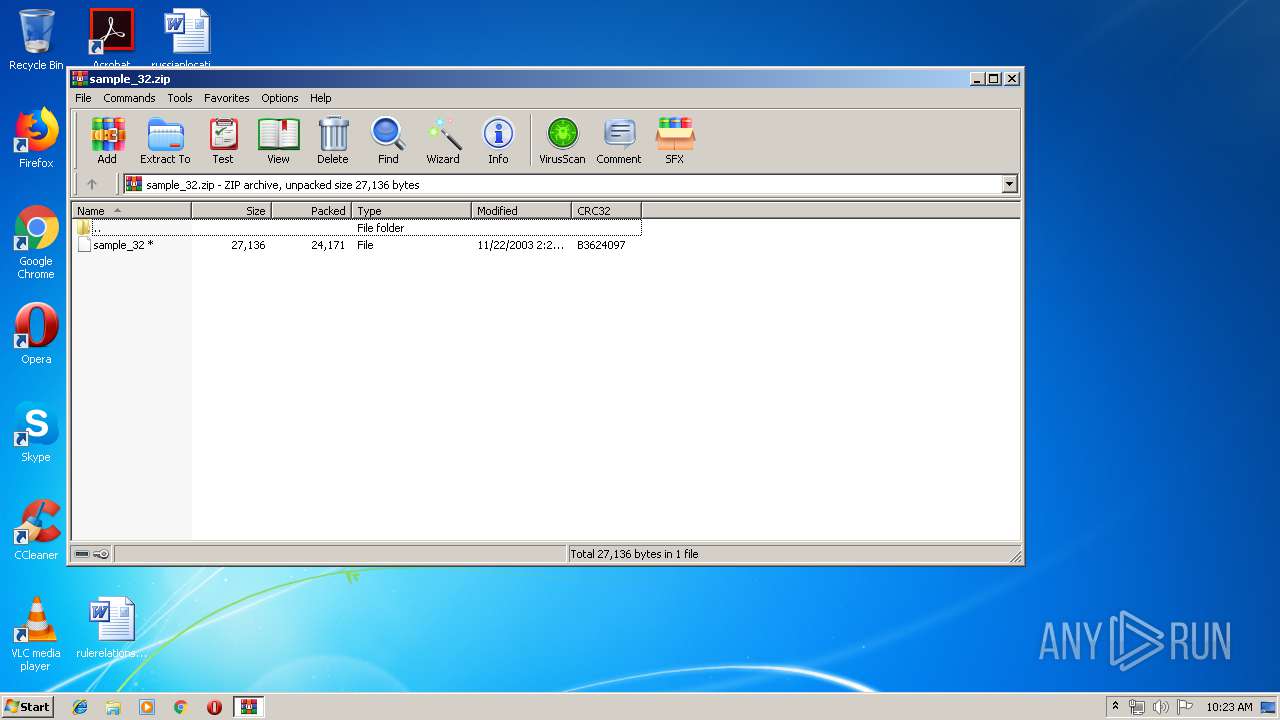
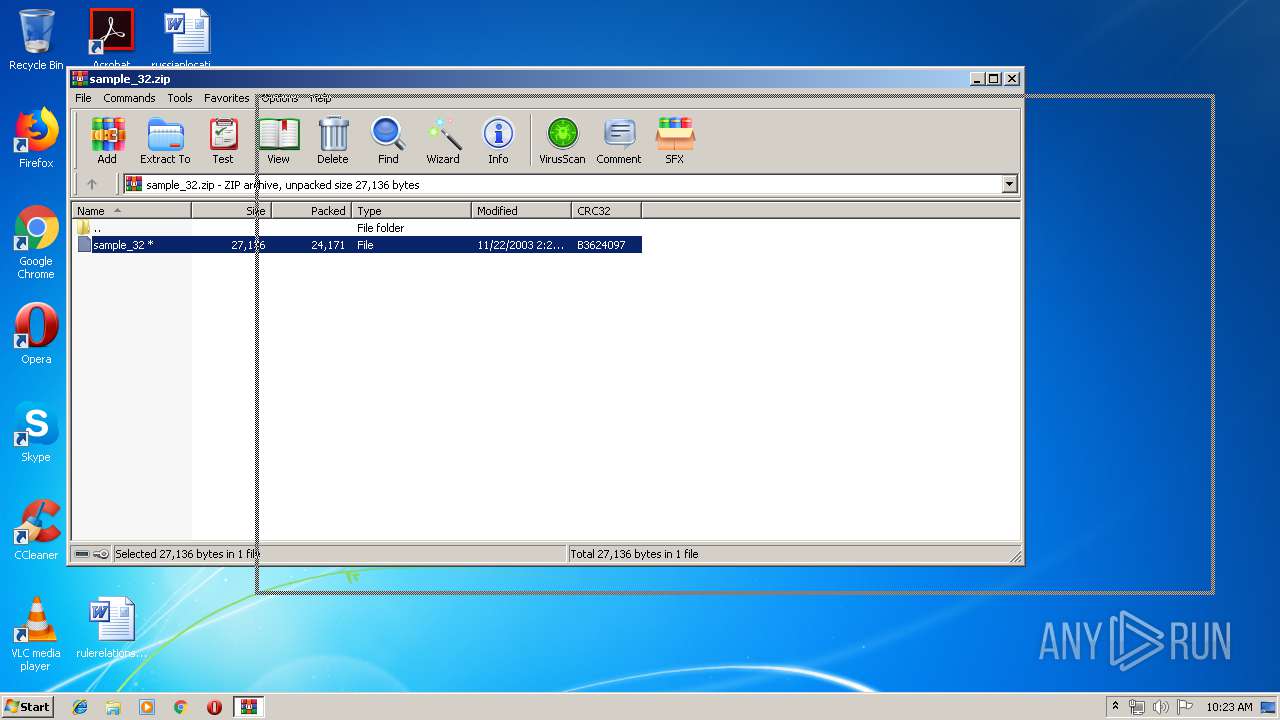
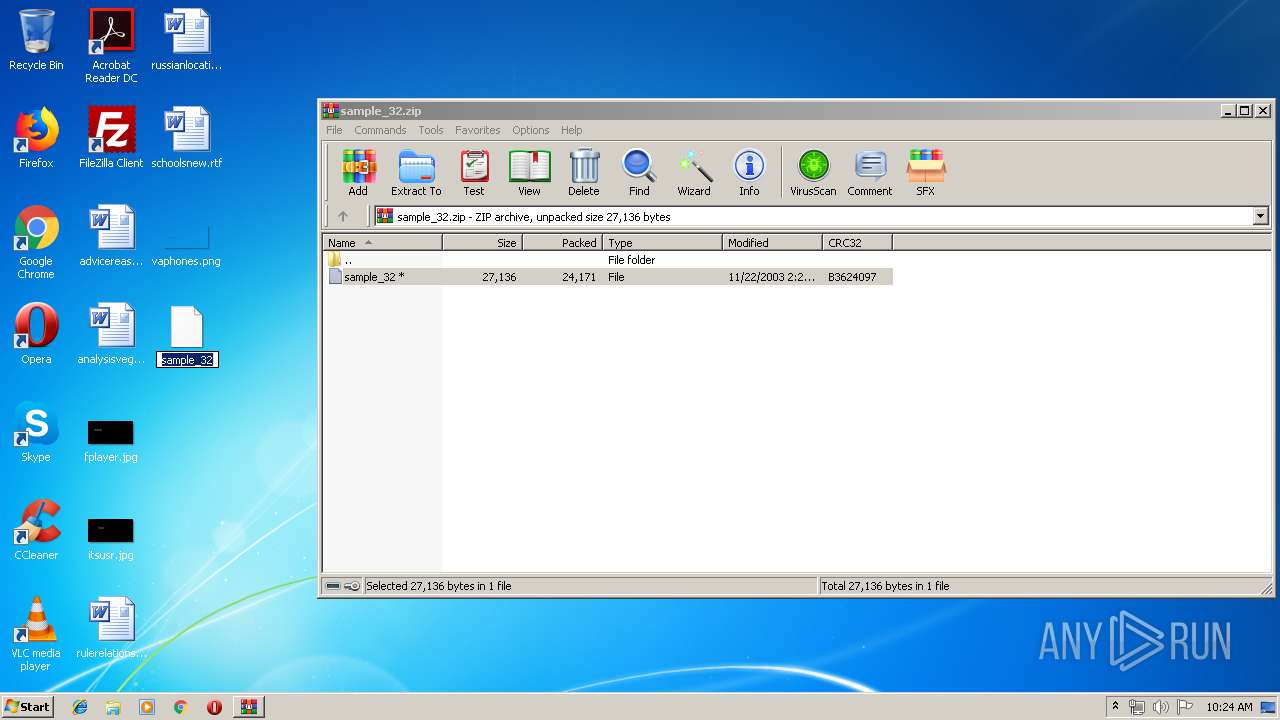
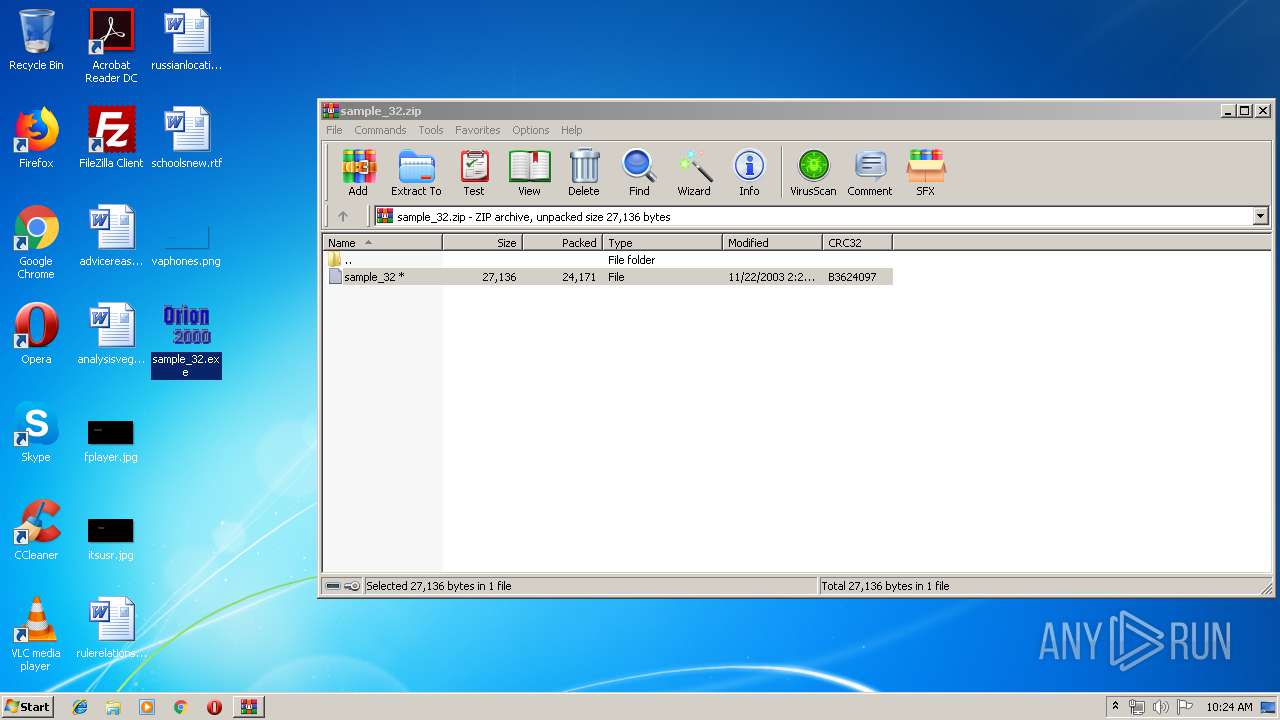
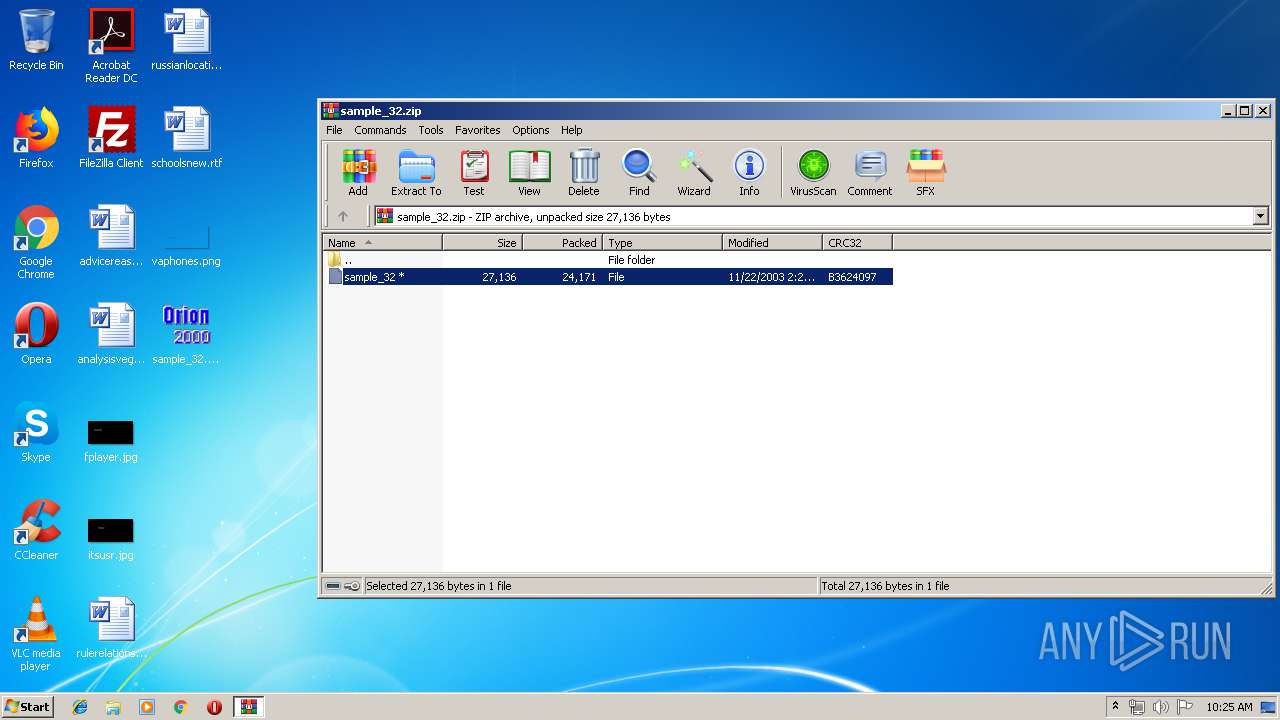
| File name: | sample_32.zip |
| Full analysis: | https://app.any.run/tasks/28a4f157-8026-4c2e-aceb-ba0e98ad2238 |
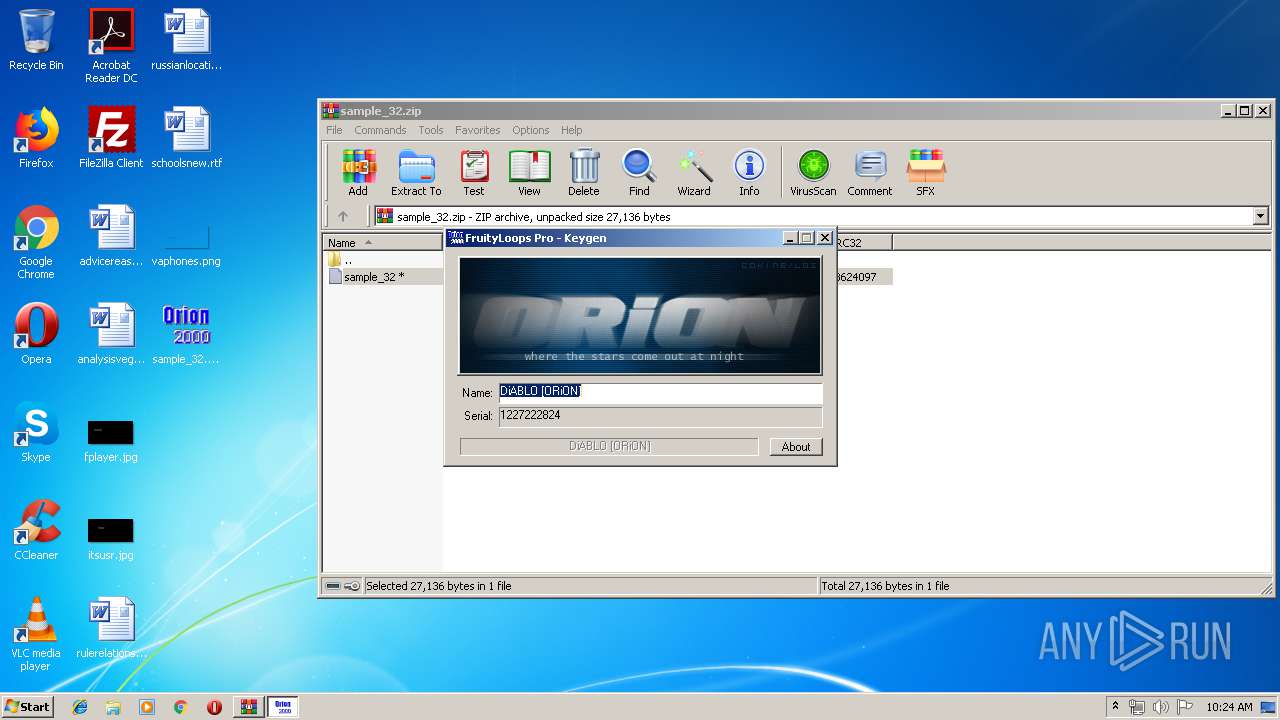
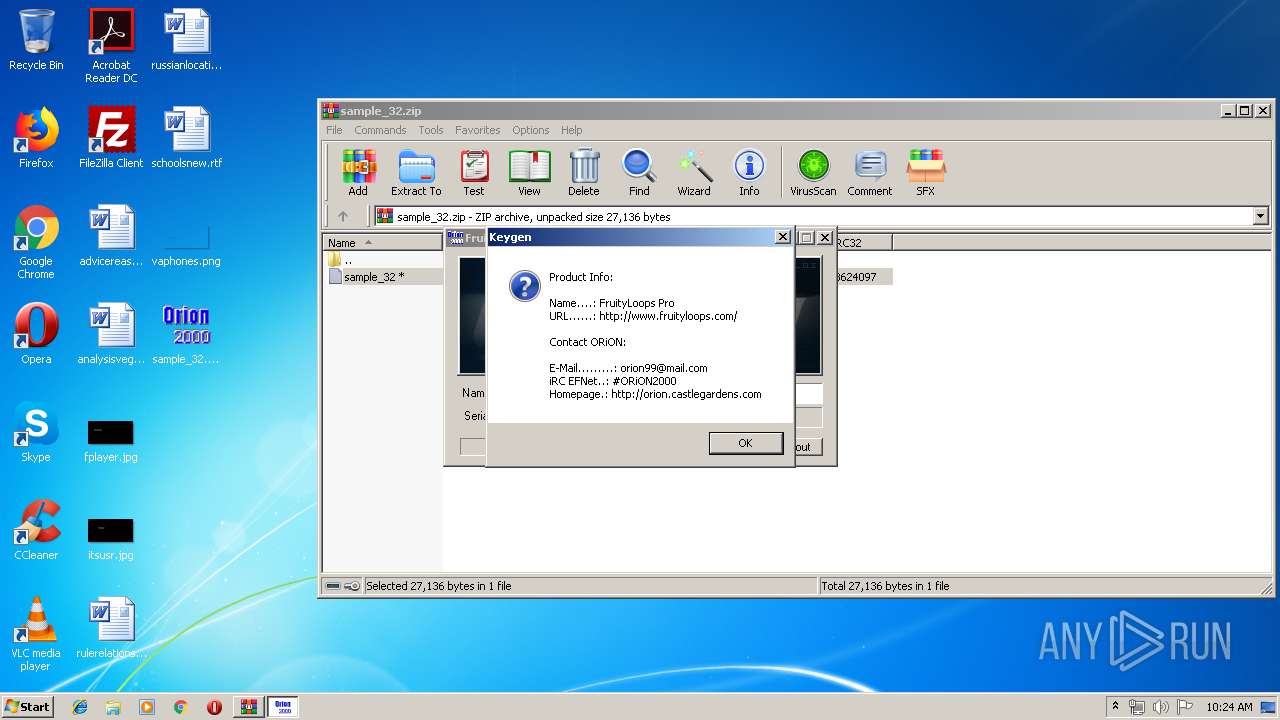
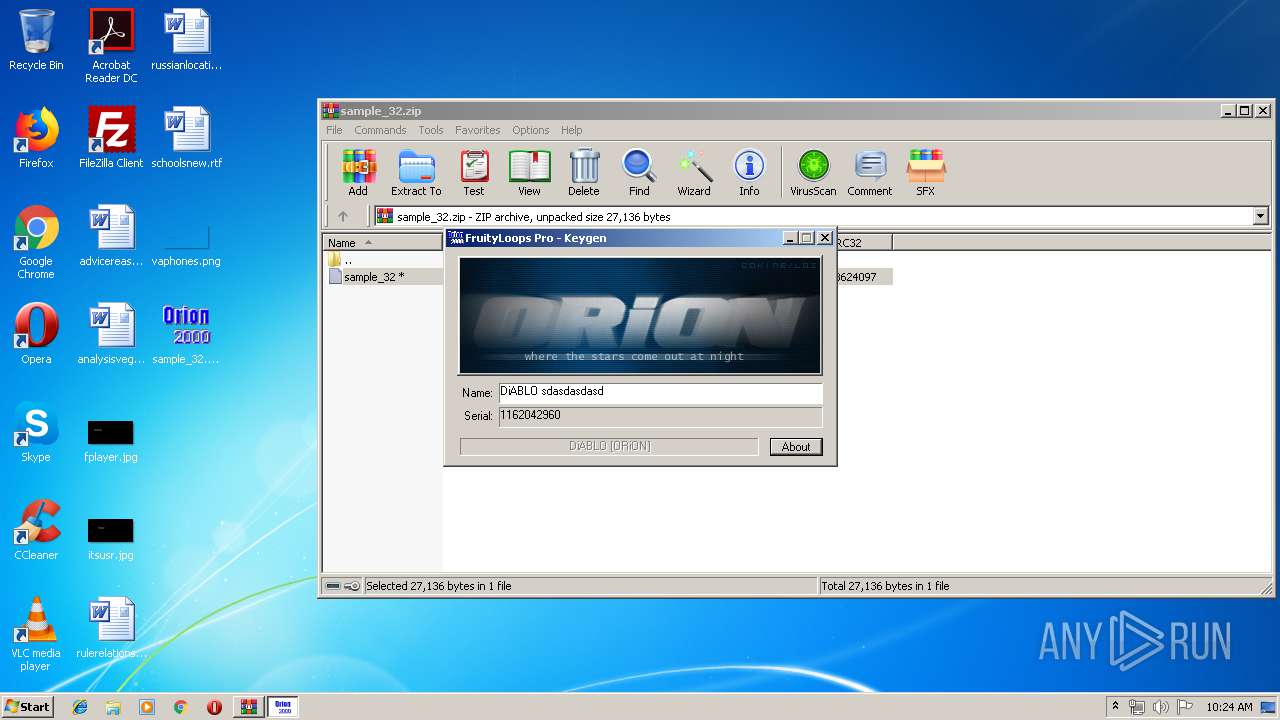
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 09:23:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 56C15159605090C1E94F44F2F86A4CF3 |
| SHA1: | BA47BFA85258261560F2E6D6843C69098D89A0F6 |
| SHA256: | 8ABA786D527103FD190E2B7320568D08861884E8665681B8B7389A011DC362C3 |
| SSDEEP: | 384:TV+tL5Ard81Aq2/XUFo/y0BryHWQAqTjzaEfI9r0p70oHJl5LdScf6F14aw:TViEdQgPMo/DryHUovtXCWr5LwZSaw |
MALICIOUS
Application was dropped or rewritten from another process
- sample_32.exe (PID: 3156)
- sample_32.exe (PID: 4000)
- sample_32.exe (PID: 3664)
- sample_32.exe (PID: 3820)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2716)
INFO
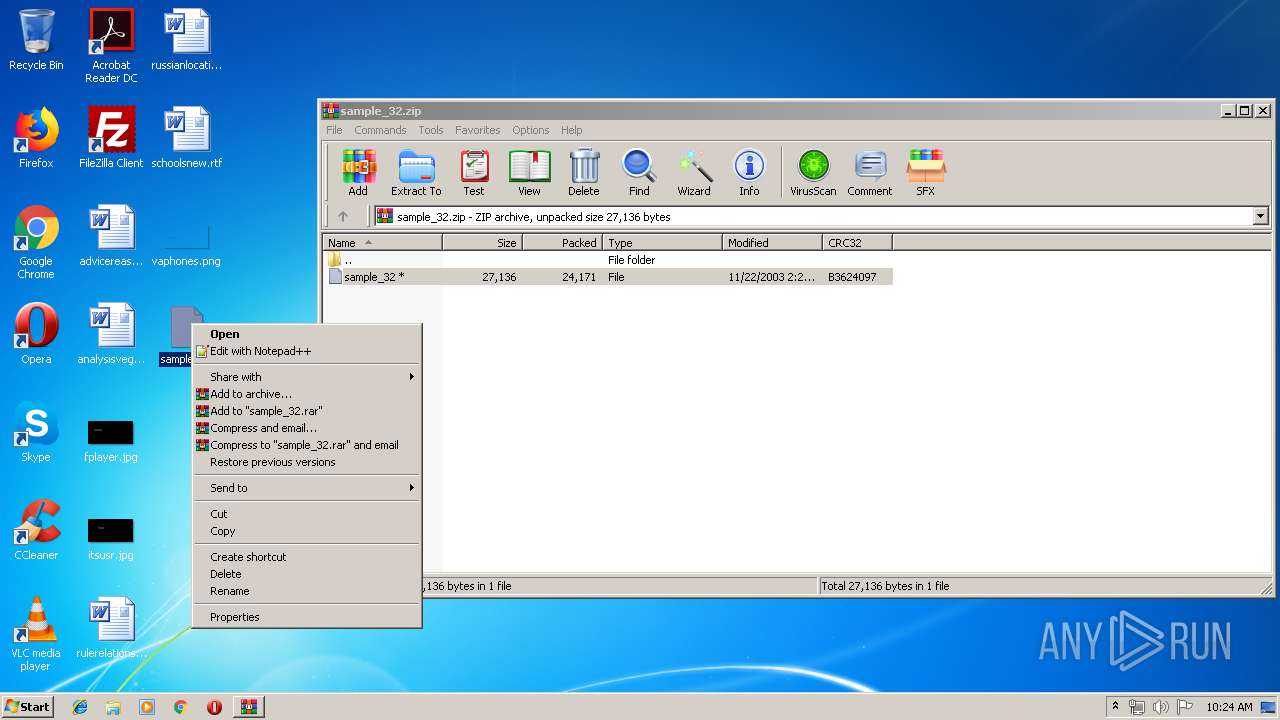
Manual execution by user
- sample_32.exe (PID: 4000)
- wermgr.exe (PID: 3620)
- wermgr.exe (PID: 3232)
- sample_32.exe (PID: 3664)
- sample_32.exe (PID: 3820)
- sample_32.exe (PID: 3156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
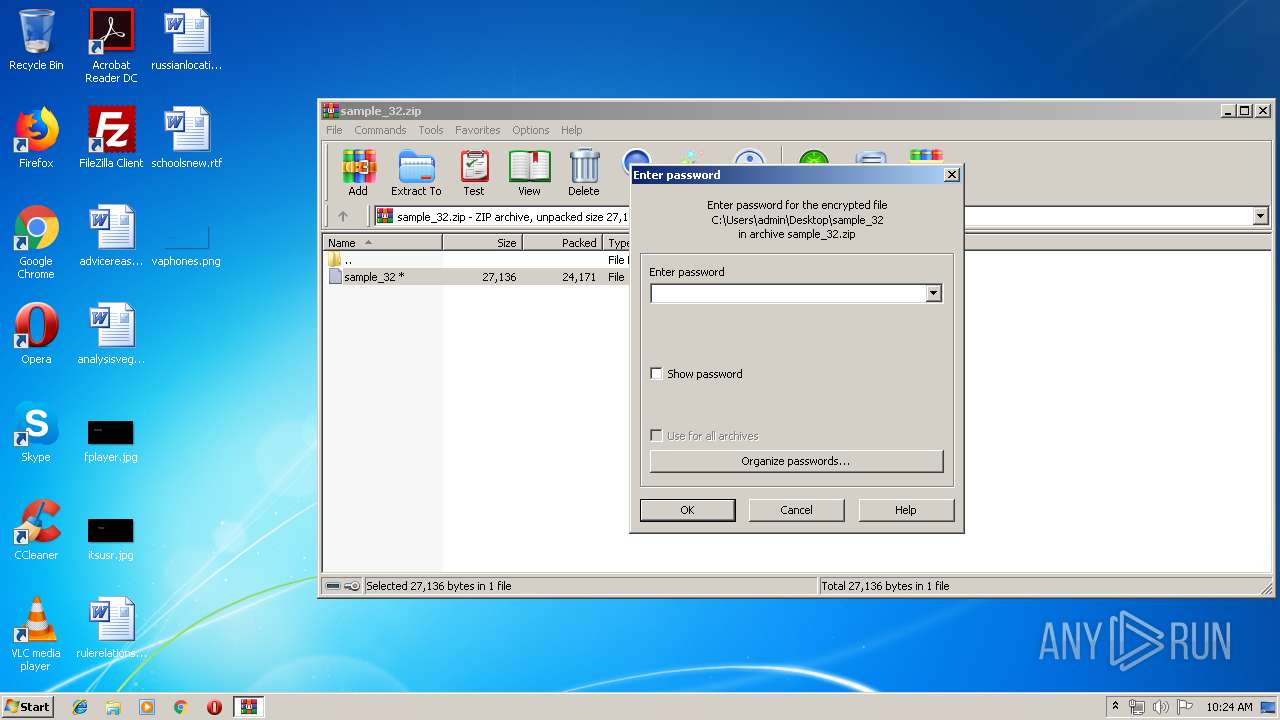
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2003:11:22 10:23:27 |
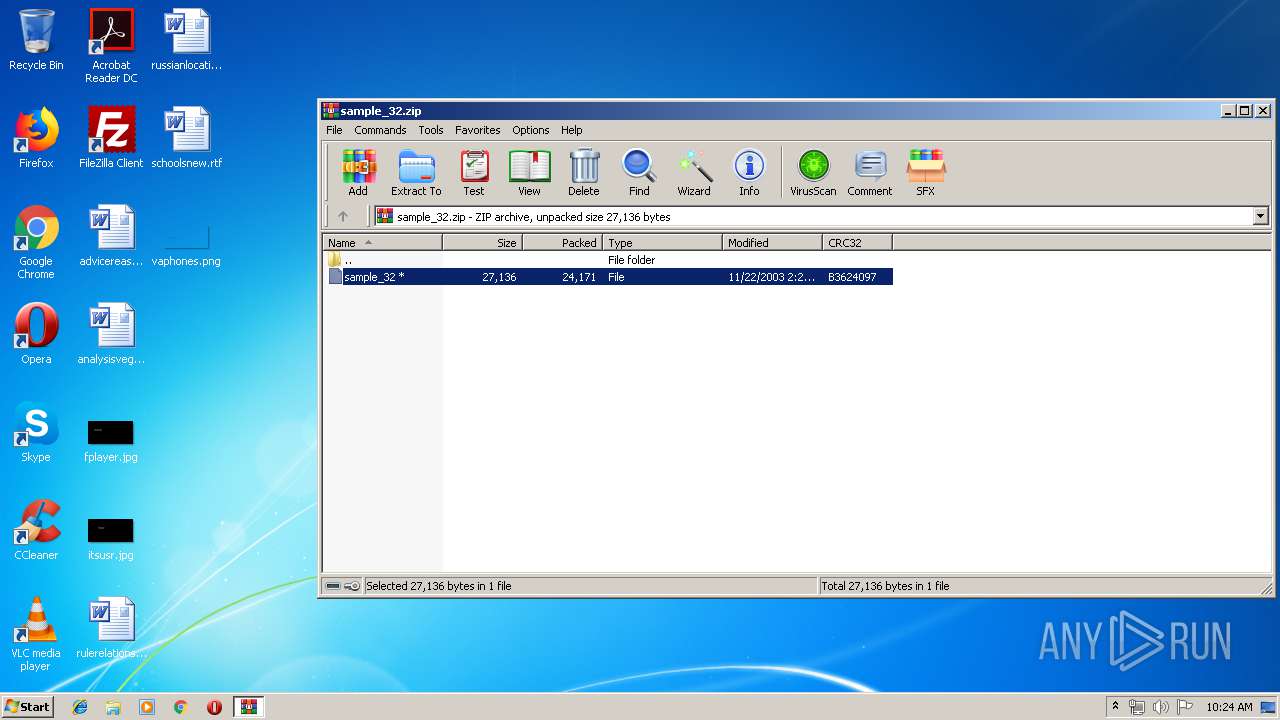
| ZipCRC: | 0xb3624097 |
| ZipCompressedSize: | 24171 |
| ZipUncompressedSize: | 27136 |
| ZipFileName: | sample_32 |
Total processes
43
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
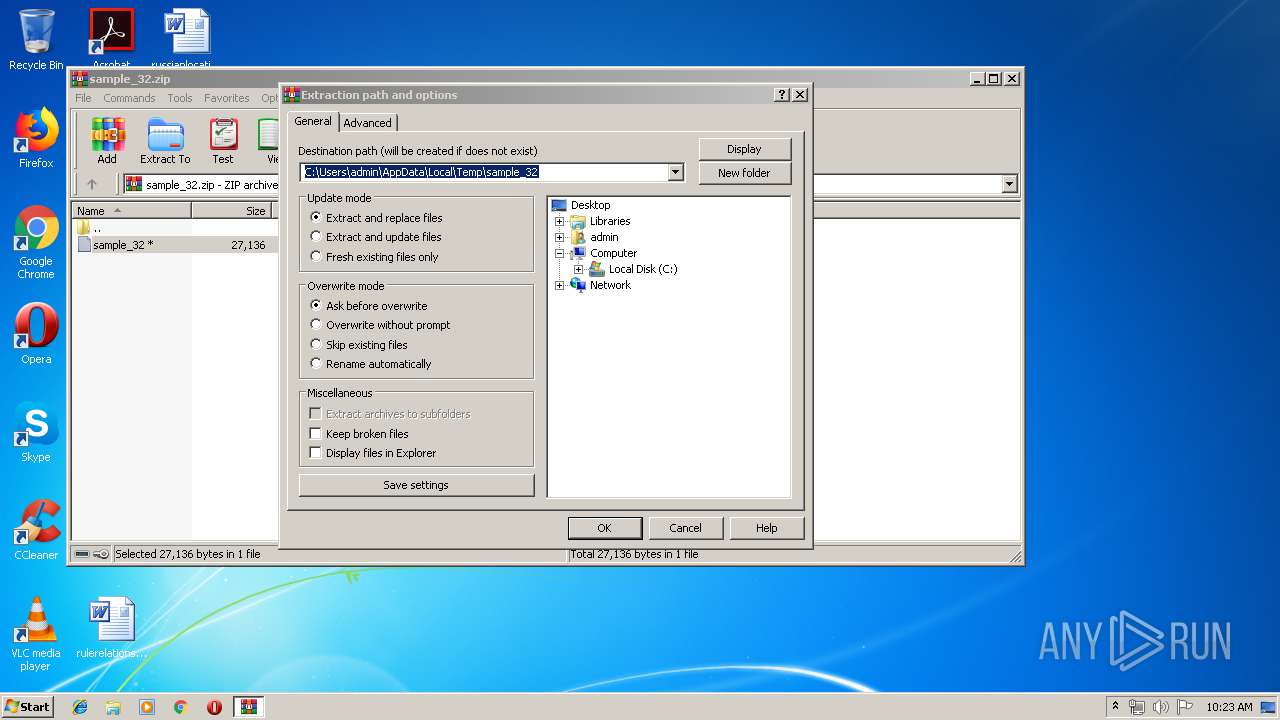
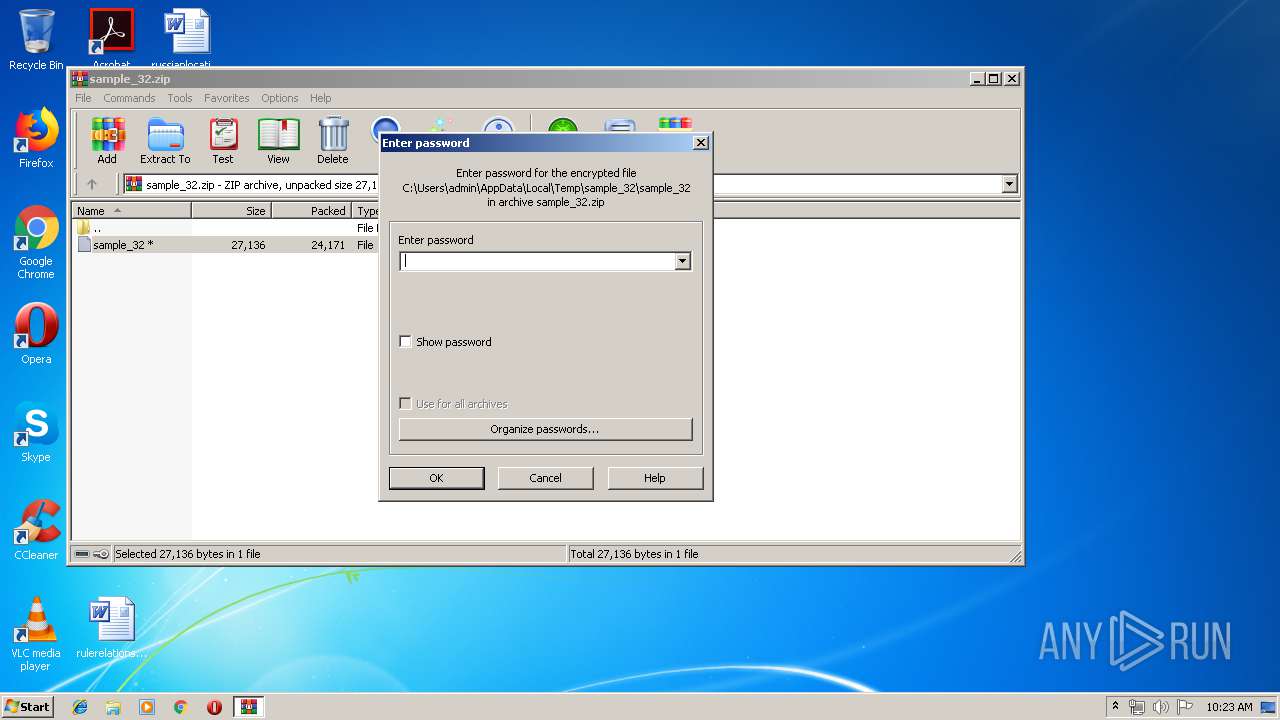
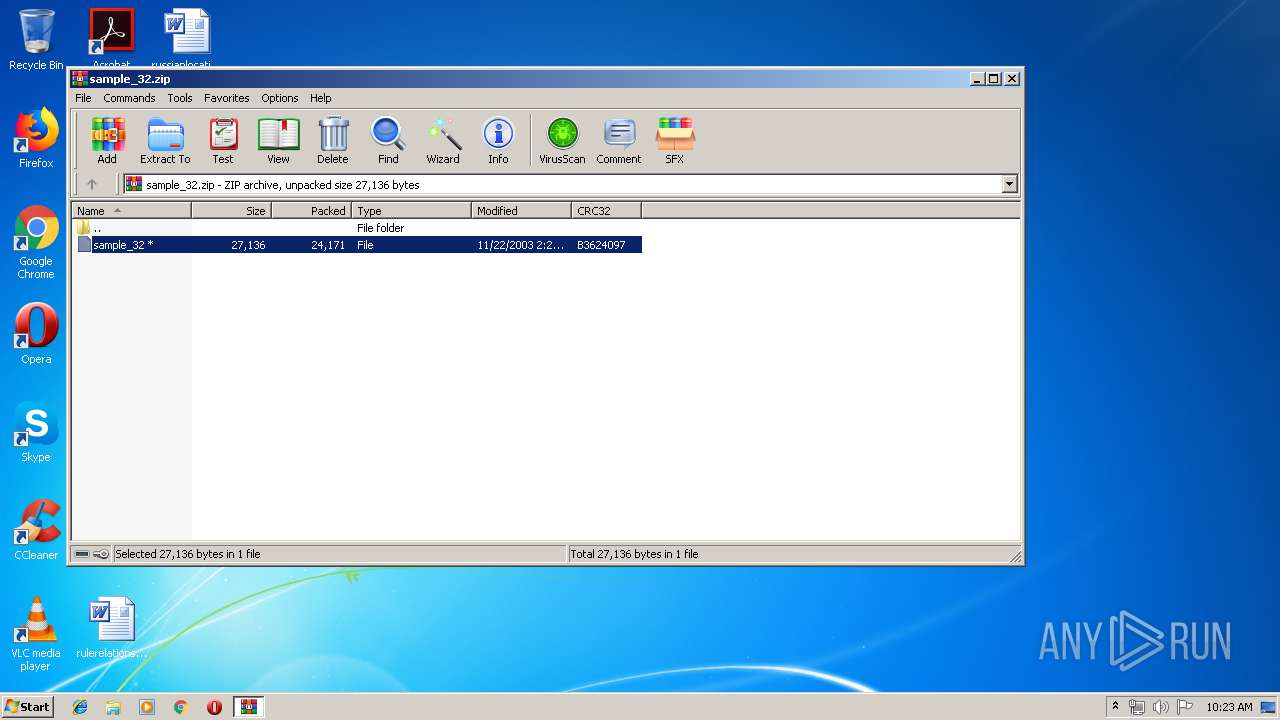
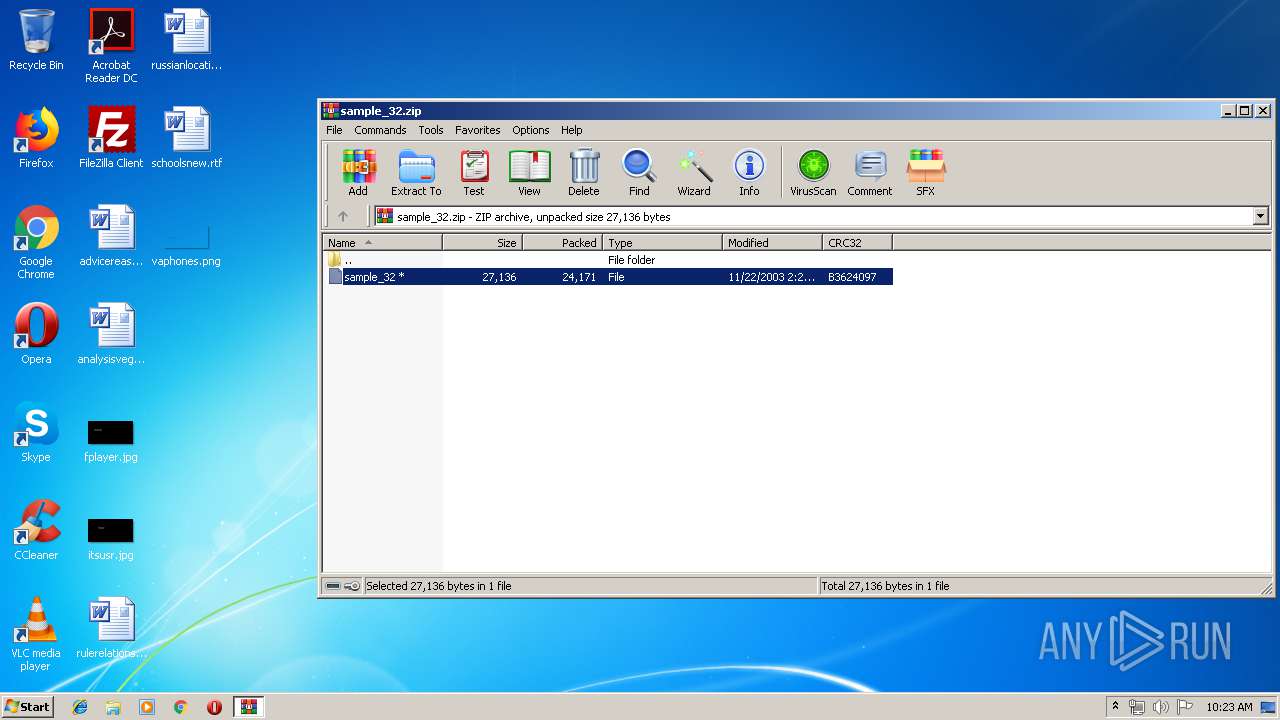
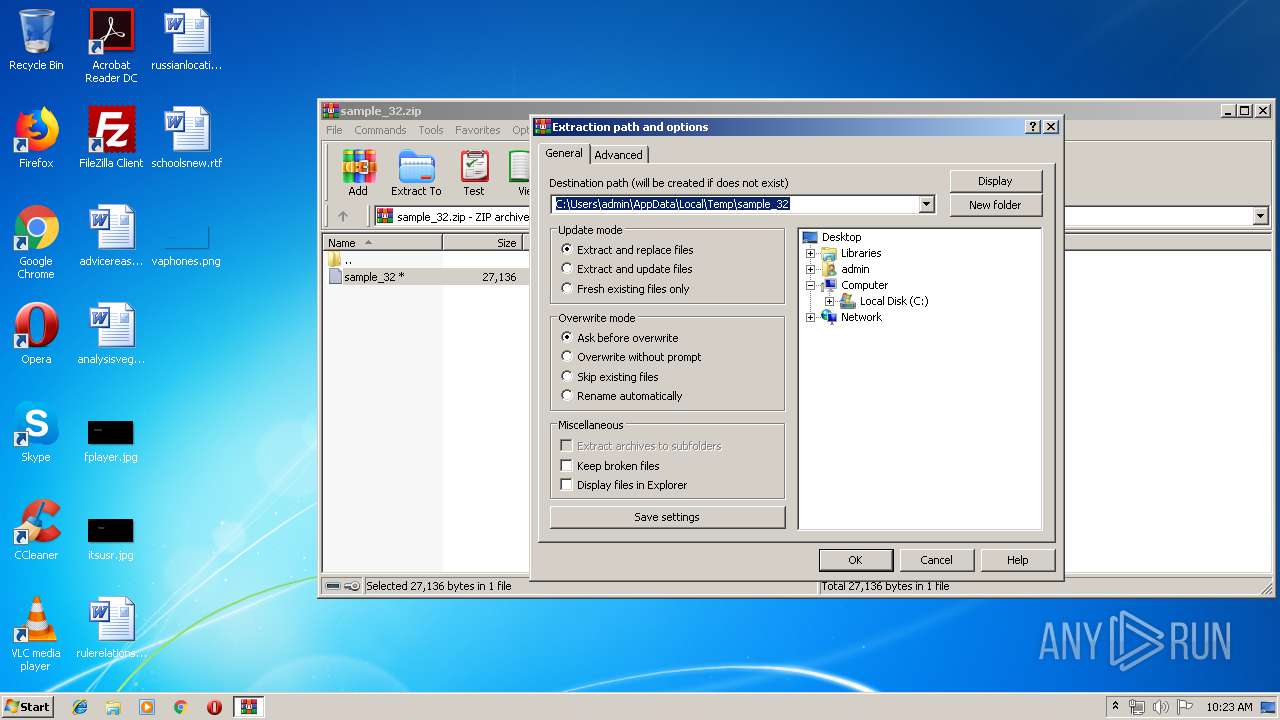
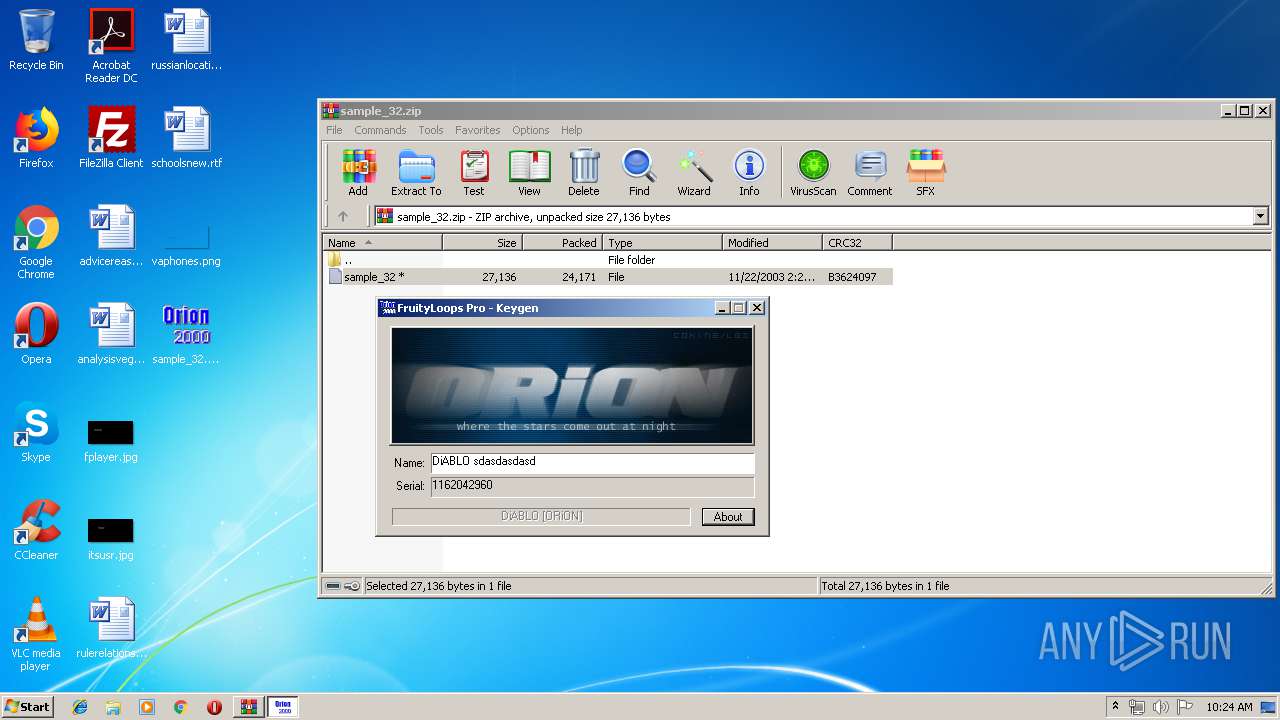
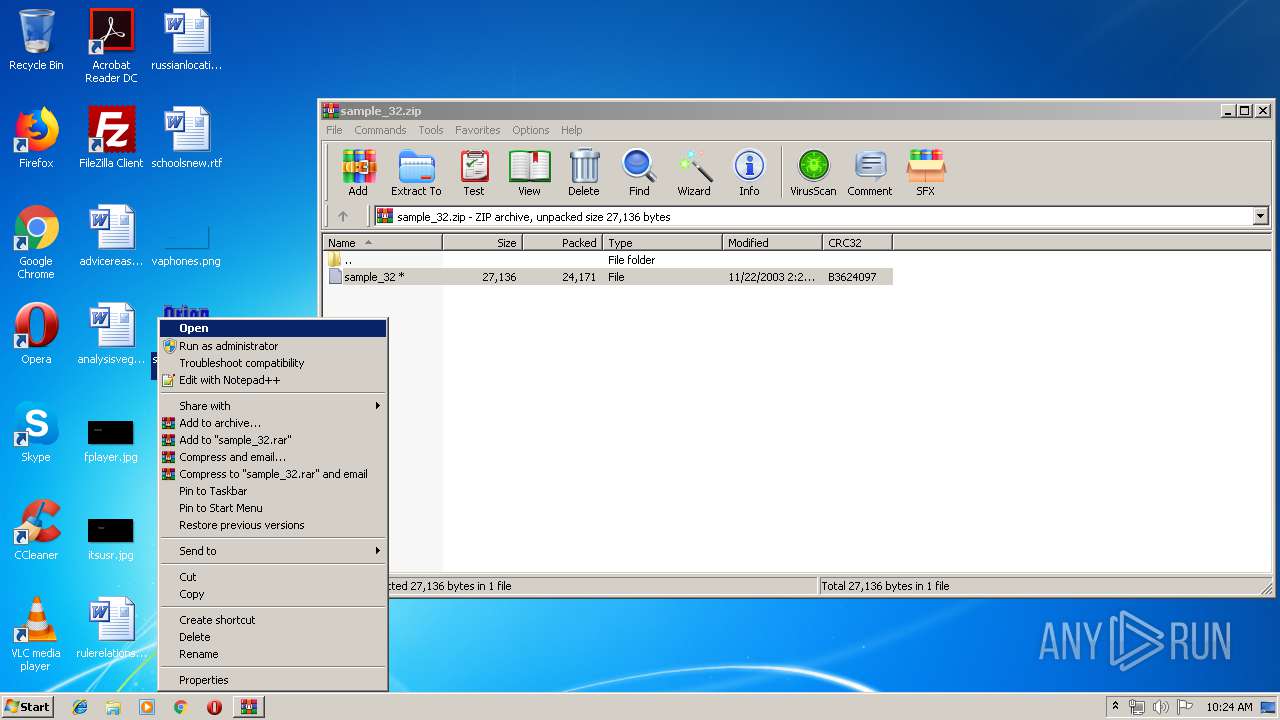
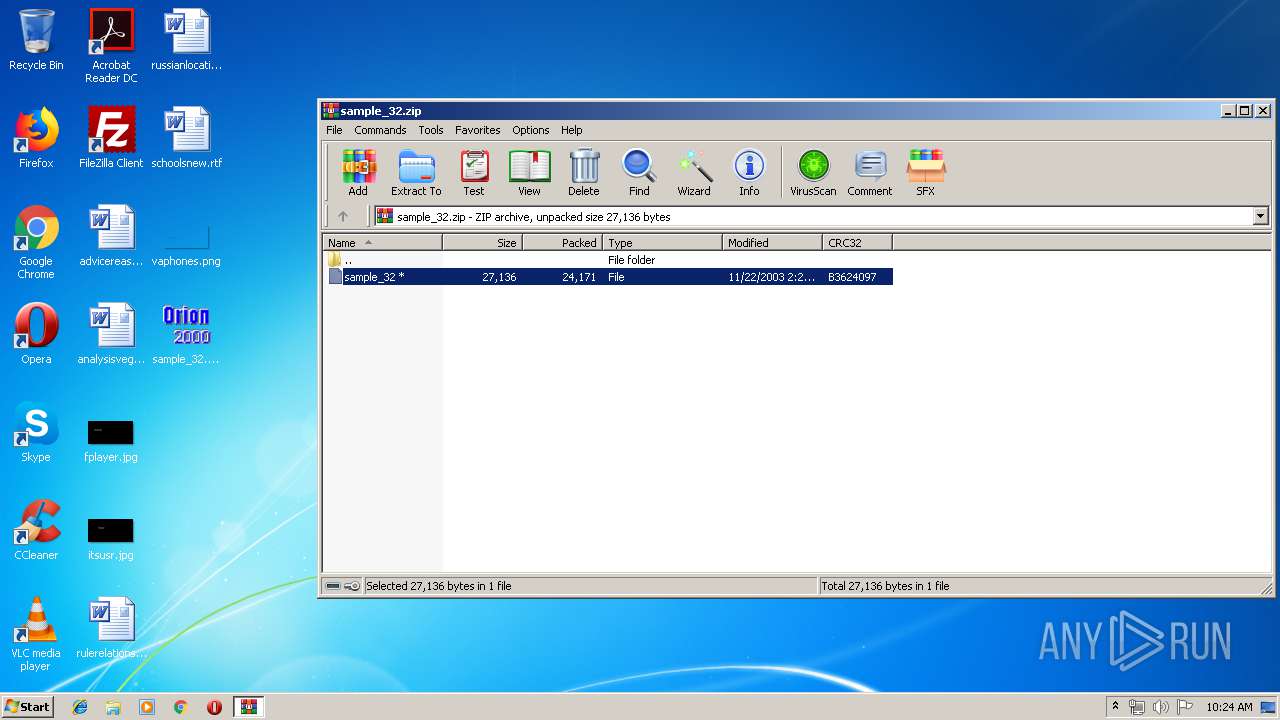
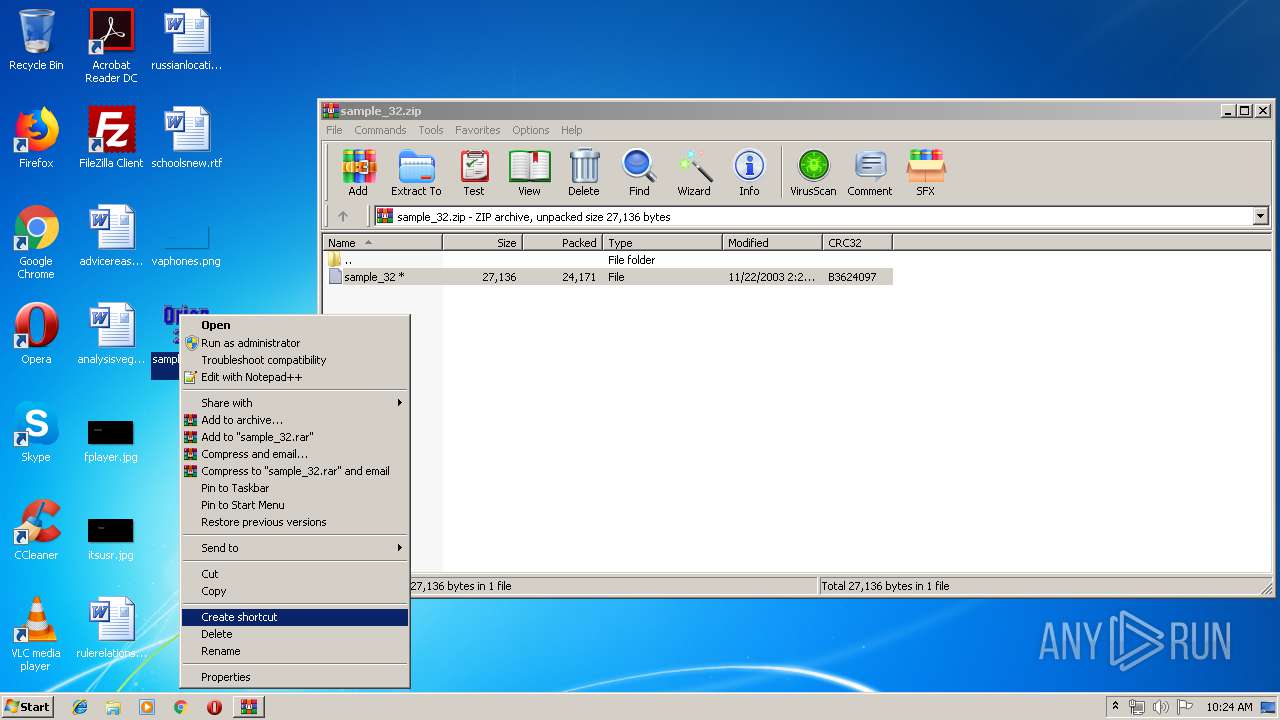
| 2716 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample_32.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
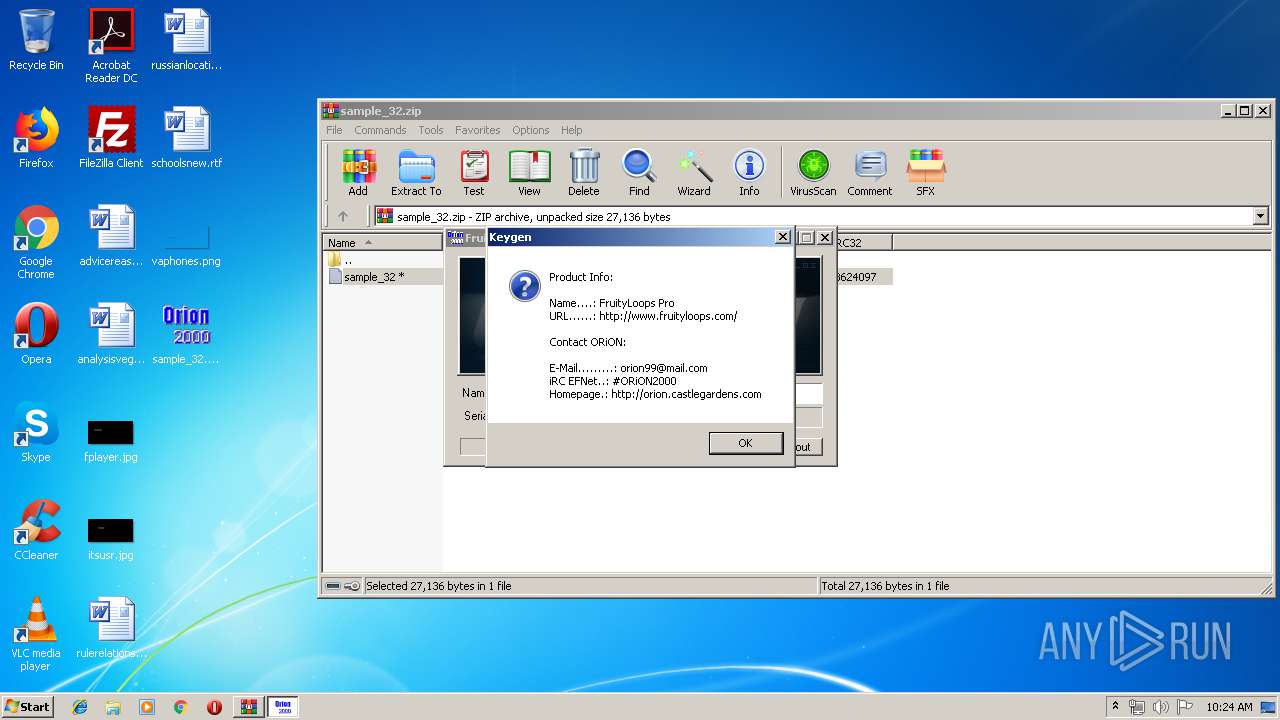
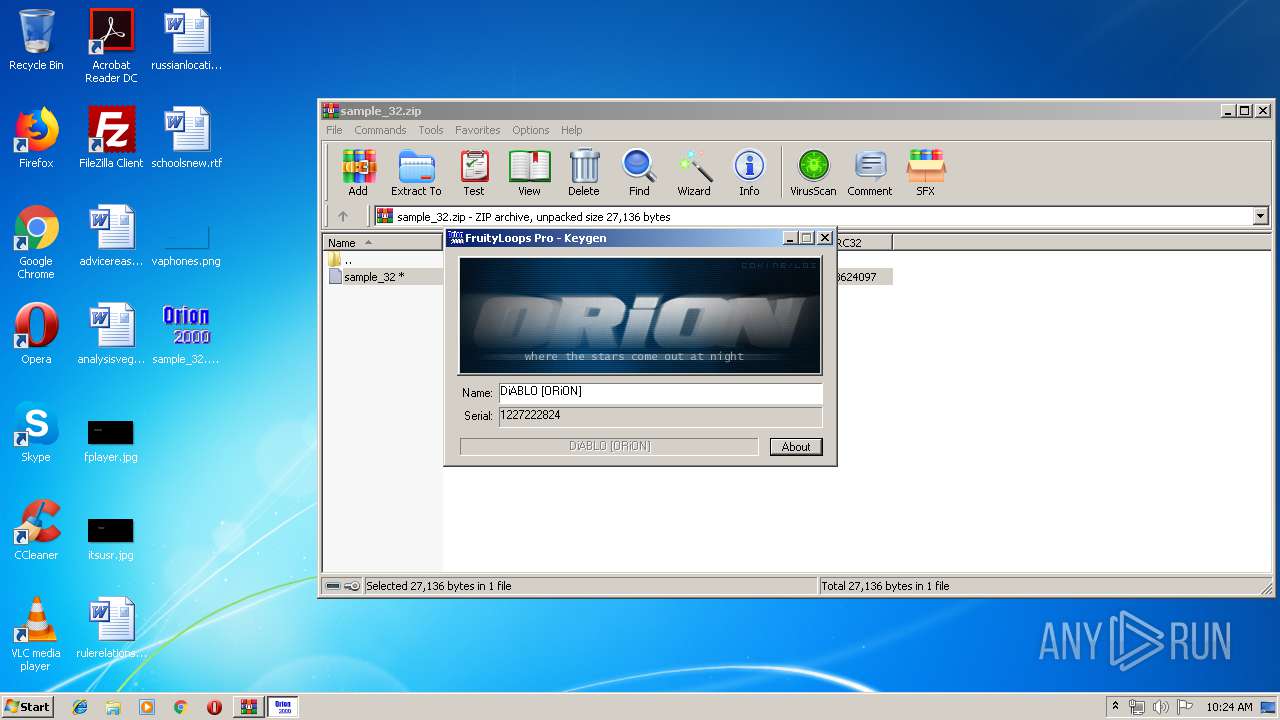
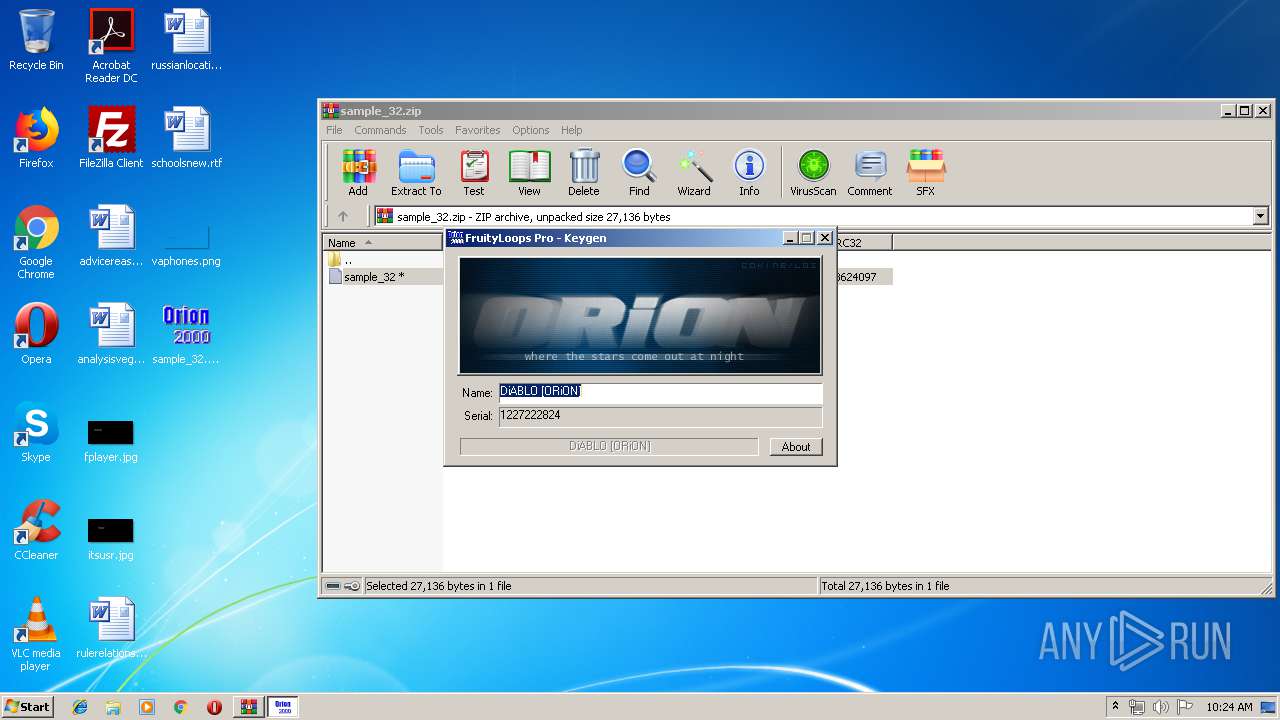
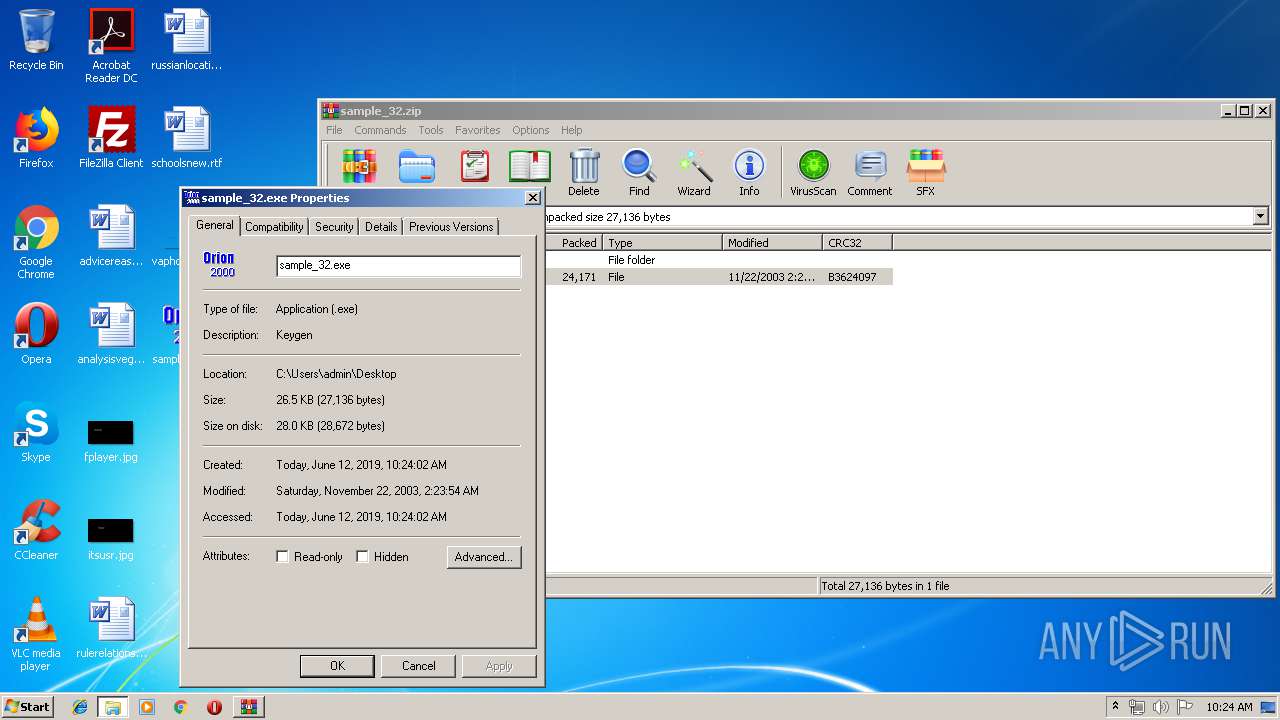
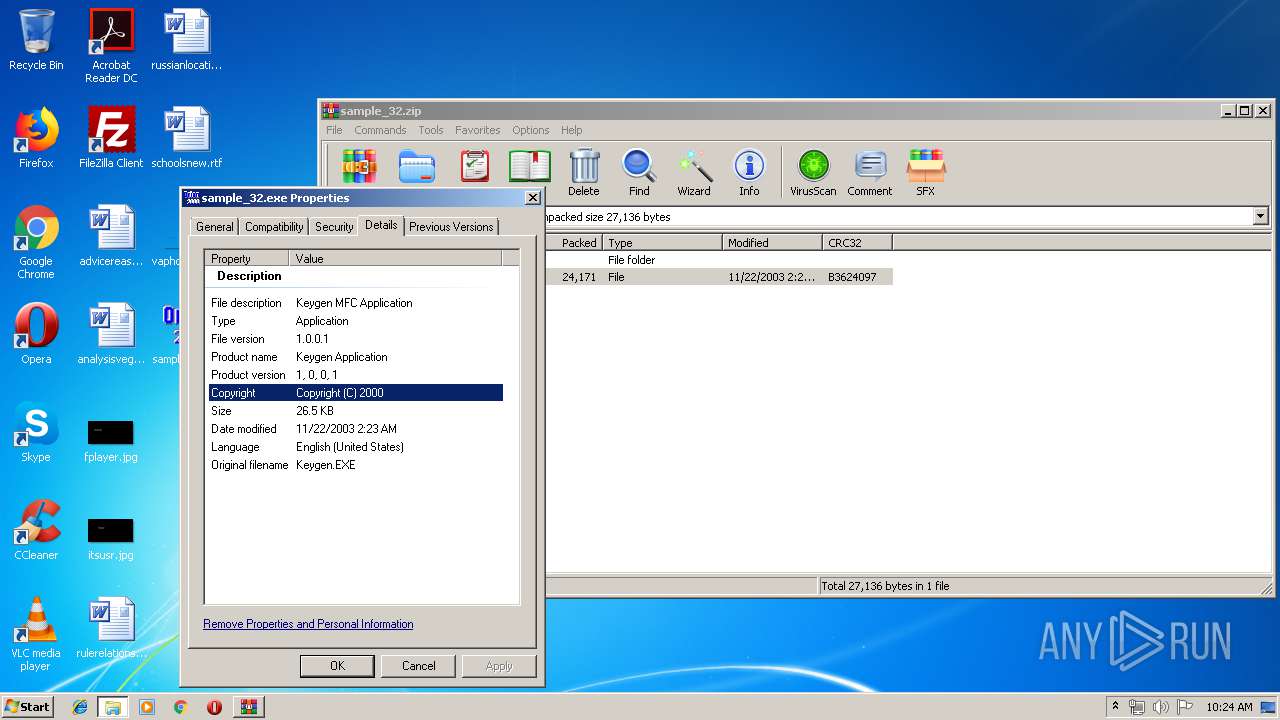
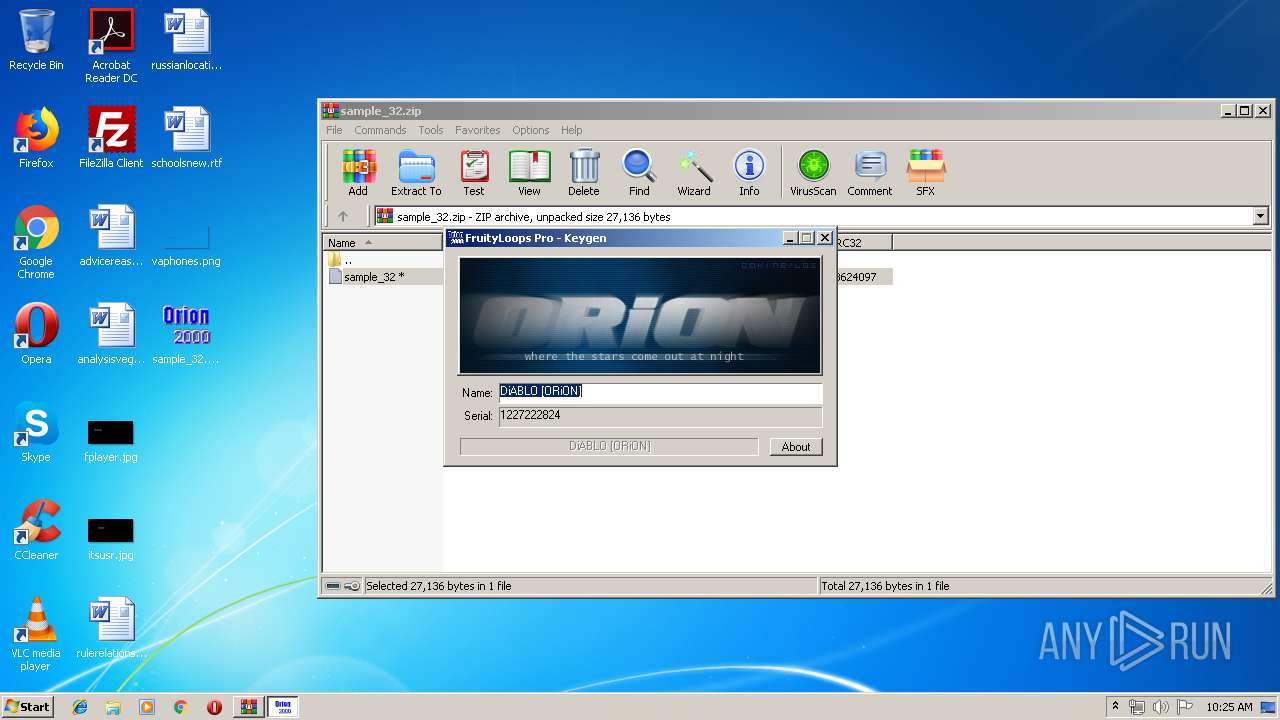
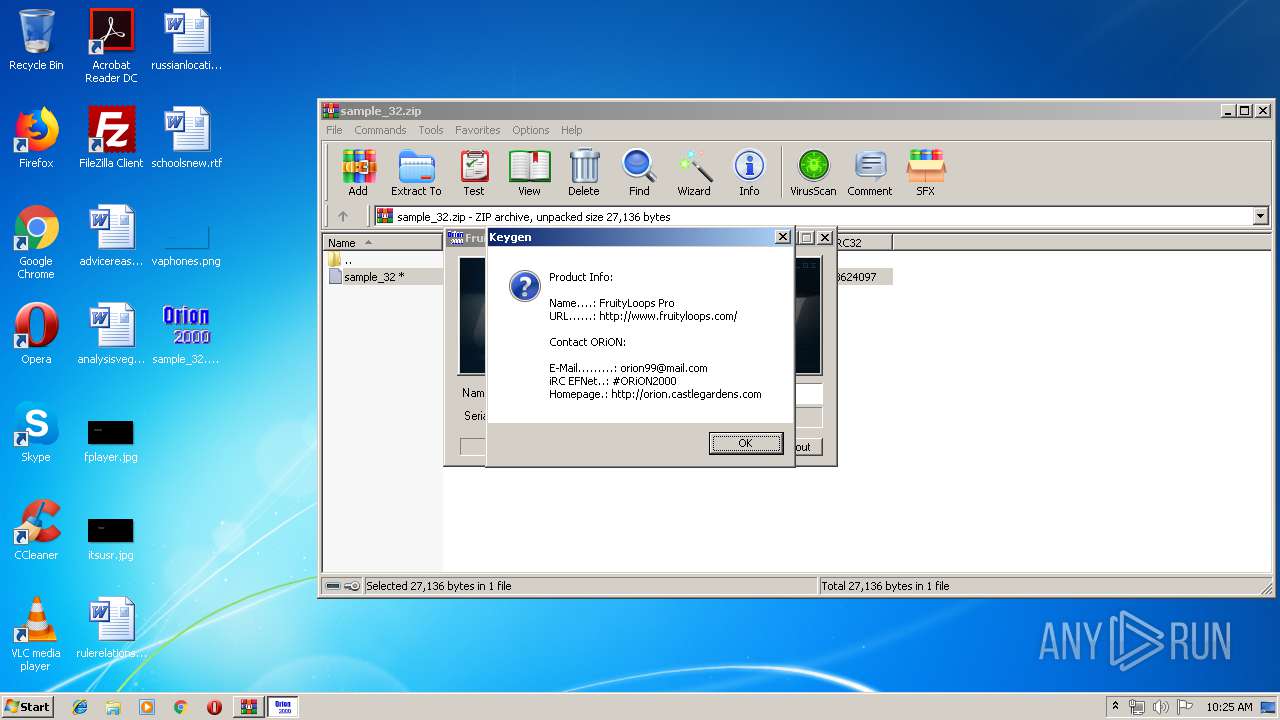
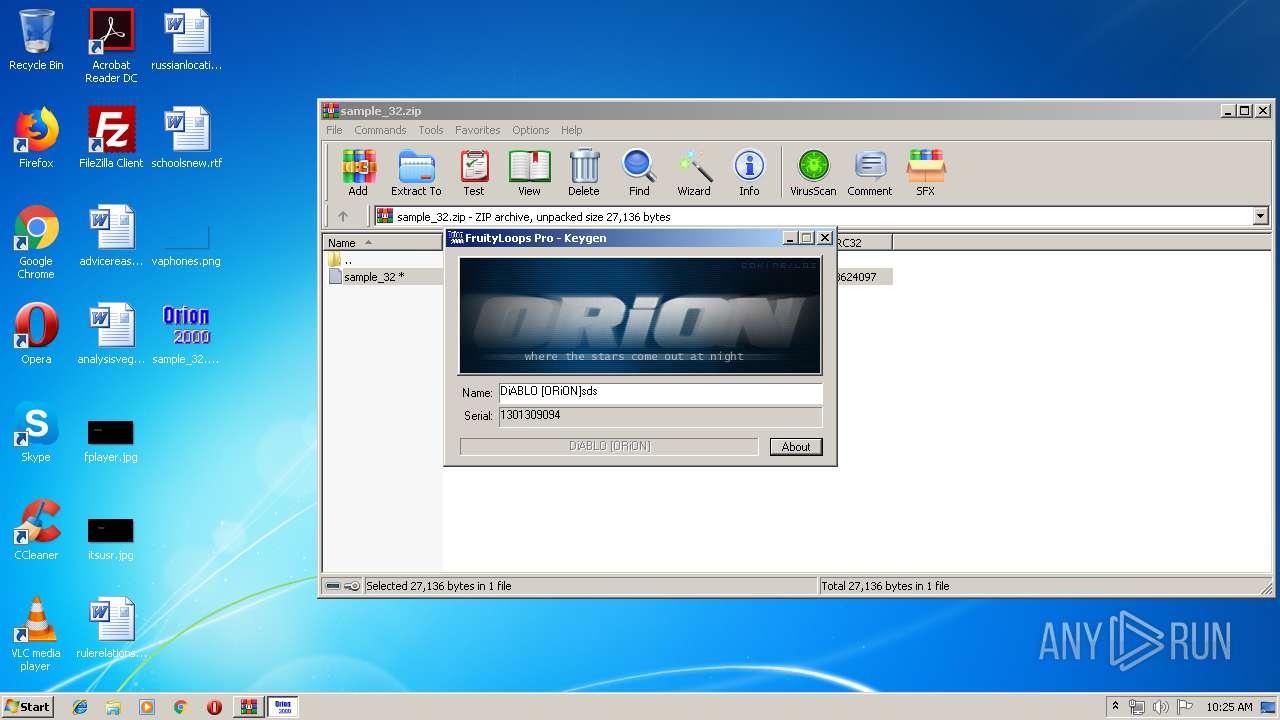
| 3156 | "C:\Users\admin\Desktop\sample_32.exe" | C:\Users\admin\Desktop\sample_32.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Keygen MFC Application Exit code: 2 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3232 | "C:\Windows\system32\wermgr.exe" "-outproc" "2044" "3708" | C:\Windows\system32\wermgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3620 | "C:\Windows\system32\wermgr.exe" "-outproc" "2044" "3680" | C:\Windows\system32\wermgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3664 | "C:\Users\admin\Desktop\sample_32.exe" | C:\Users\admin\Desktop\sample_32.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Keygen MFC Application Exit code: 3221226540 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3820 | "C:\Users\admin\Desktop\sample_32.exe" | C:\Users\admin\Desktop\sample_32.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Keygen MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 4000 | "C:\Users\admin\Desktop\sample_32.exe" | C:\Users\admin\Desktop\sample_32.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Keygen MFC Application Exit code: 2 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
526
Read events
511
Write events
15
Delete events
0
Modification events
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_32.zip | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_32 | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2716 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\sample_32\sample_32 | executable | |
MD5:— | SHA256:— | |||
| 3232 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_sample_32.exe_ecb36be8f4aea25a48e389493e444add412c2ba_cab_0cb4b6ac\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 2716 | WinRAR.exe | C:\Users\admin\Desktop\sample_32 | executable | |
MD5:— | SHA256:— | |||
| 3620 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_sample_32.exe_ecb36be8f4aea25a48e389493e444add412c2ba_0e30c487\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 3232 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_sample_32.exe_ecb36be8f4aea25a48e389493e444add412c2ba_cab_0cb4b6ac\appcompat.txt | xml | |
MD5:— | SHA256:— | |||
| 3232 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_sample_32.exe_ecb36be8f4aea25a48e389493e444add412c2ba_cab_0cb4b6ac\TabB63F.tmp | text | |
MD5:35ED452BF054111134EE0A22CF29B770 | SHA256:A6C27302C2C28217F4619165F1FAEC76C65CC6B2E77C304A1D4EDBFB1BEC4A4F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
sample_32.exe | FTH: (3820): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|