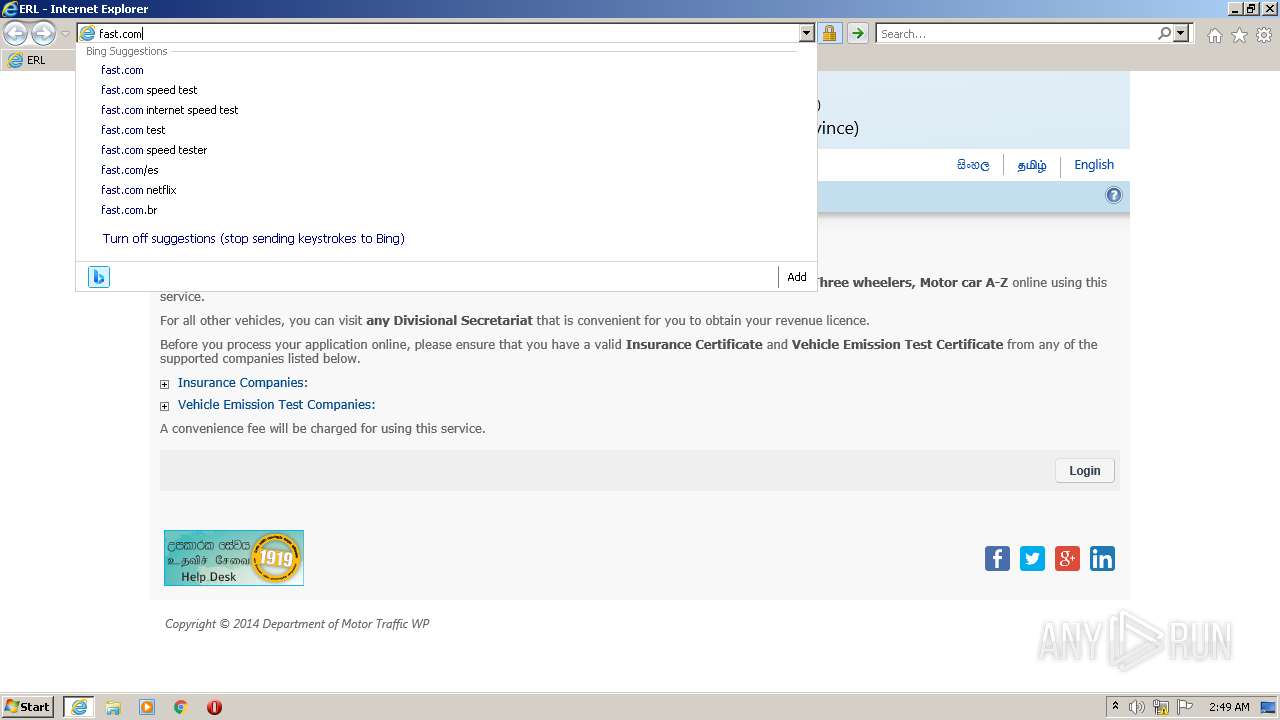
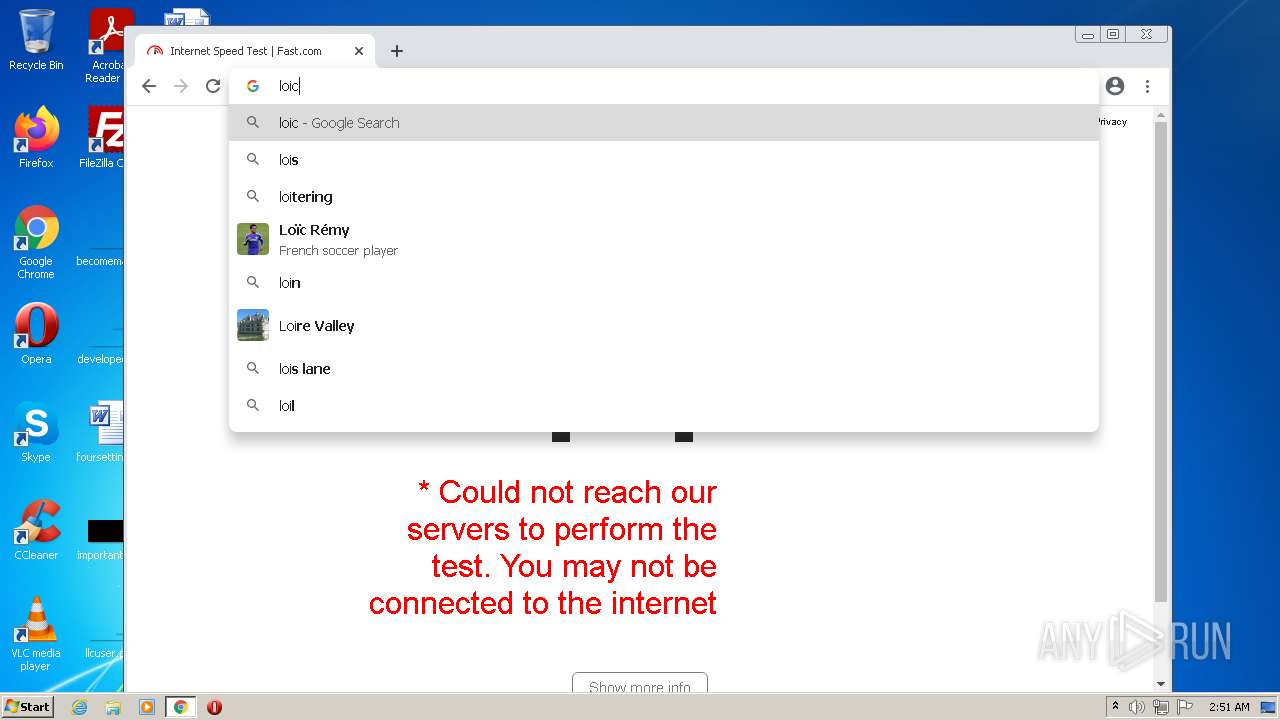
| URL: | https://www.gov.lk/services/erl/es/erl/view/index.action |
| Full analysis: | https://app.any.run/tasks/8cba94a0-69f6-4d1f-b6d6-21056b5557c3 |
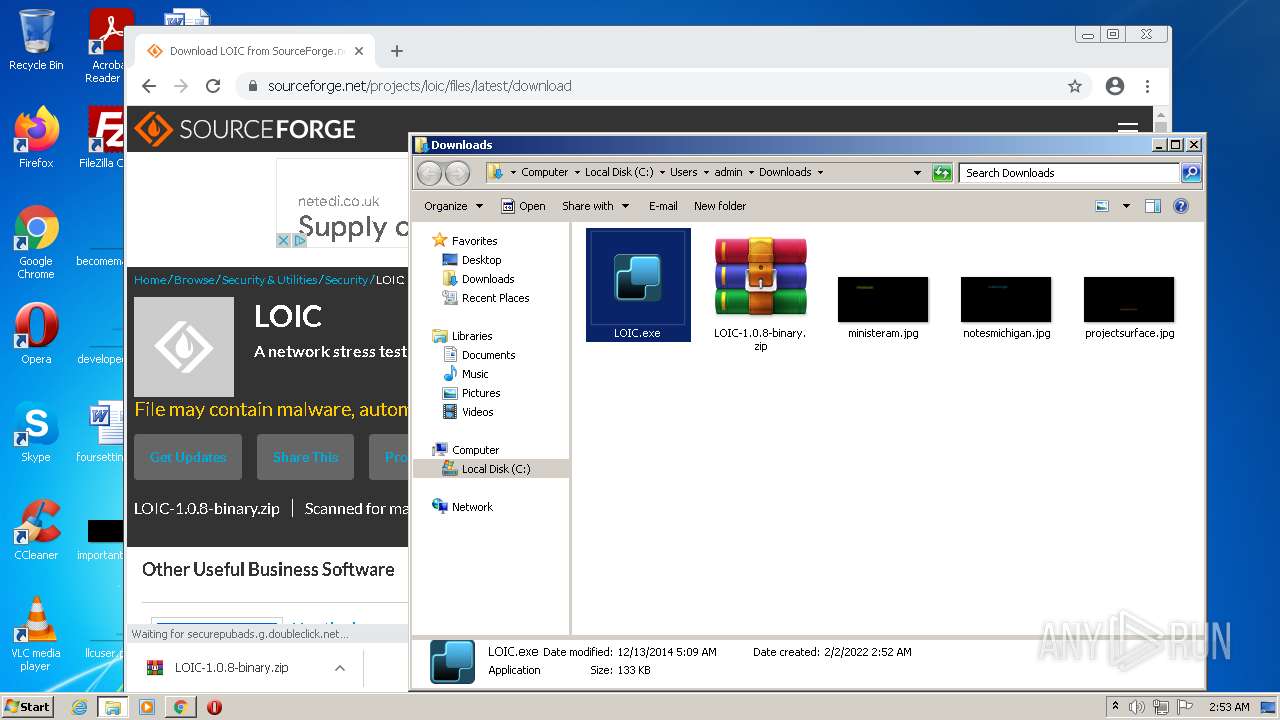
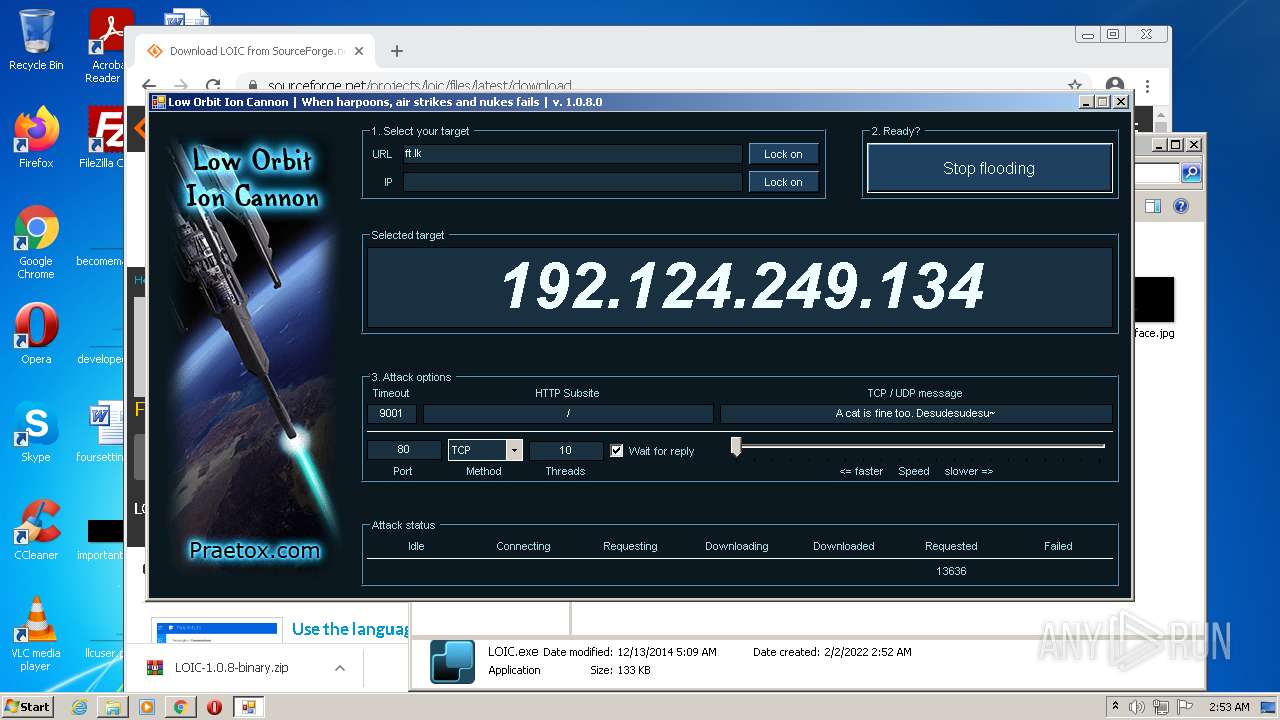
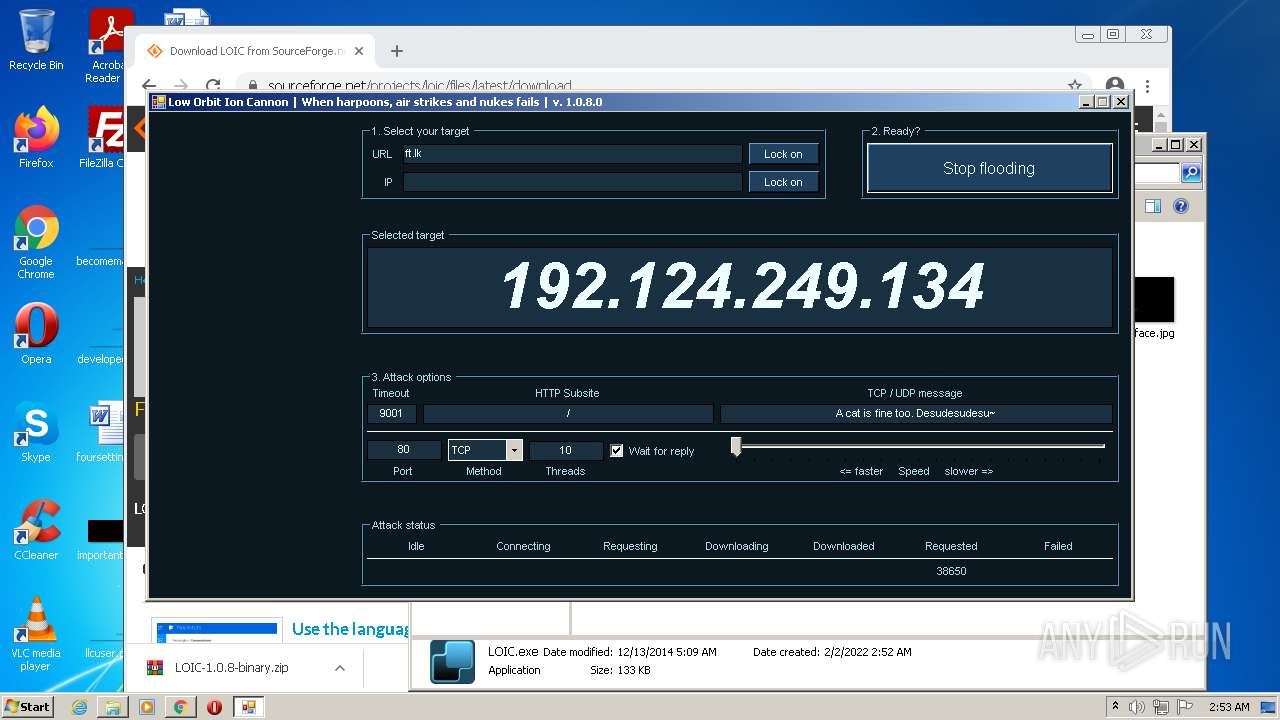
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2022, 02:48:47 |
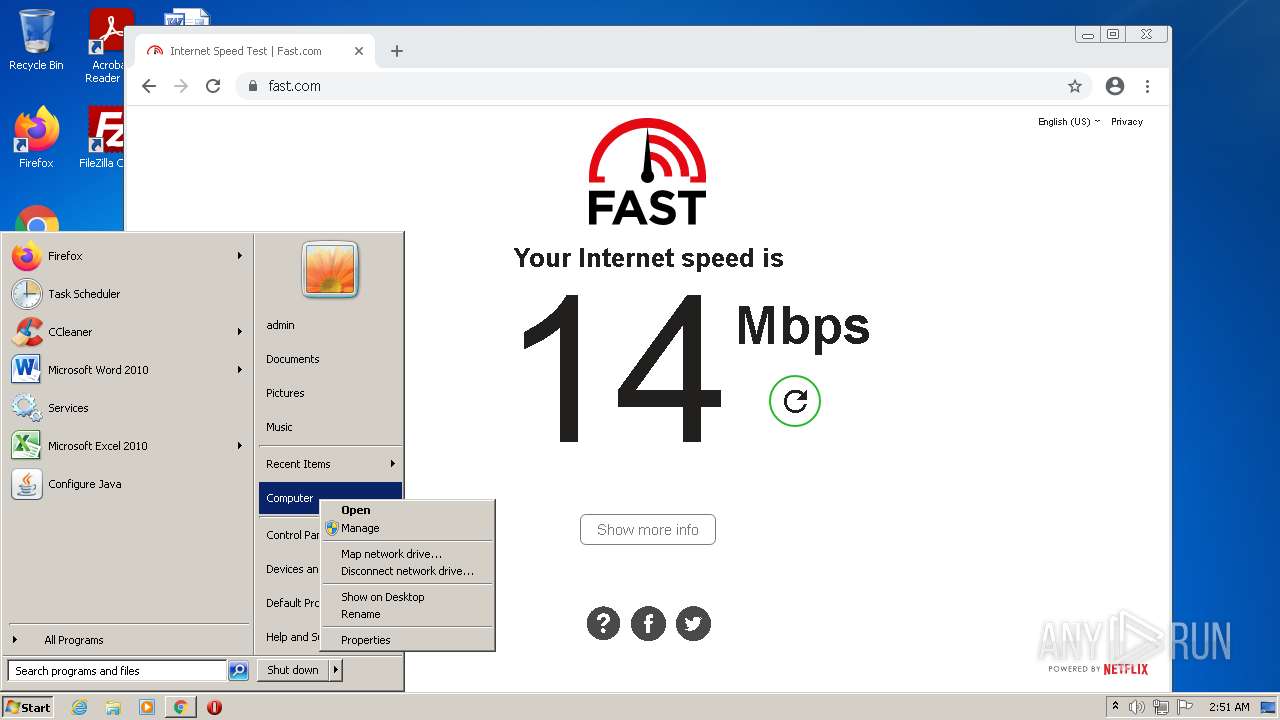
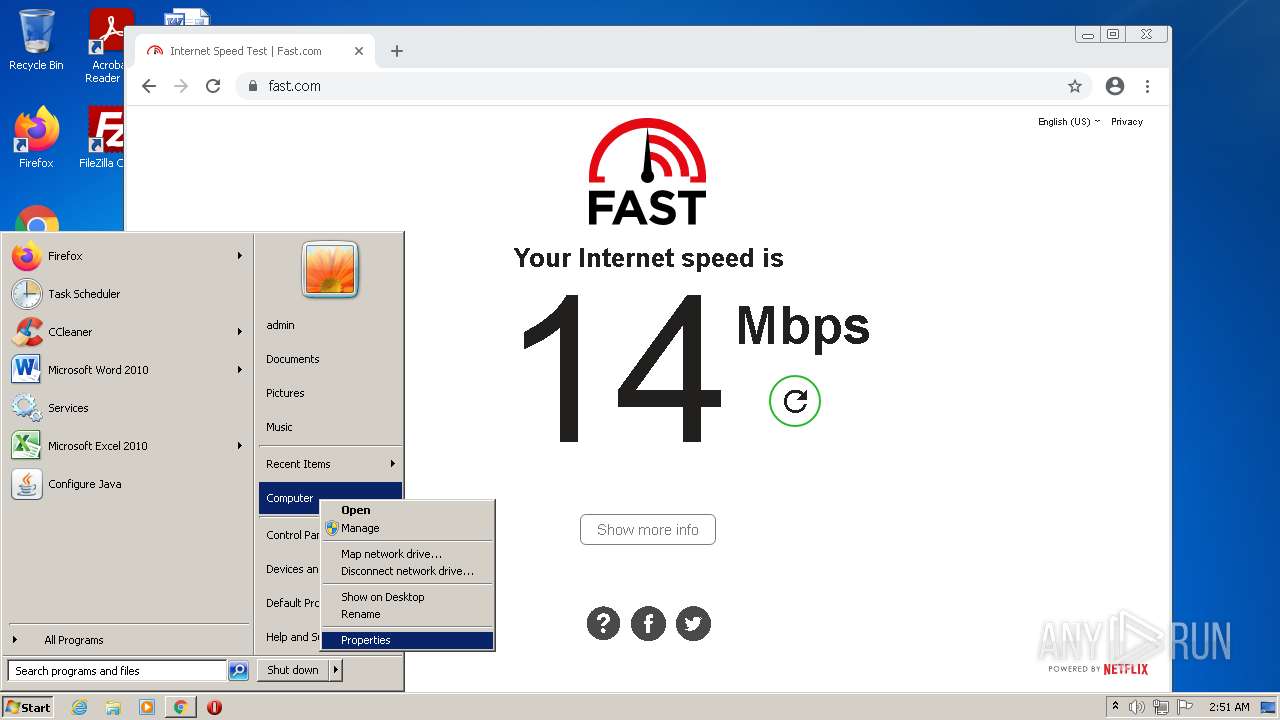
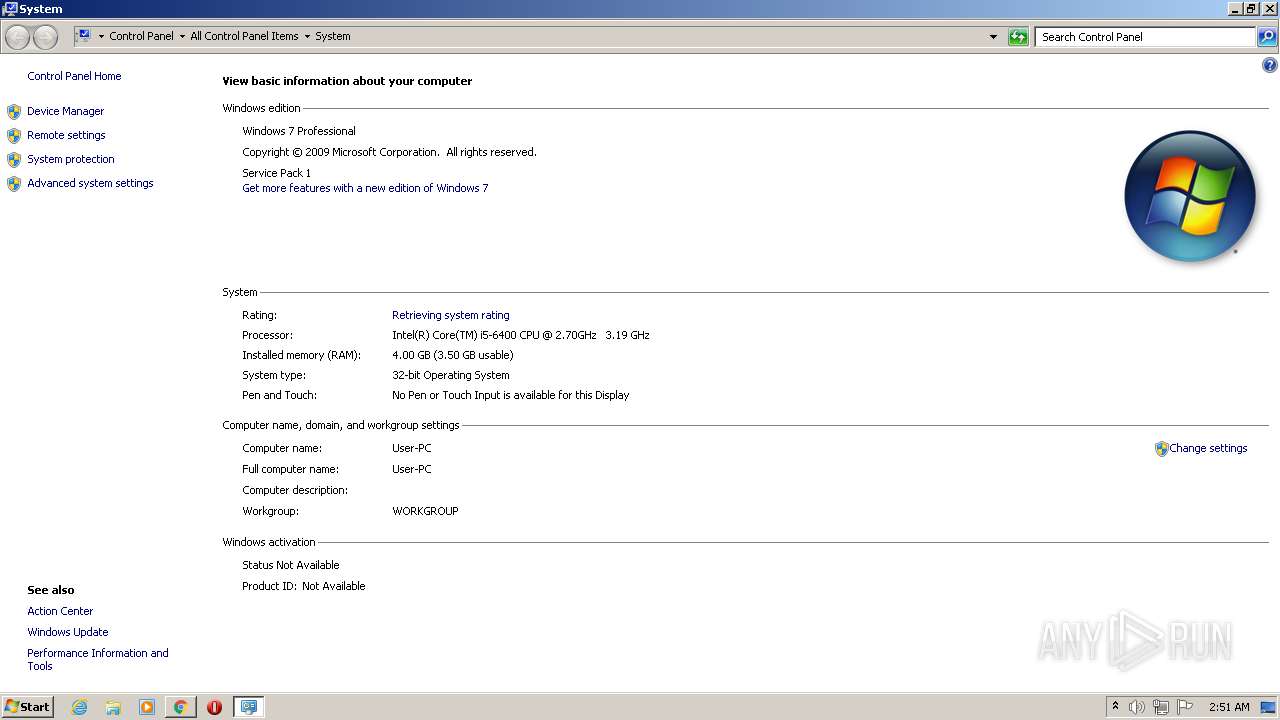
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C52C600E4E5407E17D1645A288775982 |
| SHA1: | FAB159AD4A764913B0518428699FB60E355DCF88 |
| SHA256: | 8B1E062D6BDB9F79042EF807EE50F188D65F175A2ABE306FC35D5EF8EAE1778D |
| SSDEEP: | 3:N8DSLFz3XEmA0lMTGN:2OLFznEmA0lN |
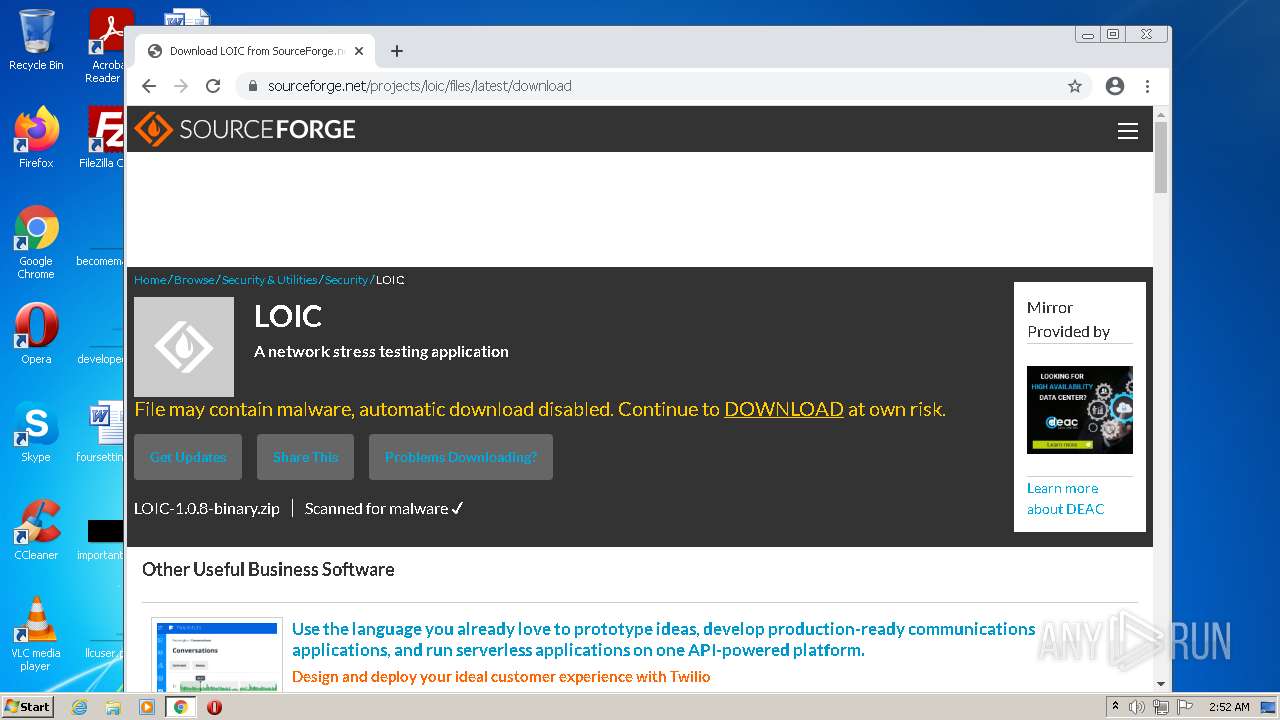
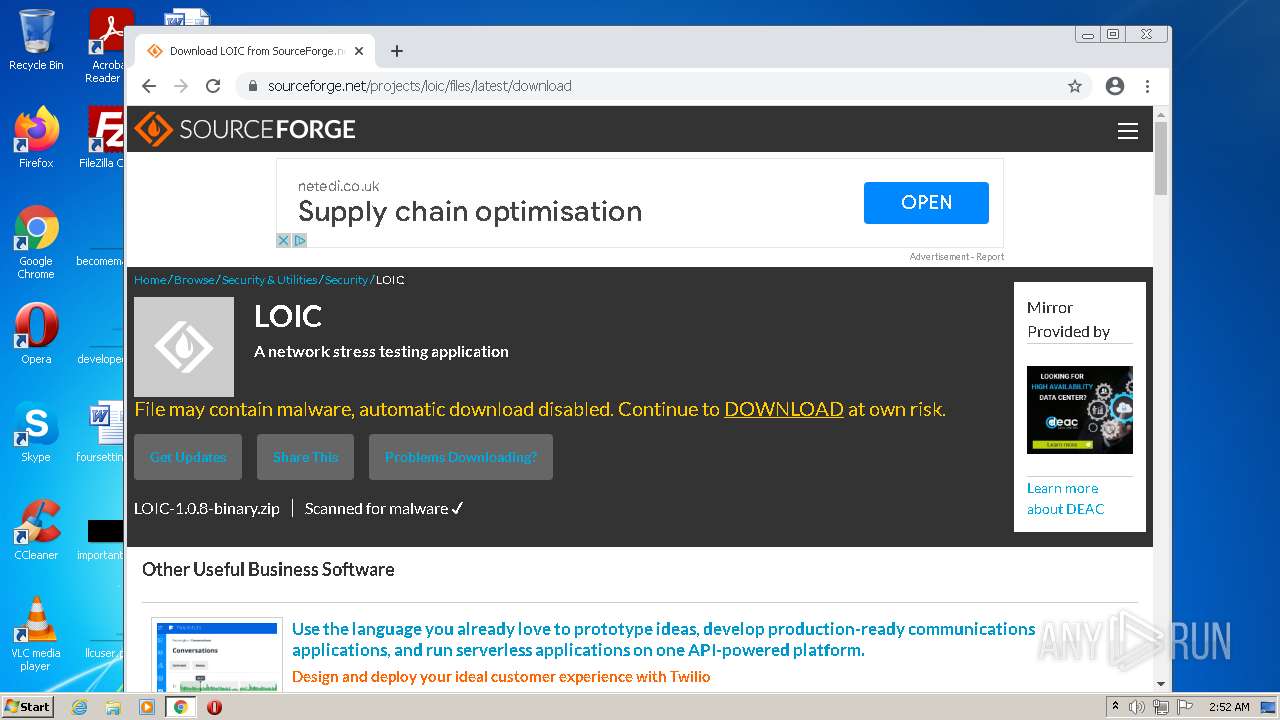
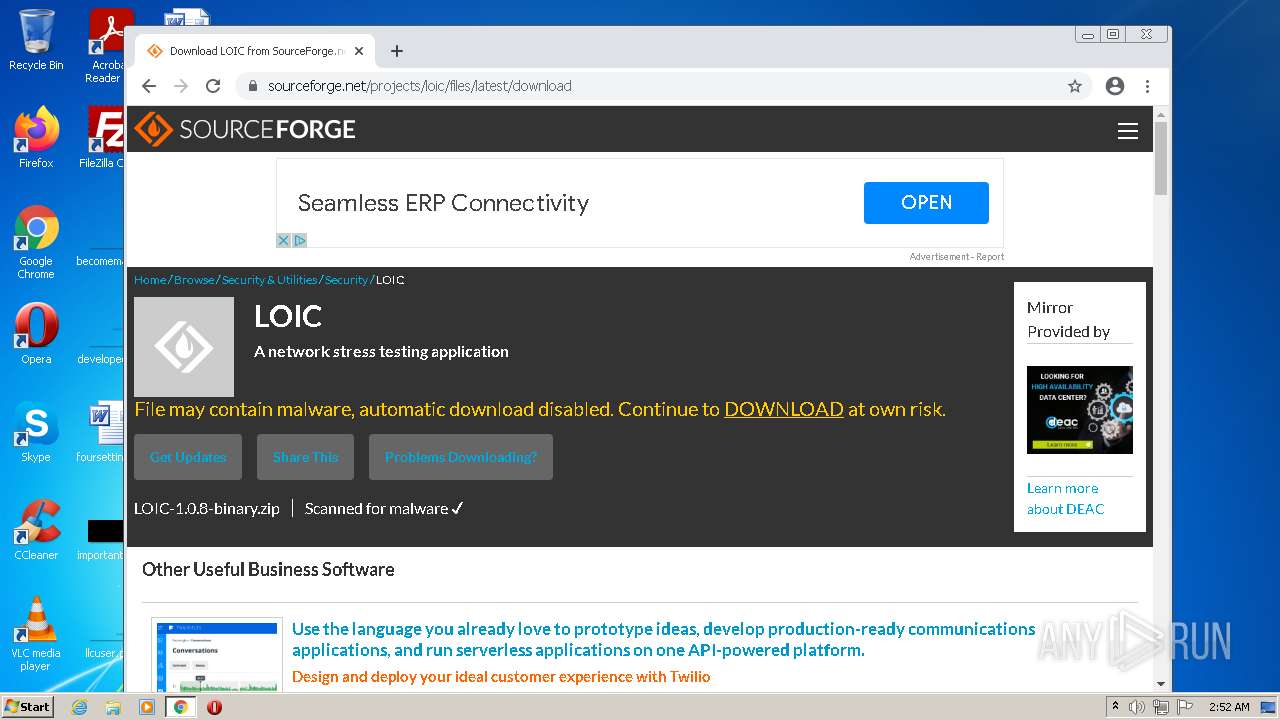
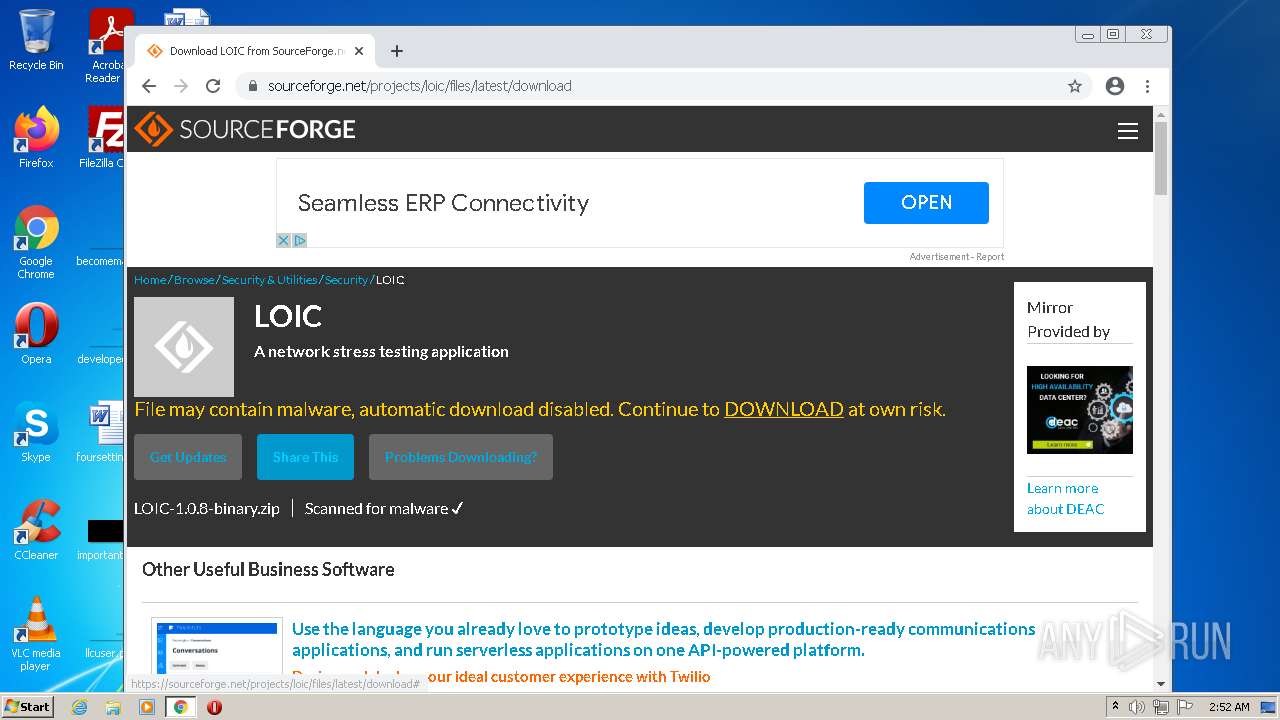
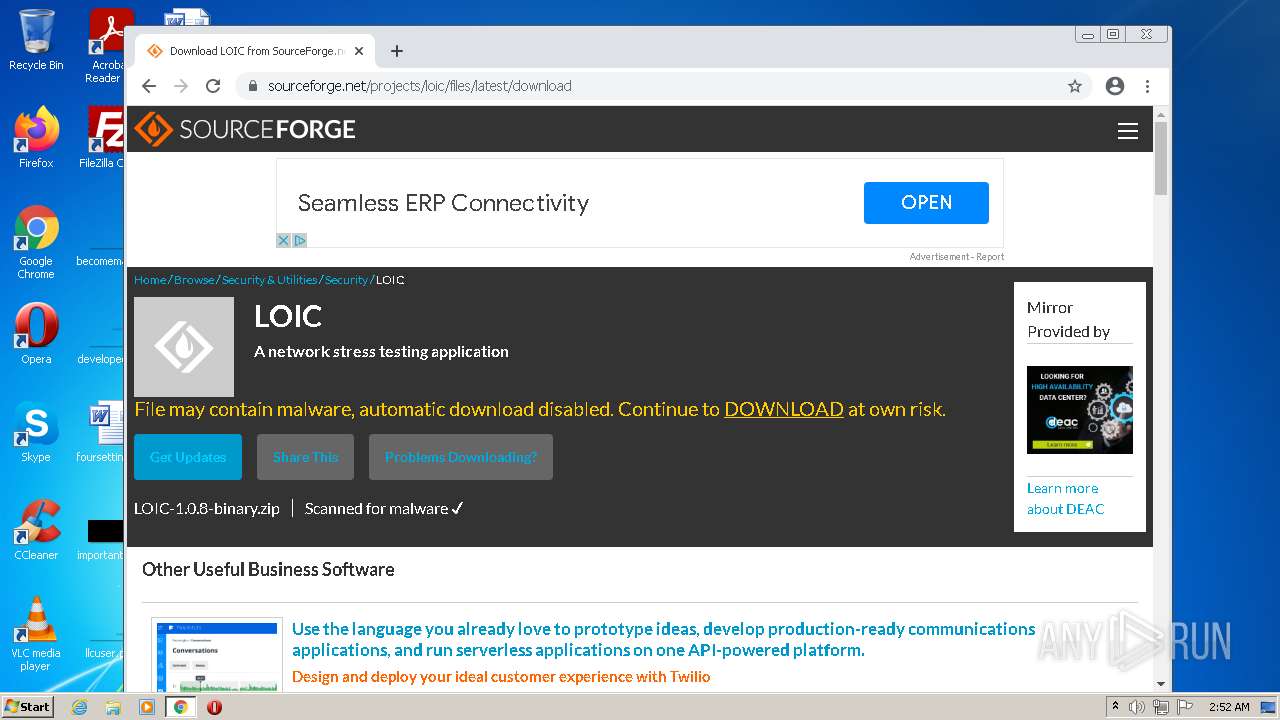
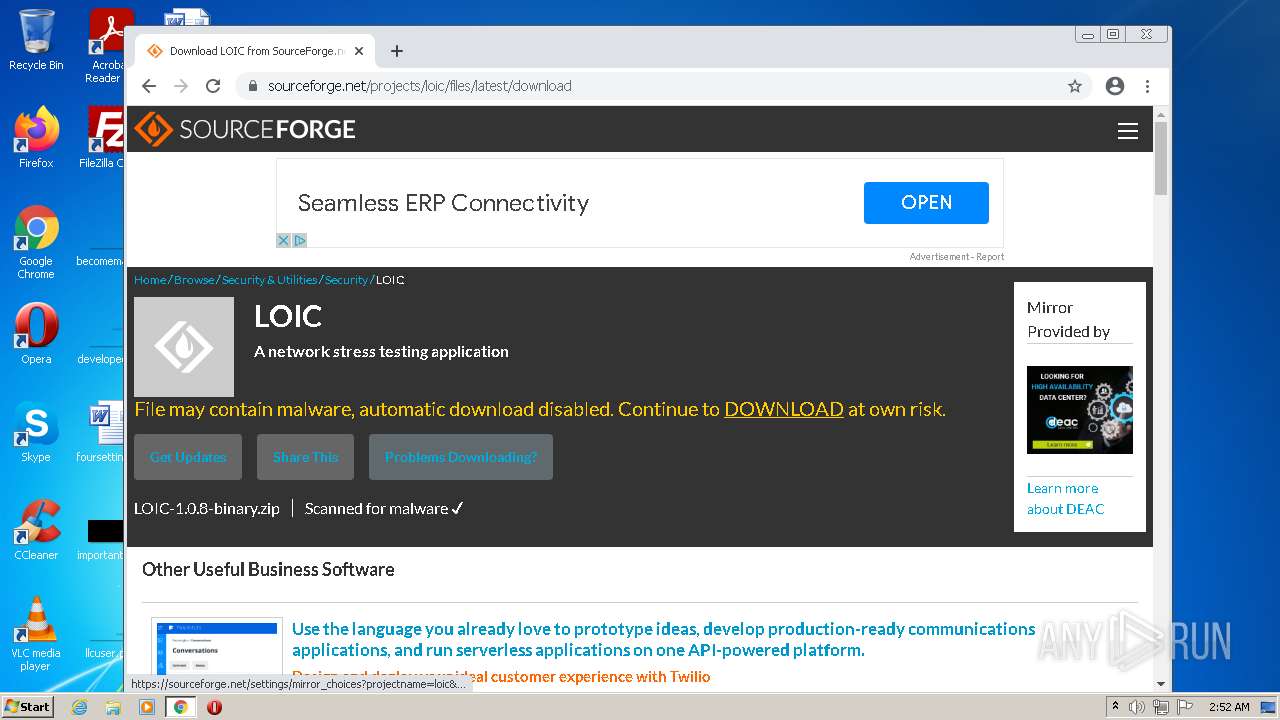
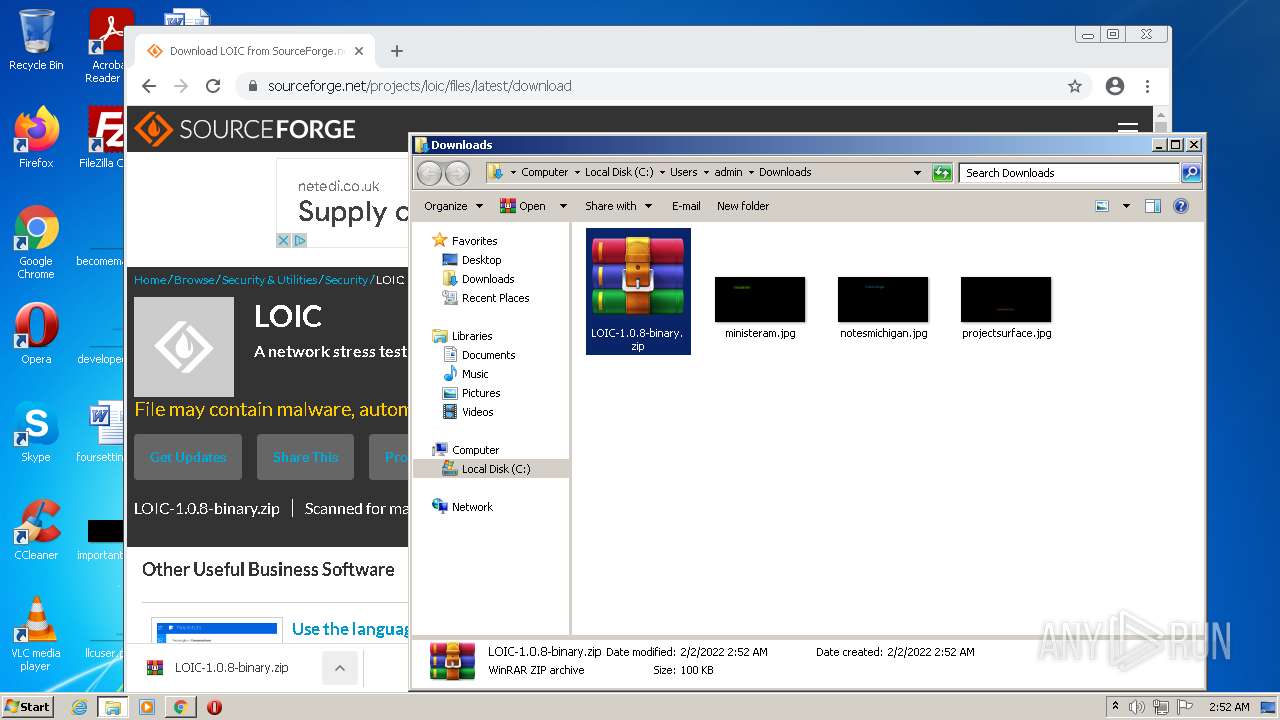
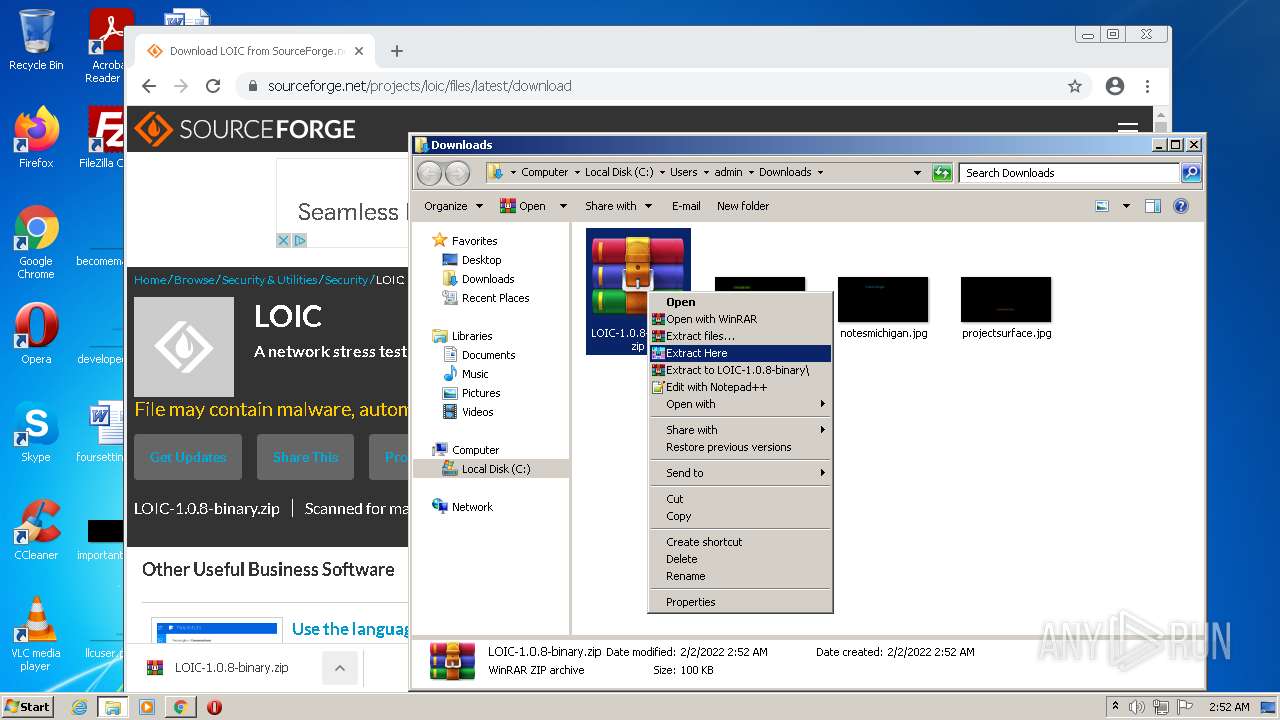
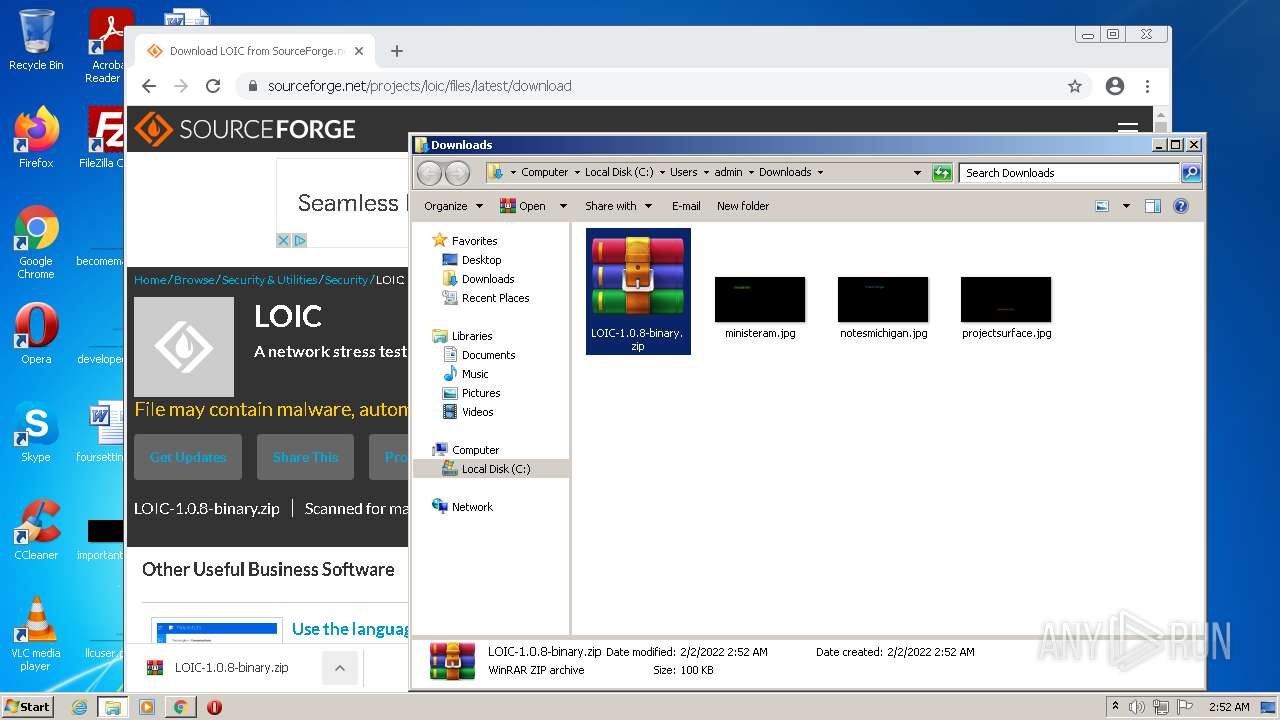
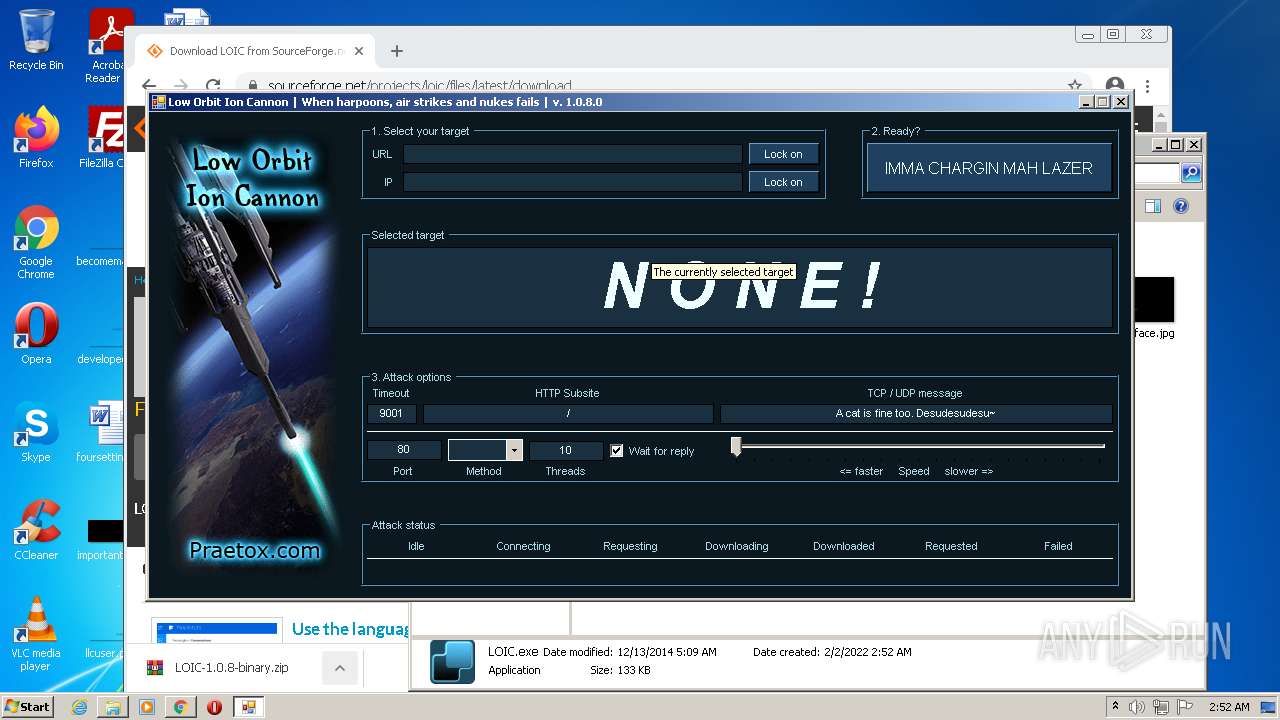
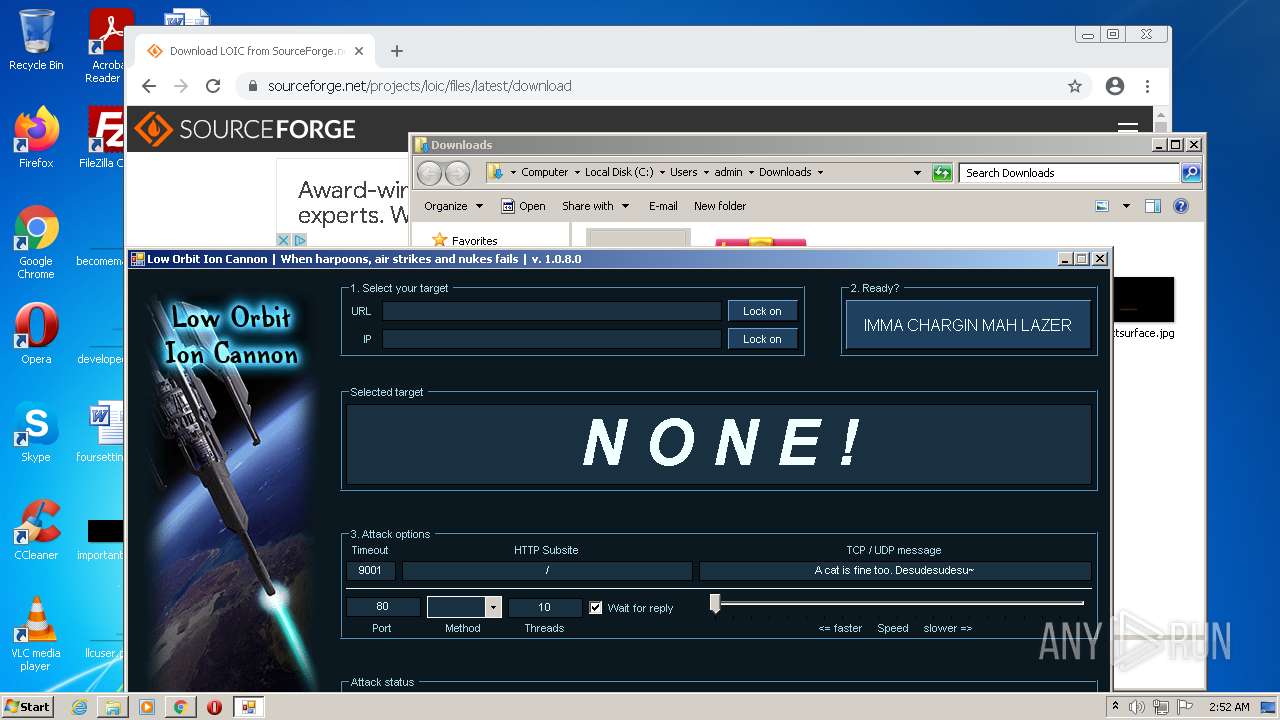
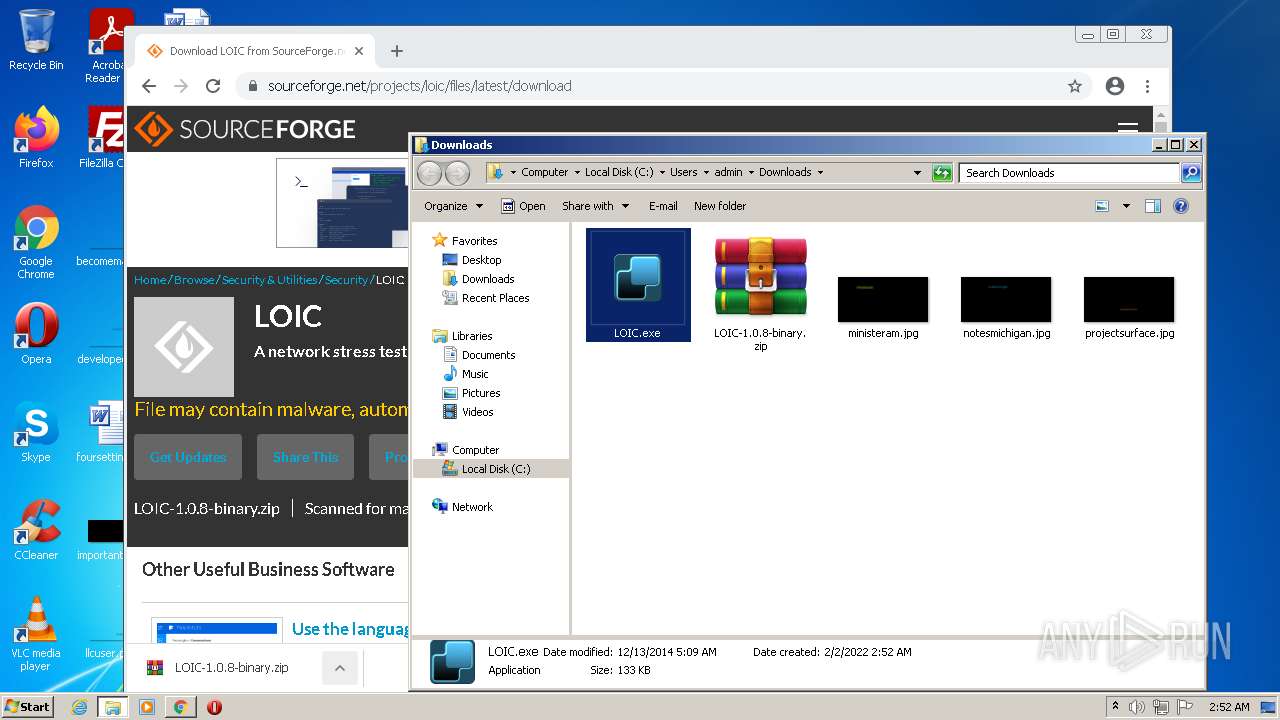
MALICIOUS
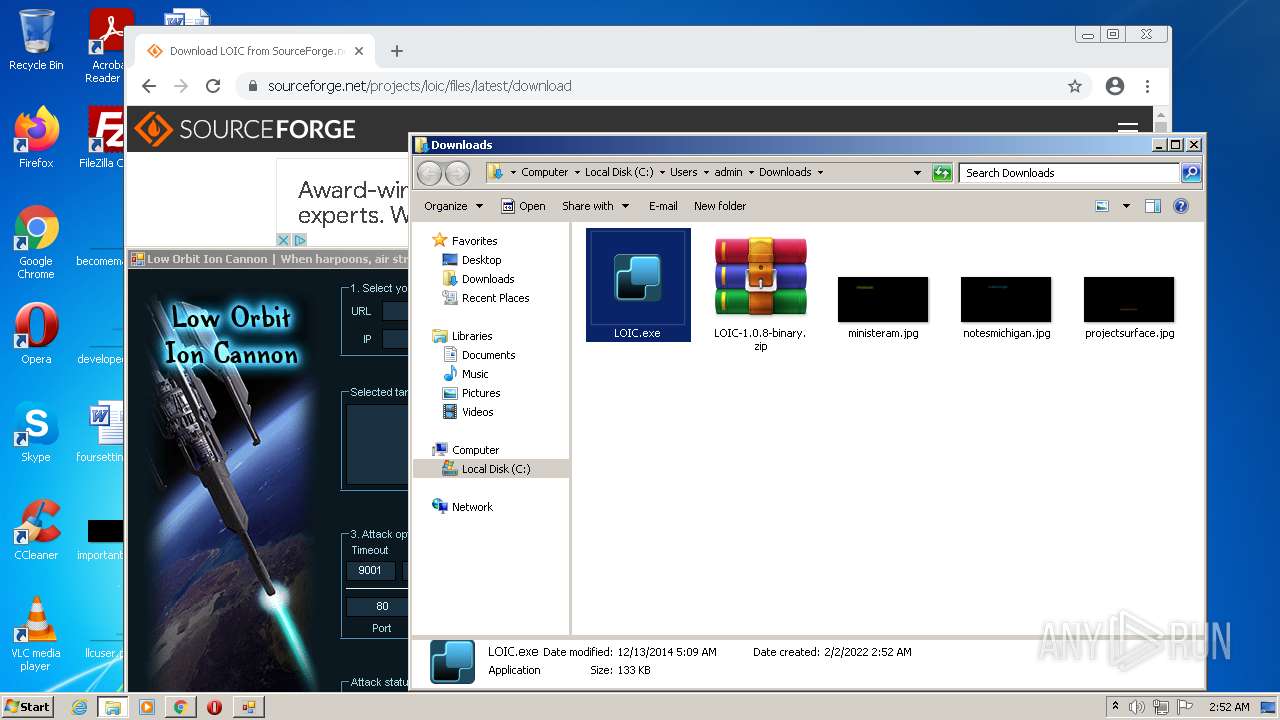
Drops executable file immediately after starts
- chrome.exe (PID: 1612)
- WinRAR.exe (PID: 3656)
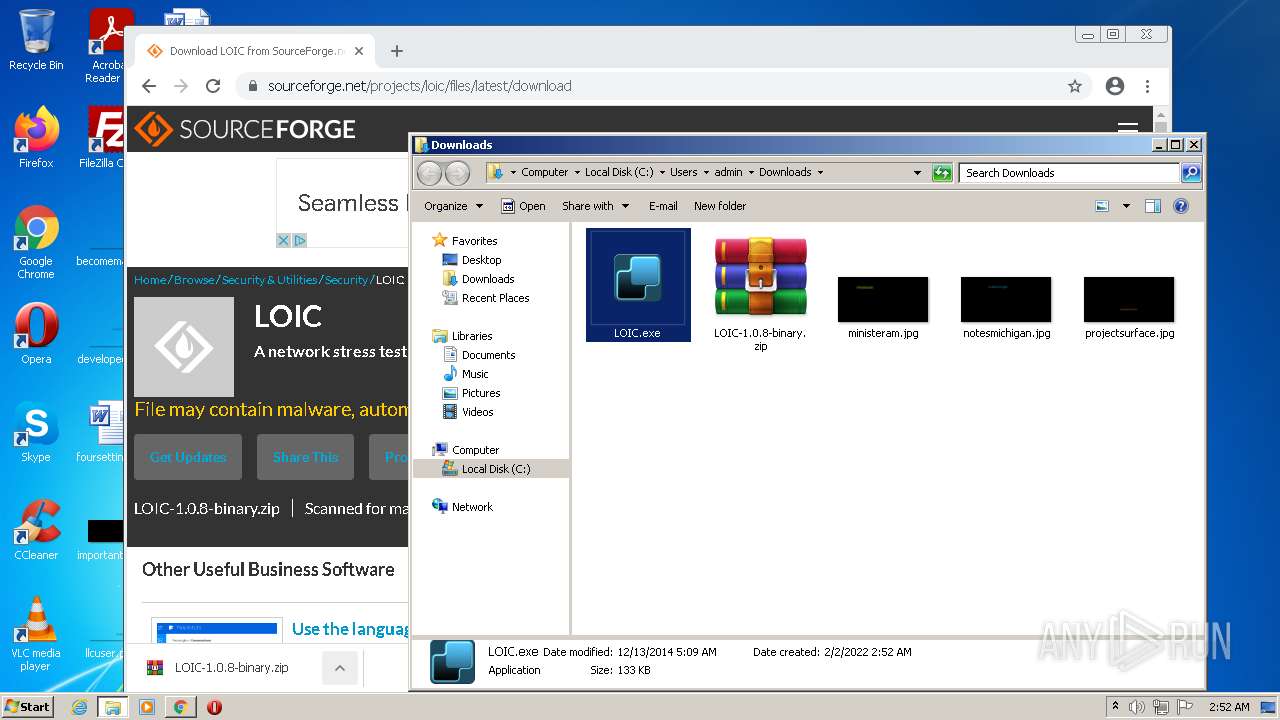
Application was dropped or rewritten from another process
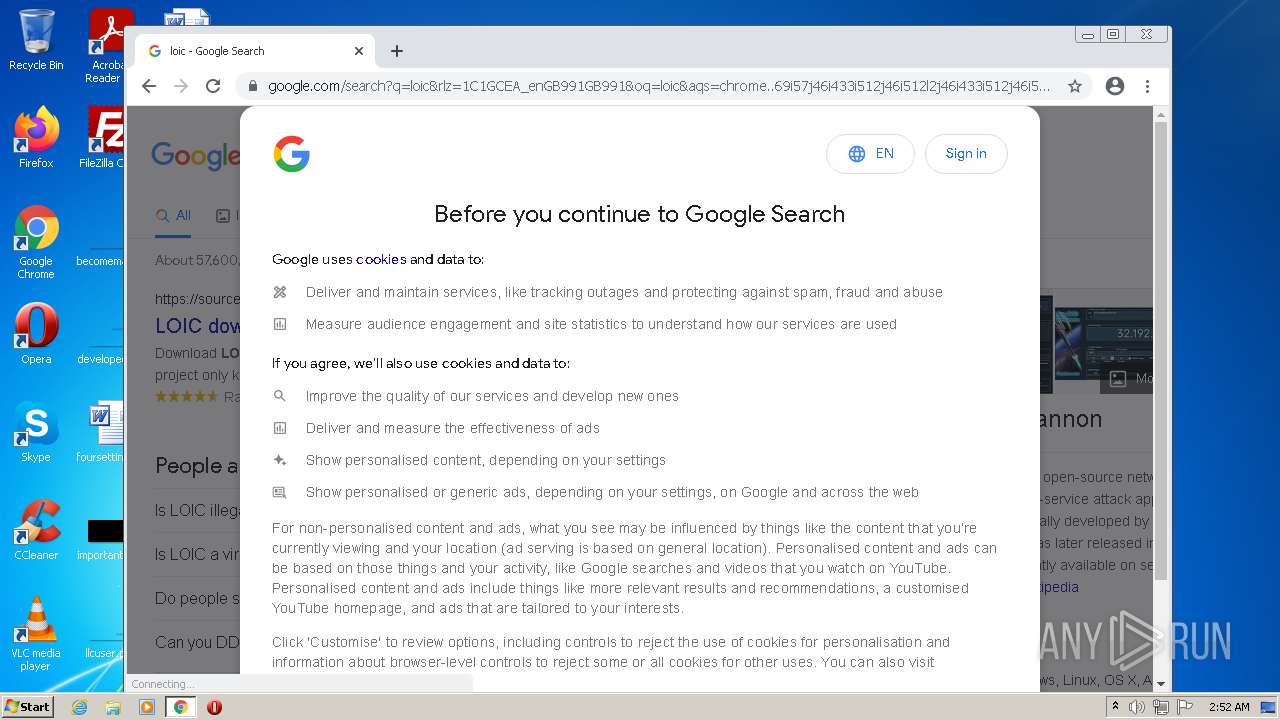
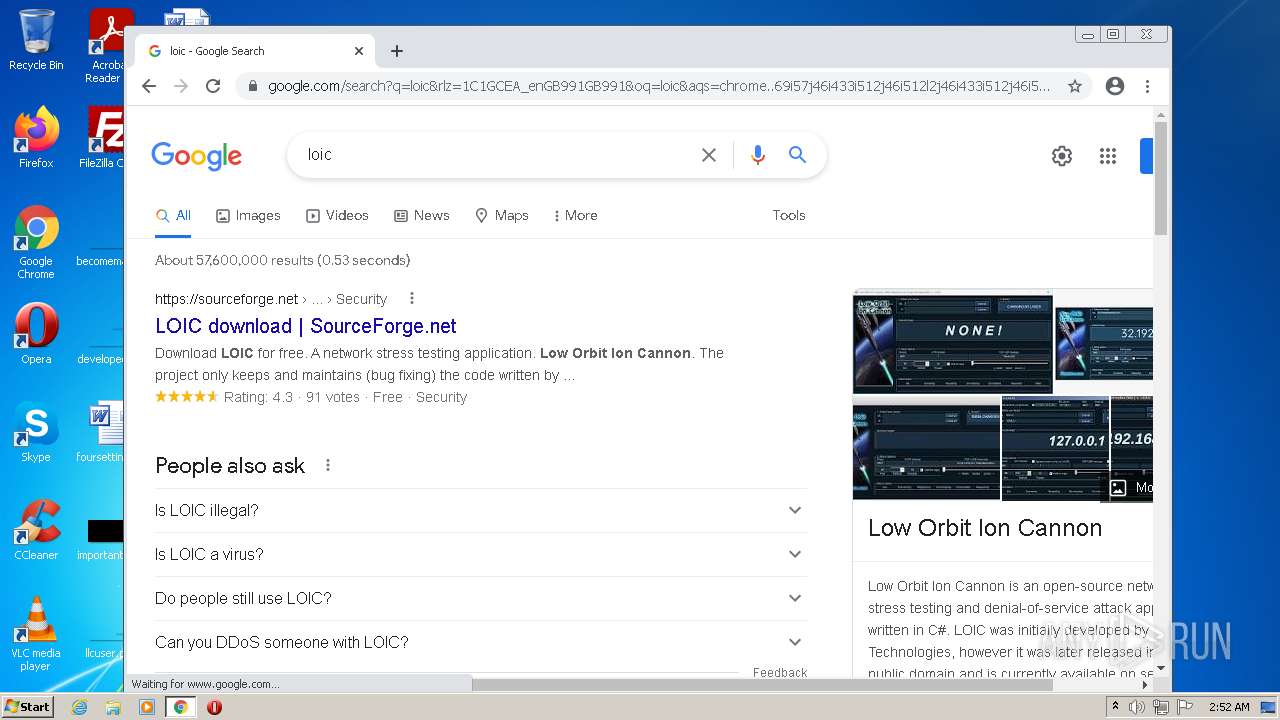
- LOIC.exe (PID: 1864)
- LOIC.exe (PID: 3220)
- LOIC.exe (PID: 2072)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2708)
- LOIC.exe (PID: 2072)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3432)
Executable content was dropped or overwritten
- chrome.exe (PID: 1612)
- WinRAR.exe (PID: 3656)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 1612)
- WinRAR.exe (PID: 3656)
Checks supported languages
- WinRAR.exe (PID: 3656)
- LOIC.exe (PID: 1864)
- LOIC.exe (PID: 3220)
- LOIC.exe (PID: 2072)
Reads the computer name
- LOIC.exe (PID: 1864)
- WinRAR.exe (PID: 3656)
- LOIC.exe (PID: 3220)
- LOIC.exe (PID: 2072)
INFO
Checks supported languages
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 2708)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 1252)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 4028)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 1124)
- chrome.exe (PID: 1408)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 832)
- chrome.exe (PID: 2288)
- chrome.exe (PID: 3060)
- control.exe (PID: 3800)
- chrome.exe (PID: 2300)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 1548)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 4084)
- chrome.exe (PID: 2504)
- chrome.exe (PID: 3844)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 1324)
- chrome.exe (PID: 1672)
- chrome.exe (PID: 3552)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 1968)
- chrome.exe (PID: 1272)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 852)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 572)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 872)
- chrome.exe (PID: 880)
- chrome.exe (PID: 824)
- chrome.exe (PID: 2324)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 1784)
- chrome.exe (PID: 436)
- chrome.exe (PID: 496)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 1408)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 3372)
- chrome.exe (PID: 1612)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 3908)
Application launched itself
- iexplore.exe (PID: 1536)
- chrome.exe (PID: 3432)
Reads the computer name
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 2708)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 832)
- chrome.exe (PID: 2288)
- control.exe (PID: 3800)
- chrome.exe (PID: 1784)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3732)
Changes internet zones settings
- iexplore.exe (PID: 1536)
Reads internet explorer settings
- iexplore.exe (PID: 2708)
Reads settings of System Certificates
- iexplore.exe (PID: 2708)
- iexplore.exe (PID: 1536)
- chrome.exe (PID: 2332)
- LOIC.exe (PID: 2072)
Checks Windows Trust Settings
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 2708)
Creates files in the user directory
- iexplore.exe (PID: 2708)
- iexplore.exe (PID: 1536)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2708)
Reads the date of Windows installation
- iexplore.exe (PID: 1536)
- chrome.exe (PID: 832)
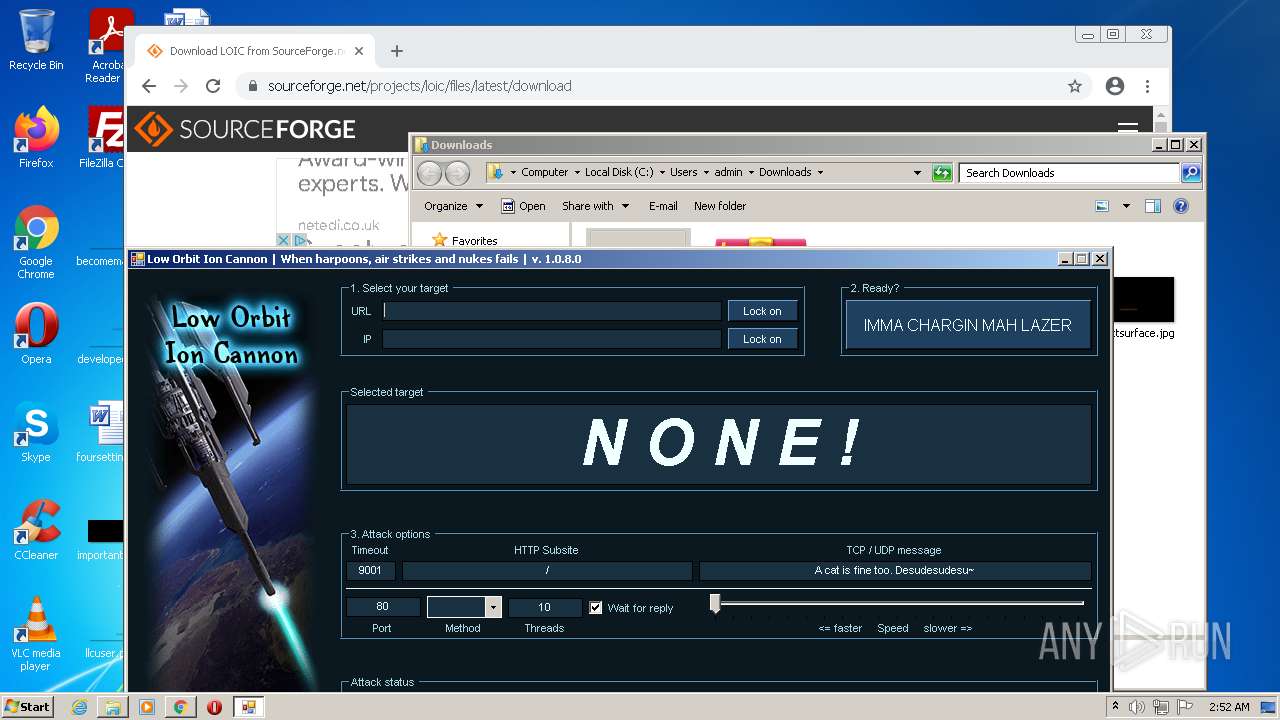
Manual execution by user
- chrome.exe (PID: 3432)
- control.exe (PID: 3800)
- WinRAR.exe (PID: 3656)
- LOIC.exe (PID: 3220)
- LOIC.exe (PID: 1864)
- LOIC.exe (PID: 2072)
Reads the hosts file
- chrome.exe (PID: 3432)
- chrome.exe (PID: 2332)
Changes default file association
- chrome.exe (PID: 3432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
131
Monitored processes
87
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1329442169327060171,3994410280352804432,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=69 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3724 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1329442169327060171,3994410280352804432,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=70 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,1329442169327060171,3994410280352804432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2928 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,1329442169327060171,3994410280352804432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4136 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,1329442169327060171,3994410280352804432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1868 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,1329442169327060171,3994410280352804432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2764 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,1329442169327060171,3994410280352804432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3756 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,1329442169327060171,3994410280352804432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3744 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,1329442169327060171,3994410280352804432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3884 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,1329442169327060171,3994410280352804432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3656 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
44 307
Read events
43 830
Write events
461
Delete events
16
Modification events
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30939103 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30939103 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
267
Text files
215
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_86C2A03C133240EC4C95180B9FD368BB | der | |
MD5:— | SHA256:— | |||
| 2708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\709A8EC0F6D3194AD001E9041914421F_9FEB028B53045166689A9651752DFB66 | der | |
MD5:— | SHA256:— | |||
| 2708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\tablet[1].css | text | |
MD5:— | SHA256:— | |||
| 2708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\desktop[1].css | text | |
MD5:— | SHA256:— | |||
| 2708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\hspplus[1].gif | image | |
MD5:— | SHA256:— | |||
| 2708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_86C2A03C133240EC4C95180B9FD368BB | binary | |
MD5:— | SHA256:— | |||
| 2708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\erl_styles[1].css | text | |
MD5:— | SHA256:— | |||
| 2708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\common[1].js | text | |
MD5:— | SHA256:— | |||
| 2708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\709A8EC0F6D3194AD001E9041914421F_9FEB028B53045166689A9651752DFB66 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
284
DNS requests
116
Threats
33
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
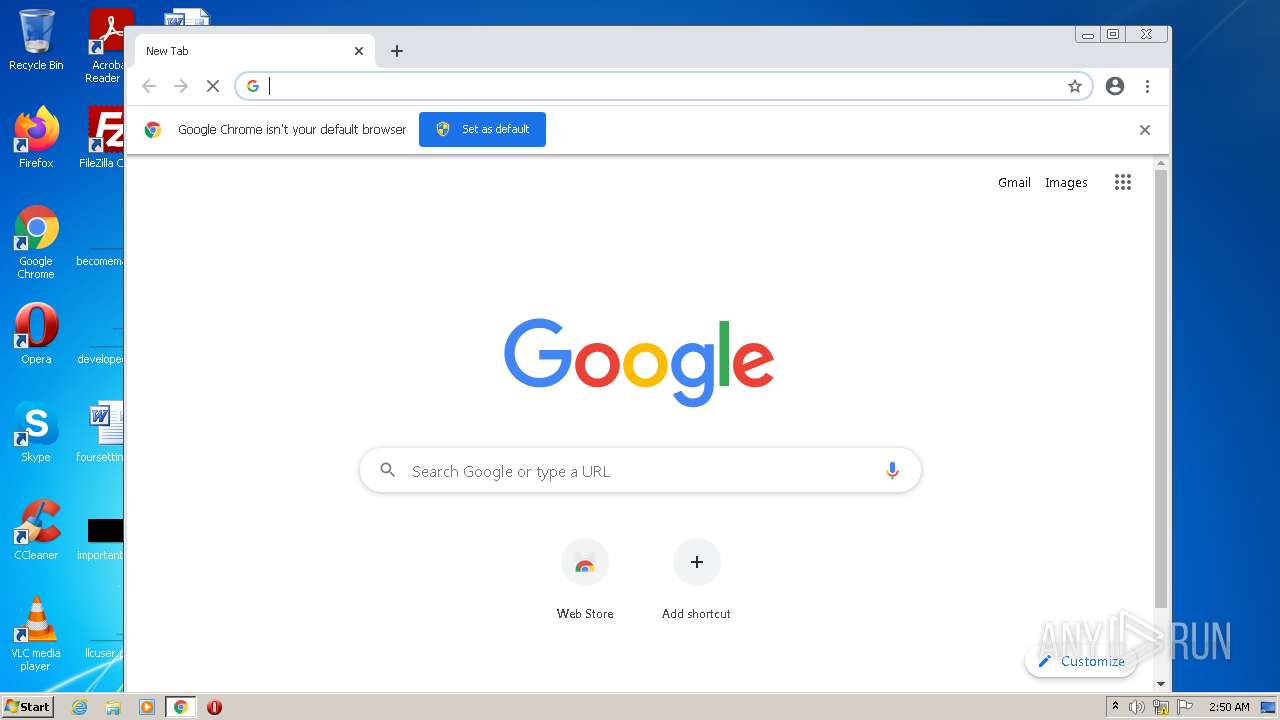
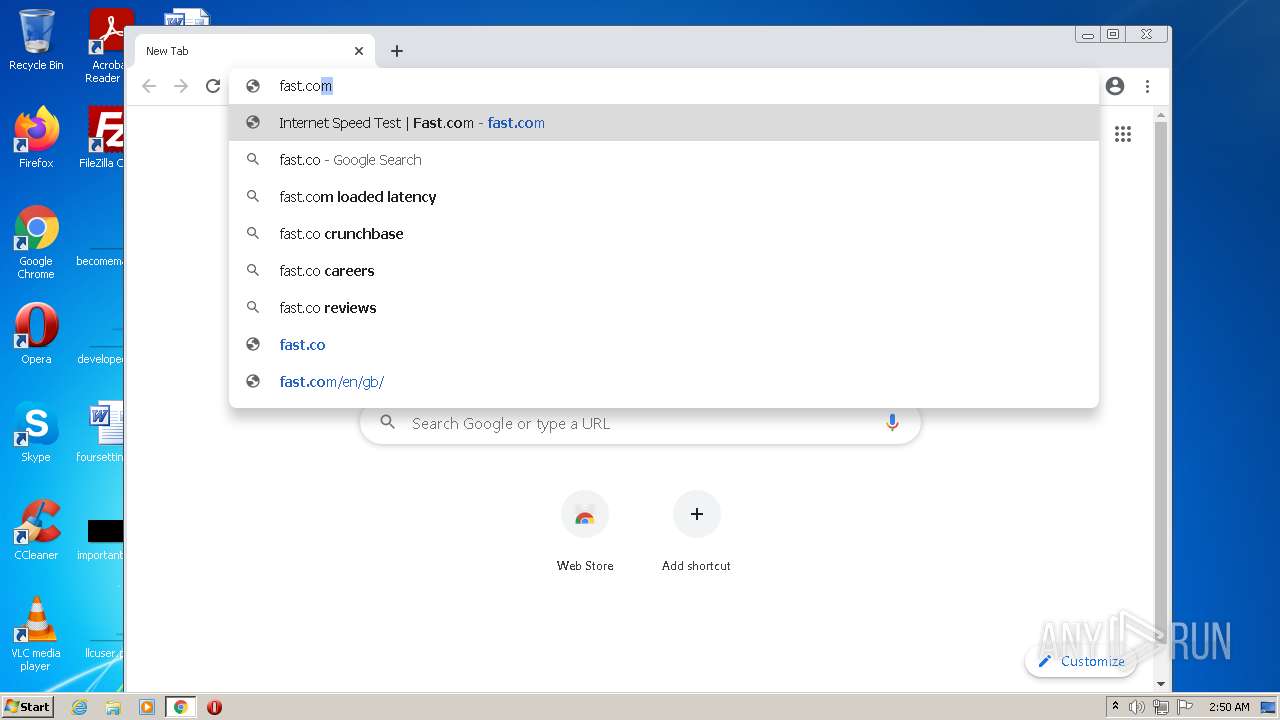
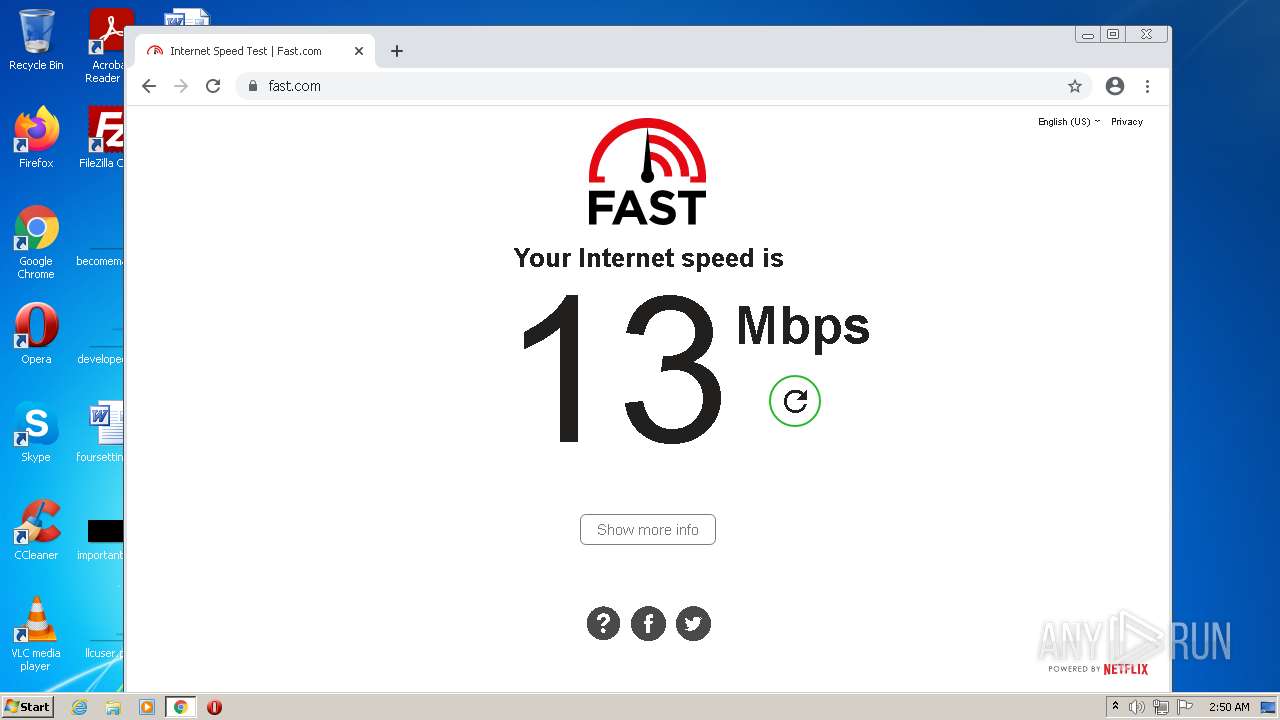
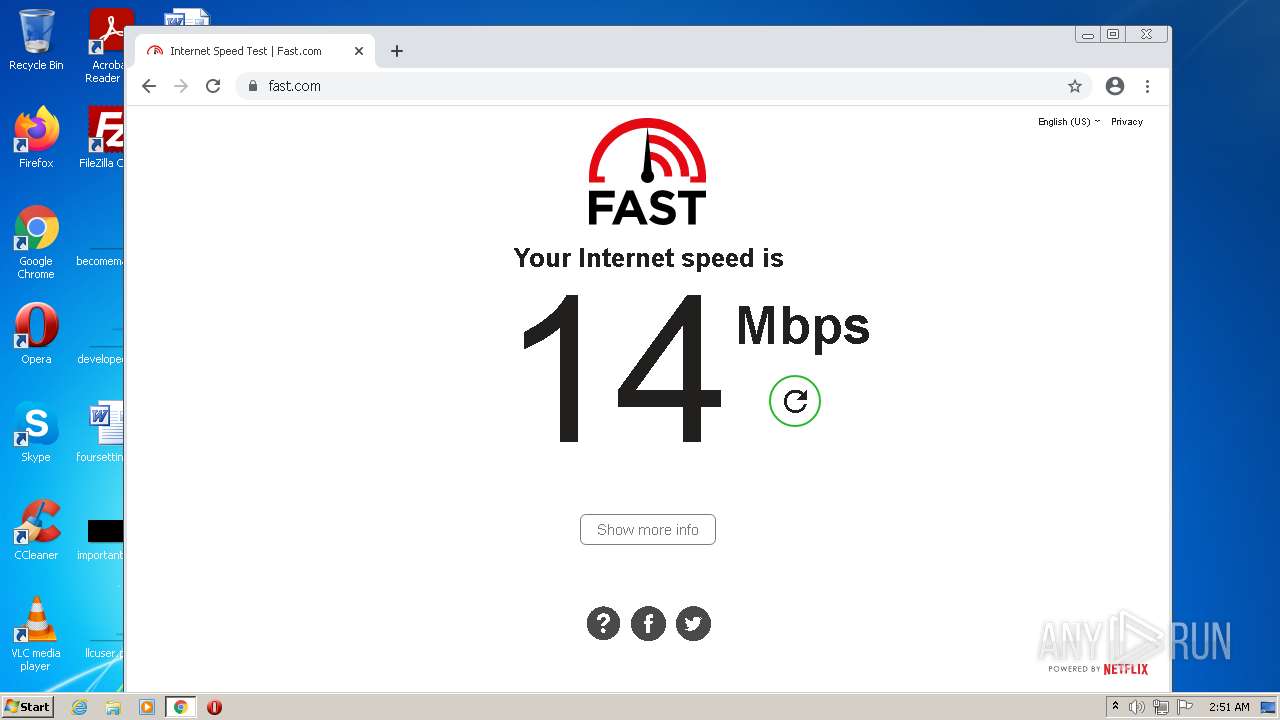
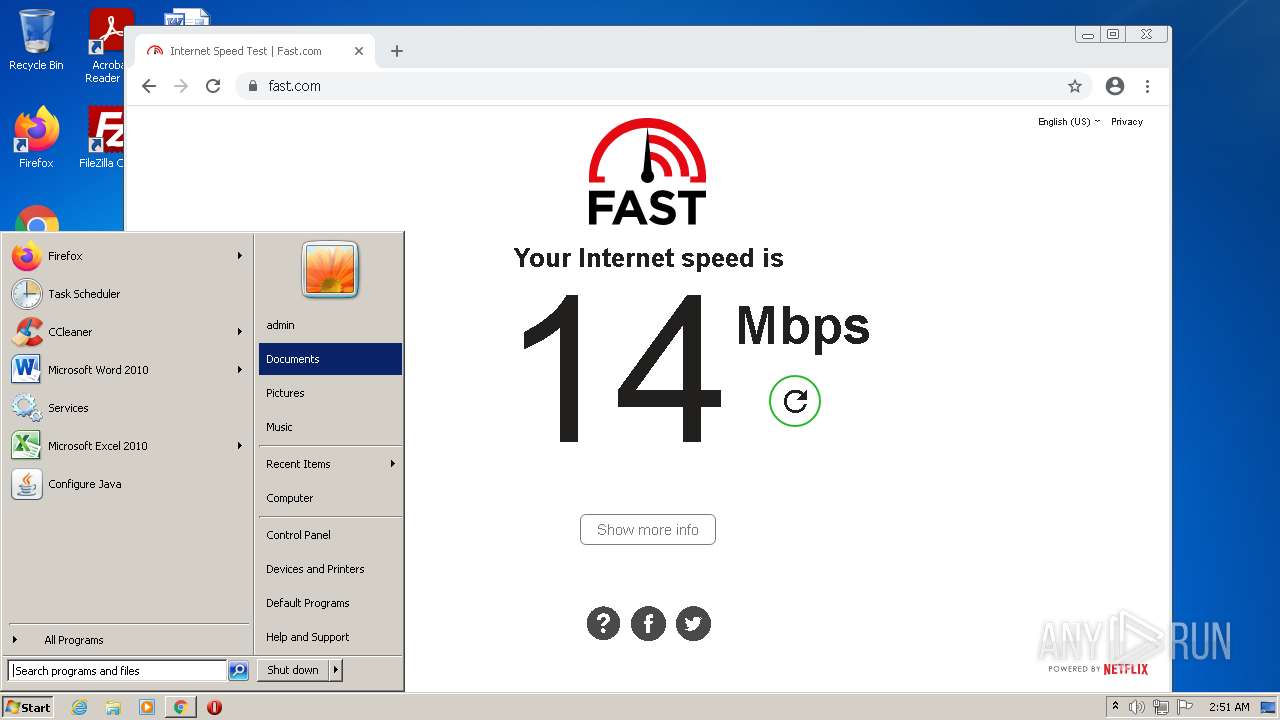
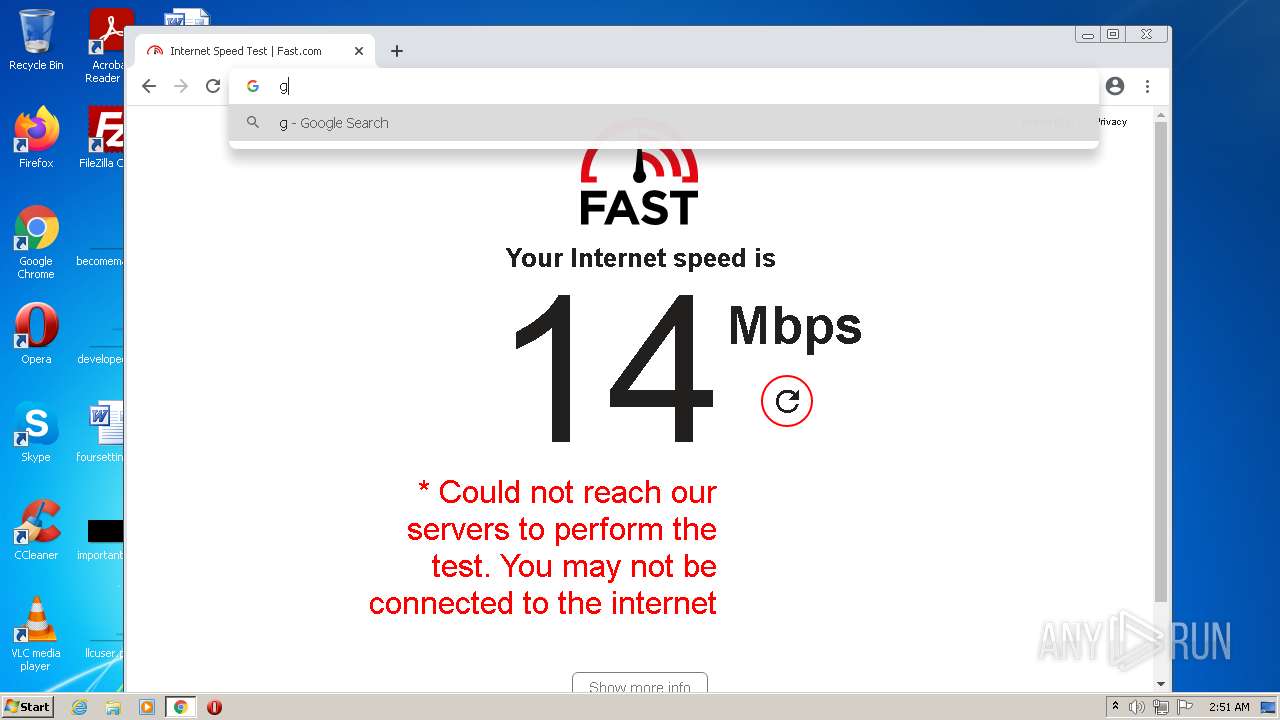
2708 | iexplore.exe | GET | 301 | 104.92.111.166:80 | http://fast.com/ | NL | — | — | whitelisted |
924 | svchost.exe | HEAD | 200 | 74.125.105.103:80 | http://r2---sn-aigl6nsk.gvt1.com/edgedl/release2/chrome_component/czka5fc33qq67ao7g67evi5jte_9.32.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.32.0_all_hkbbg5yepfmg4tn57zz6rpfdiy.crx3?cms_redirect=yes&mh=1f&mip=185.217.117.59&mm=28&mn=sn-aigl6nsk&ms=nvh&mt=1643769857&mv=m&mvi=2&pl=25&rmhost=r4---sn-aigl6nsk.gvt1.com&shardbypass=yes&smhost=r4---sn-aigl6nsr.gvt1.com | US | — | — | whitelisted |
924 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/czka5fc33qq67ao7g67evi5jte_9.32.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.32.0_all_hkbbg5yepfmg4tn57zz6rpfdiy.crx3 | US | — | — | whitelisted |
2708 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAeYNgOt45kIIZygDCe8imw%3D | US | der | 471 b | whitelisted |
2708 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | US | der | 471 b | whitelisted |
1536 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2708 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR0tOcjGcdlkhVARHvHzj6Qwhh26wQUpI3lvnx55HAjbS4pNK0jWNz1MX8CEATDcwoBw2lgvoNh%2BUGGS3o%3D | US | der | 471 b | whitelisted |
2708 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEANzC2zymYxD1ms6GLZWt78%3D | US | der | 471 b | whitelisted |
1536 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2708 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAqx4seAxsTiwmDNn2ftPvc%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
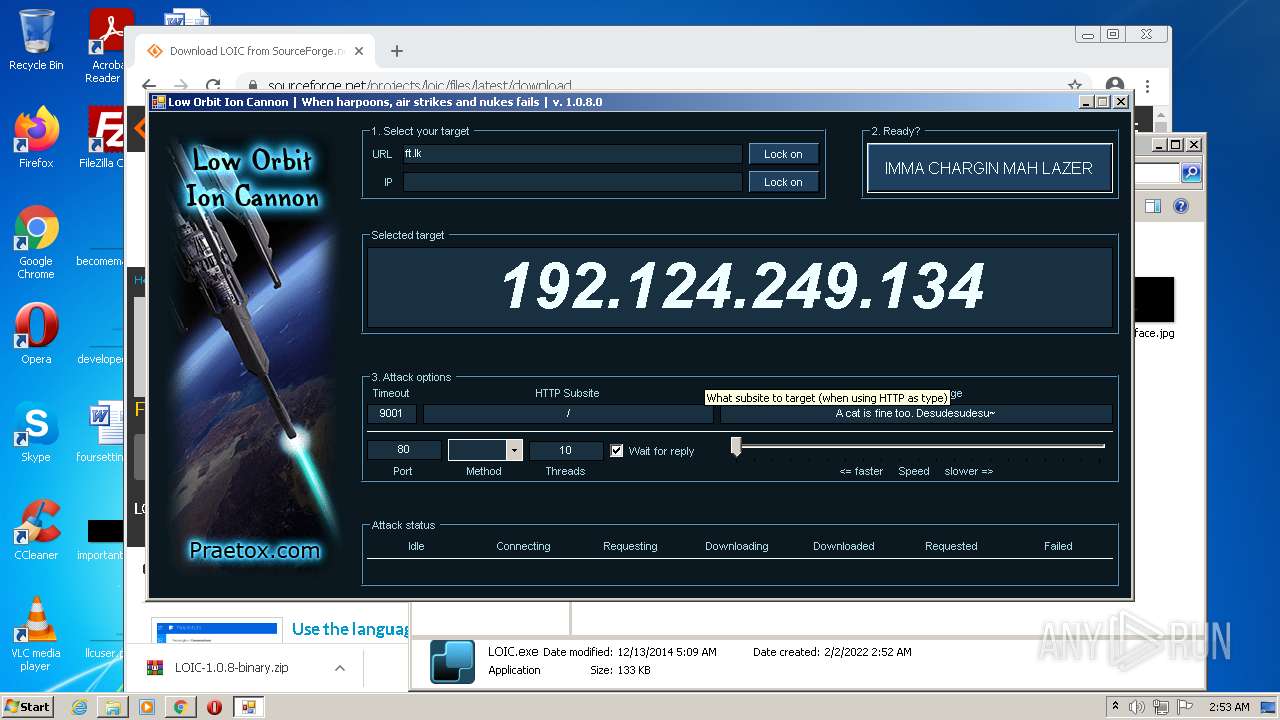
2708 | iexplore.exe | 43.224.127.40:443 | www.gov.lk | Information and Communication Technology Agency of Sri Lanka | LK | unknown |
2708 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2708 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1536 | iexplore.exe | 43.224.127.40:443 | www.gov.lk | Information and Communication Technology Agency of Sri Lanka | LK | unknown |
1536 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1536 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2708 | iexplore.exe | 13.107.5.80:443 | api.bing.com | Microsoft Corporation | US | whitelisted |
2708 | iexplore.exe | 104.92.111.166:443 | fast.com | Akamai Technologies, Inc. | NL | unknown |
2708 | iexplore.exe | 104.92.111.166:80 | fast.com | Akamai Technologies, Inc. | NL | unknown |
2708 | iexplore.exe | 63.34.115.211:443 | ichnaea-web.netflix.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gov.lk |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
fast.com |
| whitelisted |
ichnaea-web.netflix.com |
| whitelisted |
api.fast.com |
| whitelisted |
ipv4-c065-lhr004-ix.1.oca.nflxvideo.net |
| suspicious |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
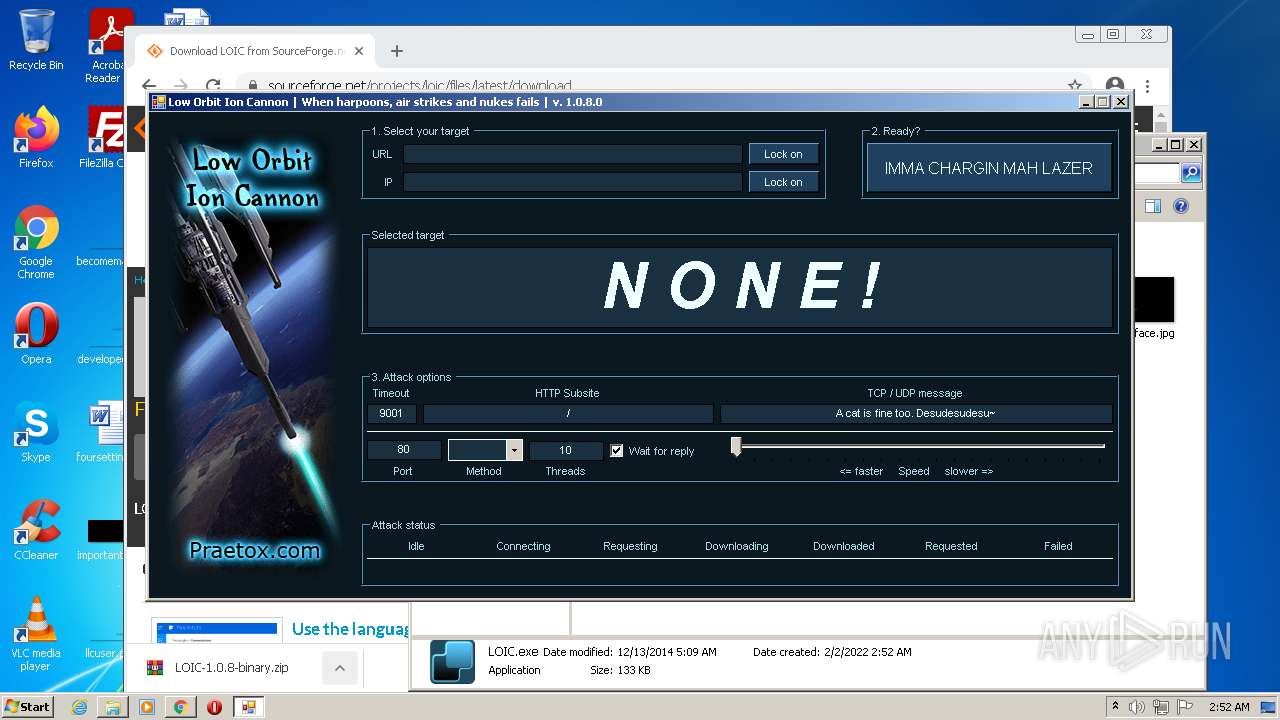
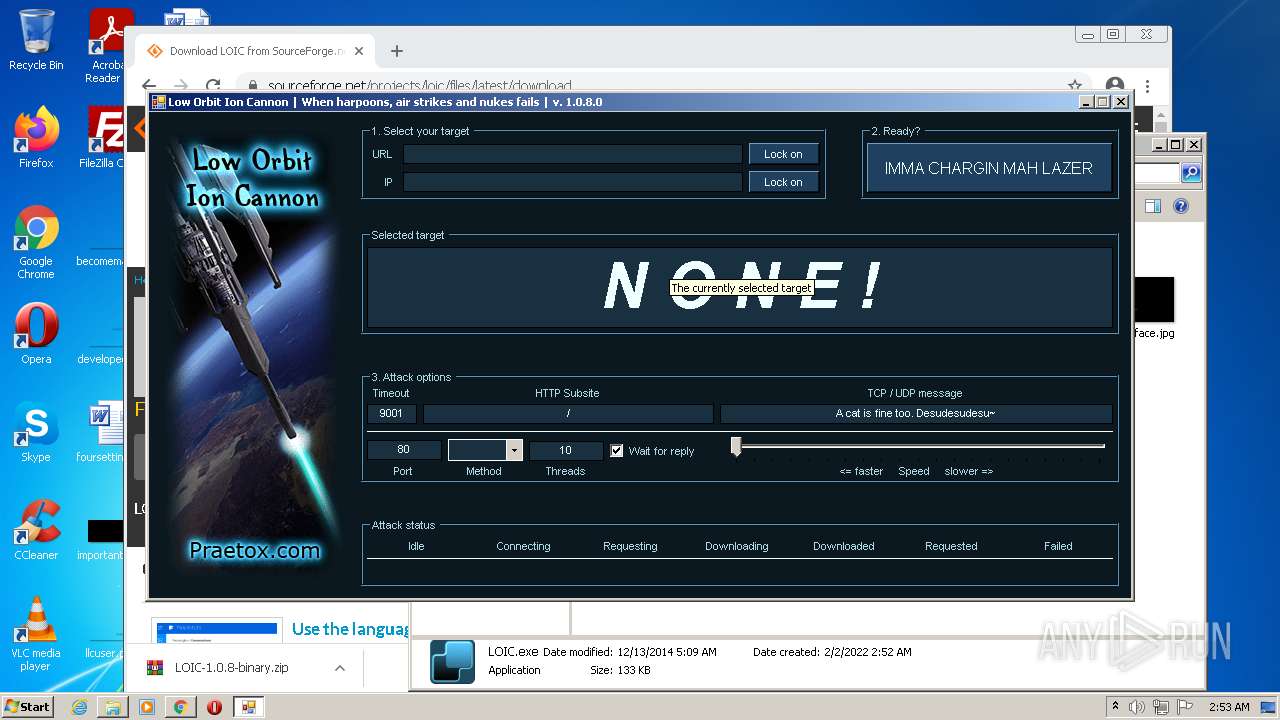
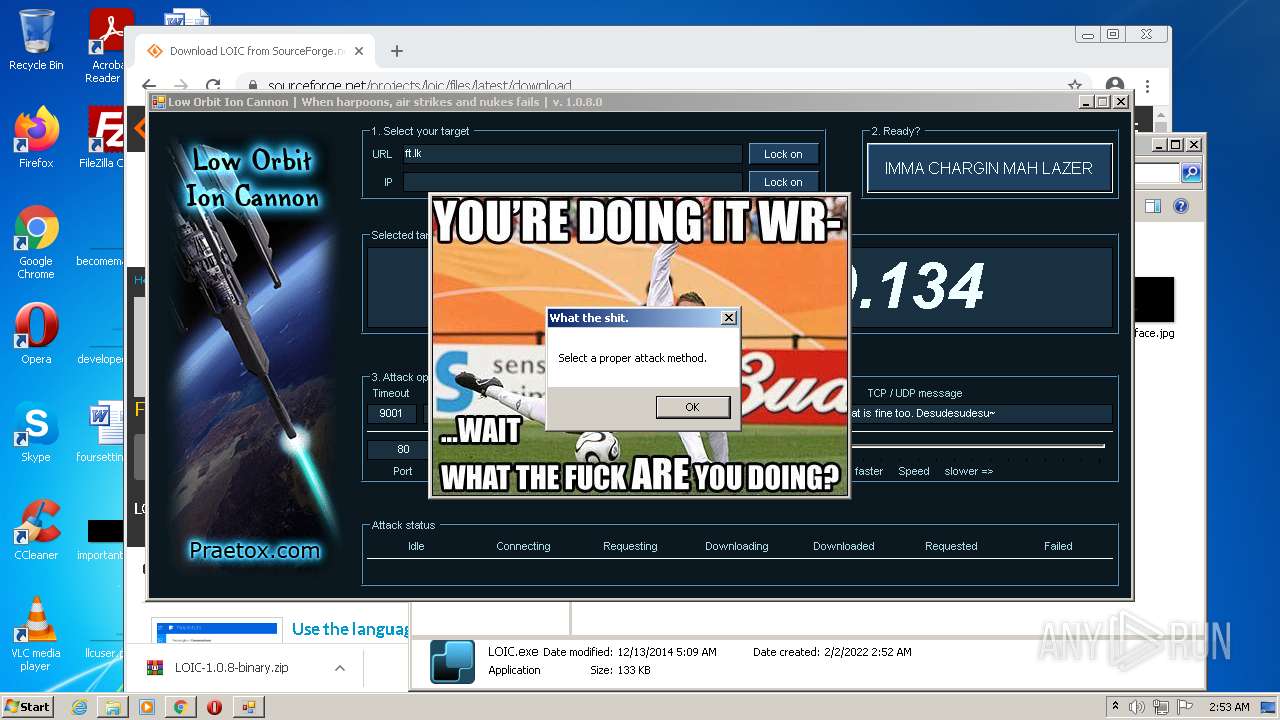
PID | Process | Class | Message |
|---|---|---|---|
2072 | LOIC.exe | Generic Protocol Command Decode | SURICATA HTTP Request line incomplete |
2072 | LOIC.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2072 | LOIC.exe | Generic Protocol Command Decode | SURICATA HTTP Request line incomplete |
2072 | LOIC.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2072 | LOIC.exe | Generic Protocol Command Decode | SURICATA HTTP Request line incomplete |
2072 | LOIC.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2072 | LOIC.exe | Generic Protocol Command Decode | SURICATA STREAM bad window update |
2072 | LOIC.exe | Generic Protocol Command Decode | SURICATA STREAM bad window update |
2072 | LOIC.exe | Generic Protocol Command Decode | SURICATA HTTP Request line incomplete |
2072 | LOIC.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
1 ETPRO signatures available at the full report