| download: | 65515-chernobyl-in-modern-times-nuclear-emergency.html |
| Full analysis: | https://app.any.run/tasks/5716593a-6752-43f9-aa37-9605cf3c0456 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 22:24:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 98BD9A8045EDA1EC9594A7CE9B0B26CB |
| SHA1: | FBEF5102265E96D8DB66D3F228627FBD8A13650A |
| SHA256: | 8B4554EAEED0B9A01DC111B3C5A7B9DD203A982825FF1C7C120BE413EB61AE34 |
| SSDEEP: | 1536:srytmKSjtrLGkQwm4LtnaTikFNGFKT5z2TVM/tCF3z+/CuciD:s+tmKSj1D7xtmik/QKT2VM/tCt+D |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 2316)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2316)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 3368)
Application launched itself
- iexplore.exe (PID: 2816)
- chrome.exe (PID: 2316)
Manual execution by user
- chrome.exe (PID: 2316)
Changes internet zones settings
- iexplore.exe (PID: 2816)
Reads settings of System Certificates
- iexplore.exe (PID: 3368)
- chrome.exe (PID: 2316)
Changes settings of System certificates
- chrome.exe (PID: 2316)
- iexplore.exe (PID: 3368)
Reads Internet Cache Settings
- iexplore.exe (PID: 3368)
Creates files in the user directory
- iexplore.exe (PID: 3368)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
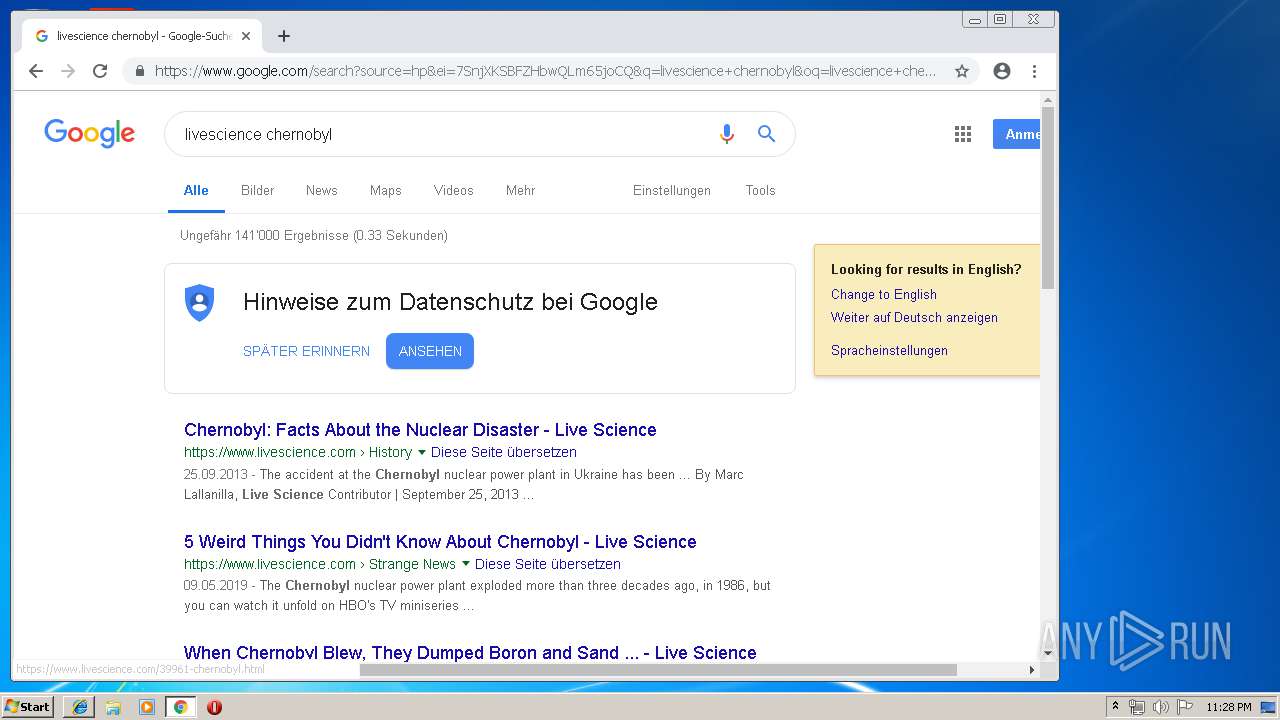
| Description: | In 1986, the Soviets dumped sand and boron from helicopters onto the exposed Chernobyl uranium core. How would we handle it today? |
|---|---|
| Title: | When Chernobyl Blew, They Dumped Boron and Sand into the Breach. What Would We Do Today? |
| HTTPEquivXUACompatible: | IE=9; IE=8; IE=7; IE=EDGE |
| googleSiteVerification: | 9idATXqhUCskCzkXvGEmuGx6t9G5-cpFLIVMpREAg-8 |
| viewport: | width=device-width, initial-scale=1 |
| Robots: | index, follow |
| msapplicationTileColor: | #ffffff |
| msapplicationTileImage: | /resources/ms-icon-144x144.png |
| themeColor: | #ffffff |
| twitterCard: | summary_large_image |
| twitterSite: | 15428397 |
| twitterCreator: | @LiveScience |
| twitterTitle: | When Chernobyl Blew, They Dumped Boron and Sand into the Breach. What Would We Do Today? |
| twitterDescription: | In 1986, the Soviets dumped sand and boron from helicopters onto the exposed Chernobyl uranium core. How would we handle it today? |
| twitterImage: | https://img.purch.com/h/1000/aHR0cDovL3d3dy5saXZlc2NpZW5jZS5jb20vaW1hZ2VzL2kvMDAwLzEwNS83MzAvb3JpZ2luYWwvY3E1ZGFtLndlYi4xMjAwLjY3NS5qcGVn |
| news_keywords: | chernobyl,nuclear disaster,Fukushima,soviet union,hbo,nuclear power,uranium |
Total processes
143
Monitored processes
109
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,5226969541726532706,6857720521082376480,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3111866391186747589 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3111866391186747589 --renderer-client-id=53 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,5226969541726532706,6857720521082376480,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5222405858321359488 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5222405858321359488 --renderer-client-id=58 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5088 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,5226969541726532706,6857720521082376480,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1998227132250258762 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1998227132250258762 --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7684 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,5226969541726532706,6857720521082376480,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8941554021844640474 --mojo-platform-channel-handle=3968 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,5226969541726532706,6857720521082376480,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=18312992704868485194 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18312992704868485194 --renderer-client-id=73 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,5226969541726532706,6857720521082376480,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4393791783789783614 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4393791783789783614 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,5226969541726532706,6857720521082376480,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13409989232967989501 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13409989232967989501 --renderer-client-id=77 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,5226969541726532706,6857720521082376480,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17426795210272669602 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17426795210272669602 --renderer-client-id=62 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5580 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,5226969541726532706,6857720521082376480,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10281256686978313713 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10281256686978313713 --renderer-client-id=79 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,5226969541726532706,6857720521082376480,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11555059351004638372 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11555059351004638372 --renderer-client-id=65 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 145
Read events
863
Write events
270
Delete events
12
Modification events
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {19825751-7B4E-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E307050001001400160018003B00D600 | |||
Executable files
0
Suspicious files
540
Text files
319
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2816 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fbcbe313-7270-4217-8dea-890b14e6871a.tmp | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
419
DNS requests
305
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
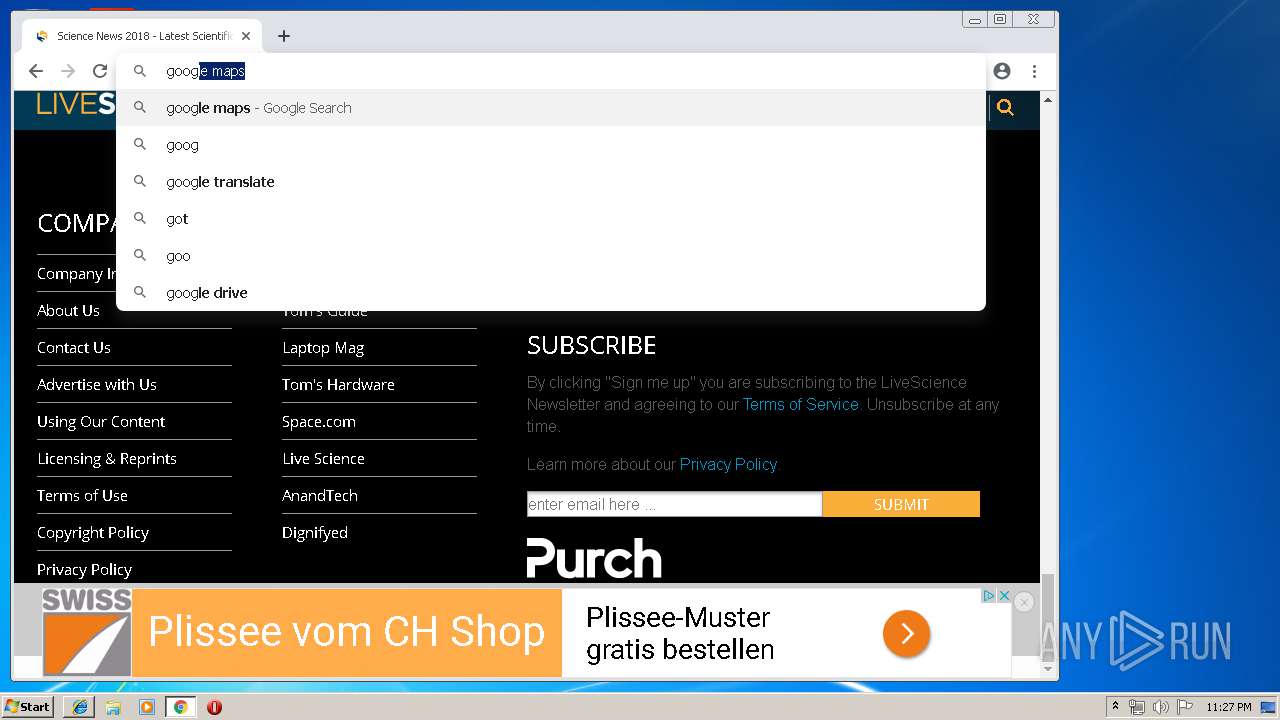
2316 | chrome.exe | GET | 301 | 104.111.219.119:80 | http://www.livescience.com/ | NL | — | — | suspicious |
2316 | chrome.exe | GET | 200 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.1 Kb | whitelisted |
2316 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 505 b | whitelisted |
2316 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2316 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2316 | chrome.exe | GET | 200 | 173.194.139.6:80 | http://r1---sn-aigzrn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.212.170.83&mm=28&mn=sn-aigzrn7k&ms=nvh&mt=1558391058&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2816 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3368 | iexplore.exe | OPTIONS | 400 | 216.58.210.8:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2316 | chrome.exe | GET | 200 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | unknown | der | 969 b | whitelisted |
3368 | iexplore.exe | OPTIONS | 400 | 216.58.210.8:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 64.233.167.82:445 | html5shim.googlecode.com | Google Inc. | US | whitelisted |
2816 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2316 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
2316 | chrome.exe | 216.58.205.227:443 | www.google.ch | Google Inc. | US | whitelisted |
2316 | chrome.exe | 172.217.23.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2316 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2316 | chrome.exe | 216.58.208.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2316 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3368 | iexplore.exe | 104.111.219.119:443 | www.livescience.com | Akamai International B.V. | NL | whitelisted |
2316 | chrome.exe | 216.58.210.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
html5shim.googlecode.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
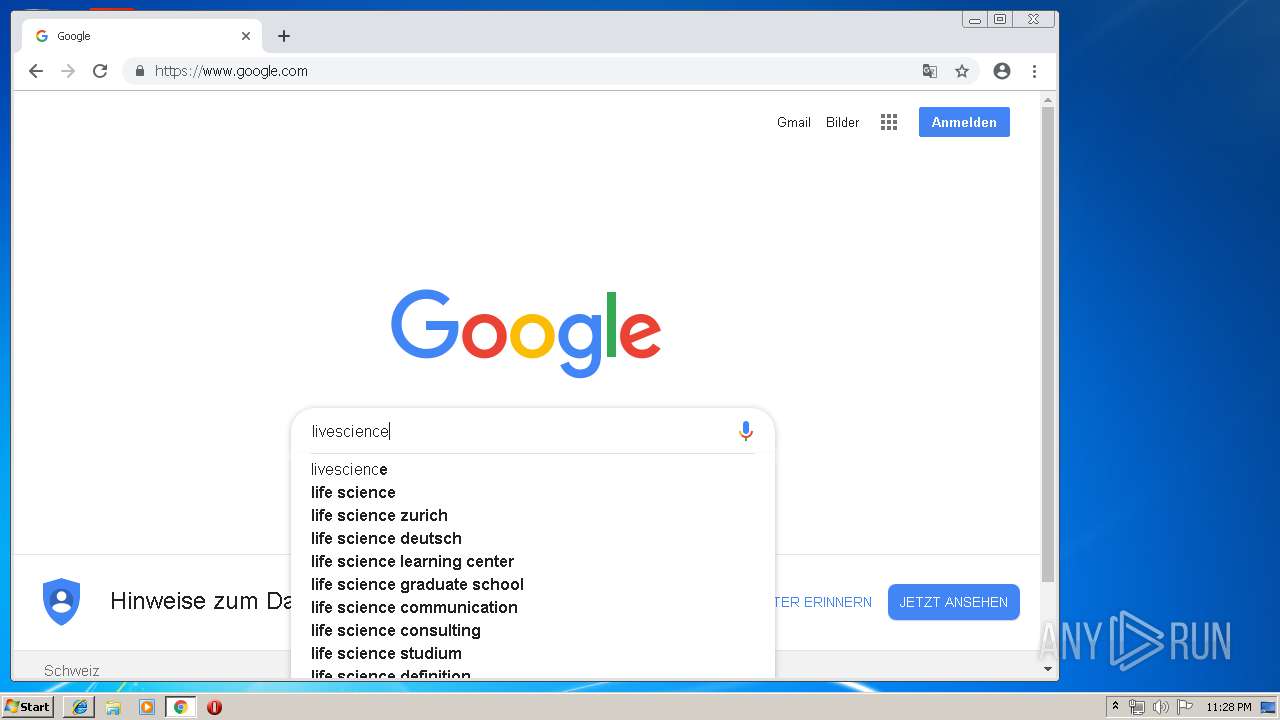
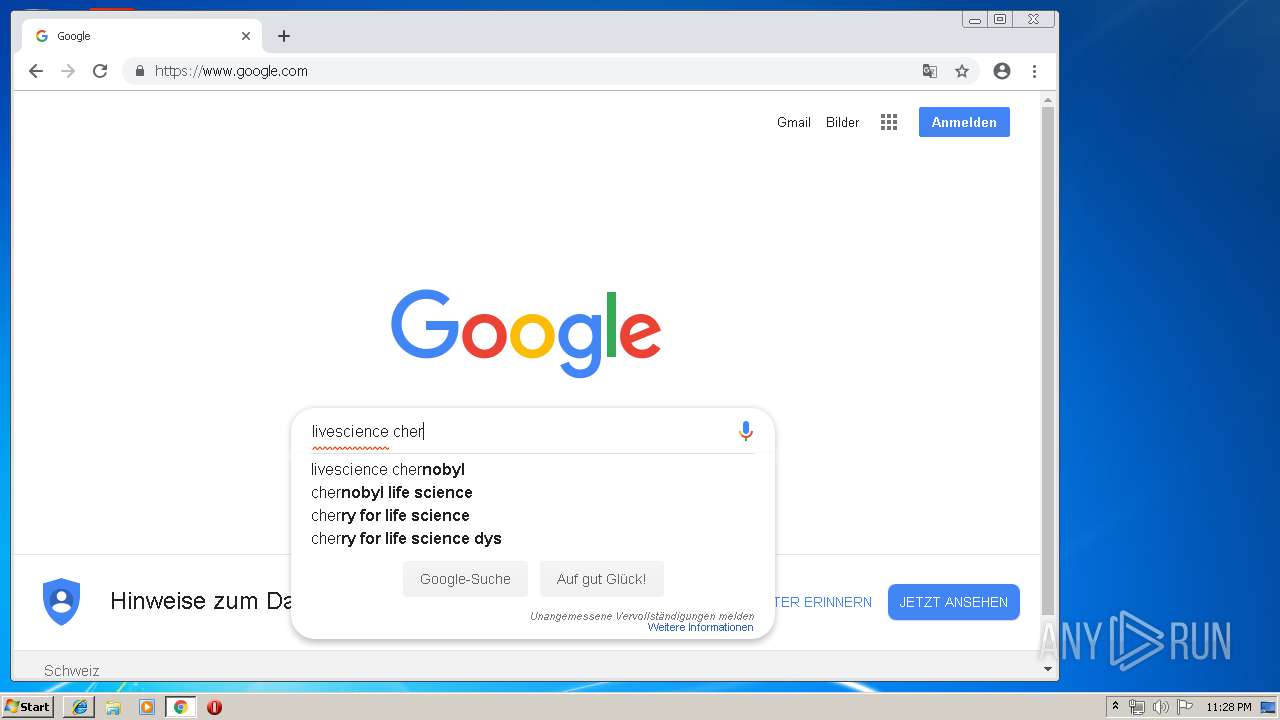
www.google.com |
| malicious |
www.google.ch |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2316 | chrome.exe | A Network Trojan was detected | ET CNC Ransomware Tracker Reported CnC Server group 65 |
2316 | chrome.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
2316 | chrome.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
2316 | chrome.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
2316 | chrome.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
2316 | chrome.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
10 ETPRO signatures available at the full report