| File name: | GNBot Crack - Baseult - Kopie.zip |
| Full analysis: | https://app.any.run/tasks/162ddeb6-e240-4536-b295-169e5f16d6b2 |
| Verdict: | Malicious activity |
| Analysis date: | February 04, 2020, 14:55:52 |
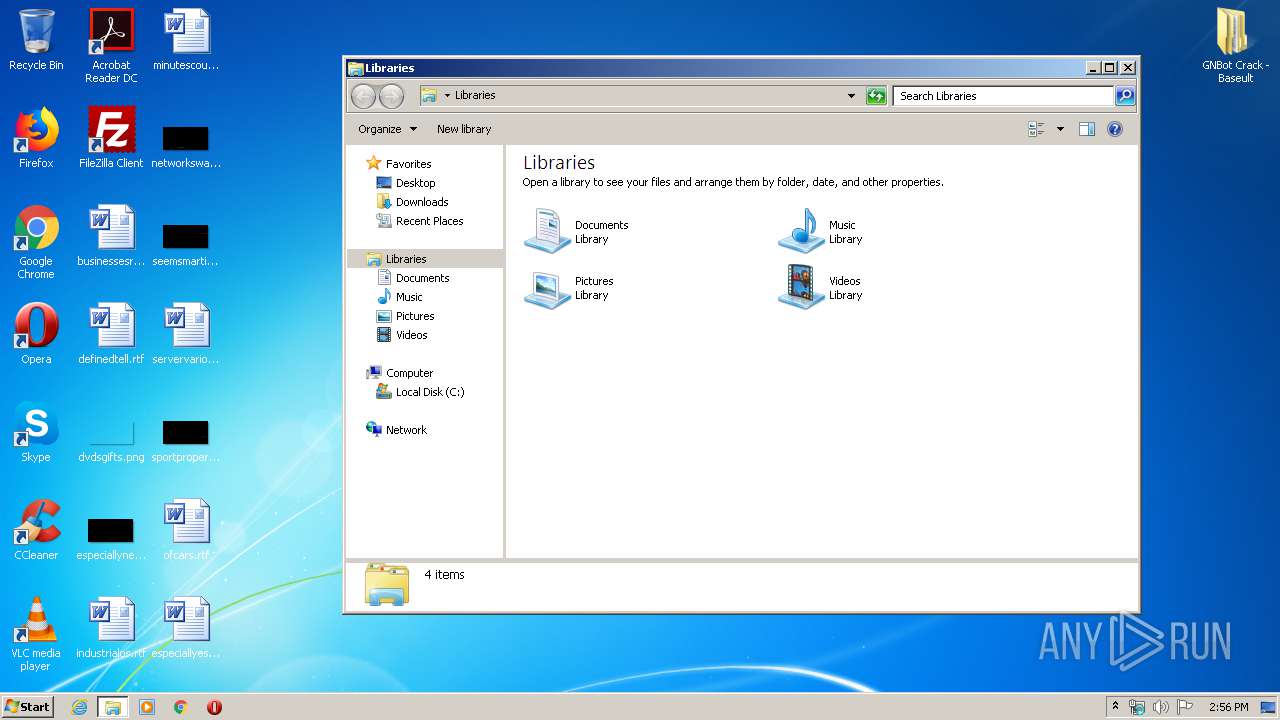
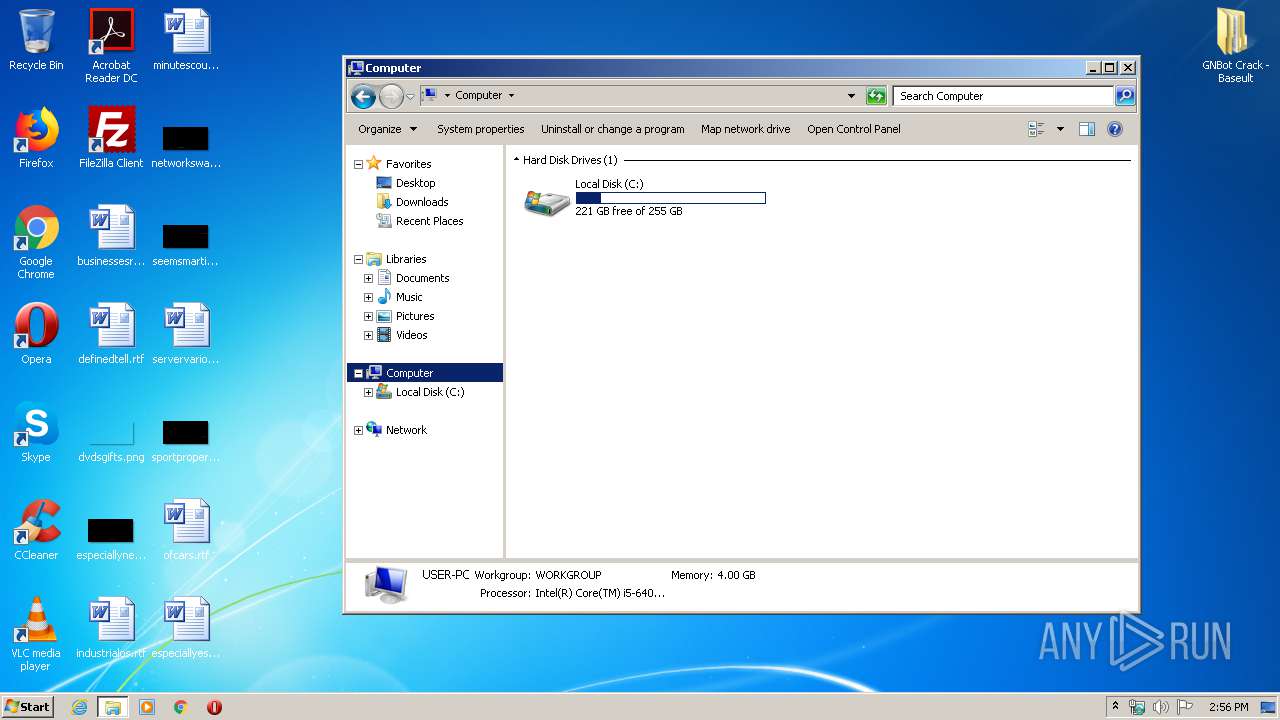
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 32A9BC239201E46EB511799D103961AD |
| SHA1: | F6599CC36BA64C9FE5067E9AD98587682405322E |
| SHA256: | 8AFDC1B6143369A53236873DBFE4234F797BC900054AF1EDB29CFEF984466C53 |
| SSDEEP: | 393216:QixDDJ4zV16PaanzoAAjIa5pWRNtL0b19zkP:VDqzV1Kaahb3Yb194P |
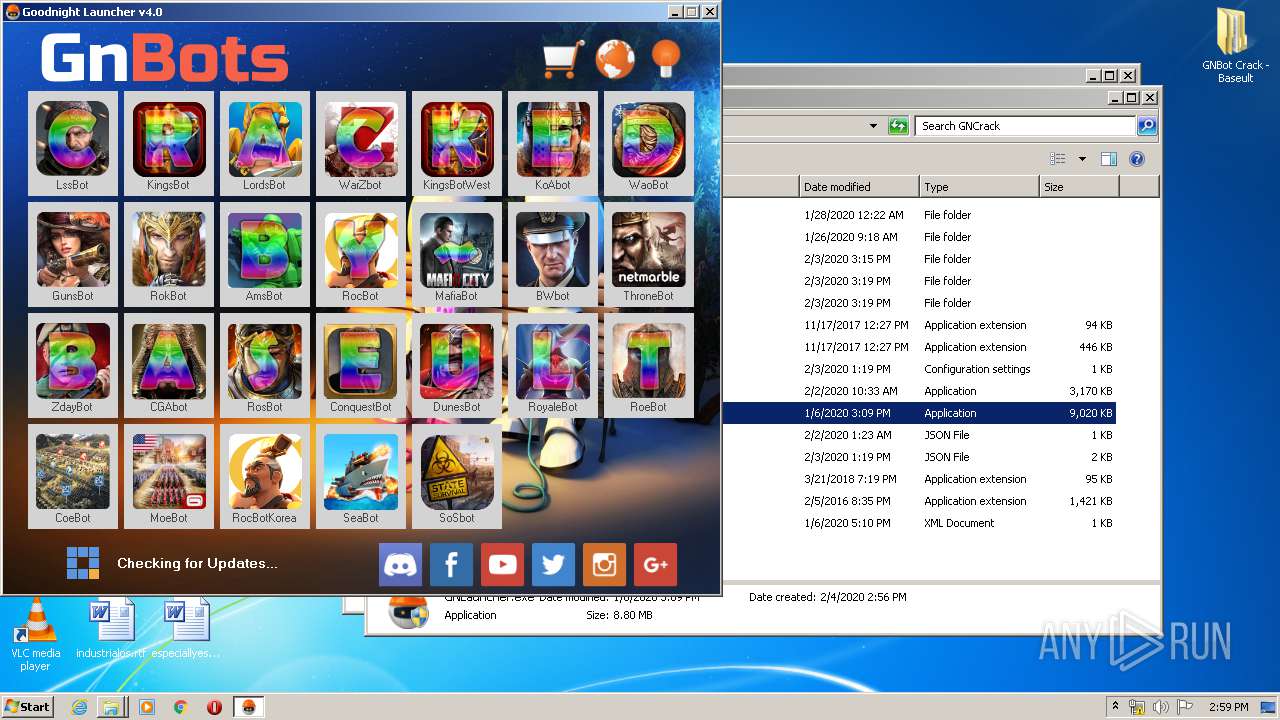
MALICIOUS
Starts Visual C# compiler
- GNLauncher.exe (PID: 3800)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 3888)
- DllHost.exe (PID: 3300)
Reads the machine GUID from the registry
- GNLauncher.exe (PID: 3800)
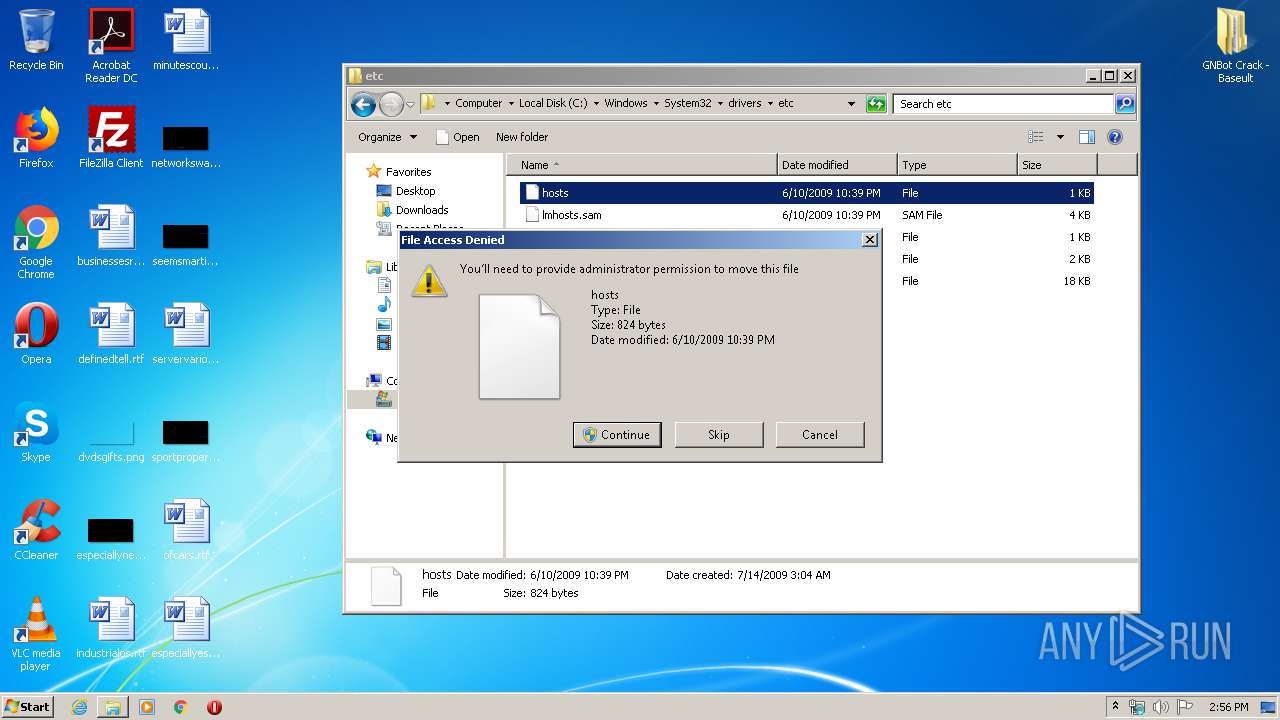
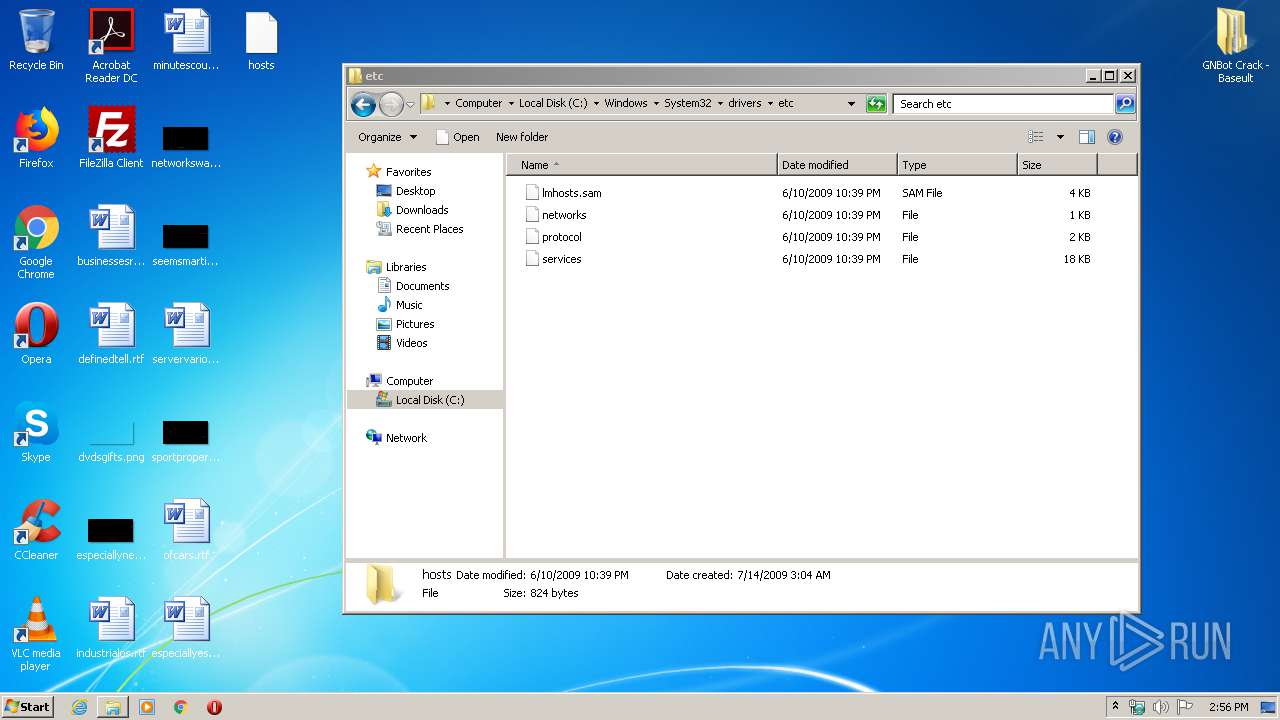
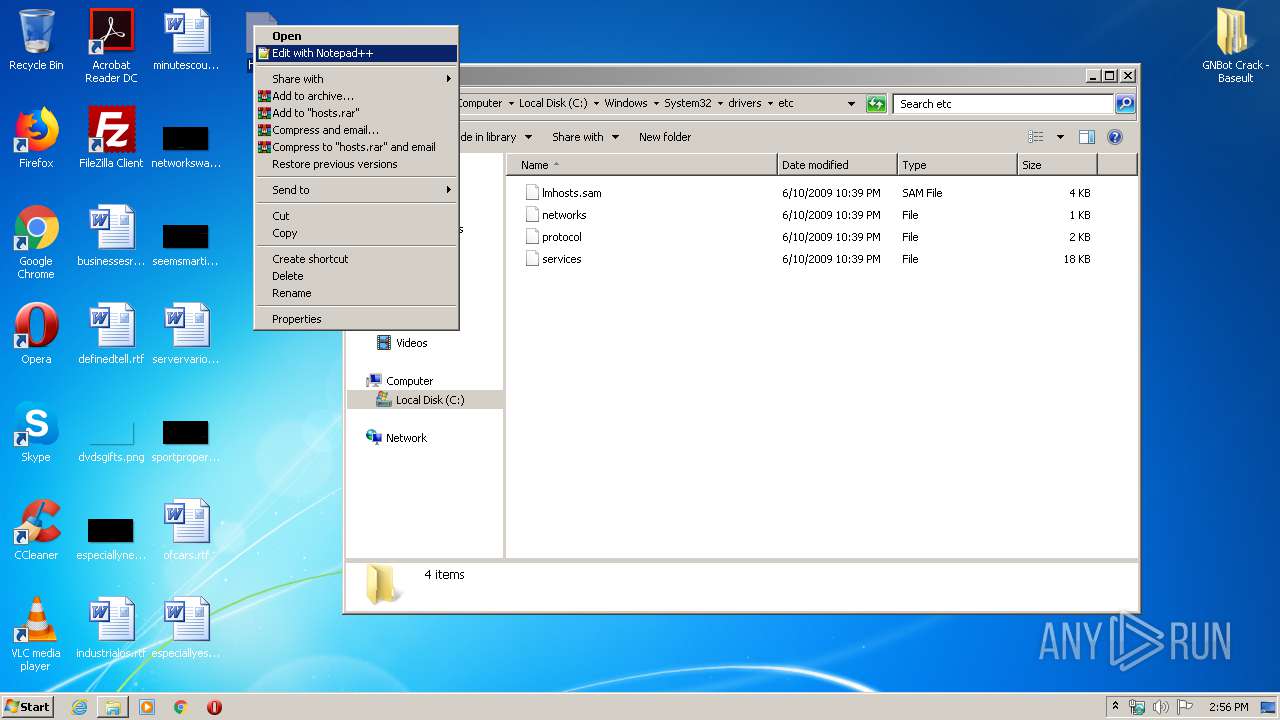
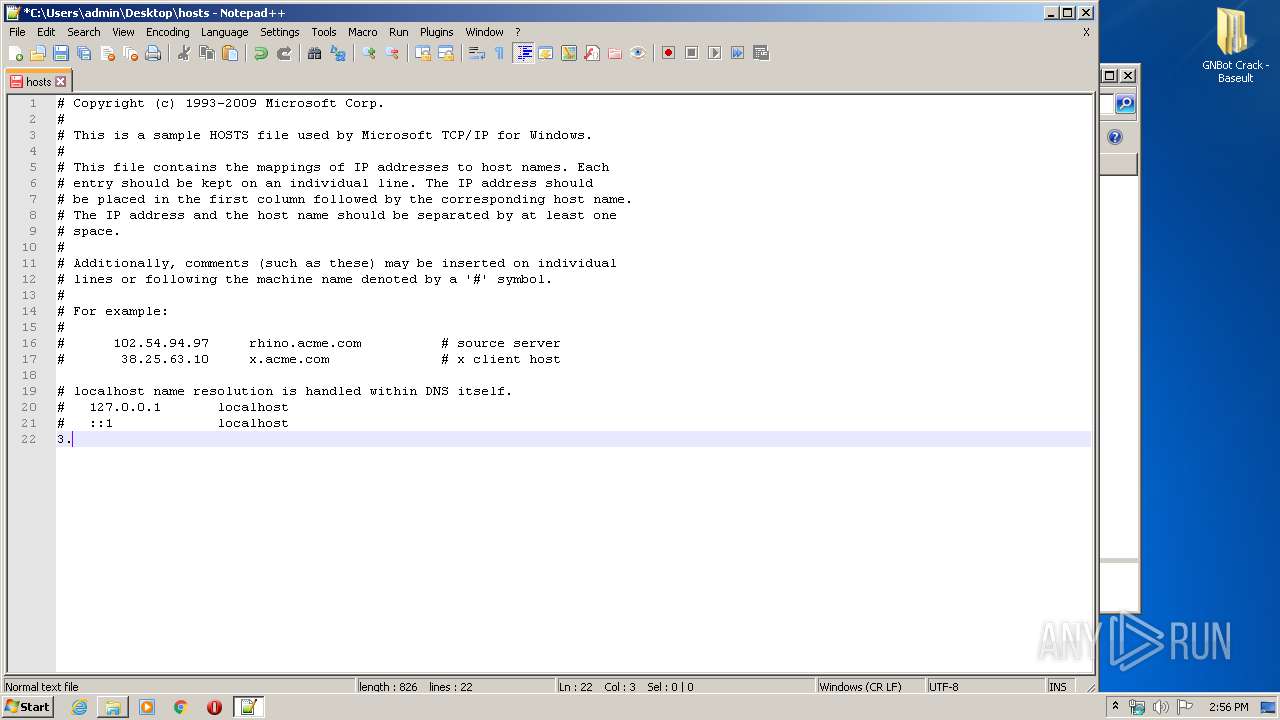
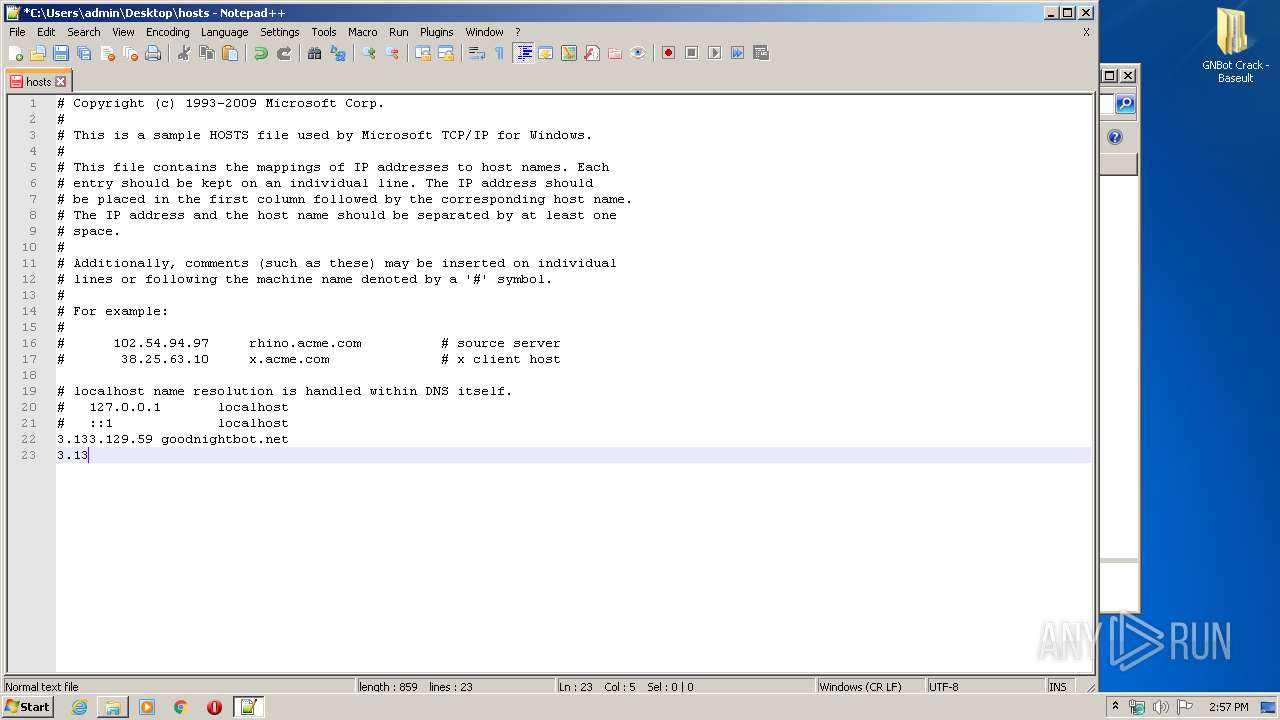
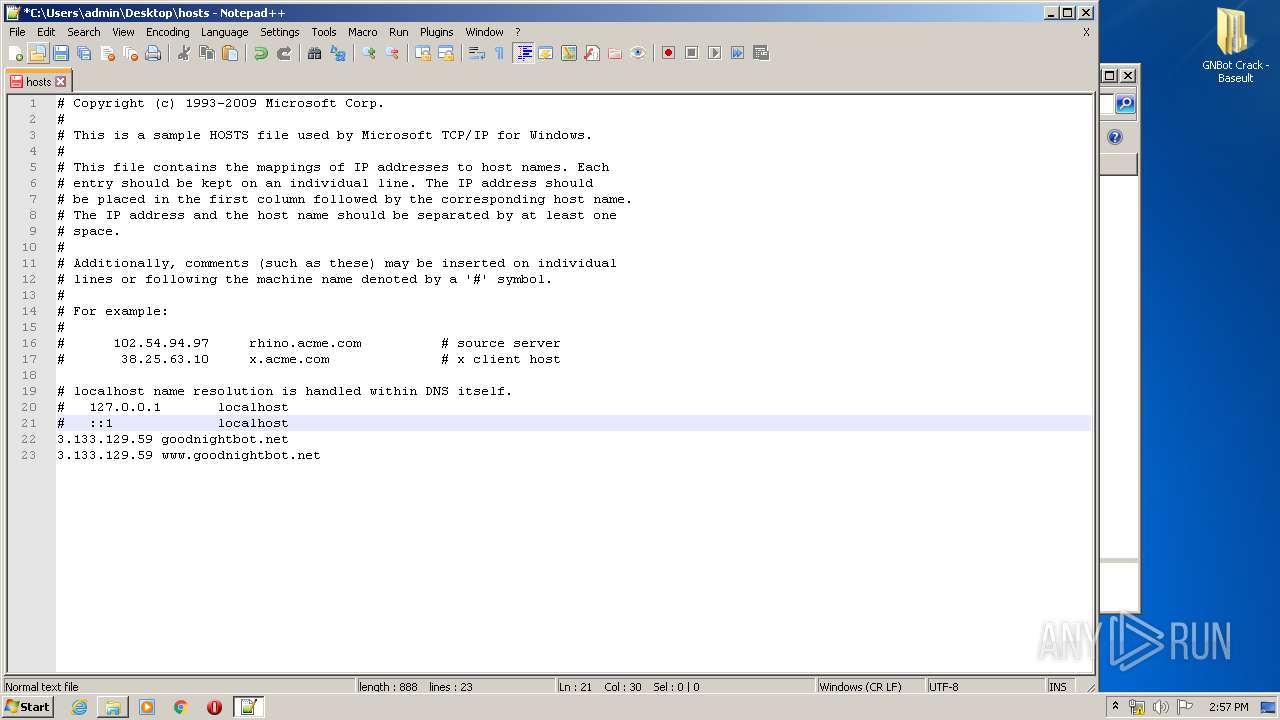
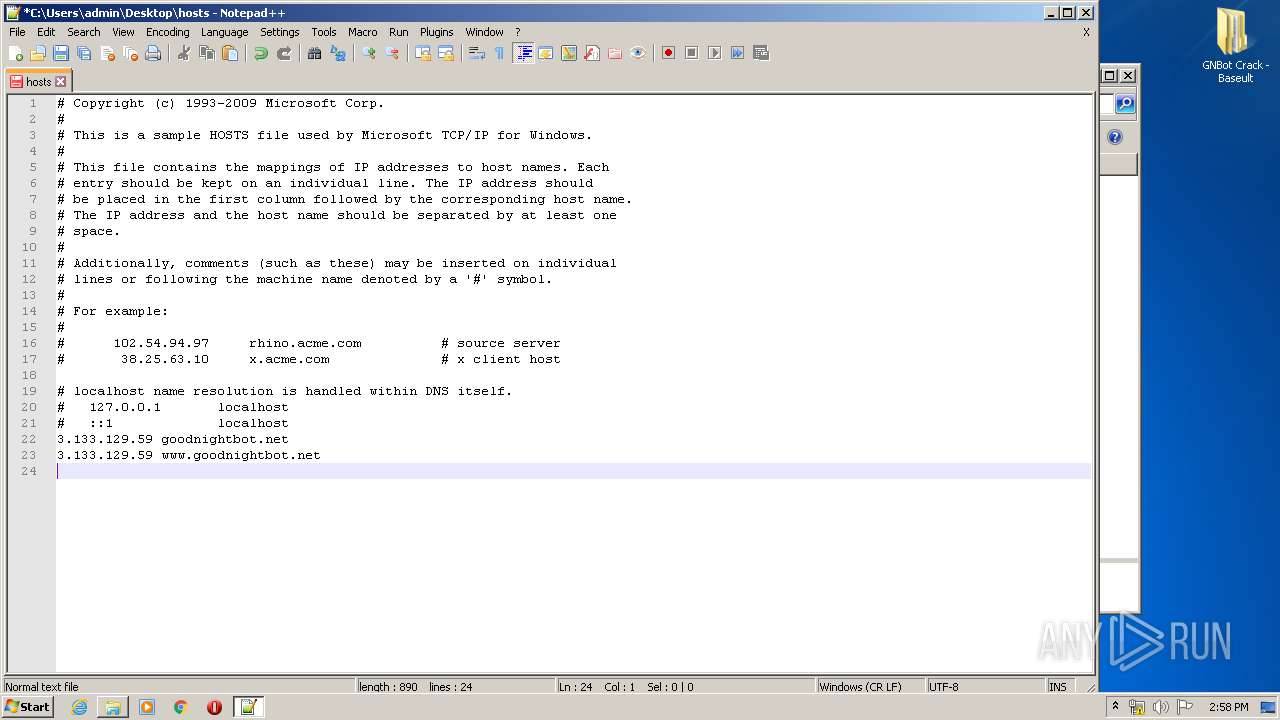
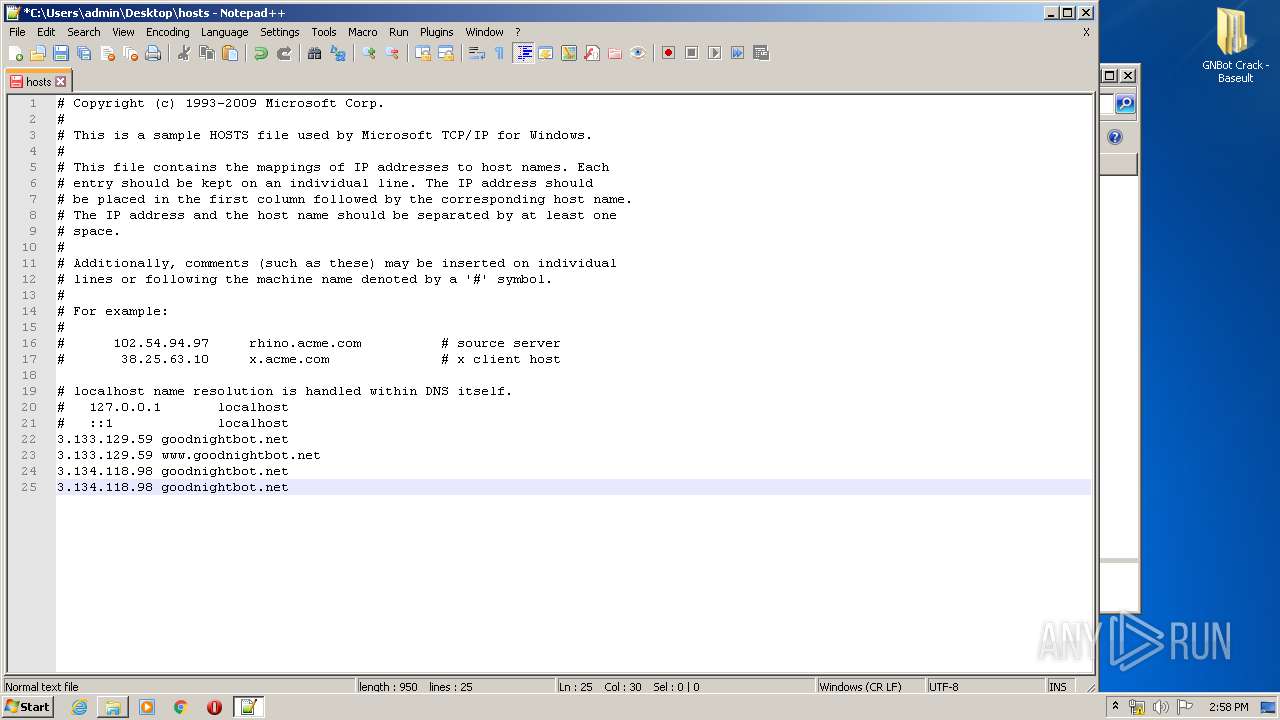
Creates files in the user directory
- notepad++.exe (PID: 1944)
INFO
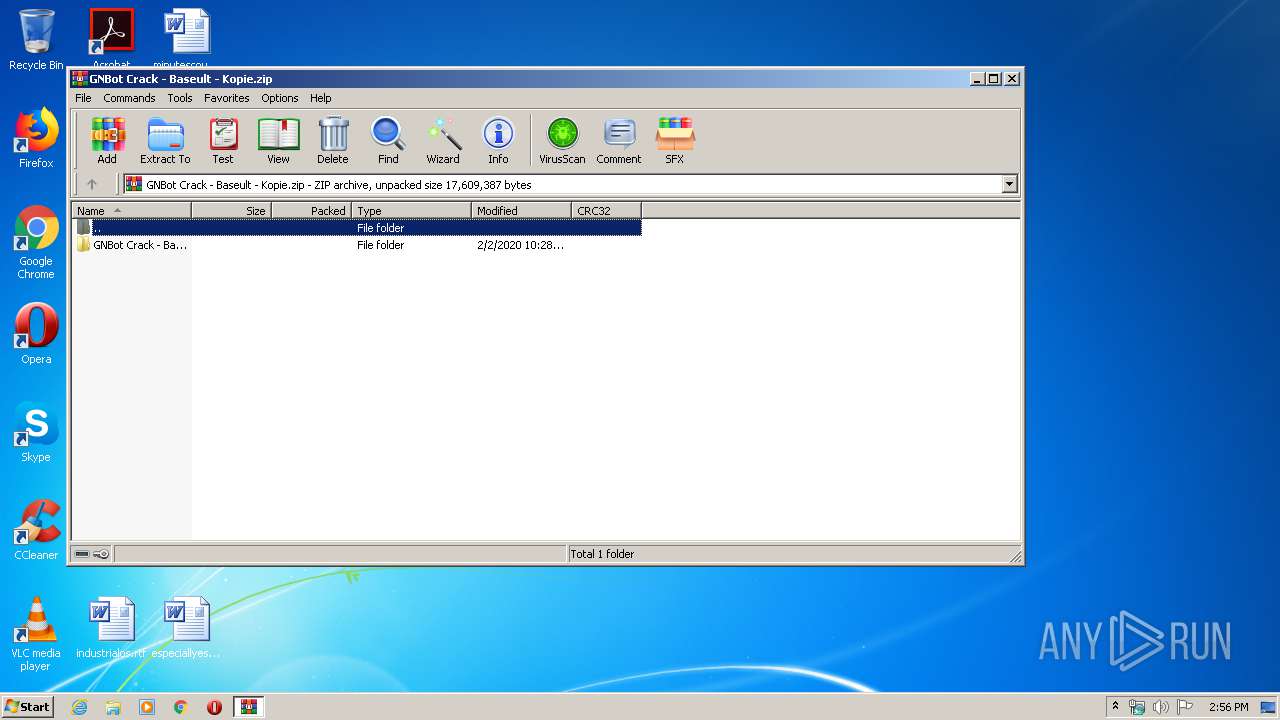
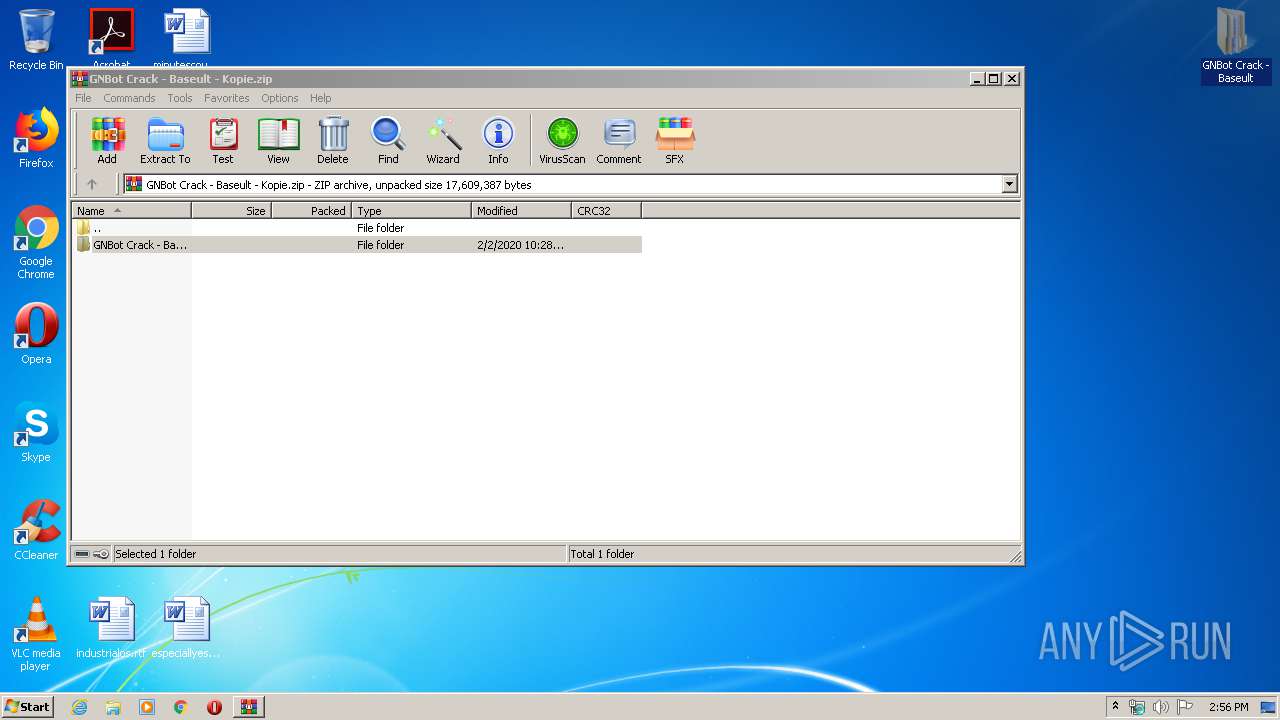
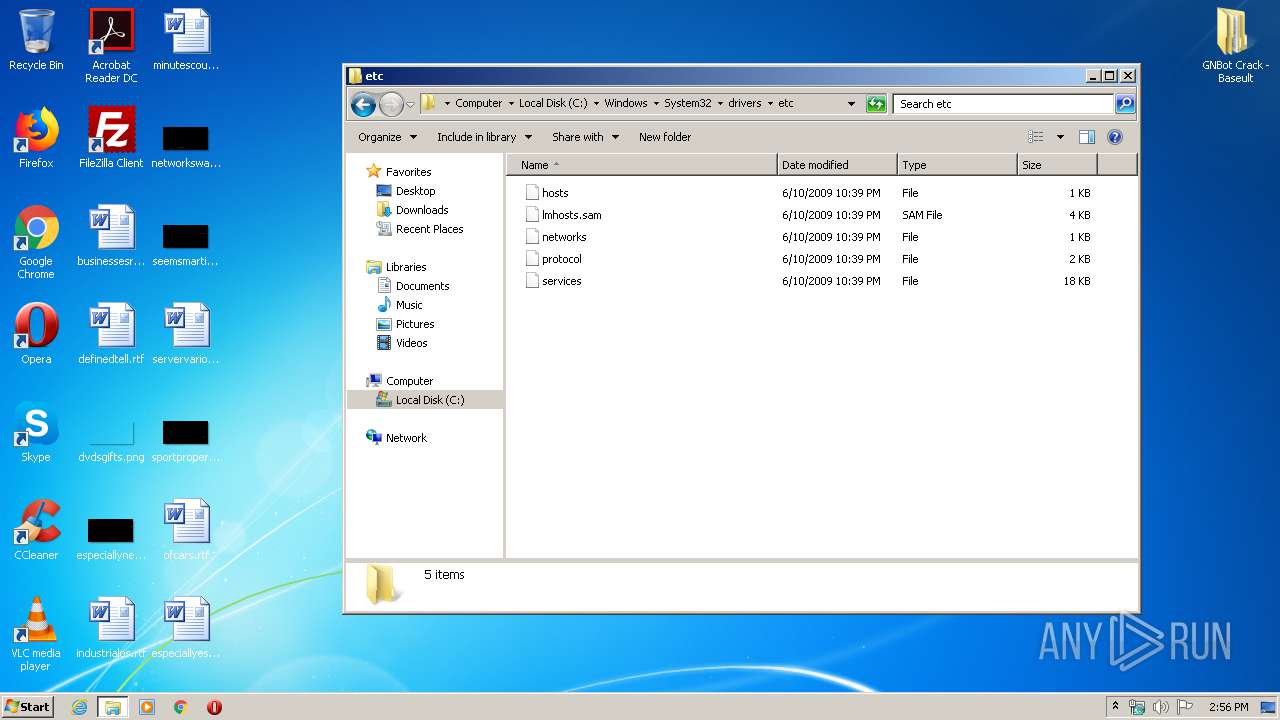
Manual execution by user
- explorer.exe (PID: 3020)
- notepad++.exe (PID: 1944)
- GNLauncher.exe (PID: 3332)
- GNLauncher.exe (PID: 3800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:02:02 11:28:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
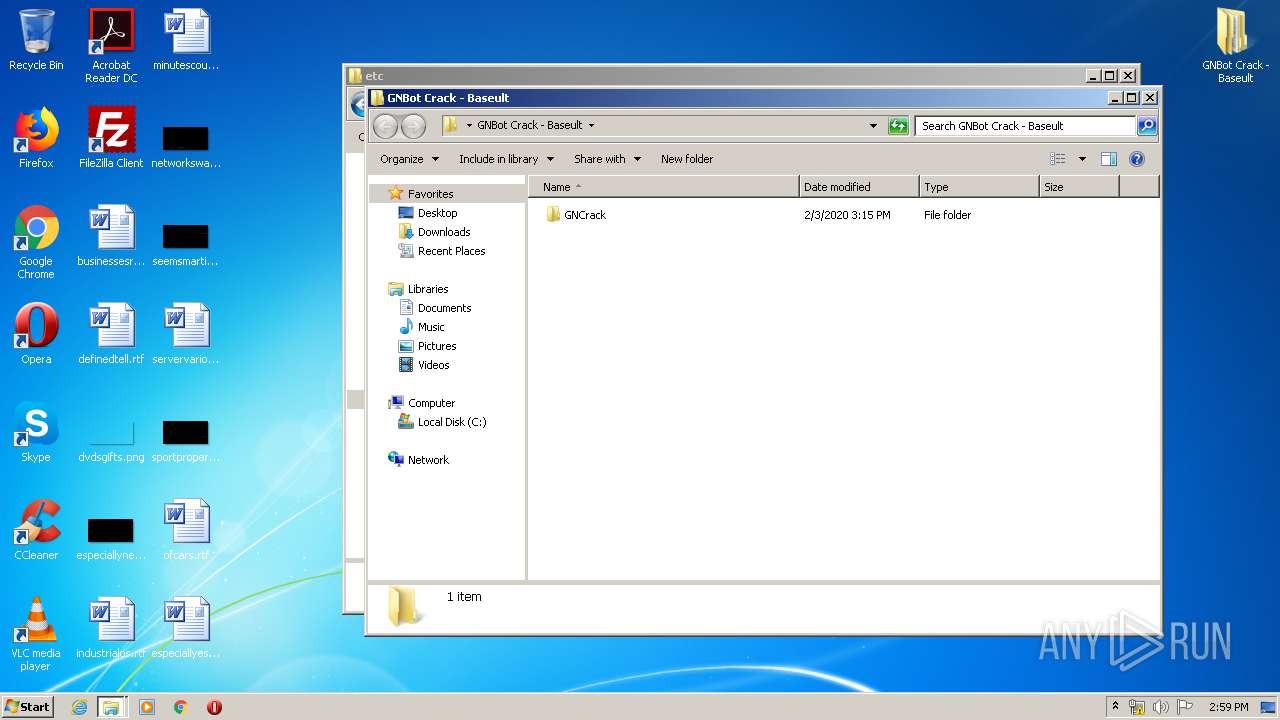
| ZipFileName: | GNBot Crack - Baseult/ |
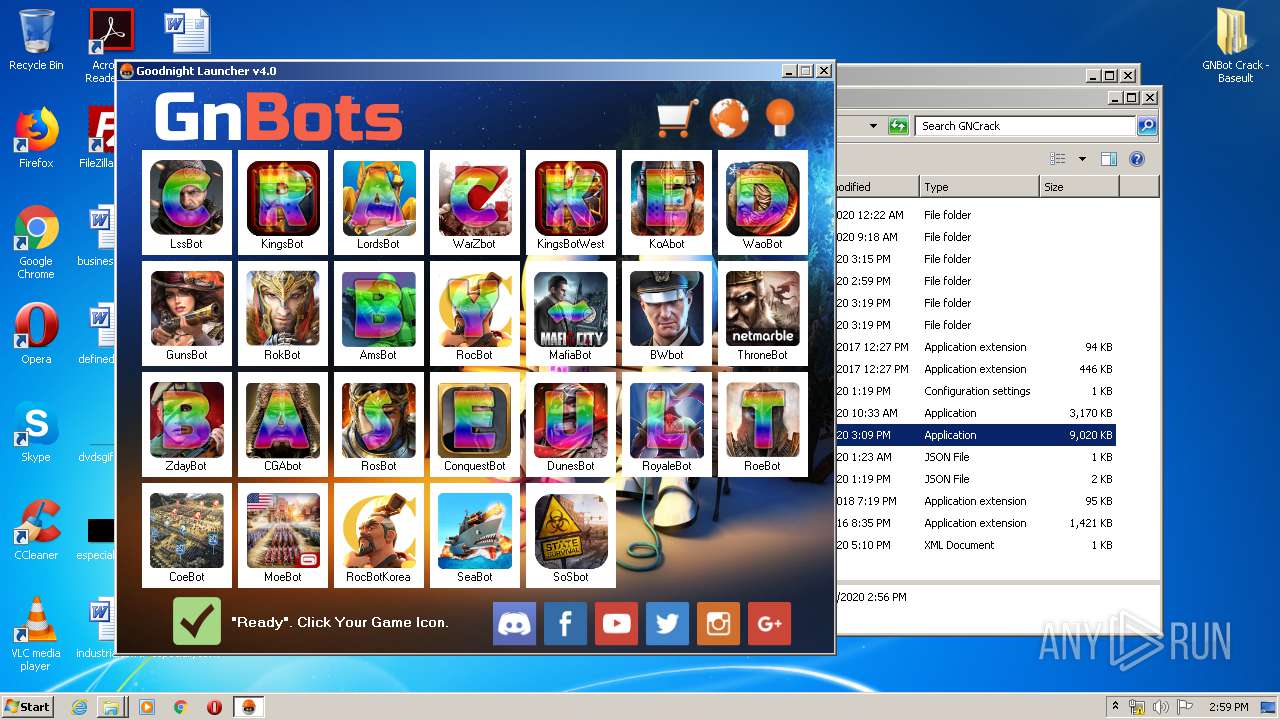
Total processes
58
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
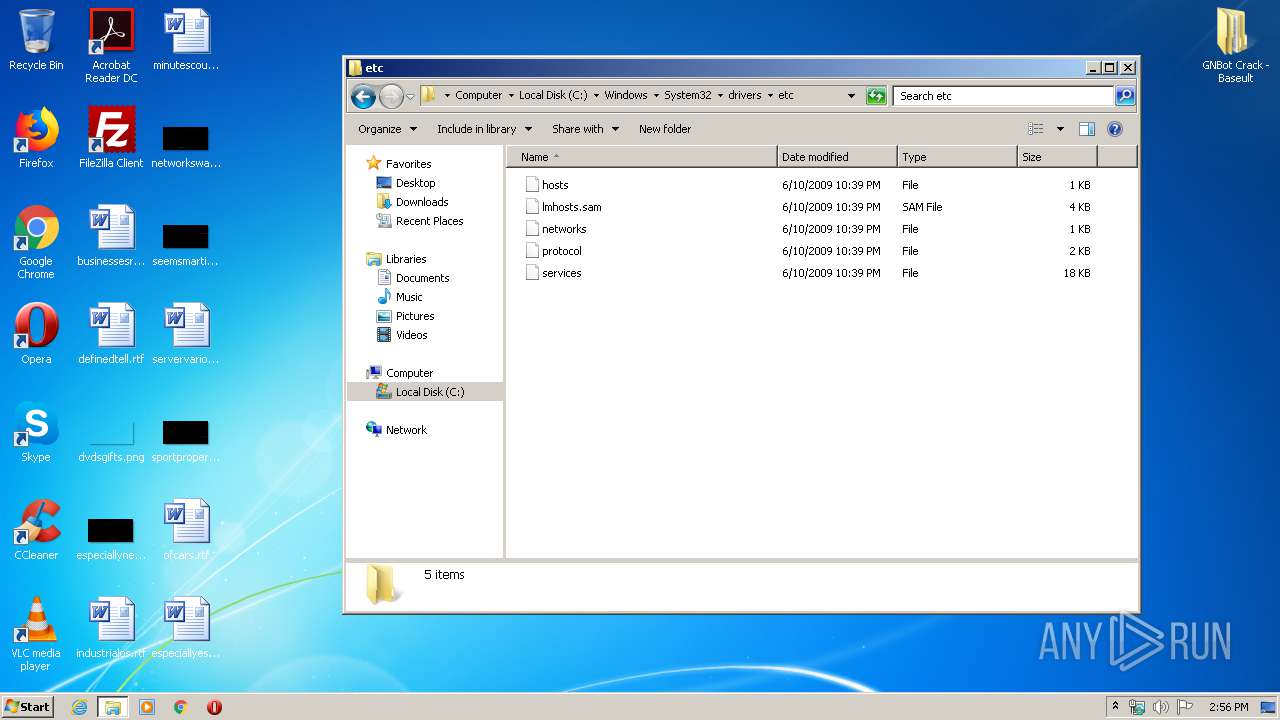
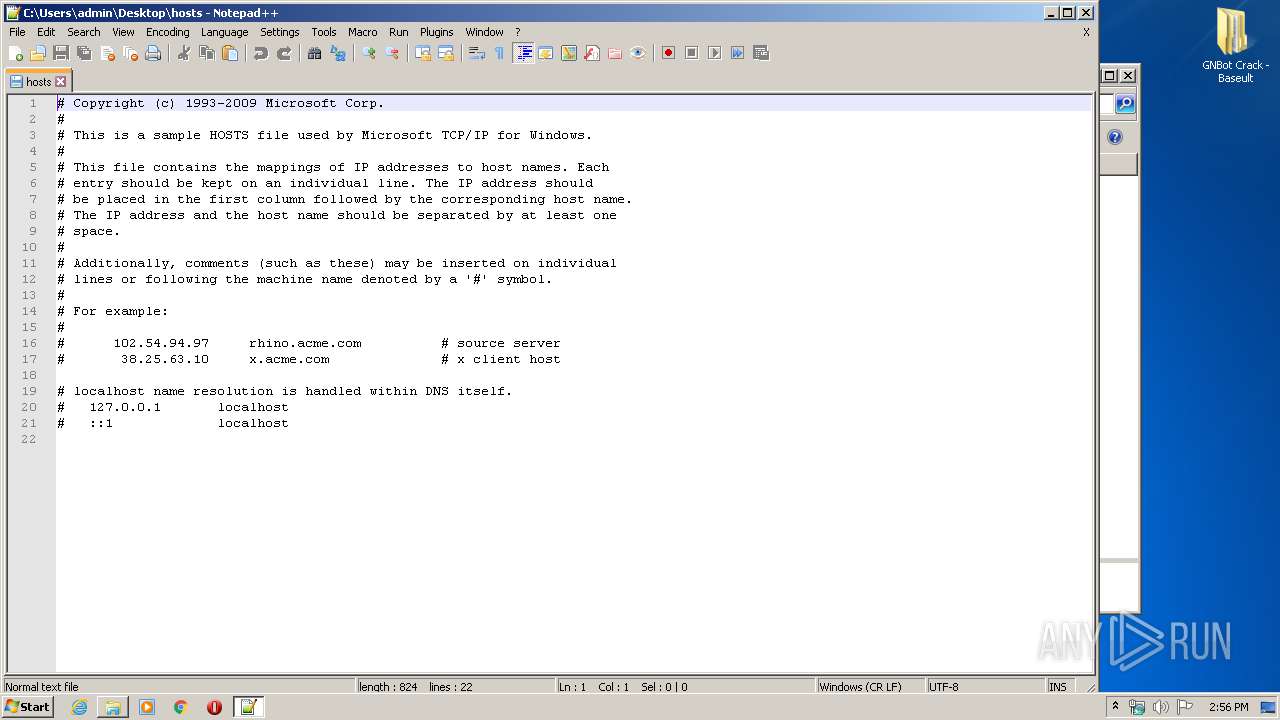
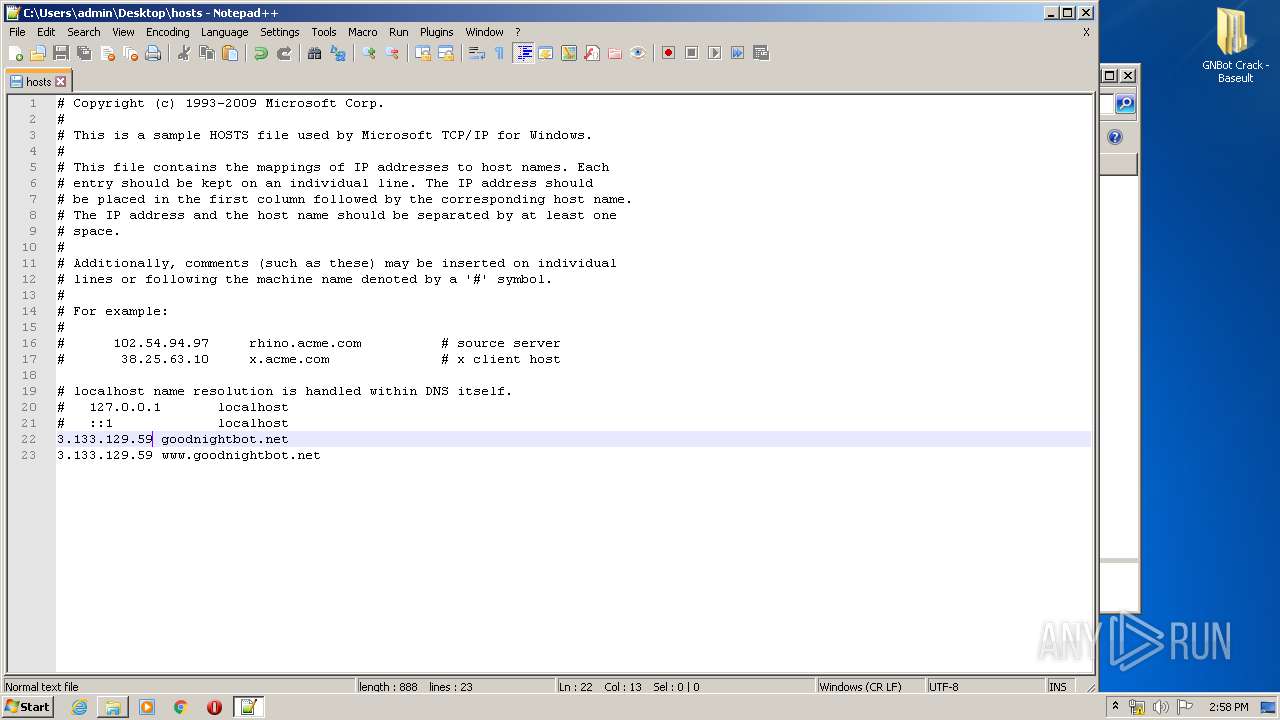
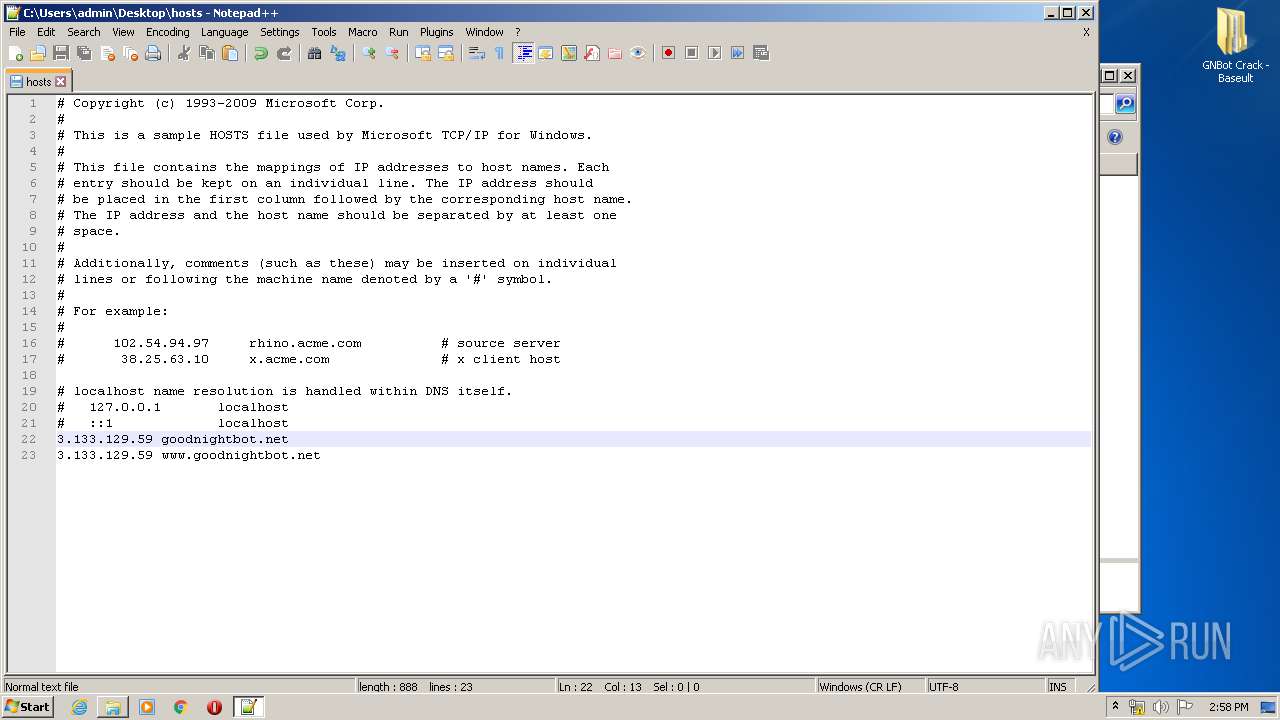
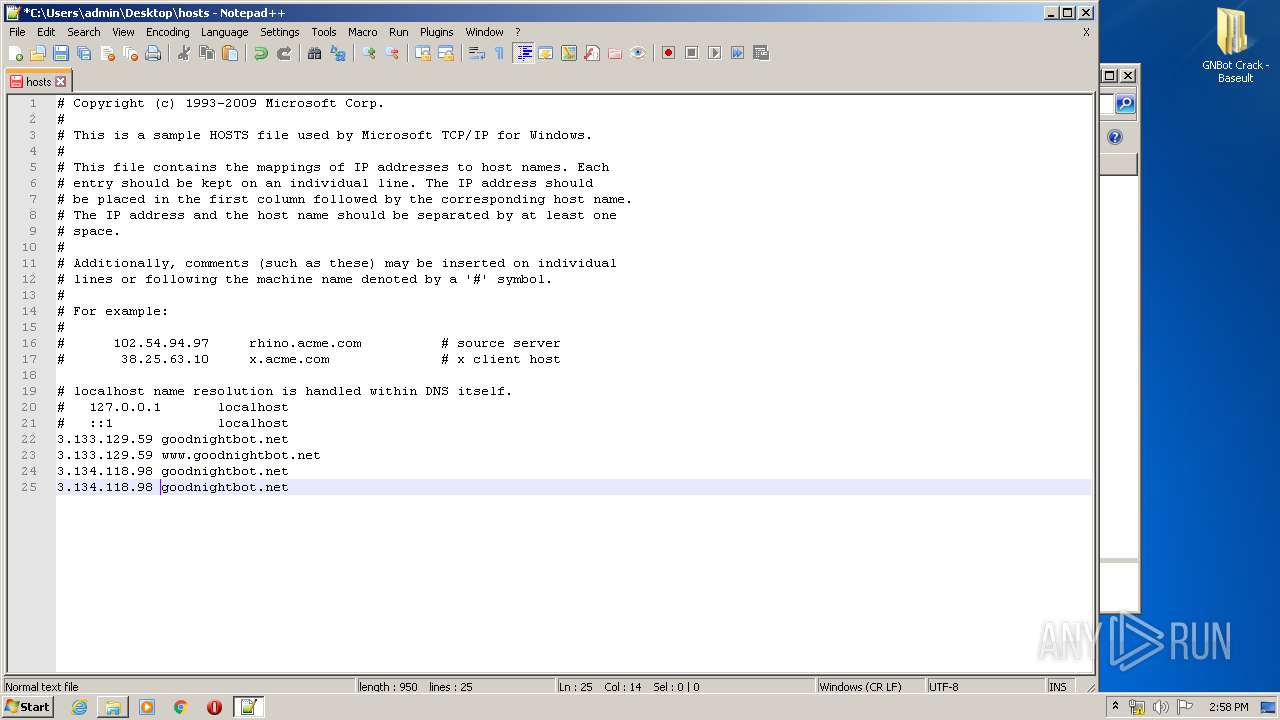
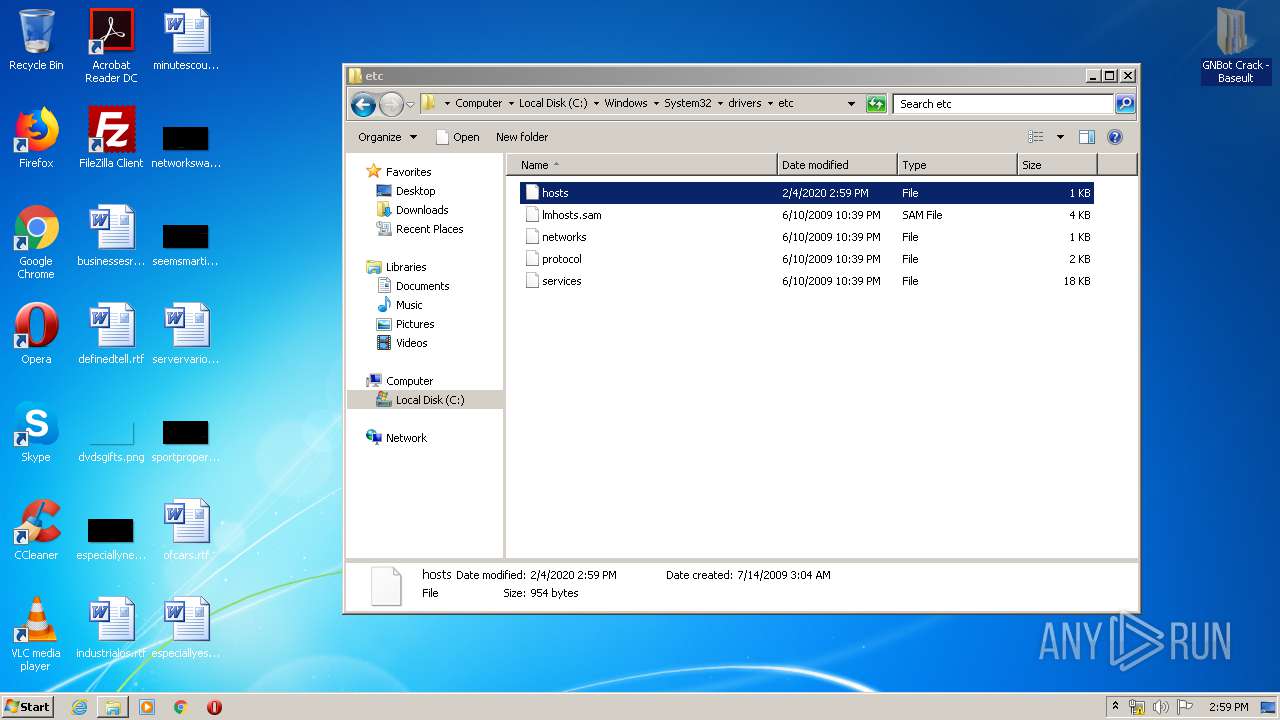
| 1944 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\hosts" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 4294967295 Version: 4.1 Modules
| |||||||||||||||
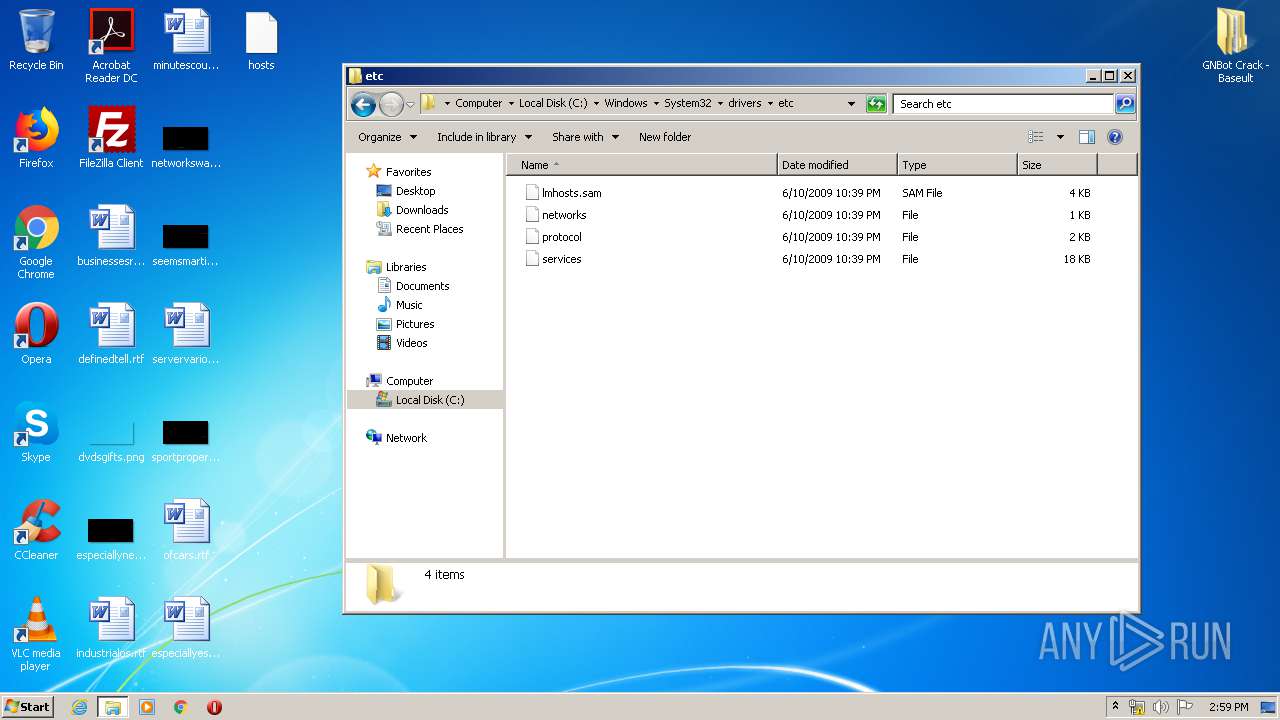
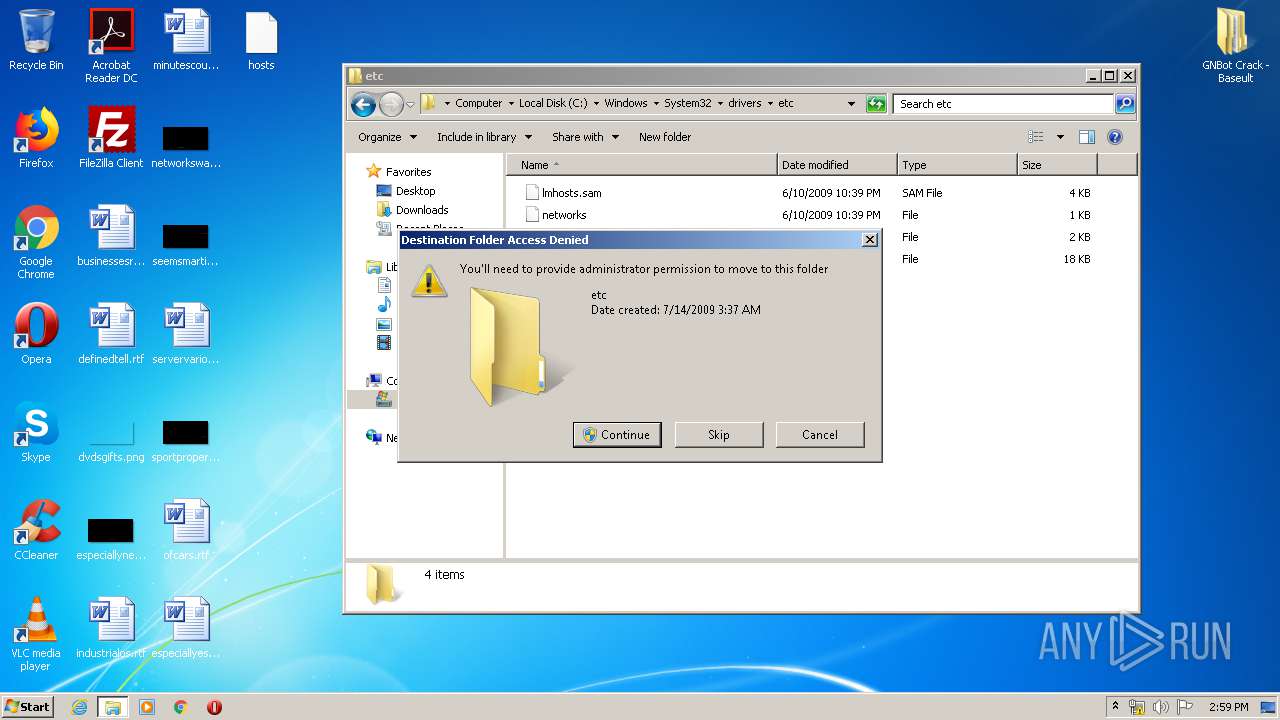
| 3020 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3300 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
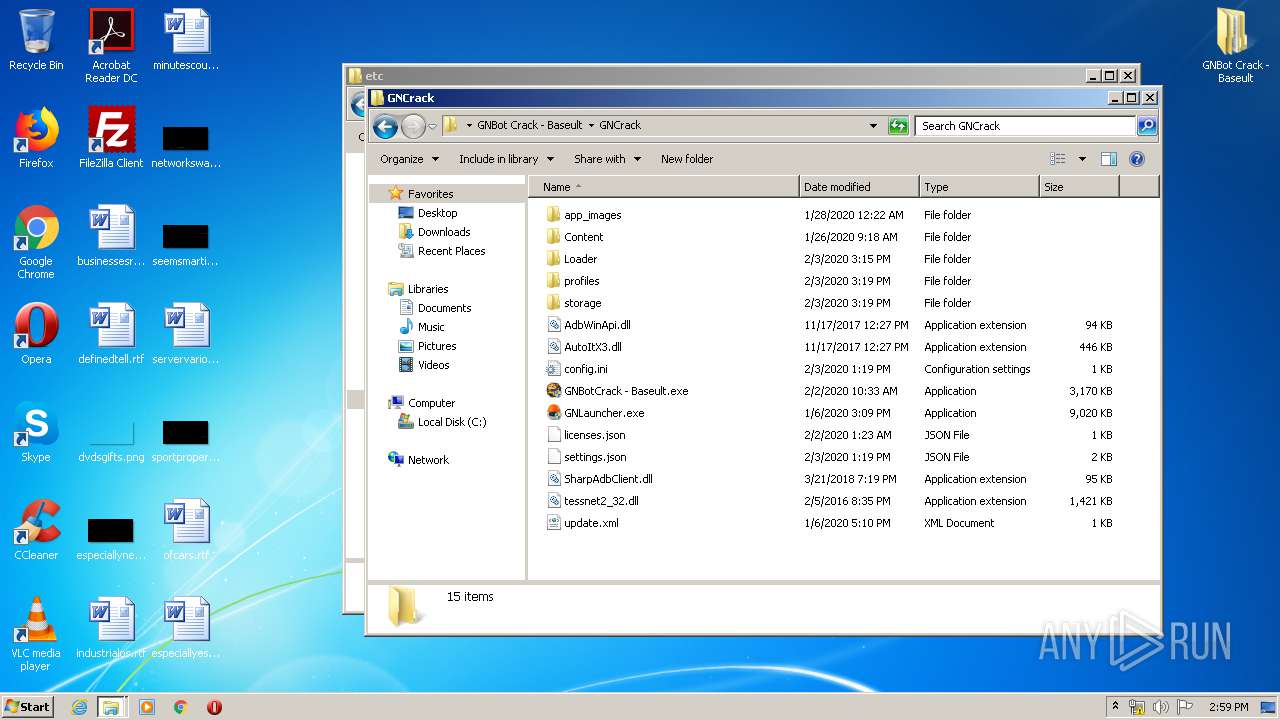
| 3332 | "C:\Users\admin\Desktop\GNBot Crack - Baseult\GNCrack\GNLauncher.exe" | C:\Users\admin\Desktop\GNBot Crack - Baseult\GNCrack\GNLauncher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GNLauncher Exit code: 3221226540 Version: 1.0.194.57723 Modules
| |||||||||||||||
| 3524 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\23tyfpjn\23tyfpjn.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | GNLauncher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 1 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 3776 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\GNBot Crack - Baseult - Kopie.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
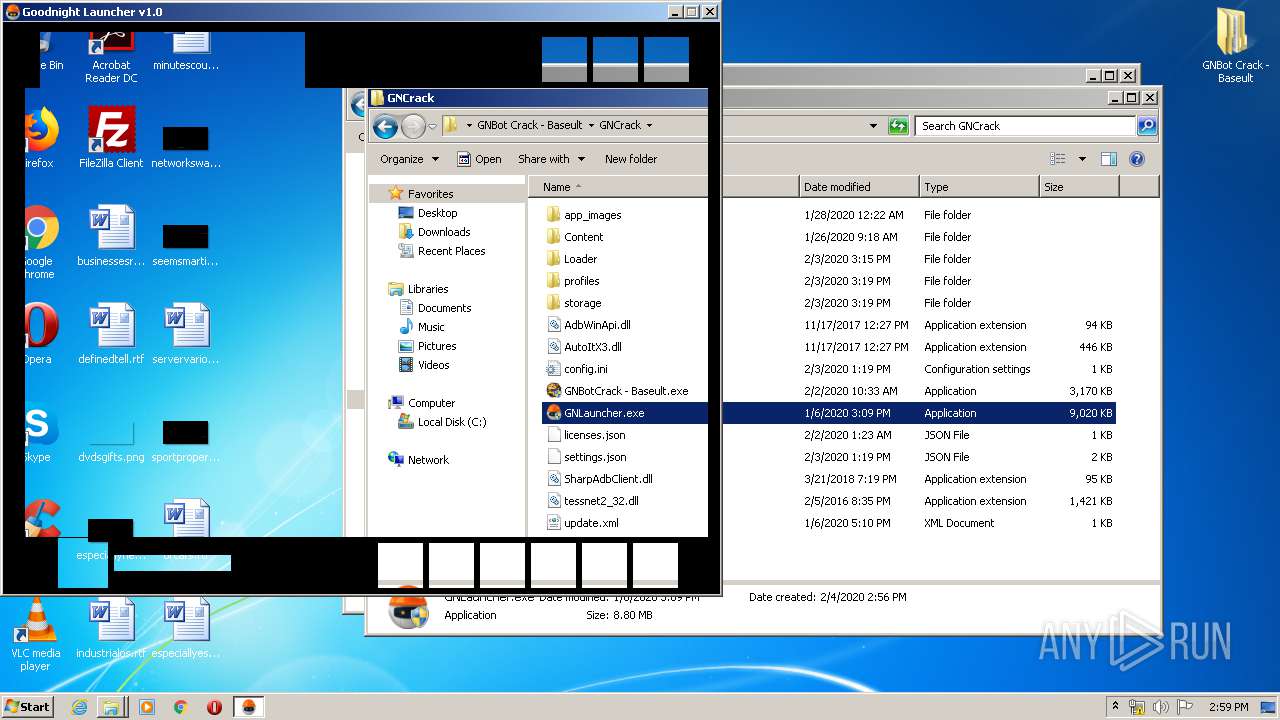
| 3800 | "C:\Users\admin\Desktop\GNBot Crack - Baseult\GNCrack\GNLauncher.exe" | C:\Users\admin\Desktop\GNBot Crack - Baseult\GNCrack\GNLauncher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: GNLauncher Exit code: 0 Version: 1.0.194.57723 Modules
| |||||||||||||||
| 3888 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
672
Read events
626
Write events
46
Delete events
0
Modification events
| (PID) Process: | (3776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3776) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\GNBot Crack - Baseult - Kopie.zip | |||
| (PID) Process: | (3776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3776) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
0
Suspicious files
0
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3776.18351\GNBot Crack - Baseult\GNCrack\AdbWinApi.dll | — | |
MD5:— | SHA256:— | |||
| 3776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3776.18351\GNBot Crack - Baseult\GNCrack\app_images\AmsBot.png | — | |
MD5:— | SHA256:— | |||
| 3776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3776.18351\GNBot Crack - Baseult\GNCrack\app_images\BWbot.png | — | |
MD5:— | SHA256:— | |||
| 3776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3776.18351\GNBot Crack - Baseult\GNCrack\app_images\CGAbot.png | — | |
MD5:— | SHA256:— | |||
| 3776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3776.18351\GNBot Crack - Baseult\GNCrack\app_images\CoeBot.png | — | |
MD5:— | SHA256:— | |||
| 3776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3776.18351\GNBot Crack - Baseult\GNCrack\app_images\ConquestBot.png | — | |
MD5:— | SHA256:— | |||
| 3776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3776.18351\GNBot Crack - Baseult\GNCrack\app_images\DunesBot.png | — | |
MD5:— | SHA256:— | |||
| 3776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3776.18351\GNBot Crack - Baseult\GNCrack\app_images\GunsBot.png | — | |
MD5:— | SHA256:— | |||
| 3776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3776.18351\GNBot Crack - Baseult\GNCrack\app_images\KingsBot.png | — | |
MD5:— | SHA256:— | |||
| 3776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3776.18351\GNBot Crack - Baseult\GNCrack\app_images\KingsBotWest.png | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
7
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 72.21.91.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 5.21 Kb | whitelisted |
3800 | GNLauncher.exe | GET | 200 | 3.133.129.59:80 | http://goodnightbot.net/gn/gnbot/update.xml | US | xml | 377 b | unknown |
3800 | GNLauncher.exe | GET | 200 | 3.133.129.59:80 | http://www.goodnightbot.net/gn/services/definitions.php | US | text | 4.13 Kb | unknown |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAxHWpoyfQpCuYL7zNoKQA4%3D | US | der | 278 b | whitelisted |
3800 | GNLauncher.exe | GET | 200 | 3.133.129.59:80 | http://www.goodnightbot.net/gn/auth/trial.php?action=mtc&uuid=90059c37-1320-41a4-b58d-2b75a9850d2f | US | text | 31 b | unknown |
3800 | GNLauncher.exe | POST | 200 | 3.133.129.59:80 | http://www.goodnightbot.net/gn/services/settings.php?seid=mkc | US | text | 172 b | unknown |
3800 | GNLauncher.exe | POST | 200 | 3.133.129.59:80 | http://www.goodnightbot.net/gn/services/loader.php?data=JYuqQeFQmw0LunqxnUvh24UN/qaJd/9UDQl3ABzHn3s= | US | text | 684 b | unknown |
3800 | GNLauncher.exe | POST | 200 | 3.133.129.59:80 | http://www.goodnightbot.net/gn/services/settings.php?seid=config | US | text | 1.96 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2368 | gup.exe | 104.31.89.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
— | — | 72.21.91.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3800 | GNLauncher.exe | 3.133.129.59:80 | — | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|