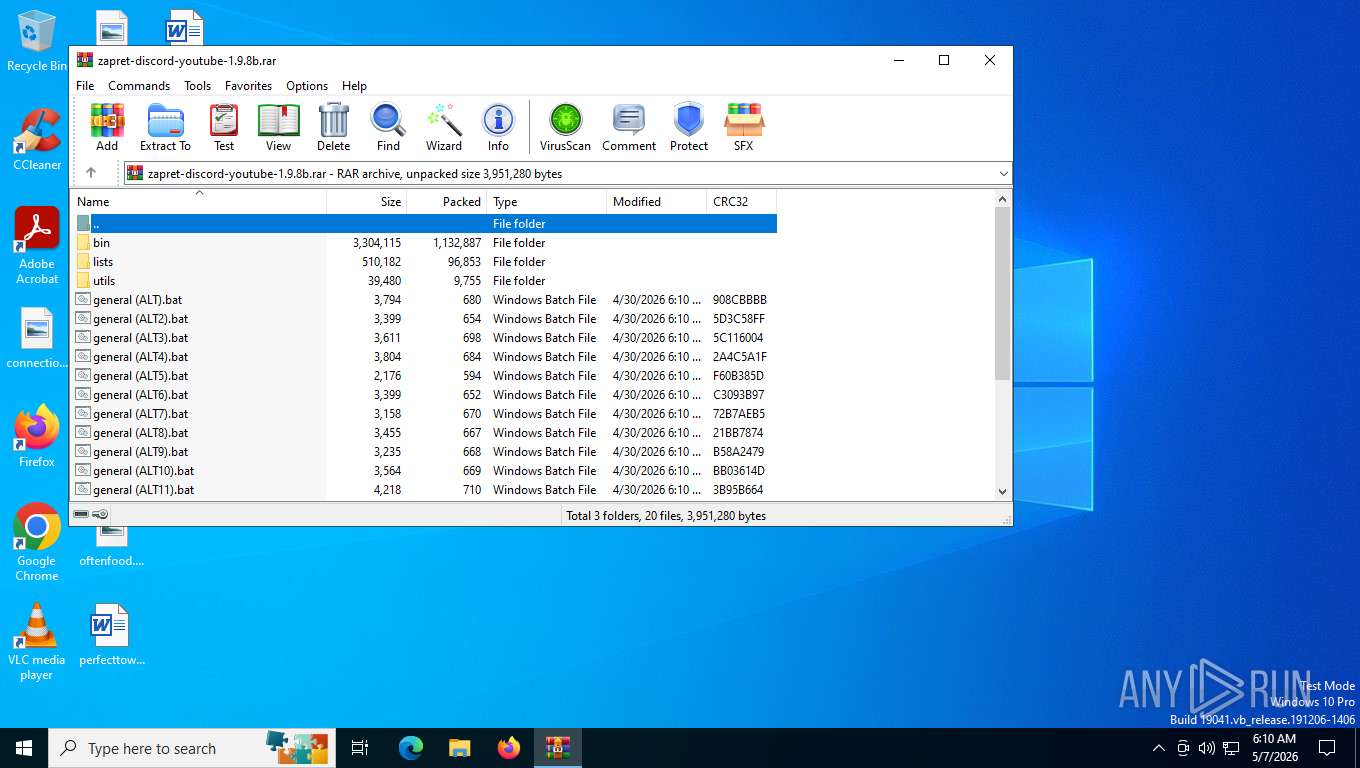
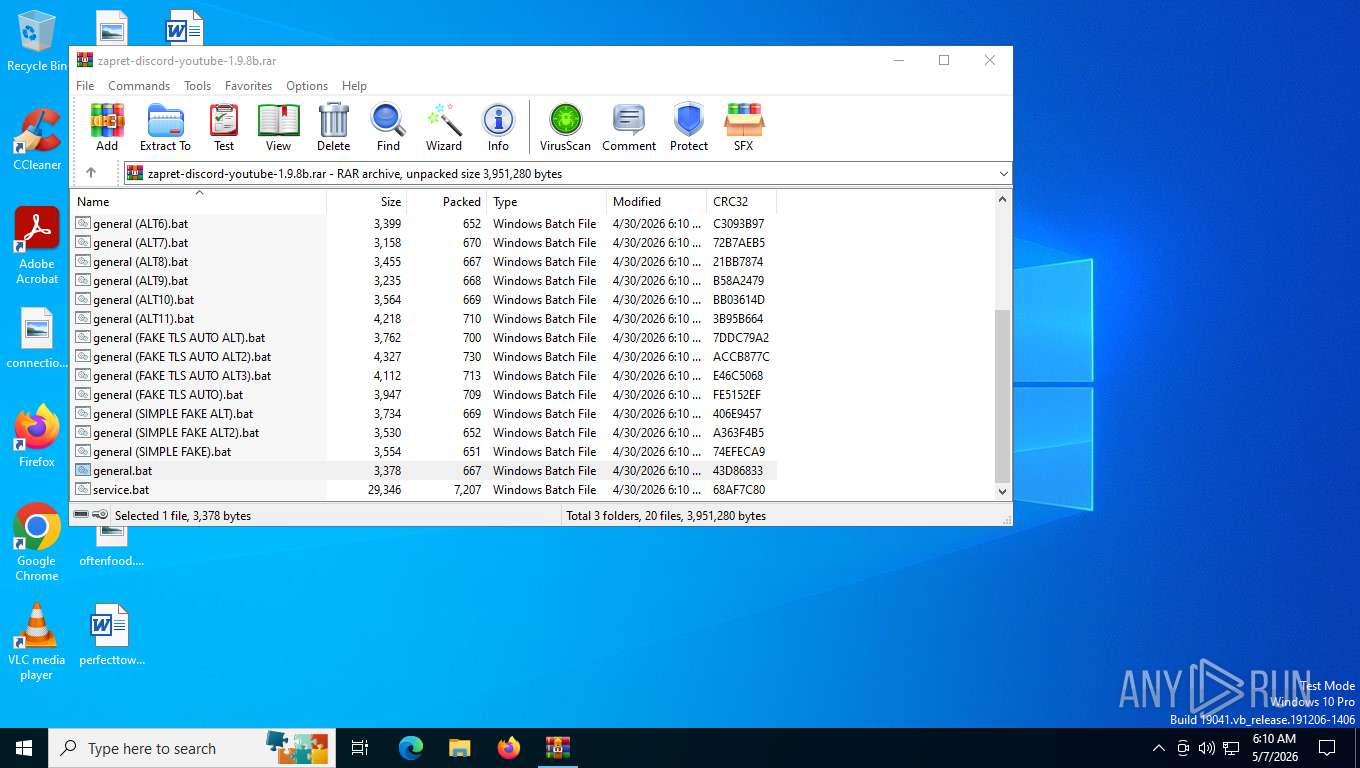
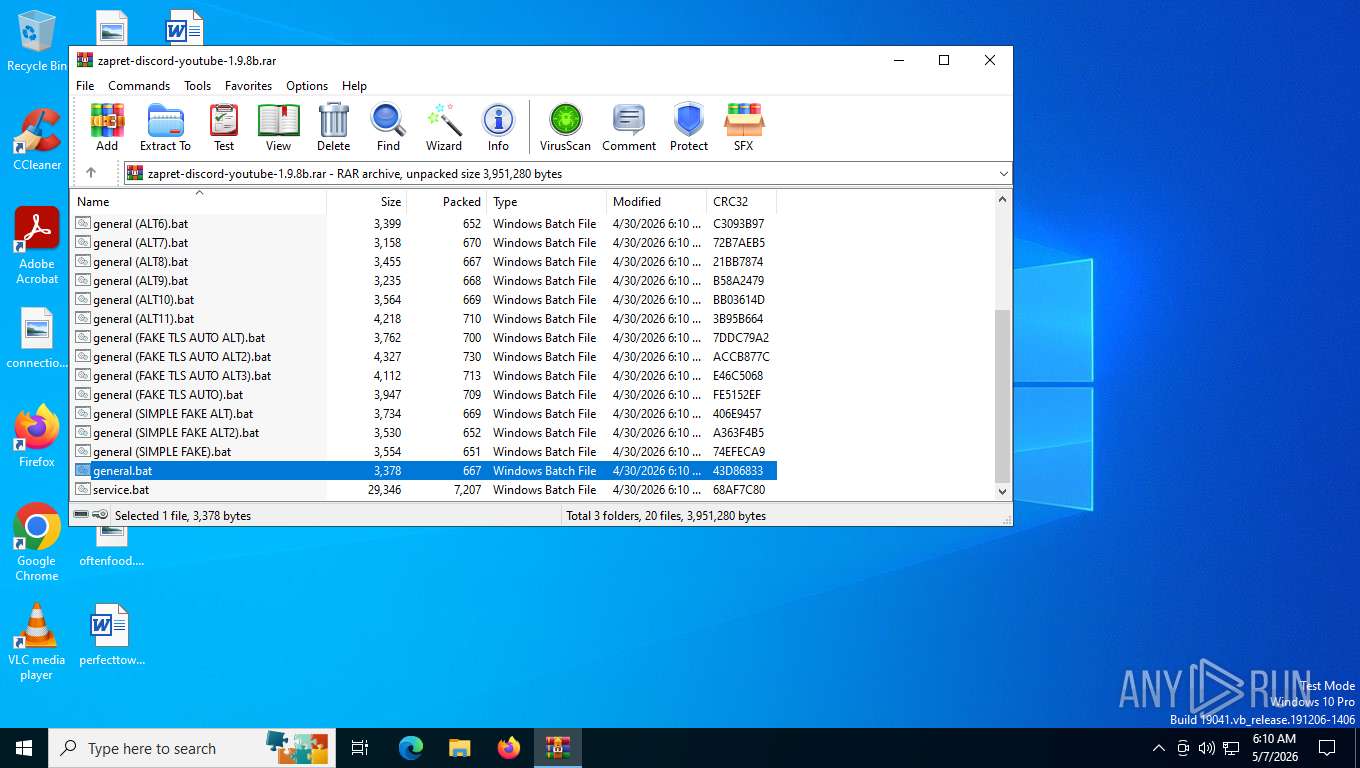
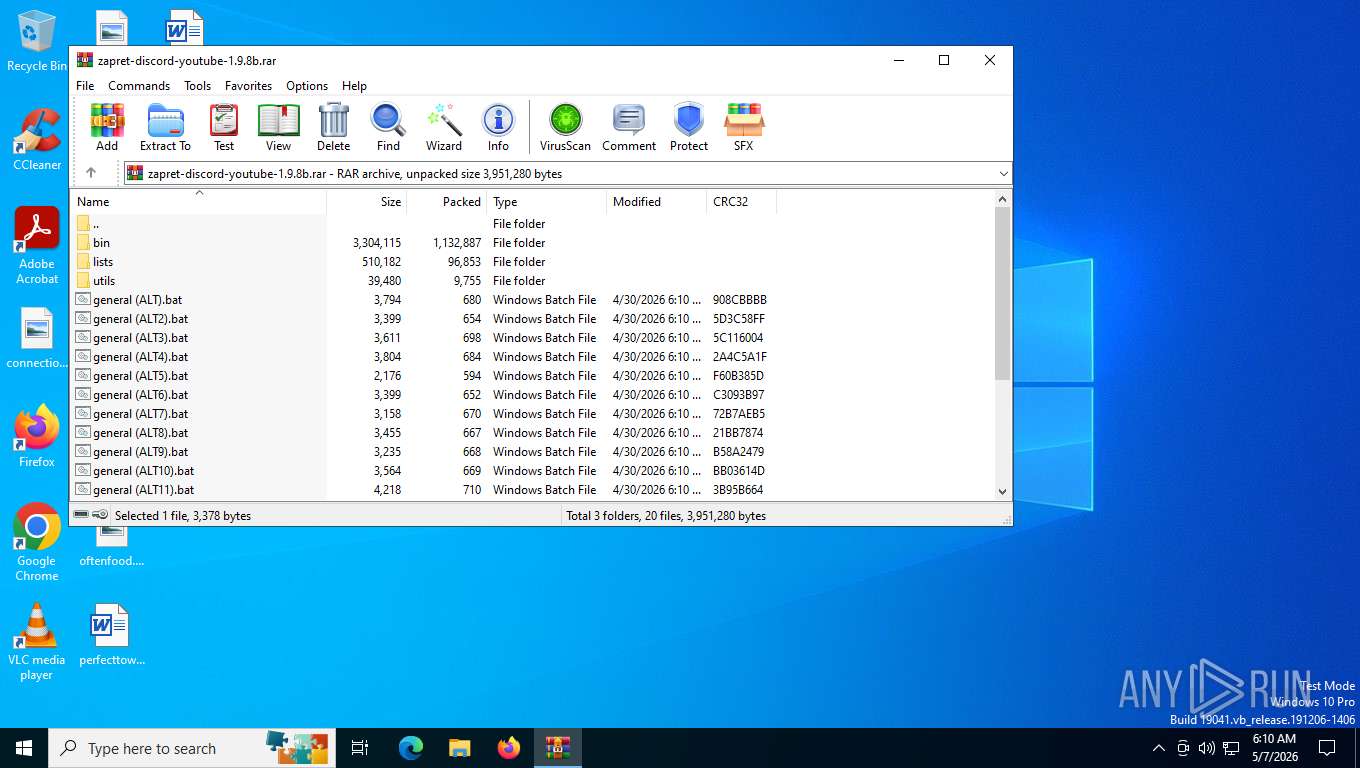
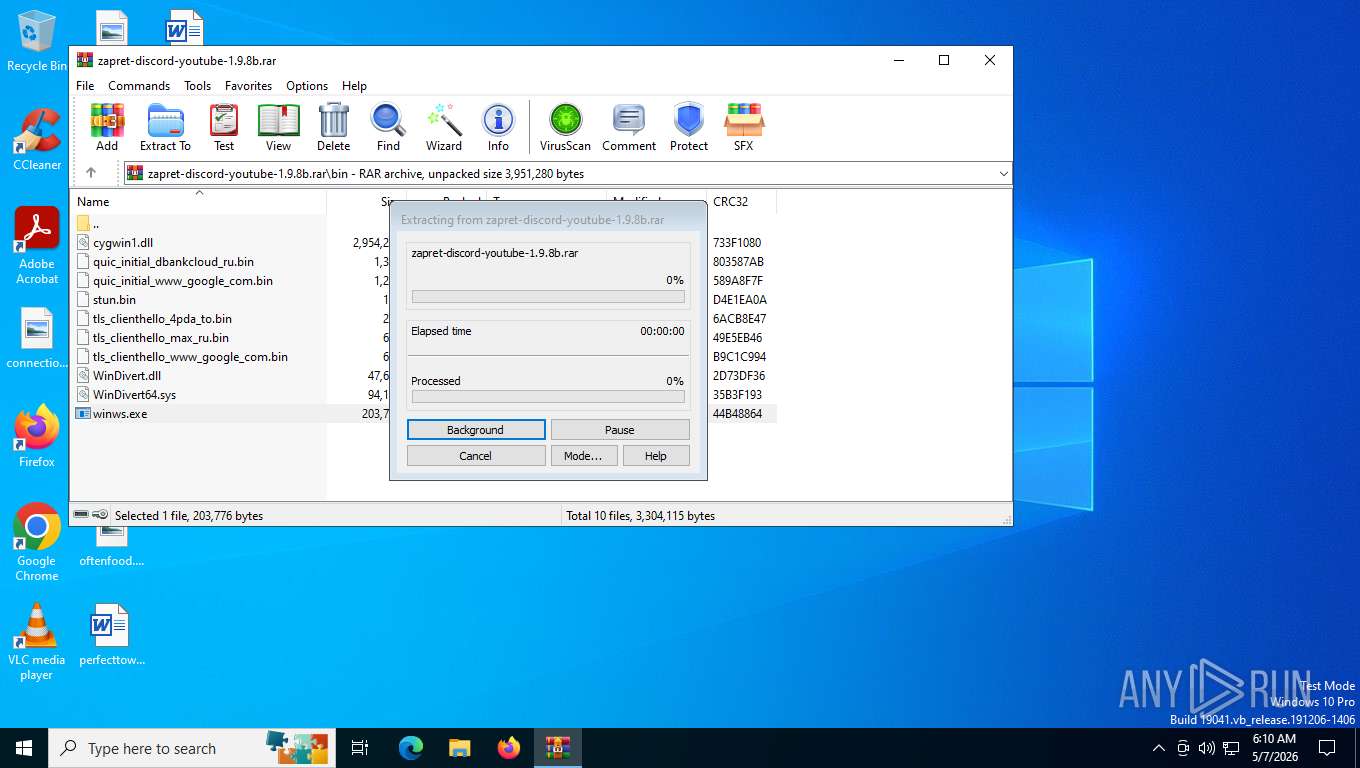
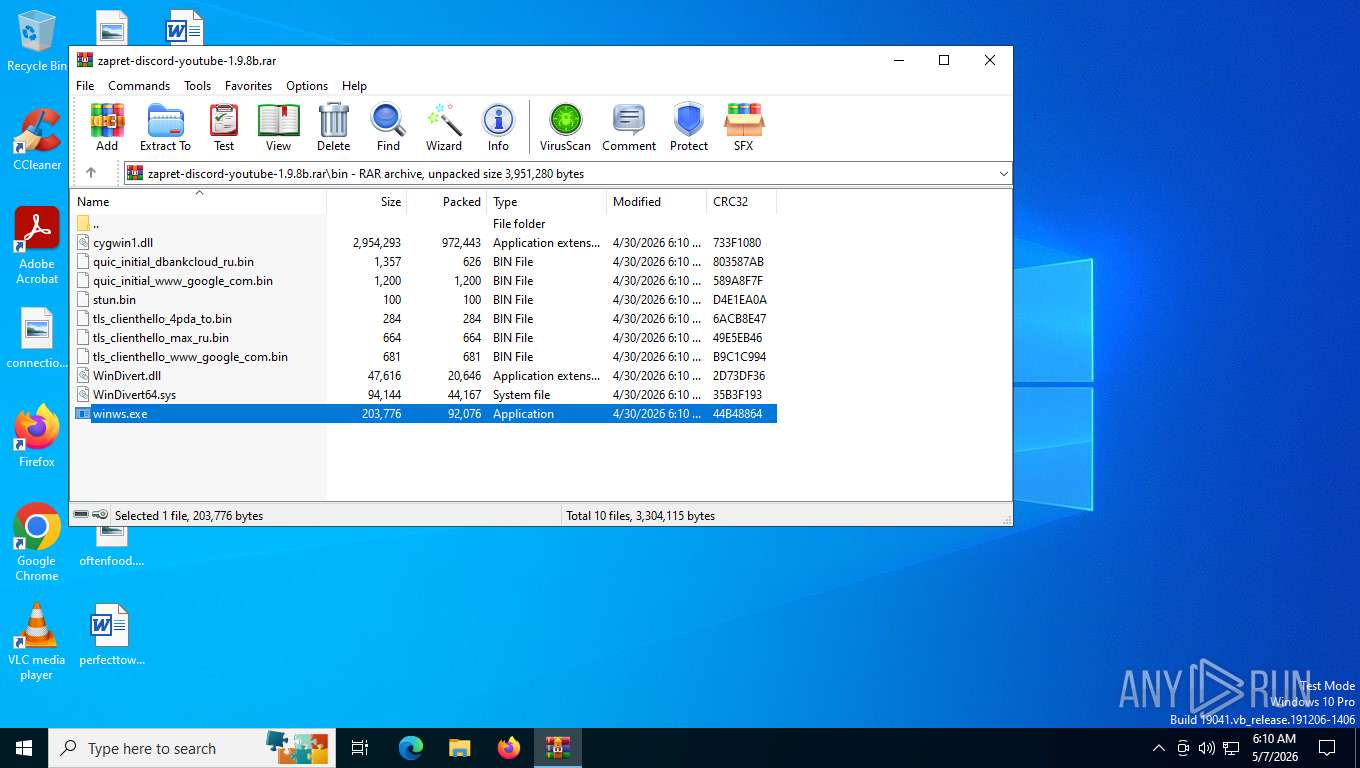
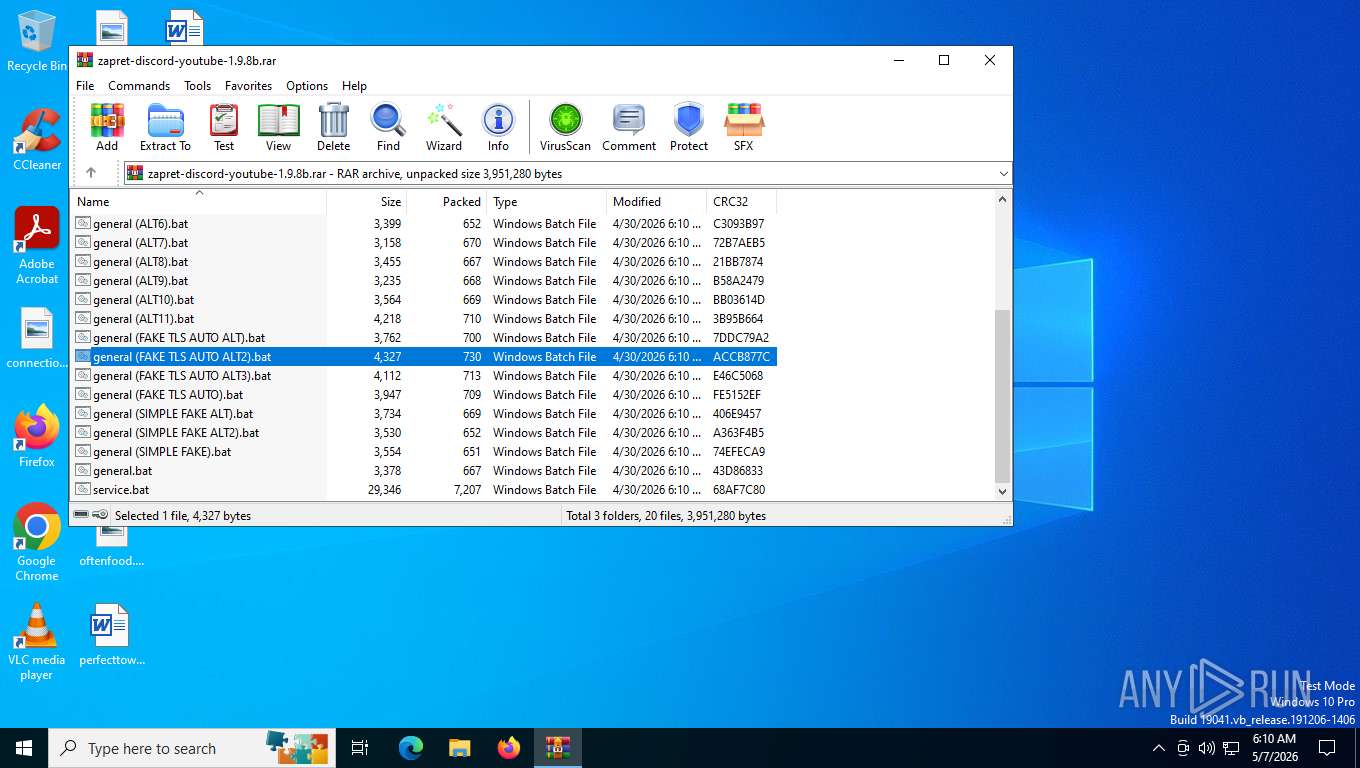
| File name: | zapret-discord-youtube-1.9.8b.rar |
| Full analysis: | https://app.any.run/tasks/dd19afb5-735d-4c28-9248-9ce5e17f9fb4 |
| Verdict: | Malicious activity |
| Analysis date: | May 07, 2026, 10:09:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
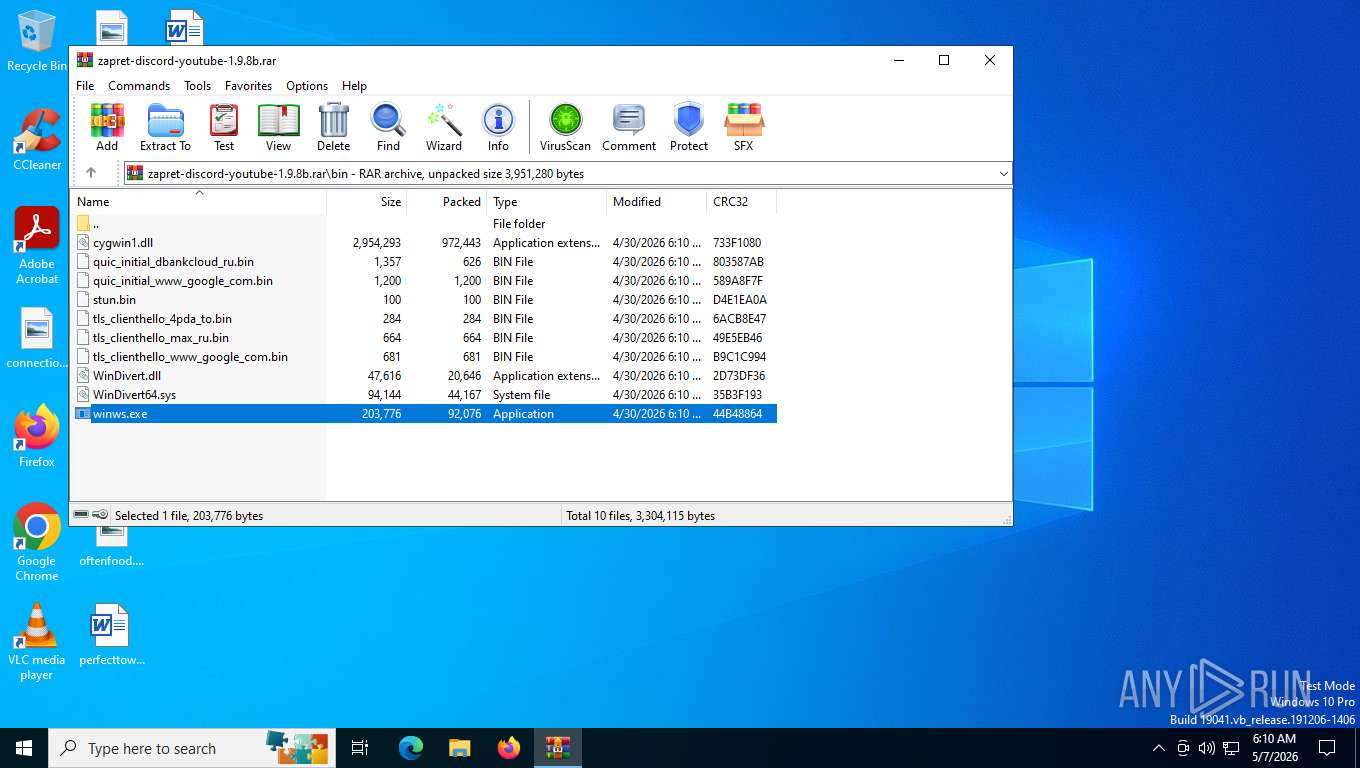
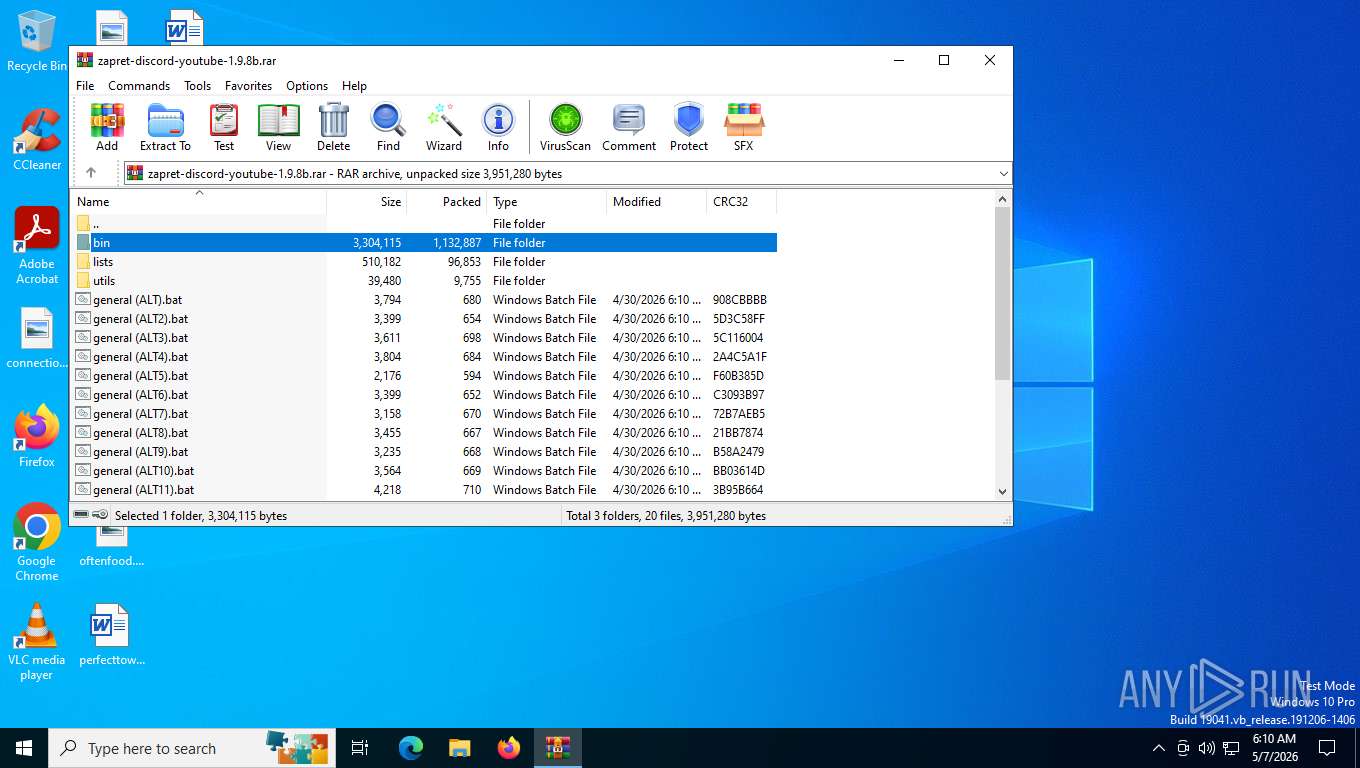
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | D2DA9EBDA1B4C29C547A4C422C31822F |
| SHA1: | 380A59843A1F4F8FA98EB2036668E45982B8287B |
| SHA256: | 8B57786CEA540DAAA73DADAAEC12ADB7EF93EA95271352A8D619149E0250A2EE |
| SSDEEP: | 49152:0yRG33TZ0b4FMyNCQMf5udb/DNj7Ze9rm45sDC69wDe1fwTCFvppsBS9VWIwQtk2:tRg0b4utV58b/Jj789rv5D6uDefjFvpr |
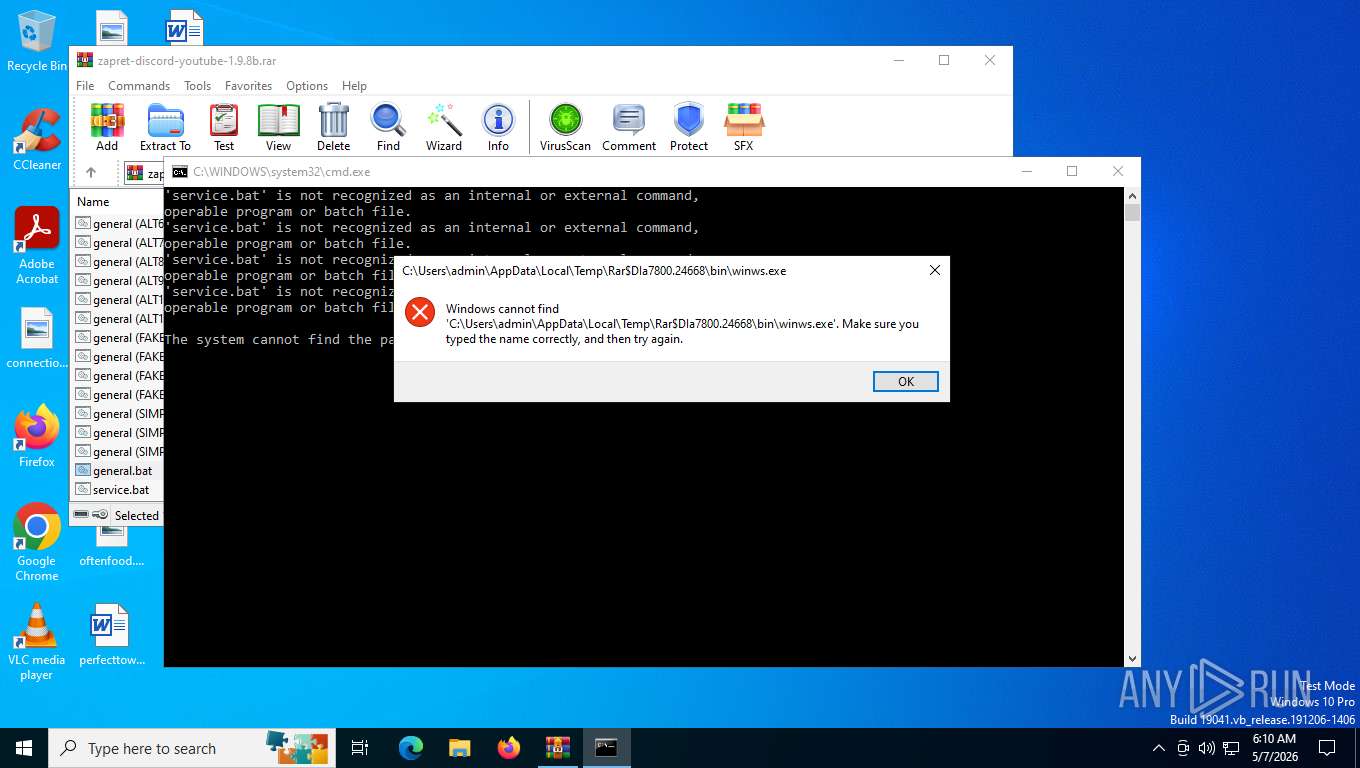
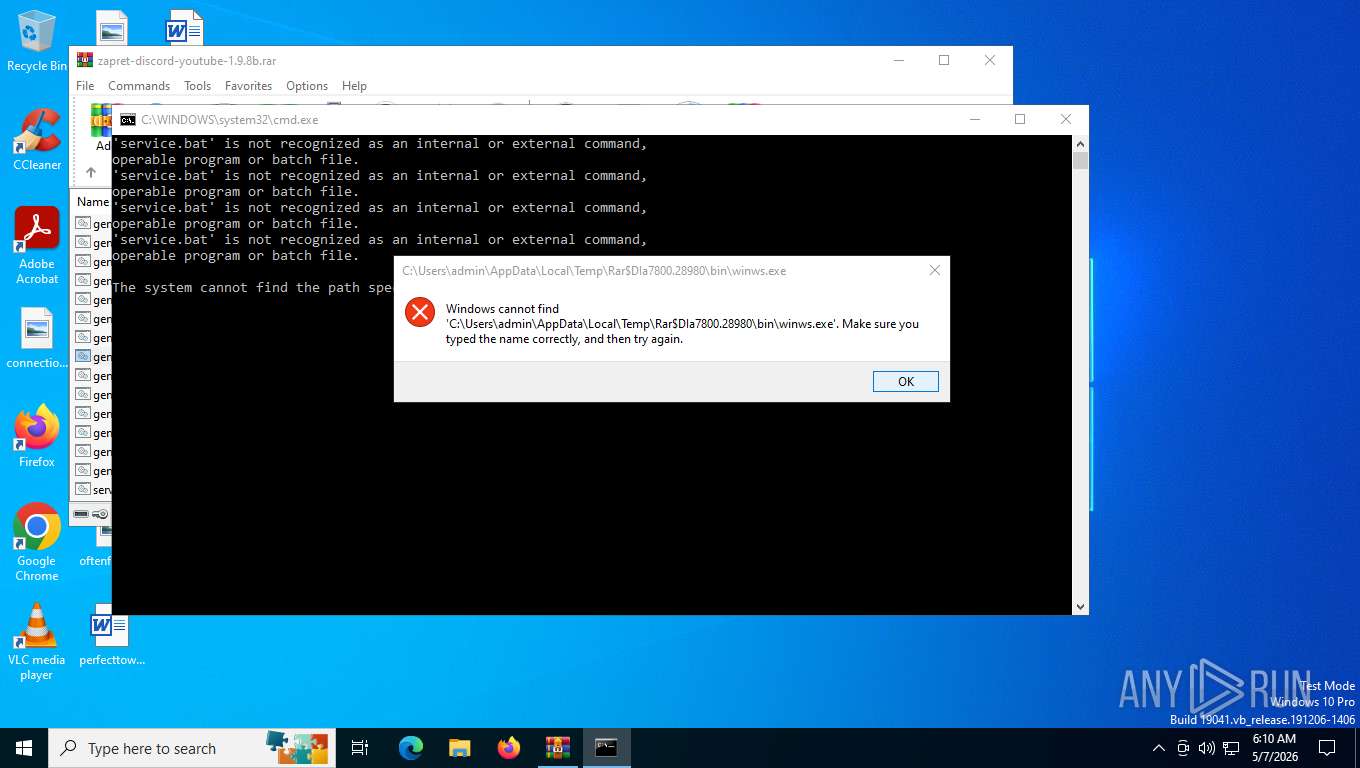
MALICIOUS
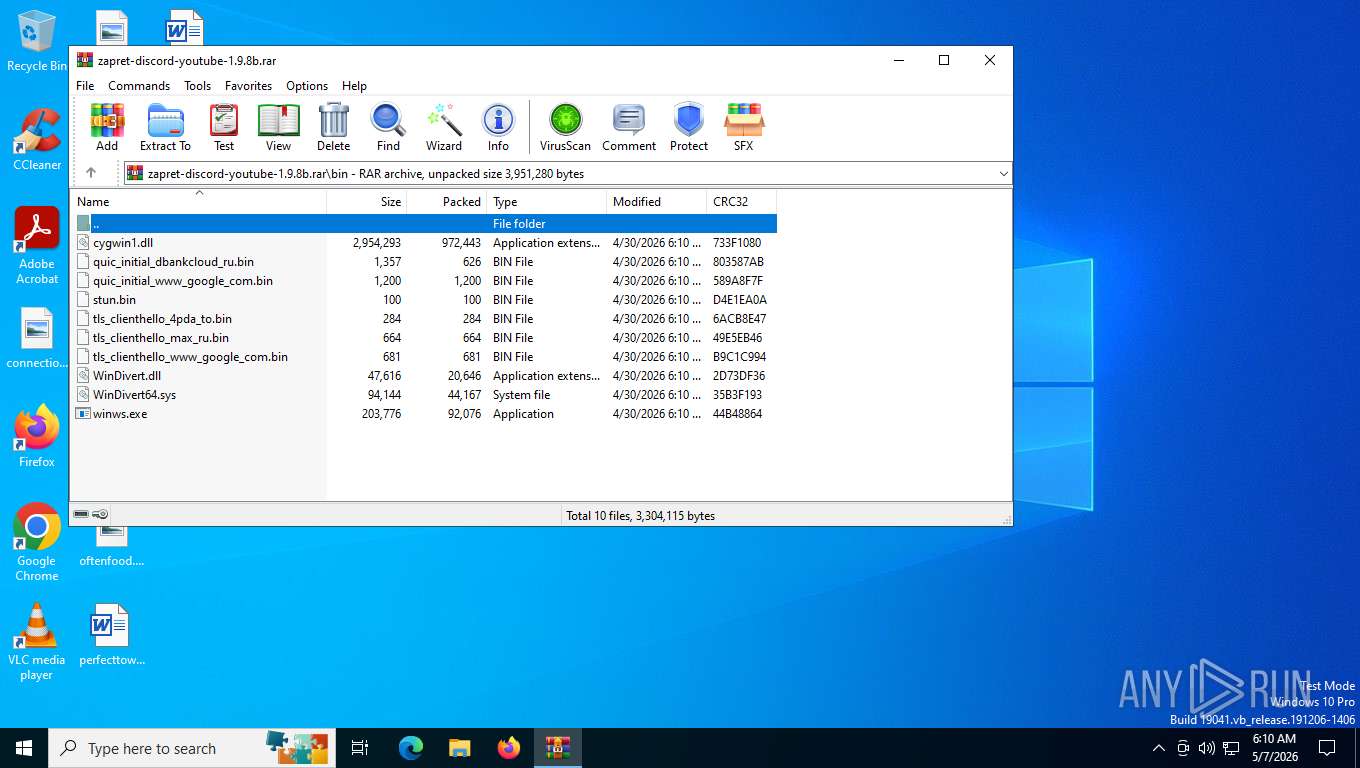
Detects Cygwin installation
- WinRAR.exe (PID: 7800)
SUSPICIOUS
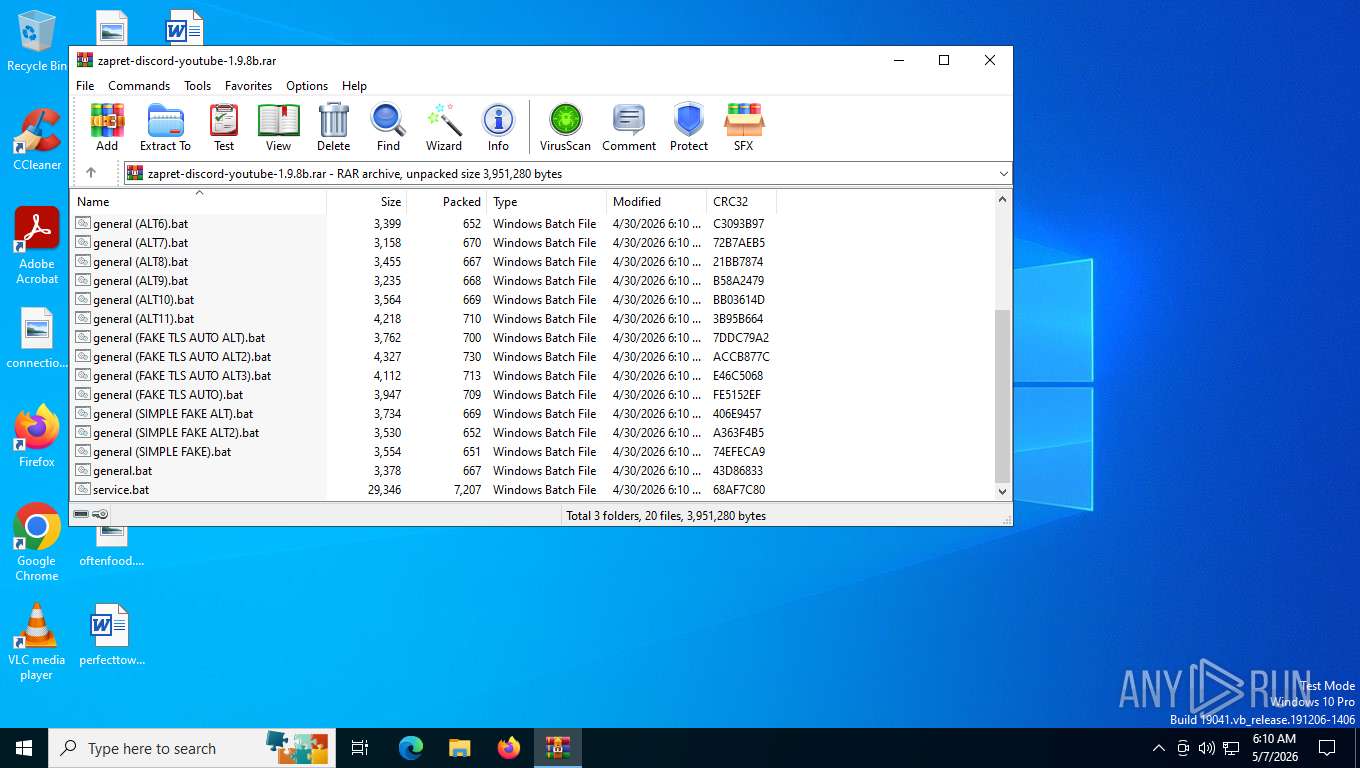
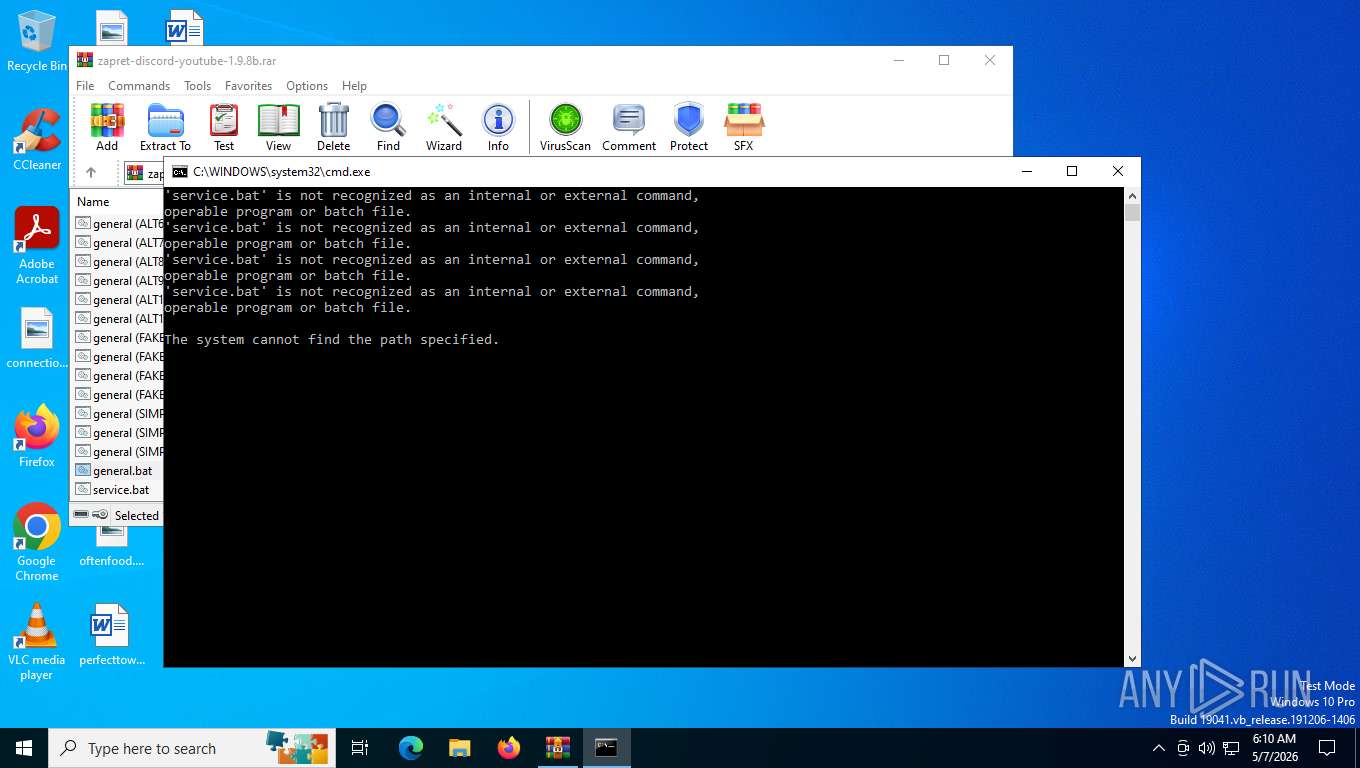
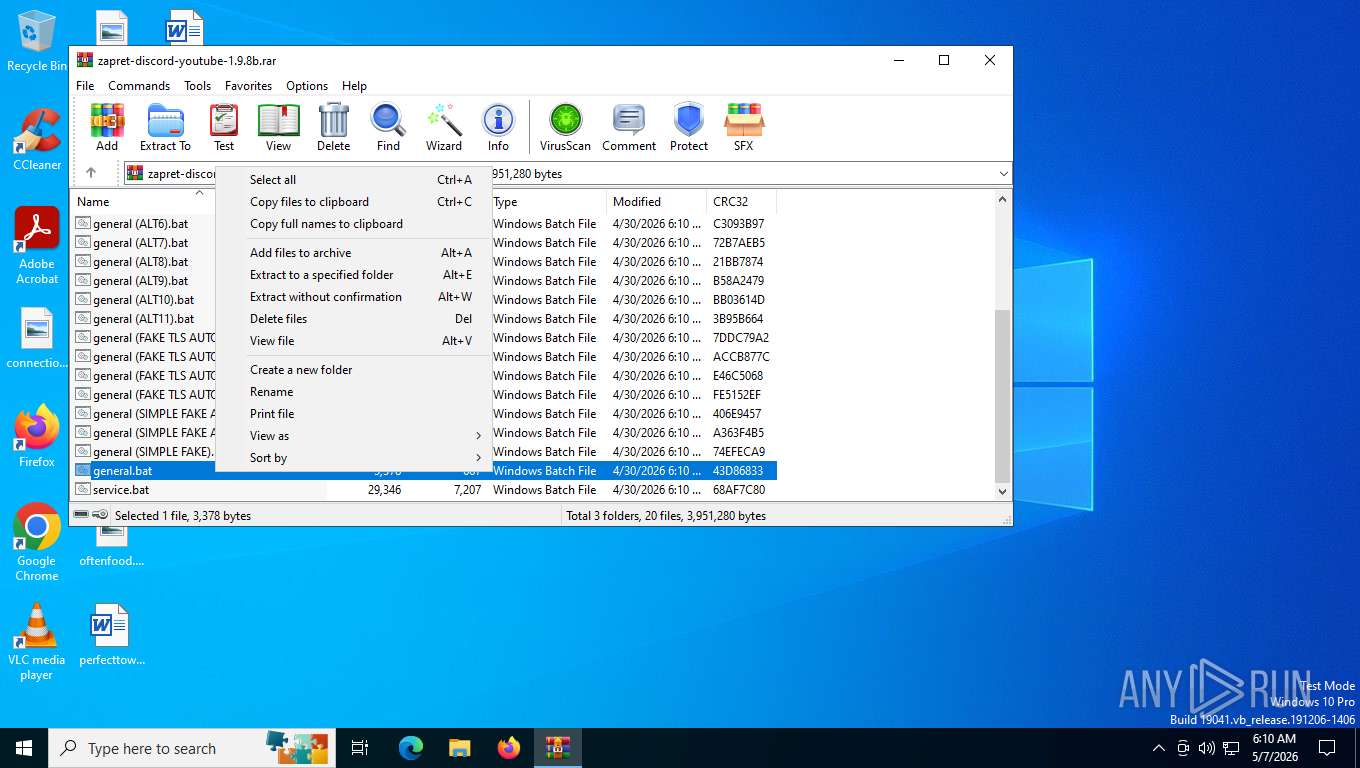
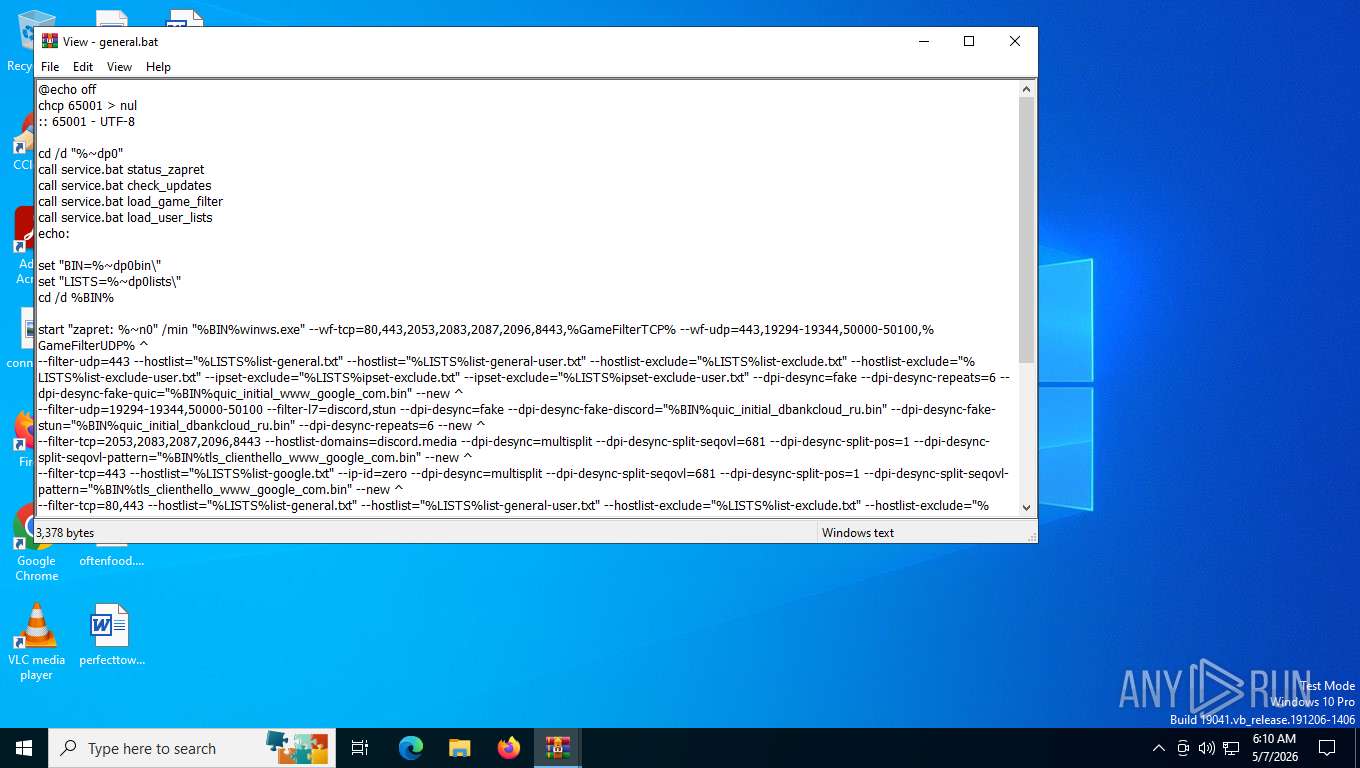
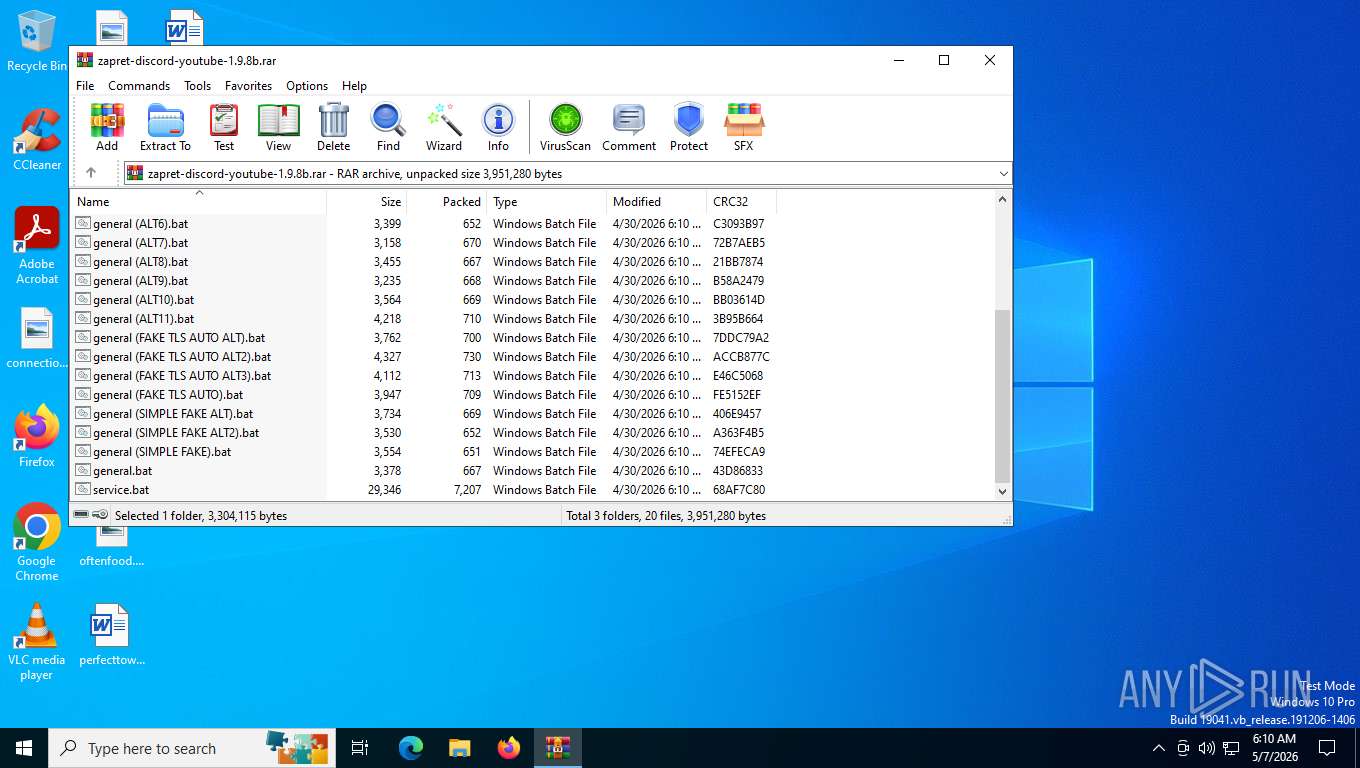
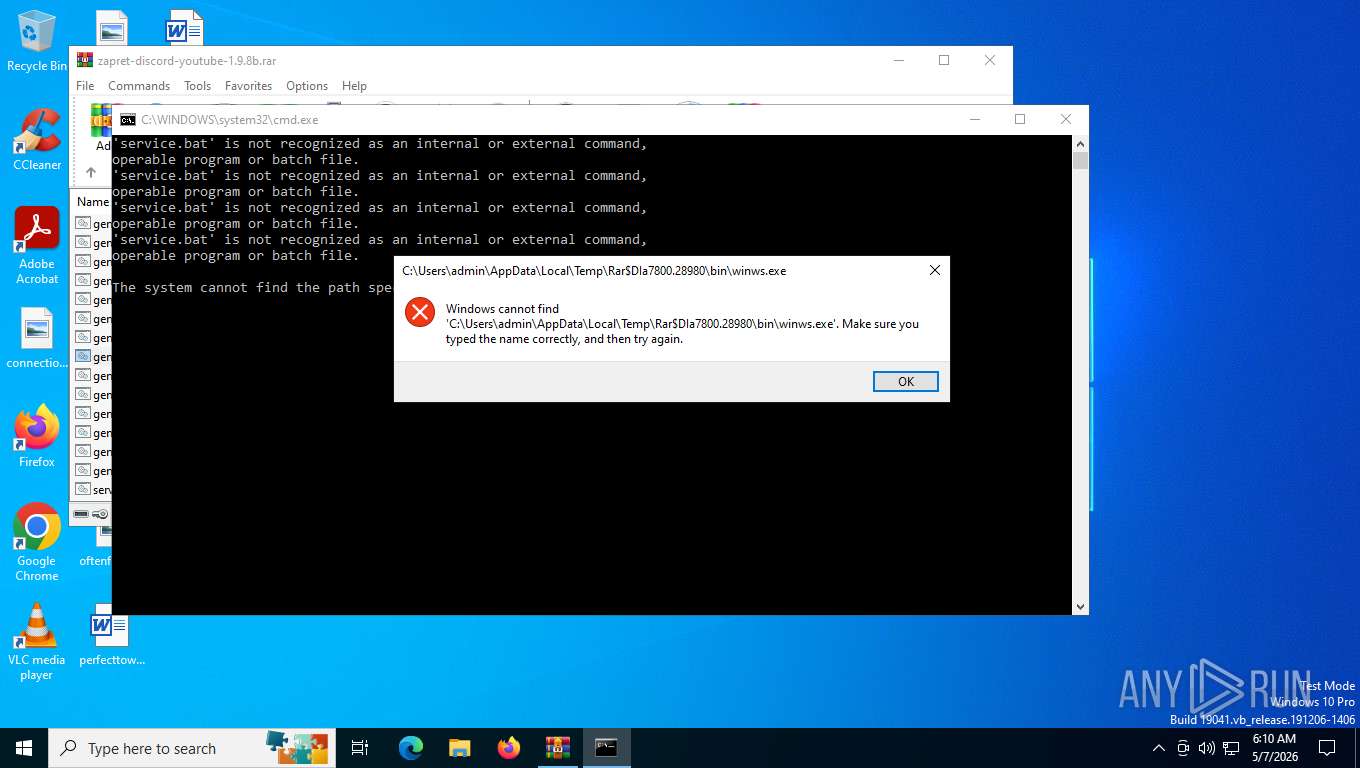
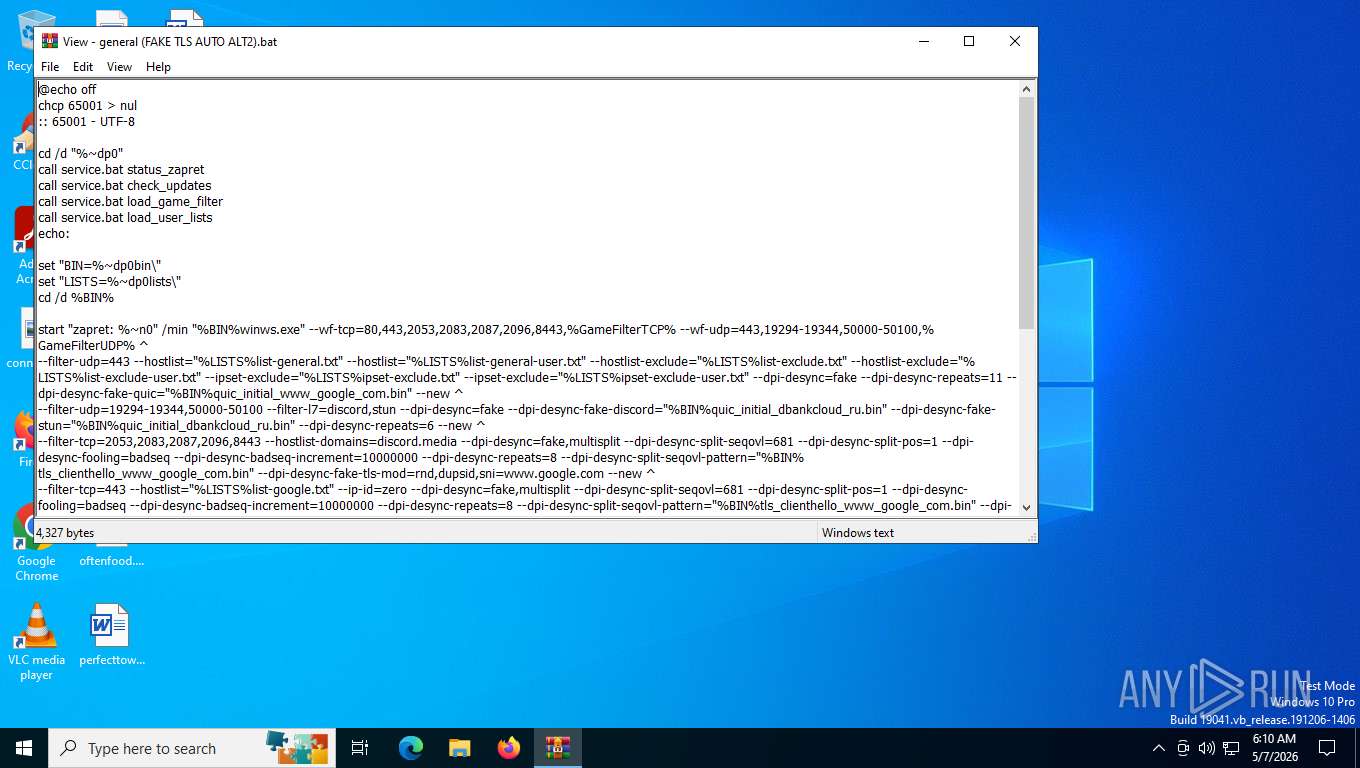
Executing commands from a ".bat" file
- WinRAR.exe (PID: 7800)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6472)
- cmd.exe (PID: 1980)
Starts application with an unusual extension
- cmd.exe (PID: 6472)
- cmd.exe (PID: 1980)
INFO
Generic archive extractor
- WinRAR.exe (PID: 7800)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7800)
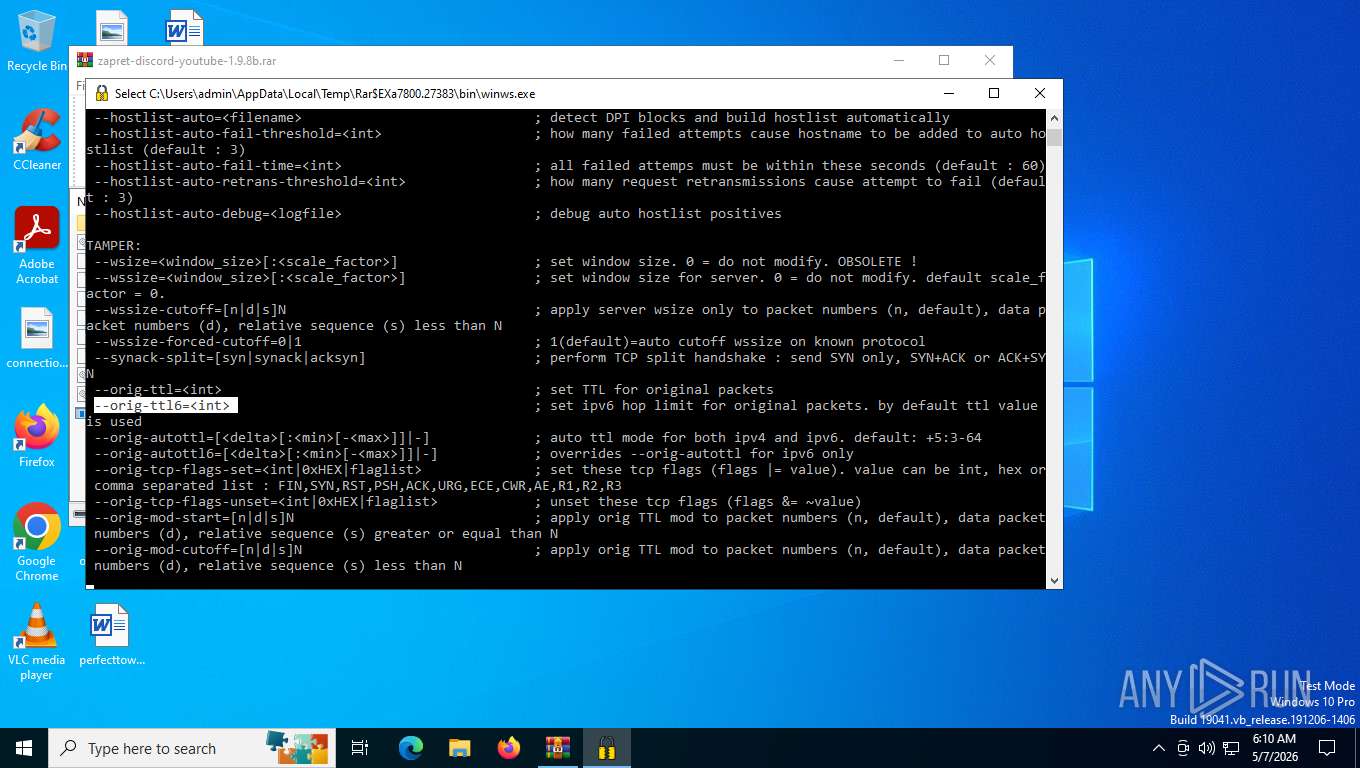
Changes the display of characters in the console
- cmd.exe (PID: 6472)
- cmd.exe (PID: 1980)
Checks supported languages
- chcp.com (PID: 4684)
- winws.exe (PID: 8012)
- winws.exe (PID: 5748)
- chcp.com (PID: 7704)
Reads the computer name
- winws.exe (PID: 8012)
- winws.exe (PID: 5748)
The sample was built using Cygwin
- winws.exe (PID: 8012)
- winws.exe (PID: 5748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 100 |
| UncompressedSize: | 100 |
| OperatingSystem: | Unix |
| ArchivedFileName: | bin/stun.bin |
Total processes
141
Monitored processes
13
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
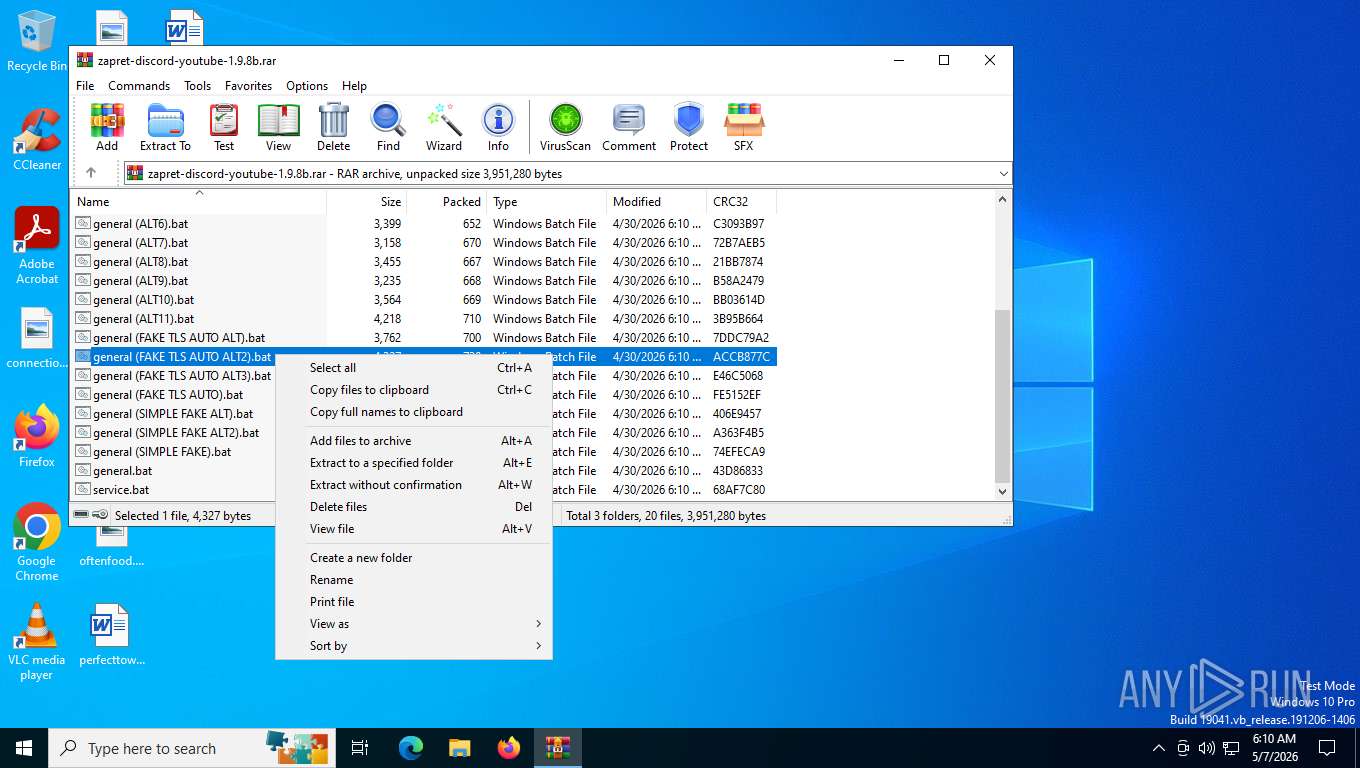
| 1980 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa7800.28980\general (FAKE TLS AUTO ALT2).bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2940 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27383\bin\winws.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27383\bin\winws.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4312 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4684 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5564 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | winws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5716 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27359\bin\winws.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27359\bin\winws.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 5748 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27383\bin\winws.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27383\bin\winws.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225786 Modules
| |||||||||||||||
| 6472 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa7800.24668\general.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | winws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27359\bin\cygwin1.dll | — | |
MD5:A1C82ED072DC079DD7851F82D9AA7678 | SHA256:103104A52E5293CE418944725DF19E2BF81AD9269B9A120D71D39028E821499B | |||
| 7800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27359\lists\list-google.txt | — | |
MD5:56EFE0D7AE91448EB5D6B452E65FF165 | SHA256:C5A5CC941366033E86B835B500614DA1CBE5DFB49C2EAA589F5FEBAD89661913 | |||
| 7800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27359\bin\stun.bin | — | |
MD5:0357596C0E38A10A4B99DCA2032419CC | SHA256:9CD5469309780CA56C0BD97266524A48C7EE529D02C3179CFECB20B260A59641 | |||
| 7800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7800.24668\general.bat | — | |
MD5:0AC556C85F0D739609285815922D1699 | SHA256:C4F7F5708DE5323B55EA85E2EF140C43426352875593EAE1C0B94BFC769A4477 | |||
| 7800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7800.25356\general.bat | — | |
MD5:0AC556C85F0D739609285815922D1699 | SHA256:C4F7F5708DE5323B55EA85E2EF140C43426352875593EAE1C0B94BFC769A4477 | |||
| 7800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27359\bin\WinDivert.dll | — | |
MD5:B2014D33EE645112D5DC16FE9D9FCBFF | SHA256:C1E060EE19444A259B2162F8AF0F3FE8C4428A1C6F694DCE20DE194AC8D7D9A2 | |||
| 7800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27359\bin\winws.exe | — | |
MD5:D498E19BC7A79DD1EFCB6B928CBE9909 | SHA256:AFFB4F69D2EA302A7ABCCD5325D81826E140DDAE014F1E070BC4A6C0DD555188 | |||
| 7800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27359\bin\tls_clienthello_4pda_to.bin | — | |
MD5:E6D649DE132C3C10CB62531EF74F5B73 | SHA256:EEFEAF09DDE8D69B1F176212541F63C68B314A33A335ECED99A8A29F17254DA8 | |||
| 7800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27359\bin\WinDivert64.sys | — | |
MD5:89ED5BE7EA83C01D0DE33D3519944AA5 | SHA256:8DA085332782708D8767BCACE5327A6EC7283C17CFB85E40B03CD2323A90DDC2 | |||
| 7800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7800.27359\bin\quic_initial_dbankcloud_ru.bin | — | |
MD5:5E594564FD03D52D6257356DCD25909E | SHA256:F7A1C1CFFC8F65BD47412B7CA5588653D21EEC916BB79203C9914890A62874DF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
25
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6792 | svchost.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
4336 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
4336 | SIHClient.exe | GET | 200 | 135.233.95.135:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
4336 | SIHClient.exe | GET | 200 | 74.179.77.204:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
4336 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
5316 | svchost.exe | POST | 200 | 20.190.159.2:443 | https://login.live.com/RST2.srf | US | — | 1.24 Kb | whitelisted |
— | — | GET | 200 | 23.11.40.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | — | 313 b | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | — | 922 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.159.2:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | — | 204 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.159.2:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | — | 204 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 2.19.126.133:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5276 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6792 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.241.197:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.40.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6792 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |