| File name: | Hangaroo.exe |
| Full analysis: | https://app.any.run/tasks/f99fecff-3fc7-4805-8d37-88f8f5a68bbe |
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2020, 07:00:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DC53653C0F94515F8A51234EBFA7A349 |
| SHA1: | 11B4BCC85B4DAAA1B4F5C58072A99DEEE25A73A8 |
| SHA256: | 8B6BD8204ECF1F4BC3AC5E061ADA757E3CCDE5862C543AD28EA1C1BE84AA3EEF |
| SSDEEP: | 12288:NhrQ94mER9Pn0Xi1em6M71qHfgudE0SXeoBcRAGiUGkHTxsgEYtOiVws7VnhWSG:XrmUPn+YJzKO5+jGkHTaYzqsdLG |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 352)
- Hangaroo.exe (PID: 868)
- hangaroo_proj.exe (PID: 2908)
Application was dropped or rewritten from another process
- hangaroo_proj.exe (PID: 2908)
SUSPICIOUS
Executable content was dropped or overwritten
- Hangaroo.exe (PID: 868)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 5 (56.3) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 3 (32.7) |
| .exe | | | InstallShield setup (5.3) |
| .exe | | | Win32 Executable Delphi generic (1.7) |
| .scr | | | Windows screen saver (1.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 99328 |
| InitializedDataSize: | 28160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x19304 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.32766.32766 |
| ProductVersionNumber: | 1.0.32766.32766 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | NetCent Communications |
| FileDescription: | HangARoo |
| FileVersion: | 1.1 |
| InternalName: | NCBuy Entertainment Network HangARoo |
| LegalCopyright: | © Copyright 2001 NetCent Communications |
| LegalTrademarks: | |
| OriginalFileName: | HangARoo.exe |
| ProductName: | HangARoo |
| ProductVersion: | 1.1 |
| Comments: | http://enetwork.ncbuy.com |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | NetCent Communications |
| FileDescription: | HangARoo |
| FileVersion: | 1.1 |
| InternalName: | NCBuy Entertainment Network HangARoo |
| LegalCopyright: | © Copyright 2001 NetCent Communications |
| LegalTrademarks: | - |
| OriginalFilename: | HangARoo.exe |
| ProductName: | HangARoo |
| ProductVersion: | 1.1 |
| Comments: | http://enetwork.ncbuy.com |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00018330 | 0x00018400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44212 |
DATA | 0x0001A000 | 0x00000848 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70087 |
BSS | 0x0001B000 | 0x000016B5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001D000 | 0x000012DA | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.77962 |
.tls | 0x0001F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00020000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00021000 | 0x000016E4 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.56345 |
.rsrc | 0x00023000 | 0x00004600 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.33801 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 1.82699 | 4548 | UNKNOWN | English - United Kingdom | RT_VERSION |
2 | 2.67254 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.10397 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
4090 | 2.42393 | 144 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.18646 | 792 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 2.96358 | 240 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.80205 | 192 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.27621 | 756 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.23595 | 896 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.16152 | 704 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
35
Monitored processes
3
Malicious processes
1
Suspicious processes
0
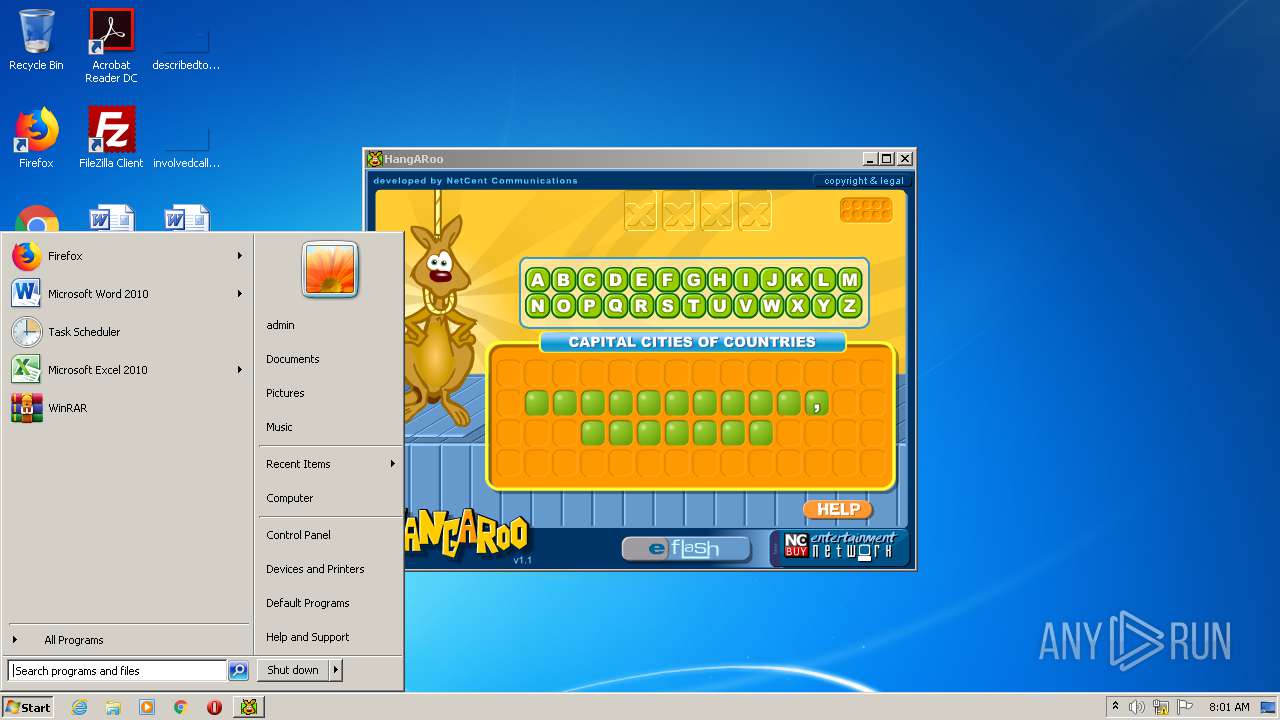
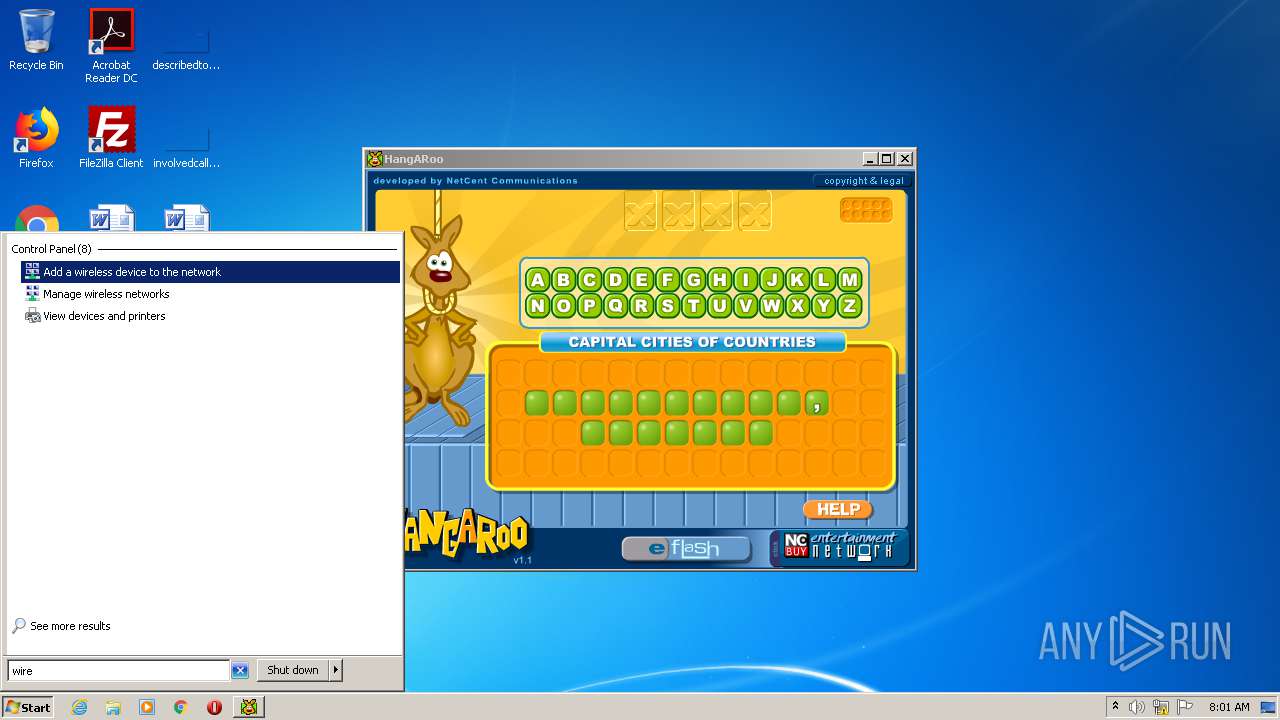
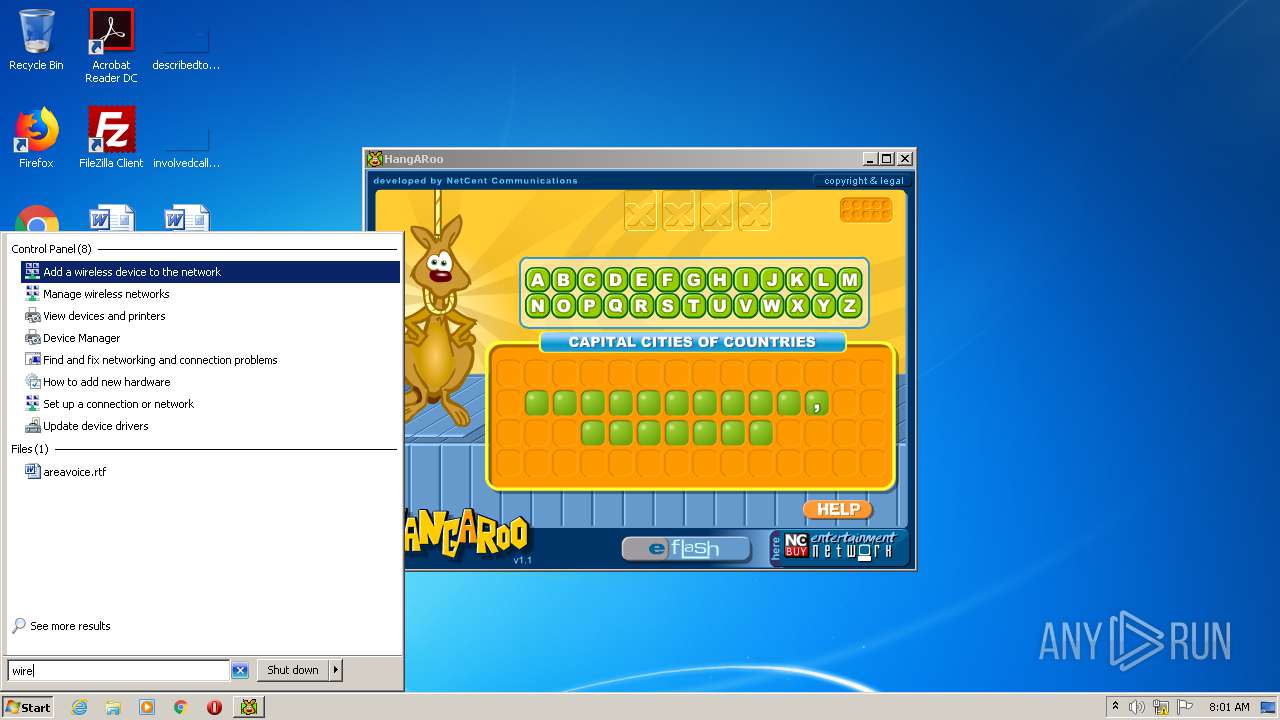
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 868 | "C:\Users\admin\AppData\Local\Temp\Hangaroo.exe" | C:\Users\admin\AppData\Local\Temp\Hangaroo.exe | explorer.exe | ||||||||||||
User: admin Company: NetCent Communications Integrity Level: MEDIUM Description: HangARoo Exit code: 0 Version: 1.1 Modules
| |||||||||||||||
| 2908 | "C:\Users\admin\AppData\Local\Temp\Jgl_Rt\hangaroo_proj.exe" | C:\Users\admin\AppData\Local\Temp\Jgl_Rt\hangaroo_proj.exe | — | Hangaroo.exe | |||||||||||
User: admin Company: Macromedia, Inc. Integrity Level: MEDIUM Description: Flash Player 5.0 r30 Exit code: 0 Version: 5,0,30,0 Modules
| |||||||||||||||
Total events
426
Read events
273
Write events
153
Delete events
0
Modification events
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\Unatnebb.rkr |
Value: 00000000000000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000490000006F000000572C30000C000000250000006D9313007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000030E9C9010000000000000000C0DB2C02050000002000000000000000000000000100000064666C7464666C7400000000400000000459FF754803016300000000000000000100000000000000000000000000000000000000E803000000000000FFFFFFFF000000000000000008B72C02CCE8C90105000000FFFFFFFFAC54FF75000000000000000000000000C054FF754803016308B72C0200000000622902764803016308B72C0205000000D80B2C020000000040EBC90148EBC901C0DB2C02940A2C0220000000000000000000000000000000000000000500000000000000010000006C61746E64666C740000000011000000483D2B00403D2B0000EAC9012261FF754803016320EA0000F71FA3B6D4E9C9018291307620EAC90134A300009B1FA3B6E8E9C901B69C307638A31F024C06000000EAC901A89E1F020CEAC90111000000483D2B00403D2B0000EAC901C89E1F0270EA0000431CA3B620EAC9018291307670EAC90124EAC901279530760000000034A31F024CEAC901CD94307634A31F02F8EAC901A89E1F02E194307600000000A89E1F02F8EAC90154EAC9010C000000250000006D9313007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000030E9C9010000000000000000C0DB2C02050000002000000000000000000000000100000064666C7464666C7400000000400000000459FF754803016300000000000000000100000000000000000000000000000000000000E803000000000000FFFFFFFF000000000000000008B72C02CCE8C90105000000FFFFFFFFAC54FF75000000000000000000000000C054FF754803016308B72C0200000000622902764803016308B72C0205000000D80B2C020000000040EBC90148EBC901C0DB2C02940A2C0220000000000000000000000000000000000000000500000000000000010000006C61746E64666C740000000011000000483D2B00403D2B0000EAC9012261FF754803016320EA0000F71FA3B6D4E9C9018291307620EAC90134A300009B1FA3B6E8E9C901B69C307638A31F024C06000000EAC901A89E1F020CEAC90111000000483D2B00403D2B0000EAC901C89E1F0270EA0000431CA3B620EAC9018291307670EAC90124EAC901279530760000000034A31F024CEAC901CD94307634A31F02F8EAC901A89E1F02E194307600000000A89E1F02F8EAC90154EAC9010C000000250000006D9313007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000030E9C9010000000000000000C0DB2C02050000002000000000000000000000000100000064666C7464666C7400000000400000000459FF754803016300000000000000000100000000000000000000000000000000000000E803000000000000FFFFFFFF000000000000000008B72C02CCE8C90105000000FFFFFFFFAC54FF75000000000000000000000000C054FF754803016308B72C0200000000622902764803016308B72C0205000000D80B2C020000000040EBC90148EBC901C0DB2C02940A2C0220000000000000000000000000000000000000000500000000000000010000006C61746E64666C740000000011000000483D2B00403D2B0000EAC9012261FF754803016320EA0000F71FA3B6D4E9C9018291307620EAC90134A300009B1FA3B6E8E9C901B69C307638A31F024C06000000EAC901A89E1F020CEAC90111000000483D2B00403D2B0000EAC901C89E1F0270EA0000431CA3B620EAC9018291307670EAC90124EAC901279530760000000034A31F024CEAC901CD94307634A31F02F8EAC901A89E1F02E194307600000000A89E1F02F8EAC90154EAC901 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ApplicationDestinations |
| Operation: | write | Name: | MaxEntries |
Value: 15 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 010000000000000002000000070000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 868 | Hangaroo.exe | C:\Users\admin\AppData\Local\Temp\hangaroo.ini | — | |
MD5:— | SHA256:— | |||
| 868 | Hangaroo.exe | C:\Users\admin\AppData\Local\Temp\Jgl_Rt\hangaroo_proj.exe | executable | |
MD5:1C3976CDAEA6834FC687806552318910 | SHA256:19AAAEF723087D95E6AC6A08E9A96CD90982DD36B01AE4AB1C2BE4AA9D3ECF89 | |||
| 868 | Hangaroo.exe | C:\Users\admin\AppData\Local\Temp\Jgl_Rt\jweb.exe | executable | |
MD5:29282FC5703E13226477240BF1C8070C | SHA256:EBA601B90AC44BFFDA6D7E725AD6A21A838C405FDFB9DC35F8FD02DBCE0BADC0 | |||
| 868 | Hangaroo.exe | C:\Users\admin\AppData\Local\Temp\Jgl_Rt\jesterrun0.dll | executable | |
MD5:4790B1E1397B3777002B8C6B233C5B11 | SHA256:B7B412298B3DA546FE0F7E3F732C4ED5AAE678D401CAD662CD1E9C3978B4E13E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report