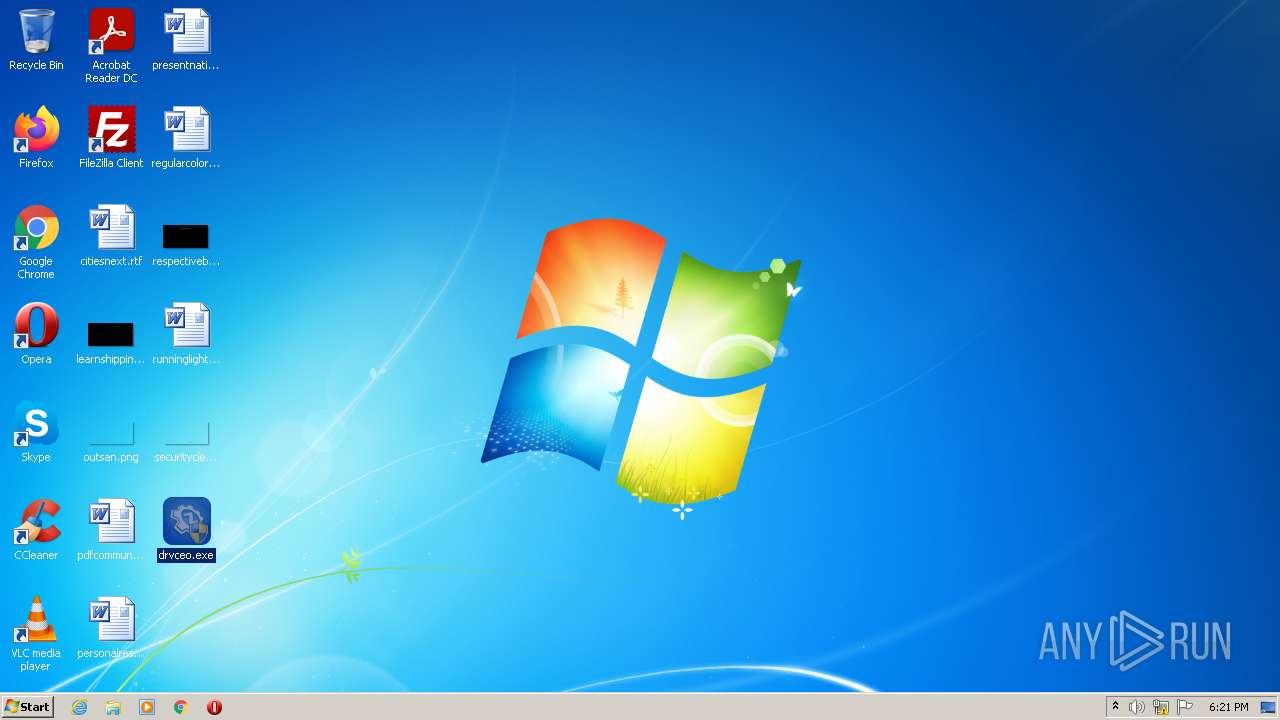
| File name: | drvceo.exe |
| Full analysis: | https://app.any.run/tasks/da38edba-7325-4ebb-8411-cefcf2f2a85c |
| Verdict: | Malicious activity |
| Analysis date: | January 21, 2022, 18:20:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 61BF62109EC9A4E33517DE2E6D6EF24F |
| SHA1: | E61EC54DC74D956C6230D8E59AE256CA2303B055 |
| SHA256: | 8B4C0BF04266140E598F48D4A5788B0F244C379F900800AD9176E404E6DFC633 |
| SSDEEP: | 49152:qjfT+6ngdZqU8nWw08pbGKjJJ4sZ0BxpKGHdtOlsmgUuyv9rTC:qjfT+9Hv8Ww0E34siginOicu29re |
MALICIOUS
Loads dropped or rewritten executable
- drvceo.exe (PID: 3708)
- drvceo.exe (PID: 2320)
- consent.exe (PID: 2524)
- DllHost.exe (PID: 2244)
- DllHost.exe (PID: 2740)
- drvceo.exe (PID: 1992)
SUSPICIOUS
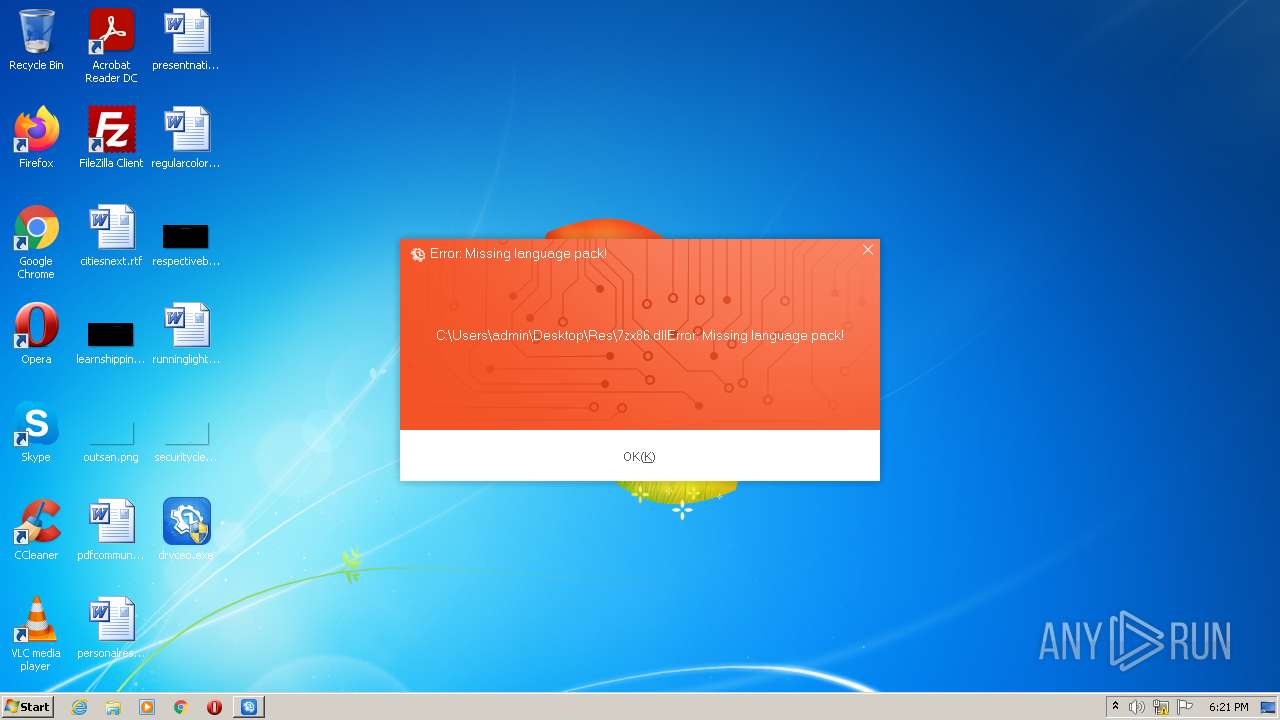
Checks supported languages
- drvceo.exe (PID: 3708)
- drvceo.exe (PID: 1992)
Reads the computer name
- drvceo.exe (PID: 3708)
- drvceo.exe (PID: 1992)
Creates files in the Windows directory
- drvceo.exe (PID: 3708)
Executable content was dropped or overwritten
- drvceo.exe (PID: 3708)
- drvceo.exe (PID: 1992)
Drops a file that was compiled in debug mode
- drvceo.exe (PID: 3708)
- drvceo.exe (PID: 1992)
INFO
Manual execution by user
- drvceo.exe (PID: 2320)
- drvceo.exe (PID: 1992)
Reads the computer name
- consent.exe (PID: 2524)
- DllHost.exe (PID: 2244)
- DllHost.exe (PID: 2740)
Checks Windows Trust Settings
- consent.exe (PID: 2524)
Checks supported languages
- consent.exe (PID: 2524)
- DllHost.exe (PID: 2244)
- DllHost.exe (PID: 2740)
Reads settings of System Certificates
- consent.exe (PID: 2524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (42.1) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (41.3) |
| .exe | | | Win32 Executable (generic) (7) |
| .exe | | | Win16/32 Executable Delphi generic (3.2) |
| .exe | | | Generic Win/DOS Executable (3.1) |
EXIF
EXE
| Comments: | 驱动总裁 |
|---|---|
| ProductVersion: | 2.8.0.0 |
| ProductName: | 驱动总裁 |
| LegalCopyright: | Copyright (C) 2012-2021 Jiangmen Eyun Network Co.,Ltd. |
| FileVersion: | 2.8.0.0 |
| FileDescription: | 驱动总裁 |
| CompanyName: | SysCeo.com |
| CharacterSet: | Windows, Chinese (Simplified) |
| LanguageCode: | Chinese (Simplified) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2.8.0.0 |
| FileVersionNumber: | 2.8.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0xd6ea90 |
| UninitializedDataSize: | 11665408 |
| InitializedDataSize: | 106496 |
| CodeSize: | 2420736 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2021:10:26 14:12:07+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Oct-2021 12:12:07 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 26-Oct-2021 12:12:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00B20000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00B21000 | 0x0024F000 | 0x0024E800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9999 |
.rsrc | 0x00D70000 | 0x0001A000 | 0x00019C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.6404 |
Imports
AdvApi32.dll |
KERNEL32.DLL |
cfgmgr32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
gdiplus.dll |
iphlpapi.dll |
msvcrt.dll |
ole32.dll |
Total processes
44
Monitored processes
7
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1992 | "C:\Users\admin\Desktop\drvceo.exe" | C:\Users\admin\Desktop\drvceo.exe | Explorer.EXE | ||||||||||||
User: admin Company: SysCeo.com Integrity Level: HIGH Description: ???? Exit code: 0 Version: 2.8.0.0 Modules
| |||||||||||||||
| 2244 | C:\Windows\system32\DllHost.exe /Processid:{E10F6C3A-F1AE-4ADC-AA9D-2FE65525666E} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\Desktop\drvceo.exe" | C:\Users\admin\Desktop\drvceo.exe | — | Explorer.EXE | |||||||||||
User: admin Company: SysCeo.com Integrity Level: MEDIUM Description: ???? Exit code: 3221226540 Version: 2.8.0.0 Modules
| |||||||||||||||
| 2320 | "C:\Users\admin\Desktop\drvceo.exe" | C:\Users\admin\Desktop\drvceo.exe | — | Explorer.EXE | |||||||||||
User: admin Company: SysCeo.com Integrity Level: MEDIUM Description: ???? Exit code: 3221226540 Version: 2.8.0.0 Modules
| |||||||||||||||
| 2524 | consent.exe 924 276 02AC1DC8 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2740 | C:\Windows\system32\DllHost.exe /Processid:{E10F6C3A-F1AE-4ADC-AA9D-2FE65525666E} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3708 | "C:\Users\admin\Desktop\drvceo.exe" | C:\Users\admin\Desktop\drvceo.exe | Explorer.EXE | ||||||||||||
User: admin Company: SysCeo.com Integrity Level: HIGH Description: ???? Exit code: 0 Version: 2.8.0.0 Modules
| |||||||||||||||
Total events
3 544
Read events
3 530
Write events
14
Delete events
0
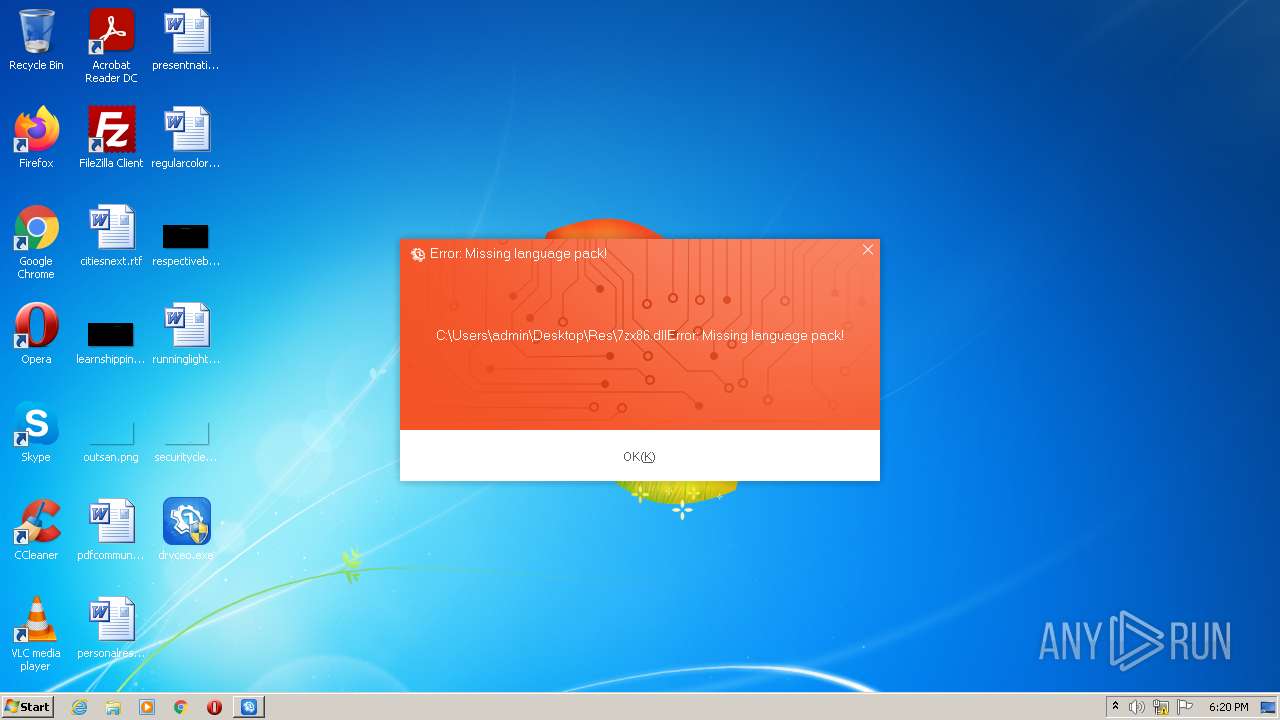
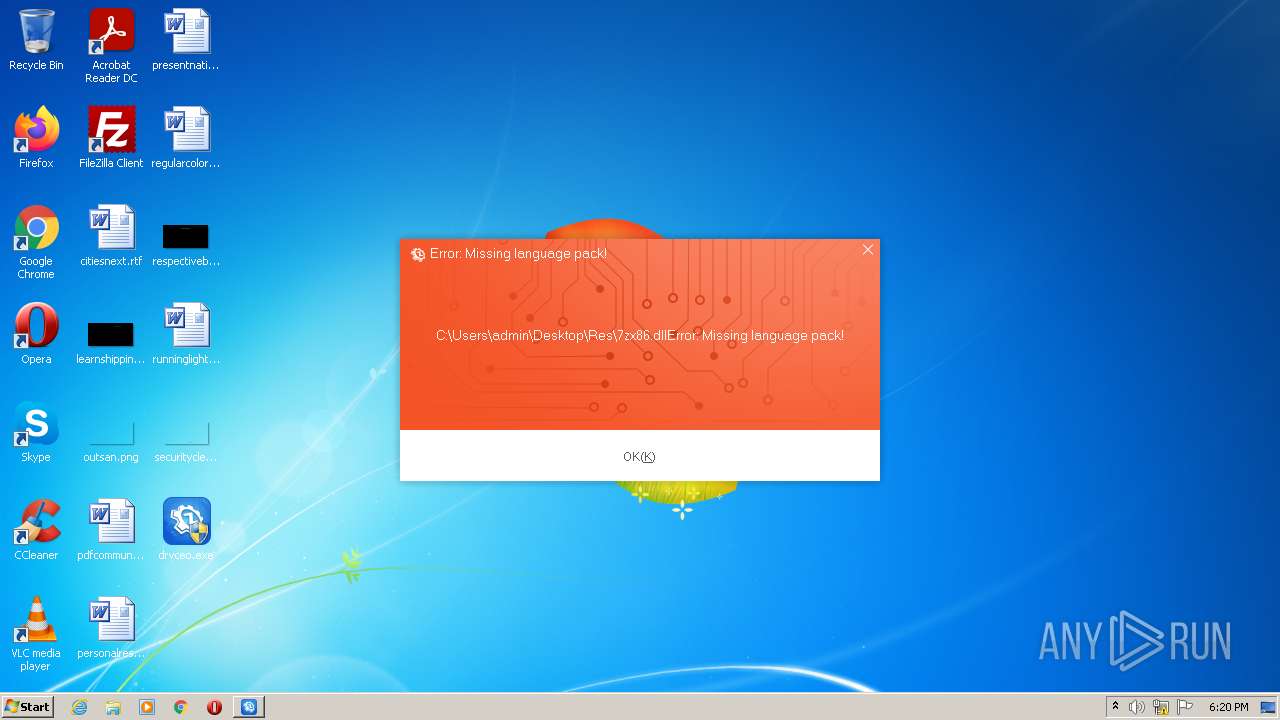
Modification events
| (PID) Process: | (2524) consent.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3708 | drvceo.exe | C:\Windows\Temp\~DrvCeoLog\DrvCeoRun22.0121.log | text | |
MD5:F3BDBB4AD0398651F58C4384292F6E37 | SHA256:ED3983F5910D837EE6CEC52963EC95BA67E5DF33F12AC5303CF9A515BDFB9258 | |||
| 3708 | drvceo.exe | C:\Users\admin\AppData\Local\Temp\ntdll.dll | executable | |
MD5:EBB2B4FD62087283D9448F7F8796727D | SHA256:9C9EA64C0D56BF17D388C58B36AB7A79CA6AA74446B6DD2F614F5CBF9D828529 | |||
| 1992 | drvceo.exe | C:\Users\admin\AppData\Local\Temp\ntdll.dll | executable | |
MD5:EBB2B4FD62087283D9448F7F8796727D | SHA256:9C9EA64C0D56BF17D388C58B36AB7A79CA6AA74446B6DD2F614F5CBF9D828529 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report