| File name: | TSPlus_12.70.0.16.exe |
| Full analysis: | https://app.any.run/tasks/4dfd433e-8d53-49a8-a883-eda820f351b7 |
| Verdict: | Malicious activity |
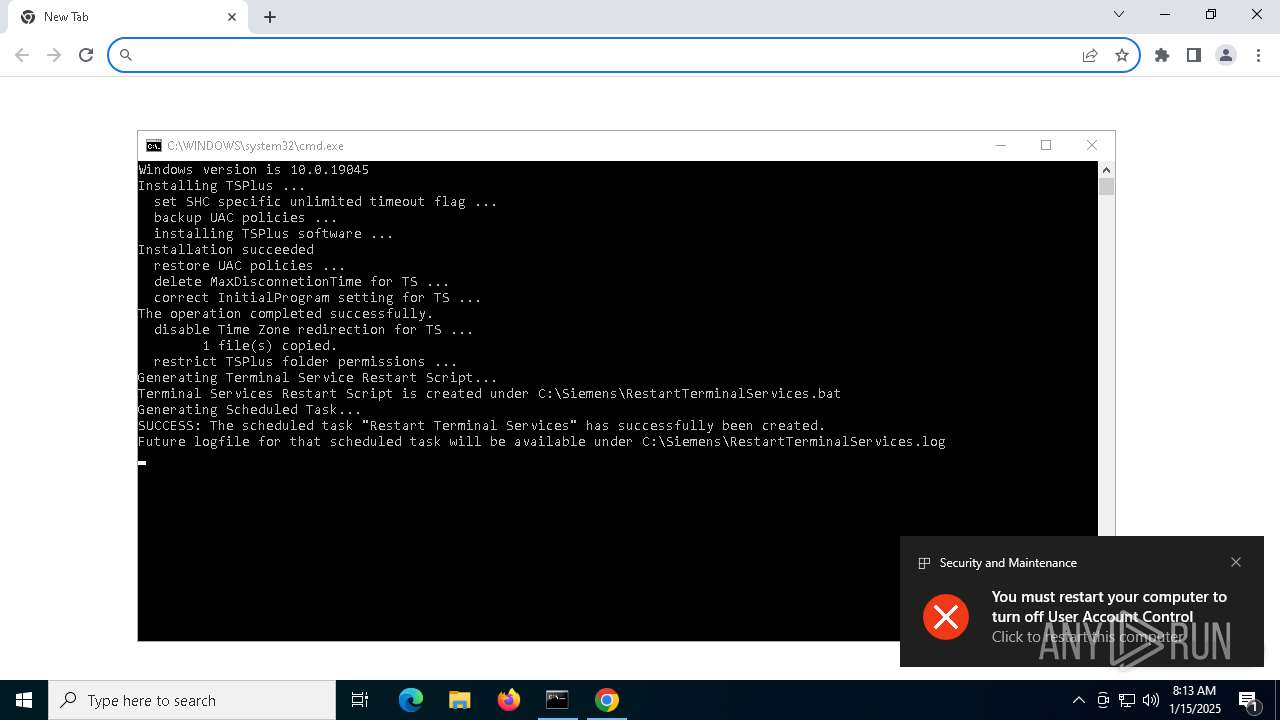
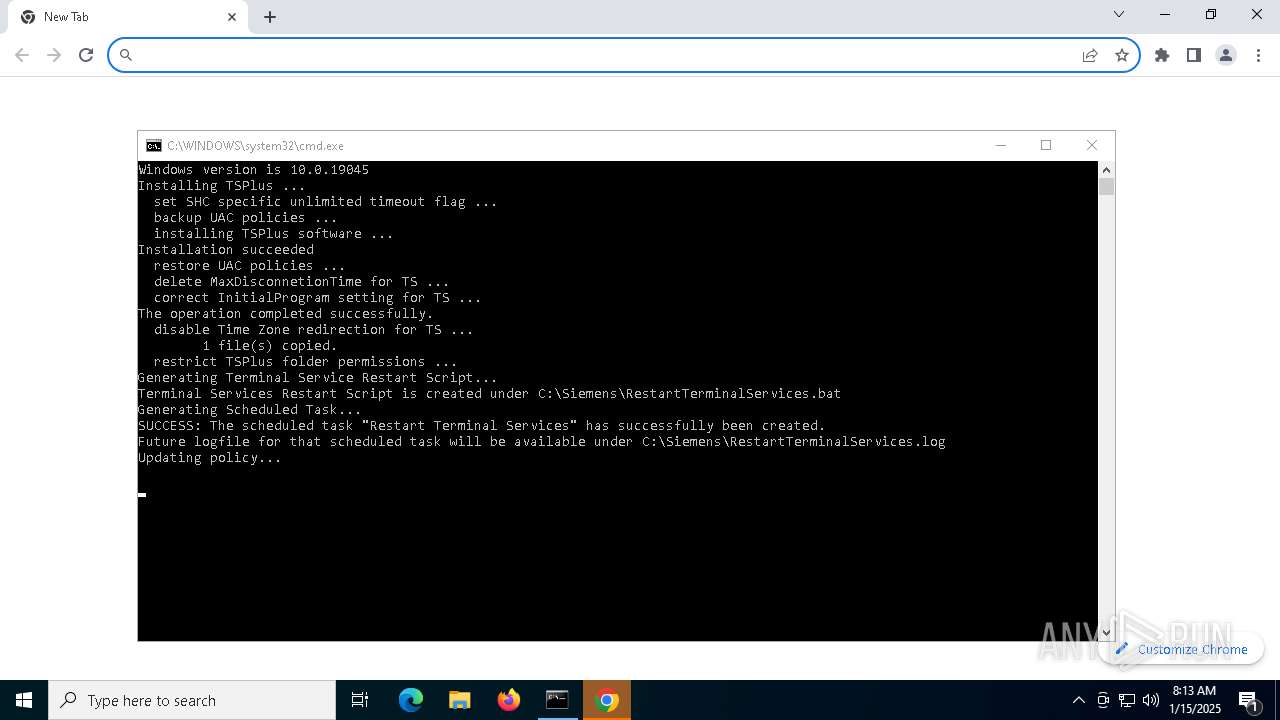
| Analysis date: | January 15, 2025, 08:13:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | FA7F9D2AA80E0EF977B1FEDBDED4B796 |
| SHA1: | AFE56572977CE5A714B272E4C85FB044CCC09C9F |
| SHA256: | 8B7CEF74F3A335B70756ABEB85D9356BE72DDD3D7387E07BB1ECEEC2D40AD8D7 |
| SSDEEP: | 98304:owUyDT1rdsO50tRcVb0onZMWuuJ714xpEtj0rmjBTilyQP20a9Z9yJX87D2hbA0l:vxBVE |
MALICIOUS
Process uses Reg.exe to dump credentials
- cmd.exe (PID: 6760)
Creates or modifies Windows services
- Setup-Siemens.exe (PID: 7008)
Starts NET.EXE for service management
- net.exe (PID: 2092)
- cmd.exe (PID: 5588)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 8124)
- net.exe (PID: 8180)
- cmd.exe (PID: 7576)
- net.exe (PID: 4824)
- net.exe (PID: 7068)
Runs injected code in another process
- svcmain.exe (PID: 6548)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 6760)
Application was injected by another process
- svchost.exe (PID: 2192)
SUSPICIOUS
Drops 7-zip archiver for unpacking
- TSPlus_12.70.0.16.exe (PID: 6164)
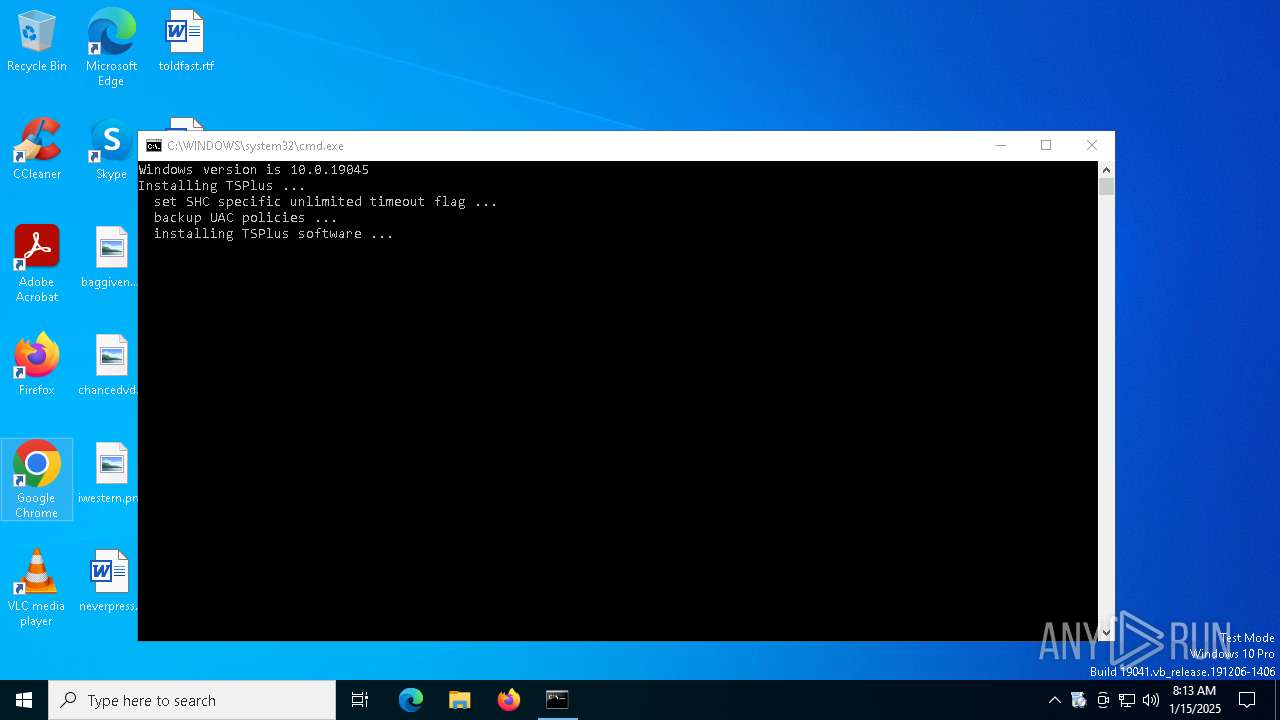
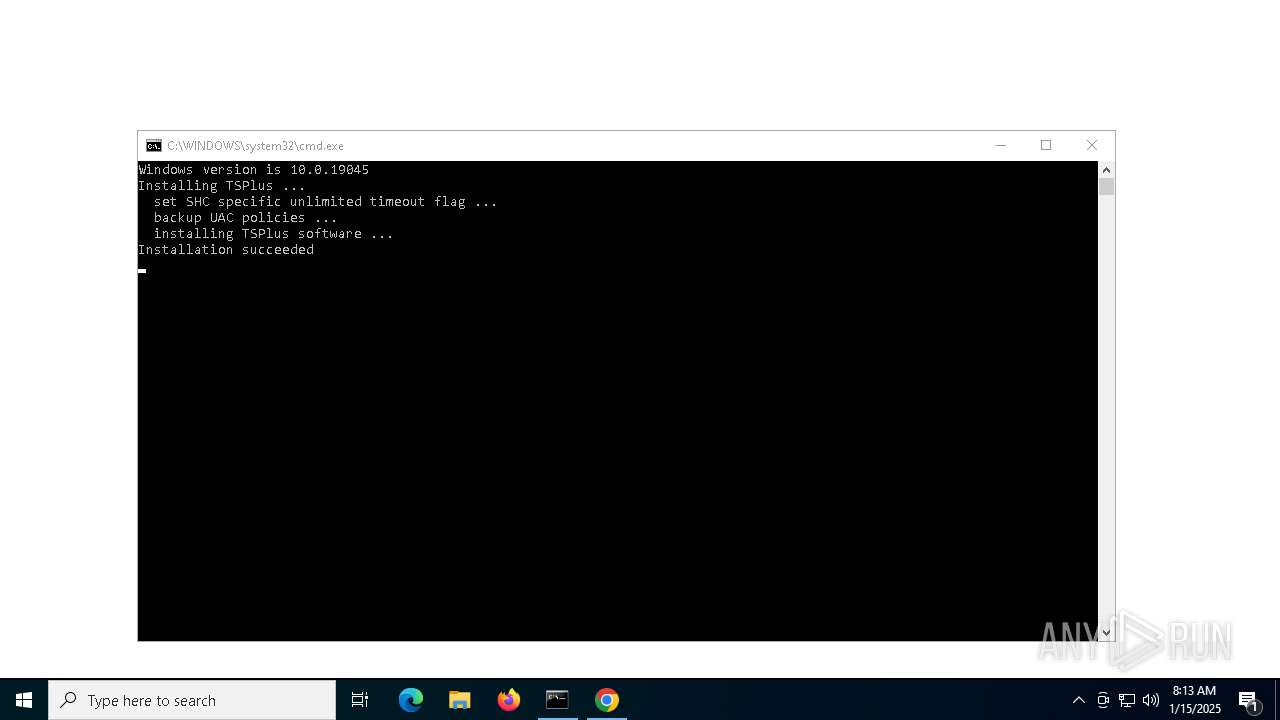
Executing commands from a ".bat" file
- TSPlus_12.70.0.16.exe (PID: 6164)
Starts CMD.EXE for commands execution
- TSPlus_12.70.0.16.exe (PID: 6164)
- cmd.exe (PID: 6760)
- Setup-Siemens.exe (PID: 7008)
Executable content was dropped or overwritten
- TSPlus_12.70.0.16.exe (PID: 6164)
- Setup-Siemens.exe (PID: 7008)
Application launched itself
- cmd.exe (PID: 6760)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 6816)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6816)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6760)
The executable file from the user directory is run by the CMD process
- Setup-Siemens.exe (PID: 7008)
Uses NETSH.EXE to change the status of the firewall
- cmd.exe (PID: 2612)
- cmd.exe (PID: 7108)
- cmd.exe (PID: 7100)
- cmd.exe (PID: 1344)
Potential Corporate Privacy Violation
- Setup-Siemens.exe (PID: 7008)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 6160)
- cmd.exe (PID: 2956)
- cmd.exe (PID: 1480)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 4932)
- cmd.exe (PID: 5300)
- cmd.exe (PID: 7124)
- cmd.exe (PID: 628)
Creates a software uninstall entry
- Setup-Siemens.exe (PID: 7008)
Windows service management via SC.EXE
- sc.exe (PID: 7848)
- sc.exe (PID: 8012)
Starts SC.EXE for service management
- cmd.exe (PID: 7072)
- cmd.exe (PID: 7944)
- cmd.exe (PID: 8040)
Sets the service to start on system boot
- sc.exe (PID: 8100)
Executes as Windows Service
- svcmain.exe (PID: 6548)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 6760)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6760)
INFO
Reads the computer name
- TSPlus_12.70.0.16.exe (PID: 6164)
- ShellExperienceHost.exe (PID: 7228)
Checks supported languages
- TSPlus_12.70.0.16.exe (PID: 6164)
- Setup-Siemens.exe (PID: 7008)
- ShellExperienceHost.exe (PID: 7228)
The sample compiled with english language support
- TSPlus_12.70.0.16.exe (PID: 6164)
- Setup-Siemens.exe (PID: 7008)
Create files in a temporary directory
- TSPlus_12.70.0.16.exe (PID: 6164)
- reg.exe (PID: 6988)
- Setup-Siemens.exe (PID: 7008)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6824)
- netsh.exe (PID: 6848)
Creates files or folders in the user directory
- Setup-Siemens.exe (PID: 7008)
Creates files in the program directory
- Setup-Siemens.exe (PID: 7008)
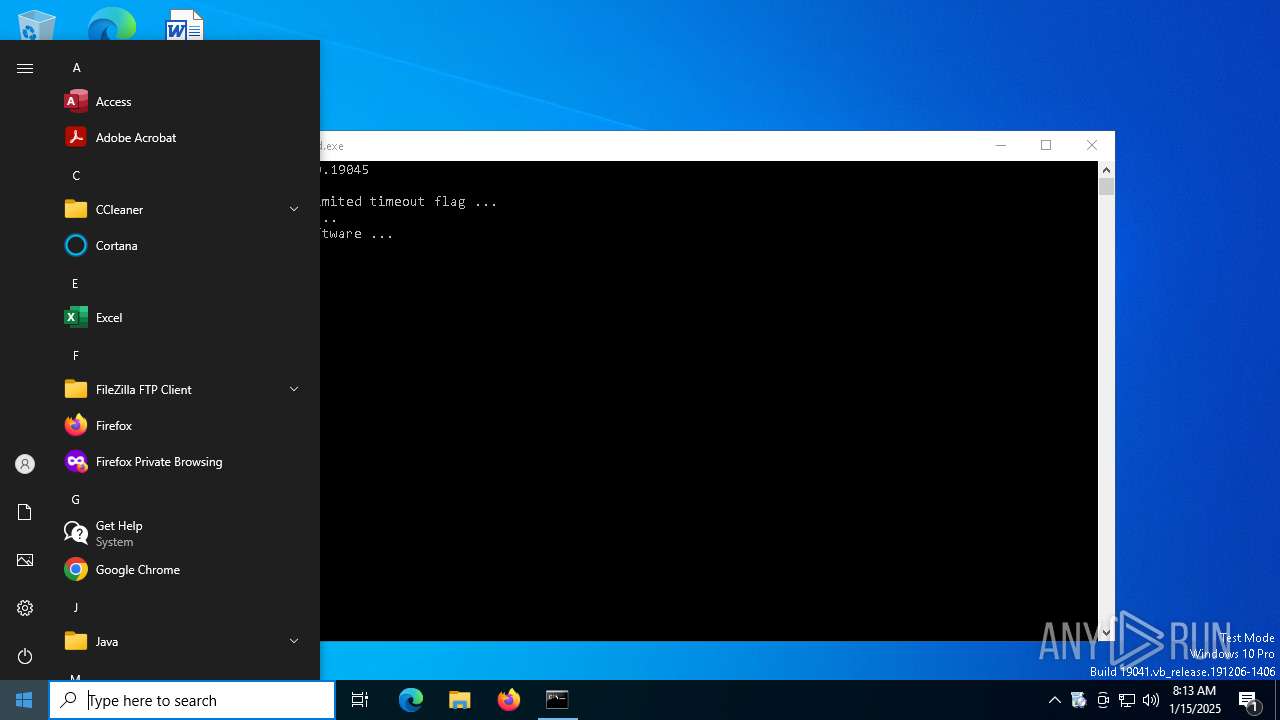
Manual execution by a user
- chrome.exe (PID: 1944)
Application launched itself
- chrome.exe (PID: 1944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:21 16:00:00+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 104448 |
| InitializedDataSize: | 28160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1910c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.0.0.0 |
| ProductVersionNumber: | 19.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 19 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2018 Igor Pavlov |
| OriginalFileName: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 19 |
Total processes
234
Monitored processes
96
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | netsh advfirewall firewall add rule name="Open Port 443" dir=in action=allow protocol=TCP localport=443 | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | C:\WINDOWS\system32\cmd.exe /c netsh firewall add portopening TCP 80 "HTTP" enable all | C:\Windows\System32\cmd.exe | — | Setup-Siemens.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1936 --field-trial-handle=1940,i,522522688443929993,11971750934205228836,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1344 | C:\WINDOWS\system32\cmd.exe /c netsh firewall set service remotedesktop enable | C:\Windows\System32\cmd.exe | — | Setup-Siemens.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1480 | C:\WINDOWS\system32\cmd.exe /c netsh firewall add portopening TCP 443 "HTTPS" enable all | C:\Windows\System32\cmd.exe | — | Setup-Siemens.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2004 | schtasks.exe /Create /RU "SYSTEM" /rl highest /SC ONSTART /TN "Restart Terminal Services" /TR "'C:\WINDOWS\System32\cmd.exe' /C C:\Siemens\RestartTerminalServices.bat > C:\Siemens\RestartTerminalServices.log" /F | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2092 | NET STOP SVCM | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 781
Read events
11 688
Write events
89
Delete events
4
Modification events
| (PID) Process: | (6964) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Siemens\syngo |
| Operation: | write | Name: | TS+ |
Value: 1 | |||
| (PID) Process: | (7008) Setup-Siemens.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\TermService\Parameters |
| Operation: | write | Name: | ServiceDll |
Value: %SystemRoot%\System32\termsrv.dll | |||
| (PID) Process: | (7008) Setup-Siemens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services |
| Operation: | write | Name: | MaxInstanceCount |
Value: 999999 | |||
| (PID) Process: | (7008) Setup-Siemens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services |
| Operation: | write | Name: | AllowSignedFiles |
Value: 1 | |||
| (PID) Process: | (7008) Setup-Siemens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services |
| Operation: | write | Name: | AllowUnsignedFiles |
Value: 1 | |||
| (PID) Process: | (7008) Setup-Siemens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services |
| Operation: | write | Name: | VisualExperiencePolicy |
Value: 2 | |||
| (PID) Process: | (7008) Setup-Siemens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services |
| Operation: | write | Name: | fPromptForPassword |
Value: 0 | |||
| (PID) Process: | (7008) Setup-Siemens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services |
| Operation: | write | Name: | fDisableCam |
Value: 0 | |||
| (PID) Process: | (7008) Setup-Siemens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services |
| Operation: | write | Name: | fDisableAudioCapture |
Value: 0 | |||
| (PID) Process: | (7008) Setup-Siemens.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services |
| Operation: | write | Name: | fDisableClip |
Value: 0 | |||
Executable files
5
Suspicious files
38
Text files
24
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7008 | Setup-Siemens.exe | C:\tmp\setup_versions.txt | binary | |
MD5:826270936F26452A167E0D2717A7B438 | SHA256:9151579CEE985DAC9664596B13016E8957E50C68C9B570DD15C757A1E39B0E11 | |||
| 6164 | TSPlus_12.70.0.16.exe | C:\Users\admin\AppData\Local\Temp\7zS418E6103\TSplus.cat | binary | |
MD5:D3031B7FD935211F319E995DF75260CD | SHA256:6BCABEE3B602B50950E07D6657BC7065E7A37B20BDCADFA2784DF37756377A16 | |||
| 6164 | TSPlus_12.70.0.16.exe | C:\Users\admin\AppData\Local\Temp\7zS418E6103\Install_TSPlus.bat | text | |
MD5:CCE6387C6B6C83FC8029B15E2BCD9CDA | SHA256:CB16D36BB8E2CEC2C59BE22DC1A4ED1D945F49533BE376AFD604FEB678599646 | |||
| 6164 | TSPlus_12.70.0.16.exe | C:\Users\admin\AppData\Local\Temp\7zS418E6103\TSplus.version | text | |
MD5:0020D1857DC14453AE04ACFE9F0D14DD | SHA256:5CBB96DCFF2A5C50780C6BE0F9BBDF5695C6210896B8600C3725C4AD1FA3FC54 | |||
| 6988 | reg.exe | C:\Users\admin\AppData\Local\Temp\UAC.reg | binary | |
MD5:1D35CBCFEEB164E304ABDEB31931FFE0 | SHA256:795EDF74E0529DE12AF432101062CB38B2C5B7D07CFF819DF7E3B7DD16818CCF | |||
| 7008 | Setup-Siemens.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\versions[1].txt | binary | |
MD5:826270936F26452A167E0D2717A7B438 | SHA256:9151579CEE985DAC9664596B13016E8957E50C68C9B570DD15C757A1E39B0E11 | |||
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF137bcb.TMP | — | |
MD5:— | SHA256:— | |||
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF137bda.TMP | — | |
MD5:— | SHA256:— | |||
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
44
DNS requests
29
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7008 | Setup-Siemens.exe | GET | 200 | 83.166.153.206:80 | http://update.dl-files.com/update/svcmain/versions.txt | CH | binary | 7.74 Kb | unknown |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | DE | binary | 471 b | whitelisted |
6248 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
1904 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | QA | binary | 419 b | whitelisted |
1904 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | QA | binary | 408 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3700 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 92.123.104.58:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
update.dl-files.com |
| unknown |
fp.msedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7008 | Setup-Siemens.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |