| File name: | 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0 |
| Full analysis: | https://app.any.run/tasks/211906c5-38ac-40f5-a782-5fc04386984f |
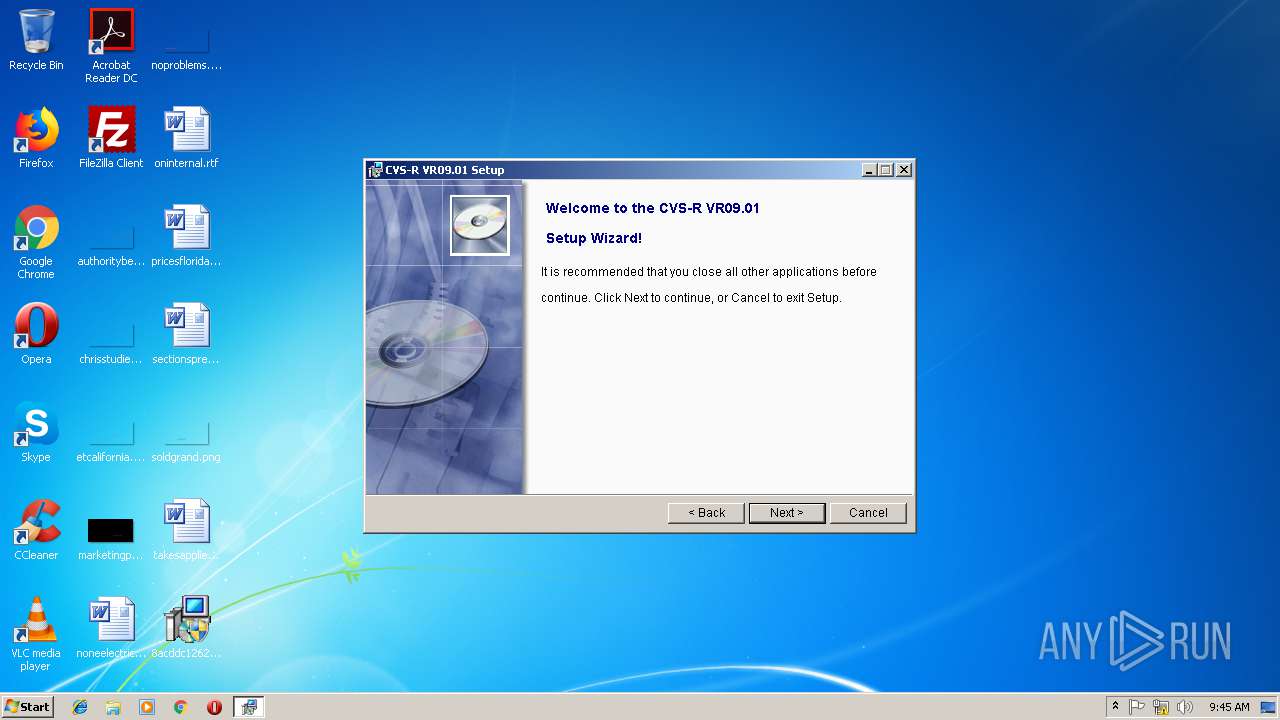
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 09:45:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F261C02E954471354C65ABD55F57B336 |
| SHA1: | EBD134D63DE56E81CD0E32A2092605DAB7A8187A |
| SHA256: | 8ACDDC1262C5A926CEA343B1D8D93CCBBE70D5182313EBD8EDB7F4219C4BC1B0 |
| SSDEEP: | 49152:kAkxGF35xTSRTDe+858E8n3tW85fxiSNjB/AAvUOxeW2kB59kKOOjZ722:kVxG55xMnHvE83tWepiSN9Ib8xe1OjZ/ |
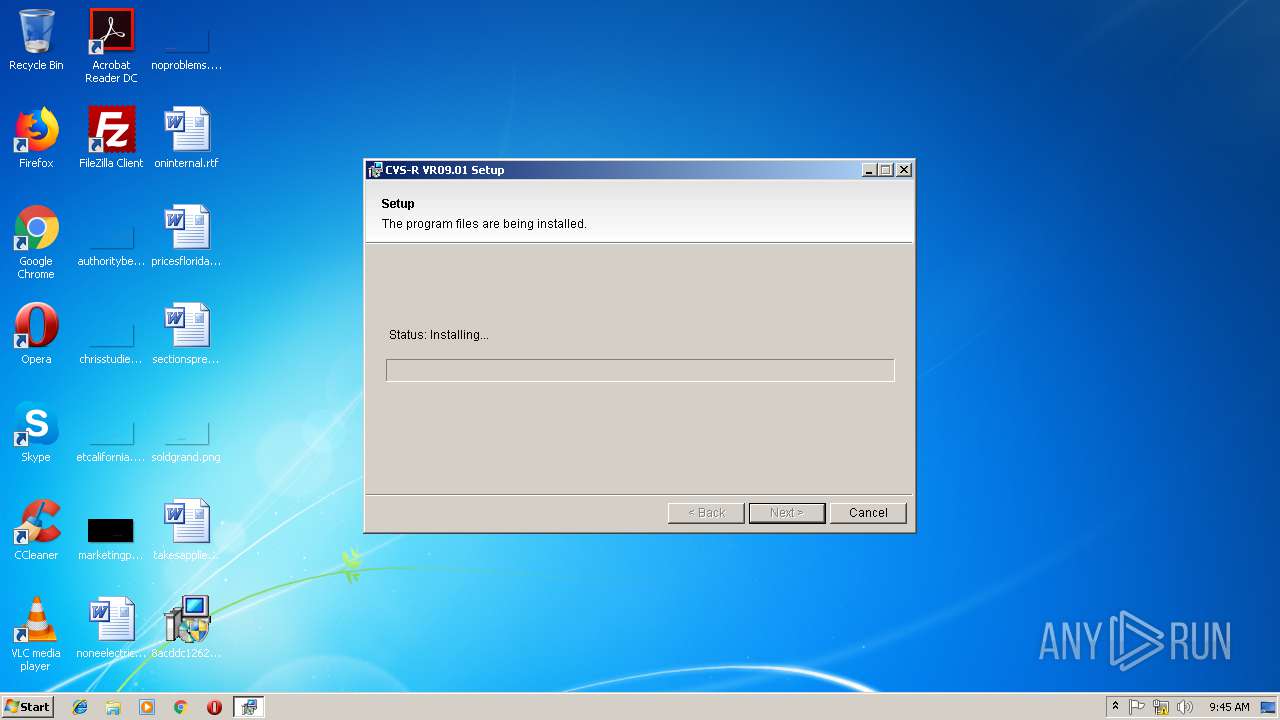
MALICIOUS
Application was dropped or rewritten from another process
- pLanguage.exe (PID: 2920)
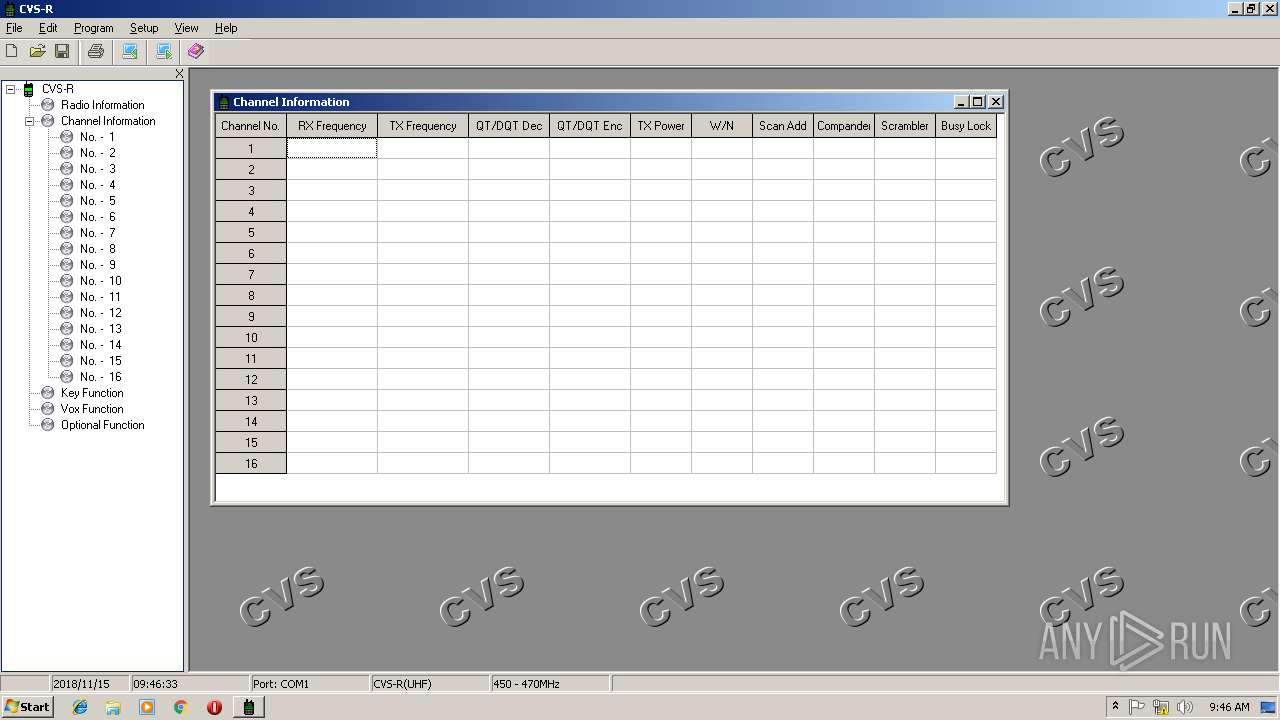
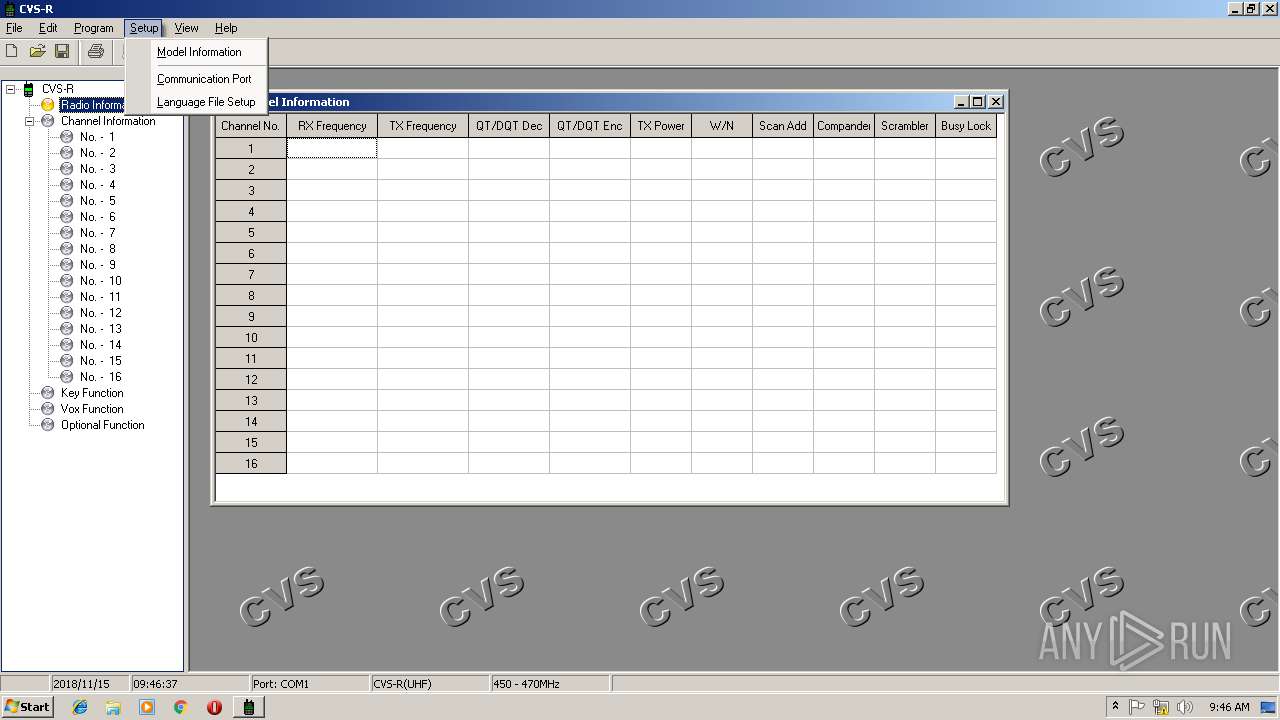
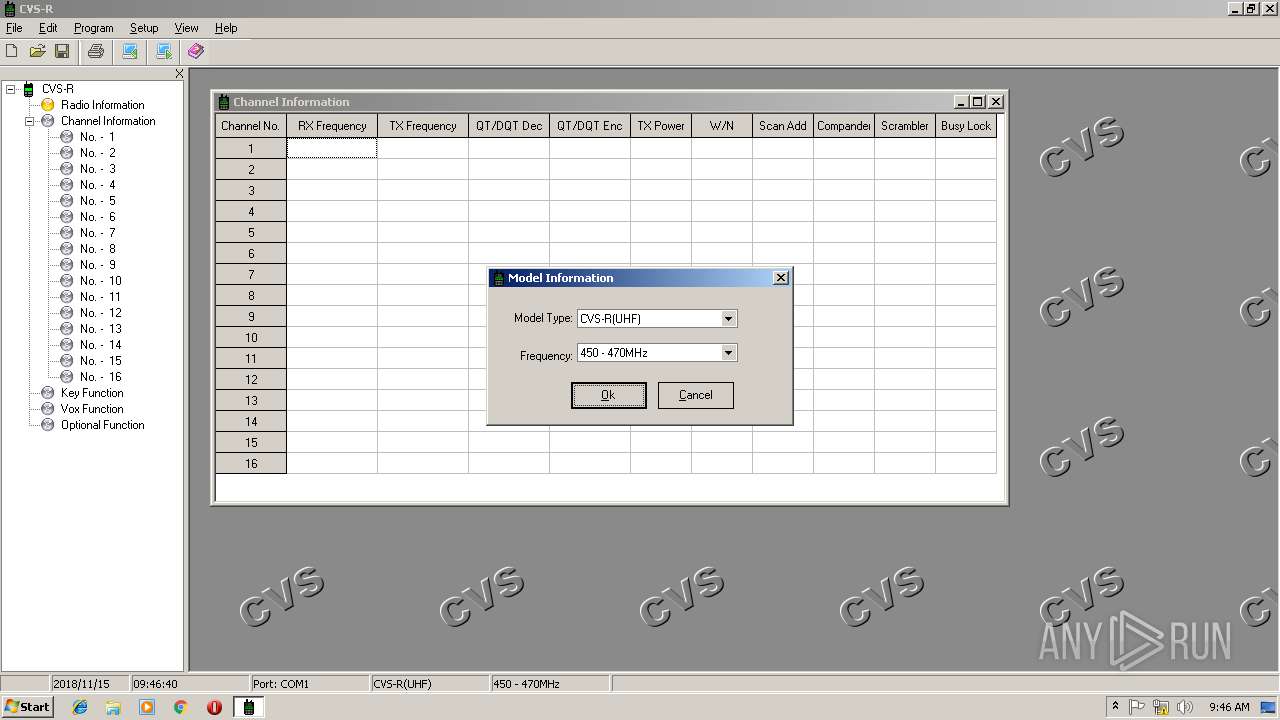
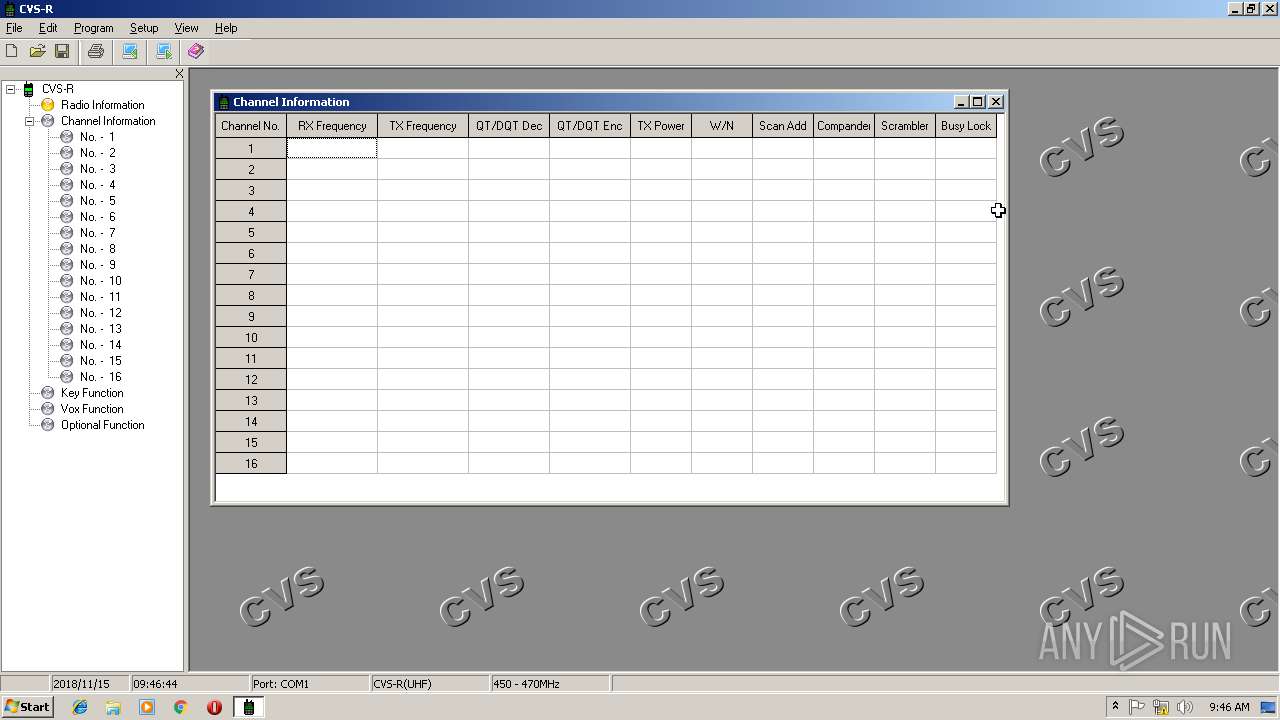
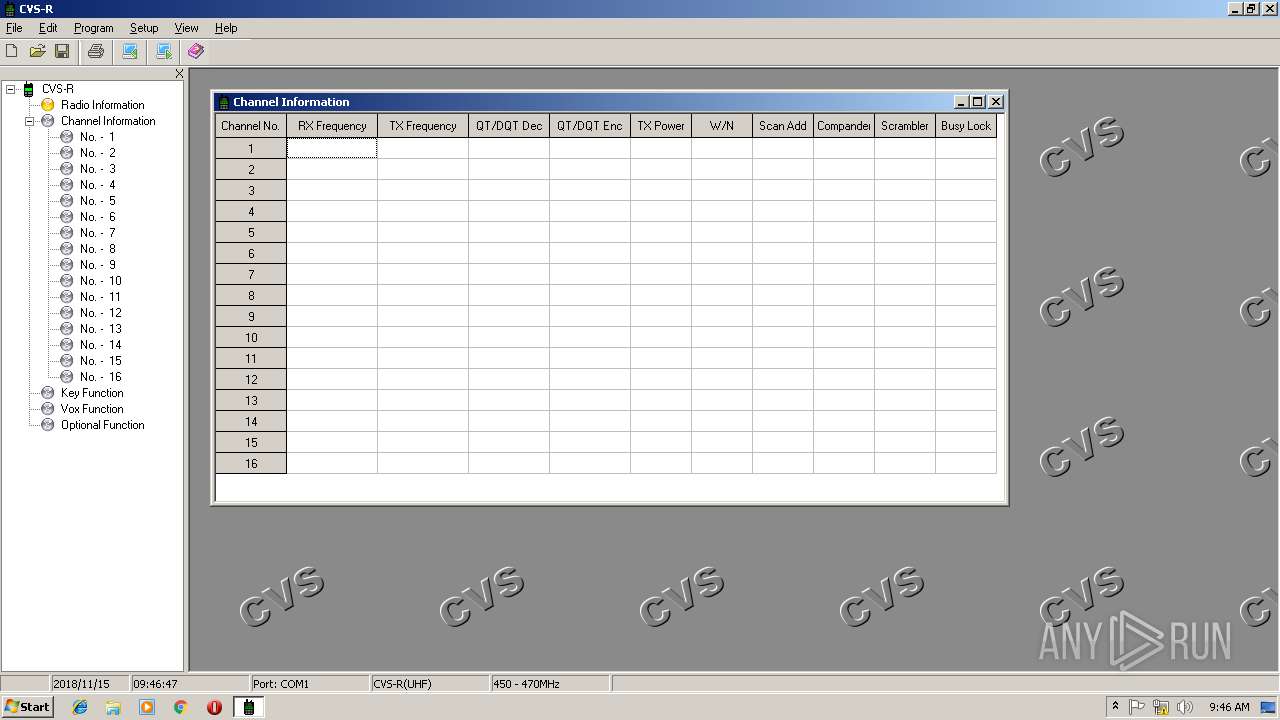
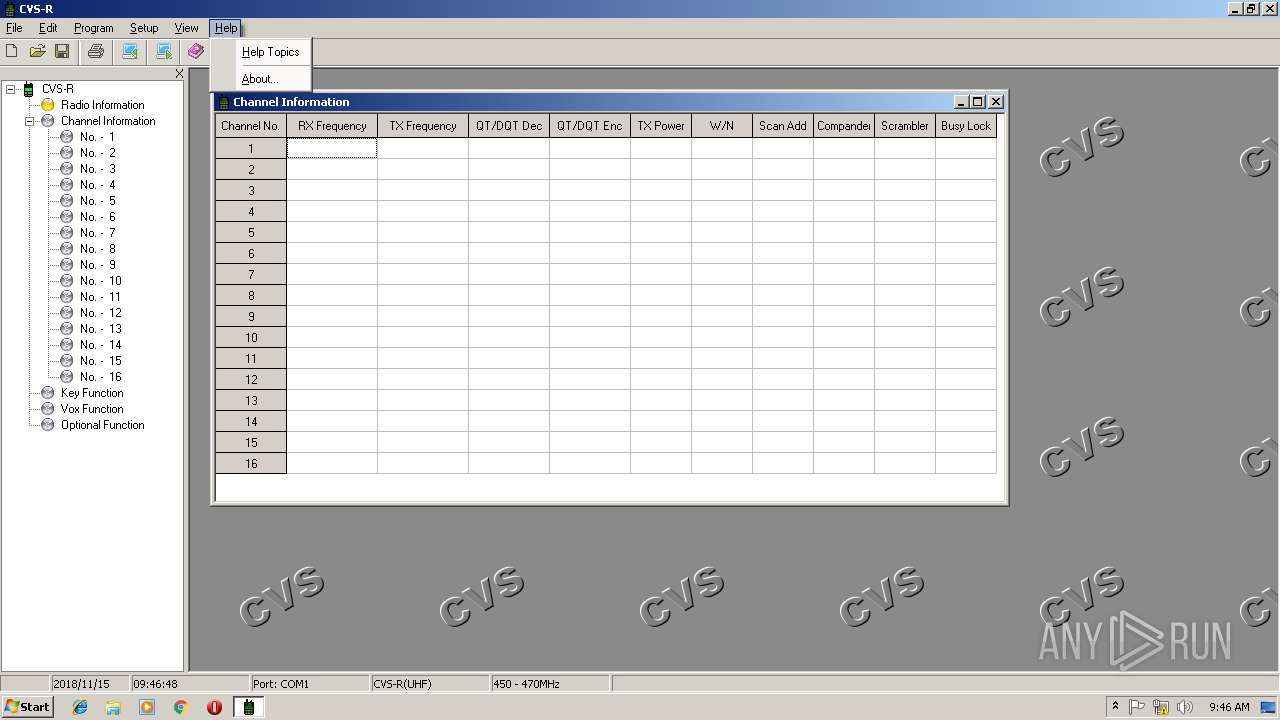
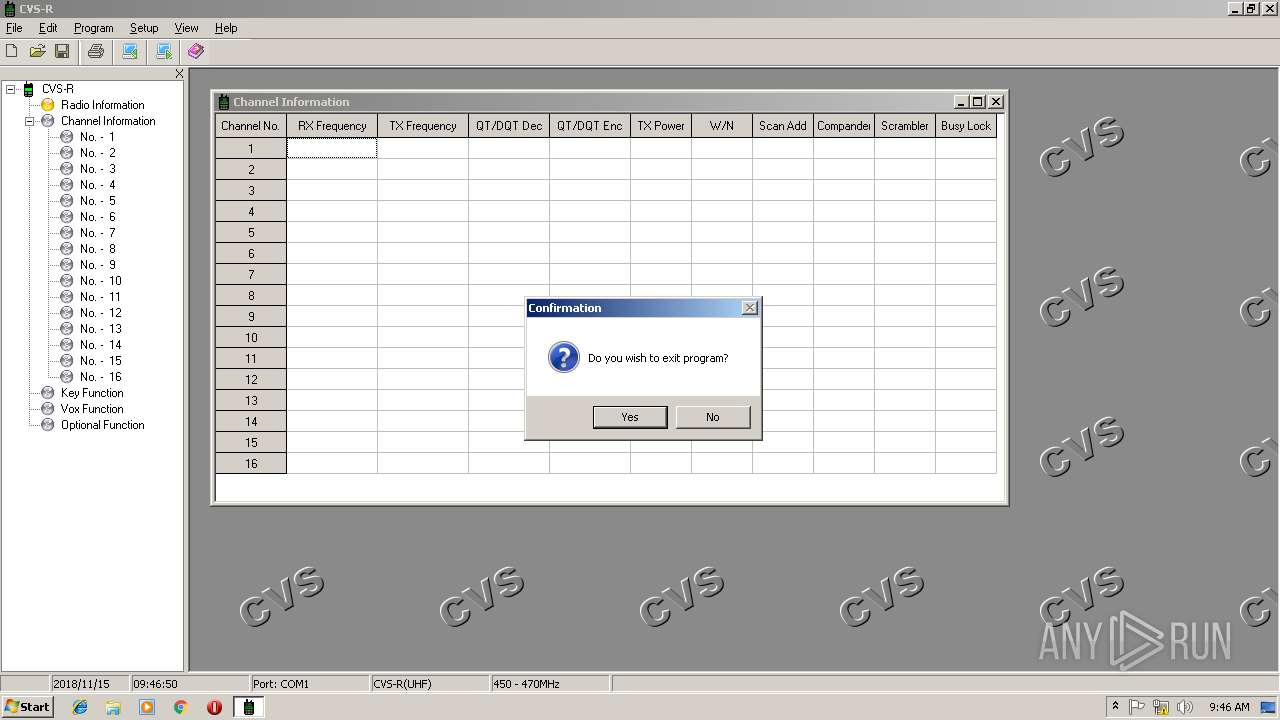
- CVSR.exe (PID: 3240)
- CVSR.exe (PID: 2832)
SUSPICIOUS
Executable content was dropped or overwritten
- 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe (PID: 3012)
Creates files in the Windows directory
- 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe (PID: 3012)
Modifies the open verb of a shell class
- 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe (PID: 3012)
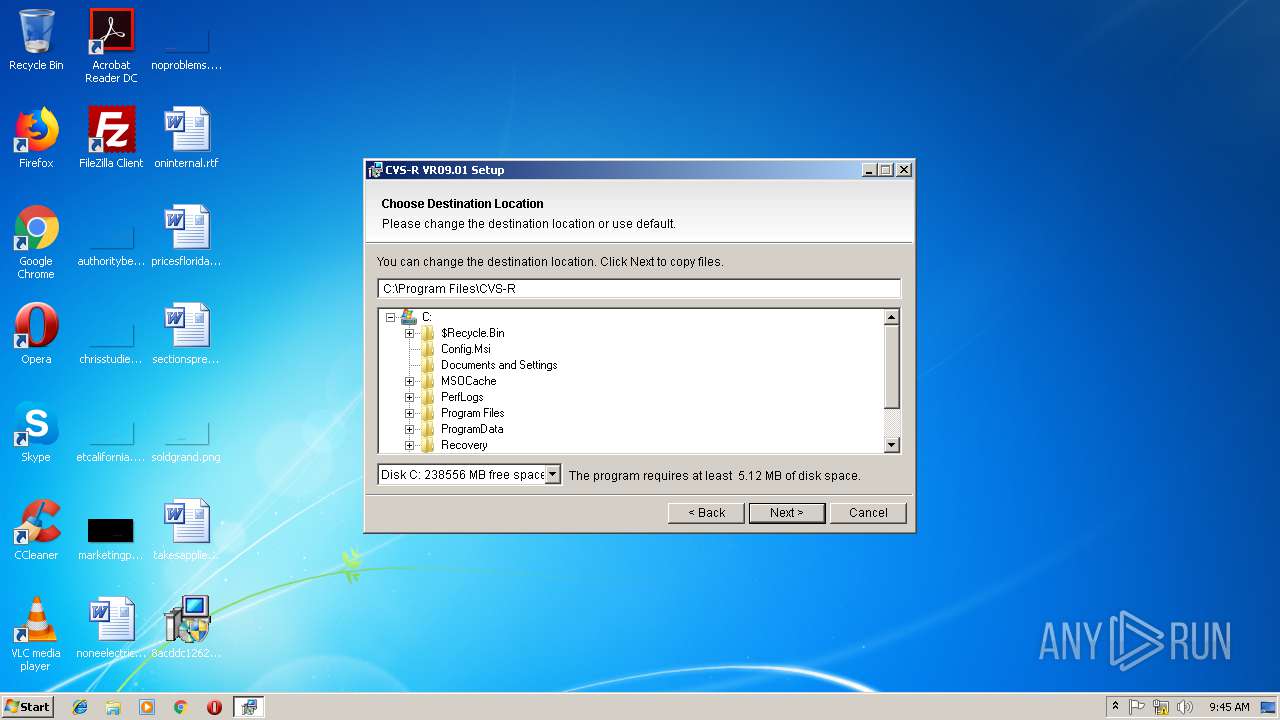
Creates files in the program directory
- 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe (PID: 3012)
- CVSR.exe (PID: 3240)
Creates a software uninstall entry
- 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe (PID: 3012)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:09:09 14:21:56+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 425984 |
| InitializedDataSize: | 151552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x49a71 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.4.6.0 |
| ProductVersionNumber: | 5.4.6.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileVersion: | 5, 4, 6, 0 |
| ProductName: | YingInstall |
| ProductVersion: | 5, 4, 6, 0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Sep-2007 12:21:56 |
| Detected languages: |
|
| FileVersion: | 5, 4, 6, 0 |
| ProductName: | YingInstall |
| ProductVersion: | 5, 4, 6, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 09-Sep-2007 12:21:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00067CEB | 0x00068000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.598 |
.rdata | 0x00069000 | 0x0001B7A6 | 0x0001C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16396 |
.data | 0x00085000 | 0x00012320 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.52164 |
.rsrc | 0x00098000 | 0x00004970 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.81074 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.65542 | 86 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.02695 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
3 | 2.74274 | 180 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
4 | 2.34038 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
5 | 2.34004 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
6 | 2.51649 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
7 | 2.45401 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
8 | 2.34864 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
9 | 2.82349 | 352 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
10 | 2.34864 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WINMM.dll |
Total processes
41
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2532 | "C:\Users\admin\Desktop\8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe" | C:\Users\admin\Desktop\8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 5, 4, 6, 0 Modules
| |||||||||||||||
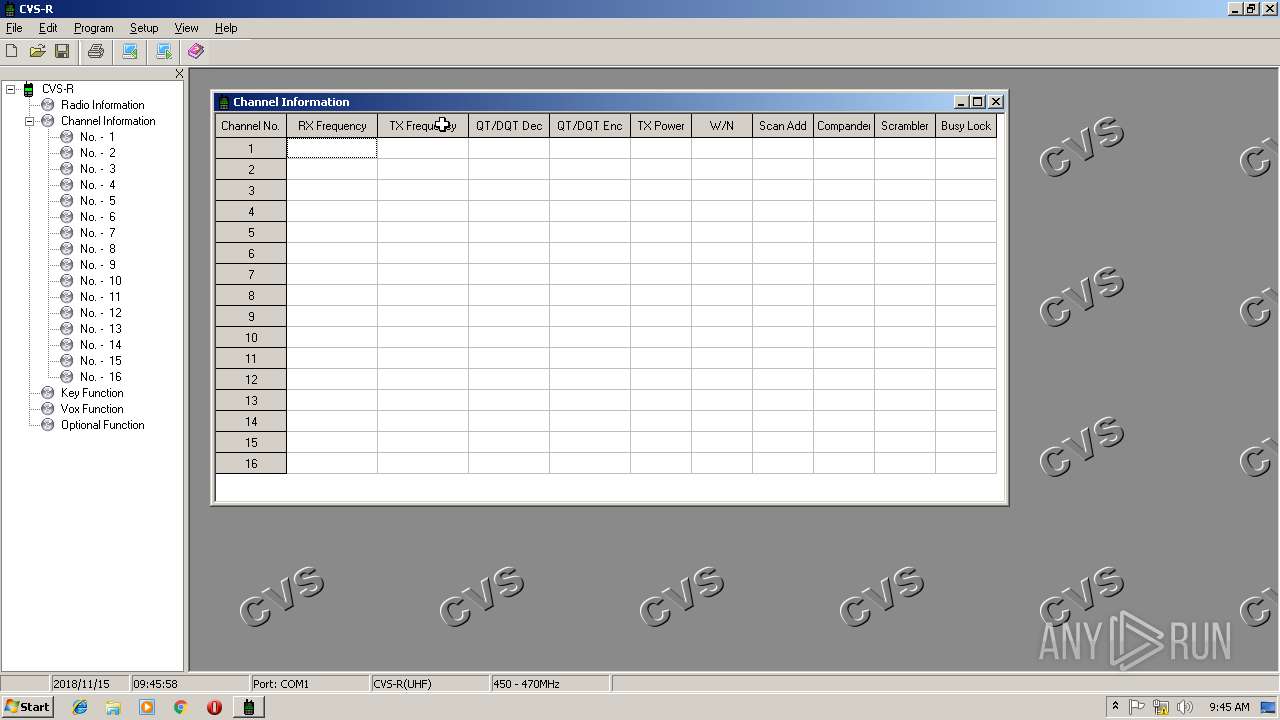
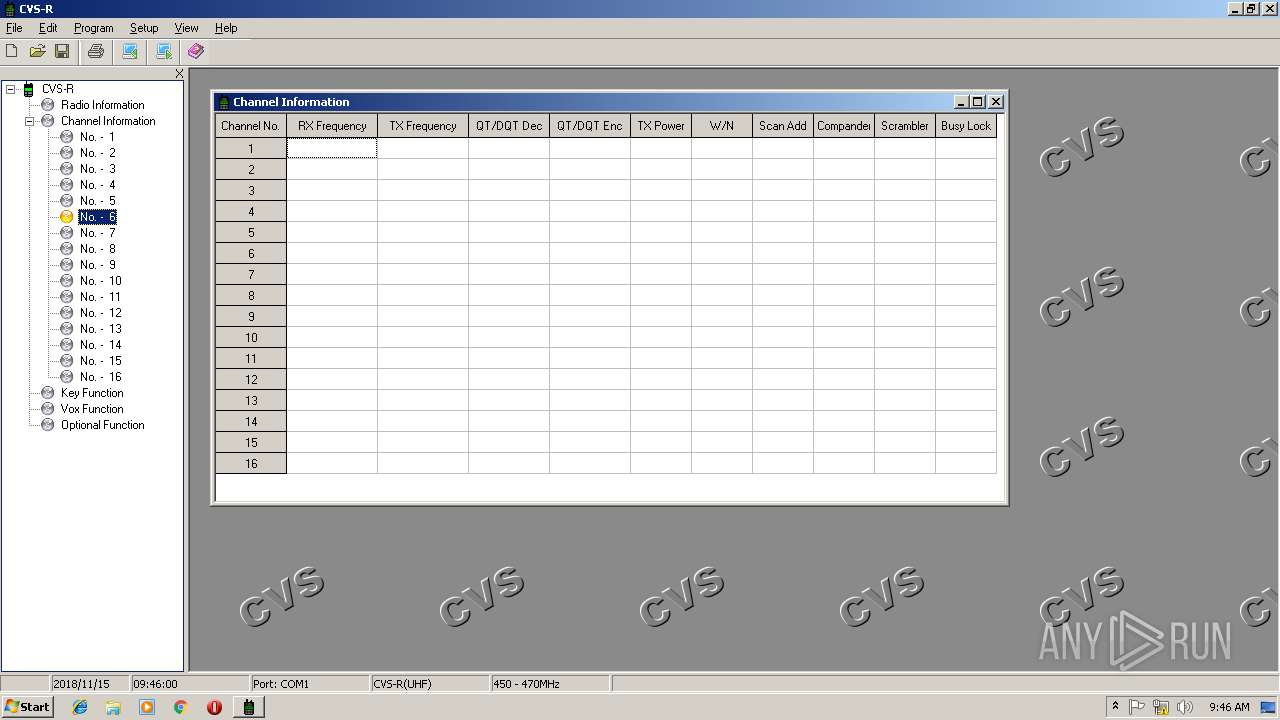
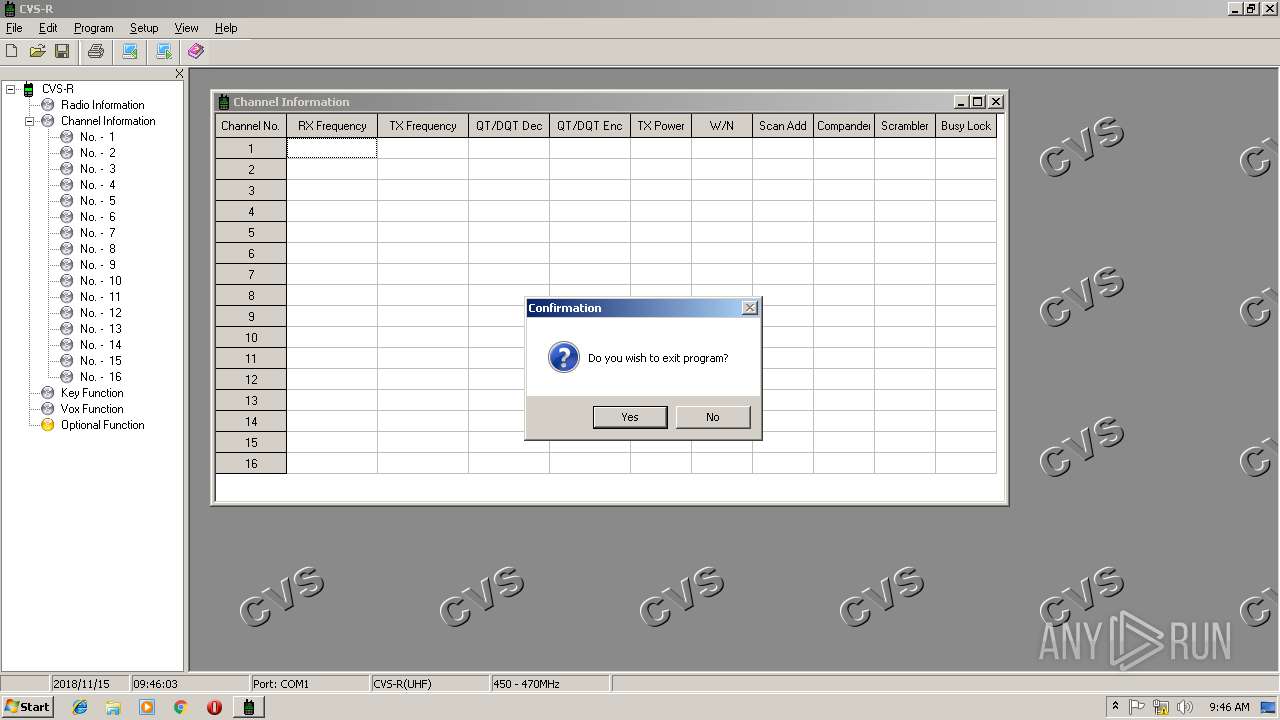
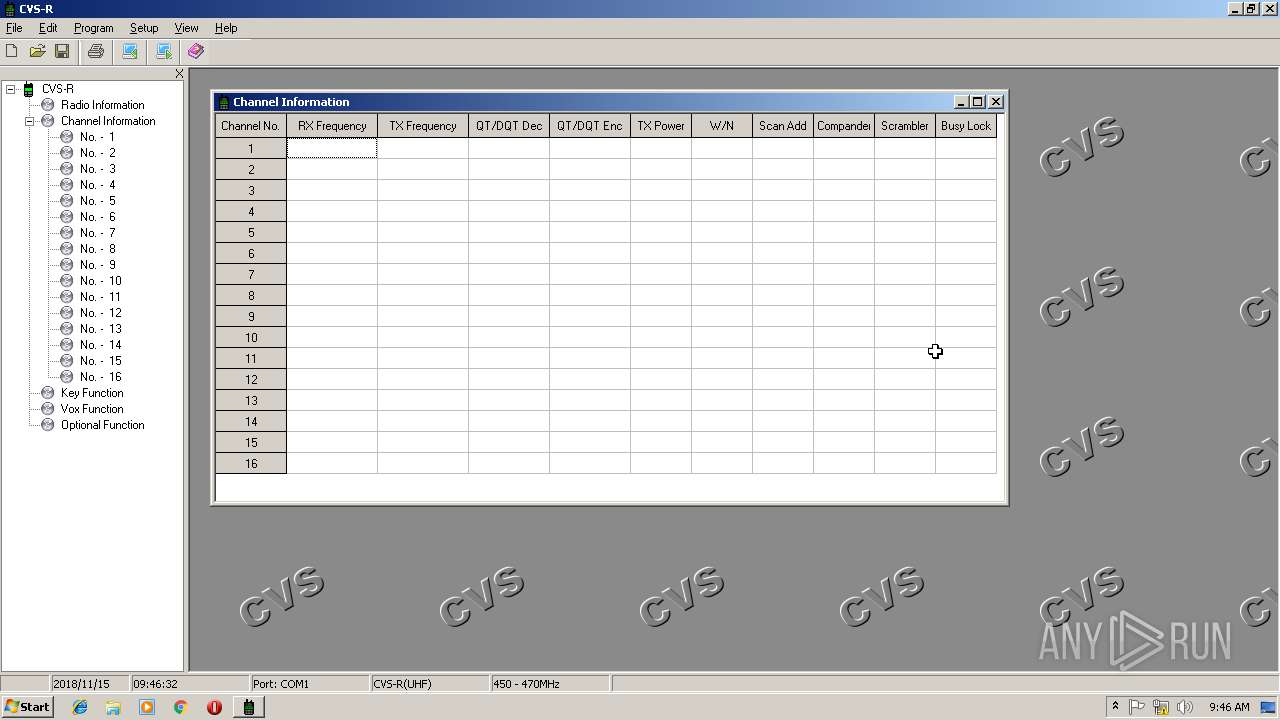
| 2832 | "C:\Program Files\CVS-R\CVSR.exe" | C:\Program Files\CVS-R\CVSR.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2920 | "C:\Program Files\CVS-R\pLanguage.exe" | C:\Program Files\CVS-R\pLanguage.exe | — | 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3012 | "C:\Users\admin\Desktop\8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe" | C:\Users\admin\Desktop\8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 5, 4, 6, 0 Modules
| |||||||||||||||
| 3240 | "C:\Program Files\CVS-R\CVSR.exe" | C:\Program Files\CVS-R\CVSR.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
388
Read events
376
Write events
12
Delete events
0
Modification events
| (PID) Process: | (3012) 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\YingSoft\YingInstall |
| Operation: | write | Name: | LastVersion |
Value: 5.45 | |||
| (PID) Process: | (3012) 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CVS-R VR09.01 |
| Operation: | write | Name: | DisplayName |
Value: CVS-R VR09.01 | |||
| (PID) Process: | (3012) 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CVS-R VR09.01 |
| Operation: | write | Name: | UninstallString |
Value: C:\Windows\Ying-UnInstall.exe C:\Program Files\CVS-R\CVS-R VR09.01.UCIP | |||
| (PID) Process: | (3012) 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.UCIP |
| Operation: | write | Name: | |
Value: YingUnInstall | |||
| (PID) Process: | (3012) 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\YingUnInstall |
| Operation: | write | Name: | |
Value: Uninstall File | |||
| (PID) Process: | (3012) 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\YingUnInstall\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Windows\Ying-UnInstall.exe,0 | |||
| (PID) Process: | (3012) 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\YingUnInstall\Shell\Open |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (3012) 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\YingUnInstall\Shell\Open\Command |
| Operation: | write | Name: | |
Value: "C:\Windows\Ying-UnInstall.exe" %1 | |||
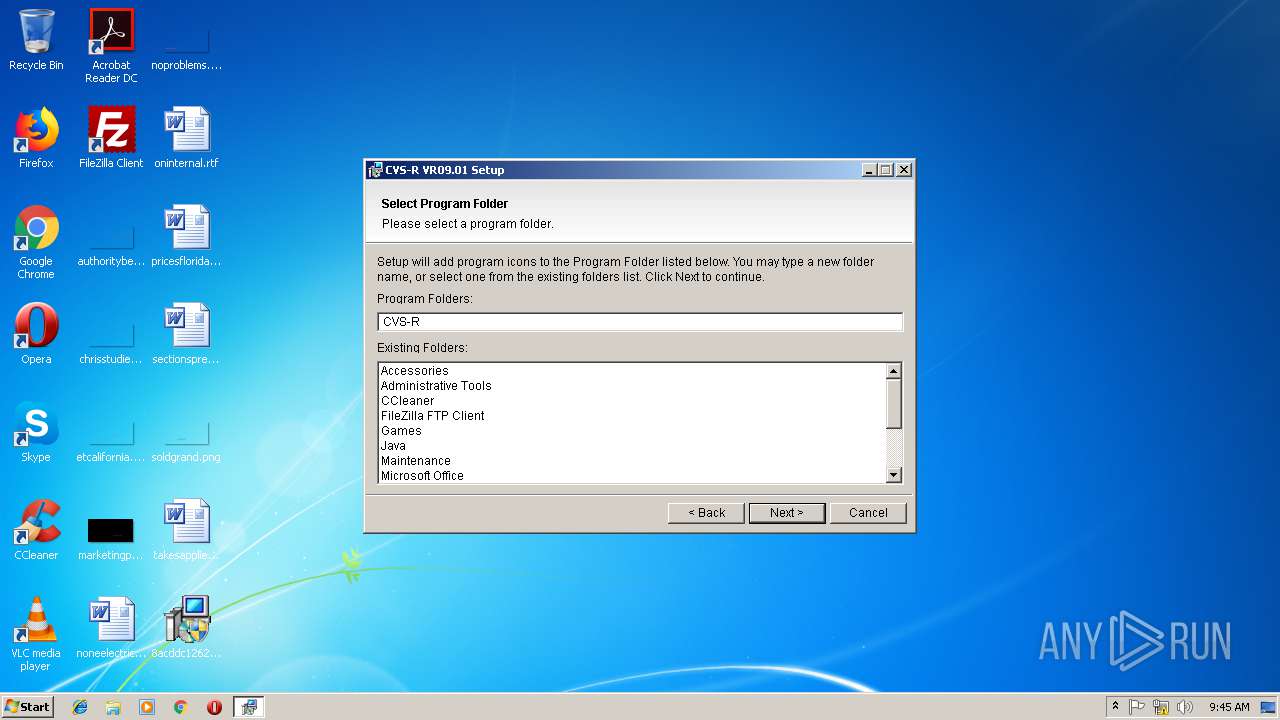
| (PID) Process: | (3012) 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\YingSoft\YingInstall\ZWX\CVS-R\VR09.01 |
| Operation: | write | Name: | ProgramFolder |
Value: C:\ProgramData\Microsoft\Windows\Start Menu\Programs\CVS-R | |||
| (PID) Process: | (3012) 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\YingSoft\YingInstall\ZWX\CVS-R\VR09.01 |
| Operation: | write | Name: | UnInstallFileLink |
Value: C:\ProgramData\Microsoft\Windows\Start Menu\Programs\CVS-R\Uninstall CVS-R VR09.01.lnk | |||
Executable files
3
Suspicious files
0
Text files
15
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | C:\Users\admin\AppData\Local\Temp\20181115094538188~YingInstall-TopFramePicture.bmp | image | |
MD5:3484D86629E1919532FFC79725C9CAA2 | SHA256:51AC8618CE8C51B73FE0439C1997BCA3F6CAF7D9BF50AD2F2330A8C10E37ECFC | |||
| 3012 | 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | C:\Users\admin\AppData\Local\Temp\20181115094538188~YingInstall-Language.ini | text | |
MD5:FB9971A9CB19A9DDA5CAA9D64ABFD04D | SHA256:F1B856EFB5773500DA745260B19CA3ECC4496DB1FF1582134CD4A430C0C7379F | |||
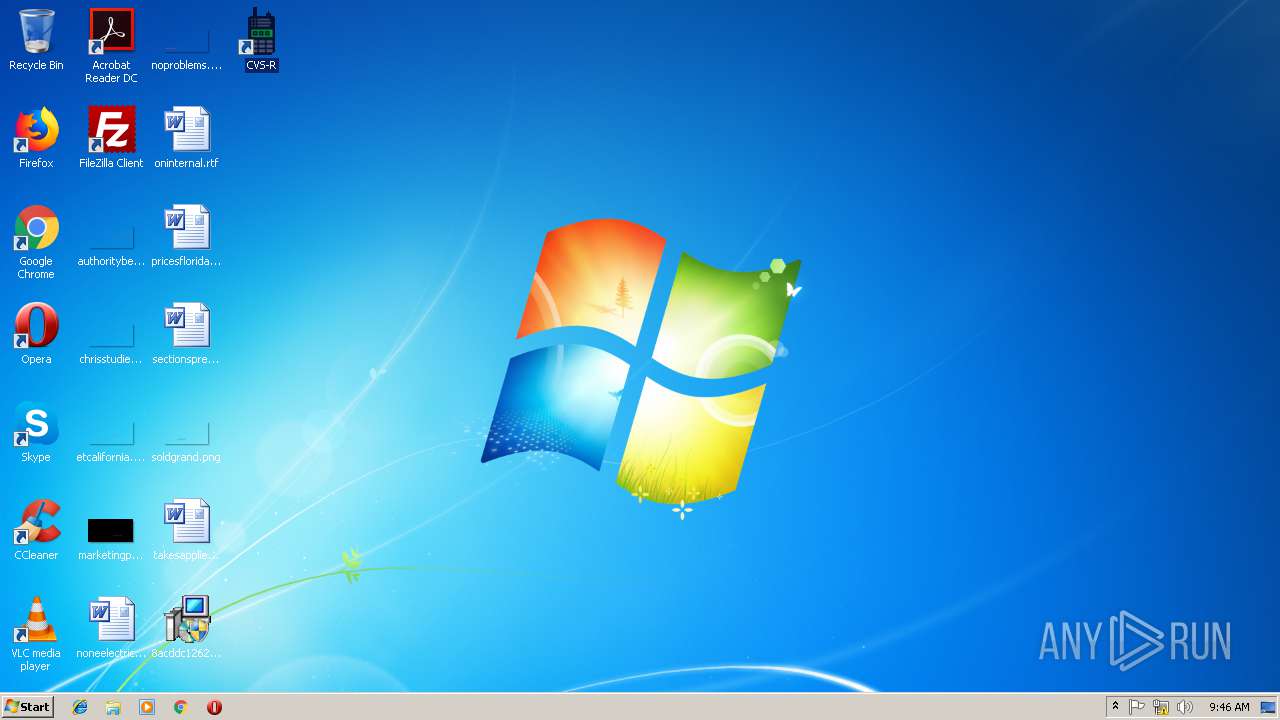
| 3012 | 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | C:\Users\Administrator\Desktop\CVS-R.Lnk | lnk | |
MD5:— | SHA256:— | |||
| 3012 | 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\CVS-R\Uninstall CVS-R VR09.01.Lnk | lnk | |
MD5:— | SHA256:— | |||
| 3012 | 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | C:\Program Files\CVS-R\SysInfo.Ini | text | |
MD5:F36334679ED9A9C79BE0E3F5F918A966 | SHA256:1FFE4912A9D7C7A9A32F3E2AD0008CB8FE5B63DFB67E7F4B8304FD05806267F9 | |||
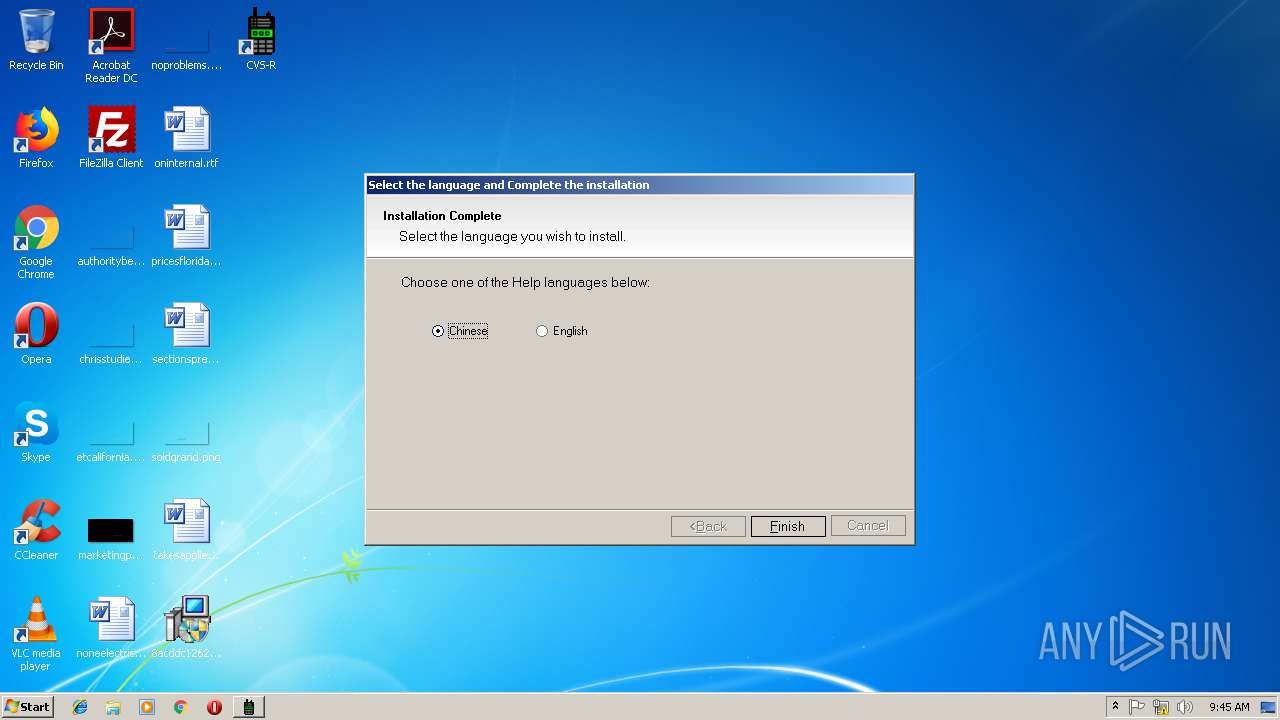
| 3012 | 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | C:\Program Files\CVS-R\Chinese.Ini | text | |
MD5:0C24B94766496DE9A23AF23D3DCE3070 | SHA256:EEA7FC4EFF540F04F8B3A7BD768120034B013545B602107AE0C708BB3BDC7400 | |||
| 3012 | 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | C:\Program Files\CVS-R\English.Ini | text | |
MD5:F2D40EF80128E301F82748D1EA2074FB | SHA256:1151756A7D5816BFEAAF0873A0C808B6A57A56E2737F4CD36876D5B8DCEBC933 | |||
| 3012 | 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | C:\Program Files\CVS-R\CVSR_Chinese.chm | chm | |
MD5:3FEC22D1E6167DA7E5C9268574FA50D9 | SHA256:B8399109485DCF2CC6BFBCA97FDF866560DF198F201F9DC78A949A2E481A0070 | |||
| 3012 | 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | C:\Program Files\CVS-R\CVSR_English.chm | chm | |
MD5:BD20930E0486A67EA663B2A1B57A265D | SHA256:CEC56B92EA61730D134506BE2DE3AA4D5710D9EB20ED06A466F060A3F8897E86 | |||
| 3012 | 8acddc1262c5a926cea343b1d8d93ccbbe70d5182313ebd8edb7f4219c4bc1b0.exe | C:\Program Files\CVS-R\Print.fr3 | xml | |
MD5:0F9820A0956D22612CB6C7B5C1C94BC8 | SHA256:8708B89706ACBECE88C9664793A073B28C08A3226946B580063B3C49272833AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report