| File name: | pg.ps1 |
| Full analysis: | https://app.any.run/tasks/772287a9-3626-44f8-9fee-9e1c1698ecaa |
| Verdict: | Malicious activity |
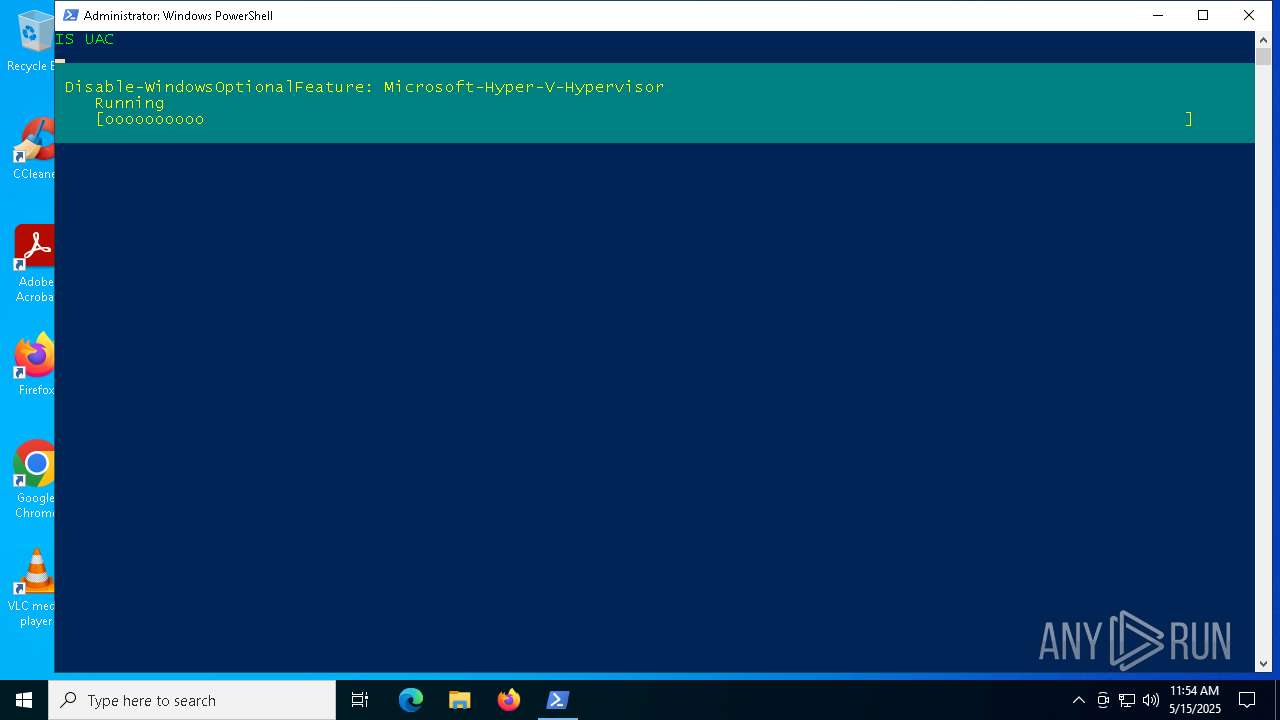
| Analysis date: | May 15, 2025, 11:53:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Non-ISO extended-ASCII text, with LF, NEL line terminators |
| MD5: | E55284D0B3DC01176F3AF139BBC796ED |
| SHA1: | A80F0791FD8B06BABB229A2D440B1C70CEE4557E |
| SHA256: | 8B56AA16BCB0861022CF43F10EEF8303644B1908D0F5AD4B617948369CA3D919 |
| SSDEEP: | 96:KmPEYpJPmvu4Qts98TzVJfcC0uSAA27QUH:K4EOOvu4EsIfcduV/7QUH |
MALICIOUS
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 3100)
Bypass execution policy to execute commands
- powershell.exe (PID: 3100)
- powershell.exe (PID: 5680)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 3100)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 3100)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 5680)
The process executes Powershell scripts
- powershell.exe (PID: 3100)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 4892)
Removes files via Powershell
- powershell.exe (PID: 4892)
Application launched itself
- powershell.exe (PID: 3100)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 5680)
The process creates files with name similar to system file names
- powershell.exe (PID: 5680)
Process drops legitimate windows executable
- powershell.exe (PID: 5680)
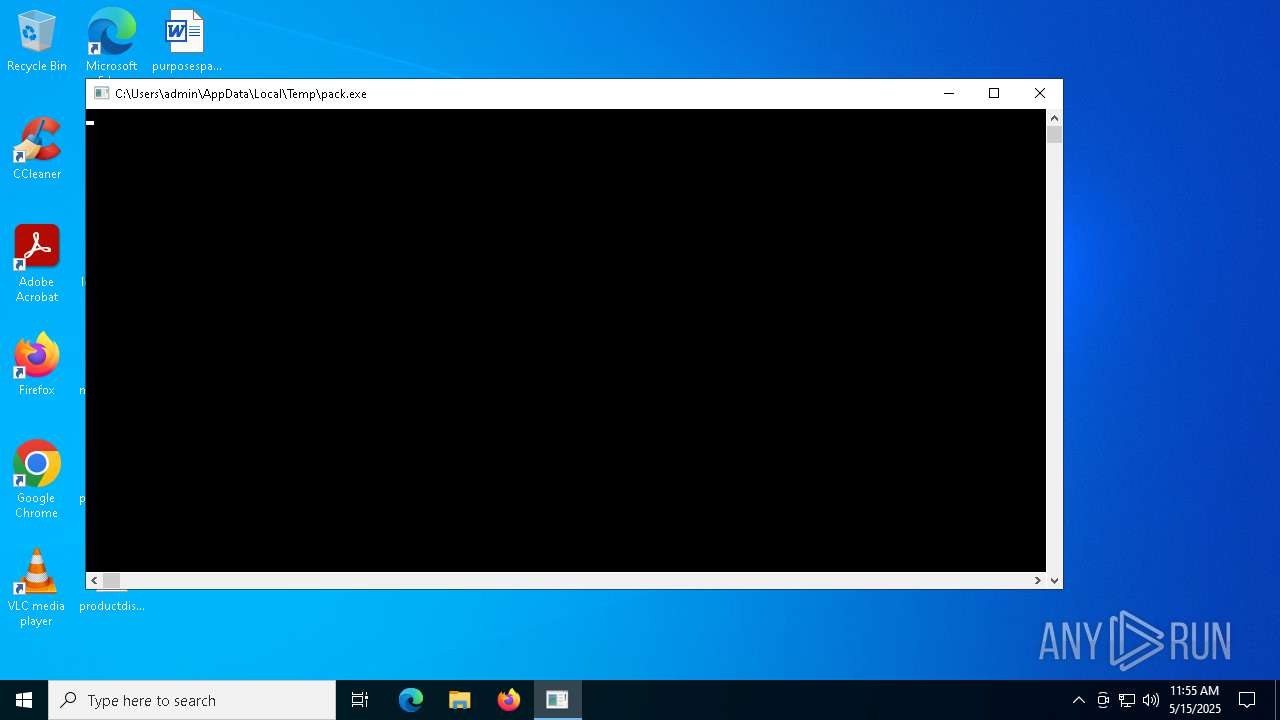
Executable content was dropped or overwritten
- powershell.exe (PID: 5680)
- pack.exe (PID: 4164)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 5116)
Connects to unusual port
- powershell.exe (PID: 5680)
Executes as Windows Service
- VSSVC.exe (PID: 4608)
Searches for installed software
- TiWorker.exe (PID: 2980)
Potential Corporate Privacy Violation
- powershell.exe (PID: 5680)
Starts CMD.EXE for commands execution
- pack.exe (PID: 4164)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 2064)
INFO
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5680)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4892)
The sample compiled with english language support
- powershell.exe (PID: 5680)
The executable file from the user directory is run by the Powershell process
- DismHost.exe (PID: 5116)
- pack.exe (PID: 4164)
Reads Environment values
- DismHost.exe (PID: 5116)
Manages system restore points
- SrTasks.exe (PID: 6032)
Reads the computer name
- DismHost.exe (PID: 5116)
Checks supported languages
- DismHost.exe (PID: 5116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .669 | | | Composer 669 module (100) |
|---|
Total processes
144
Monitored processes
19
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 928 | rundll32.exe C:\Users\admin\AppData\Local\Temp\ZCXLgnBrHm.TTF,GO | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | C:\WINDOWS\system32\cmd.exe /c start rundll32.exe C:\Users\admin\AppData\Local\Temp\ZCXLgnBrHm.TTF,GO | C:\Windows\System32\cmd.exe | — | pack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | C:\WINDOWS\system32\cmd.exe /c del C:\Users\admin\AppData\Local\Temp\*.dat | C:\Windows\System32\cmd.exe | — | pack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2980 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3100 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\pg.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3896 | C:\WINDOWS\system32\cmd.exe /c del C:\Users\admin\AppData\Local\Temp\*.dll | C:\Windows\System32\cmd.exe | — | pack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4012 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4164 | "C:\Users\admin\AppData\Local\Temp\pack.exe" | C:\Users\admin\AppData\Local\Temp\pack.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
42 643
Read events
41 552
Write events
593
Delete events
498
Modification events
| (PID) Process: | (5680) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\TypedPaths |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5680) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRULegacy |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5680) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\* |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5680) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\crt |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5680) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\exe |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5680) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\lnk |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5680) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\xpi |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5680) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5680) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5680) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppBadgeUpdated |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
52
Suspicious files
10
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10c044.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vu32k5mt.ynq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5680 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7QTJLNPMAU3GMX4RDI3E.temp | binary | |
MD5:FC2DBF84B184FC5B01BFBD10E93A1C29 | SHA256:8BD8B6C231BF454286A19D0F2C1CD826AD0F57EBA8AD40746D99137469D60918 | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\96AV4E4VVL82832ZKT5F.temp | binary | |
MD5:7A2C632E7CCB313087FC824BB63DB00E | SHA256:2CFF48C33F6F174286FC6922A89B14A21D03FBF22854C6F0A55DA54C6A7AB0D4 | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wrapper_809053809.ps1 | text | |
MD5:9455509BFABF174A9AA1A35745ACC8CA | SHA256:43D9916942FAAF02E96A64ED06E36E0EC5BE05D27D2FD492DE0F02BE8EA84681 | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bjsajxfn.ks5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5680 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10cdb2.TMP | binary | |
MD5:7A2C632E7CCB313087FC824BB63DB00E | SHA256:2CFF48C33F6F174286FC6922A89B14A21D03FBF22854C6F0A55DA54C6A7AB0D4 | |||
| 5680 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:FC2DBF84B184FC5B01BFBD10E93A1C29 | SHA256:8BD8B6C231BF454286A19D0F2C1CD826AD0F57EBA8AD40746D99137469D60918 | |||
| 4892 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ztmfwhj1.uc2.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5680 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kcggxgzi.fc2.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
22
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
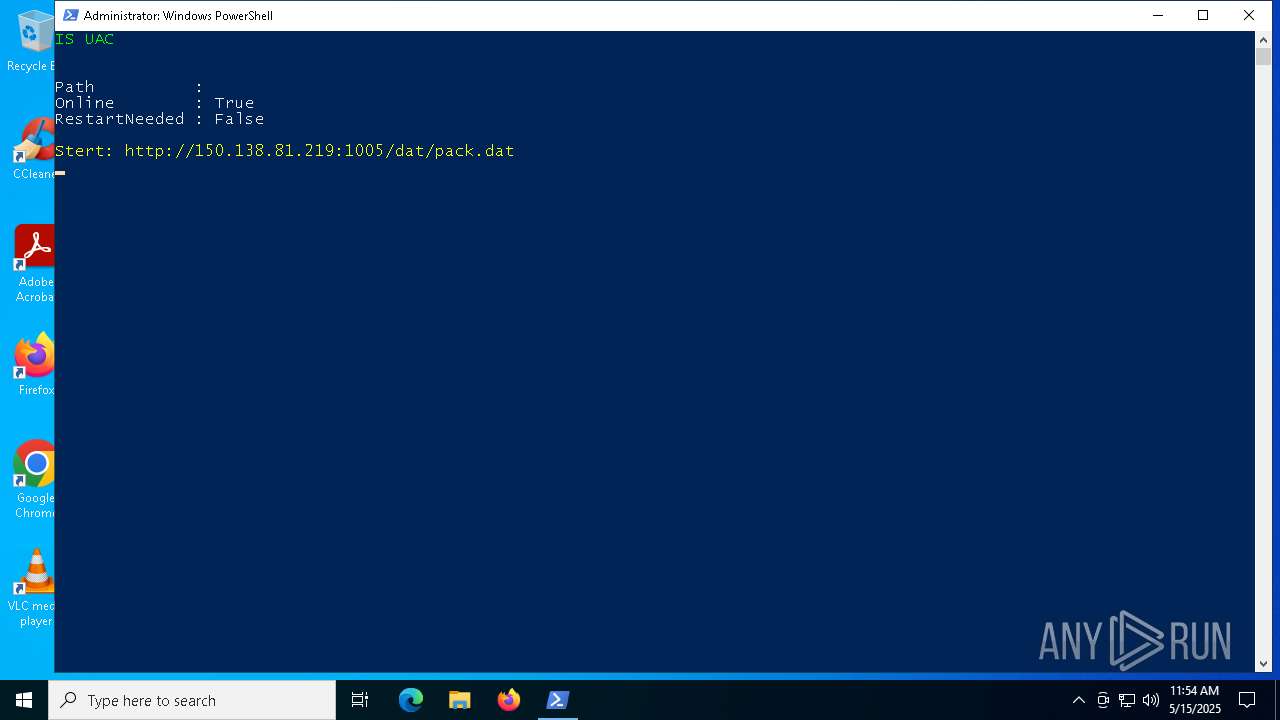
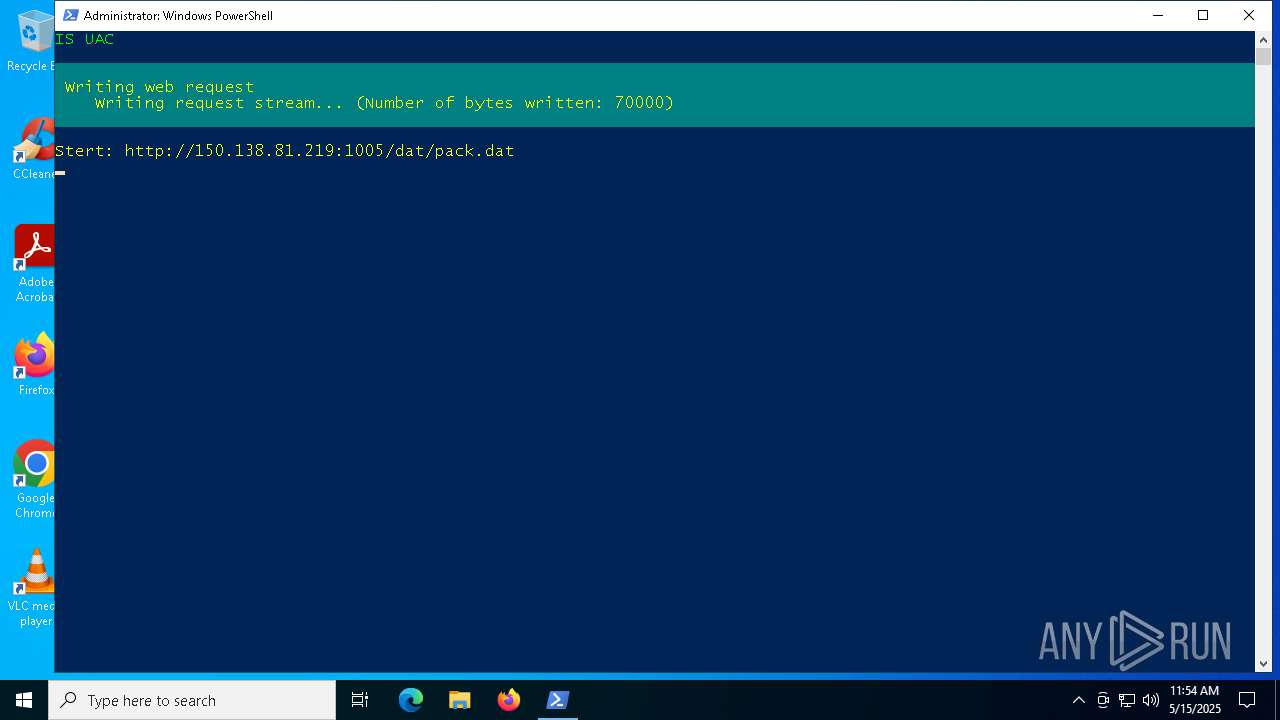
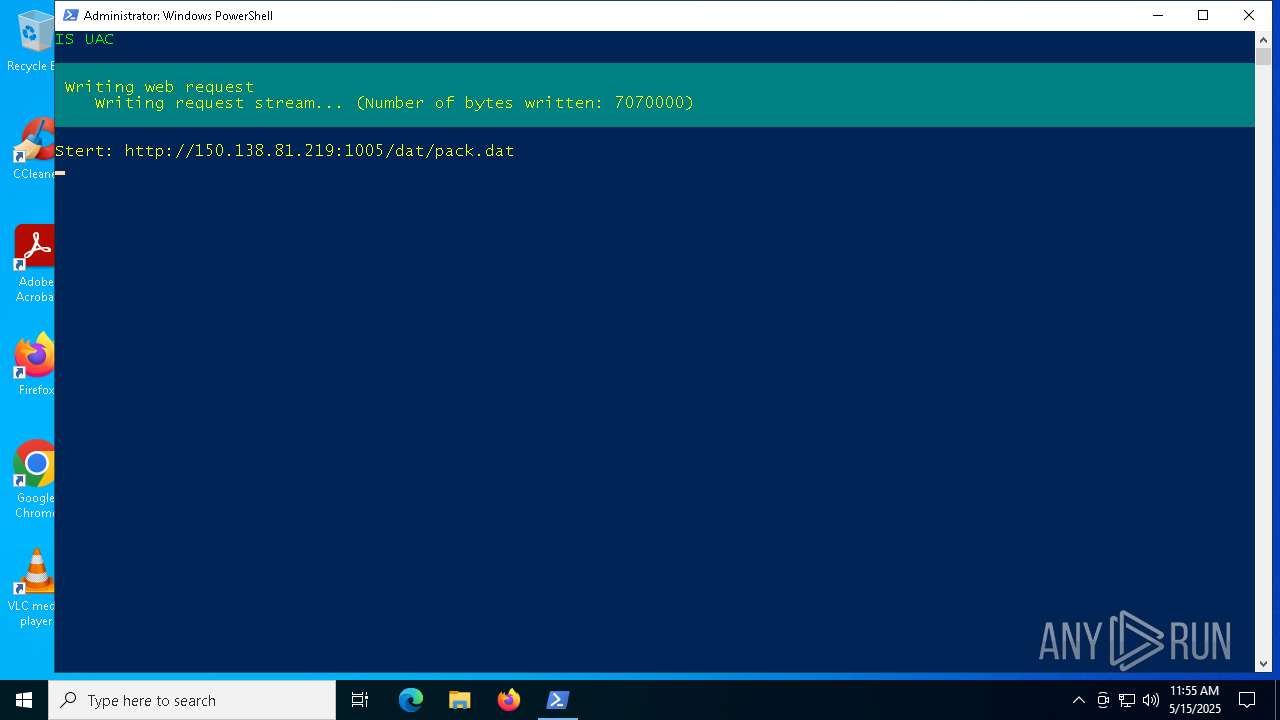
5680 | powershell.exe | GET | — | 150.138.81.219:1005 | http://150.138.81.219:1005/dat/pack.dat | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2292 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
3812 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5680 | powershell.exe | 150.138.81.219:1005 | — | Zaozhuang,Shandong Province, P.R.China. | CN | unknown |
3900 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5056 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5680 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5680 | powershell.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
5680 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
5680 | powershell.exe | Misc activity | ET INFO Packed Executable Download |