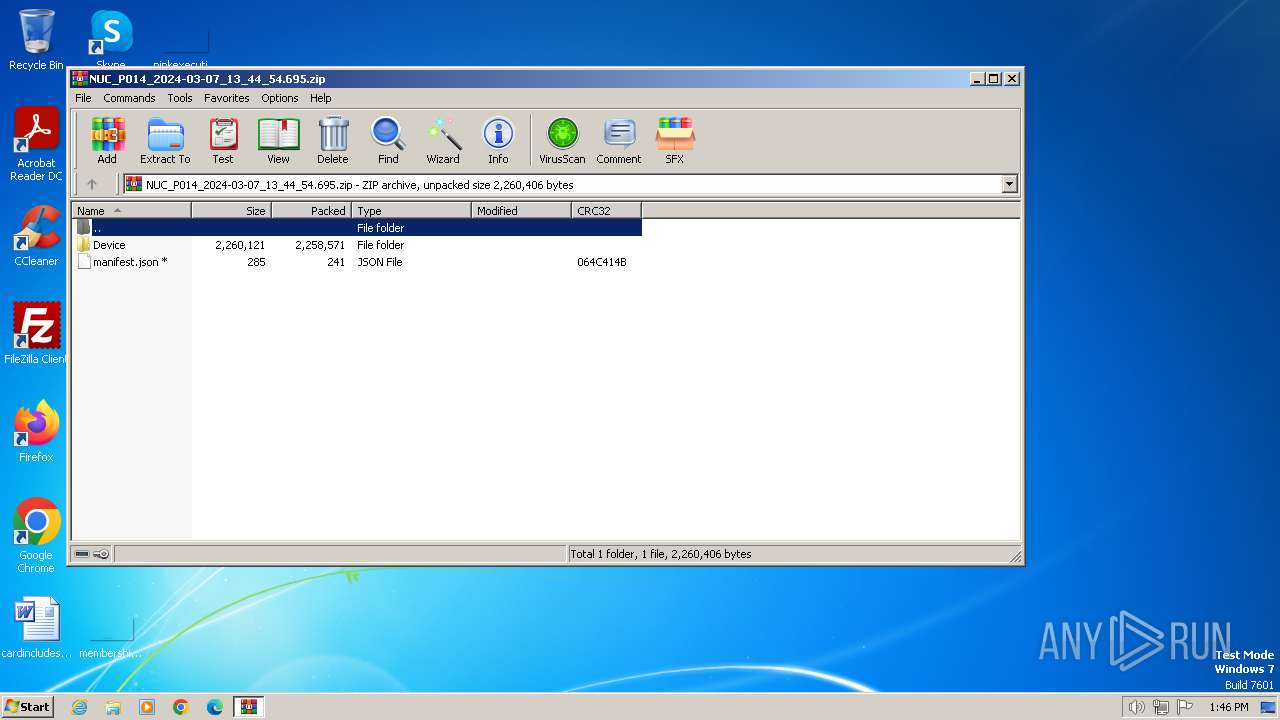
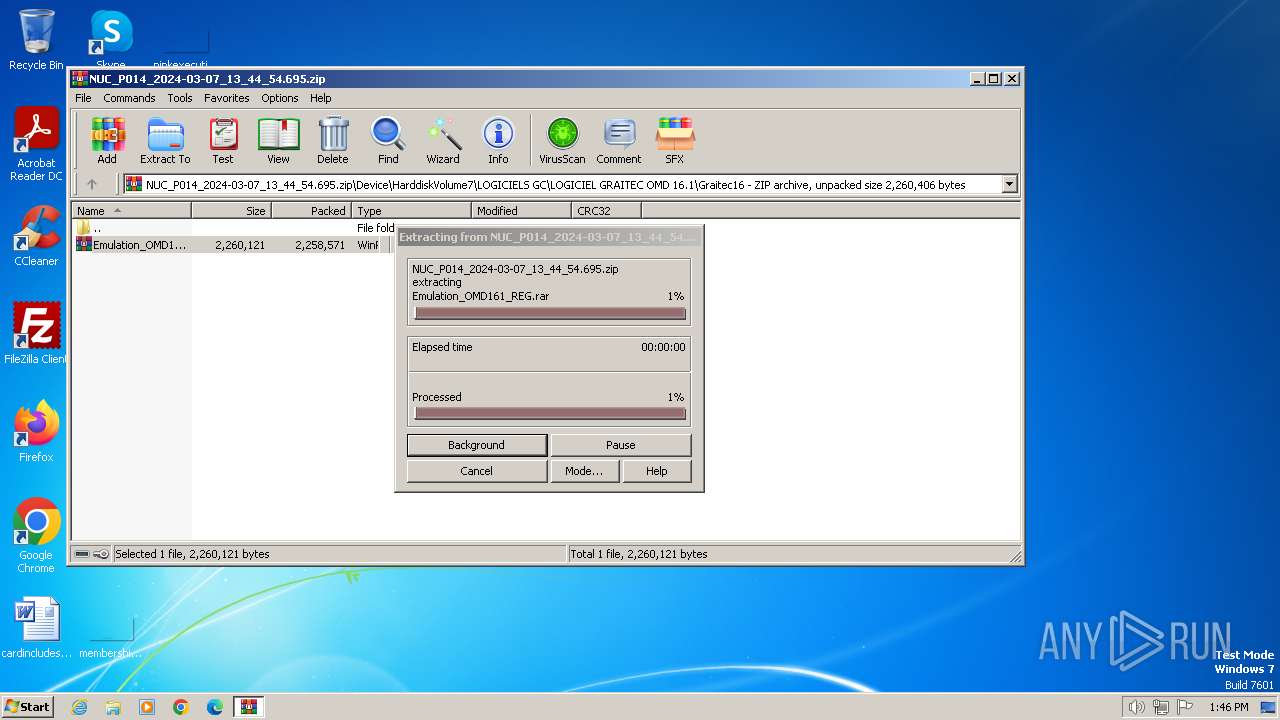
| File name: | NUC_P014_2024-03-07_13_44_54.695.zip |
| Full analysis: | https://app.any.run/tasks/c641e4b8-8ba0-4182-9ad8-3bbbda2c931c |
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2024, 13:45:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 00D9CEEA66754A94F5A46B8F6505AA93 |
| SHA1: | 3935D15C302CA336E92EDCB5F49E9351B89621C6 |
| SHA256: | 8A8B95D189ACF7C3407DF6B84745B8039652925BF75118E4873466A9E6DE9D60 |
| SSDEEP: | 98304:y9L/4/8rzuvxIs/fAPtfT/aPXyqCIjqw20J/8MmTvMqBQpOoDlWnZ2wk5f1Ogl7F:tiJfX5JAR |
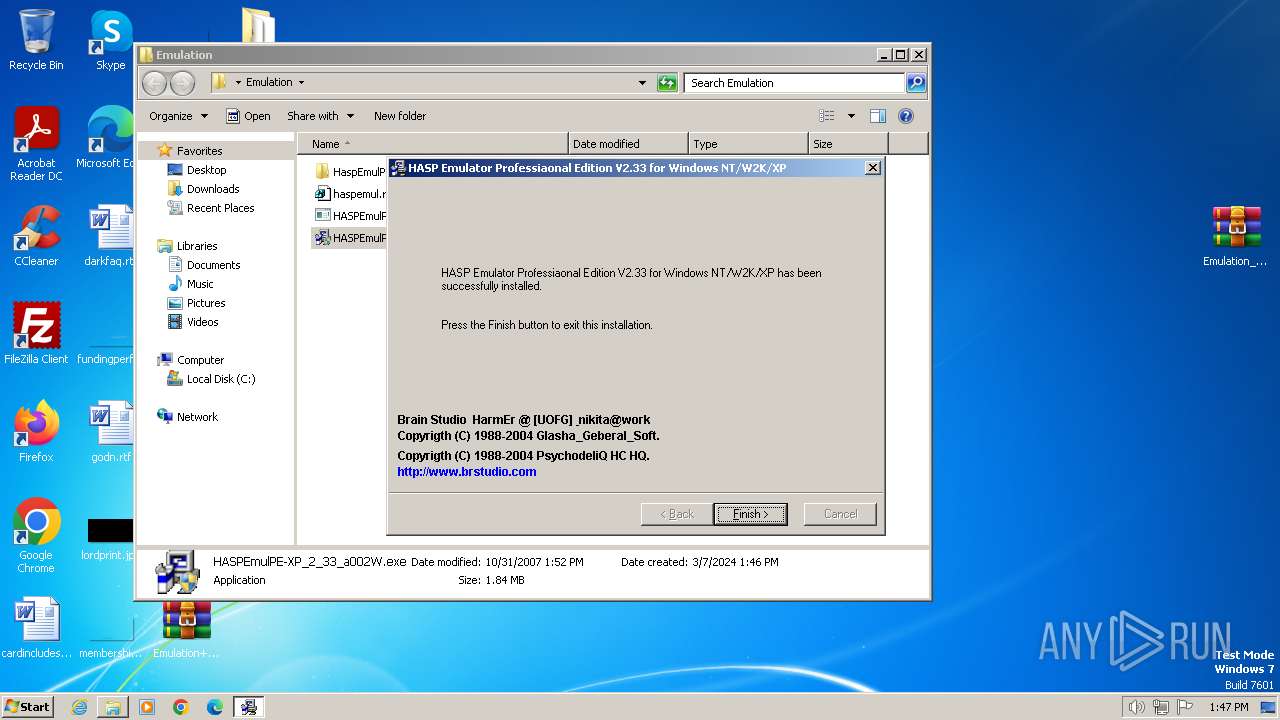
MALICIOUS
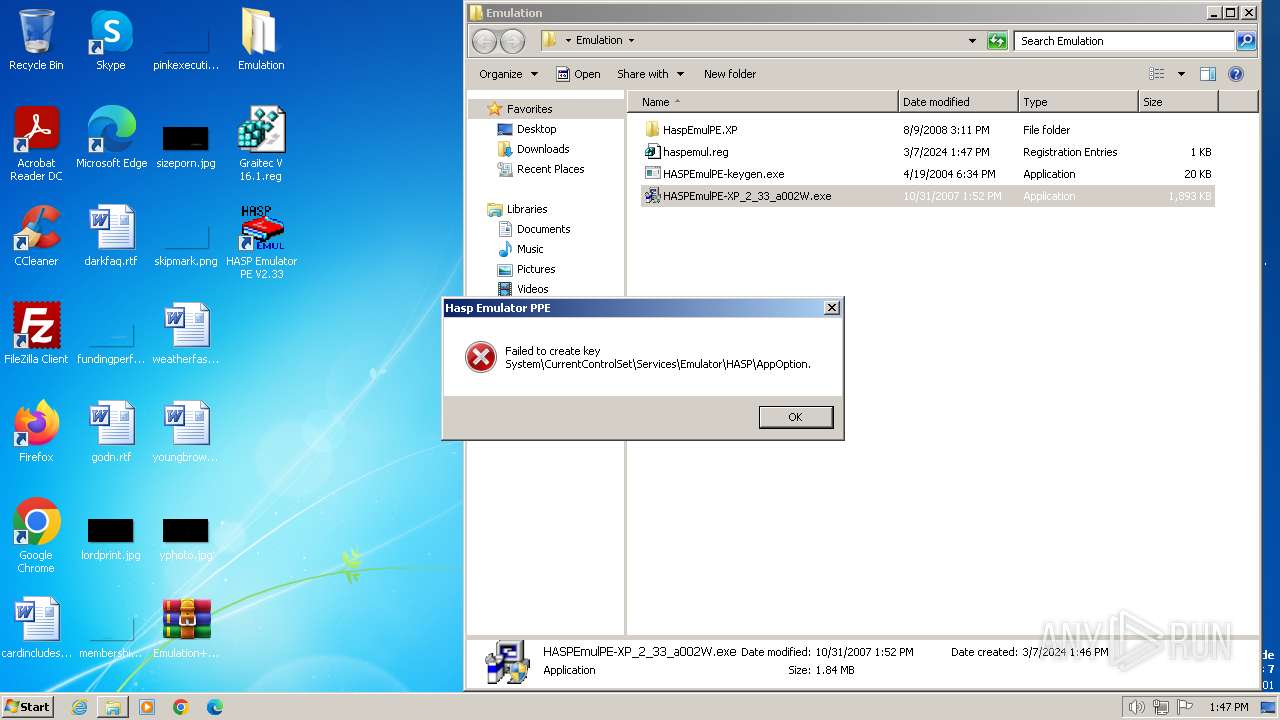
Creates a writable file in the system directory
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
Drops the executable file immediately after the start
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 3180)
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3460)
Executable content was dropped or overwritten
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
Creates file in the systems drive root
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
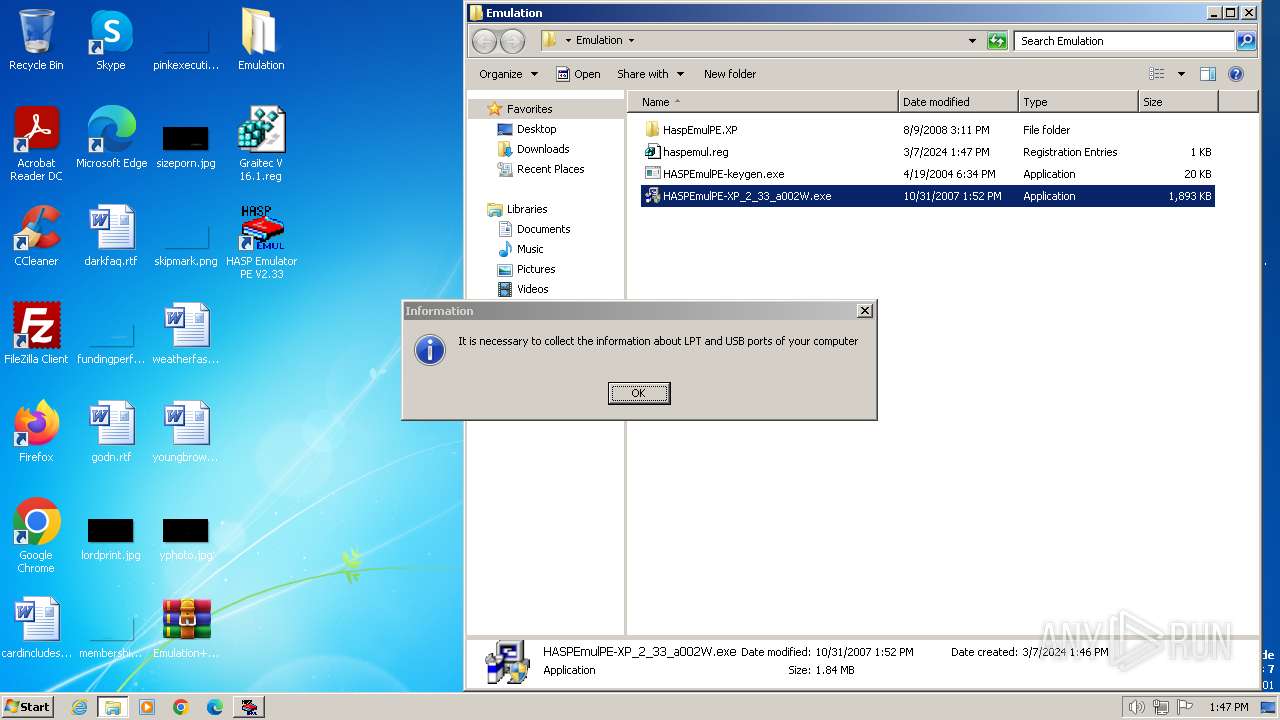
Searches for installed software
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
Starts application with an unusual extension
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
Creates a software uninstall entry
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
INFO
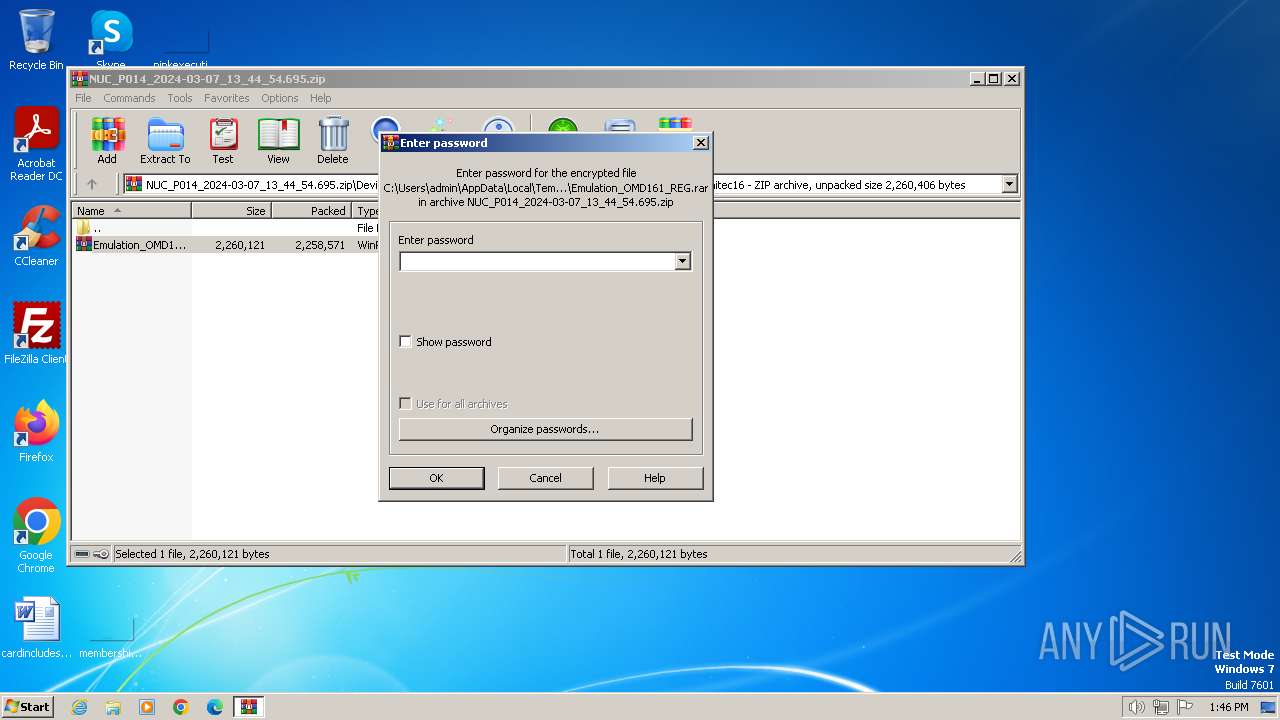
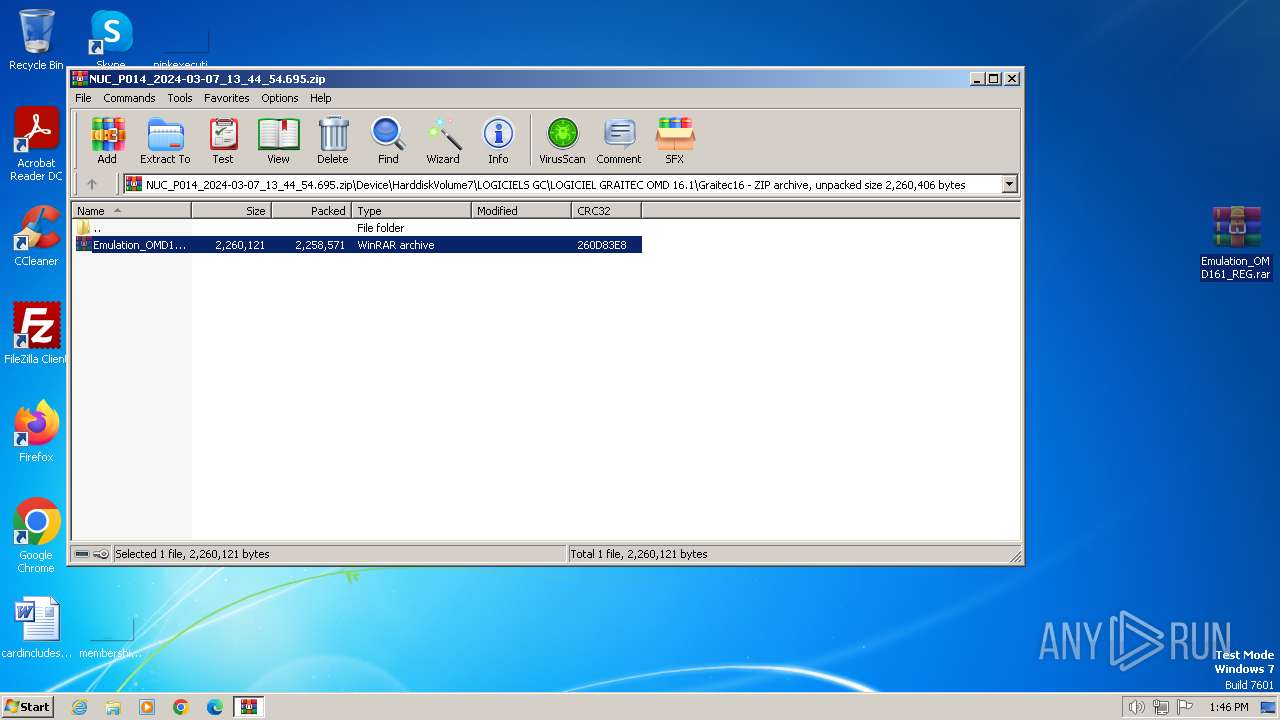
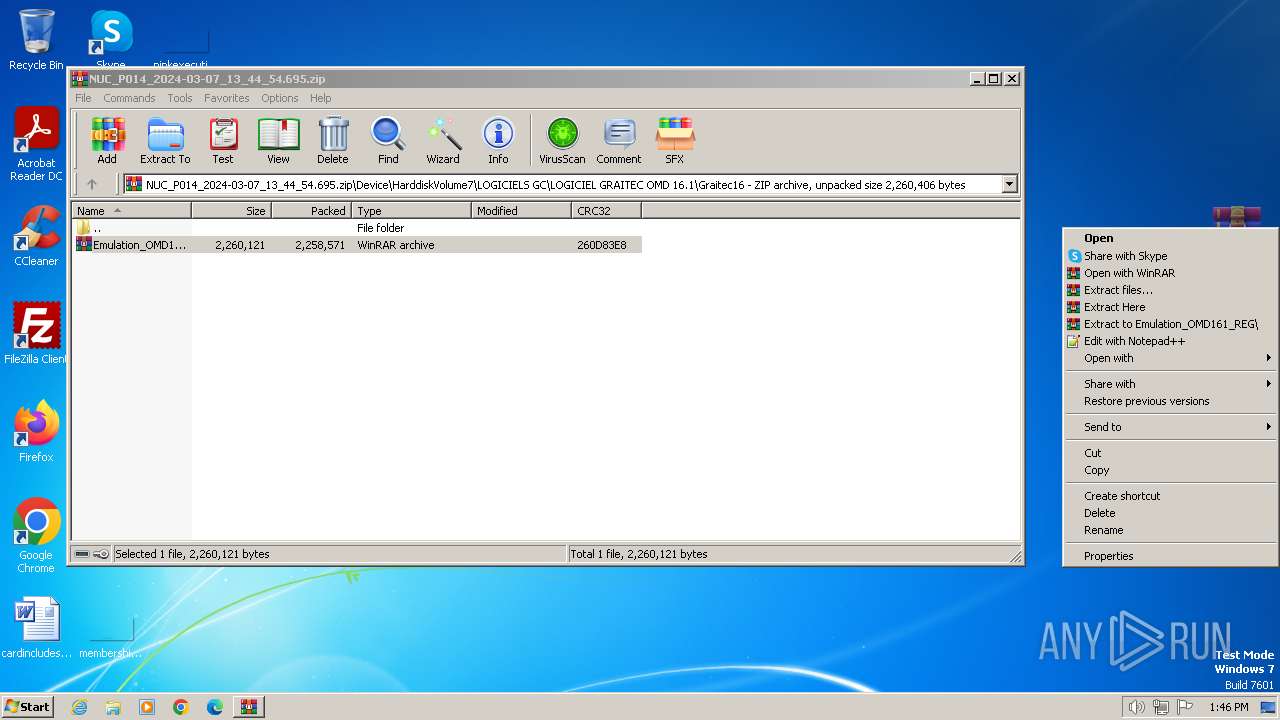
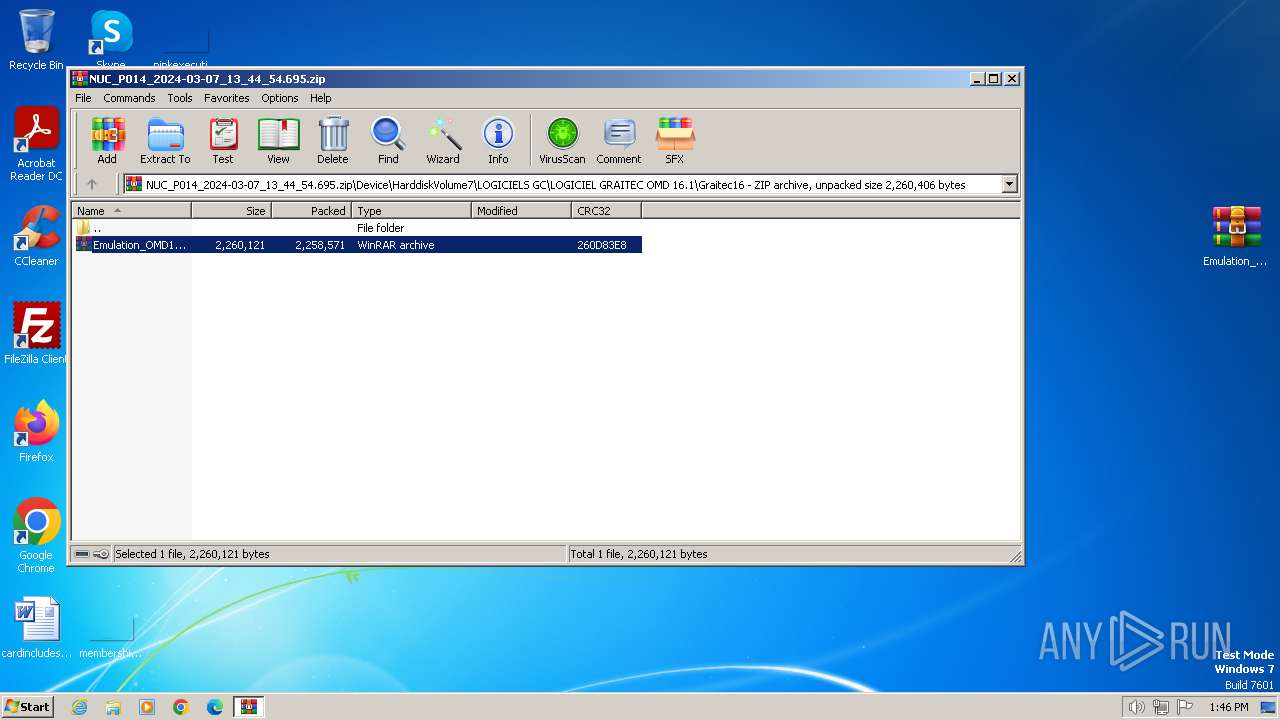
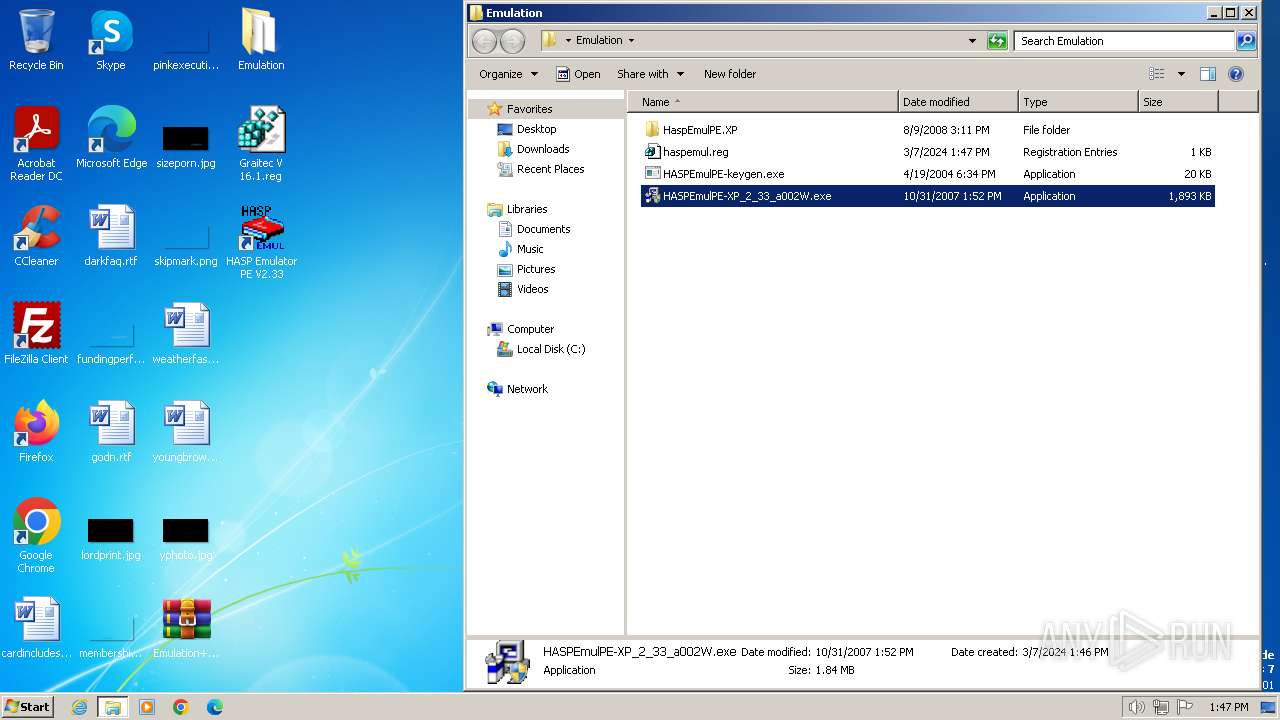
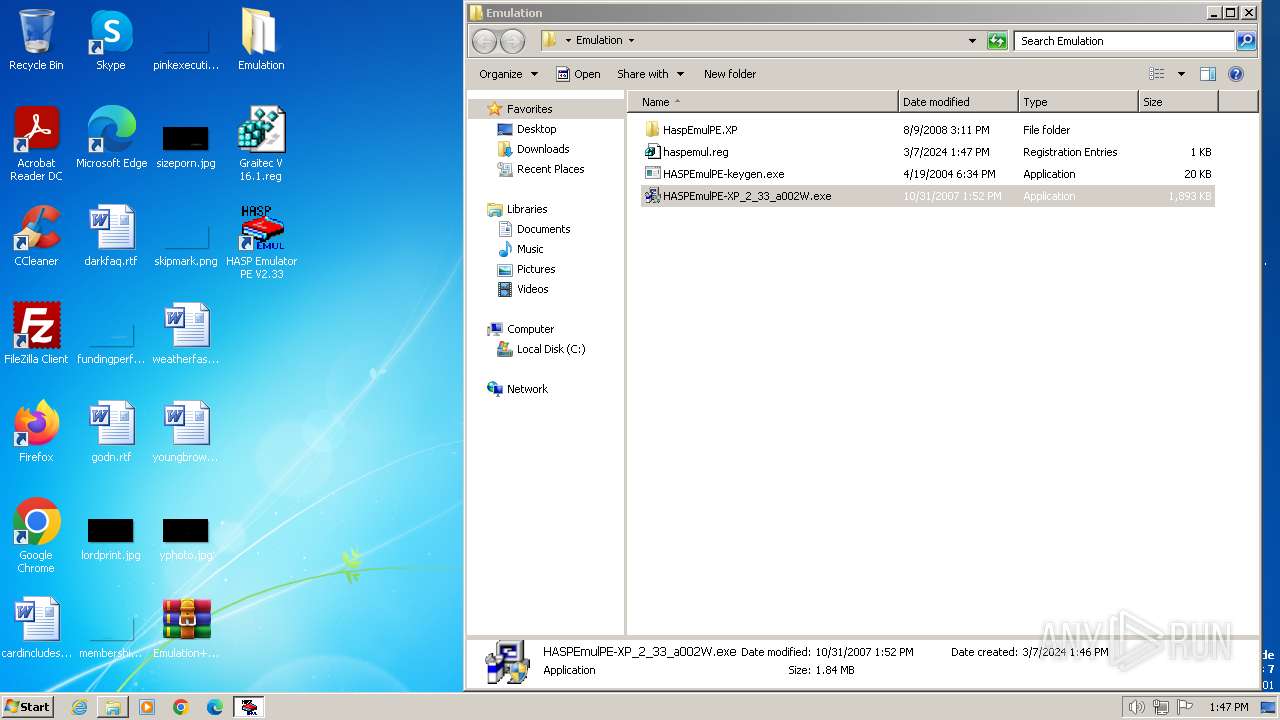
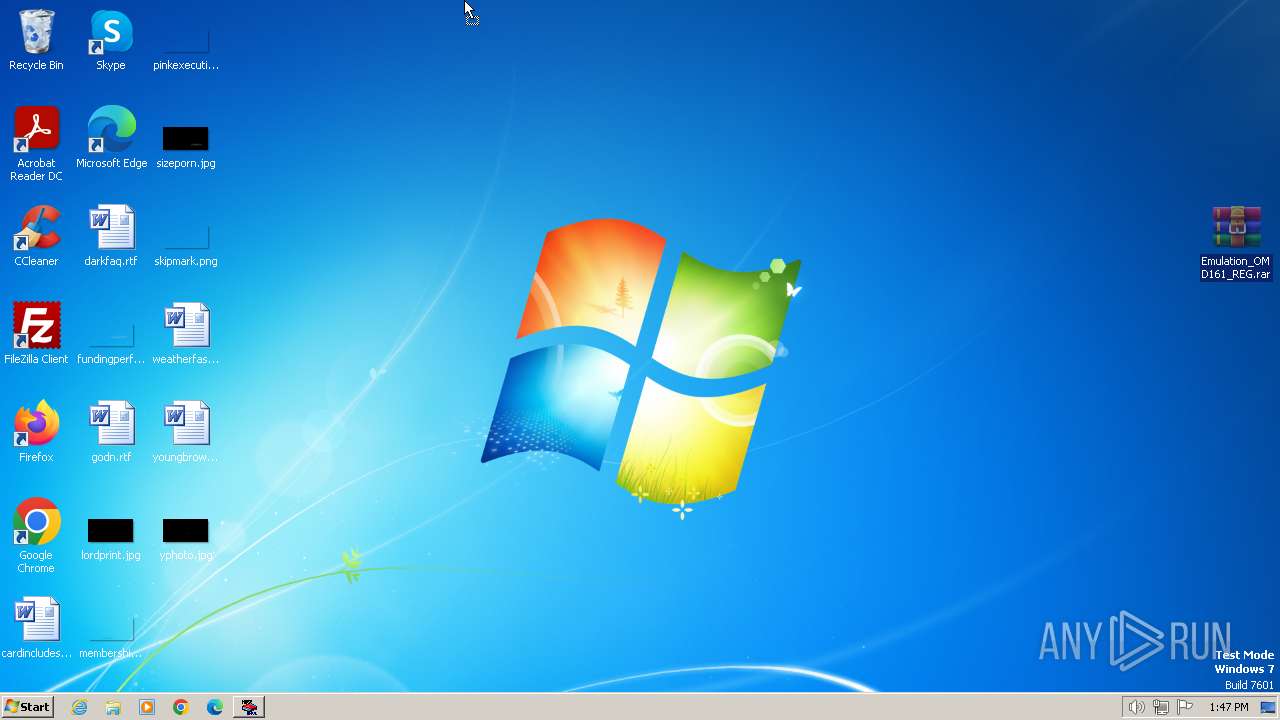
Manual execution by a user
- WinRAR.exe (PID: 3180)
- WinRAR.exe (PID: 2848)
- WinRAR.exe (PID: 3460)
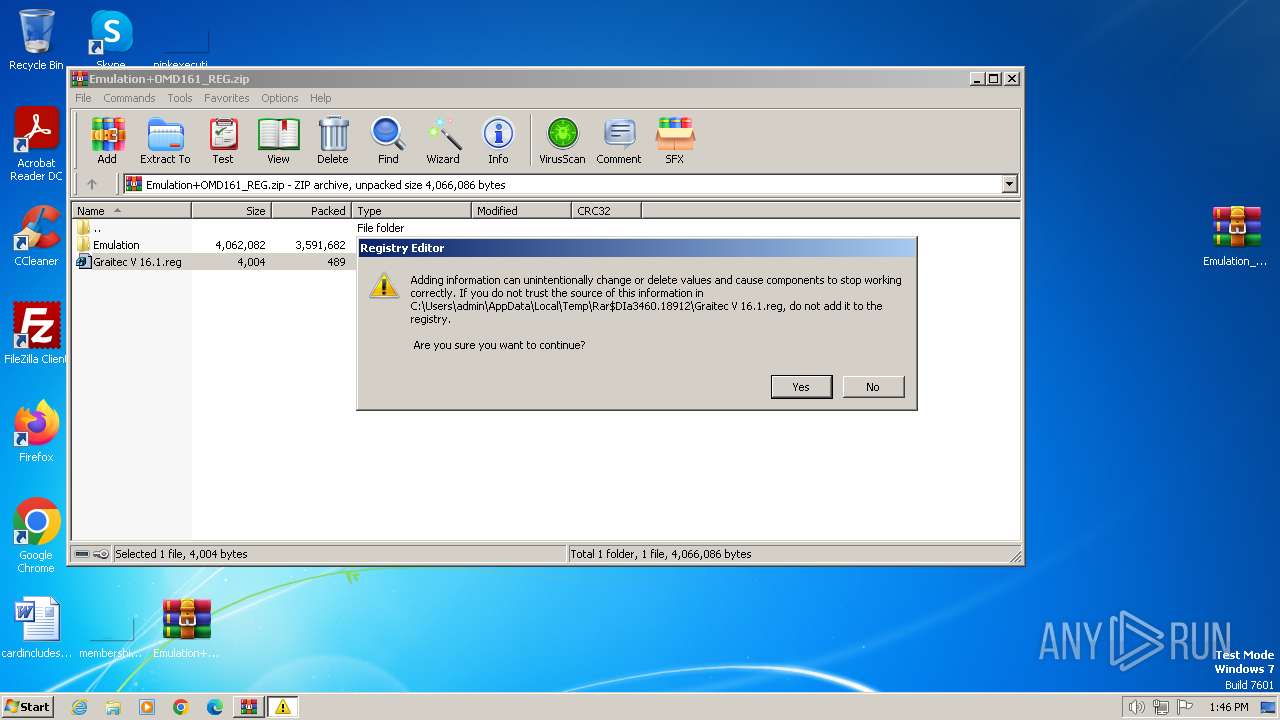
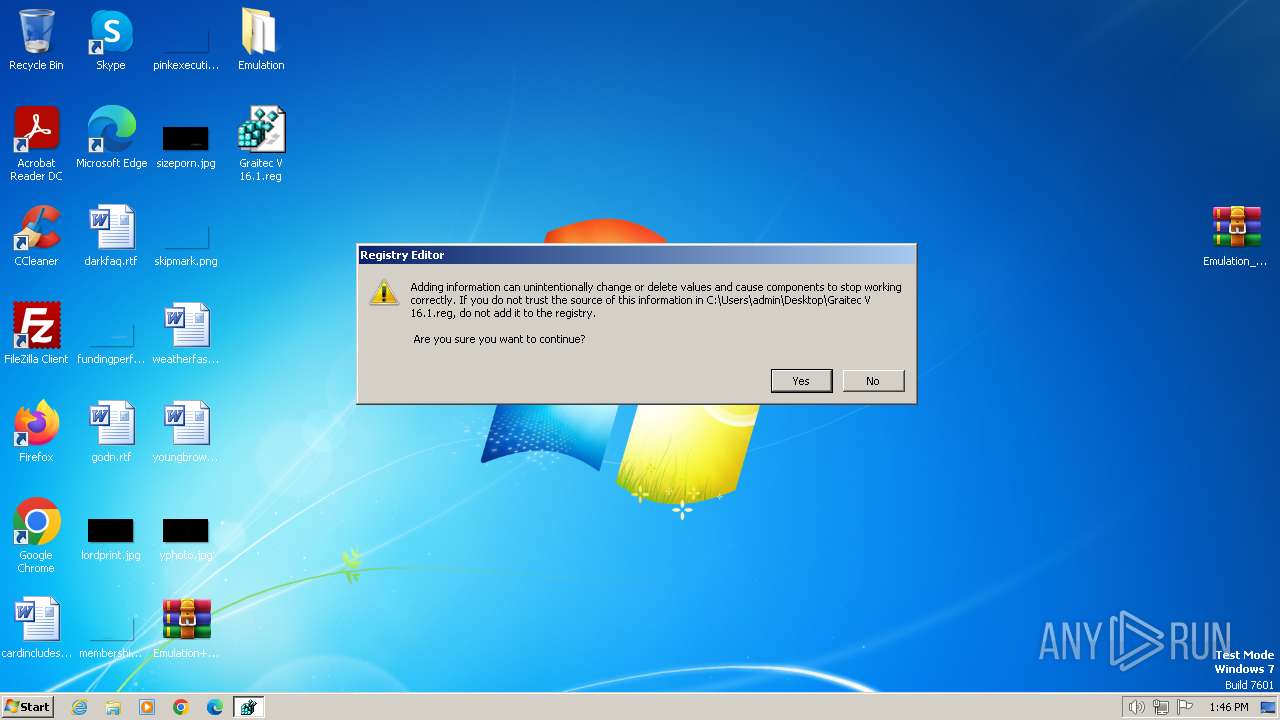
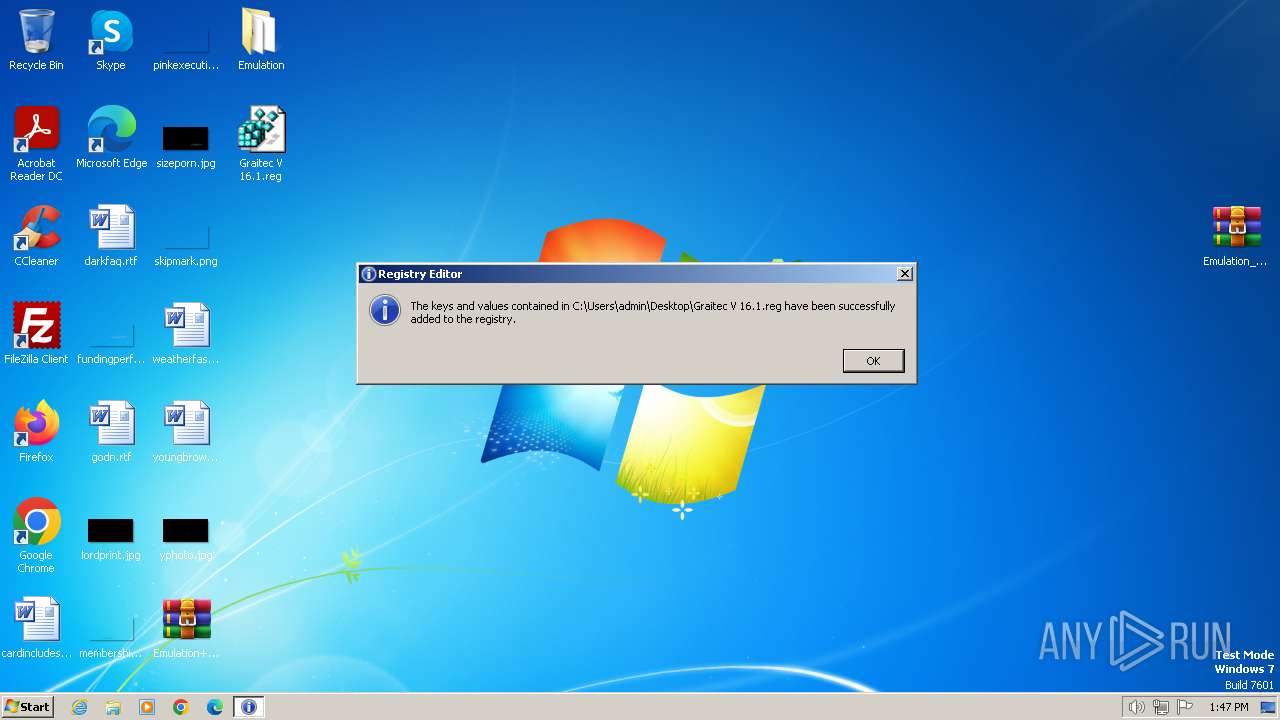
- regedit.exe (PID: 3308)
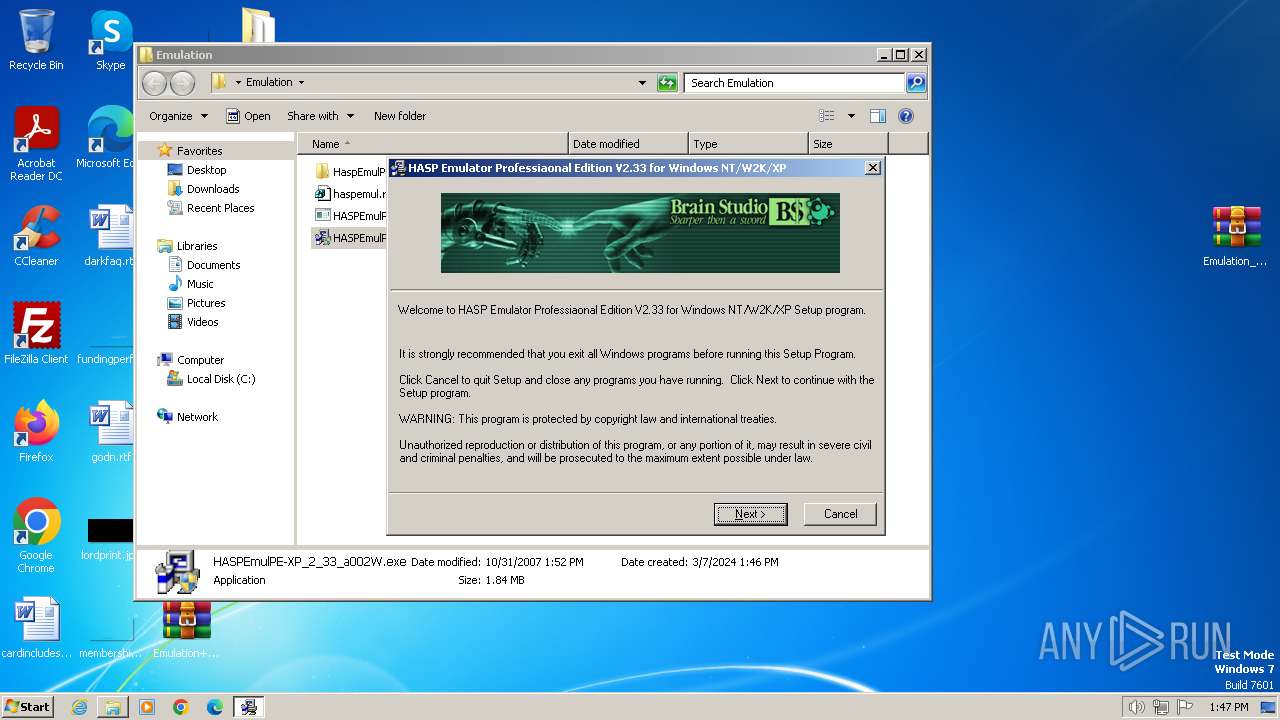
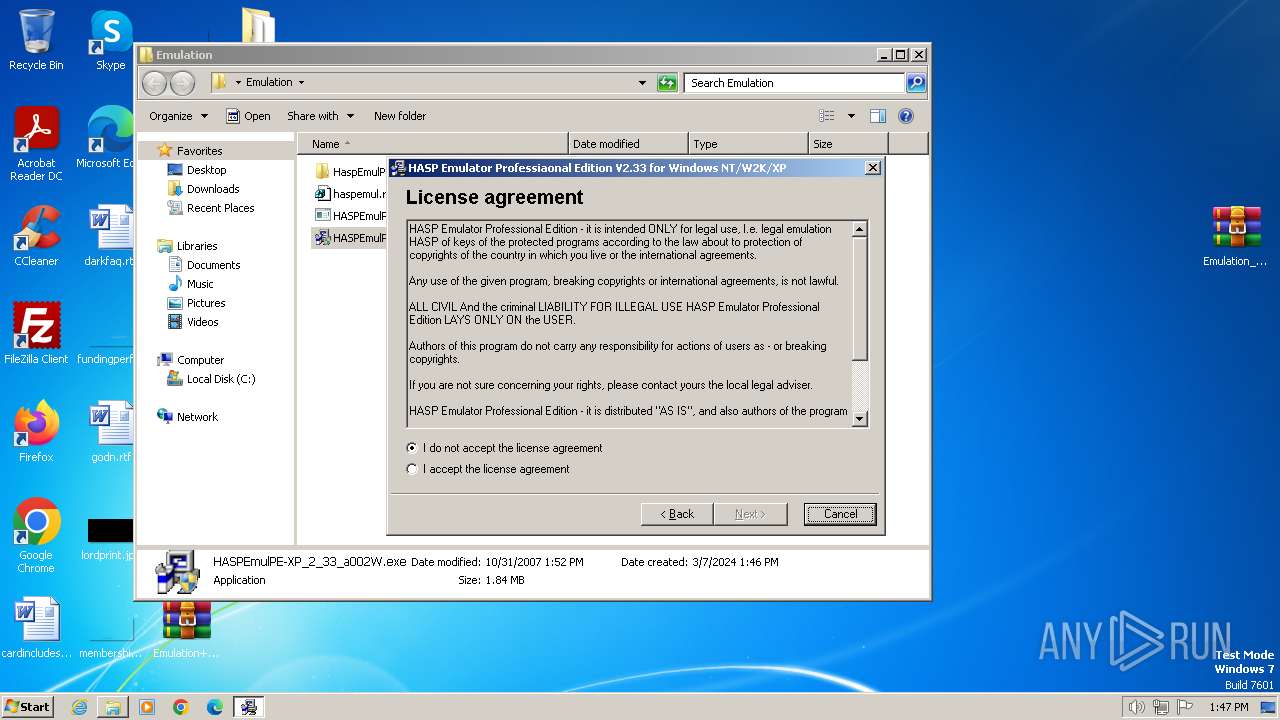
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
- regedit.exe (PID: 3724)
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2240)
- HaspEmulPE.exe (PID: 3444)
- HaspEmulPE.exe (PID: 952)
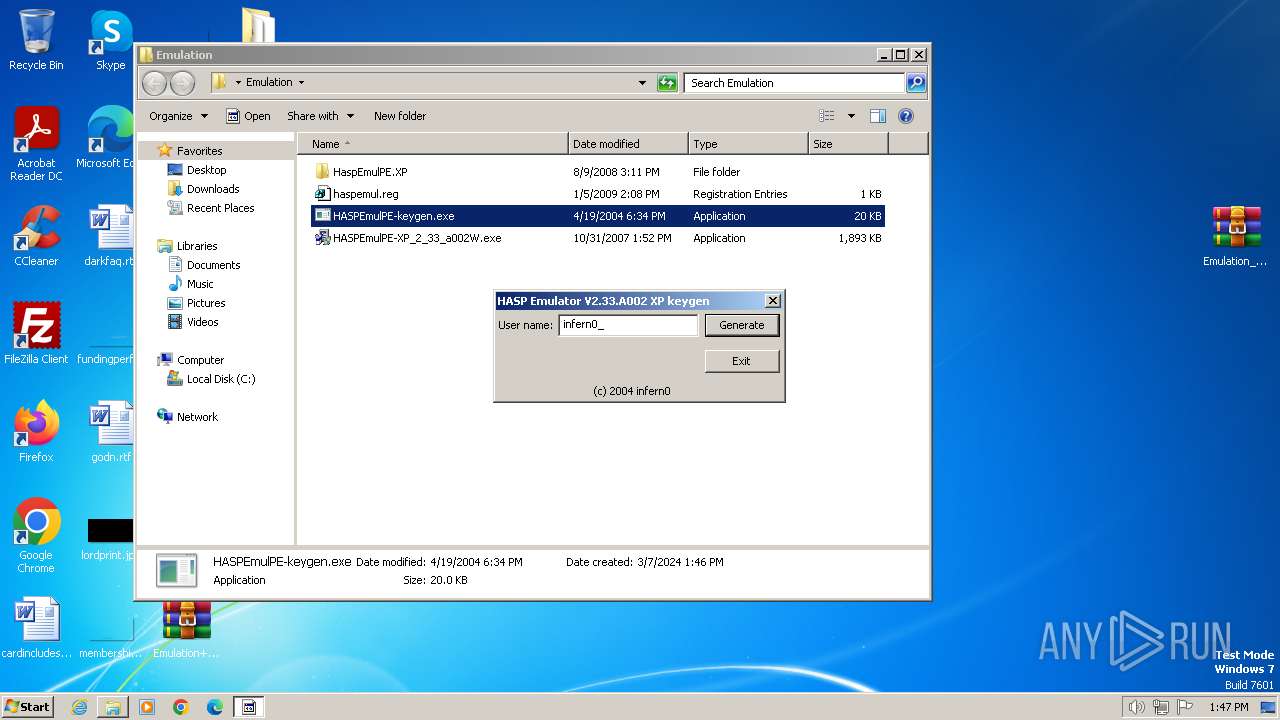
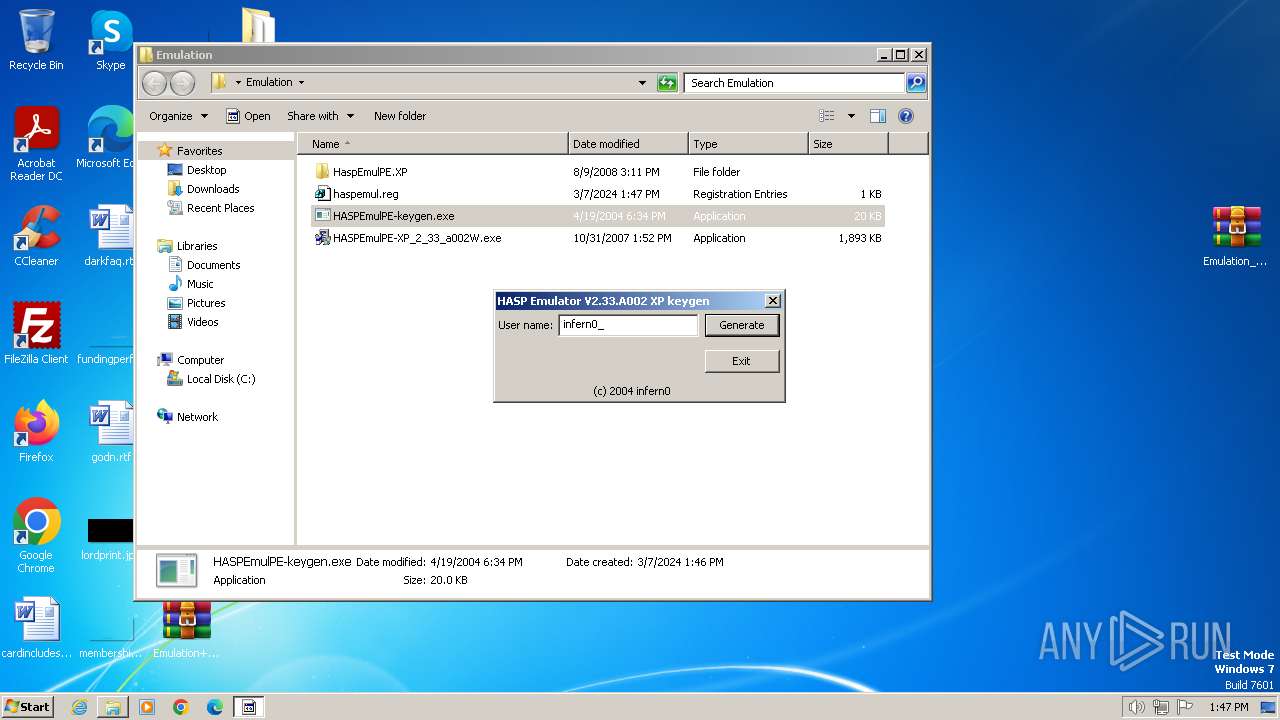
- HASPEmulPE-keygen.exe (PID: 2728)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3180)
Checks supported languages
- HASPEmulPE-keygen.exe (PID: 2728)
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
- GLJF52A.tmp (PID: 1624)
- GLJF52A.tmp (PID: 2772)
- HaspEmulPE.exe (PID: 3444)
- HaspEmulPE.exe (PID: 952)
- GLJF52A.tmp (PID: 3088)
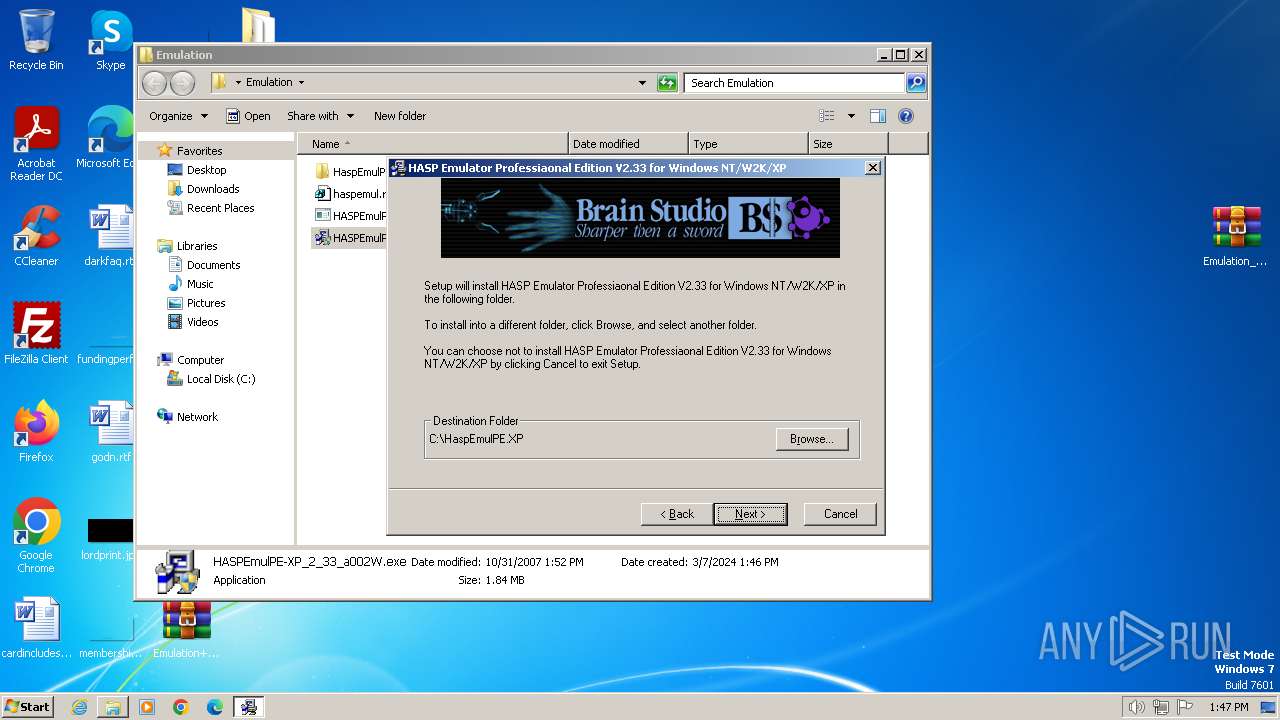
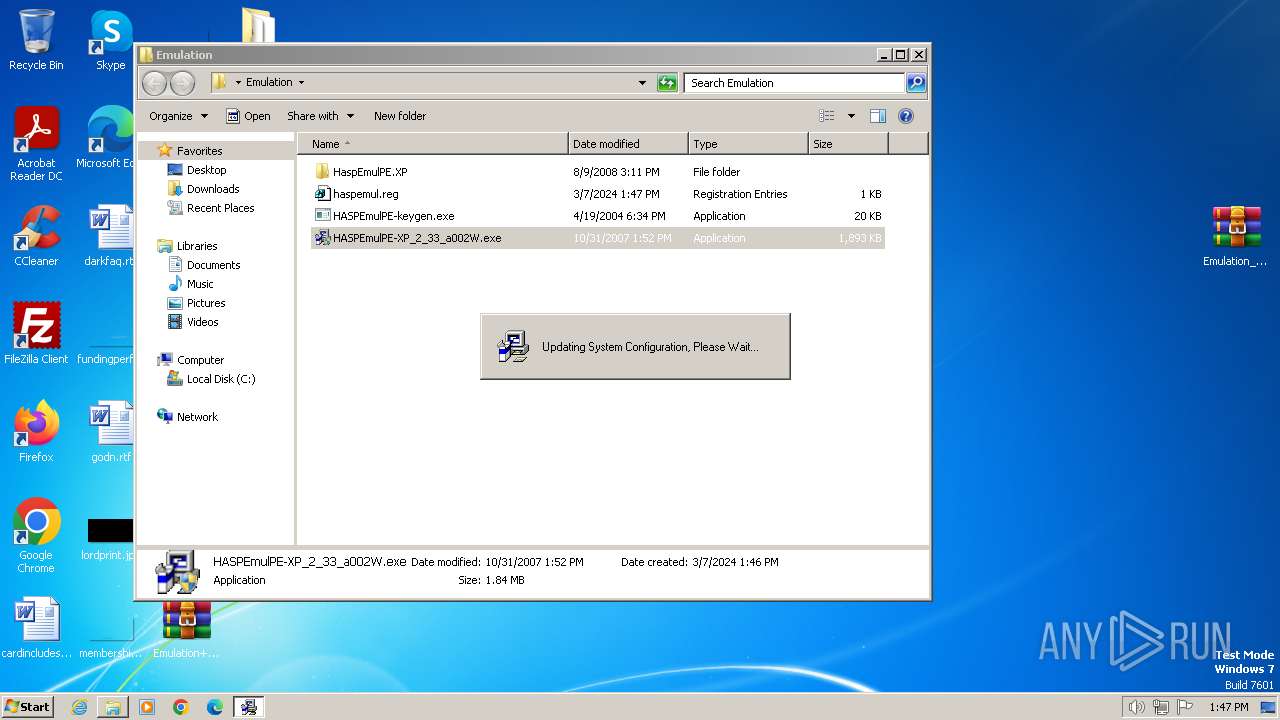
Creates files in the program directory
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
Reads the computer name
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
- HaspEmulPE.exe (PID: 3444)
Create files in a temporary directory
- HASPEmulPE-XP_2_33_a002W.exe (PID: 2112)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
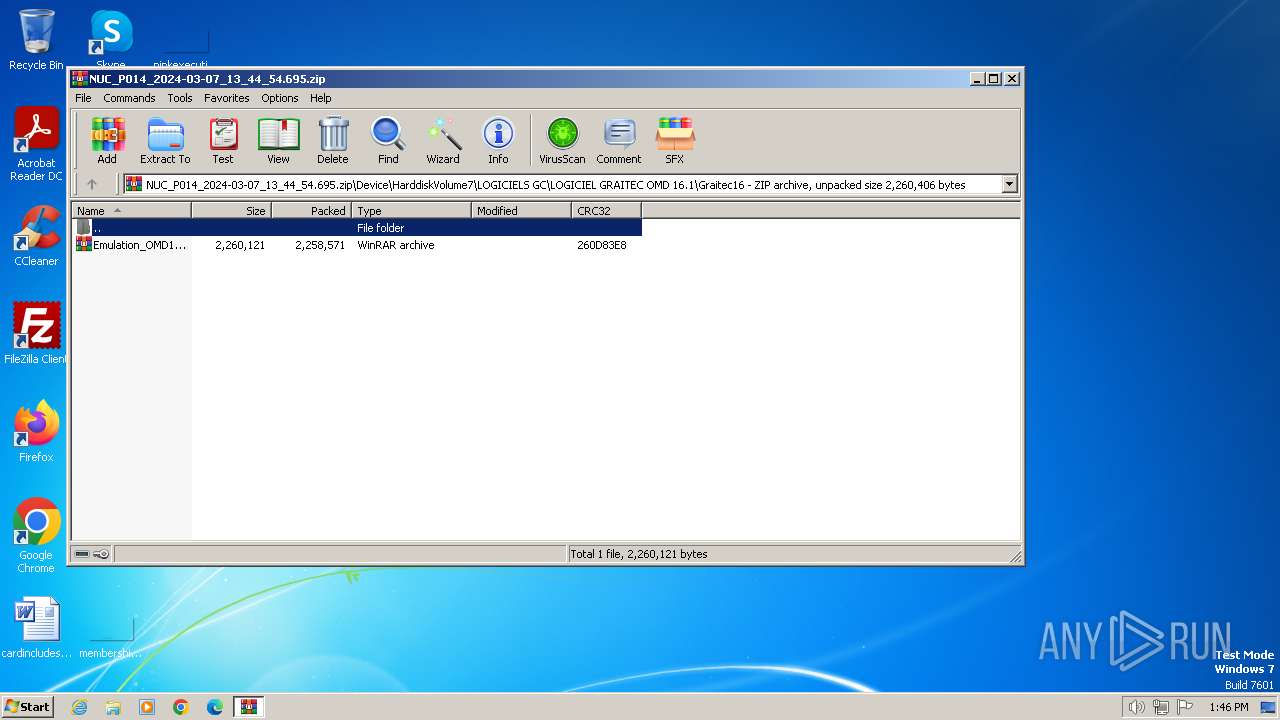
| ZipCRC: | 0x260d83e8 |
| ZipCompressedSize: | 2258571 |
| ZipUncompressedSize: | 2260121 |
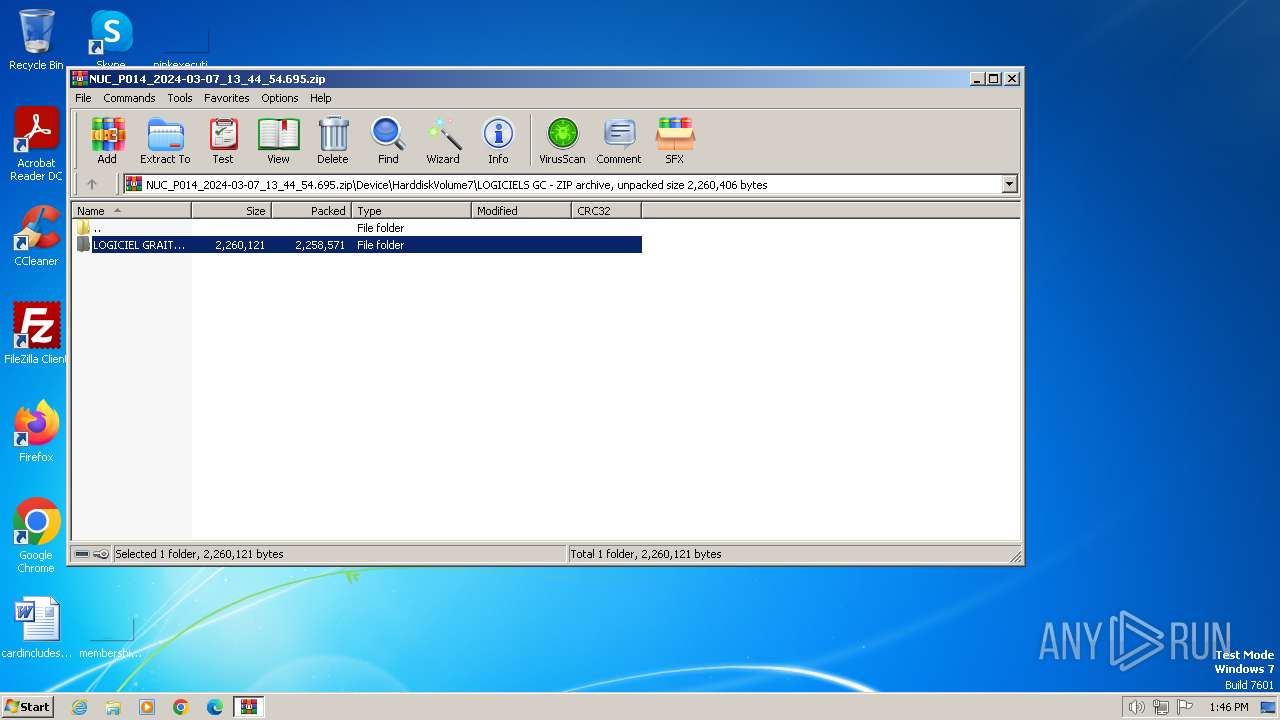
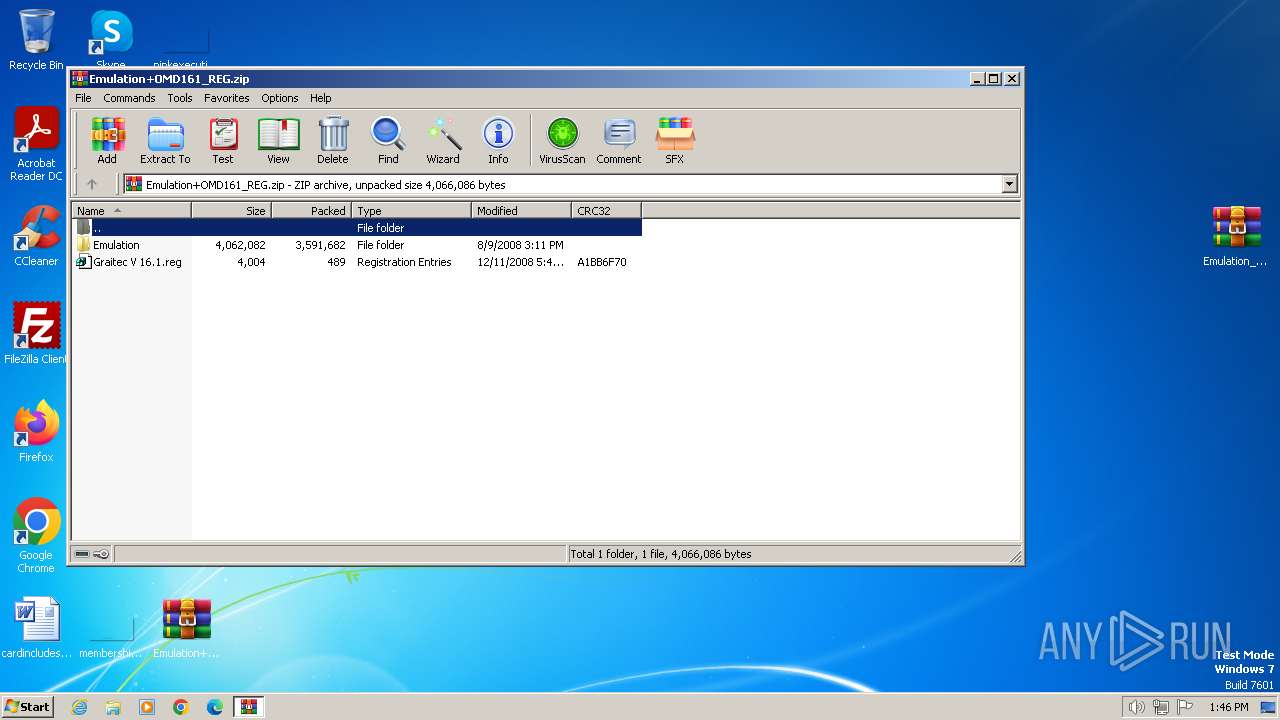
| ZipFileName: | Device/HarddiskVolume7/LOGICIELS GC/LOGICIEL GRAITEC OMD 16.1/Graitec16/Emulation_OMD161_REG.rar |
Total processes
65
Monitored processes
16
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
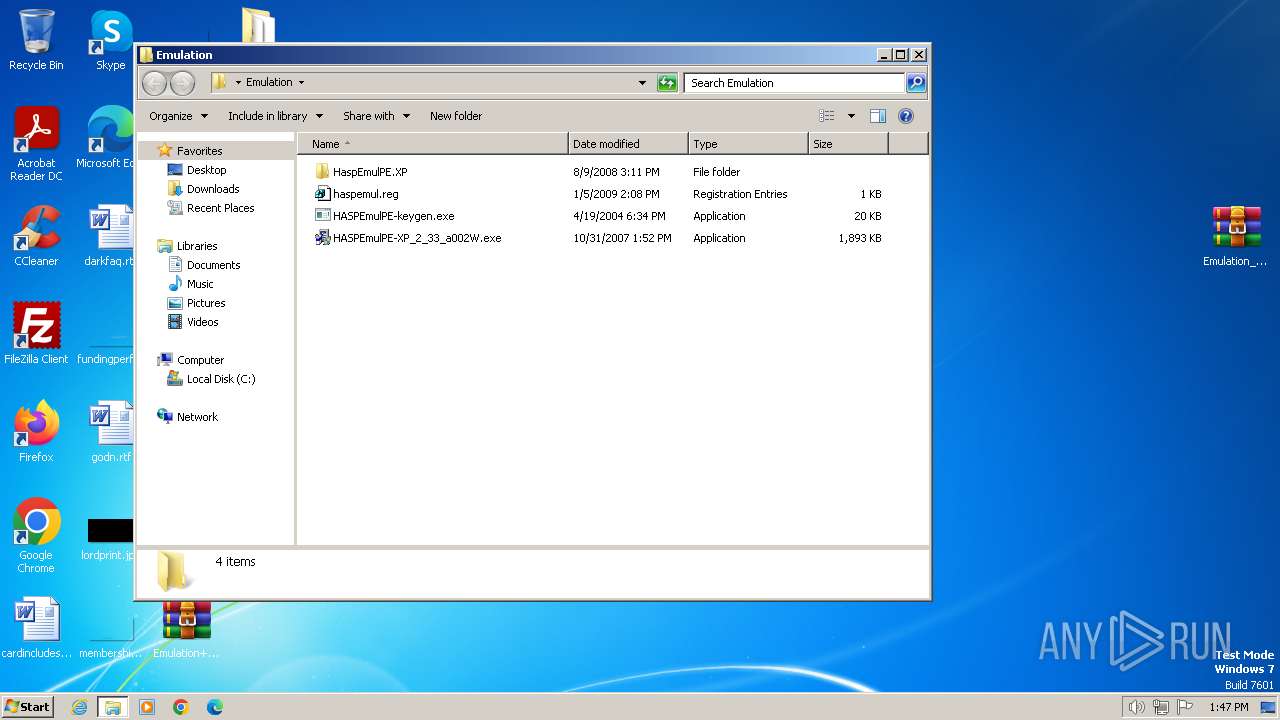
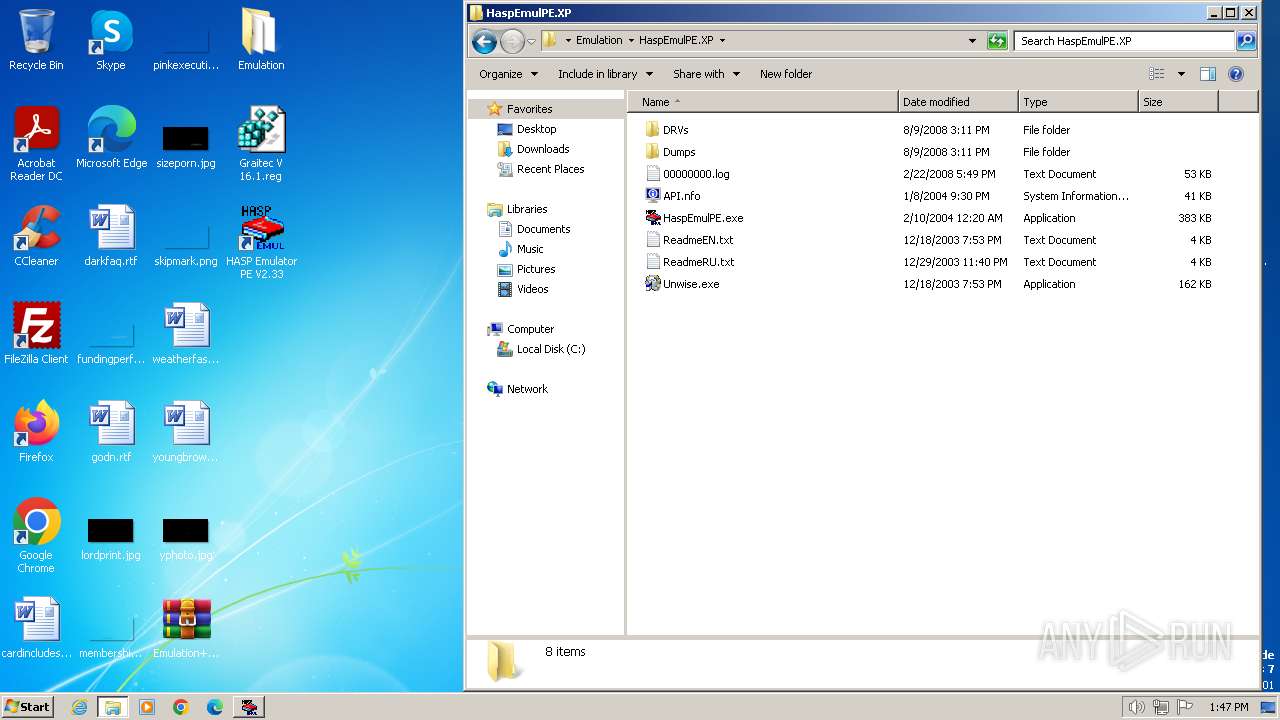
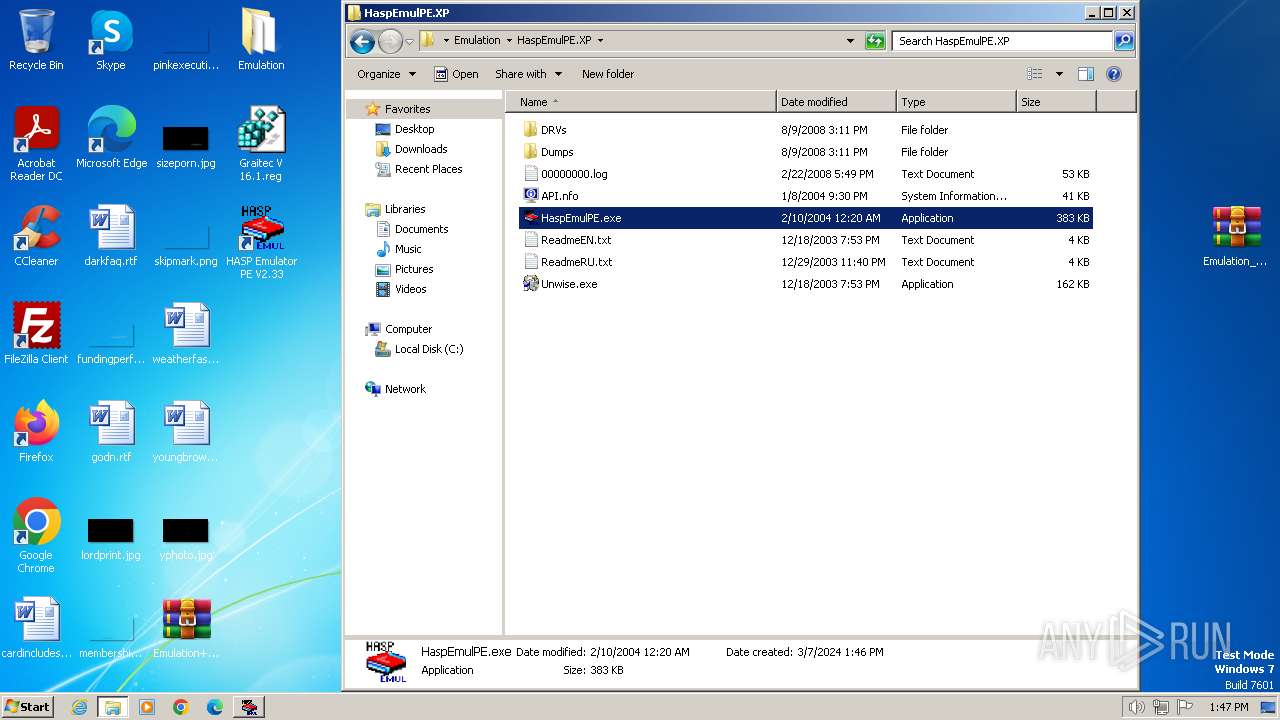
| 952 | "C:\Users\admin\Desktop\Emulation\HaspEmulPE.XP\HaspEmulPE.exe" | C:\Users\admin\Desktop\Emulation\HaspEmulPE.XP\HaspEmulPE.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1624 | "C:\Users\admin\AppData\Local\Temp\GLJF52A.tmp" C:\HaspEmulPE.XP\DRVs\Ohardlock.sys | C:\Users\admin\AppData\Local\Temp\GLJF52A.tmp | — | HASPEmulPE-XP_2_33_a002W.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2112 | "C:\Users\admin\Desktop\Emulation\HASPEmulPE-XP_2_33_a002W.exe" | C:\Users\admin\Desktop\Emulation\HASPEmulPE-XP_2_33_a002W.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2240 | "C:\Users\admin\Desktop\Emulation\HASPEmulPE-XP_2_33_a002W.exe" | C:\Users\admin\Desktop\Emulation\HASPEmulPE-XP_2_33_a002W.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
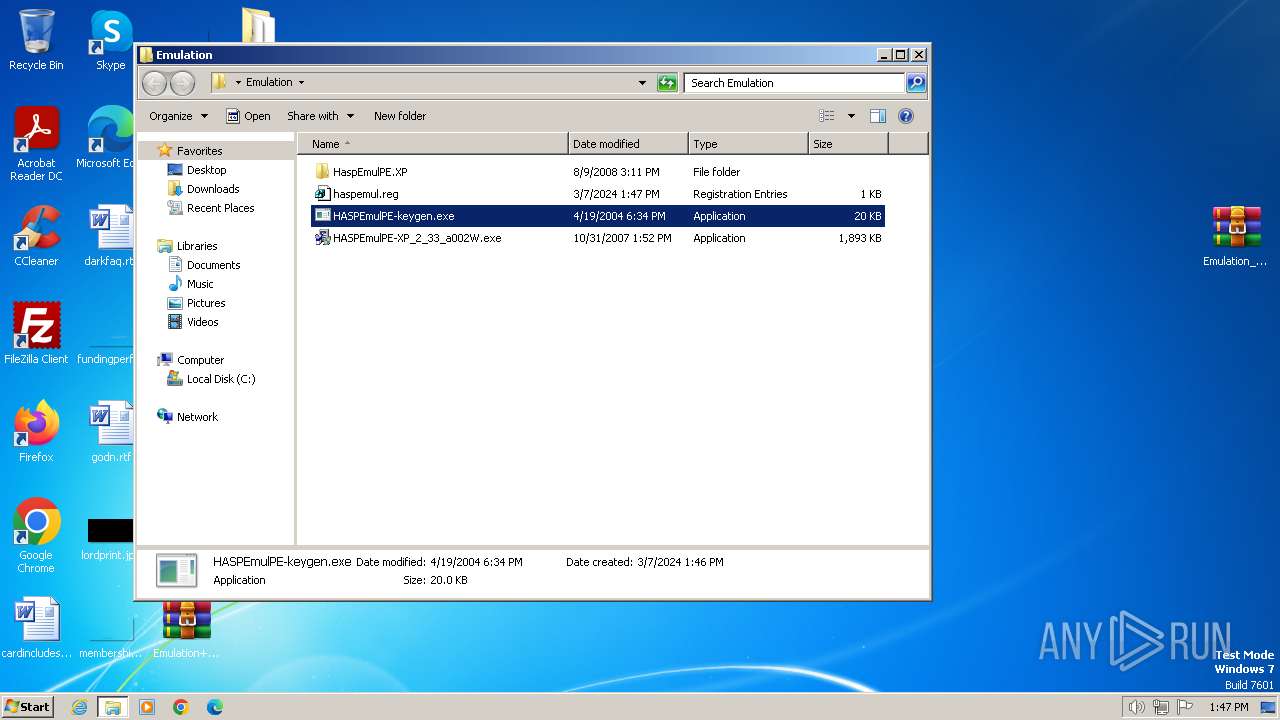
| 2728 | "C:\Users\admin\Desktop\Emulation\HASPEmulPE-keygen.exe" | C:\Users\admin\Desktop\Emulation\HASPEmulPE-keygen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2772 | "C:\Users\admin\AppData\Local\Temp\GLJF52A.tmp" C:\HaspEmulPE.XP\DRVs\Haspnt.sys | C:\Users\admin\AppData\Local\Temp\GLJF52A.tmp | — | HASPEmulPE-XP_2_33_a002W.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2848 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Emulation_OMD161_REG.rar" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3088 | "C:\Users\admin\AppData\Local\Temp\GLJF52A.tmp" C:\HaspEmulPE.XP\DRVs\hlvdd.dll | C:\Users\admin\AppData\Local\Temp\GLJF52A.tmp | — | HASPEmulPE-XP_2_33_a002W.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
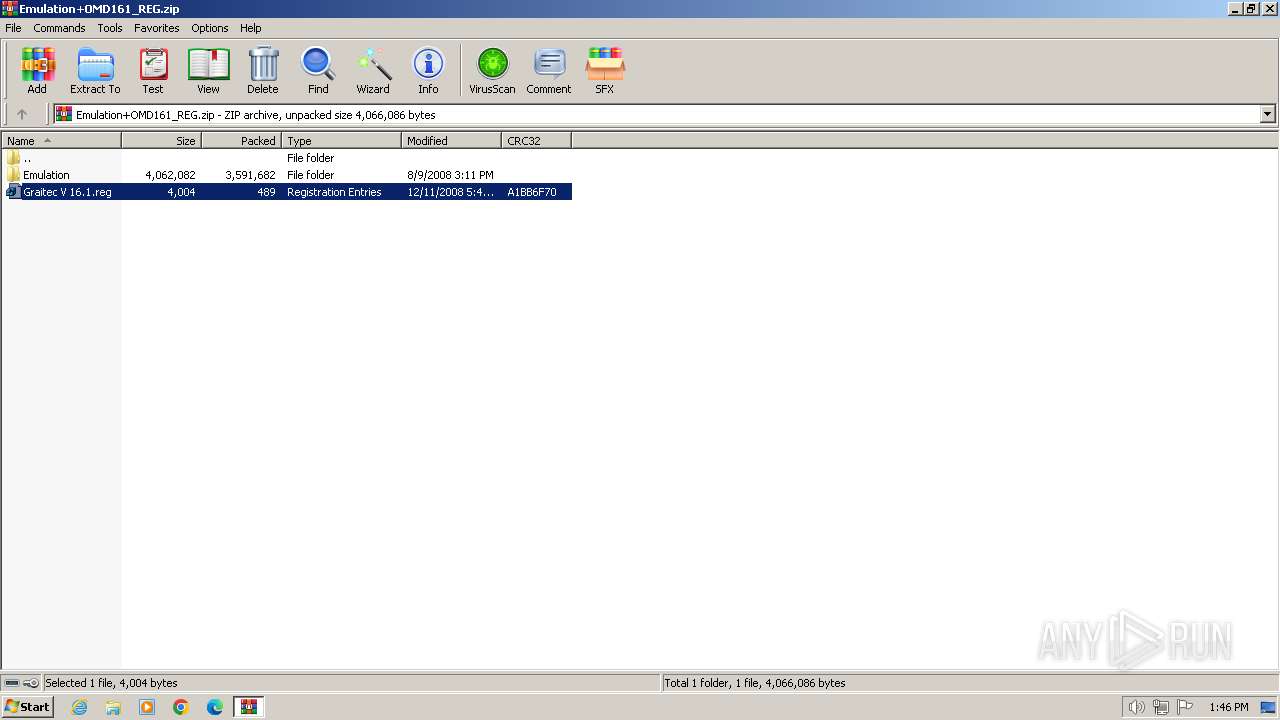
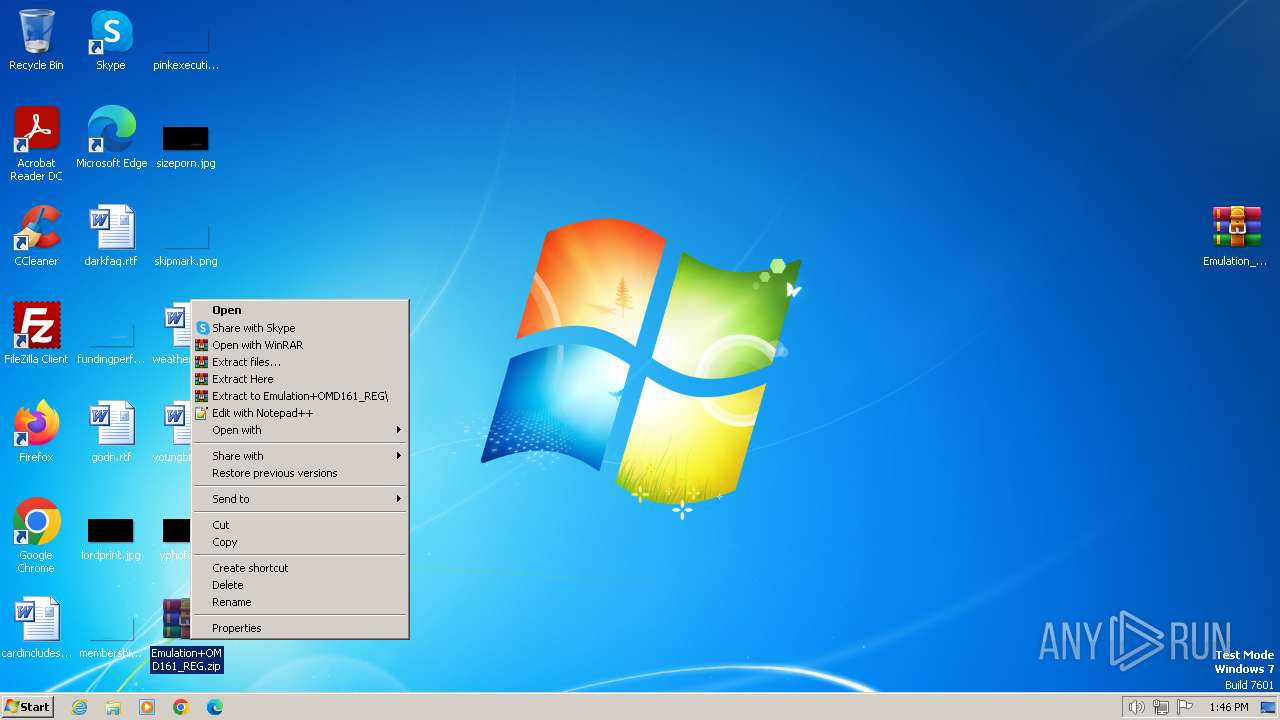
| 3180 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Emulation+OMD161_REG.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3308 | "regedit.exe" "C:\Users\admin\Desktop\Graitec V 16.1.reg" | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 966
Read events
8 877
Write events
89
Delete events
0
Modification events
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NUC_P014_2024-03-07_13_44_54.695.zip | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
38
Suspicious files
10
Text files
20
Unknown types
1
Dropped files
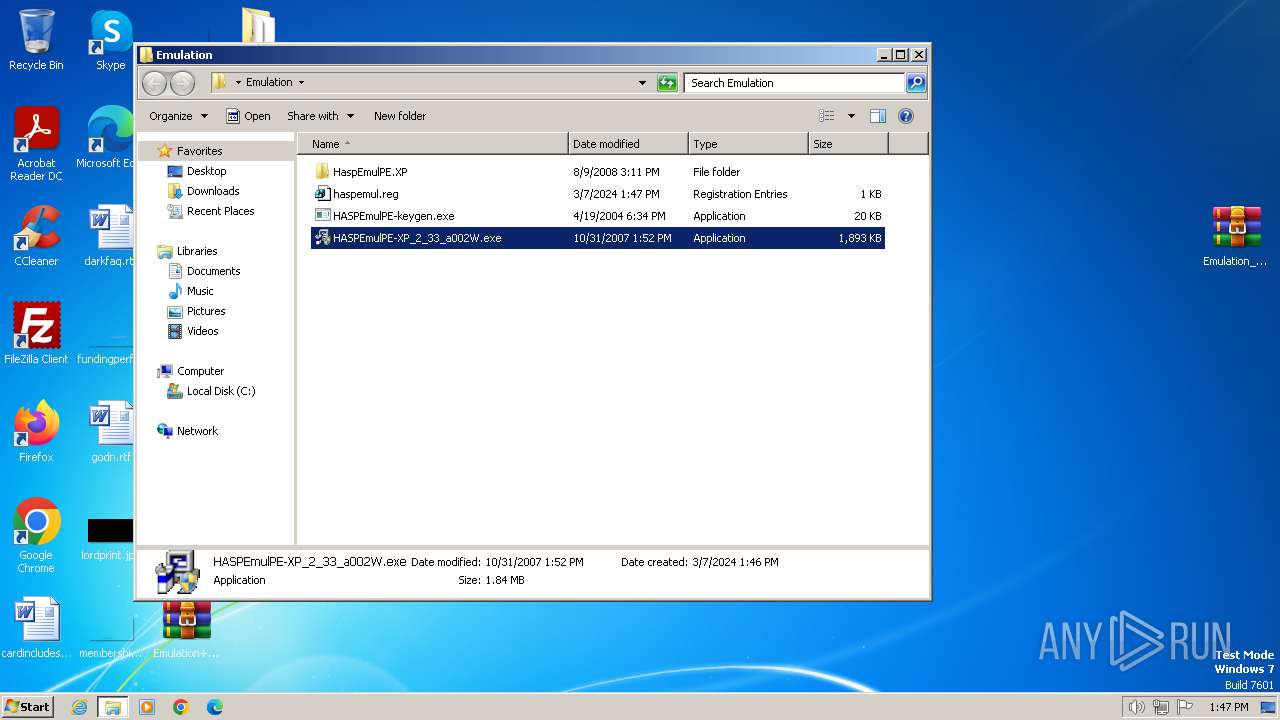
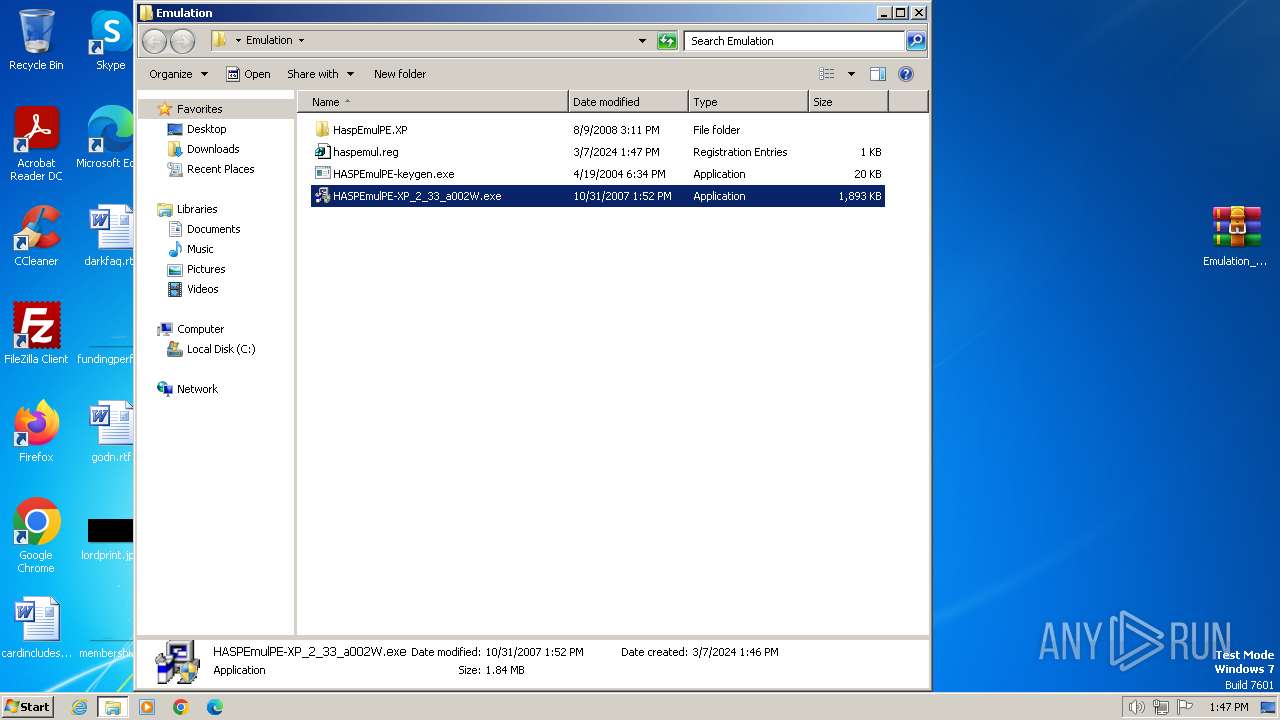
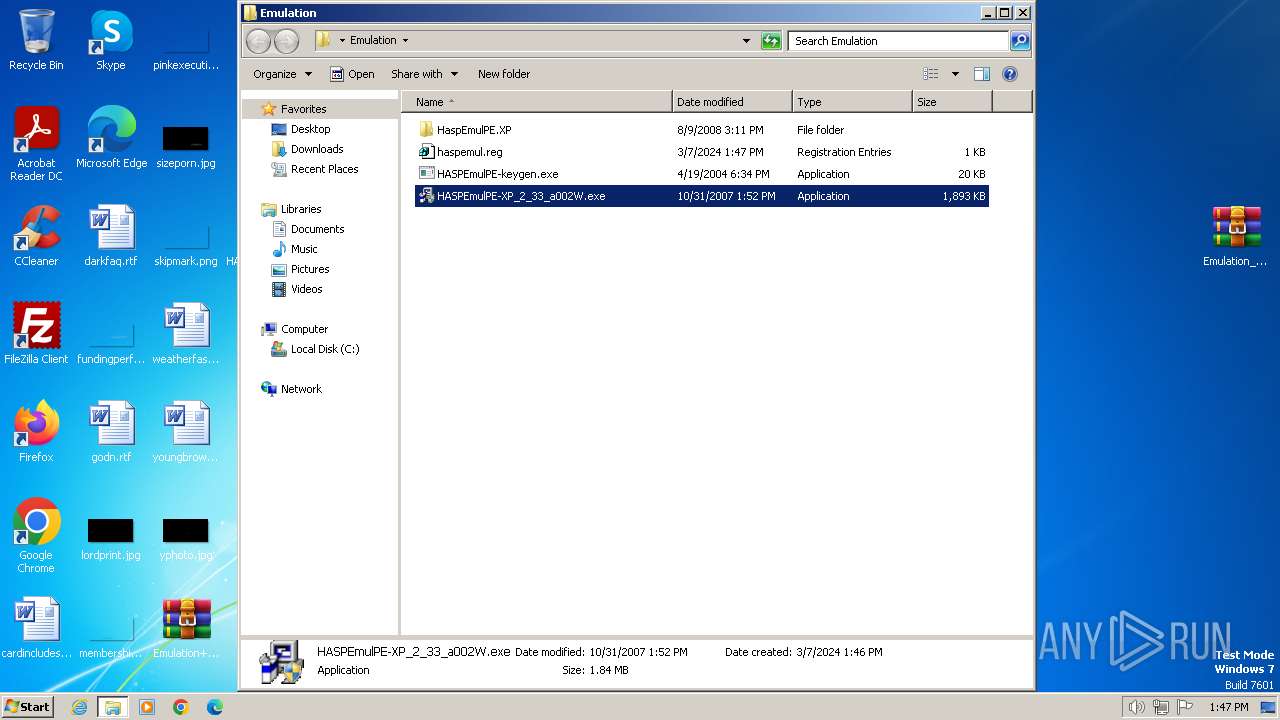
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3180 | WinRAR.exe | C:\Users\admin\Desktop\Emulation\HaspEmulPE.XP\ReadmeRU.txt | text | |
MD5:902735002EA409DE0A76E8A287B25D3A | SHA256:8B422C0FCE09DC4016777ACC9F8F678FDA03AEEC9FA6E376D74A480189446438 | |||
| 3180 | WinRAR.exe | C:\Users\admin\Desktop\Emulation\HaspEmulPE.XP\HaspEmulPE.exe | executable | |
MD5:5065487EBB55D3C5E3255EB561656269 | SHA256:6C3BE703068A3A8615C7D75BF1A195DF79C0F73FED61E8B6B11B95F952A1F568 | |||
| 2848 | WinRAR.exe | C:\Users\admin\Desktop\Emulation+OMD161_REG.zip | compressed | |
MD5:F5117CD17C80C0A3C906FDBCD1DFD82C | SHA256:2B7948A1CAB321104DC377A0D9ED71091CA31BDA4D00C6E9BDBD0DAA31DDF9BE | |||
| 3180 | WinRAR.exe | C:\Users\admin\Desktop\Emulation\HASPEmulPE-XP_2_33_a002W.exe | executable | |
MD5:B2DE0076E7E28B9D5E1EFC337E1B5D43 | SHA256:1F3C44F7F401CE13C6E30C39DB2C8C910D6BC8E8F5BDFBD8B38CFB8A28A2BB59 | |||
| 3180 | WinRAR.exe | C:\Users\admin\Desktop\Emulation\HASPEmulPE-keygen.exe | executable | |
MD5:38C7146048E7E590967AF0343E1CB61A | SHA256:36BE439739375BB7A0EF880EAE8278D72F0DED18AFF4141DEB3541BF59555ED7 | |||
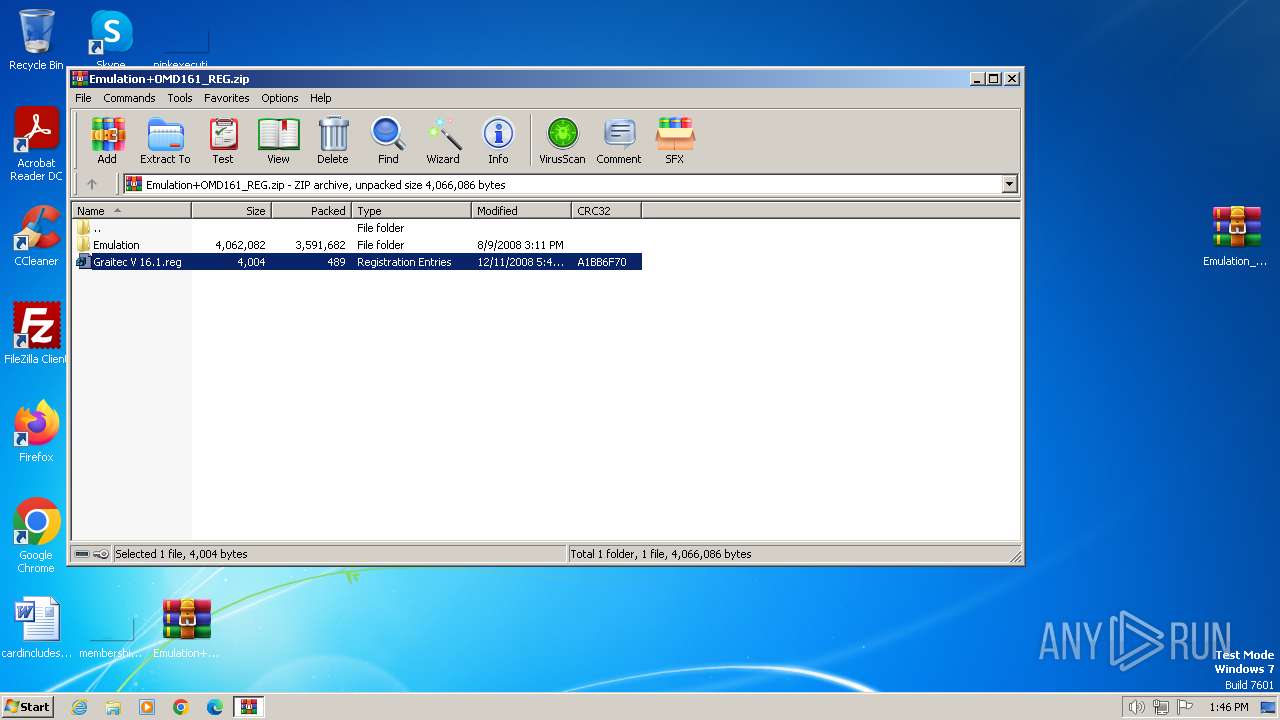
| 3180 | WinRAR.exe | C:\Users\admin\Desktop\Graitec V 16.1.reg | text | |
MD5:FC8E95265ED190021E31F646E7BF9034 | SHA256:DAEB4F622141631618CAB8A573E2500E9D0BA36CBF3AF902B08C17255017996C | |||
| 3180 | WinRAR.exe | C:\Users\admin\Desktop\Emulation\HaspEmulPE.XP\DRVs\Ohardlock.sys | executable | |
MD5:F3E34776D8B8AB665D051A8674FDF4CC | SHA256:57F15B1D90295E59390C1B83A5E66D870F27E19985E5B634A342AFD7E87E47E7 | |||
| 3180 | WinRAR.exe | C:\Users\admin\Desktop\Emulation\HaspEmulPE.XP\API.nfo | ini | |
MD5:5D53E59B84D8EADBEAE73672AC9957D5 | SHA256:283609F8A135FA54A2102D4806DE1C3163D619D11DD80FA47A94EF092D1AC6E3 | |||
| 3460 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3460.18912\Graitec V 16.1.reg | text | |
MD5:FC8E95265ED190021E31F646E7BF9034 | SHA256:DAEB4F622141631618CAB8A573E2500E9D0BA36CBF3AF902B08C17255017996C | |||
| 3180 | WinRAR.exe | C:\Users\admin\Desktop\Emulation\HaspEmulPE.XP\00000000.log | text | |
MD5:27F7B71E7FEE17B3525DF5C0FF1DCAFB | SHA256:CE4D3759CE1F98C7BC153FDFDE49040CBCDA5420C91B01C6F85F76DCF5BB00C5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |