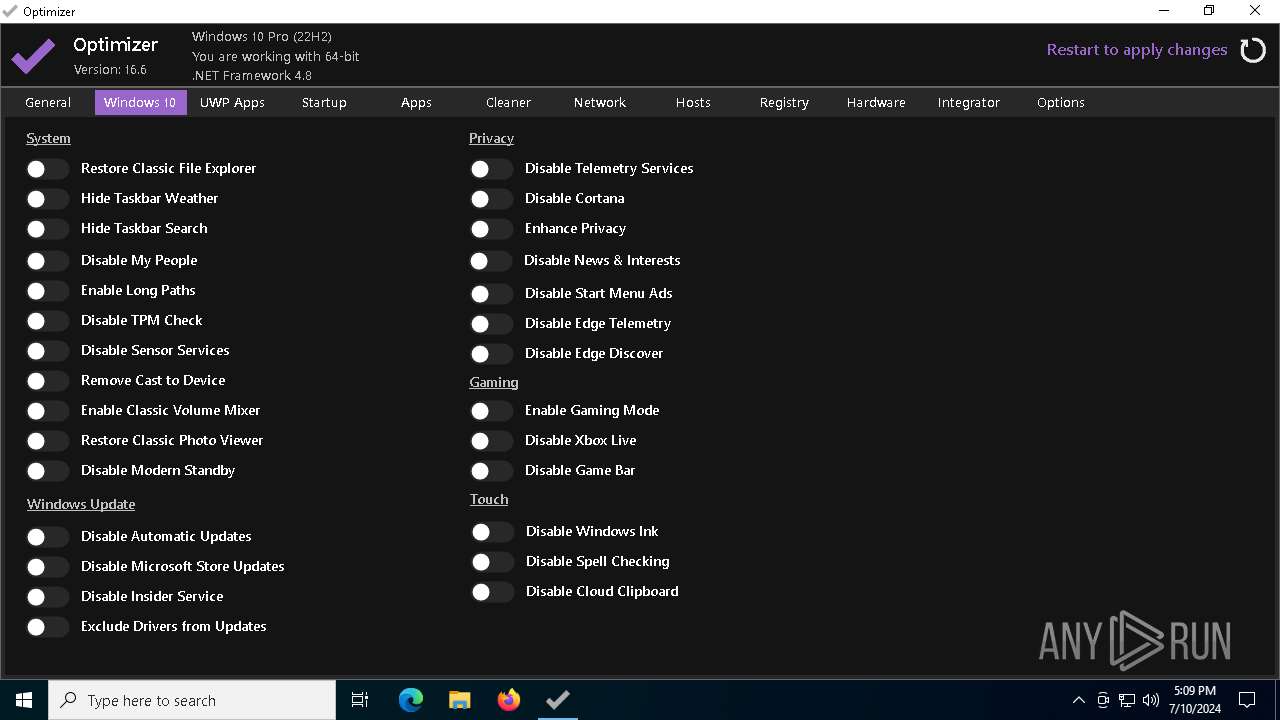
| File name: | Optimizer-16.6.exe |
| Full analysis: | https://app.any.run/tasks/5ef2574c-2e61-4282-90a1-f57561e608f4 |
| Verdict: | Malicious activity |
| Analysis date: | July 10, 2024, 17:08:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | D998782CBFCFFE2B57945E303F02F176 |
| SHA1: | BBA0FEFA7823B0951F33B79708B23A47AB4F2315 |
| SHA256: | 8B29C9349E7A814E30CCE1CFB788F5A21740C798268B0A45AB805195FAAD9105 |
| SSDEEP: | 49152:AVAED/Ya3LmftXaHhEC8yNMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMA:KwINMMMMMMMMMMMMMMMMMMMMMMMMMMMu |
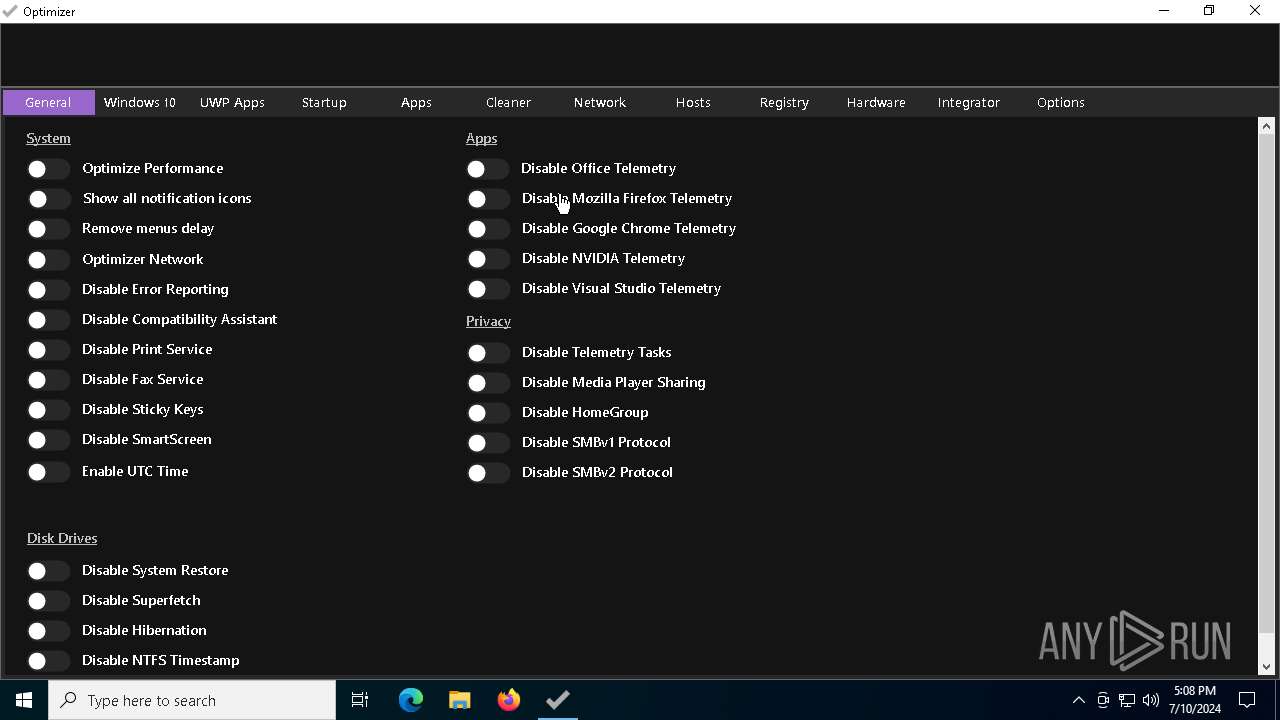
MALICIOUS
Drops the executable file immediately after the start
- Optimizer-16.6.exe (PID: 1228)
Changes appearance of the Explorer extensions
- Optimizer-16.6.exe (PID: 1824)
SUSPICIOUS
Application launched itself
- Optimizer-16.6.exe (PID: 1228)
Reads security settings of Internet Explorer
- Optimizer-16.6.exe (PID: 1228)
- Optimizer-16.6.exe (PID: 1824)
Reads the date of Windows installation
- Optimizer-16.6.exe (PID: 1228)
- Optimizer-16.6.exe (PID: 1824)
Starts CMD.EXE for commands execution
- Optimizer-16.6.exe (PID: 1824)
Starts SC.EXE for service management
- cmd.exe (PID: 6204)
Checks Windows Trust Settings
- Optimizer-16.6.exe (PID: 1824)
Creates or modifies Windows services
- Optimizer-16.6.exe (PID: 1824)
INFO
Reads the machine GUID from the registry
- Optimizer-16.6.exe (PID: 1228)
- Optimizer-16.6.exe (PID: 1824)
Reads the computer name
- Optimizer-16.6.exe (PID: 1228)
- Optimizer-16.6.exe (PID: 1824)
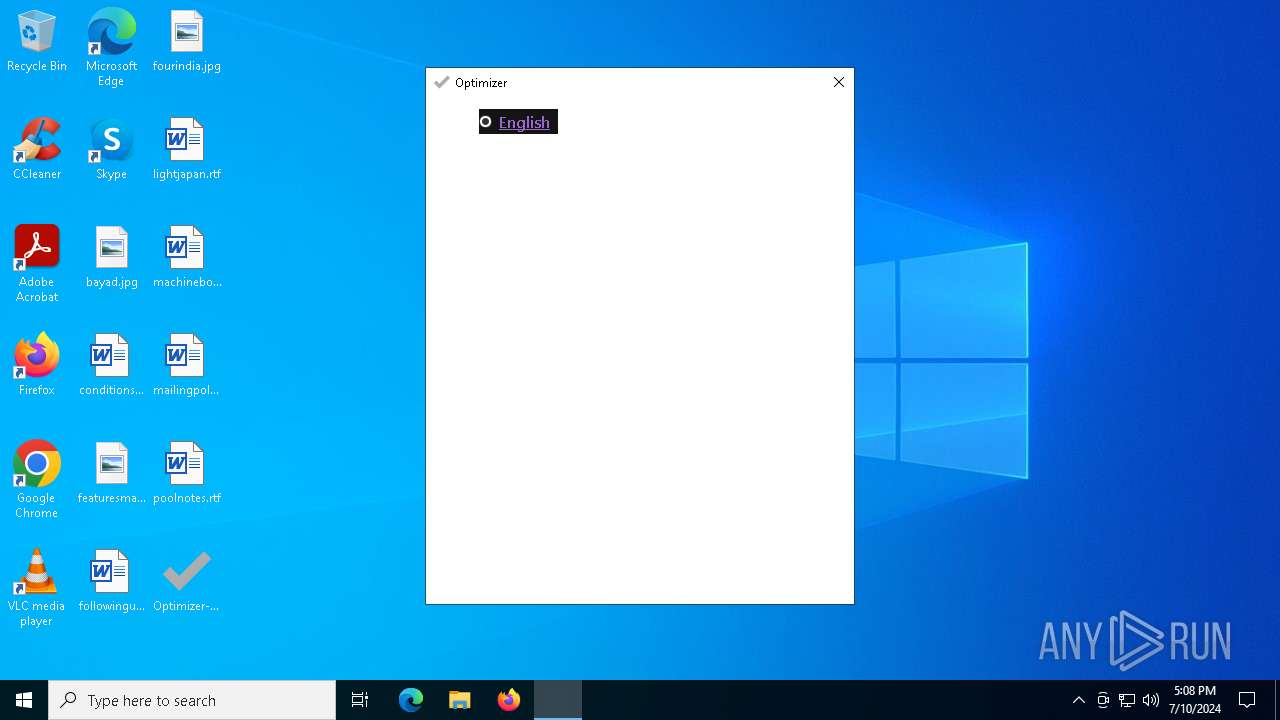
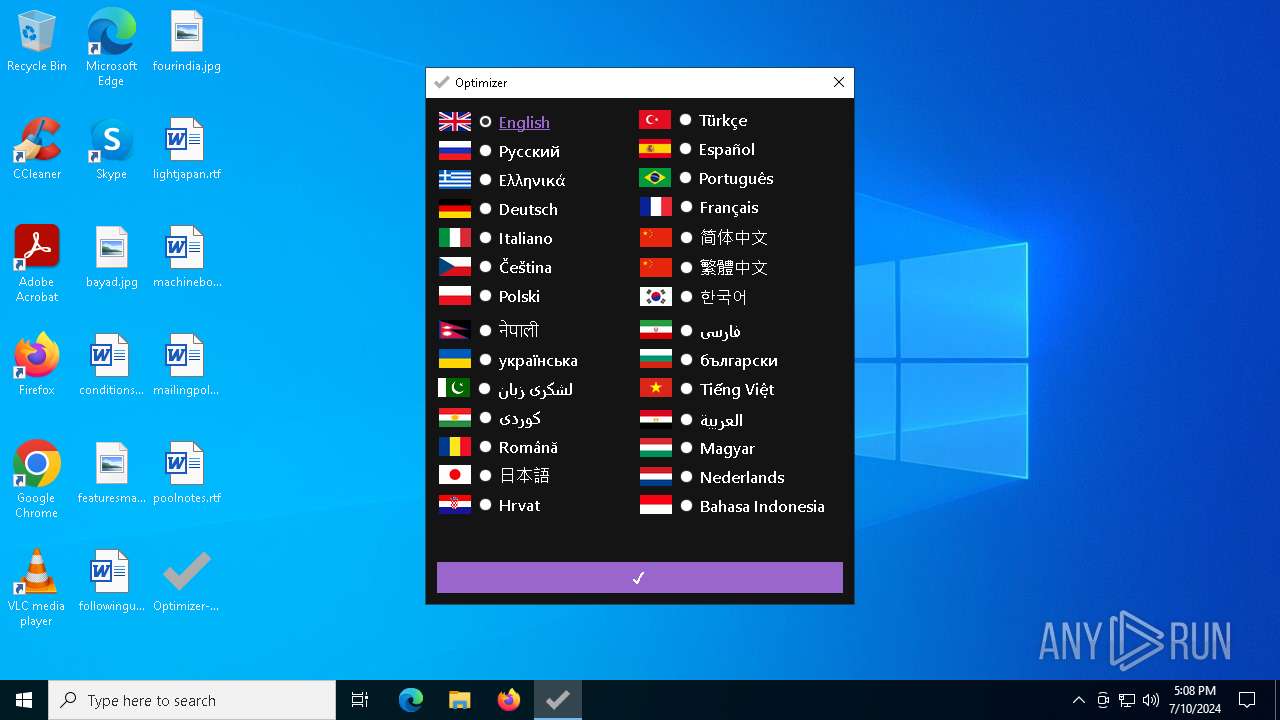
Checks supported languages
- Optimizer-16.6.exe (PID: 1228)
- Optimizer-16.6.exe (PID: 1824)
Process checks computer location settings
- Optimizer-16.6.exe (PID: 1228)
- Optimizer-16.6.exe (PID: 1824)
Reads product name
- Optimizer-16.6.exe (PID: 1824)
Reads Environment values
- Optimizer-16.6.exe (PID: 1824)
Creates files in the program directory
- Optimizer-16.6.exe (PID: 1824)
Create files in a temporary directory
- Optimizer-16.6.exe (PID: 1824)
Reads the software policy settings
- Optimizer-16.6.exe (PID: 1824)
Disables trace logs
- Optimizer-16.6.exe (PID: 1824)
Checks proxy server information
- Optimizer-16.6.exe (PID: 1824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:07:06 11:06:38+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 2532864 |
| InitializedDataSize: | 34816 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x26c4e6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | The Finest Windows Optimizer |
| CompanyName: | deadmoon © ∞ |
| FileDescription: | Optimizer |
| FileVersion: | 0.0.0.0 |
| InternalName: | Optimizer.exe |
| LegalCopyright: | deadmoon © ∞ |
| LegalTrademarks: | - |
| OriginalFileName: | Optimizer.exe |
| ProductName: | Optimizer |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
142
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1228 | "C:\Users\admin\Desktop\Optimizer-16.6.exe" | C:\Users\admin\Desktop\Optimizer-16.6.exe | — | explorer.exe | |||||||||||
User: admin Company: deadmoon © ∞ Integrity Level: MEDIUM Description: Optimizer Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1824 | "C:\Users\admin\Desktop\Optimizer-16.6.exe" | C:\Users\admin\Desktop\Optimizer-16.6.exe | Optimizer-16.6.exe | ||||||||||||
User: admin Company: deadmoon © ∞ Integrity Level: HIGH Description: Optimizer Version: 0.0.0.0 Modules
| |||||||||||||||
| 6204 | "C:\Windows\System32\cmd.exe" /C sc config "RemoteRegistry" start= disabled | C:\Windows\System32\cmd.exe | — | Optimizer-16.6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6640 | sc config "RemoteRegistry" start= disabled | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6680 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 703
Read events
13 602
Write events
101
Delete events
0
Modification events
| (PID) Process: | (1228) Optimizer-16.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1228) Optimizer-16.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1228) Optimizer-16.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1228) Optimizer-16.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1824) Optimizer-16.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Optimizer-16_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1824) Optimizer-16.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Optimizer-16_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1824) Optimizer-16.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Optimizer-16_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1824) Optimizer-16.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Optimizer-16_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1824) Optimizer-16.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Optimizer-16_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1824) Optimizer-16.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Optimizer-16_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
1
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1824 | Optimizer-16.6.exe | C:\ProgramData\Optimizer\ReadyMadeMenus\InstallTakeOwnership.reg | text | |
MD5:4E6D14D29CF28E40616D2BEF0CF8E8A8 | SHA256:A7FA8AE88B1A6B0140C8DC47F46683B6AAE752D15FA95807034144C178358C76 | |||
| 1824 | Optimizer-16.6.exe | C:\ProgramData\Optimizer\ReadyMadeMenus\SystemTools.reg | text | |
MD5:13B285768D5140BC337089840E1A9A3B | SHA256:0DC2F4E580BF09632E0961F857556D5F9378A9EBDE76F4D89F302E02DD829C21 | |||
| 1824 | Optimizer-16.6.exe | C:\ProgramData\Optimizer\ReadyMadeMenus\PowerMenu.reg | text | |
MD5:2640EC954A779D0C212822991FF7CF57 | SHA256:1C842C9395AAF625908F6579D201AF2754A92F08859D49D1BC7B55BBA2EAACE5 | |||
| 1824 | Optimizer-16.6.exe | C:\ProgramData\Optimizer\Required\DisableOfficeTelemetryTasks.reg | text | |
MD5:7F7B192506491E4105E2AE1CF5EA9067 | SHA256:41CF9DB9E395349B94EC7A1EE99DB68062F27BF95C3B364AA6B035DC39FF1DC0 | |||
| 1824 | Optimizer-16.6.exe | C:\ProgramData\Optimizer\Required\DisableOfficeTelemetryTasks.bat | text | |
MD5:74D8445BE29F93A57F3427D36307A650 | SHA256:9B4E4F516B45F4D8C6FC399B5FE25797298FD51782C922A1372A57807635B3EF | |||
| 1824 | Optimizer-16.6.exe | C:\ProgramData\Optimizer\ReadyMadeMenus\WindowsApps.reg | text | |
MD5:A1714039AB00D6275EF7EF2559346D71 | SHA256:21223E33A52A85EC5EA797457DDF8458A5040760BABC5E5367646C312D74D5D4 | |||
| 1824 | Optimizer-16.6.exe | C:\ProgramData\Optimizer\Required\EnableOfficeTelemetryTasks.bat | text | |
MD5:C5A64B235A48F30517C4D93959F13A39 | SHA256:CBA9719B6CE9D9BDF44DC80080C0A1BA60660FF2312FC1D46900A271E1CB9F3D | |||
| 1824 | Optimizer-16.6.exe | C:\ProgramData\Optimizer\Required\EnableOfficeTelemetryTasks.reg | text | |
MD5:496768EA845782927C2A9E0DD172D241 | SHA256:6A8F76C97FD957AFEC1F416363DF1E56843C8A56E0F2C470AAE66D9BE8CD2A1A | |||
| 1824 | Optimizer-16.6.exe | C:\ProgramData\Optimizer\Required\DisableTelemetryTasks.bat | text | |
MD5:0080A81E8536BACFA428F3E39ED0D219 | SHA256:A65F9F4B5859E4154D5B78B85AC3343B8CF76BFA78120CDB50EF92CB27C6BA49 | |||
| 1824 | Optimizer-16.6.exe | C:\ProgramData\Optimizer\ReadyMadeMenus\SystemShortcuts.reg | text | |
MD5:3B894F19CDEF342C0704E7774BB20AFA | SHA256:02C4C6610F2BAA98CEF5005A2155A76DD5D52B9B2C8BB49CB31E1A1EF5B74B9A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
63
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1776 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.150:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1776 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
3652 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
4720 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
6156 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
6508 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
6508 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1828 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3828 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1776 | MoUsoCoreWorker.exe | 23.48.23.150:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1776 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6004 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.123.104.4:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |