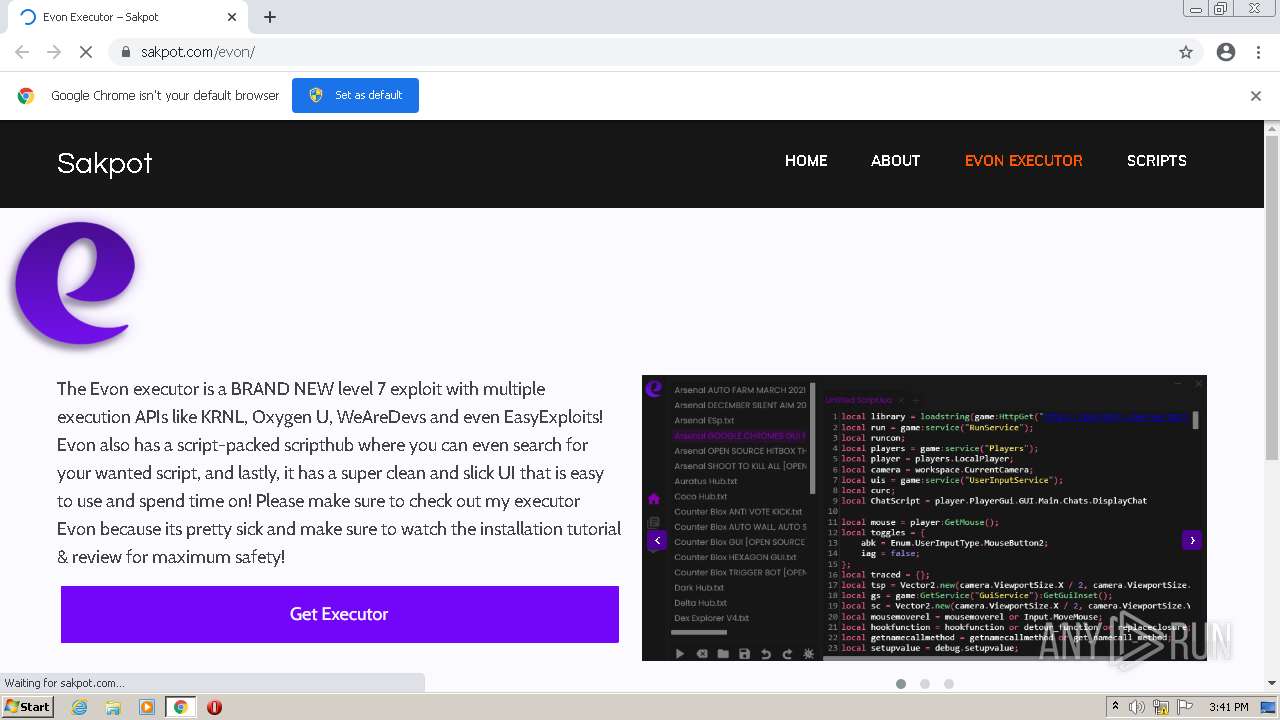
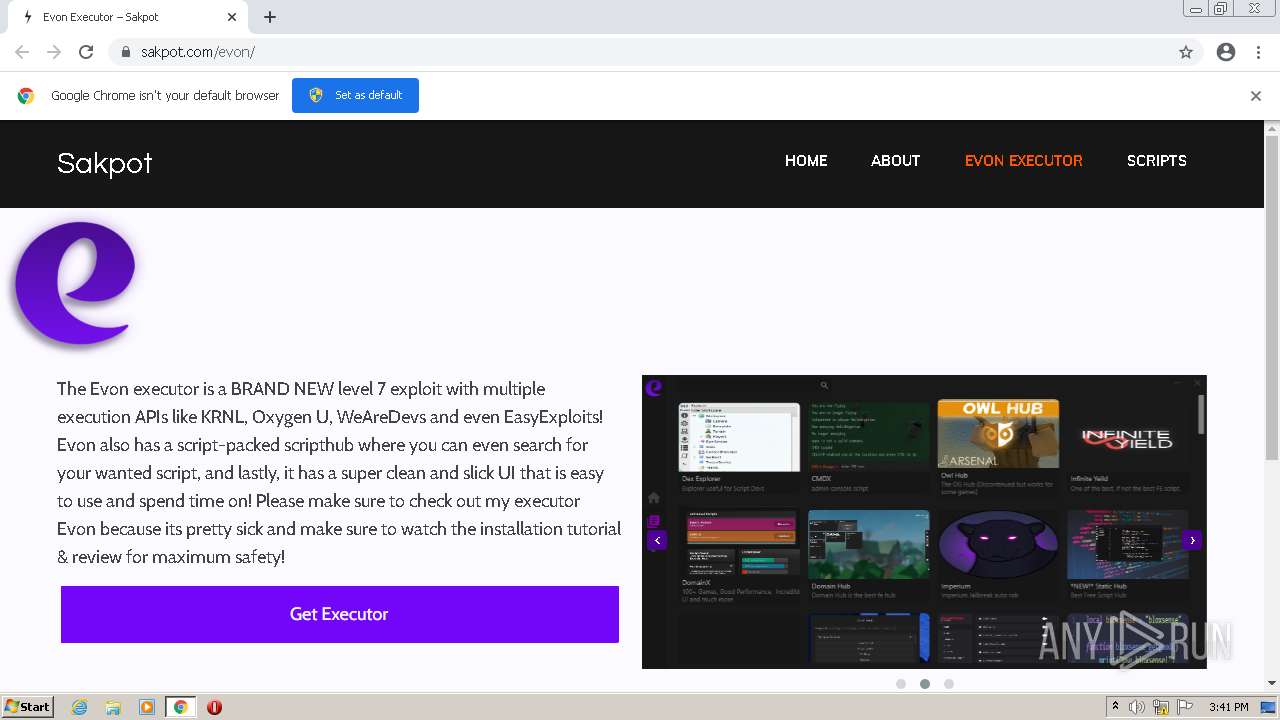
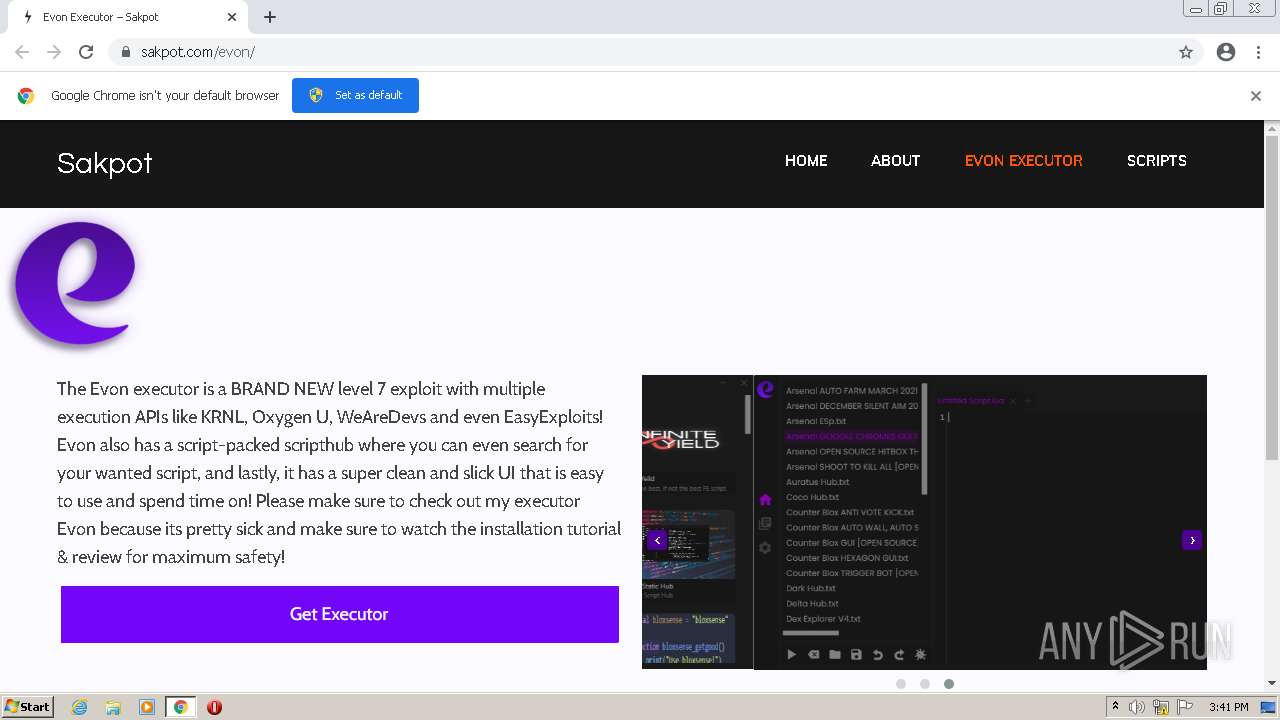
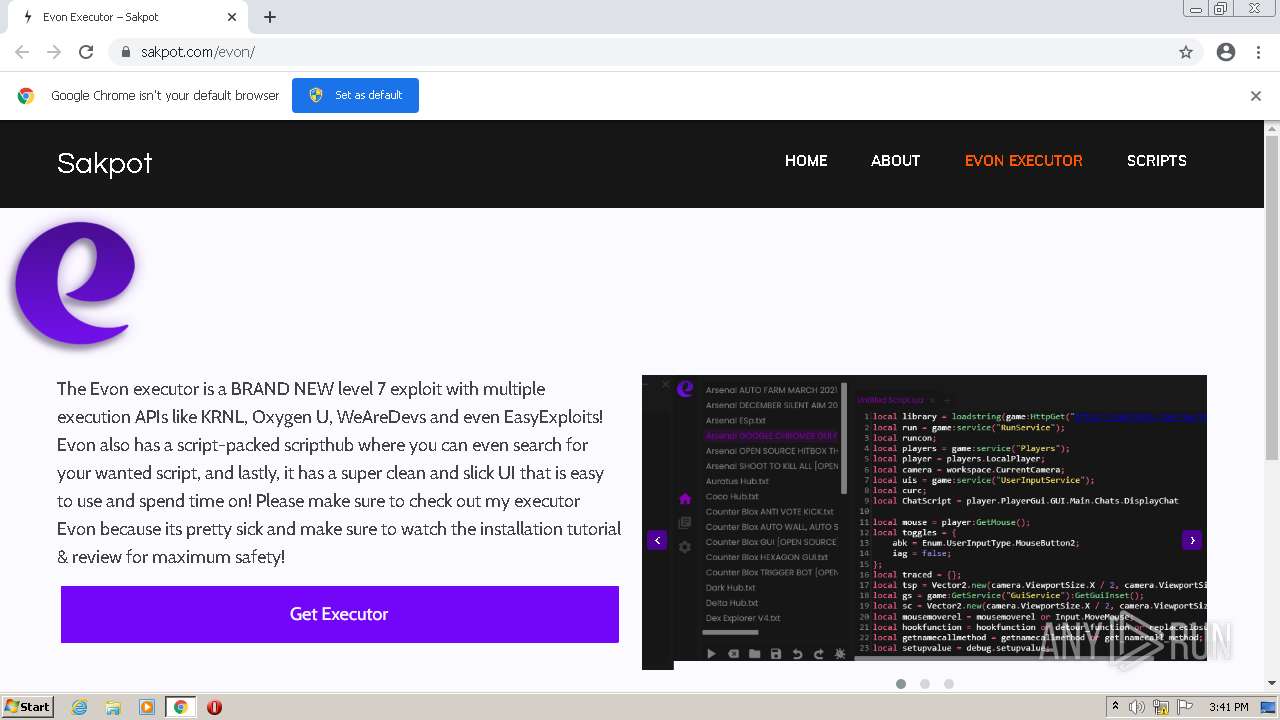
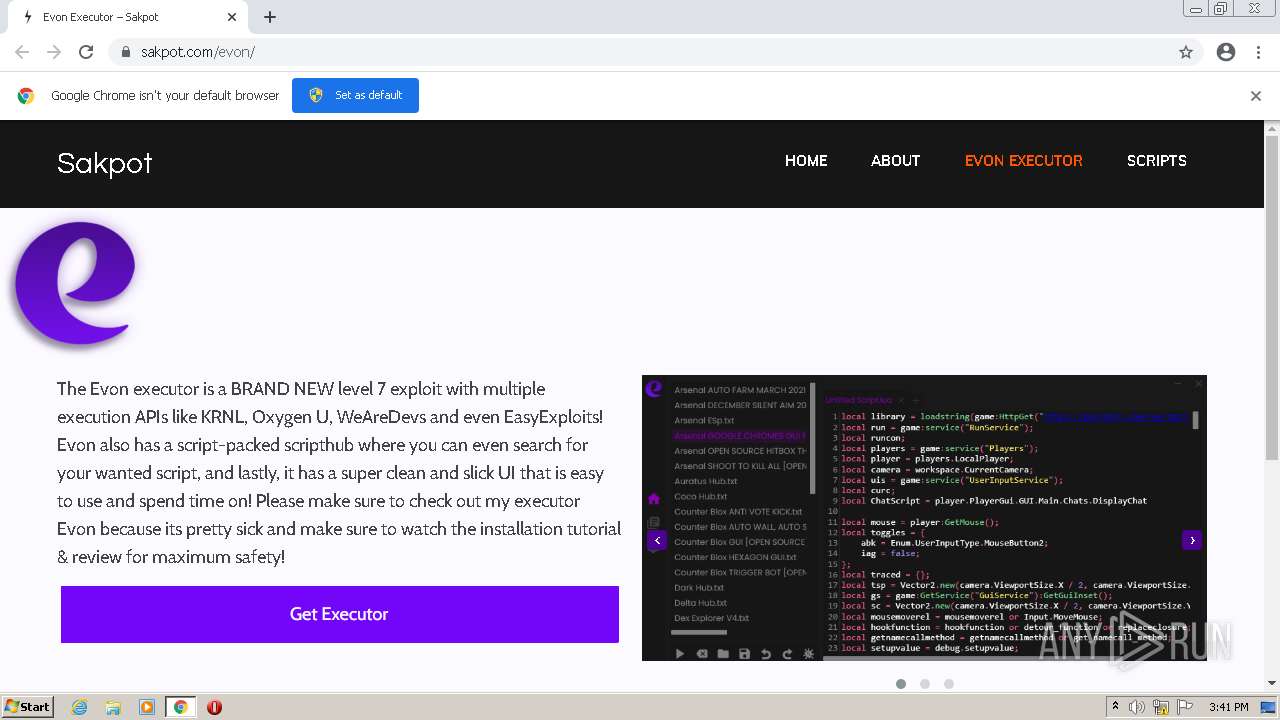
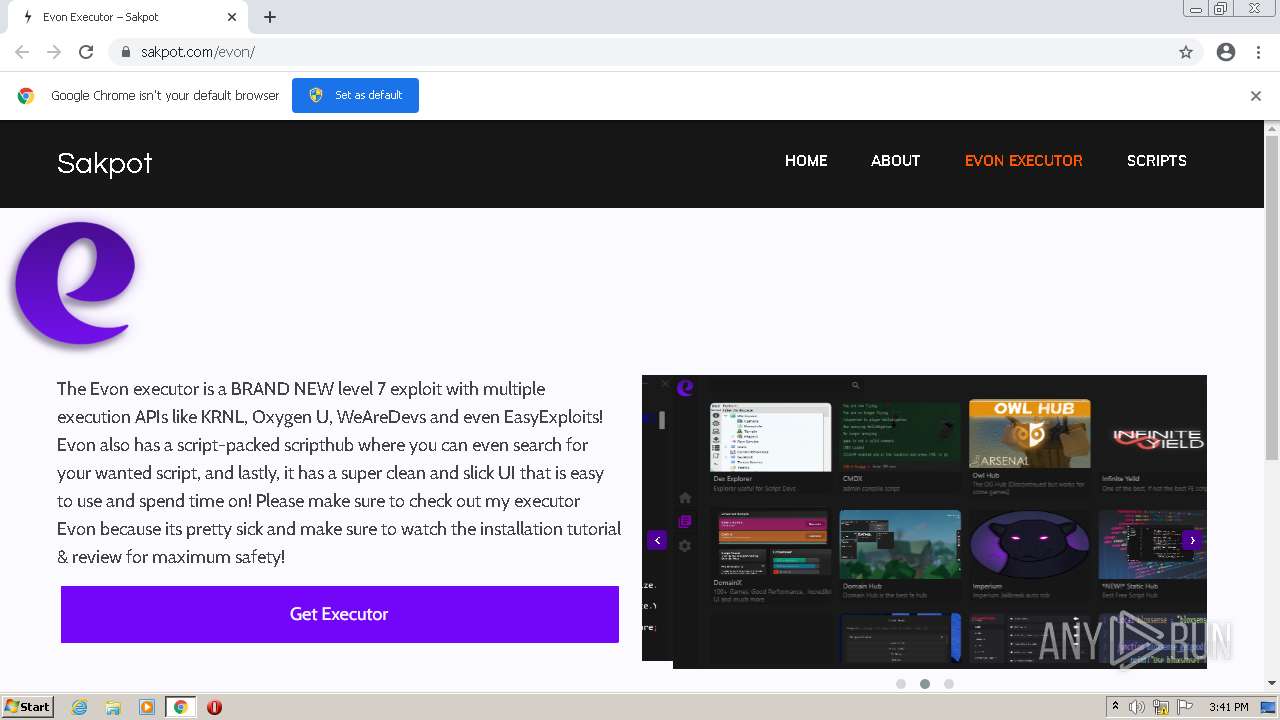
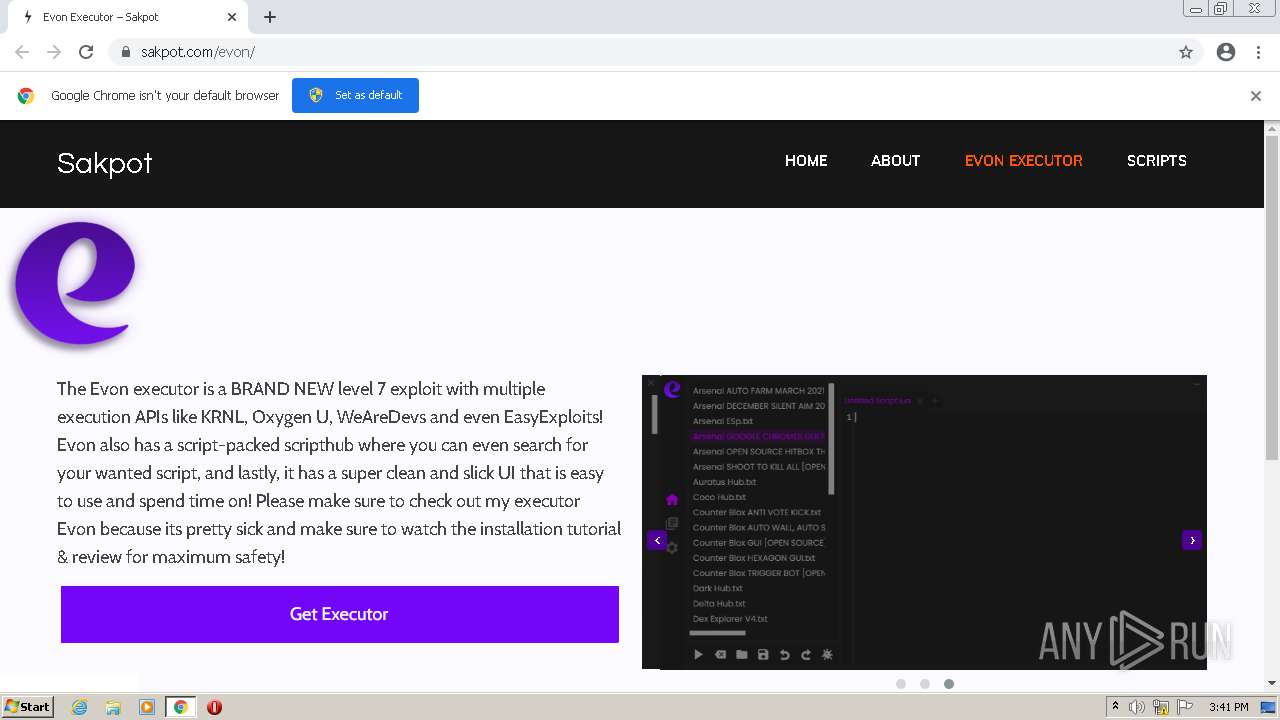
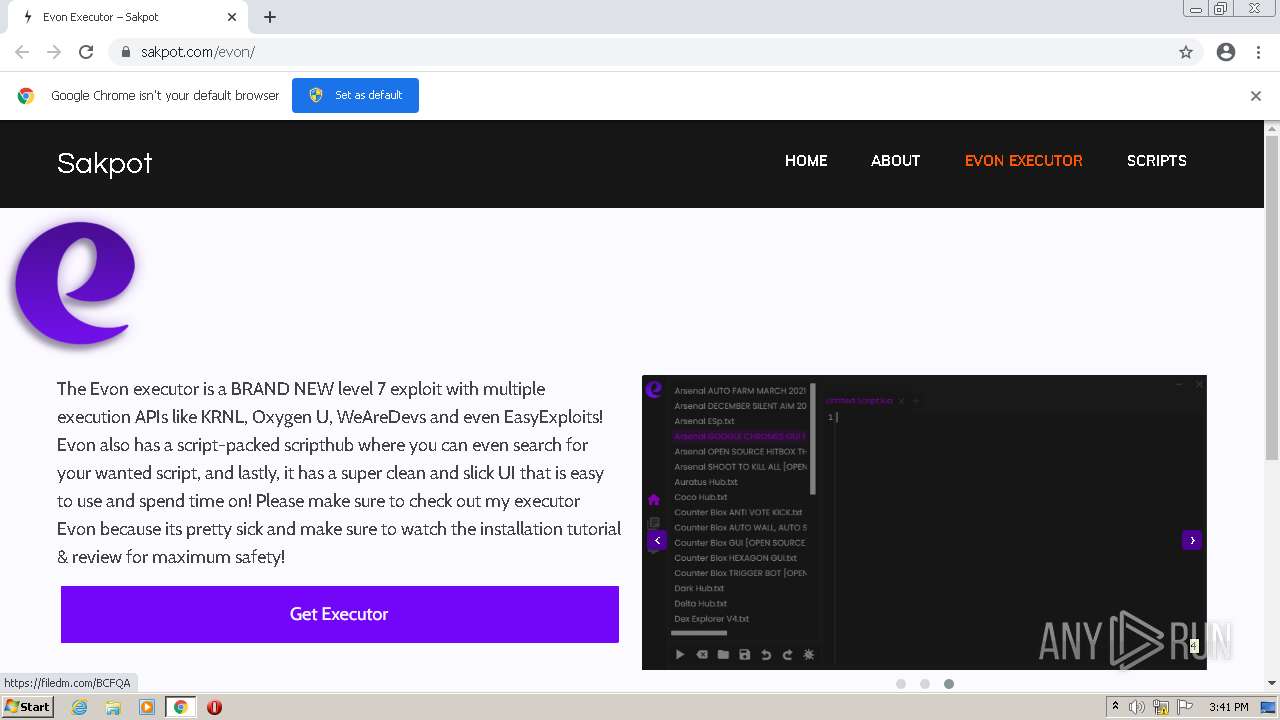
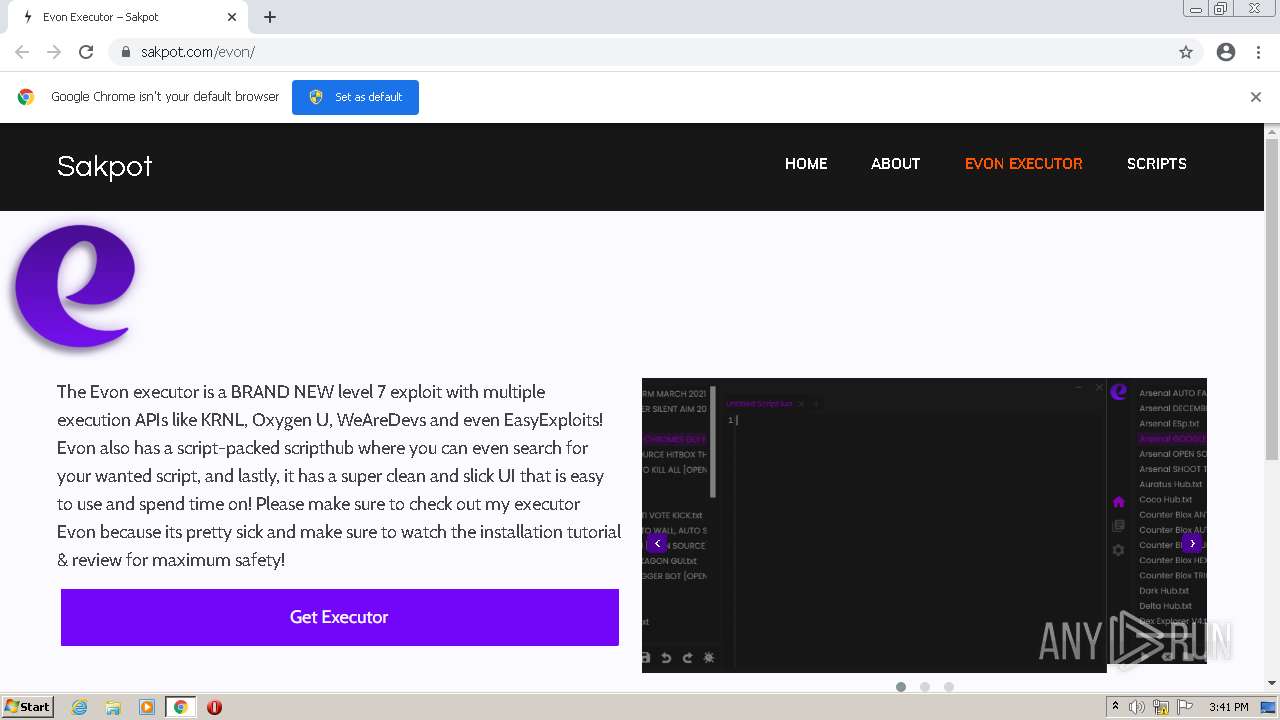
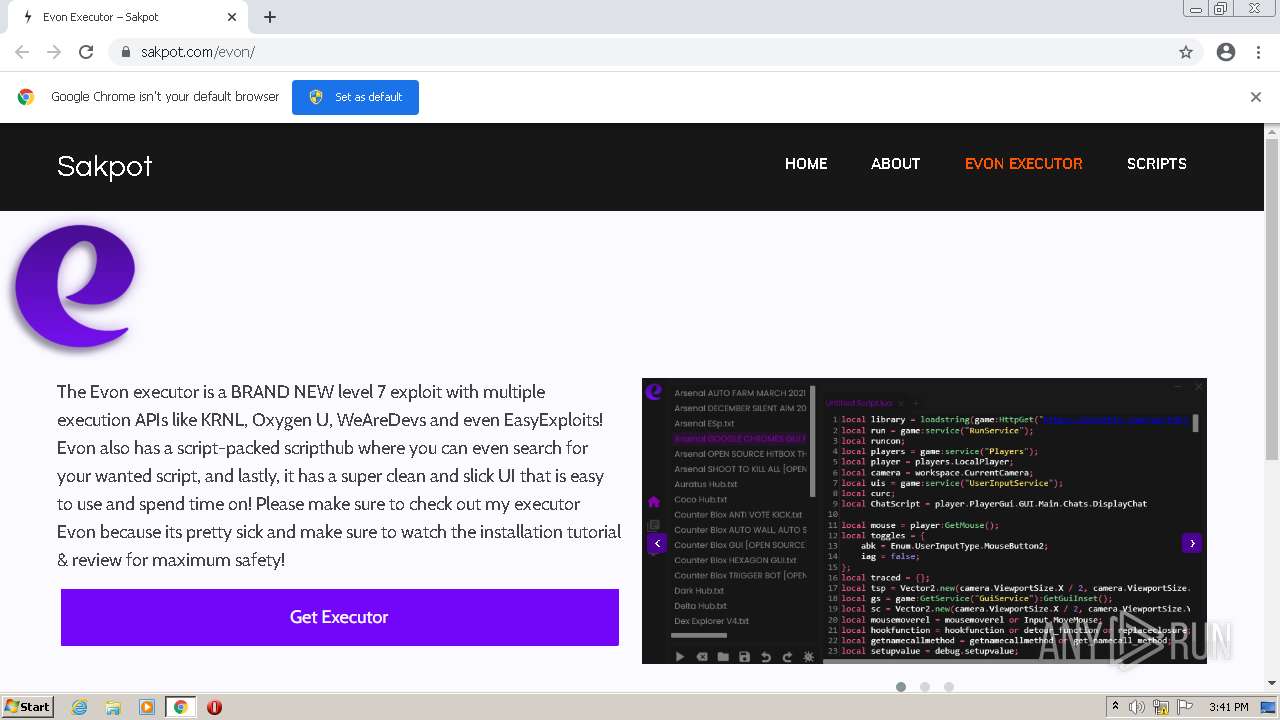
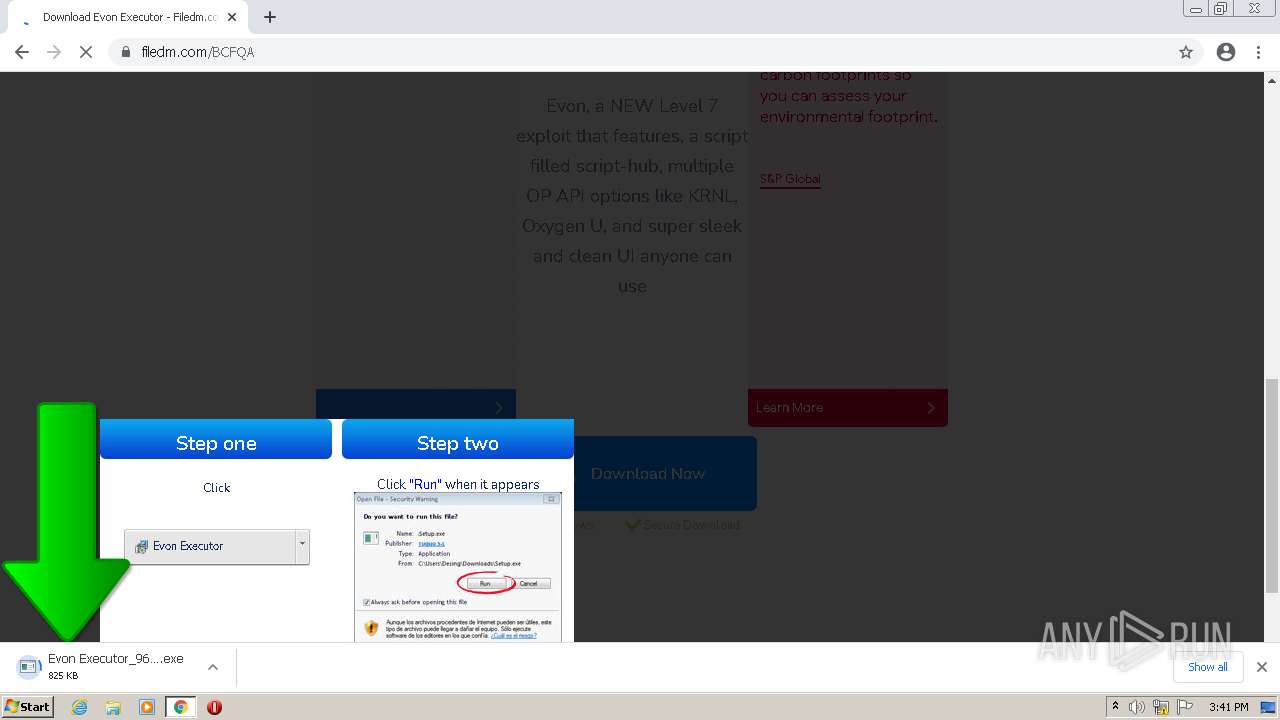
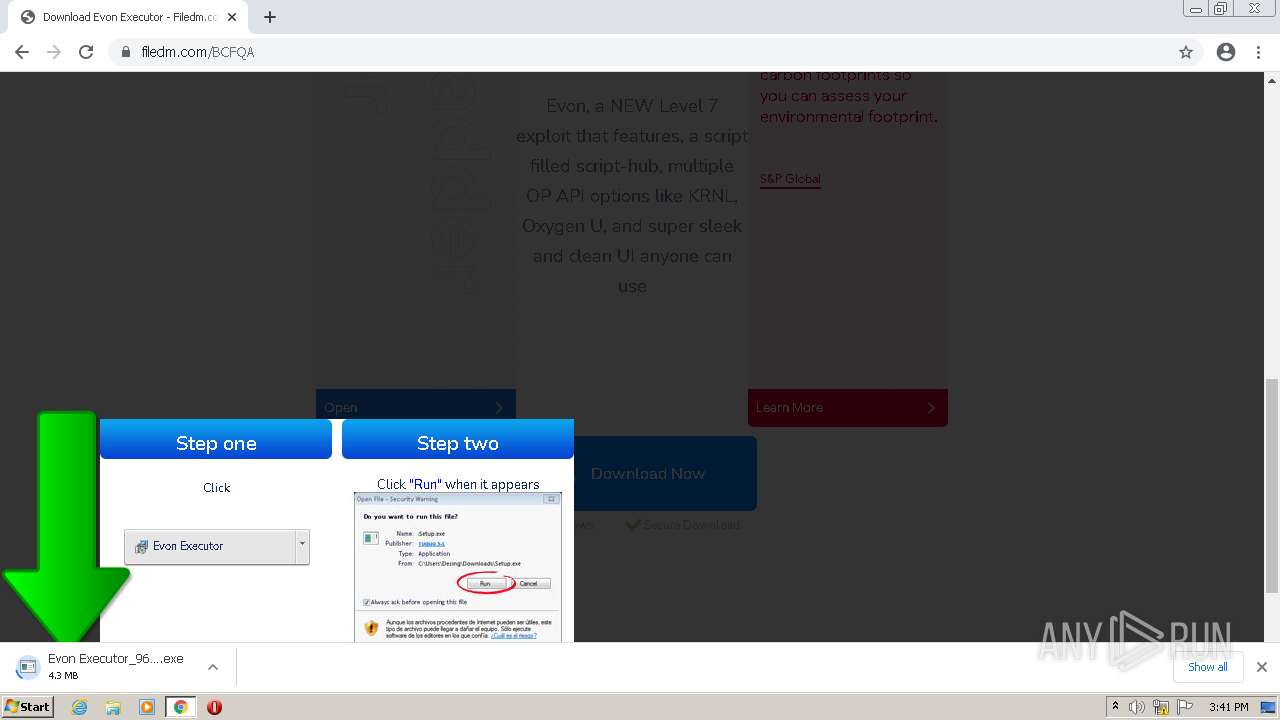
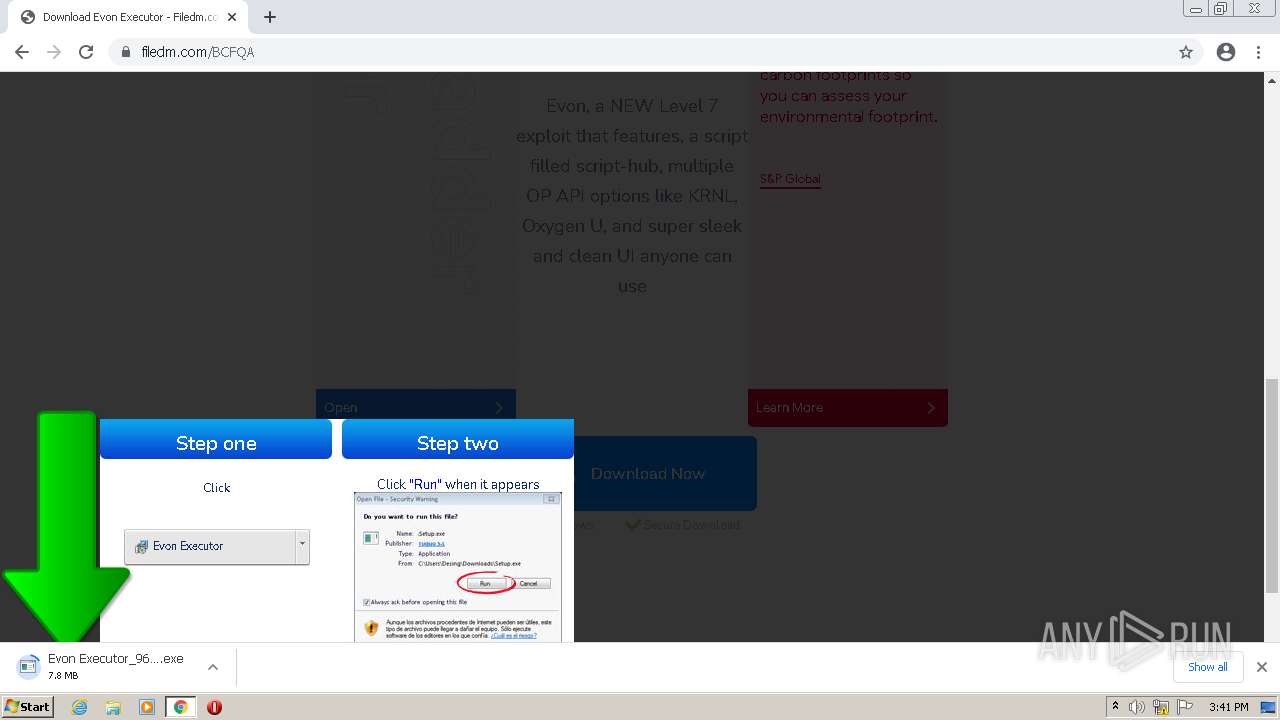
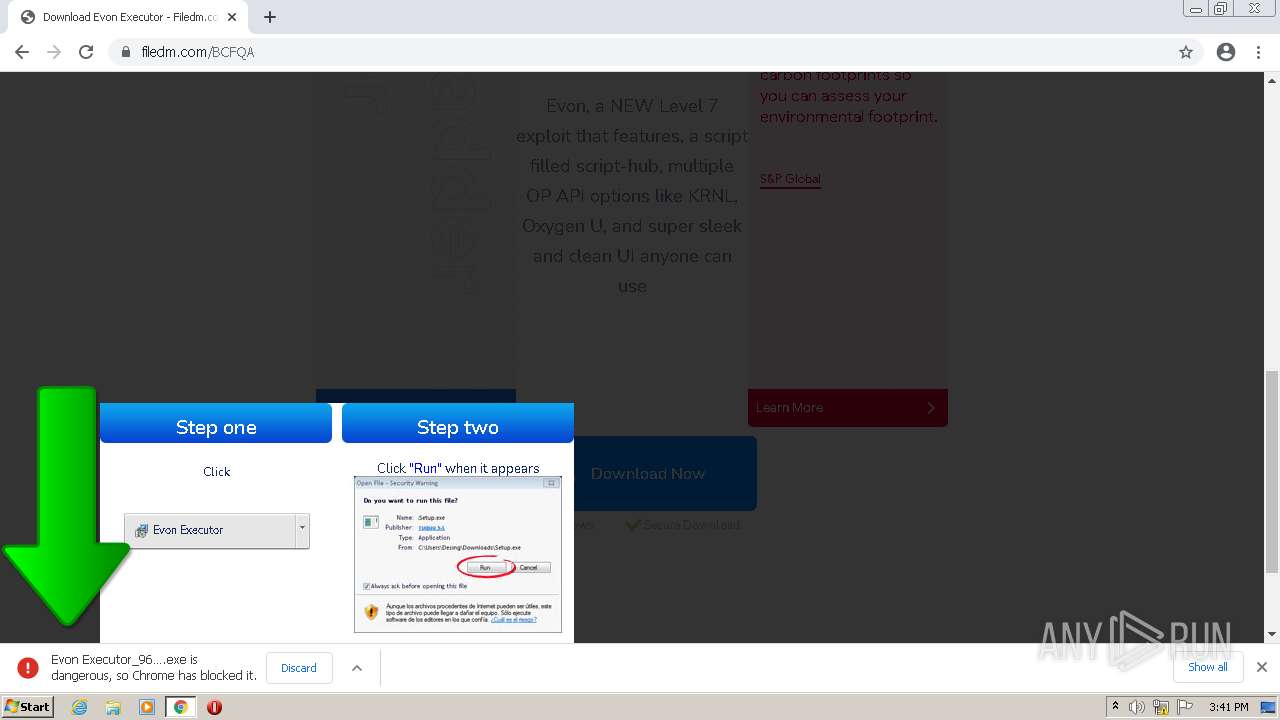
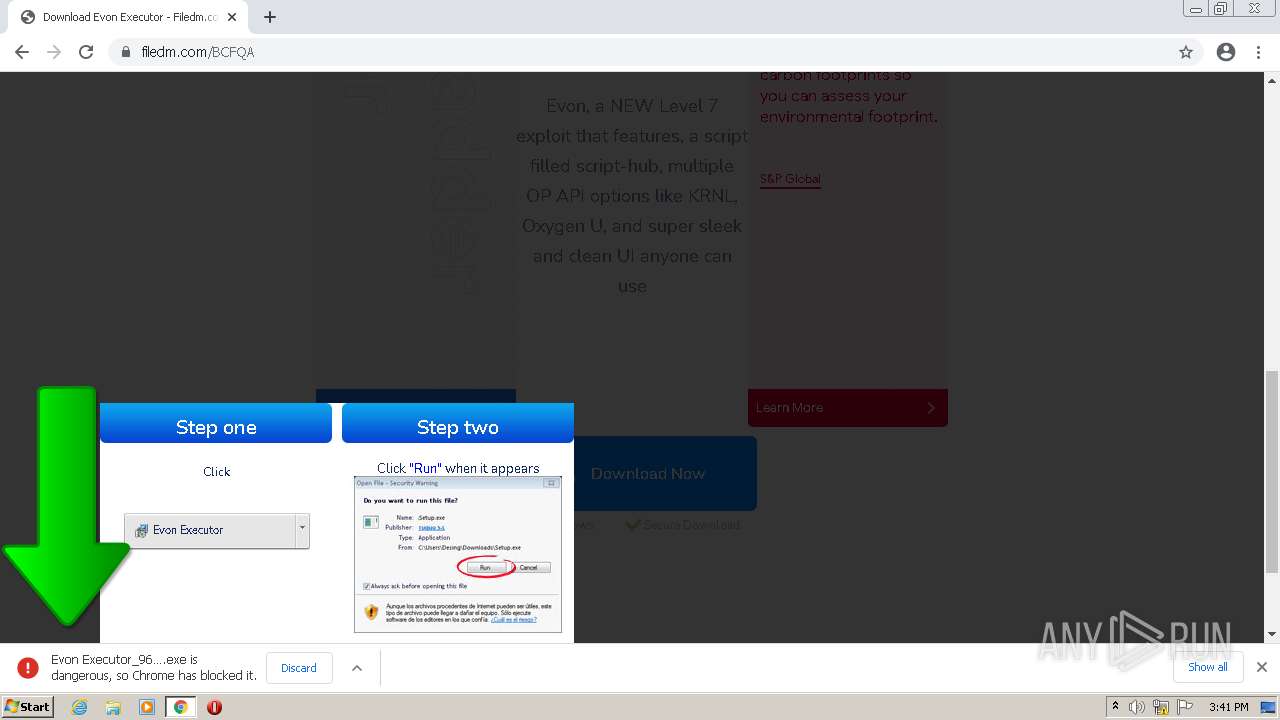
| URL: | https://sakpot.com/evon/ |
| Full analysis: | https://app.any.run/tasks/71a615a5-4a17-40a2-8aca-c38a32a327c1 |
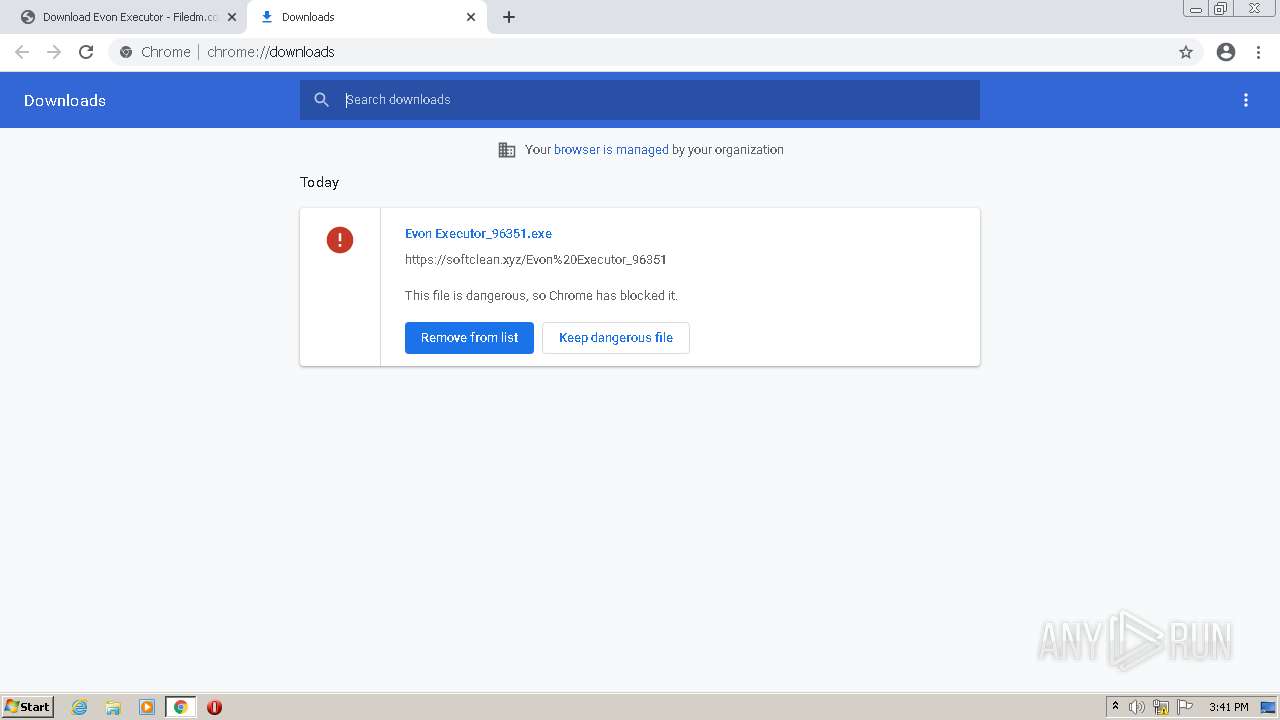
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2022, 15:40:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C4BB566E3905D2E82DB338A1F60872A4 |
| SHA1: | 26A97C12801AE5B95F1BF1ECBBAC3B048A36679F |
| SHA256: | 8A6EA025E430DC57136DDC27418E8233C8843E8BC2B49018FC88E1BBB195FBCB |
| SSDEEP: | 3:N8J6QdIP:2wQKP |
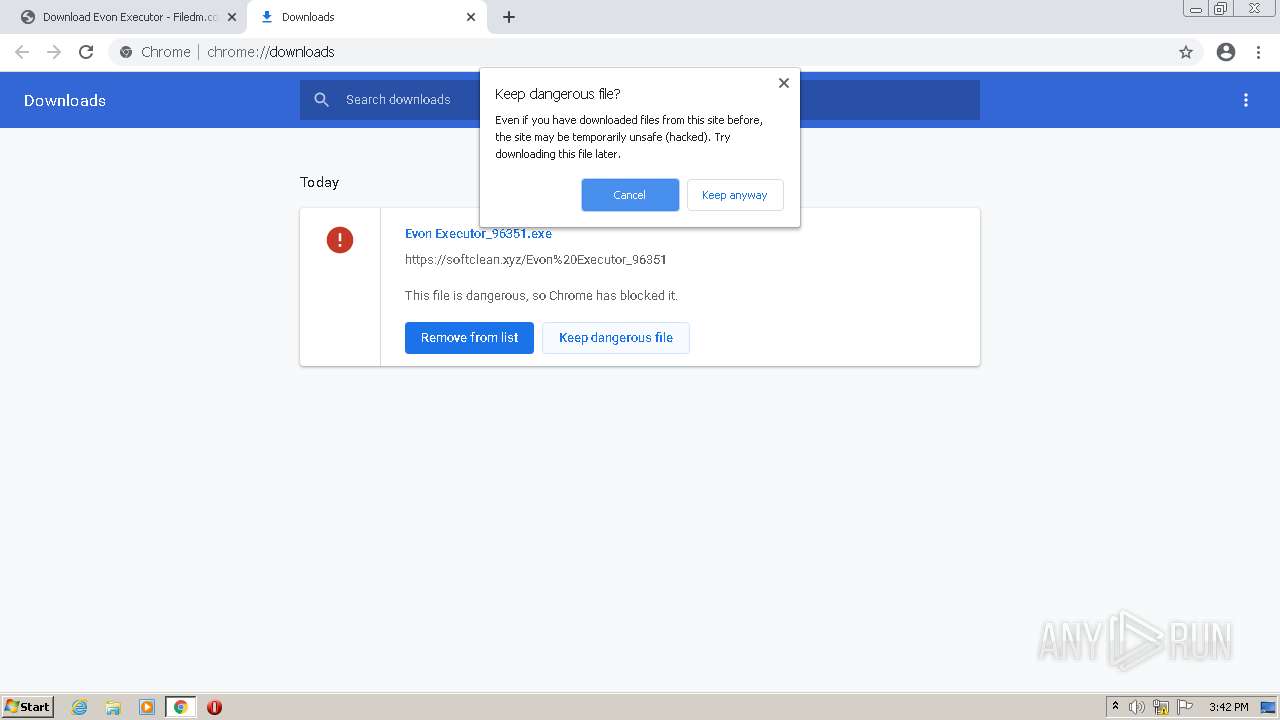
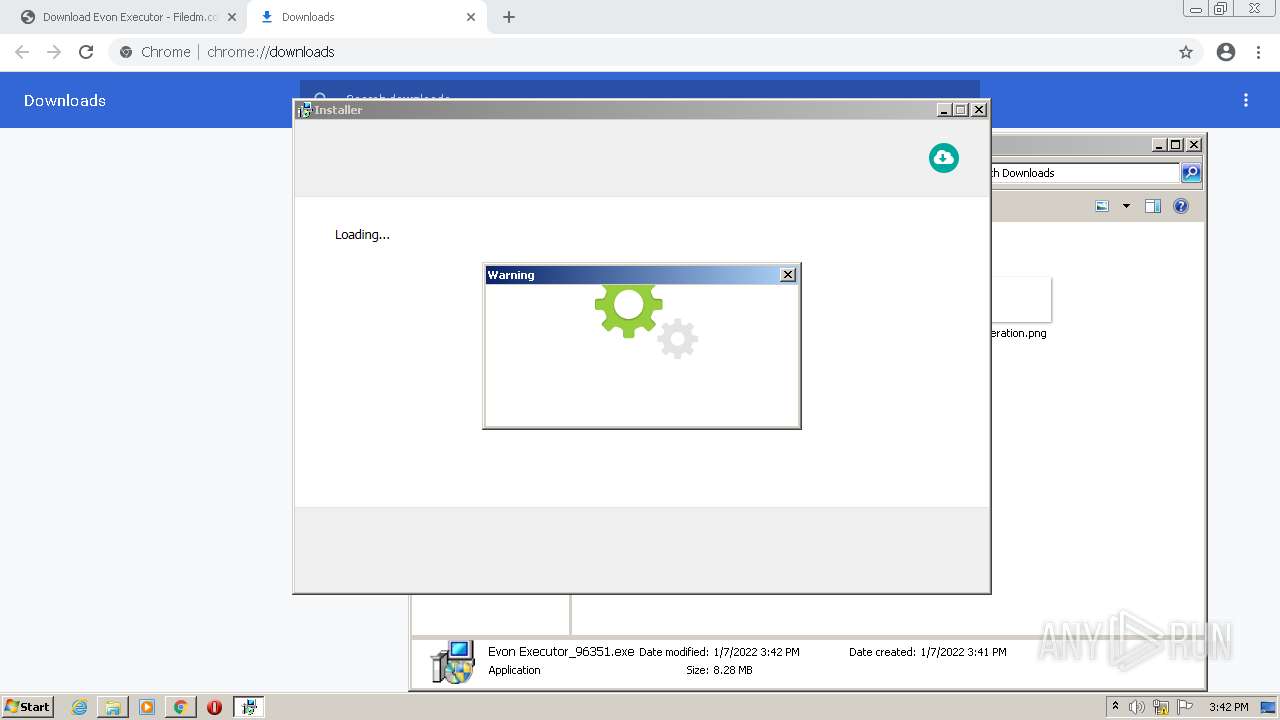
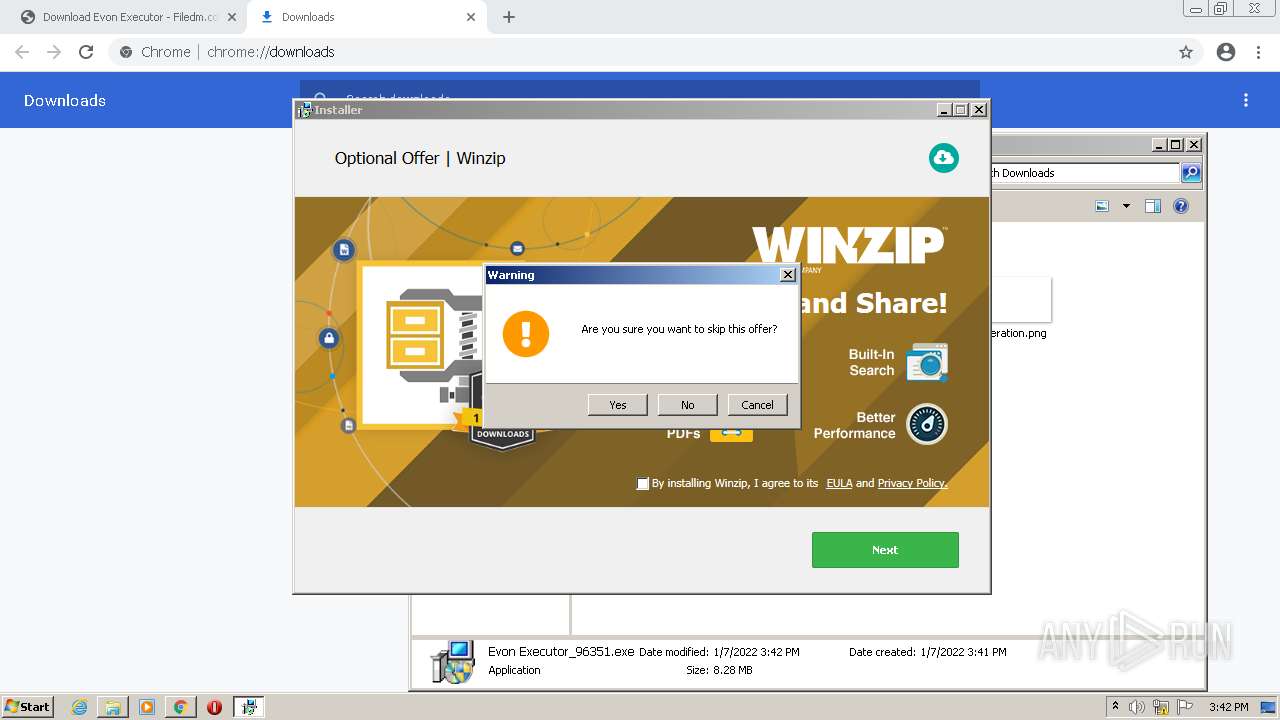
MALICIOUS
Application was dropped or rewritten from another process
- Evon Executor_96351.exe (PID: 1076)
- Evon Executor_96351.exe (PID: 2144)
- setup96351.exe (PID: 1312)
- setup96351.exe (PID: 4020)
- GenericSetup.exe (PID: 2008)
- GenericSetup.exe (PID: 1400)
Drops executable file immediately after starts
- Evon Executor_96351.exe (PID: 2144)
- setup96351.exe (PID: 1312)
- setup96351.exe (PID: 4020)
Changes settings of System certificates
- GenericSetup.exe (PID: 2008)
Actions looks like stealing of personal data
- GenericSetup.exe (PID: 2008)
Loads dropped or rewritten executable
- GenericSetup.exe (PID: 2008)
- GenericSetup.exe (PID: 1400)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3228)
- Evon Executor_96351.exe (PID: 2144)
- setup96351.exe (PID: 1312)
- setup96351.exe (PID: 4020)
Checks supported languages
- Evon Executor_96351.exe (PID: 2144)
- setup96351.exe (PID: 1312)
- GenericSetup.exe (PID: 2008)
- setup96351.exe (PID: 4020)
- GenericSetup.exe (PID: 1400)
Drops a file with a compile date too recent
- Evon Executor_96351.exe (PID: 2144)
- setup96351.exe (PID: 1312)
- setup96351.exe (PID: 4020)
Drops a file with too old compile date
- setup96351.exe (PID: 1312)
- setup96351.exe (PID: 4020)
Reads the computer name
- Evon Executor_96351.exe (PID: 2144)
- GenericSetup.exe (PID: 2008)
- GenericSetup.exe (PID: 1400)
Drops a file that was compiled in debug mode
- setup96351.exe (PID: 1312)
- setup96351.exe (PID: 4020)
Reads the Windows organization settings
- GenericSetup.exe (PID: 2008)
Reads Environment values
- GenericSetup.exe (PID: 2008)
Reads Windows owner or organization settings
- GenericSetup.exe (PID: 2008)
Adds / modifies Windows certificates
- GenericSetup.exe (PID: 2008)
Searches for installed software
- GenericSetup.exe (PID: 2008)
INFO
Reads the hosts file
- chrome.exe (PID: 3228)
- chrome.exe (PID: 3948)
Application launched itself
- chrome.exe (PID: 3228)
Checks supported languages
- chrome.exe (PID: 3948)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 2280)
- chrome.exe (PID: 2460)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 3844)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 3340)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 2344)
- chrome.exe (PID: 2700)
- chrome.exe (PID: 2016)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 1408)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 2152)
- chrome.exe (PID: 272)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 908)
- chrome.exe (PID: 3900)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 1420)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 2508)
Reads the computer name
- chrome.exe (PID: 2776)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 2280)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 1420)
Reads settings of System Certificates
- chrome.exe (PID: 3948)
- chrome.exe (PID: 3228)
- GenericSetup.exe (PID: 2008)
Checks Windows Trust Settings
- chrome.exe (PID: 3228)
- GenericSetup.exe (PID: 2008)
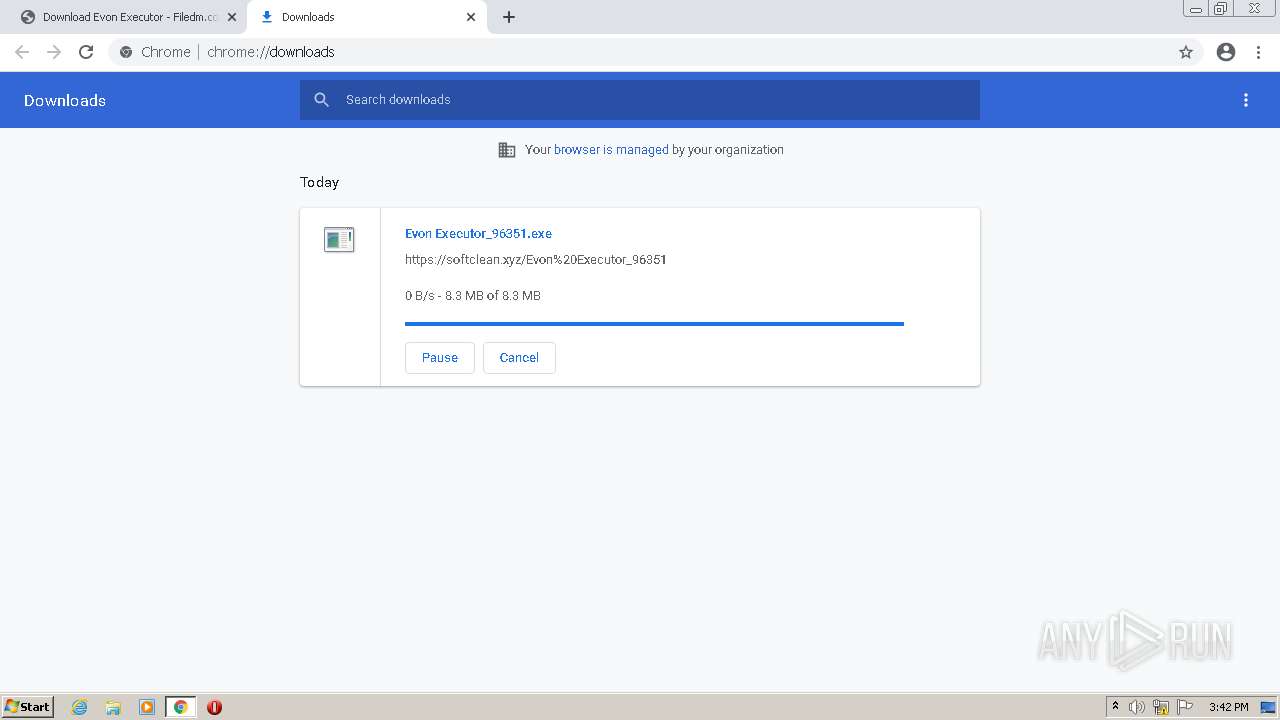
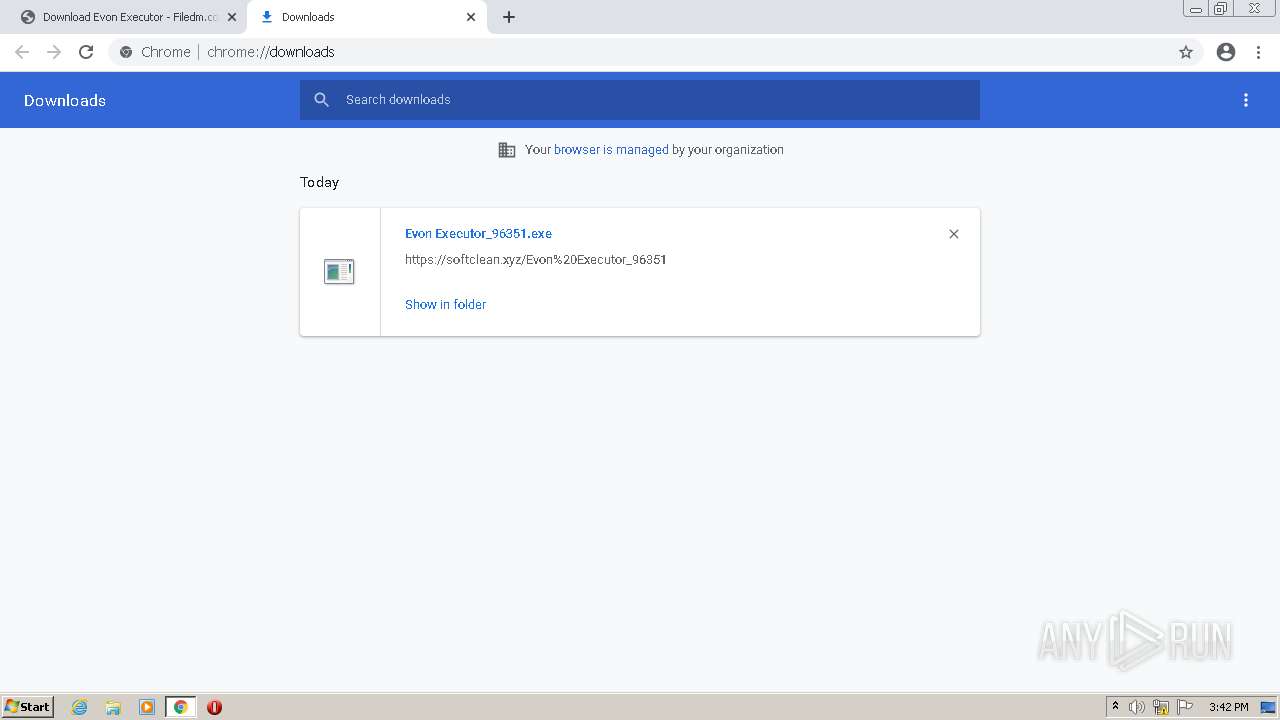
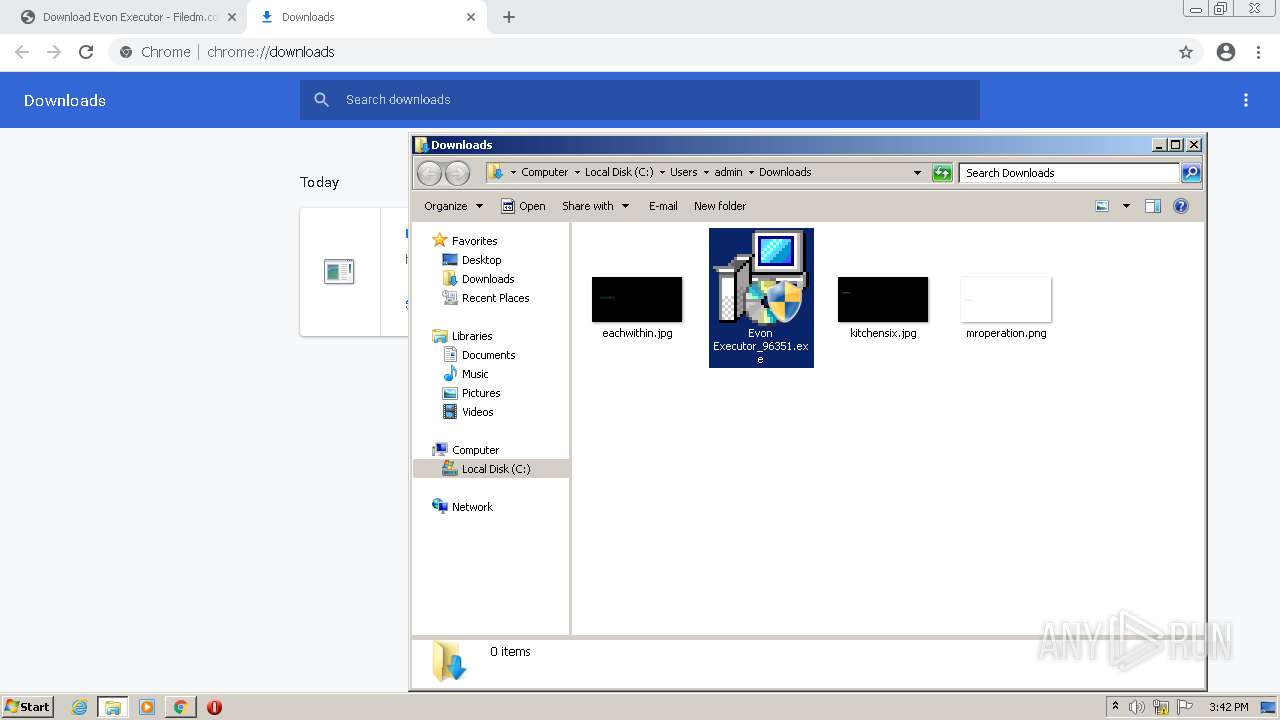
Manual execution by user
- Evon Executor_96351.exe (PID: 1076)
- Evon Executor_96351.exe (PID: 2144)
Reads the date of Windows installation
- chrome.exe (PID: 3360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
34
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1032,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=640 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1076 | "C:\Users\admin\Downloads\Evon Executor_96351.exe" | C:\Users\admin\Downloads\Evon Executor_96351.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1312 | C:\Users\admin\AppData\Local\setup96351.exe hhwnd=131548 hreturntoinstaller hextras=id:<!DOCTYPE html> <html lang=en> <meta charset=utf-8> <meta name=viewport content="initial-scale=1- minimum-scale=1-<!DOCTYPE html> <html lang=en> <meta charset=utf-8> <meta name=viewport content="initial-scale=1, minimum-scale=1, width=device-width"> <title>Error 403 (Forbidden)!!1</title> <style> *{margin:0;padding:0}html,code{font:15px/22px arial,sans-serif}html{background:#fff;color:#222;padding:15px}body{margin:7% auto 0;max-width:390px;min-height:180px;padding:30px 0 15px}* > body{background:url(//www.google.com/images/errors/robot.png) 100% 5px no-repeat;padding-right:205px}p{margin:11px 0 22px;overflow:hidden}ins{color:#777;text-decoration:none}a img{border:0}@media screen and (max-width:772px){body{background:none;margin-top:0;max-width:none;padding-right:0}}#logo{background:url(//www.google.com/images/branding/googlelogo/1x/googlelogo_color_150x54dp.png) no-repeat;margin-left:-5px}@media only screen and (min-resolution:192dpi){#logo{background:url(//www.google.com/images/branding/googlelogo/2x/googlelogo_color_150x54dp.png) no-repeat 0% 0%/100% 100%;-moz-border-image:url(//www.google.com/images/branding/googlelogo/2x/googlelogo_color_150x54dp.png) 0}}@media only screen and (-webkit-min-device-pixel-ratio:2){#logo{background:url(//www.google.com/images/branding/googlelogo/2x/googlelogo_color_150x54dp.png) no-repeat;-webkit-background-size:100% 100%}}#logo{display:inline-block;height:54px;width:150px} </style> <a href=//www.google.com/><span id=logo aria-label=Google></span></a> <p><b>403.</b> <ins>That???s an error.</ins> <p>Your client does not have permission to get URL <code>/callback/info.php</code> from this server. <ins>That???s all we know.</ins> | C:\Users\admin\AppData\Local\setup96351.exe | Evon Executor_96351.exe | ||||||||||||
User: admin Company: DT001 Integrity Level: HIGH Description: Software Installation Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1400 | .\GenericSetup.exe hready | C:\Users\admin\AppData\Local\Temp\7zS4BF12D62\GenericSetup.exe | — | setup96351.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Software Installation Exit code: 1 Version: 2.0.2.5023 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3692 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2008 | .\GenericSetup.exe hhwnd=131548 hreturntoinstaller hextras=id:<!DOCTYPE html> <html lang=en> <meta charset=utf-8> <meta name=viewport content="initial-scale=1- minimum-scale=1-<!DOCTYPE html> <html lang=en> <meta charset=utf-8> <meta name=viewport content="initial-scale=1, minimum-scale=1, width=device-width"> <title>Error 403 (Forbidden)!!1</title> <style> *{margin:0;padding:0}html,code{font:15px/22px arial,sans-serif}html{background:#fff;color:#222;padding:15px}body{margin:7% auto 0;max-width:390px;min-height:180px;padding:30px 0 15px}* > body{background:url(//www.google.com/images/errors/robot.png) 100% 5px no-repeat;padding-right:205px}p{margin:11px 0 22px;overflow:hidden}ins{color:#777;text-decoration:none}a img{border:0}@media screen and (max-width:772px){body{background:none;margin-top:0;max-width:none;padding-right:0}}#logo{background:url(//www.google.com/images/branding/googlelogo/1x/googlelogo_color_150x54dp.png) no-repeat;margin-left:-5px}@media only screen and (min-resolution:192dpi){#logo{background:url(//www.google.com/images/branding/googlelogo/2x/googlelogo_color_150x54dp.png) no-repeat 0% 0%/100% 100%;-moz-border-image:url(//www.google.com/images/branding/googlelogo/2x/googlelogo_color_150x54dp.png) 0}}@media only screen and (-webkit-min-device-pixel-ratio:2){#logo{background:url(//www.google.com/images/branding/googlelogo/2x/googlelogo_color_150x54dp.png) no-repeat;-webkit-background-size:100% 100%}}#logo{display:inline-block;height:54px;width:150px} </style> <a href=//www.google.com/><span id=logo aria-label=Google></span></a> <p><b>403.</b> <ins>That___s an error.</ins> <p>Your client does not have permission to get URL <code>/callback/info.php</code> from this server. <ins>That___s all we know.</ins> | C:\Users\admin\AppData\Local\Temp\7zS025B2F42\GenericSetup.exe | setup96351.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Software Installation Exit code: 0 Version: 2.0.2.5023 Modules
| |||||||||||||||
| 2016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
39 815
Read events
39 573
Write events
236
Delete events
6
Modification events
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
38
Suspicious files
30
Text files
114
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61D85F0C-C9C.pma | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cc03bc7f-2084-4b3b-91b4-5848076964a5.tmp | text | |
MD5:— | SHA256:— | |||
| 3340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\606d21de-2129-44ba-8c3d-e21f5881481b.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF113313.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF112c6c.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF112c4d.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
81
DNS requests
46
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
2144 | Evon Executor_96351.exe | POST | 403 | 35.190.60.70:80 | http://dlsft.com/callback/geo/geo.php | US | html | 1.56 Kb | malicious |
2144 | Evon Executor_96351.exe | GET | 403 | 35.190.60.70:80 | http://dlsft.com/callback/offers.php | US | html | 1.56 Kb | malicious |
2144 | Evon Executor_96351.exe | GET | 403 | 35.190.60.70:80 | http://dlsft.com/callback/info.php?id=96351 | US | html | 1.56 Kb | malicious |
3948 | chrome.exe | GET | 200 | 67.26.137.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?86f17d38d408d1b2 | US | compressed | 59.9 Kb | whitelisted |
860 | svchost.exe | HEAD | 302 | 142.250.185.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 172.67.183.248:443 | sakpot.com | — | US | unknown |
3948 | chrome.exe | 172.67.183.248:443 | sakpot.com | — | US | unknown |
3948 | chrome.exe | 18.66.188.206:443 | d2u2lv2h6u18yc.cloudfront.net | Massachusetts Institute of Technology | US | unknown |
3948 | chrome.exe | 142.250.185.136:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3948 | chrome.exe | 142.250.184.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 142.250.184.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 18.66.188.78:443 | dhrhzii89gpwo.cloudfront.net | Massachusetts Institute of Technology | US | unknown |
3948 | chrome.exe | 185.60.216.35:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
3948 | chrome.exe | 104.21.45.207:443 | freychang.fun | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
sakpot.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
dhrhzii89gpwo.cloudfront.net |
| suspicious |
fonts.gstatic.com |
| whitelisted |
d2u2lv2h6u18yc.cloudfront.net |
| suspicious |
s.w.org |
| whitelisted |
freychang.fun |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .work TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .work TLD |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
GenericSetup.exe | Error: File not found - genericsetup.wrappers.sciter:console.tis
|
GenericSetup.exe | at sciter:init-script.tis
|
GenericSetup.exe | |
GenericSetup.exe | |
GenericSetup.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|
GenericSetup.exe | Error: (undefined) has no property - String("Cancel")
|
GenericSetup.exe | at CancelRequestCallBack (file:resources/tis/EventHandler.tis(279))
|
GenericSetup.exe | |
GenericSetup.exe |