| download: | click |
| Full analysis: | https://app.any.run/tasks/26ead472-5203-4a51-bab4-2a91b09d181e |
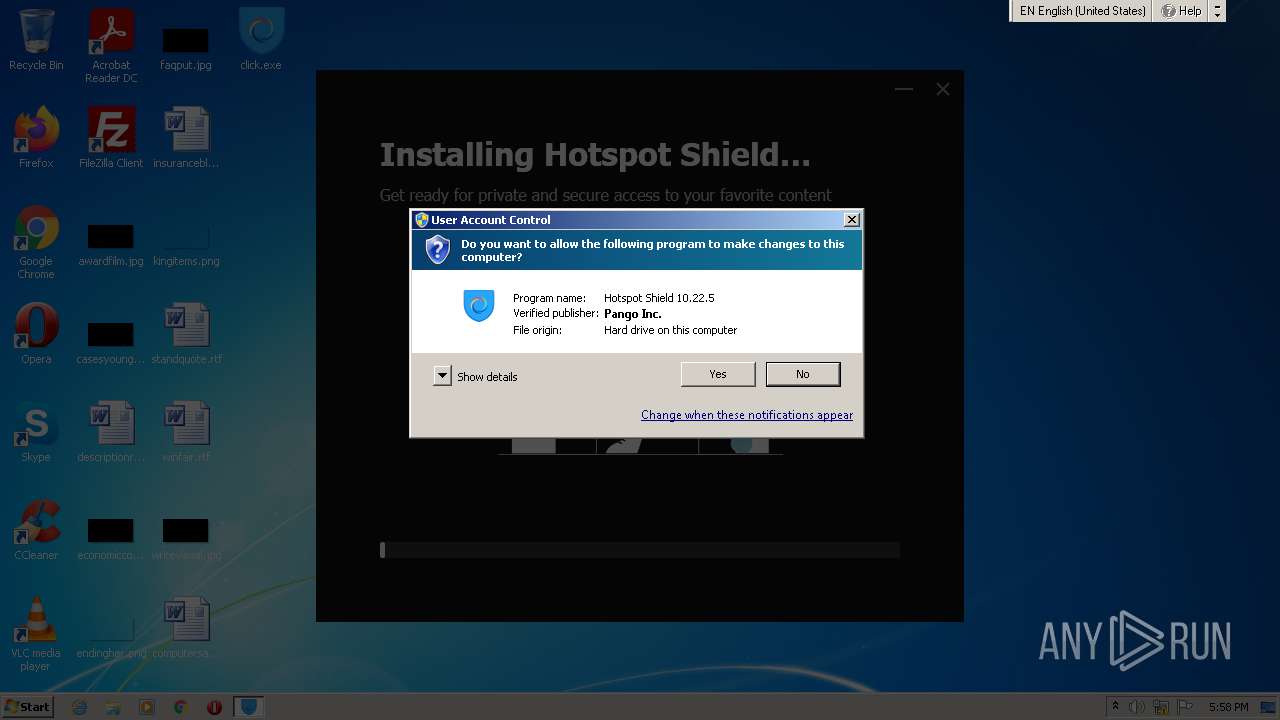
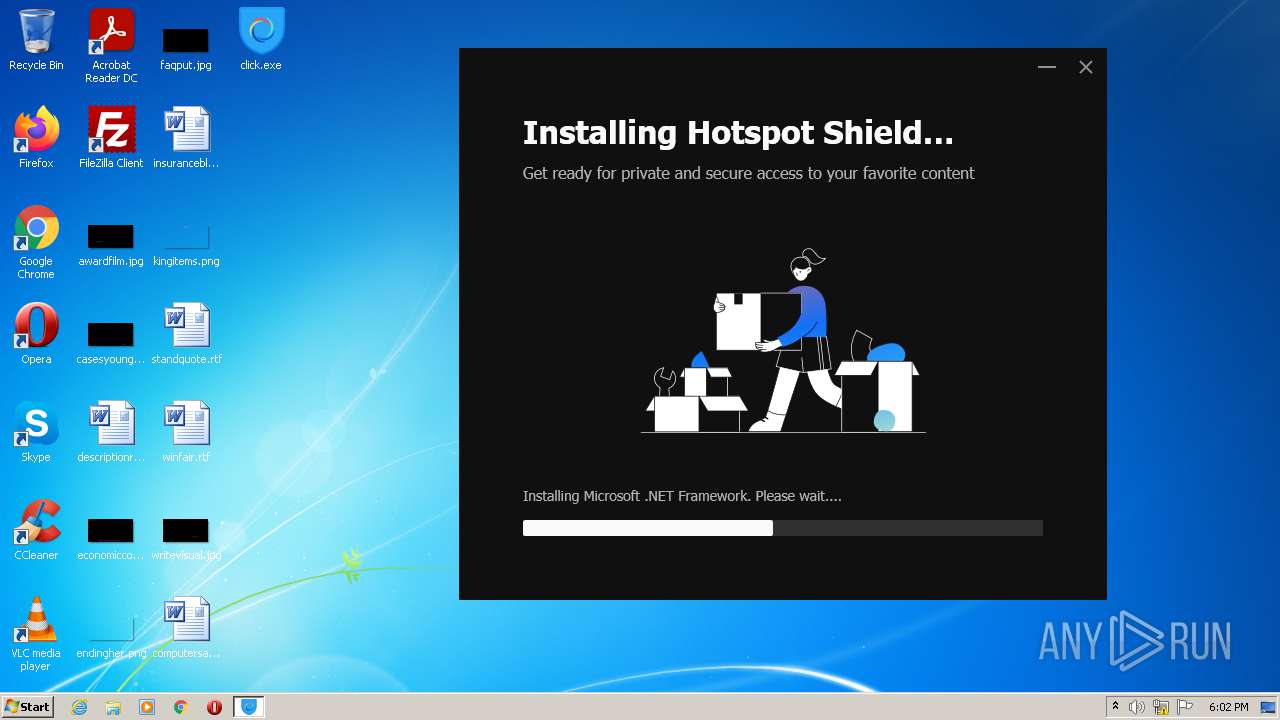
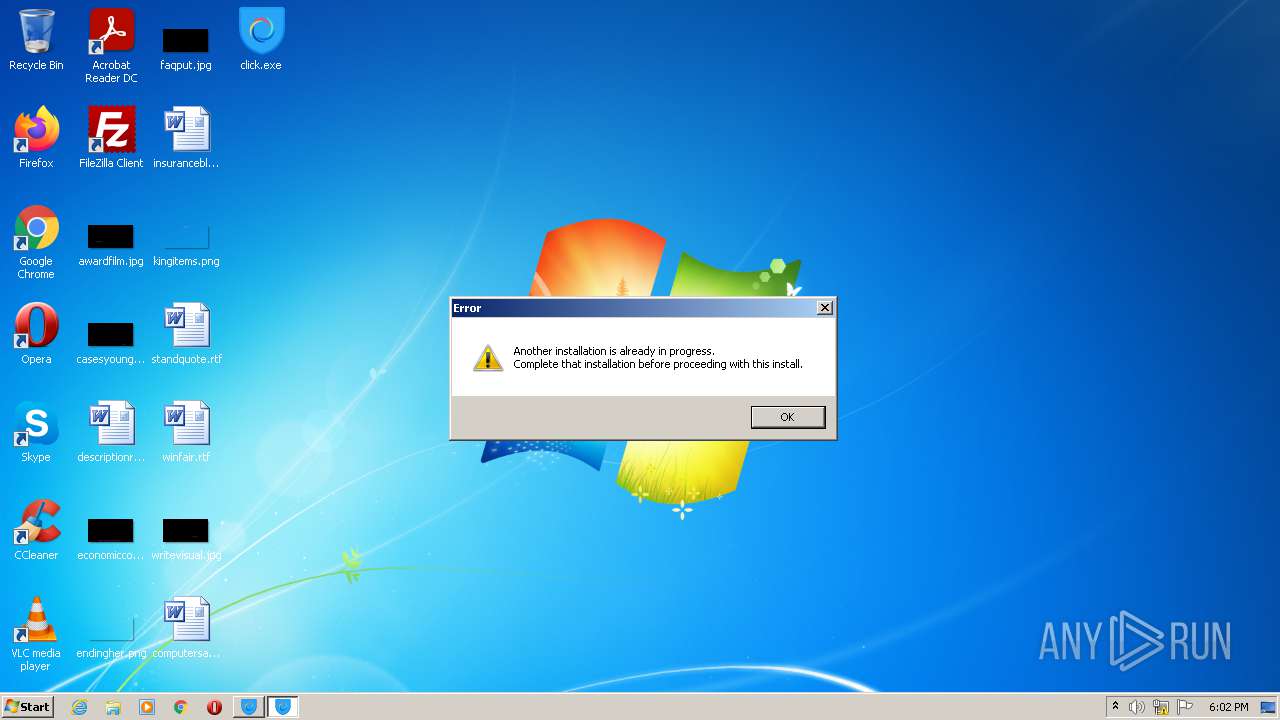
| Verdict: | Malicious activity |
| Analysis date: | November 18, 2021, 17:58:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E9D5F515458D905D99241F91A367A446 |
| SHA1: | BB46A573D8577AC3661E5FED1045F6DEA5D12FC2 |
| SHA256: | 8ACBA6A43E3E58ED56CEED407F4AE8AC22F13EAC419E73FD60415AB5CB9E266C |
| SSDEEP: | 393216:B8SHqzVhrv2K9gDw1q96j0PcPy3p2tWUhz24SejlDdq0IuqyZ4Bv+IZhuiEM3g9C:B8BVJf1Wc0PRoS4Rzq0hqZFZIEI/AUU |
MALICIOUS
Application was dropped or rewritten from another process
- click.exe (PID: 2148)
- HSS-10.22.5-install-plain-773-plain.exe (PID: 3988)
- ndp48-web.exe (PID: 656)
- Setup.exe (PID: 1280)
- SetupUtility.exe (PID: 3024)
- SetupUtility.exe (PID: 2960)
- ServiceModelReg.exe (PID: 3820)
- regtlibv12.exe (PID: 3240)
- regtlibv12.exe (PID: 2936)
- regtlibv12.exe (PID: 2344)
- aspnet_regiis.exe (PID: 1032)
- regtlibv12.exe (PID: 3956)
- regtlibv12.exe (PID: 3644)
- regtlibv12.exe (PID: 2656)
- regtlibv12.exe (PID: 2432)
- click.exe (PID: 1520)
- ngen.exe (PID: 3504)
- mscorsvw.exe (PID: 2744)
- mscorsvw.exe (PID: 3600)
- mscorsvw.exe (PID: 2356)
- ngen.exe (PID: 2248)
- ngen.exe (PID: 464)
- mscorsvw.exe (PID: 3420)
- mscorsvw.exe (PID: 2152)
- mscorsvw.exe (PID: 3860)
- mscorsvw.exe (PID: 3544)
- mscorsvw.exe (PID: 2884)
- mscorsvw.exe (PID: 3912)
- mscorsvw.exe (PID: 1004)
- mscorsvw.exe (PID: 3240)
- mscorsvw.exe (PID: 4064)
- mscorsvw.exe (PID: 664)
- mscorsvw.exe (PID: 3304)
- mscorsvw.exe (PID: 2376)
- mscorsvw.exe (PID: 2368)
- mscorsvw.exe (PID: 900)
- mscorsvw.exe (PID: 1360)
Loads dropped or rewritten executable
- click.exe (PID: 2148)
- Setup.exe (PID: 1280)
- MsiExec.exe (PID: 764)
- MsiExec.exe (PID: 680)
- msiexec.exe (PID: 3036)
- svchost.exe (PID: 1992)
- aspnet_regiis.exe (PID: 1032)
- click.exe (PID: 1520)
- ngen.exe (PID: 3504)
- mscorsvw.exe (PID: 2744)
- mscorsvw.exe (PID: 3600)
- mscorsvw.exe (PID: 2356)
- ngen.exe (PID: 2248)
- ngen.exe (PID: 464)
- mscorsvw.exe (PID: 2152)
- mscorsvw.exe (PID: 3860)
- mscorsvw.exe (PID: 3420)
- mscorsvw.exe (PID: 3544)
- mscorsvw.exe (PID: 2884)
- mscorsvw.exe (PID: 3240)
- mscorsvw.exe (PID: 3912)
- mscorsvw.exe (PID: 4064)
- mscorsvw.exe (PID: 664)
- mscorsvw.exe (PID: 1004)
- mscorsvw.exe (PID: 900)
- mscorsvw.exe (PID: 2368)
- mscorsvw.exe (PID: 3304)
- mscorsvw.exe (PID: 2376)
Changes the autorun value in the registry
- HSS-10.22.5-install-plain-773-plain.exe (PID: 3988)
- msiexec.exe (PID: 3036)
Drops executable file immediately after starts
- click.exe (PID: 2576)
- click.exe (PID: 2148)
- ndp48-web.exe (PID: 656)
- click.exe (PID: 3696)
- click.exe (PID: 1520)
Actions looks like stealing of personal data
- ndp48-web.exe (PID: 656)
Changes settings of System certificates
- Setup.exe (PID: 1280)
Loads the Task Scheduler COM API
- ngen.exe (PID: 3504)
- mscorsvw.exe (PID: 2744)
- ngen.exe (PID: 2248)
- ngen.exe (PID: 464)
SUSPICIOUS
Checks supported languages
- click.exe (PID: 2576)
- HSS-10.22.5-install-plain-773-plain.exe (PID: 3988)
- click.exe (PID: 2148)
- ndp48-web.exe (PID: 656)
- Setup.exe (PID: 1280)
- SetupUtility.exe (PID: 2960)
- TMPADBE.tmp.exe (PID: 2216)
- ServiceModelReg.exe (PID: 3820)
- SetupUtility.exe (PID: 3024)
- regtlibv12.exe (PID: 3240)
- regtlibv12.exe (PID: 2344)
- regtlibv12.exe (PID: 2936)
- mofcomp.exe (PID: 2940)
- regtlibv12.exe (PID: 3956)
- regtlibv12.exe (PID: 3644)
- regtlibv12.exe (PID: 2656)
- aspnet_regiis.exe (PID: 1032)
- mofcomp.exe (PID: 608)
- click.exe (PID: 3696)
- click.exe (PID: 1520)
- ngen.exe (PID: 3504)
- mscorsvw.exe (PID: 2744)
- mscorsvw.exe (PID: 3600)
- mscorsvw.exe (PID: 2356)
- ngen.exe (PID: 464)
- mscorsvw.exe (PID: 3420)
- regtlibv12.exe (PID: 2432)
- mofcomp.exe (PID: 3204)
- ngen.exe (PID: 2248)
- mscorsvw.exe (PID: 2152)
- mscorsvw.exe (PID: 3860)
- mscorsvw.exe (PID: 3544)
- mscorsvw.exe (PID: 3240)
- mscorsvw.exe (PID: 3912)
- mscorsvw.exe (PID: 2884)
- mscorsvw.exe (PID: 4064)
- mscorsvw.exe (PID: 2376)
- mscorsvw.exe (PID: 664)
- mscorsvw.exe (PID: 1004)
- mscorsvw.exe (PID: 900)
- mscorsvw.exe (PID: 3304)
- mscorsvw.exe (PID: 2368)
Drops a file that was compiled in debug mode
- click.exe (PID: 2576)
- click.exe (PID: 2148)
- HSS-10.22.5-install-plain-773-plain.exe (PID: 3988)
- ndp48-web.exe (PID: 656)
- msiexec.exe (PID: 3036)
- click.exe (PID: 1520)
- click.exe (PID: 3696)
Drops a file with a compile date too recent
- click.exe (PID: 2148)
- click.exe (PID: 1520)
Reads the computer name
- click.exe (PID: 2148)
- HSS-10.22.5-install-plain-773-plain.exe (PID: 3988)
- ndp48-web.exe (PID: 656)
- Setup.exe (PID: 1280)
- TMPADBE.tmp.exe (PID: 2216)
- SetupUtility.exe (PID: 3024)
- SetupUtility.exe (PID: 2960)
- ServiceModelReg.exe (PID: 3820)
- mofcomp.exe (PID: 2940)
- mofcomp.exe (PID: 608)
- aspnet_regiis.exe (PID: 1032)
- mofcomp.exe (PID: 3204)
- click.exe (PID: 1520)
- ngen.exe (PID: 3504)
- mscorsvw.exe (PID: 2744)
- mscorsvw.exe (PID: 3600)
- mscorsvw.exe (PID: 2356)
- ngen.exe (PID: 464)
- mscorsvw.exe (PID: 3420)
- mscorsvw.exe (PID: 3860)
- mscorsvw.exe (PID: 2152)
- mscorsvw.exe (PID: 3544)
- mscorsvw.exe (PID: 2884)
- mscorsvw.exe (PID: 3240)
- mscorsvw.exe (PID: 3912)
- mscorsvw.exe (PID: 4064)
- mscorsvw.exe (PID: 2376)
- mscorsvw.exe (PID: 664)
- mscorsvw.exe (PID: 1004)
- mscorsvw.exe (PID: 3304)
- mscorsvw.exe (PID: 900)
- mscorsvw.exe (PID: 2368)
- ngen.exe (PID: 2248)
Reads Environment values
- click.exe (PID: 2148)
- Setup.exe (PID: 1280)
- click.exe (PID: 1520)
Searches for installed software
- click.exe (PID: 2148)
- HSS-10.22.5-install-plain-773-plain.exe (PID: 3988)
- msiexec.exe (PID: 3036)
- click.exe (PID: 1520)
Creates files in the program directory
- click.exe (PID: 2148)
- HSS-10.22.5-install-plain-773-plain.exe (PID: 3988)
Starts itself from another location
- click.exe (PID: 2148)
Creates a software uninstall entry
- HSS-10.22.5-install-plain-773-plain.exe (PID: 3988)
- msiexec.exe (PID: 3036)
Executable content was dropped or overwritten
- click.exe (PID: 2576)
- HSS-10.22.5-install-plain-773-plain.exe (PID: 3988)
- click.exe (PID: 2148)
- ndp48-web.exe (PID: 656)
- TMPADBE.tmp.exe (PID: 2216)
- Setup.exe (PID: 1280)
- msiexec.exe (PID: 3036)
- click.exe (PID: 3696)
- click.exe (PID: 1520)
Reads CPU info
- Setup.exe (PID: 1280)
Executed as Windows Service
- msiexec.exe (PID: 3036)
Application launched itself
- msiexec.exe (PID: 3036)
- mscorsvw.exe (PID: 2744)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3036)
Drops a file with too old compile date
- msiexec.exe (PID: 3036)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 3036)
- aspnet_regiis.exe (PID: 1032)
Checks for the .NET to be installed
- msiexec.exe (PID: 3036)
Creates files in the Windows directory
- msiexec.exe (PID: 3036)
- lodctr.exe (PID: 2884)
- ngen.exe (PID: 3504)
- lodctr.exe (PID: 3528)
- lodctr.exe (PID: 2796)
- lodctr.exe (PID: 3472)
- lodctr.exe (PID: 1060)
- mscorsvw.exe (PID: 2744)
- ngen.exe (PID: 2248)
- ngen.exe (PID: 464)
- aspnet_regiis.exe (PID: 1032)
Removes files from Windows directory
- msiexec.exe (PID: 3036)
- aspnet_regiis.exe (PID: 1032)
- lodctr.exe (PID: 2884)
- lodctr.exe (PID: 3528)
- lodctr.exe (PID: 1060)
- lodctr.exe (PID: 3472)
- lodctr.exe (PID: 2796)
Reads the Windows organization settings
- msiexec.exe (PID: 3036)
INFO
Reads settings of System Certificates
- click.exe (PID: 2148)
- HSS-10.22.5-install-plain-773-plain.exe (PID: 3988)
- Setup.exe (PID: 1280)
- msiexec.exe (PID: 3036)
Checks Windows Trust Settings
- click.exe (PID: 2148)
- HSS-10.22.5-install-plain-773-plain.exe (PID: 3988)
- Setup.exe (PID: 1280)
- msiexec.exe (PID: 3036)
Checks supported languages
- WISPTIS.EXE (PID: 3056)
- msiexec.exe (PID: 3036)
- MsiExec.exe (PID: 764)
- MsiExec.exe (PID: 680)
- wevtutil.exe (PID: 2416)
- wevtutil.exe (PID: 2512)
- lodctr.exe (PID: 1276)
- lodctr.exe (PID: 2884)
- lodctr.exe (PID: 1060)
- lodctr.exe (PID: 3472)
- lodctr.exe (PID: 2796)
- lodctr.exe (PID: 276)
- lodctr.exe (PID: 1436)
- lodctr.exe (PID: 3528)
Reads the computer name
- WISPTIS.EXE (PID: 3056)
- msiexec.exe (PID: 3036)
- MsiExec.exe (PID: 764)
- MsiExec.exe (PID: 680)
- wevtutil.exe (PID: 2416)
- lodctr.exe (PID: 2884)
- wevtutil.exe (PID: 2512)
- lodctr.exe (PID: 1436)
- lodctr.exe (PID: 1276)
- lodctr.exe (PID: 3528)
- lodctr.exe (PID: 1060)
- lodctr.exe (PID: 3472)
- lodctr.exe (PID: 2796)
- lodctr.exe (PID: 276)
Dropped object may contain Bitcoin addresses
- Setup.exe (PID: 1280)
- svchost.exe (PID: 1992)
- msiexec.exe (PID: 3036)
- mscorsvw.exe (PID: 2744)
Creates or modifies windows services
- msiexec.exe (PID: 3036)
Manual execution by user
- click.exe (PID: 3696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:17 07:33:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 299008 |
| InitializedDataSize: | 197120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2df71 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.22.5.12023 |
| ProductVersionNumber: | 10.22.5.12023 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Pango Inc. |
| FileDescription: | Hotspot Shield 10.22.5 |
| FileVersion: | 10.22.5.12023 |
| InternalName: | setup |
| LegalCopyright: | © Pango Inc. All rights reserved. |
| OriginalFileName: | HSS-10.22.5-install-plain-773-plain.exe |
| ProductName: | Hotspot Shield 10.22.5 |
| ProductVersion: | 10.22.5.12023 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Sep-2019 05:33:38 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Pango Inc. |
| FileDescription: | Hotspot Shield 10.22.5 |
| FileVersion: | 10.22.5.12023 |
| InternalName: | setup |
| LegalCopyright: | © Pango Inc. All rights reserved. |
| OriginalFilename: | HSS-10.22.5-install-plain-773-plain.exe |
| ProductName: | Hotspot Shield 10.22.5 |
| ProductVersion: | 10.22.5.12023 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 17-Sep-2019 05:33:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00048FF7 | 0x00049000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57206 |
.rdata | 0x0004A000 | 0x0001F760 | 0x0001F800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13752 |
.data | 0x0006A000 | 0x000016FC | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.15516 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.744582 |
.rsrc | 0x0006D000 | 0x0000BEC0 | 0x0000C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.24894 |
.reloc | 0x00079000 | 0x00003DD0 | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78827 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.19553 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.42272 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.8706 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.72244 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.49242 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 7.93074 | 10436 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.72819 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.98 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.22043 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
125
Monitored processes
60
Malicious processes
36
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Windows\system32\lodctr.exe" C:\Windows\Microsoft.NET\Framework\v4.0.30319\_DataOracleClientPerfCounters_shared12_neutral.ini | C:\Windows\system32\lodctr.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 464 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe executeQueuedItems 1 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 608 | mofcomp C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet.mof | C:\Windows\system32\wbem\mofcomp.exe | — | aspnet_regiis.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: The Managed Object Format (MOF) Compiler Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 656 | "C:\ProgramData\Package Cache\3727DC47F12D9EA5EBA87145228DFF0CE8076E25\redist\ndp48-web.exe" /q /norestart /ChainingPackage "Hotspot Shield 10.22.5" /log "C:\Users\admin\AppData\Local\Temp\Hotspot_Shield_10.22.5_20211118175828_000_NetFx48Web.log.html" /pipe NetFxSection.{2123B2C1-4AFC-4E2C-B5B5-DCEDD46BEA03} | C:\ProgramData\Package Cache\3727DC47F12D9EA5EBA87145228DFF0CE8076E25\redist\ndp48-web.exe | HSS-10.22.5-install-plain-773-plain.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.8 Setup Exit code: 0 Version: 4.8.04115.00 Modules
| |||||||||||||||
| 664 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 1dc -InterruptEvent 0 -NGENProcess 1c8 -Pipe 1d0 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 680 | C:\Windows\system32\MsiExec.exe -Embedding 43FC8ED09F914285E14FCA853417D9F3 E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 764 | C:\Windows\system32\MsiExec.exe -Embedding A7B65122DBDF000E035FF4BB125349C6 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 1e4 -InterruptEvent 0 -NGENProcess 1dc -Pipe 1c4 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 1004 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 1c8 -InterruptEvent 0 -NGENProcess 1bc -Pipe 1cc -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 1032 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_regiis.exe" -iru | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_regiis.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: aspnet_regiis.exe Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
Total events
96 410
Read events
78 350
Write events
16 085
Delete events
1 975
Modification events
| (PID) Process: | (2148) click.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\click_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2148) click.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\click_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2148) click.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\click_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2148) click.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\click_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2148) click.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\click_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2148) click.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\click_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2148) click.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\click_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2148) click.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\click_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2148) click.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\click_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2148) click.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\click_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
2 649
Suspicious files
71
Text files
585
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2148 | click.exe | C:\Users\admin\AppData\Local\Temp\{407DAEEE-90E4-4C89-B17C-F30256F226B3}\.ba\Hss.Setup.Bootstrapper.dll | executable | |
MD5:— | SHA256:— | |||
| 2576 | click.exe | C:\Users\admin\AppData\Local\Temp\{F13AA9AC-B03A-44F9-A5E3-FA2060634F58}\.cr\click.exe | executable | |
MD5:— | SHA256:— | |||
| 2148 | click.exe | C:\Users\admin\AppData\Local\Temp\{407DAEEE-90E4-4C89-B17C-F30256F226B3}\.ba\Foundation.Bcl.dll | executable | |
MD5:— | SHA256:— | |||
| 2148 | click.exe | C:\Users\admin\AppData\Local\Temp\{407DAEEE-90E4-4C89-B17C-F30256F226B3}\.ba\Foundation.Installer.Common.dll | executable | |
MD5:— | SHA256:— | |||
| 2148 | click.exe | C:\Users\admin\AppData\Local\Temp\{407DAEEE-90E4-4C89-B17C-F30256F226B3}\.ba\1030\mbapreq.wxl | xml | |
MD5:7C6E4CE87870B3B5E71D3EF4555500F8 | SHA256:CAC263E0E90A4087446A290055257B1C39F17E11F065598CB2286DF4332C7696 | |||
| 2148 | click.exe | C:\Users\admin\AppData\Local\Temp\{407DAEEE-90E4-4C89-B17C-F30256F226B3}\.ba\1060\mbapreq.wxl | xml | |
MD5:5836F0C655BDD97093F68AAF69AB2BAB | SHA256:C015247D022BDC108B4FFCAE89CB55D1E313034D7E6EED18744C1BB55F108F8C | |||
| 2148 | click.exe | C:\Users\admin\AppData\Local\Temp\{407DAEEE-90E4-4C89-B17C-F30256F226B3}\.ba\lang\fr.tsv | text | |
MD5:BB3983F64EDF0F8BBC30635C010AEA2F | SHA256:4520249FC38EB600BA2E3C03B17E42E3256BFCF6F8C4207F130151B0A204BD39 | |||
| 2148 | click.exe | C:\Users\admin\AppData\Local\Temp\{407DAEEE-90E4-4C89-B17C-F30256F226B3}\.ba\lang\ko.tsv | text | |
MD5:43DB5412930DE80F372D8F31939DB44E | SHA256:FC71C5262CF9DD90FC70C7852A8A5FDBF871943863D804B8F0E8B30A99899399 | |||
| 2148 | click.exe | C:\Users\admin\AppData\Local\Temp\{407DAEEE-90E4-4C89-B17C-F30256F226B3}\.ba\BootstrapperCore.dll | executable | |
MD5:B0D10A2A622A322788780E7A3CBB85F3 | SHA256:F2C2B3CE2DF70A3206F3111391FFC7B791B32505FA97AEF22C0C2DBF6F3B0426 | |||
| 2148 | click.exe | C:\Users\admin\AppData\Local\Temp\{407DAEEE-90E4-4C89-B17C-F30256F226B3}\.ba\mbahost.dll | executable | |
MD5:C59832217903CE88793A6C40888E3CAE | SHA256:9DFA1BC5D2AB4C652304976978749141B8C312784B05CB577F338A0AA91330DB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
19
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
932 | svchost.exe | GET | 302 | 104.92.93.19:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03761.00&sar=x86&o1=netfx_Full.mzz | NL | — | — | whitelisted |
932 | svchost.exe | HEAD | 302 | 104.92.93.19:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03761.00&sar=amd64&o1=netfx_Full_x86.msi | NL | — | — | whitelisted |
932 | svchost.exe | HEAD | 302 | 104.92.93.19:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03761.00&sar=x86&o1=netfx_Full.mzz | NL | — | — | whitelisted |
932 | svchost.exe | GET | 302 | 104.92.93.19:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03761.00&sar=amd64&o1=netfx_Full_x86.msi | NL | — | — | whitelisted |
932 | svchost.exe | HEAD | 302 | 104.92.93.19:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=04115.00&sar=amd64&o1=netfx_Patch_x86.msp | NL | — | — | whitelisted |
932 | svchost.exe | HEAD | 302 | 104.92.93.19:80 | http://go.microsoft.com/fwlink/?LinkId=328846&clcid=0x409 | NL | — | — | whitelisted |
932 | svchost.exe | GET | 302 | 104.92.93.19:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=04115.00&sar=amd64&o1=netfx_Patch_x86.msp | NL | — | — | whitelisted |
2148 | click.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT5hgD4pKvs0jFFLEKNQ1CjblLIPQQU9LbhIB3%2BKa7S5GGlsqIlssgXNW4CEA1CSuC%2BOoj%2FYEAhzhQA8N0%3D | US | der | 471 b | whitelisted |
2148 | click.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAqhJdbWMht%2BQeQF2jaXwhU%3D | US | der | 471 b | whitelisted |
2148 | click.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2148 | click.exe | 143.204.101.96:443 | d21j7etzkdo9k9.cloudfront.net | — | US | unknown |
2148 | click.exe | 138.68.77.102:443 | www.legaladviser.us | Digital Ocean, Inc. | DE | unknown |
2148 | click.exe | 159.89.100.215:443 | www.legaladviser.us | — | US | unknown |
2148 | click.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2148 | click.exe | 143.204.101.65:443 | d3h88i27t2k9za.cloudfront.net | — | US | suspicious |
2148 | click.exe | 68.232.34.200:443 | download.visualstudio.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2148 | click.exe | 104.92.93.19:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | unknown |
3988 | HSS-10.22.5-install-plain-773-plain.exe | 92.123.194.162:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
2148 | click.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
932 | svchost.exe | 104.92.93.19:80 | go.microsoft.com | Akamai Technologies, Inc. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d21j7etzkdo9k9.cloudfront.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
www.legaladviser.us |
| unknown |
ocsp.digicert.com |
| whitelisted |
d3h88i27t2k9za.cloudfront.net |
| suspicious |
go.microsoft.com |
| whitelisted |
download.visualstudio.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |