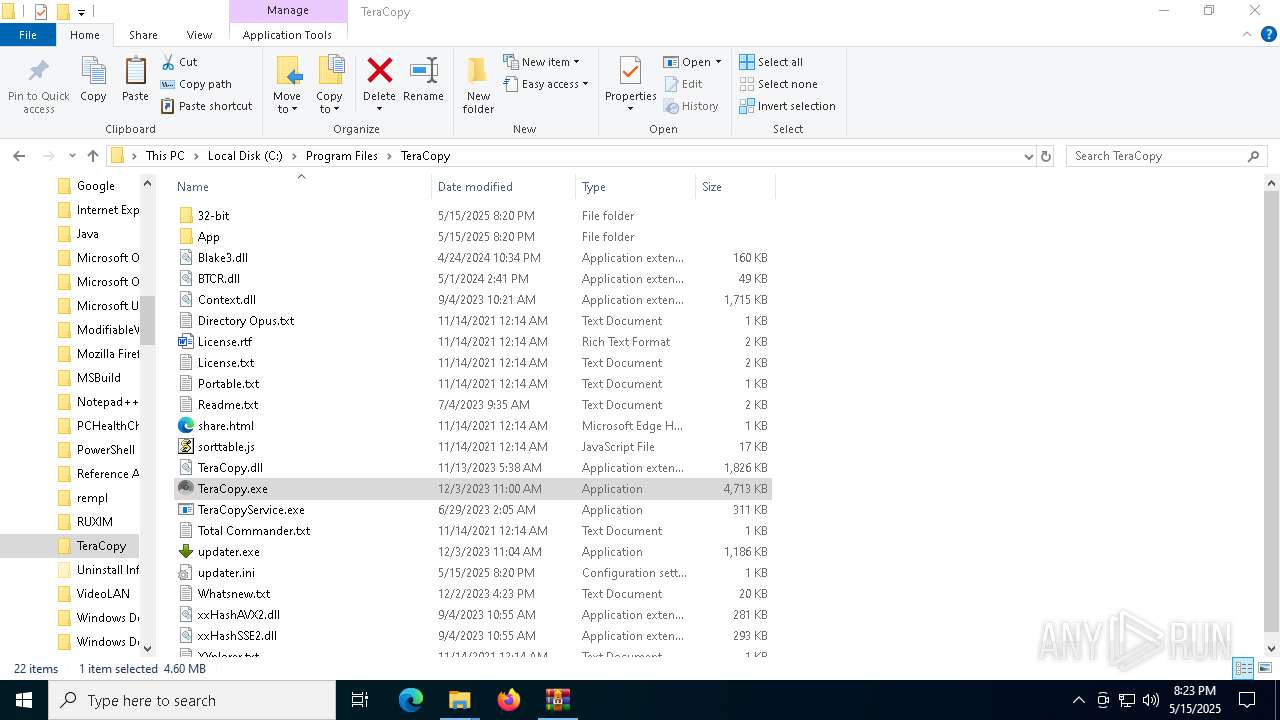
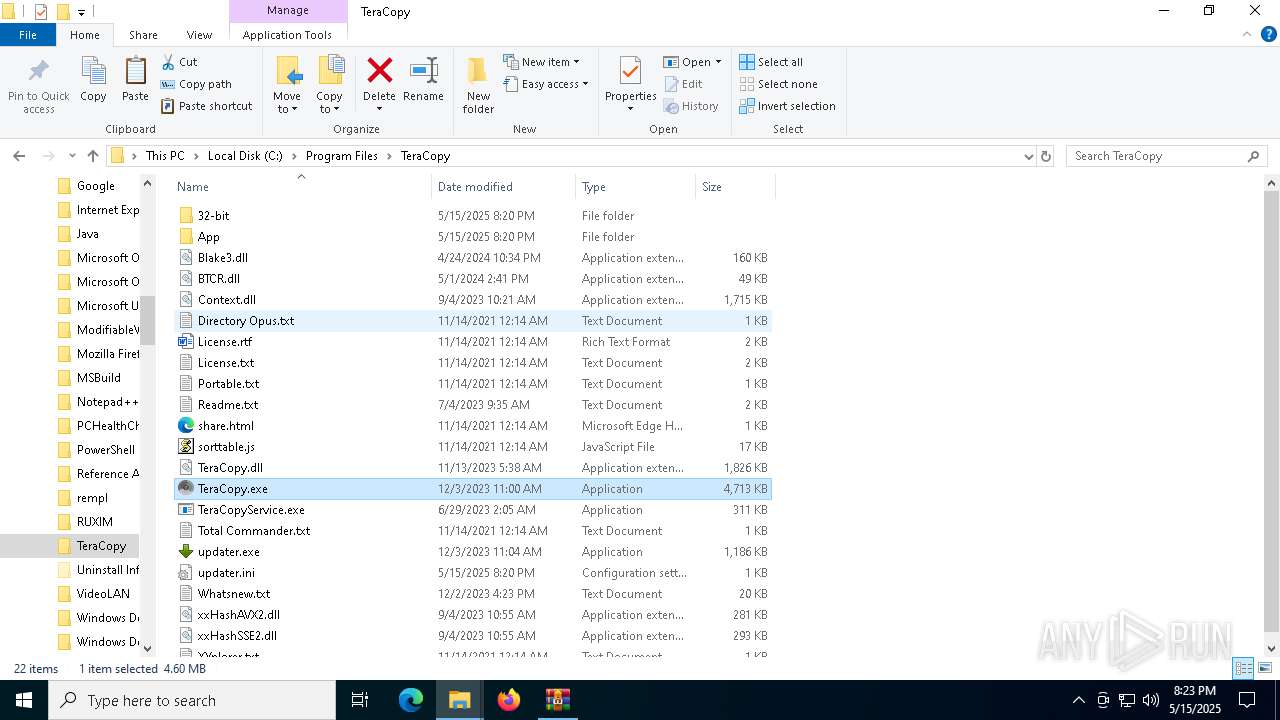
Creates files in the program directory
- teracopy.exe (PID: 5304)
Manages system restore points
- SrTasks.exe (PID: 872)
Creates files or folders in the user directory
- teracopy.exe (PID: 5972)
Checks proxy server information
- teracopy.exe (PID: 5972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 42201 |
| UncompressedSize: | 90734 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Crack/32-Bit/Blake3.dll |
Total processes
165
Monitored processes
24
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
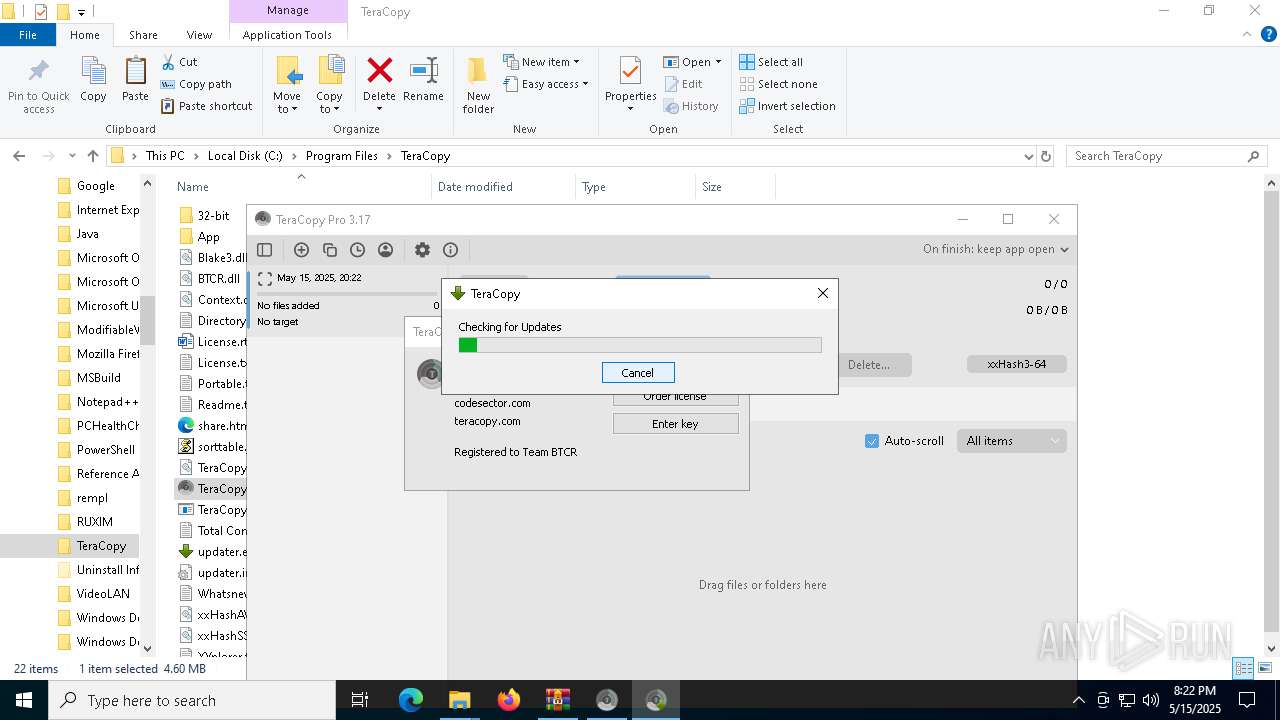
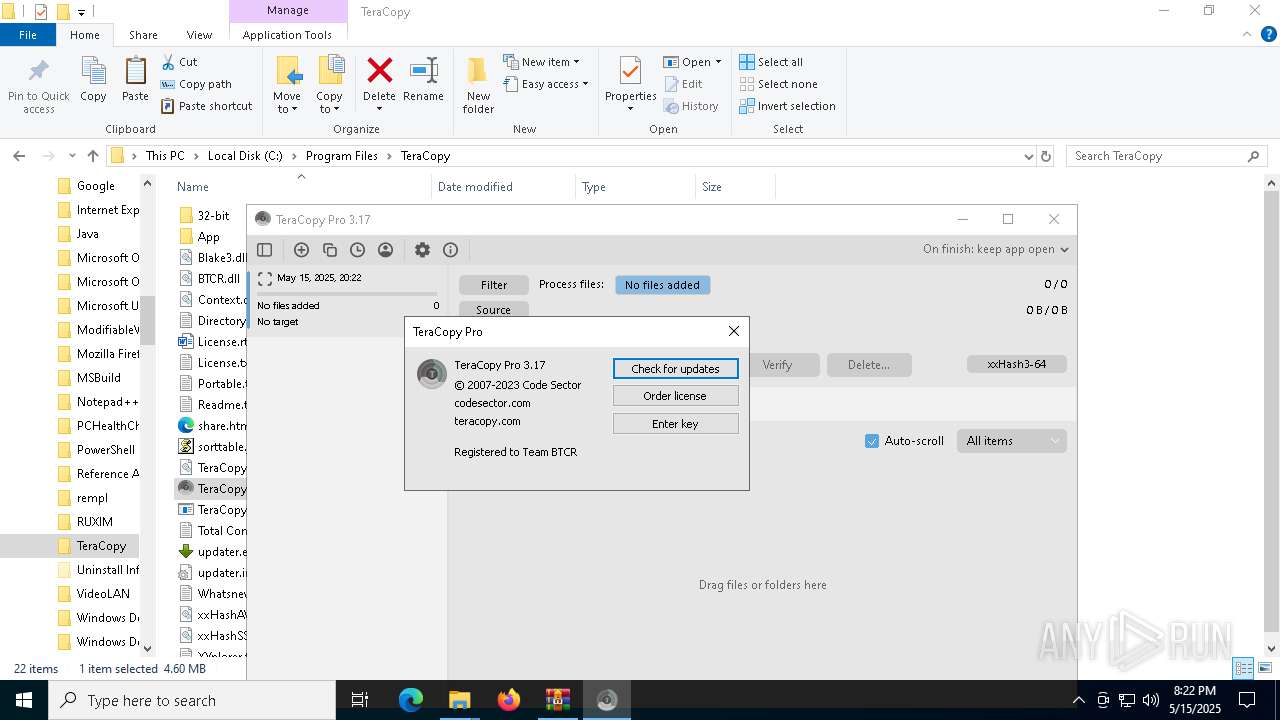
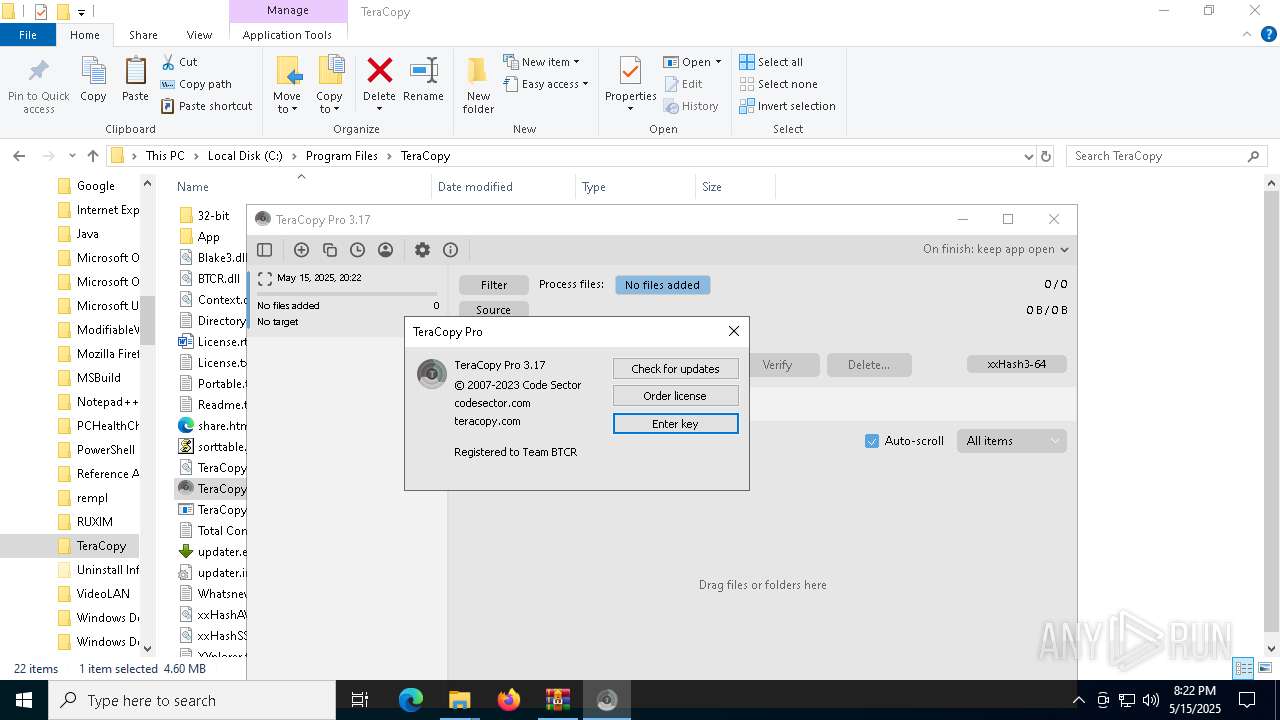
| 2192 | "C:\Program Files\TeraCopy\updater.exe" /silent | C:\Program Files\TeraCopy\updater.exe | TeraCopy.exe | ||||||||||||
User: admin Company: Code Sector Integrity Level: MEDIUM Description: updater 3.17 Exit code: 3758096401 Version: 3.17 Modules
| |||||||||||||||
| 3156 | "C:\Windows\System32\MsiExec.exe" /Y "C:\Program Files\TeraCopy\Context.dll" | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
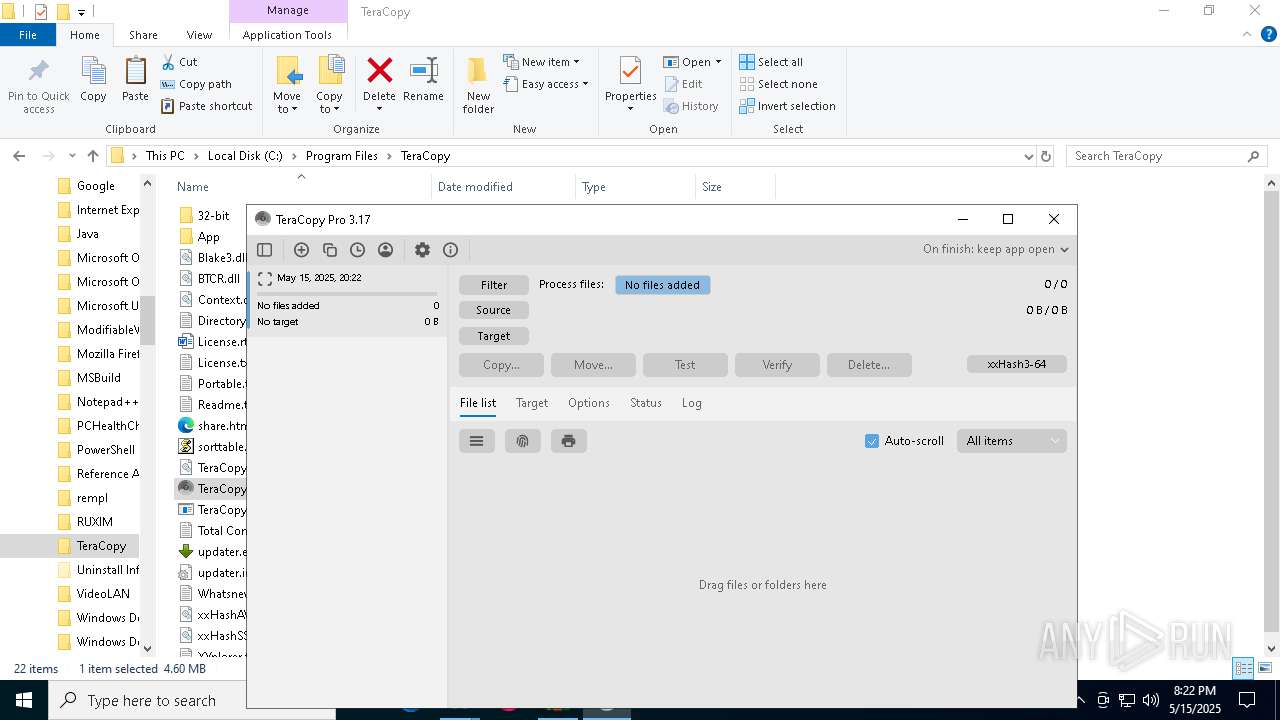
| 3884 | "C:\Program Files\TeraCopy\TeraCopy.exe" | C:\Program Files\TeraCopy\TeraCopy.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: TeraCopy Exit code: 0 Modules
| |||||||||||||||
| 4000 | "C:\Program Files\TeraCopy\updater.exe" /checknow | C:\Program Files\TeraCopy\updater.exe | TeraCopy.exe | ||||||||||||
User: admin Company: Code Sector Integrity Level: MEDIUM Description: updater 3.17 Exit code: 3758096401 Version: 3.17 Modules
| |||||||||||||||
| 4112 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | C:\WINDOWS\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4284 | "C:\Program Files\TeraCopy\TeraCopyService.exe" | C:\Program Files\TeraCopy\TeraCopyService.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: TeraCopy Exit code: 1 Version: 3.10.0.0 Modules
| |||||||||||||||
| 4380 | C:\Windows\syswow64\MsiExec.exe -Embedding 97C521BEBA084A219FAA2481B4ABF33A | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
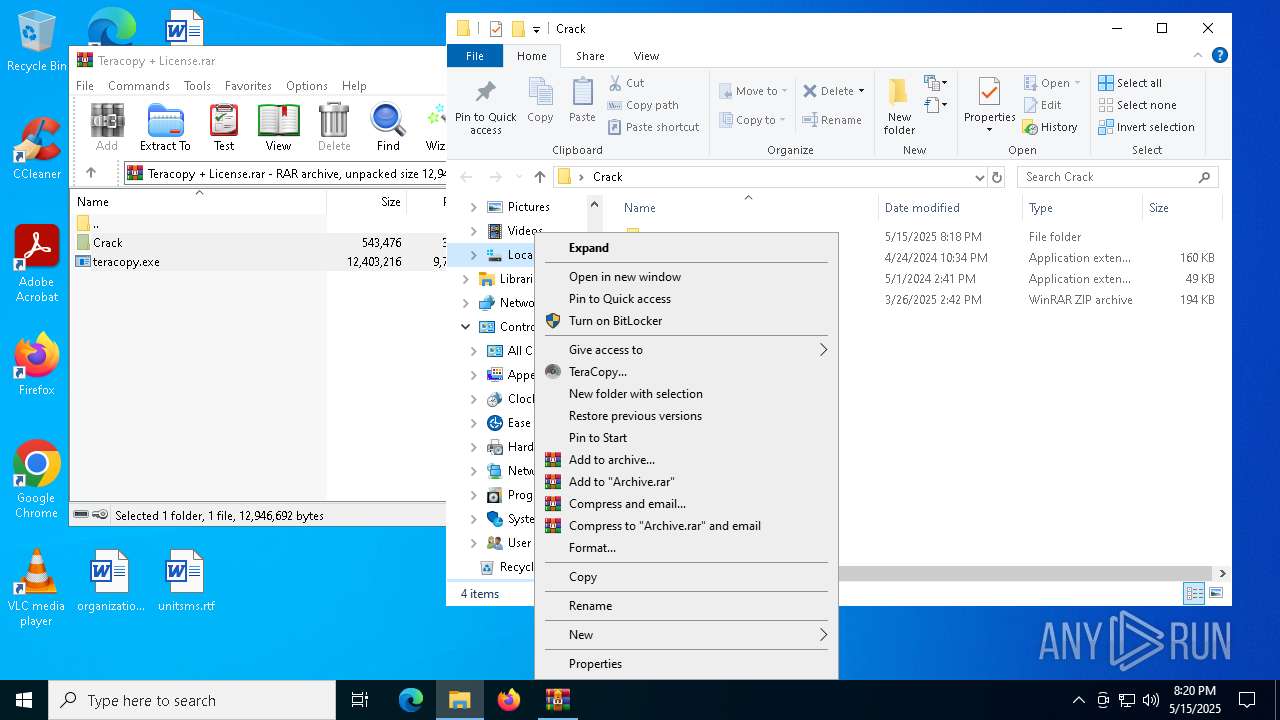
| 4652 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Teracopy + License.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
30 380
Read events
29 817
Write events
536
Delete events
27
Modification events
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Teracopy + License.rar | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5204) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000000C52EEC4D6C5DB0154140000DC170000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5204) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000000C52EEC4D6C5DB0154140000DC170000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
64
Suspicious files
159
Text files
154
Unknown types
0
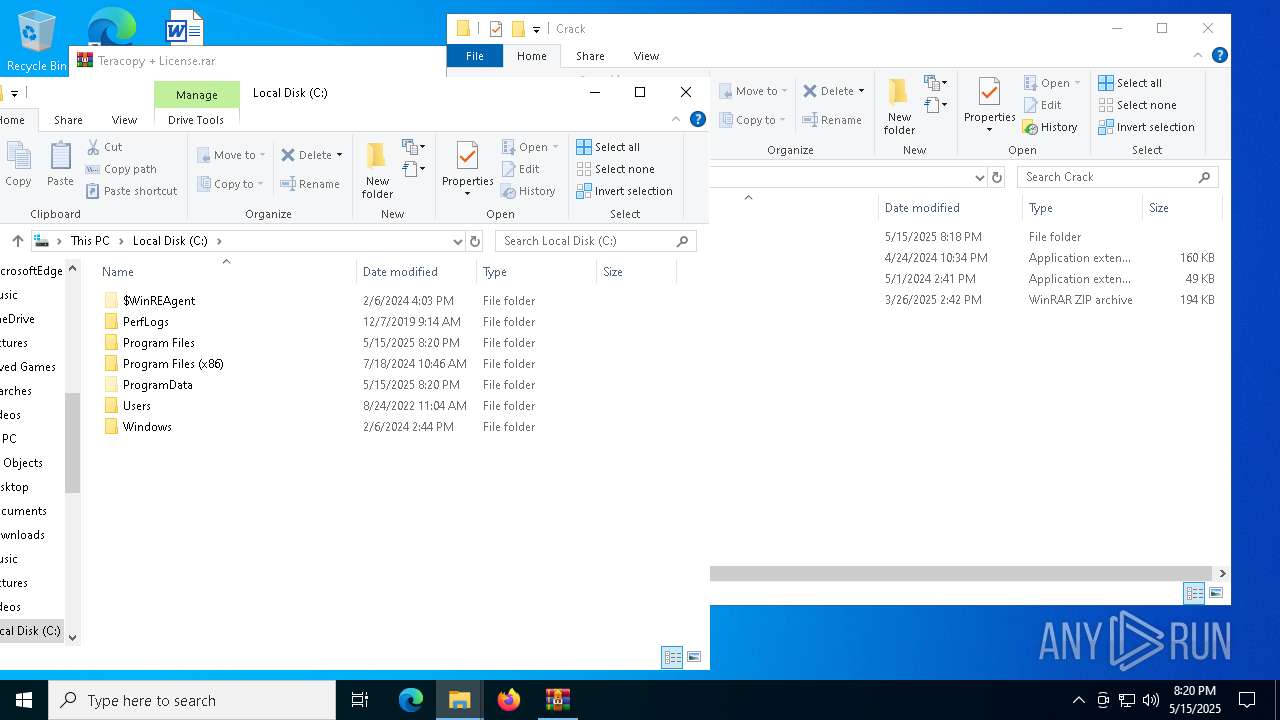
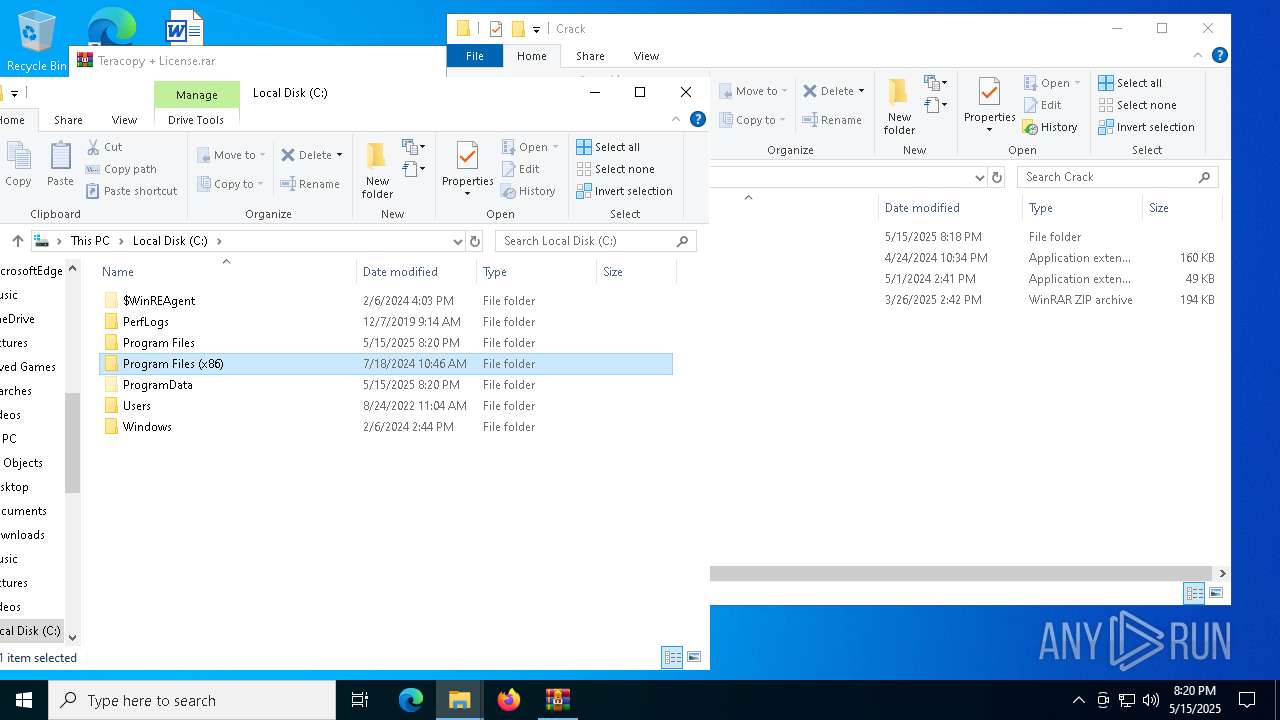
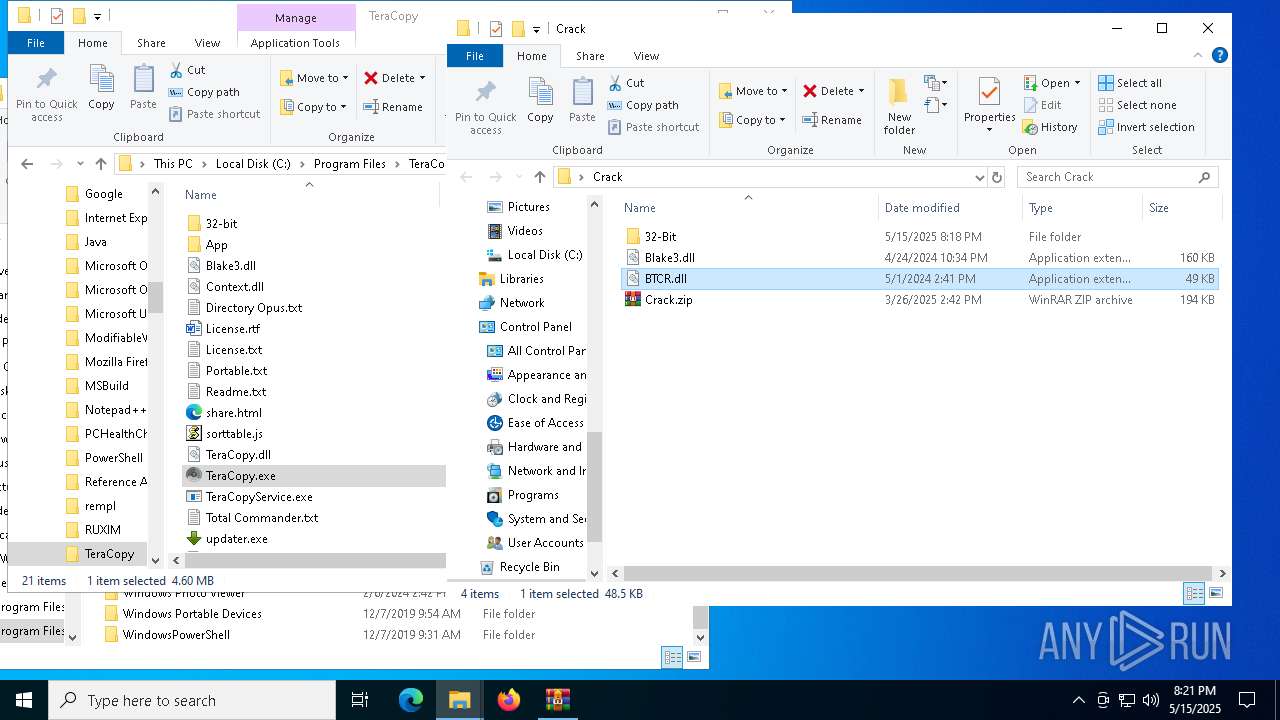
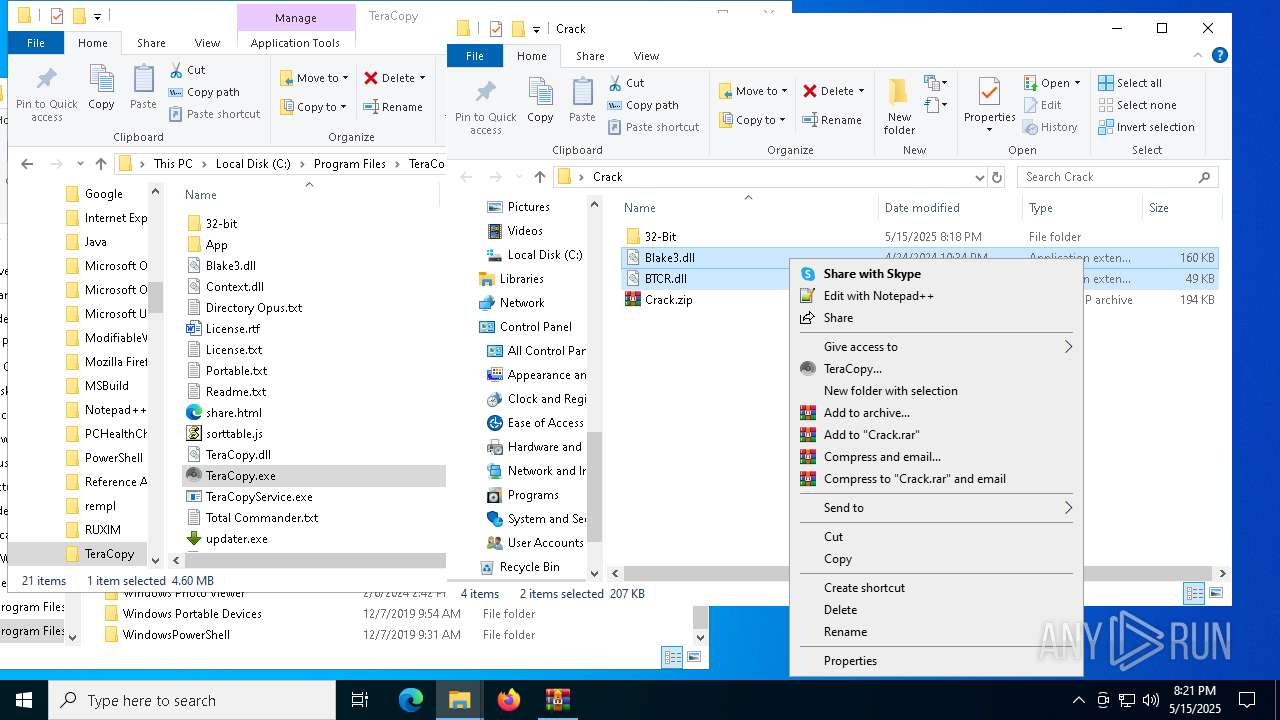
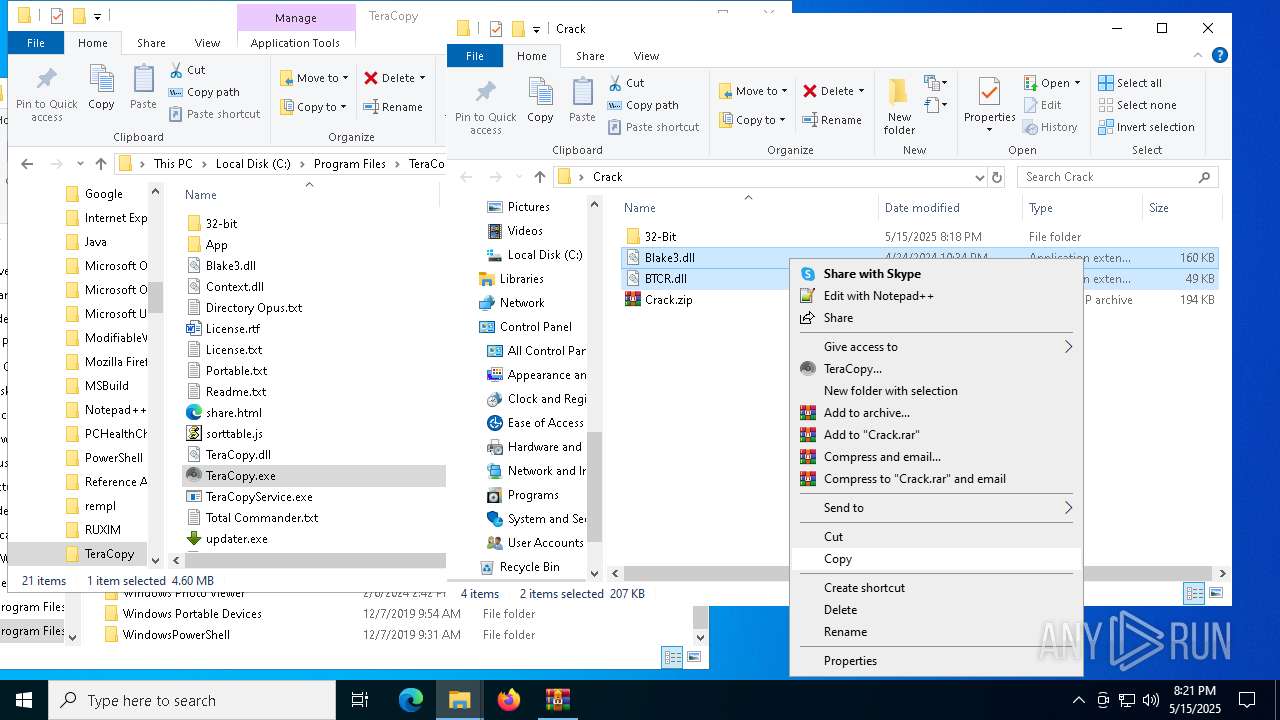
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5972 | teracopy.exe | C:\Users\admin\AppData\Roaming\Code Sector\TeraCopy 3.17\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 5972 | teracopy.exe | C:\Users\admin\AppData\Roaming\Code Sector\TeraCopy 3.17\install\53E6B13\TeraCopy.msi | — | |
MD5:— | SHA256:— | |||
| 5972 | teracopy.exe | C:\Users\admin\AppData\Roaming\Code Sector\TeraCopy 3.17\install\53E6B13\TeraCopy.x64.msi | — | |
MD5:— | SHA256:— | |||
| 5972 | teracopy.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\05DDC6AA91765AACACDB0A5F96DF8199 | binary | |
MD5:CFD4CBCC1EC599BA2A4ECBB381F06414 | SHA256:AA3009B9E4F3683BC0659896DB1CE3BAE4D066D5463B1463F330E00571B96125 | |||
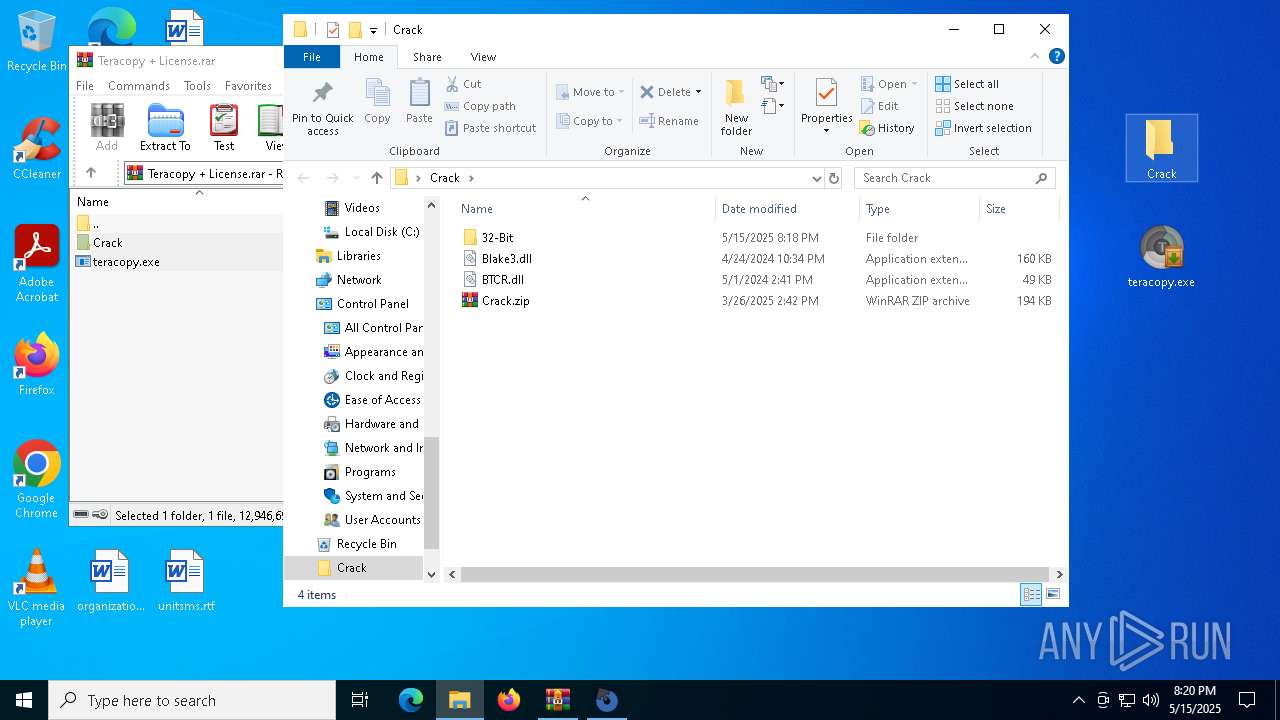
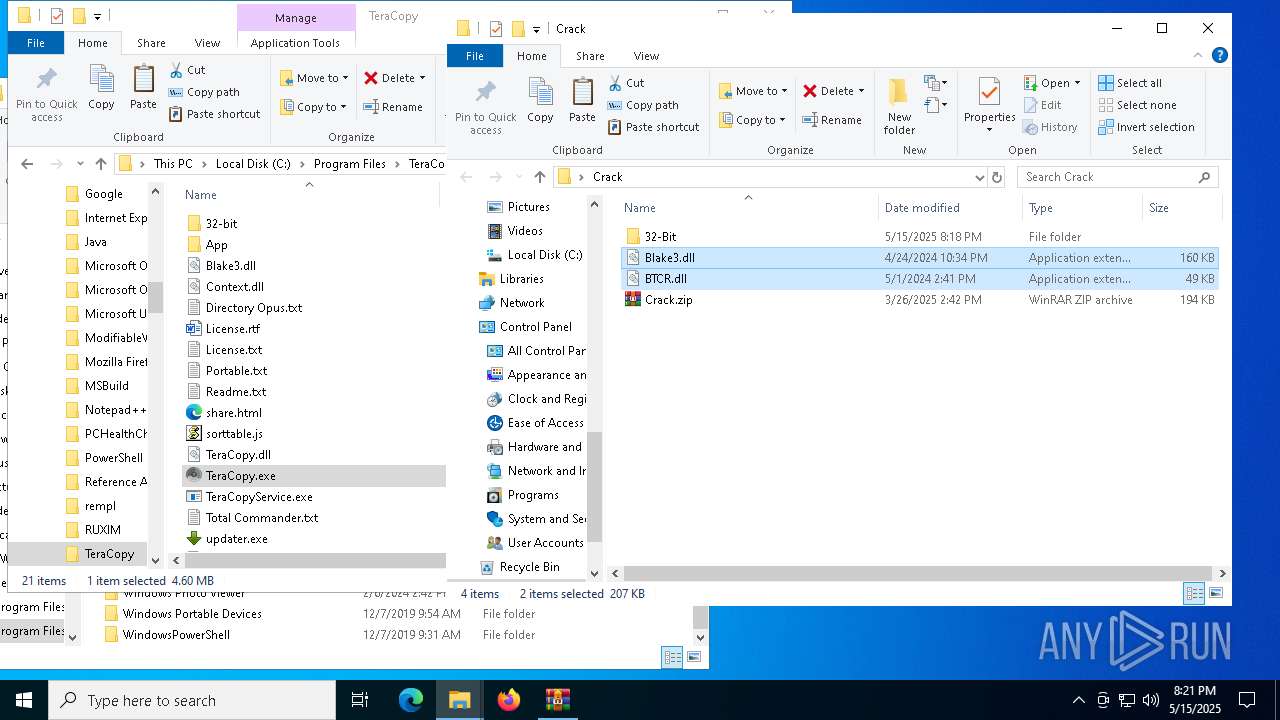
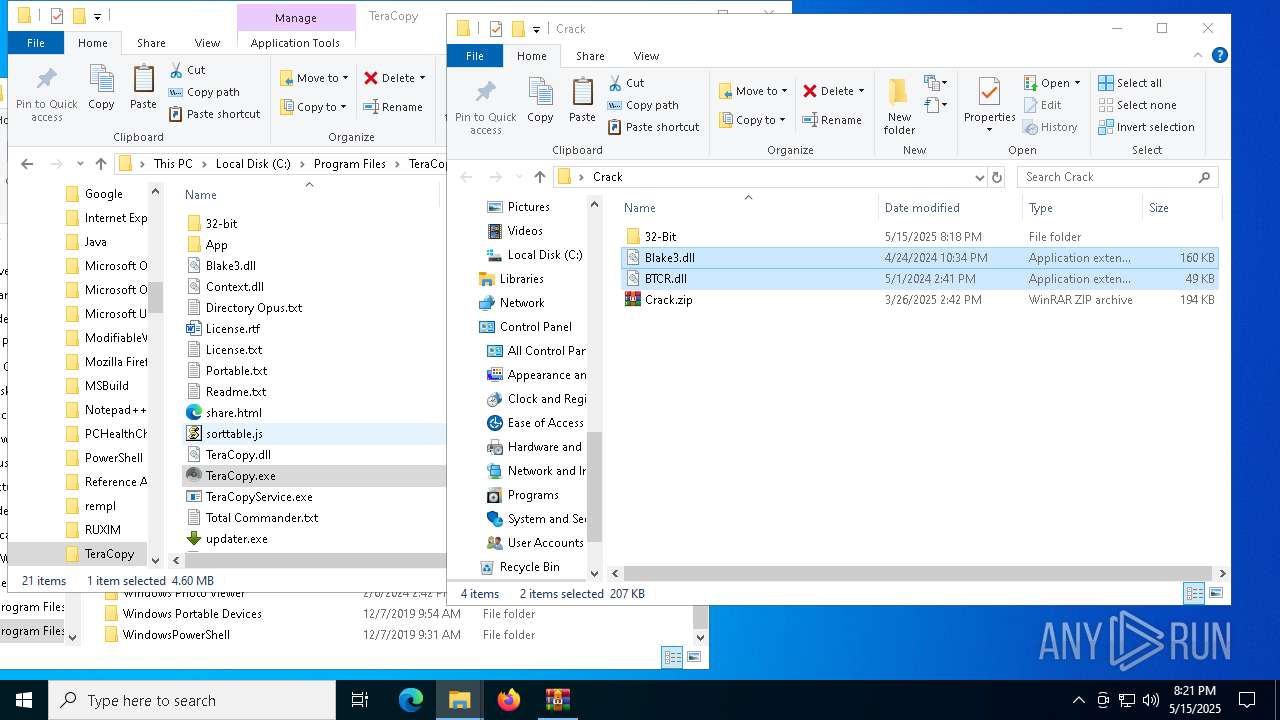
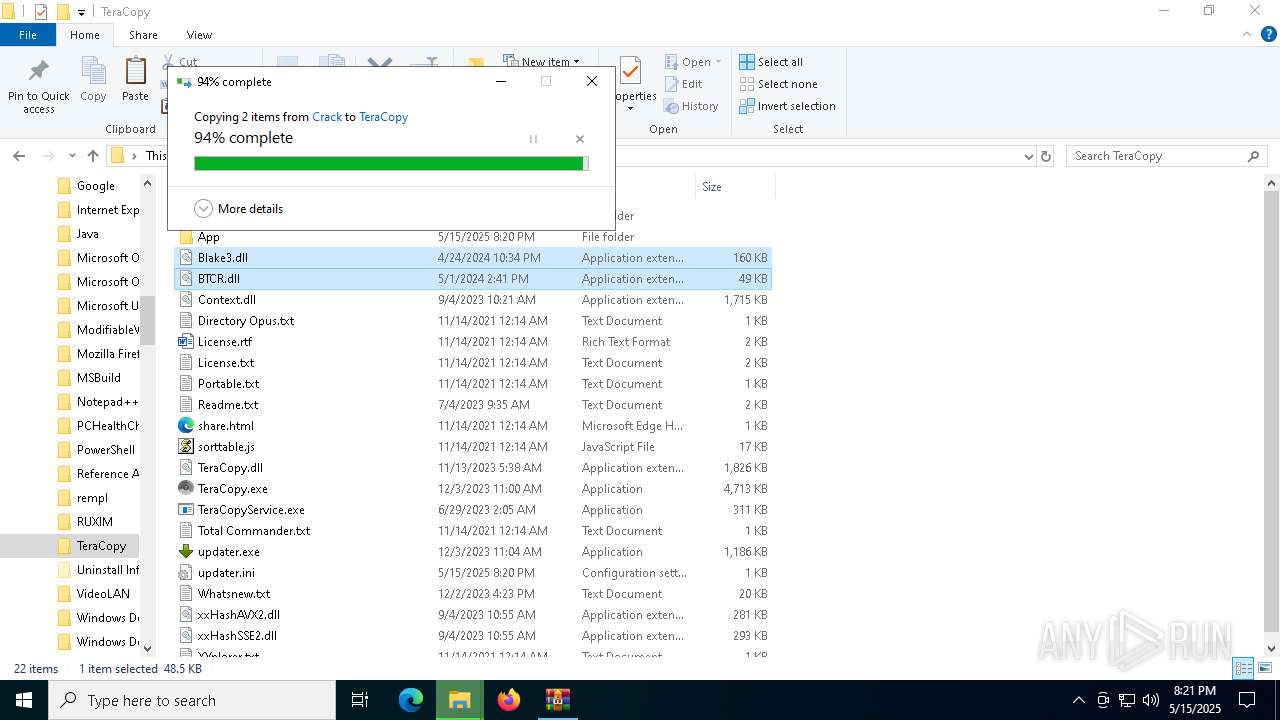
| 4652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4652.21302\teracopy.exe | executable | |
MD5:D704E453E065A23ED414927D9B203086 | SHA256:AC03DB52BB68A013D3A8BF4DB703EC11976FA1D0AA557EB988E3F926A26656CF | |||
| 4652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4652.21302\Crack\BTCR.dll | executable | |
MD5:B15EE48317737C1DAE6AE7895BDAF131 | SHA256:5DD7B69808EC6DC2341A9056466E30936EA82D56514D2A5DEA3CEFB8517E67AB | |||
| 4652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4652.21302\Crack\32-Bit\Blake3.dll | executable | |
MD5:26DA963DB1601F6518C15F7BEAF8CD9F | SHA256:3E8381CBA2DB07AE9A7D298E9A9E56473FDA9060AE531CCA3352CD7E7D779506 | |||
| 4652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4652.21302\Crack\Blake3.dll | executable | |
MD5:D463CDFB8A433D9F916CF3BC6FD82109 | SHA256:230BD8803629AABE80BF4B4A109787B330CA1C8200B6A04CCD91D5F480C5446E | |||
| 5972 | teracopy.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\18E6B4A57A6BC7EC9B861CDF2D6D0D02_C3B142D2C5374581DC2FDFFDEDBDEDDB | binary | |
MD5:DF1344D33B4A55BD172EE52038CE7C89 | SHA256:905D7A7FB36826C01CB594E00A2D4C1BF239339048BF7DF350BCE0D4283B4E0A | |||
| 5972 | teracopy.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F48443C99DFCF2F4044889332EC438A8_82CF301050F40867111B6DC0F0038E2D | binary | |
MD5:F3014CE5E4F24036D29E32CEEA939D1D | SHA256:DEF723CCCBAD81FA30C5F59210568F02FAAEC896876B8C7CB9028D9DFD36C33A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
44
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.192:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5972 | teracopy.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
5972 | teracopy.exe | GET | 200 | 142.250.186.35:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
5972 | teracopy.exe | GET | 200 | 142.250.186.35:80 | http://o.pki.goog/s/wr3/PW0/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQSq0i5t2Pafi2Gw9uzwnc7KTctWgQUx4H1%2FY6I2QA8TWOiUDEkoM4j%2FiMCED1tgY7O1fHJEF8dpX3pDpo%3D | unknown | — | — | whitelisted |
5972 | teracopy.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
5972 | teracopy.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEGIdbQxSAZ47kHkVIIkhHAo%3D | unknown | — | — | whitelisted |
5972 | teracopy.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQVD%2BnGf79Hpedv3mhy6uKMVZkPCQQUDyrLIIcouOxvSK4rVKYpqhekzQwCEQDG1n8v3OsBZV0hg%2FBJyvbo | unknown | — | — | whitelisted |
6752 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.192:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5972 | teracopy.exe | 216.239.34.21:443 | codesector.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
codesector.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
c.pki.goog |
| whitelisted |