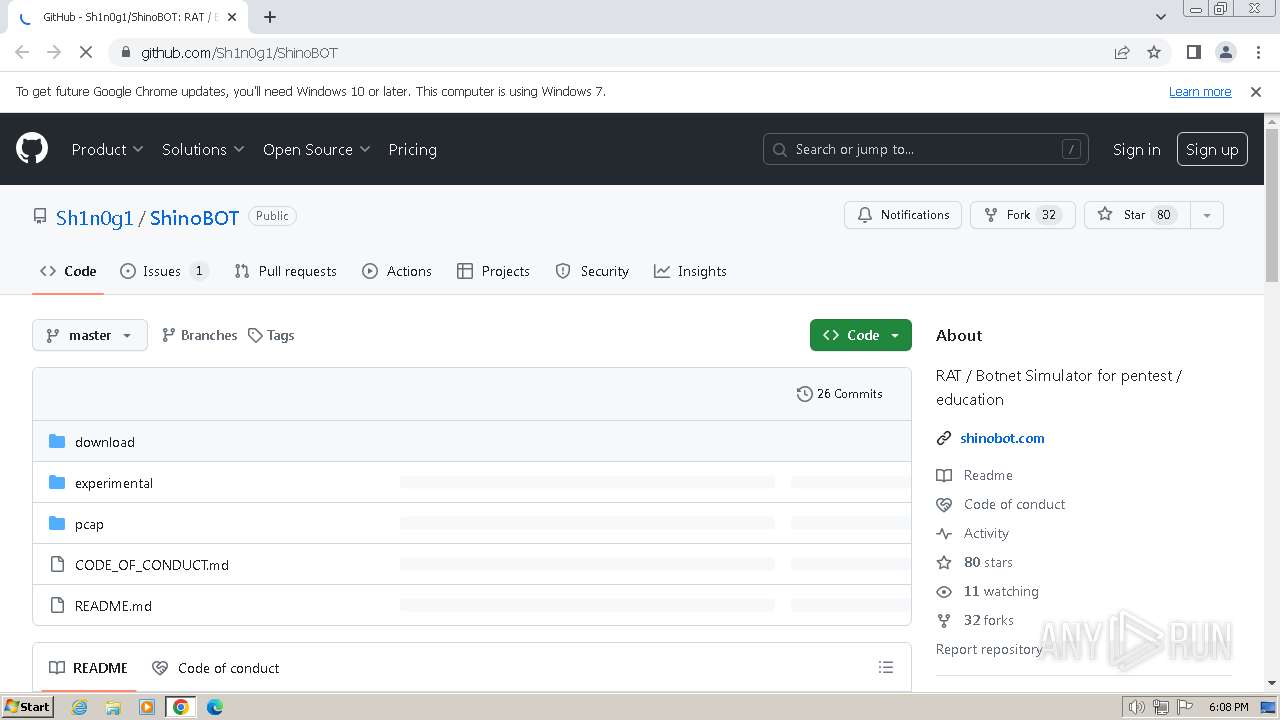
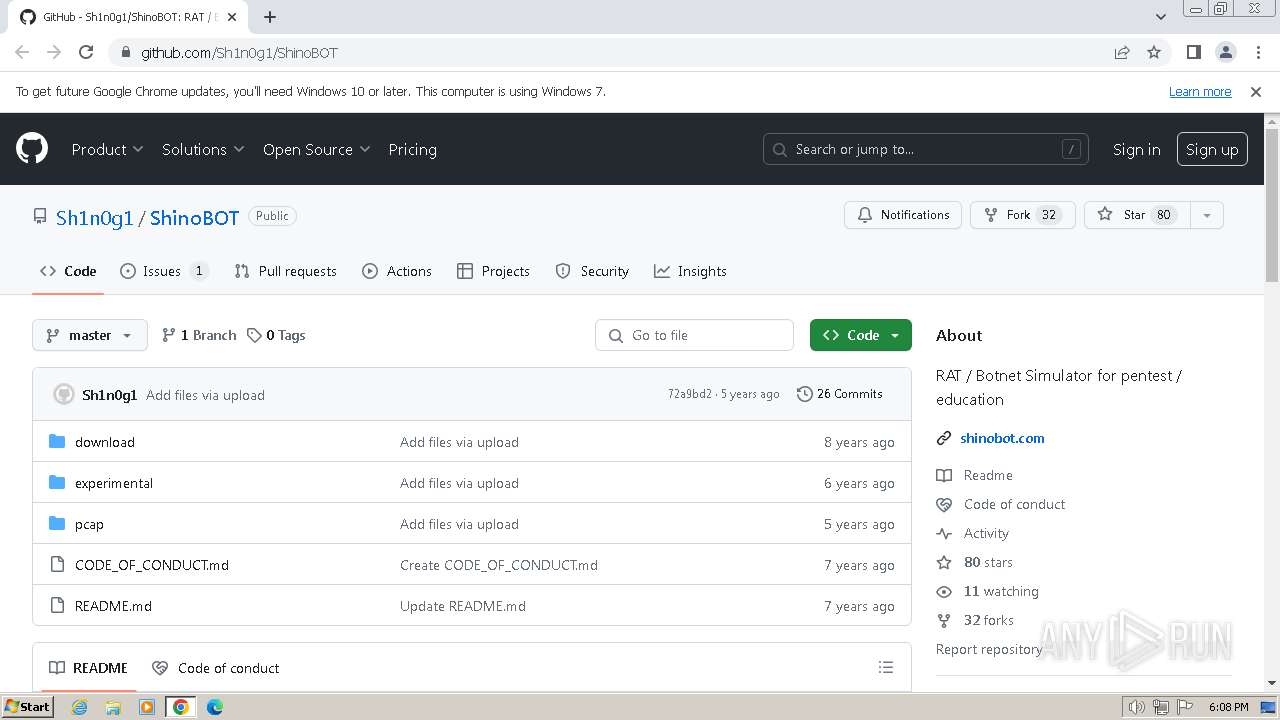
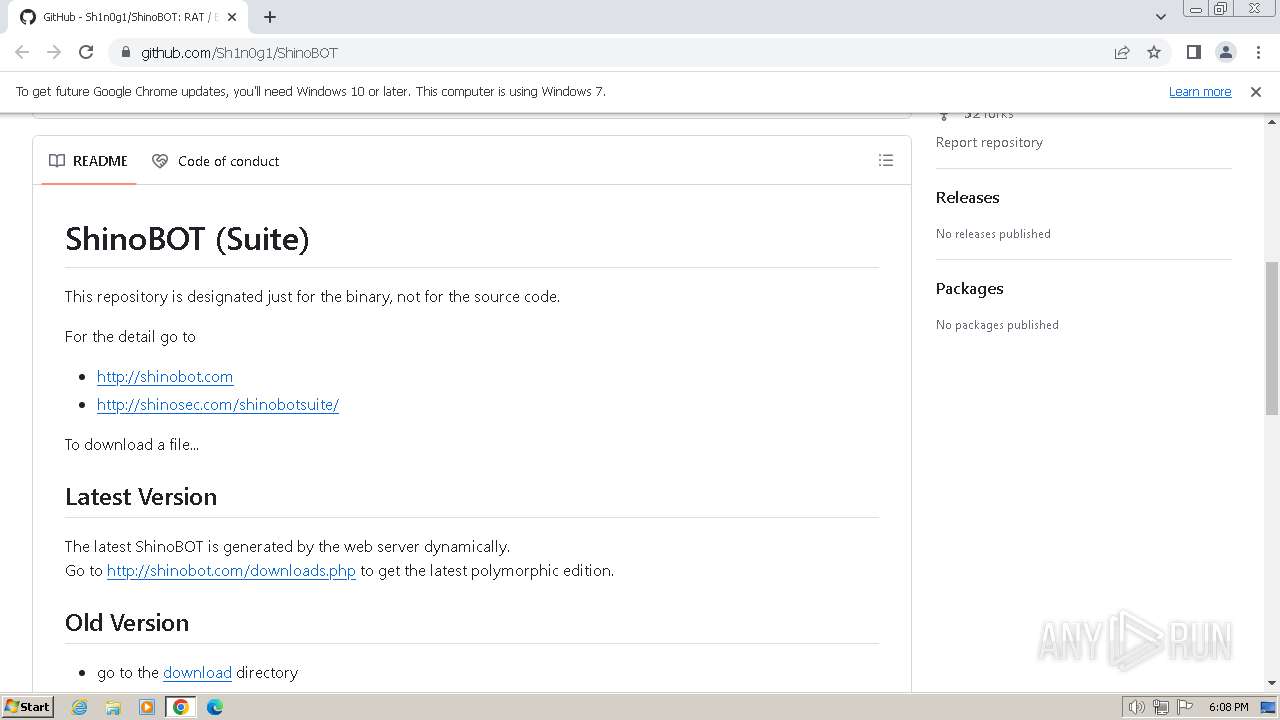
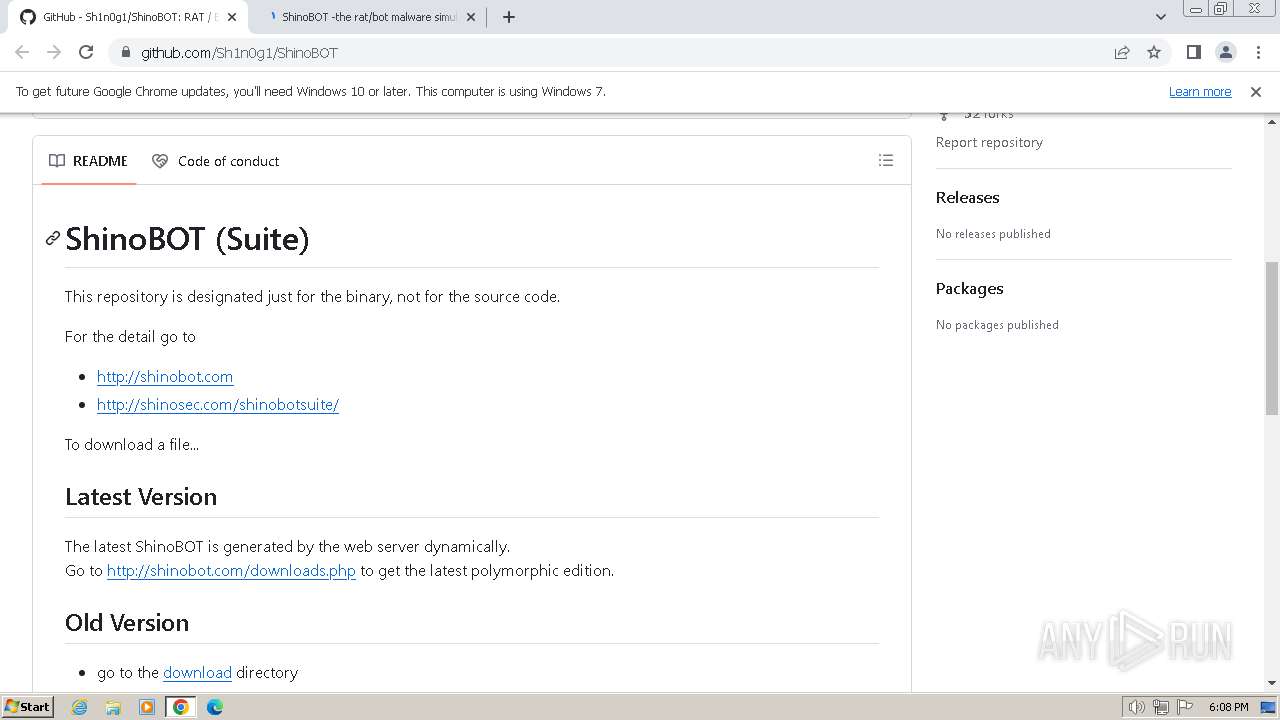
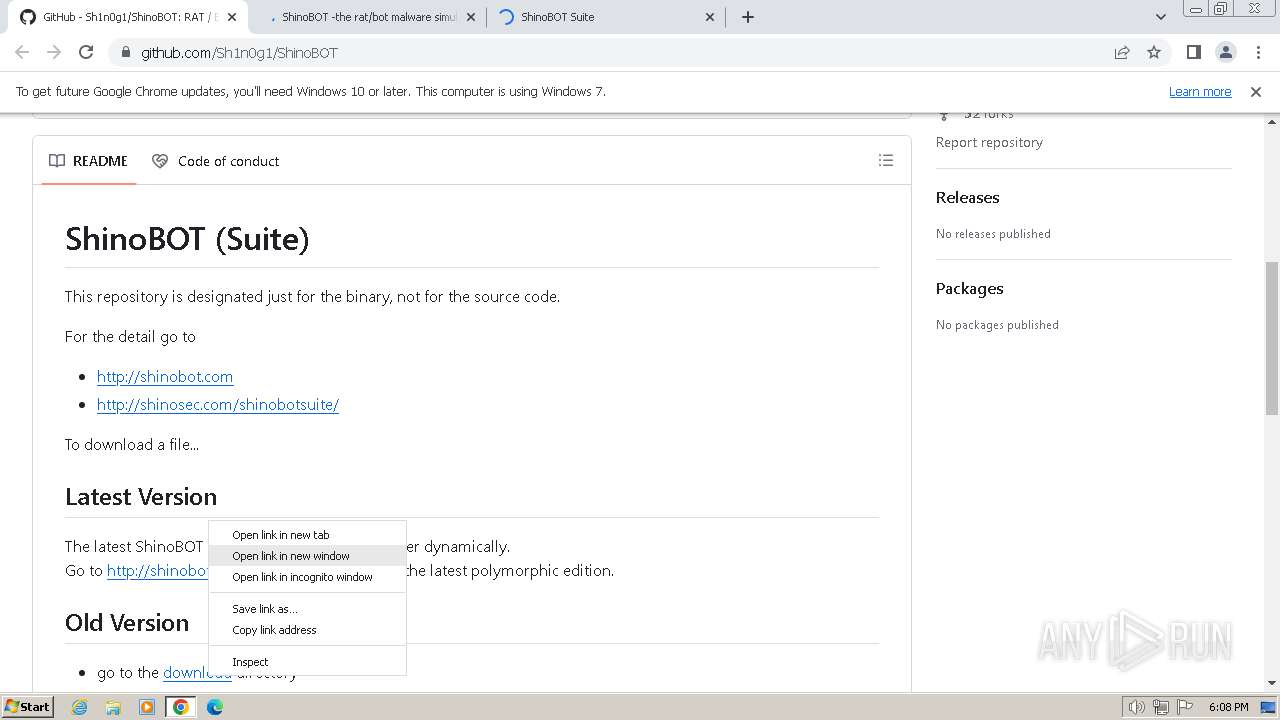
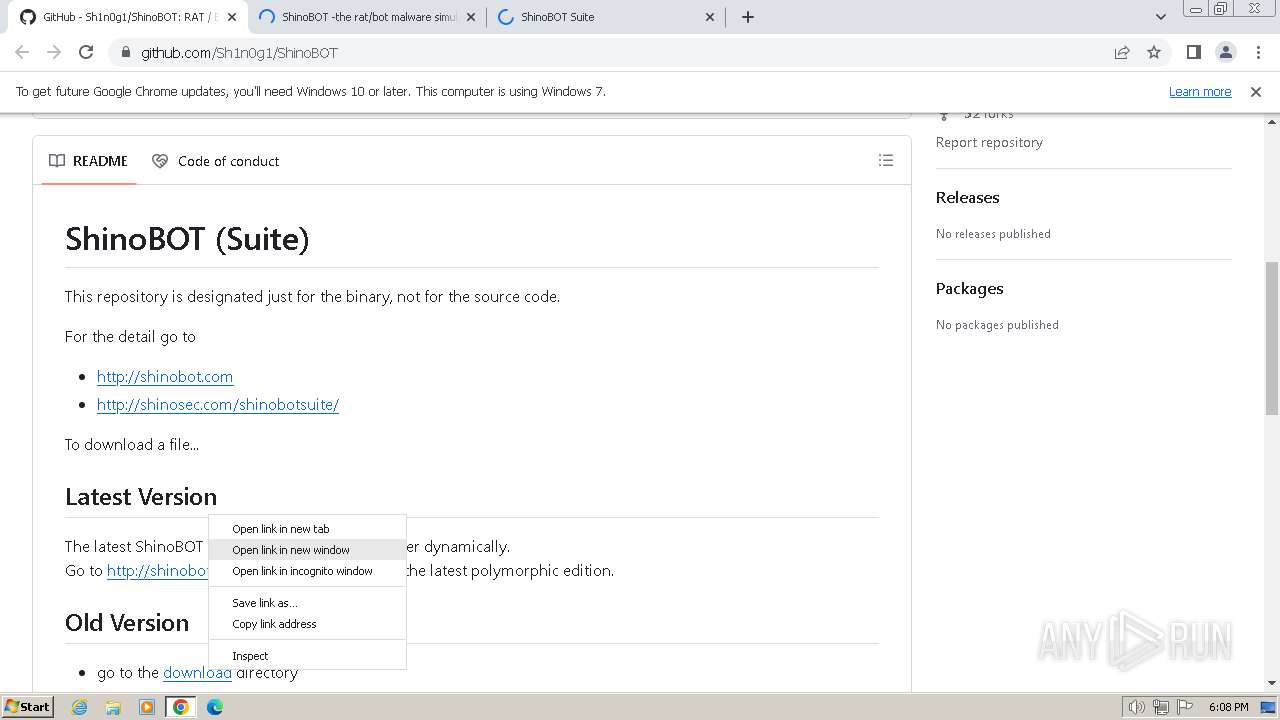
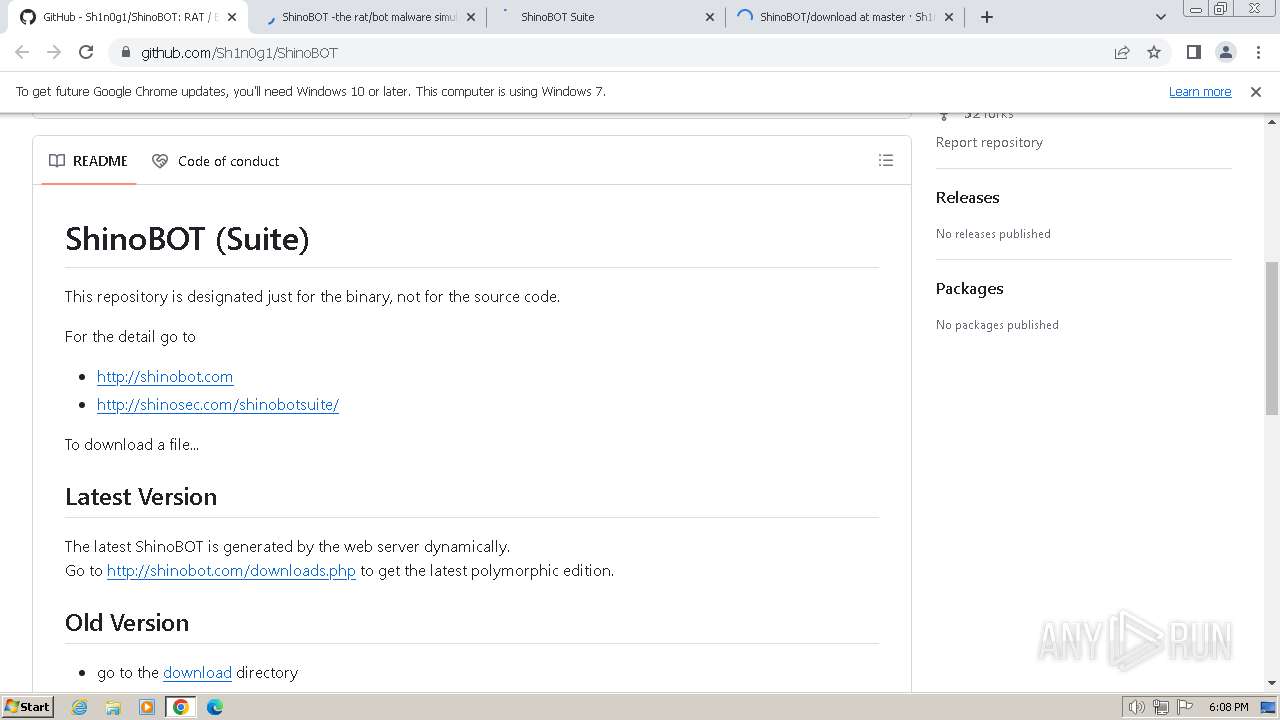
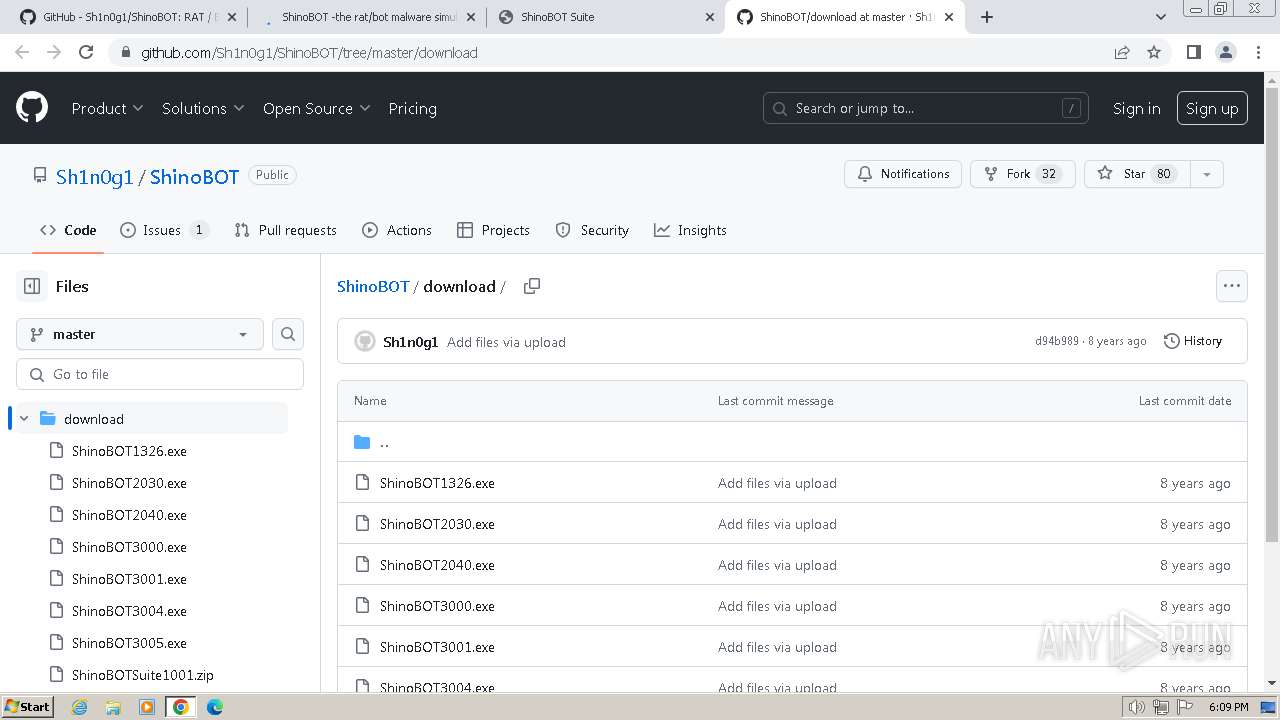
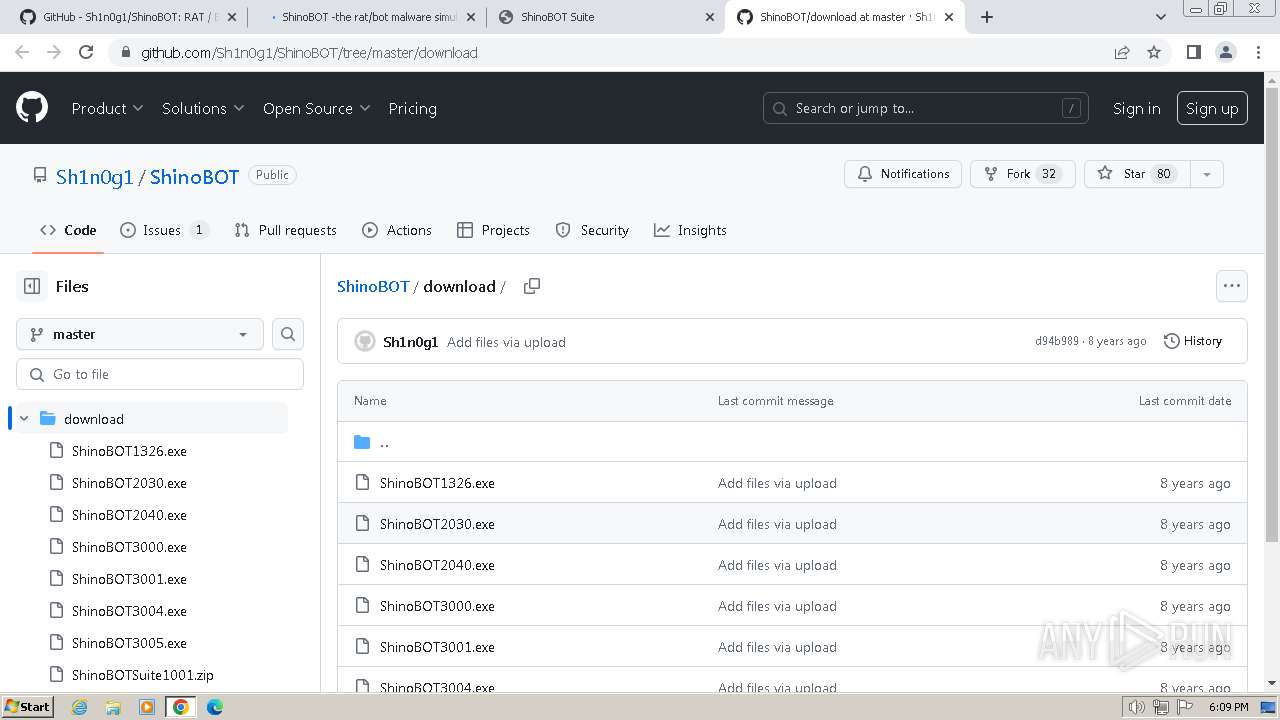
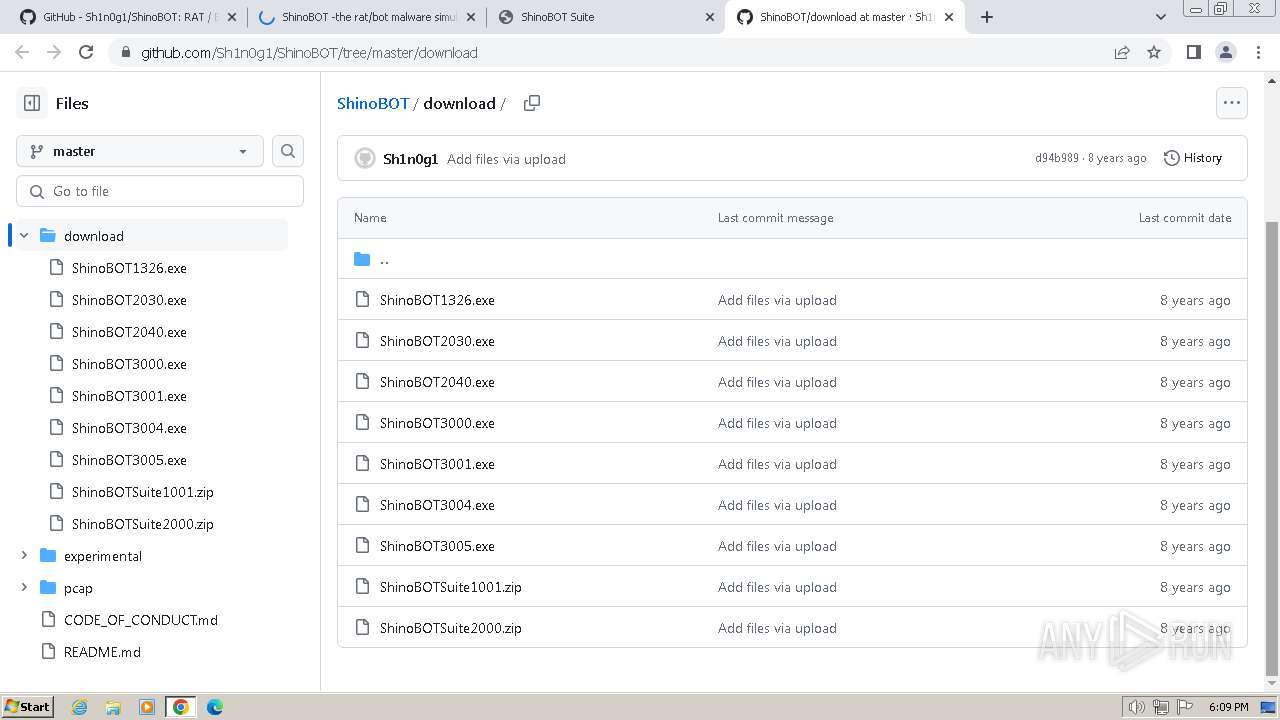
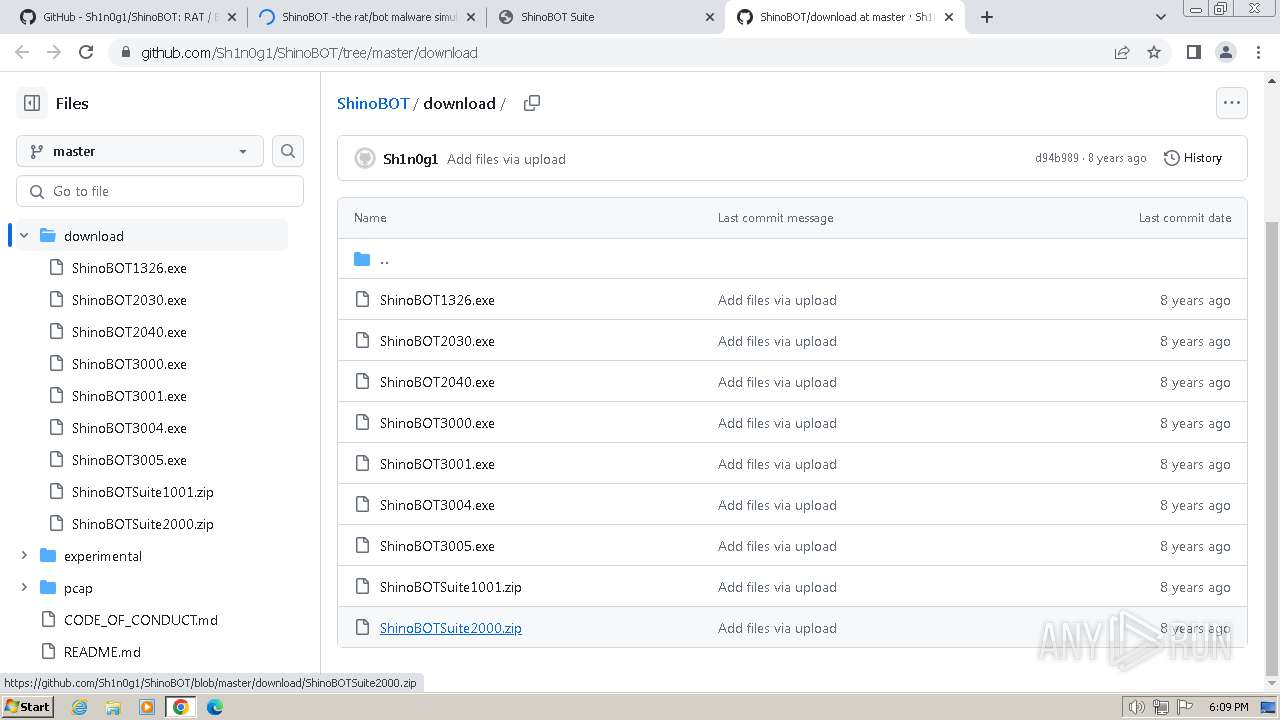
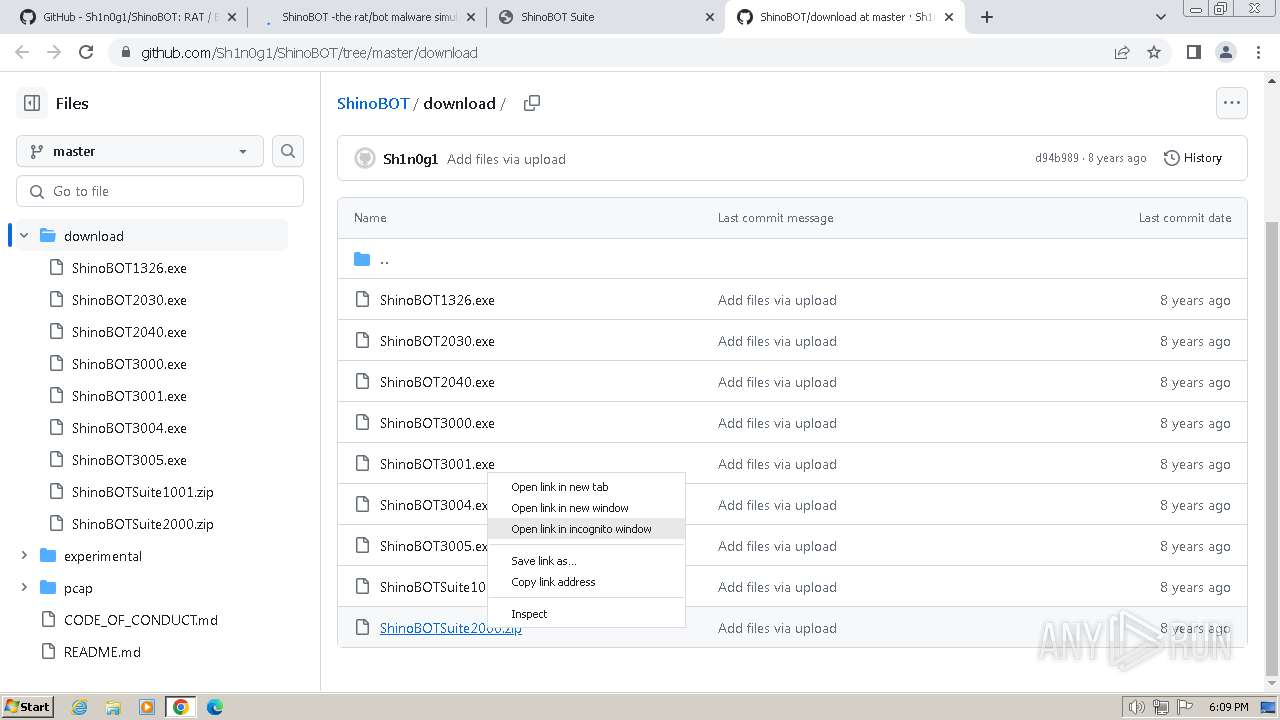
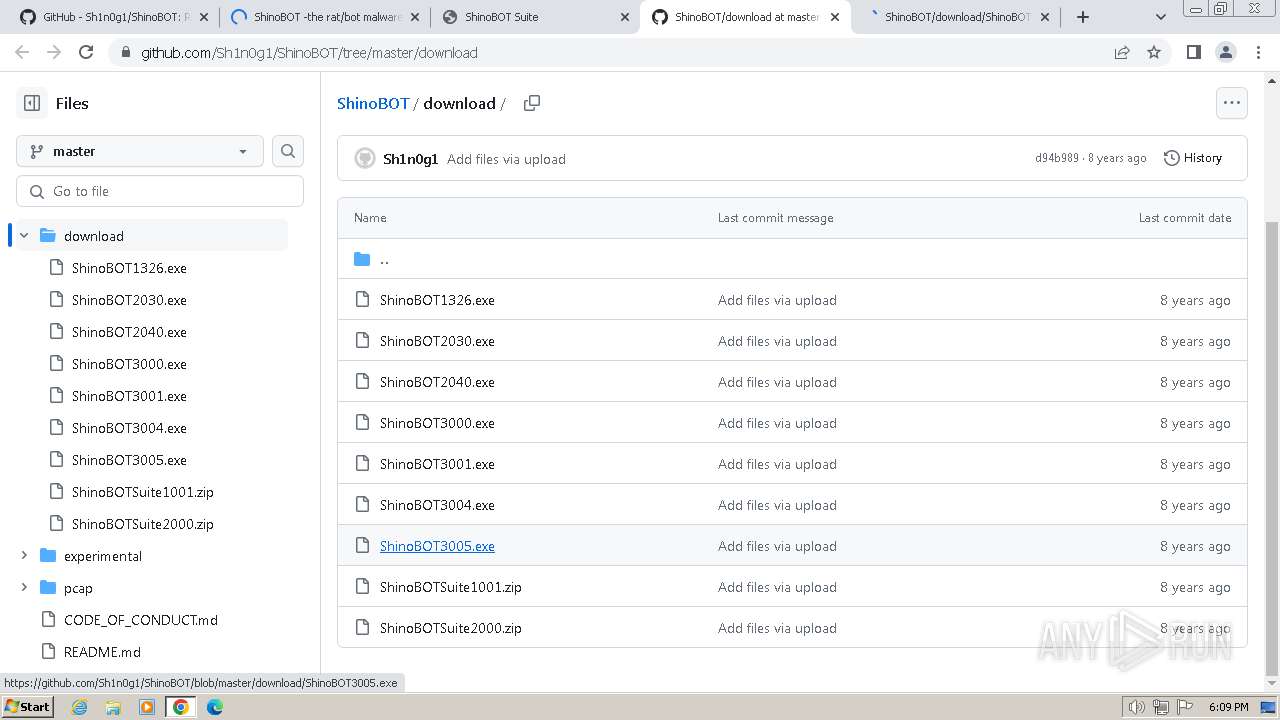
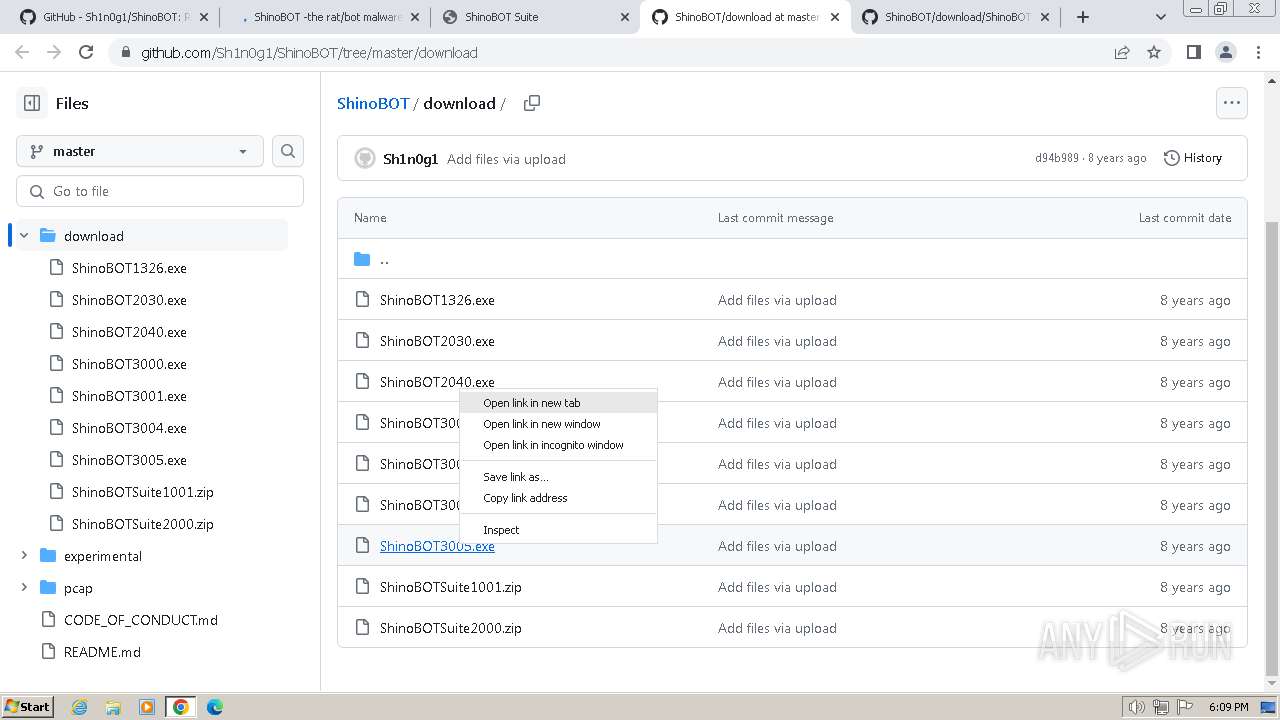
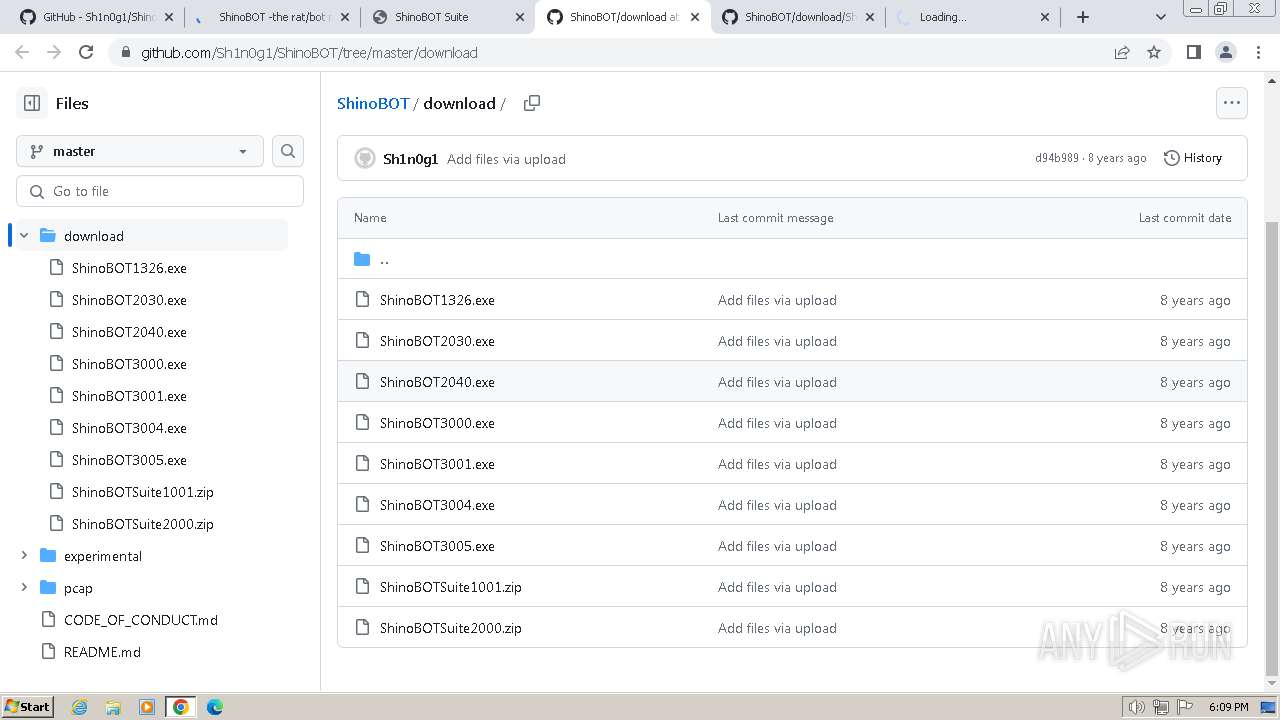
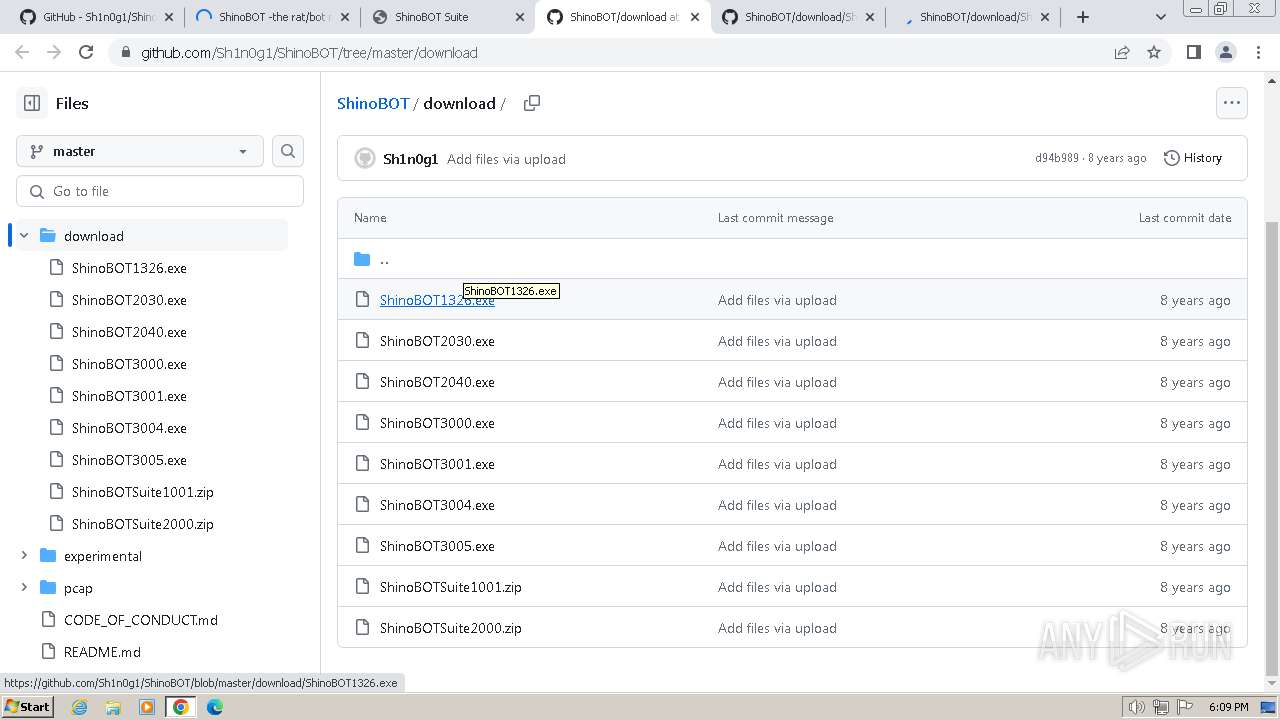
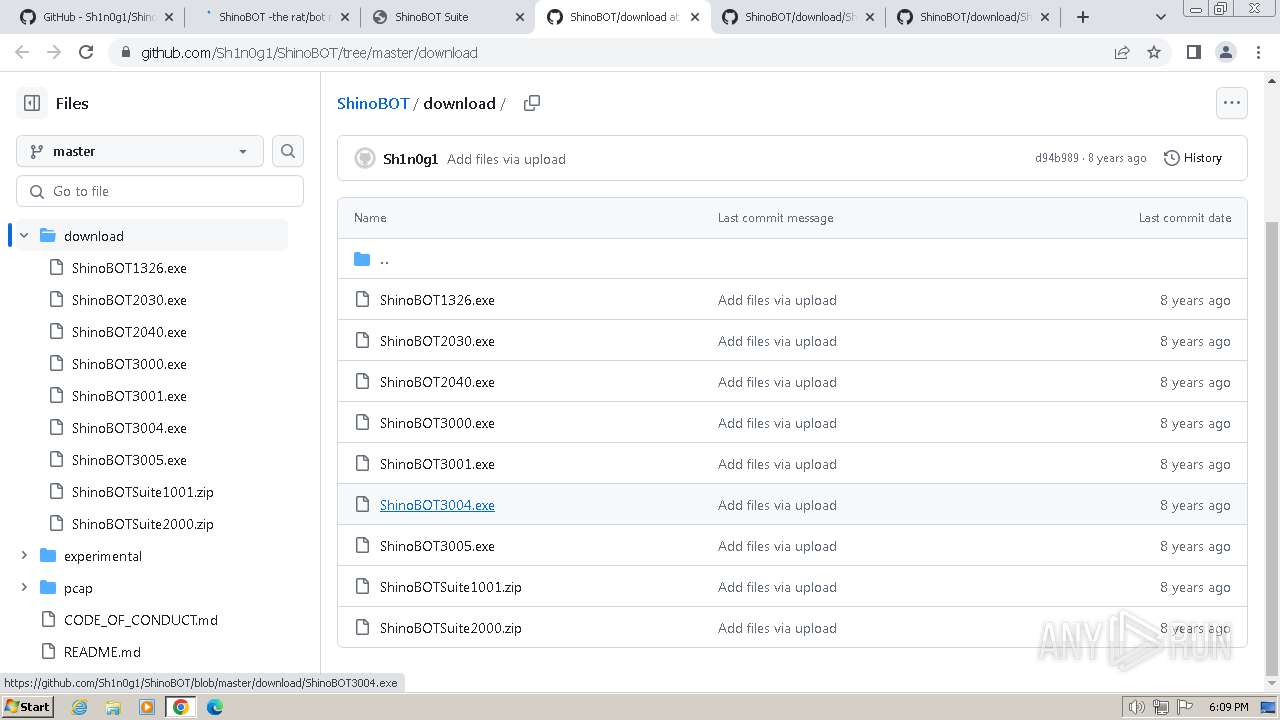
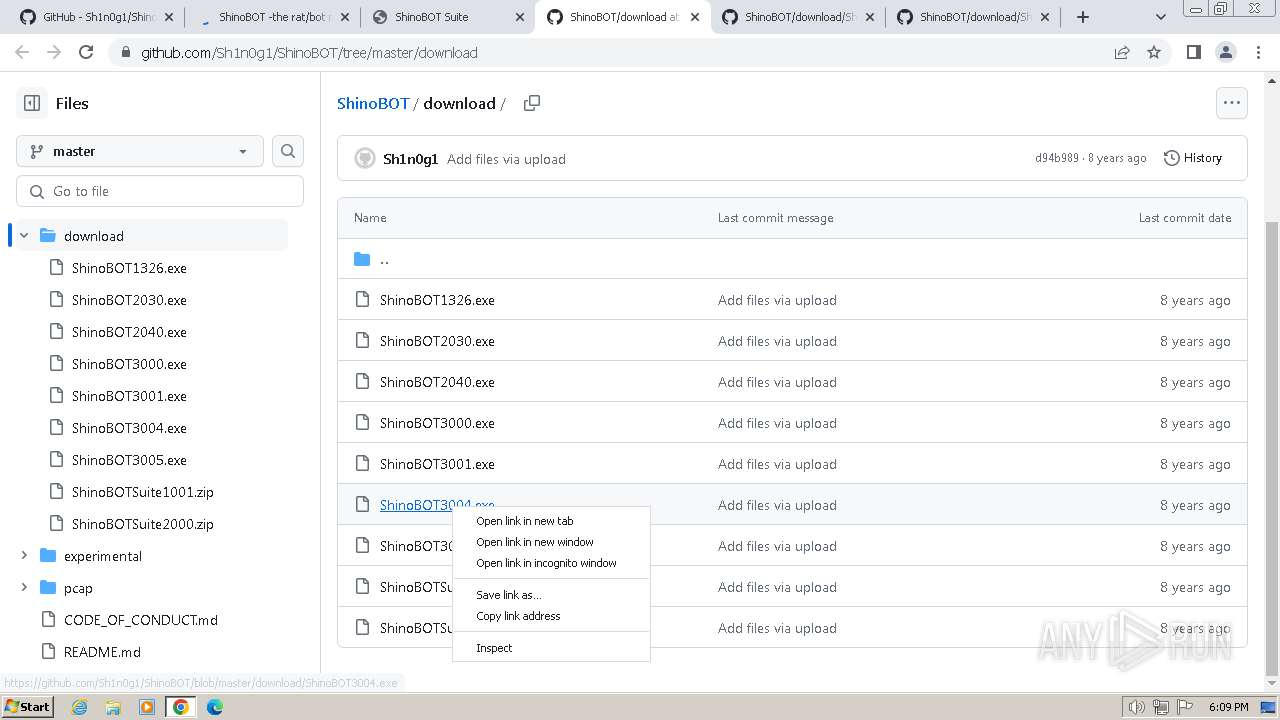
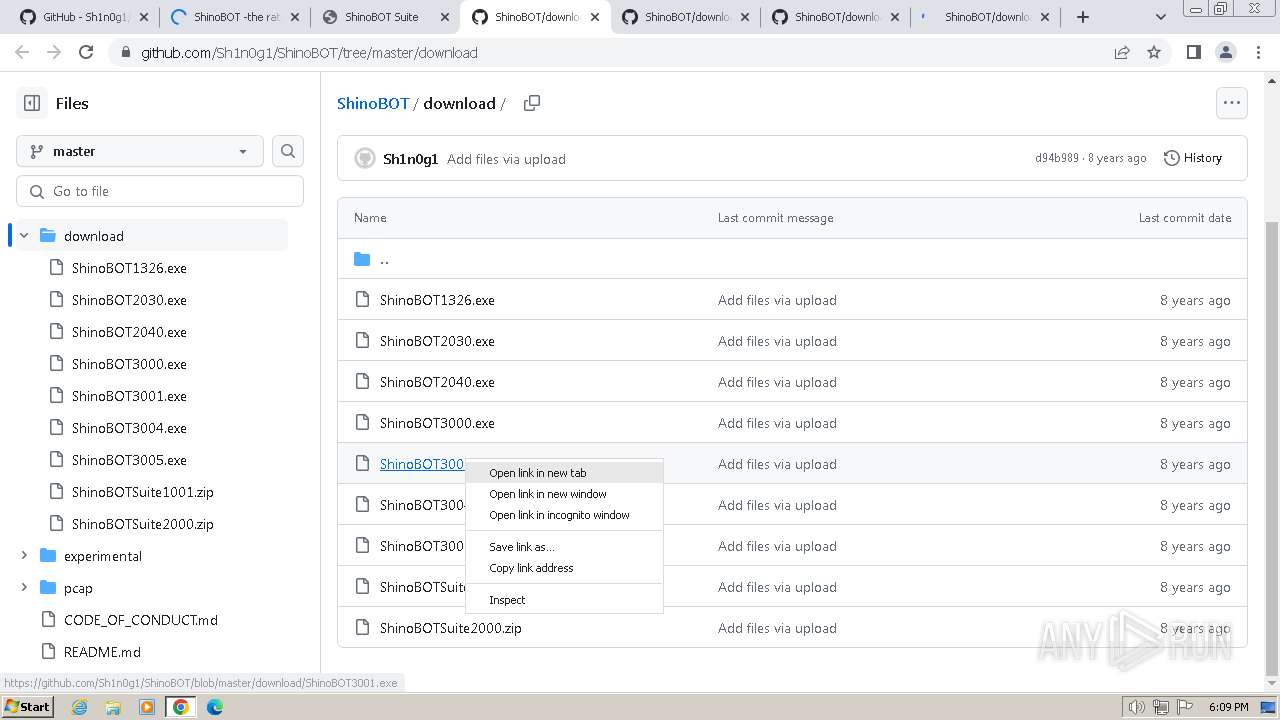
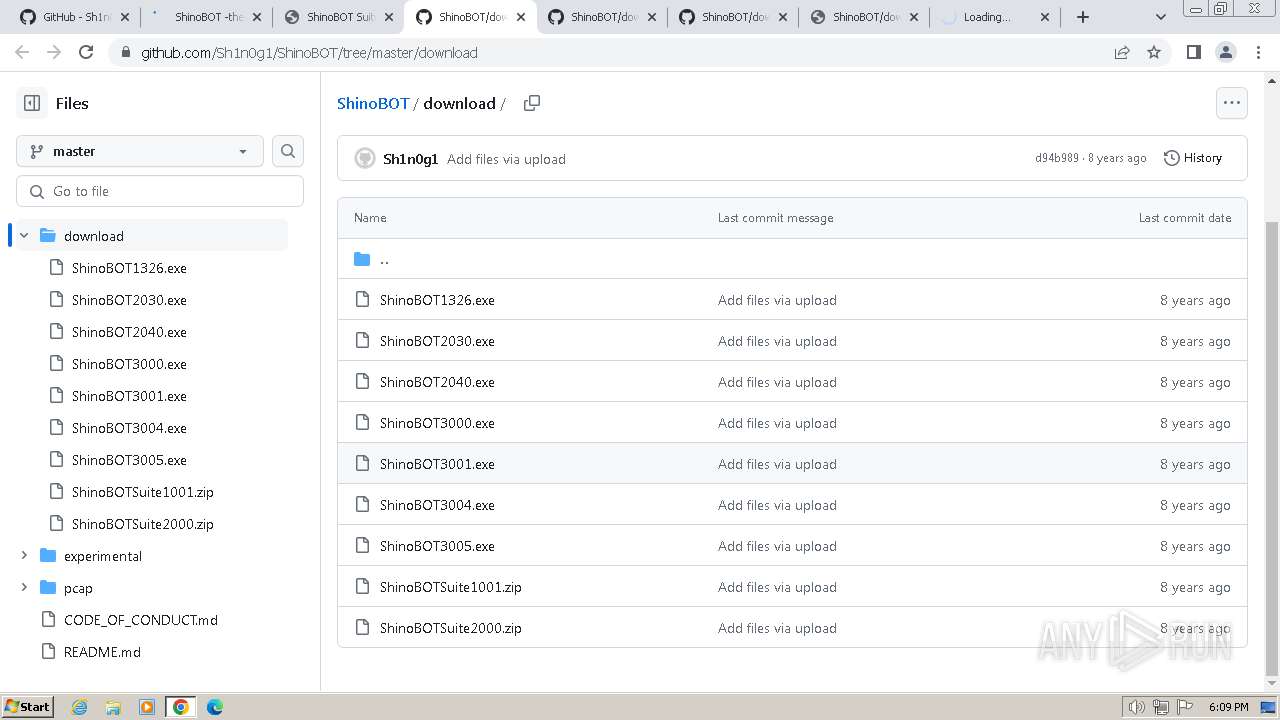
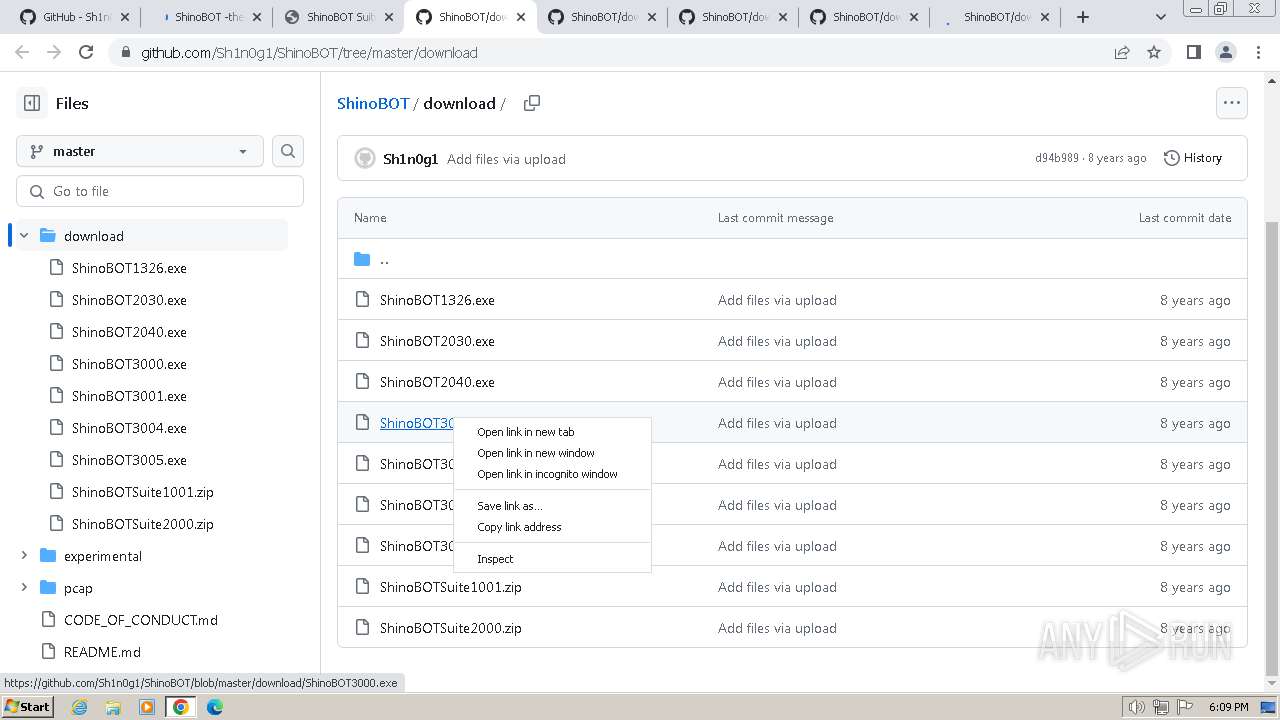
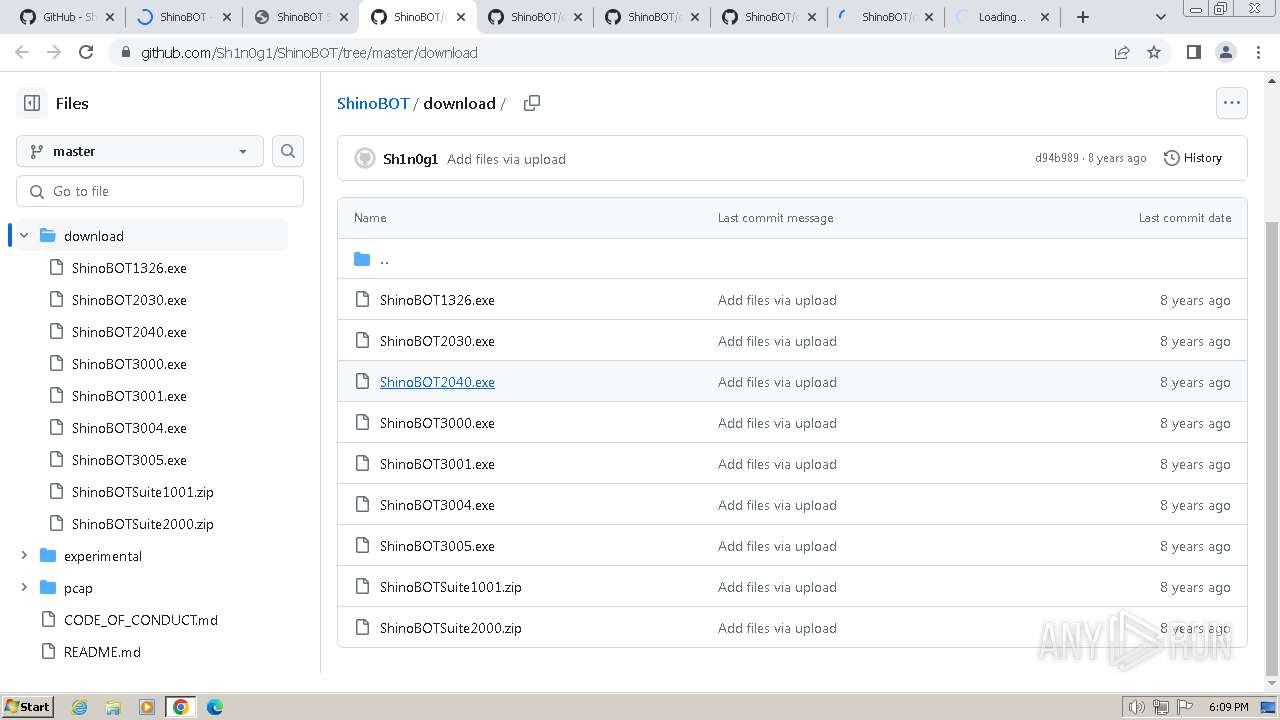
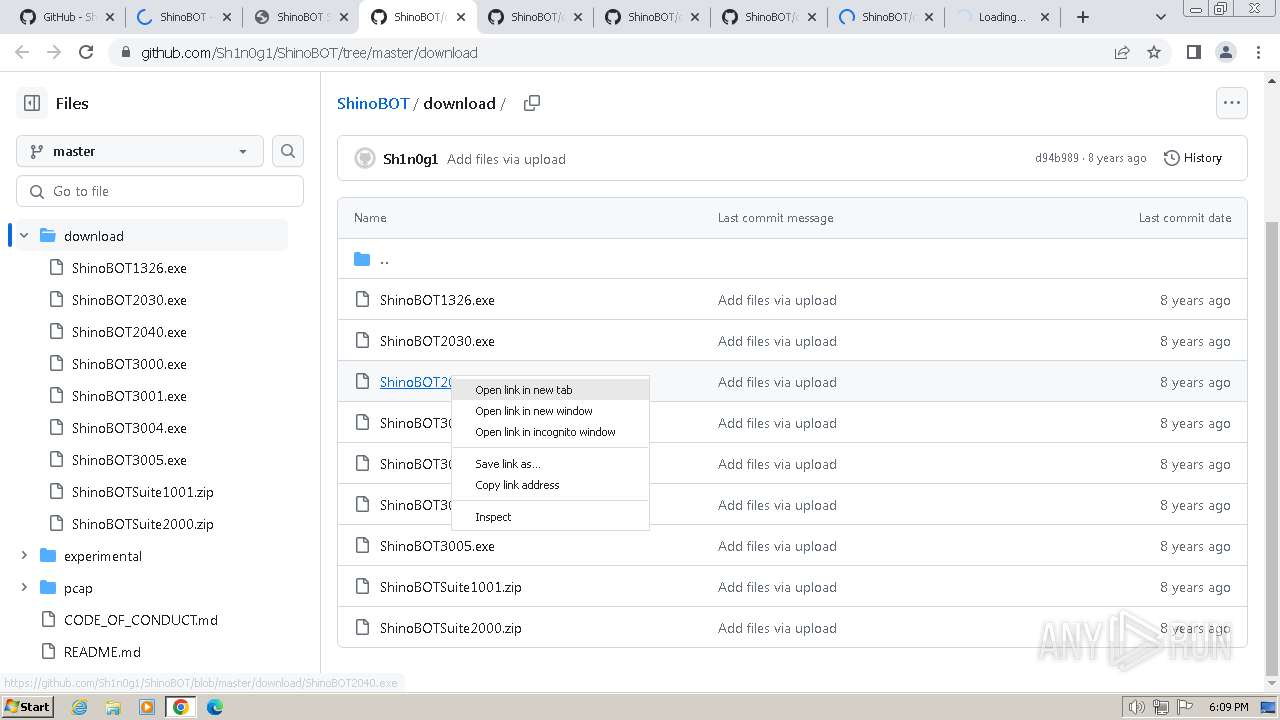
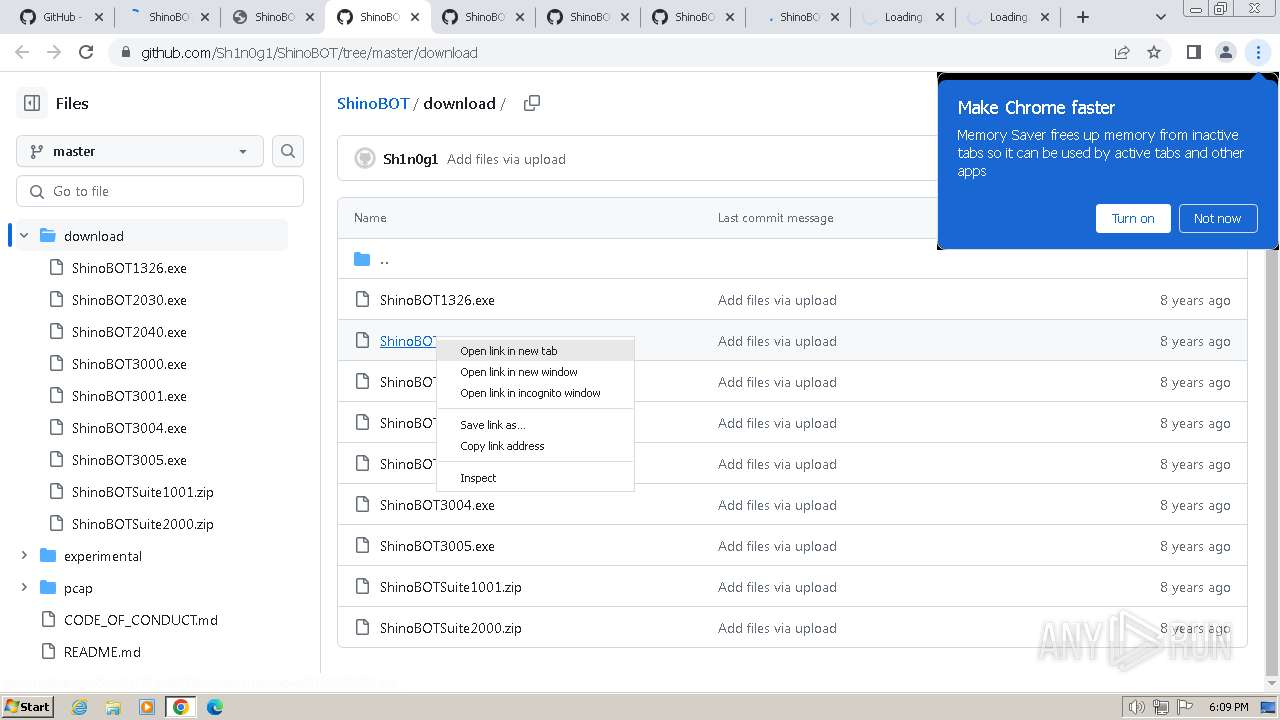
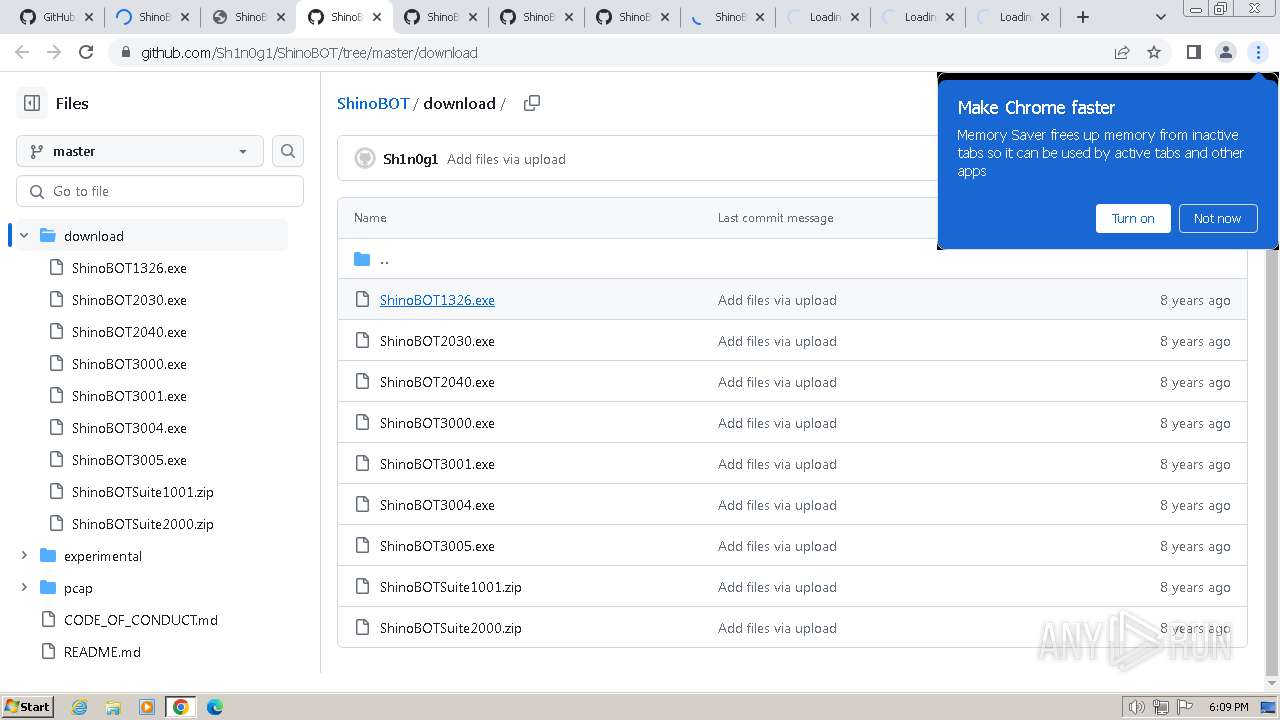
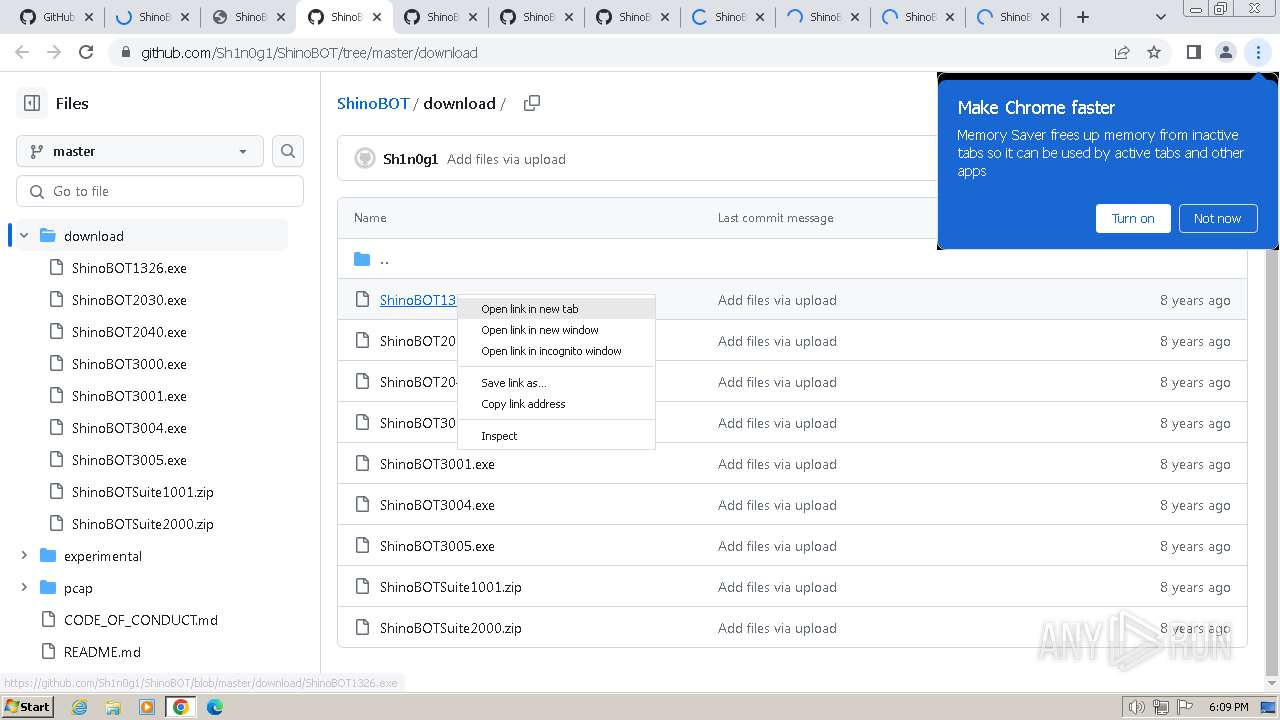
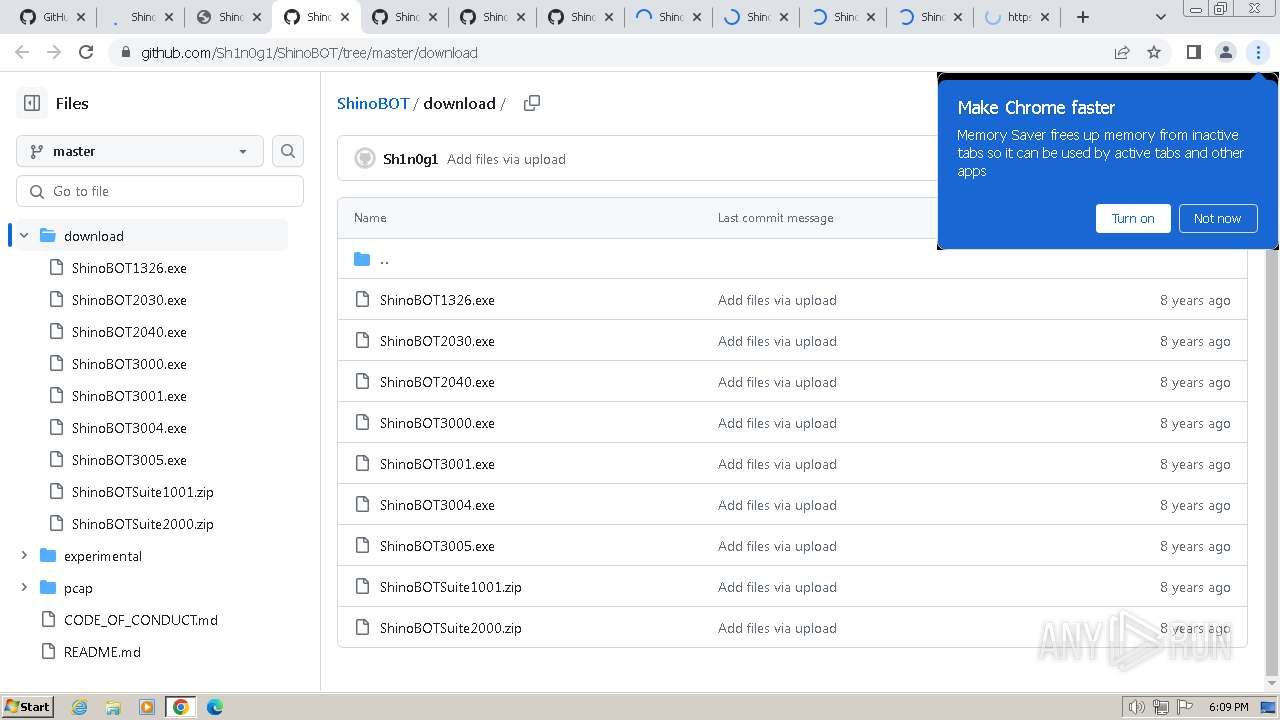
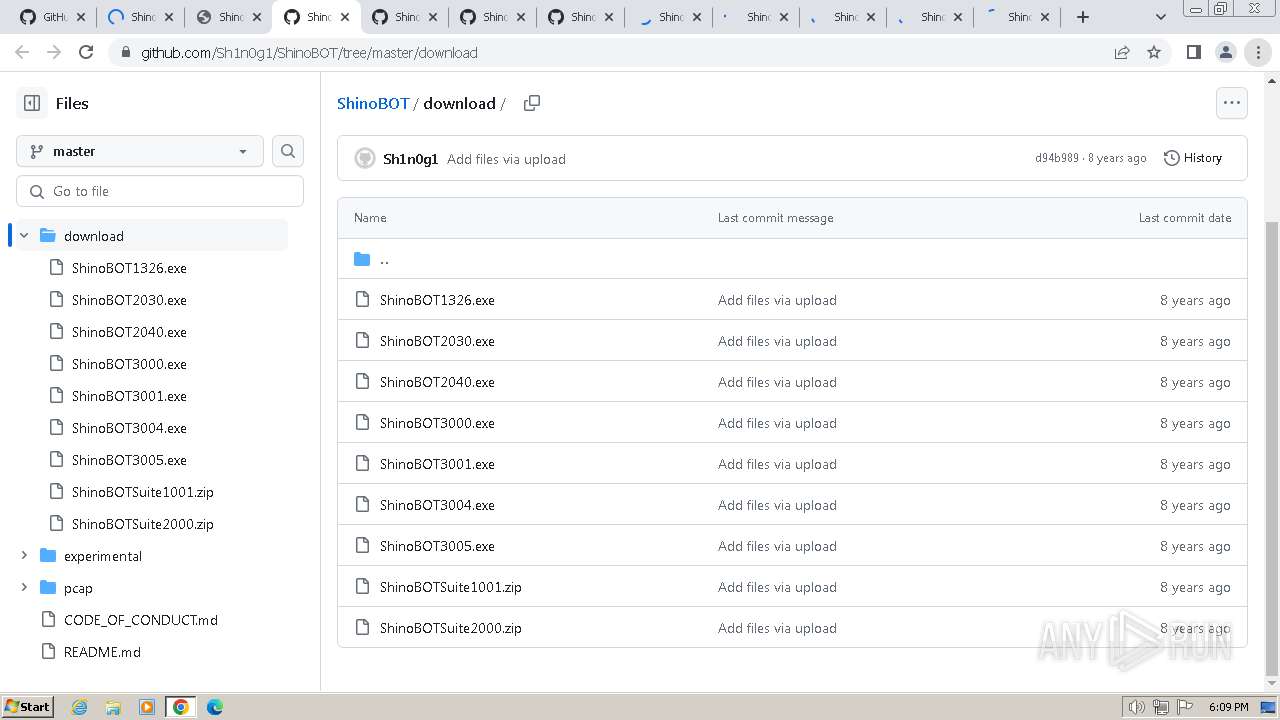
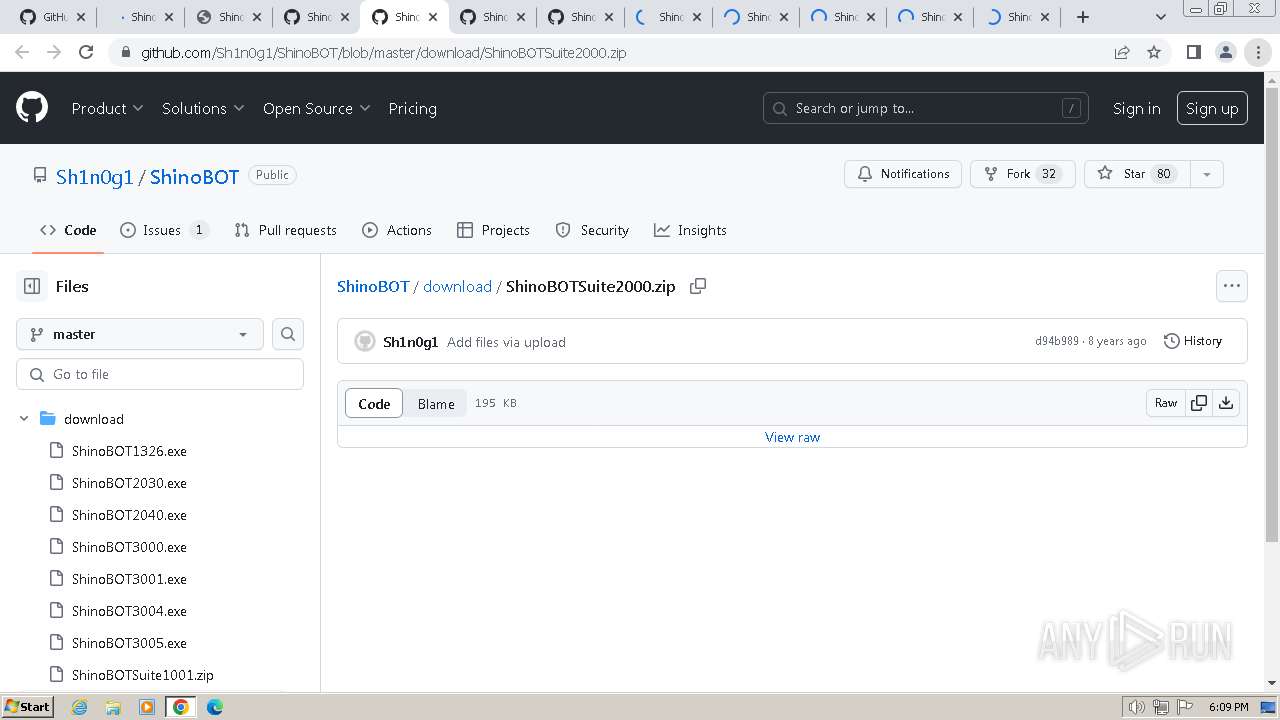
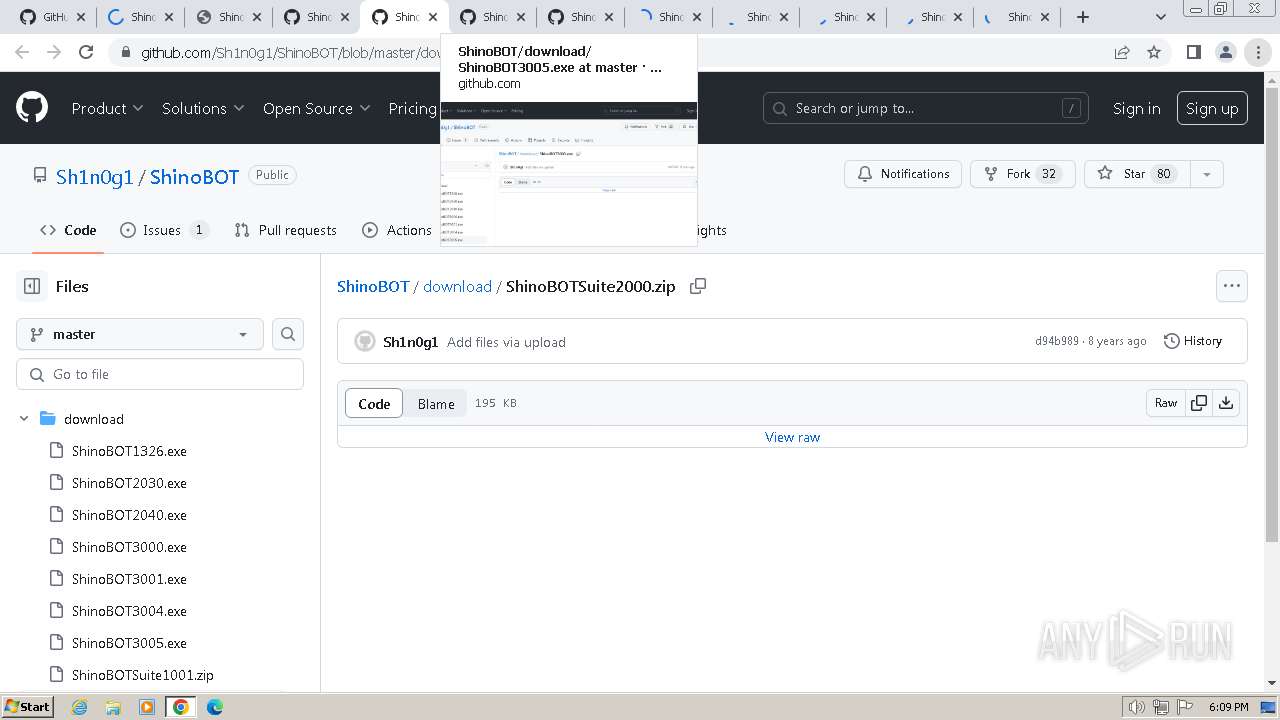
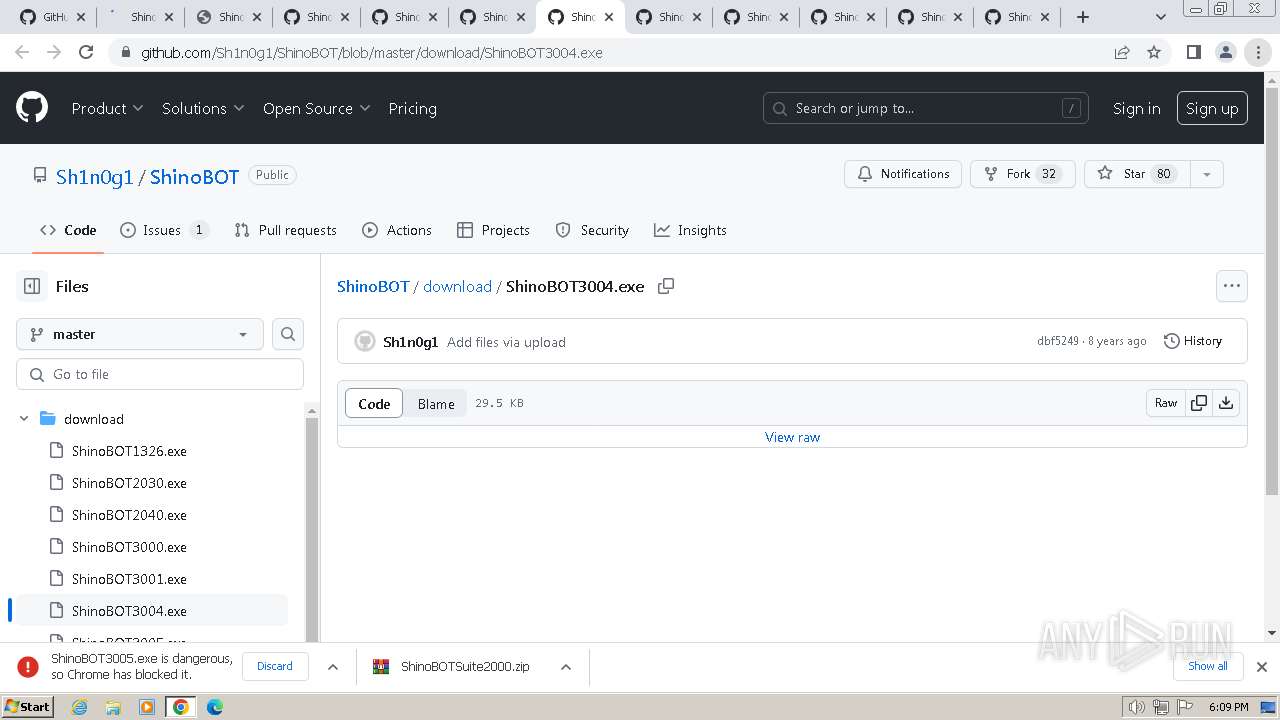
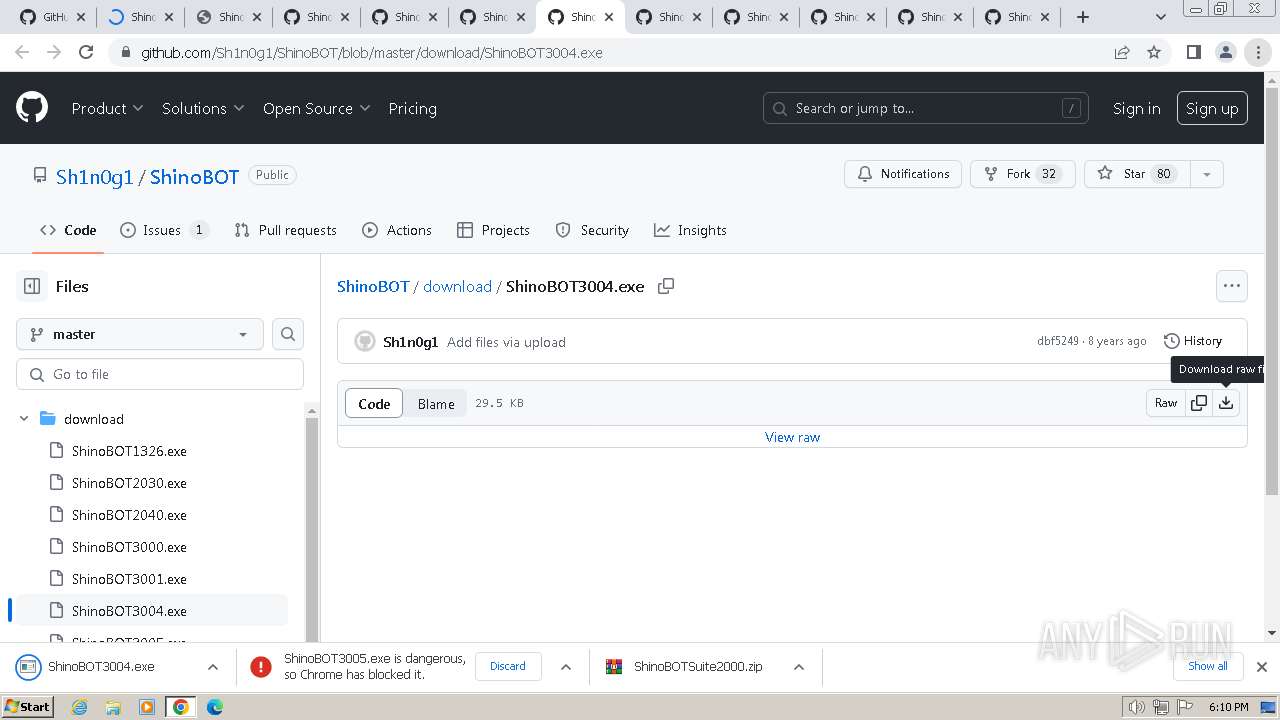
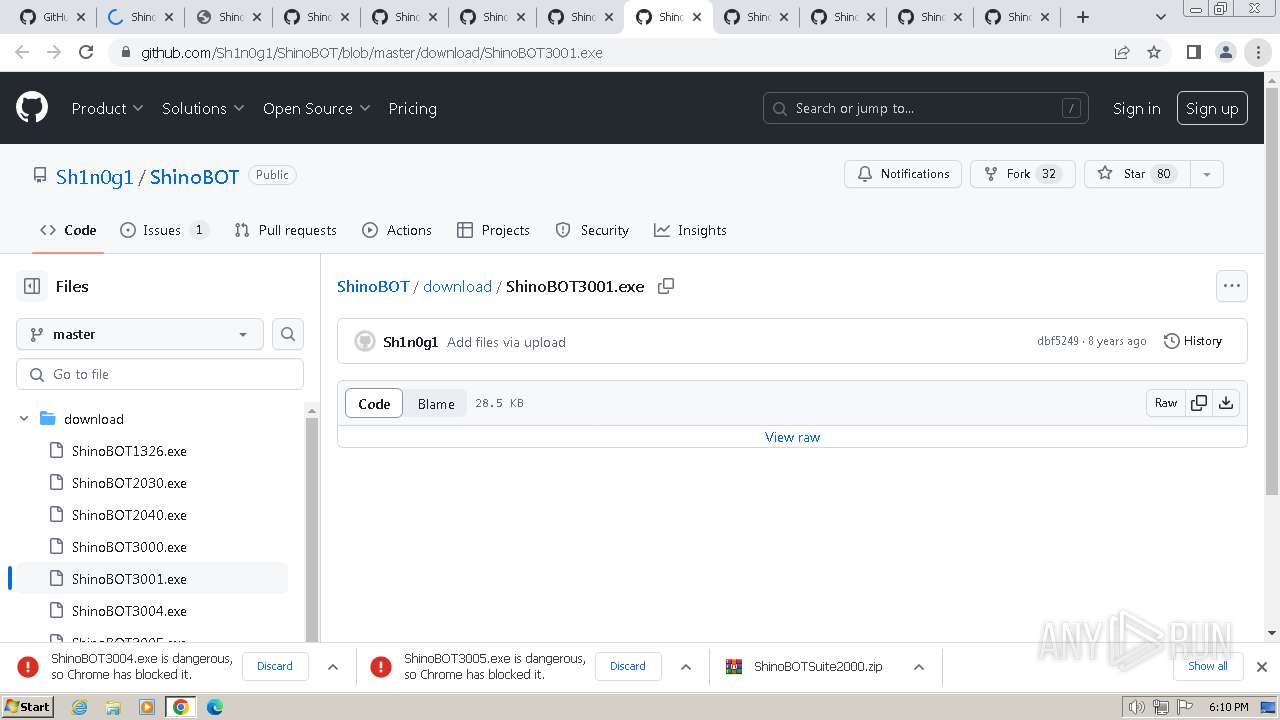
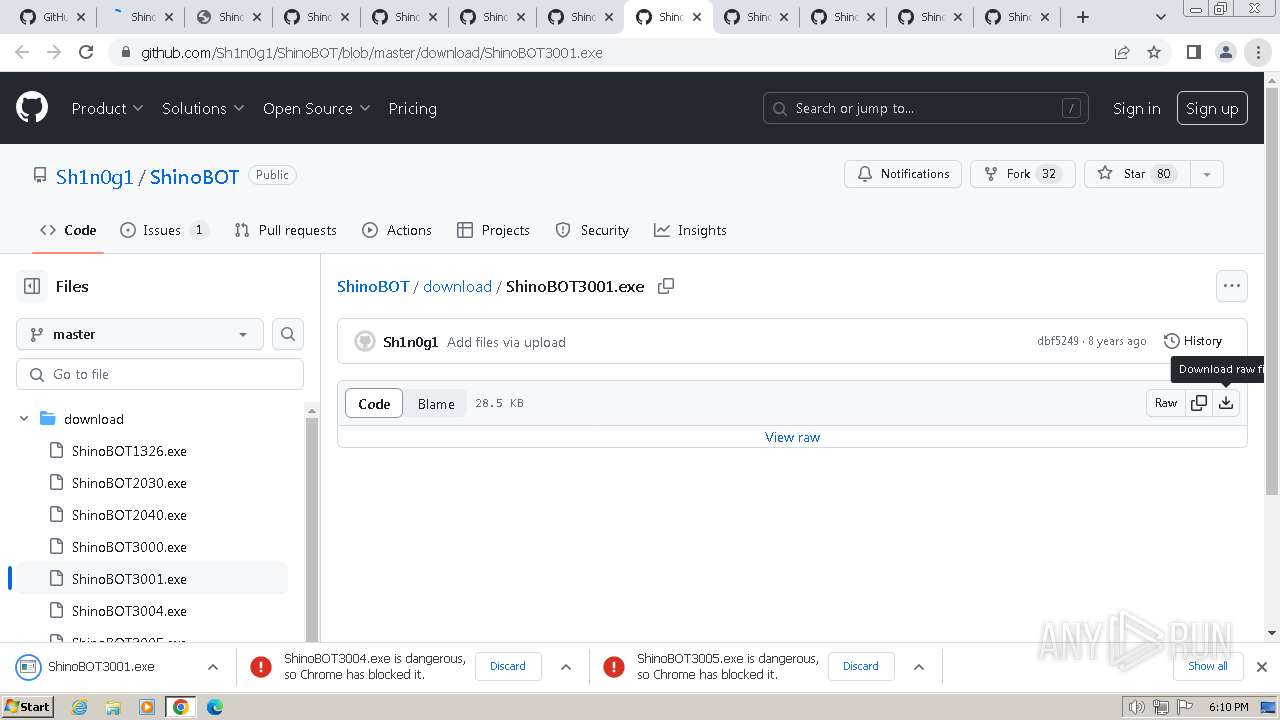
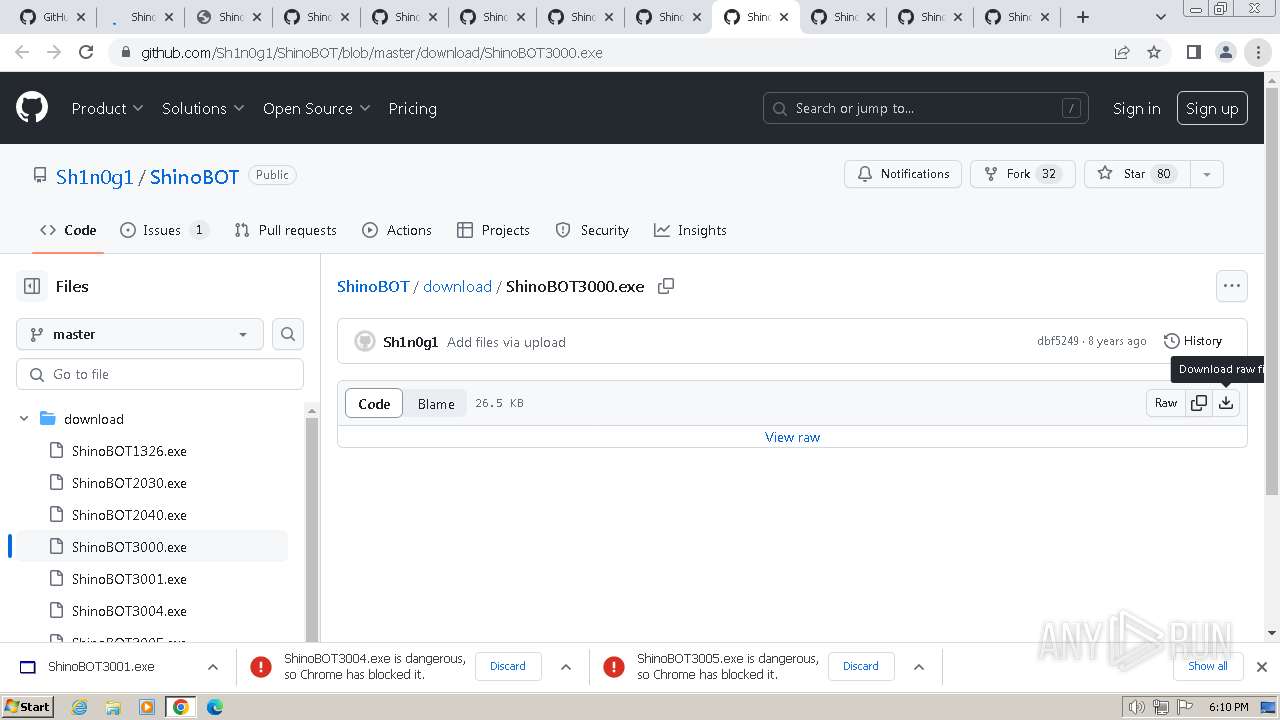
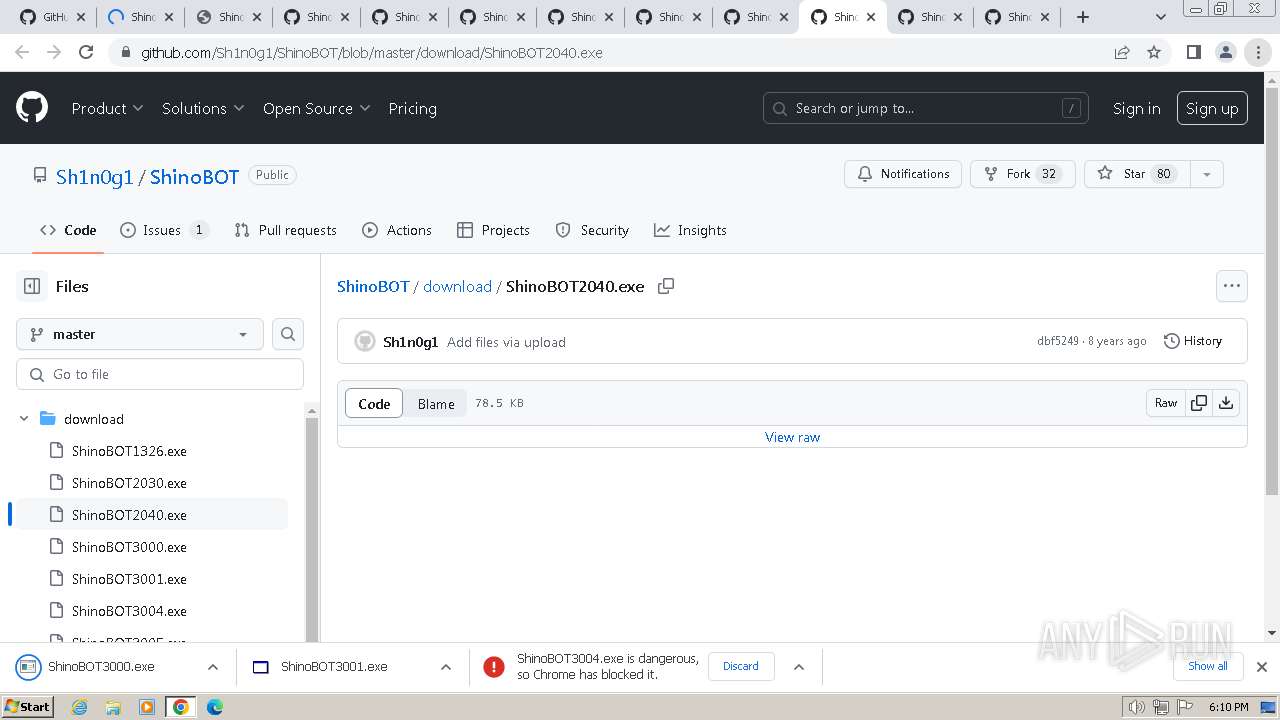
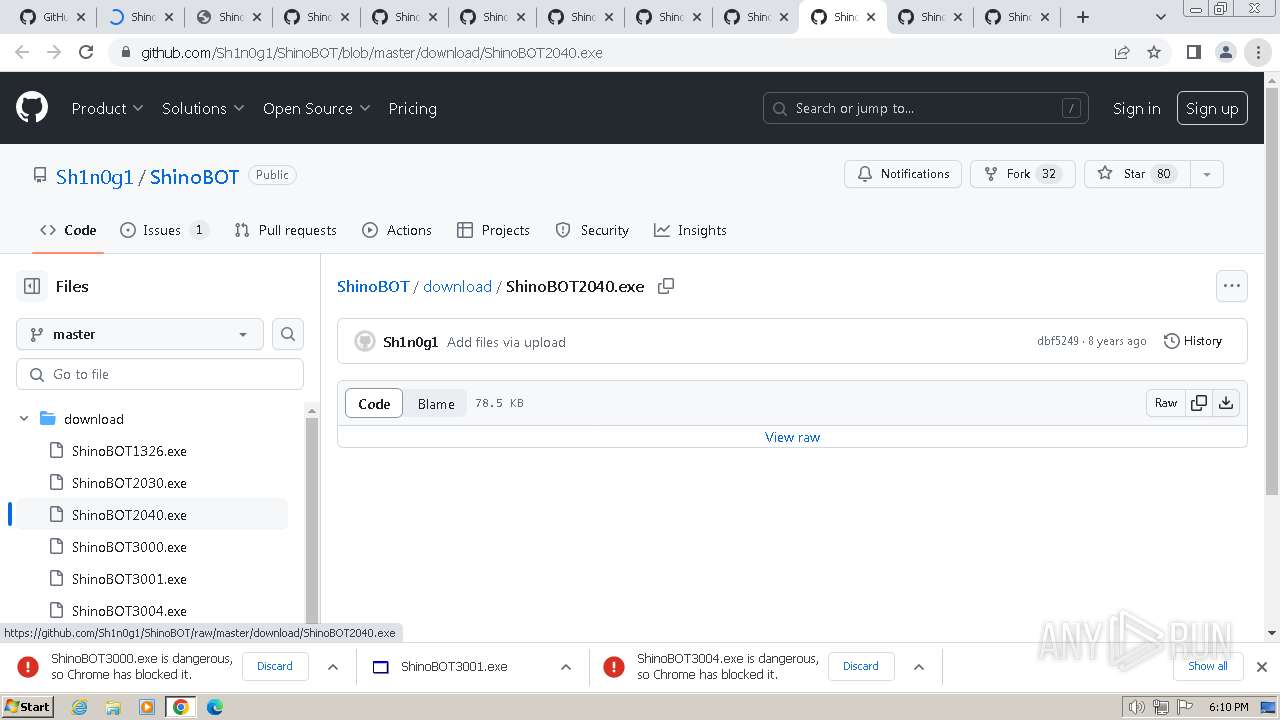
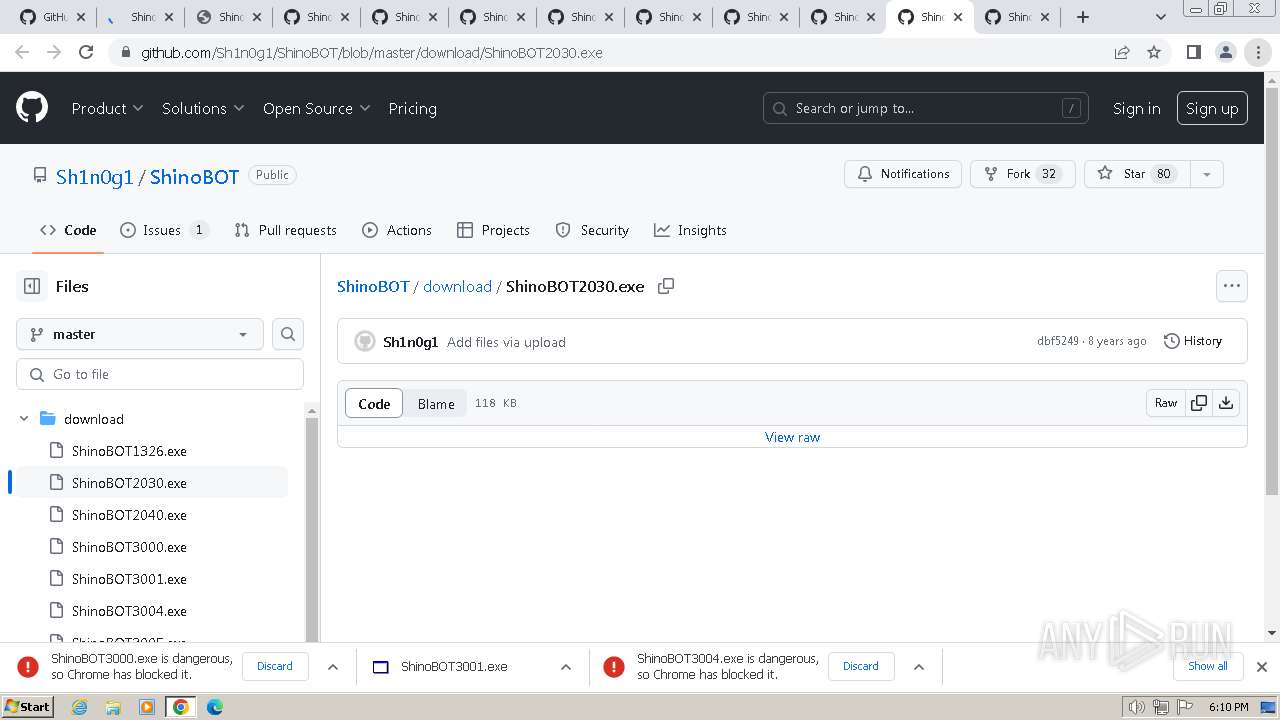
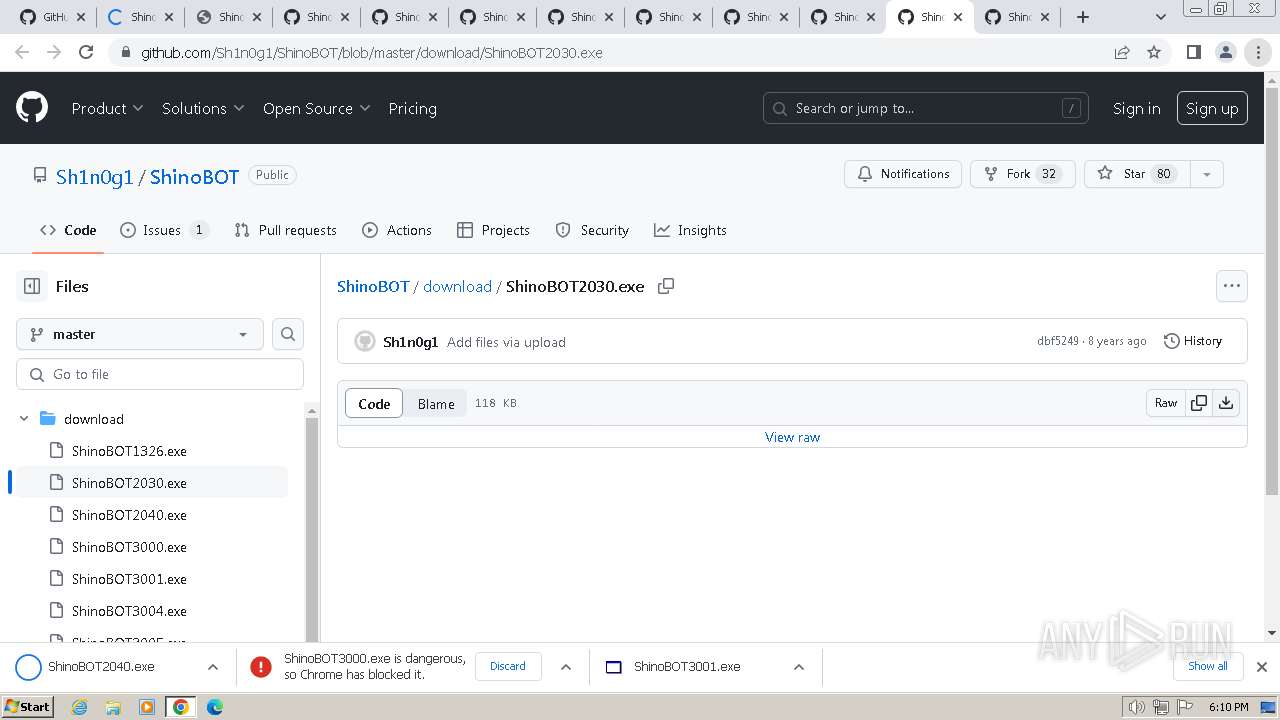
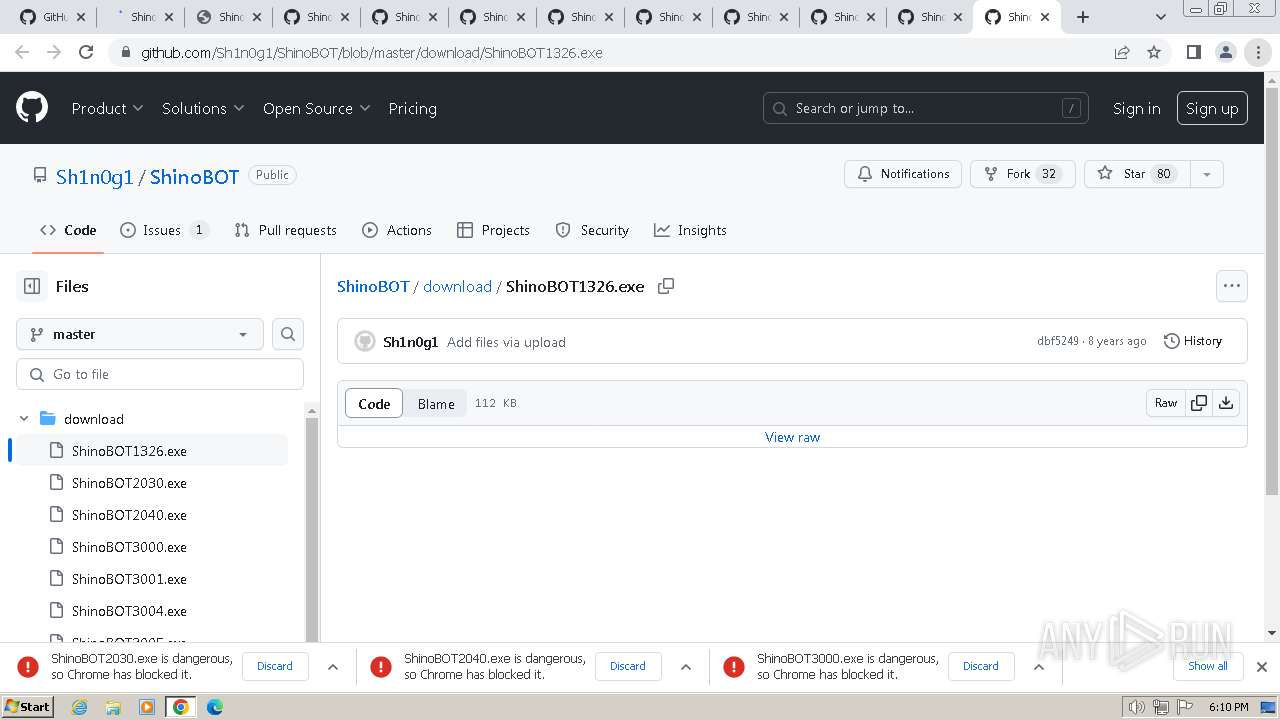
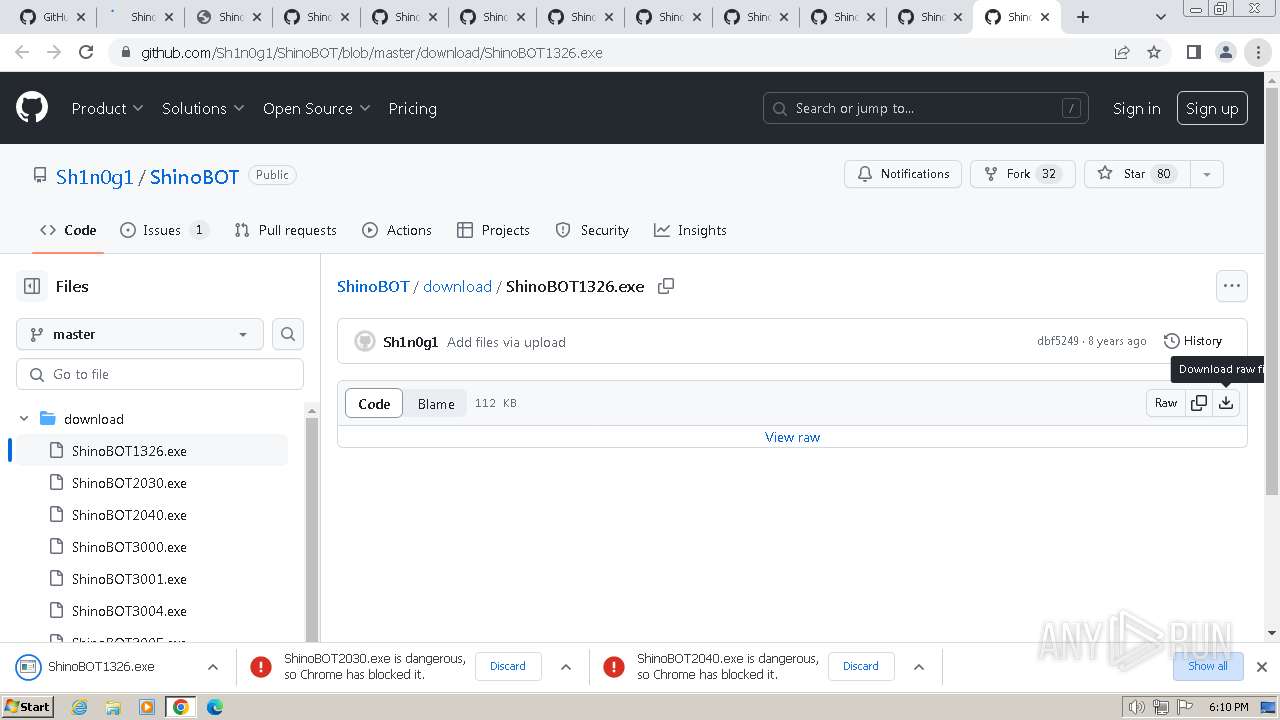
| URL: | https://github.com/Sh1n0g1/ShinoBOT |
| Full analysis: | https://app.any.run/tasks/c2ac970f-c1cf-4e51-884a-5c4e76c260bb |
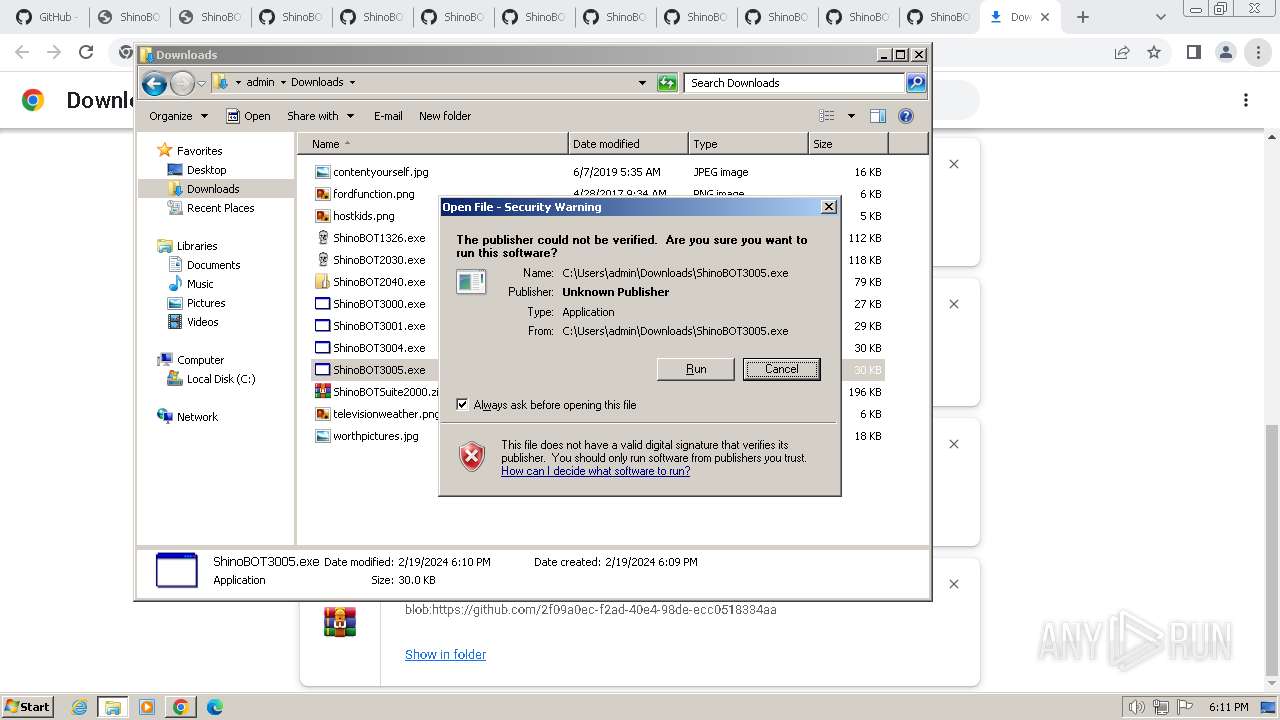
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2024, 18:07:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7D5B593399C9076B26C6C491699B7473 |
| SHA1: | EF024B2E87DAB84708EDDAD8B020C7D594C33D13 |
| SHA256: | 8BB879066A42C22C6631E54165C0B4F554DFB11658600D3F89979B150FCFB306 |
| SSDEEP: | 3:N8tEdfh9TK:2u5h9O |
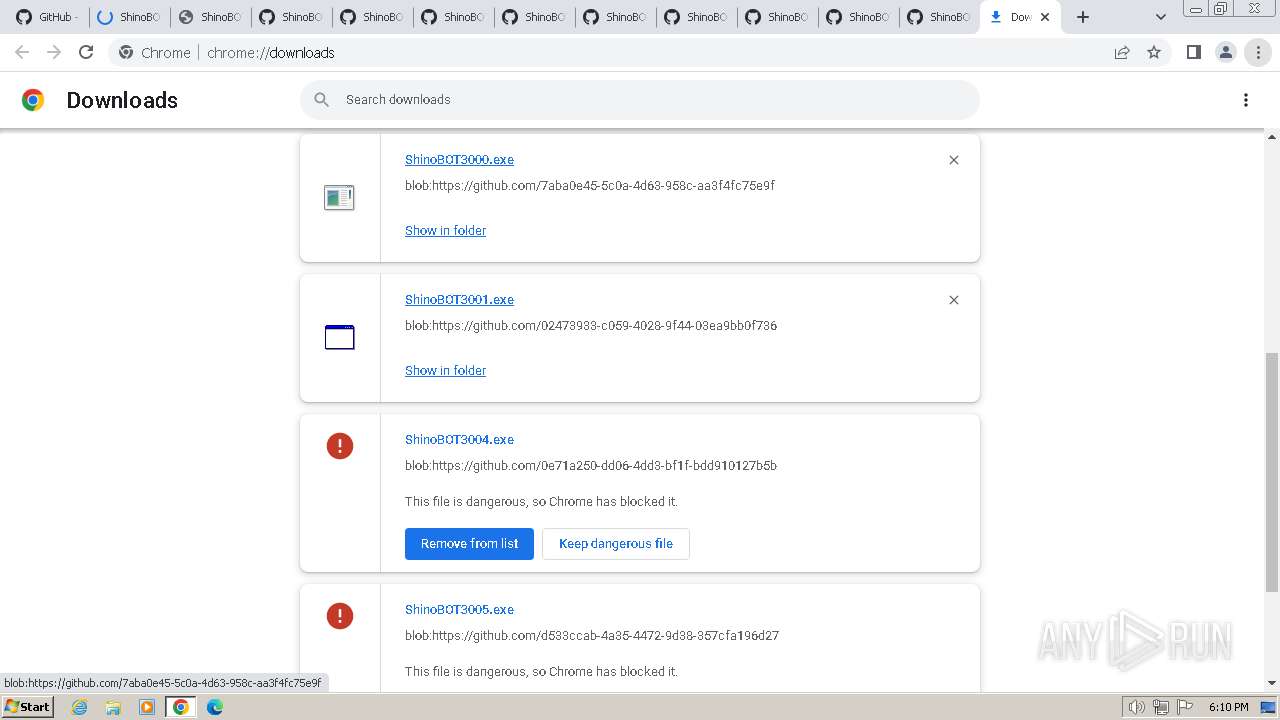
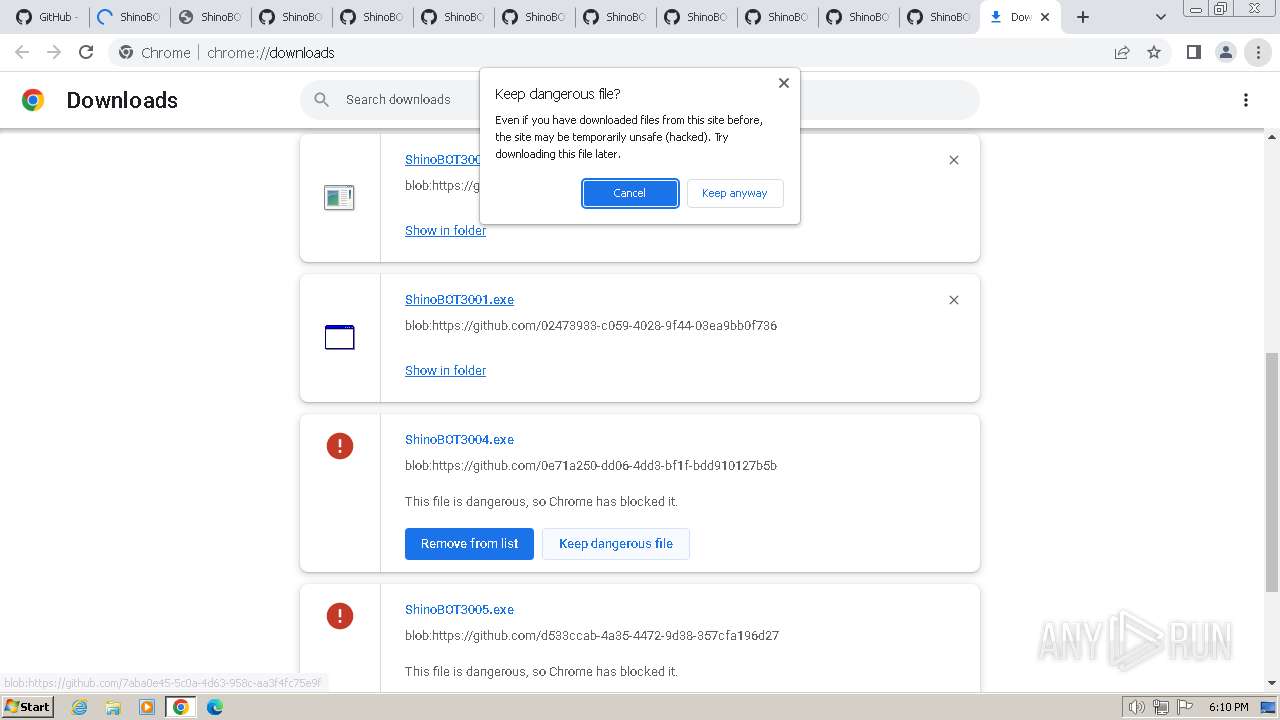
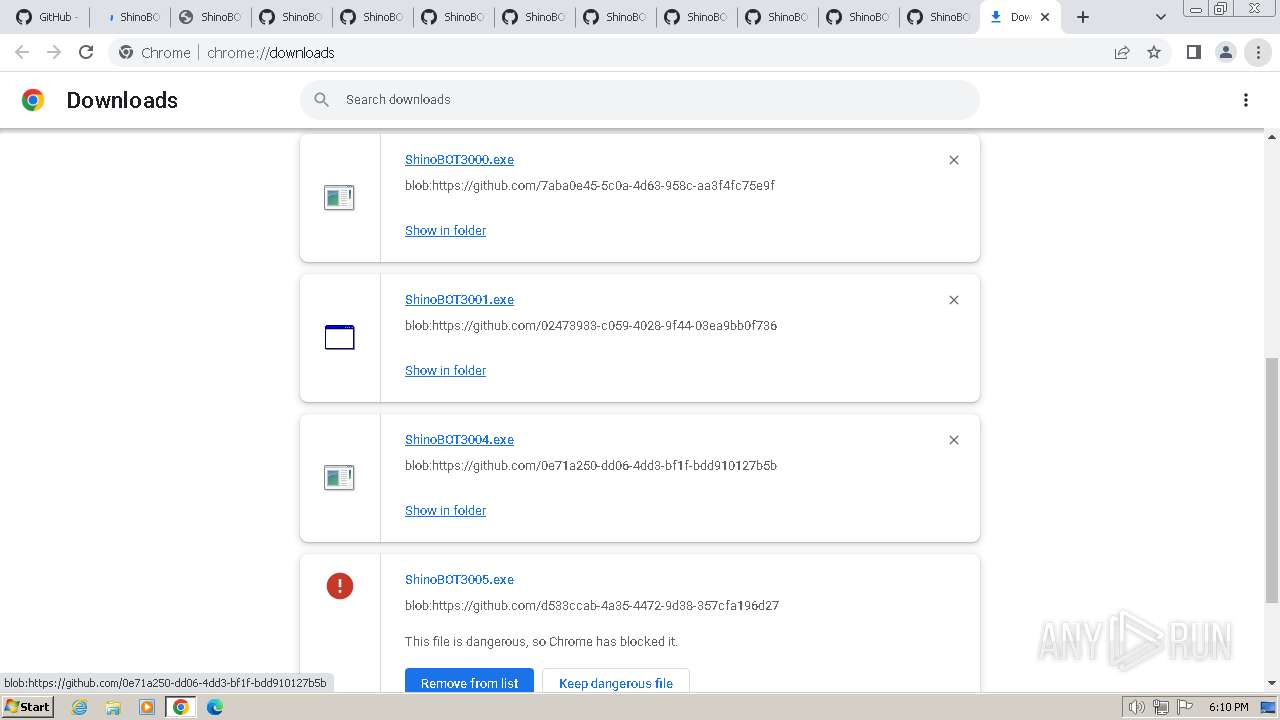
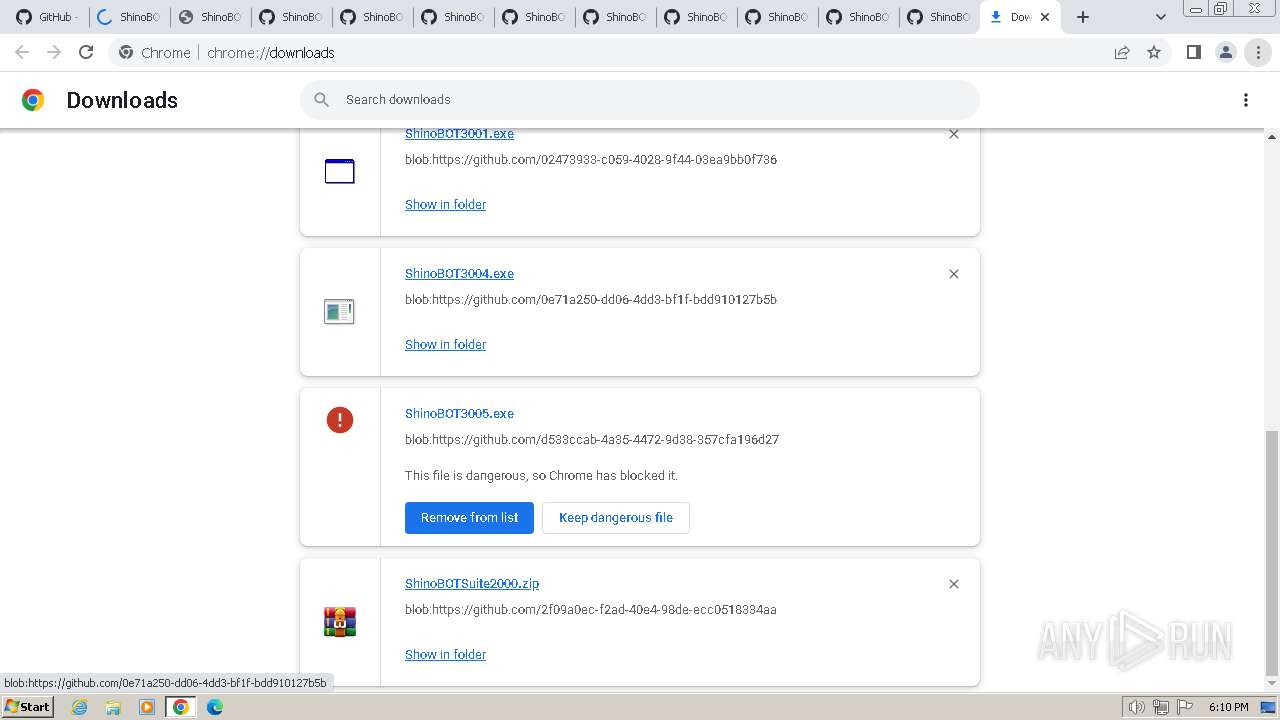
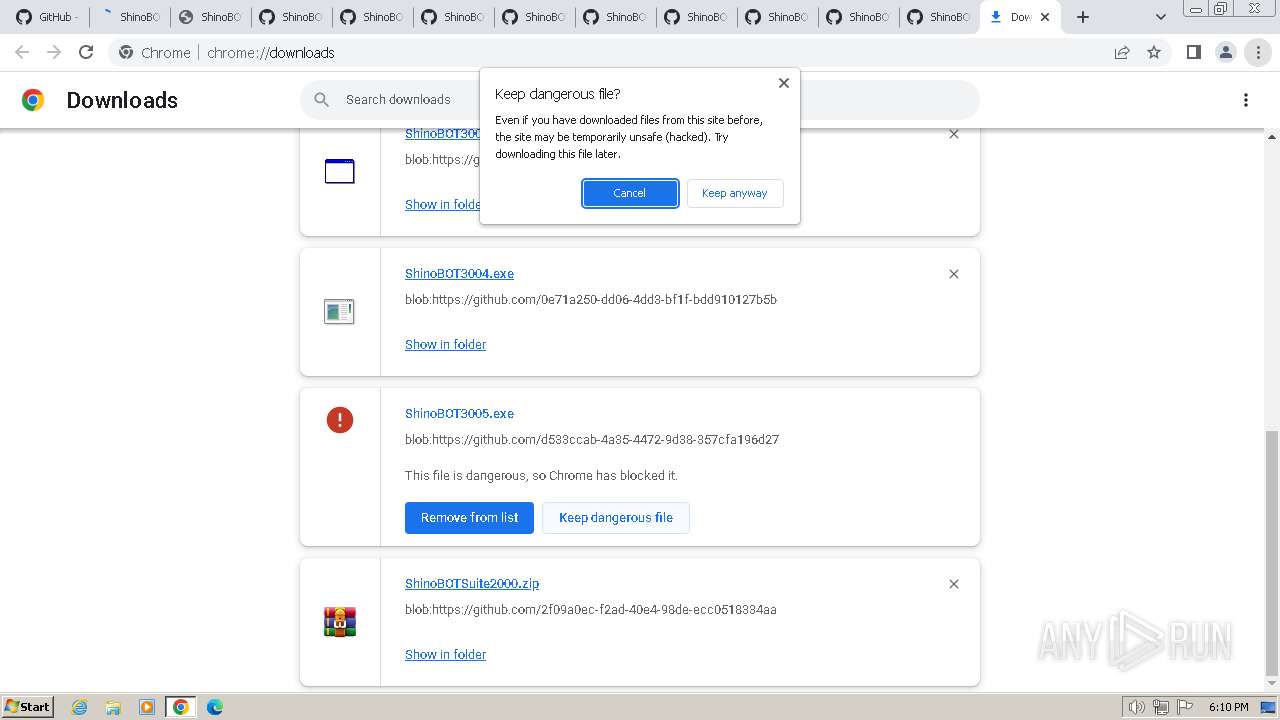
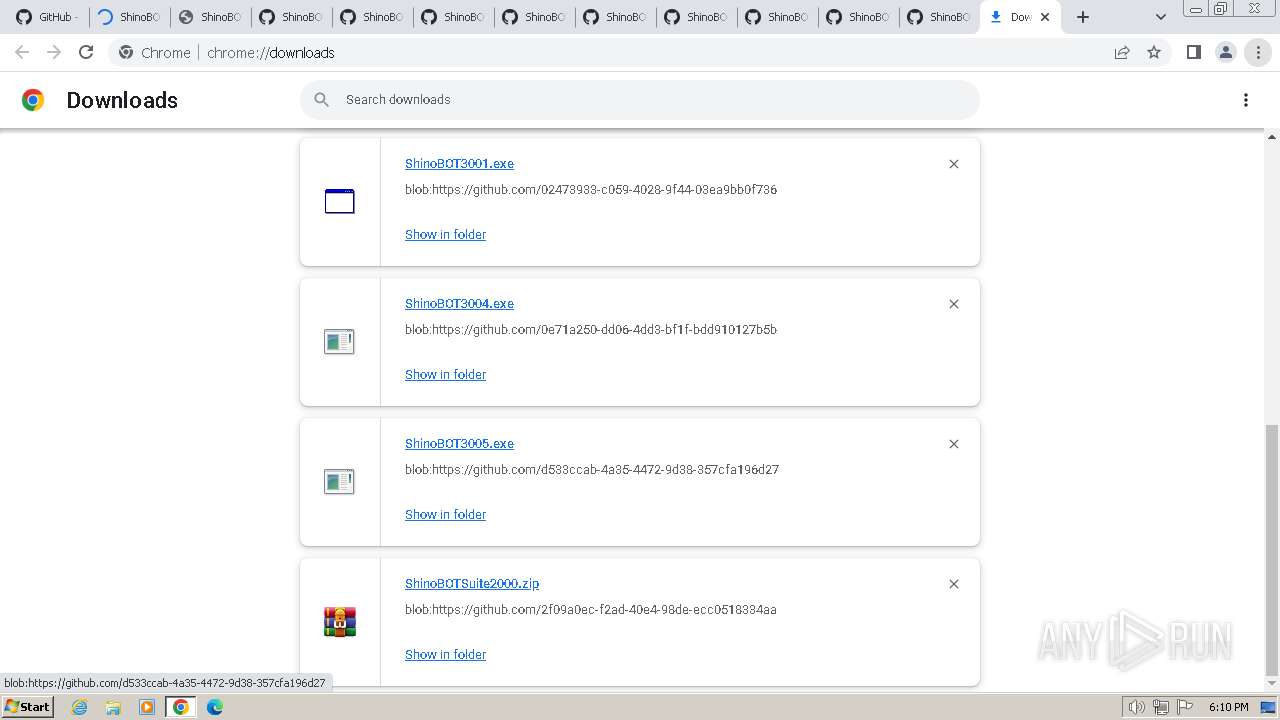
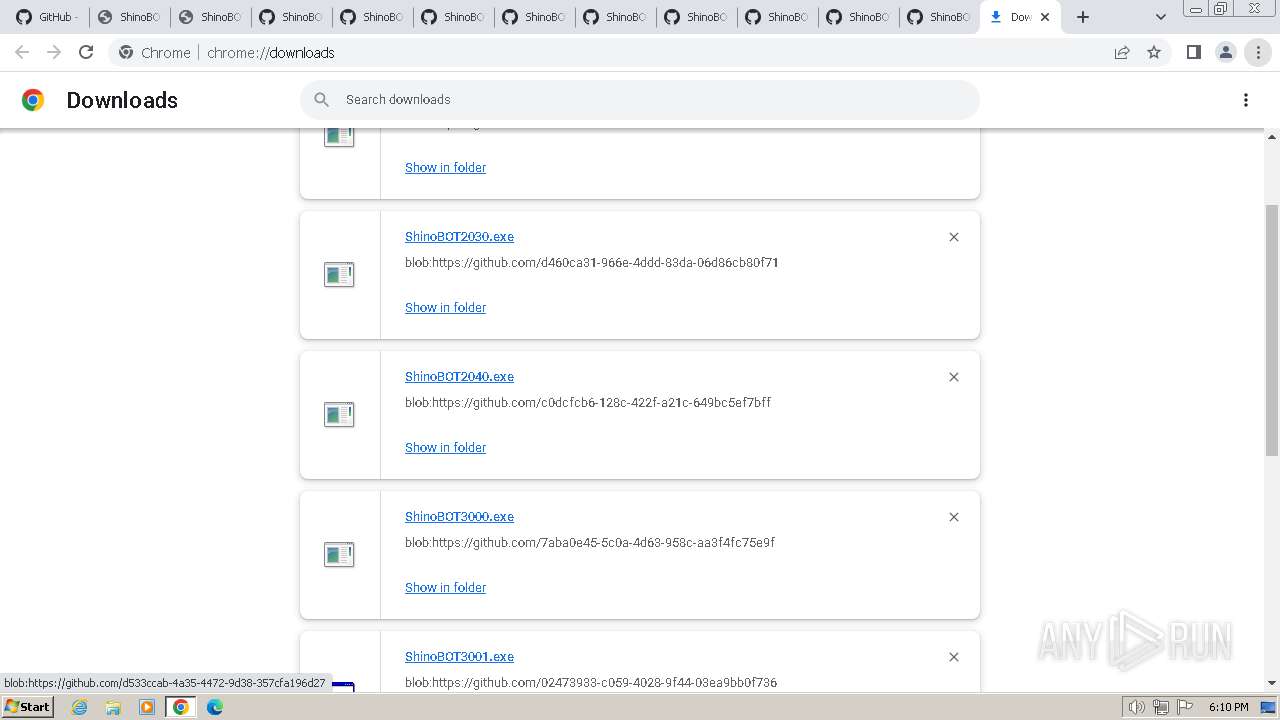
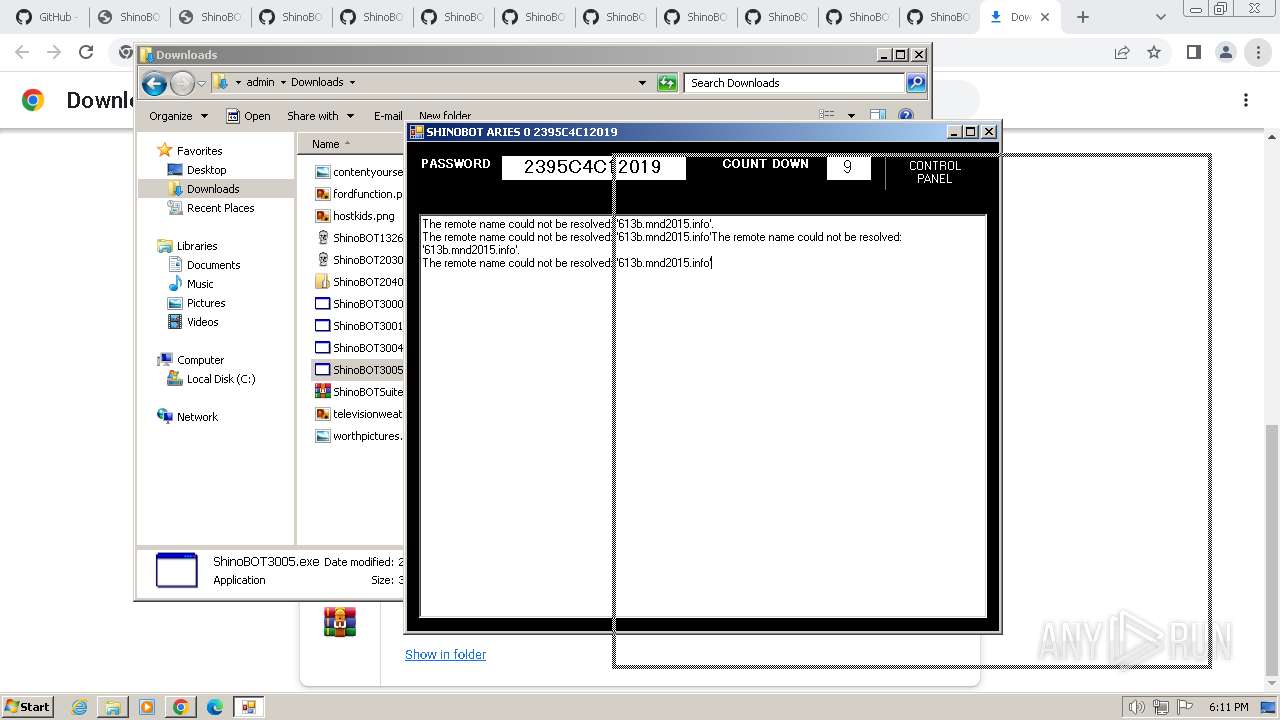
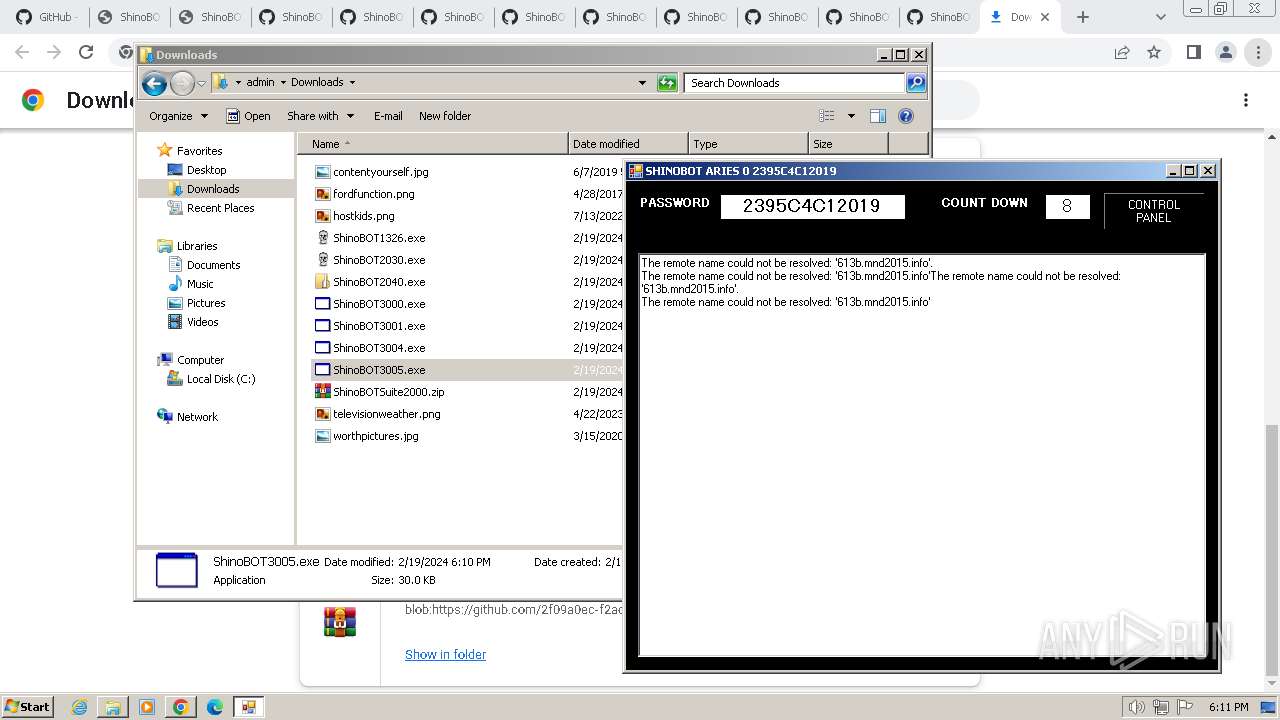
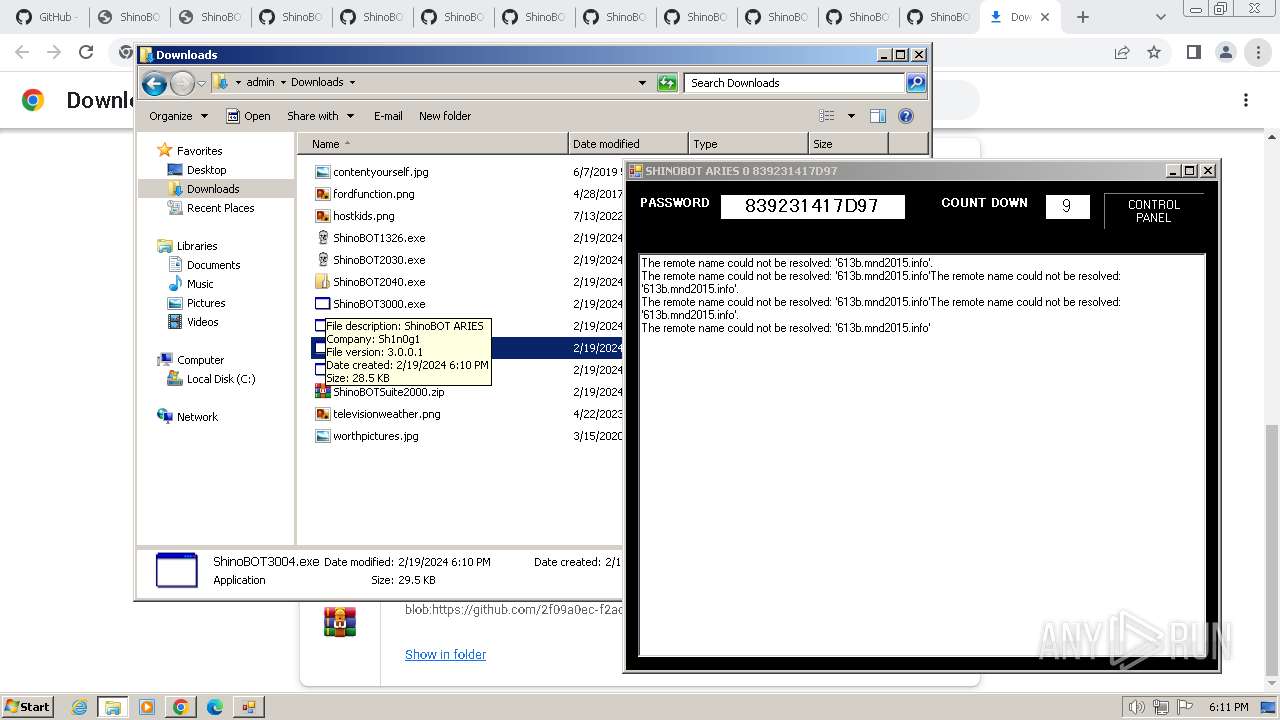
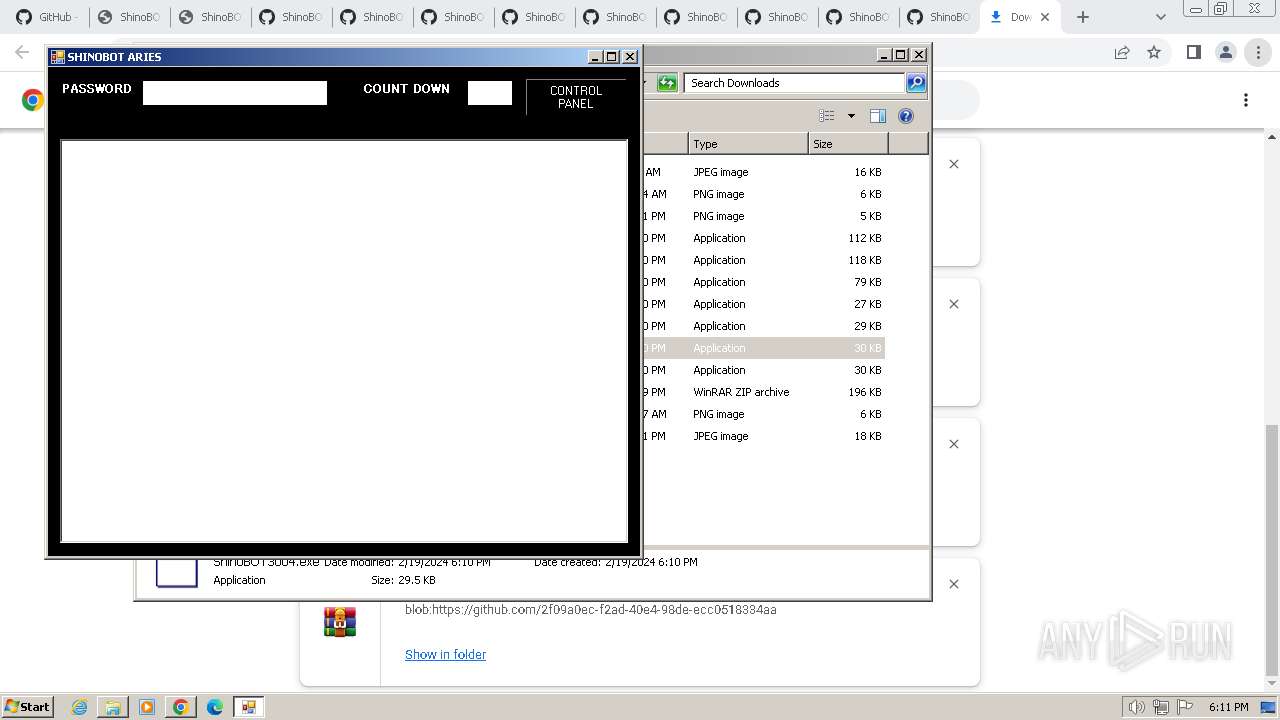
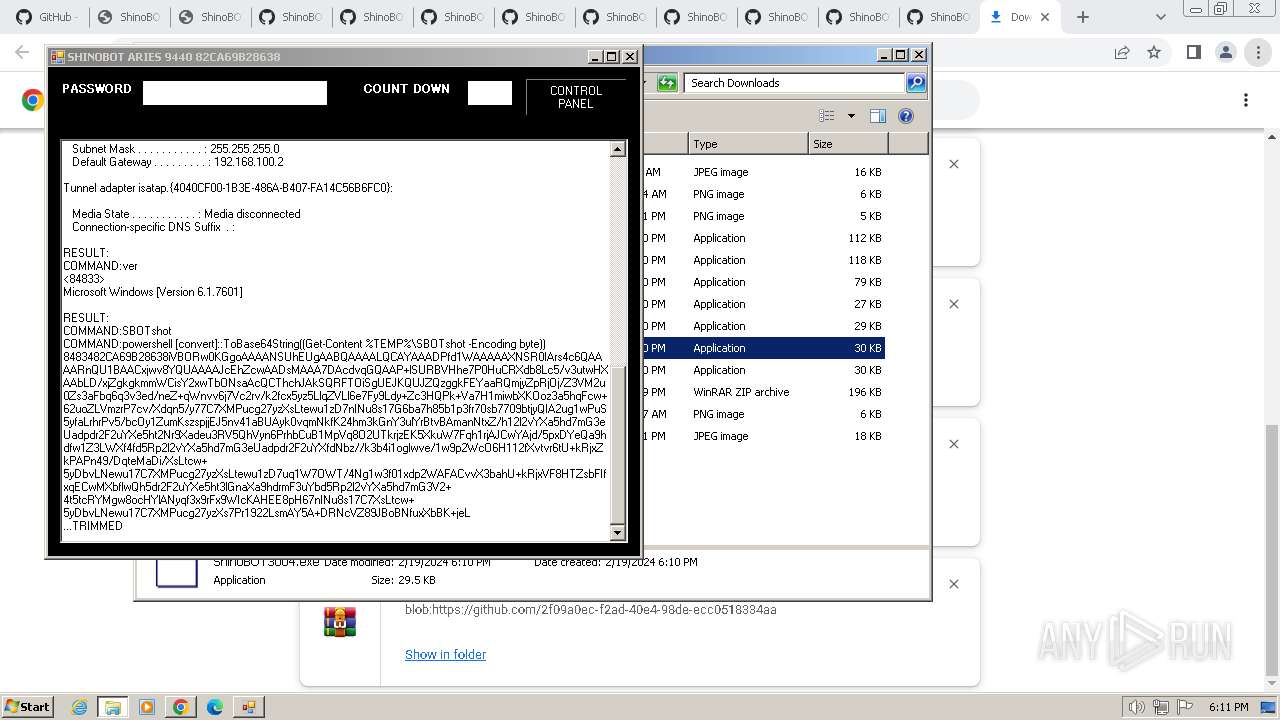
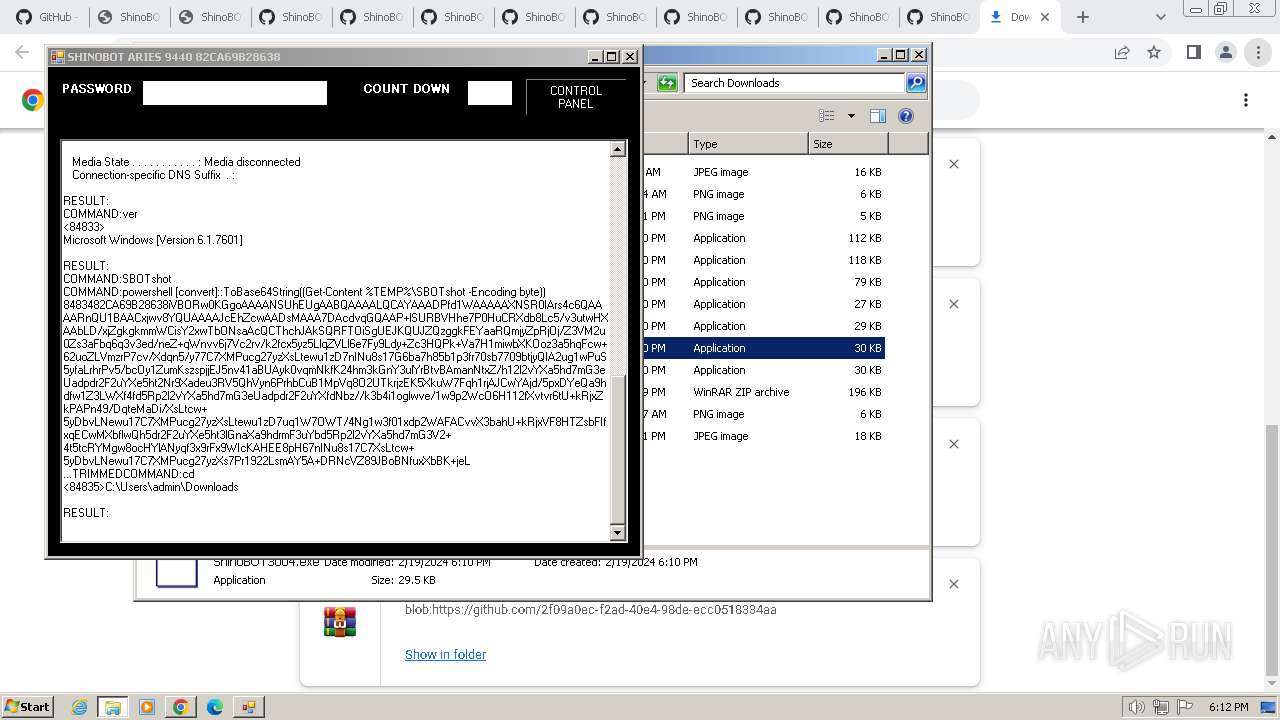
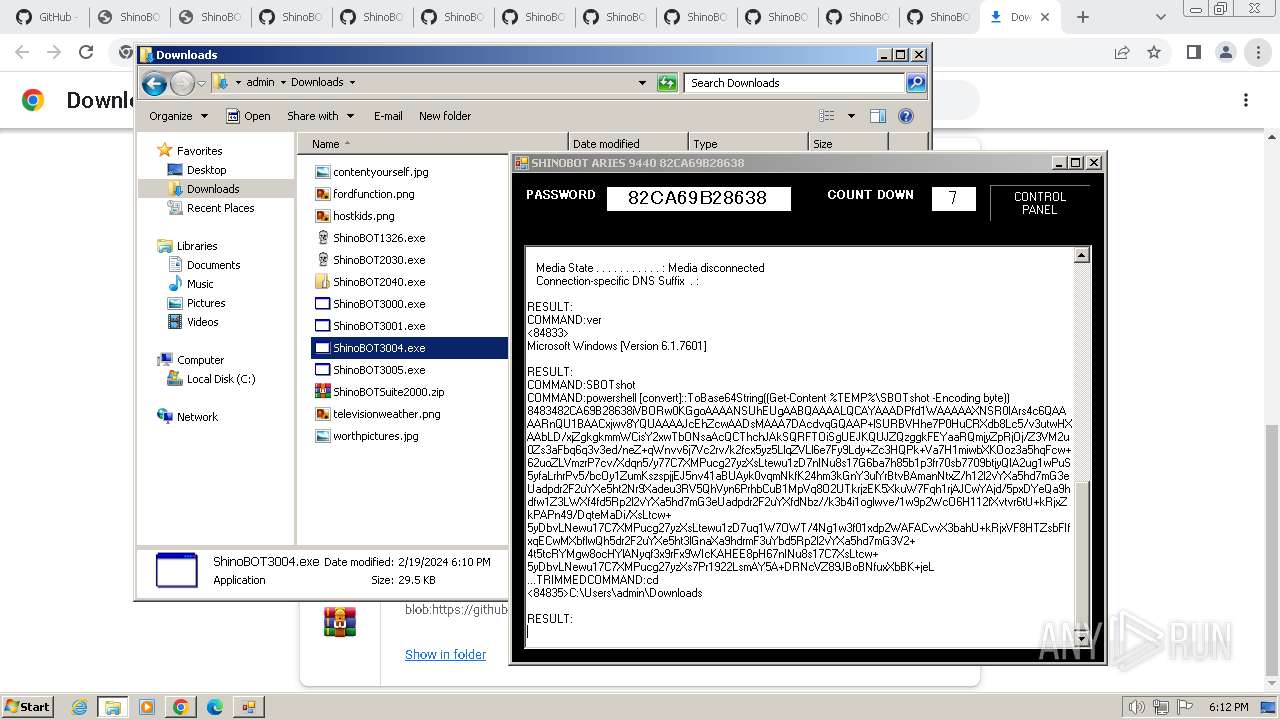
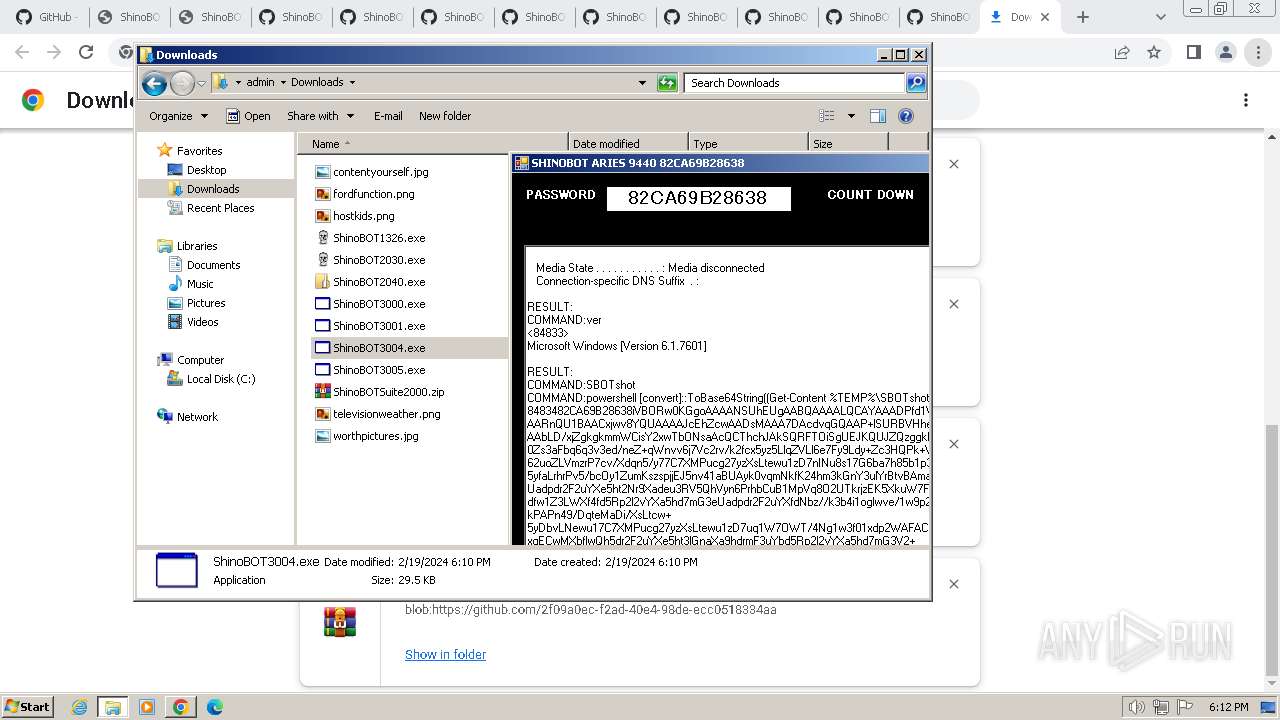
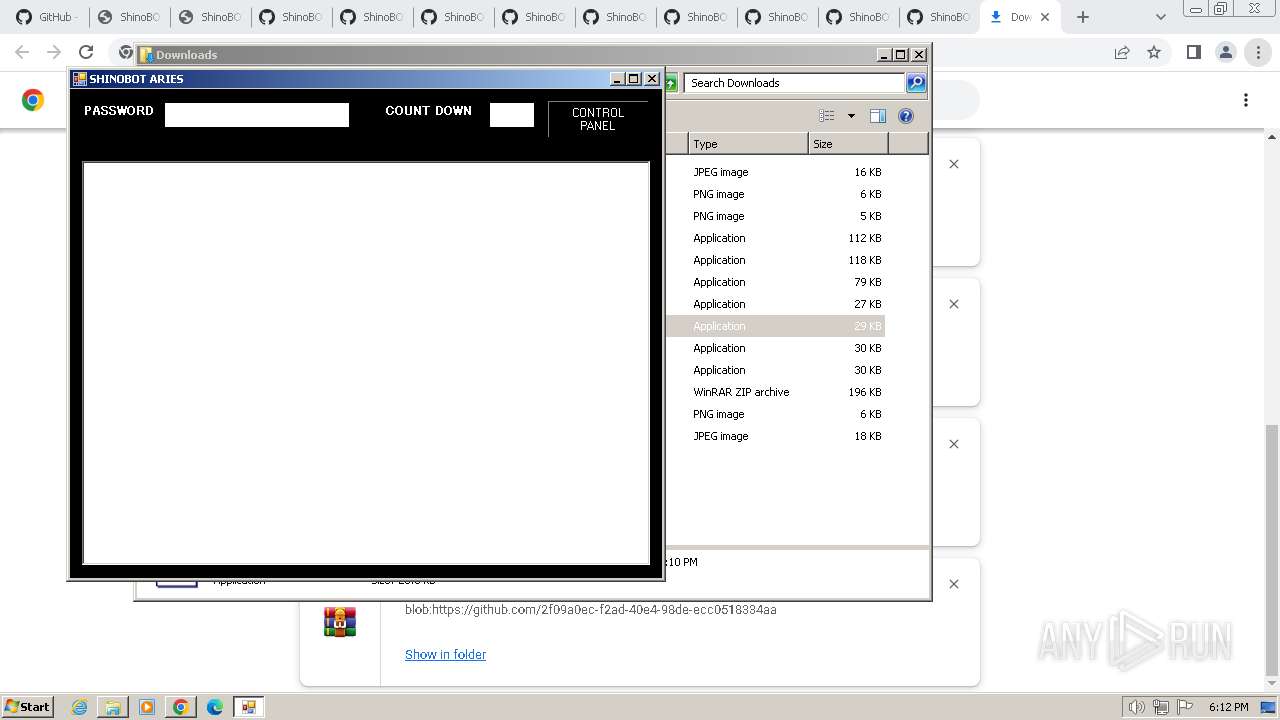
MALICIOUS
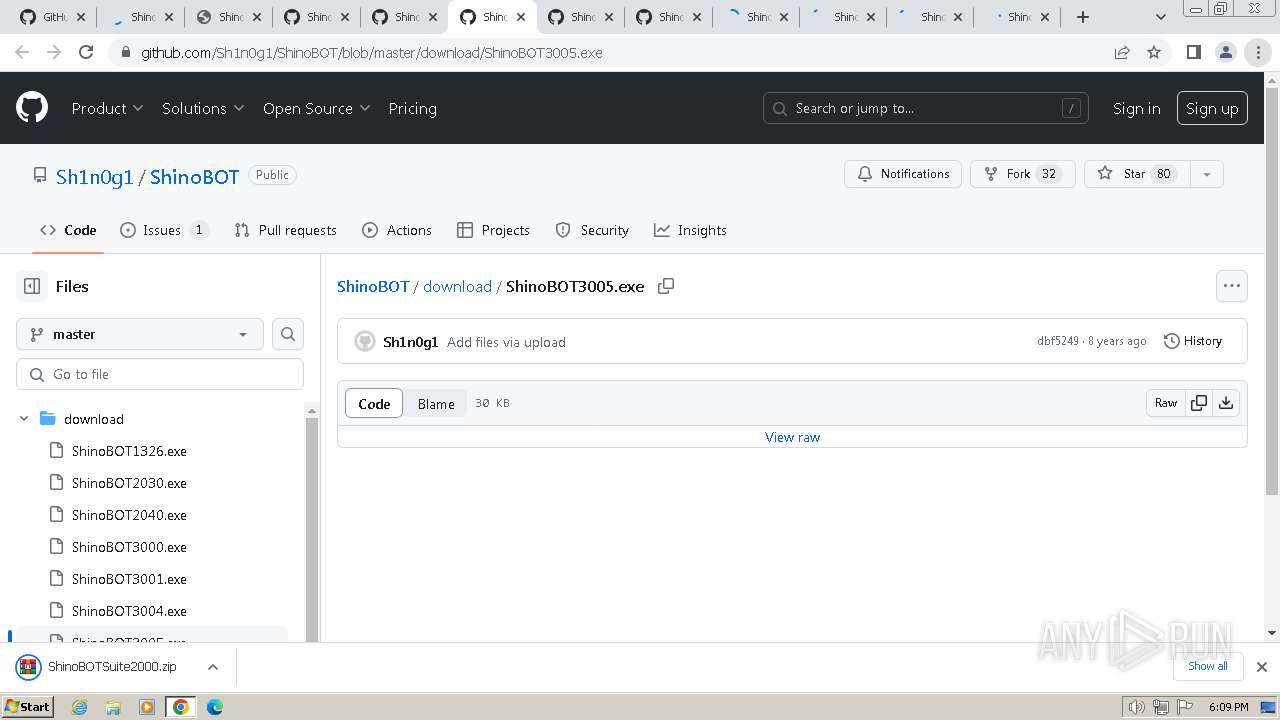
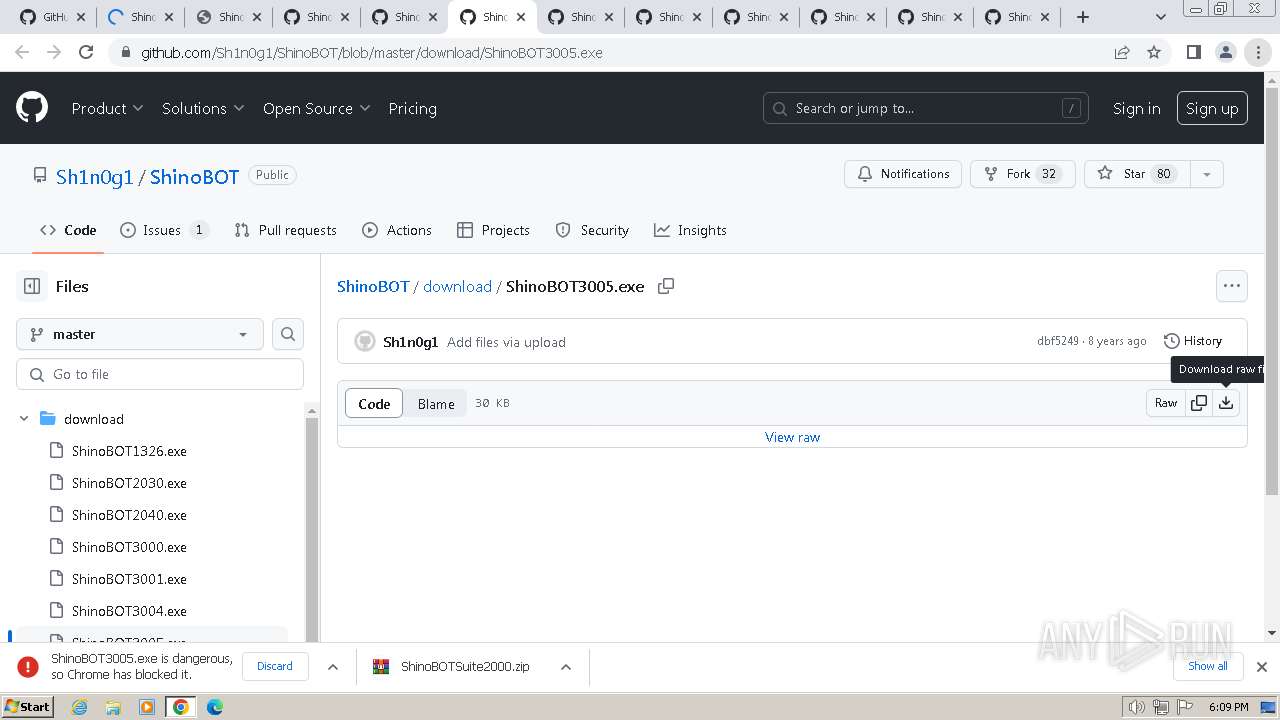
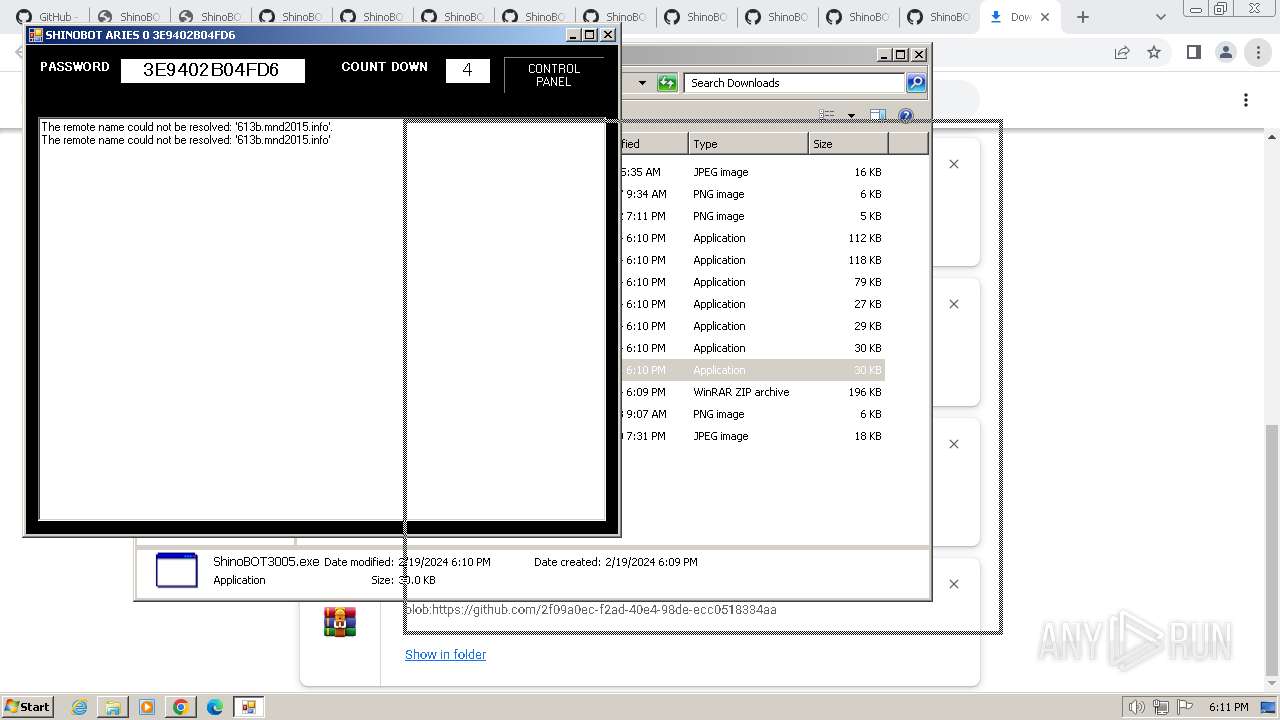
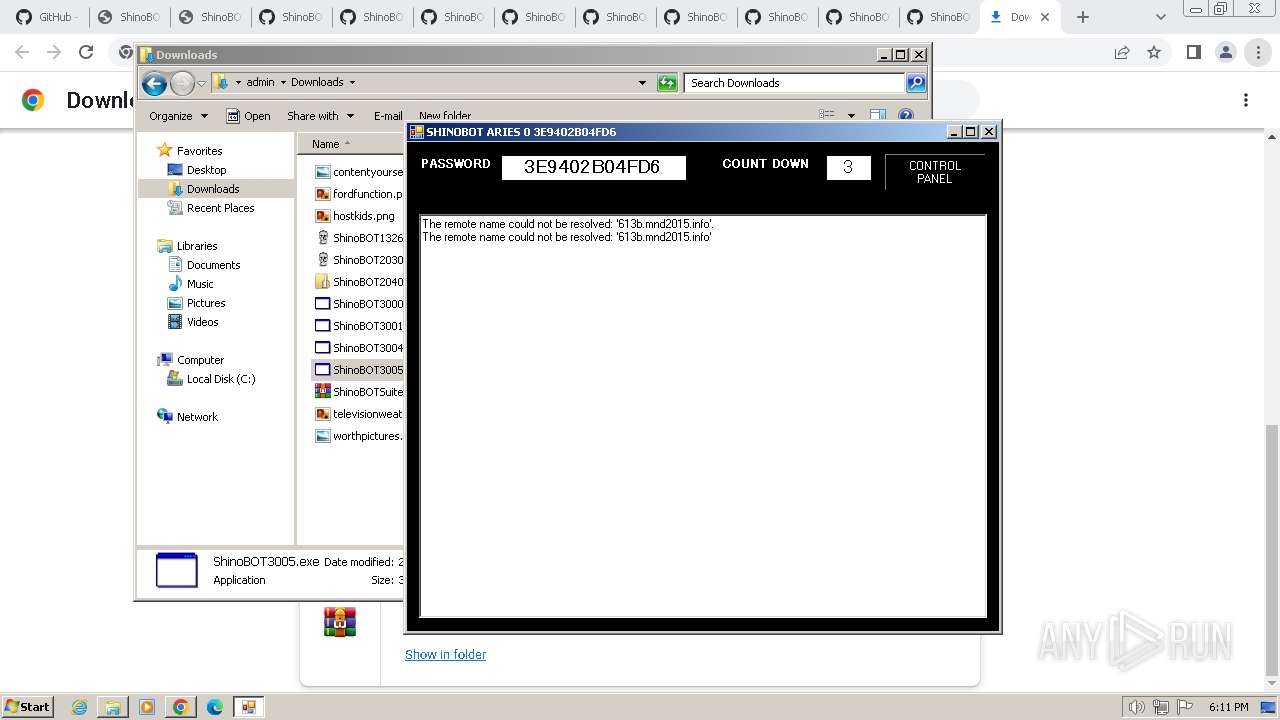
Connects to the CnC server
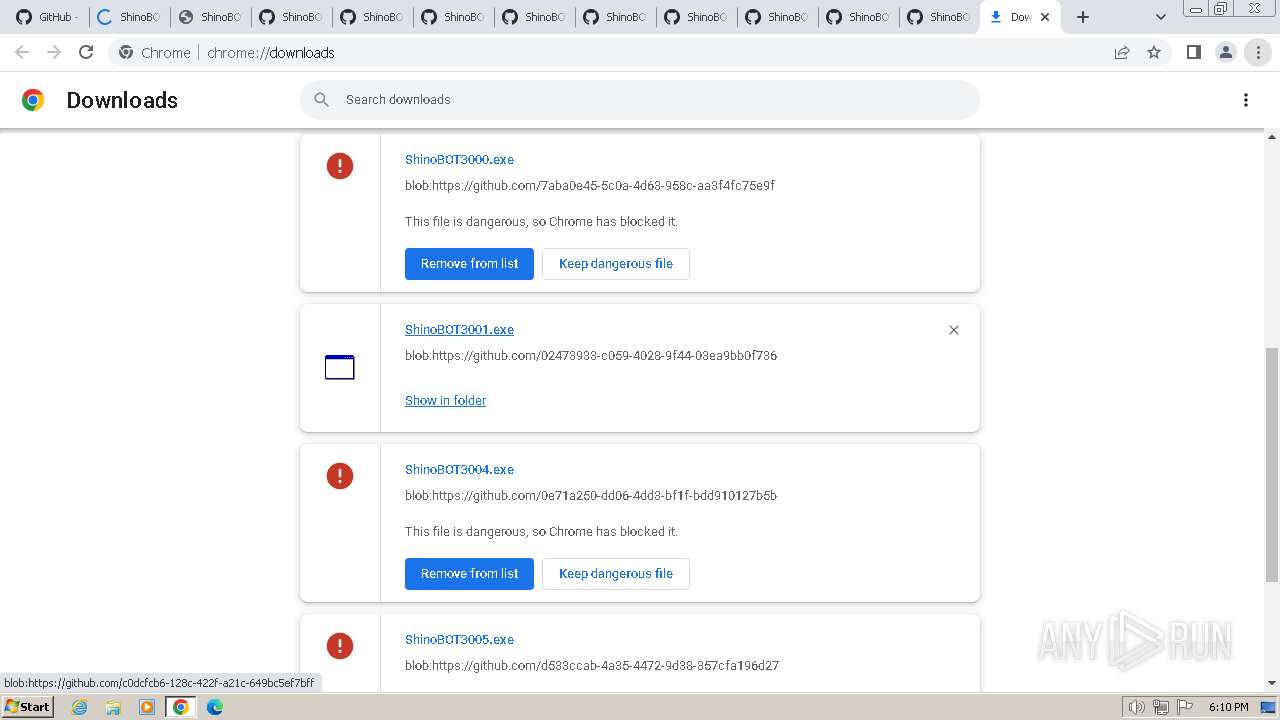
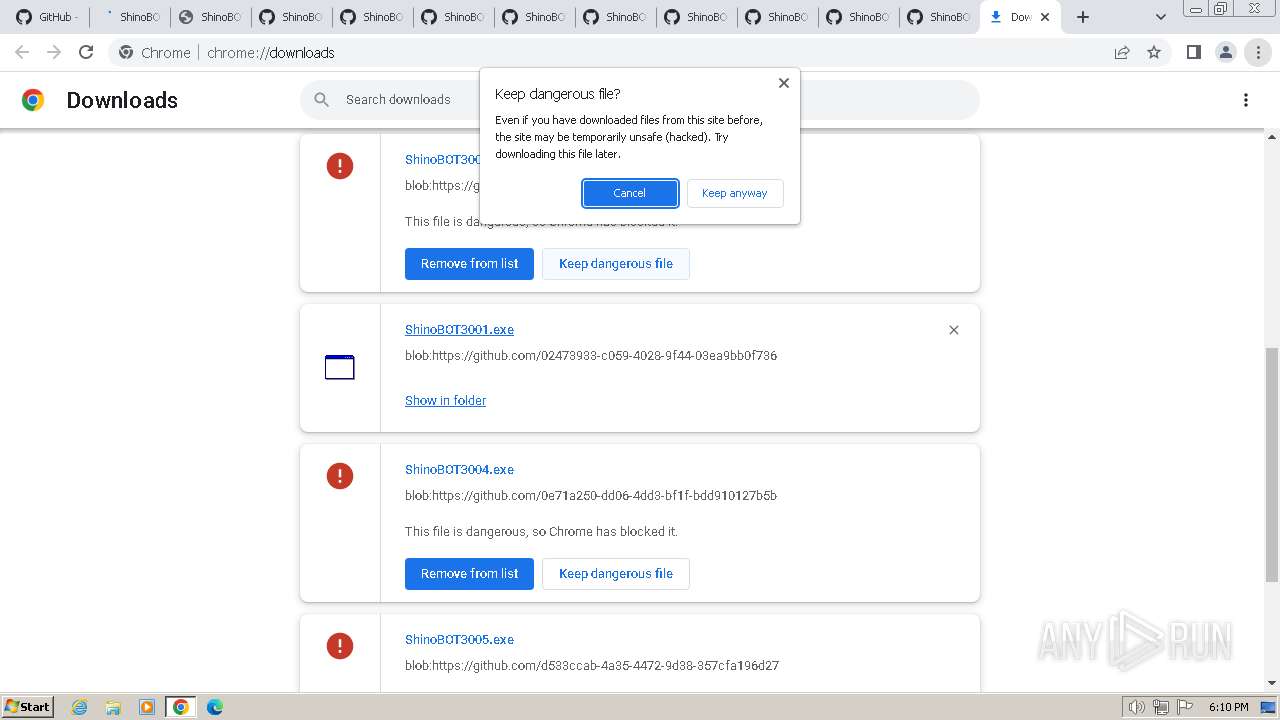
- ShinoBOT3004.exe (PID: 3496)
SUSPICIOUS
Reads the Internet Settings
- ShinoBOT3005.exe (PID: 2548)
- ShinoBOT3004.exe (PID: 3496)
- ShinoBOT3001.exe (PID: 3200)
- ShinoBOT3000.exe (PID: 2916)
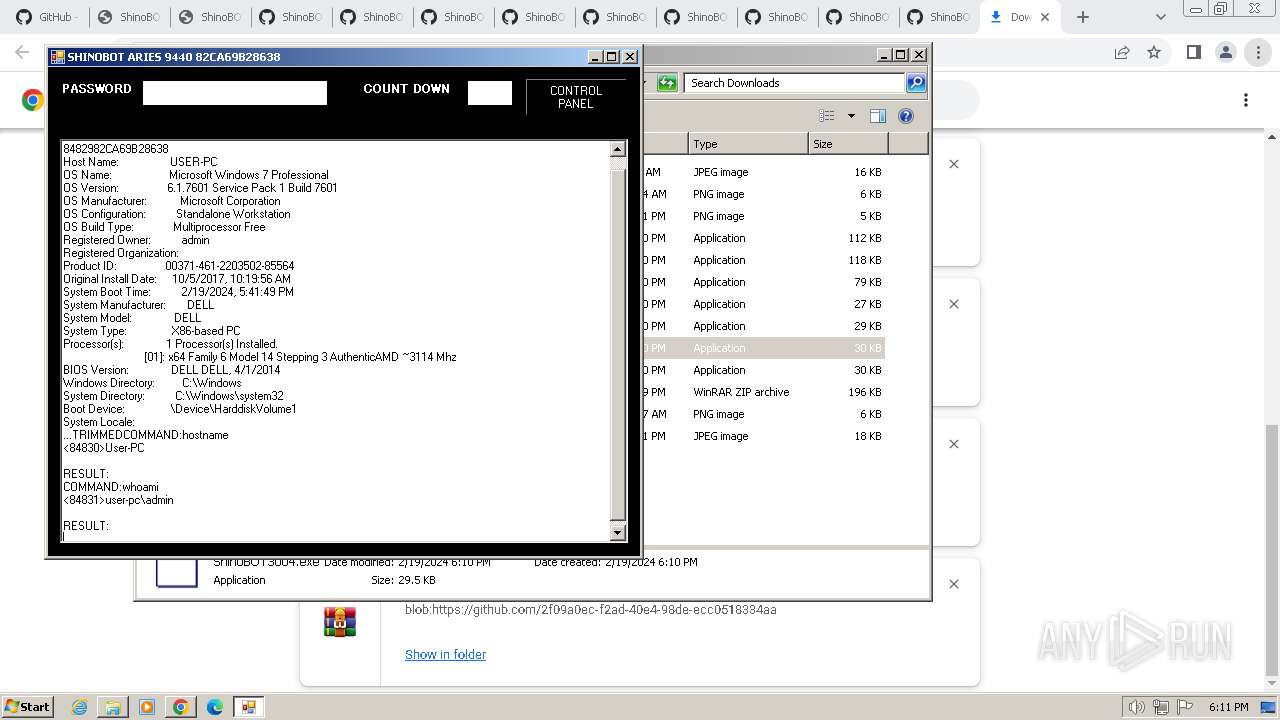
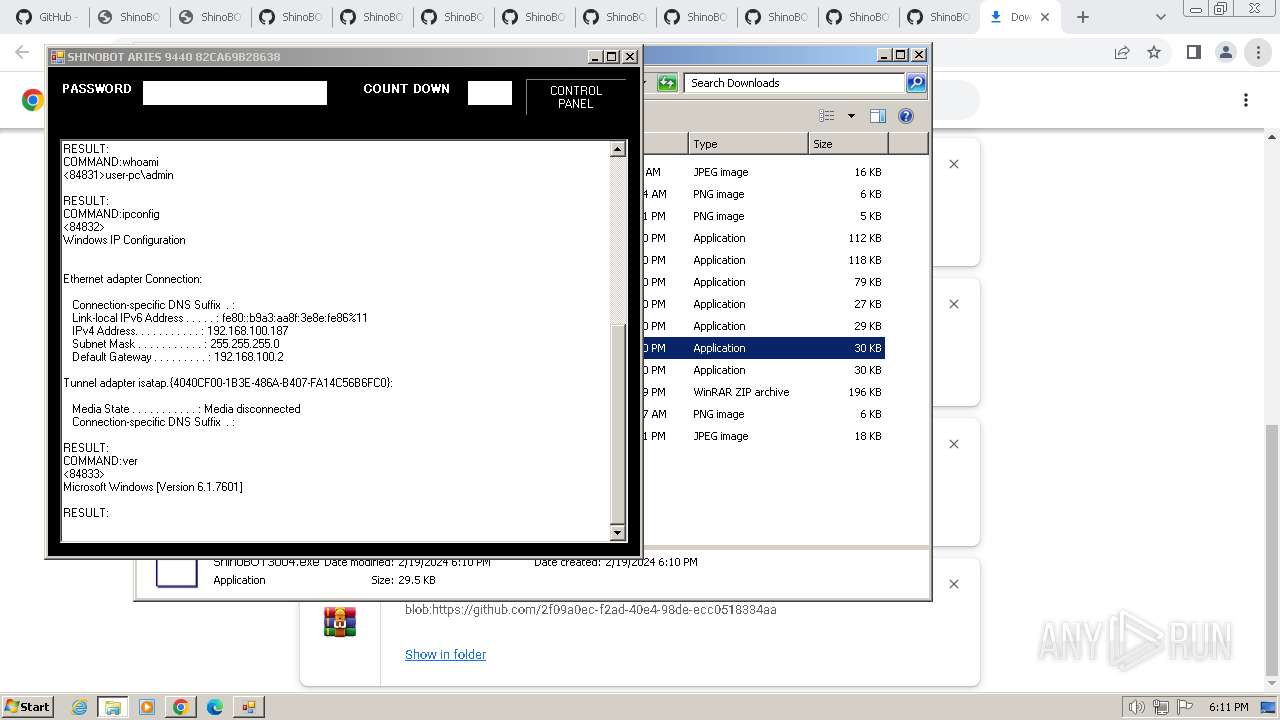
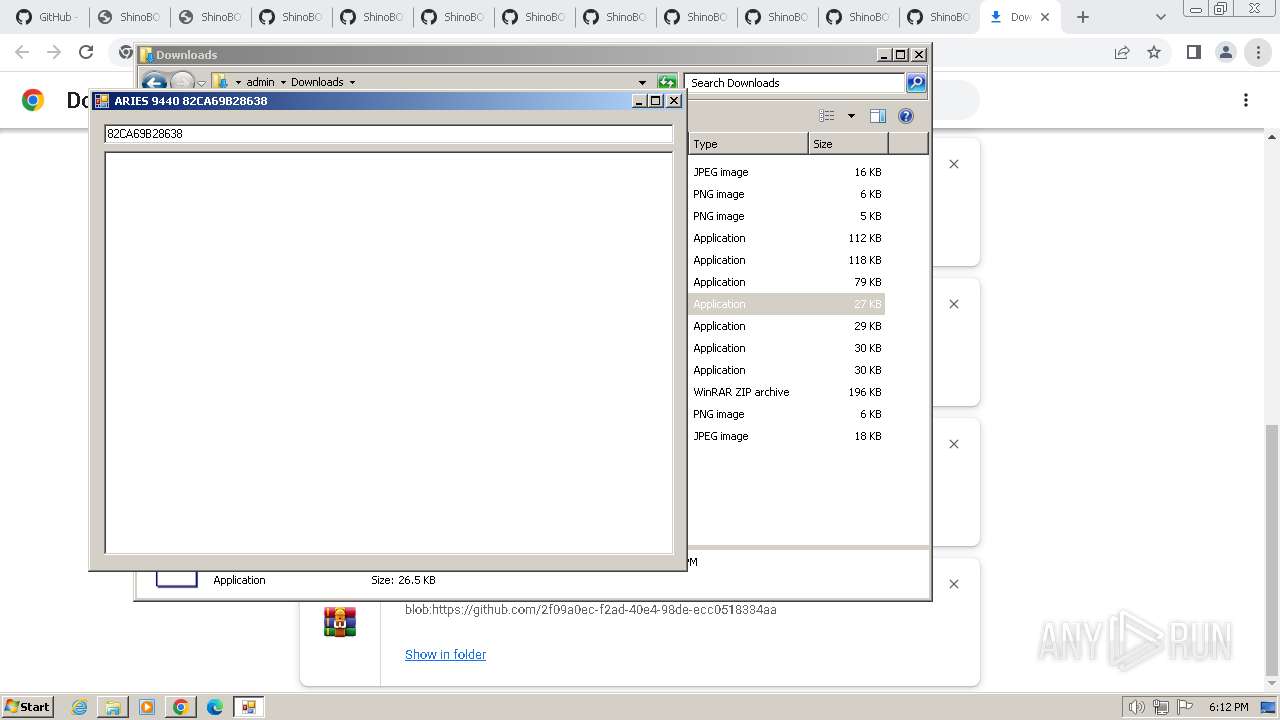
Identifying current user with WHOAMI command
- cmd.exe (PID: 1588)
Starts CMD.EXE for commands execution
- ShinoBOT3004.exe (PID: 3496)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1548)
Process uses IPCONFIG to get network configuration information
- cmd.exe (PID: 3808)
INFO
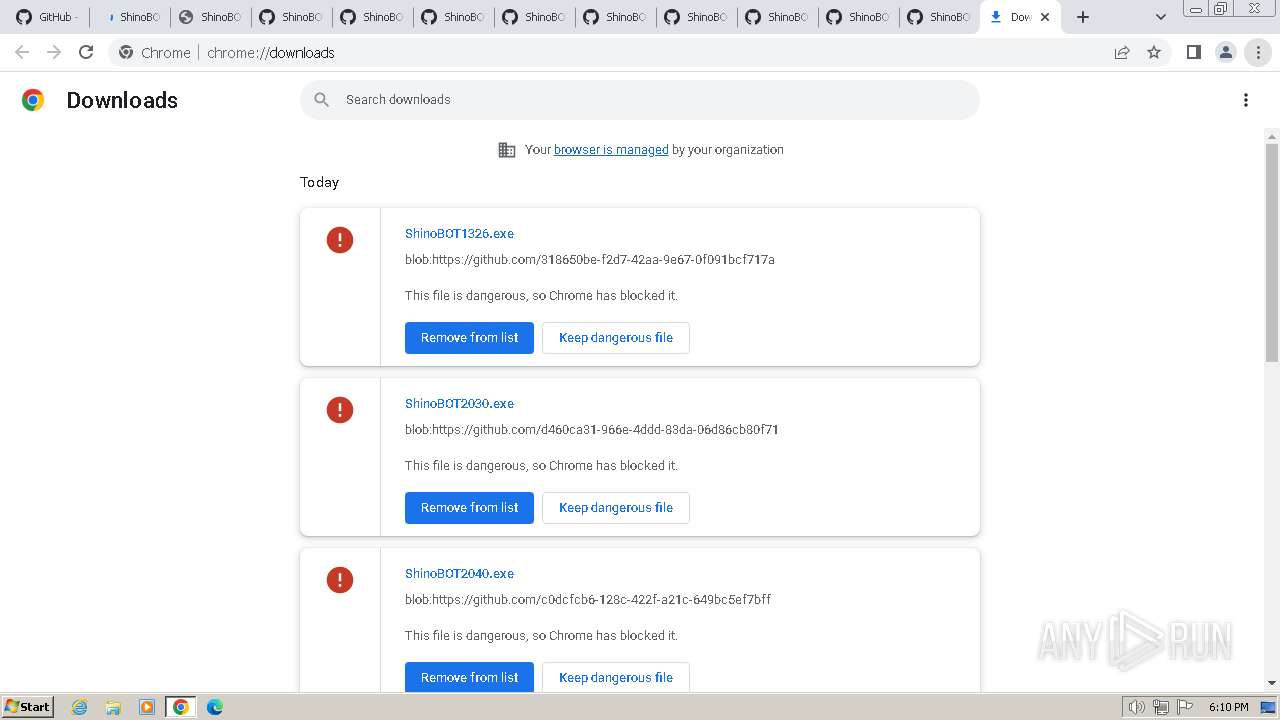
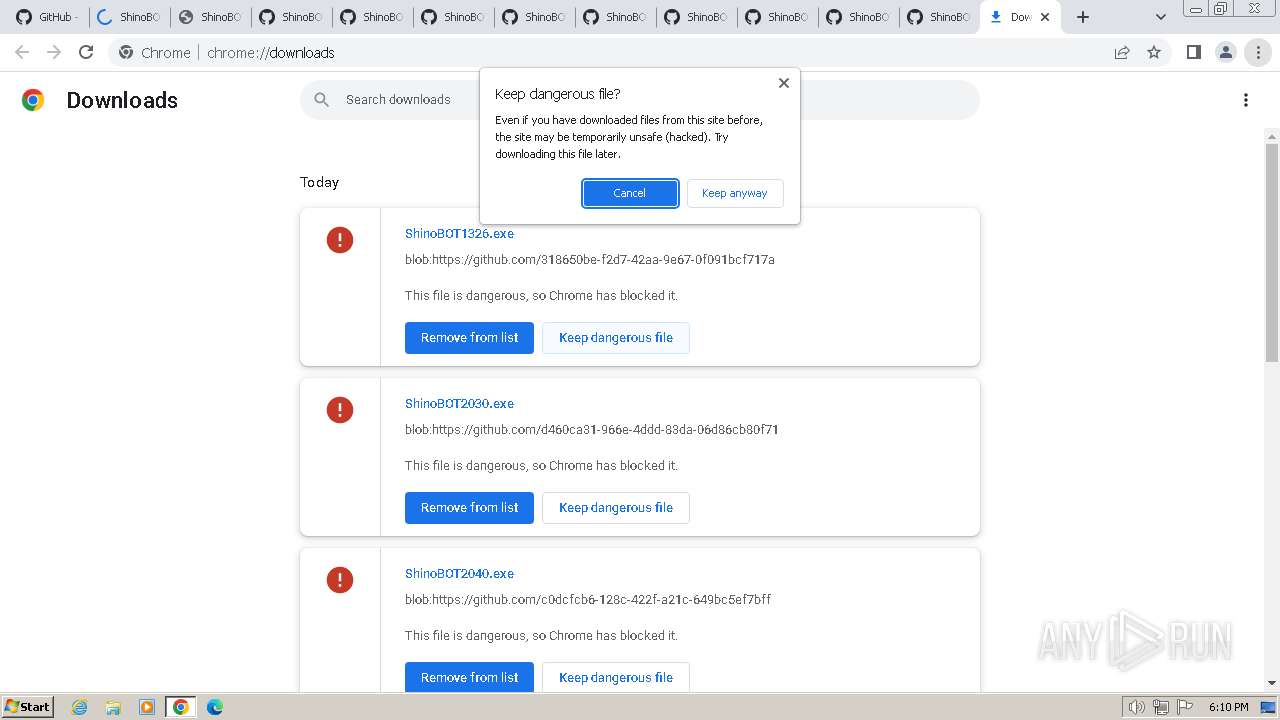
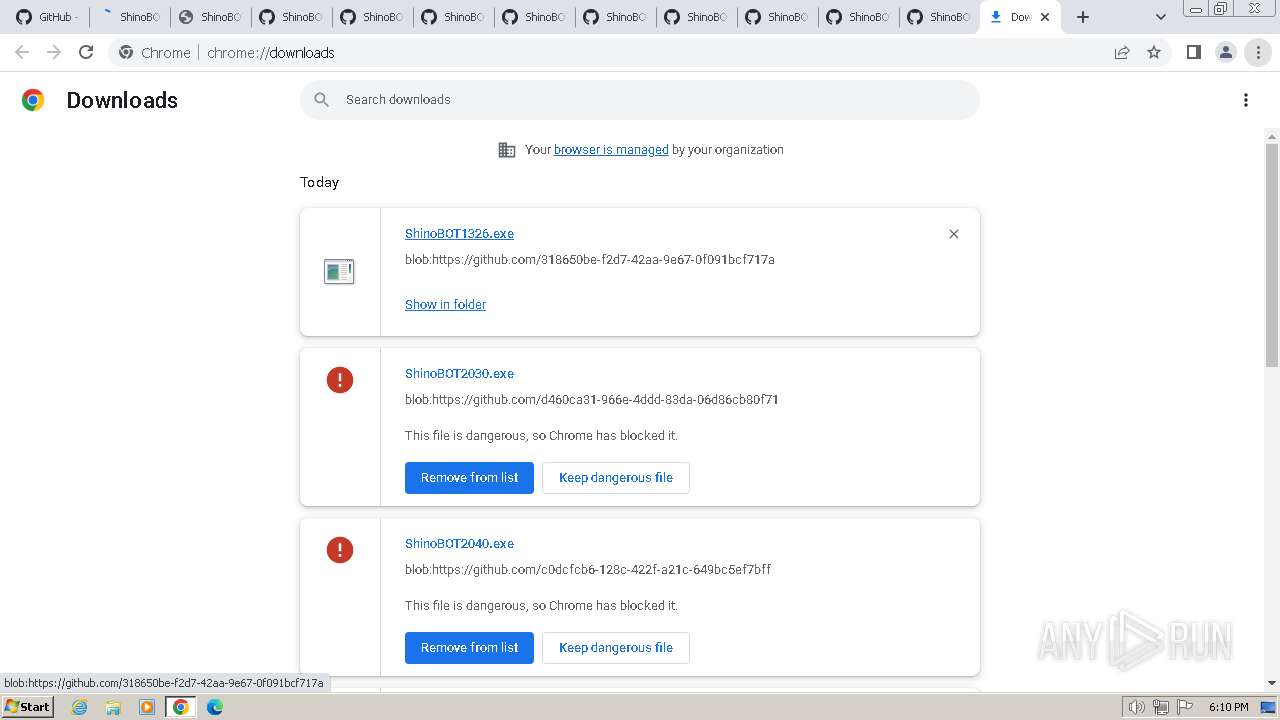
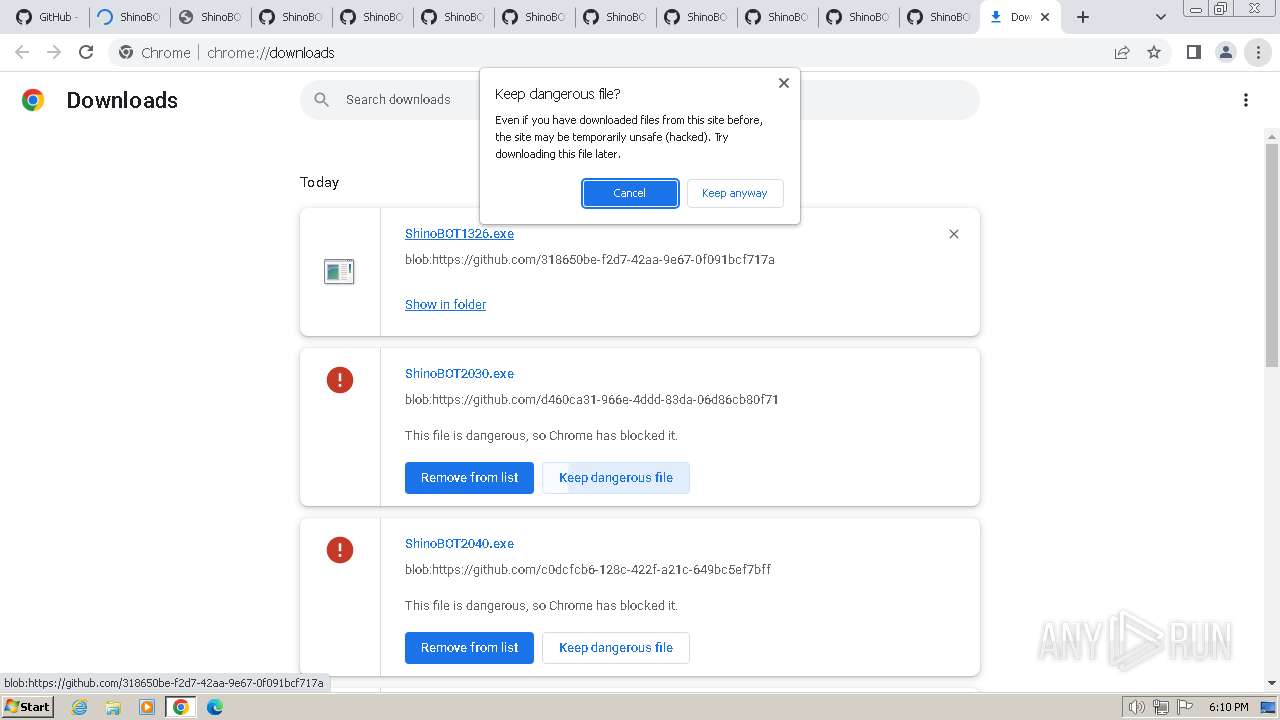
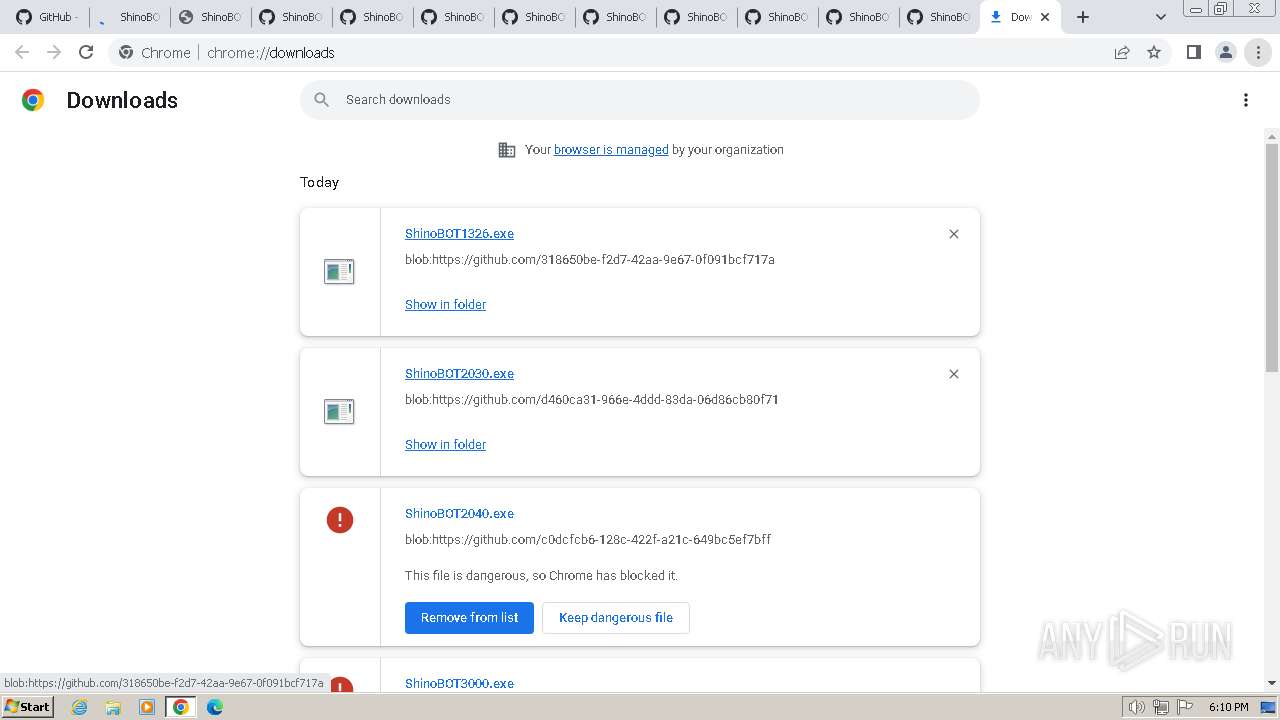
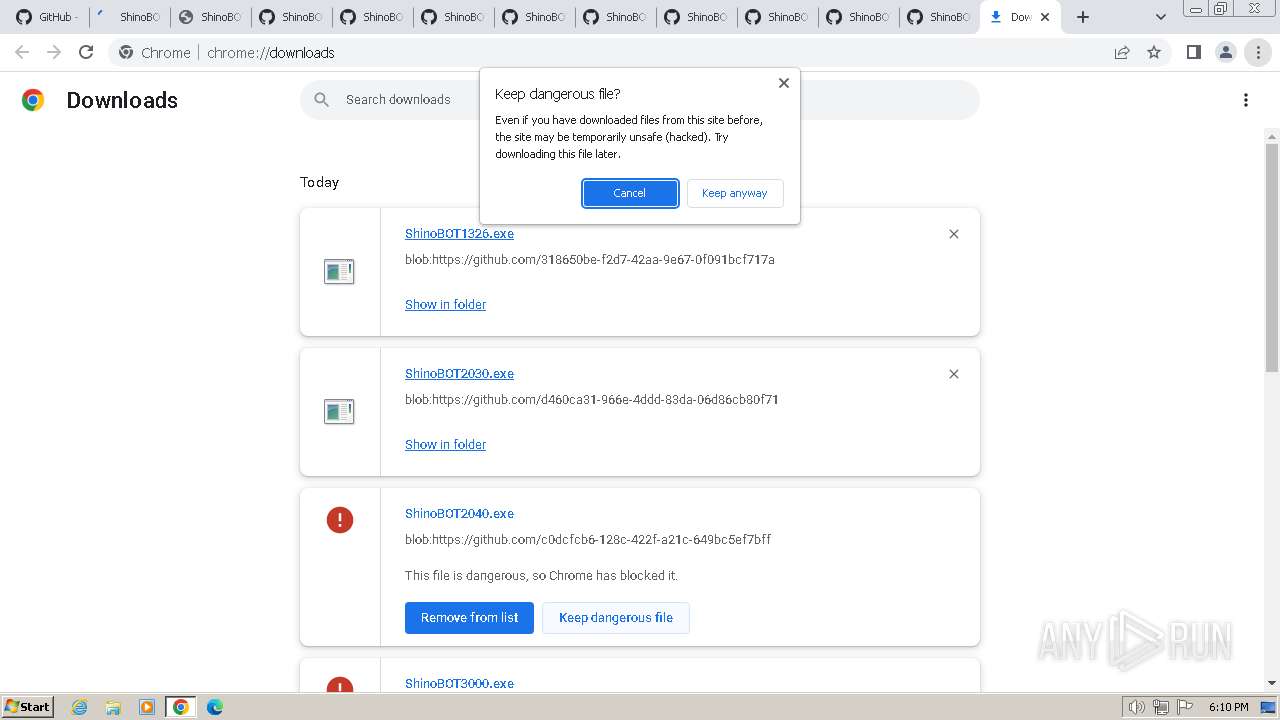
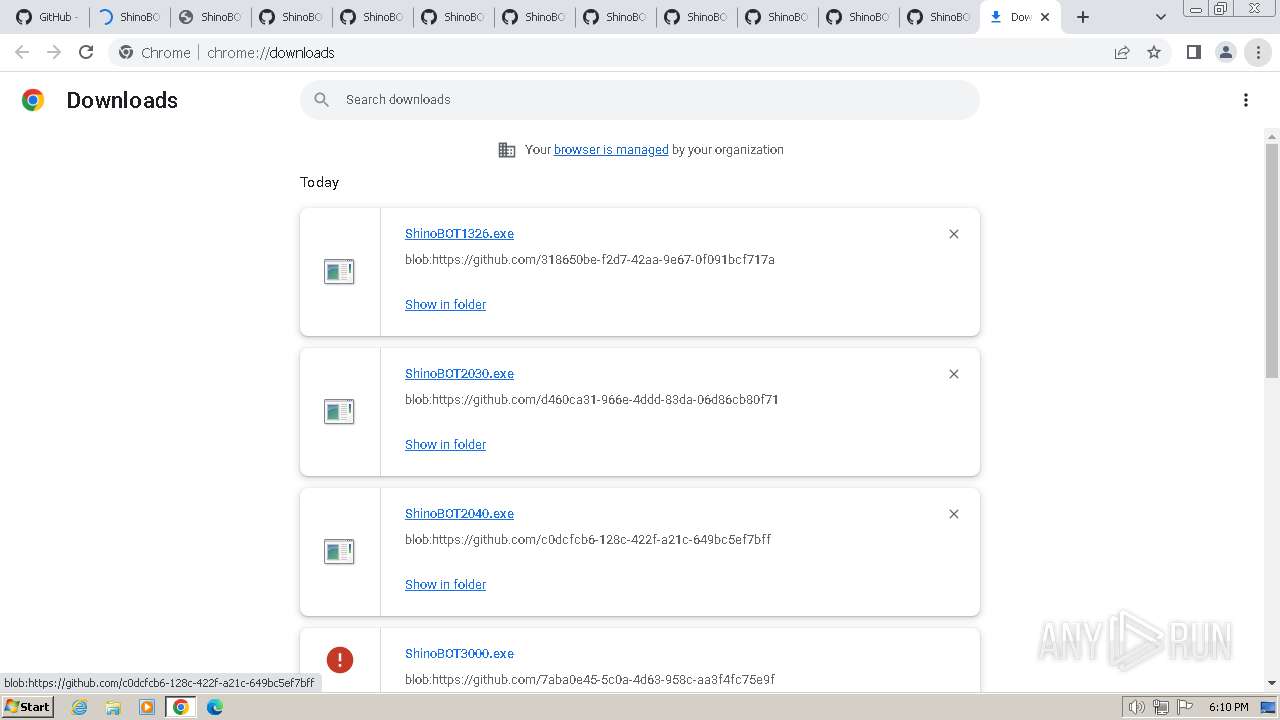
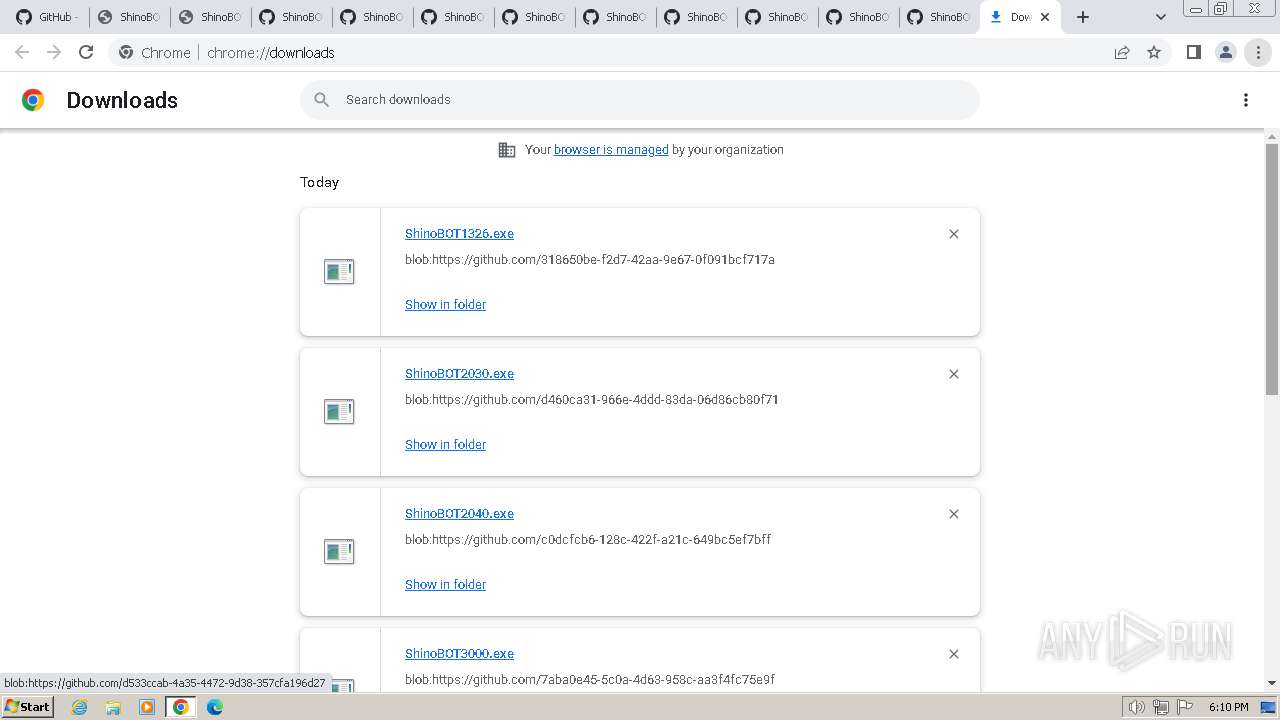
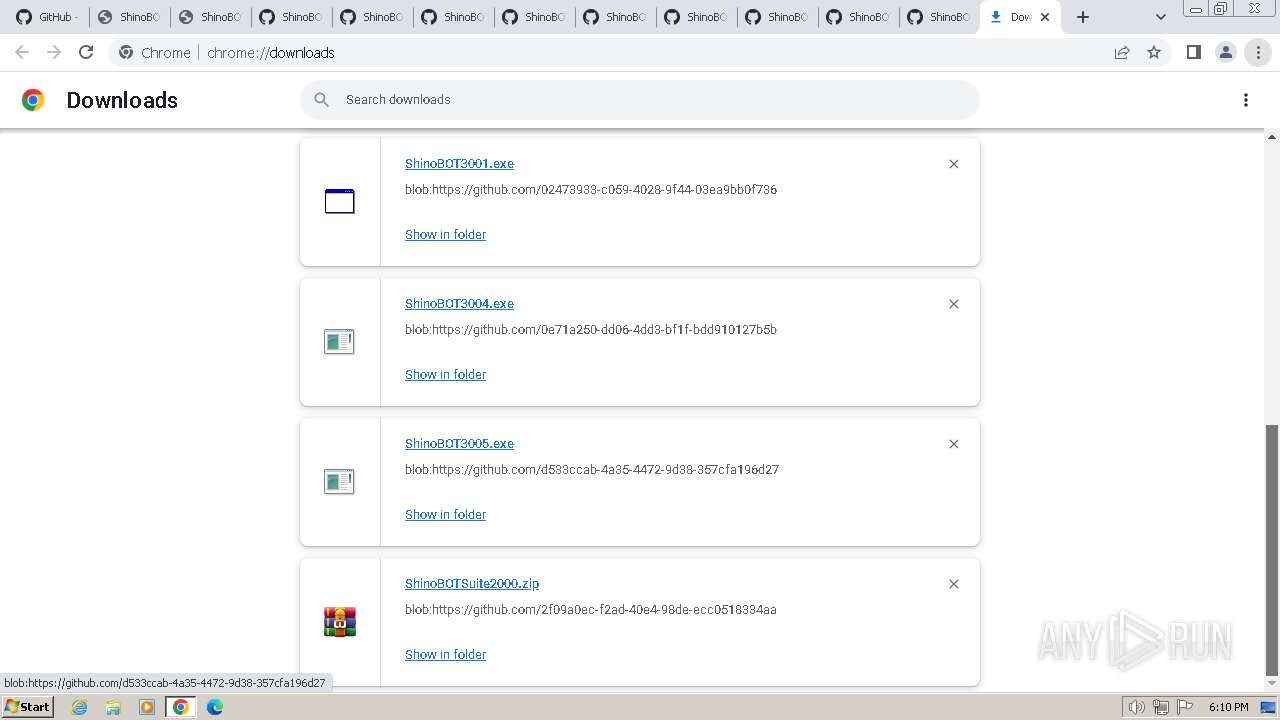
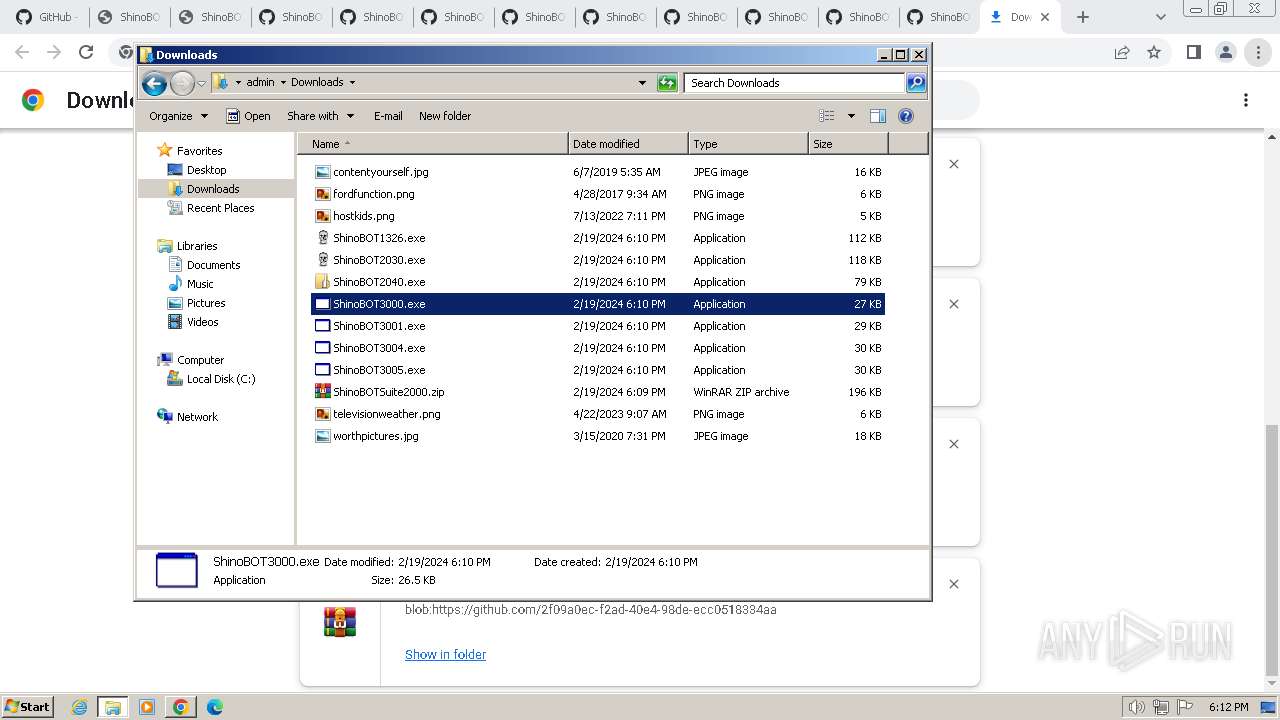
Drops the executable file immediately after the start
- chrome.exe (PID: 1404)
- chrome.exe (PID: 2160)
The process uses the downloaded file
- chrome.exe (PID: 3836)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 2348)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 1972)
- chrome.exe (PID: 296)
- chrome.exe (PID: 1852)
- chrome.exe (PID: 3120)
Executable content was dropped or overwritten
- chrome.exe (PID: 2160)
- chrome.exe (PID: 1404)
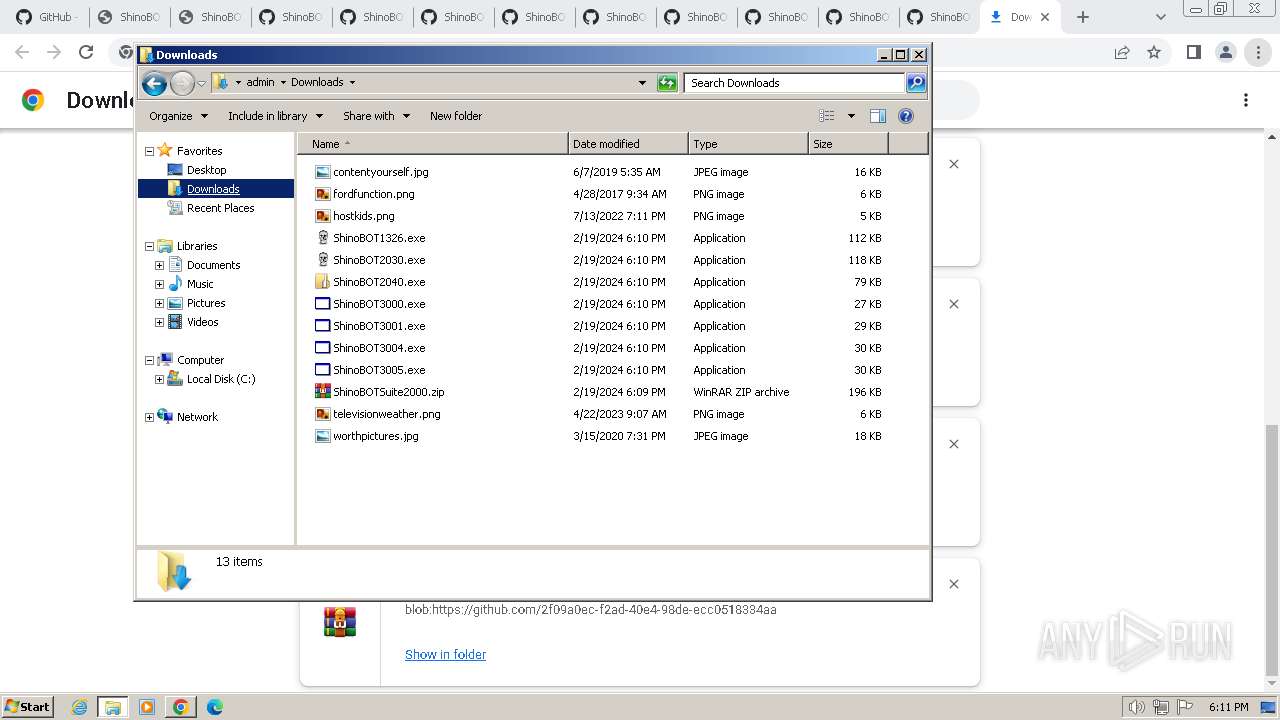
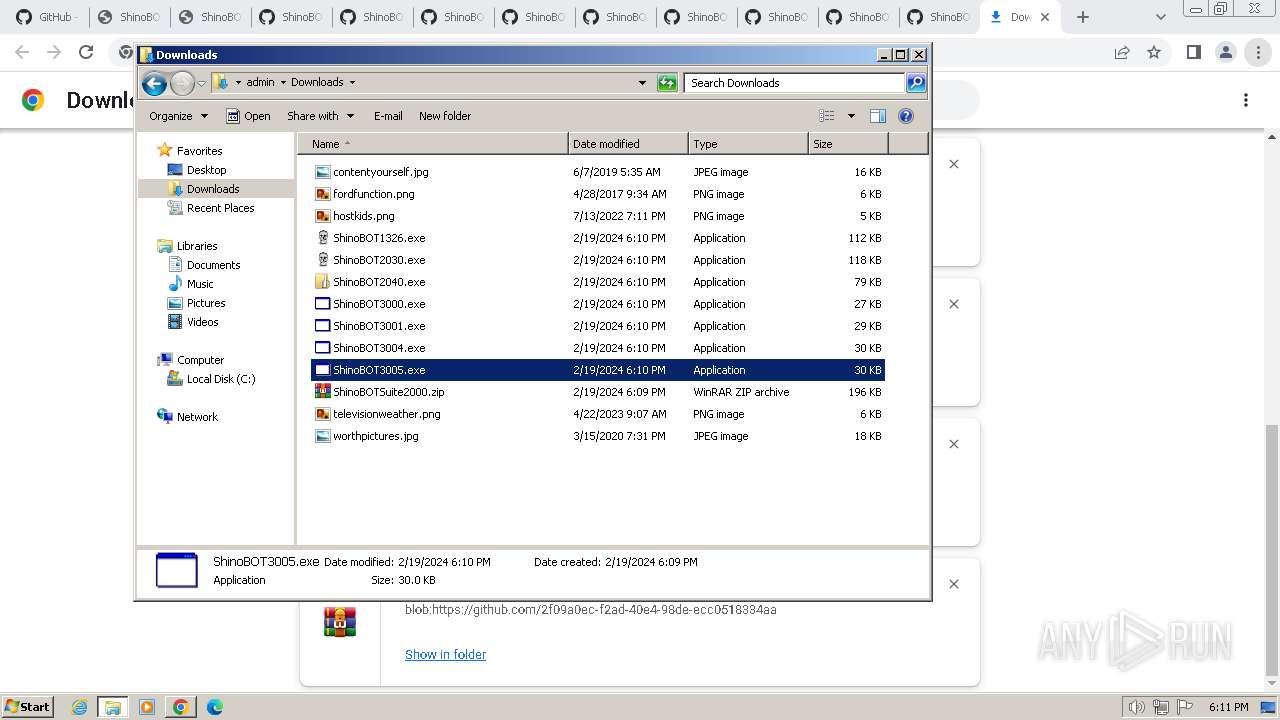
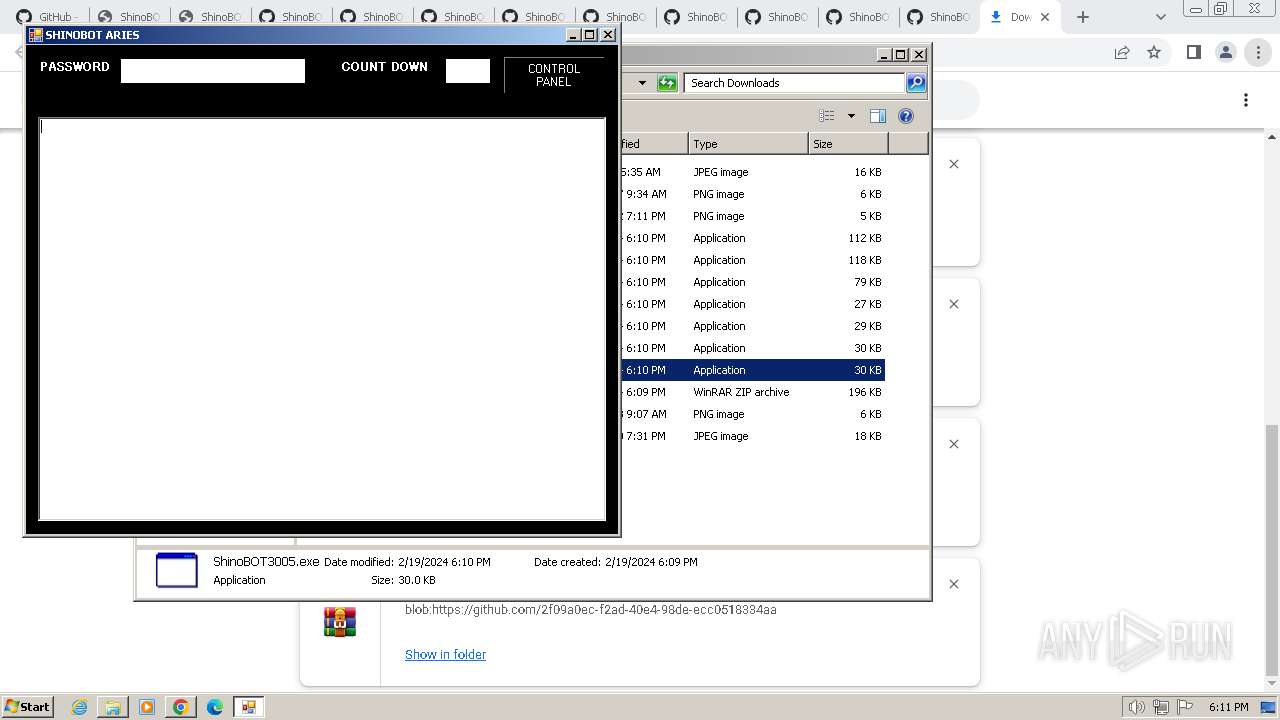
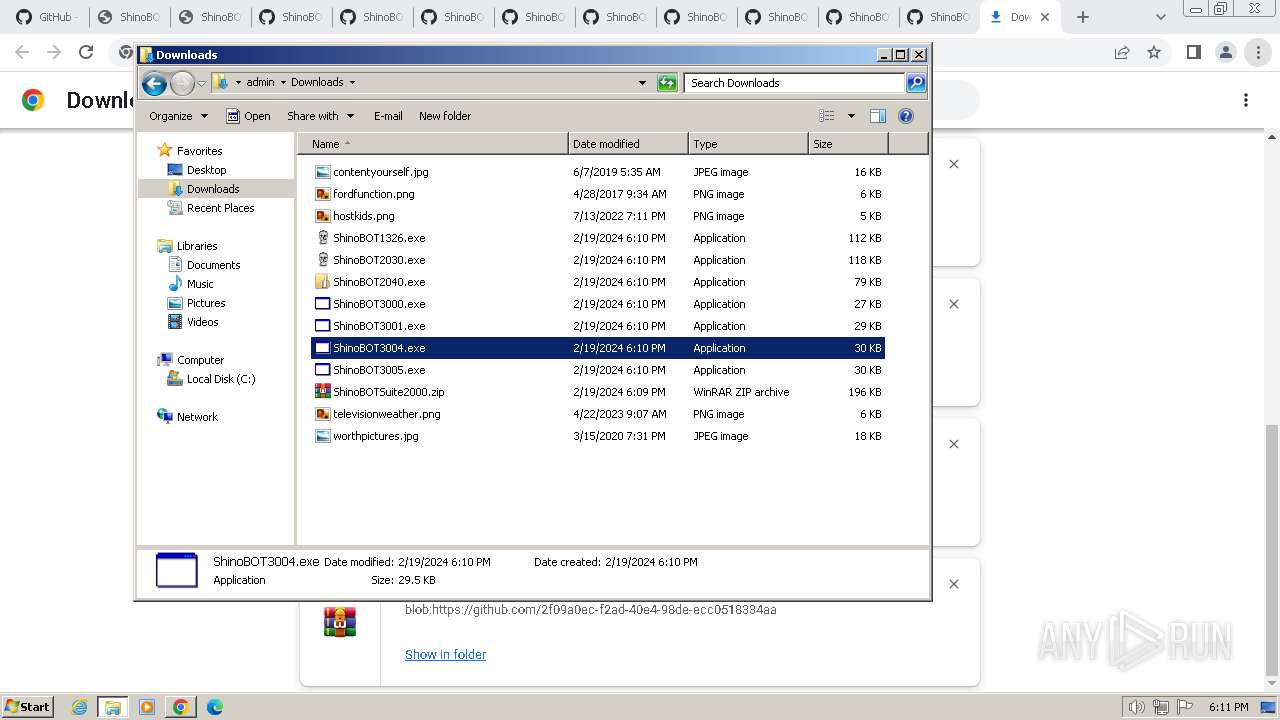
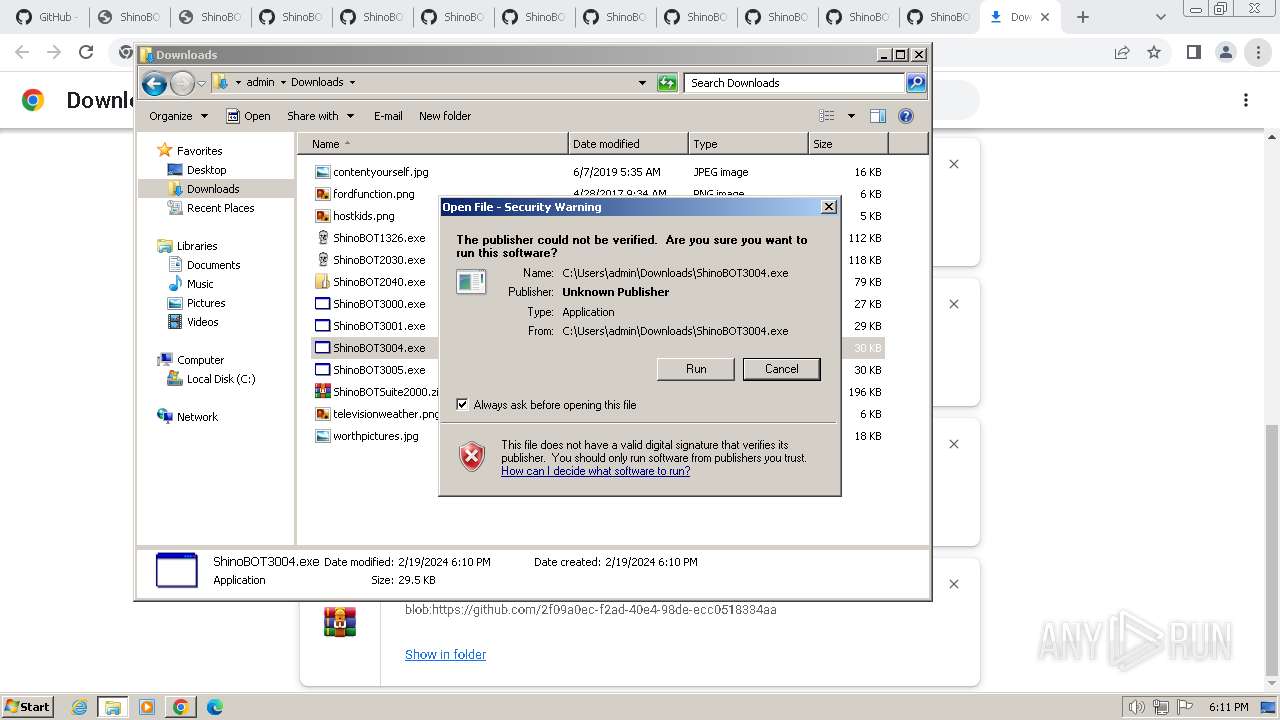
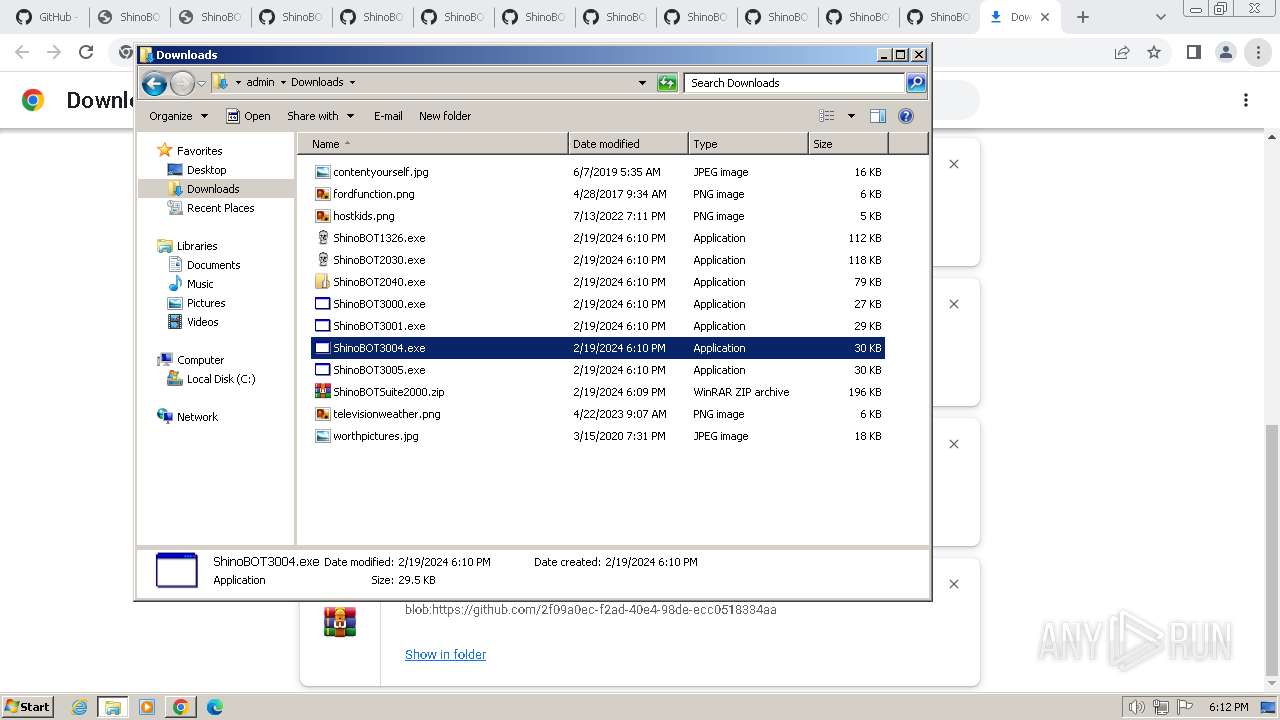
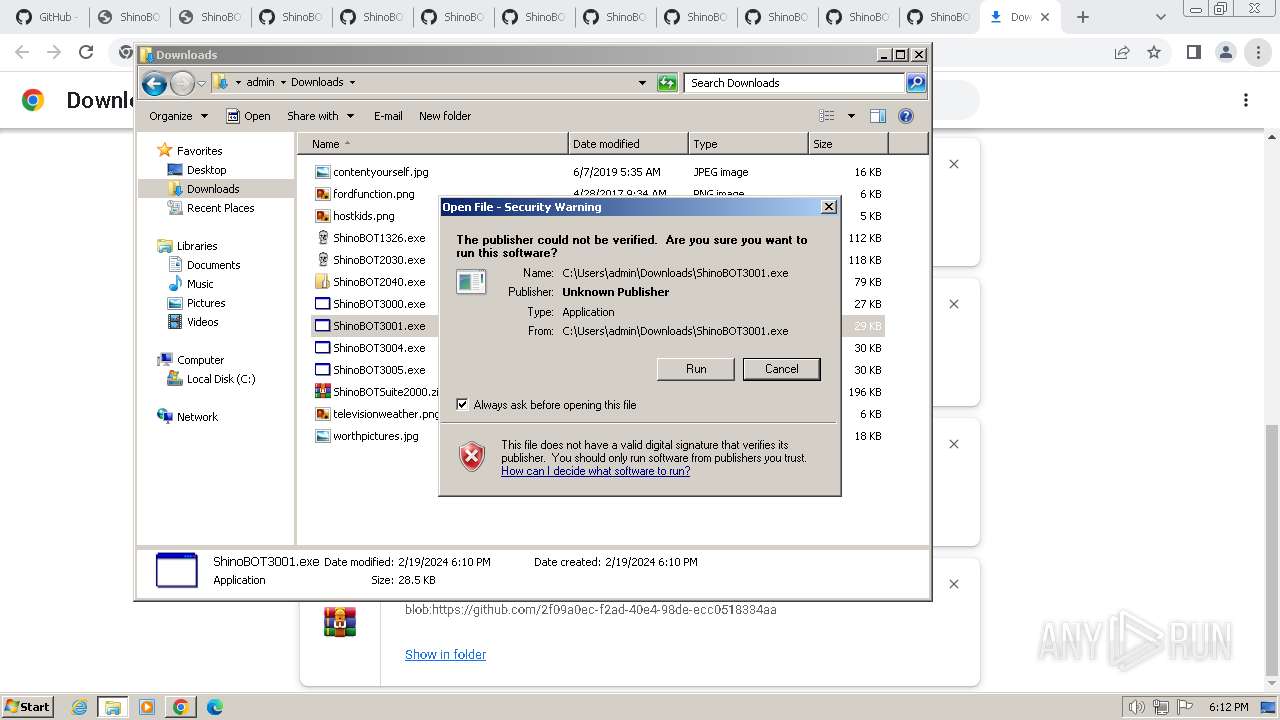
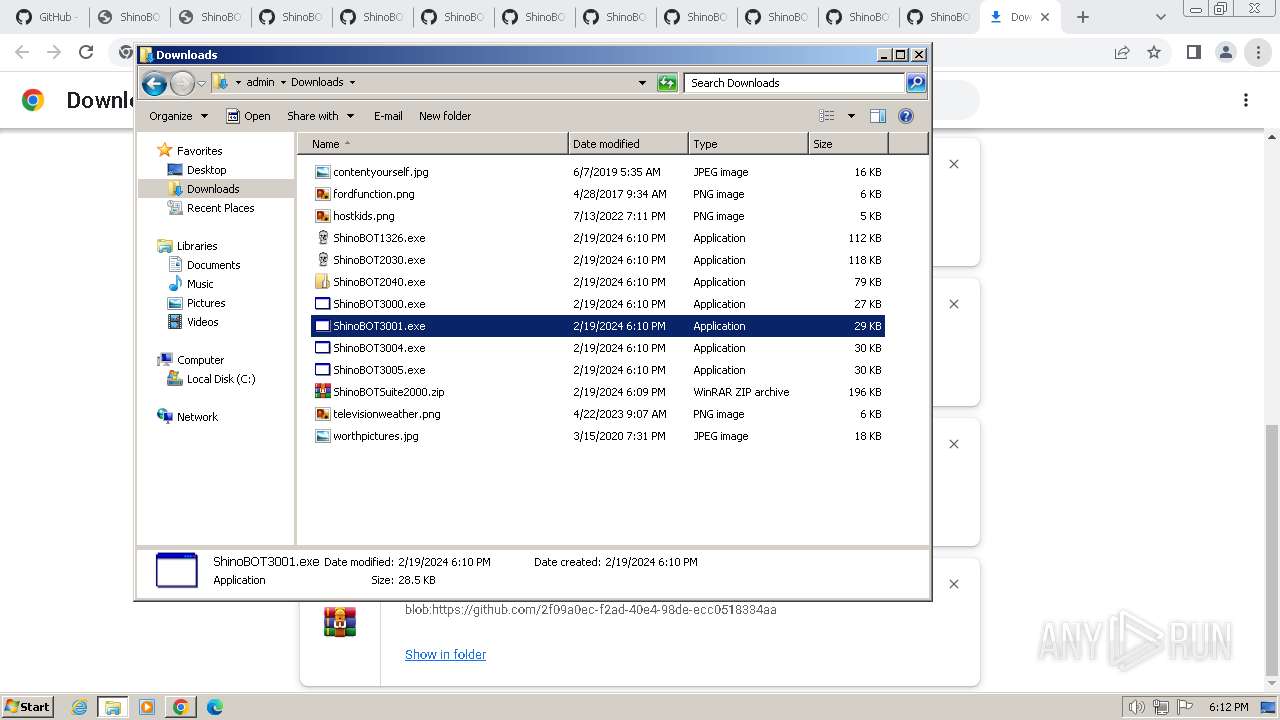
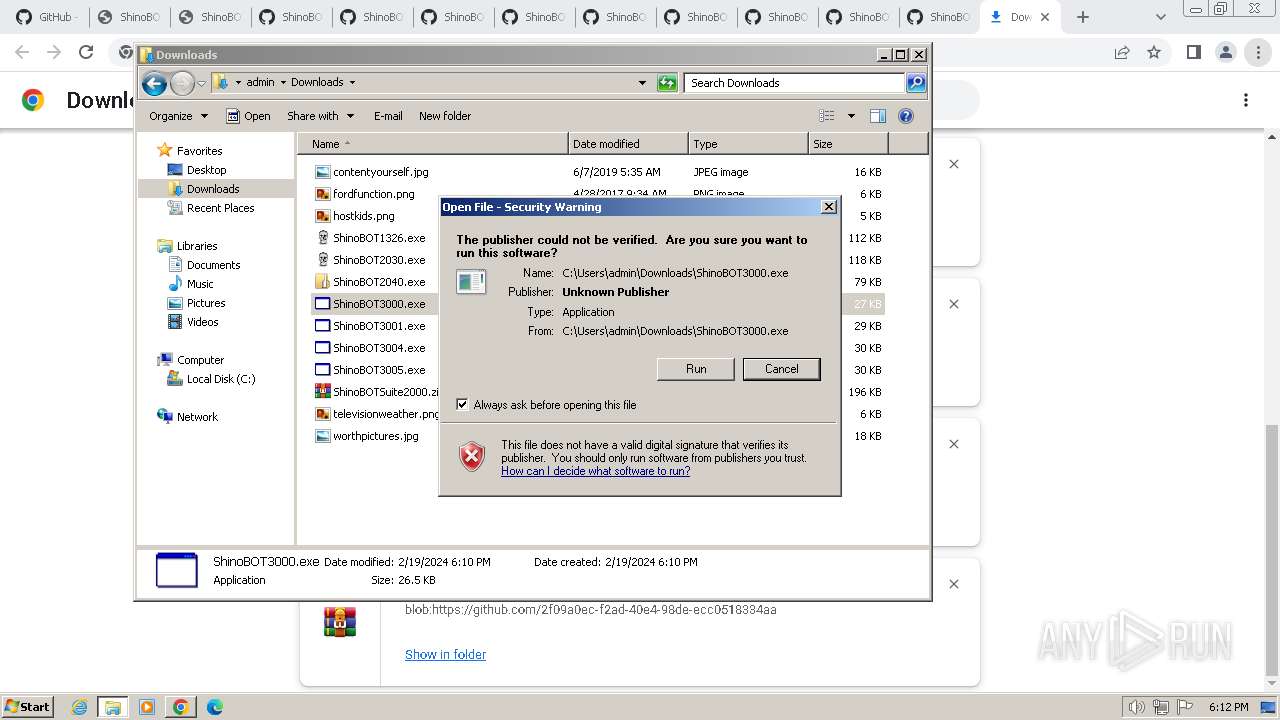
Manual execution by a user
- ShinoBOT3005.exe (PID: 2548)
- explorer.exe (PID: 1936)
- ShinoBOT3004.exe (PID: 3496)
- ShinoBOT3001.exe (PID: 3200)
- ShinoBOT3000.exe (PID: 2916)
Checks supported languages
- ShinoBOT3005.exe (PID: 2548)
- ShinoBOT3004.exe (PID: 3496)
- ShinoBOT3001.exe (PID: 3200)
- ShinoBOT3000.exe (PID: 2916)
Reads the computer name
- ShinoBOT3005.exe (PID: 2548)
- ShinoBOT3004.exe (PID: 3496)
- ShinoBOT3001.exe (PID: 3200)
- ShinoBOT3000.exe (PID: 2916)
Reads the machine GUID from the registry
- ShinoBOT3005.exe (PID: 2548)
- ShinoBOT3004.exe (PID: 3496)
- ShinoBOT3001.exe (PID: 3200)
- ShinoBOT3000.exe (PID: 2916)
Reads Environment values
- ShinoBOT3005.exe (PID: 2548)
- ShinoBOT3001.exe (PID: 3200)
- ShinoBOT3004.exe (PID: 3496)
- ShinoBOT3000.exe (PID: 2916)
Application launched itself
- chrome.exe (PID: 2160)
Checks operating system version
- ShinoBOT3004.exe (PID: 3496)
Create files in a temporary directory
- ShinoBOT3004.exe (PID: 3496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
143
Monitored processes
87
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=5660 --field-trial-handle=1172,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=5664 --field-trial-handle=1172,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=4272 --field-trial-handle=1172,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=5596 --field-trial-handle=1172,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=6052 --field-trial-handle=1172,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=3508 --field-trial-handle=1172,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=5416 --field-trial-handle=1172,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=5636 --field-trial-handle=1172,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=5596 --field-trial-handle=1172,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=5880 --field-trial-handle=1172,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
22 797
Read events
22 531
Write events
233
Delete events
33
Modification events
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
24
Suspicious files
311
Text files
90
Unknown types
71
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f7dd.TMP | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17f7dd.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17feb3.TMP | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c51c3f4e-8a0f-4d9f-84c4-3084a53613f5.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF180fca.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
98
DNS requests
132
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
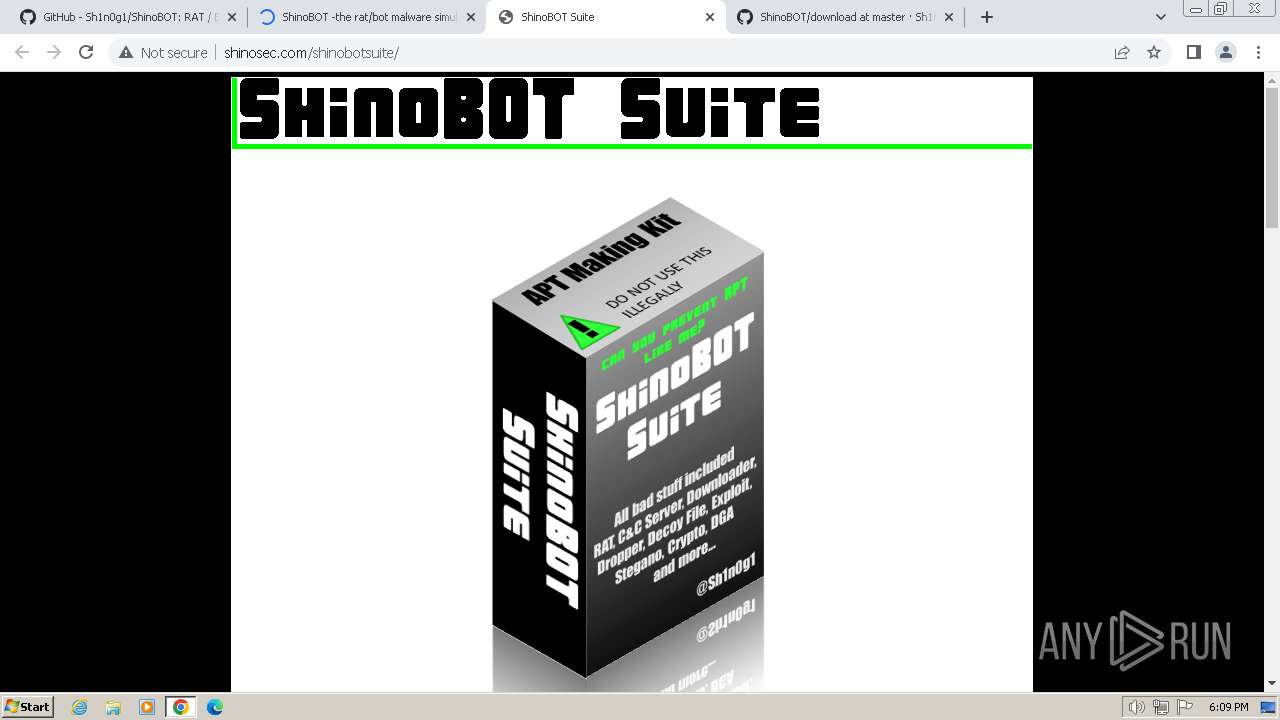
1492 | chrome.exe | GET | 200 | 128.199.83.111:80 | http://shinosec.com/shinobuilder/shinobot/ | unknown | html | 925 b | unknown |
1492 | chrome.exe | GET | 200 | 104.248.158.253:80 | http://shinobot.com/res/uc.ttf | unknown | binary | 27.7 Kb | unknown |
1492 | chrome.exe | GET | 200 | 104.248.158.253:80 | http://shinobot.com/res/icon_small_download.png | unknown | image | 940 b | unknown |
1492 | chrome.exe | GET | 200 | 142.250.185.174:80 | http://www.google-analytics.com/analytics.js | unknown | text | 20.5 Kb | unknown |
1492 | chrome.exe | GET | 200 | 104.248.158.253:80 | http://shinobot.com/downloads.php | unknown | html | 1.44 Kb | unknown |
1492 | chrome.exe | GET | 200 | 104.248.158.253:80 | http://shinobot.com/res/main.css | unknown | text | 1.69 Kb | unknown |
1492 | chrome.exe | GET | 200 | 104.248.158.253:80 | http://shinobot.com/res/jquery-1.11.2.min.js | unknown | text | 32.5 Kb | unknown |
1492 | chrome.exe | GET | 200 | 104.248.158.253:80 | http://shinobot.com/res/icon_small_home.png | unknown | image | 876 b | unknown |
1492 | chrome.exe | GET | — | 128.199.83.111:80 | http://shinosec.com/shinobotsuite/main.css | unknown | — | — | unknown |
1492 | chrome.exe | GET | 200 | 128.199.83.111:80 | http://shinosec.com/shinobotsuite/ | unknown | html | 1.18 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1492 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
2160 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1492 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
1492 | chrome.exe | 185.199.111.154:443 | github.githubassets.com | FASTLY | US | unknown |
1492 | chrome.exe | 142.250.185.74:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
1492 | chrome.exe | 185.199.109.133:443 | avatars.githubusercontent.com | FASTLY | US | unknown |
1492 | chrome.exe | 185.199.110.133:443 | avatars.githubusercontent.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
github.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
camo.githubusercontent.com |
| shared |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
collector.github.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report