| File name: | Topic.fakeapp |
| Full analysis: | https://app.any.run/tasks/8a84d379-8722-43aa-aa3f-74bc6bc947da |
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2024, 04:37:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | BAB0CE07CA98173E057FEA7D85286464 |
| SHA1: | 5AC936068BA5C030A00C83BFE239E6962A263F3C |
| SHA256: | 8B31CB0113424B2B158713CD29C9B123C97728F11DA08CC21040012DA0DE2B35 |
| SSDEEP: | 98304:iDrpK4L00MTSMVr0Xb002l0M2s6jRzvy7KV3rt8nOBl6M8Q/kh5AaftsXJnJnuzX:z5emUrG |
MALICIOUS
Drops the executable file immediately after the start
- Topic.fakeapp.exe (PID: 6548)
- irsetup.exe (PID: 6600)
Changes the autorun value in the registry
- reg.exe (PID: 7348)
SUSPICIOUS
Reads security settings of Internet Explorer
- Topic.fakeapp.exe (PID: 6548)
- irsetup.exe (PID: 6600)
- GeekerPDF.exe (PID: 6684)
- GeekerPDF.exe (PID: 8116)
Reads the date of Windows installation
- Topic.fakeapp.exe (PID: 6548)
- irsetup.exe (PID: 6600)
Executable content was dropped or overwritten
- Topic.fakeapp.exe (PID: 6548)
- irsetup.exe (PID: 6600)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 6600)
Creates a software uninstall entry
- irsetup.exe (PID: 6600)
Checks Windows Trust Settings
- GeekerPDF.exe (PID: 6684)
- GeekerPDF.exe (PID: 8116)
Application launched itself
- GeekerPDF.exe (PID: 6684)
Uses REG/REGEDIT.EXE to modify registry
- GeekerPDF.exe (PID: 6684)
INFO
Reads the computer name
- Topic.fakeapp.exe (PID: 6548)
- irsetup.exe (PID: 6600)
- GeekerPDF.exe (PID: 6684)
- TextInputHost.exe (PID: 2628)
- GeekerPDF.exe (PID: 8116)
Checks supported languages
- Topic.fakeapp.exe (PID: 6548)
- irsetup.exe (PID: 6600)
- GeekerPDF.exe (PID: 8116)
- GeekerPDF.exe (PID: 6684)
- TextInputHost.exe (PID: 2628)
Creates files in the program directory
- irsetup.exe (PID: 6600)
- WINWORD.EXE (PID: 6748)
Process checks computer location settings
- Topic.fakeapp.exe (PID: 6548)
- irsetup.exe (PID: 6600)
Create files in a temporary directory
- irsetup.exe (PID: 6600)
- Topic.fakeapp.exe (PID: 6548)
Creates files or folders in the user directory
- irsetup.exe (PID: 6600)
Reads Microsoft Office registry keys
- irsetup.exe (PID: 6600)
Reads the machine GUID from the registry
- GeekerPDF.exe (PID: 6684)
- GeekerPDF.exe (PID: 8116)
Reads the software policy settings
- GeekerPDF.exe (PID: 6684)
- GeekerPDF.exe (PID: 8116)
Checks proxy server information
- GeekerPDF.exe (PID: 8116)
- GeekerPDF.exe (PID: 6684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .scr | | | Windows screen saver (76.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (11.7) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2012:06:14 16:16:12+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 10 |
| CodeSize: | 25088 |
| InitializedDataSize: | 189952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2d1c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.1.0.0 |
| ProductVersionNumber: | 9.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | Created with Setup Factory |
| FileDescription: | Setup Application |
| FileVersion: | 9.1.0.0 |
| InternalName: | suf_launch |
| LegalCopyright: | Setup Engine Copyright © 2004-2012 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFileName: | suf_launch.exe |
| ProductName: | Setup Factory Runtime |
| ProductVersion: | 9.1.0.0 |
Total processes
144
Monitored processes
9
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1108 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "61720396-922B-4200-97F2-3CBA2144479A" "88E154F0-C6F1-4584-AB56-9E17CED22342" "6748" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 2628 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 6548 | "C:\Users\admin\AppData\Local\Temp\Topic.fakeapp.exe" | C:\Users\admin\AppData\Local\Temp\Topic.fakeapp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Application Exit code: 0 Version: 9.1.0.0 Modules
| |||||||||||||||
| 6600 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe" __IRAOFF:5706098 "__IRAFN:C:\Users\admin\AppData\Local\Temp\Topic.fakeapp.exe" "__IRCT:0" "__IRTSS:0" "__IRSID:S-1-5-21-1693682860-607145093-2874071422-1001" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | Topic.fakeapp.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: MEDIUM Description: Setup Application Exit code: 0 Version: 9.1.0.0 Modules
| |||||||||||||||
| 6684 | "C:\ProgramData\101world\GeekerPDF.exe" | C:\ProgramData\101world\GeekerPDF.exe | irsetup.exe | ||||||||||||
User: admin Company: AmindPDF Integrity Level: MEDIUM Description: AmindPDF Exit code: 0 Version: 2.0.0.824 Modules
| |||||||||||||||
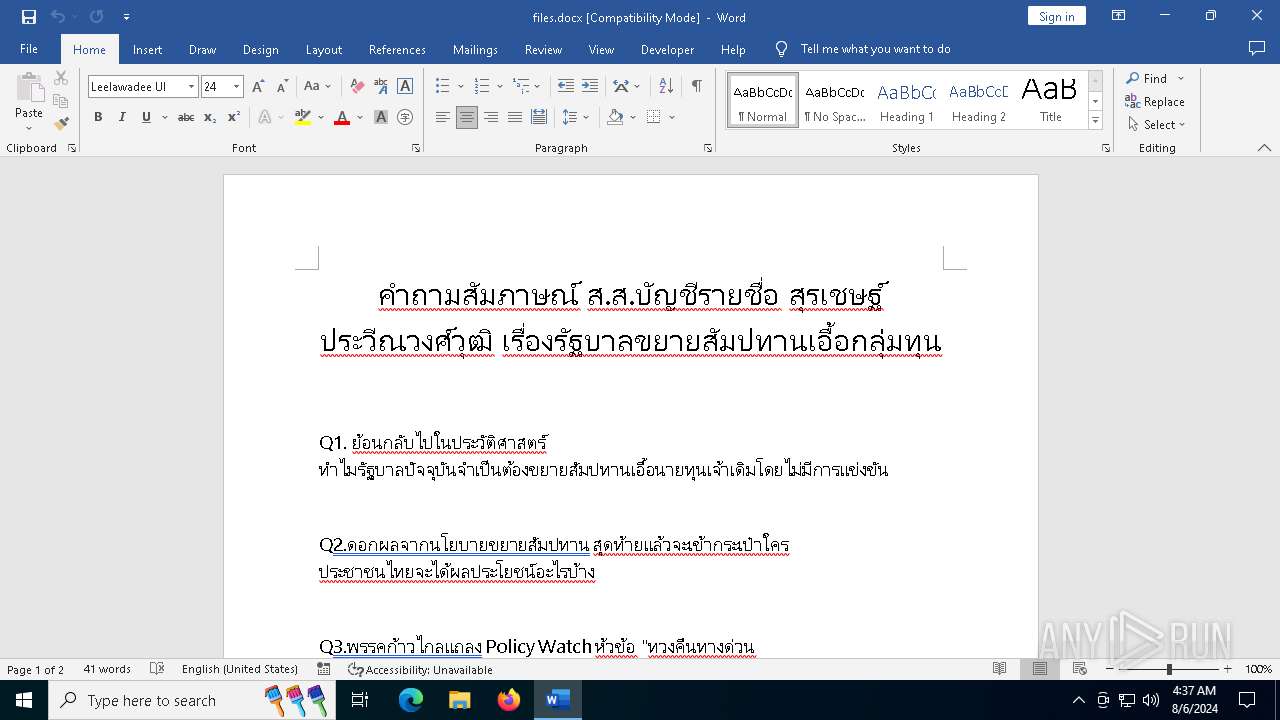
| 6748 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\ProgramData\101world\files.docx" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | irsetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 7348 | reg add HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\ /v MicrosoftEdgeAutoLaunch_ACB5CC041F98E32A012CE084078F0CF7 /t REG_SZ /d "\"C:\ProgramData\101world\GeekerPDF.exe\" --no-startup-window" /f | C:\Windows\SysWOW64\reg.exe | GeekerPDF.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8116 | "C:\ProgramData\101world\GeekerPDF.exe" --no-startup-window | C:\ProgramData\101world\GeekerPDF.exe | GeekerPDF.exe | ||||||||||||
User: admin Company: AmindPDF Integrity Level: MEDIUM Description: AmindPDF Version: 2.0.0.824 Modules
| |||||||||||||||
Total events
27 625
Read events
27 174
Write events
424
Delete events
27
Modification events
| (PID) Process: | (6548) Topic.fakeapp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6548) Topic.fakeapp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6548) Topic.fakeapp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6548) Topic.fakeapp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6600) irsetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\101world1.0 |
| Operation: | write | Name: | DisplayName |
Value: 101world | |||
| (PID) Process: | (6600) irsetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\101world1.0 |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (6600) irsetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\101world1.0 |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (6600) irsetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\101world1.0 |
| Operation: | write | Name: | UninstallString |
Value: "C:\ProgramData\101world\uninstall.exe" "/U:C:\ProgramData\101world\Uninstall\uninstall.xml" | |||
| (PID) Process: | (6600) irsetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\101world1.0 |
| Operation: | write | Name: | Publisher |
Value: 101world | |||
| (PID) Process: | (6600) irsetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\101world1.0 |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.101world.com | |||
Executable files
39
Suspicious files
126
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6600 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\101world Setup Log.txt | text | |
MD5:702F115E9E99C72EAA941B6BB48DC434 | SHA256:C1D0F19C58318C141423D38DC776BF0434A6207417313EB1D895D51A568528E3 | |||
| 6600 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG2.JPG | image | |
MD5:AC40DED6736E08664F2D86A65C47EF60 | SHA256:F35985FE1E46A767BE7DCEA35F8614E1EDD60C523442E6C2C2397D1E23DBD3EA | |||
| 6548 | Topic.fakeapp.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | executable | |
MD5:2E0592AE7EF0EAC76C78A676E65BE9B8 | SHA256:B9C5343BAC47F2E8492ED75E2424A0789909EA822048232E16F5C270D6C5A2CF | |||
| 6600 | irsetup.exe | C:\ProgramData\101world\AmindPDFCore.dll | executable | |
MD5:6206C4682BA2B9D3ADFDCBD410CEF5EF | SHA256:0BD114FECFD3C09820FA013D8CD8AADEDEE69906B6F81A2E827BBA68DDF1023B | |||
| 6600 | irsetup.exe | C:\ProgramData\101world\files.docx | document | |
MD5:ACA5AD705F3AD552F5CF9D01B141F0E0 | SHA256:07C3B7E553BF4A99CA419A83FC57F0875419FFAD695C7901D74DD05B9E03FCF9 | |||
| 6548 | Topic.fakeapp.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\lua5.1.dll | executable | |
MD5:958103E55C74427E5C66D7E18F3BF237 | SHA256:3EA4A4C3C6DEA44D8917B342E93D653F59D93E1F552ACE16E97E43BB04E951D8 | |||
| 6600 | irsetup.exe | C:\ProgramData\101world\lua5.1.dll | executable | |
MD5:958103E55C74427E5C66D7E18F3BF237 | SHA256:3EA4A4C3C6DEA44D8917B342E93D653F59D93E1F552ACE16E97E43BB04E951D8 | |||
| 6600 | irsetup.exe | C:\ProgramData\101world\uninstall.exe | executable | |
MD5:2E0592AE7EF0EAC76C78A676E65BE9B8 | SHA256:B9C5343BAC47F2E8492ED75E2424A0789909EA822048232E16F5C270D6C5A2CF | |||
| 6600 | irsetup.exe | C:\ProgramData\101world\Uninstall\uninstall.dat | binary | |
MD5:EF8BD6913A1D78A8F40D85D090773259 | SHA256:A2A660AC63F7576FE9D6DD4EA7A42956D734970866BDDCD966ECC3BD00472289 | |||
| 6600 | irsetup.exe | C:\ProgramData\101world\Uninstall\IRIMG2.JPG | image | |
MD5:AC40DED6736E08664F2D86A65C47EF60 | SHA256:F35985FE1E46A767BE7DCEA35F8614E1EDD60C523442E6C2C2397D1E23DBD3EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
99
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
640 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
640 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6528 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6428 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6748 | WINWORD.EXE | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | — | — | whitelisted |
6748 | WINWORD.EXE | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
6748 | WINWORD.EXE | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
6748 | WINWORD.EXE | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
6748 | WINWORD.EXE | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5588 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2464 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6684 | GeekerPDF.exe | 47.89.131.190:443 | client.amindpdf.com | Alibaba US Technology Co., Ltd. | US | unknown |
6748 | WINWORD.EXE | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | unknown |
6748 | WINWORD.EXE | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6748 | WINWORD.EXE | 2.19.126.160:443 | omex.cdn.office.net | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.amindpdf.com |
| unknown |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|