| File name: | 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe |
| Full analysis: | https://app.any.run/tasks/5f530a08-5649-47da-9bb9-51fcac531c1d |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | July 08, 2024, 08:47:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6BF34DEBE3788625E4FCF5305560DD29 |
| SHA1: | 1B5F4D8C5855C5ABD27ED4B535E184F9DAD63C9F |
| SHA256: | 8AC5083F52DA0FF312259331F65B326782803AA837A7B371A6D43A021B0C24C3 |
| SSDEEP: | 196608:1lKBUMjqQBJa0Kq5JTtIYHTJ5LSGIuINytq:sjh0fq5JpIunBIu6Eq |
MALICIOUS
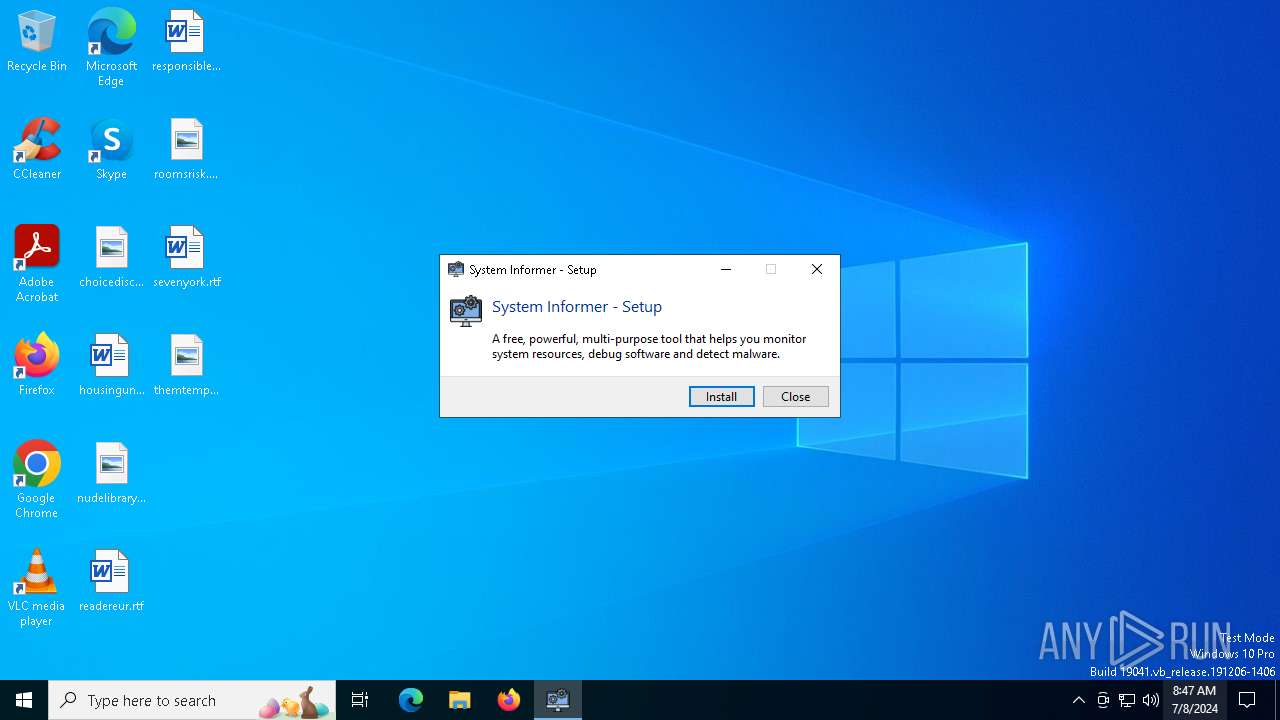
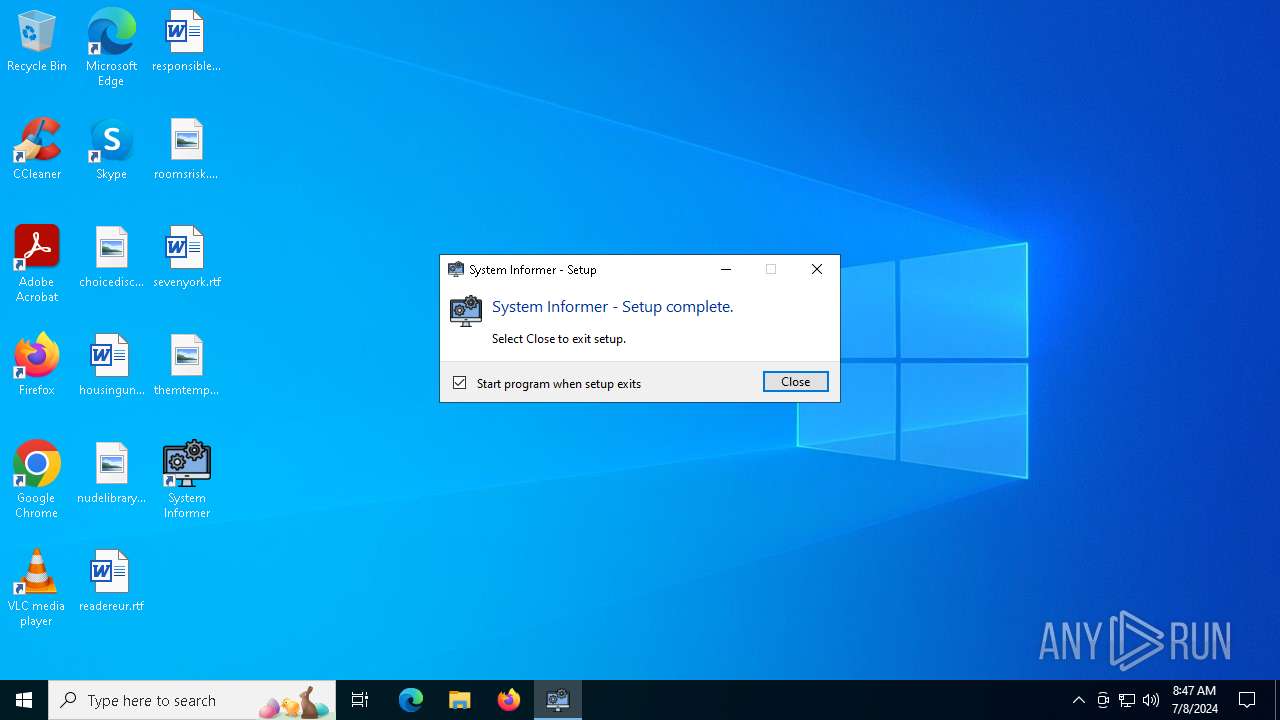
Drops the executable file immediately after the start
- 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe (PID: 1132)
- cheac.exe (PID: 1332)
- Perfdhcp.exe (PID: 5284)
- systeminformer-3.0.7660-release-setup.exe (PID: 5112)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 4180)
METASTEALER has been detected (SURICATA)
- Sabad0n.exe (PID: 4320)
REDLINE has been detected (SURICATA)
- Sabad0n.exe (PID: 4320)
Connects to the CnC server
- Sabad0n.exe (PID: 4320)
Steals credentials from Web Browsers
- Sabad0n.exe (PID: 4320)
Actions looks like stealing of personal data
- Sabad0n.exe (PID: 4320)
SUSPICIOUS
Reads security settings of Internet Explorer
- 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe (PID: 1132)
- cheac.exe (PID: 1332)
- Perfdhcp.exe (PID: 5284)
- systeminformer-3.0.7660-release-setup.exe (PID: 5112)
- SystemInformer.exe (PID: 6800)
Reads the date of Windows installation
- 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe (PID: 1132)
- cheac.exe (PID: 1332)
- Perfdhcp.exe (PID: 5284)
- systeminformer-3.0.7660-release-setup.exe (PID: 5112)
Executable content was dropped or overwritten
- 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe (PID: 1132)
- cheac.exe (PID: 1332)
- Perfdhcp.exe (PID: 5284)
- systeminformer-3.0.7660-release-setup.exe (PID: 5112)
Executed via WMI
- schtasks.exe (PID: 5140)
- schtasks.exe (PID: 2392)
- schtasks.exe (PID: 1052)
- schtasks.exe (PID: 3976)
- schtasks.exe (PID: 4764)
- schtasks.exe (PID: 3152)
- schtasks.exe (PID: 4280)
- schtasks.exe (PID: 5888)
- schtasks.exe (PID: 4220)
- schtasks.exe (PID: 2100)
- schtasks.exe (PID: 5228)
- schtasks.exe (PID: 5244)
- schtasks.exe (PID: 1440)
- schtasks.exe (PID: 3656)
- schtasks.exe (PID: 2020)
- schtasks.exe (PID: 3660)
- schtasks.exe (PID: 5812)
- schtasks.exe (PID: 5508)
- schtasks.exe (PID: 4764)
- schtasks.exe (PID: 3976)
- schtasks.exe (PID: 1048)
- schtasks.exe (PID: 5624)
- schtasks.exe (PID: 5764)
- schtasks.exe (PID: 5988)
- schtasks.exe (PID: 4456)
- schtasks.exe (PID: 2992)
- schtasks.exe (PID: 4152)
- schtasks.exe (PID: 1220)
- schtasks.exe (PID: 5264)
- schtasks.exe (PID: 2328)
- schtasks.exe (PID: 1972)
- schtasks.exe (PID: 5288)
- schtasks.exe (PID: 4020)
- schtasks.exe (PID: 4180)
- schtasks.exe (PID: 5604)
- schtasks.exe (PID: 8)
- schtasks.exe (PID: 3628)
- schtasks.exe (PID: 2104)
- schtasks.exe (PID: 1048)
- schtasks.exe (PID: 1908)
- schtasks.exe (PID: 3156)
- schtasks.exe (PID: 4152)
- schtasks.exe (PID: 2140)
- schtasks.exe (PID: 3656)
- schtasks.exe (PID: 1740)
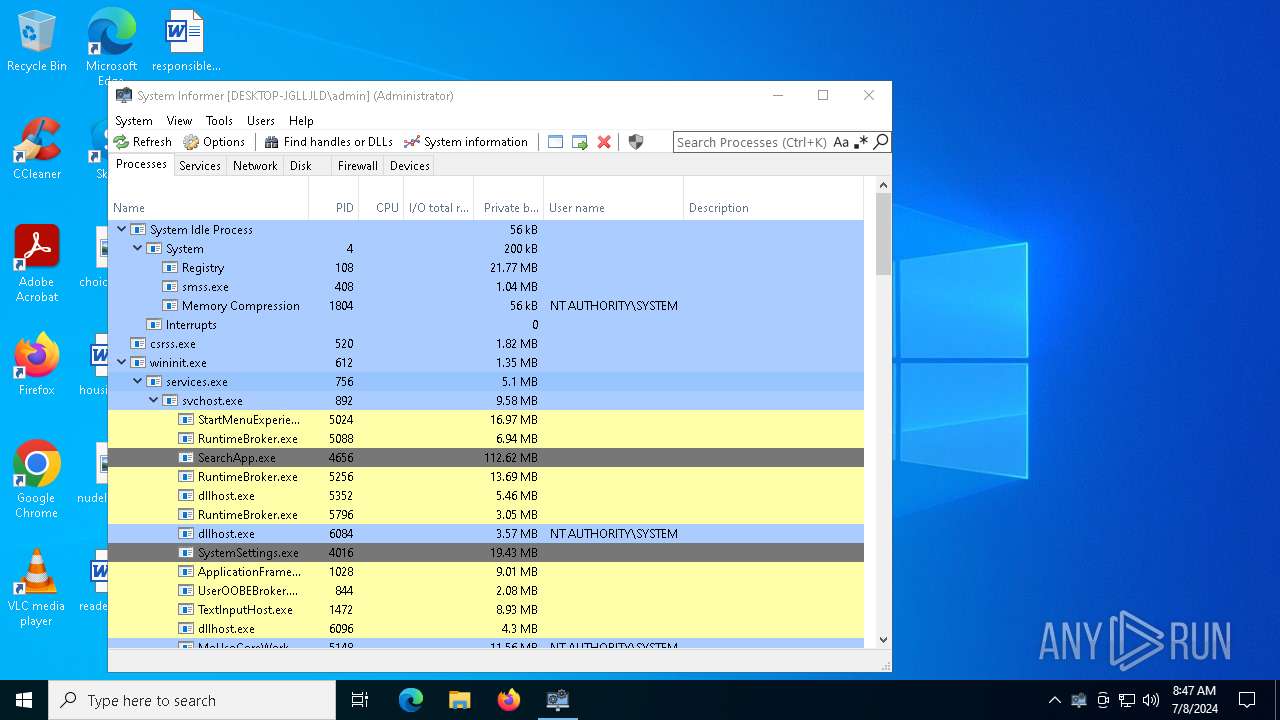
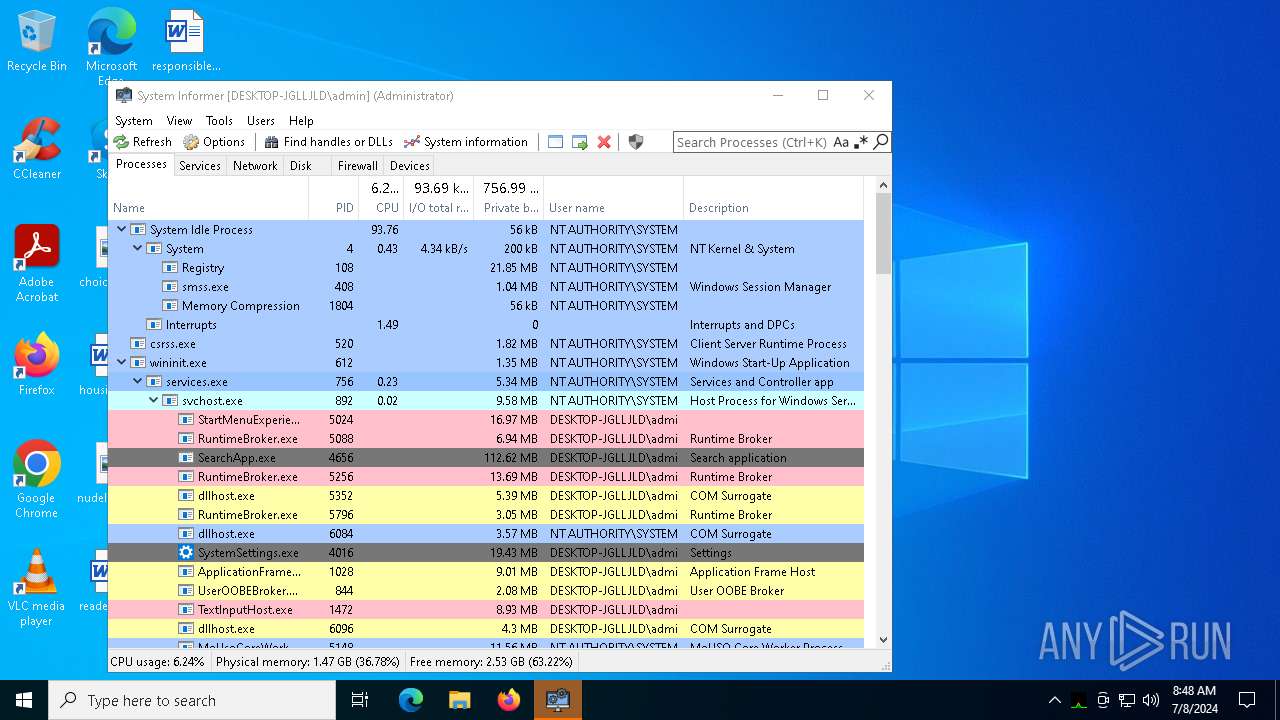
The process creates files with name similar to system file names
- Perfdhcp.exe (PID: 5284)
- systeminformer-3.0.7660-release-setup.exe (PID: 5112)
Executing commands from a ".bat" file
- wscript.exe (PID: 4180)
- Perfdhcp.exe (PID: 5284)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 4180)
- Perfdhcp.exe (PID: 5284)
Runs shell command (SCRIPT)
- wscript.exe (PID: 4180)
Connects to unusual port
- Sabad0n.exe (PID: 4320)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 3152)
Searches for installed software
- Sabad0n.exe (PID: 4320)
Creates a software uninstall entry
- systeminformer-3.0.7660-release-setup.exe (PID: 5112)
Drops a system driver (possible attempt to evade defenses)
- systeminformer-3.0.7660-release-setup.exe (PID: 5112)
Checks Windows Trust Settings
- SystemInformer.exe (PID: 6800)
INFO
Create files in a temporary directory
- 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe (PID: 1132)
- Perfdhcp.exe (PID: 5284)
Checks supported languages
- 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe (PID: 1132)
- systeminformer-3.0.7660-release-setup.exe (PID: 5112)
- Sabad0n.exe (PID: 4320)
- cheac.exe (PID: 1332)
- Perfdhcp.exe (PID: 5284)
- dllhost.exe (PID: 5888)
- SystemInformer.exe (PID: 6800)
Reads the computer name
- 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe (PID: 1132)
- cheac.exe (PID: 1332)
- systeminformer-3.0.7660-release-setup.exe (PID: 5112)
- Sabad0n.exe (PID: 4320)
- Perfdhcp.exe (PID: 5284)
- dllhost.exe (PID: 5888)
- SystemInformer.exe (PID: 6800)
Process checks computer location settings
- 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe (PID: 1132)
- cheac.exe (PID: 1332)
- Perfdhcp.exe (PID: 5284)
- systeminformer-3.0.7660-release-setup.exe (PID: 5112)
Reads the machine GUID from the registry
- Sabad0n.exe (PID: 4320)
- Perfdhcp.exe (PID: 5284)
- dllhost.exe (PID: 5888)
- SystemInformer.exe (PID: 6800)
Reads Environment values
- Perfdhcp.exe (PID: 5284)
- Sabad0n.exe (PID: 4320)
- dllhost.exe (PID: 5888)
Creates files in the program directory
- Perfdhcp.exe (PID: 5284)
- systeminformer-3.0.7660-release-setup.exe (PID: 5112)
Reads the software policy settings
- dllhost.exe (PID: 5888)
- SystemInformer.exe (PID: 6800)
Checks proxy server information
- dllhost.exe (PID: 5888)
- SystemInformer.exe (PID: 6800)
Disables trace logs
- dllhost.exe (PID: 5888)
Reads the time zone
- SystemInformer.exe (PID: 6800)
Reads CPU info
- SystemInformer.exe (PID: 6800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (25.6) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (2.6) |
| .exe | | | Generic Win/DOS Executable (1.1) |
| .exe | | | DOS Executable Generic (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 5120 |
| InitializedDataSize: | 18832384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20cc |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.12187.7660 |
| ProductVersionNumber: | 3.0.12187.7660 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | System Informer |
| FileDescription: | System Informer - Setup |
| FileVersion: | 3.0.12187.7660 |
| InternalName: | systeminformer-setup.exe |
| LegalCopyright: | Copyright (c) Winsider Seminars & Solutions, Inc. All rights reserved. |
| OriginalFileName: | systeminformer-setup.exe |
| ProductName: | System Informer |
| ProductVersion: | 3.0.12187.7660 |
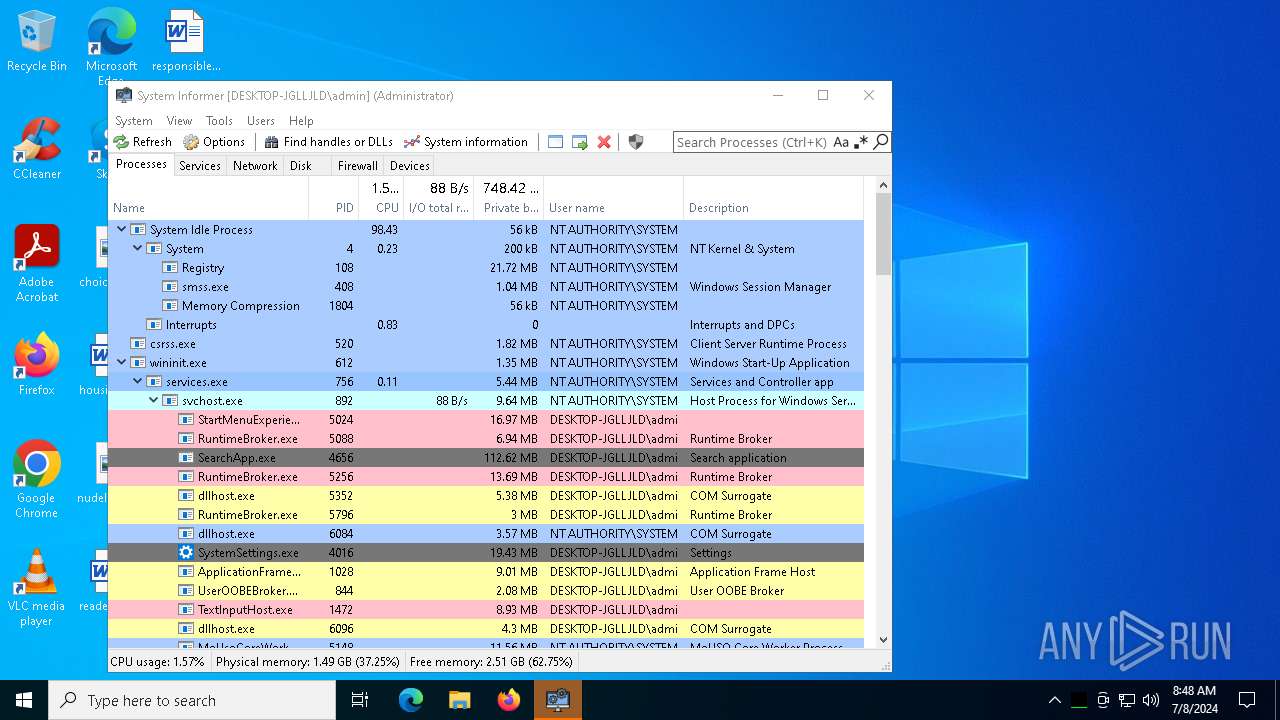
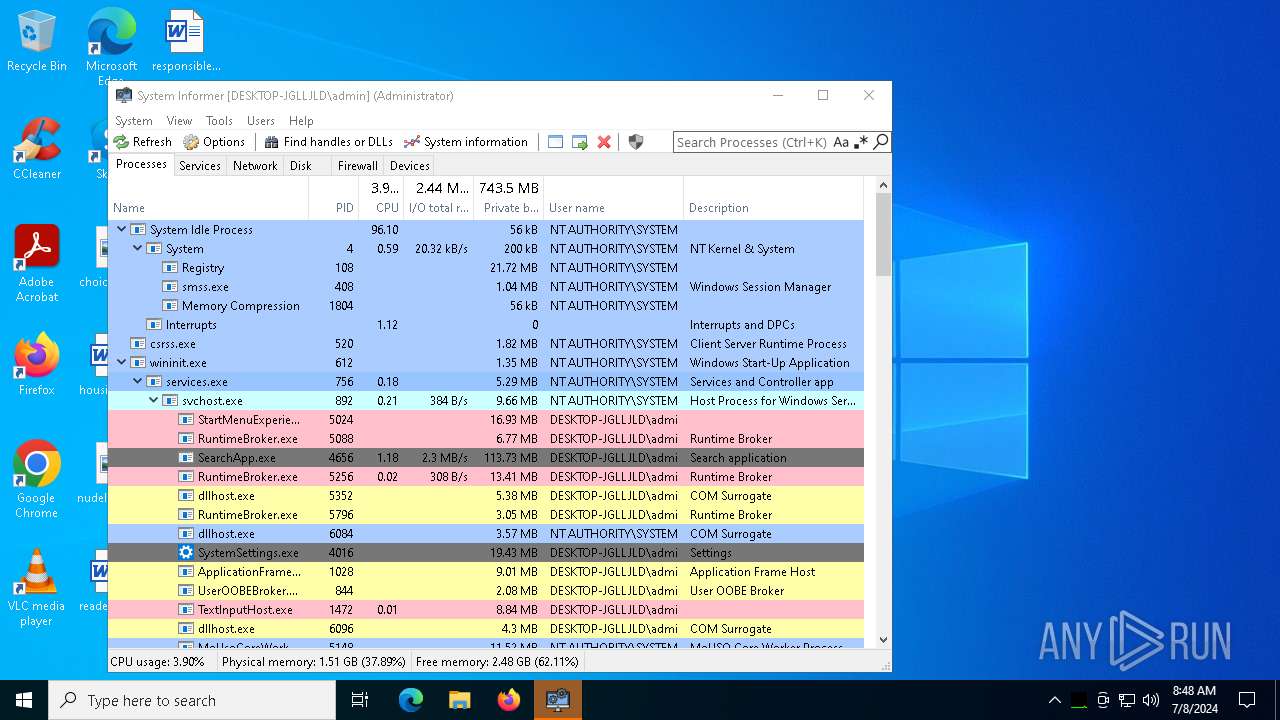
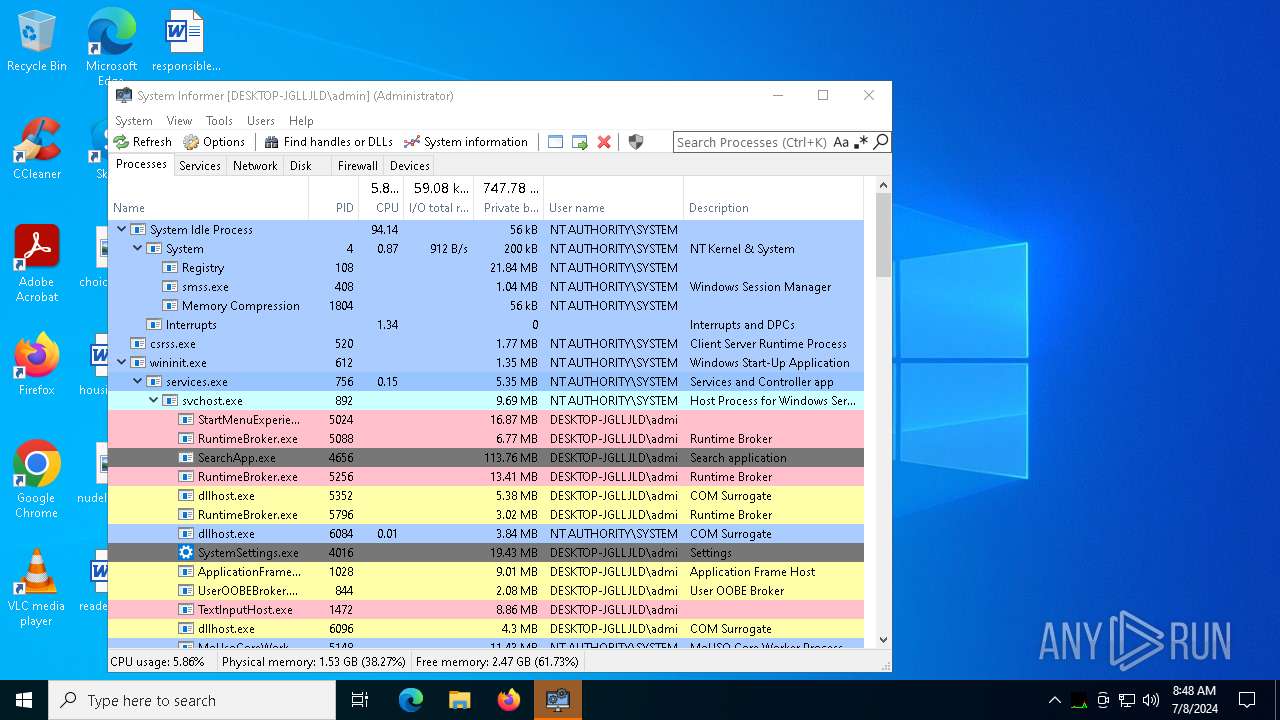
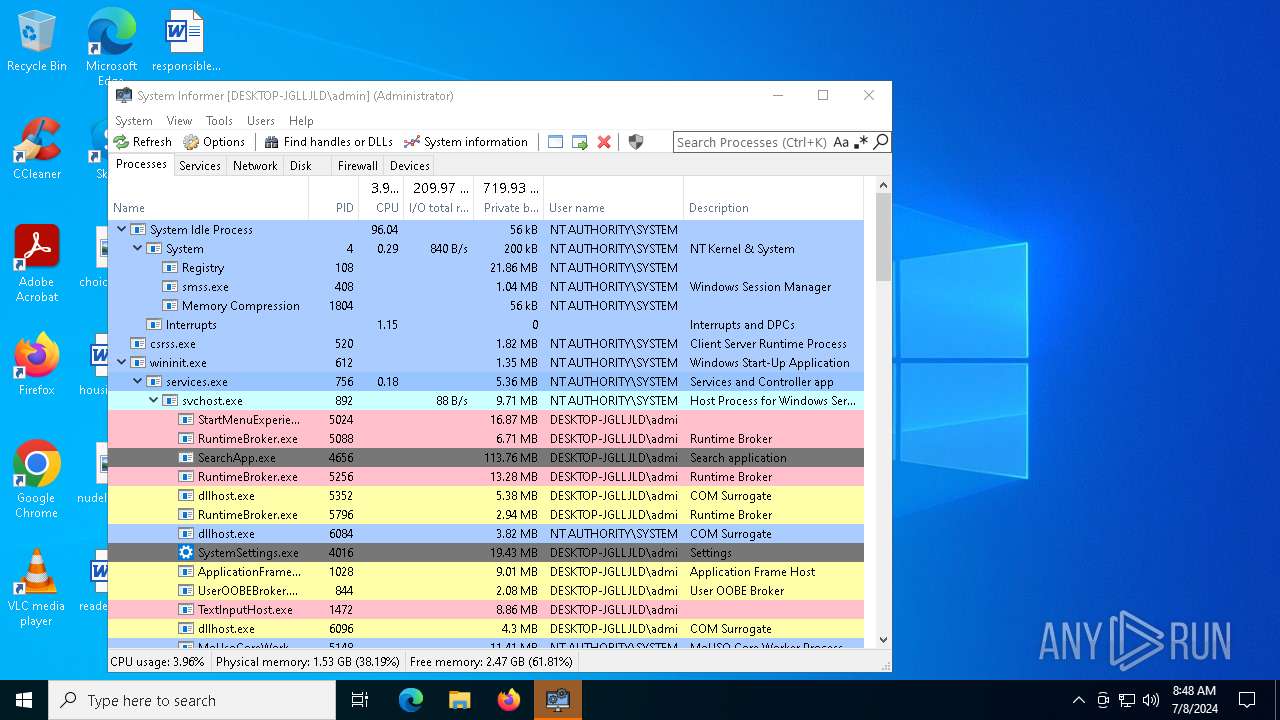
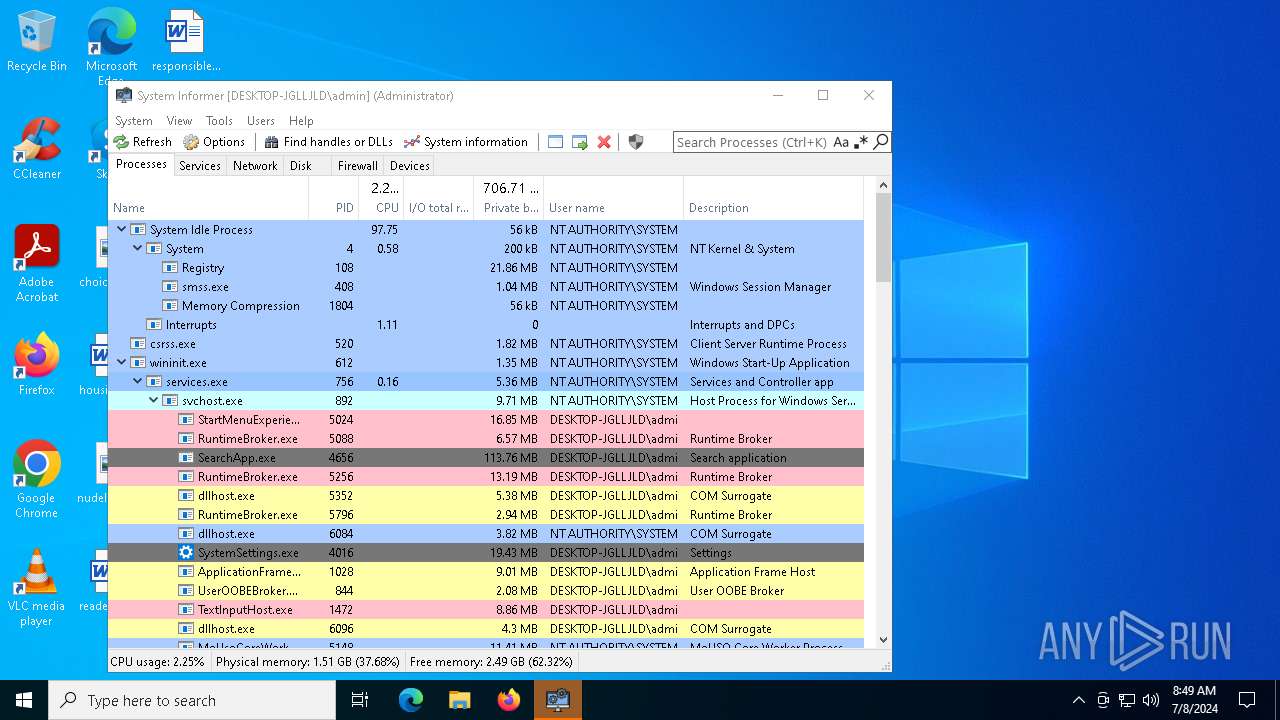
Total processes
197
Monitored processes
59
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | schtasks.exe /create /tn "dllhost" /sc ONLOGON /tr "'C:\Program Files (x86)\Windows Mail\dllhost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | "C:\Users\admin\AppData\Local\Temp\8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe" | C:\Users\admin\AppData\Local\Temp\8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe | — | explorer.exe | |||||||||||
User: admin Company: System Informer Integrity Level: MEDIUM Description: System Informer - Setup Exit code: 3221226540 Version: 3.0.12187.7660 Modules
| |||||||||||||||
| 1048 | schtasks.exe /create /tn "winlogon" /sc ONLOGON /tr "'C:\comagentWinintoBroker\winlogon.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | schtasks.exe /create /tn "RuntimeBrokerR" /sc MINUTE /mo 9 /tr "'C:\Program Files (x86)\Internet Explorer\en-US\RuntimeBroker.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | schtasks.exe /create /tn "cmdc" /sc MINUTE /mo 12 /tr "'C:\Windows\Performance\WinSAT\DataStore\cmd.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Users\admin\AppData\Local\Temp\8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe" | C:\Users\admin\AppData\Local\Temp\8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe | explorer.exe | ||||||||||||
User: admin Company: System Informer Integrity Level: HIGH Description: System Informer - Setup Exit code: 0 Version: 3.0.12187.7660 Modules
| |||||||||||||||
| 1220 | schtasks.exe /create /tn "cmd" /sc ONLOGON /tr "'C:\Program Files (x86)\Windows Sidebar\Gadgets\cmd.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | "C:\Users\admin\AppData\Local\Temp\cheac.exe" | C:\Users\admin\AppData\Local\Temp\cheac.exe | 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1440 | schtasks.exe /create /tn "explorer" /sc ONLOGON /tr "'C:\found.000\dir0000.chk\explorer.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
26 929
Read events
26 856
Write events
67
Delete events
6
Modification events
| (PID) Process: | (1132) 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (1132) 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1132) 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1132) 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1132) 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1332) cheac.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\ApplicationAssociationToasts |
| Operation: | write | Name: | VBEFile_.vbe |
Value: 0 | |||
| (PID) Process: | (1332) cheac.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbe\OpenWithProgids |
| Operation: | write | Name: | VBEFile |
Value: | |||
| (PID) Process: | (1332) cheac.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1332) cheac.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1332) cheac.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
38
Suspicious files
22
Text files
25
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1332 | cheac.exe | C:\comagentWinintoBroker\yFjSoONubLQ.vbe | binary | |
MD5:77A46676F244154F11521F33845F801D | SHA256:3ED59A88A1B673DE3B3F60DD04246EFDC55204C129F617F934EBB10FA35AD7B2 | |||
| 5284 | Perfdhcp.exe | C:\Program Files\Mozilla Firefox\fonts\0a1fd5f707cd16 | text | |
MD5:932C5149584AD19E819E93ADD54C9A3D | SHA256:93DB96DA0C9595BBEE78B74A633A97D8E2E87A16218B46E69B9C972AC4E43767 | |||
| 1332 | cheac.exe | C:\comagentWinintoBroker\Perfdhcp.exe | executable | |
MD5:1A742AAD27D12710D42F36274E85B59E | SHA256:5C6255CDF1E831099E8B4E7C7EFE1AFA875E1295736E9A64F000CA8C61F65D6E | |||
| 5284 | Perfdhcp.exe | C:\Program Files\Mozilla Firefox\fonts\sppsvc.exe | executable | |
MD5:1A742AAD27D12710D42F36274E85B59E | SHA256:5C6255CDF1E831099E8B4E7C7EFE1AFA875E1295736E9A64F000CA8C61F65D6E | |||
| 5284 | Perfdhcp.exe | C:\found.000\dir0000.chk\7a0fd90576e088 | text | |
MD5:63898EB548200B78EE198B8CCACBE0DF | SHA256:99EF147A0446B3990C0B217D1EF3356F54F8557F7F7D54C8F3A1F593959C2BE6 | |||
| 5284 | Perfdhcp.exe | C:\Windows\en-US\upfc.exe | executable | |
MD5:1A742AAD27D12710D42F36274E85B59E | SHA256:5C6255CDF1E831099E8B4E7C7EFE1AFA875E1295736E9A64F000CA8C61F65D6E | |||
| 5284 | Perfdhcp.exe | C:\Windows\Performance\WinSAT\DataStore\cmd.exe | executable | |
MD5:1A742AAD27D12710D42F36274E85B59E | SHA256:5C6255CDF1E831099E8B4E7C7EFE1AFA875E1295736E9A64F000CA8C61F65D6E | |||
| 5284 | Perfdhcp.exe | C:\Users\Administrator\Videos\fontdrvhost.exe | executable | |
MD5:1A742AAD27D12710D42F36274E85B59E | SHA256:5C6255CDF1E831099E8B4E7C7EFE1AFA875E1295736E9A64F000CA8C61F65D6E | |||
| 5284 | Perfdhcp.exe | C:\Windows\Performance\WinSAT\DataStore\ebf1f9fa8afd6d | text | |
MD5:1C0E5A1082916941F13A0B37A3D89889 | SHA256:3EC387376DB9733BBB15DD220B7F49BB9EBADDEBD6F68EC8015D786A56A5808A | |||
| 1132 | 8ac5083f52da0ff312259331f65b326782803aa837a7b371a6d43a021b0c24c3.exe | C:\Users\admin\AppData\Local\Temp\systeminformer-3.0.7660-release-setup.exe | executable | |
MD5:0D909A4A638465A17BC9F37C5024E574 | SHA256:A82821A4C18EF940354B84CD625CE0FD8ED5CFBA5418014063F054071BD5FCCD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
66
DNS requests
21
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2056 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2056 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
5888 | dllhost.exe | GET | 301 | 92.53.96.121:80 | http://co44847.tw1.ru/L1nc0In.php?qoBdyXSURxompSYN9b6Z77LyLHN=Xe&Hhhw2=ykdxOcDFrBmjCtqOK3tcNRqKR6x&5931e12c057069f8a12af549ea7ef8be=10d9ac92447143a83147671153560534&6a477440be98de75288f7833874ee5bd=gMzQmZ1UGNlBTMwYmN0YTN4MmZwUmZlJTNxQDMlNGNkdzN5QDM2AzY&qoBdyXSURxompSYN9b6Z77LyLHN=Xe&Hhhw2=ykdxOcDFrBmjCtqOK3tcNRqKR6x | unknown | — | — | unknown |
1348 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
5888 | dllhost.exe | GET | 301 | 92.53.96.121:80 | http://co44847.tw1.ru/L1nc0In.php?qoBdyXSURxompSYN9b6Z77LyLHN=Xe&Hhhw2=ykdxOcDFrBmjCtqOK3tcNRqKR6x&5931e12c057069f8a12af549ea7ef8be=10d9ac92447143a83147671153560534&6a477440be98de75288f7833874ee5bd=gMzQmZ1UGNlBTMwYmN0YTN4MmZwUmZlJTNxQDMlNGNkdzN5QDM2AzY&qoBdyXSURxompSYN9b6Z77LyLHN=Xe&Hhhw2=ykdxOcDFrBmjCtqOK3tcNRqKR6x | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
6960 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
6960 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
900 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
4808 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2056 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2088 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5148 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4320 | Sabad0n.exe | 77.73.129.75:1912 | — | SD Intelect SRL | KZ | malicious |
2056 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
2056 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
4656 | SearchApp.exe | 2.20.142.154:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
co44847.tw1.ru |
| unknown |
www.bing.com |
| whitelisted |
vh432.timeweb.ru |
| unknown |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4320 | Sabad0n.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
4320 | Sabad0n.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
4320 | Sabad0n.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] RedLine Stealer/MetaStealer Family Related (MC-NMF Authorization) |
4320 | Sabad0n.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC - Id1Response |
4320 | Sabad0n.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
4320 | Sabad0n.exe | A Network Trojan was detected | ET MALWARE Redline Stealer/MetaStealer Family Activity (Response) |
5888 | dllhost.exe | A Network Trojan was detected | ET MALWARE DCRAT Activity (GET) |
4320 | Sabad0n.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |