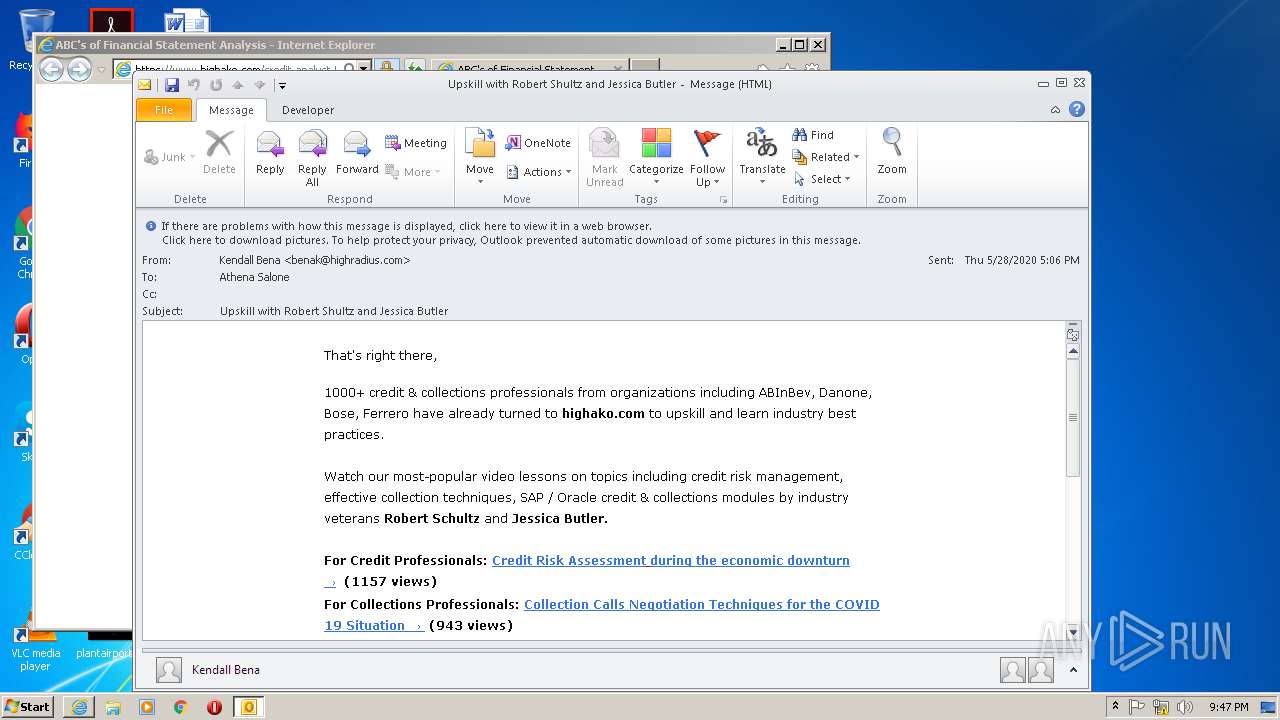
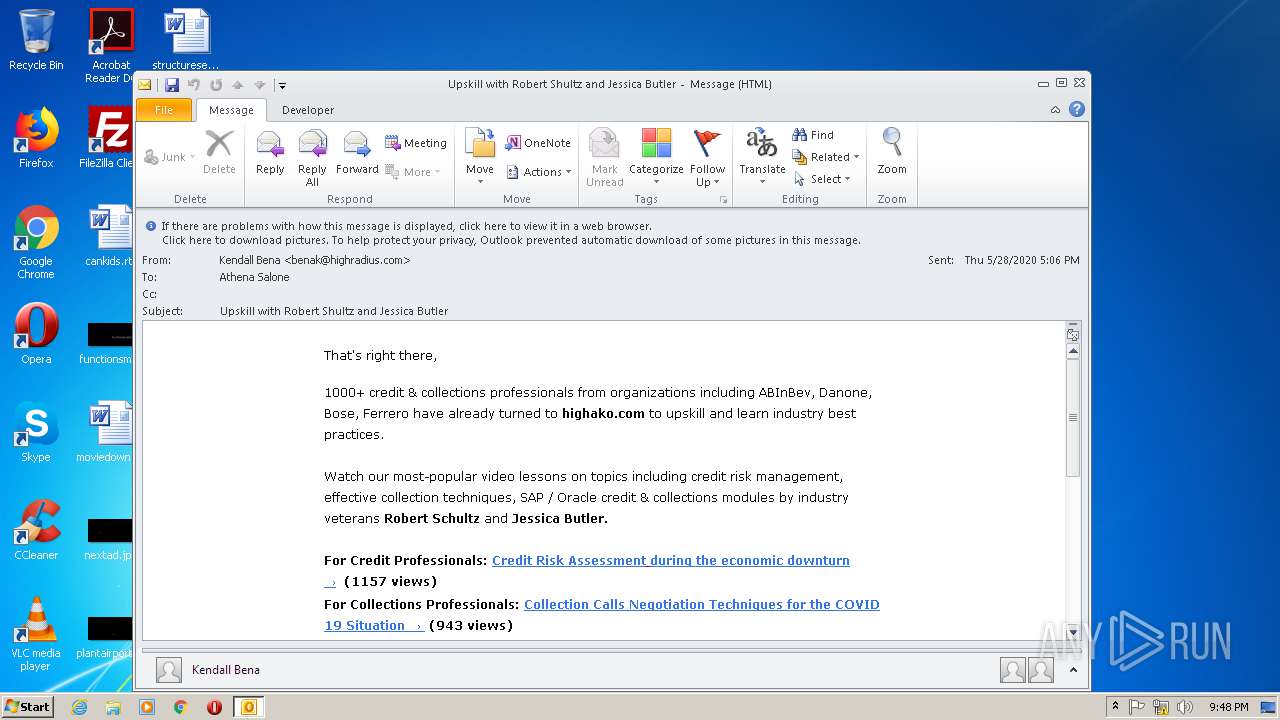
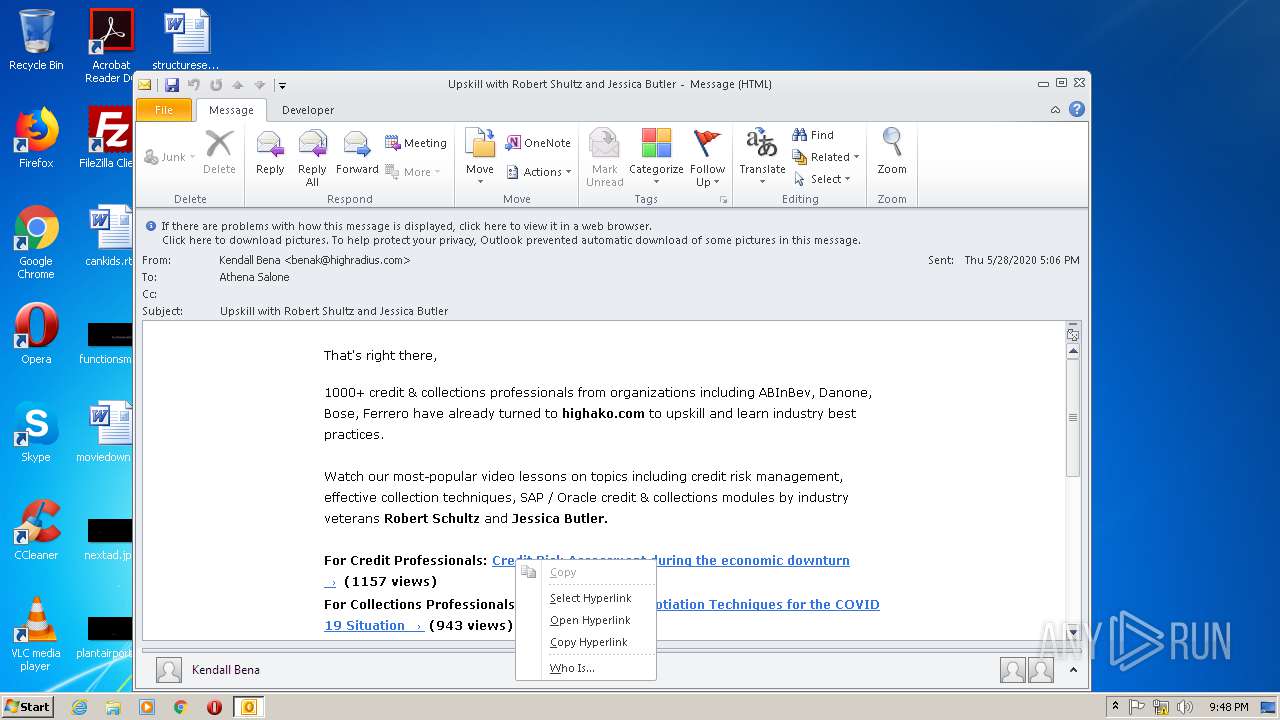
| File name: | Upskill with Robert Shultz and Jessica Butler.msg |
| Full analysis: | https://app.any.run/tasks/79e716b0-365a-48f1-a12b-e7f550032591 |
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2020, 20:46:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | C512EA36596DFB996AD7B487CF9534B0 |
| SHA1: | 433B734F5FA147B4A16389481BFF326E771A6401 |
| SHA256: | 8BB11E4B2E70B956445C4E84FA686879DCE9B7CC79FF13D1089A6752B679860D |
| SSDEEP: | 1536:rbu89tz4FTcKAuUClnRNKwpS2ZLndkk3N3v905HSp3c:rbu89t8BALCfYOZak3N3F4S |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2792)
SUSPICIOUS
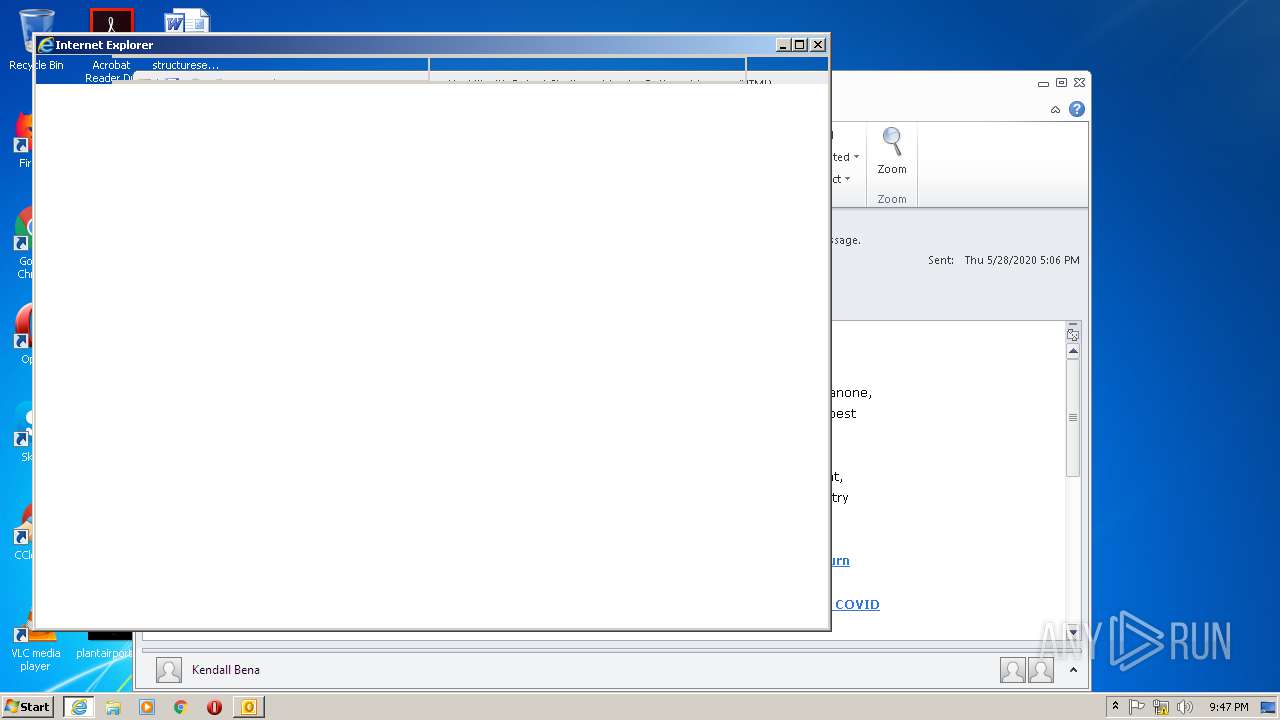
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2792)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2792)
INFO
Creates files in the user directory
- iexplore.exe (PID: 3840)
- iexplore.exe (PID: 2464)
- iexplore.exe (PID: 3180)
- iexplore.exe (PID: 4008)
Reads internet explorer settings
- iexplore.exe (PID: 3840)
- iexplore.exe (PID: 2464)
- iexplore.exe (PID: 4008)
- iexplore.exe (PID: 2160)
Changes internet zones settings
- iexplore.exe (PID: 3180)
Reads Internet Cache Settings
- iexplore.exe (PID: 3180)
- iexplore.exe (PID: 3840)
- iexplore.exe (PID: 4008)
- iexplore.exe (PID: 2464)
- iexplore.exe (PID: 2160)
- OUTLOOK.EXE (PID: 2792)
Application launched itself
- iexplore.exe (PID: 3180)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2792)
Reads settings of System Certificates
- iexplore.exe (PID: 3840)
- iexplore.exe (PID: 3180)
- iexplore.exe (PID: 4008)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3180)
Changes settings of System certificates
- iexplore.exe (PID: 3180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
42
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2160 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3180 CREDAT:4003103 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3180 CREDAT:3478817 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2792 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Upskill with Robert Shultz and Jessica Butler.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
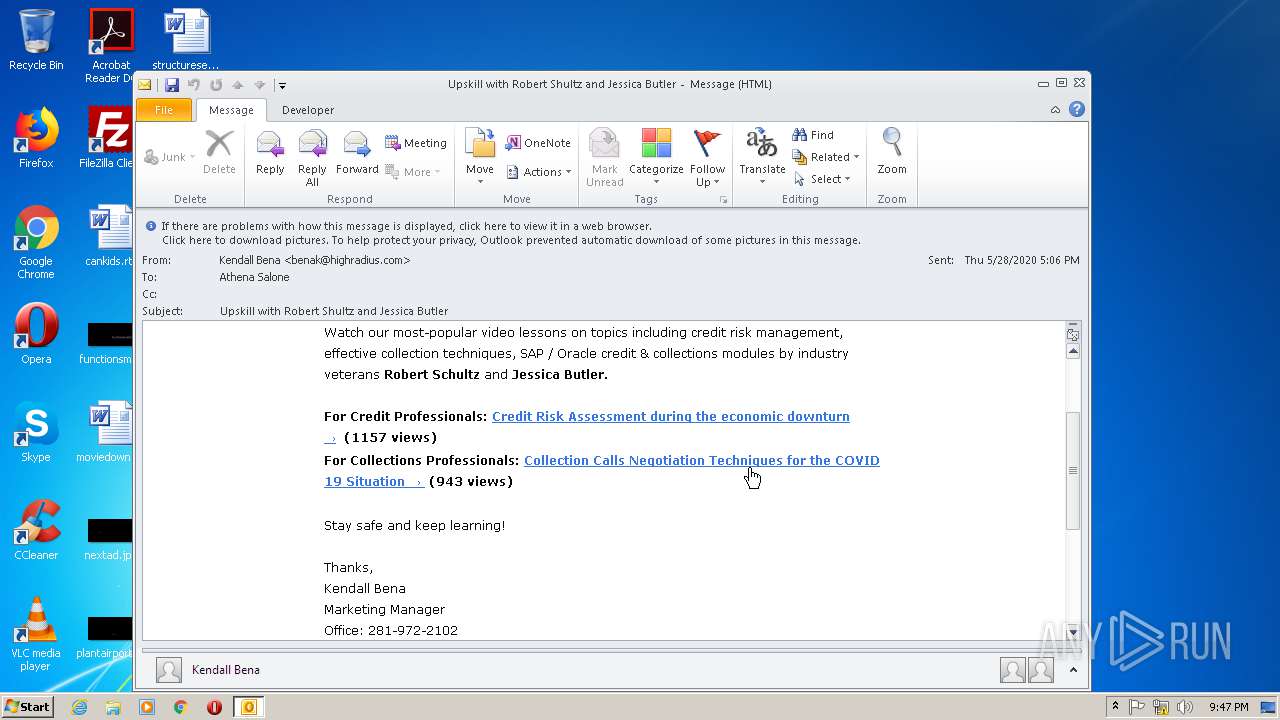
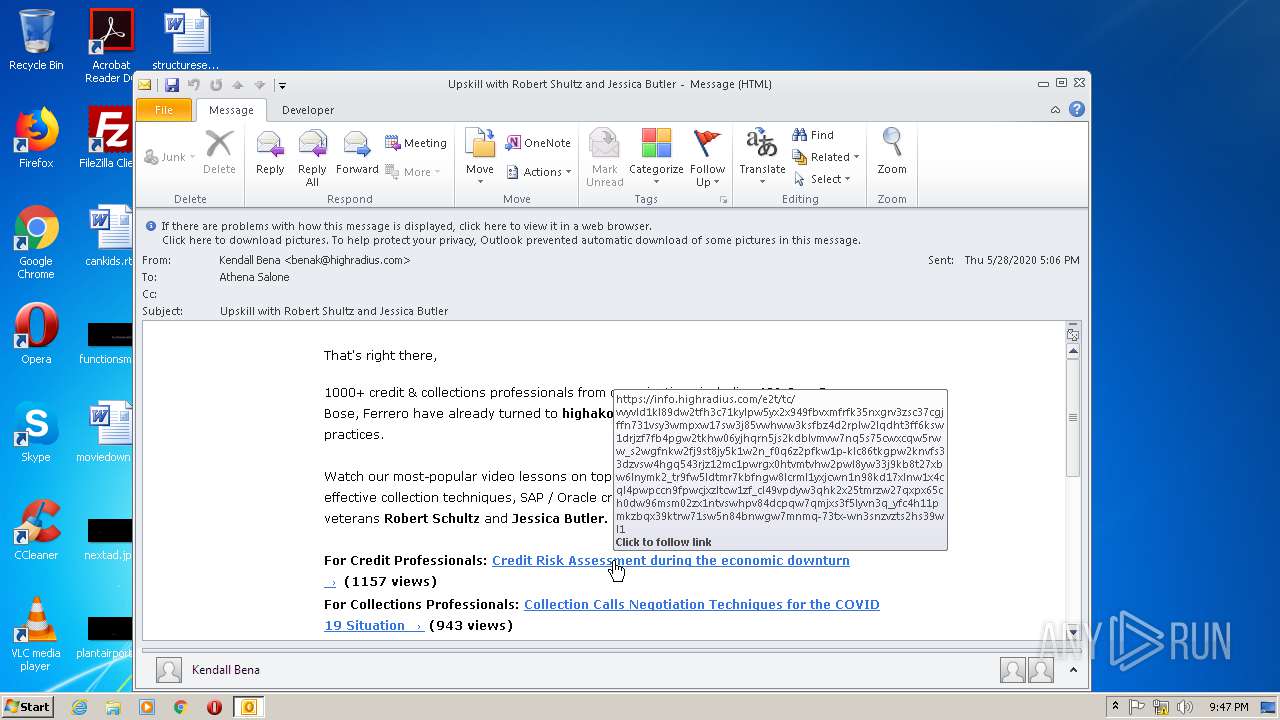
| 3180 | "C:\Program Files\Internet Explorer\iexplore.exe" https://info.highradius.com/e2t/tc/VVyVLD1kl89DW2tFH3C71KYlPW5yX2x949FBvXMfRfk35nxGrV3Zsc37CgJFFN731VSY3WmPXW17sW3j85vwhwW3KsfBz4d2rplW2LQDhT3Ff6kSW1DRJZF7FB4PGW2tKHW06YJHQRN5Js2KdblvMVW7nq5S75CwxCQW5rww_s2wgFNKW2fj9St8JY5k1W2n_F0Q6z2pfKW1P-klC86TkgpW2KnvfS33DzvSW4Hgq543rJZ12Mc1PWRgX0htVMtVhw2pWl8yW33j9kB8T27xBW6LNYMK2_TR9fW5LdtMR7KBfngW8LCrmL1YXJCWN1n98Kd17XlnW1X4Cql4pwPcCN9fPWcJXzLtCW1zf_Cl49VPDYW3qhk2x25tmRZW27QxPX65cH0DW96msM02zx1nTVSwhPv84dcpQW7QMjXs3F5lyvN3q_yFc4H11PMkZbqx39KtRW71SW5n84BnWgW7MNMq-73tX-wN3sNzVzTS2hs39Wl1 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3840 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3180 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4008 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3180 CREDAT:4134184 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
9 903
Read events
2 312
Write events
5 850
Delete events
1 741
Modification events
| (PID) Process: | (2792) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2792) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2792) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2792) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2792) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2792) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2792) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2792) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2792) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2792) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
78
Text files
732
Unknown types
79
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2792 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRCB3D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2573.tmp | — | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2574.tmp | — | |
MD5:— | SHA256:— | |||
| 2792 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2792 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | binary | |
MD5:— | SHA256:— | |||
| 2792 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B1D9FBC74905A72CA453452841079F8F_78F8A4D299EA6A66D6EB4D33A86AA12F | der | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:— | SHA256:— | |||
| 3840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
133
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2792 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3840 | iexplore.exe | GET | 200 | 52.222.157.6:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3840 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3840 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAvdR%2Fk%2FfD%2Bgxv0P8LS5Ph8%3D | US | der | 280 b | whitelisted |
3840 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
3840 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3840 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEA8zRzJeq%2Fm1rQVyRnFIOqI%3D | US | der | 279 b | whitelisted |
3840 | iexplore.exe | GET | 200 | 52.222.157.171:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3840 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCJIRnrbzaAWwIAAAAAZzJX | US | der | 472 b | whitelisted |
3840 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2792 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3840 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3840 | iexplore.exe | 52.222.149.180:443 | www.highako.com | Amazon.com, Inc. | US | whitelisted |
3840 | iexplore.exe | 104.17.132.180:443 | info.highradius.com | Cloudflare Inc | US | shared |
3840 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
3840 | iexplore.exe | 2.16.186.59:443 | use.typekit.net | Akamai International B.V. | — | whitelisted |
3840 | iexplore.exe | 104.17.183.73:443 | js.hsforms.net | Cloudflare Inc | US | shared |
3840 | iexplore.exe | 52.222.157.211:80 | o.ss2.us | Amazon.com, Inc. | US | suspicious |
3840 | iexplore.exe | 52.222.157.6:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
3840 | iexplore.exe | 104.111.215.74:443 | p.typekit.net | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
info.highradius.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.highako.com |
| shared |
ocsp.godaddy.com |
| whitelisted |
use.typekit.net |
| whitelisted |
player.dacast.com |
| whitelisted |
js.hsforms.net |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |