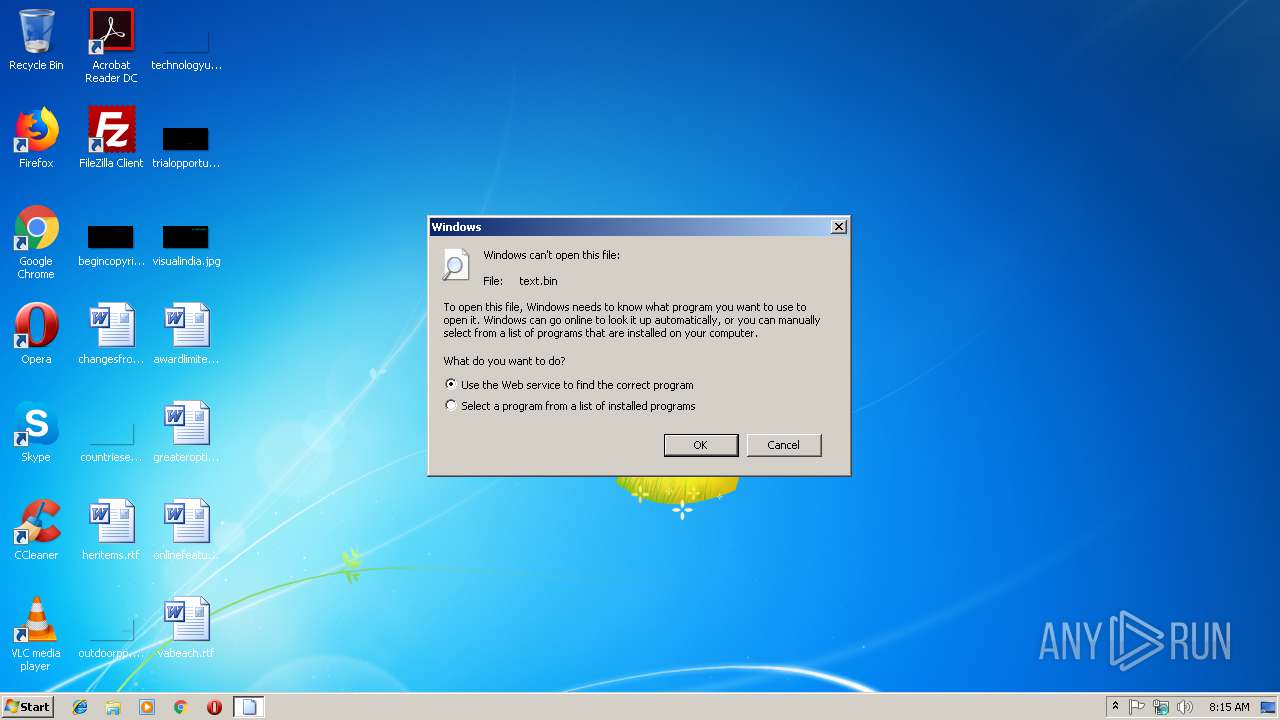
| File name: | text.bin |
| Full analysis: | https://app.any.run/tasks/5bdbba6e-cc24-4adb-9031-b66d31cd957e |
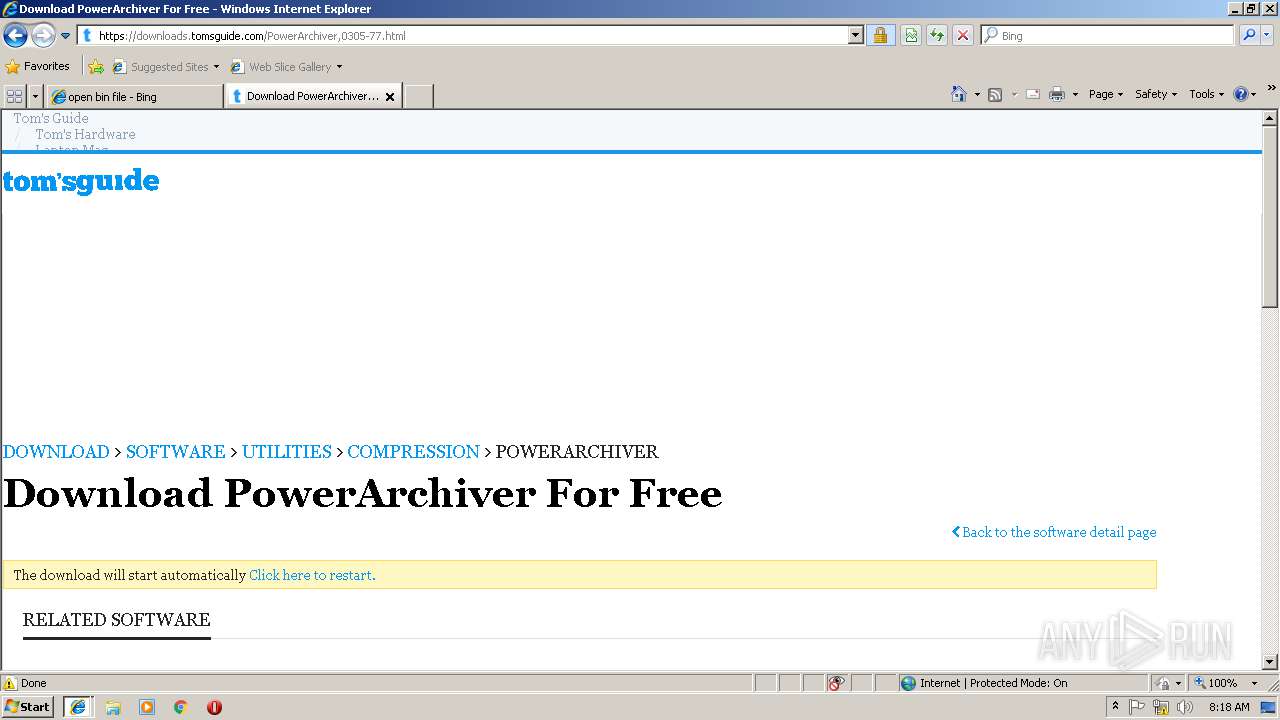
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 08:15:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | PDP-11 pure executable not stripped - version 10 |
| MD5: | 816284DBBF63570E04A1CBDC65F83972 |
| SHA1: | B9BB9A1B46C89ACB7968FF486997A5DEC09B7EC1 |
| SHA256: | 8AB683671C292D862C7A37D7ACB756F4F8B28139C4F8F96245086F5A2D739DD0 |
| SSDEEP: | 12288:VCzLLHhFRPt6z0EPm7QMcHYle9zOdFsNBldLcWY3aG/xVM9XO2h2CkI2+kdqE36v:GPBOVGId7 |
MALICIOUS
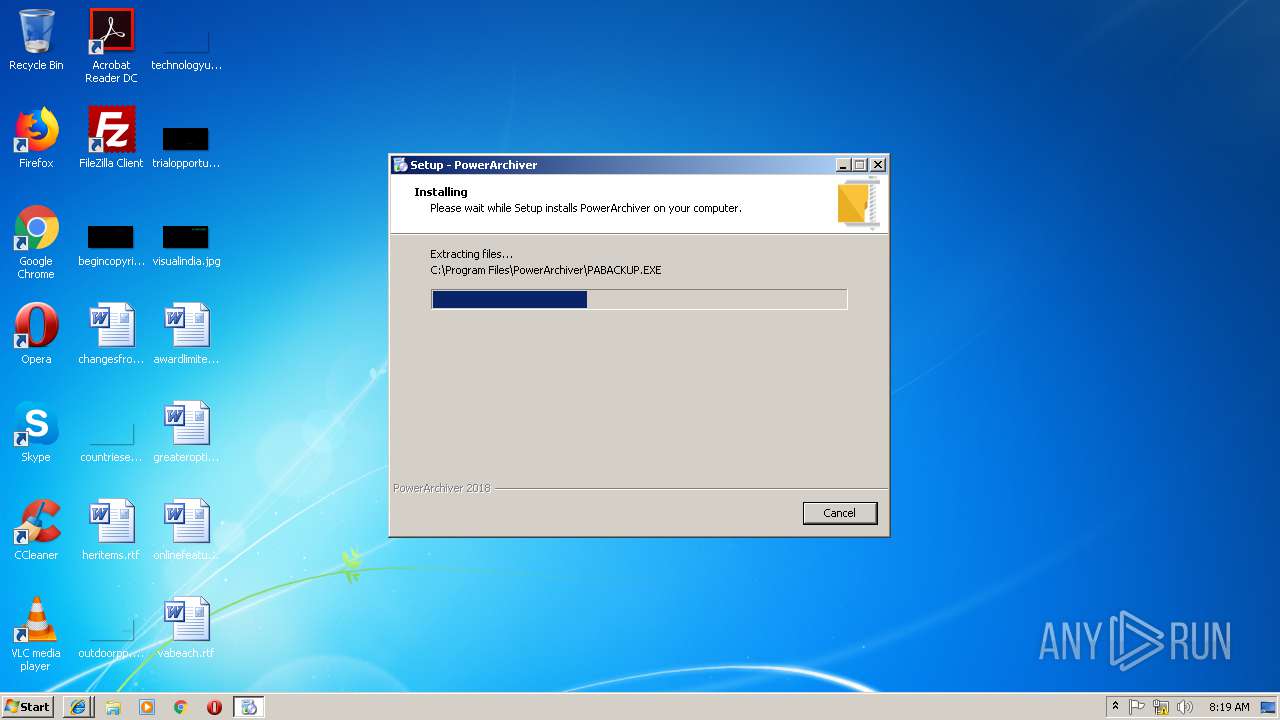
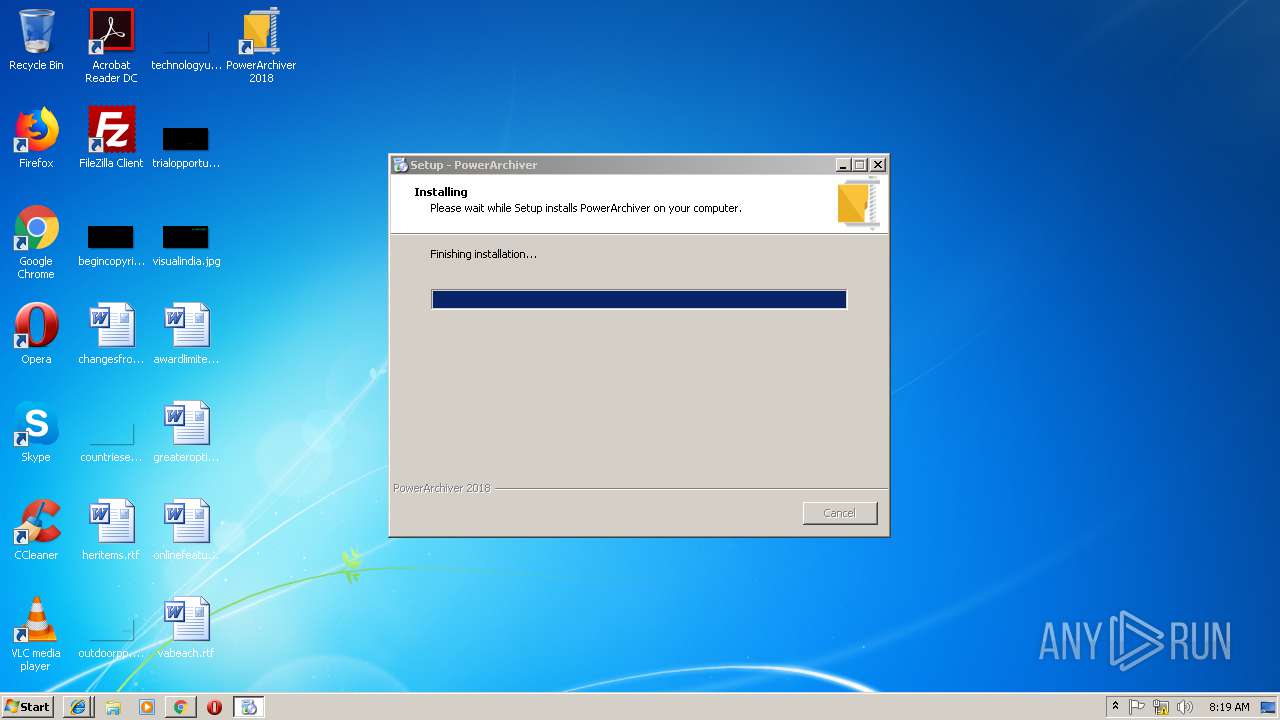
Registers / Runs the DLL via REGSVR32.EXE
- powarc180048[1].tmp (PID: 2684)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2796)
SUSPICIOUS
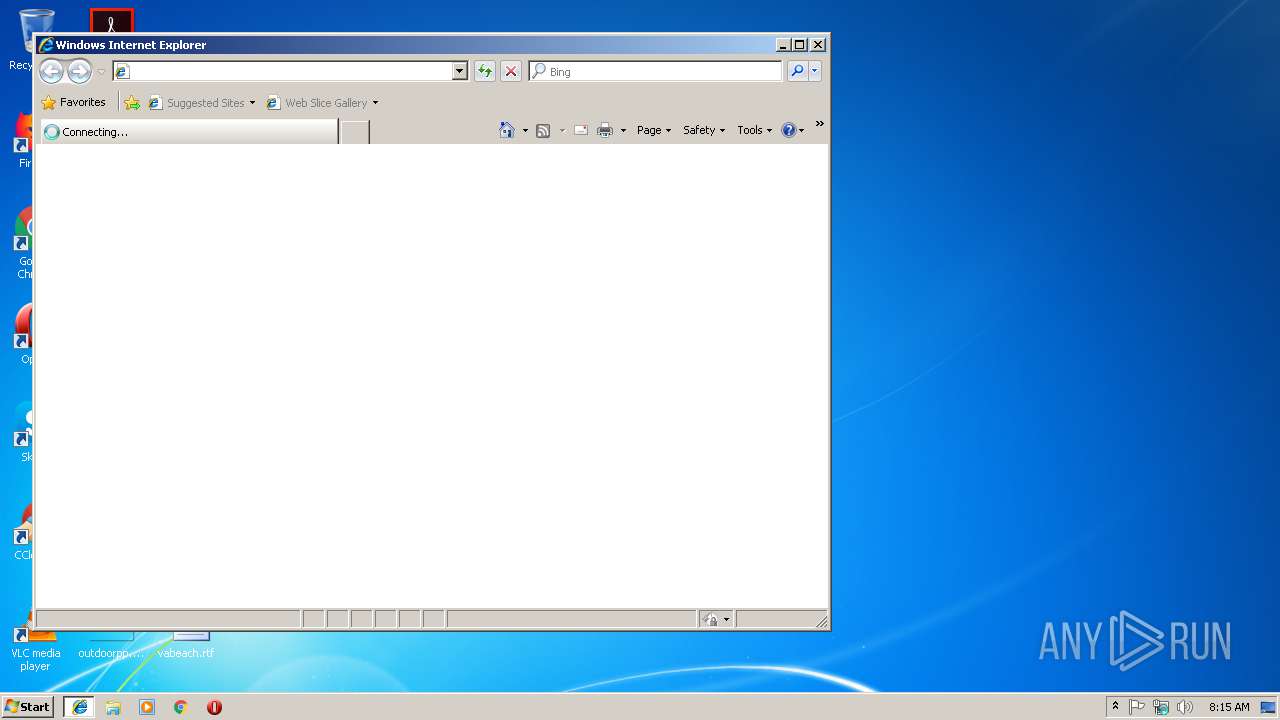
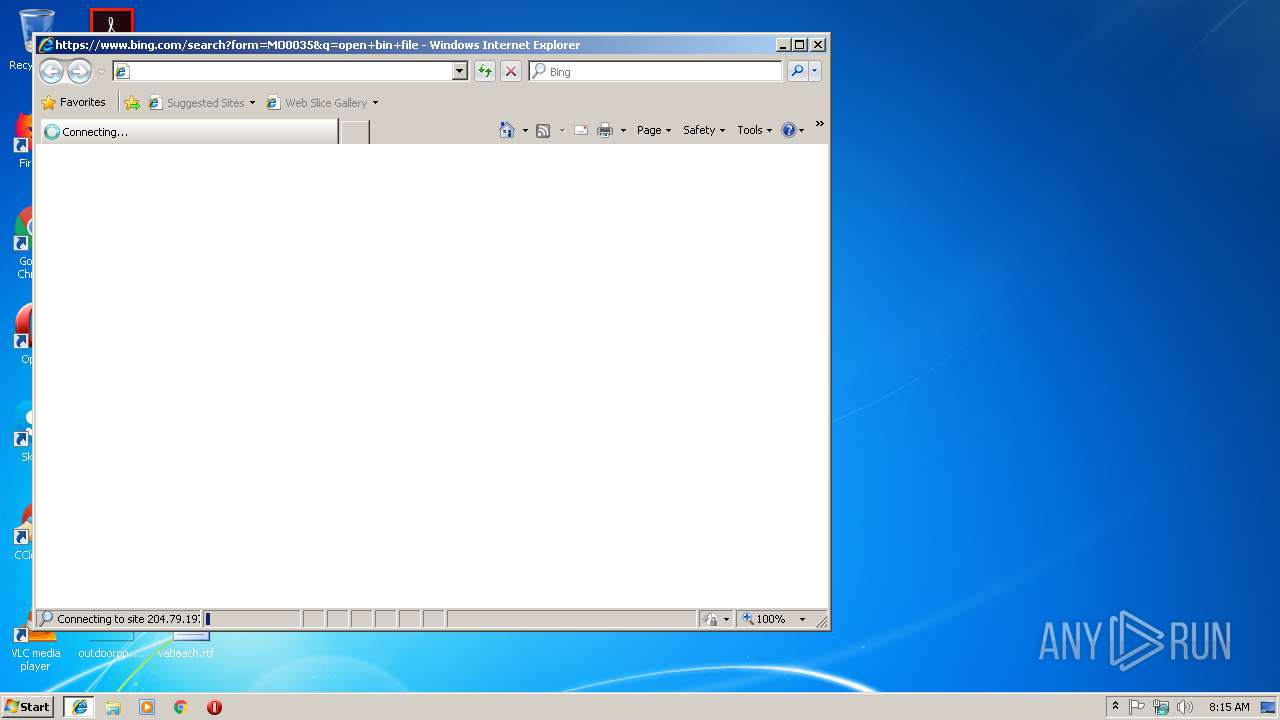
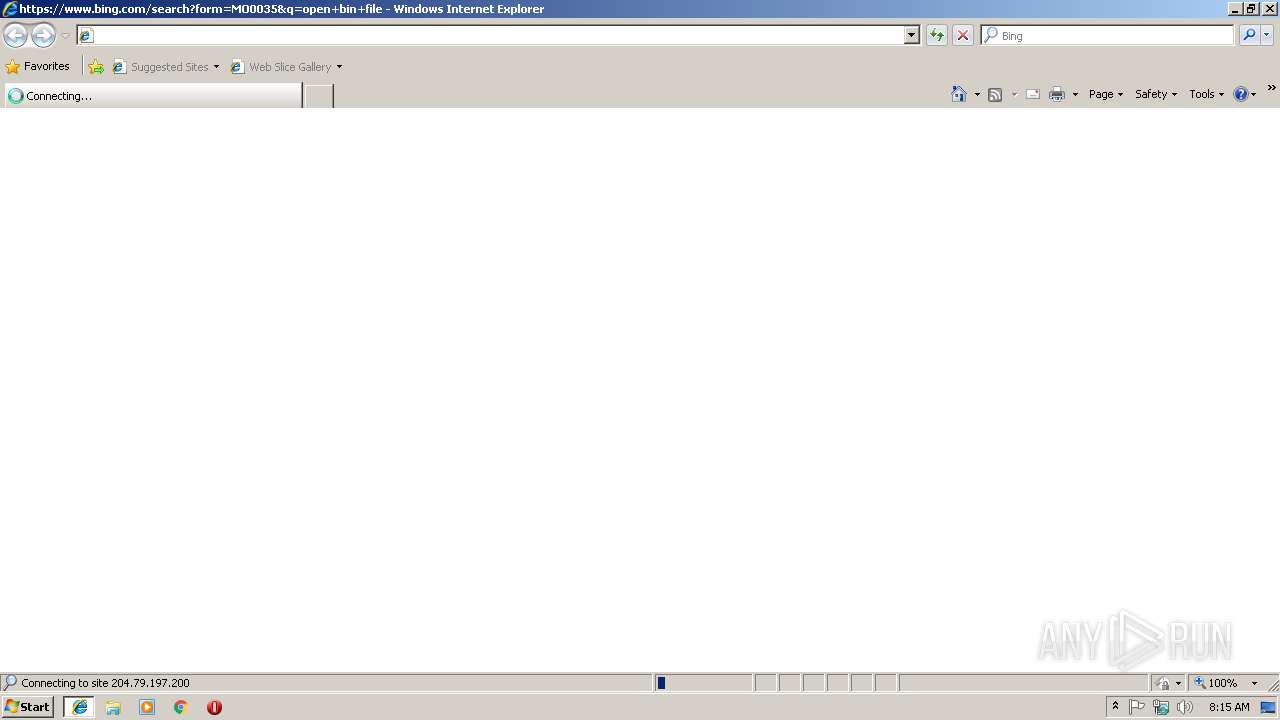
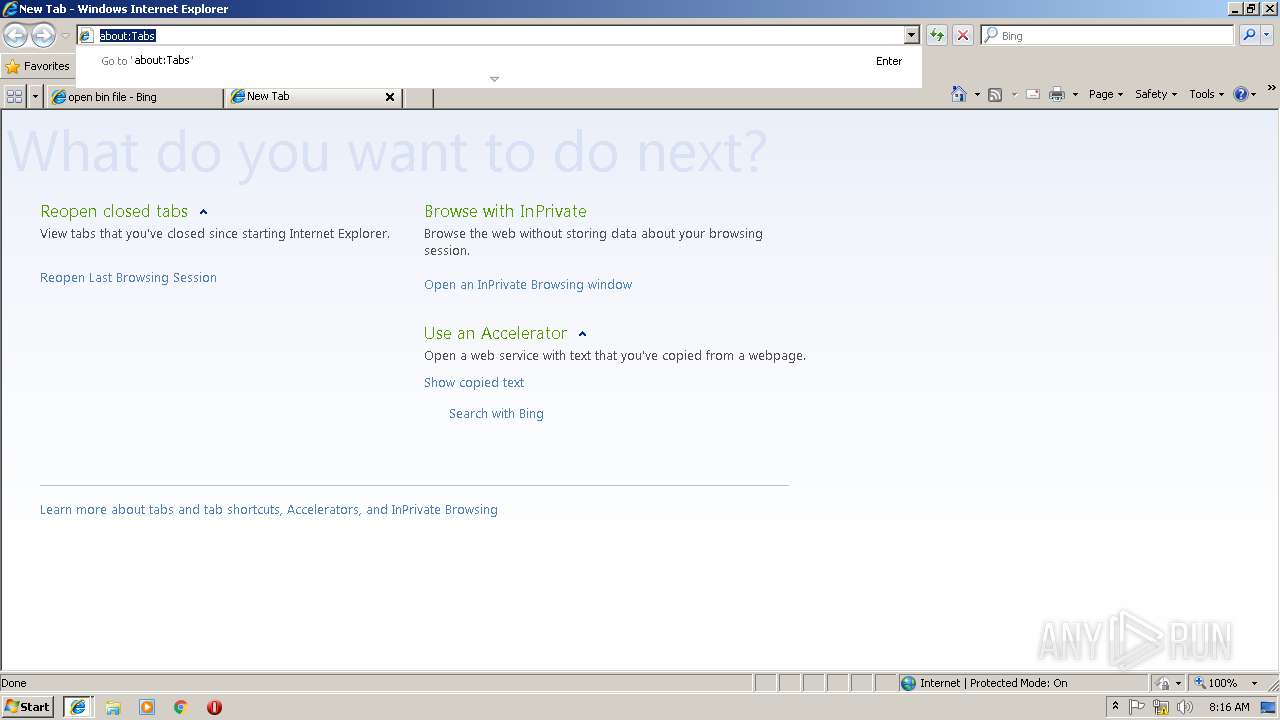
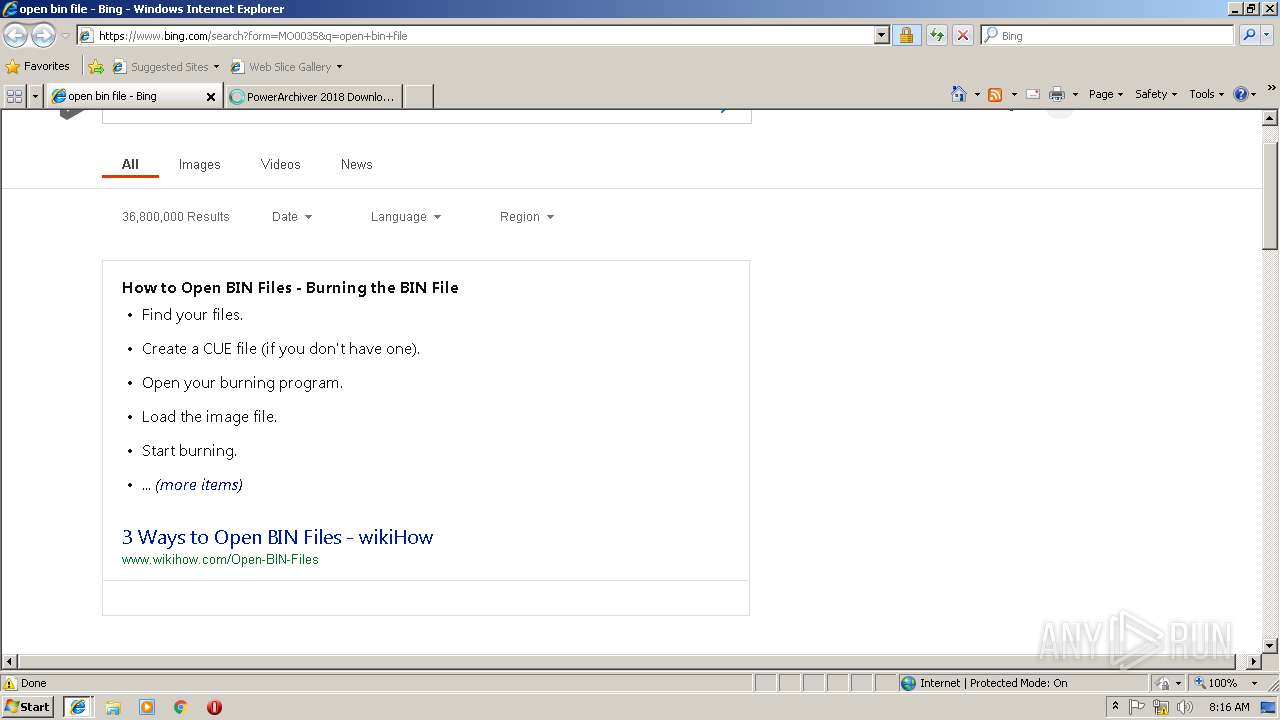
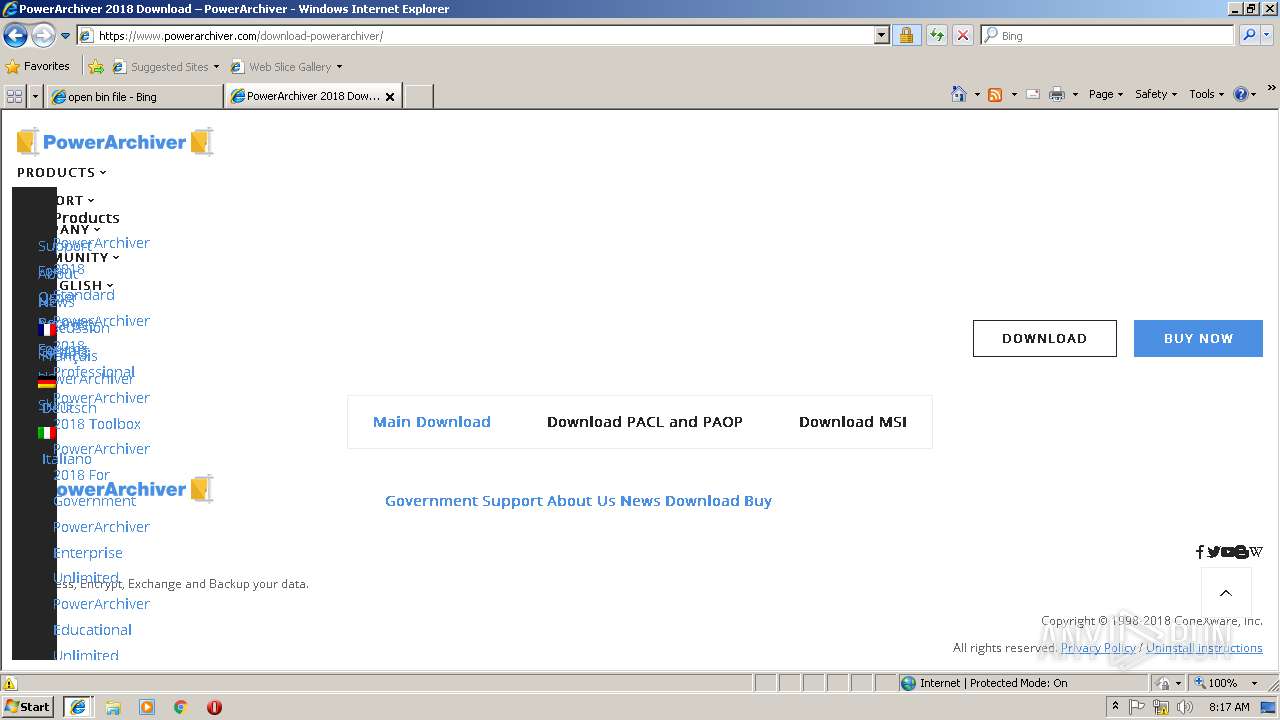
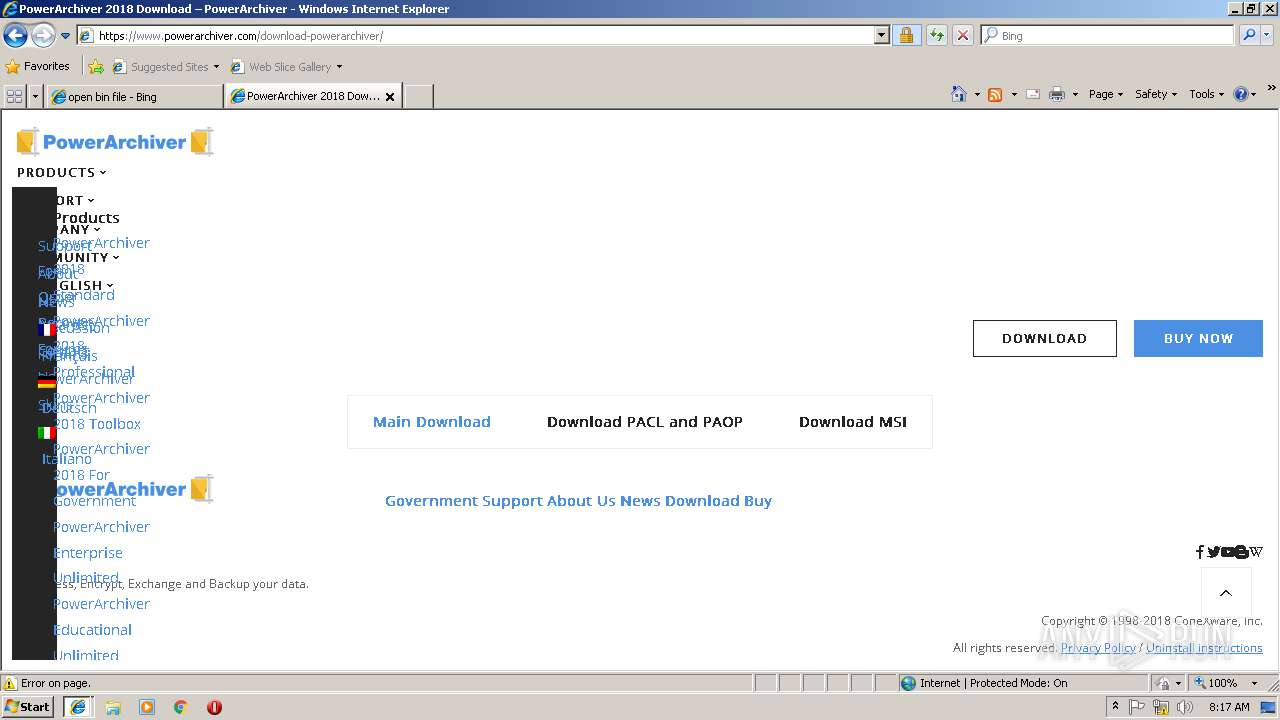
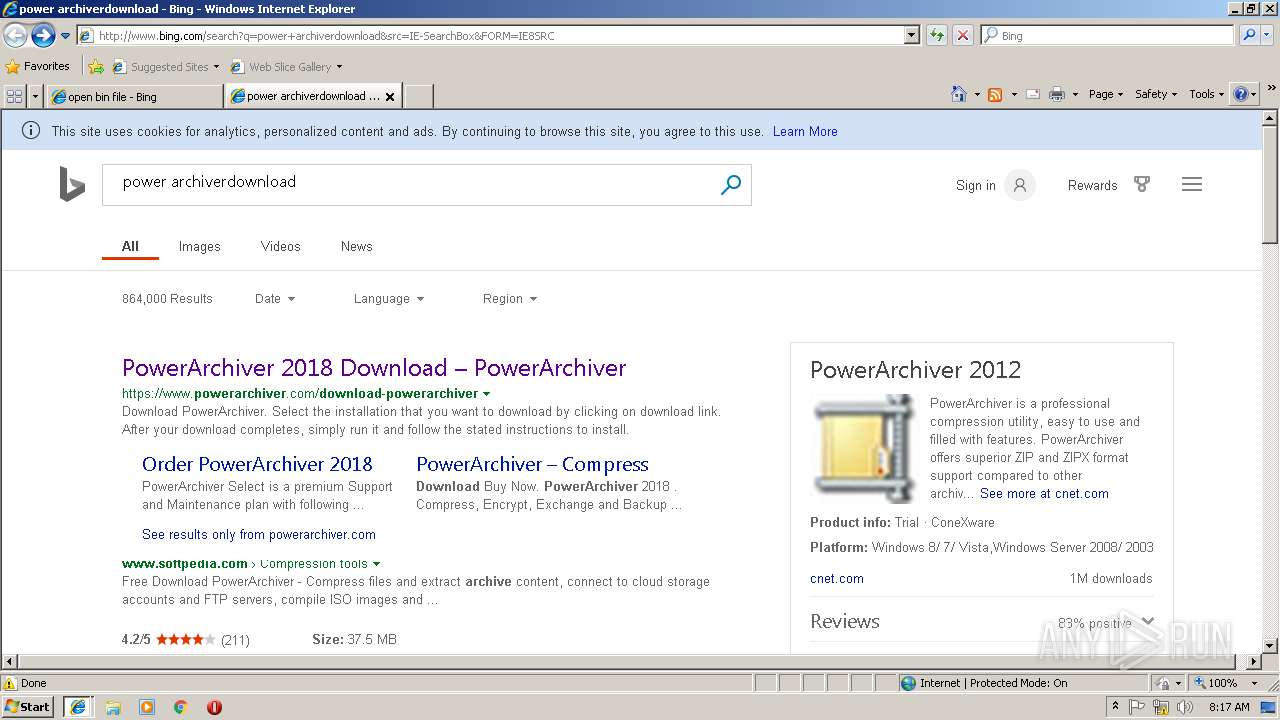
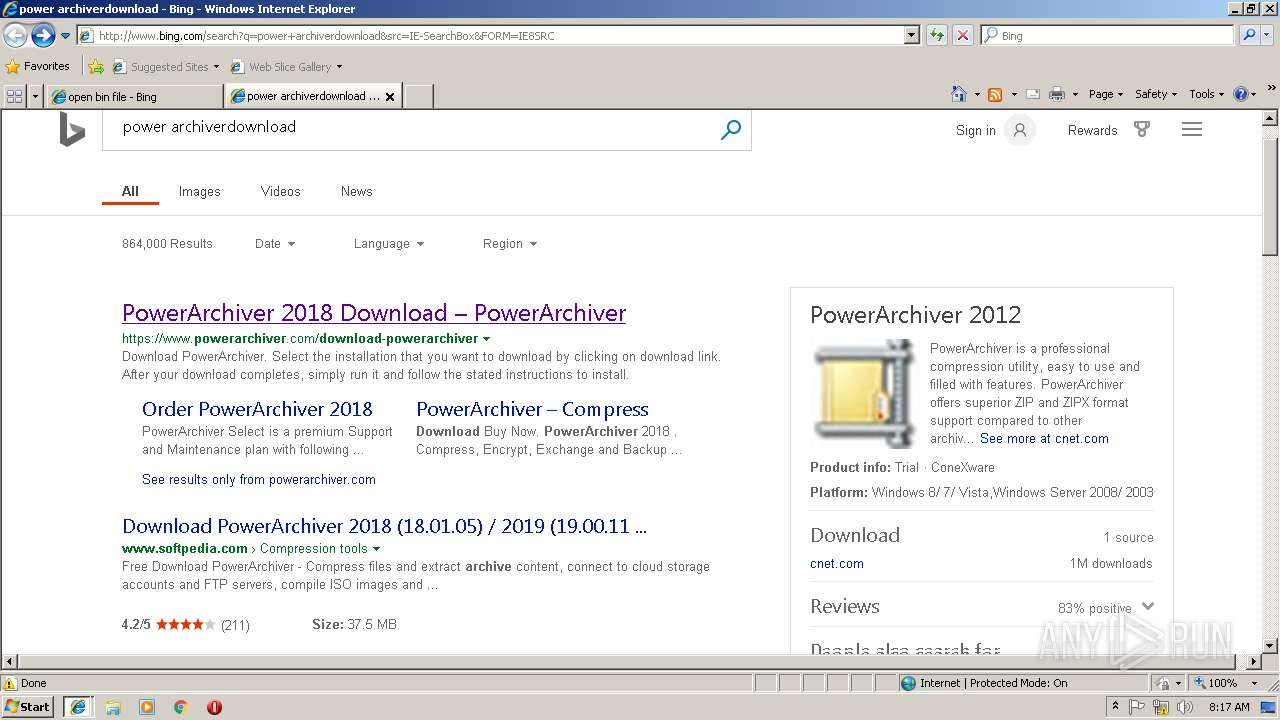
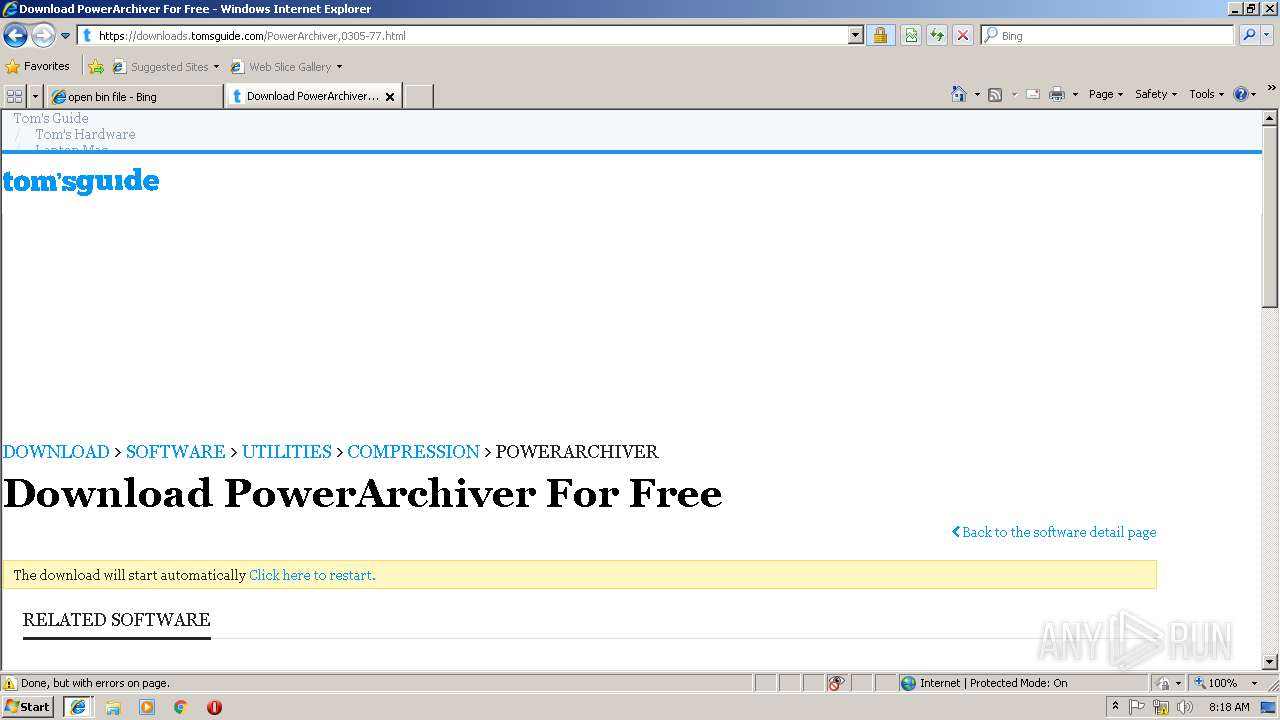
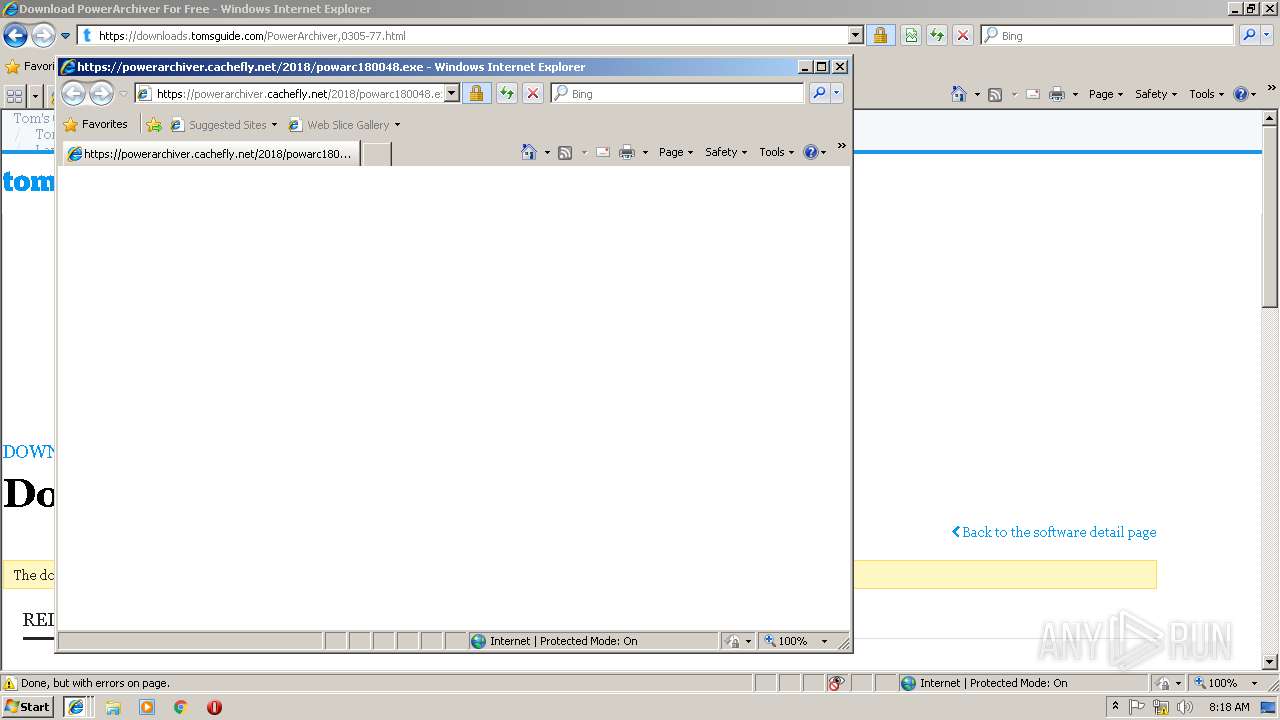
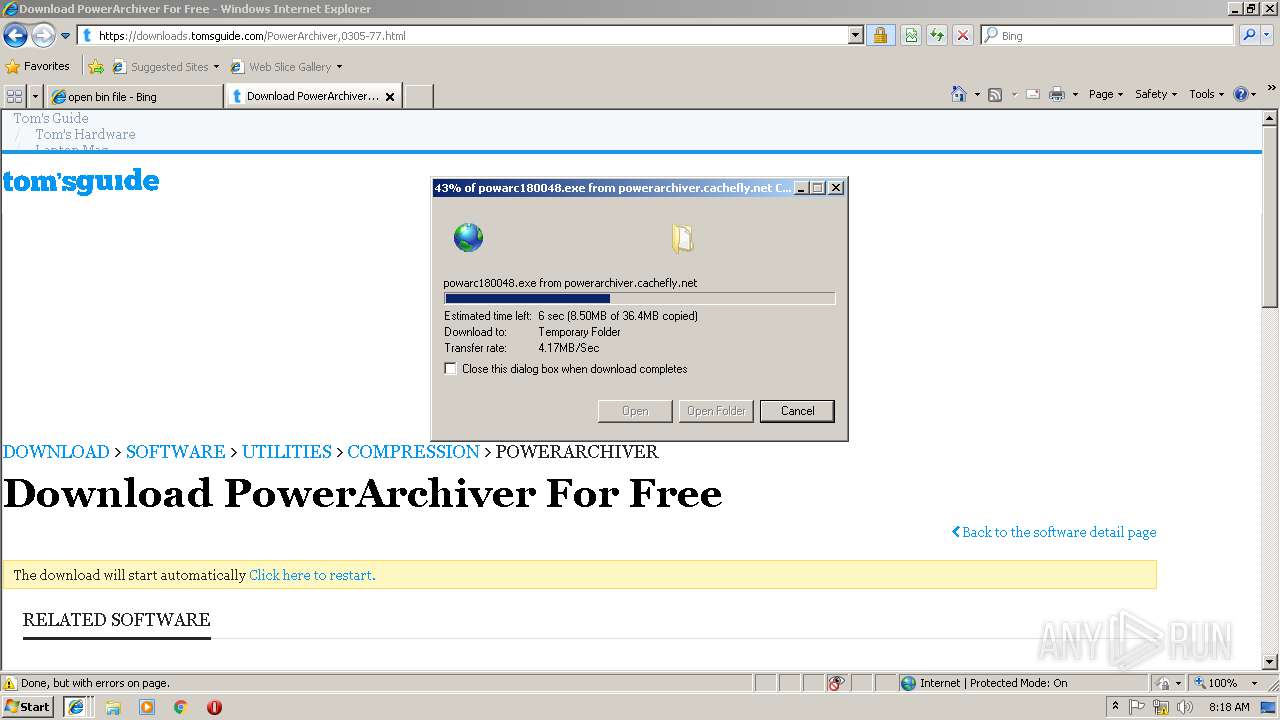
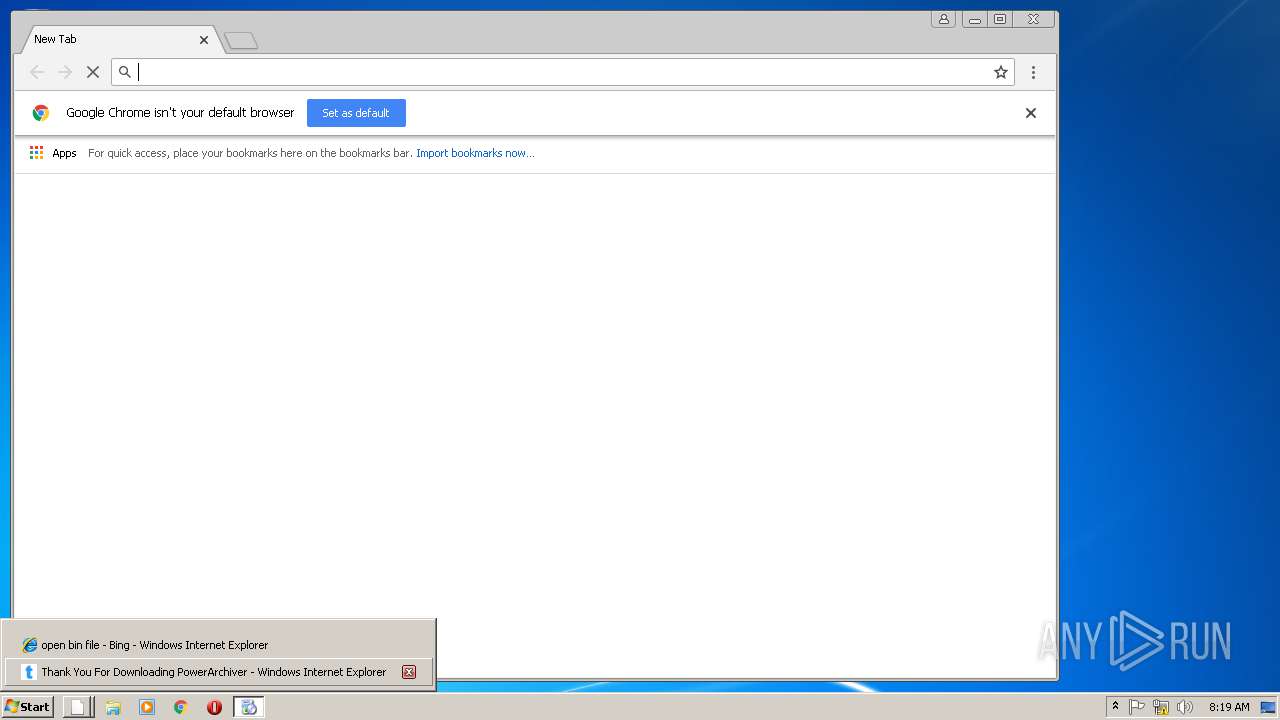
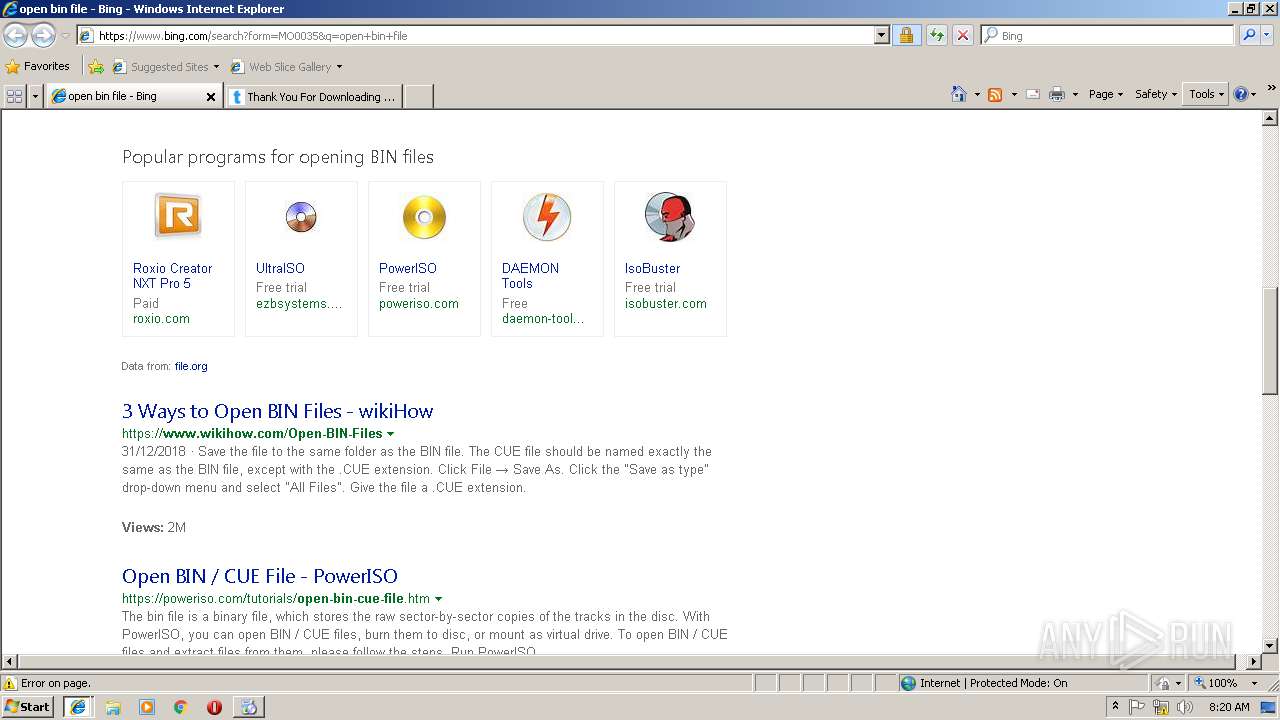
Starts Internet Explorer
- rundll32.exe (PID: 3520)
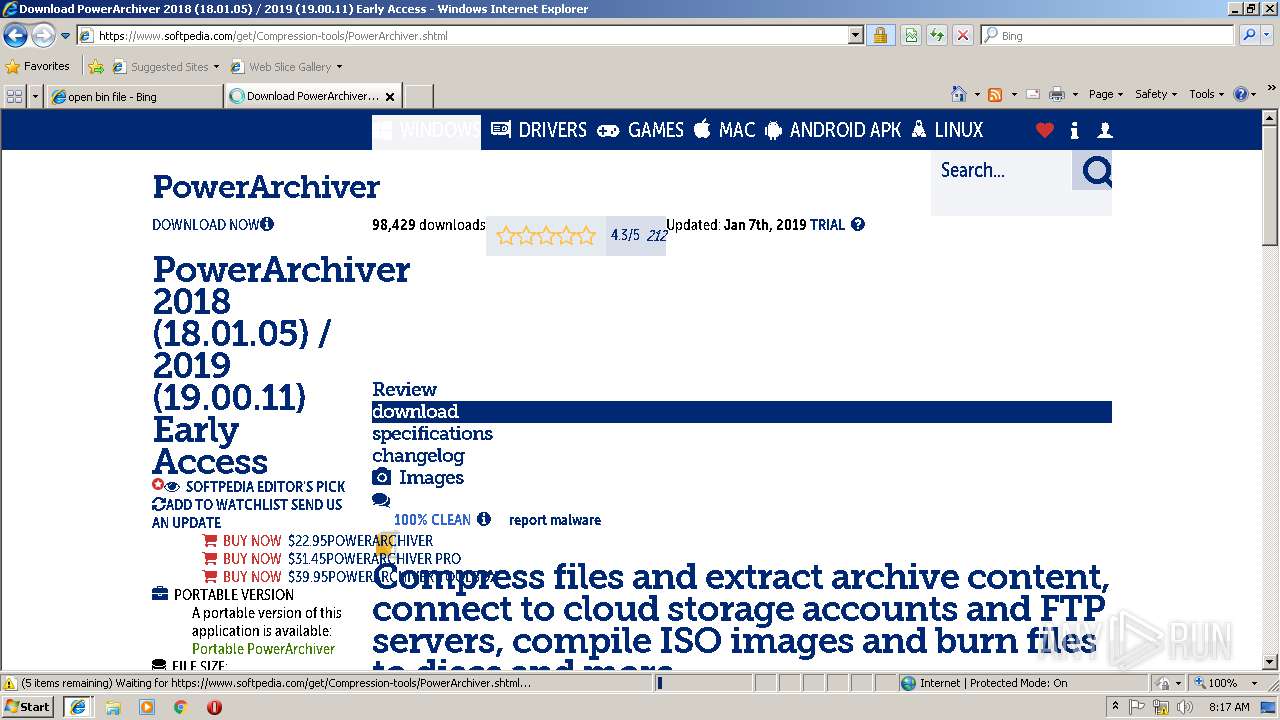
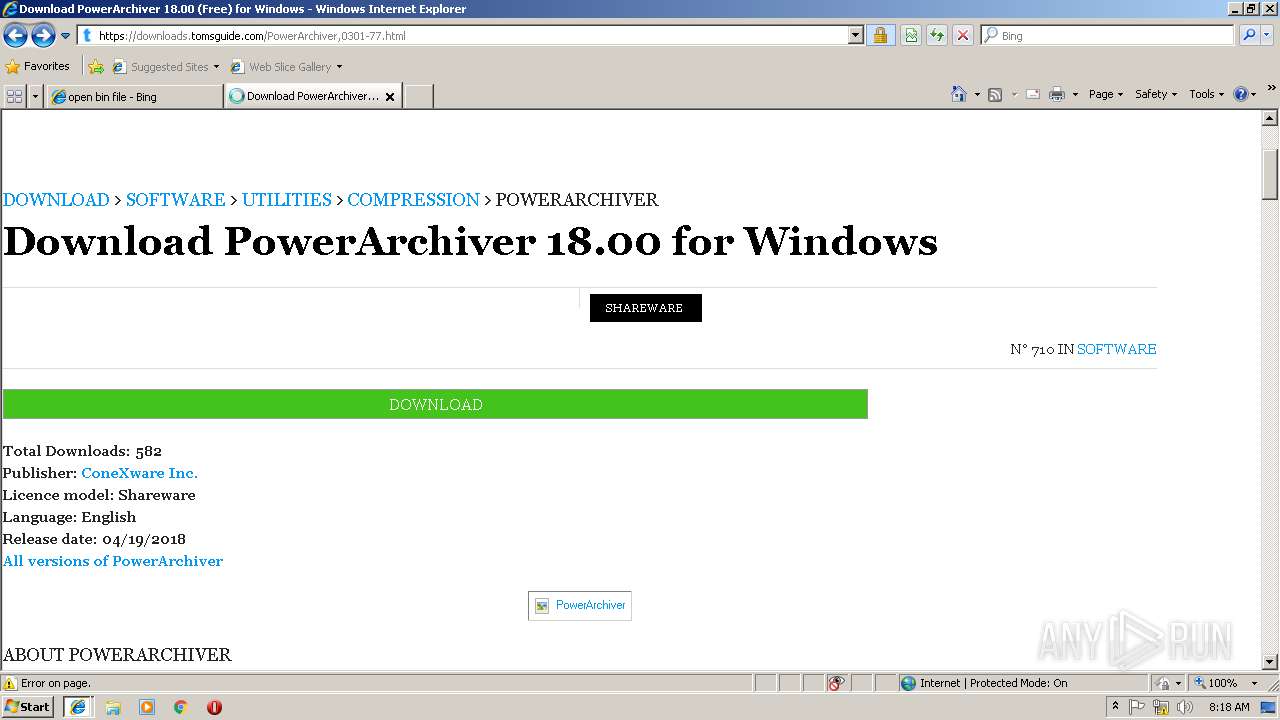
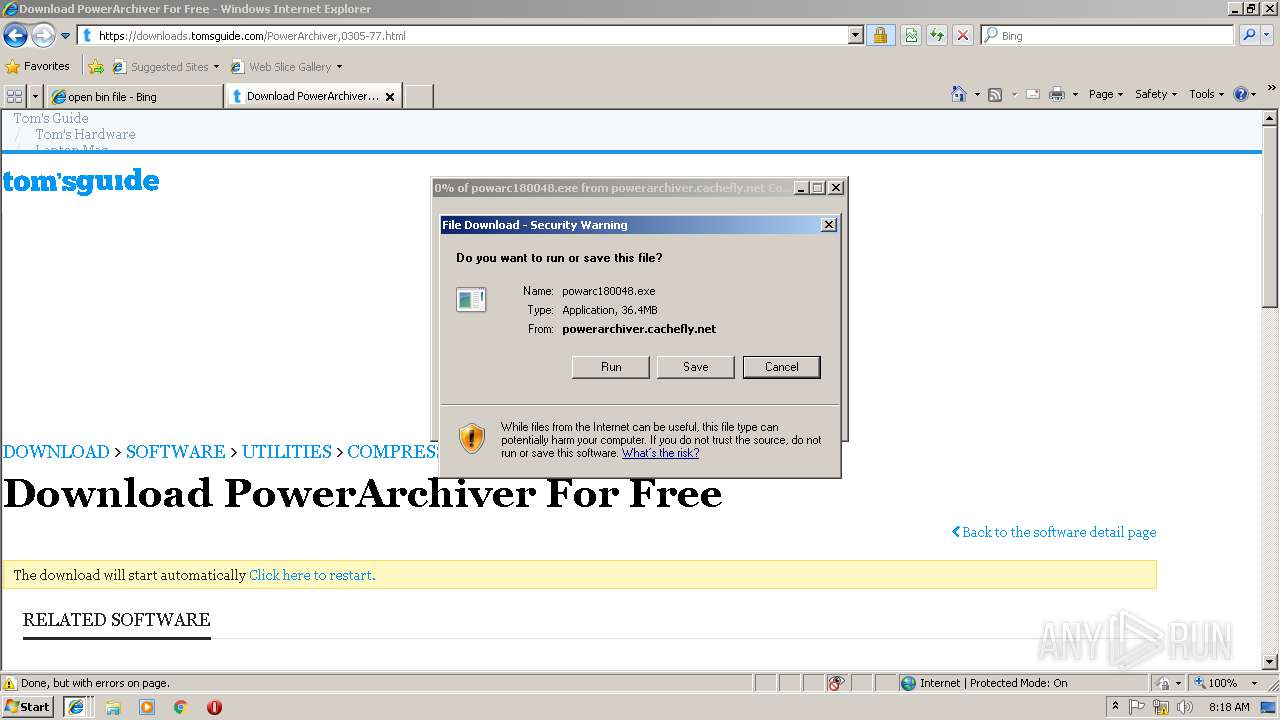
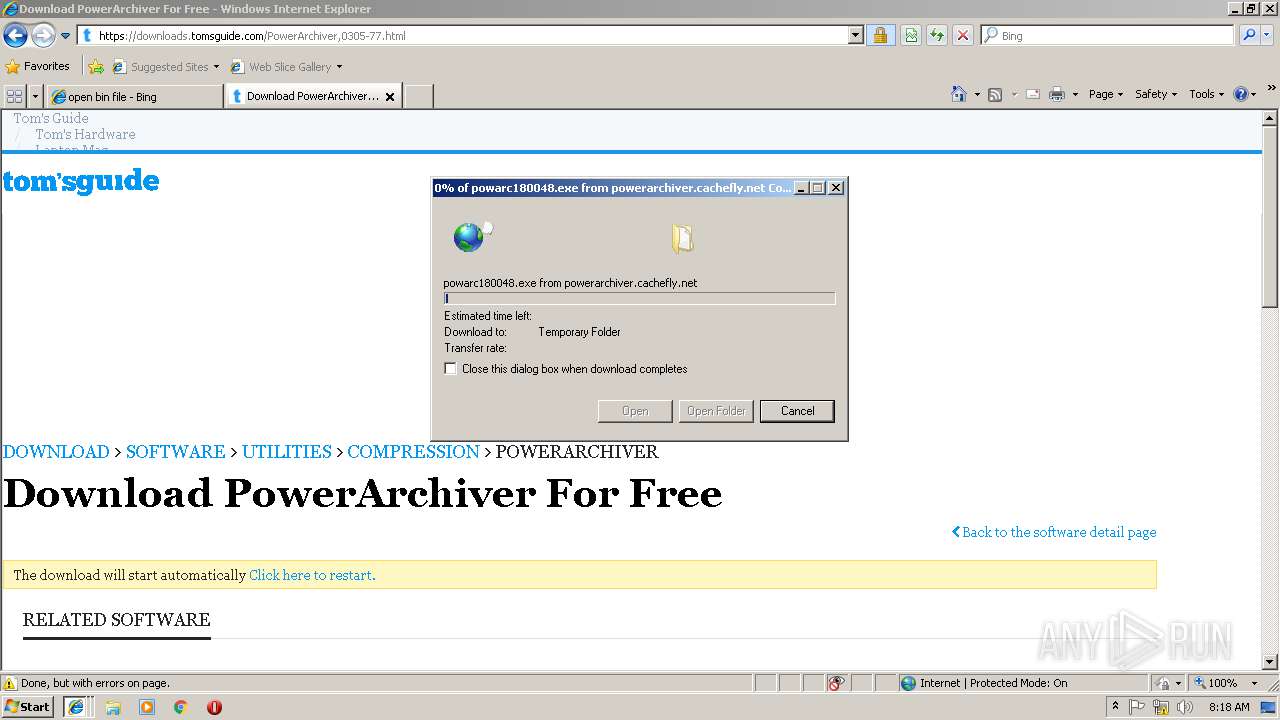
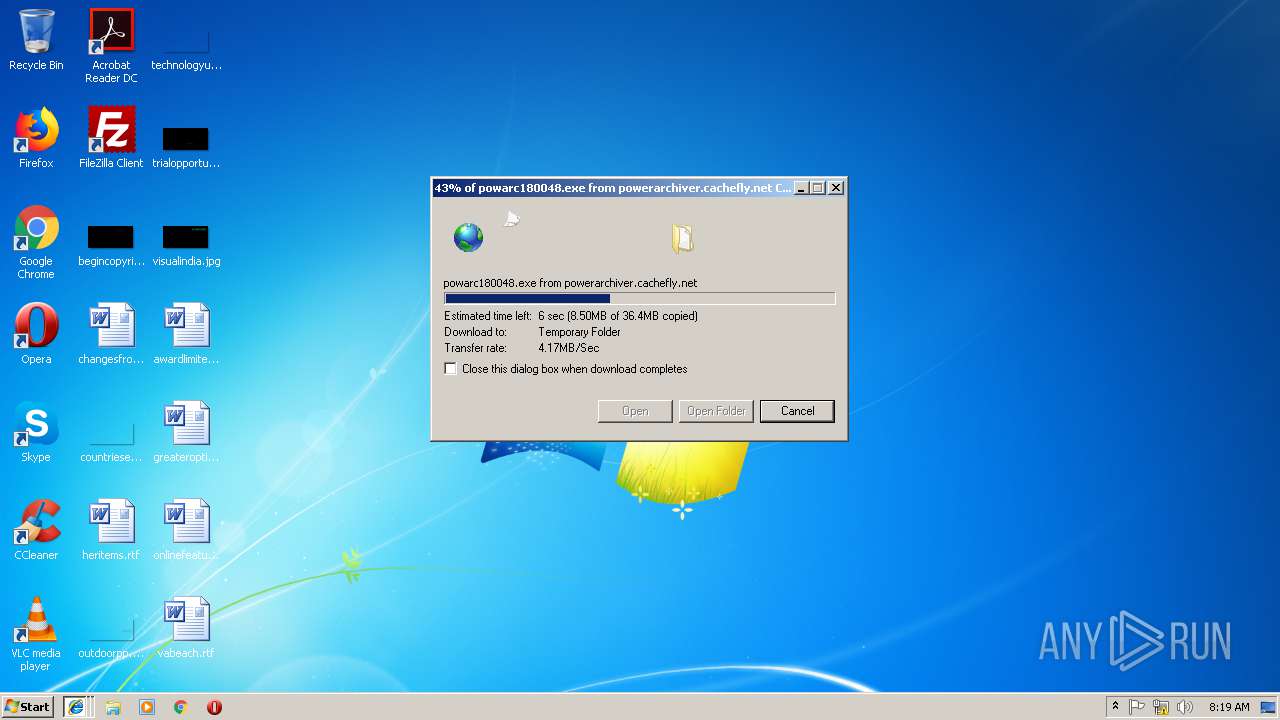
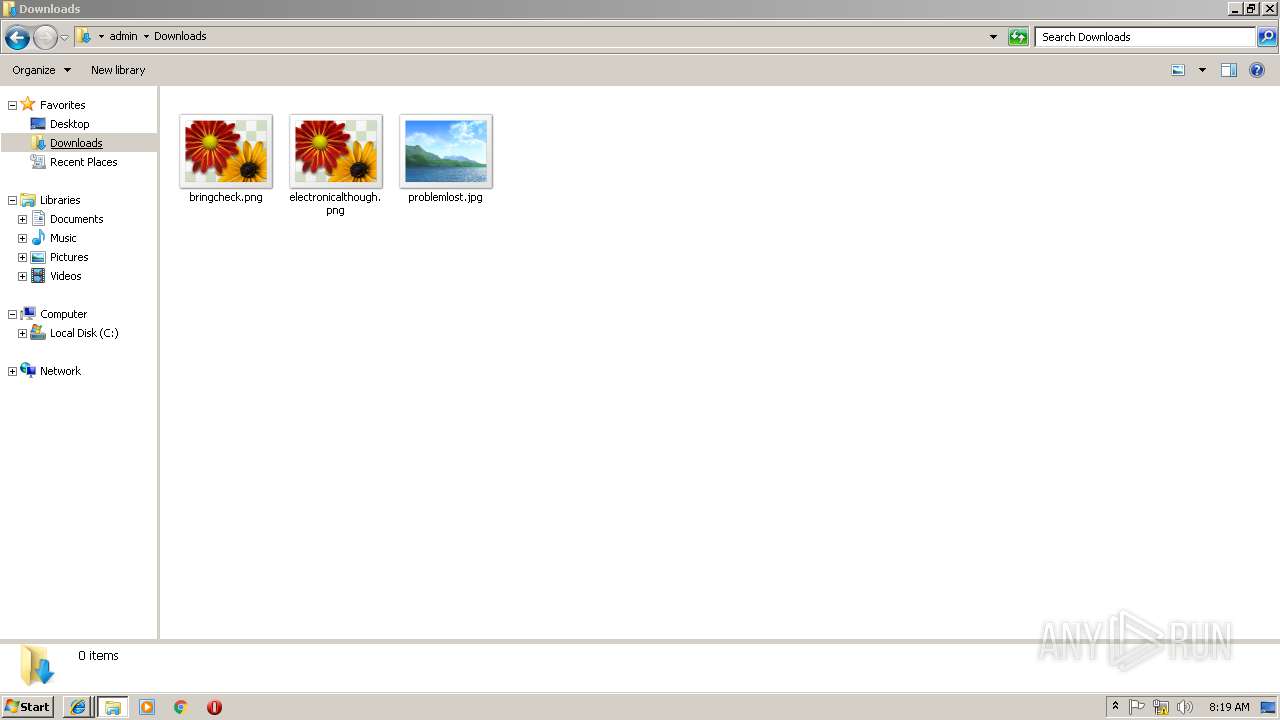
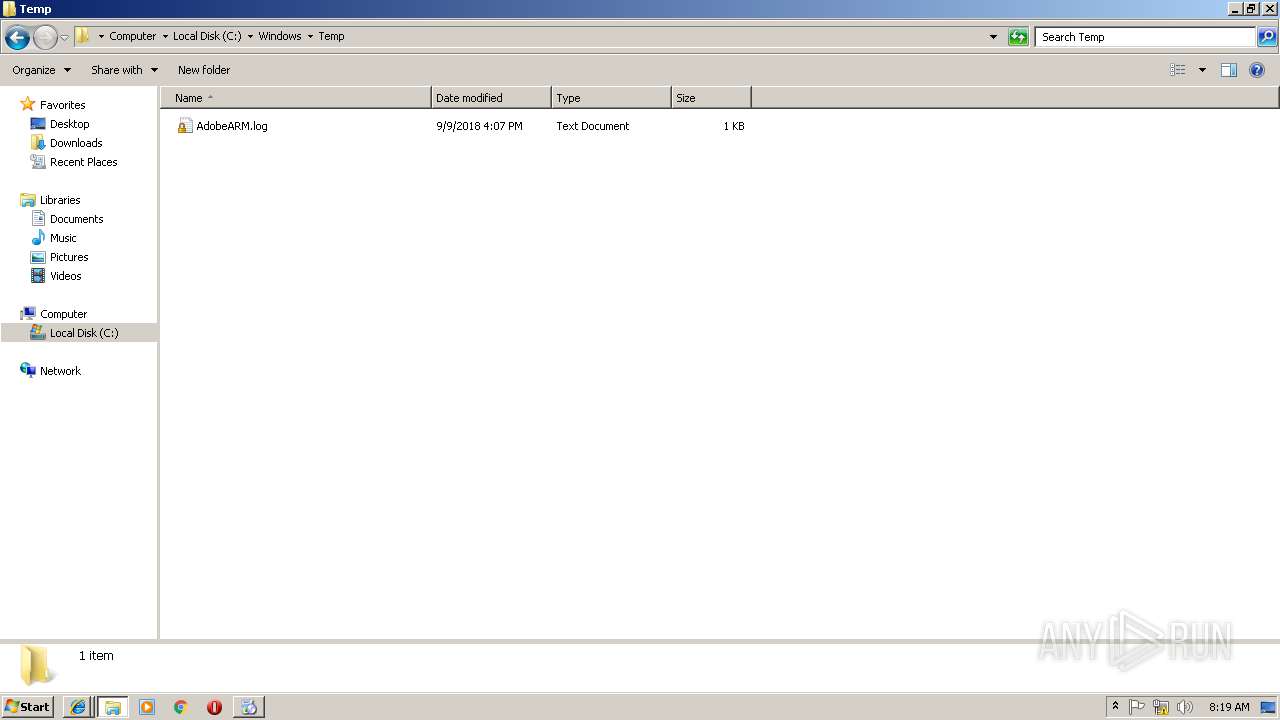
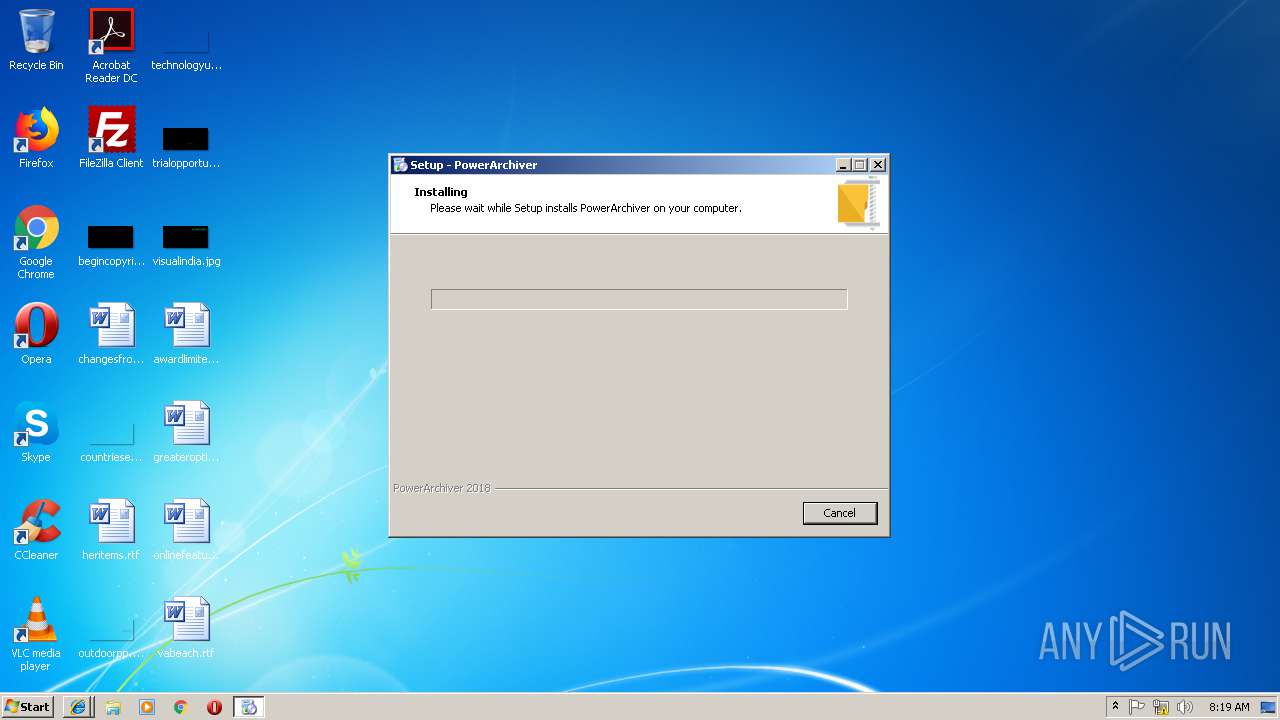
Executable content was dropped or overwritten
- powarc180048[1].exe (PID: 2520)
- powarc180048[1].exe (PID: 3968)
- powarc180048[1].tmp (PID: 2684)
Reads Windows owner or organization settings
- powarc180048[1].tmp (PID: 2684)
Reads the Windows organization settings
- powarc180048[1].tmp (PID: 2684)
Searches for installed software
- powarc180048[1].tmp (PID: 2684)
Creates files in the user directory
- powarc180048[1].tmp (PID: 2684)
Modifies the open verb of a shell class
- _pautil.exe (PID: 2424)
- _pautil.exe (PID: 3140)
Creates COM task schedule object
- regsvr32.exe (PID: 992)
- _pautil.exe (PID: 2424)
- regsvr32.exe (PID: 2796)
- _pautil.exe (PID: 3140)
- regsvr32.exe (PID: 1872)
- regsvr32.exe (PID: 3260)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3912)
- iexplore.exe (PID: 2452)
- iexplore.exe (PID: 3536)
- iexplore.exe (PID: 2764)
Reads internet explorer settings
- iexplore.exe (PID: 3912)
- iexplore.exe (PID: 2452)
- iexplore.exe (PID: 3536)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3580)
Application launched itself
- iexplore.exe (PID: 3580)
- chrome.exe (PID: 3752)
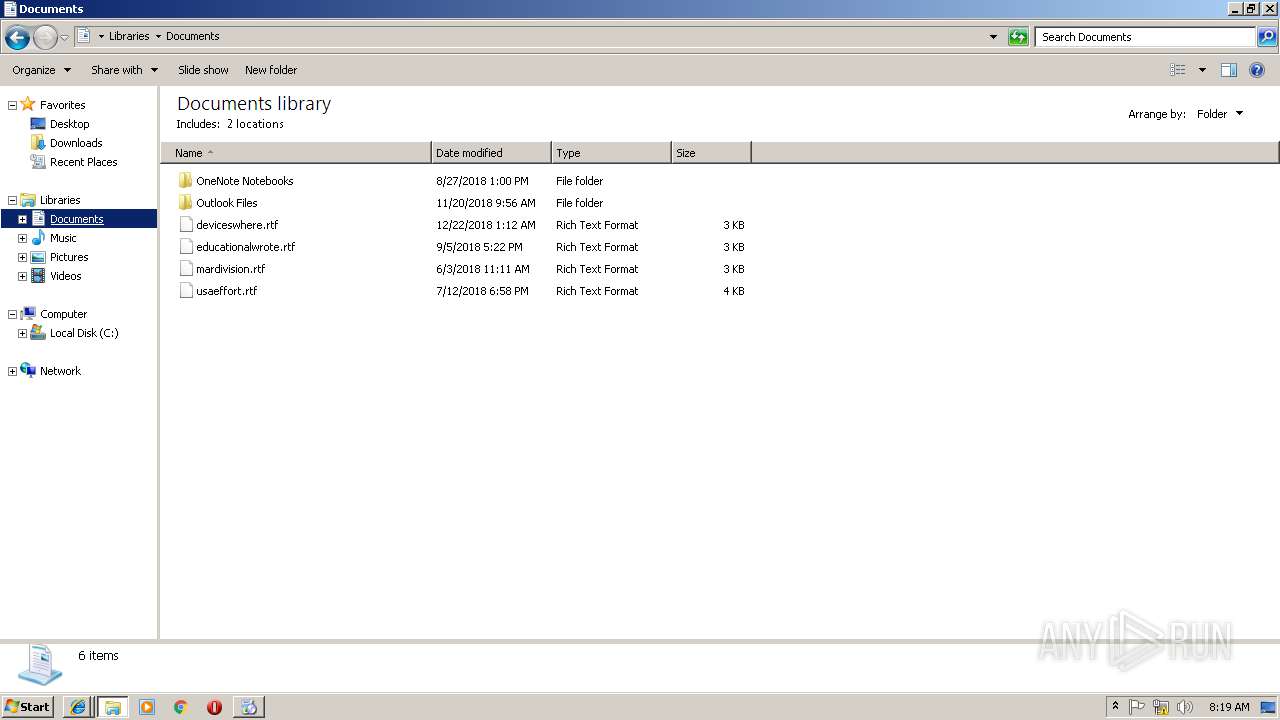
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2452)
Changes internet zones settings
- iexplore.exe (PID: 3580)
Creates files in the user directory
- iexplore.exe (PID: 3912)
- iexplore.exe (PID: 2452)
- iexplore.exe (PID: 3580)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3364)
Reads settings of System Certificates
- iexplore.exe (PID: 3580)
- iexplore.exe (PID: 2452)
- chrome.exe (PID: 3752)
Application was dropped or rewritten from another process
- powarc180048[1].tmp (PID: 1812)
- powarc180048[1].tmp (PID: 2684)
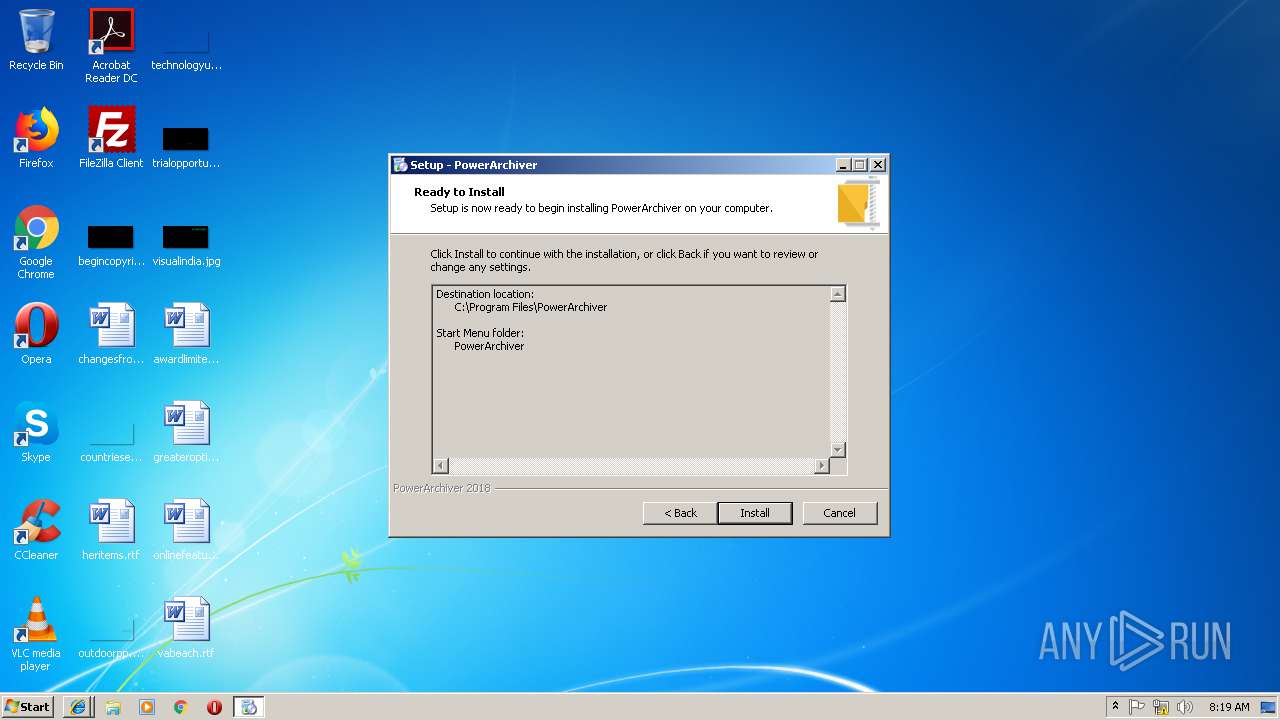
Creates a software uninstall entry
- powarc180048[1].tmp (PID: 2684)
Changes settings of System certificates
- iexplore.exe (PID: 3580)
Creates files in the program directory
- powarc180048[1].tmp (PID: 2684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
29
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
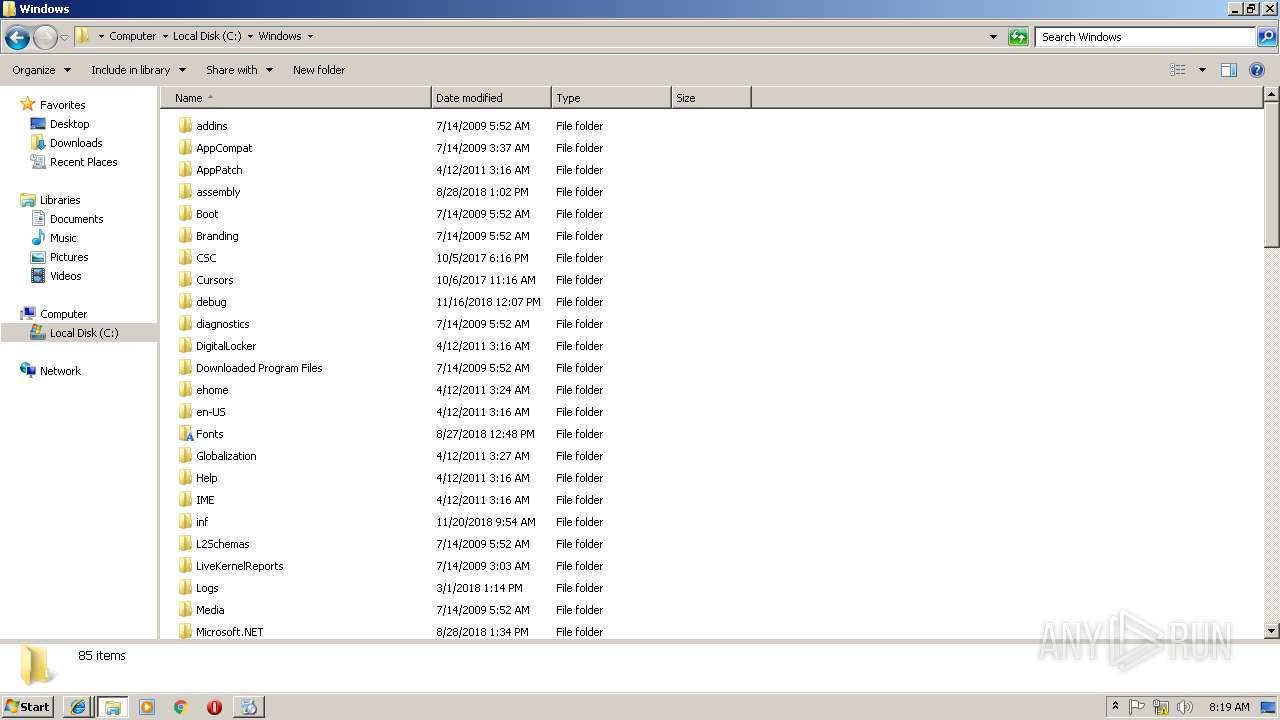
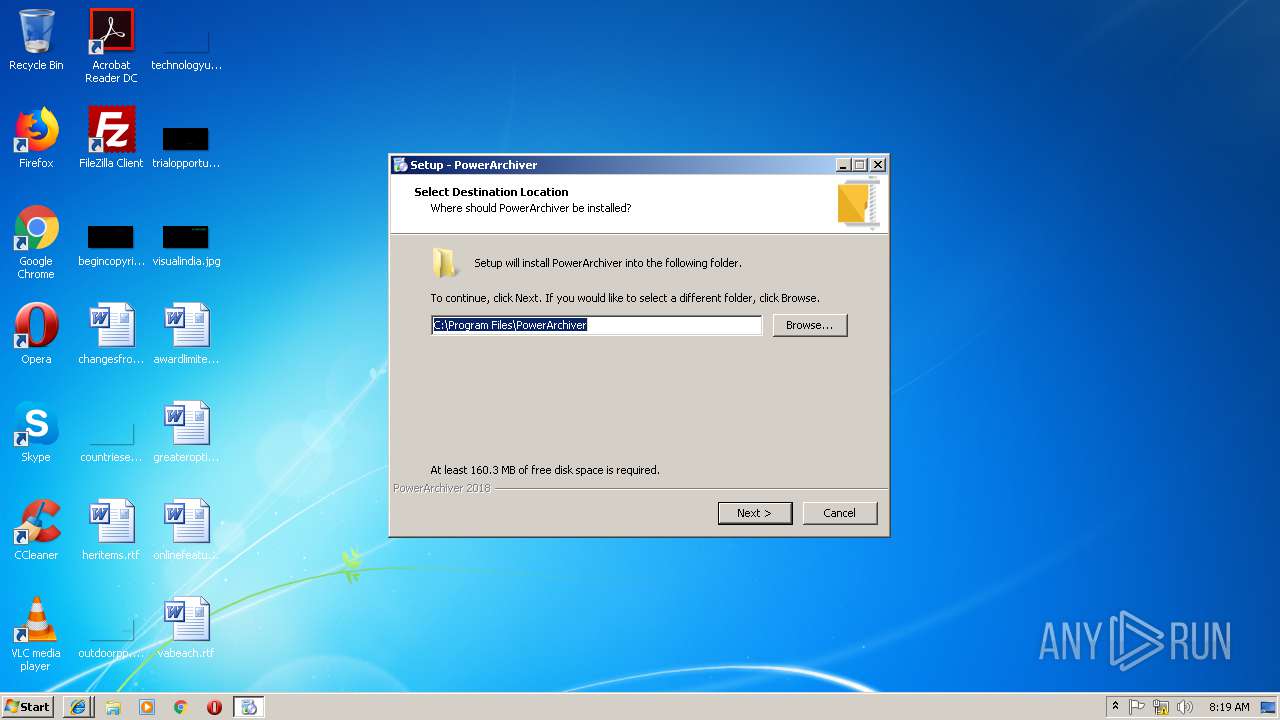
| 992 | "C:\Windows\system32\regsvr32.exe" "C:\Program Files\PowerArchiver\wodFtpDLX.dll" /S | C:\Windows\system32\regsvr32.exe | — | powarc180048[1].tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,11651557070697535174,1030721834550107494,131072 --enable-features=PasswordImport --service-pipe-token=B15A96D8452C43705C93BA95803280E0 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B15A96D8452C43705C93BA95803280E0 --renderer-client-id=3 --mojo-platform-channel-handle=2100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1812 | "C:\Users\admin\AppData\Local\Temp\is-Q38SA.tmp\powarc180048[1].tmp" /SL5="$402AC,37700562,141824,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\powarc180048[1].exe" | C:\Users\admin\AppData\Local\Temp\is-Q38SA.tmp\powarc180048[1].tmp | — | powarc180048[1].exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1872 | "C:\Windows\system32\regsvr32.exe" "C:\Program Files\PowerArchiver\wodCertificate.dll" /S | C:\Windows\system32\regsvr32.exe | — | powarc180048[1].tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2076 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2424 | "C:\Program Files\PowerArchiver\_pautil.exe" ML | C:\Program Files\PowerArchiver\_pautil.exe | — | powarc180048[1].tmp | |||||||||||
User: admin Company: ConeXware, Inc. Integrity Level: HIGH Exit code: 0 Version: 1.0.1.0 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3580 CREDAT:6404 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6ab900b0,0x6ab900c0,0x6ab900cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2520 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\powarc180048[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\powarc180048[1].exe | iexplore.exe | ||||||||||||
User: admin Company: ConeXware, Inc. Integrity Level: MEDIUM Description: PowerArchiver Setup Exit code: 0 Version: 18.00.53 Modules
| |||||||||||||||
| 2684 | "C:\Users\admin\AppData\Local\Temp\is-0EVQ7.tmp\powarc180048[1].tmp" /SL5="$3025E,37700562,141824,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\powarc180048[1].exe" /SPAWNWND=$3022A /NOTIFYWND=$402AC | C:\Users\admin\AppData\Local\Temp\is-0EVQ7.tmp\powarc180048[1].tmp | powarc180048[1].exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
6 367
Read events
2 527
Write events
3 473
Delete events
367
Modification events
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {E9D9685B-1E1D-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30701000200160008000F002D00C300 | |||
Executable files
145
Suspicious files
134
Text files
498
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3580 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3912 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[2].txt | — | |
MD5:— | SHA256:— | |||
| 3912 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\search[1].txt | — | |
MD5:— | SHA256:— | |||
| 3912 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[1].txt | text | |
MD5:— | SHA256:— | |||
| 3912 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@www.bing[1].txt | text | |
MD5:— | SHA256:— | |||
| 3580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 3912 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012019012220190123\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[3].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 3912 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\search[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
85
TCP/UDP connections
209
DNS requests
70
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
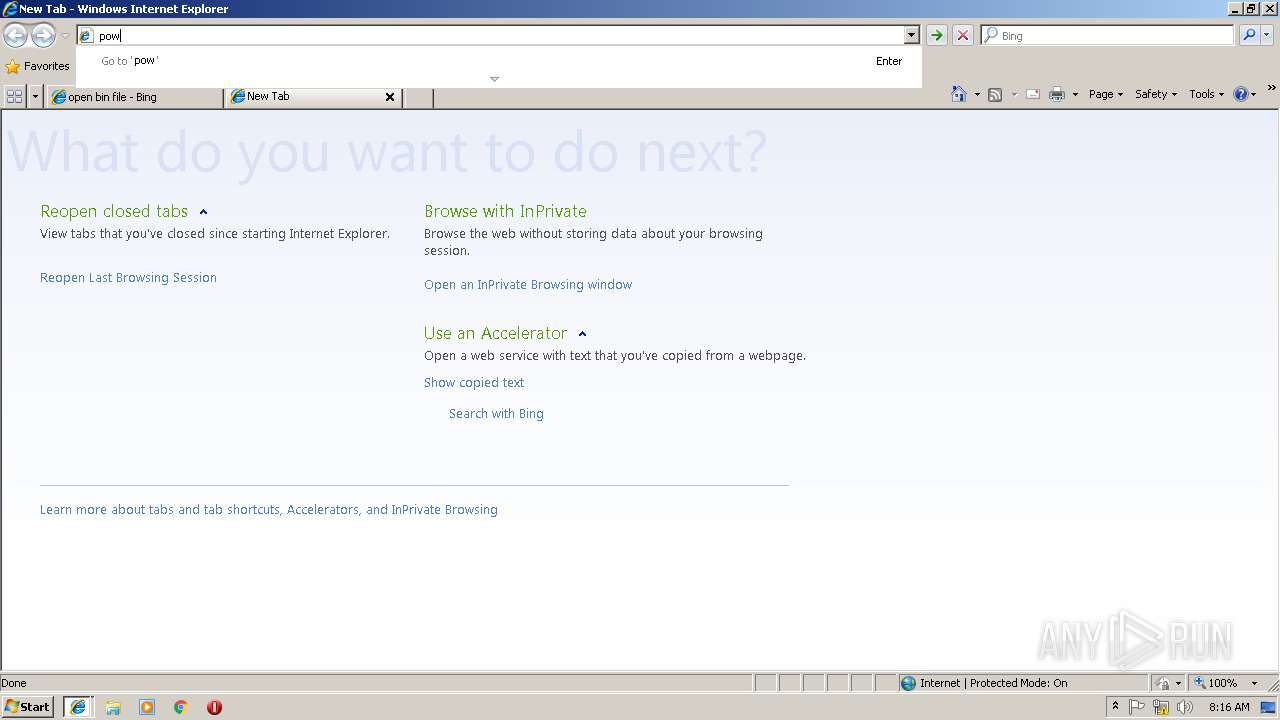
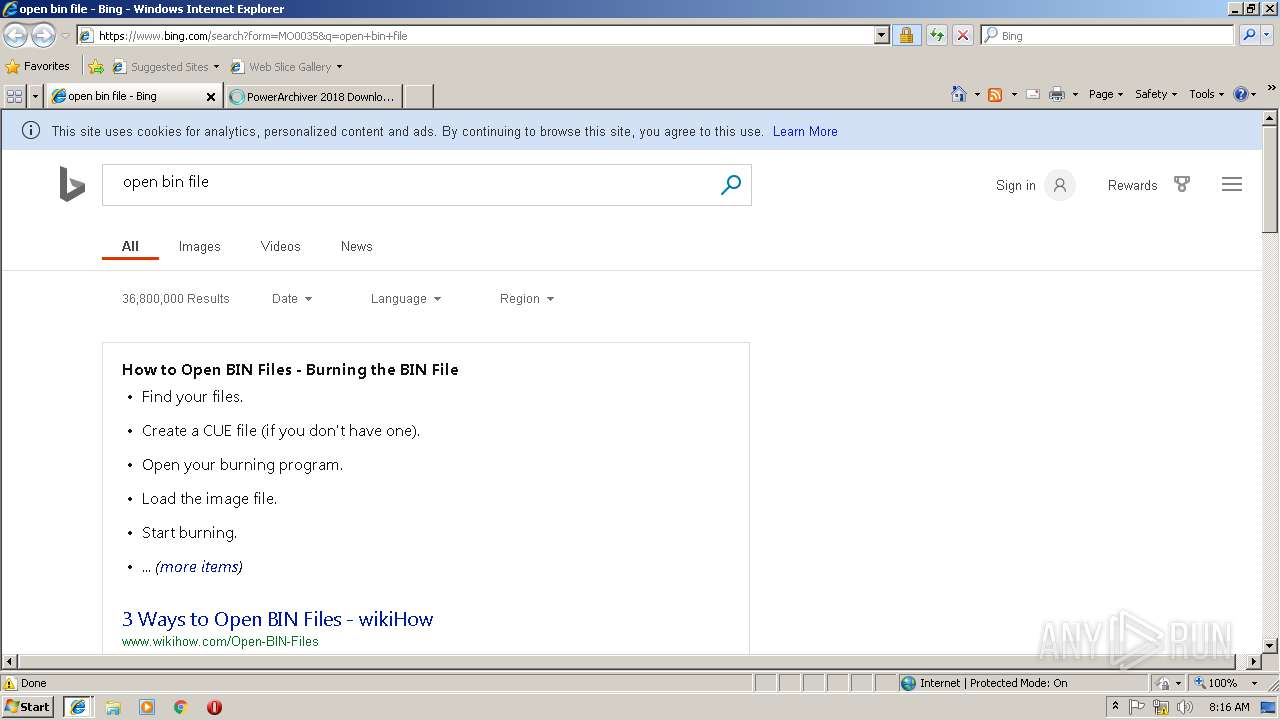
3912 | iexplore.exe | GET | 302 | 23.51.118.23:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=bin | NL | — | — | whitelisted |
3912 | iexplore.exe | GET | 301 | 2.16.186.24:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=bin | unknown | — | — | whitelisted |
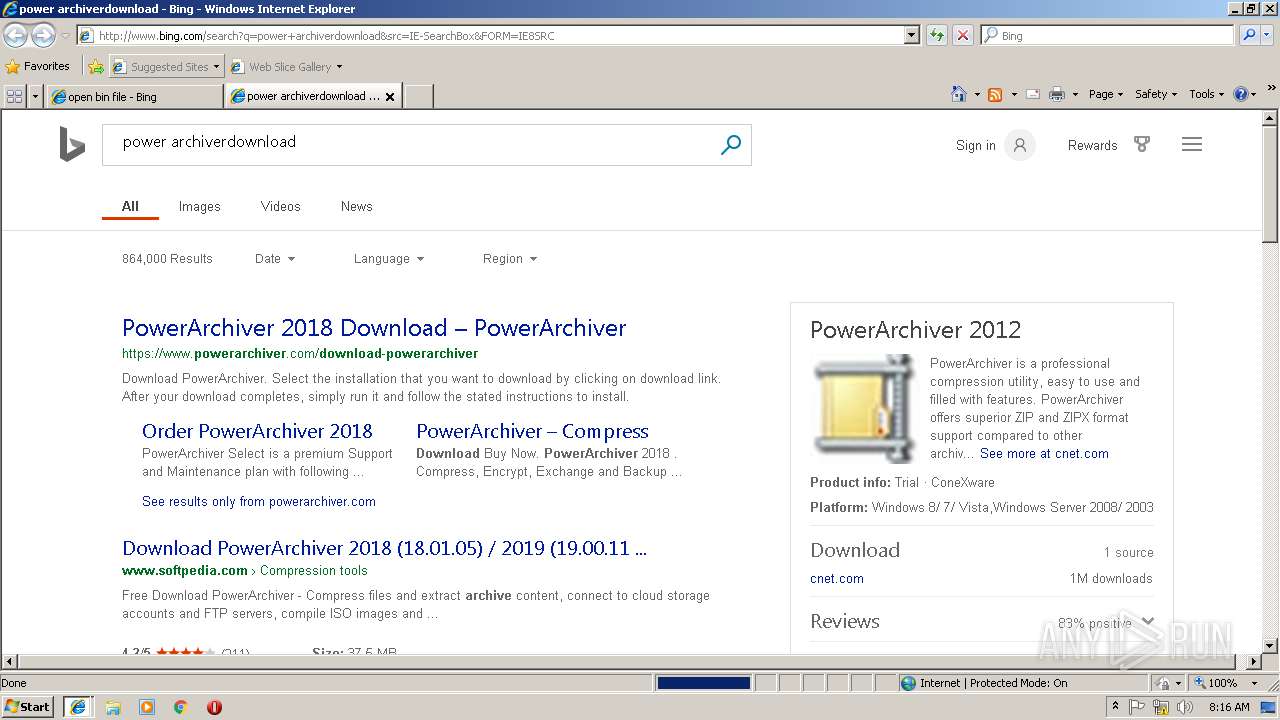
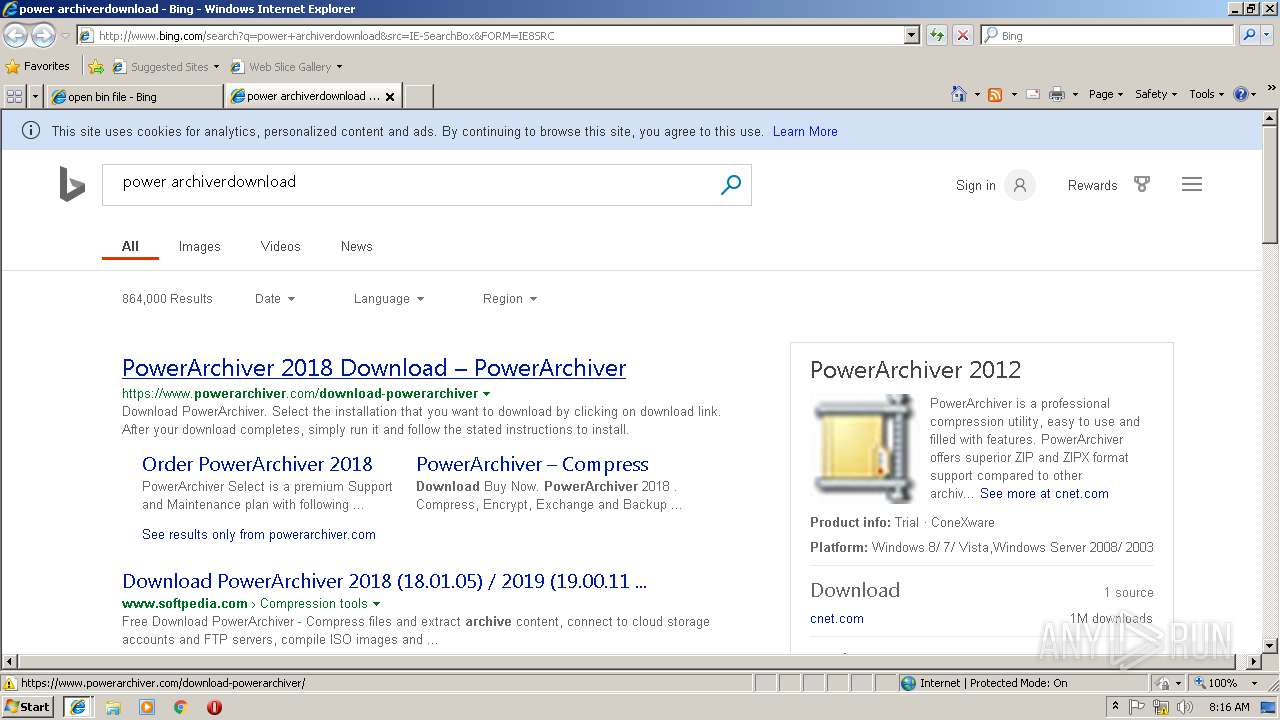
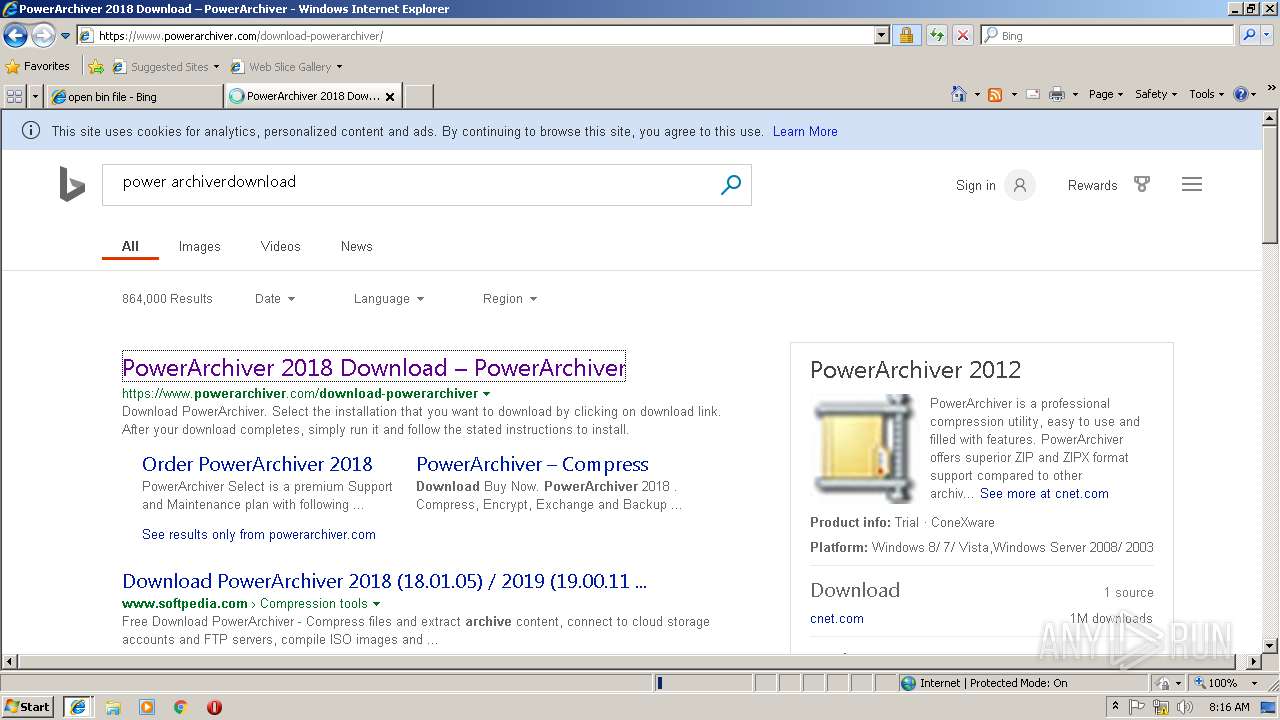
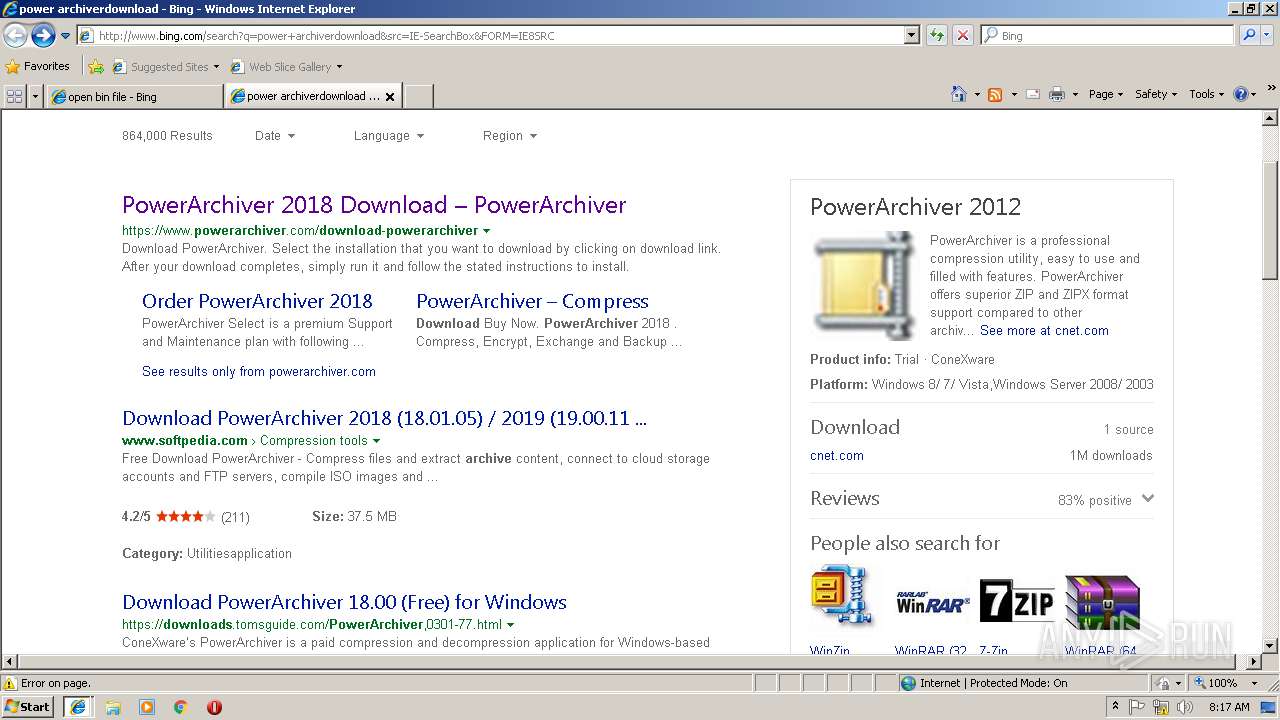
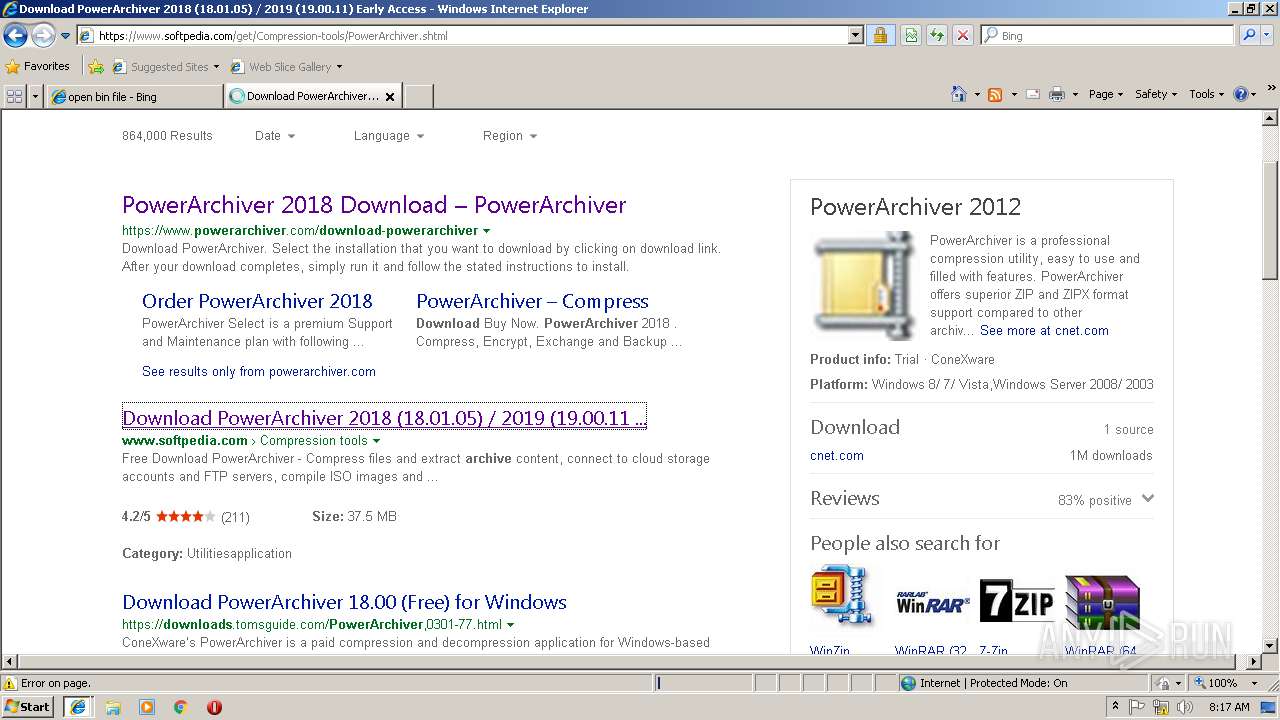
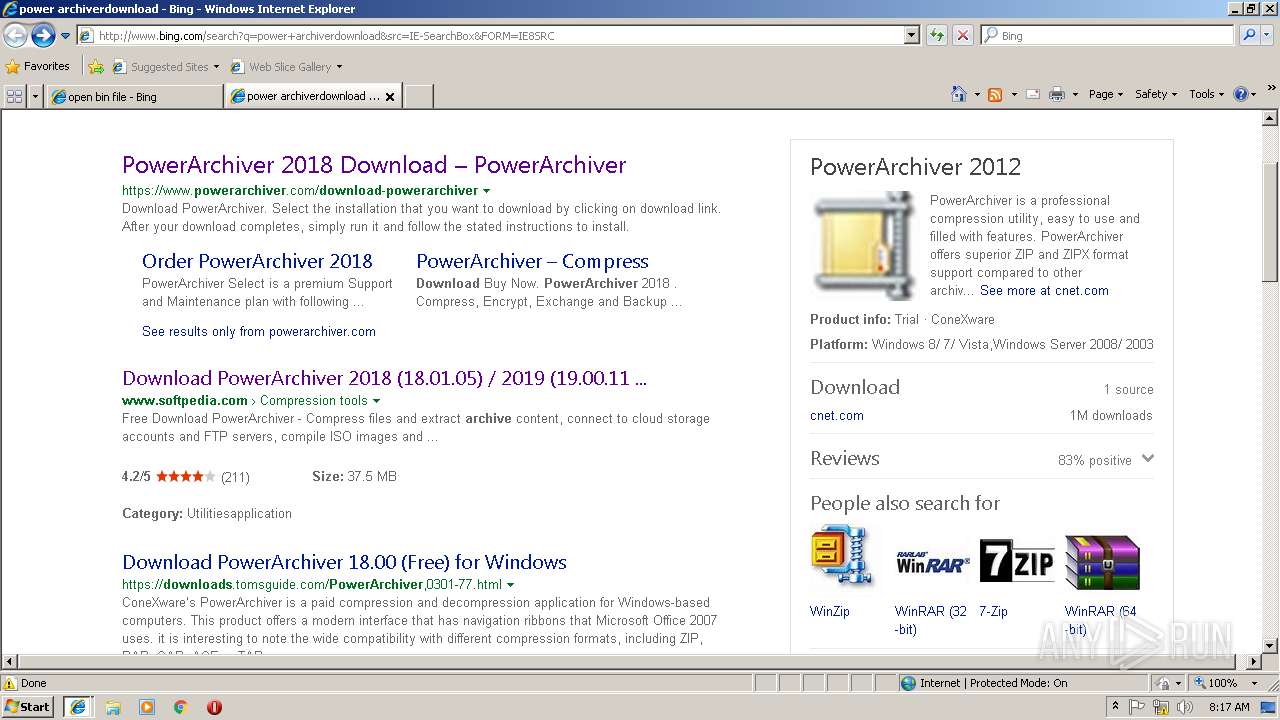
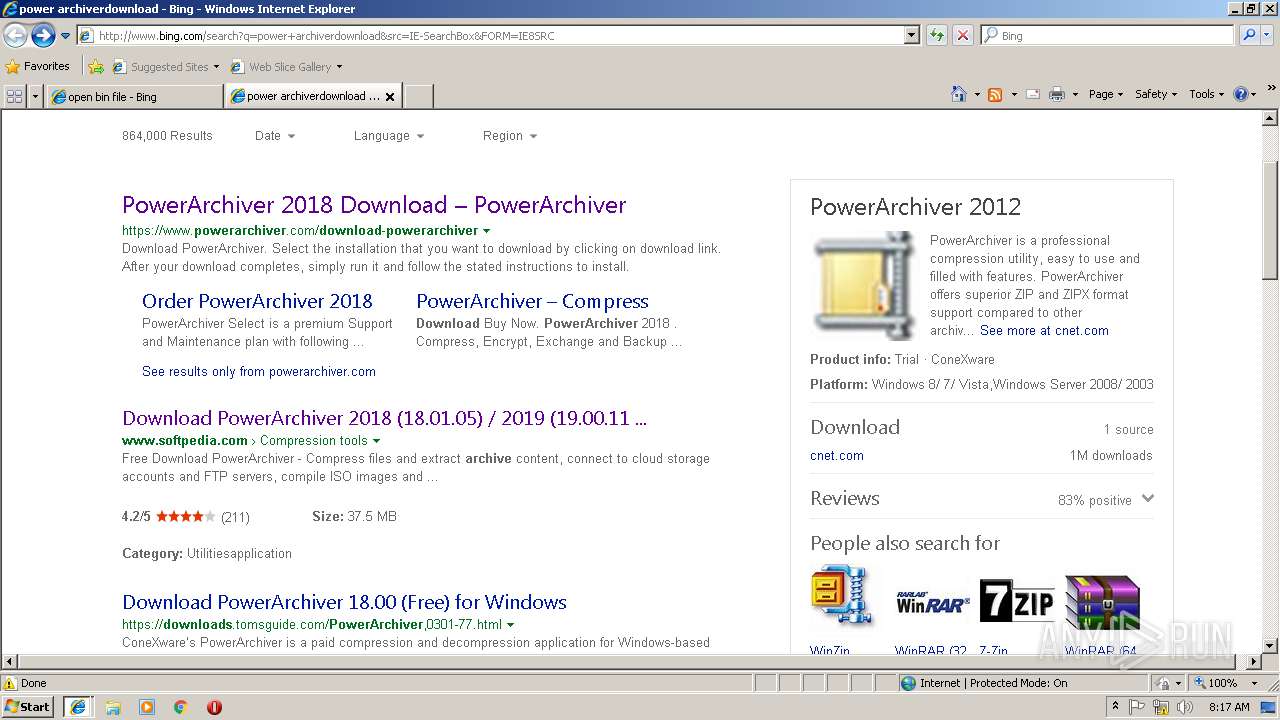
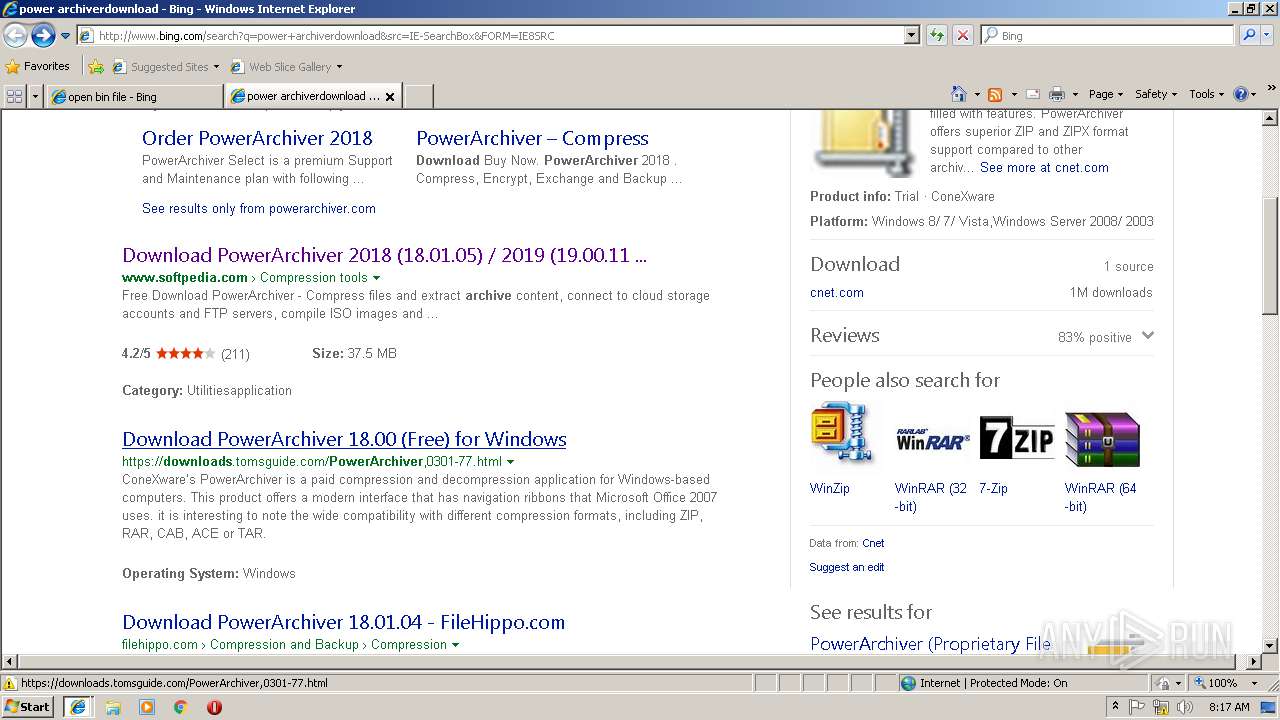
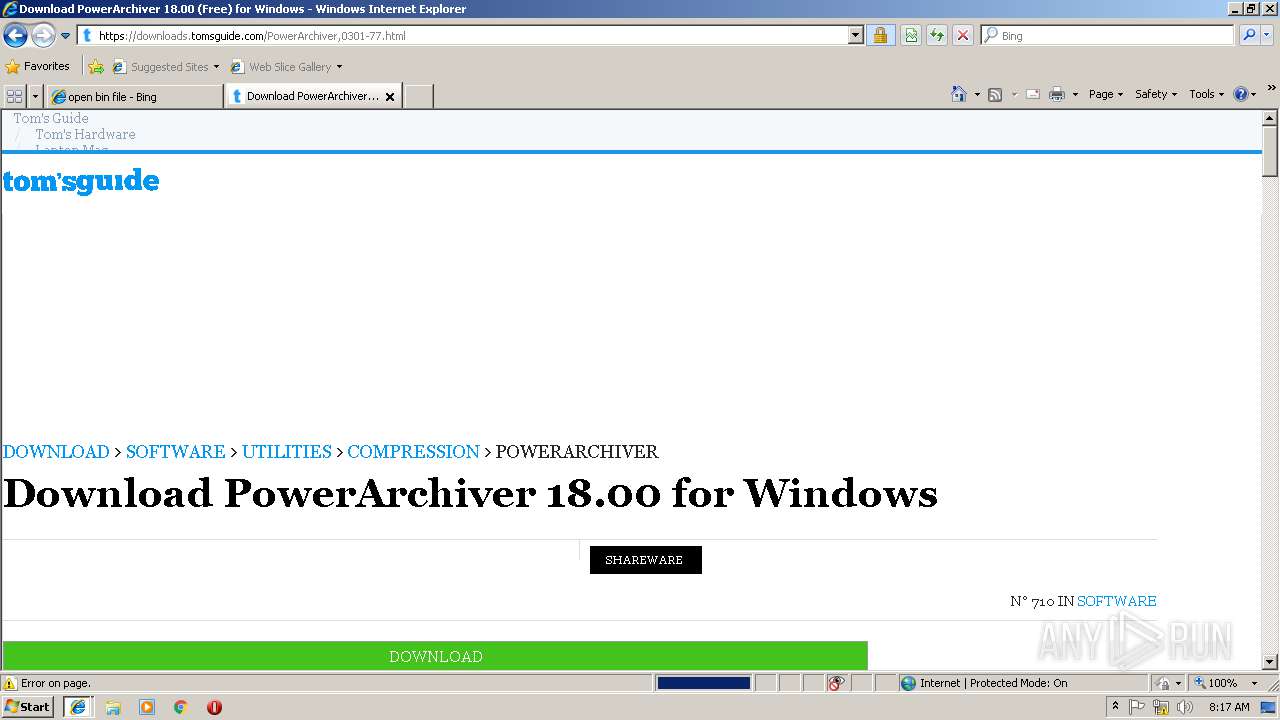
2452 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/search?q=power+archiverdownload&src=IE-SearchBox&FORM=IE8SRC | US | html | 44.7 Kb | whitelisted |
2452 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/th?id=AMMS_7df40aaee3c3c63afbdf73066ede51d9&w=75&h=75&c=7&rs=1&qlt=80&cdv=1&pid=16.1 | US | image | 1.67 Kb | whitelisted |
2452 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2Y/1H/cj,nj/5983aa50/f8c6dd44.js | US | text | 773 b | whitelisted |
2452 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2Y/1X/cj,nj/4c7364c5/40e1b425.js | US | text | 816 b | whitelisted |
2452 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=6F784E95BF8045F4AD2FD86F69C0069F&Type=Event.CPT&DATA={"pp":{"S":"L","FC":62,"BC":484,"SE":-1,"TC":-1,"H":546,"BP":578,"CT":609,"IL":3},"ad":[-1,-1,1260,560,1260,498,0]}&P=SERP&DA=DUB02 | US | image | 5.73 Kb | whitelisted |
2452 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/sa/simg/SharedSpriteDesktopRewards_022118.png | US | image | 5.73 Kb | whitelisted |
2452 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/15/cj,nj/1b7dfb88/cc8437ad.js?bu=DikuXGxwdGhgZKwBsAEuoAEu | US | text | 7.54 Kb | whitelisted |
2452 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/th?id=A06781a48a87b8faef02572bcbb2f4498&w=110&h=110&c=7&rs=1&qlt=80&pcl=f9f9f9&cdv=1&pid=16.1 | US | image | 2.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3912 | iexplore.exe | 2.16.186.24:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
3580 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3912 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3912 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3912 | iexplore.exe | 23.51.118.23:80 | go.microsoft.com | Akamai Technologies, Inc. | NL | whitelisted |
3580 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3912 | iexplore.exe | 157.55.135.132:443 | login.live.com | Microsoft Corporation | US | whitelisted |
2452 | iexplore.exe | 13.107.18.254:80 | efd52fc3b80e9bc58af4c7026f1bc2ec.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
2452 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2452 | iexplore.exe | 13.107.6.163:80 | 51a1fa498a9959568aac8bd8ea1d04ee.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
51a1fa498a9959568aac8bd8ea1d04ee.clo.footprintdns.com |
| suspicious |
efd52fc3b80e9bc58af4c7026f1bc2ec.clo.footprintdns.com |
| suspicious |
af0e5ed1ed8d83e429cdc8bf5f4f118f.clo.footprintdns.com |
| unknown |
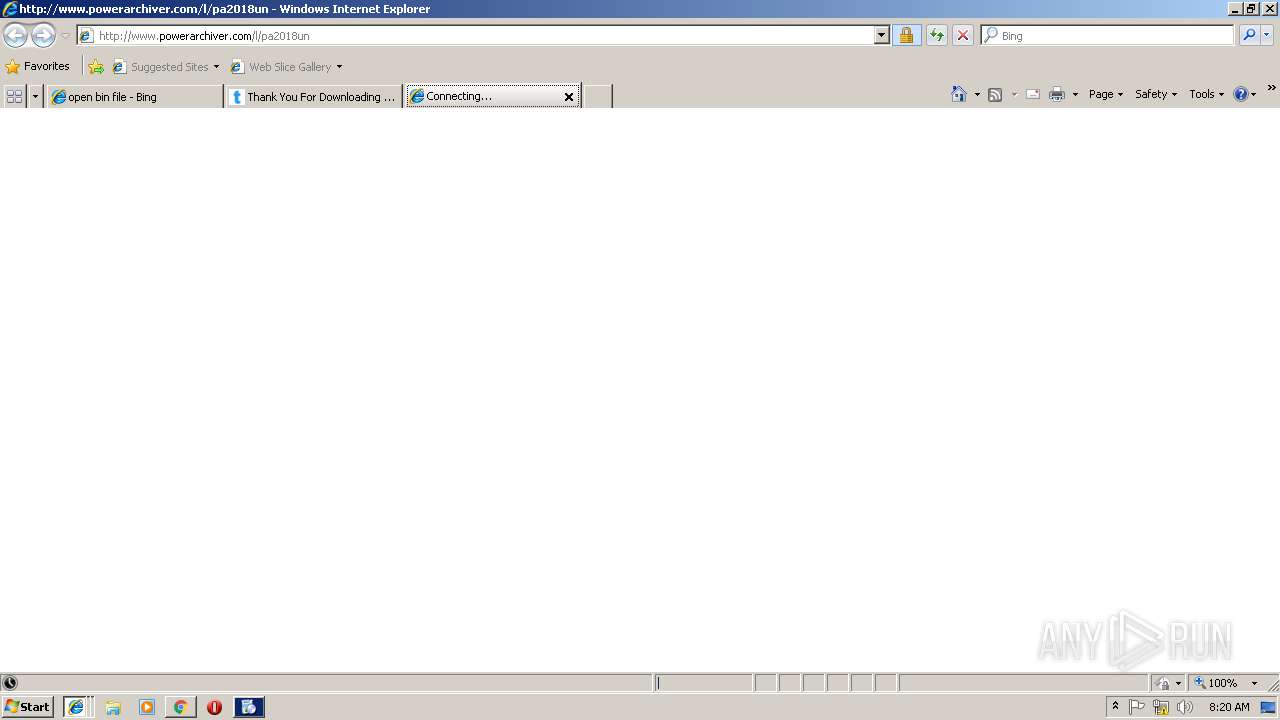
www.powerarchiver.com |
| unknown |
fp.msedge.net |
| whitelisted |
crt.comodoca.com |
| whitelisted |