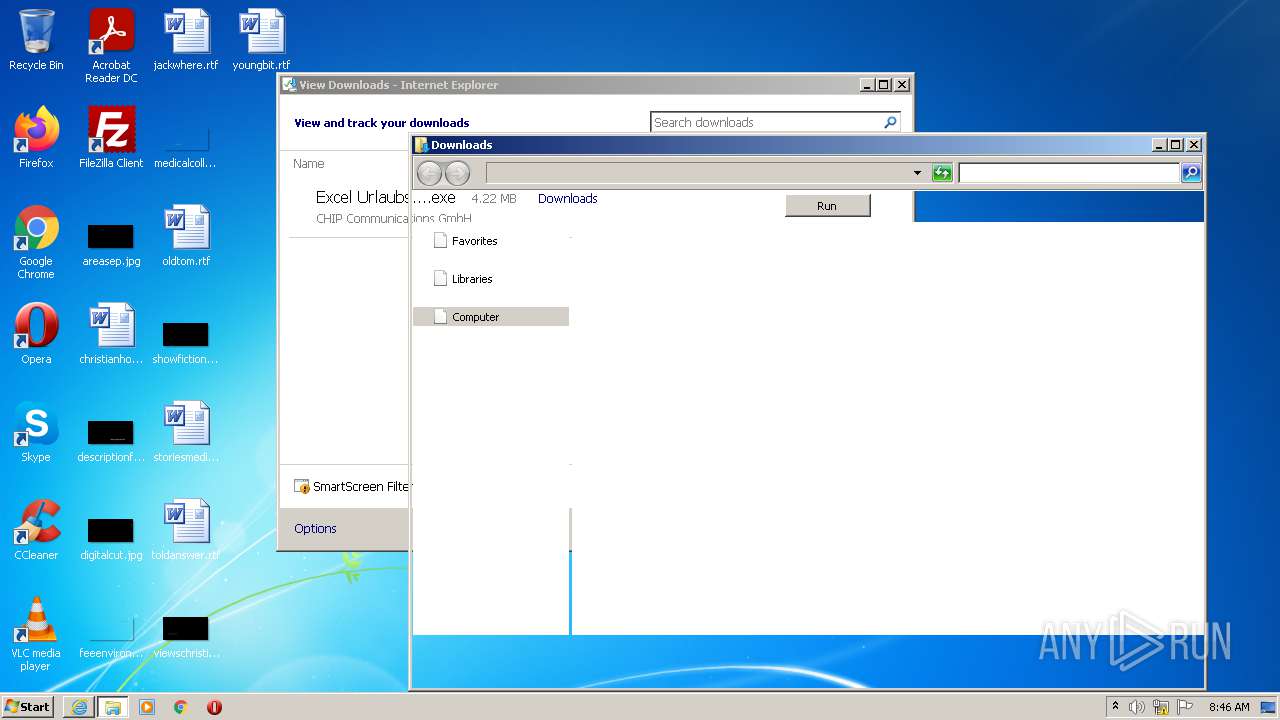
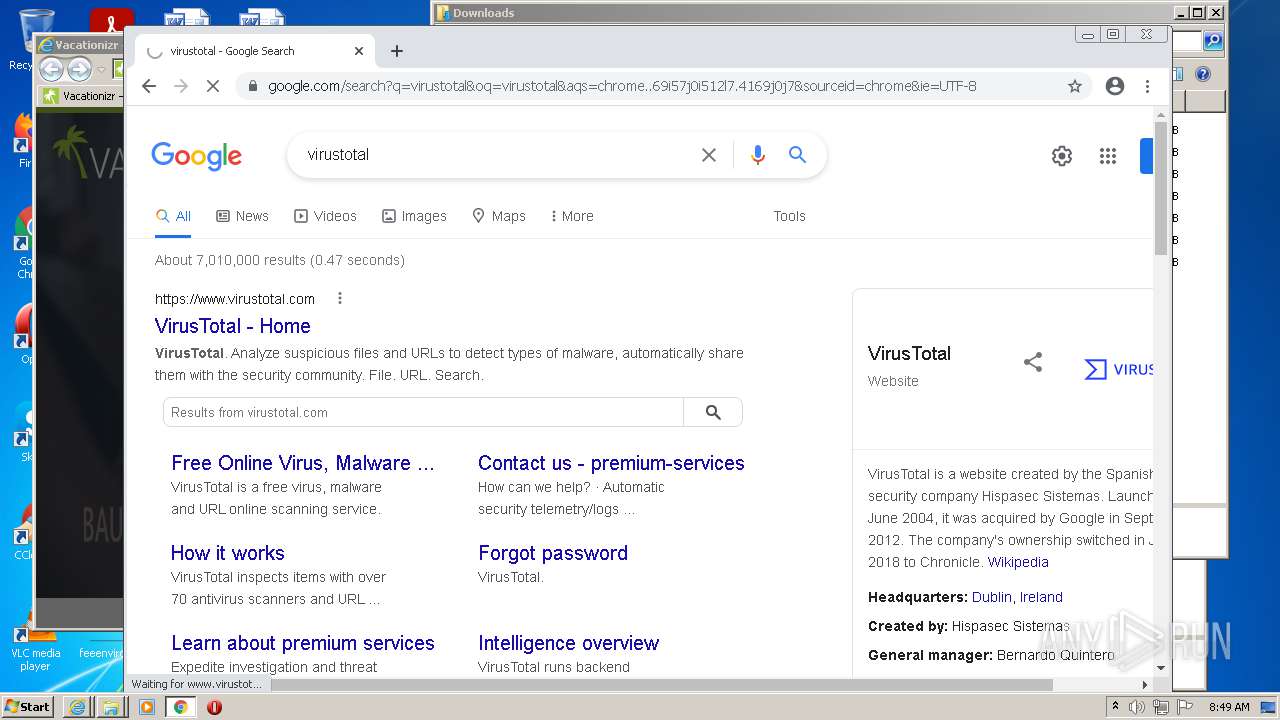
| URL: | https://chip-cluster.de/api/downloader/?lastchanged=20201006T1031000100&pid=chipderedesign&cid=183025676&euid=041c3ff7e9abb1659e6ab11e&browser=chrome&ref=&tid=&tpathid=9223_9232_75411_75413&os=windows&tname=vorlagen&ico=&proto=https://&fallbackUrl=68747470733a2f2f782e636869702e64652f696e7465726e2f646c2f3f75726c3d687474702533412532462532467777772e636869702e6465253246646f776e6c6f61647325324663315f646f776e6c6f6164735f6175737761686c5f3138333032353637382e68746d6c25334664657461696c55726c496425334431383330323536373725323664657461696c537065616b696e6755726c253344457863656c2d55726c61756273706c616e6572253236742533443136333934373637393325323676253344333630302532367325334430303139383464393439346532613732666434333463313565613663313866642665787465726e3d6e25324661266337333d3132363334303933382676313d69722d3132363334303933382b2537432b657863656c2b75726c61756273706c616e65722676363d646f776e6c6f616473267631353d446f776e6c6f6164735f55706461746573267632353d7777772e636869702e6465267636333d69722d313236333430393338267636363d687474702533412532462532467777772e636869702e6465253246646f776e6c6f616473253246457863656c2d55726c61756273706c616e65725f3138333032353637372e68746d6c267639393d30303038267633343d6e25324661267769646765746e616d653d6e25324661267075626c697368657249643d6e2532466126636f6e74656e74706172746e657249643d6e25324661267365727665723d7777772e636869702e646526706167654c61796f75743d62726f6b656e696e7374616c6c657225374365353025374368616e776973&h2o=true&source=BLUB2&v=oct2015 |
| Full analysis: | https://app.any.run/tasks/7c8b579c-9112-4caf-9cc7-bb96d1c86bfa |
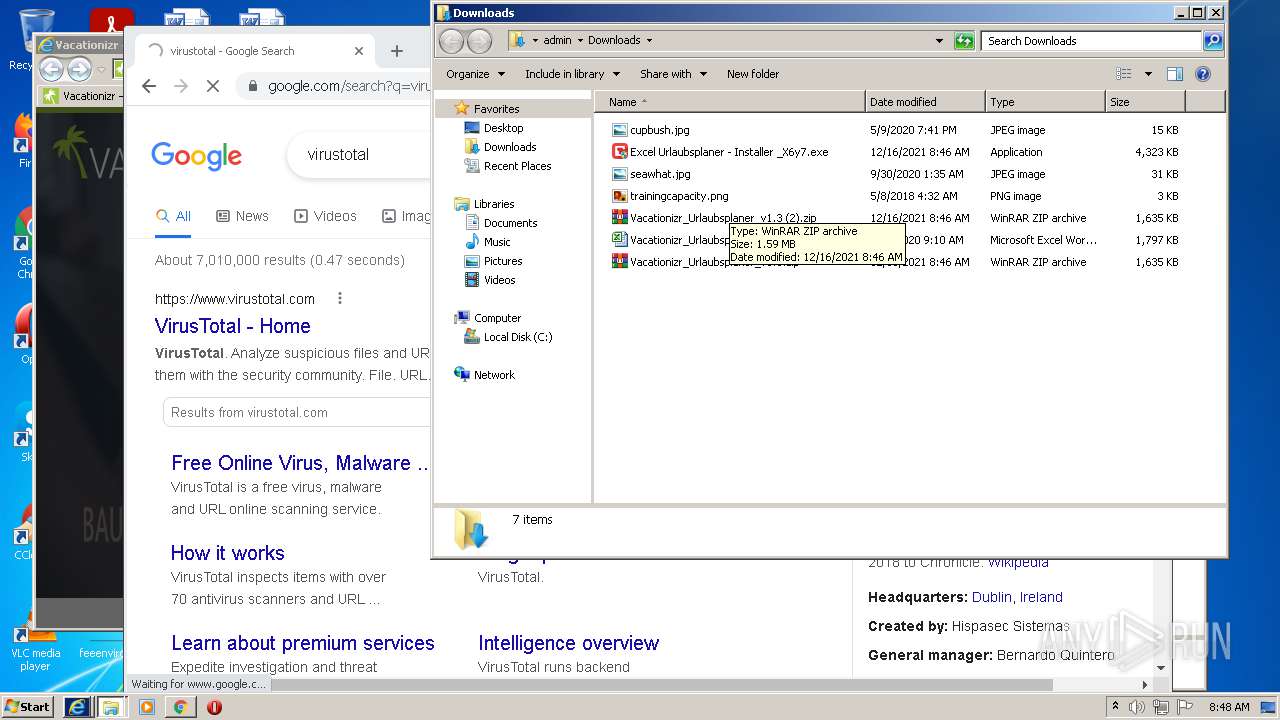
| Verdict: | Malicious activity |
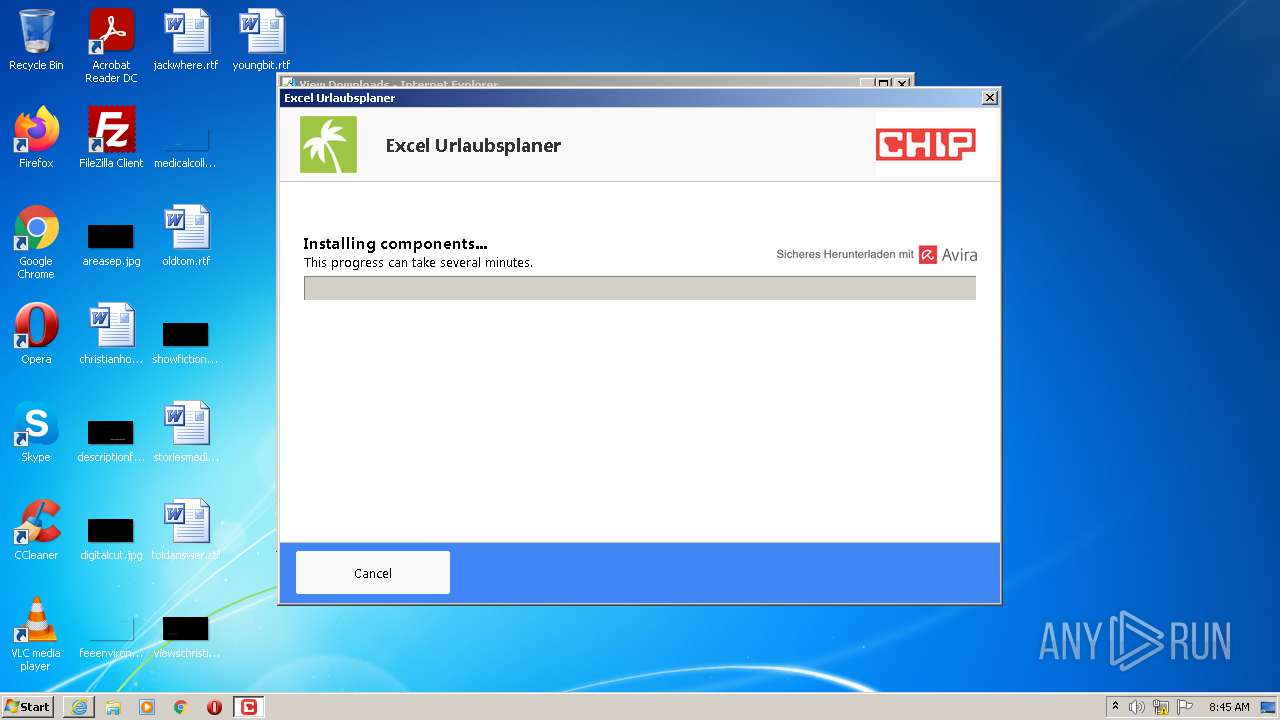
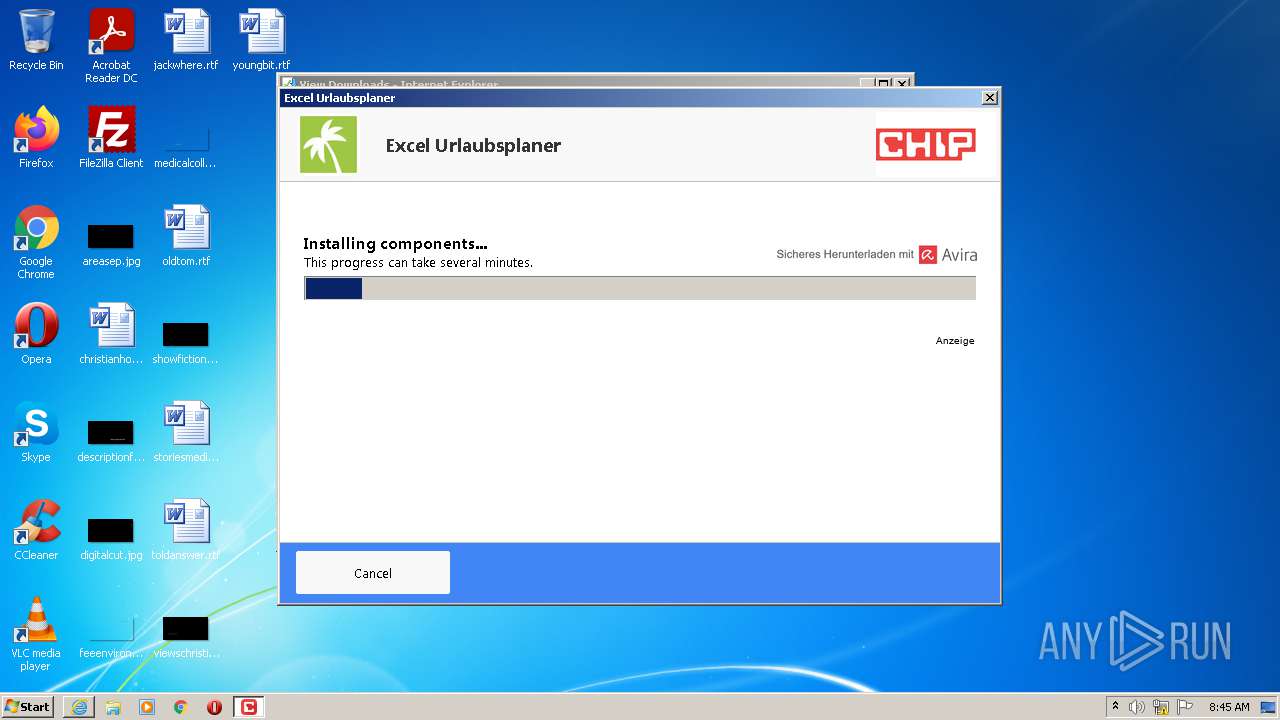
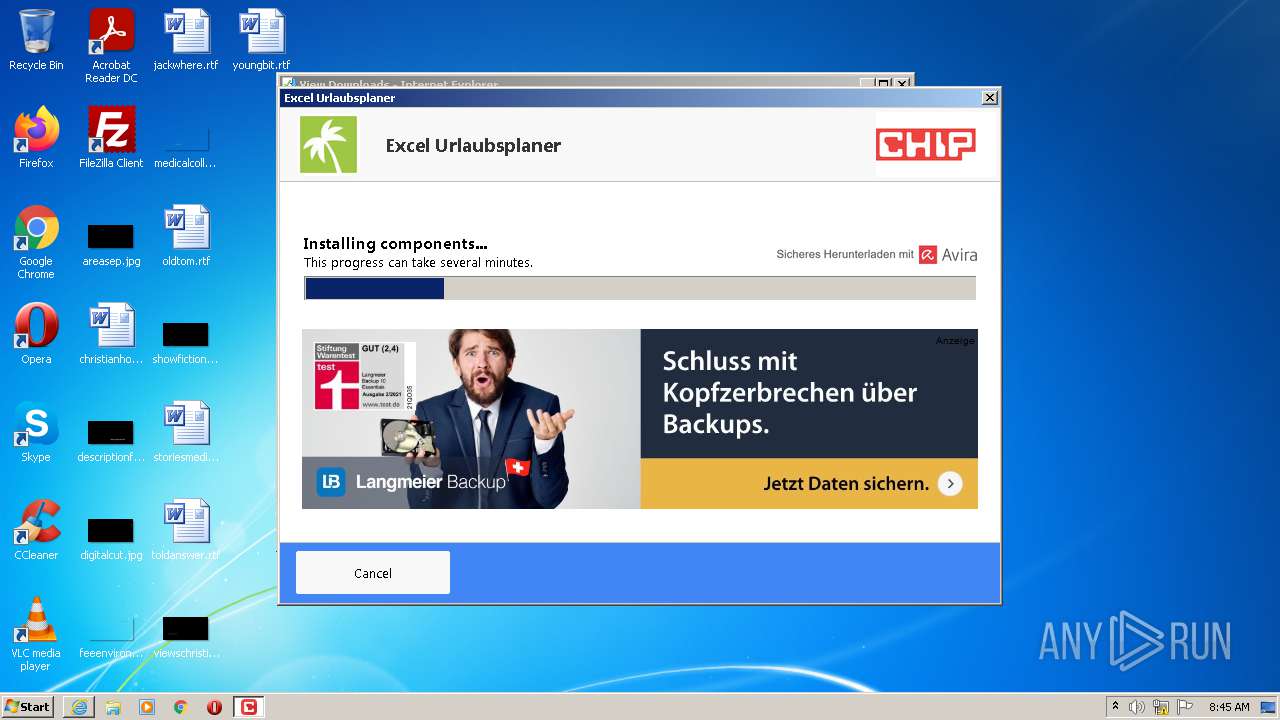
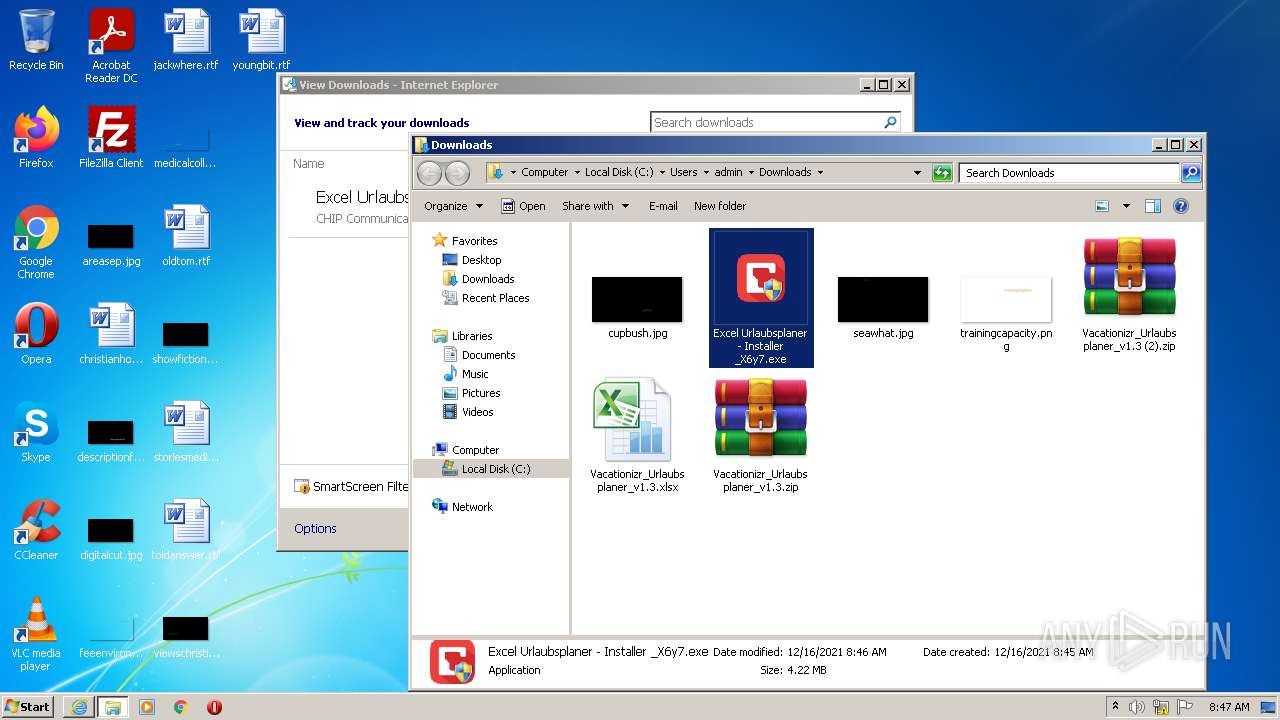
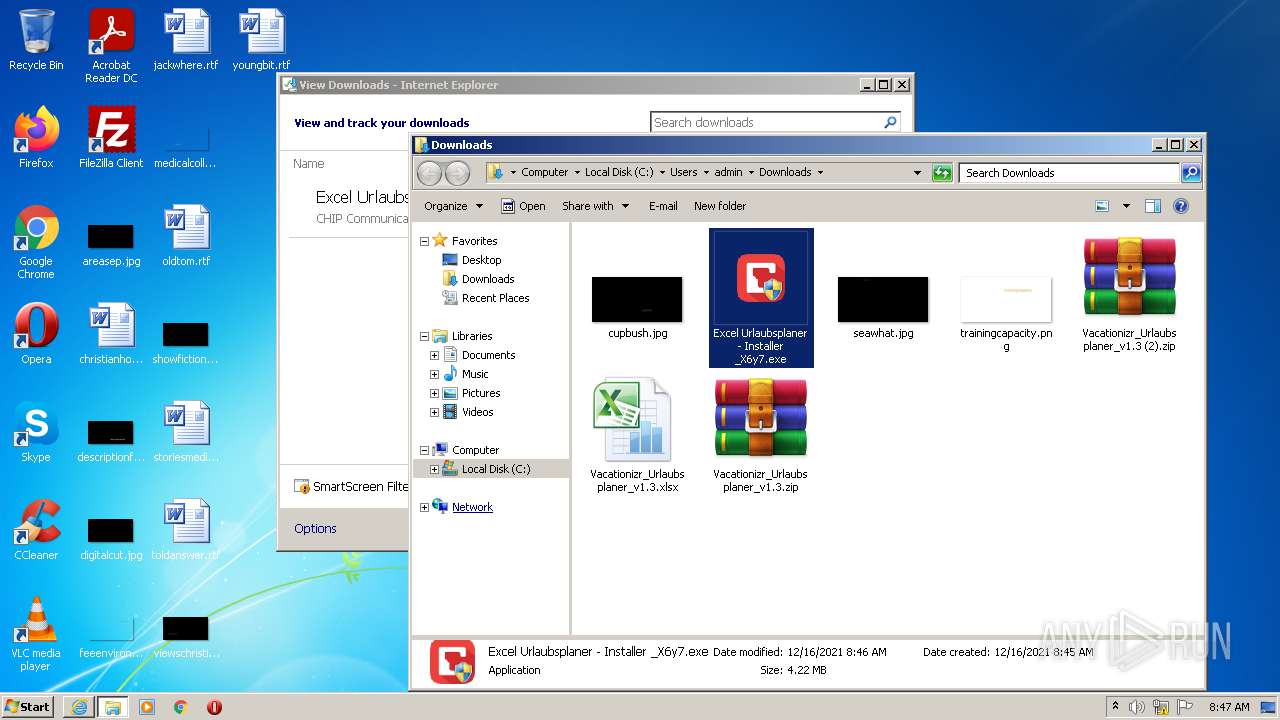
| Analysis date: | December 16, 2021, 08:45:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5AD05CC58DA2258B85AA1652B402B6E7 |
| SHA1: | 795699F12775ADA14145ED8E29B0709A3C53F28A |
| SHA256: | 8B10F56B04221C62EE546D6571B2EC8ED84006E5CA3453F7BF1B2CB350A169D6 |
| SSDEEP: | 24:24tba+M0iFXrjyn1Mnb0GRXbA8cnVoTelwohUFRHulpSXbgRXbpZAPBOXbzfeK:jbaRZFbEVGRZcVvlwTHuekR1ZoBOeK |
MALICIOUS
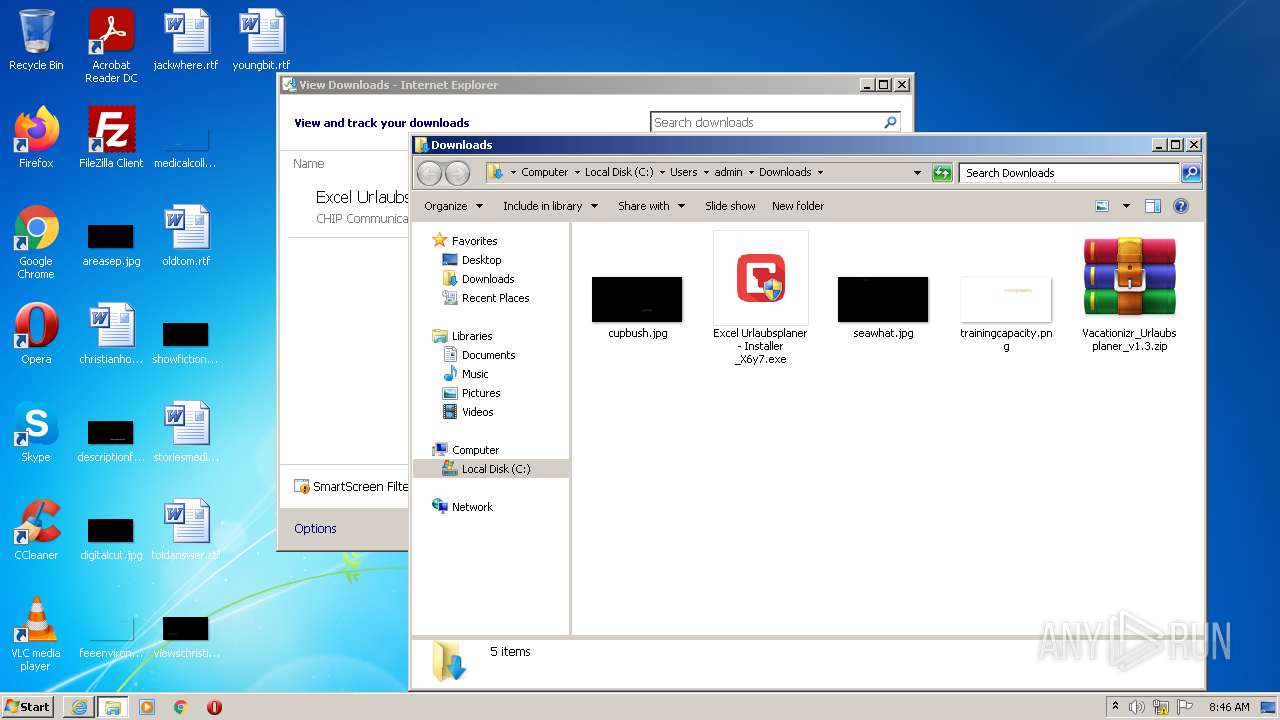
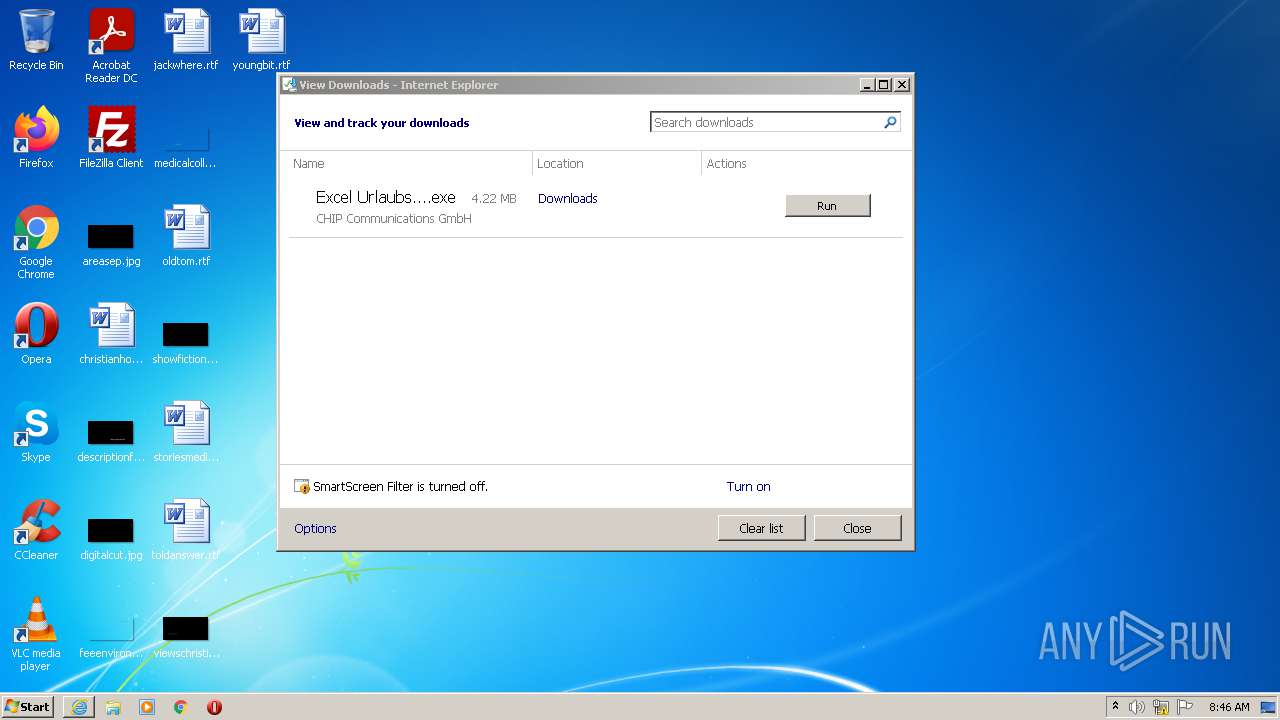
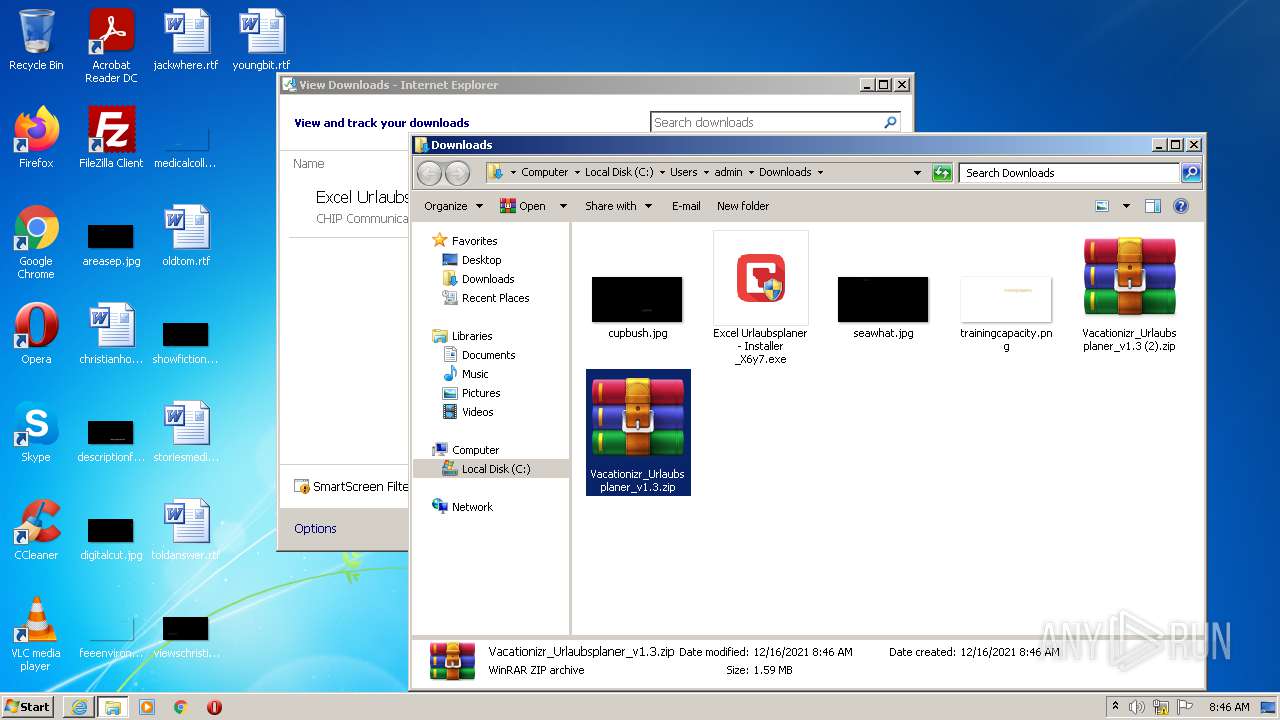
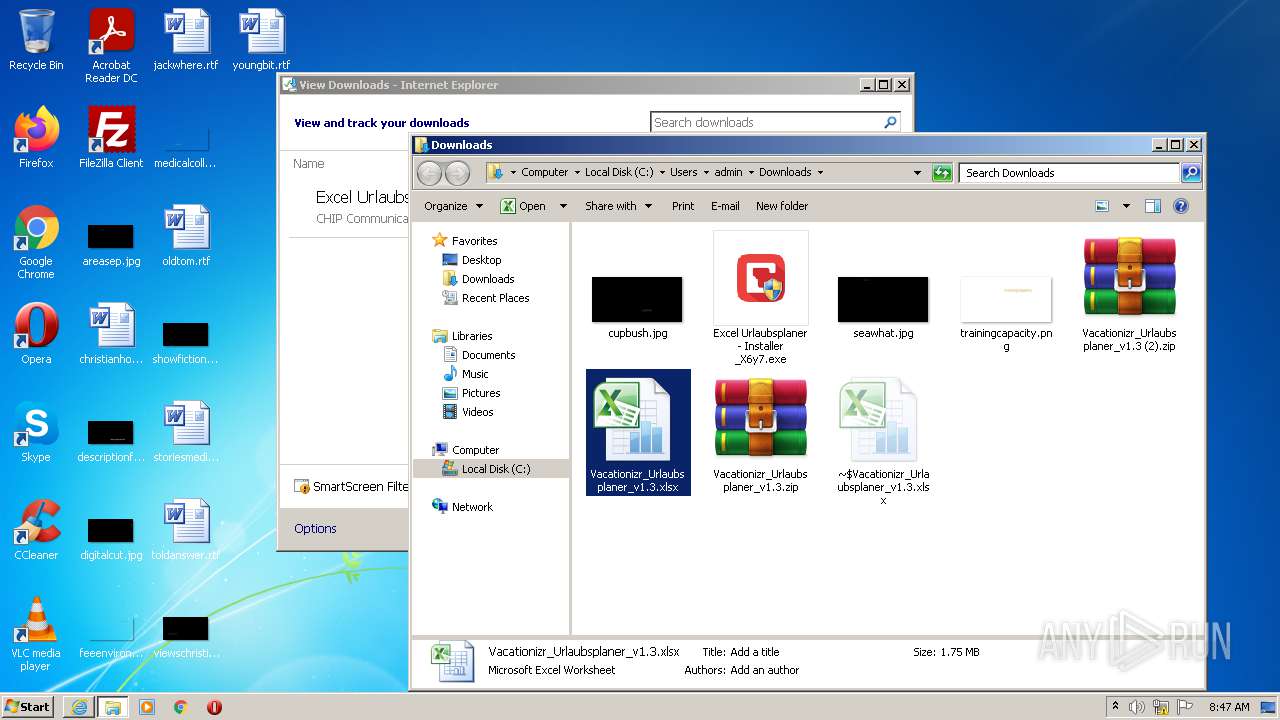
Application was dropped or rewritten from another process
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 3564)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 456)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 4020)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 2816)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 3804)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 3656)
Changes settings of System certificates
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 456)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3964)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 4020)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 456)
- iexplore.exe (PID: 1172)
- iexplore.exe (PID: 2052)
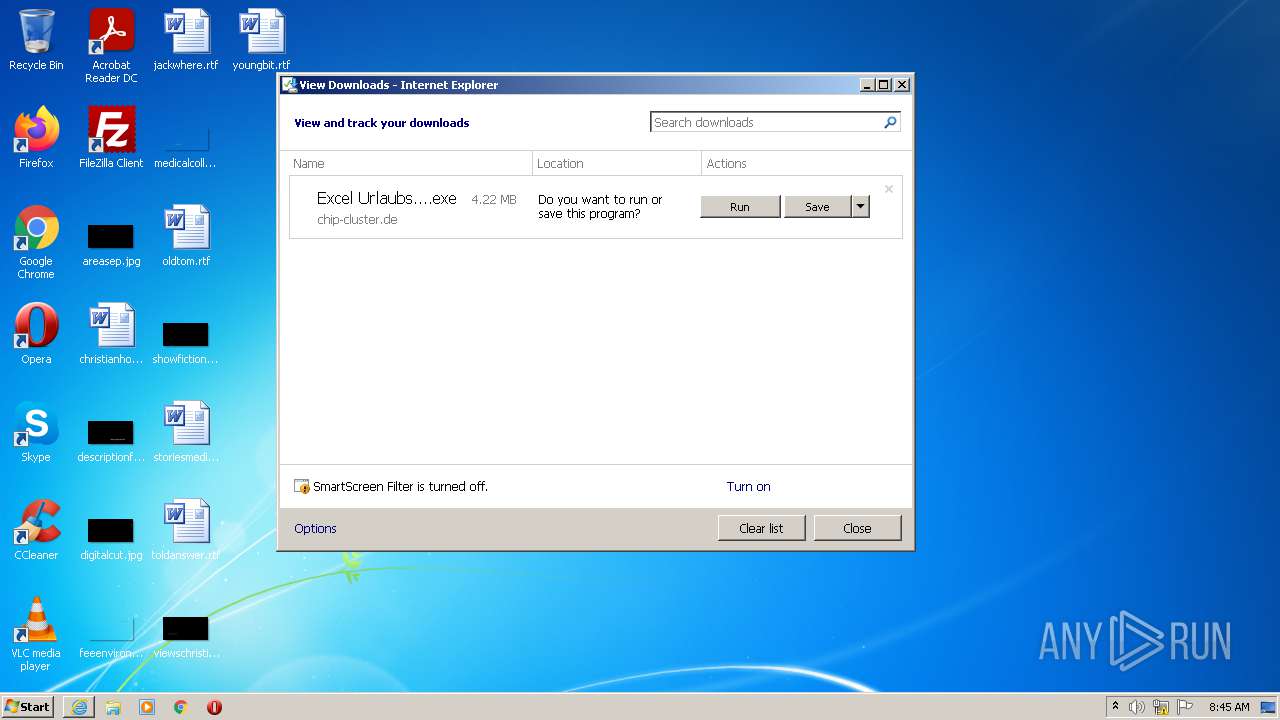
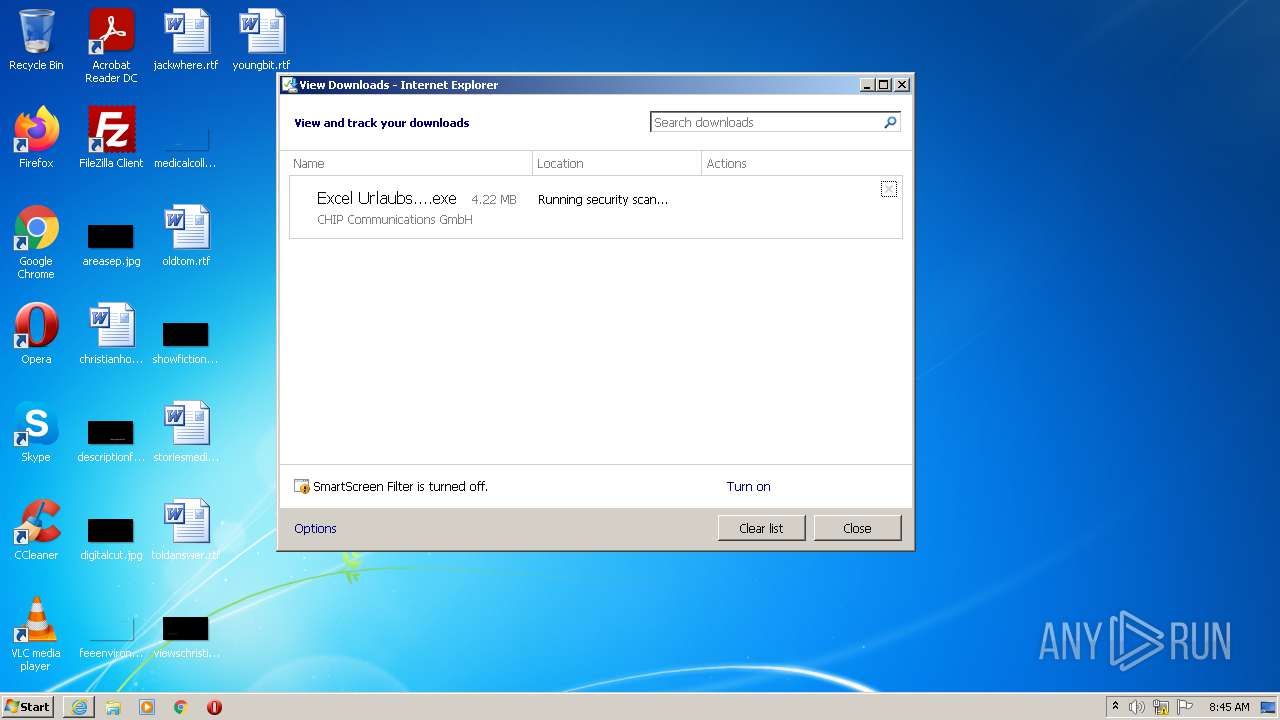
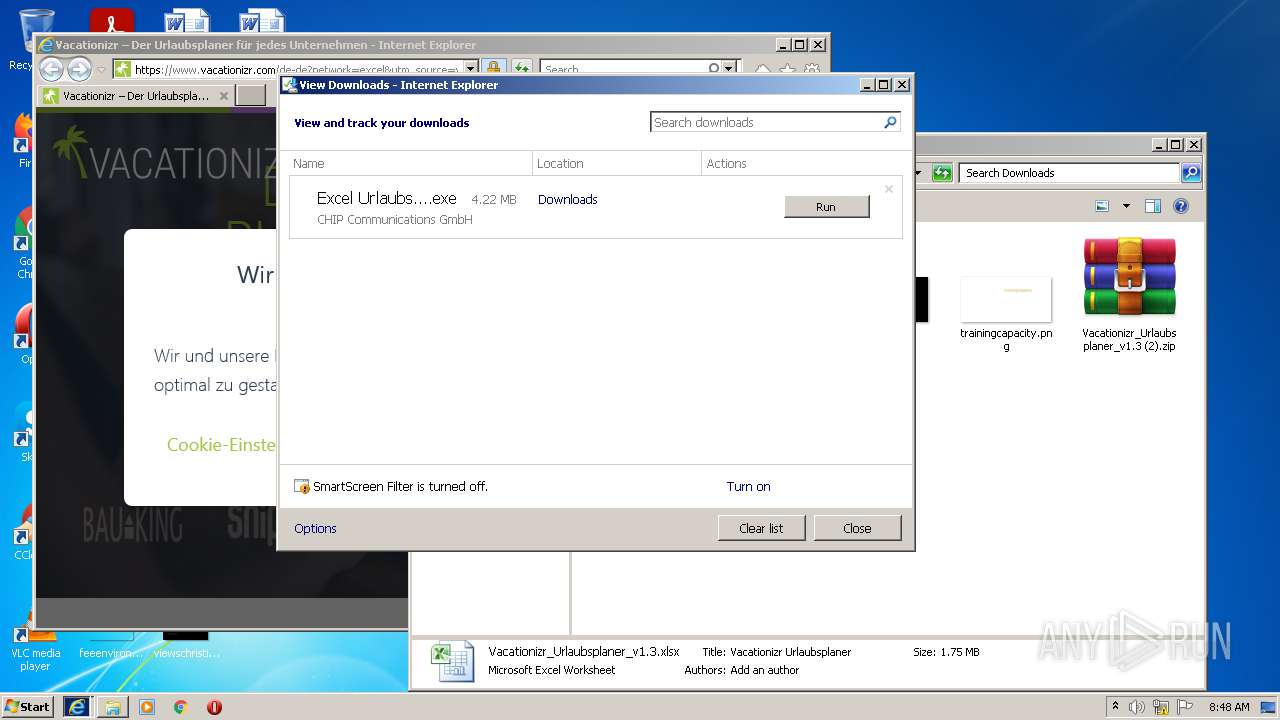
Executable content was dropped or overwritten
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 3964)
Drops a file with a compile date too recent
- iexplore.exe (PID: 3964)
- iexplore.exe (PID: 2956)
Reads the computer name
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 456)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 4020)
- WinRAR.exe (PID: 624)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 3656)
Executed via COM
- explorer.exe (PID: 3248)
- explorer.exe (PID: 2168)
Reads default file associations for system extensions
- explorer.exe (PID: 3248)
- explorer.exe (PID: 2168)
Checks supported languages
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 456)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 4020)
- WinRAR.exe (PID: 624)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 3656)
Reads internet explorer settings
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 456)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 4020)
Reads the date of Windows installation
- explorer.exe (PID: 2168)
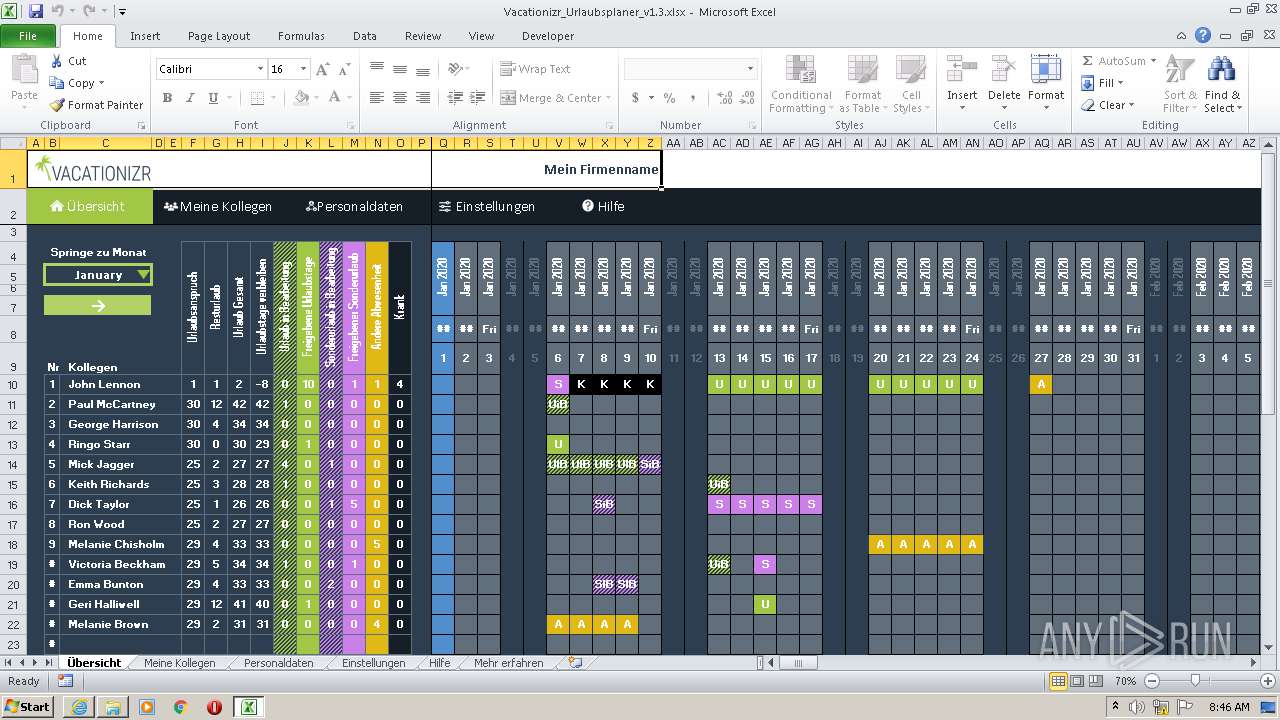
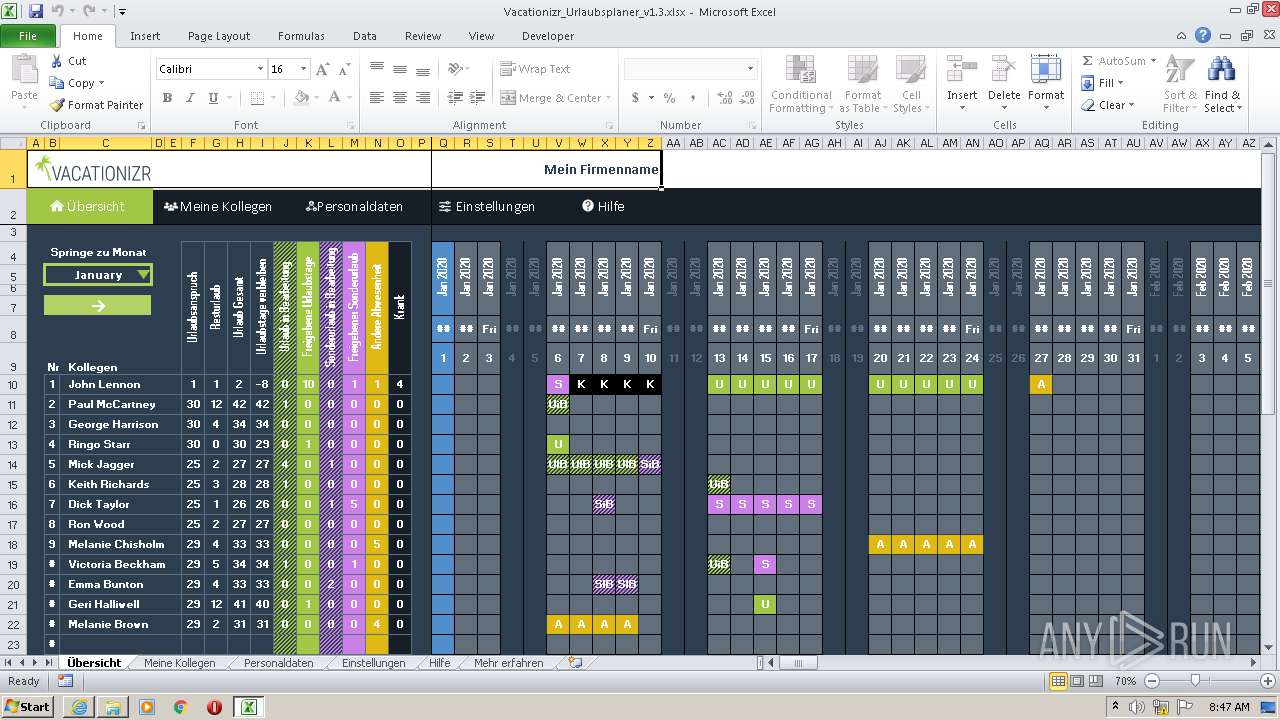
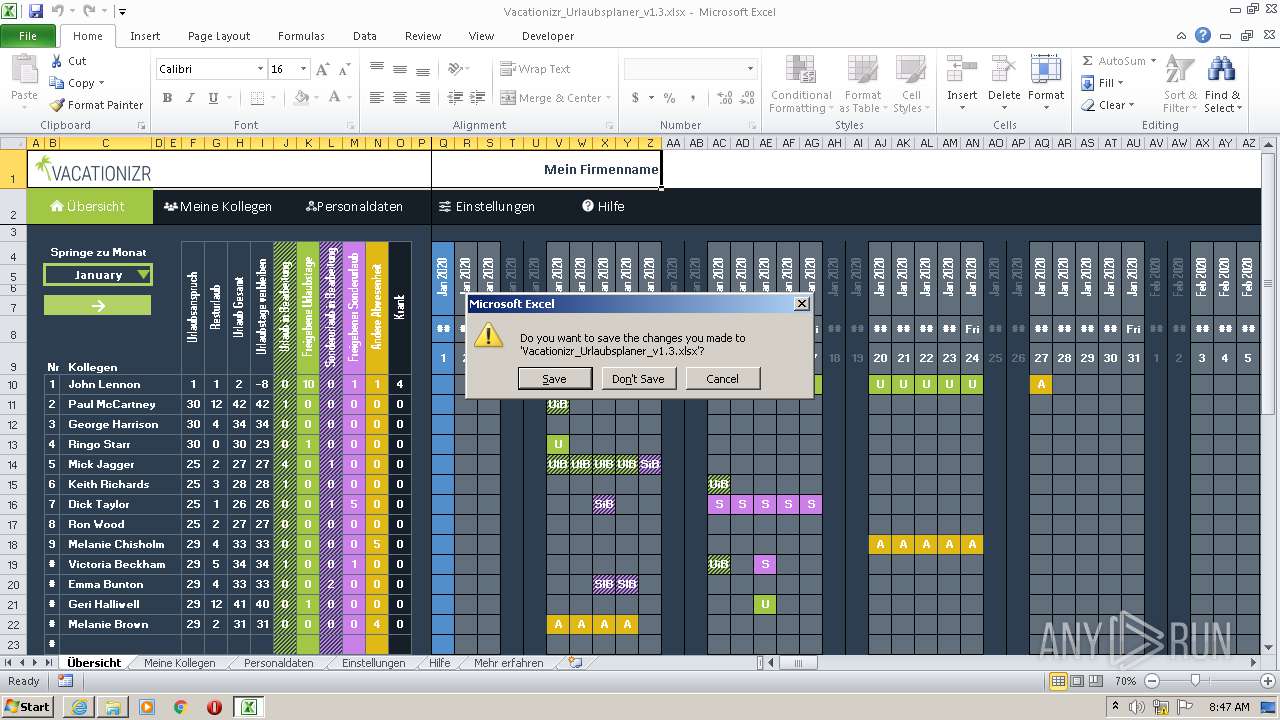
Starts Microsoft Office Application
- explorer.exe (PID: 2168)
Adds / modifies Windows certificates
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 456)
Searches for installed software
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 3656)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 456)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 4020)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3960)
INFO
Checks supported languages
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 3964)
- explorer.exe (PID: 3040)
- explorer.exe (PID: 3248)
- explorer.exe (PID: 3736)
- explorer.exe (PID: 2168)
- EXCEL.EXE (PID: 1928)
- EXCEL.EXE (PID: 1108)
- iexplore.exe (PID: 1172)
- iexplore.exe (PID: 2052)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 408)
- chrome.exe (PID: 3008)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 1528)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 2940)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 1120)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 3808)
- chrome.exe (PID: 2516)
- chrome.exe (PID: 2680)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 2828)
- chrome.exe (PID: 2520)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 2204)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 3284)
- chrome.exe (PID: 3152)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 1852)
- chrome.exe (PID: 2636)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 2504)
- chrome.exe (PID: 3984)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 888)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 3332)
Changes internet zones settings
- iexplore.exe (PID: 2956)
Checks Windows Trust Settings
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 3964)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 4020)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 456)
- EXCEL.EXE (PID: 1108)
- iexplore.exe (PID: 2052)
- iexplore.exe (PID: 1172)
Reads internet explorer settings
- iexplore.exe (PID: 3964)
- EXCEL.EXE (PID: 1108)
- iexplore.exe (PID: 2052)
- iexplore.exe (PID: 1172)
Reads settings of System Certificates
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 3964)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 456)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 4020)
- Excel Urlaubsplaner - Installer _X6y7.exe (PID: 3656)
- EXCEL.EXE (PID: 1108)
- iexplore.exe (PID: 2052)
- chrome.exe (PID: 2332)
- iexplore.exe (PID: 1172)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2956)
Reads the computer name
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 3964)
- explorer.exe (PID: 3040)
- explorer.exe (PID: 3248)
- explorer.exe (PID: 3736)
- explorer.exe (PID: 2168)
- EXCEL.EXE (PID: 1928)
- EXCEL.EXE (PID: 1108)
- iexplore.exe (PID: 1172)
- iexplore.exe (PID: 2052)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 3008)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 2828)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 3284)
Application launched itself
- iexplore.exe (PID: 2956)
- chrome.exe (PID: 3960)
Changes settings of System certificates
- iexplore.exe (PID: 2956)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2956)
Reads the date of Windows installation
- iexplore.exe (PID: 2956)
- chrome.exe (PID: 3564)
Creates files in the user directory
- iexplore.exe (PID: 2956)
- EXCEL.EXE (PID: 1928)
- EXCEL.EXE (PID: 1108)
- iexplore.exe (PID: 2052)
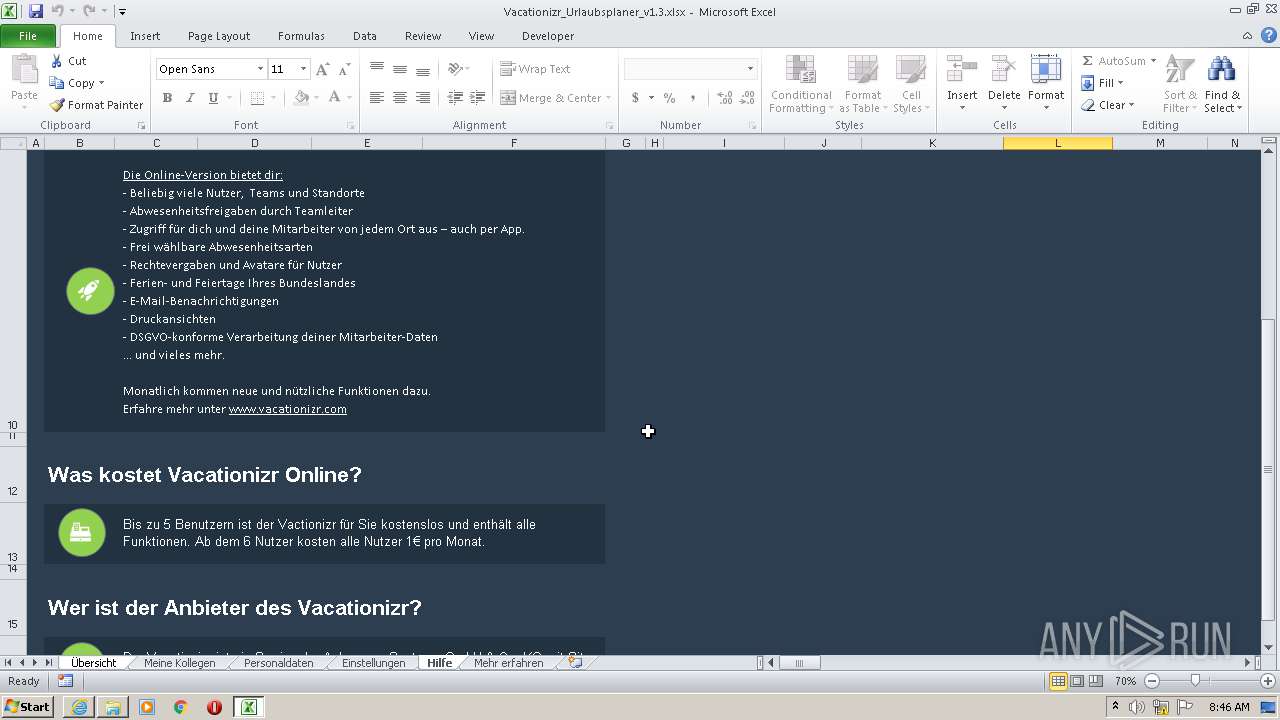
Reads Microsoft Office registry keys
- explorer.exe (PID: 2168)
- EXCEL.EXE (PID: 1928)
- EXCEL.EXE (PID: 1108)
Reads Microsoft Outlook installation path
- EXCEL.EXE (PID: 1928)
- EXCEL.EXE (PID: 1108)
Manual execution by user
- chrome.exe (PID: 3960)
Reads the hosts file
- chrome.exe (PID: 3960)
- chrome.exe (PID: 2332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
115
Monitored processes
60
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6de1d988,0x6de1d998,0x6de1d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
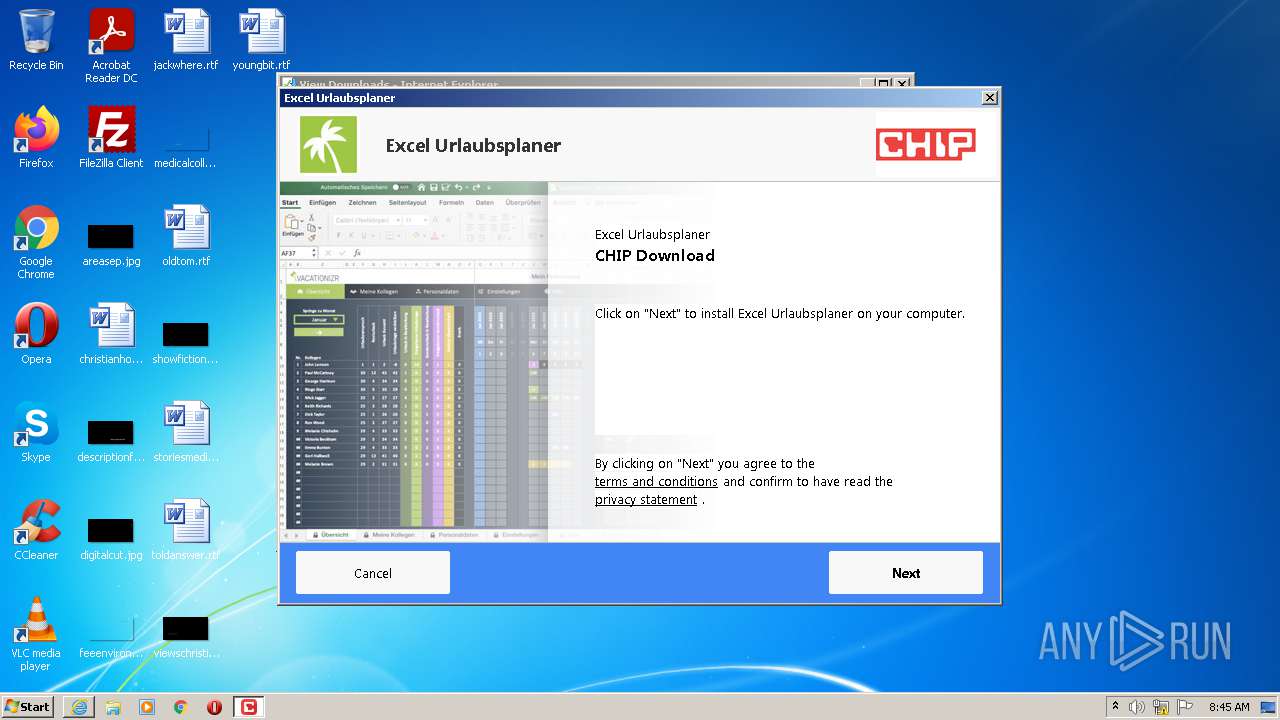
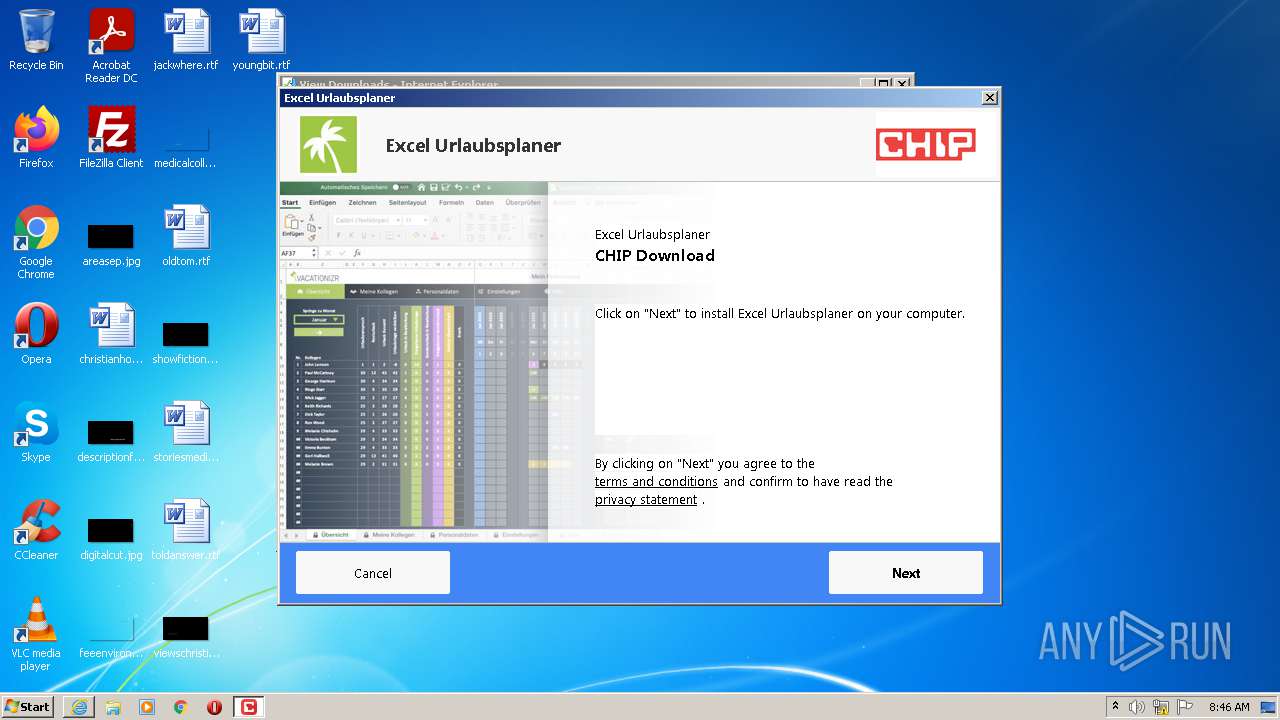
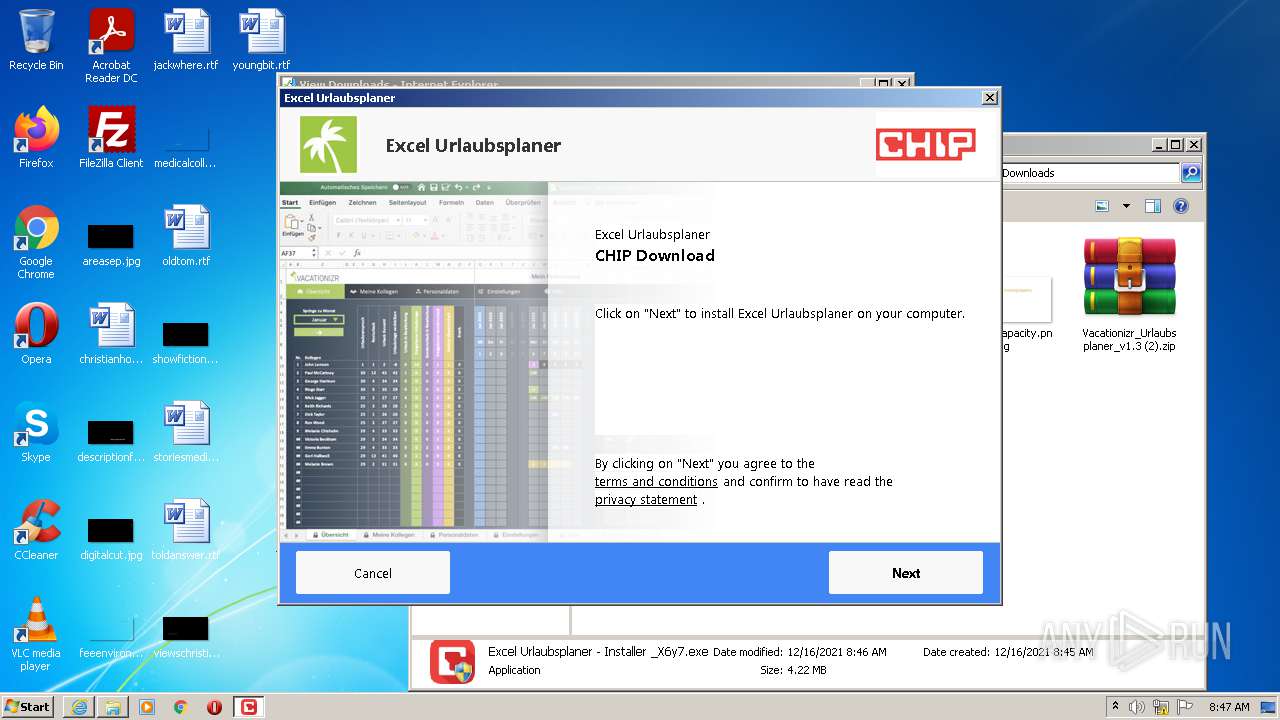
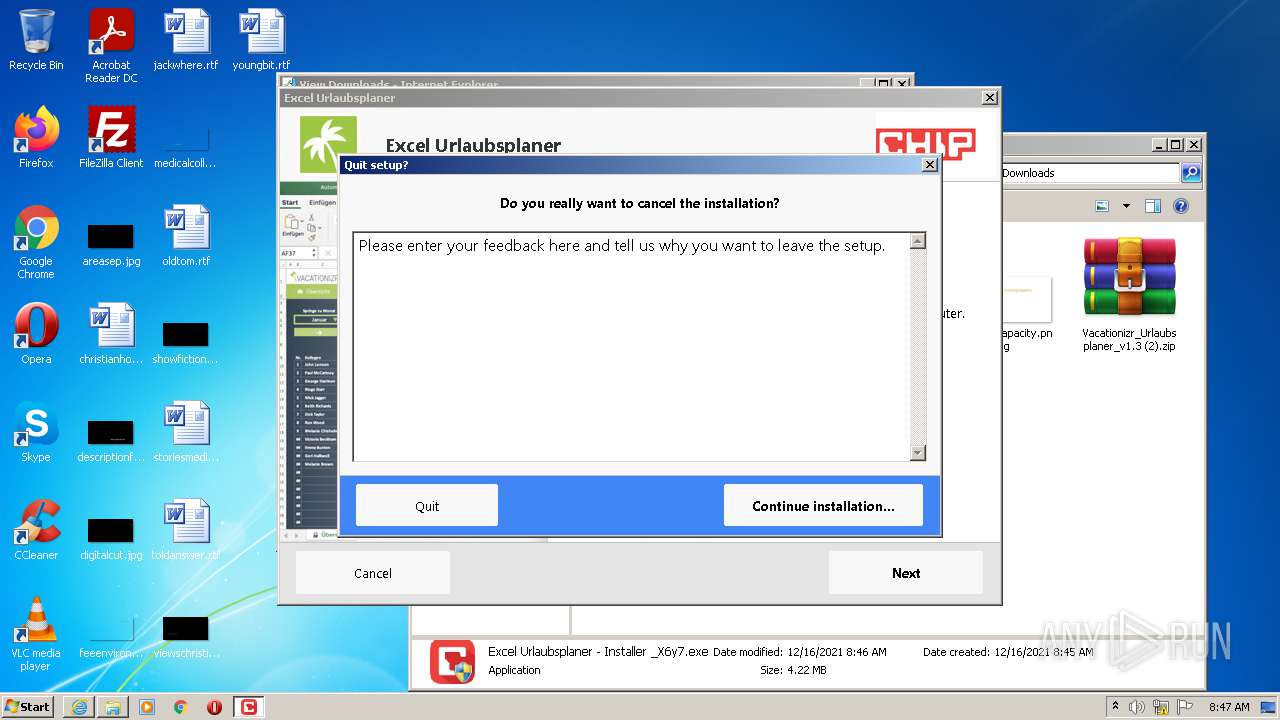
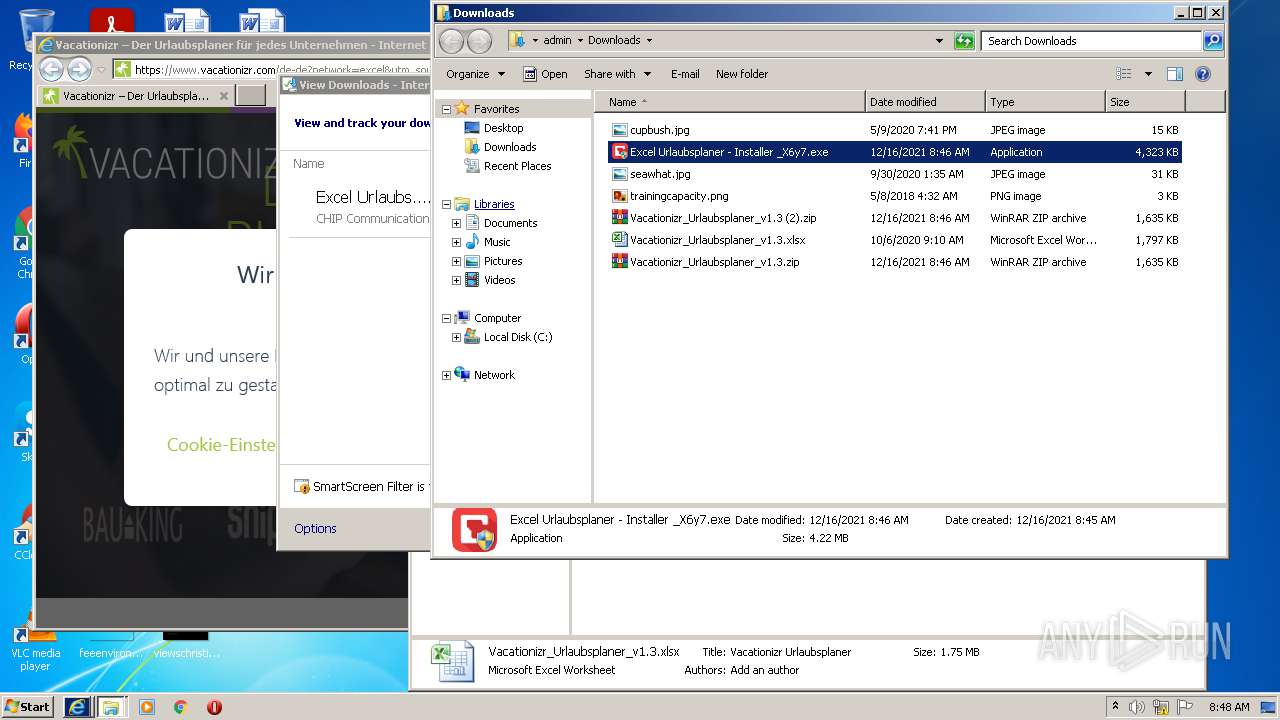
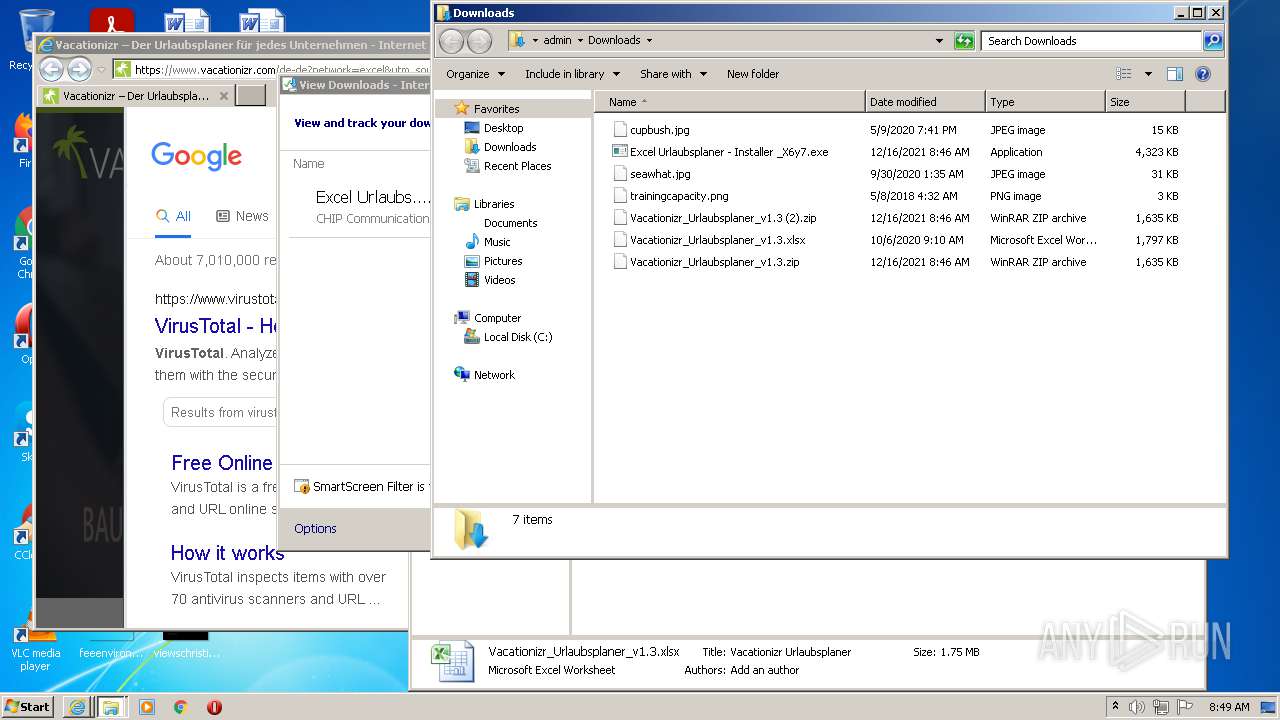
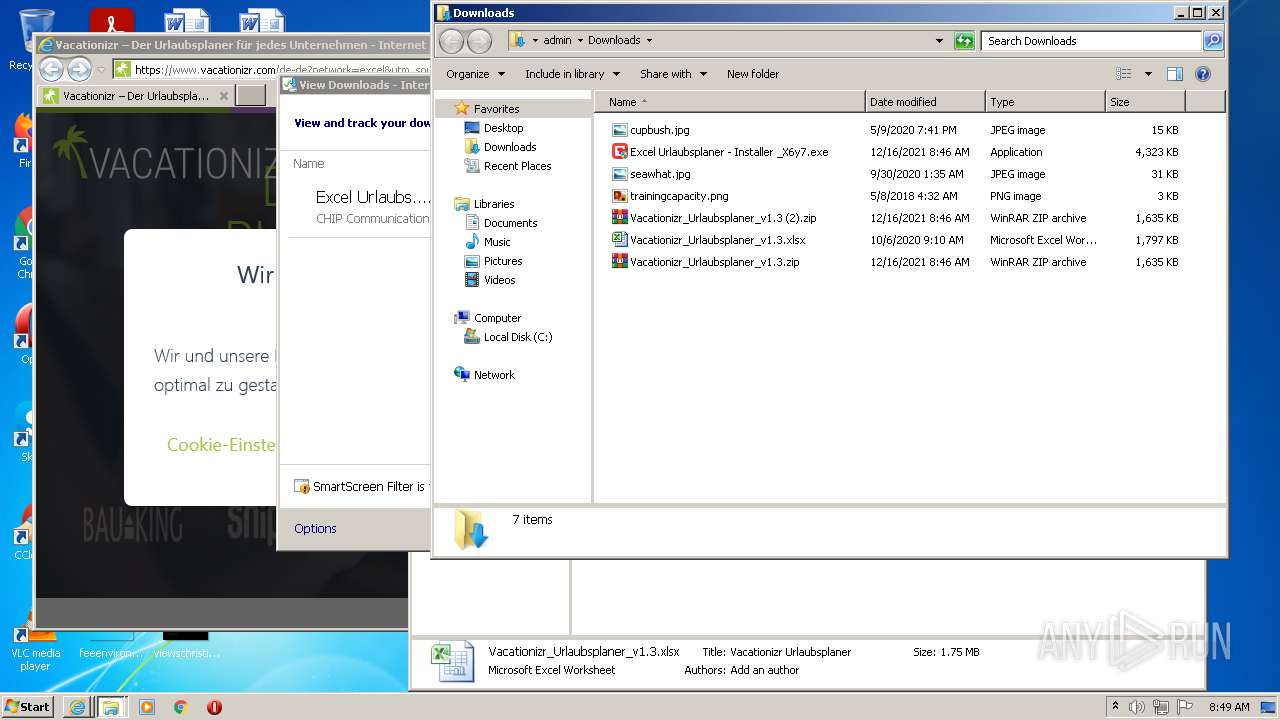
| 456 | "C:\Users\admin\Downloads\Excel Urlaubsplaner - Installer _X6y7.exe" | C:\Users\admin\Downloads\Excel Urlaubsplaner - Installer _X6y7.exe | iexplore.exe | ||||||||||||
User: admin Company: CHIP Digital GmbH Integrity Level: HIGH Description: CHIP Secured Installer Exit code: 0 Version: 1.0.8.0 Modules
| |||||||||||||||
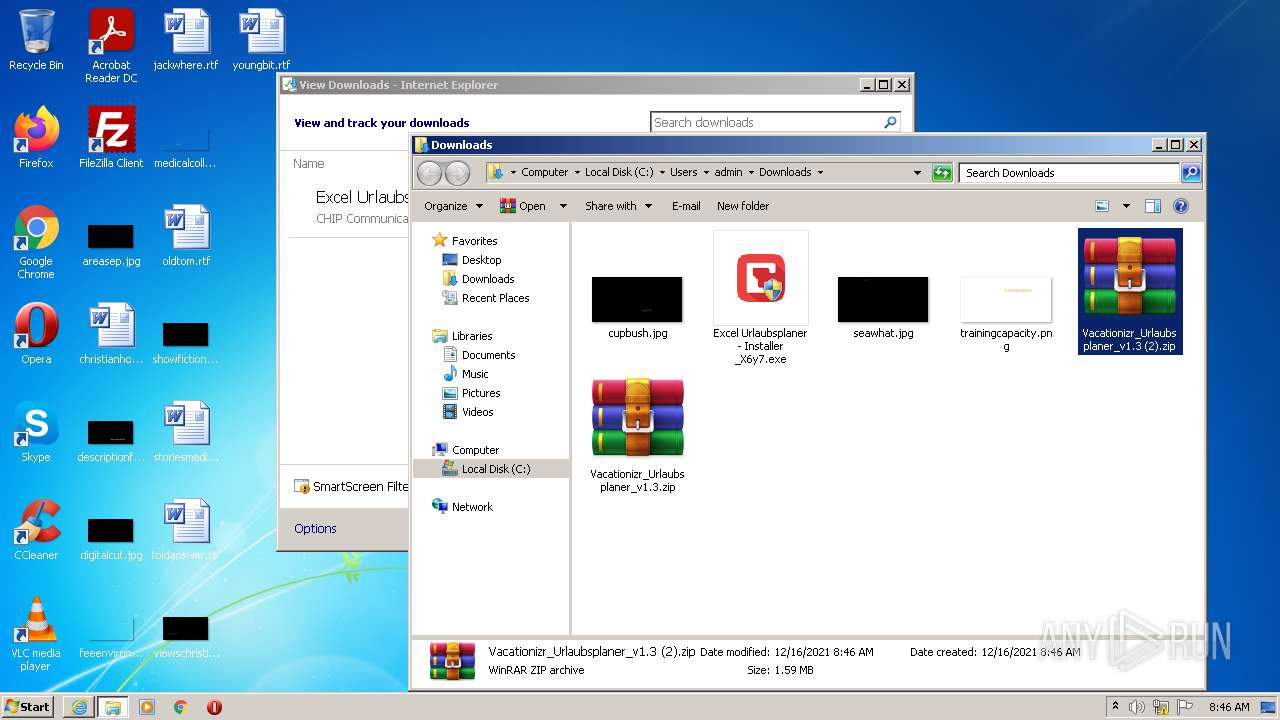
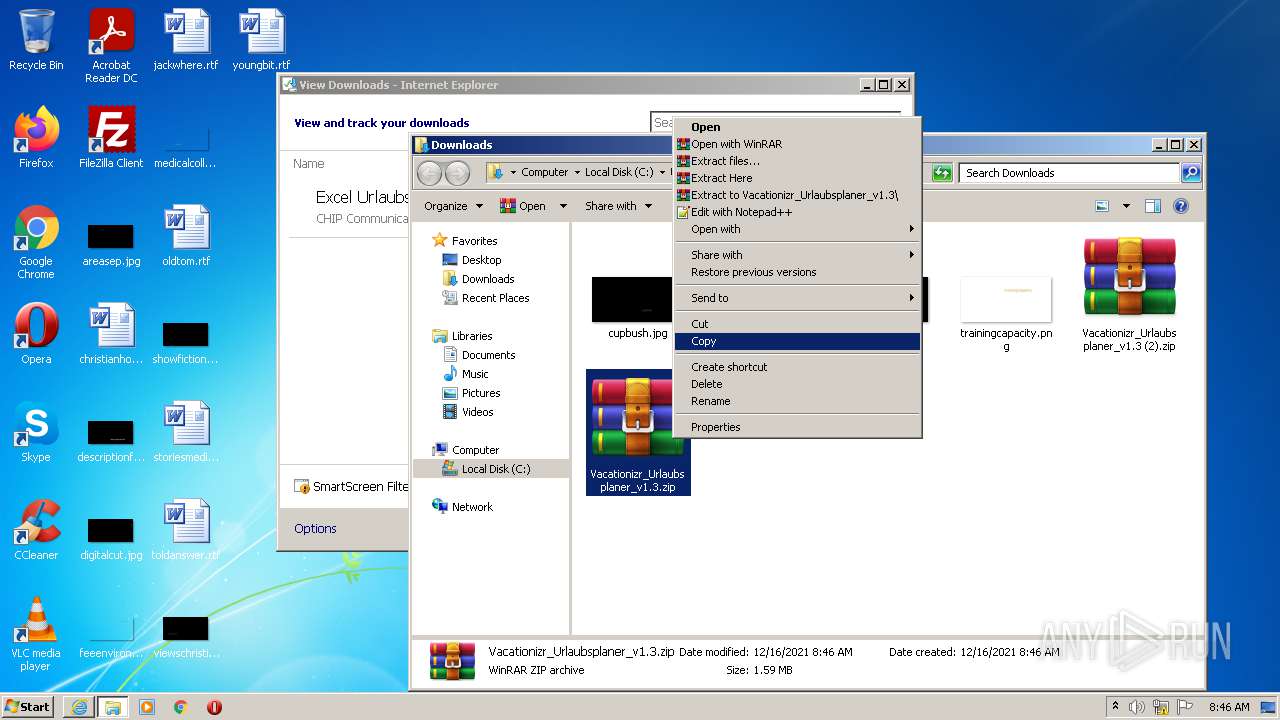
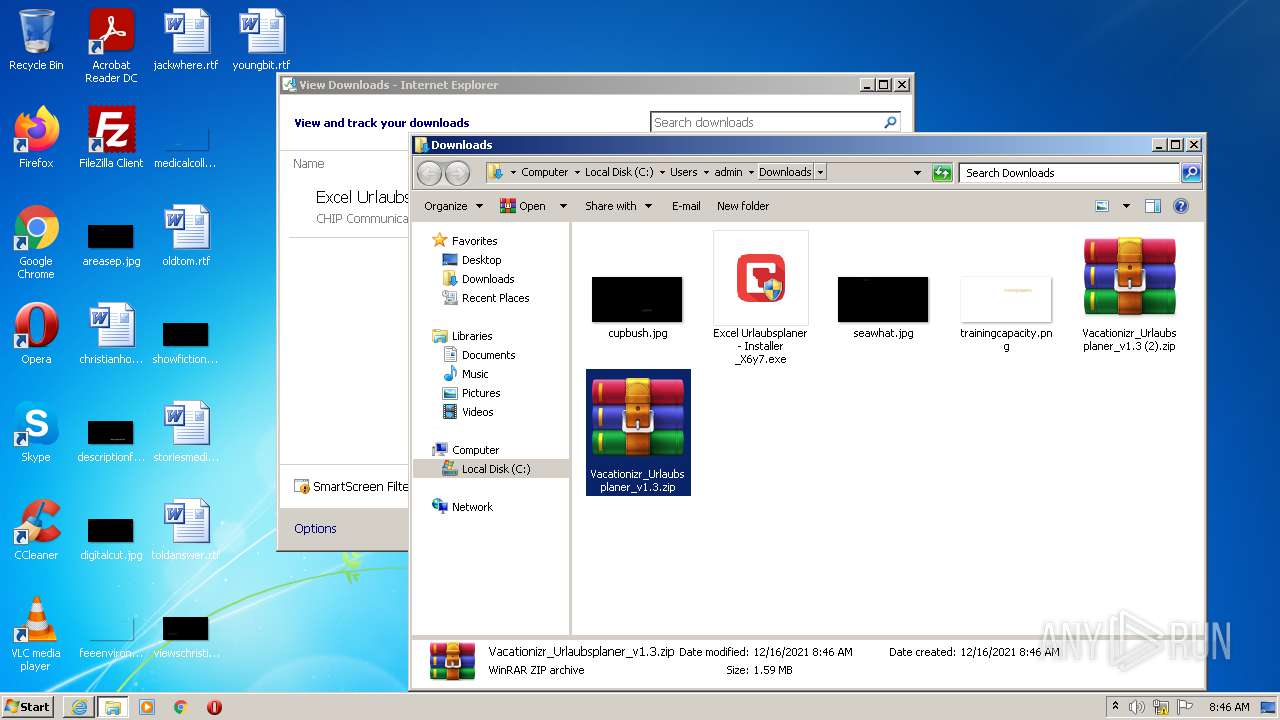
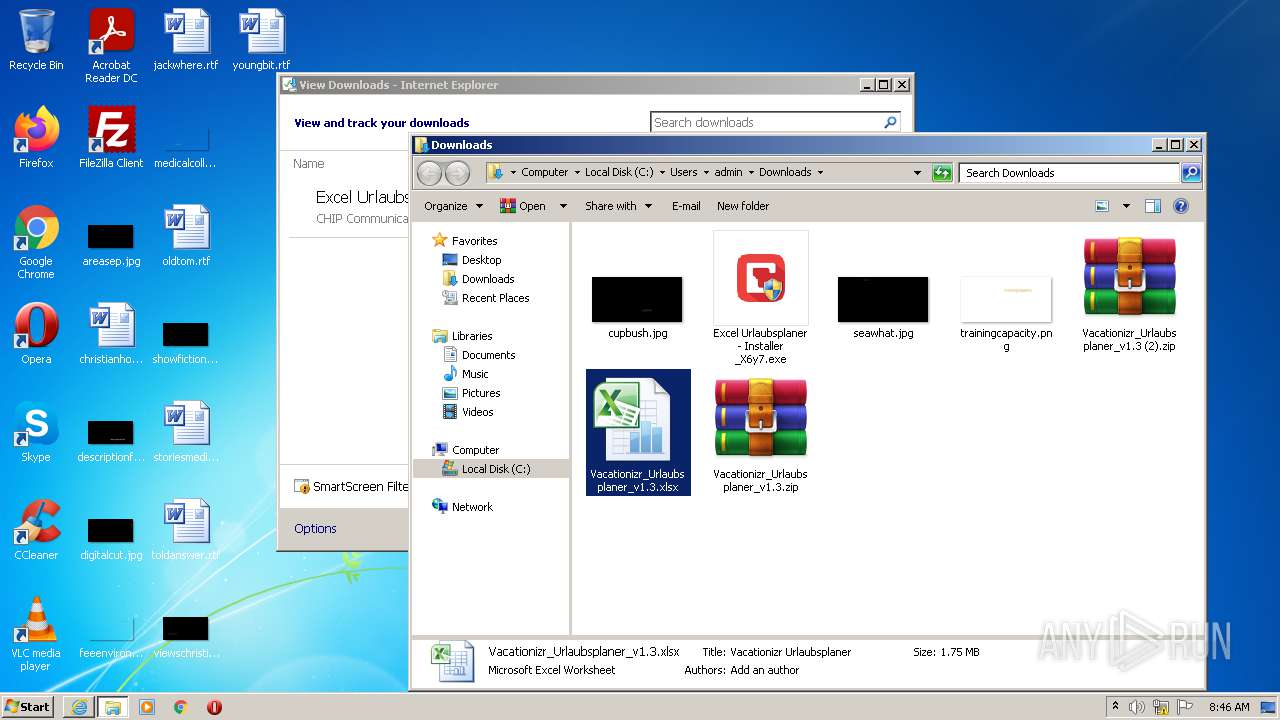
| 624 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Vacationizr_Urlaubsplaner_v1.3.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5493305633981573401,17641741636731656982,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4372 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,5493305633981573401,17641741636731656982,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4304 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,5493305633981573401,17641741636731656982,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2928 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,5493305633981573401,17641741636731656982,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2956 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,5493305633981573401,17641741636731656982,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3464 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
95 429
Read events
94 455
Write events
931
Delete events
43
Modification events
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 965729888 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30929497 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30929497 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
198
Text files
284
Unknown types
72
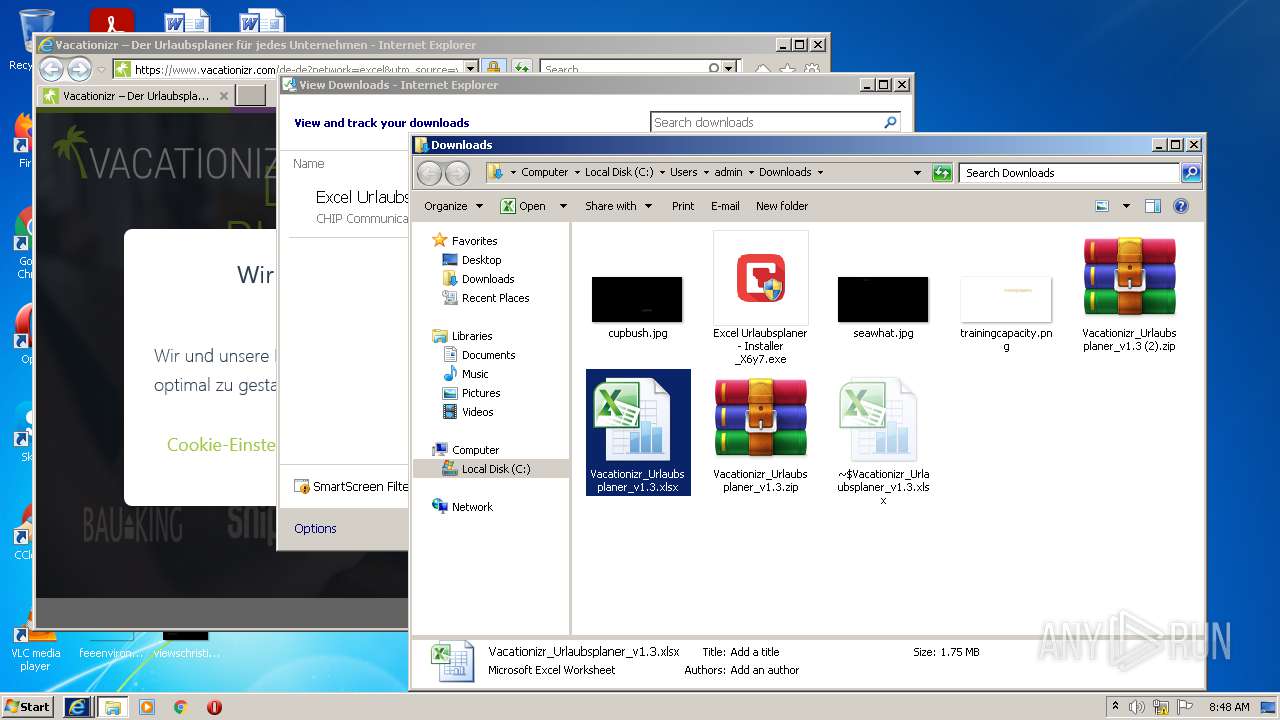
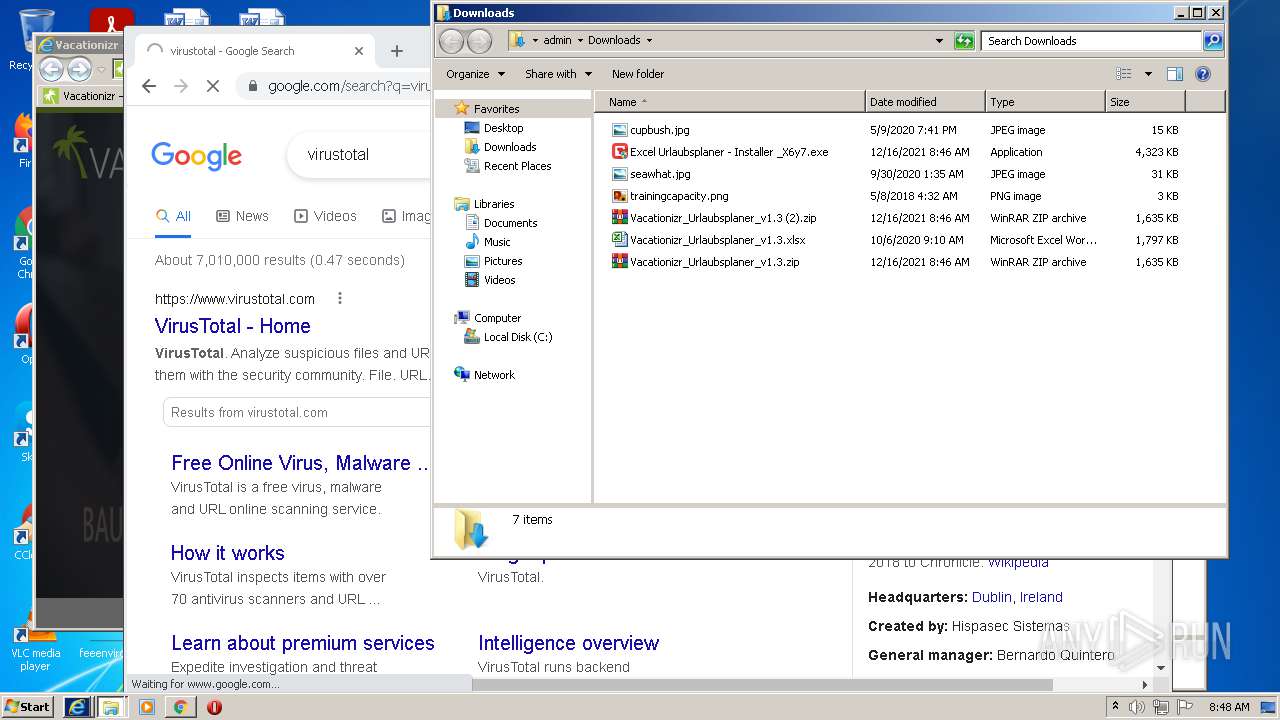
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF314CF0D791C749E9.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Excel Urlaubsplaner - Installer _X6y7[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{80A95040-5E4C-11EC-BE1B-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\683E9091A1271A1EE7311196A41F40C8 | der | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF907B53BDAD806C46.TMP | gmc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
131
DNS requests
71
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
4020 | Excel Urlaubsplaner - Installer _X6y7.exe | GET | 200 | 2.16.186.27:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPhGMYwGLo3%2FCIEPA7YXqMWmA%3D%3D | unknown | der | 503 b | shared |
2052 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1d4/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEFY9x%2BqAIlO2CQAAAADDNpI%3D | US | der | 471 b | whitelisted |
2052 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
456 | Excel Urlaubsplaner - Installer _X6y7.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1108 | EXCEL.EXE | GET | 200 | 143.204.101.74:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
2956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1108 | EXCEL.EXE | GET | 200 | 143.204.101.195:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
1108 | EXCEL.EXE | GET | 200 | 143.204.101.124:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3964 | iexplore.exe | 83.125.106.237:443 | chip-cluster.de | 3U TELECOM GmbH | DE | unknown |
3964 | iexplore.exe | 8.248.133.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
2956 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3964 | iexplore.exe | 104.89.32.83:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
2956 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3964 | iexplore.exe | 2.16.186.27:80 | r3.o.lencr.org | Akamai International B.V. | — | whitelisted |
3964 | iexplore.exe | 8.248.131.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
456 | Excel Urlaubsplaner - Installer _X6y7.exe | 2.16.186.234:443 | www.chip.de | Akamai International B.V. | — | whitelisted |
456 | Excel Urlaubsplaner - Installer _X6y7.exe | 23.213.161.10:443 | securedl.cdn.chip.de | Akamai Technologies, Inc. | US | unknown |
456 | Excel Urlaubsplaner - Installer _X6y7.exe | 185.158.249.69:443 | www.trustedoffers.de | easystores GmbH | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chip-cluster.de |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r3.o.lencr.org |
| shared |
crl3.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |