| File name: | baddoc.doc |
| Full analysis: | https://app.any.run/tasks/b221830f-18f6-4b6f-90e6-94ace7e407d0 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 10:17:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
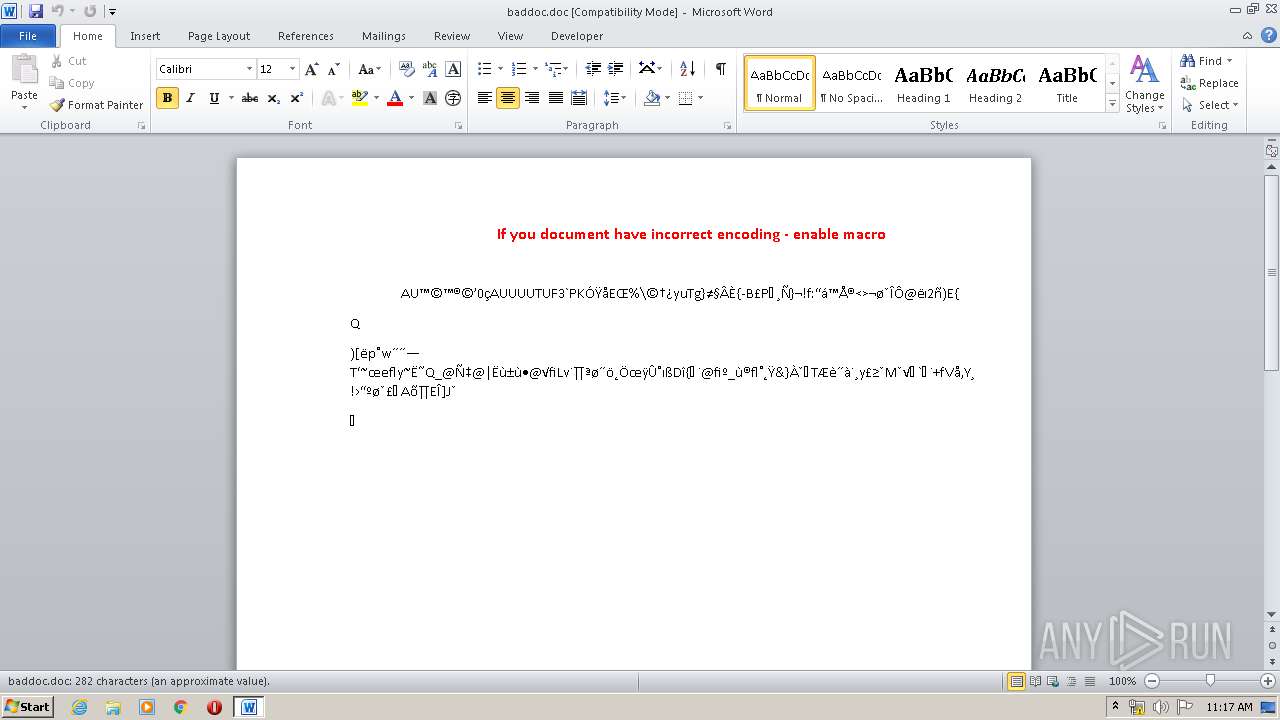
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Sun Feb 8 19:56:00 2015, Last Saved Time/Date: Tue Feb 10 15:27:00 2015, Number of Pages: 1, Number of Words: 51, Number of Characters: 291, Security: 0 |
| MD5: | A3B613D128AACE09241504E8ACC678C2 |
| SHA1: | EDDE71CCADFAD1380B881DA5ECAFC77FBA5885B8 |
| SHA256: | 8B92C23B29422131ACC150FA1EBAC67E1B0B0F8CFC1B727805B842A88DE447DE |
| SSDEEP: | 768:+0MGUUTYQin+b4C7UqCVuO1BtWmxzdrZUIdjXgAmxZp2j5s2p:+0MGUUTYQic8qS1XndrZf8pMV |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2156)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2156)
SUSPICIOUS
Executes PowerShell scripts
- cscript.exe (PID: 552)
Creates files in the user directory
- powershell.exe (PID: 1144)
Starts application with an unusual extension
- cmd.exe (PID: 2092)
Executes scripts
- cmd.exe (PID: 2092)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2156)
Creates files in the user directory
- WINWORD.EXE (PID: 2156)
Manual execution by user
- taskmgr.exe (PID: 2108)
- explorer.exe (PID: 2208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (35.9) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (33.7) |
| .doc | | | Microsoft Word document (old ver.) (21.3) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2015:02:08 19:56:00 |
| ModifyDate: | 2015:02:10 15:27:00 |
| Pages: | 1 |
| Words: | 51 |
| Characters: | 291 |
| Security: | None |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 341 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Windows Cyrillic |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | ???????? Microsoft Word 97-2003 |
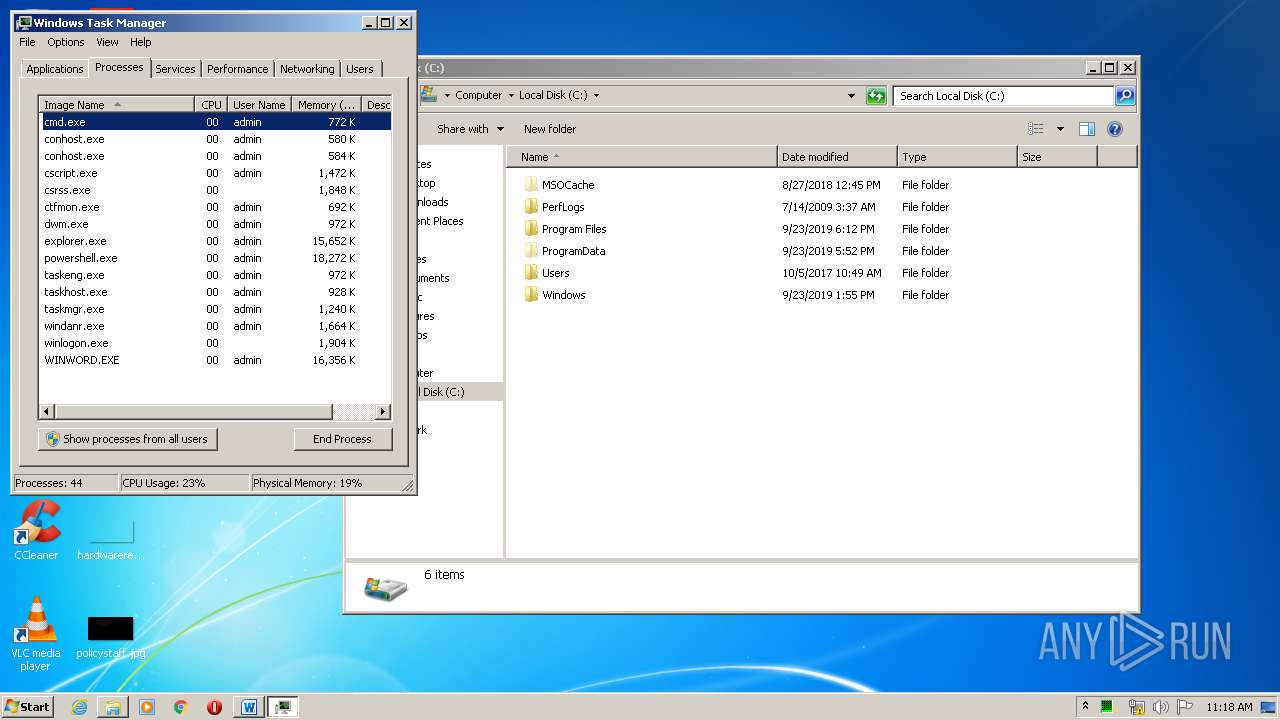
Total processes
48
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | cscript.exe "c:\Users\admin\AppData\Local\Temp\adobeacd-update"".""v""bs" | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 580 | ping 1.1.2.2 -n 2 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1144 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noexit -ExecutionPolicy bypass -noprofile -file C:\Users\admin\AppData\Local\Temp\adobeacd-update.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1884 | chcp 1251 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2092 | cmd /c c:\Users\admin\AppData\Local\Temp\adobeacd-update.bat | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2108 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\baddoc.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2208 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 947
Read events
1 228
Write events
645
Delete events
74
Modification events
| (PID) Process: | (2156) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | &d6 |
Value: 266436006C080000010000000000000000000000 | |||
| (PID) Process: | (2156) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2156) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2156) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2156) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2156) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2156) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2156) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2156) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2156) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
4
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9CA6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1144 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\I1S7EFAQ8JAW1WFGA14V.temp | — | |
MD5:— | SHA256:— | |||
| 2156 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2156 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 2156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$baddoc.doc | pgc | |
MD5:— | SHA256:— | |||
| 1144 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1144 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12d3e2.TMP | binary | |
MD5:— | SHA256:— | |||
| 2156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\adobeacd-update.vbs | text | |
MD5:969E1C8517CC2B734A1094AEF45AF8CD | SHA256:115508388A3ABF1674BE6A056459D5A2C9EE3627F8FBB4A03F73DA5598D37B5C | |||
| 2156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\adobeacd-update.ps1 | text | |
MD5:24FAA1509493E8C83213BC822FC1A12E | SHA256:F7AF75EE9948552E7E9A9DC8C9C5F3E5F64C01CFEA90F1EDE013CF9138F6EFC3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1144 | powershell.exe | GET | — | 91.220.131.44:80 | http://91.220.131.44/upd/install.exe | unknown | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.220.131.44:80 | — | — | — | suspicious |