| File name: | 8ae73acc01f72c1164324e44045cd74256c3b4be606c0932717a2b593e8c5169.doc |
| Full analysis: | https://app.any.run/tasks/0de6c103-4108-43a9-9482-c1a29d6c11b1 |
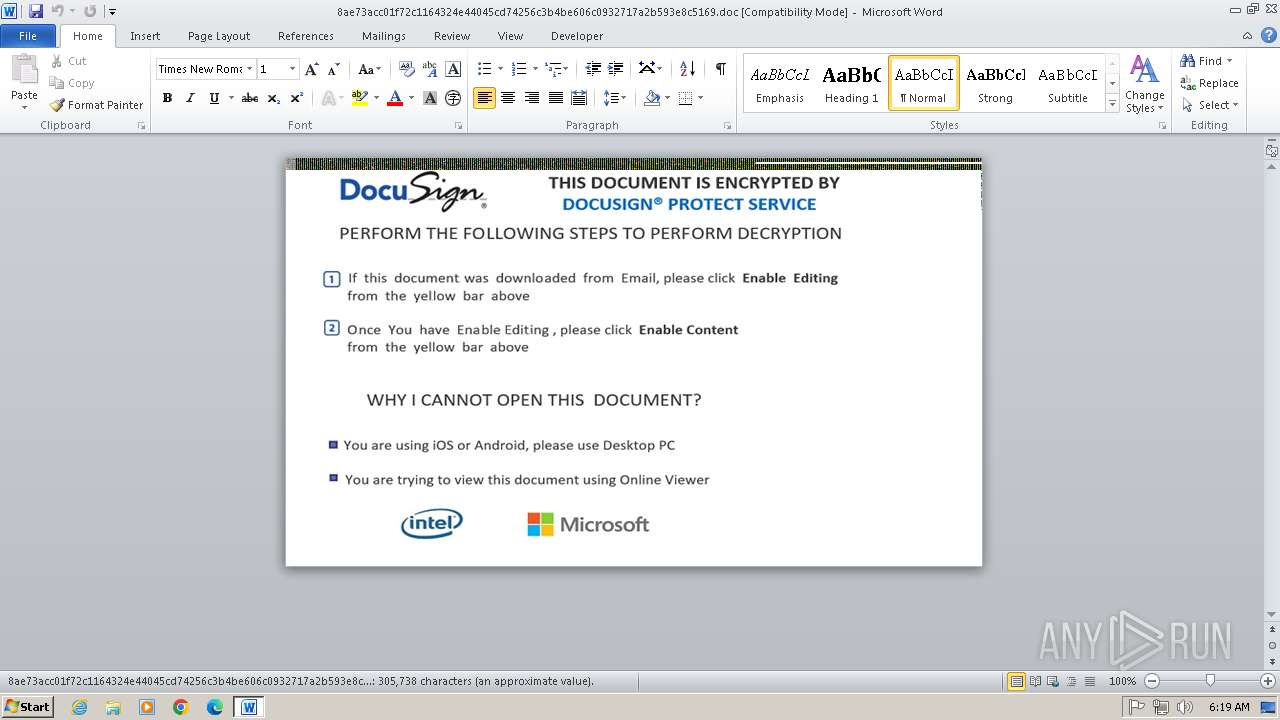
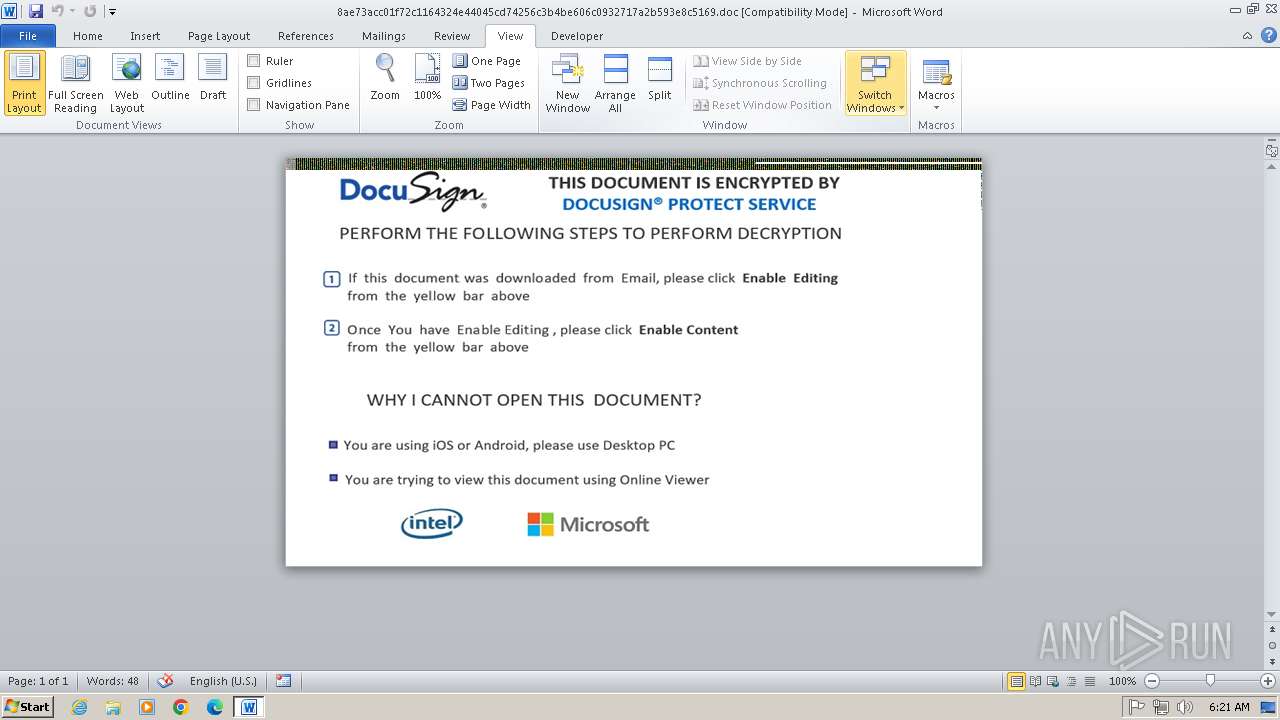
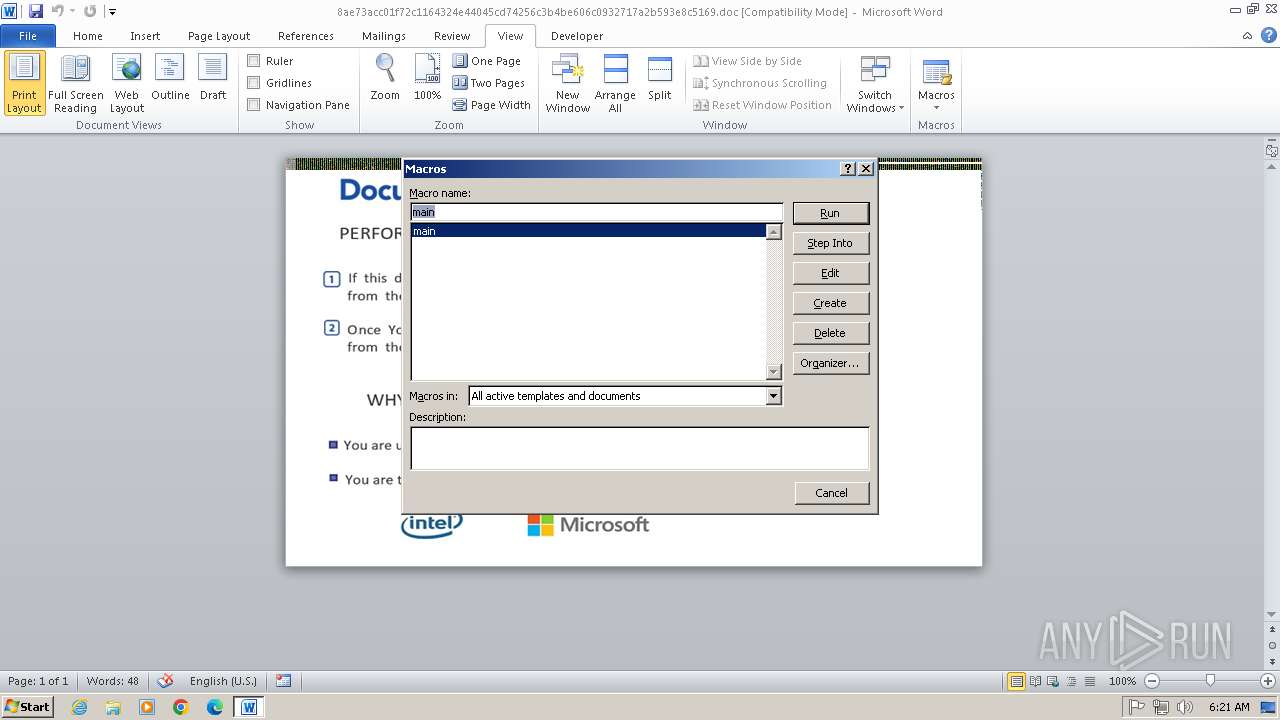
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2025, 05:19:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1251, Template: Normal.dot, Revision Number: 64, Name of Creating Application: Microsoft Office Word, Total Editing Time: 03:45:00, Create Time/Date: Fri Dec 3 17:38:00 2021, Last Saved Time/Date: Tue Dec 7 10:10:00 2021, Number of Pages: 1, Number of Words: 55341, Number of Characters: 315448, Security: 0 |
| MD5: | 23F98D6FF7329618994AC0F3E2B3A394 |
| SHA1: | 64AE82D4C4D66D2703E8E310E176808F380F727D |
| SHA256: | 8AE73ACC01F72C1164324E44045CD74256C3B4BE606C0932717A2B593E8C5169 |
| SSDEEP: | 3072:O7jFrv7YB6BAd585zcXGdTk3iYZXcychQS3sTvi:uPYB6Bc85zcXGBk3lXfcP3sTv |
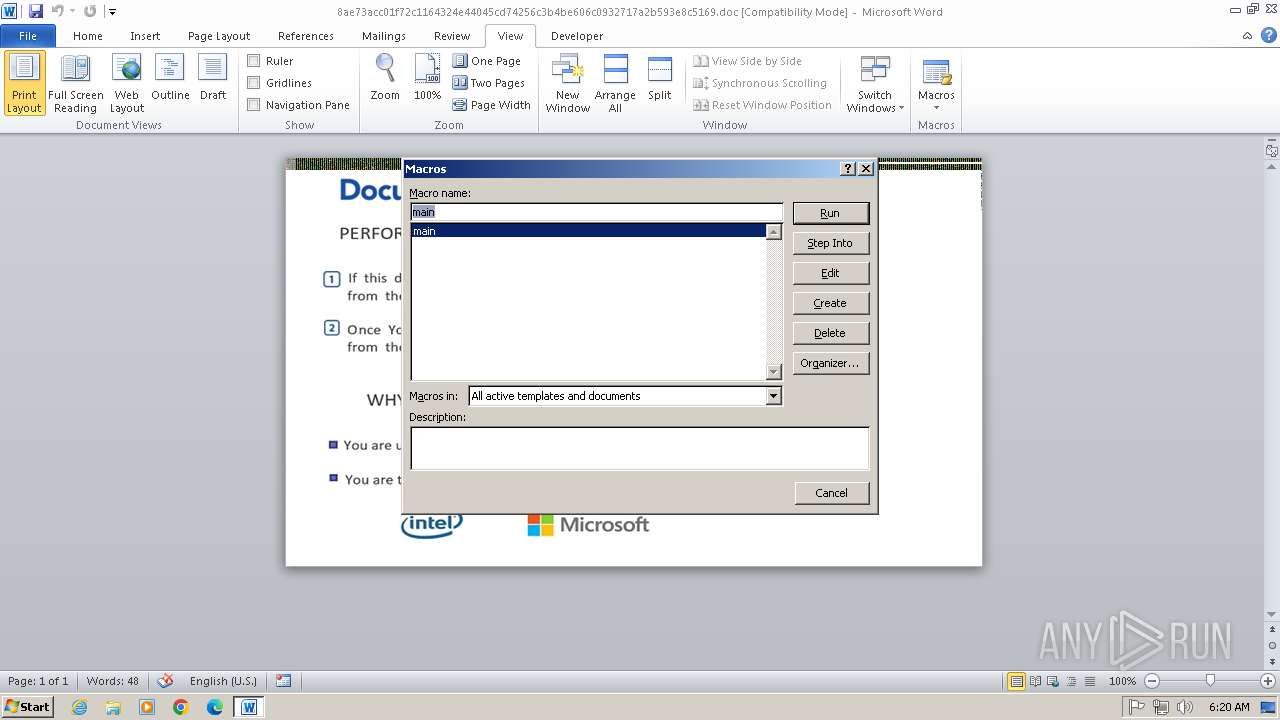
MALICIOUS
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2480)
Bypass execution policy to execute commands
- powershell.exe (PID: 2988)
- powershell.exe (PID: 3300)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3856)
- cmd.exe (PID: 2652)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 2988)
- powershell.exe (PID: 3300)
SUSPICIOUS
Likely accesses (executes) a file from the Public directory
- rundll32.exe (PID: 1844)
- rundll32.exe (PID: 1276)
Uses RUNDLL32.EXE to load library
- OUTLOOK.EXE (PID: 2336)
- OUTLOOK.EXE (PID: 1560)
- powershell.exe (PID: 3300)
- powershell.exe (PID: 2988)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 1844)
- rundll32.exe (PID: 1276)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3856)
- cmd.exe (PID: 2652)
The process executes Powershell scripts
- cmd.exe (PID: 3856)
- cmd.exe (PID: 2652)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3856)
- cmd.exe (PID: 2652)
Runs shell command (SCRIPT)
- WINWORD.EXE (PID: 2480)
Reads the Internet Settings
- powershell.exe (PID: 2988)
- powershell.exe (PID: 3300)
INFO
Disables trace logs
- powershell.exe (PID: 2988)
- powershell.exe (PID: 3300)
Checks transactions between databases Windows and Oracle
- WINWORD.EXE (PID: 2480)
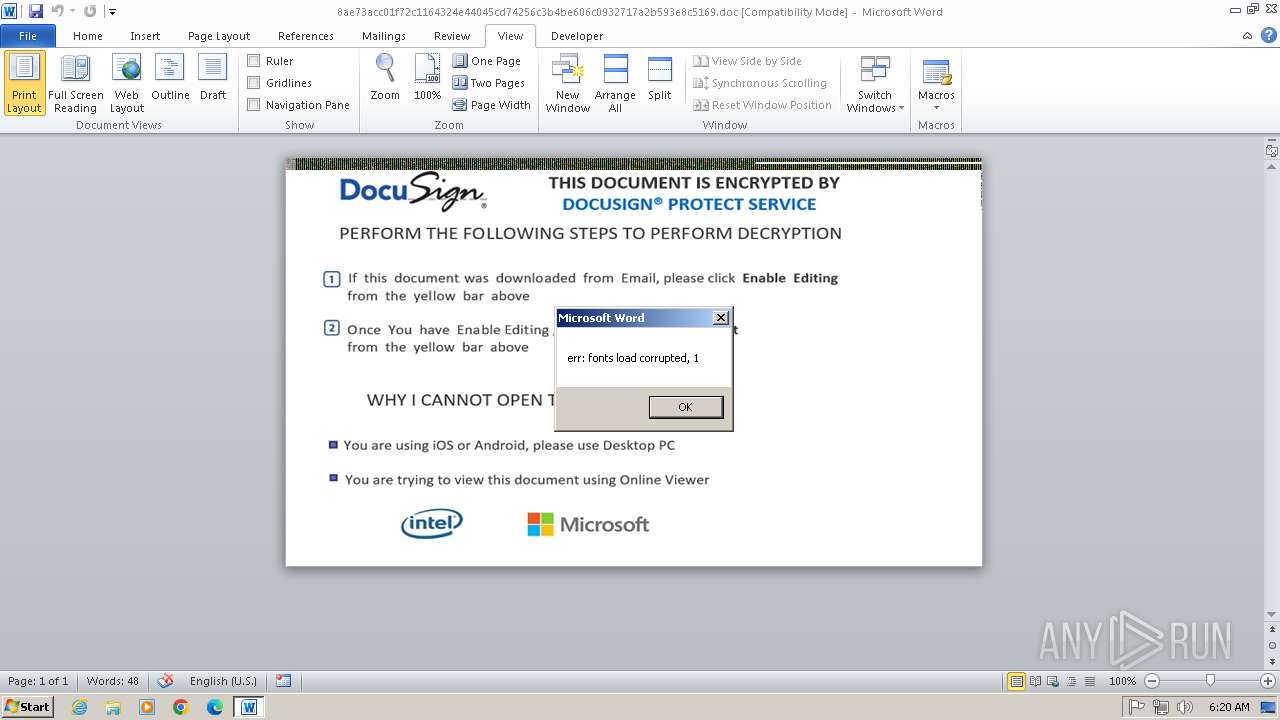
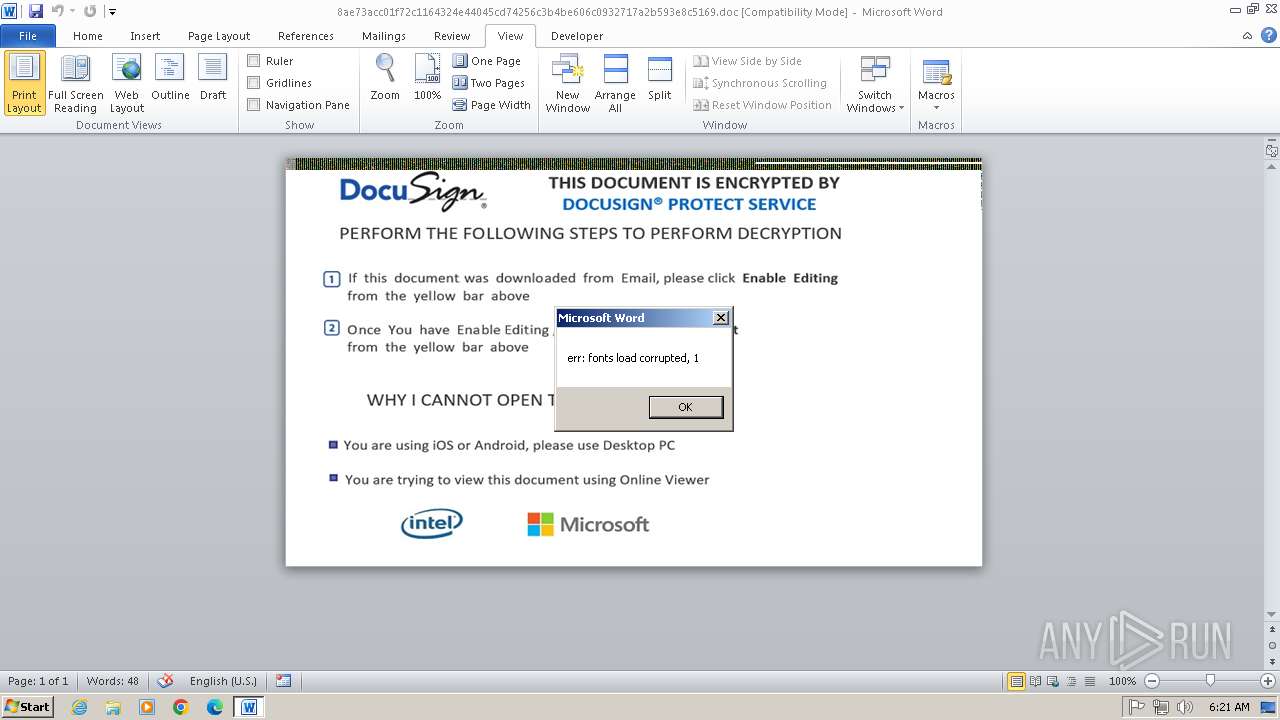
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2988)
- powershell.exe (PID: 3300)
Failed to connect to remote server (POWERSHELL)
- powershell.exe (PID: 2988)
- powershell.exe (PID: 3300)
Create files in a temporary directory
- rundll32.exe (PID: 1276)
- rundll32.exe (PID: 1844)
Manual execution by a user
- chrome.exe (PID: 2932)
Application launched itself
- chrome.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Identification: | Word 8.0 |
|---|---|
| LanguageCode: | Russian |
| DocFlags: | 1Table, ExtChar |
| System: | Windows |
| Word97: | No |
| Title: | - |
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Template: | Normal.dot |
| LastModifiedBy: | - |
| Software: | Microsoft Office Word |
| CreateDate: | 2021:12:03 17:38:00 |
| ModifyDate: | 2021:12:07 10:10:00 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Manager: | - |
| Company: | - |
| CharCountWithSpaces: | 370049 |
| AppVersion: | 11.9999 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 31 |
| CompObjUserType: | ???????? Microsoft Office Word |
| LastPrinted: | 0000:00:00 00:00:00 |
| RevisionNumber: | 64 |
| TotalEditTime: | 3.8 hours |
| Words: | 55341 |
| Characters: | 315448 |
| Pages: | 1 |
| Paragraphs: | 740 |
| Lines: | 2628 |
Total processes
63
Monitored processes
23
Malicious processes
3
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1328 --field-trial-handle=1104,i,11811145926870220921,4805694444176685858,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1544 --field-trial-handle=1104,i,11811145926870220921,4805694444176685858,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1152 --field-trial-handle=1104,i,11811145926870220921,4805694444176685858,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=2536 --field-trial-handle=1104,i,11811145926870220921,4805694444176685858,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1276 | "C:\Windows\System32\rundll32.exe" C:\Users\Public\Documents\1.mstsc, dpi360ntW | C:\Windows\System32\rundll32.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1844 | "C:\Windows\System32\rundll32.exe" C:\Users\Public\Documents\1.mstsc, dpi360ntW | C:\Windows\System32\rundll32.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1608 --field-trial-handle=1104,i,11811145926870220921,4805694444176685858,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3940 --field-trial-handle=1104,i,11811145926870220921,4805694444176685858,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
14 511
Read events
13 492
Write events
713
Delete events
306
Modification events
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: B0090000F80B4C4E59D0DB0100000000 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LCCache\Themes\1033 |
| Operation: | delete value | Name: | NextUpdate |
Value: | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LCCache\WordDocParts\1033 |
| Operation: | delete value | Name: | NextUpdate |
Value: | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LCCache\SmartArt\1033 |
| Operation: | delete value | Name: | NextUpdate |
Value: | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2! |
Value: 7F322100B009000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 1/! |
Value: 312F2100B0090000010000000000000000000000 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
Executable files
1
Suspicious files
56
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1BA1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2336 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR79DE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1560 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6D75.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1bda01.TMP | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\Public\Documents\1.mstsc | executable | |
MD5:91314D1CDD3BFB38DABA9273730ED1A4 | SHA256:BF140B914FAA90269FEA9C1DDDB55C01CF94E623F8A9E72DF74DEC359FB4068E | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1bdbb6.TMP | text | |
MD5:FA25AF7098FC1571F24F200A9D105D58 | SHA256:4F40C87070B7A151FB241CCF36E7027AA703C15CA0ACB0A1759DA07B2C318574 | |||
| 2988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\hwvlw0yl.xf1.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3300 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ouada1ur.t4h.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
22
DNS requests
12
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2988 | powershell.exe | 91.92.109.142:80 | — | Neterra Ltd. | BG | unknown |
2988 | powershell.exe | 192.99.255.33:80 | — | OVH SAS | US | unknown |
3300 | powershell.exe | 91.92.109.142:80 | — | Neterra Ltd. | BG | unknown |
2988 | powershell.exe | 185.183.98.15:80 | — | Host Sailor Ltd | NL | unknown |
3300 | powershell.exe | 192.99.255.33:80 | — | OVH SAS | US | unknown |
2988 | powershell.exe | 172.96.189.216:80 | — | HAWKHOST | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
rundll32.exe | DLL_PROCESS_ATTACH |
rundll32.exe | pathname=C:\Users\admin\AppData\Local\Temp\2.ps1 |
rundll32.exe | Function start
|
rundll32.exe | DLL_PROCESS_DETACH |
rundll32.exe | Function start
|
rundll32.exe | DLL_PROCESS_ATTACH |
rundll32.exe | pathname=C:\Users\admin\AppData\Local\Temp\2.ps1 |
rundll32.exe | DLL_PROCESS_DETACH |