| File name: | icsys.ico.exe |
| Full analysis: | https://app.any.run/tasks/6b7f2a2c-fa33-4c49-962e-636b3113cacd |
| Verdict: | Malicious activity |
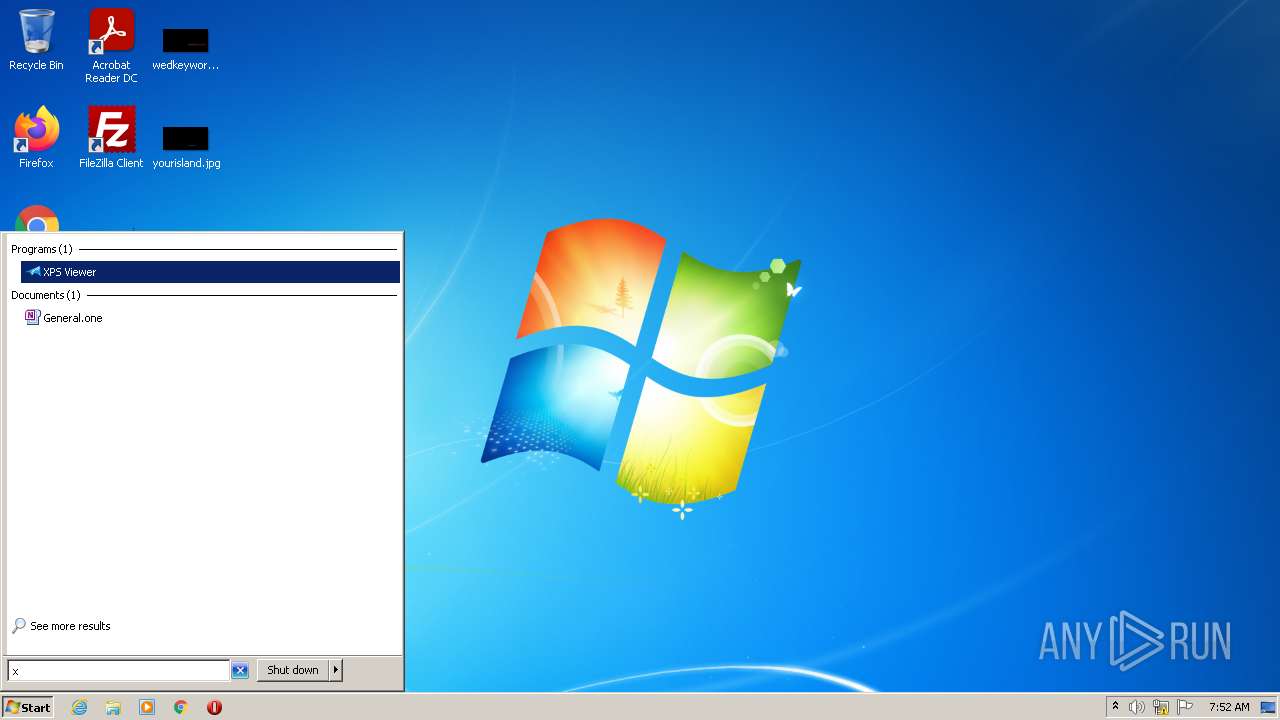
| Analysis date: | March 17, 2022, 07:51:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5A1A42E4DADFA28FB16C364E89D38E20 |
| SHA1: | F553068465BD92793456C4CB59109F90141B2984 |
| SHA256: | 8BAC4139B5485153C7A01F54DF83EC05DB041A69ADF73C8F0BB662634BB12848 |
| SSDEEP: | 24576:a2Fu/HGcDdQwWH+7aU2E0lFgG9XqcSUXI+SwBeSwtPpoc+yu0cjZxY6jRt5oHkvi:Vu/dUpCw4SIjcP0idTfTXE5JJ7g97I |
MALICIOUS
UAC/LUA settings modification
- icsys.ico.exe (PID: 596)
- wininit.exe (PID: 2708)
- spoolsv.exe (PID: 2776)
- svchost.exe (PID: 3108)
Drops executable file immediately after starts
- icsys.ico.exe (PID: 596)
- wininit.exe (PID: 2708)
- spoolsv.exe (PID: 2776)
Changes the login/logoff helper path in the registry
- icsys.ico.exe (PID: 596)
- wininit.exe (PID: 2708)
- svchost.exe (PID: 3108)
Changes the autorun value in the registry
- icsys.ico.exe (PID: 596)
SUSPICIOUS
Checks supported languages
- icsys.ico.exe (PID: 596)
- wininit.exe (PID: 2708)
- spoolsv.exe (PID: 2776)
- svchost.exe (PID: 3108)
Reads the computer name
- icsys.ico.exe (PID: 596)
- wininit.exe (PID: 2708)
- spoolsv.exe (PID: 2776)
- svchost.exe (PID: 3108)
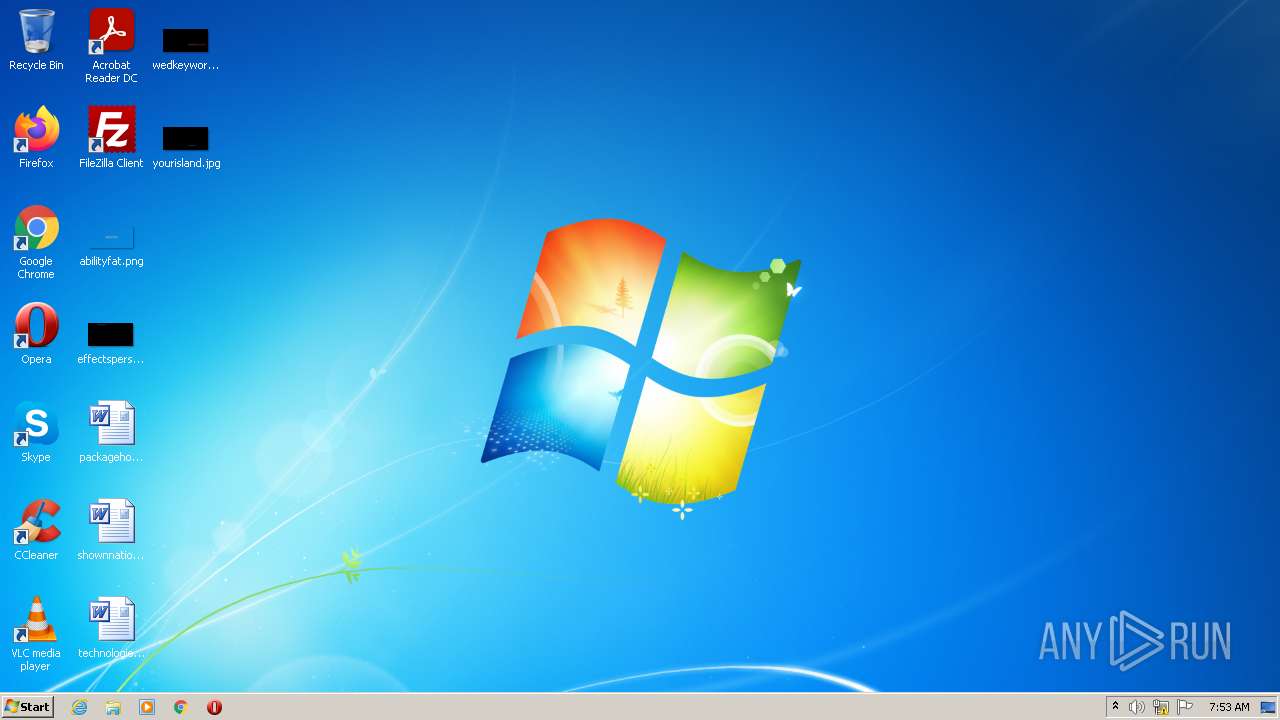
Starts itself from another location
- icsys.ico.exe (PID: 596)
- wininit.exe (PID: 2708)
- spoolsv.exe (PID: 2776)
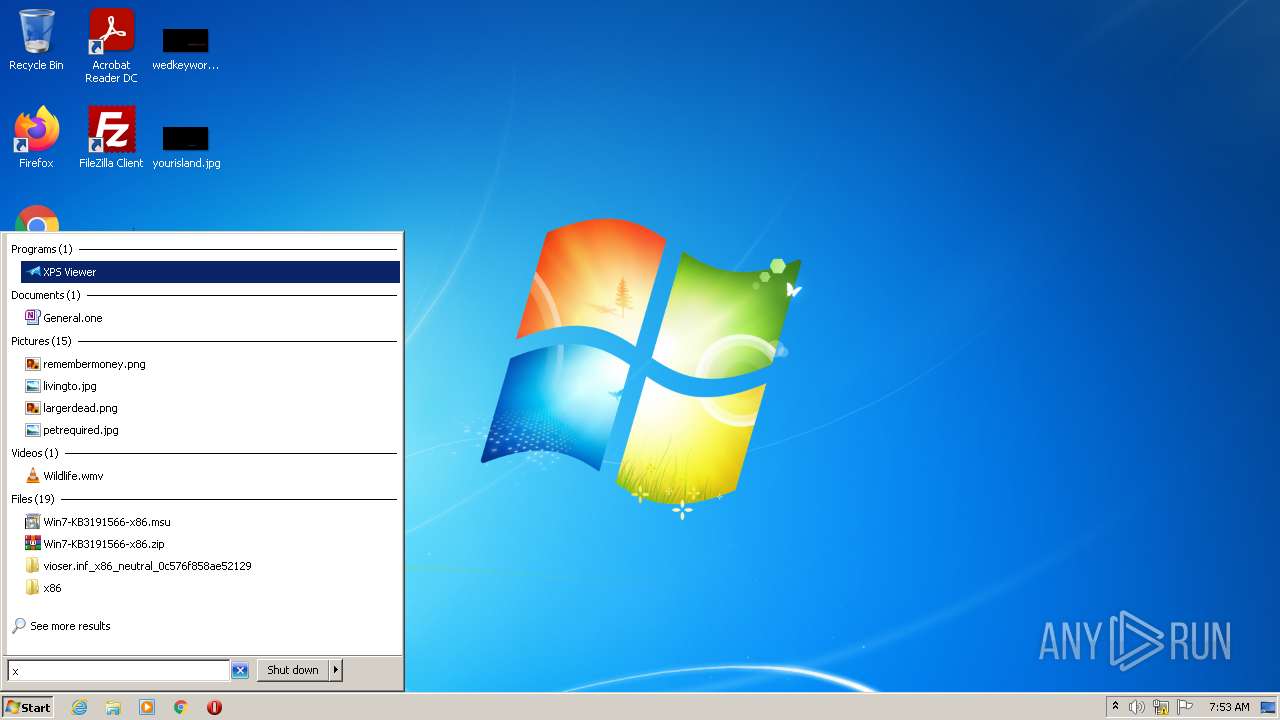
Creates files in the user directory
- wininit.exe (PID: 2708)
Executable content was dropped or overwritten
- icsys.ico.exe (PID: 596)
- wininit.exe (PID: 2708)
- spoolsv.exe (PID: 2776)
Creates files in the Windows directory
- icsys.ico.exe (PID: 596)
- spoolsv.exe (PID: 2776)
Creates executable files which already exist in Windows
- spoolsv.exe (PID: 2776)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (79.7) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (8.6) |
| .exe | | | Win16/32 Executable Delphi generic (3.9) |
| .exe | | | Generic Win/DOS Executable (3.8) |
| .exe | | | DOS Executable Generic (3.8) |
EXIF
EXE
| ProductVersion: | 1.0.0.0 |
|---|---|
| FileVersion: | 1.0.0.0 |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x25c7d4 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 519168 |
| CodeSize: | 2472448 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2018:10:24 09:34:01+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Oct-2018 07:34:01 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 24-Oct-2018 07:34:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00259F3C | 0x0025A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45209 |
.itext | 0x0025B000 | 0x00001848 | 0x00001A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.11925 |
.data | 0x0025D000 | 0x0000B1BC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.45646 |
.bss | 0x00269000 | 0x00086FC8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x002F0000 | 0x000042A4 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.20259 |
.didata | 0x002F5000 | 0x00000A68 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.81411 |
.edata | 0x002F6000 | 0x0000005E | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.10363 |
.tls | 0x002F7000 | 0x00000044 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x002F8000 | 0x0000005C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.33244 |
.reloc | 0x002F9000 | 0x00035FD4 | 0x00036000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.72455 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92553 | 703 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.80231 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4059 | 2.74785 | 156 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4060 | 3.29715 | 792 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4061 | 3.25681 | 1312 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
msvcrt.dll |
netapi32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
TMethodImplementationIntercept | 1 | 0x00065E94 |
Total processes
40
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 596 | "C:\Users\admin\AppData\Local\Temp\icsys.ico.exe" | C:\Users\admin\AppData\Local\Temp\icsys.ico.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2708 | "C:\windows\wininit.exe" | C:\windows\wininit.exe | icsys.ico.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2776 | "C:\Users\admin\appdata\roaming\spoolsv.exe" /SE | C:\Users\admin\appdata\roaming\spoolsv.exe | wininit.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3108 | "C:\windows\svchost.exe" | C:\windows\svchost.exe | spoolsv.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3740 | "C:\Users\admin\AppData\Local\Temp\icsys.ico.exe" | C:\Users\admin\AppData\Local\Temp\icsys.ico.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 165
Read events
1 112
Write events
51
Delete events
2
Modification events
| (PID) Process: | (596) icsys.ico.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (596) icsys.ico.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (596) icsys.ico.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 0 | |||
| (PID) Process: | (596) icsys.ico.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (596) icsys.ico.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (596) icsys.ico.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (596) icsys.ico.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (596) icsys.ico.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Wininit |
Value: c:\windows\wininit.exe | |||
| (PID) Process: | (596) icsys.ico.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Svchost |
Value: c:\windows\svchost.exe | |||
| (PID) Process: | (596) icsys.ico.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | shell |
Value: C:\Windows\explorer.exe, c:\windows\wininit.exe | |||
Executable files
3
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2776 | spoolsv.exe | C:\windows\svchost.exe | executable | |
MD5:5A1A42E4DADFA28FB16C364E89D38E20 | SHA256:8BAC4139B5485153C7A01F54DF83EC05DB041A69ADF73C8F0BB662634BB12848 | |||
| 2708 | wininit.exe | C:\users\admin\appdata\roaming\spoolsv.exe | executable | |
MD5:5A1A42E4DADFA28FB16C364E89D38E20 | SHA256:8BAC4139B5485153C7A01F54DF83EC05DB041A69ADF73C8F0BB662634BB12848 | |||
| 596 | icsys.ico.exe | C:\windows\wininit.exe | executable | |
MD5:5A1A42E4DADFA28FB16C364E89D38E20 | SHA256:8BAC4139B5485153C7A01F54DF83EC05DB041A69ADF73C8F0BB662634BB12848 | |||
| 596 | icsys.ico.exe | C:\Windows\Wininit | text | |
MD5:DC88C4AA03F5180BBECE1ABDFEC93E70 | SHA256:764DF4D37A31BE29B4D87041C66C520CF72260D05B22C92DF5F61E1EB67EF728 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report