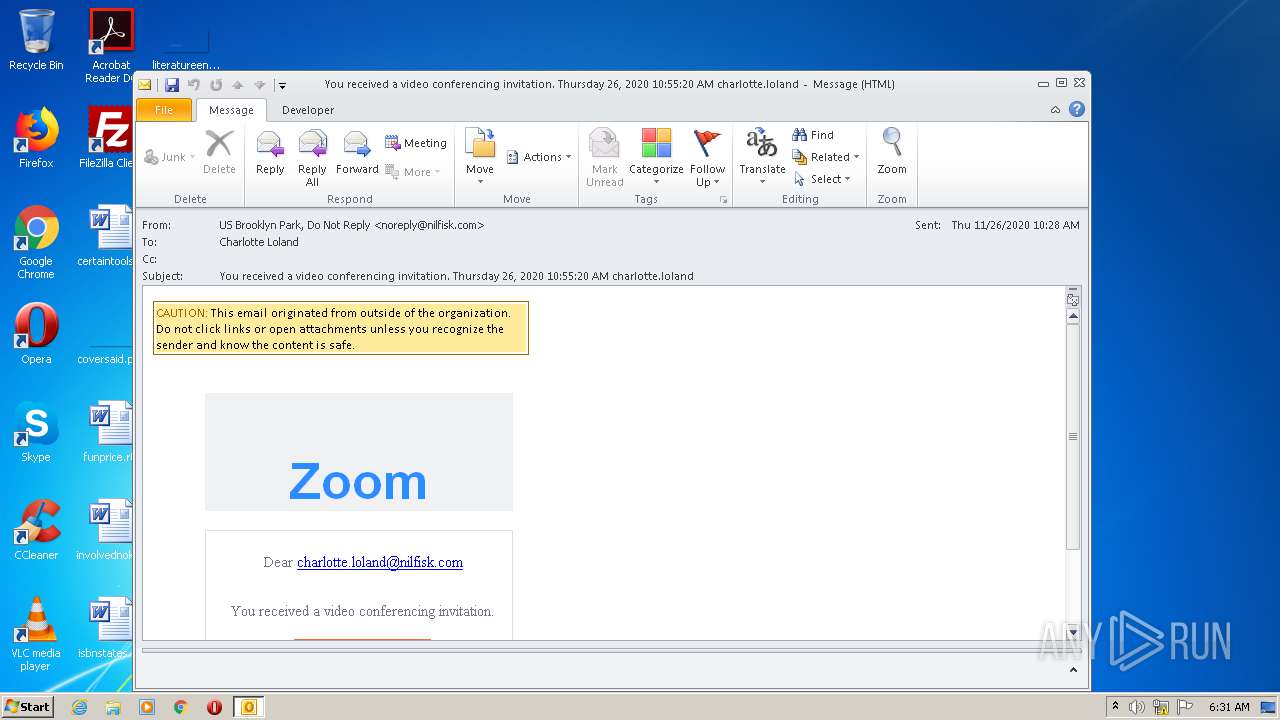
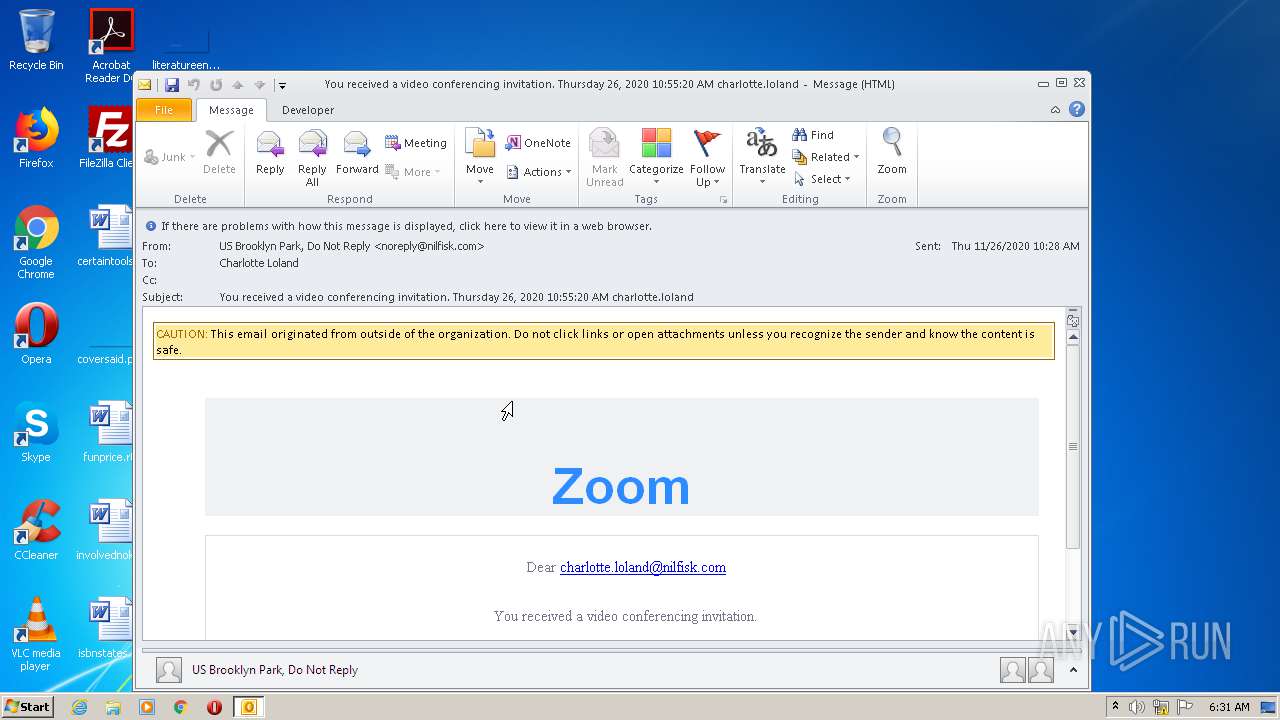
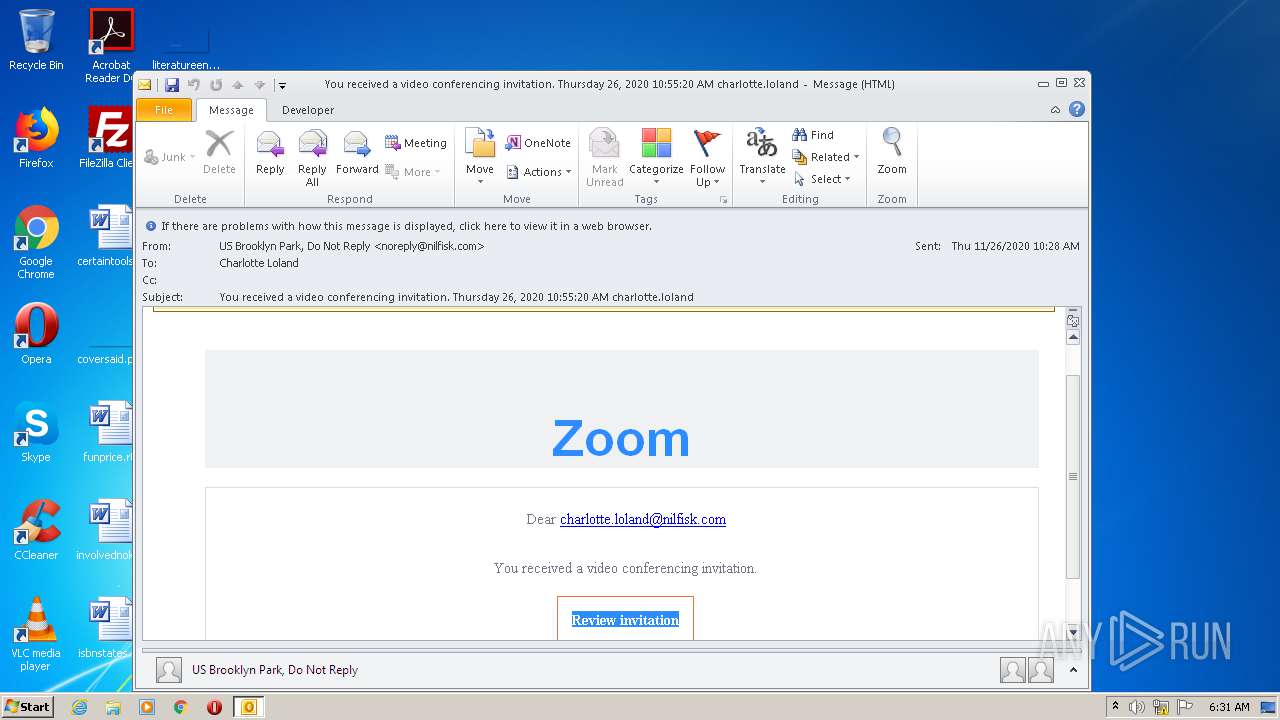
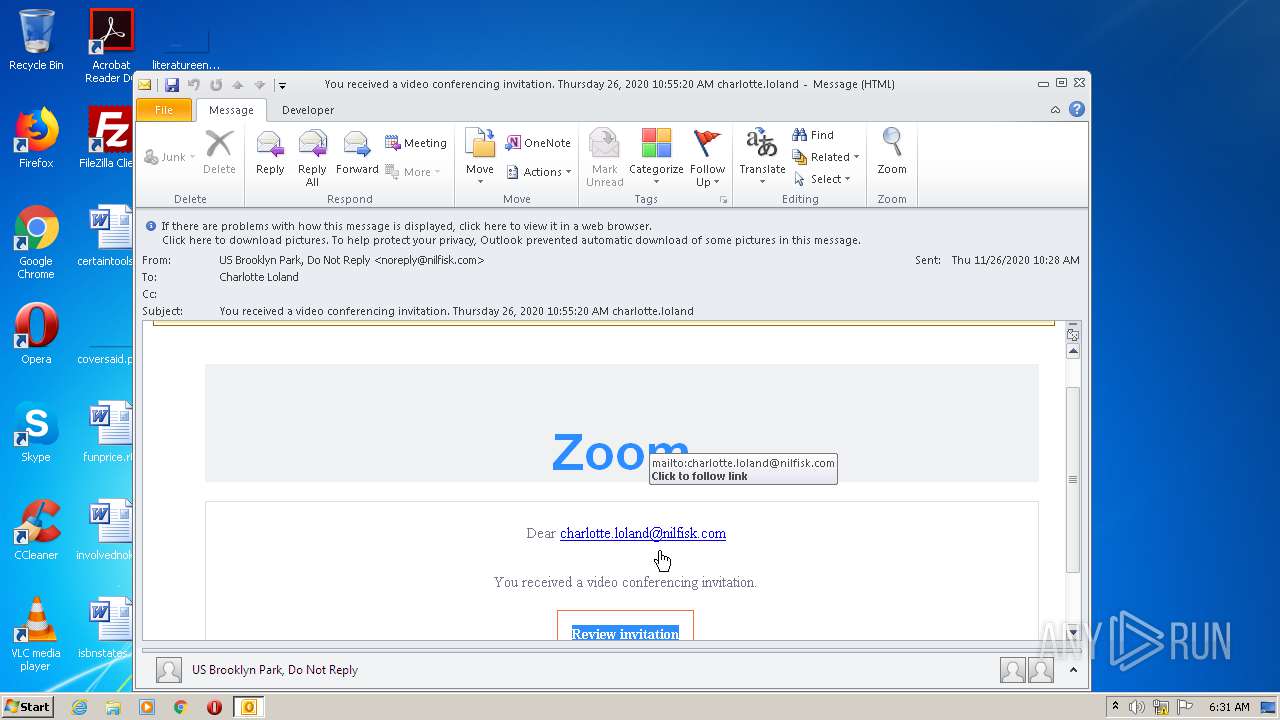
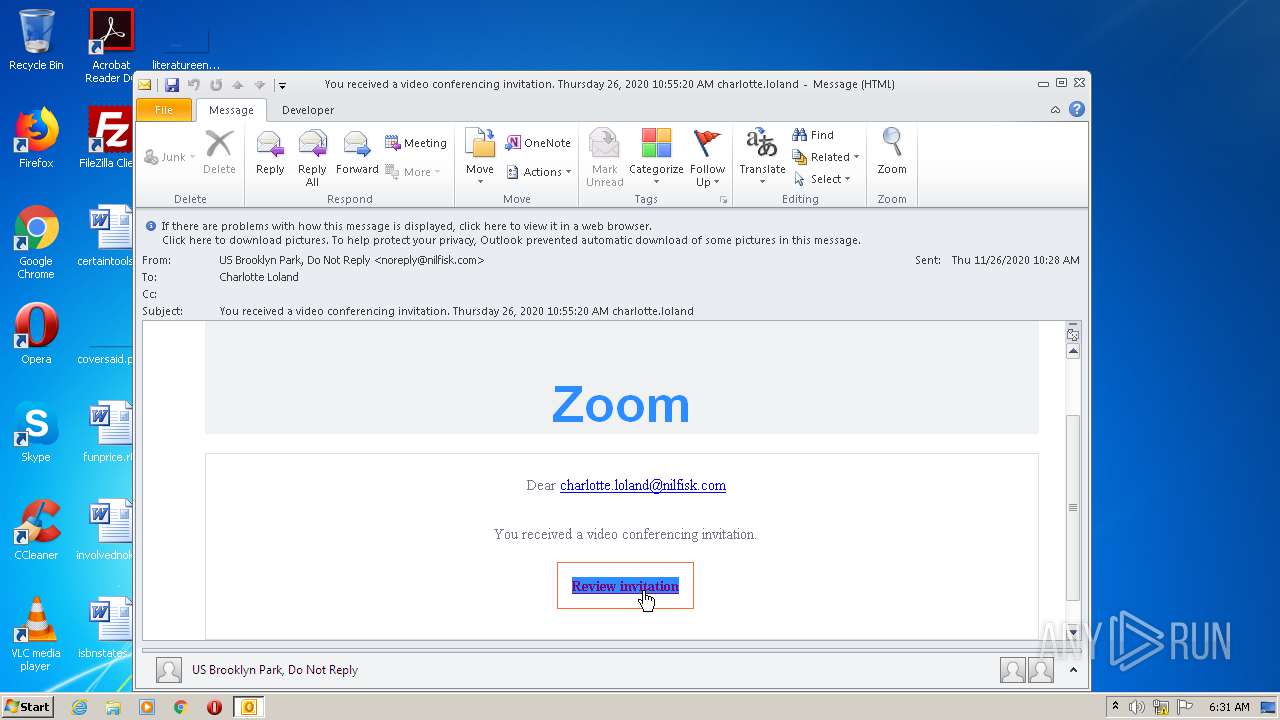
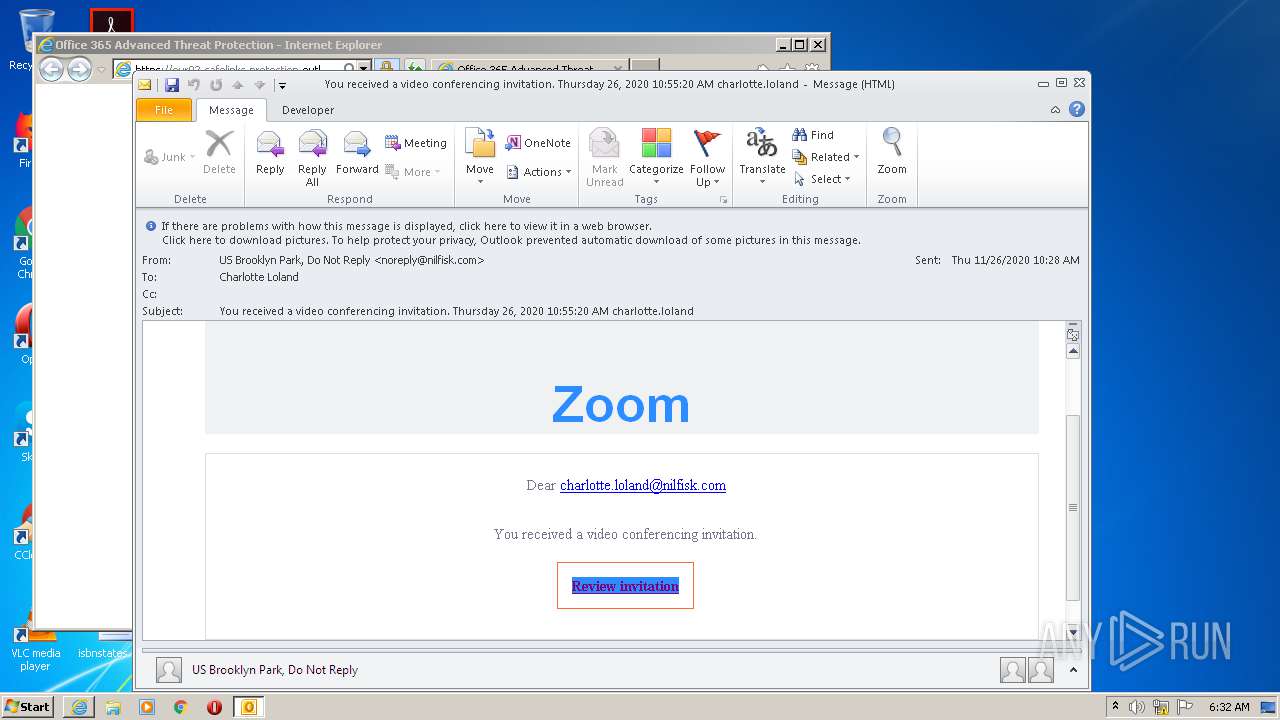
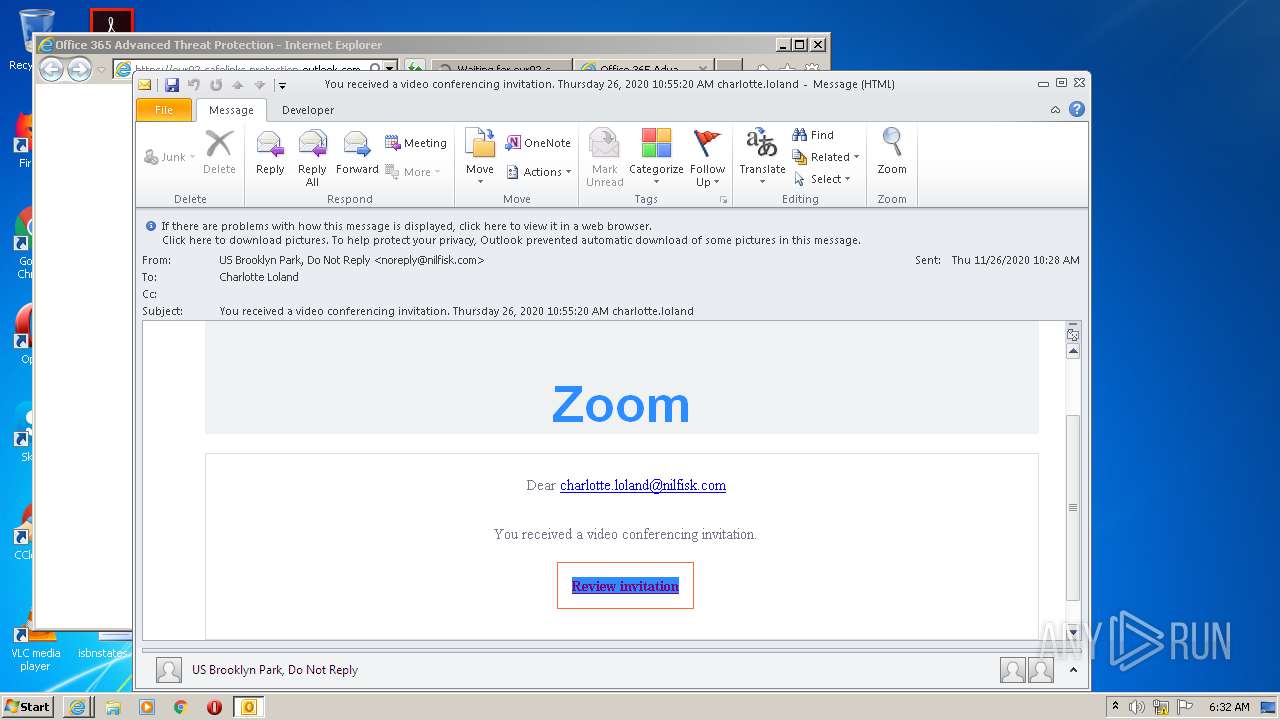
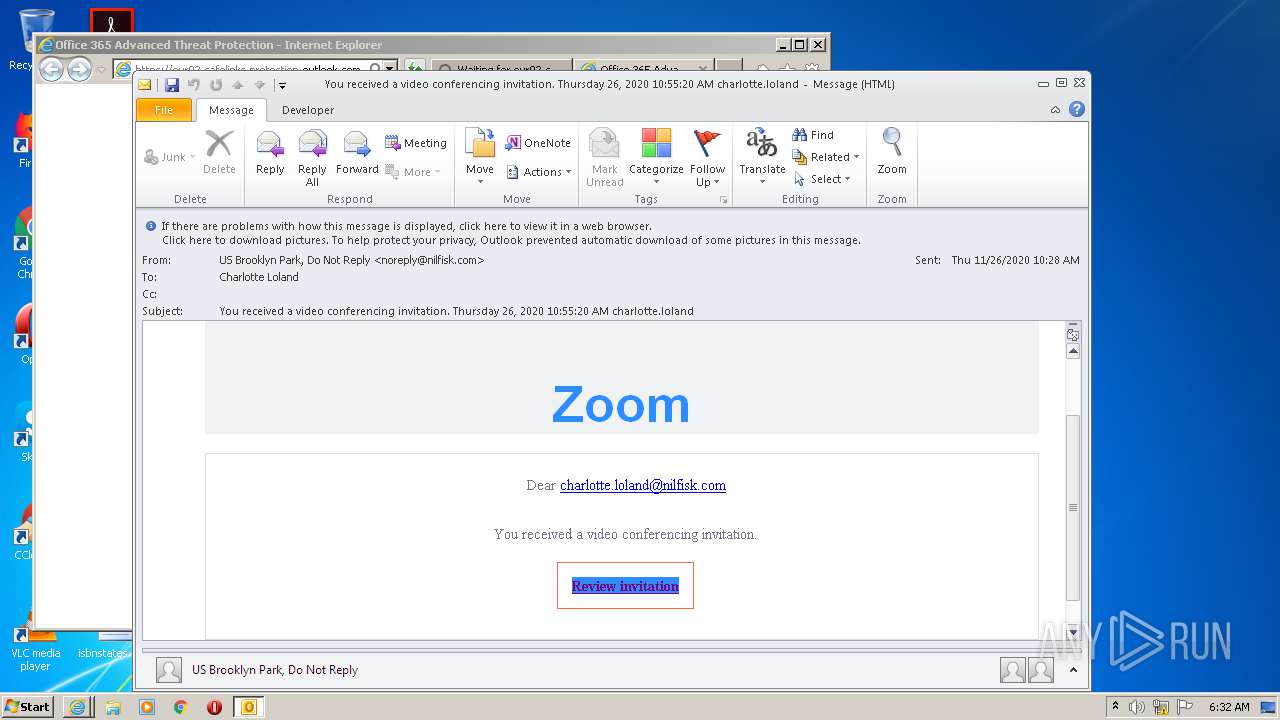
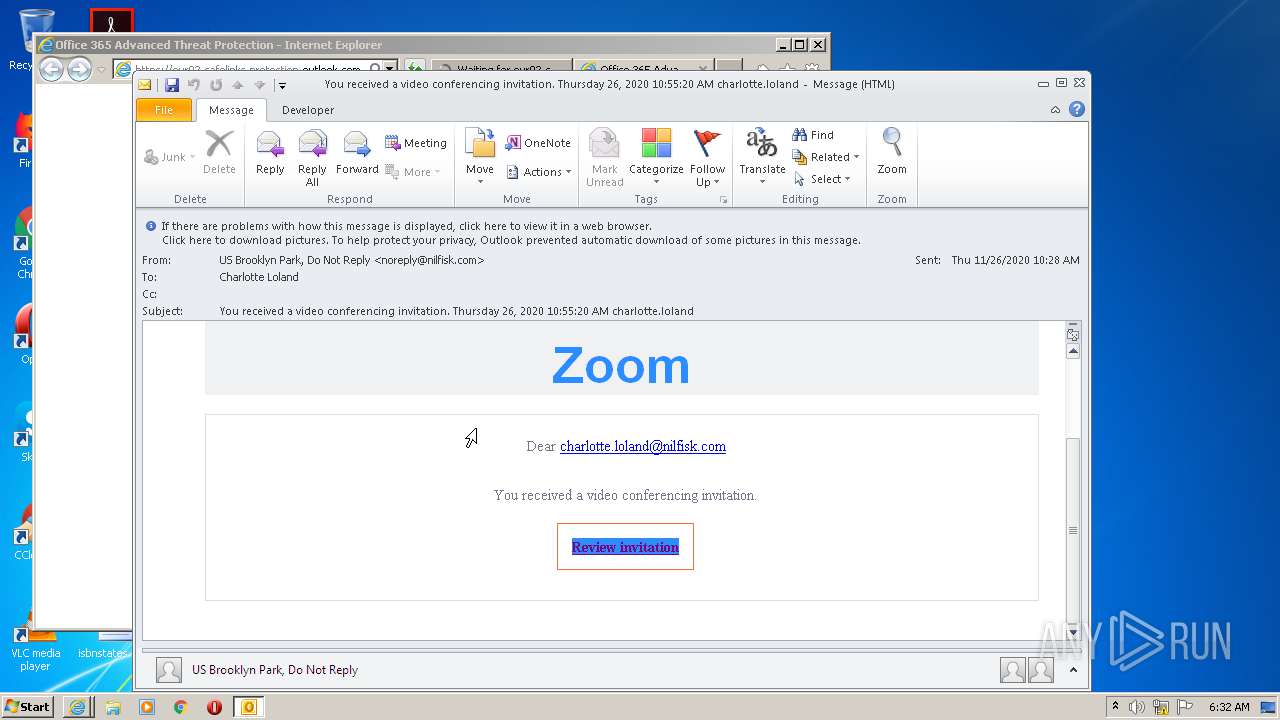
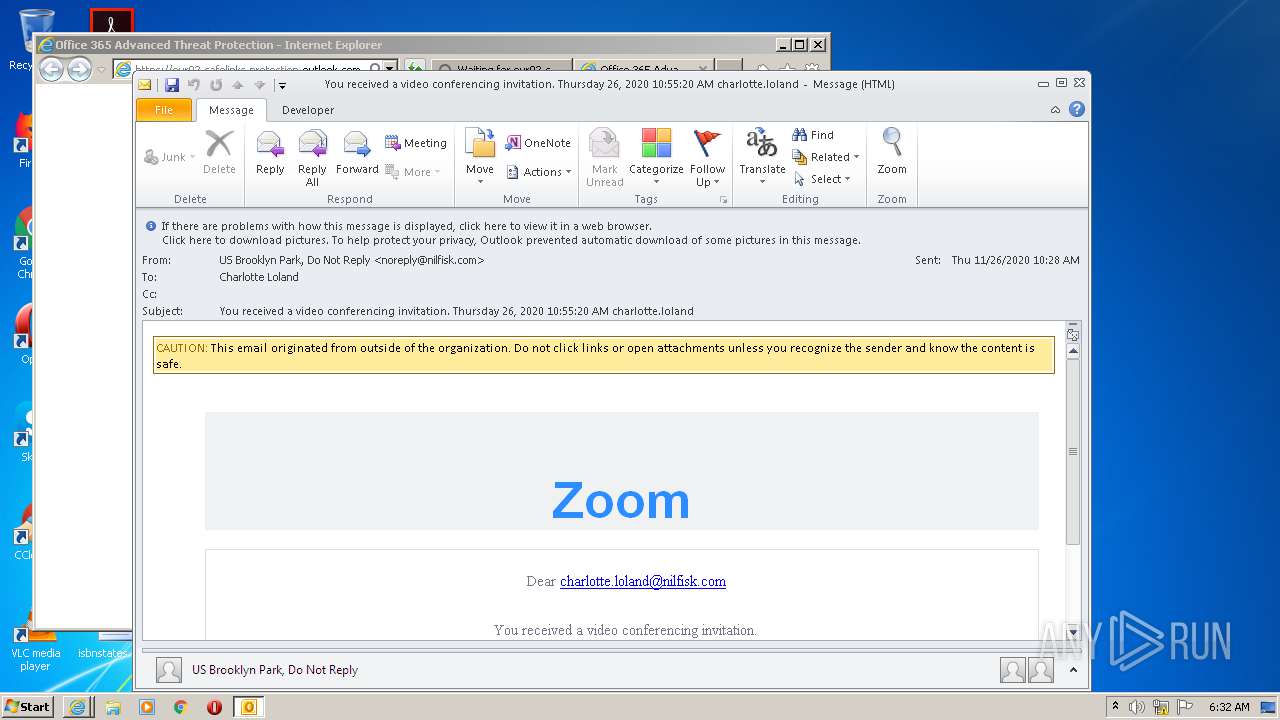
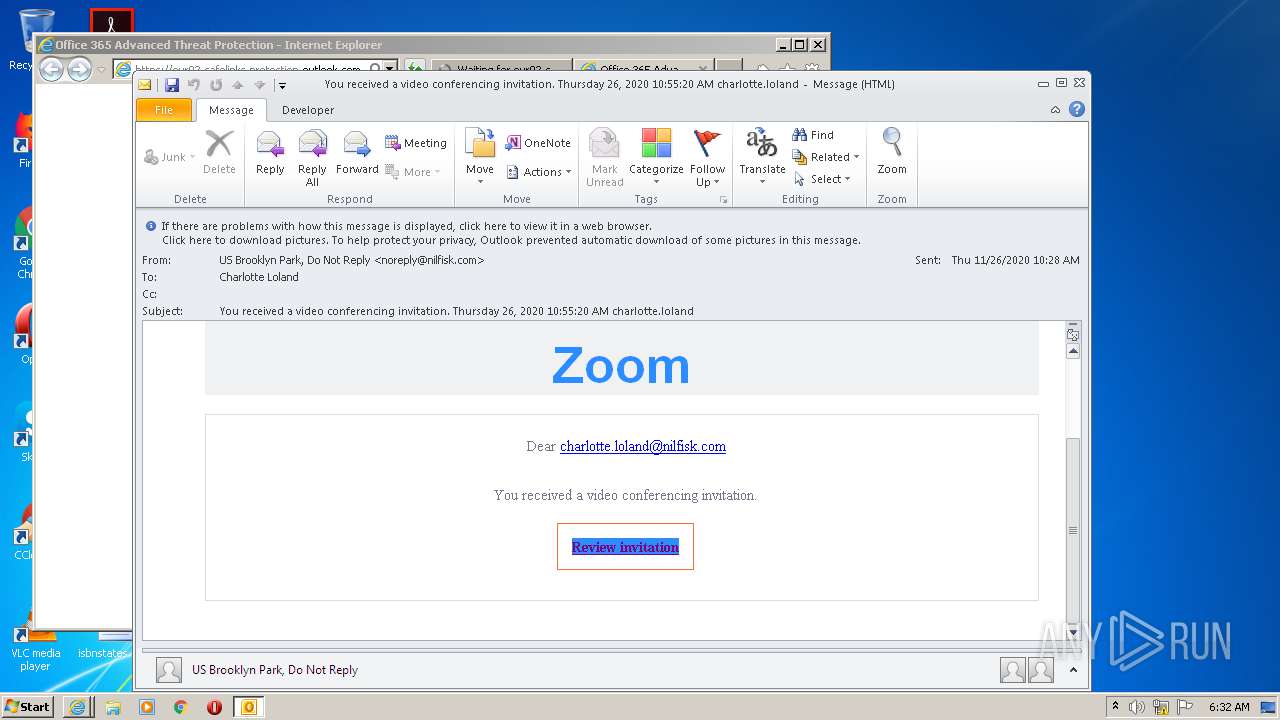
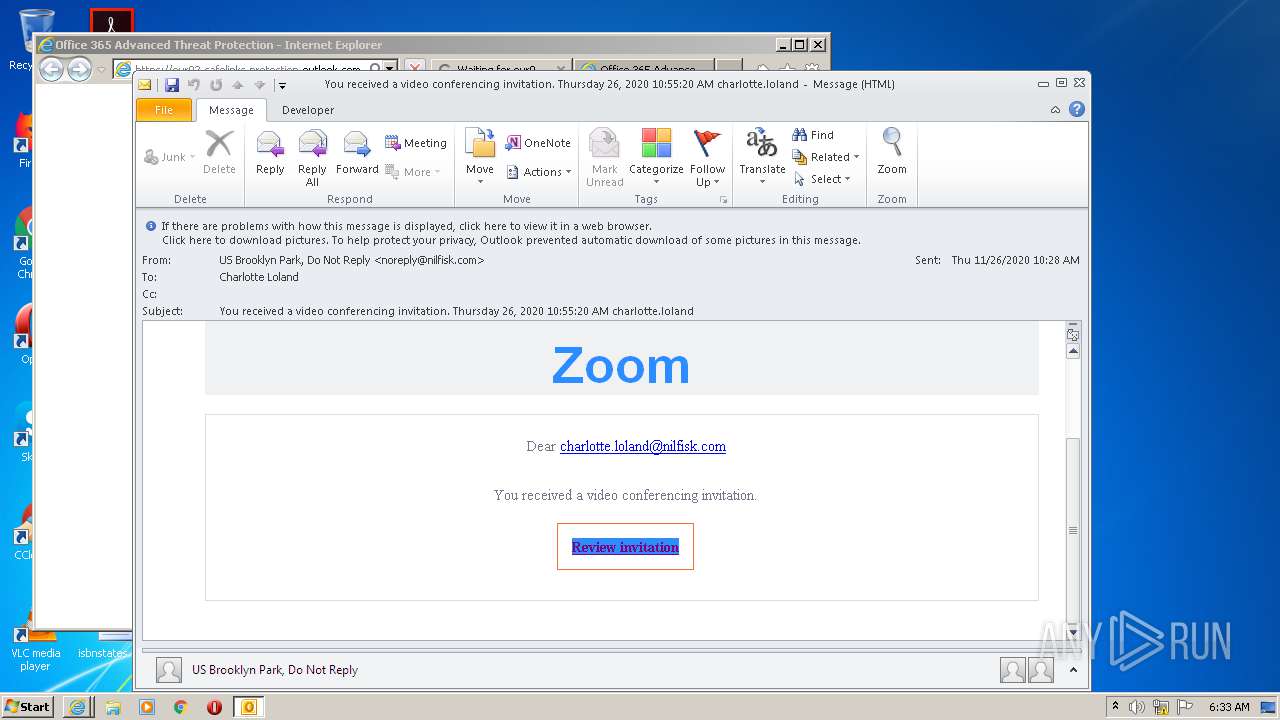
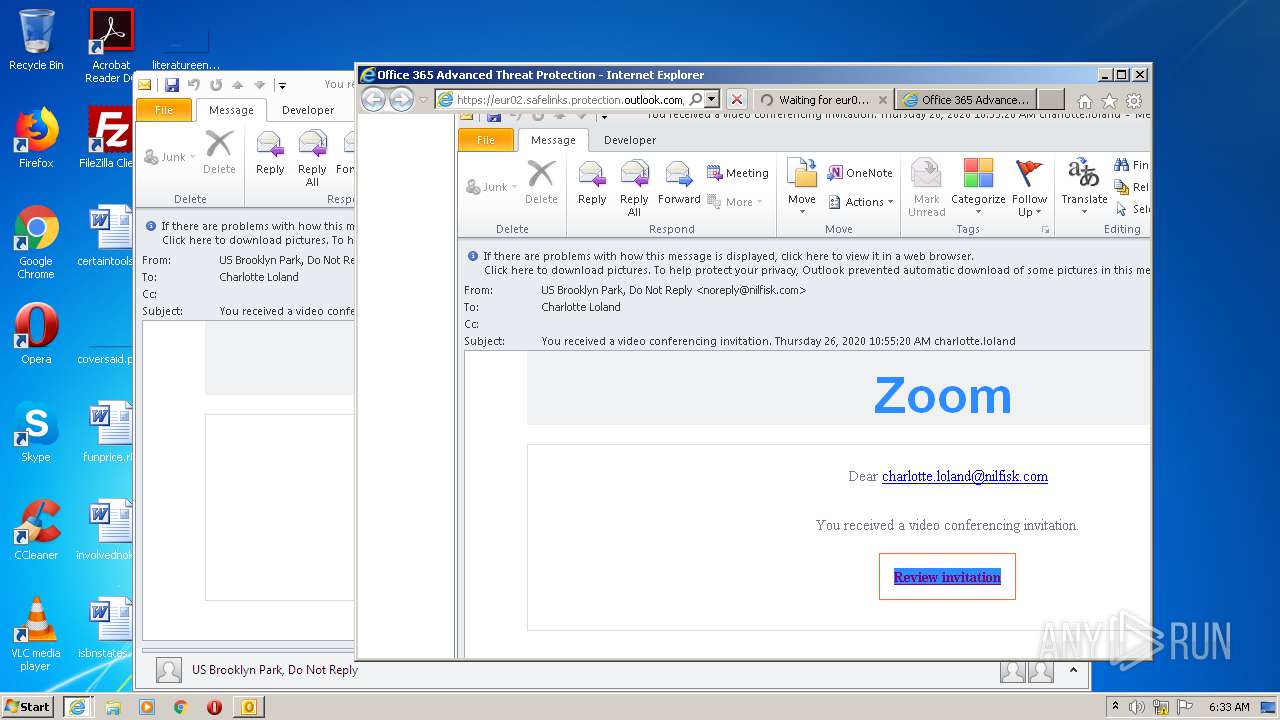
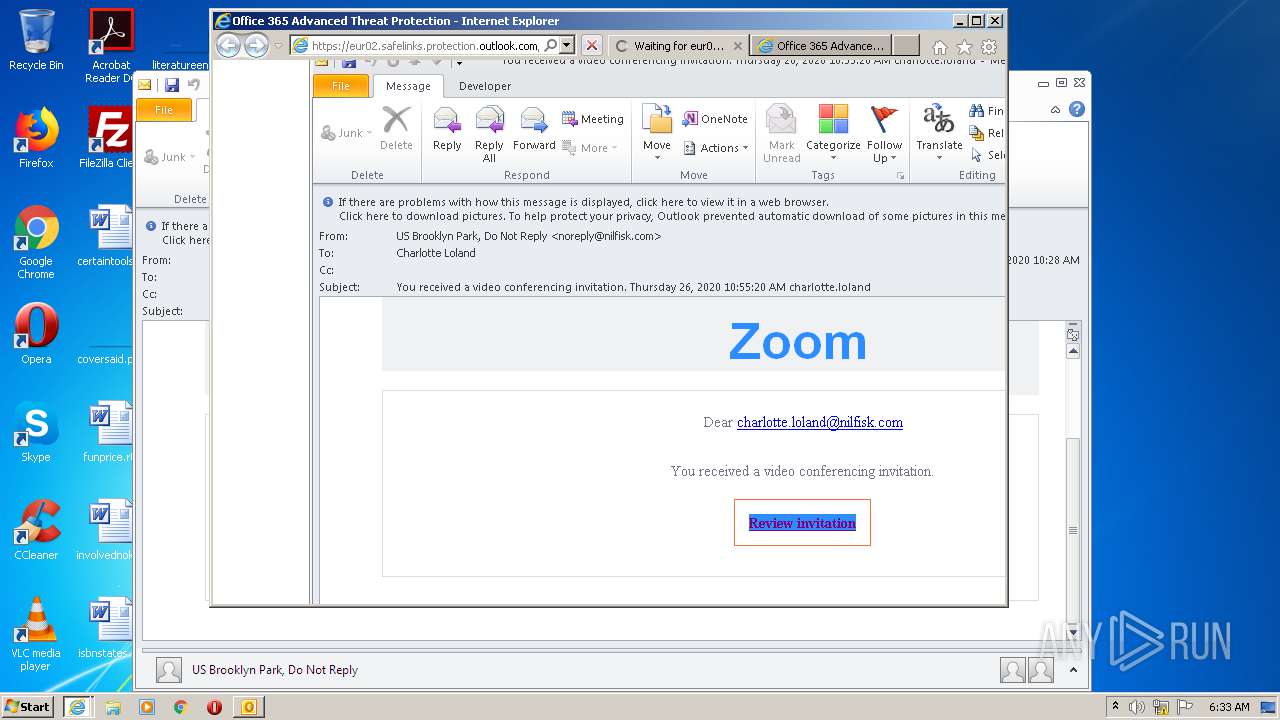
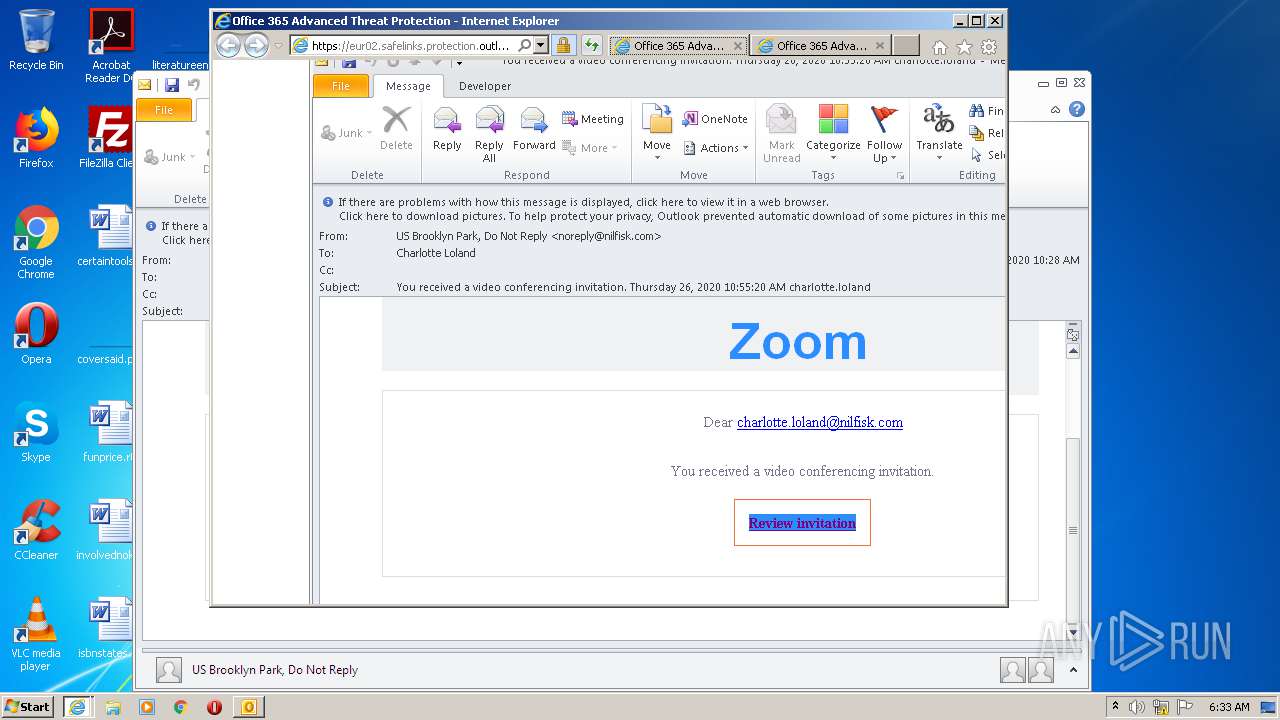
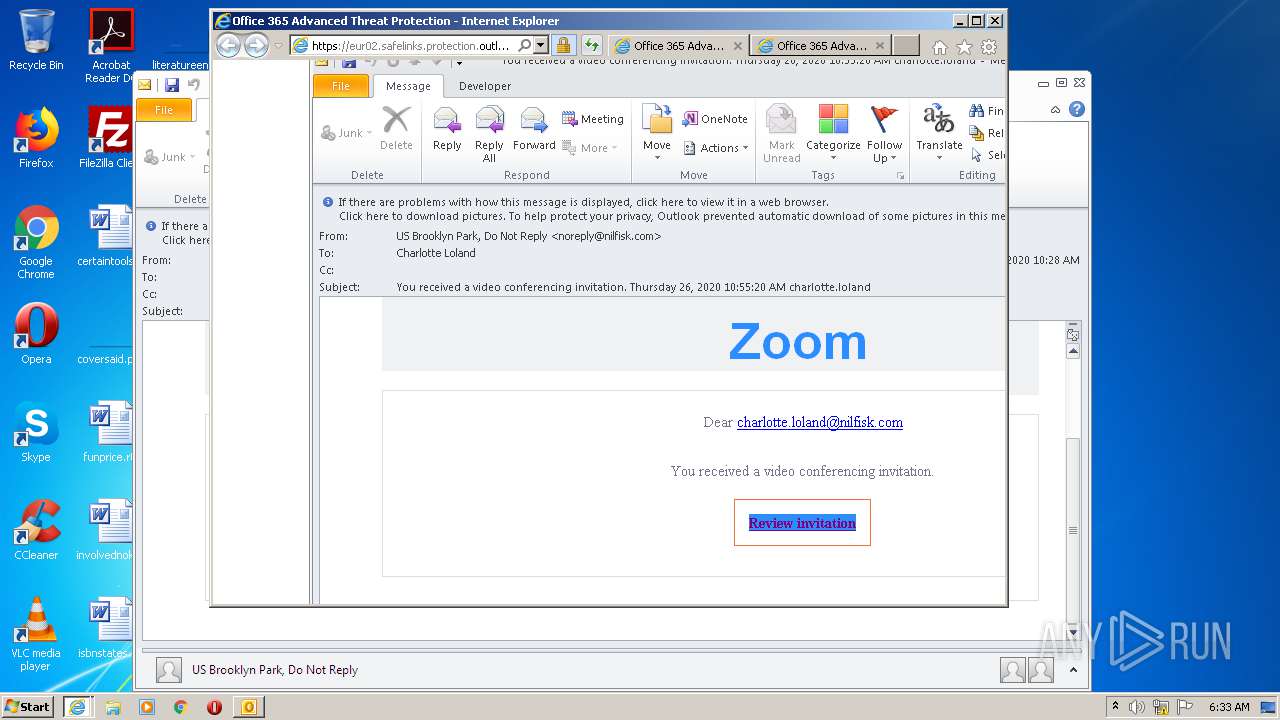
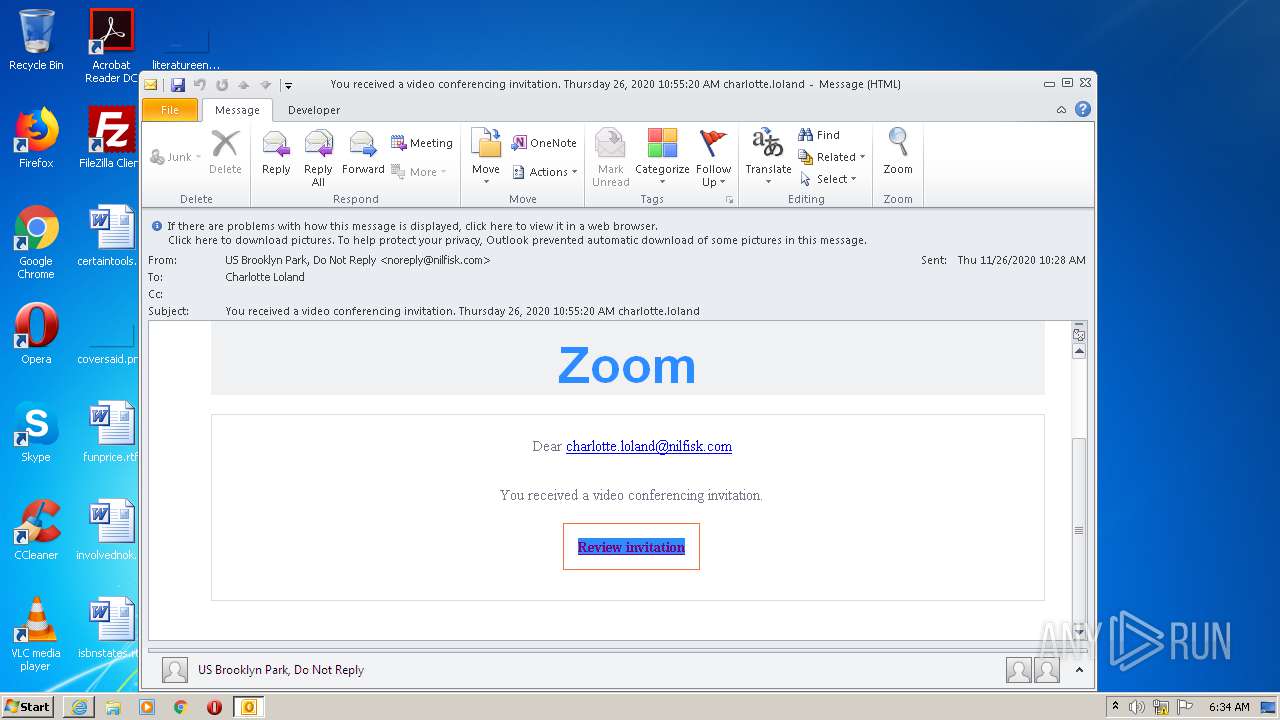
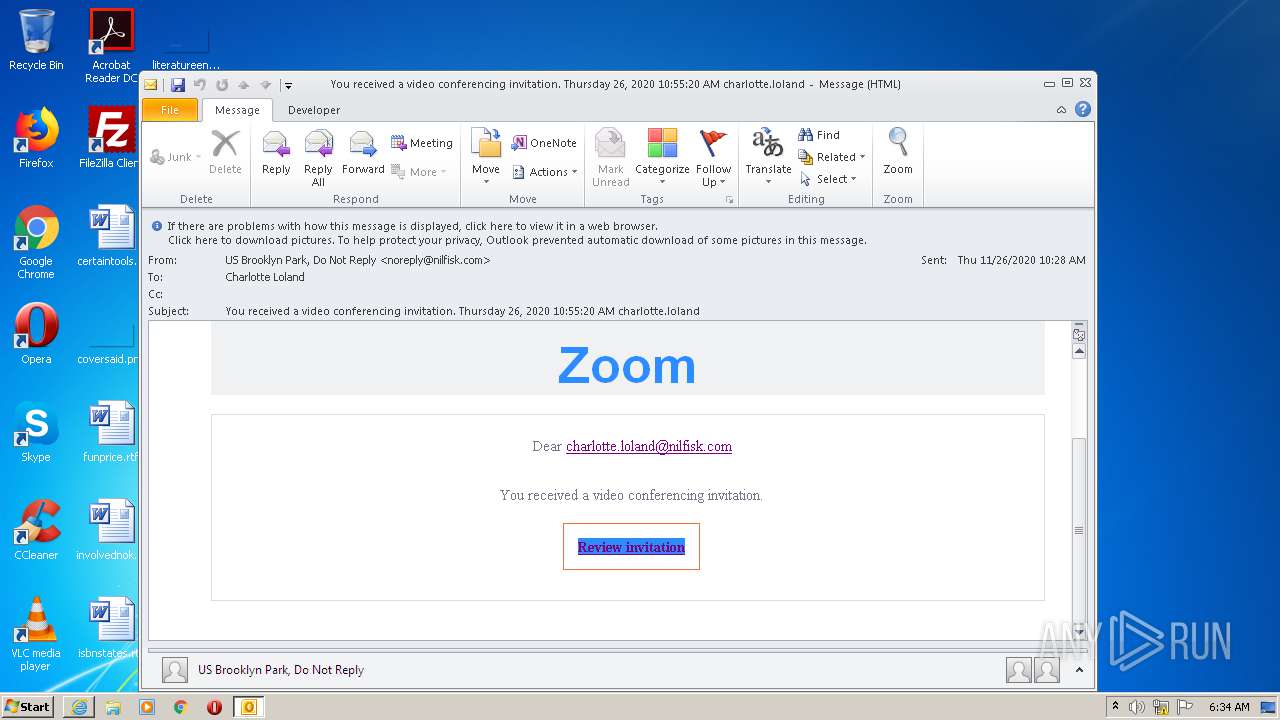
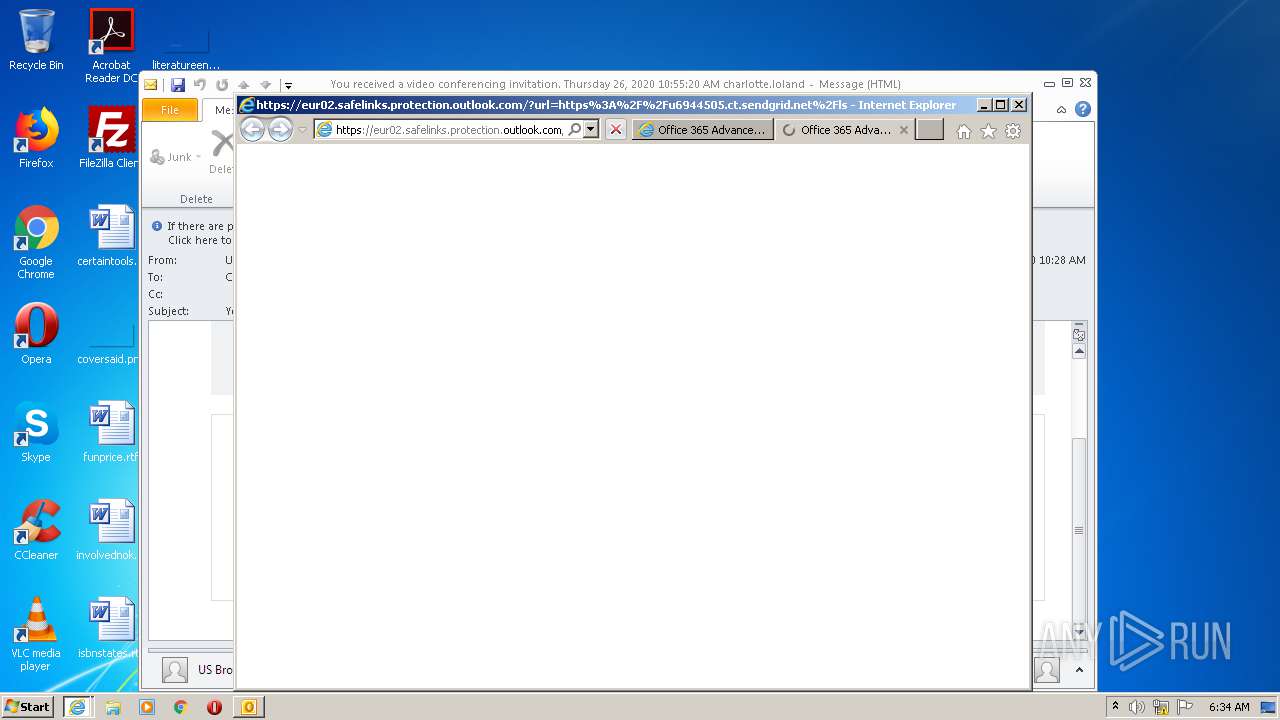
| File name: | You received a video conferencing invitation. Thursday 26 2020 105520 AM charlotte.loland.msg |
| Full analysis: | https://app.any.run/tasks/1d5a0ff7-6aac-4018-8d4d-692d47081b74 |
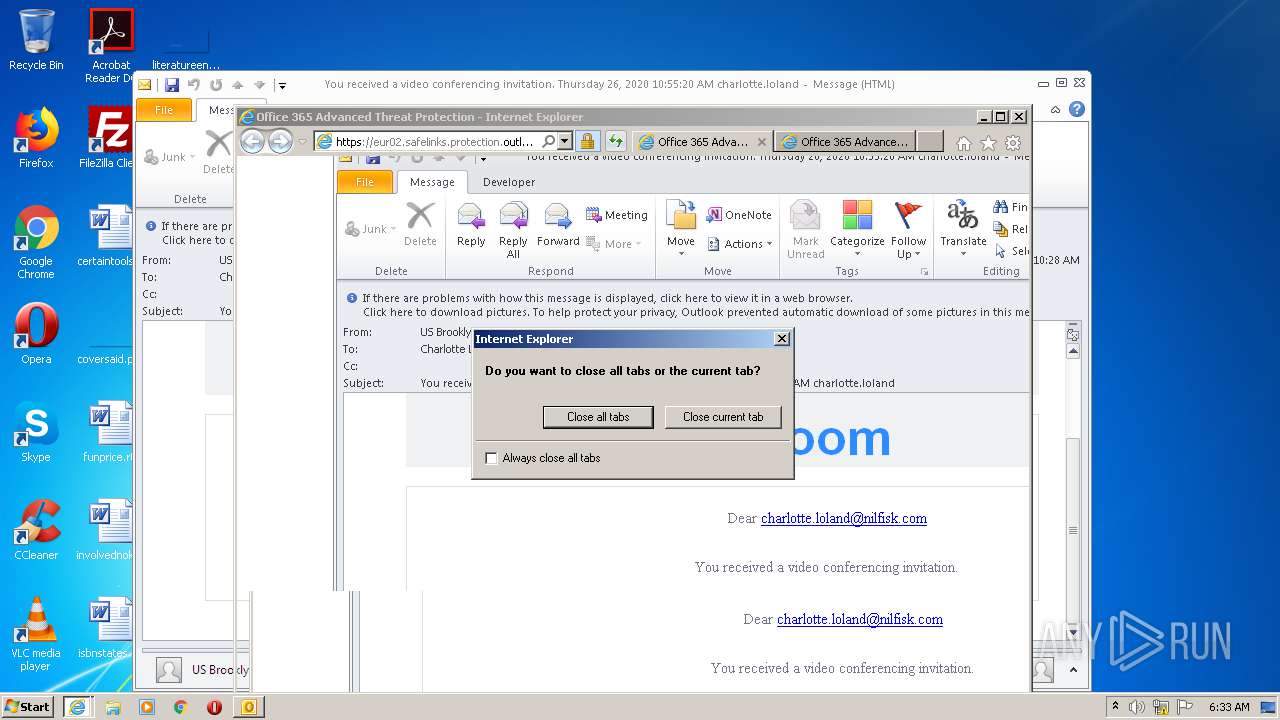
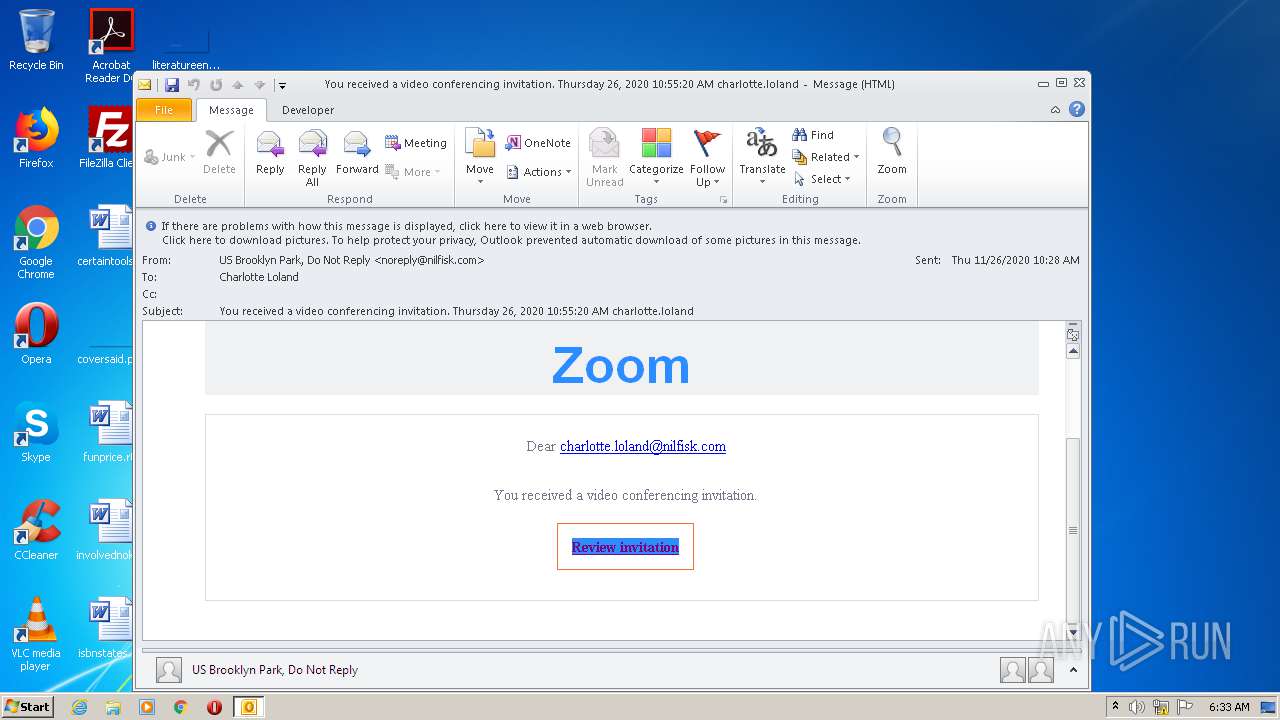
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 06:31:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 42A4EEA5AB3A23A475E754F9F6A5BE7D |
| SHA1: | 86358589054D218D29E8F7E50CA34E1616093545 |
| SHA256: | 8BA03A129D72A85324FD18D94C42CD52F61FBF615FACA2FA9C731515F47C2415 |
| SSDEEP: | 768:AM9v2dCDi/zEzYSBDrHyjIgF7SDTR/NzdZ6CgU9HjnRFfz/FNcfG45cNmiP1:kkDiwEsYIFdECg8H/fz9Ai |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2528)
SUSPICIOUS
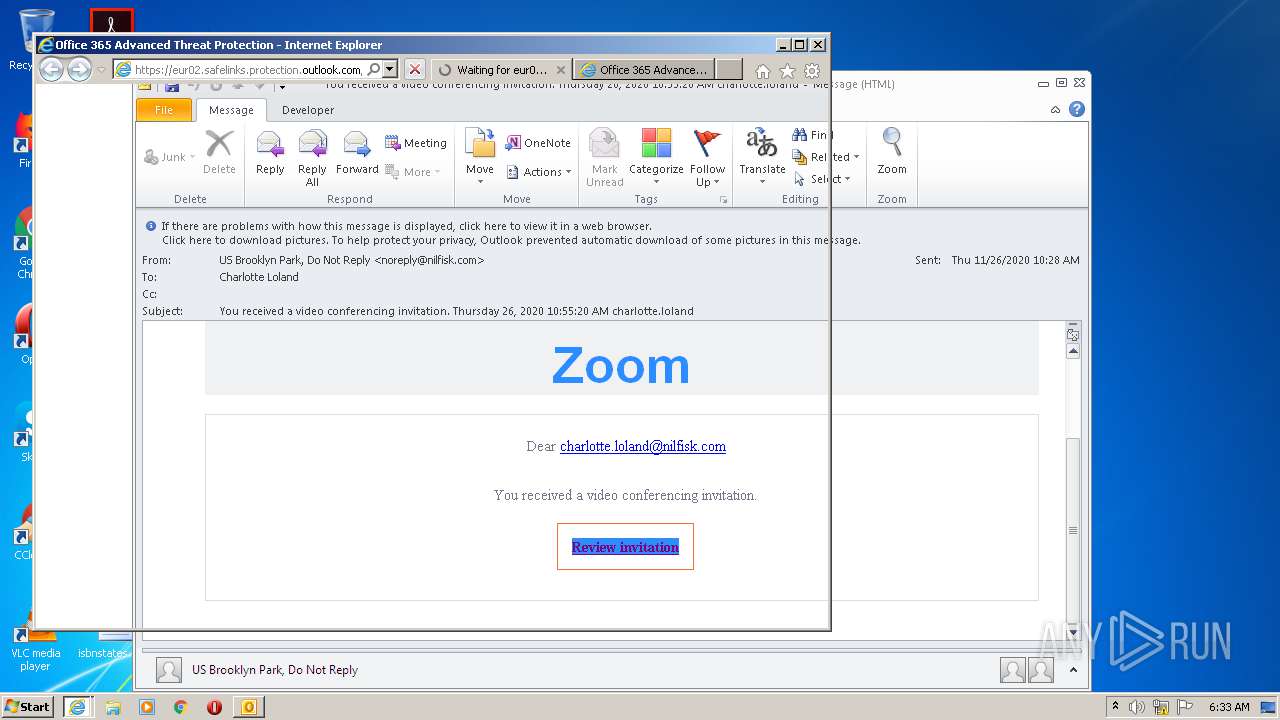
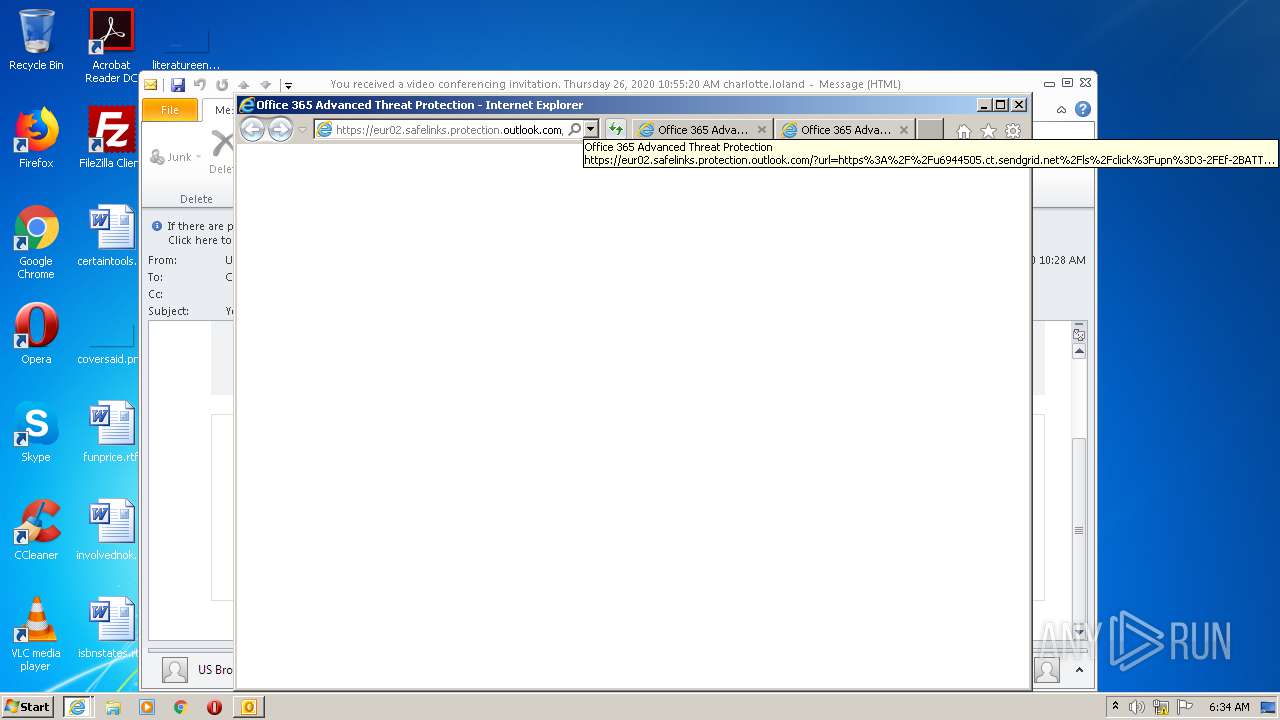
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2528)
Starts itself from another location
- OUTLOOK.EXE (PID: 2528)
INFO
Creates files in the user directory
- OUTLOOK.EXE (PID: 2528)
- iexplore.exe (PID: 2684)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2528)
- OUTLOOK.EXE (PID: 1712)
Reads settings of System Certificates
- iexplore.exe (PID: 1560)
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 2672)
Changes settings of System certificates
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 2672)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 2672)
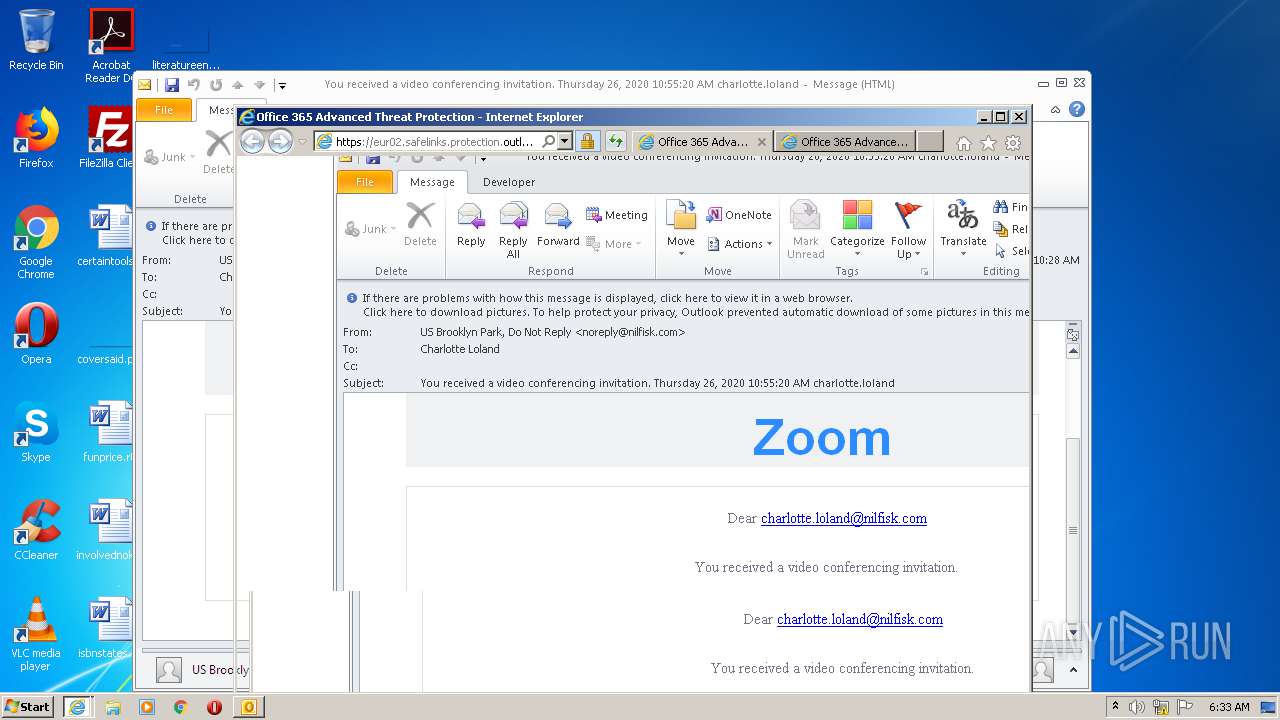
Application launched itself
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 2672)
Changes internet zones settings
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 2672)
Reads internet explorer settings
- iexplore.exe (PID: 1560)
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 1744)
- iexplore.exe (PID: 3904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
44
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1560 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2684 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
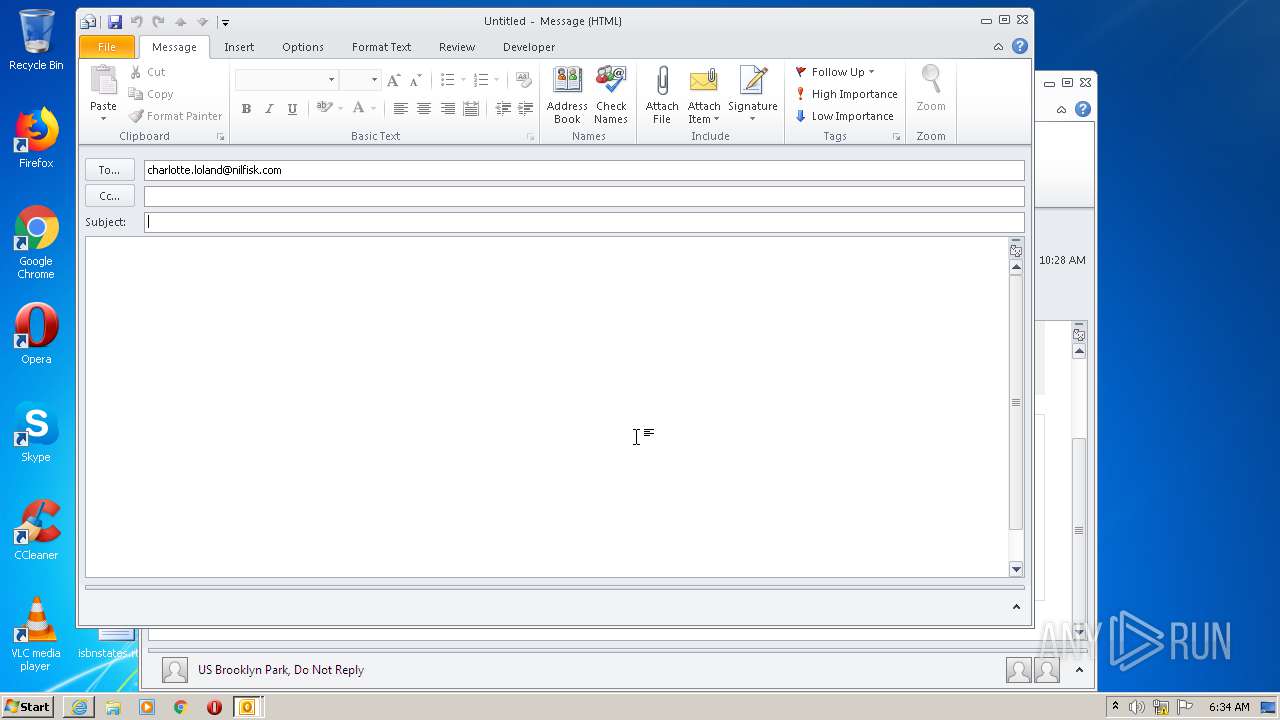
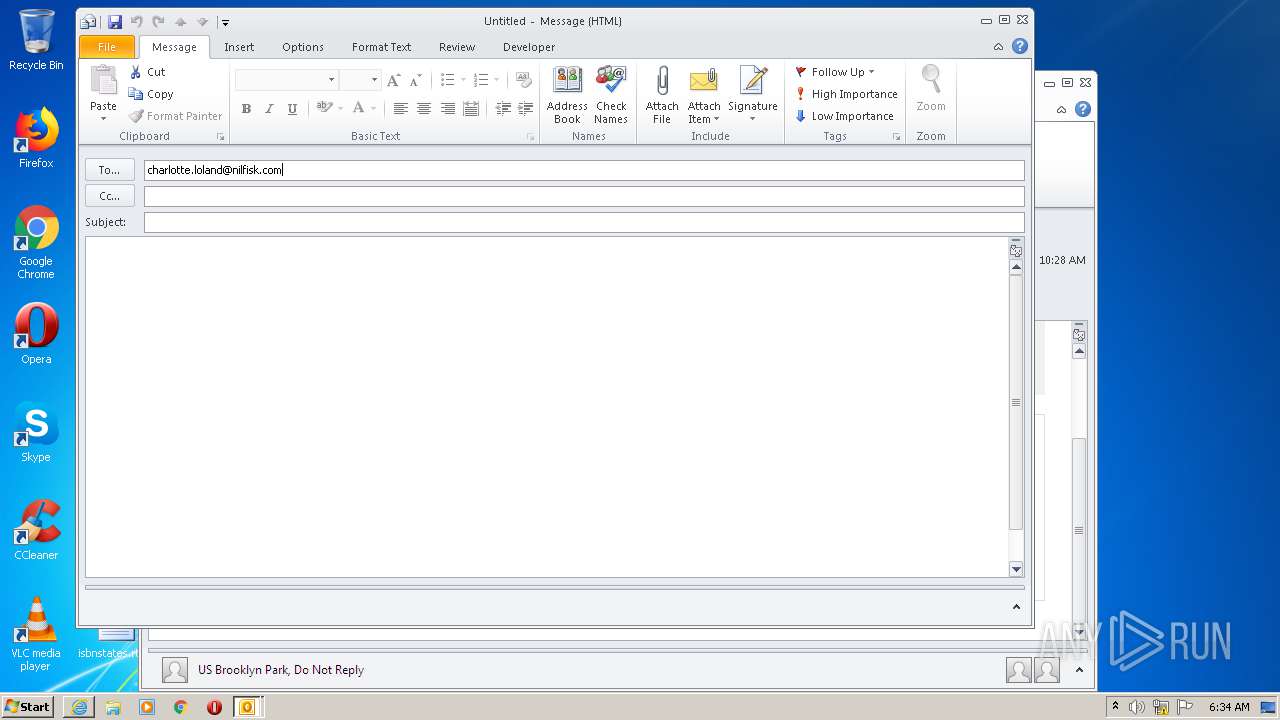
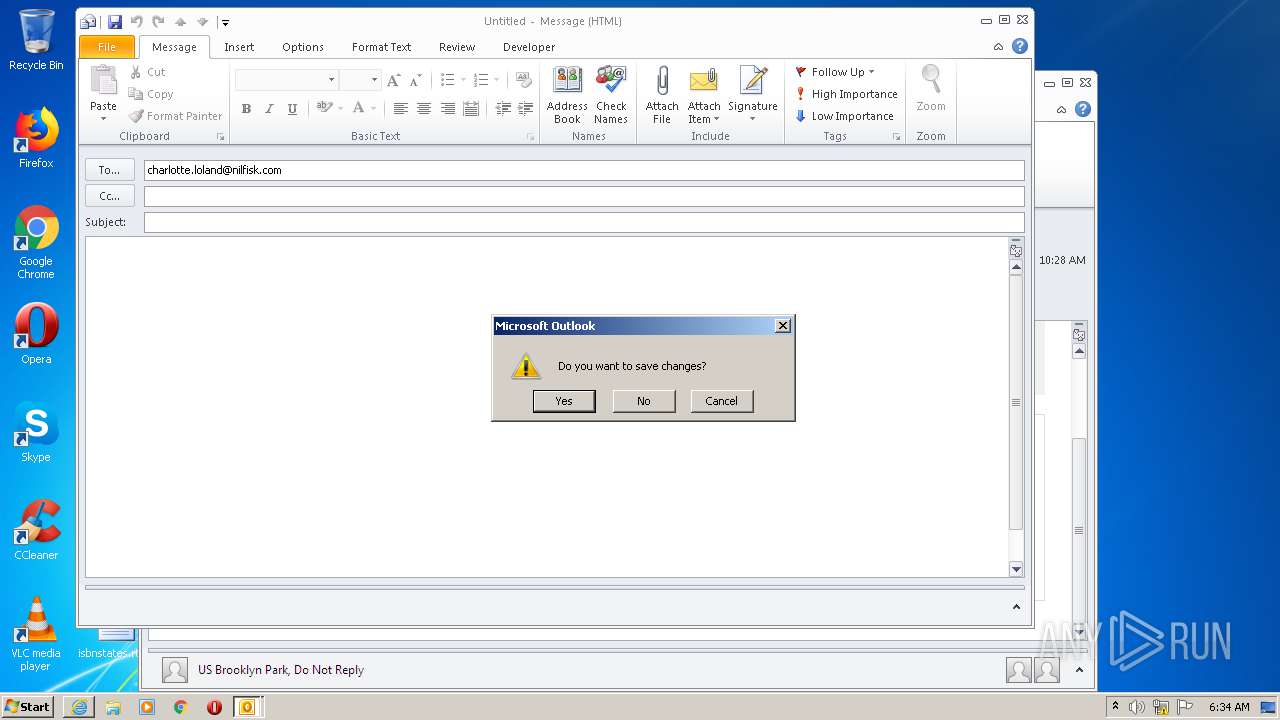
| 1712 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:charlotte.loland@nilfisk.com" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2672 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2684 CREDAT:595208 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\You received a video conferencing invitation. Thursday 26 2020 105520 AM charlotte.loland.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
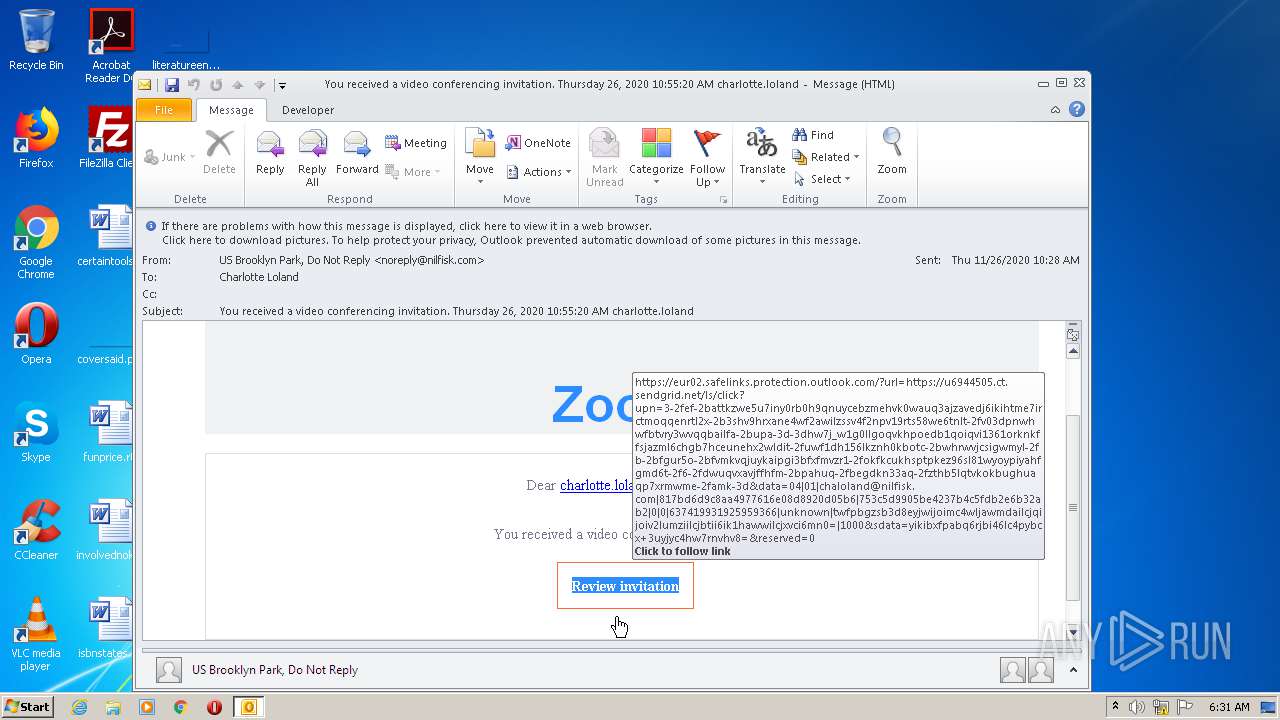
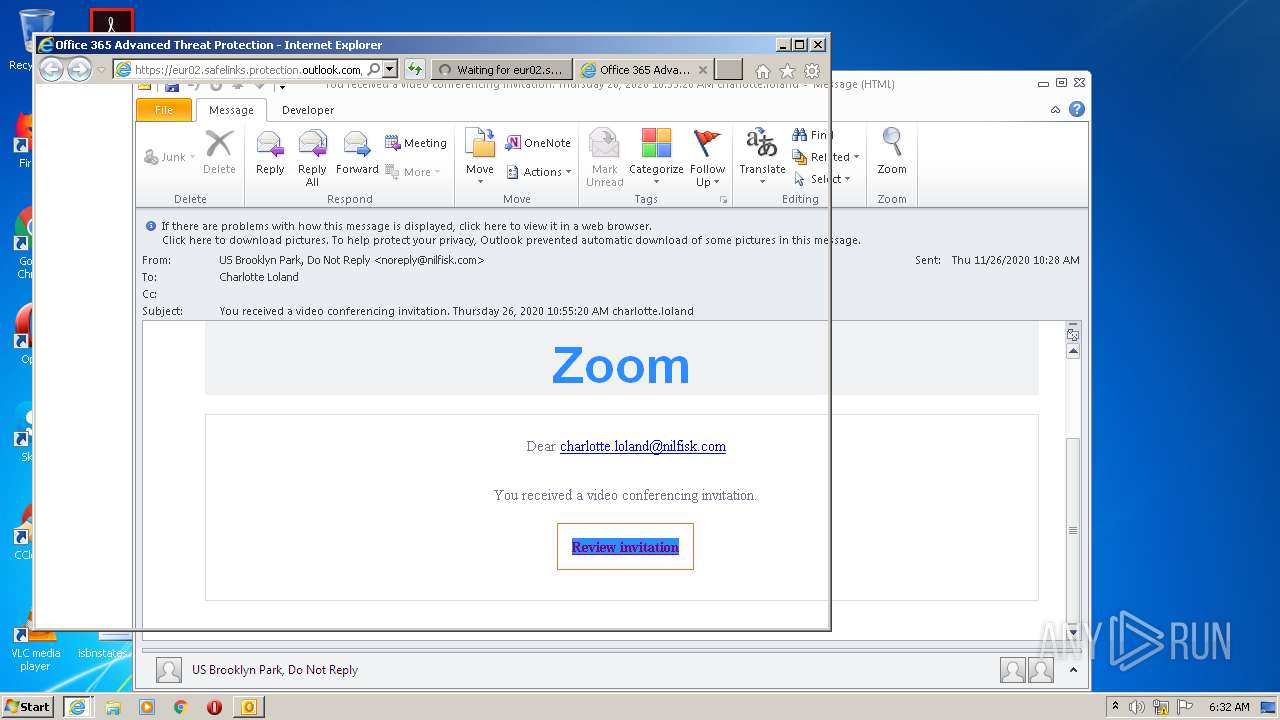
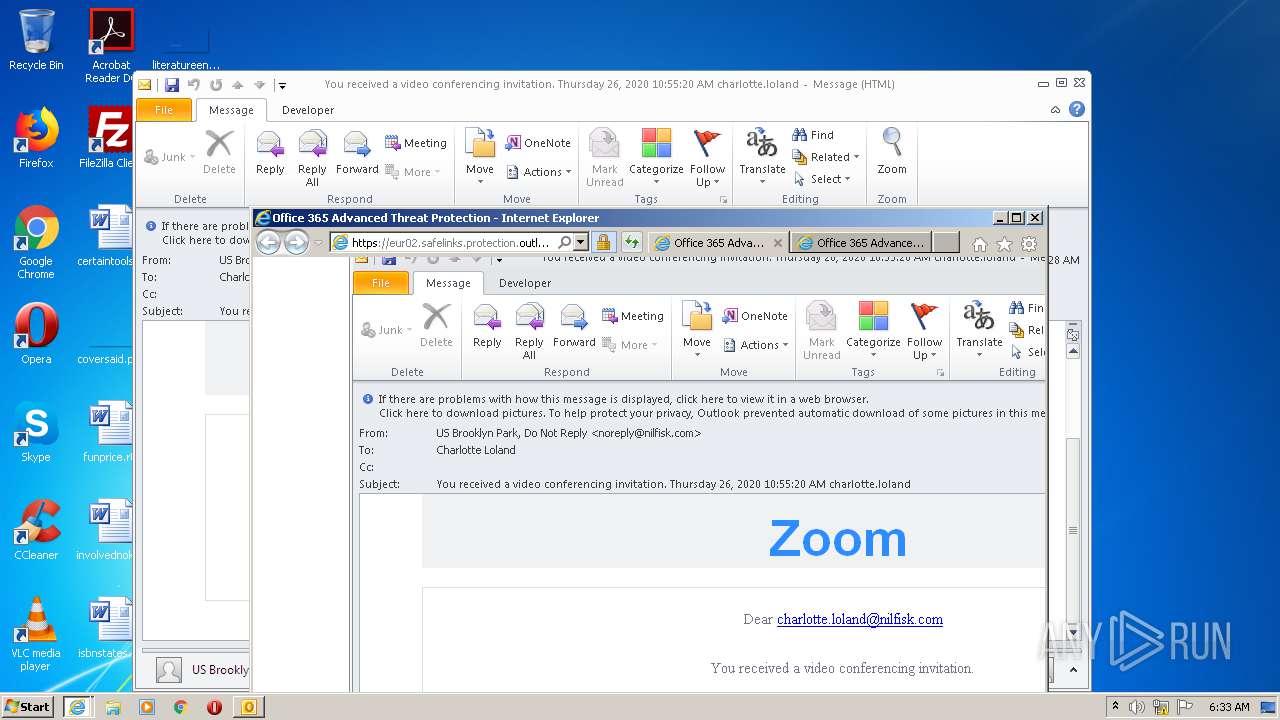
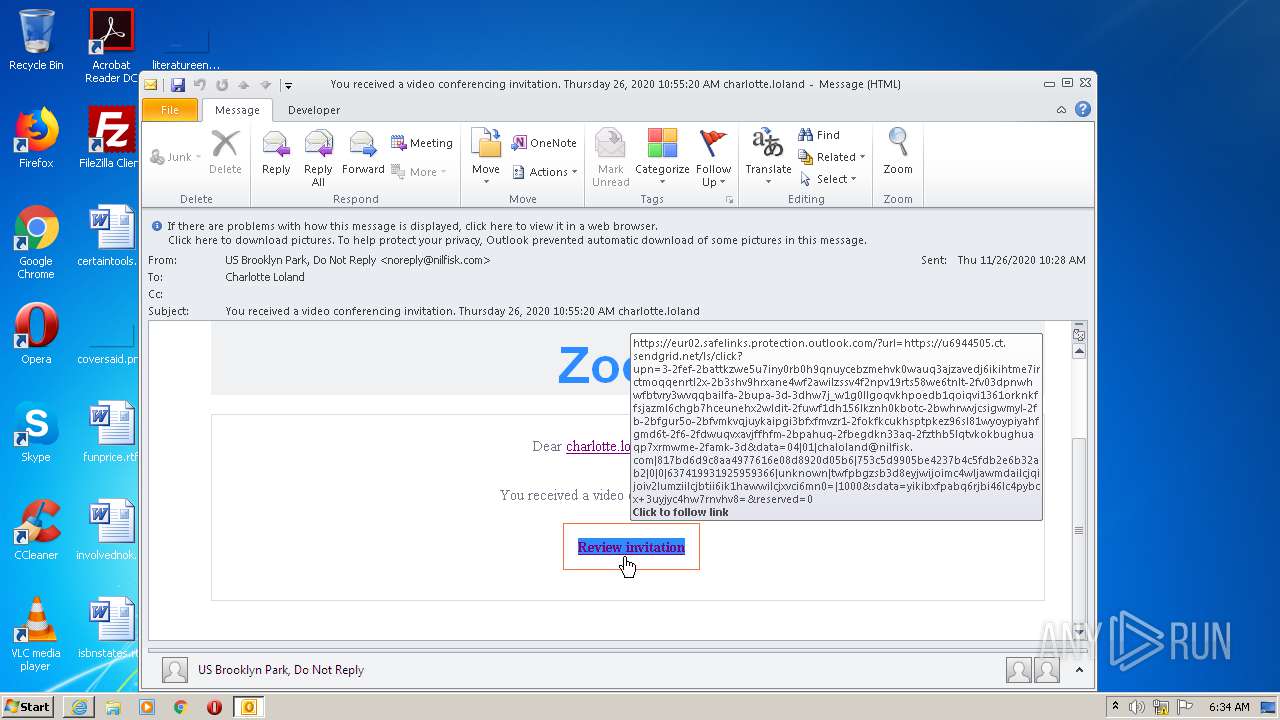
| 2672 | "C:\Program Files\Internet Explorer\iexplore.exe" https://eur02.safelinks.protection.outlook.com/?url=https%3A%2F%2Fu6944505.ct.sendgrid.net%2Fls%2Fclick%3Fupn%3D3-2FEf-2BATTkZwE5u7iny0Rb0H9qNUyceBzmEHVK0Wauq3aJzaVedj6IkIhtME7IrCTMoQqENrtL2x-2B3ShV9HRXanE4wf2aWIlzSSv4f2nPv19rTS58We6tnLT-2Fv03DpNWHwFBTVRY3wVQQBaILfA-2BuPA-3D-3DhW7J_W1g0lLgOQvKHpoedb1QOiqvi1361oRKNkfFsJAZml6cHgb7hCeUNehX2wLDiT-2FUWF1dH156lkznh0kBOTC-2BwHrWVjcsIgWmyl-2Fb-2BfGur5o-2BFVMkVqjuYKaiPGi3BFXFmvZr1-2FOKfkCUKhsptpkez96sl81wYoYPiYaHfgmd6T-2F6-2FDwUQvXaVJFfhFM-2BPaHUQ-2FbeGdkn33Aq-2FZTHB5lqtvkOkbughuAQP7xrmwme-2FAMk-3D&data=04%7C01%7Cchaloland%40nilfisk.com%7C817bd6d9c8aa4977616e08d8920d05b6%7C753c5d9905be4237b4c5fdb2e6b32ab2%7C0%7C0%7C637419931925959366%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C1000&sdata=YIKiBXfpaBQ6RjBI46lc4PYBcx%2B3uYJYc4hw7rnVHV8%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Internet Explorer\iexplore.exe" https://eur02.safelinks.protection.outlook.com/?url=https%3A%2F%2Fu6944505.ct.sendgrid.net%2Fls%2Fclick%3Fupn%3D3-2FEf-2BATTkZwE5u7iny0Rb0H9qNUyceBzmEHVK0Wauq3aJzaVedj6IkIhtME7IrCTMoQqENrtL2x-2B3ShV9HRXanE4wf2aWIlzSSv4f2nPv19rTS58We6tnLT-2Fv03DpNWHwFBTVRY3wVQQBaILfA-2BuPA-3D-3DhW7J_W1g0lLgOQvKHpoedb1QOiqvi1361oRKNkfFsJAZml6cHgb7hCeUNehX2wLDiT-2FUWF1dH156lkznh0kBOTC-2BwHrWVjcsIgWmyl-2Fb-2BfGur5o-2BFVMkVqjuYKaiPGi3BFXFmvZr1-2FOKfkCUKhsptpkez96sl81wYoYPiYaHfgmd6T-2F6-2FDwUQvXaVJFfhFM-2BPaHUQ-2FbeGdkn33Aq-2FZTHB5lqtvkOkbughuAQP7xrmwme-2FAMk-3D&data=04%7C01%7Cchaloland%40nilfisk.com%7C817bd6d9c8aa4977616e08d8920d05b6%7C753c5d9905be4237b4c5fdb2e6b32ab2%7C0%7C0%7C637419931925959366%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C1000&sdata=YIKiBXfpaBQ6RjBI46lc4PYBcx%2B3uYJYc4hw7rnVHV8%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3904 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2672 CREDAT:529674 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
3 381
Read events
2 153
Write events
1 194
Delete events
34
Modification events
| (PID) Process: | (2528) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2528) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2528) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2528) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2528) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2528) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2528) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2528) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2528) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2528) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
26
Text files
37
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2528 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR407D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1560 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7876.tmp | — | |
MD5:— | SHA256:— | |||
| 2528 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab87A8.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar87A9.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].htm | — | |
MD5:— | SHA256:— | |||
| 2404 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabC5AB.tmp | — | |
MD5:— | SHA256:— | |||
| 2404 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarC5AC.tmp | — | |
MD5:— | SHA256:— | |||
| 2528 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
27
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1560 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAGewca9P1l7sgwzOOVR2Hc%3D | US | der | 471 b | whitelisted |
2684 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2684 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 471 b | whitelisted |
1064 | svchost.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 564 b | whitelisted |
2684 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 471 b | whitelisted |
1064 | svchost.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | US | der | 813 b | whitelisted |
2684 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1560 | iexplore.exe | 104.47.6.28:443 | eur02.safelinks.protection.outlook.com | Microsoft Corporation | US | whitelisted |
2684 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2404 | iexplore.exe | 104.47.4.28:443 | eur02.safelinks.protection.outlook.com | Microsoft Corporation | NL | whitelisted |
2684 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1744 | iexplore.exe | 104.47.6.28:443 | eur02.safelinks.protection.outlook.com | Microsoft Corporation | US | whitelisted |
2672 | iexplore.exe | 104.47.6.28:443 | eur02.safelinks.protection.outlook.com | Microsoft Corporation | US | whitelisted |
1064 | svchost.exe | 104.79.89.142:80 | www.microsoft.com | Time Warner Cable Internet LLC | US | unknown |
— | — | 104.47.6.28:443 | eur02.safelinks.protection.outlook.com | Microsoft Corporation | US | whitelisted |
3904 | iexplore.exe | 104.47.6.28:443 | eur02.safelinks.protection.outlook.com | Microsoft Corporation | US | whitelisted |
— | — | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
eur02.safelinks.protection.outlook.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |