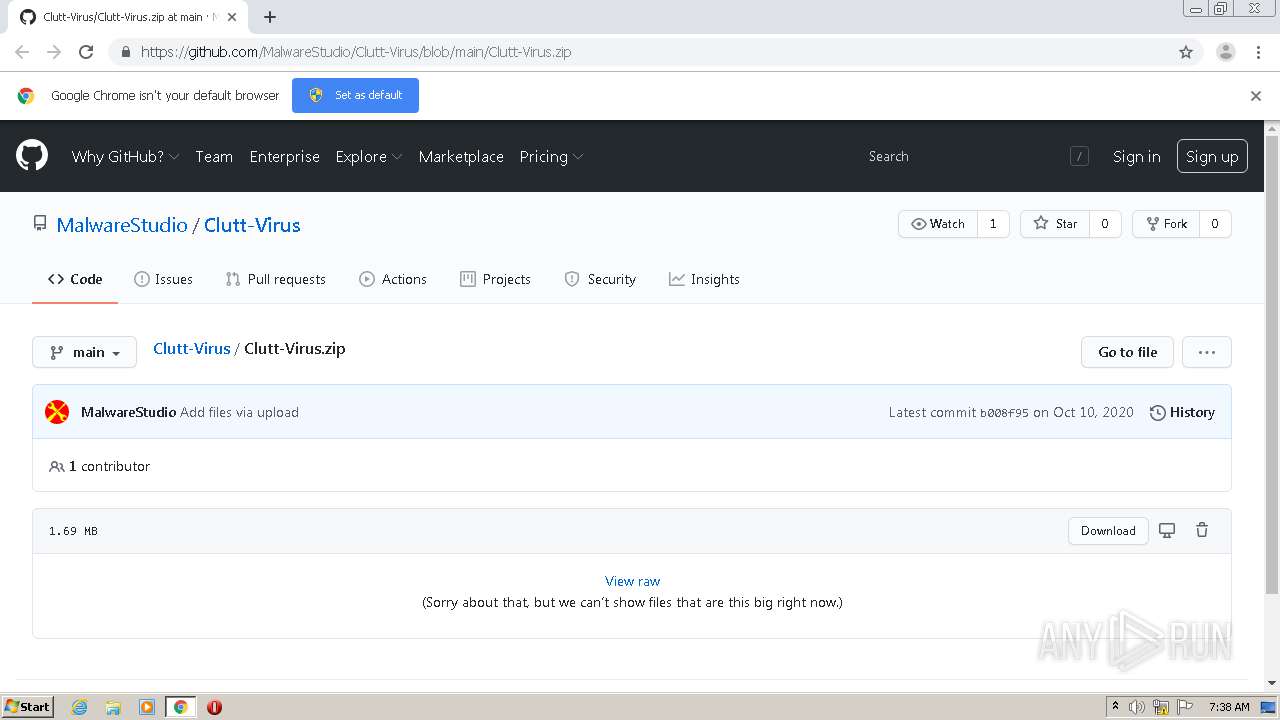
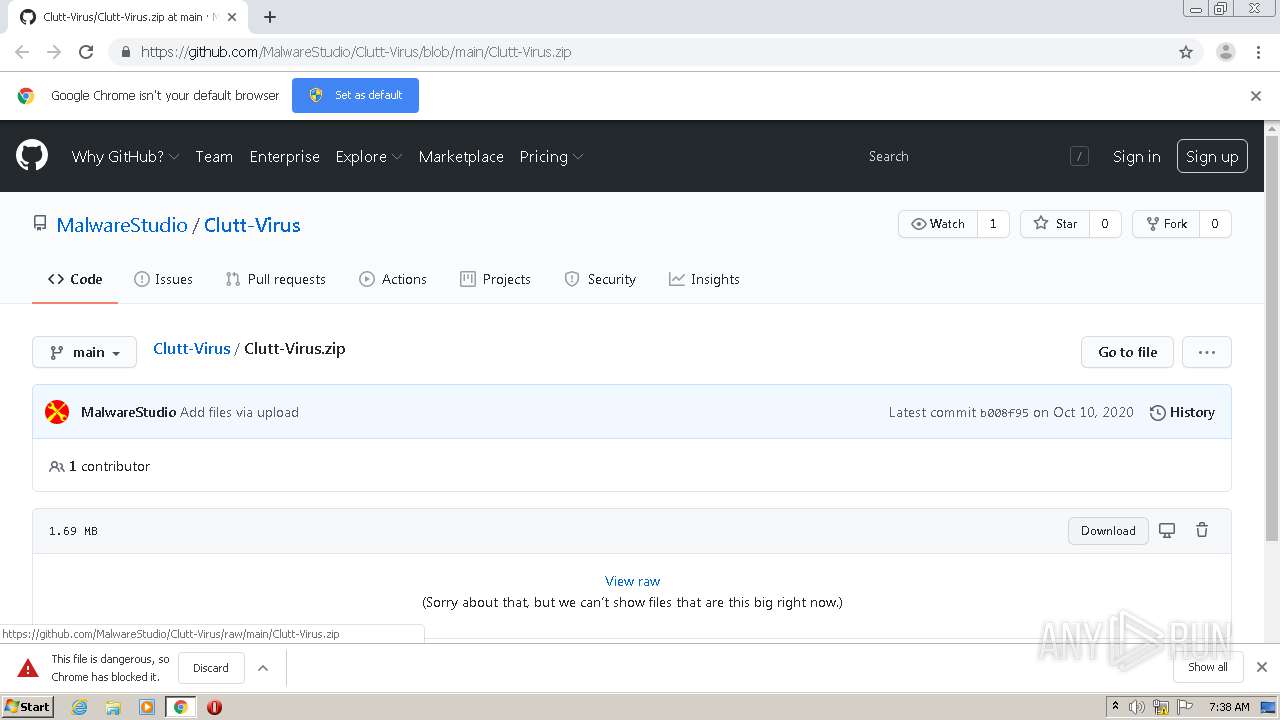
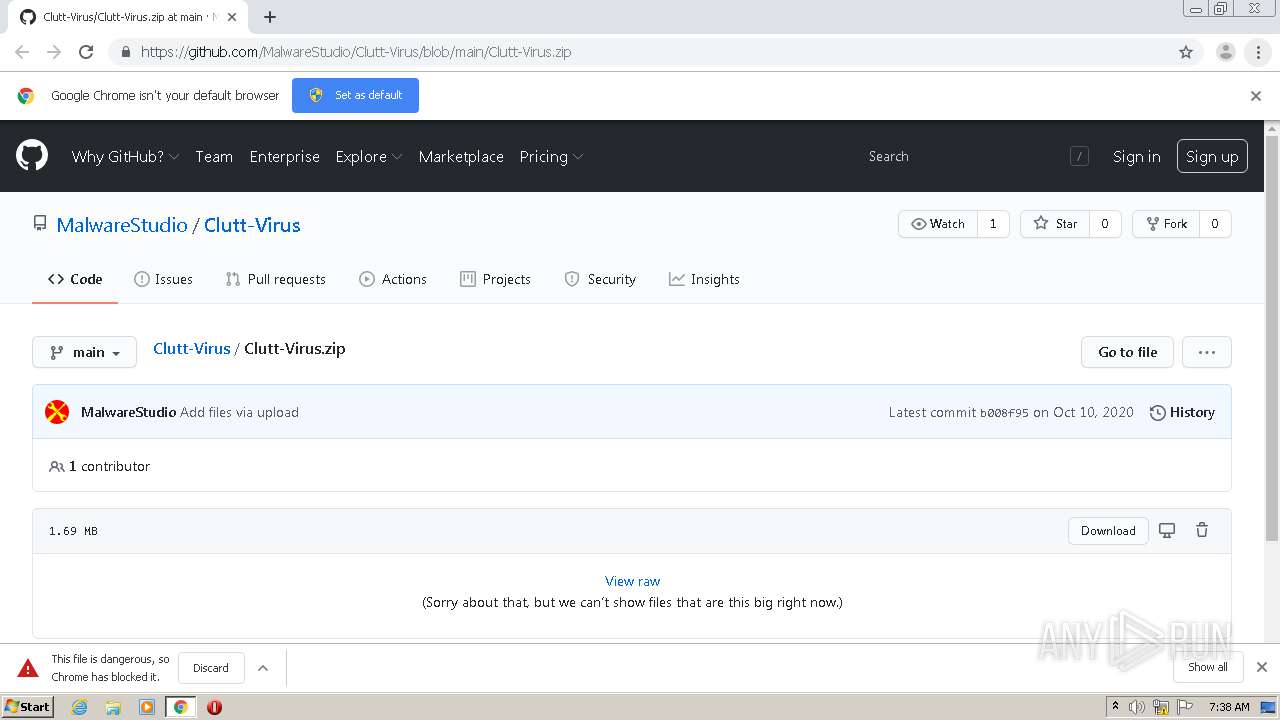
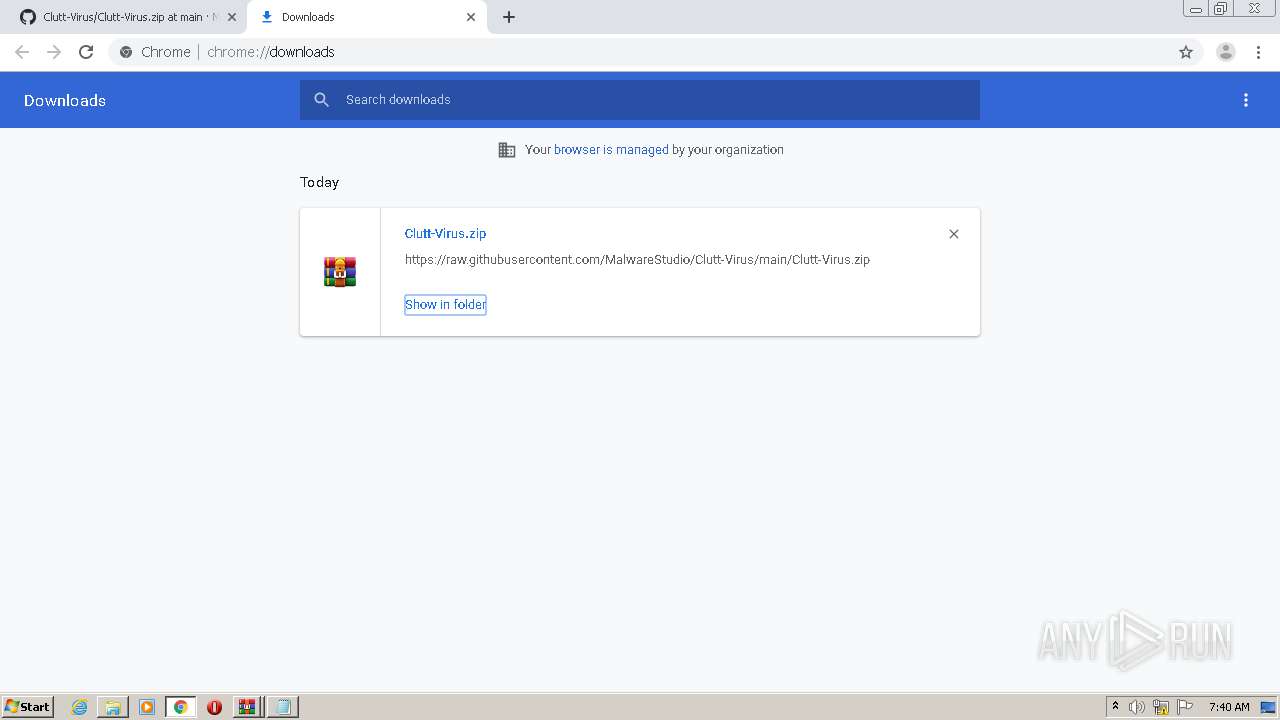
| URL: | https://github.com/MalwareStudio/Clutt-Virus/blob/main/Clutt-Virus.zip |
| Full analysis: | https://app.any.run/tasks/af4c9344-7734-4d06-aa92-1a6b39e20a37 |
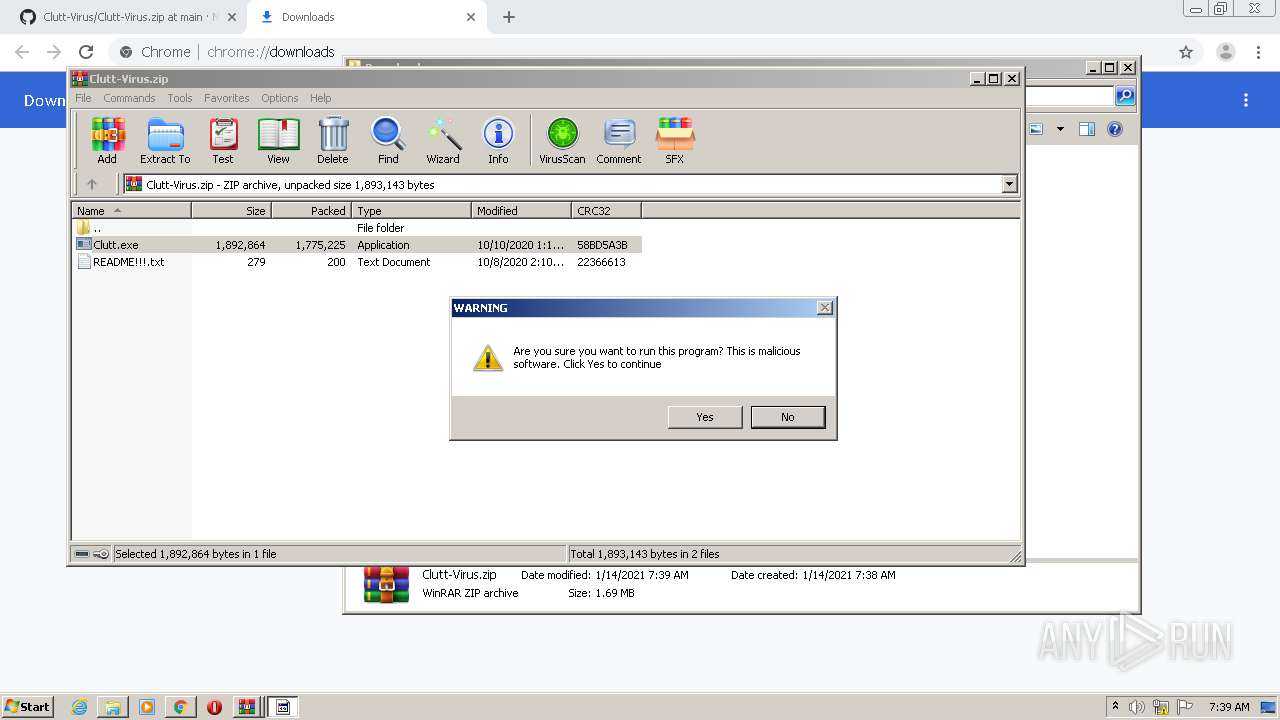
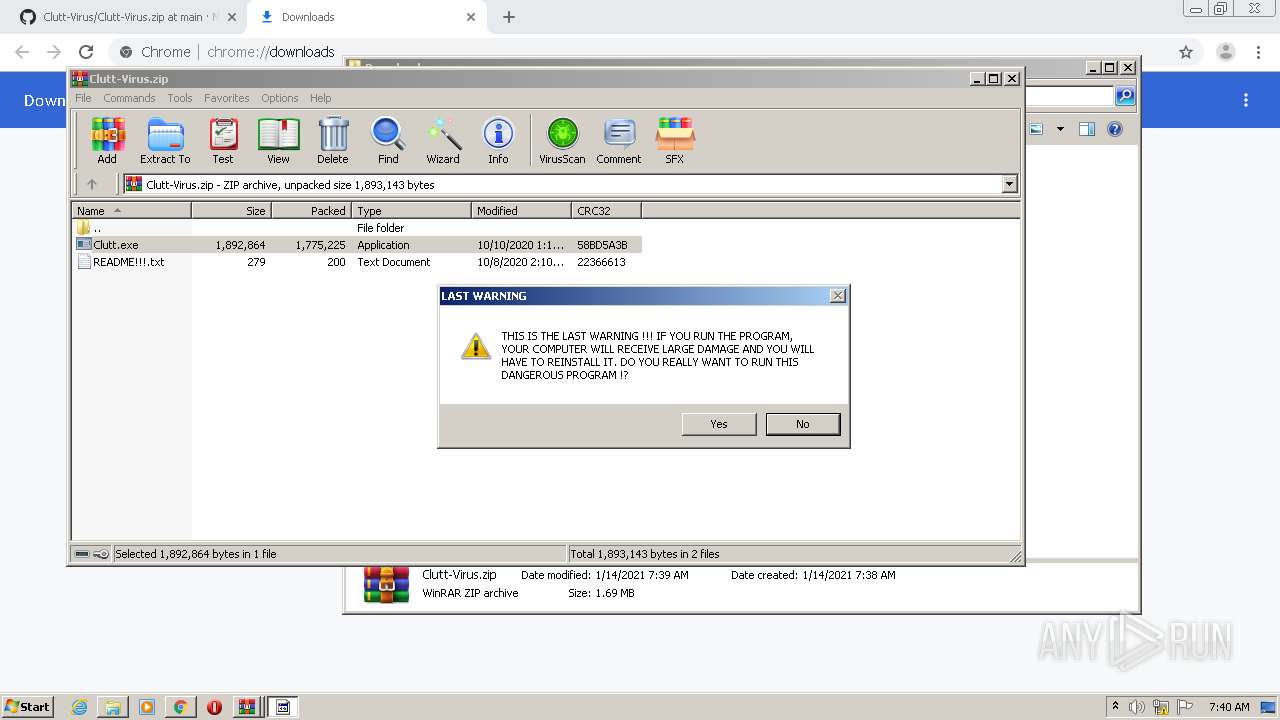
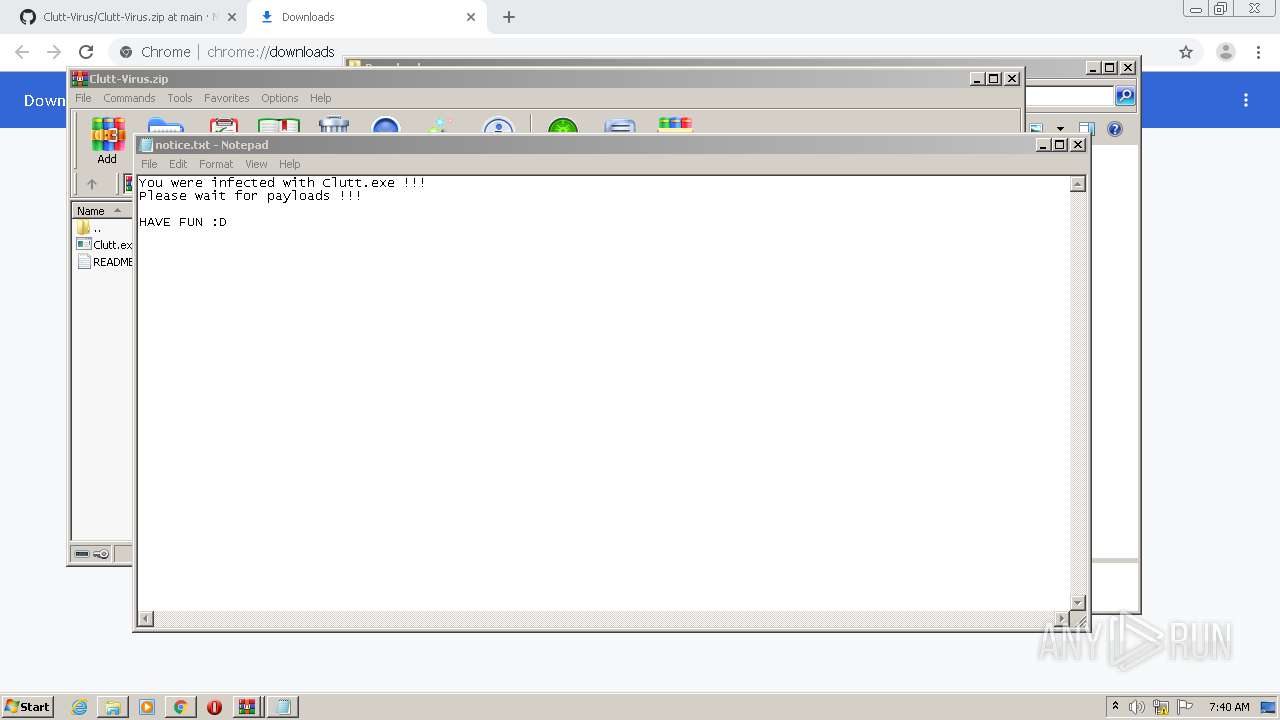
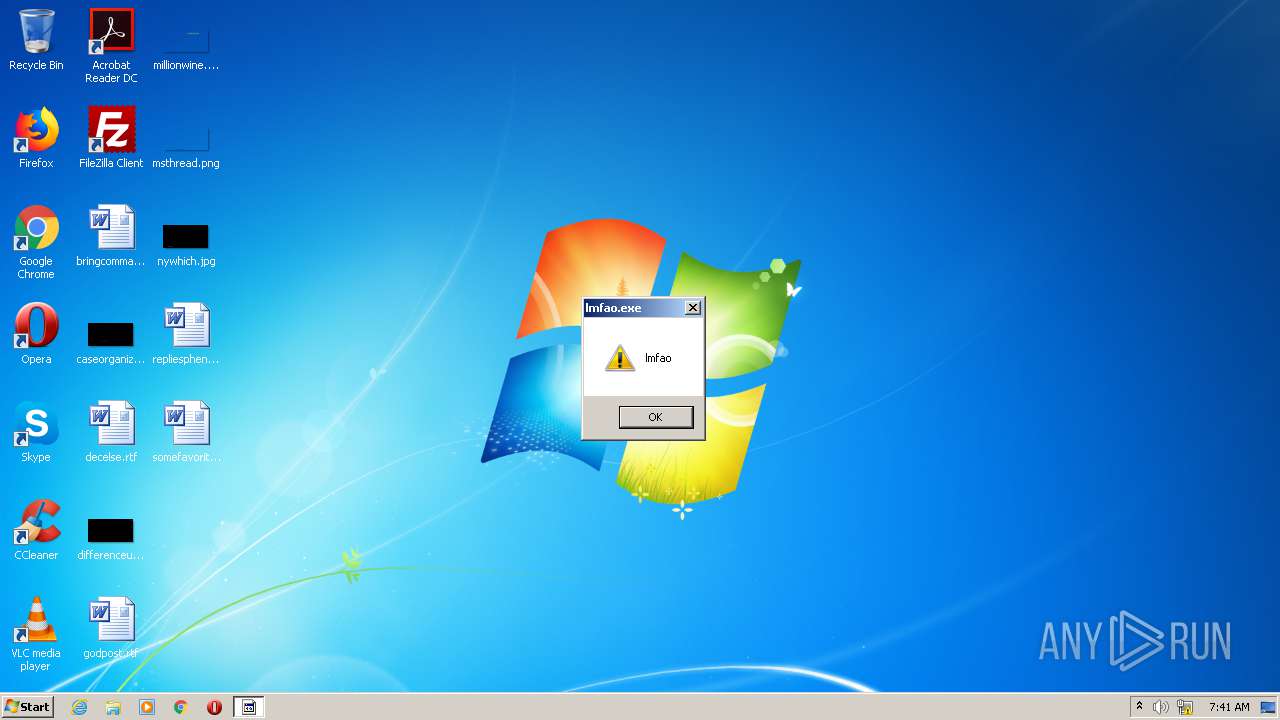
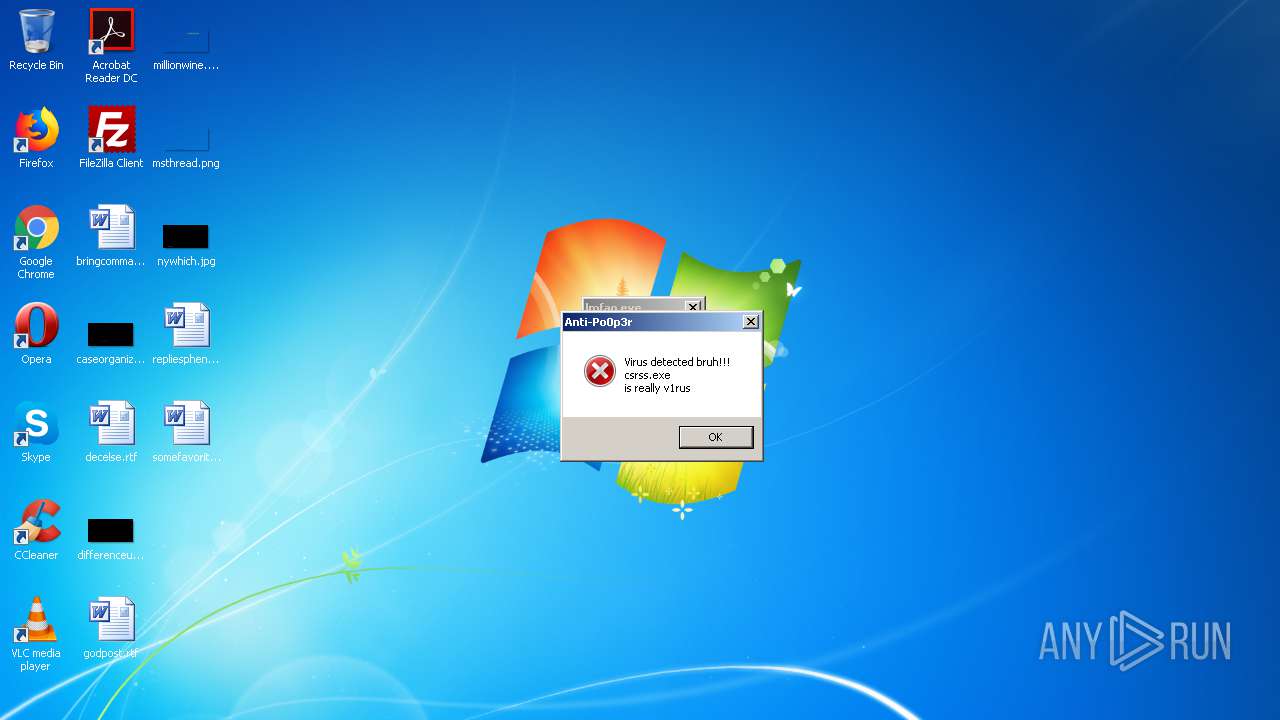
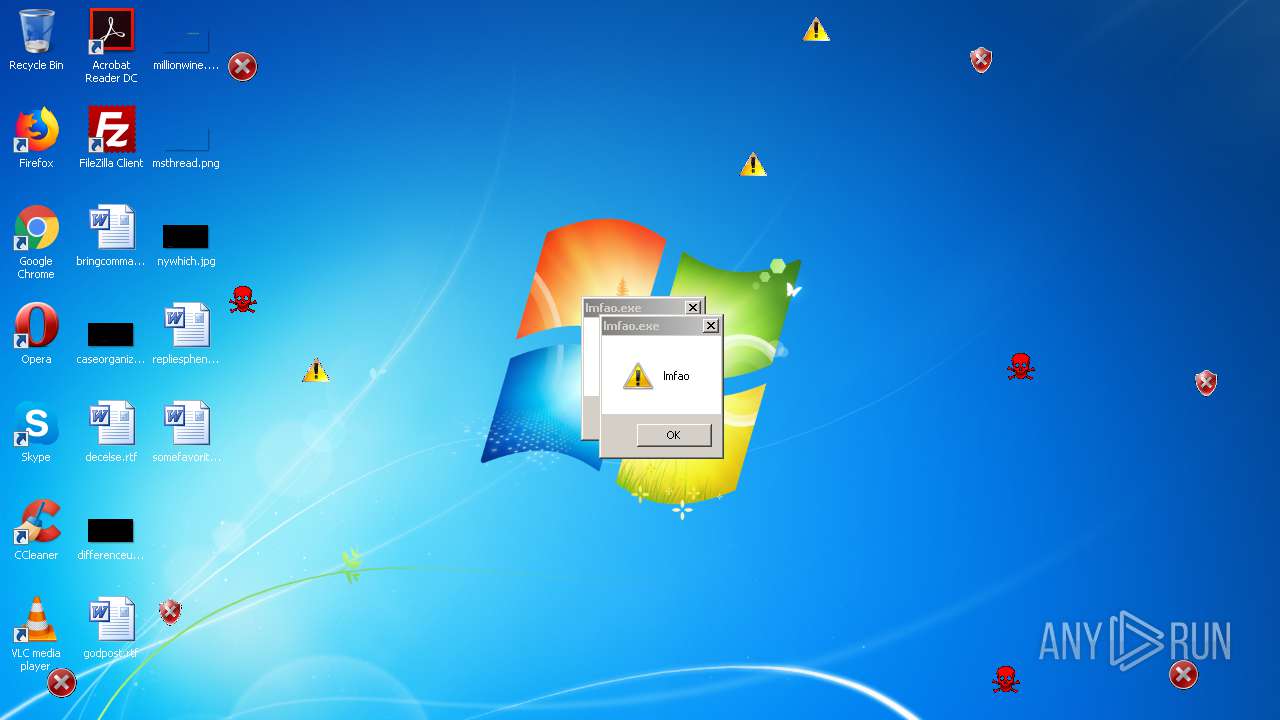
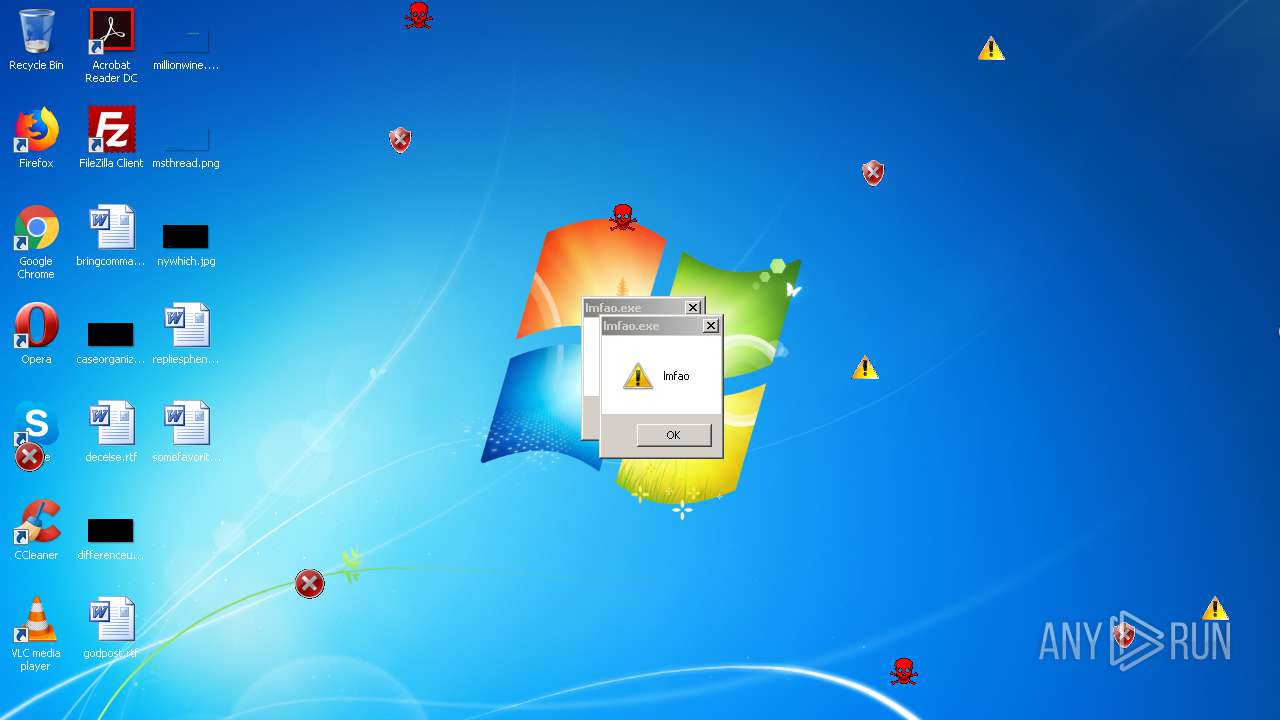
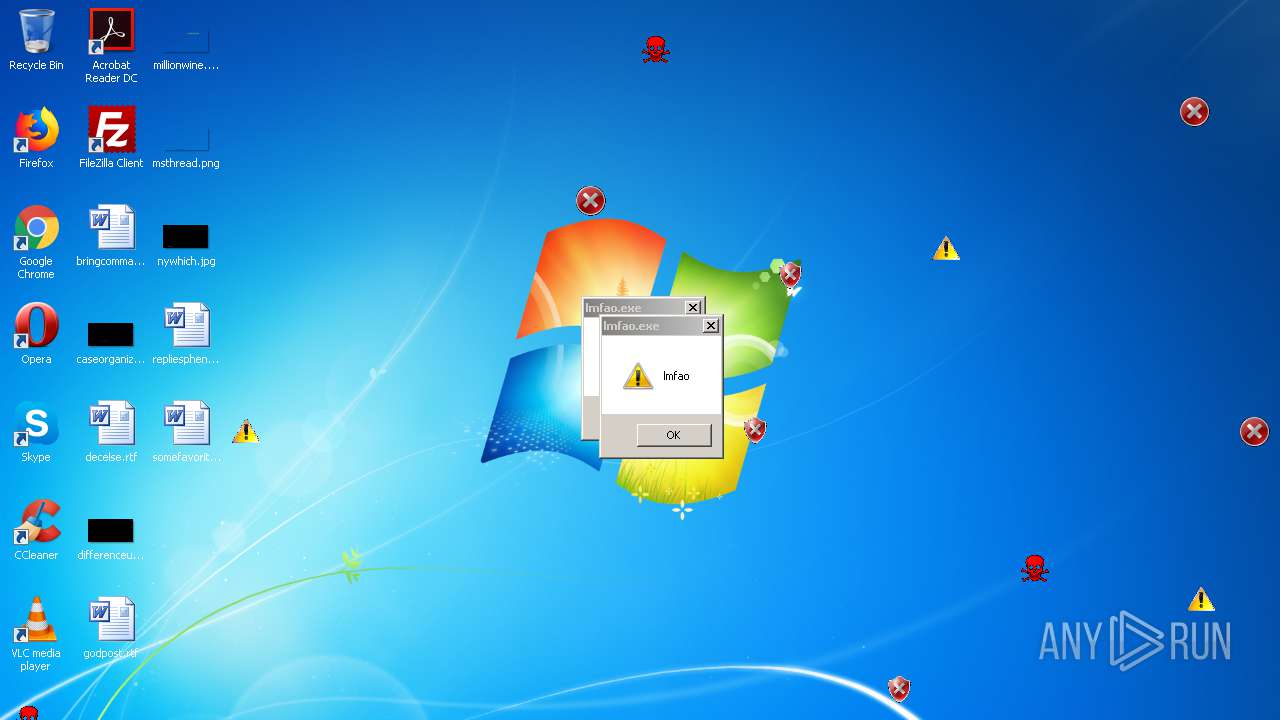
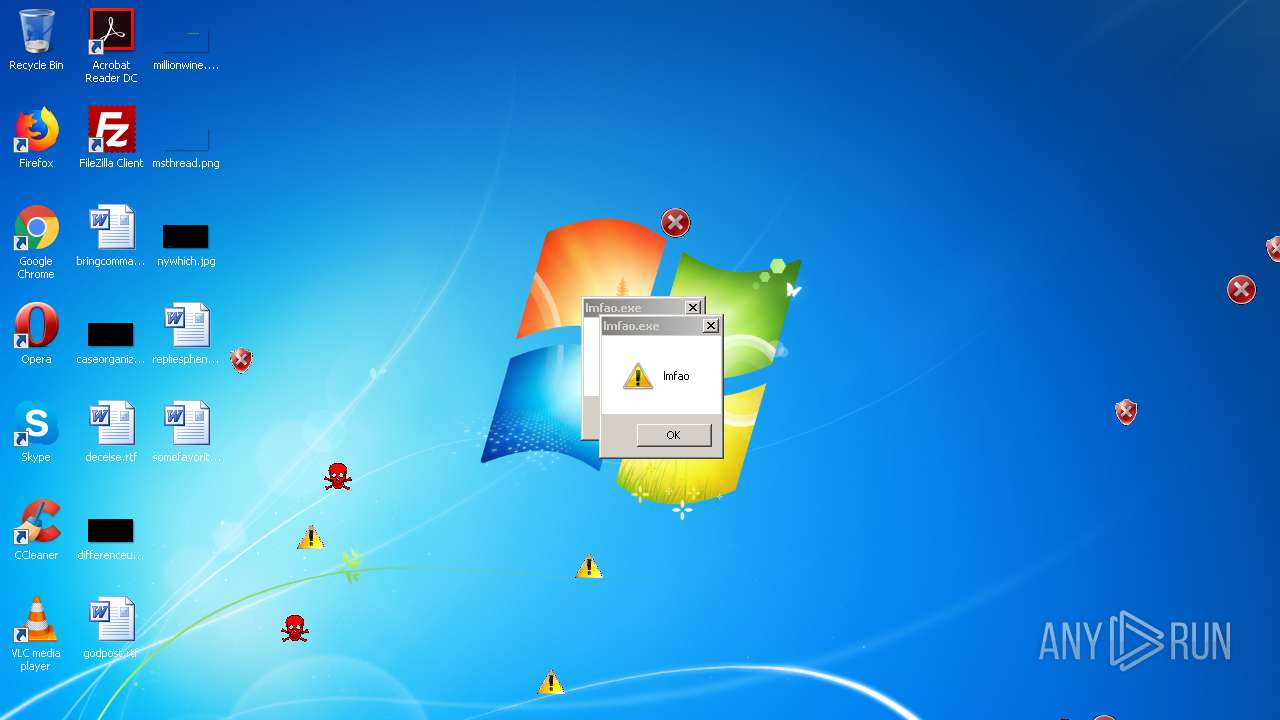
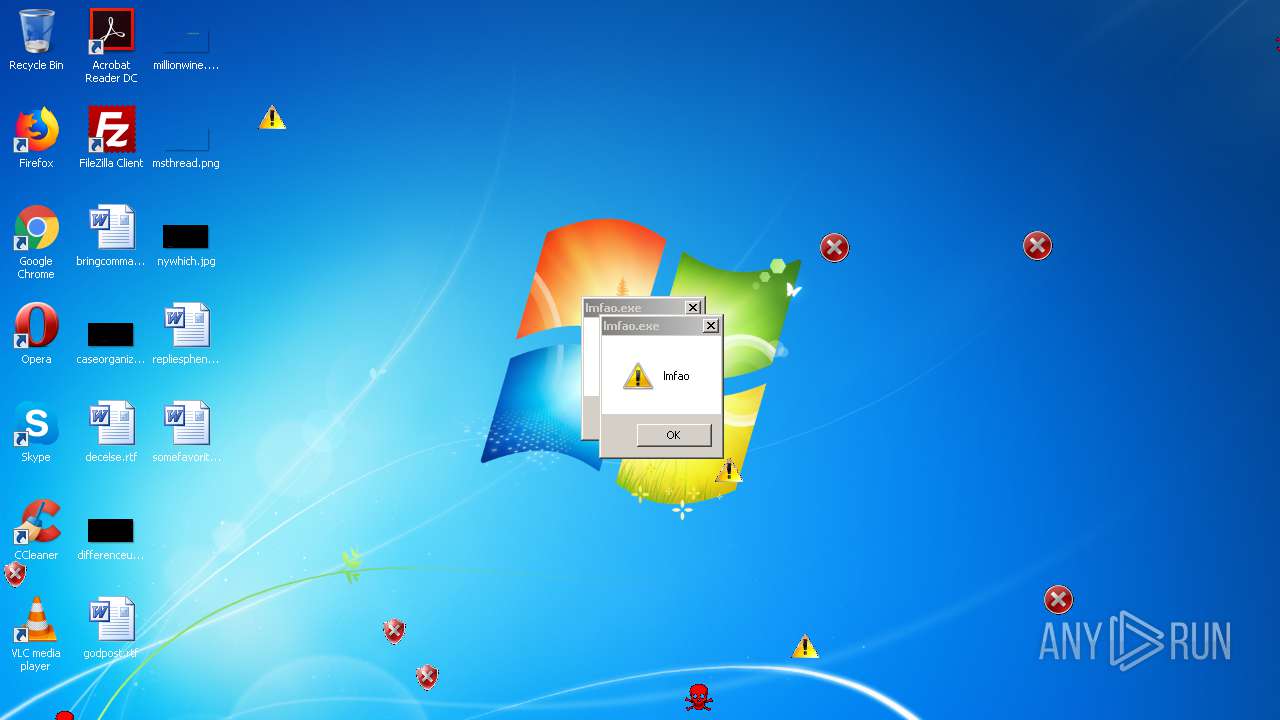
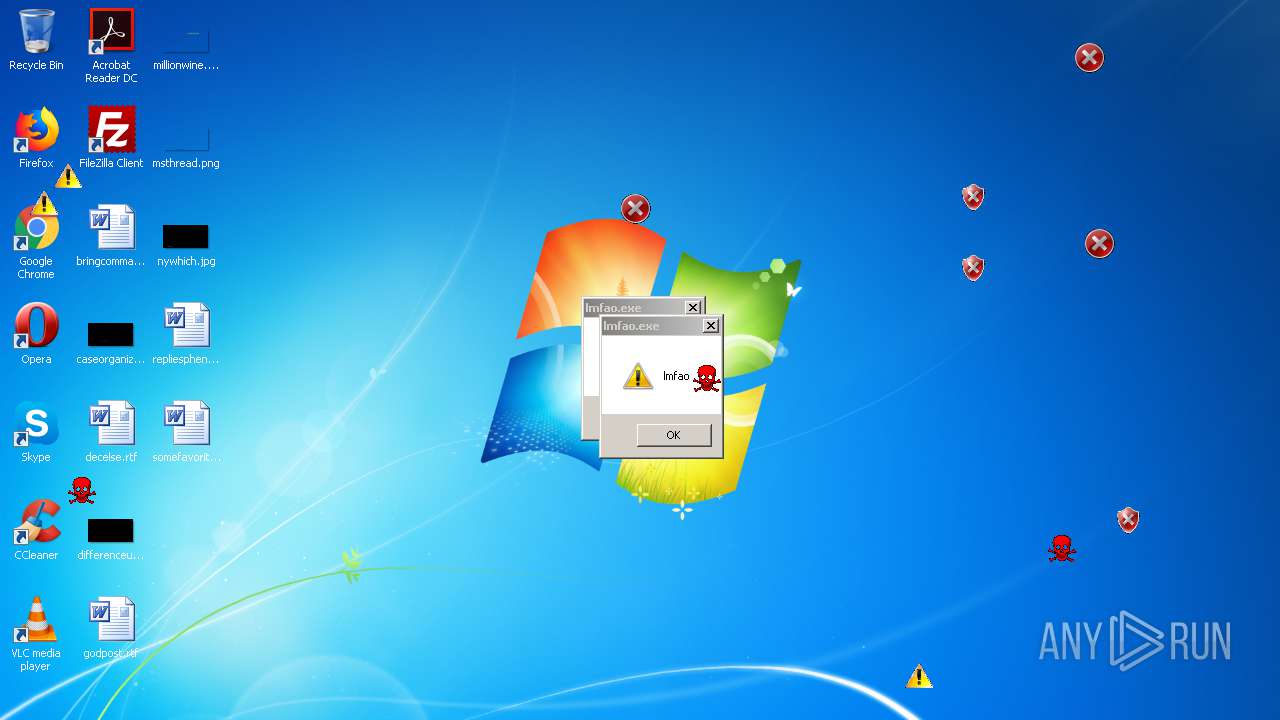
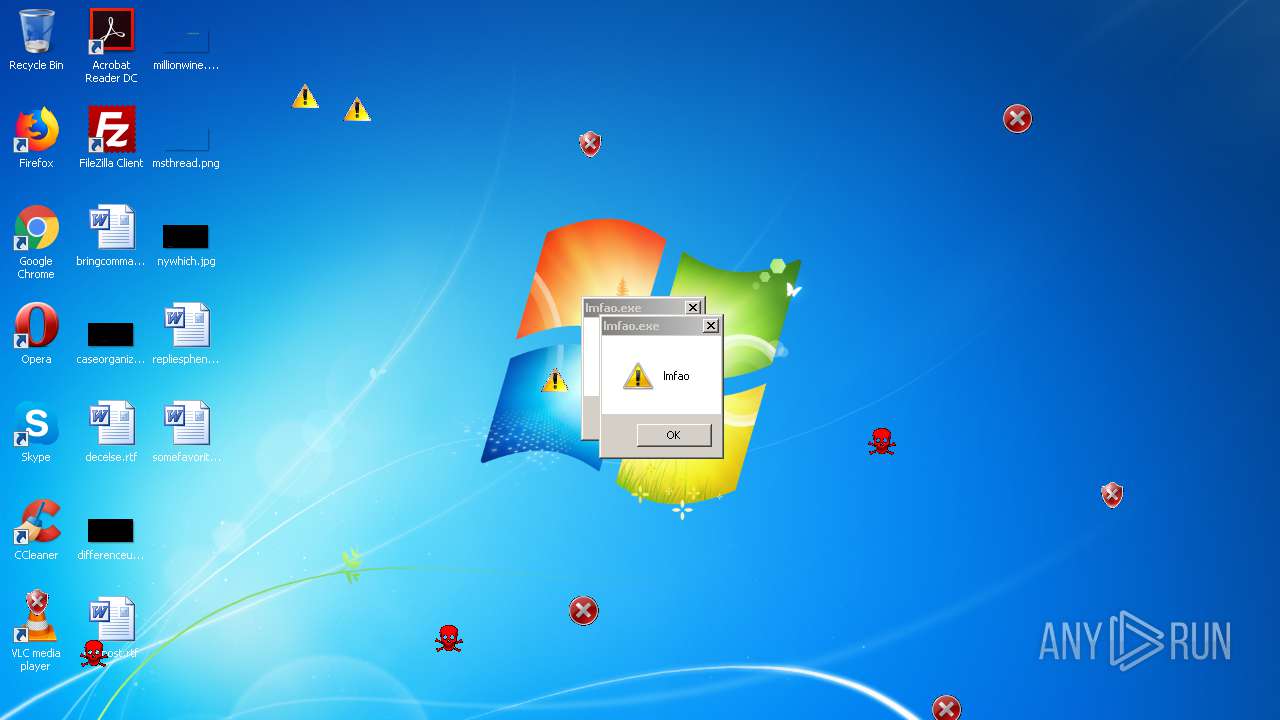
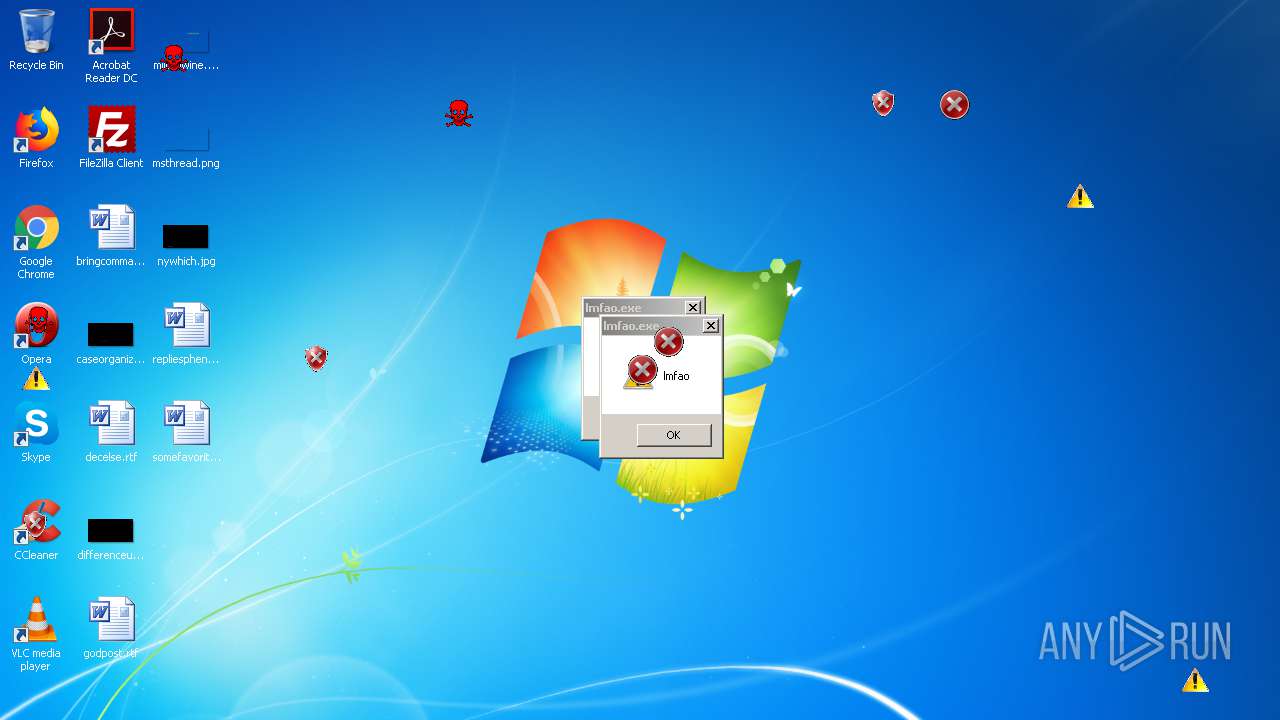
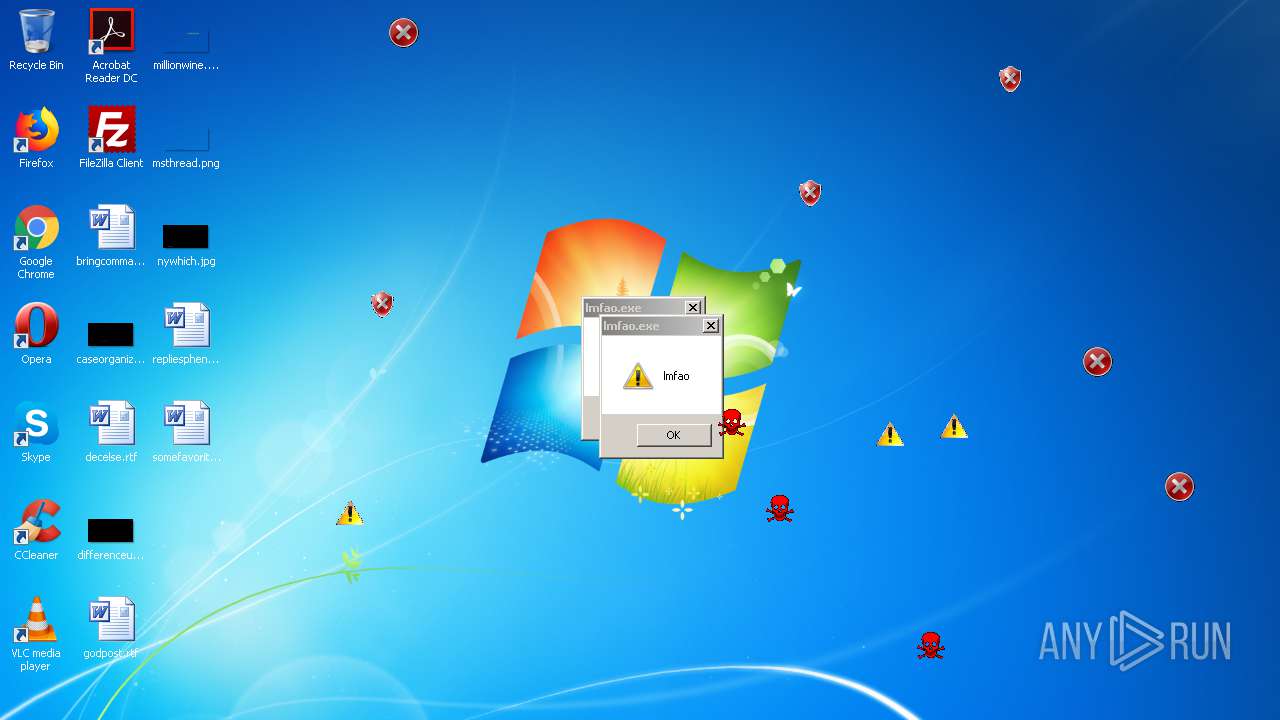
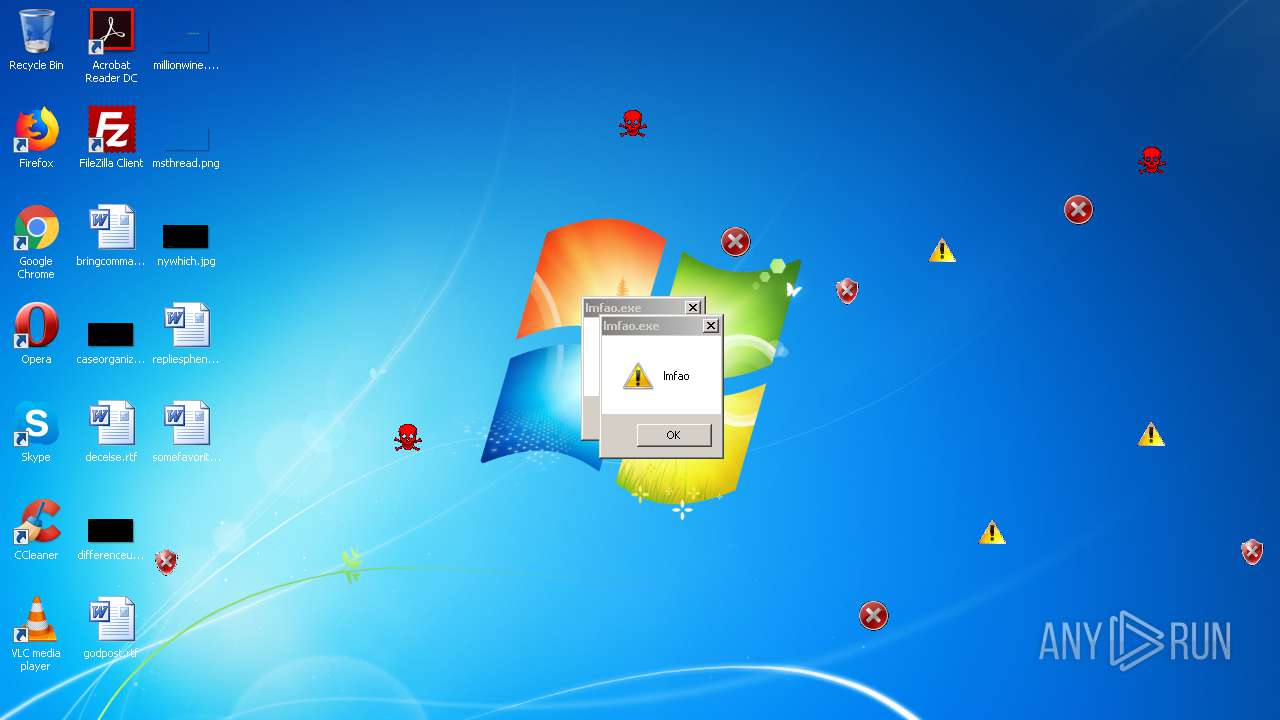
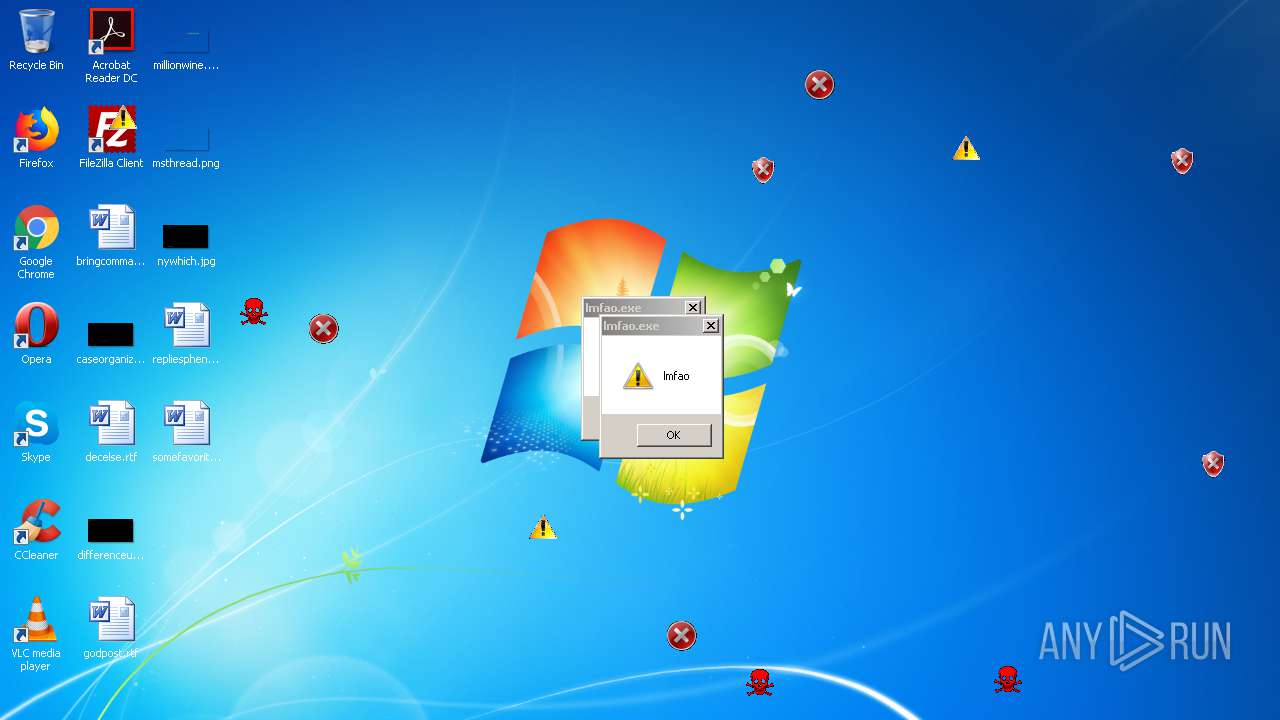
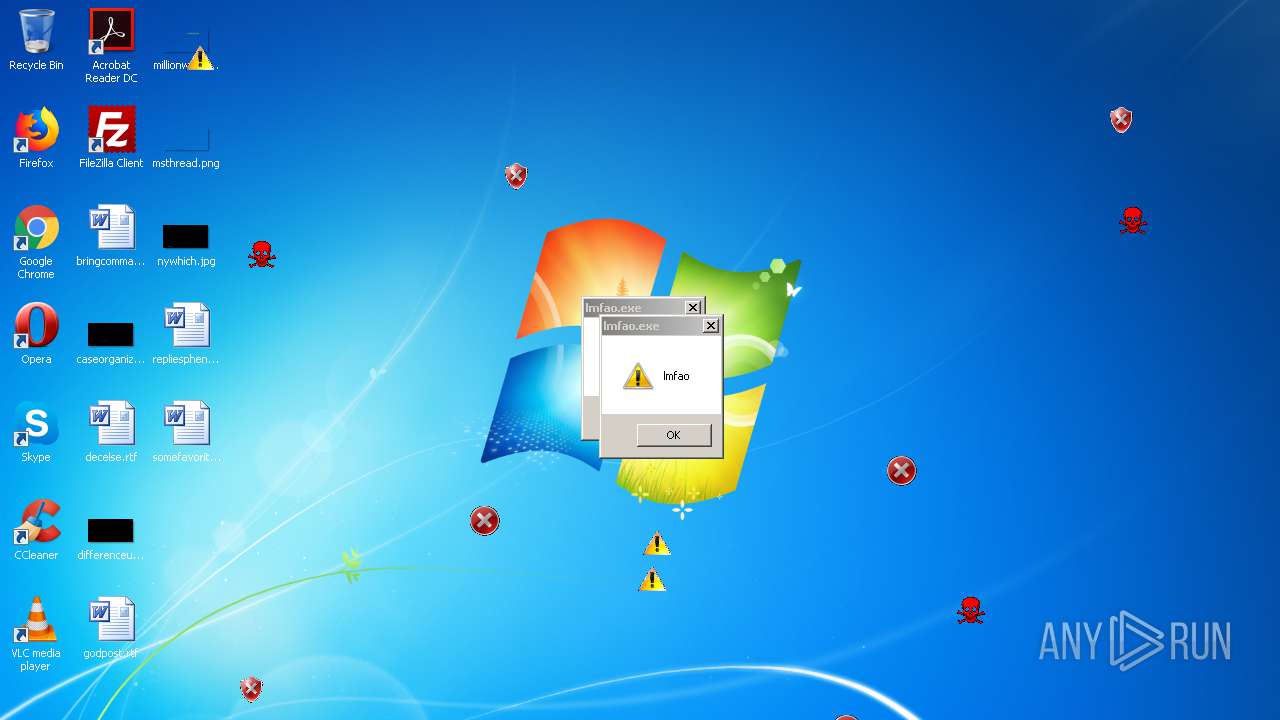
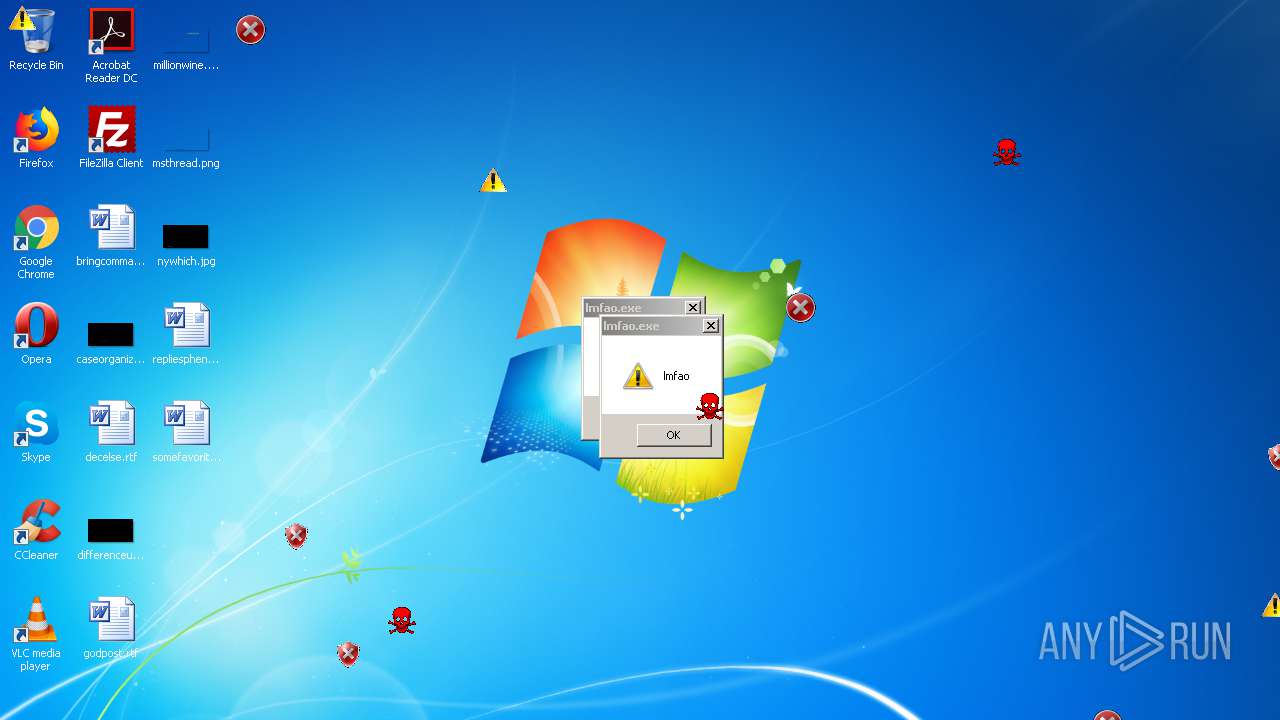
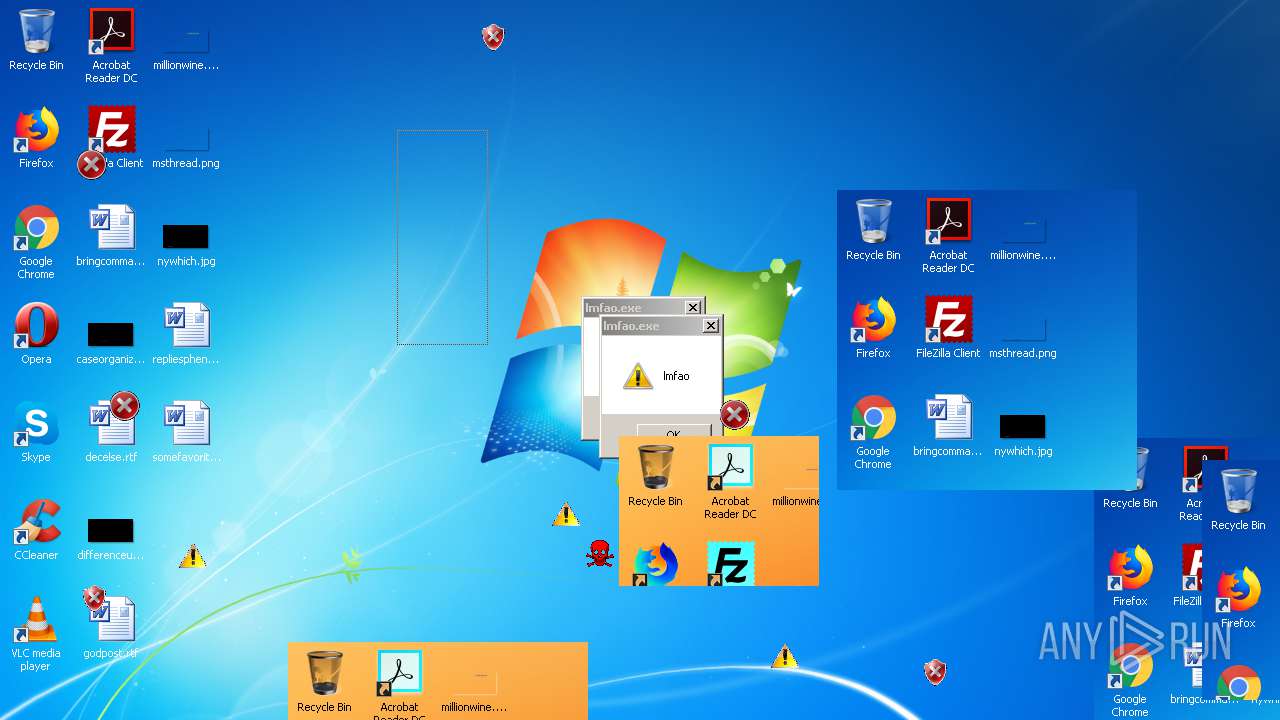
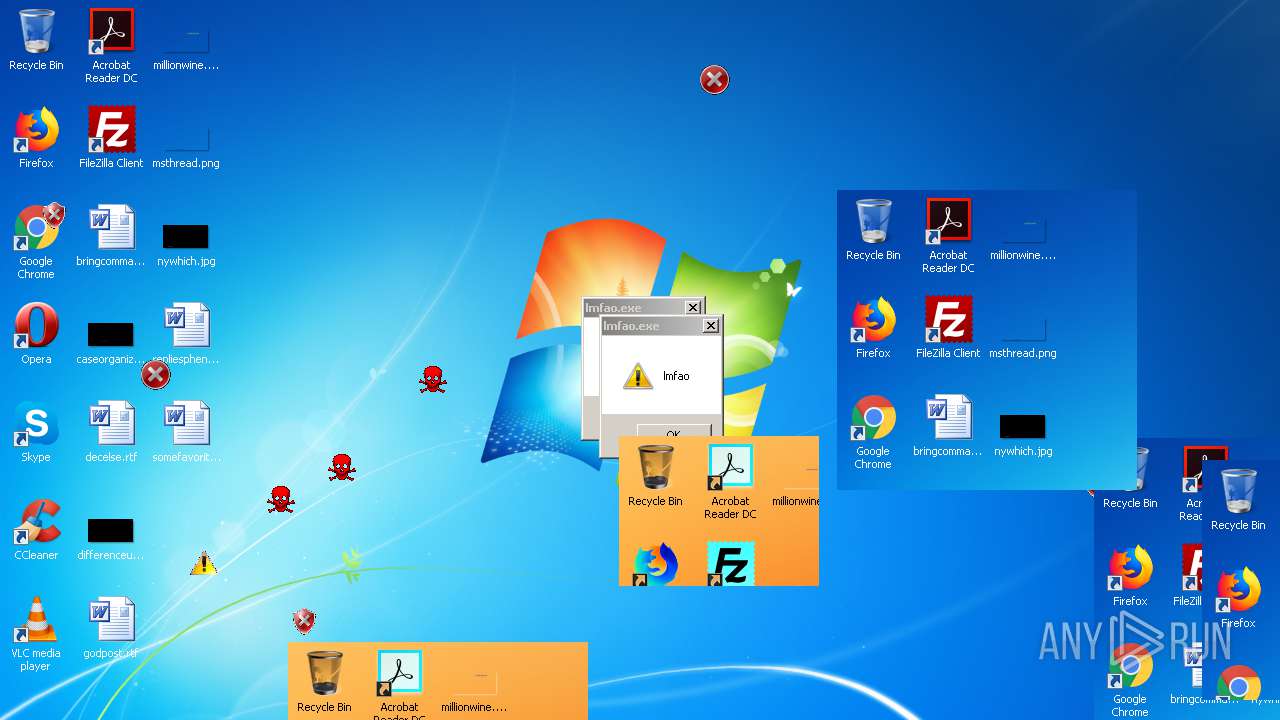
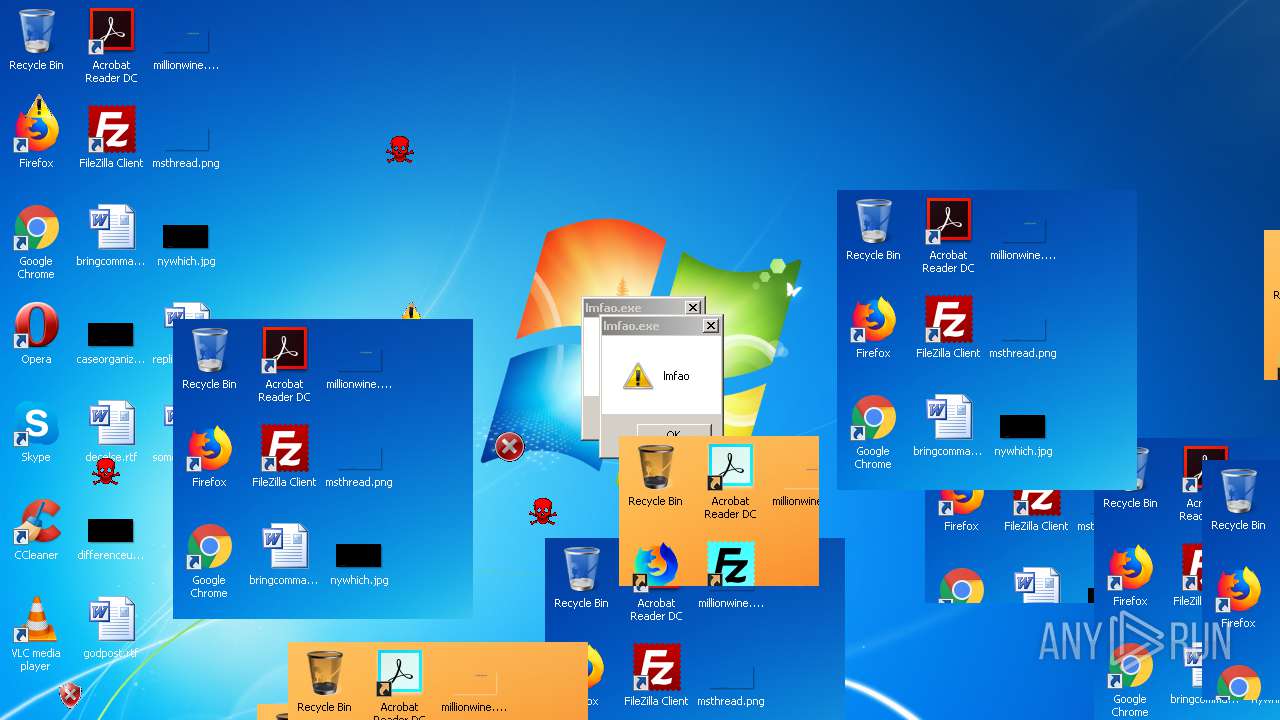
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2021, 07:38:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A600711847B5A83A5F785E234CF634BA |
| SHA1: | FB3206AEC11D10685A7F64C32845B782E95F589F |
| SHA256: | 8B2AD7044223B12499F5006E35DD863B5D113D1A0AAB42A0427688712C18FE90 |
| SSDEEP: | 3:N8tEdn3iZnSERv3DfMVn:2udS0sv3Dc |
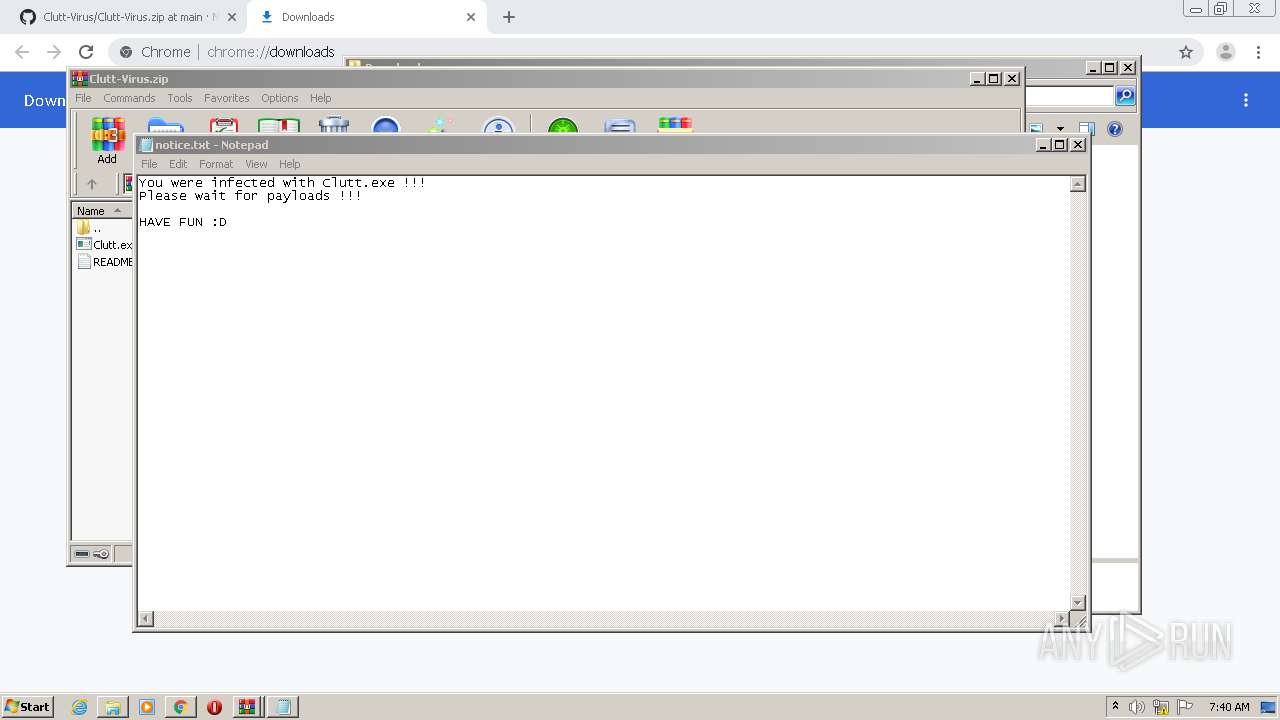
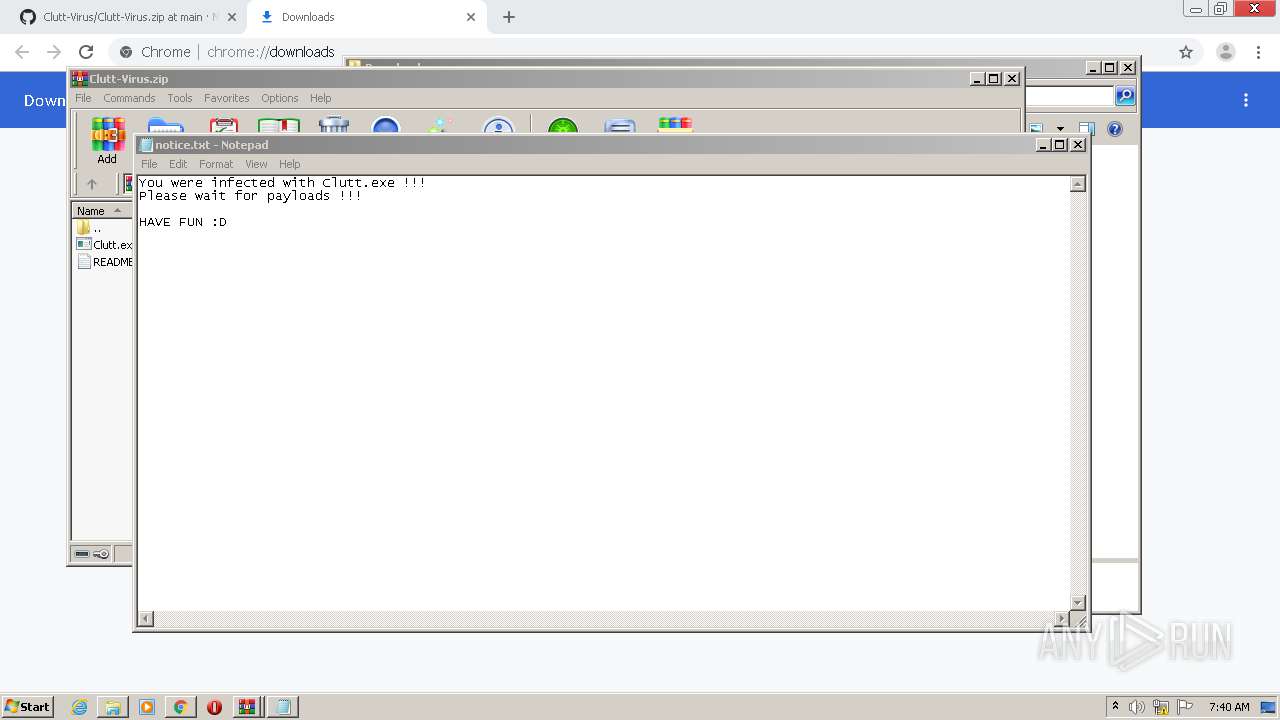
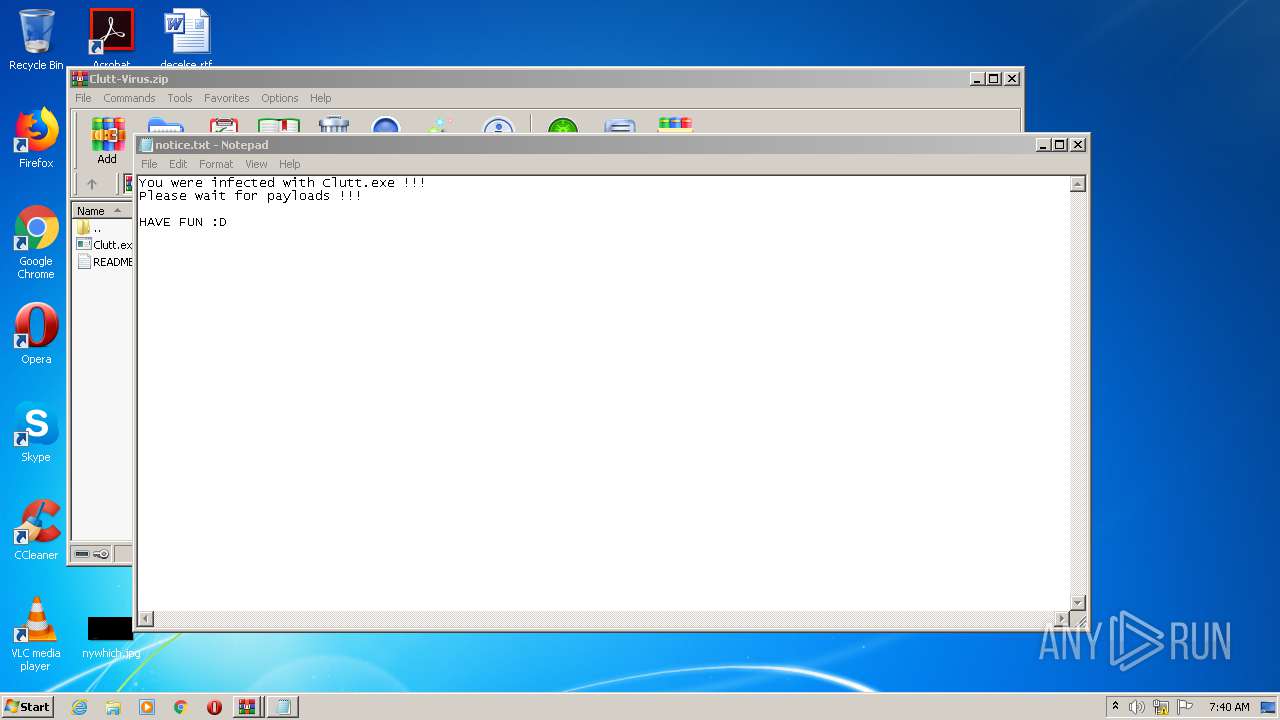
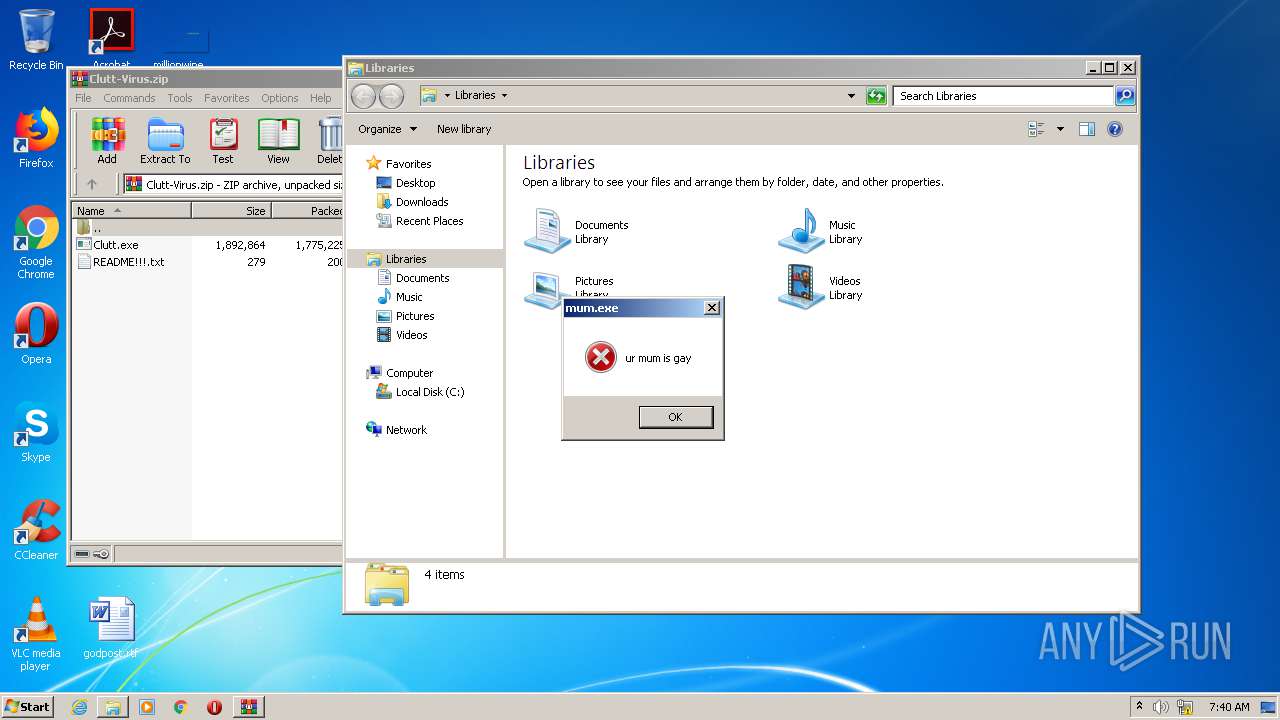
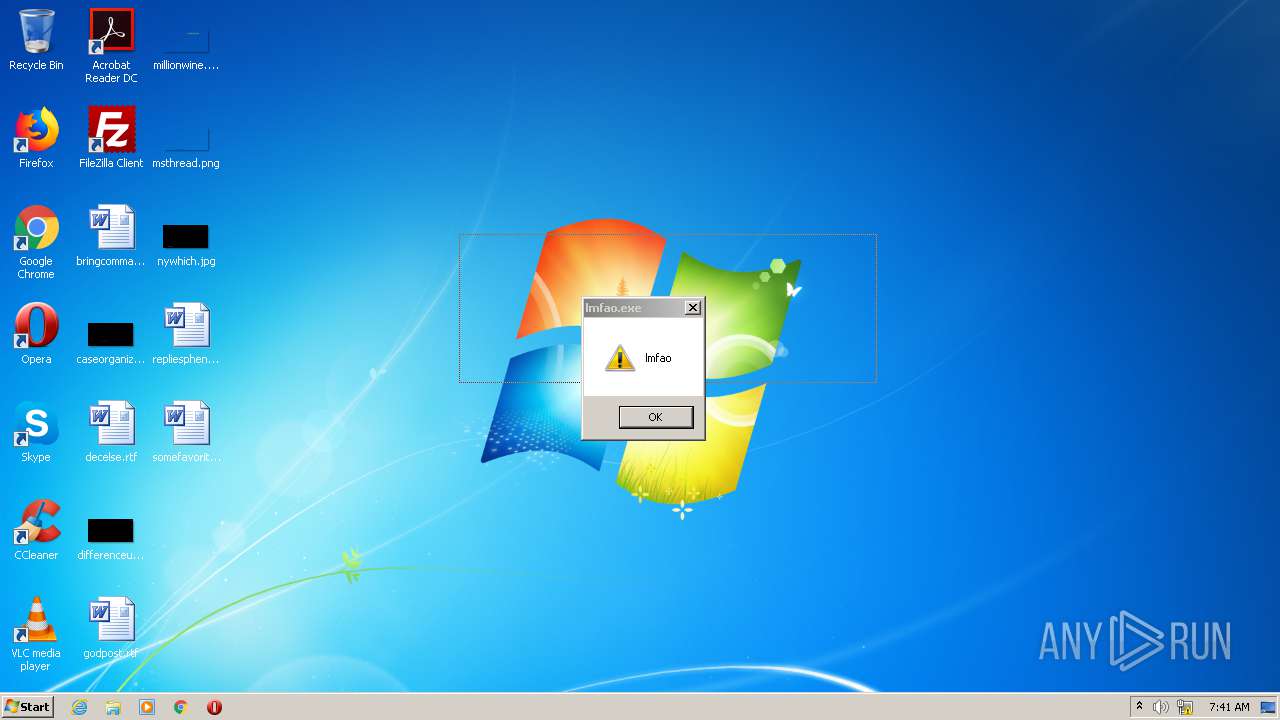
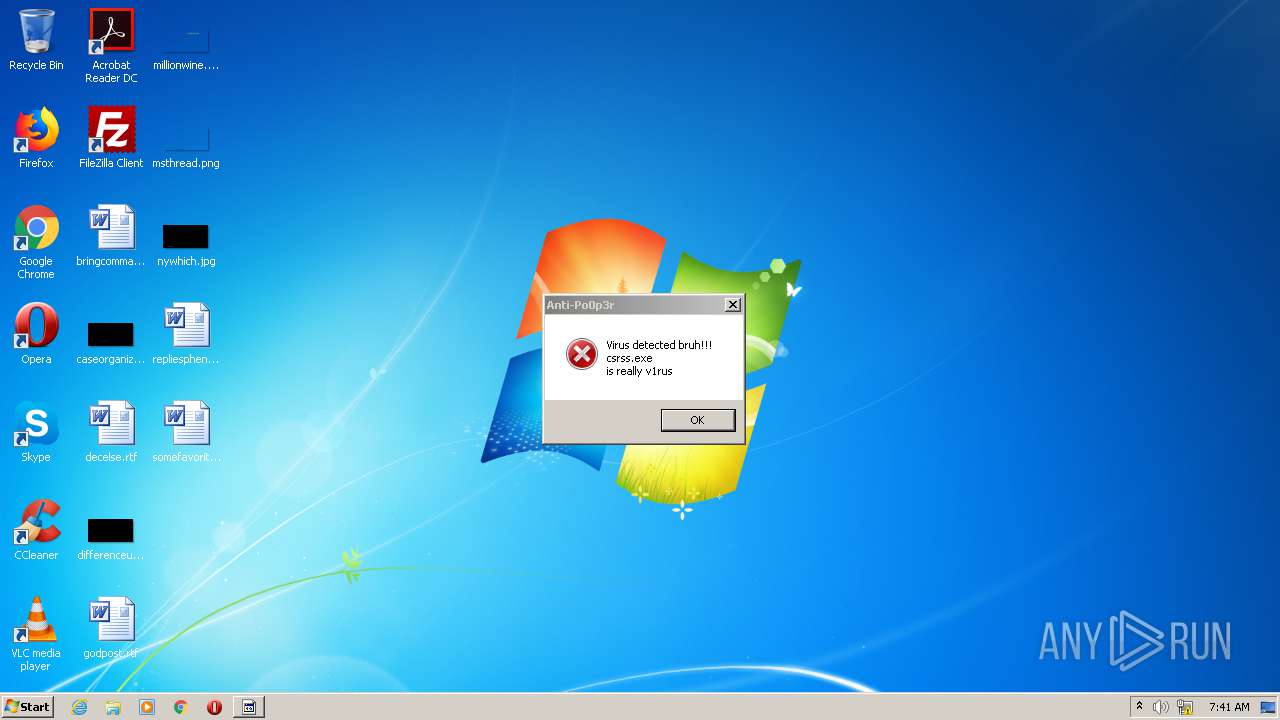
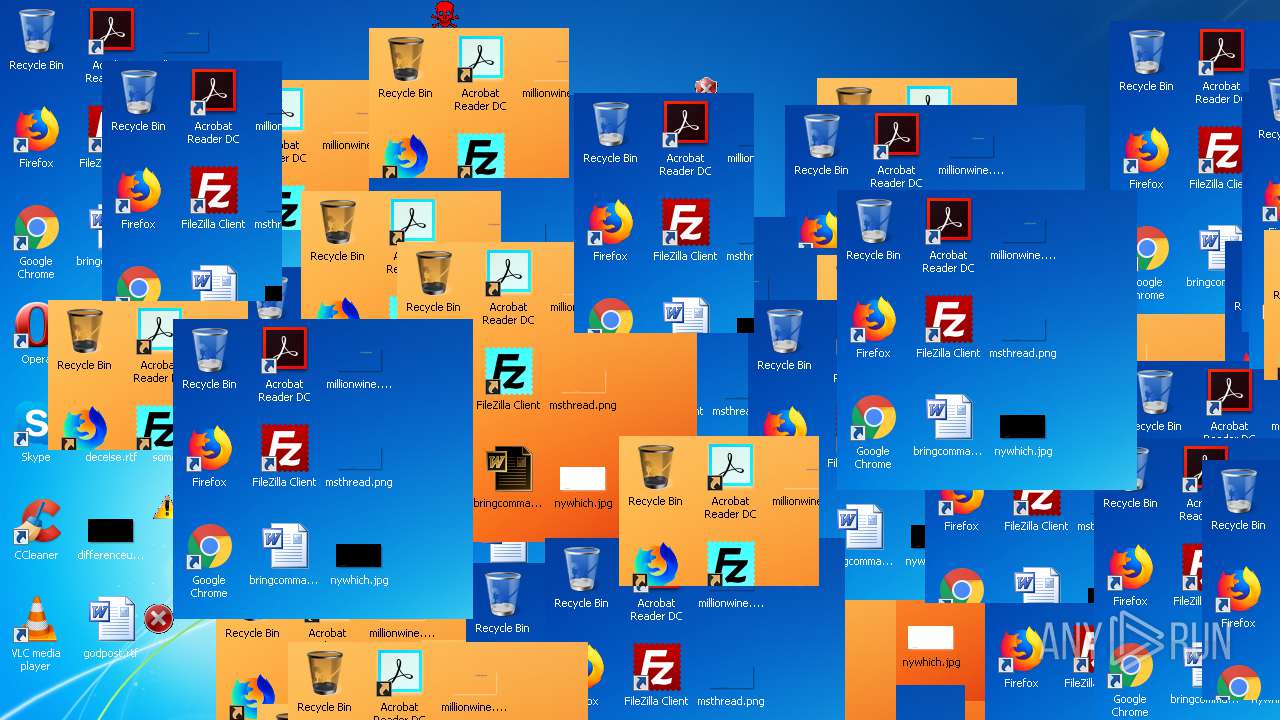
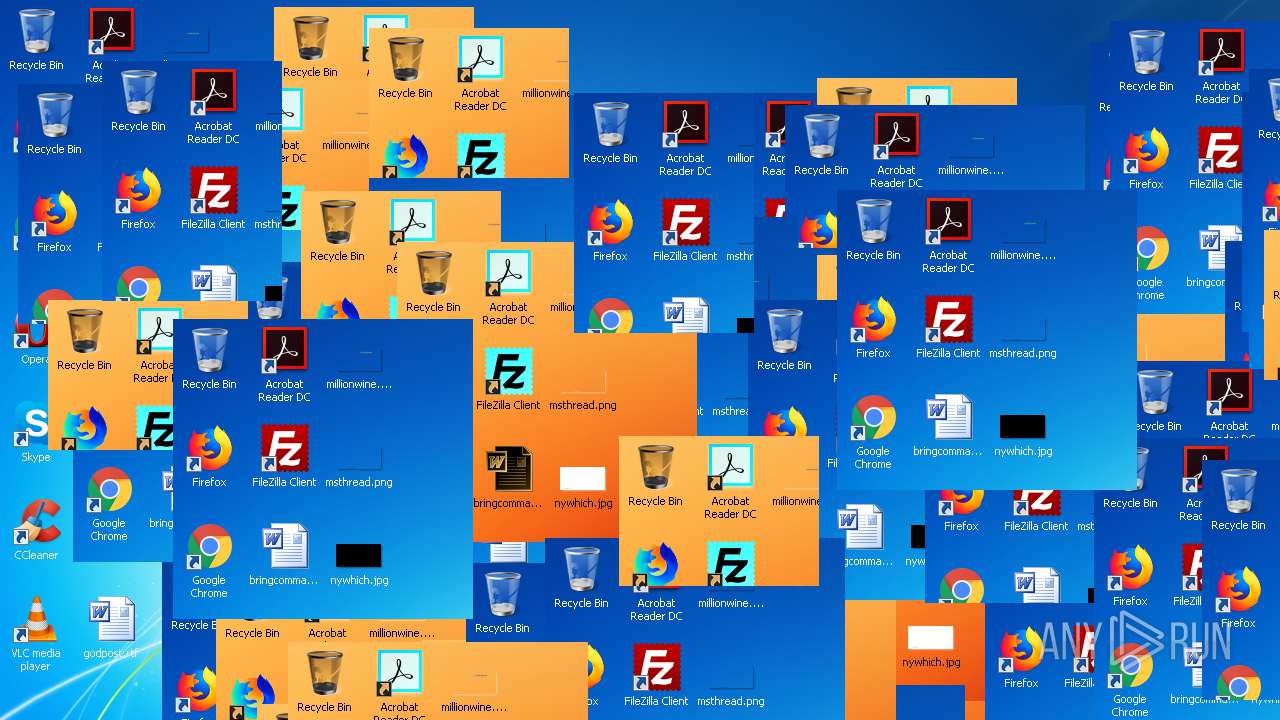
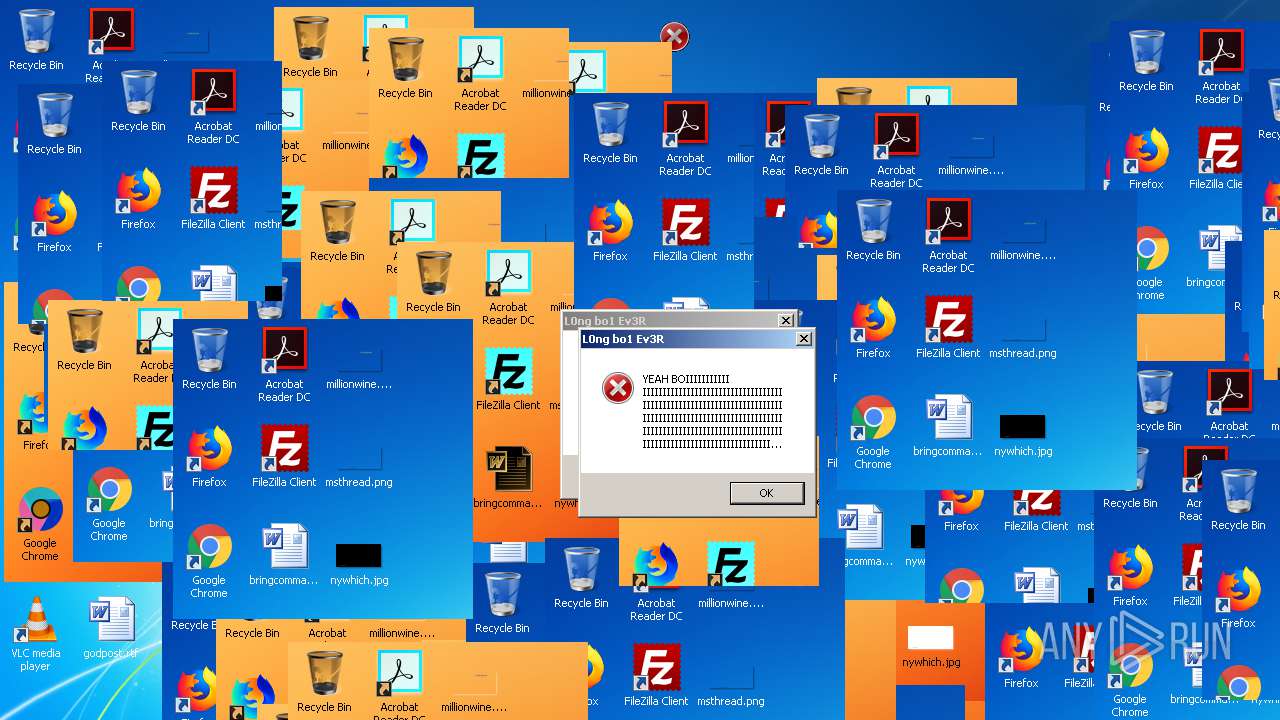
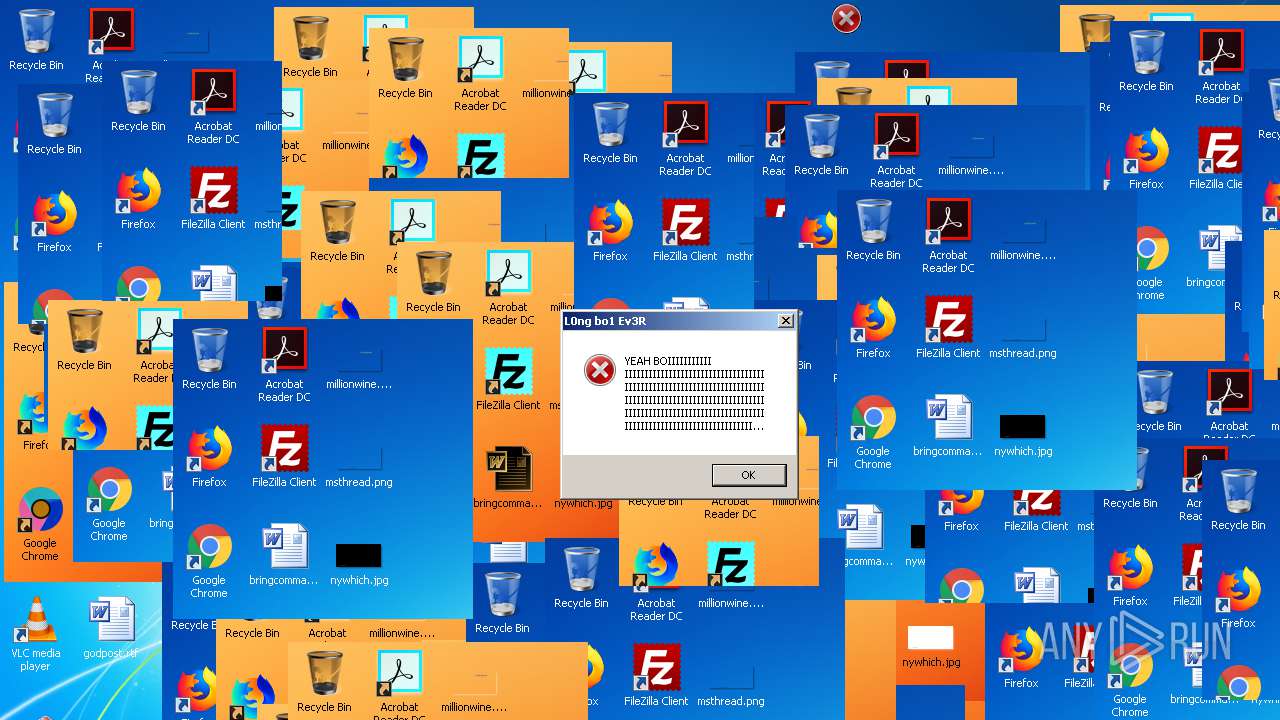
MALICIOUS
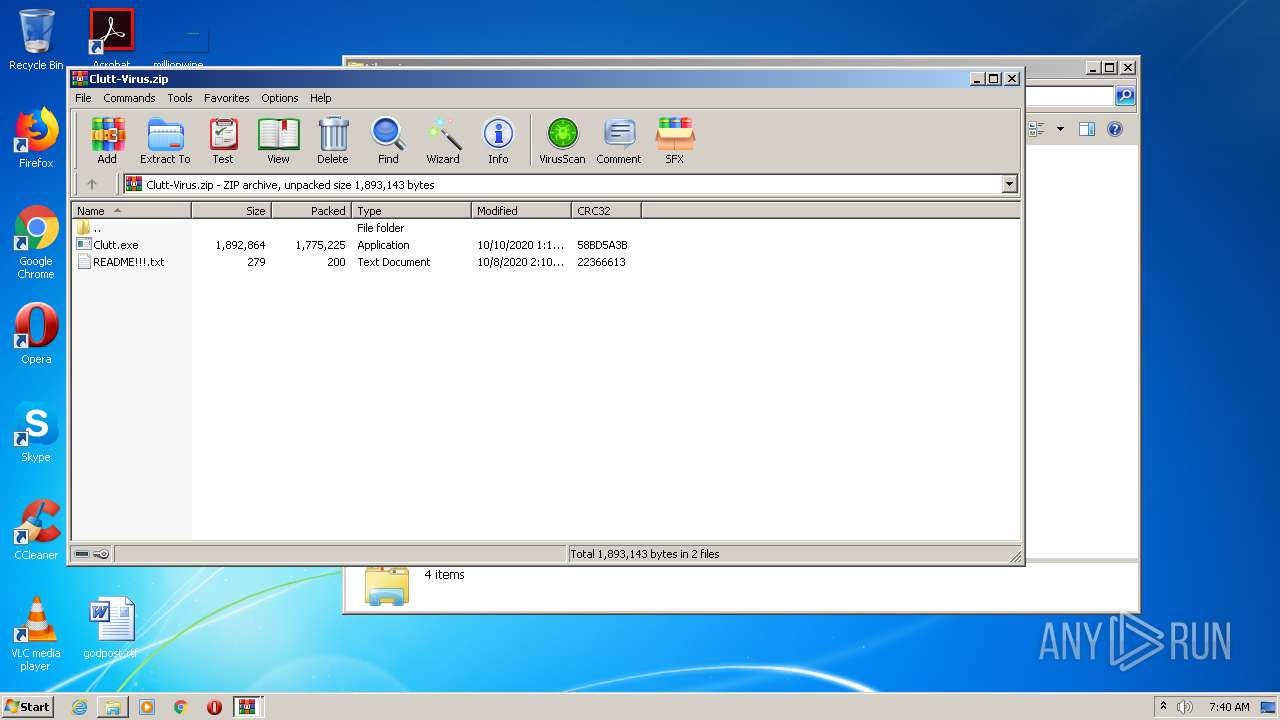
Application was dropped or rewritten from another process
- Clutt.exe (PID: 2828)
- Clutt.exe (PID: 2564)
Task Manager has been disabled (taskmgr)
- Clutt.exe (PID: 2564)
SUSPICIOUS
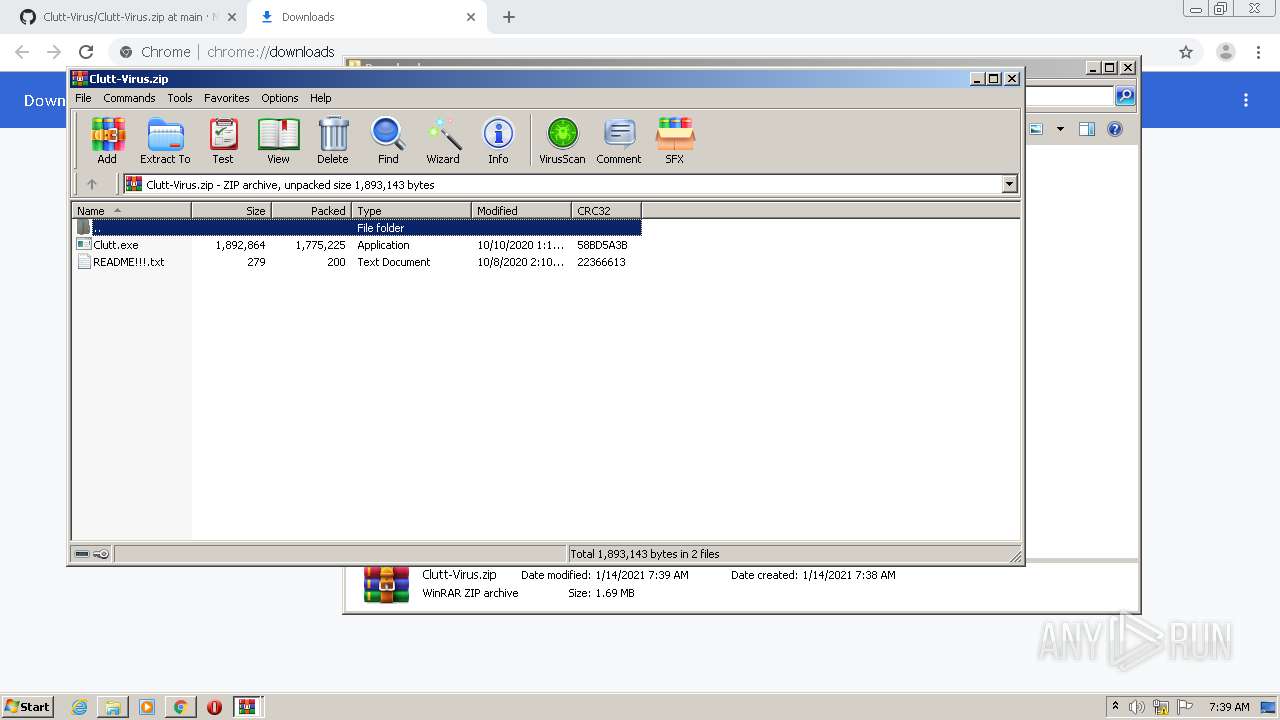
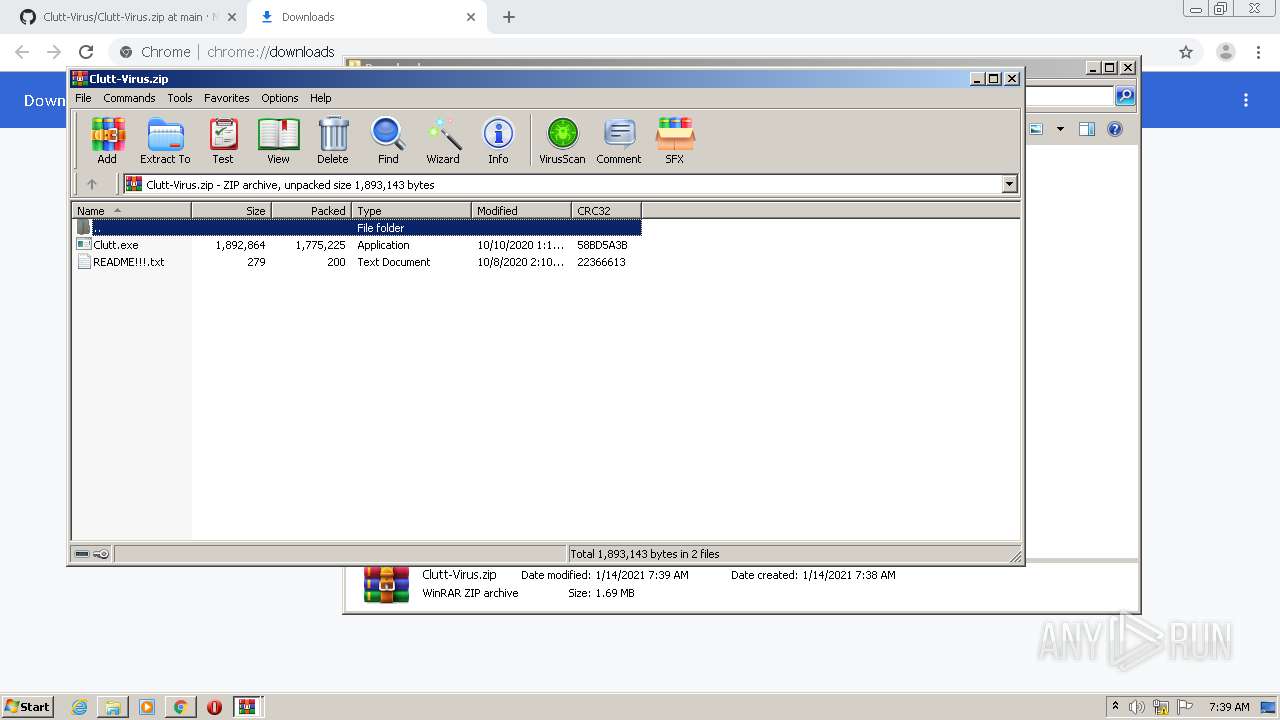
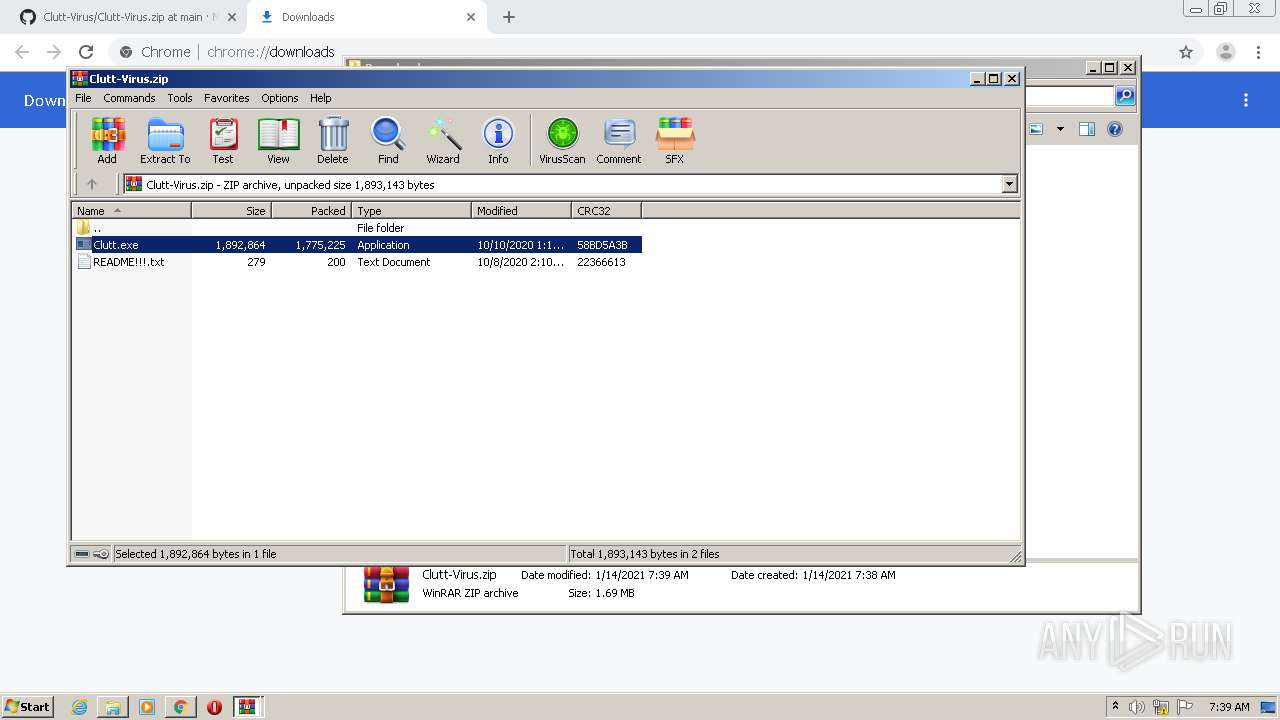
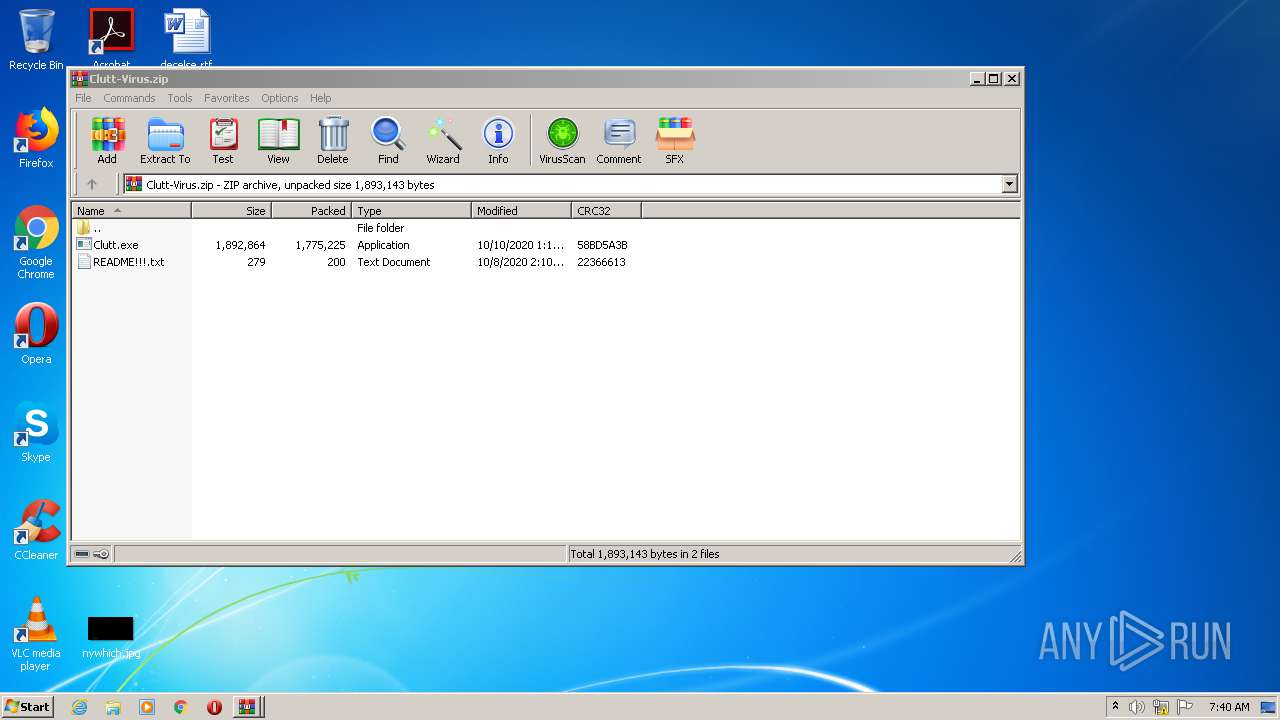
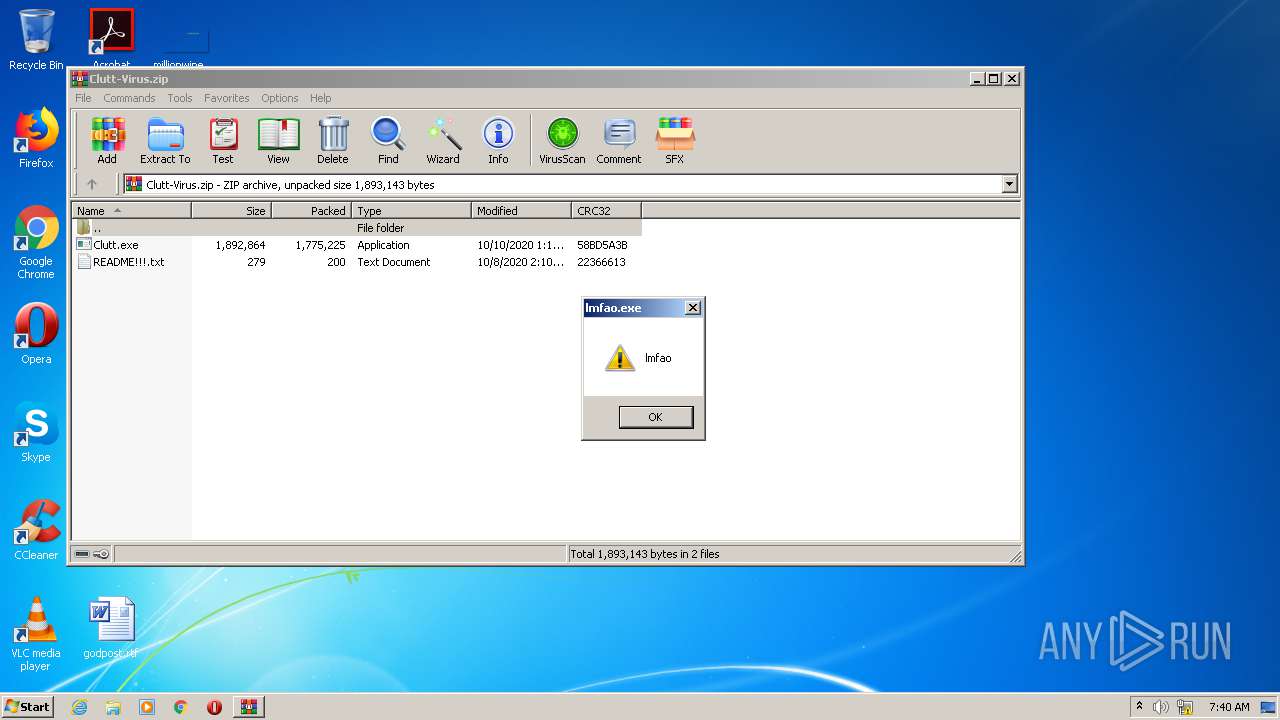
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2912)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2912)
Drops a file with too old compile date
- WinRAR.exe (PID: 2912)
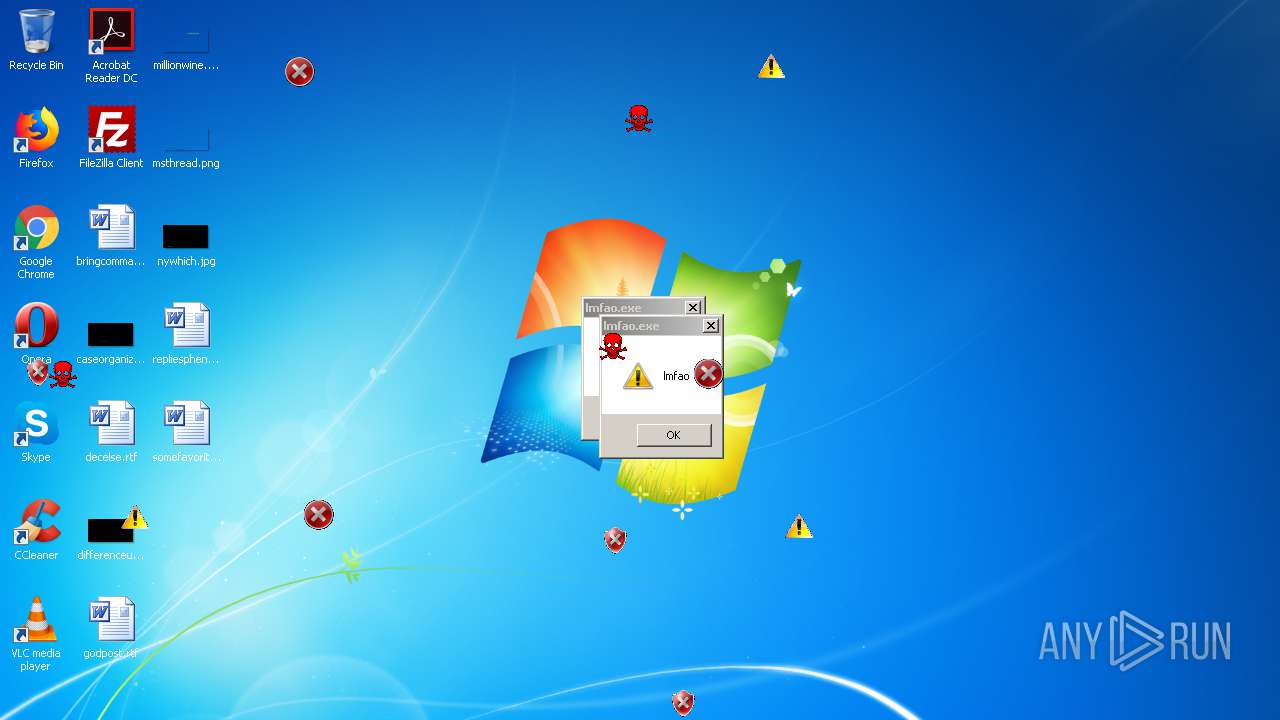
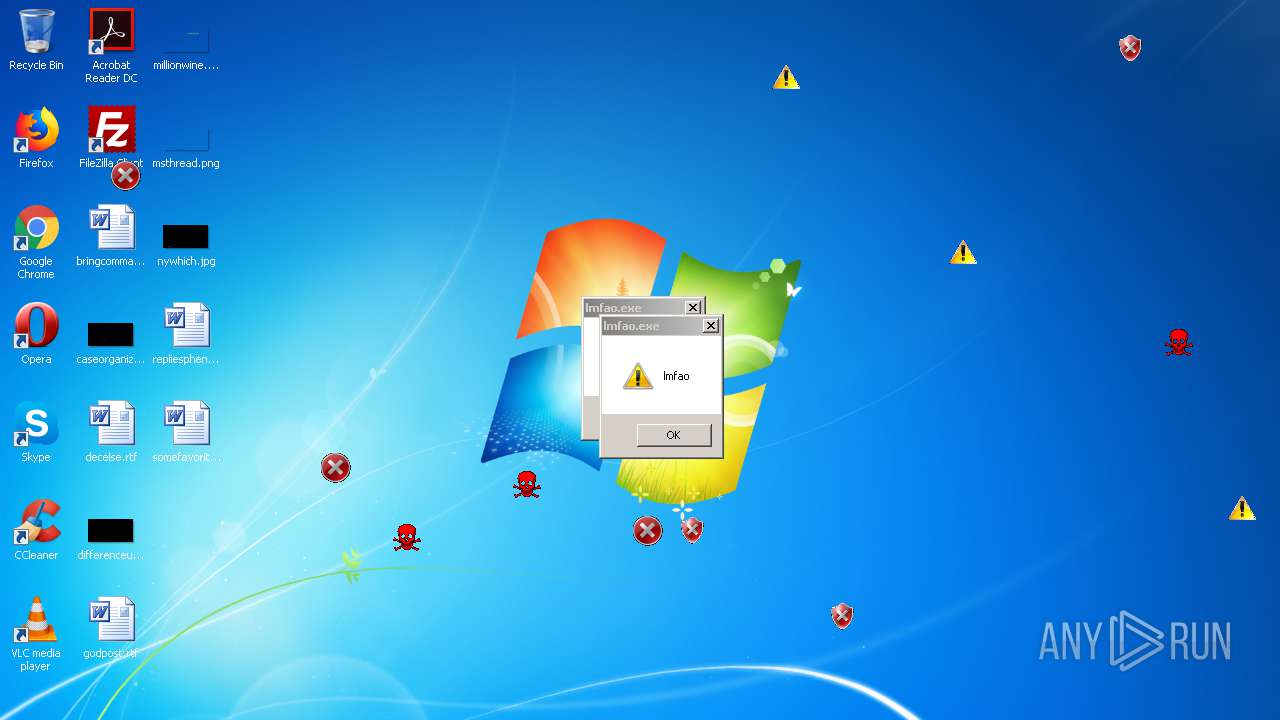
Starts CMD.EXE for commands execution
- Clutt.exe (PID: 2564)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 3260)
- cmd.exe (PID: 3348)
- cmd.exe (PID: 592)
Removes files from Windows directory
- Clutt.exe (PID: 2564)
INFO
Reads the hosts file
- chrome.exe (PID: 1464)
- chrome.exe (PID: 1788)
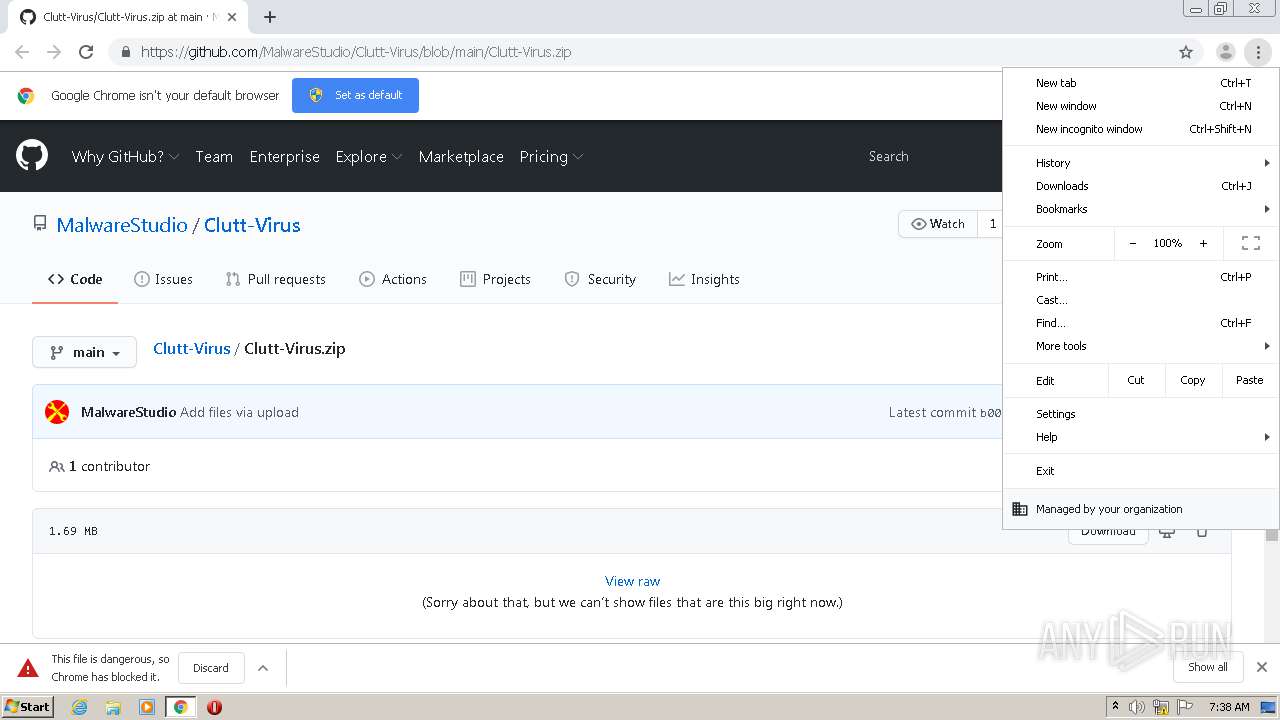
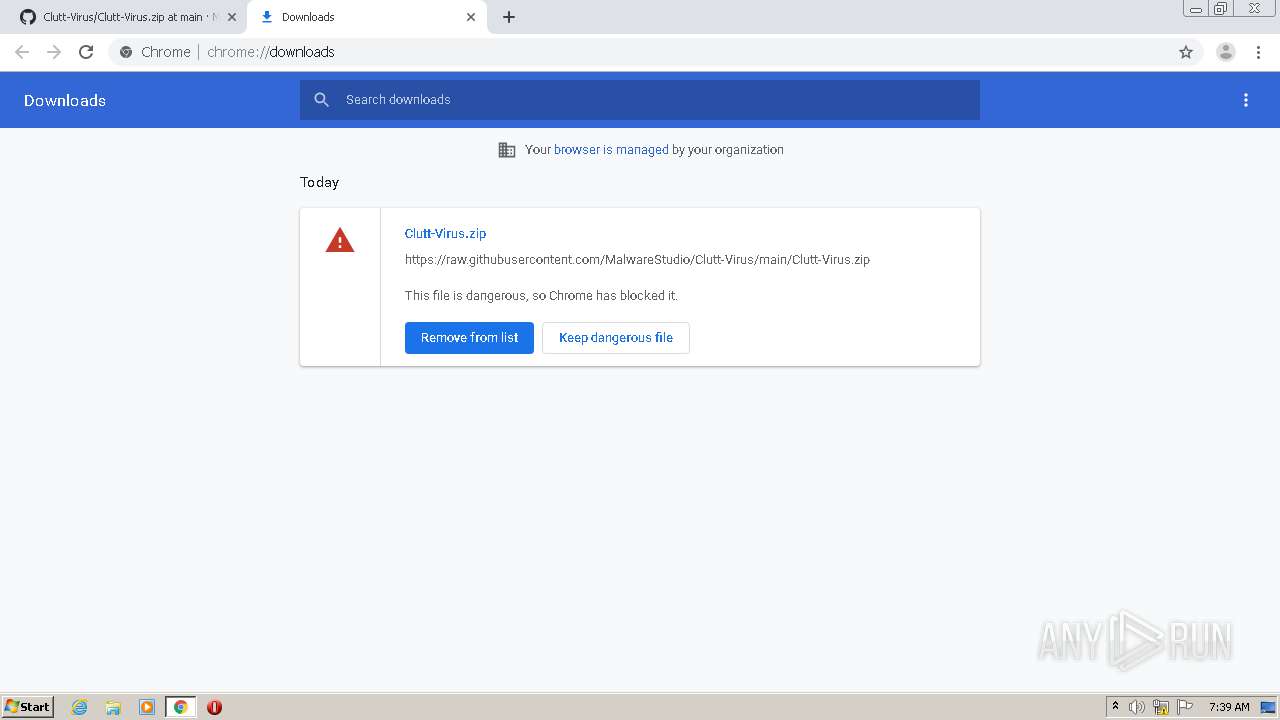
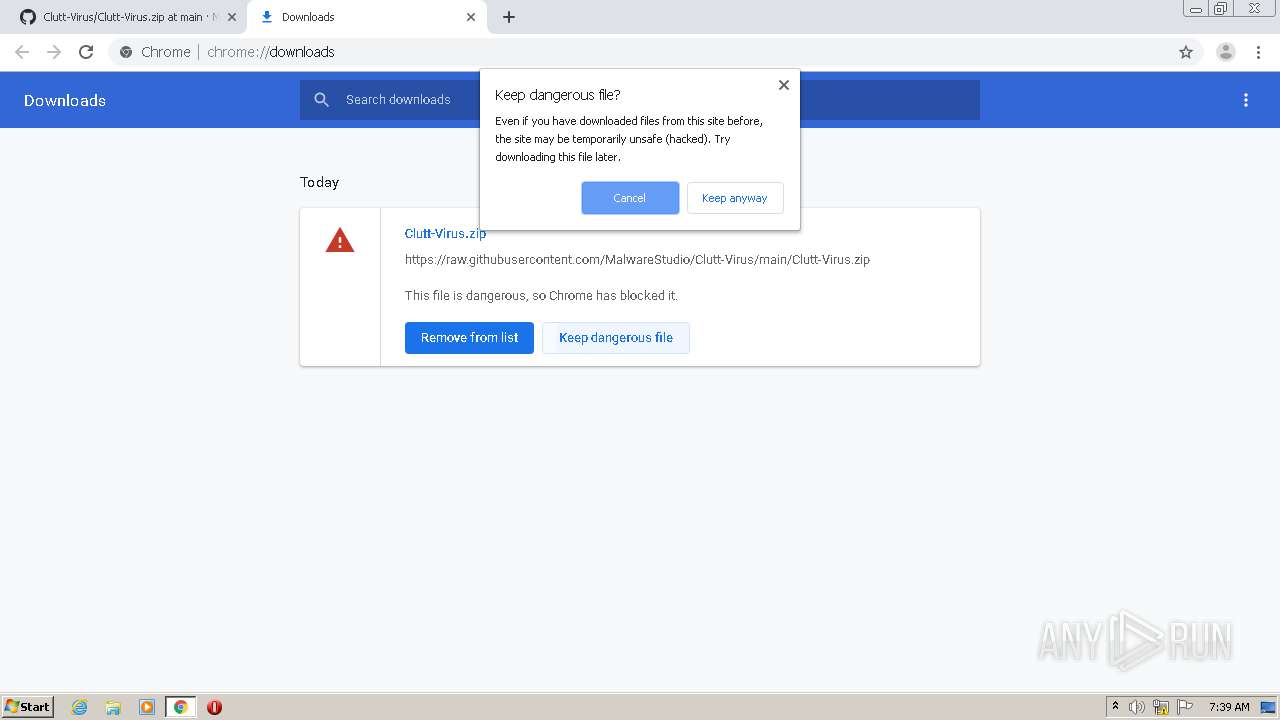
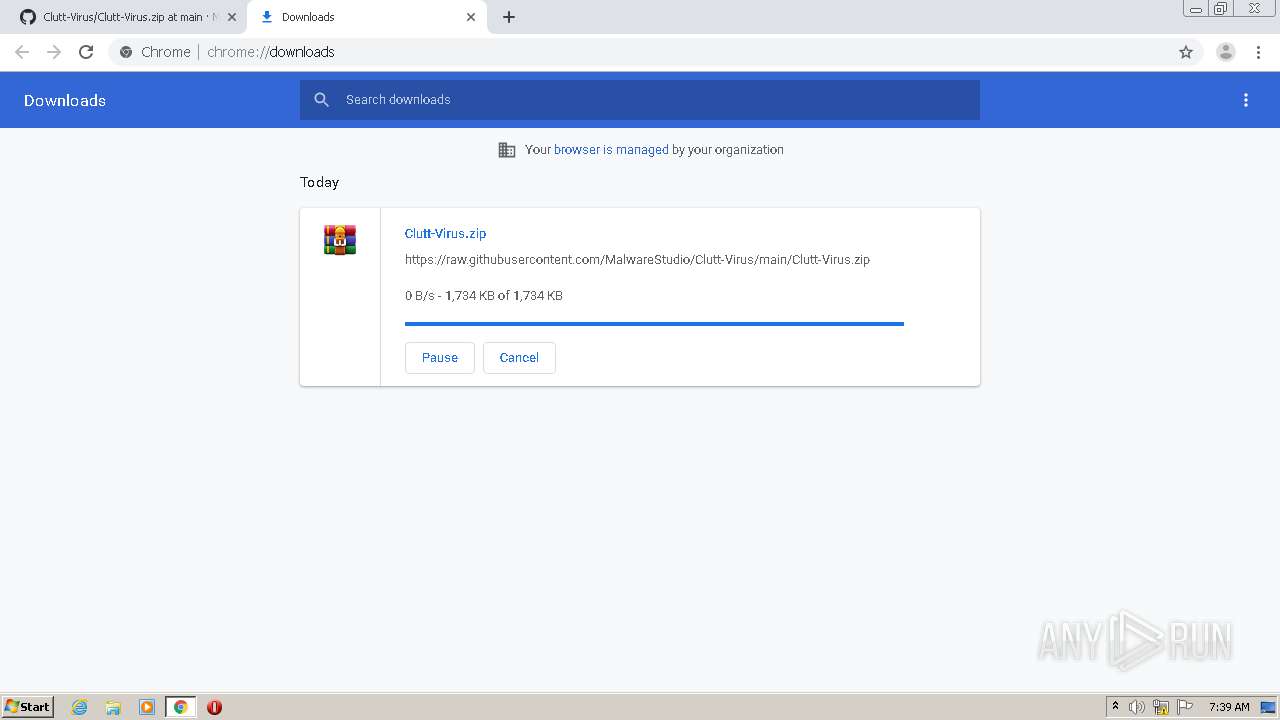
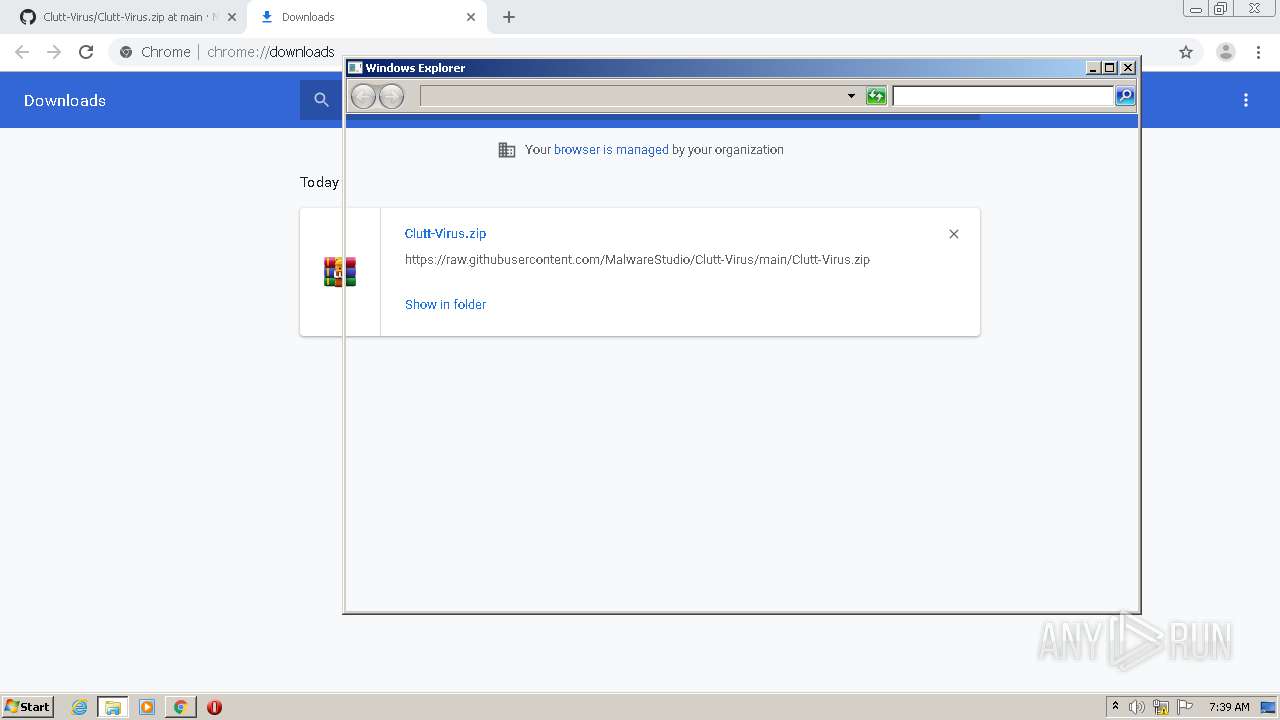
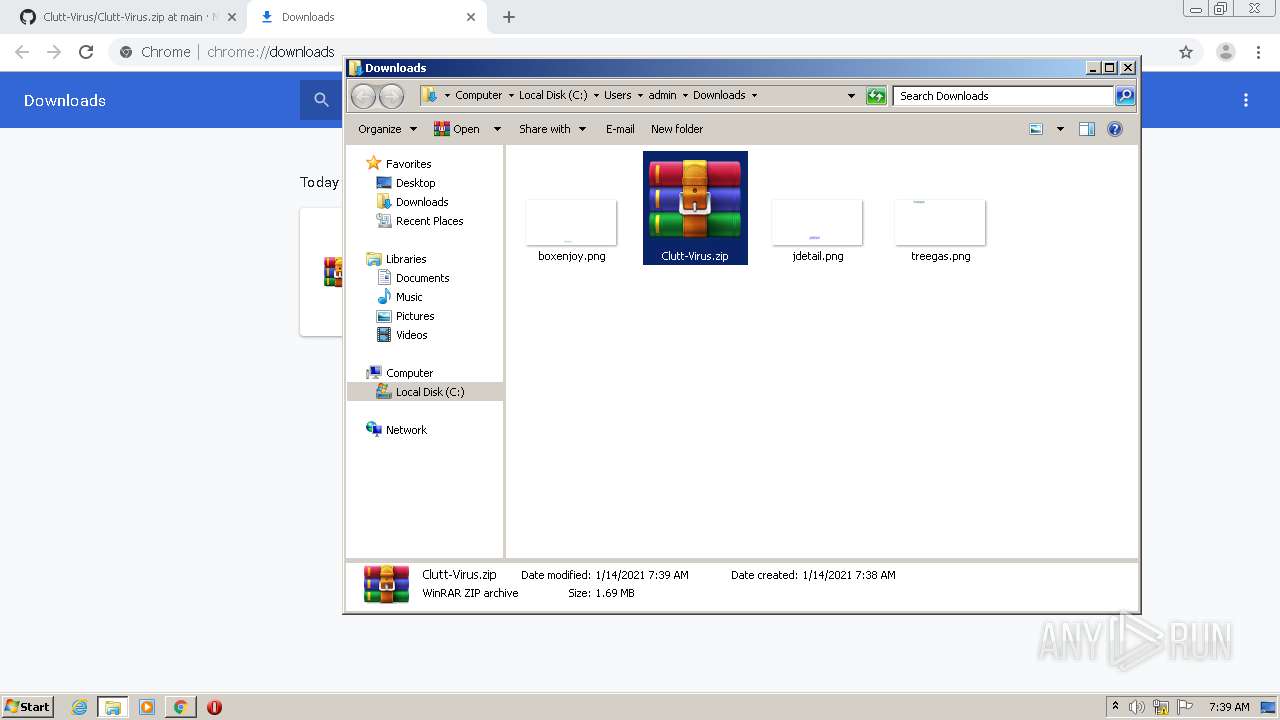
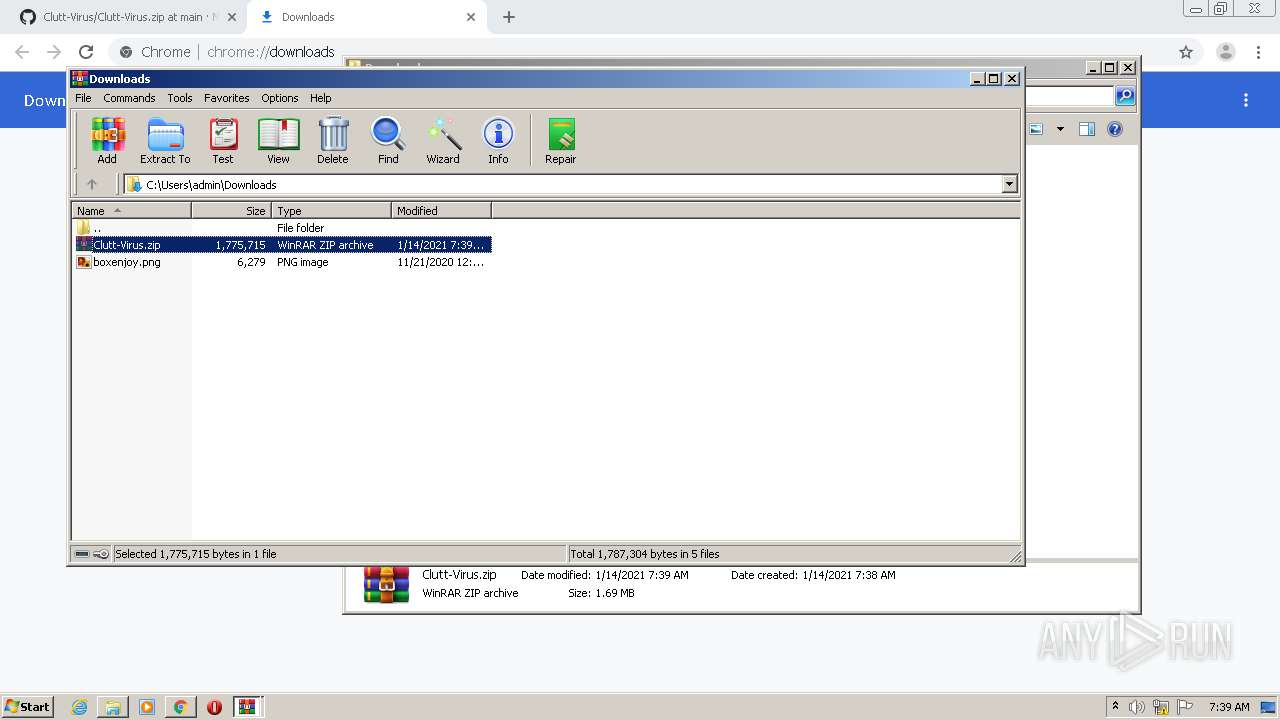
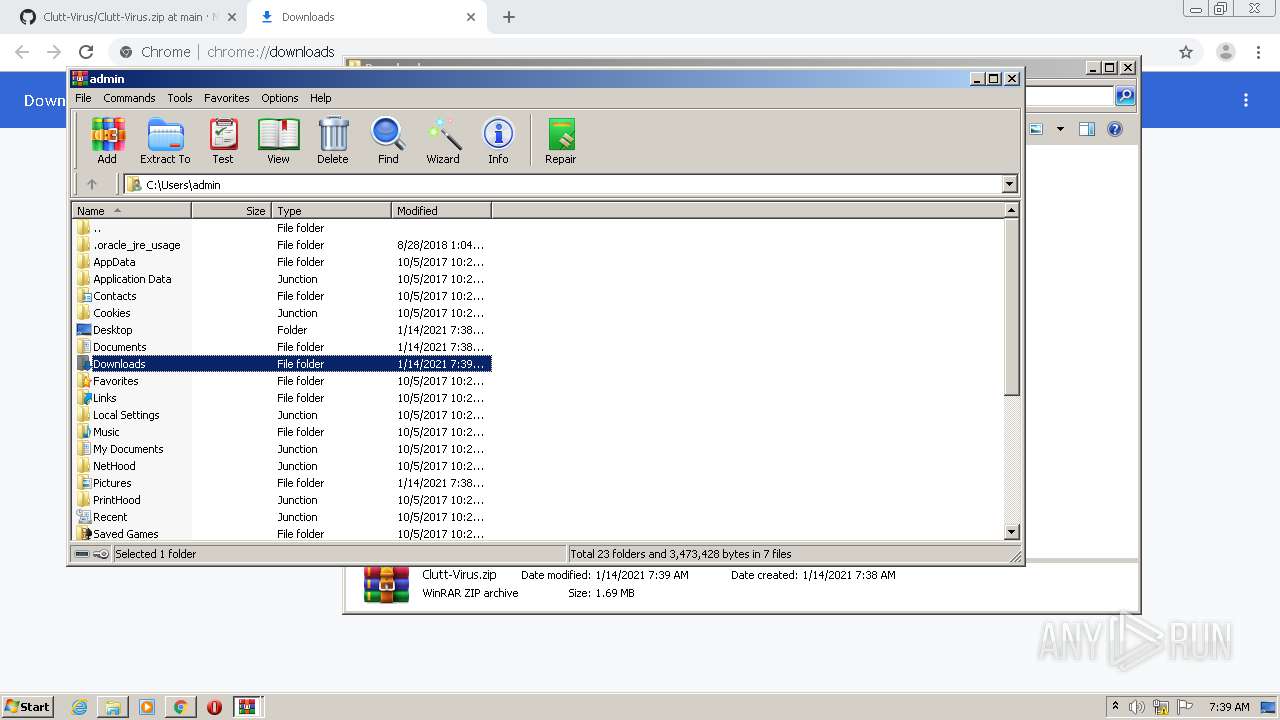
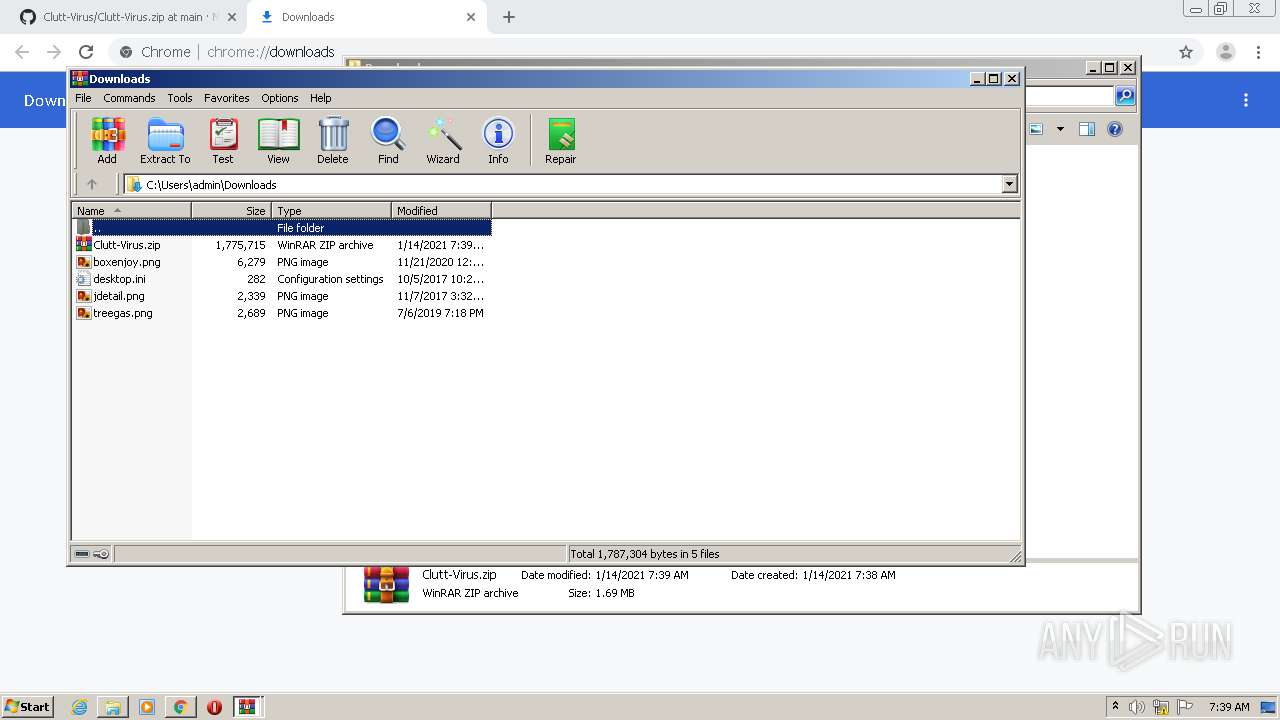
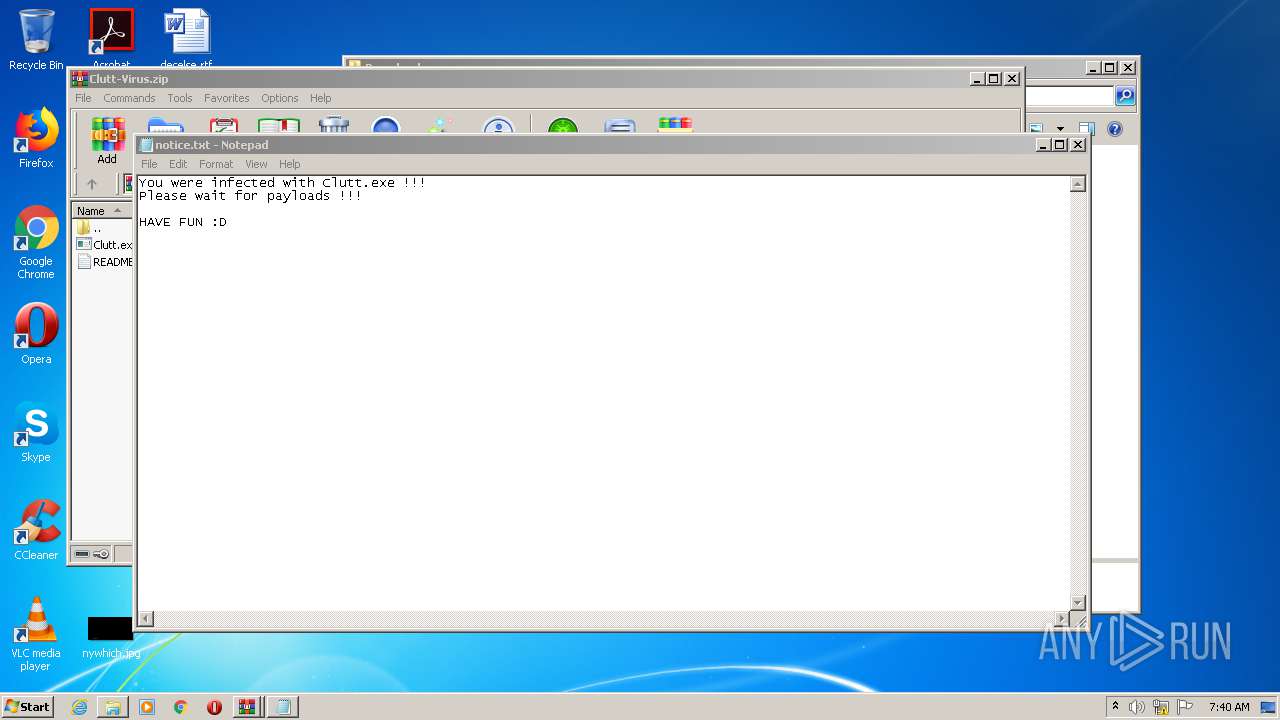
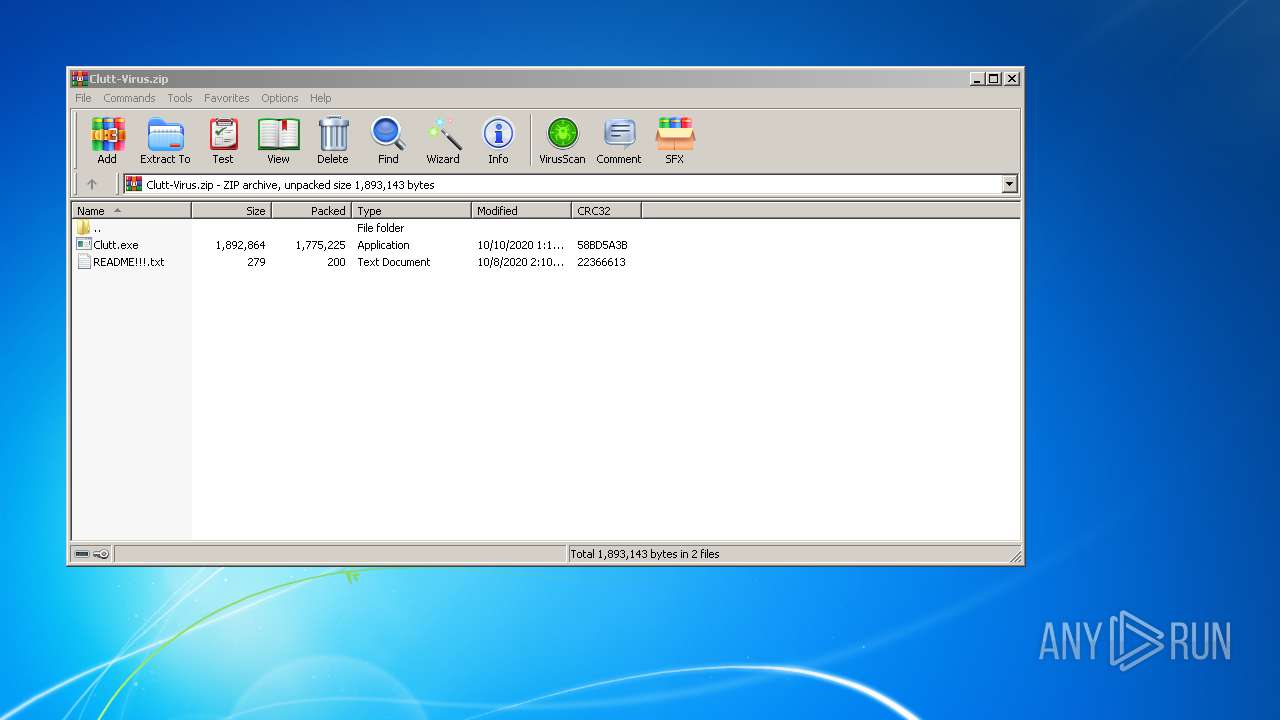
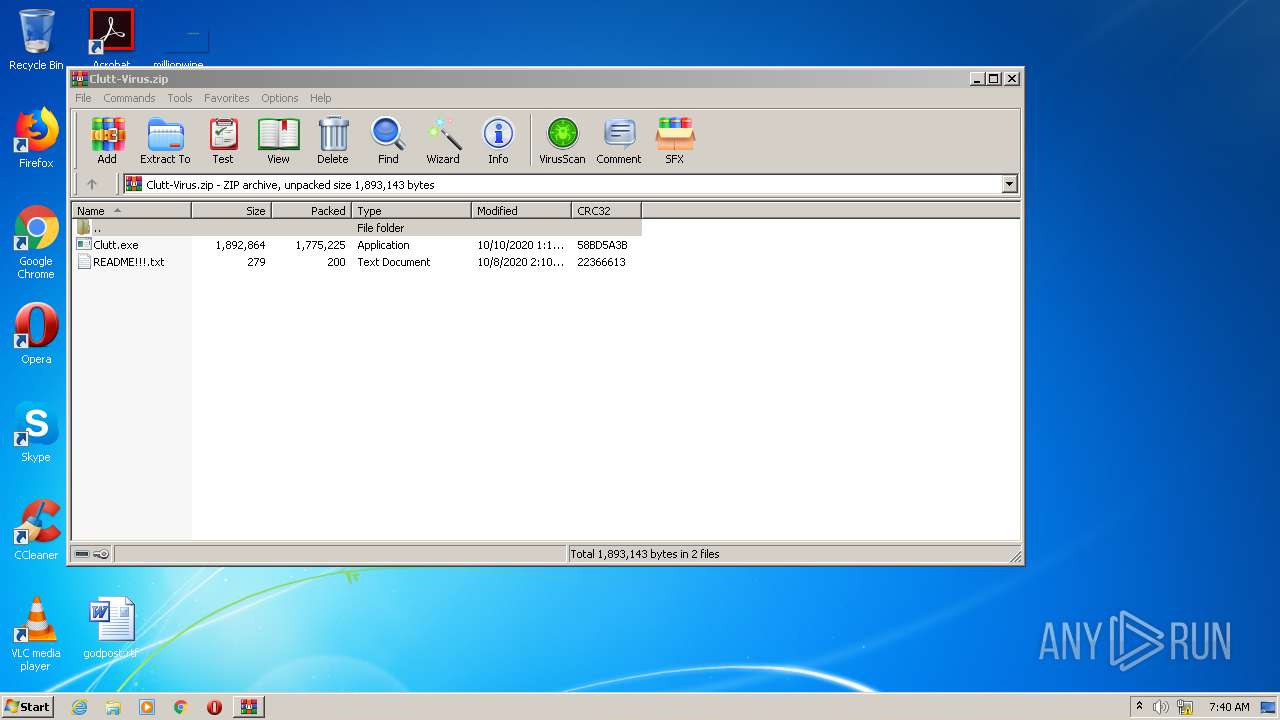
Manual execution by user
- WinRAR.exe (PID: 1624)
- WinRAR.exe (PID: 2912)
Application launched itself
- chrome.exe (PID: 1464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
28
Malicious processes
2
Suspicious processes
0
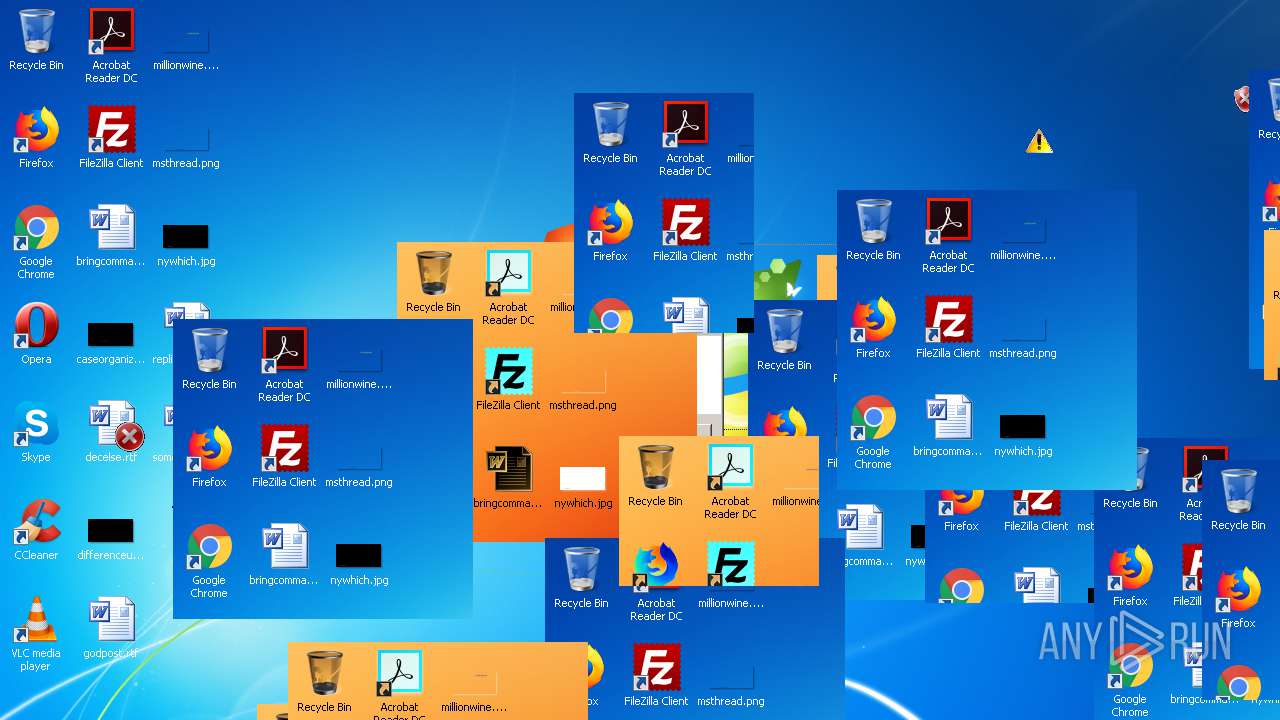
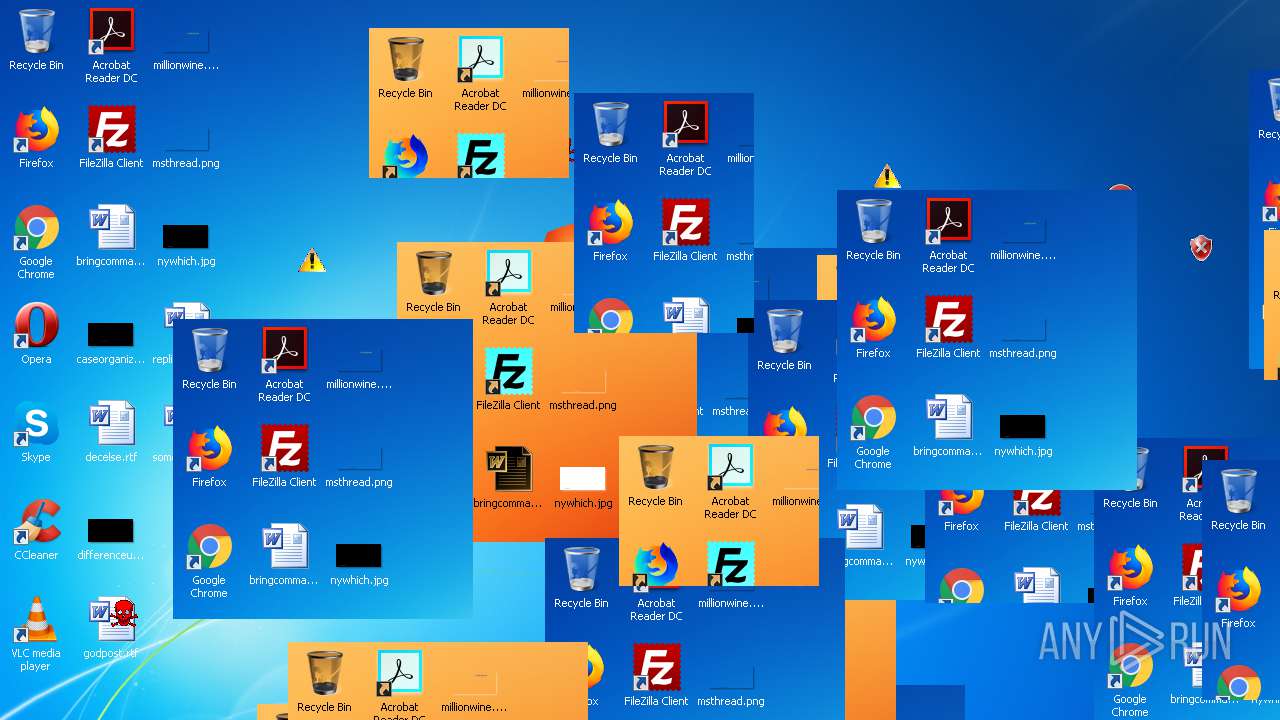
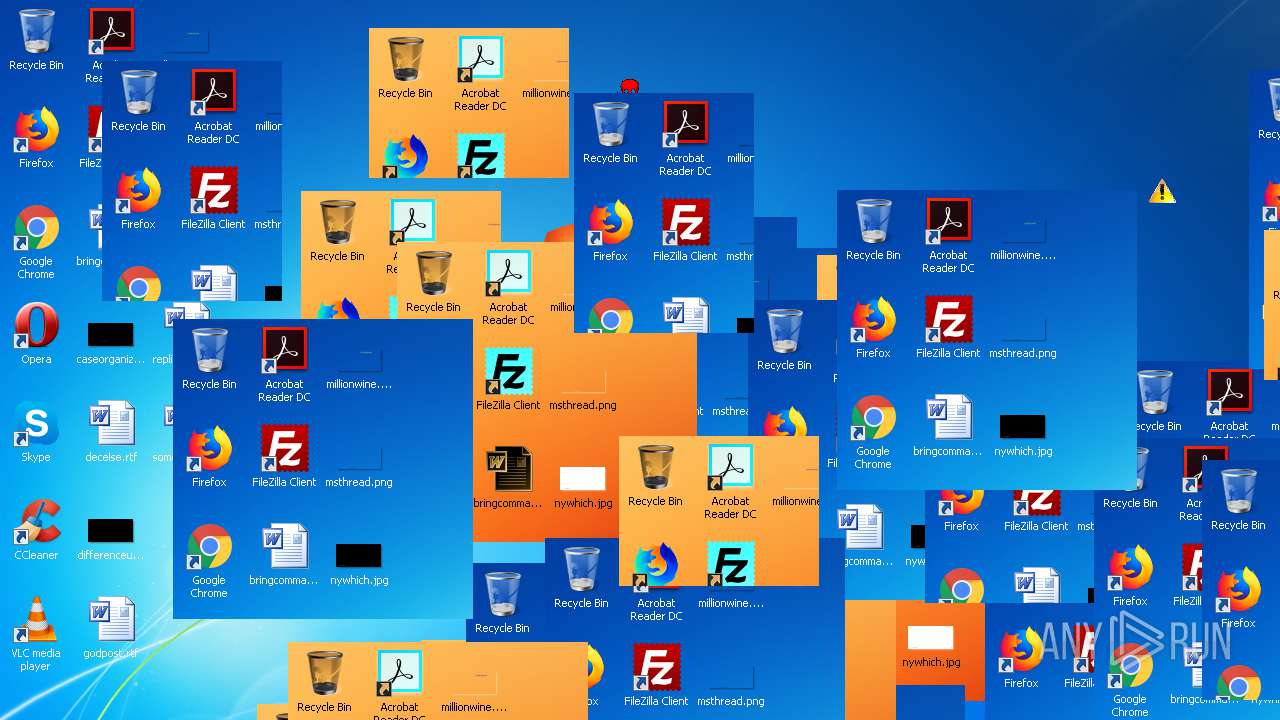
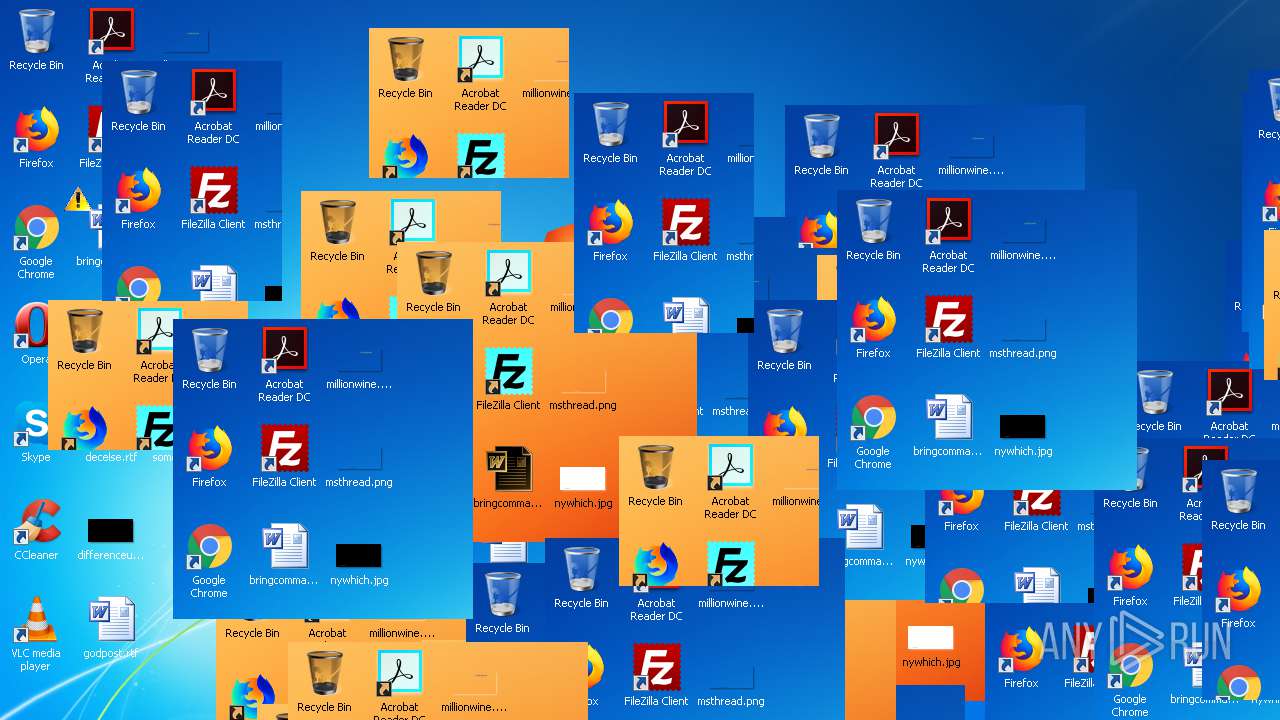
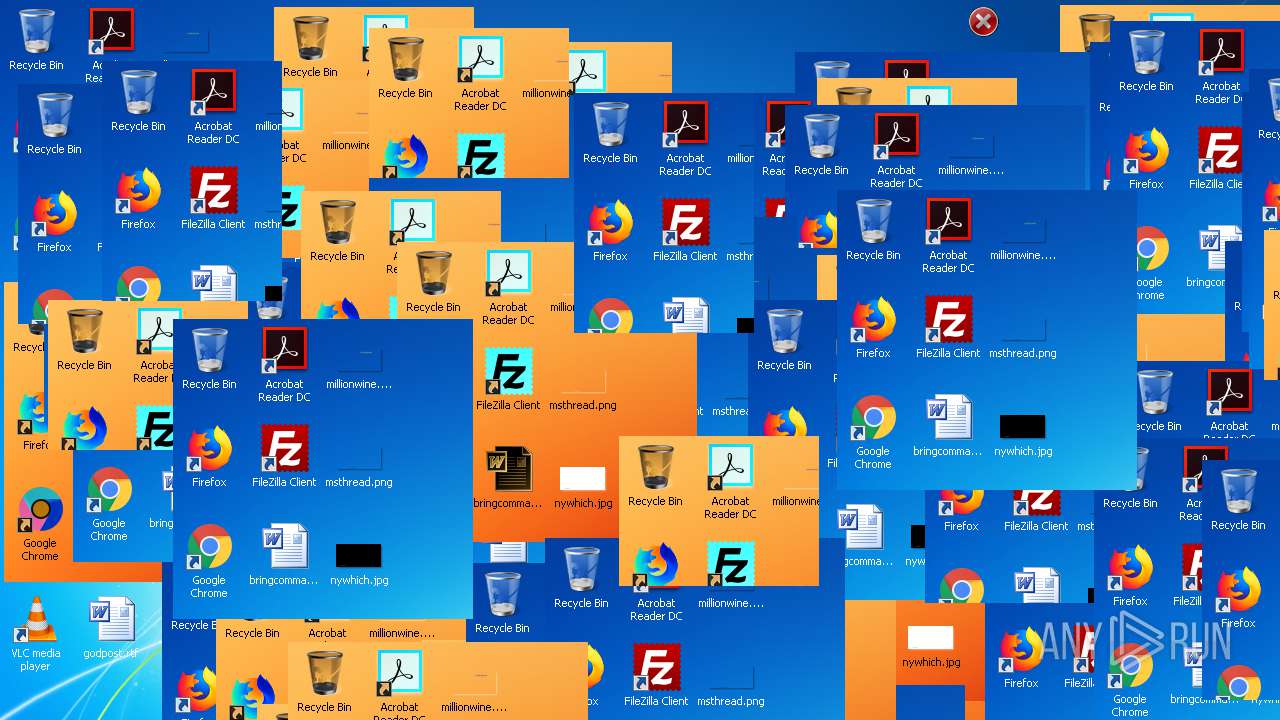
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1415009950199311578,6952705216518216422,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11413940875465116397 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 592 | "C:\Windows\System32\cmd.exe" /k takeown /f C:\Windows\System32\hal.dll && icacls C:\Windows\System32\hal.dll /grant %username%:F | C:\Windows\System32\cmd.exe | — | Clutt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 652 | takeown /f C:\Windows\System32\hal.dll | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1415009950199311578,6952705216518216422,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17525597953253480790 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1236 | takeown /f C:\Windows\System32\bcdboot.exe | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1336 | icacls C:\Windows\System32\hal.dll /grant admin:F | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://github.com/MalwareStudio/Clutt-Virus/blob/main/Clutt-Virus.zip" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1560 | takeown /f C:\Windows\System32\drivers\disk.sys | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1624 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Clutt-Virus.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1415009950199311578,6952705216518216422,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10000434914032796210 --mojo-platform-channel-handle=1560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 041
Read events
1 910
Write events
128
Delete events
3
Modification events
| (PID) Process: | (1464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2180) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1464-13255083518229250 |
Value: 259 | |||
| (PID) Process: | (1464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1464) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1
Suspicious files
27
Text files
97
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FFFF4FF-5B8.pma | — | |
MD5:— | SHA256:— | |||
| 1464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF14496b.TMP | — | |
MD5:— | SHA256:— | |||
| 1464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1448cf.TMP | text | |
MD5:— | SHA256:— | |||
| 1464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1448bf.TMP | text | |
MD5:— | SHA256:— | |||
| 1464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF144c1b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
29
DNS requests
18
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1788 | chrome.exe | 172.217.22.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1788 | chrome.exe | 172.217.18.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
1788 | chrome.exe | 54.146.190.157:443 | collector.githubapp.com | Amazon.com, Inc. | US | unknown |
1788 | chrome.exe | 140.82.121.6:443 | api.github.com | — | US | suspicious |
1788 | chrome.exe | 151.101.0.133:443 | avatars1.githubusercontent.com | Fastly | US | malicious |
1788 | chrome.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
1788 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1788 | chrome.exe | 172.217.16.206:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
1788 | chrome.exe | 172.217.22.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1788 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars1.githubusercontent.com |
| whitelisted |
avatars0.githubusercontent.com |
| whitelisted |
avatars2.githubusercontent.com |
| whitelisted |
avatars3.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |