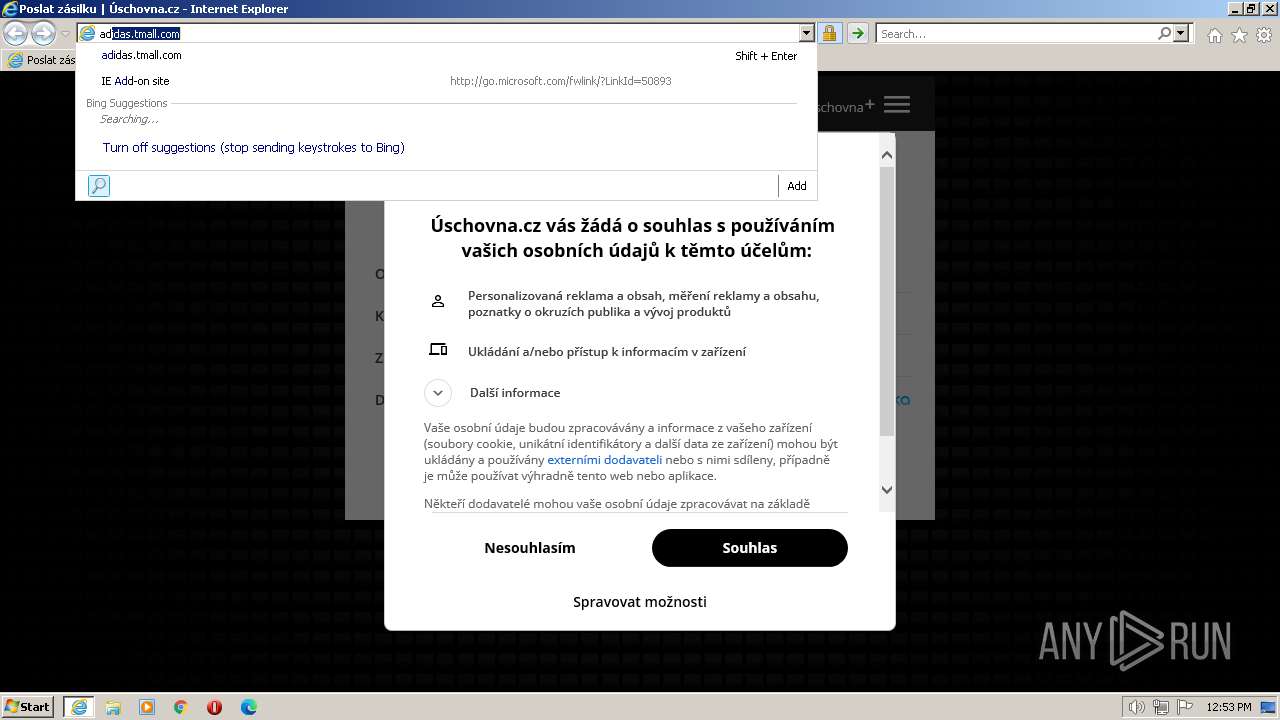
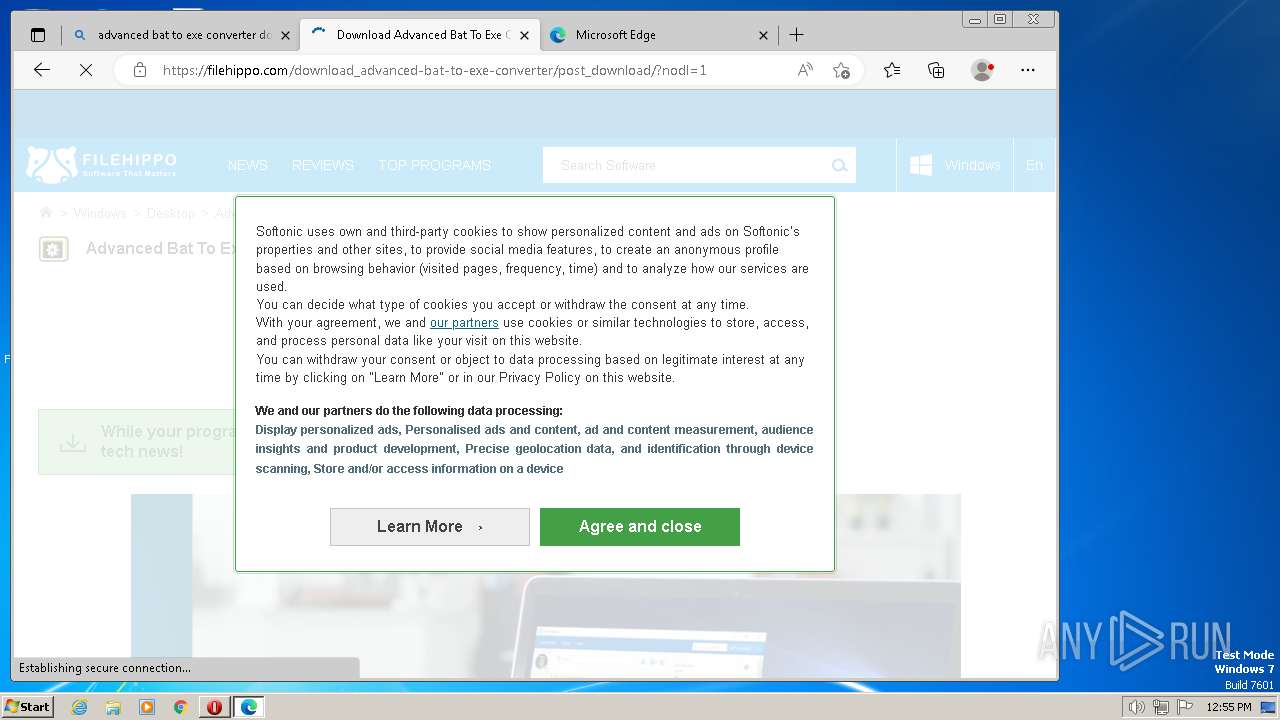
| URL: | https://www.uschovna.cz/poslat-zasilku |
| Full analysis: | https://app.any.run/tasks/32126cda-6962-44c6-b1ec-87db7fc24f66 |
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2023, 11:53:31 |
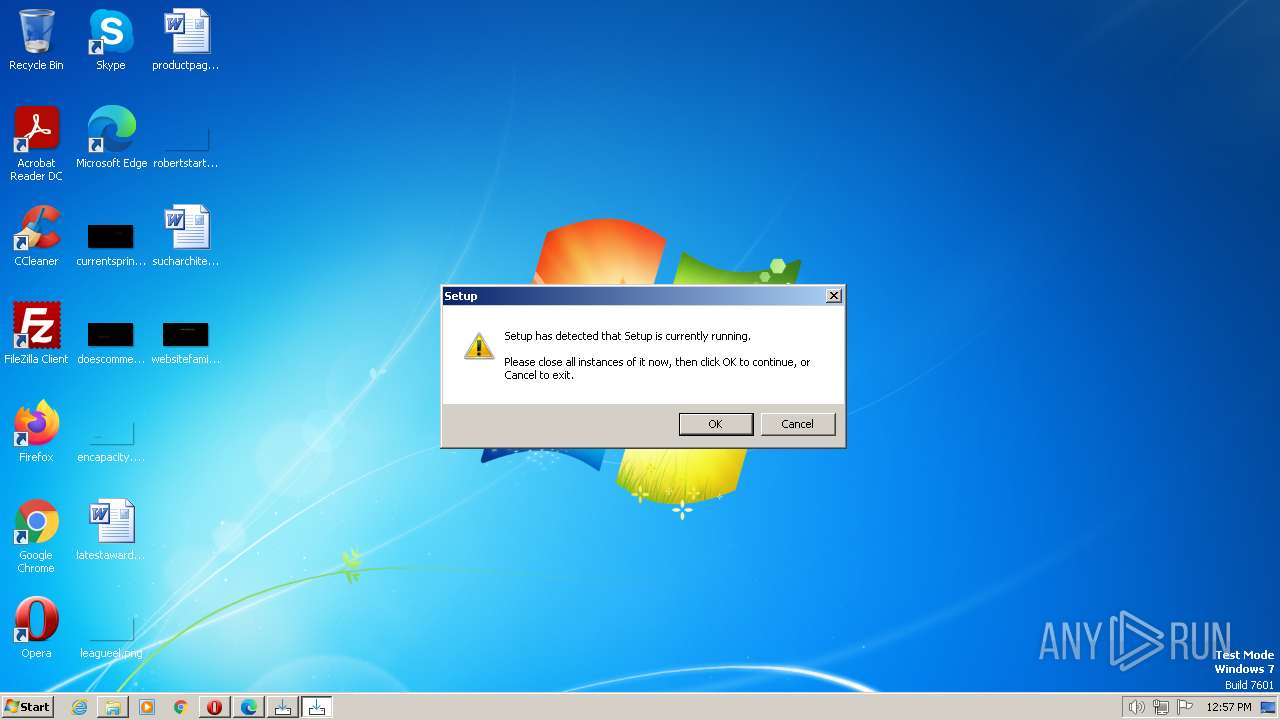
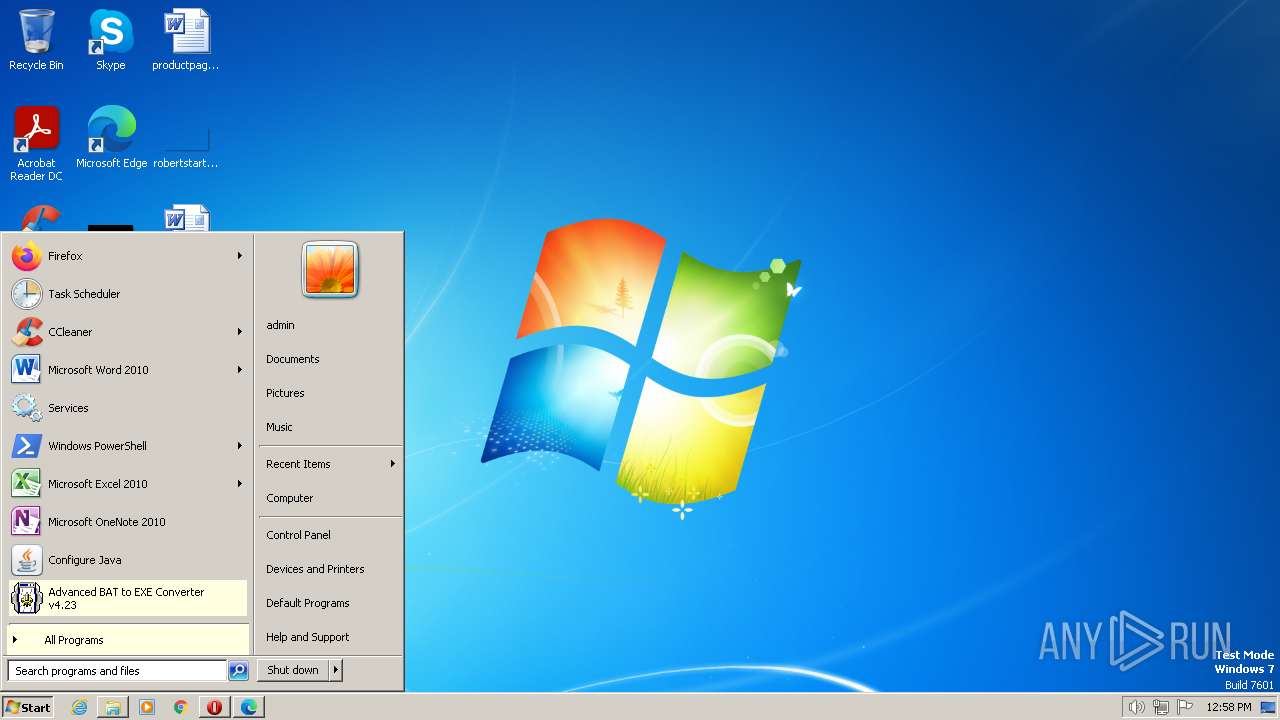
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BD23A7DB2CBDD447F1F8F2DFDD6746EF |
| SHA1: | 081FB594DF0AF6B524C84761BA828D012797CFC8 |
| SHA256: | 8A6322A5CB39F6A853B962F772C2E1DAAADA559AAFFA32872E253B196C839B68 |
| SSDEEP: | 3:N8DSLG2tt1:2OLGAL |
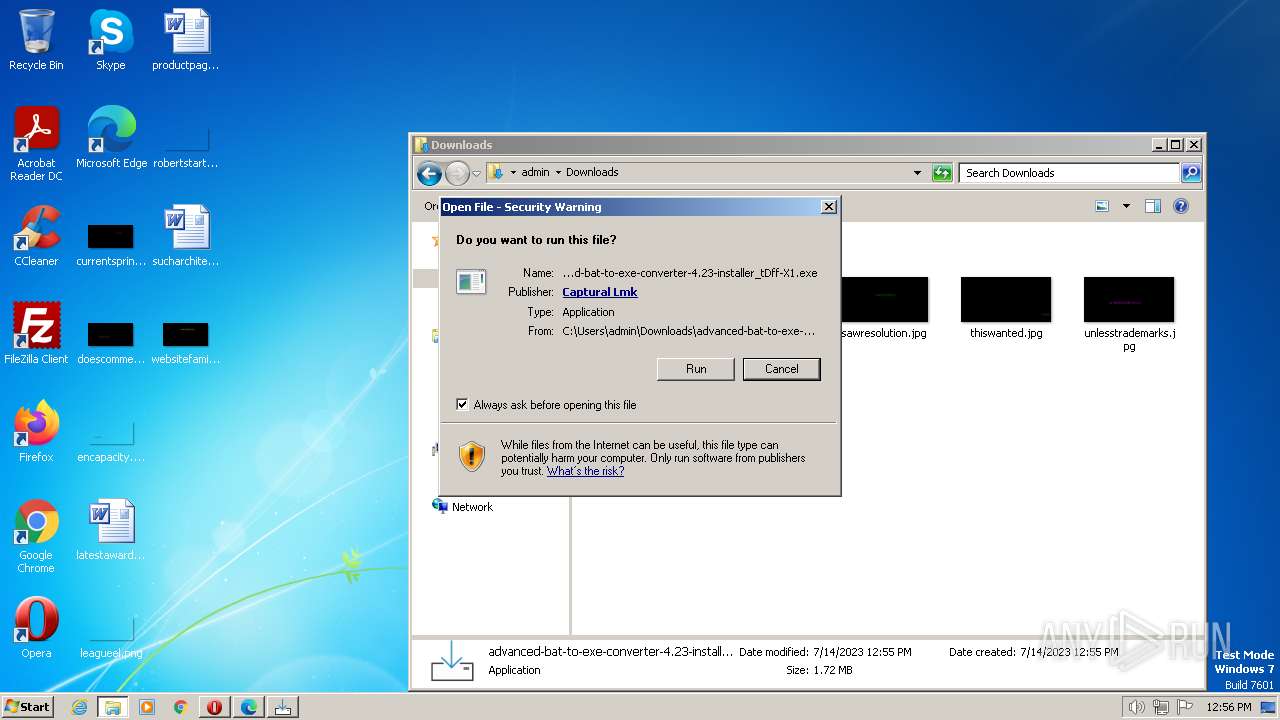
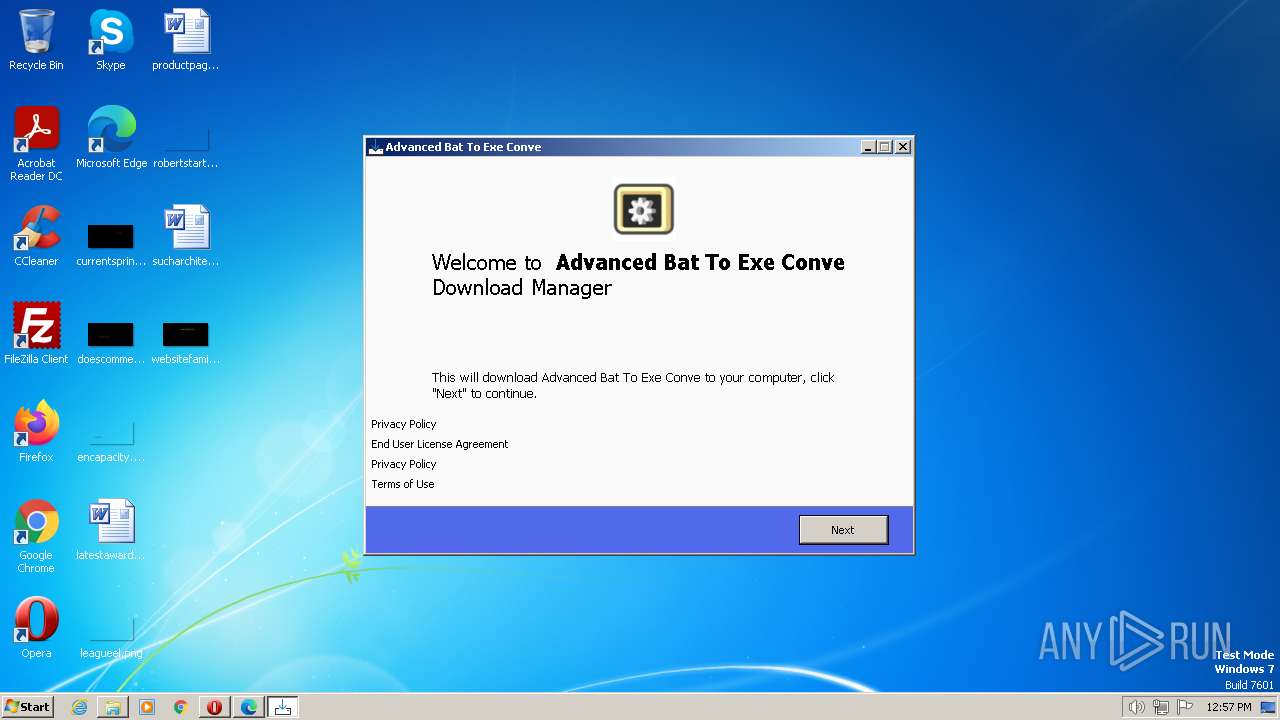
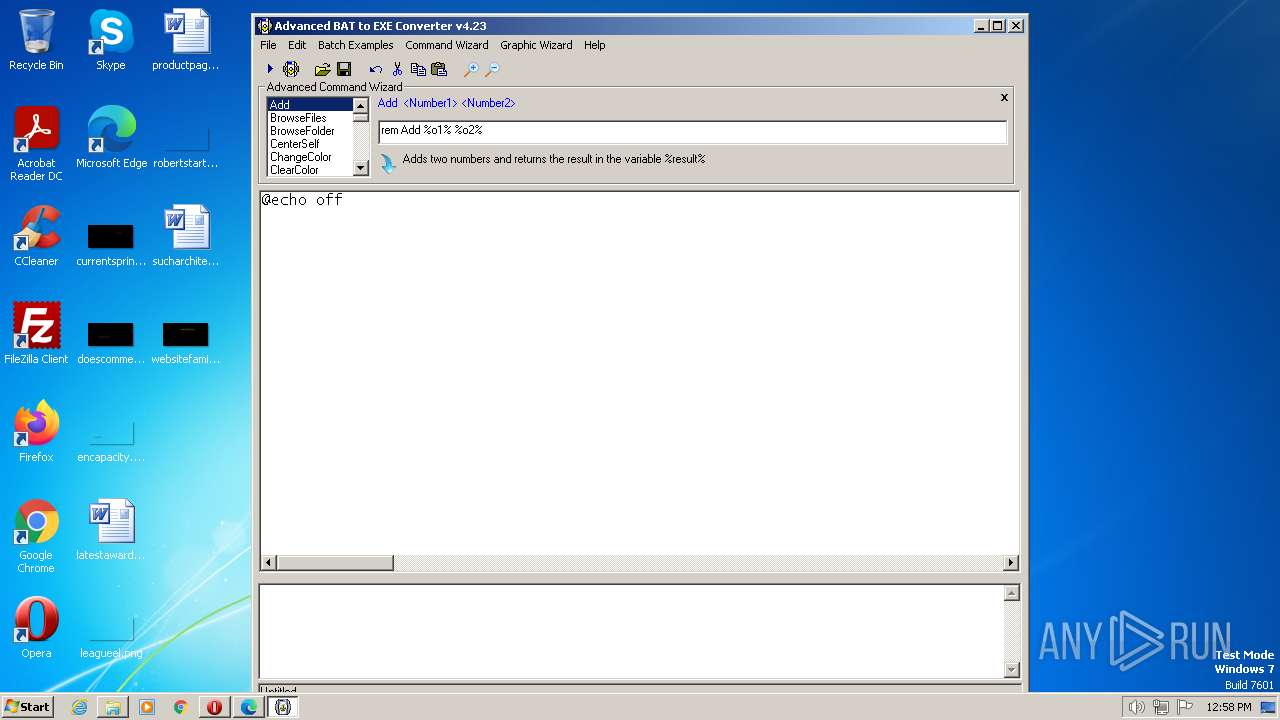
MALICIOUS
Application was dropped or rewritten from another process
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 856)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 3028)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 4036)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 2868)
- saBSI.exe (PID: 2984)
- advanced-bat-to-exe-converter-4.23-installer.exe (PID: 680)
- setupinf.exe (PID: 3740)
- aB2Econv.exe (PID: 3664)
Loads dropped or rewritten executable
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3788)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 1188)
- advanced-bat-to-exe-converter-4.23-installer.exe (PID: 680)
- aB2Econv.exe (PID: 3664)
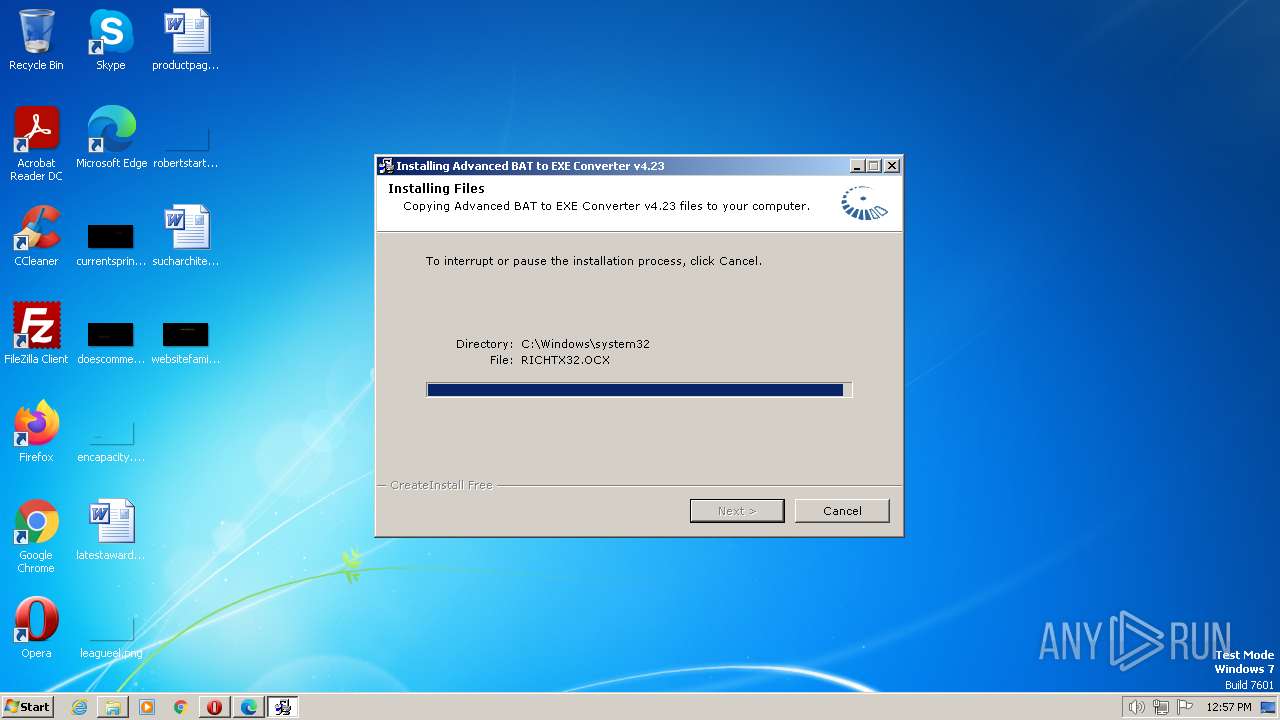
Creates a writable file the system directory
- advanced-bat-to-exe-converter-4.23-installer.exe (PID: 680)
SUSPICIOUS
Reads the Internet Settings
- cookie_exporter.exe (PID: 2604)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3788)
- saBSI.exe (PID: 2984)
Executable content was dropped or overwritten
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 856)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 3028)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3788)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 2868)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 4036)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 1188)
- advanced-bat-to-exe-converter-4.23-installer.exe (PID: 680)
Reads the Windows owner or organization settings
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3788)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 1188)
Reads settings of System Certificates
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3788)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 1188)
- saBSI.exe (PID: 2984)
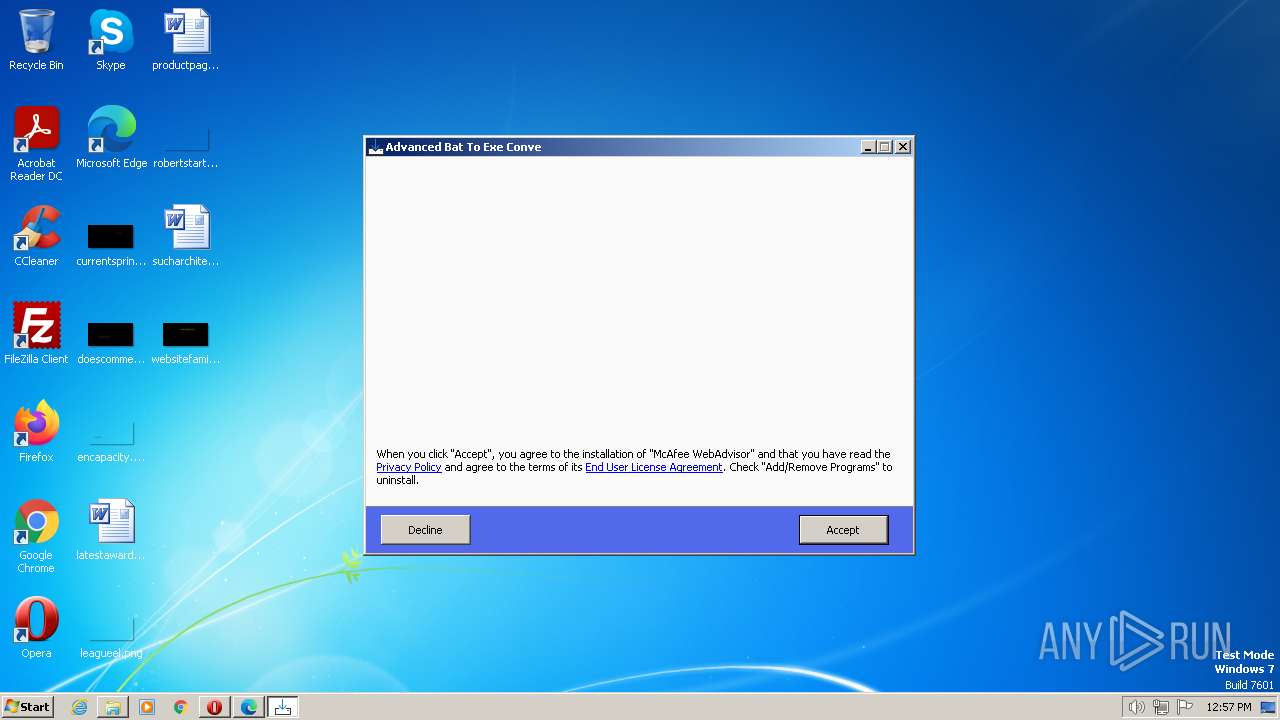
Adds/modifies Windows certificates
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 3028)
The process creates files with name similar to system file names
- advanced-bat-to-exe-converter-4.23-installer.exe (PID: 680)
Checks Windows Trust Settings
- saBSI.exe (PID: 2984)
Reads security settings of Internet Explorer
- saBSI.exe (PID: 2984)
INFO
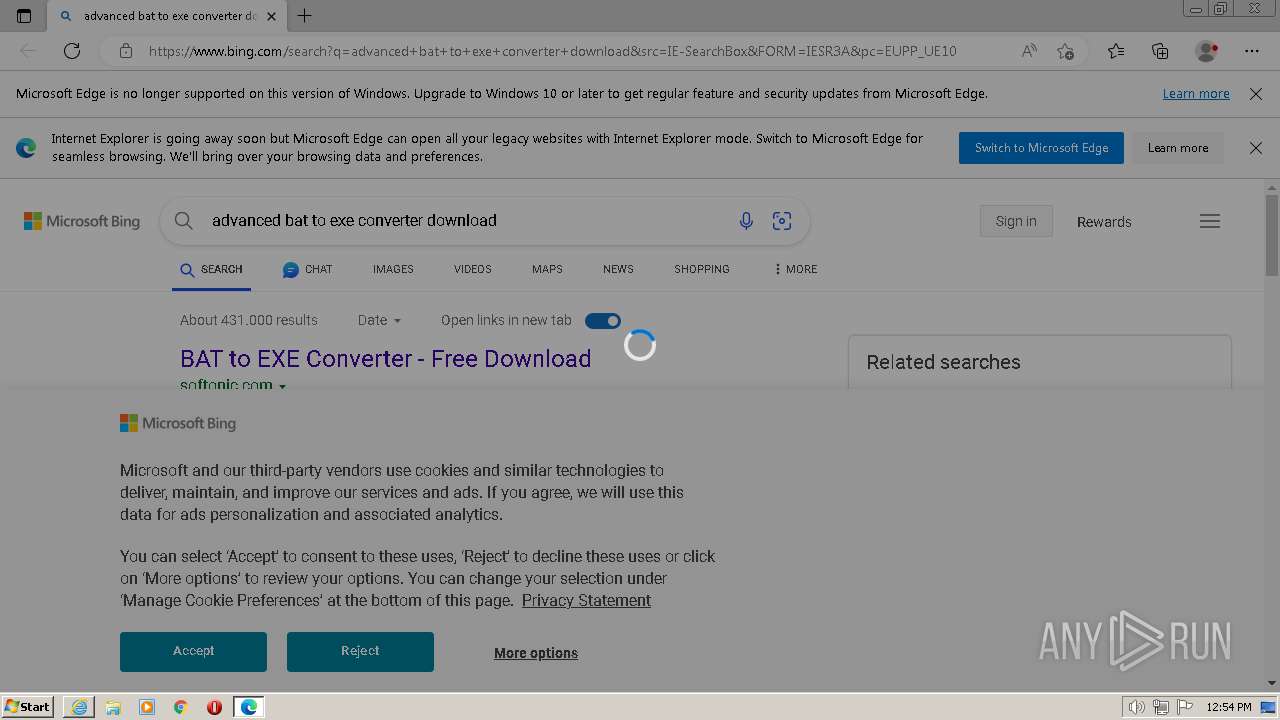
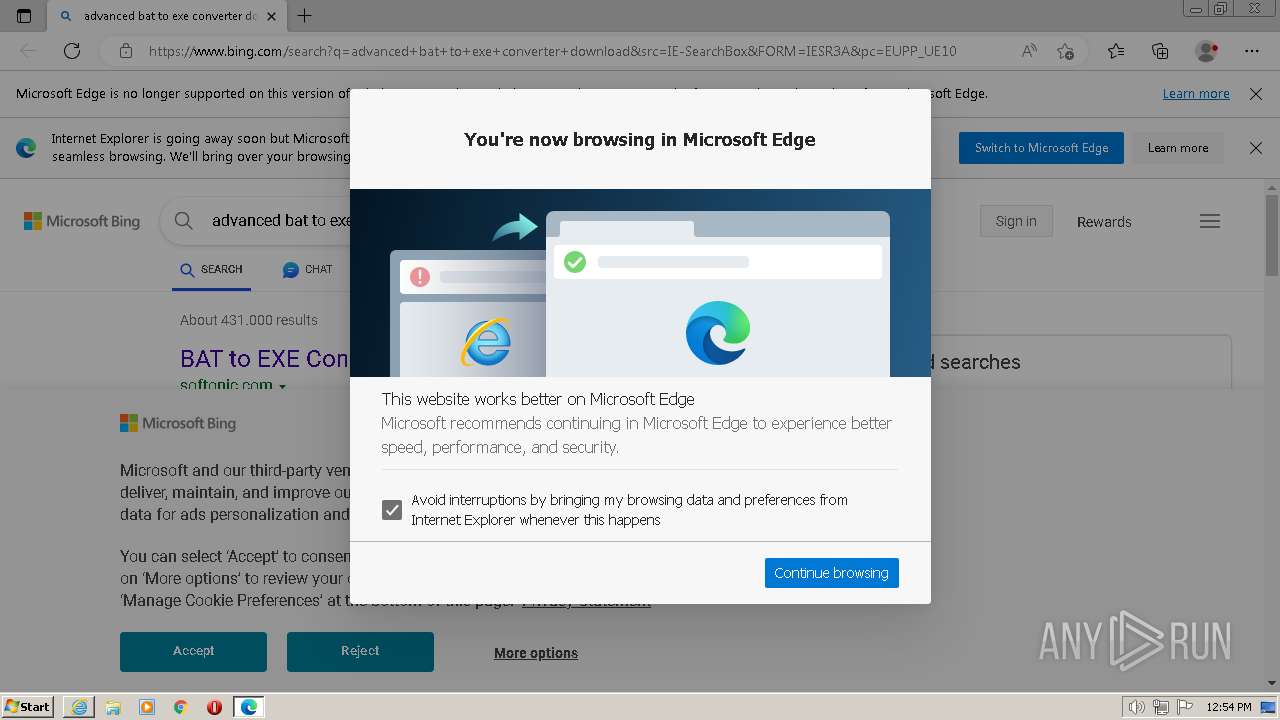
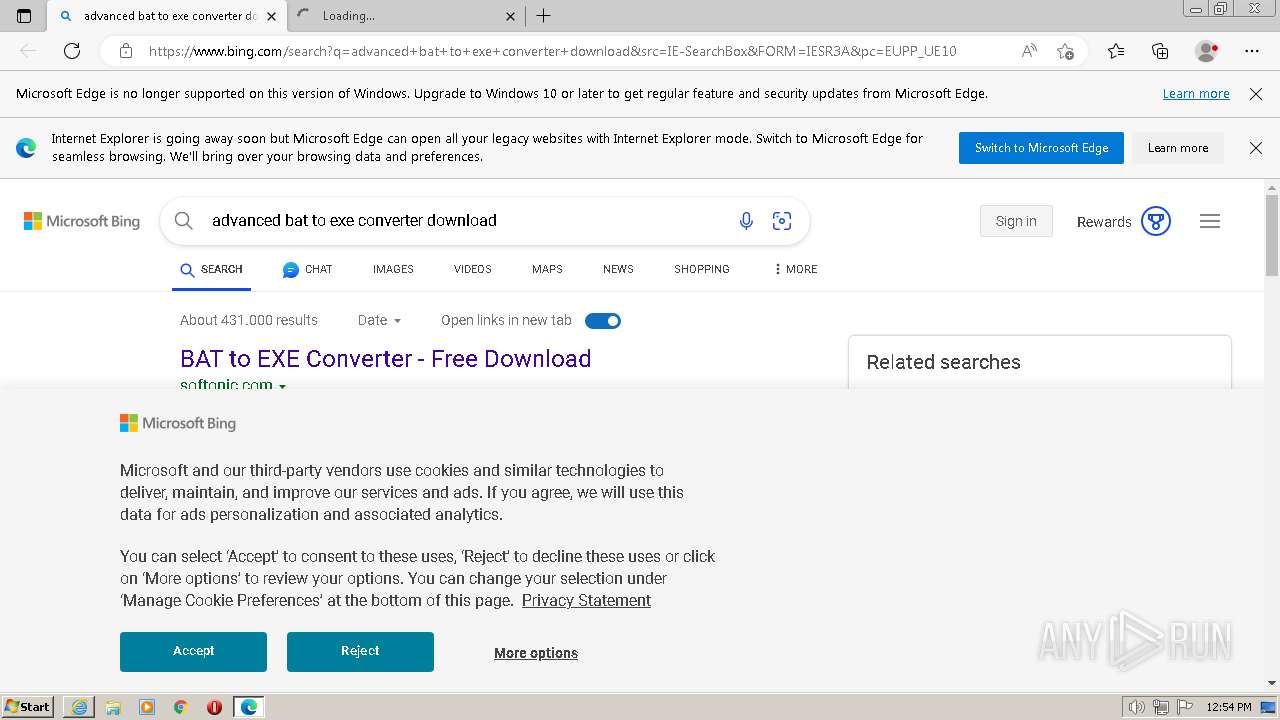
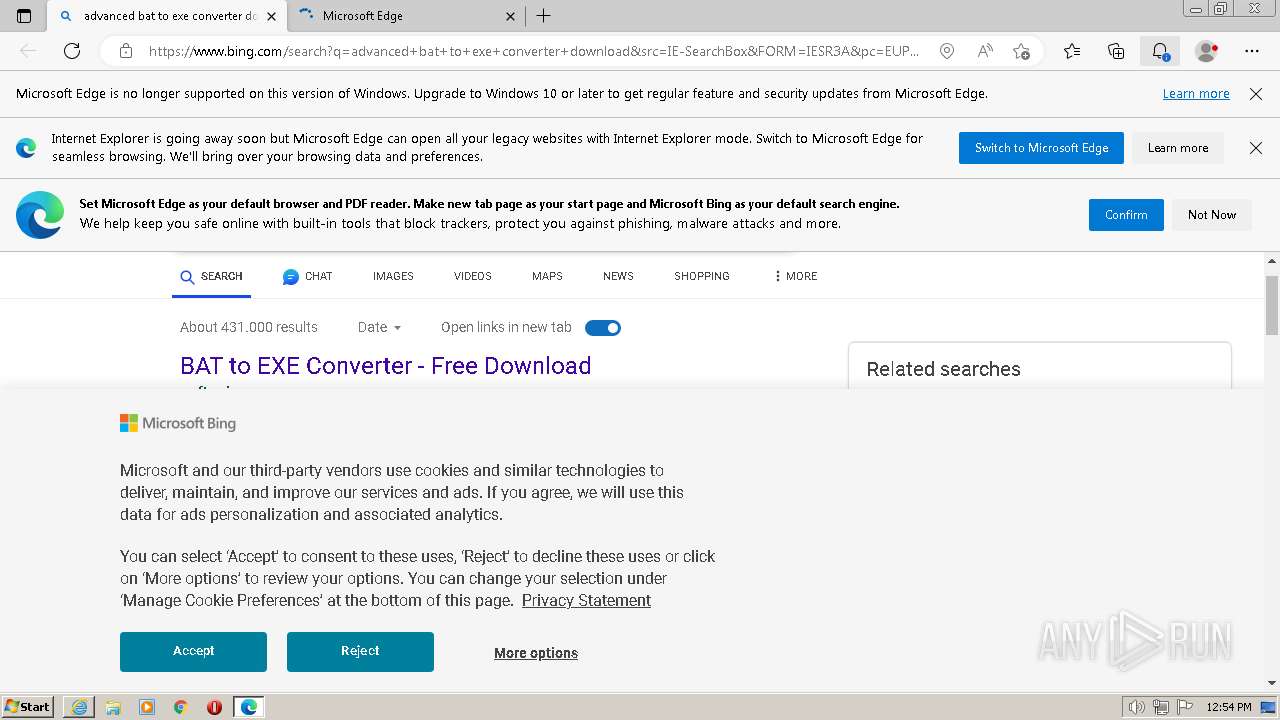
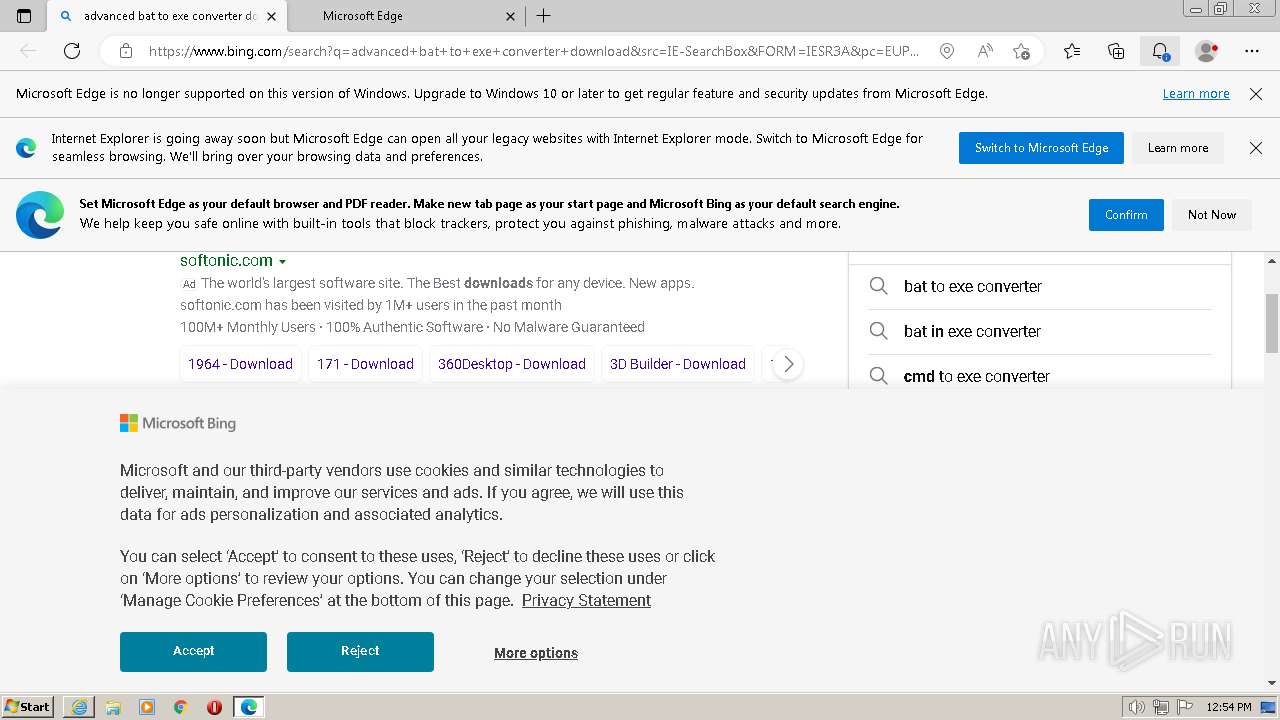
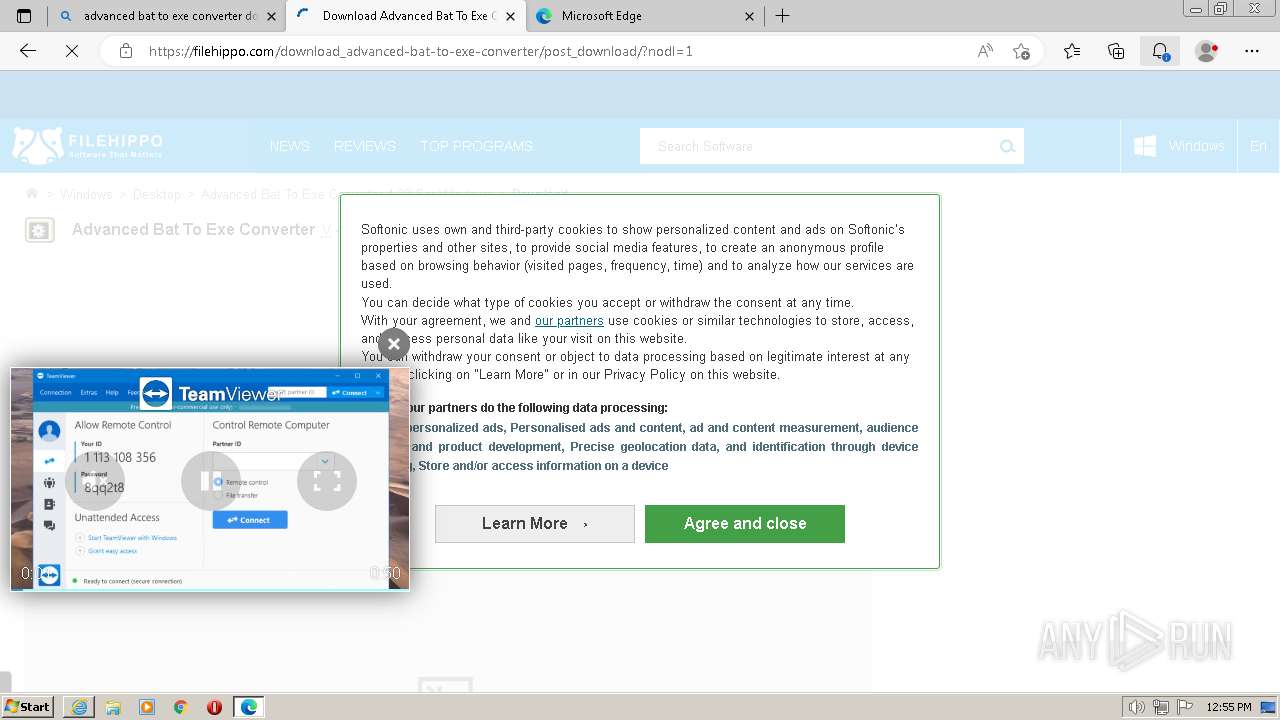
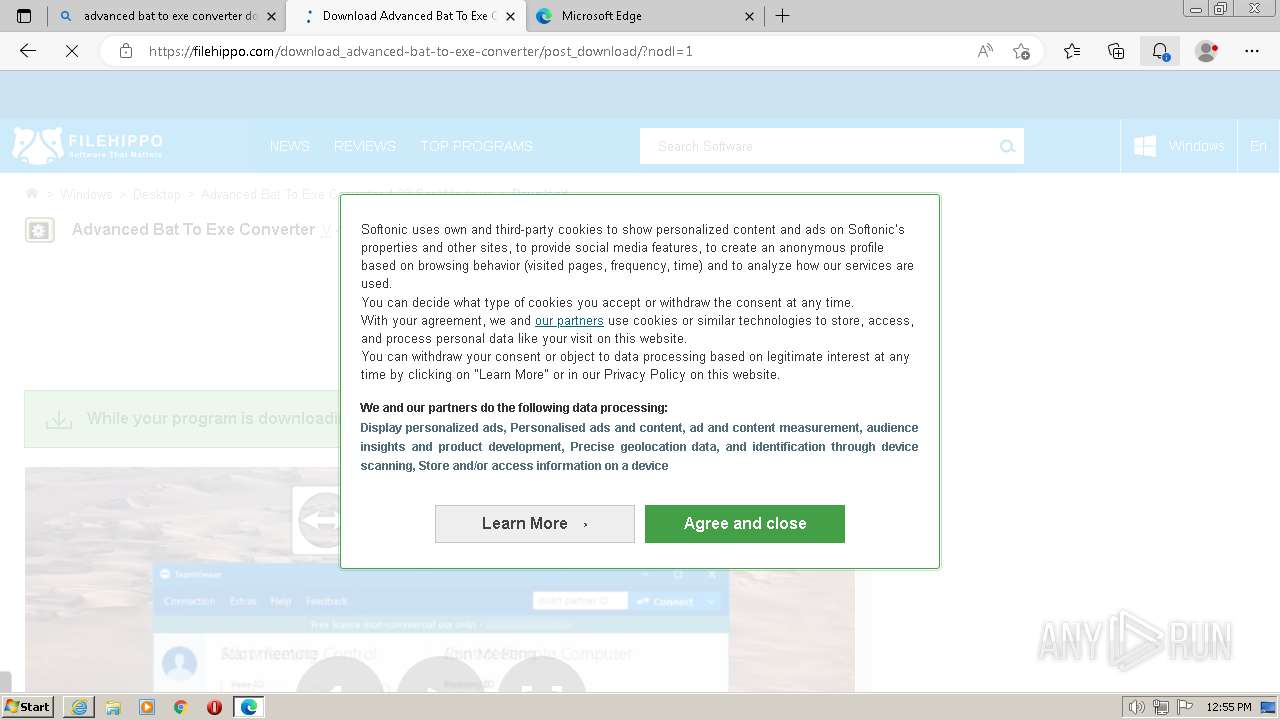
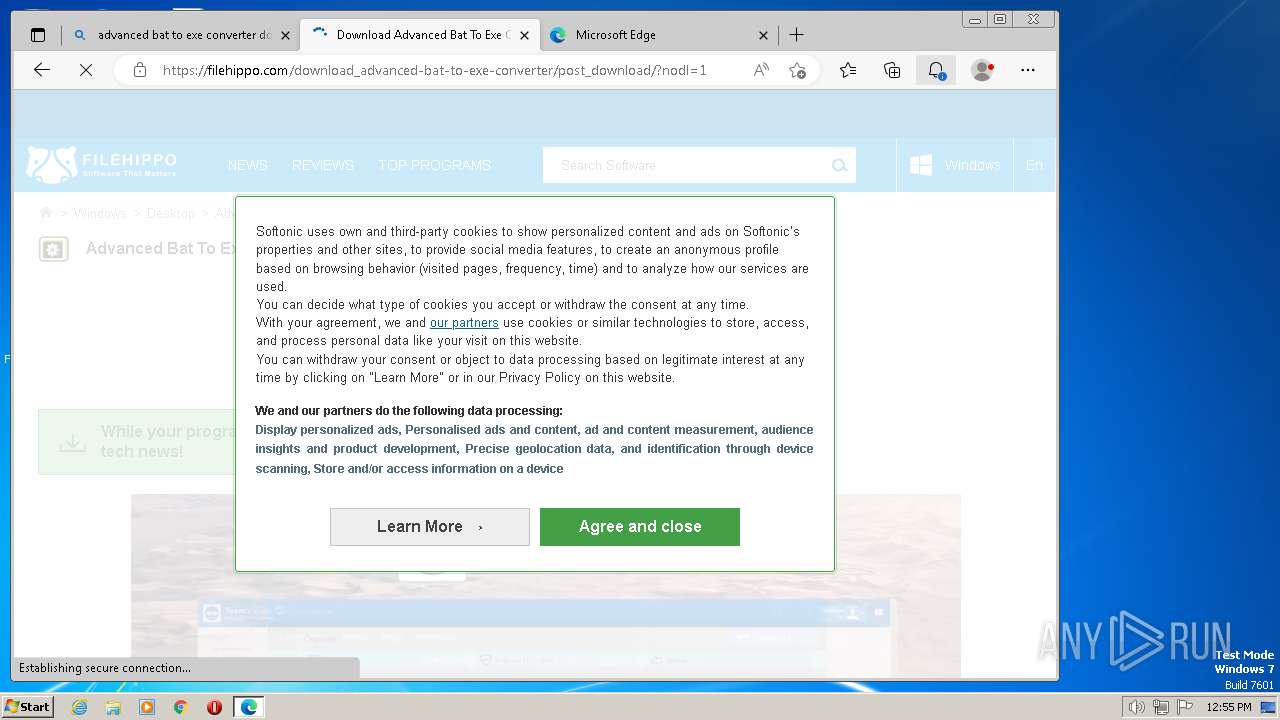
Application launched itself
- msedge.exe (PID: 2756)
- msedge.exe (PID: 856)
- iexplore.exe (PID: 1132)
- msedge.exe (PID: 1084)
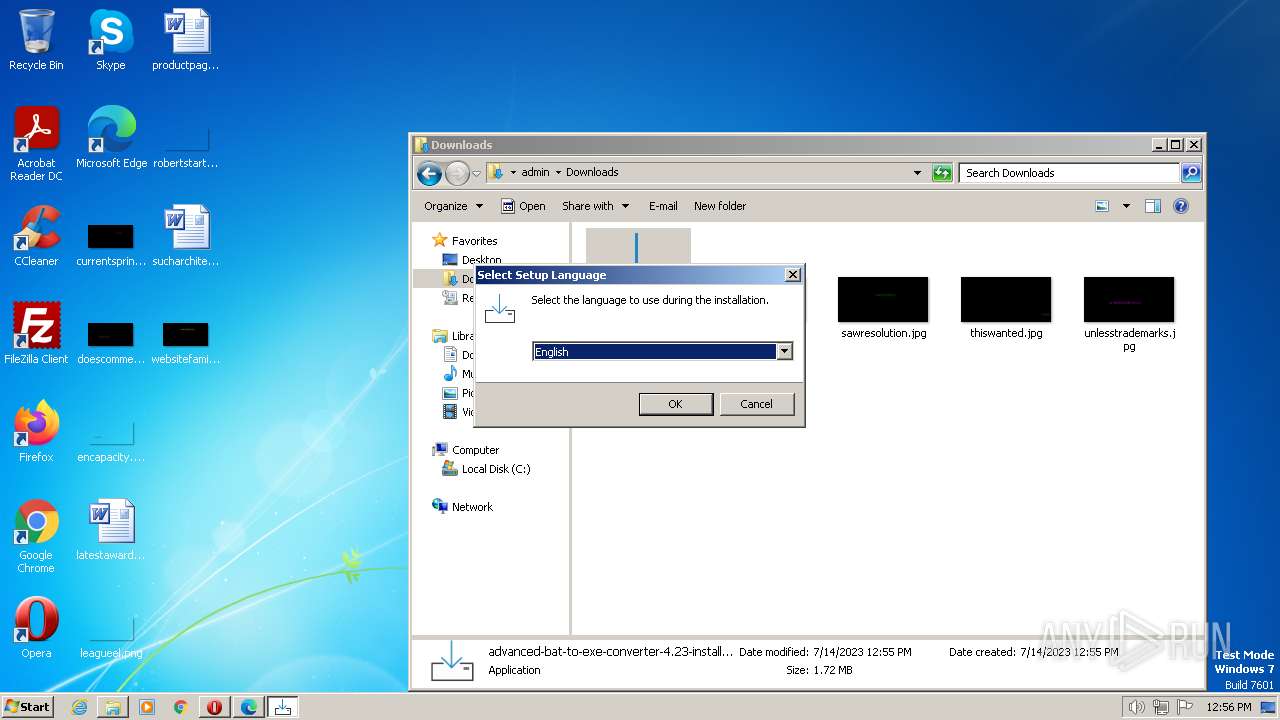
Checks supported languages
- cookie_exporter.exe (PID: 2604)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 856)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 2952)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 3028)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3788)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 2868)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3556)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 4036)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 1188)
- saBSI.exe (PID: 2984)
- advanced-bat-to-exe-converter-4.23-installer.exe (PID: 680)
- setupinf.exe (PID: 3740)
- aB2Econv.exe (PID: 3664)
Executable content was dropped or overwritten
- msedge.exe (PID: 1084)
- msedge.exe (PID: 3744)
- msedge.exe (PID: 2124)
Reads the computer name
- cookie_exporter.exe (PID: 2604)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3788)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 2952)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3556)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 1188)
- saBSI.exe (PID: 2984)
- advanced-bat-to-exe-converter-4.23-installer.exe (PID: 680)
The process checks LSA protection
- explorer.exe (PID: 4036)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 2952)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3788)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3556)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 1188)
- saBSI.exe (PID: 2984)
- advanced-bat-to-exe-converter-4.23-installer.exe (PID: 680)
- setupinf.exe (PID: 3740)
- aB2Econv.exe (PID: 3664)
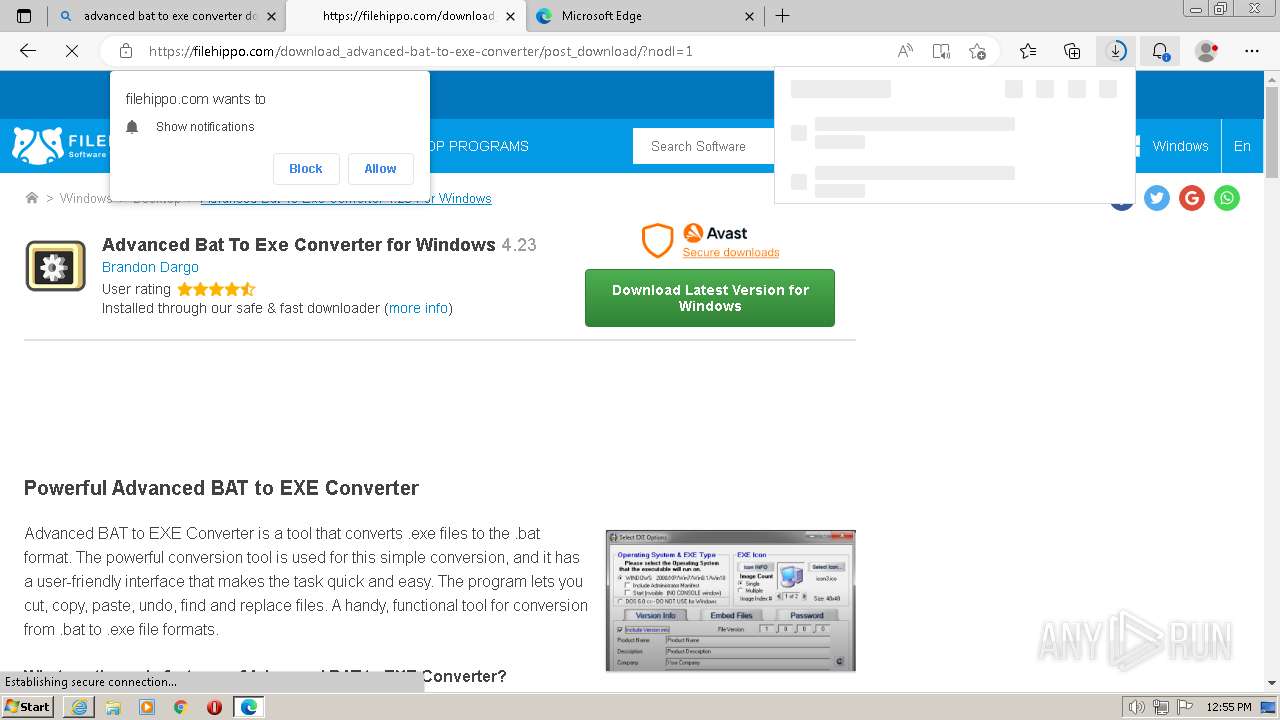
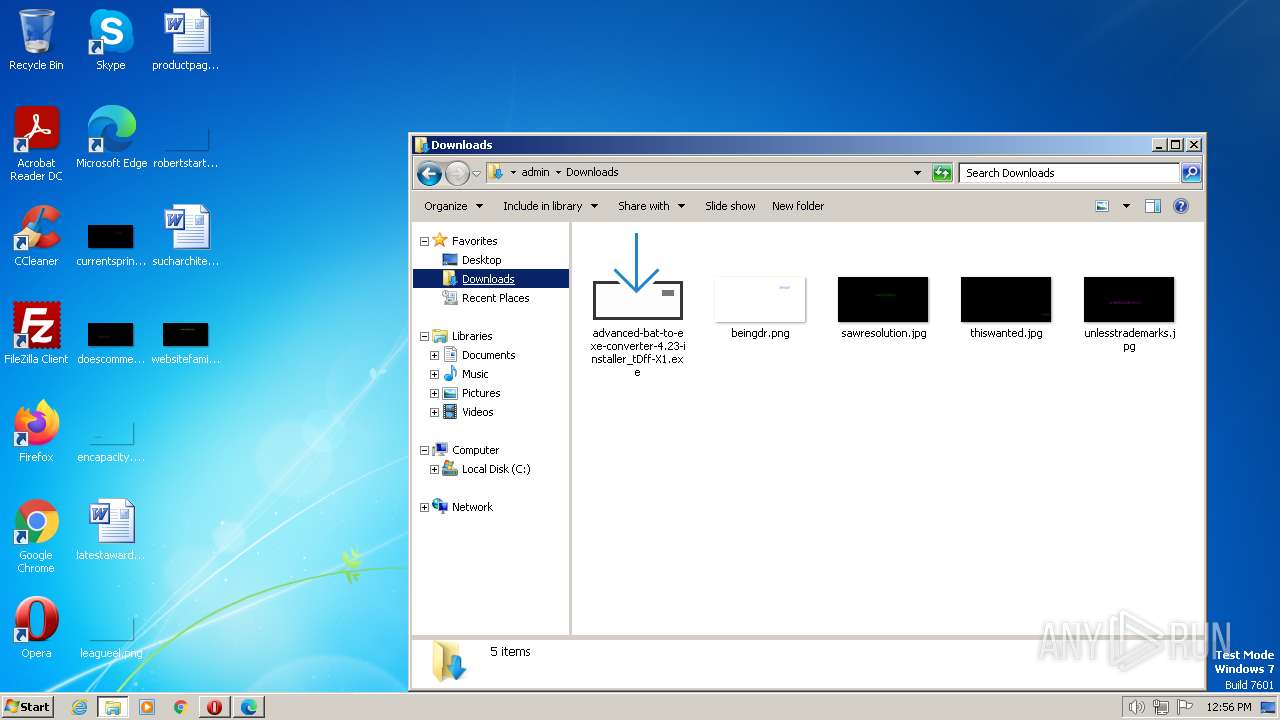
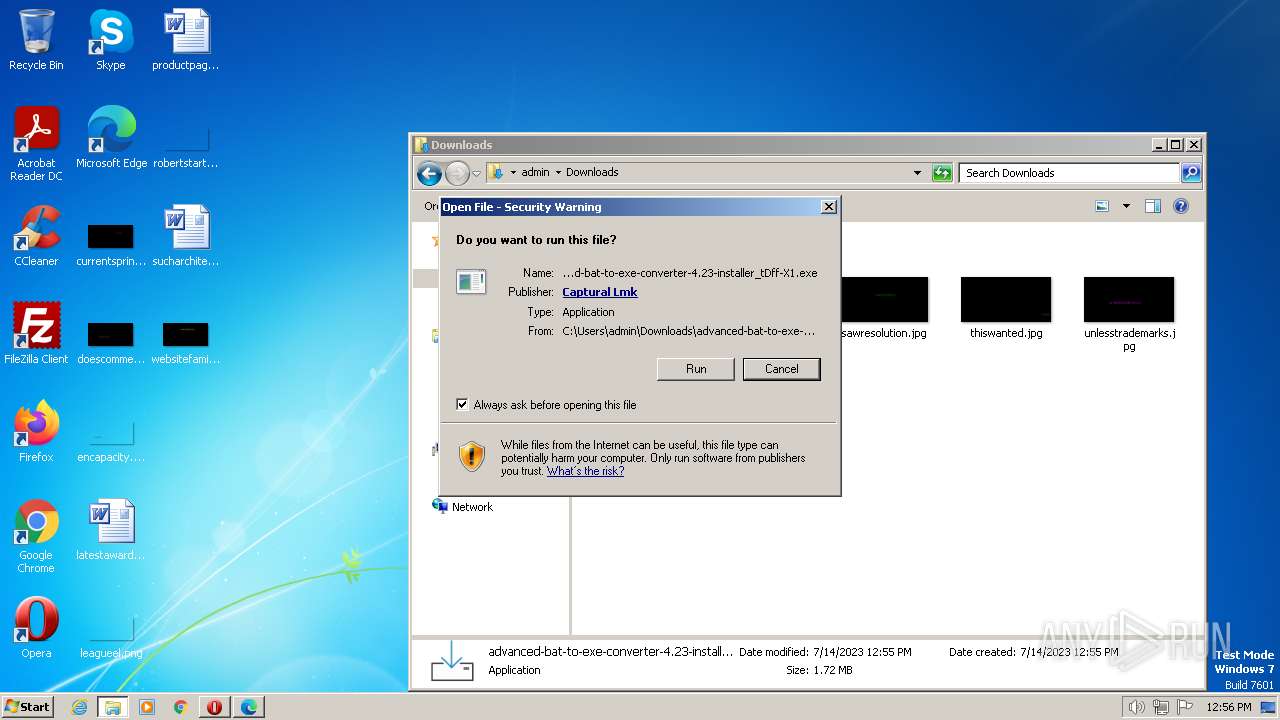
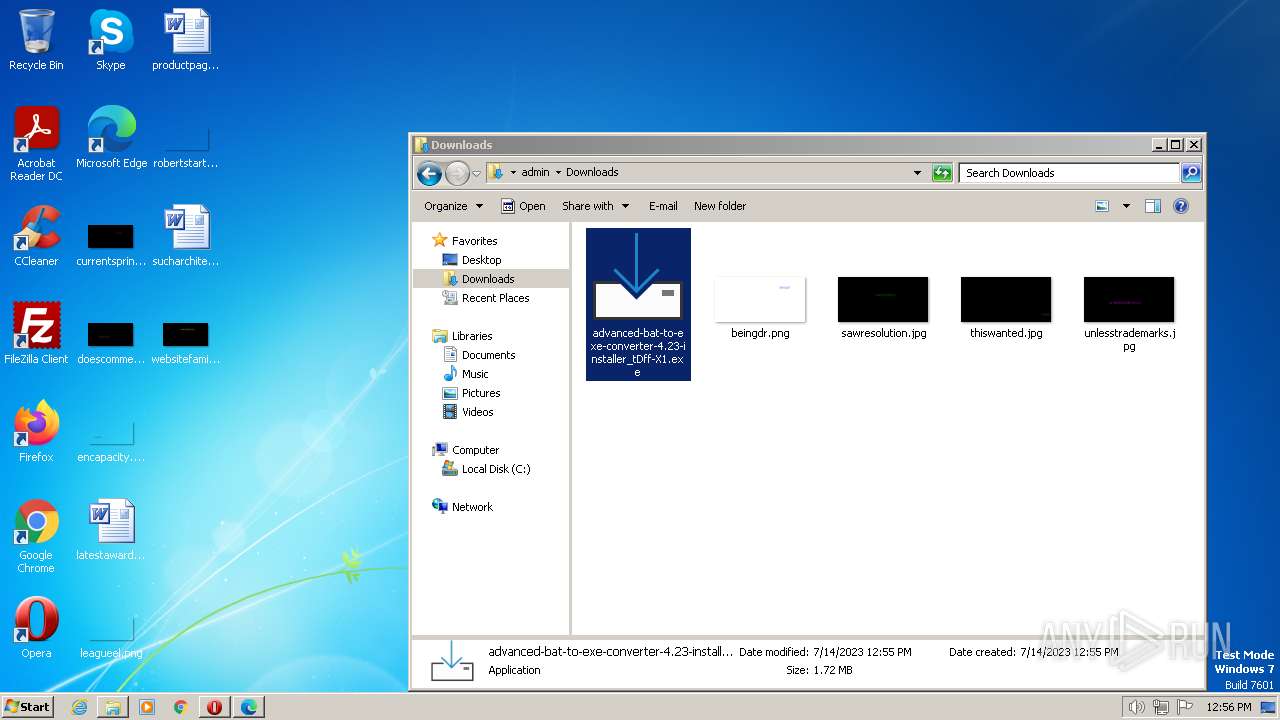
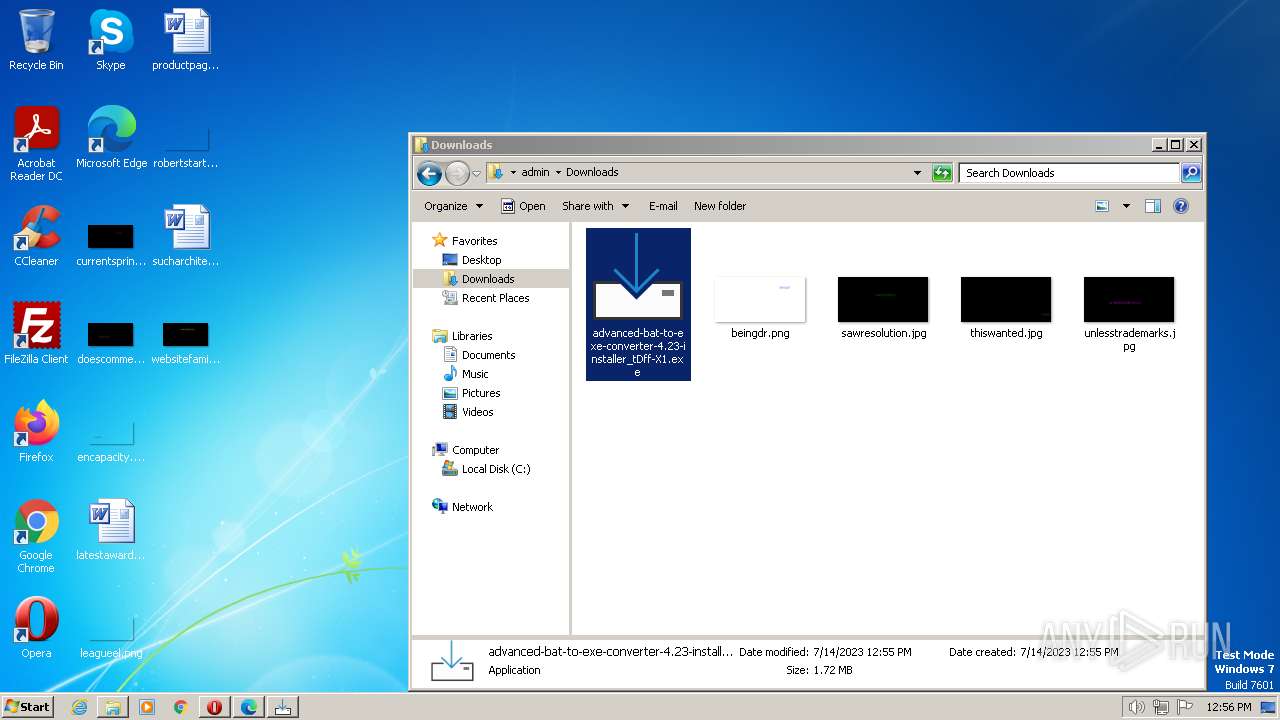
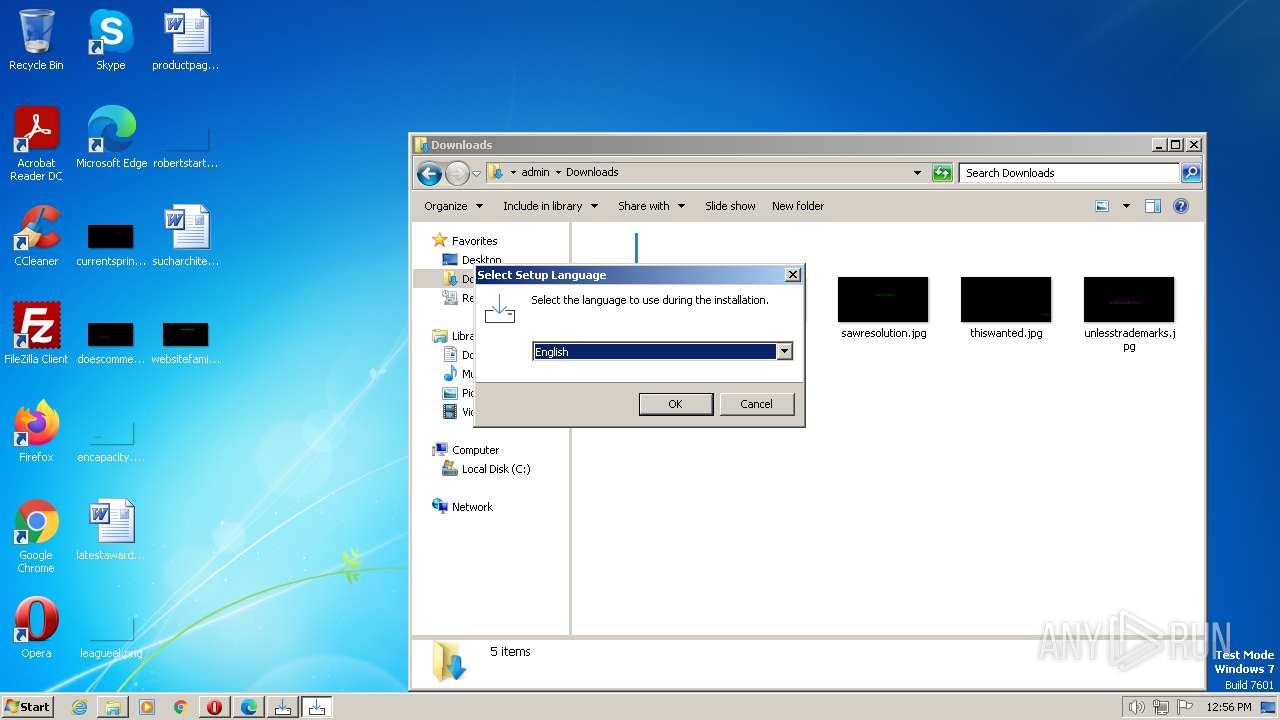
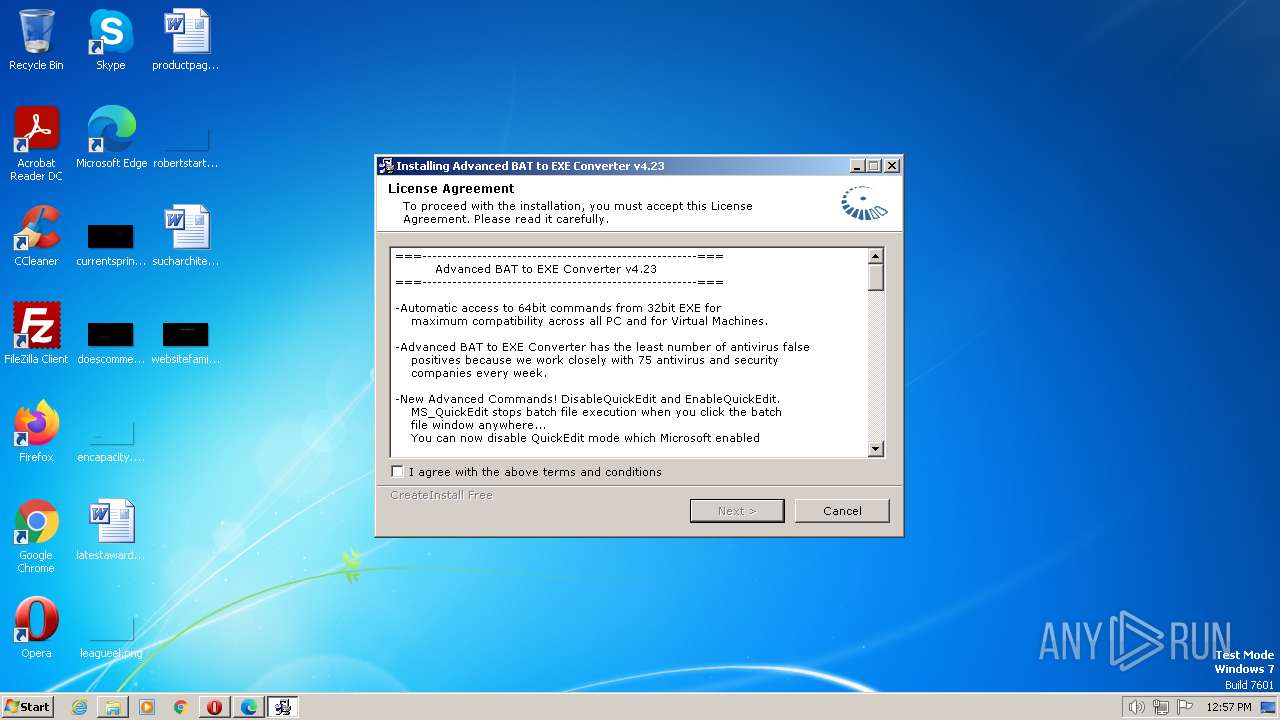
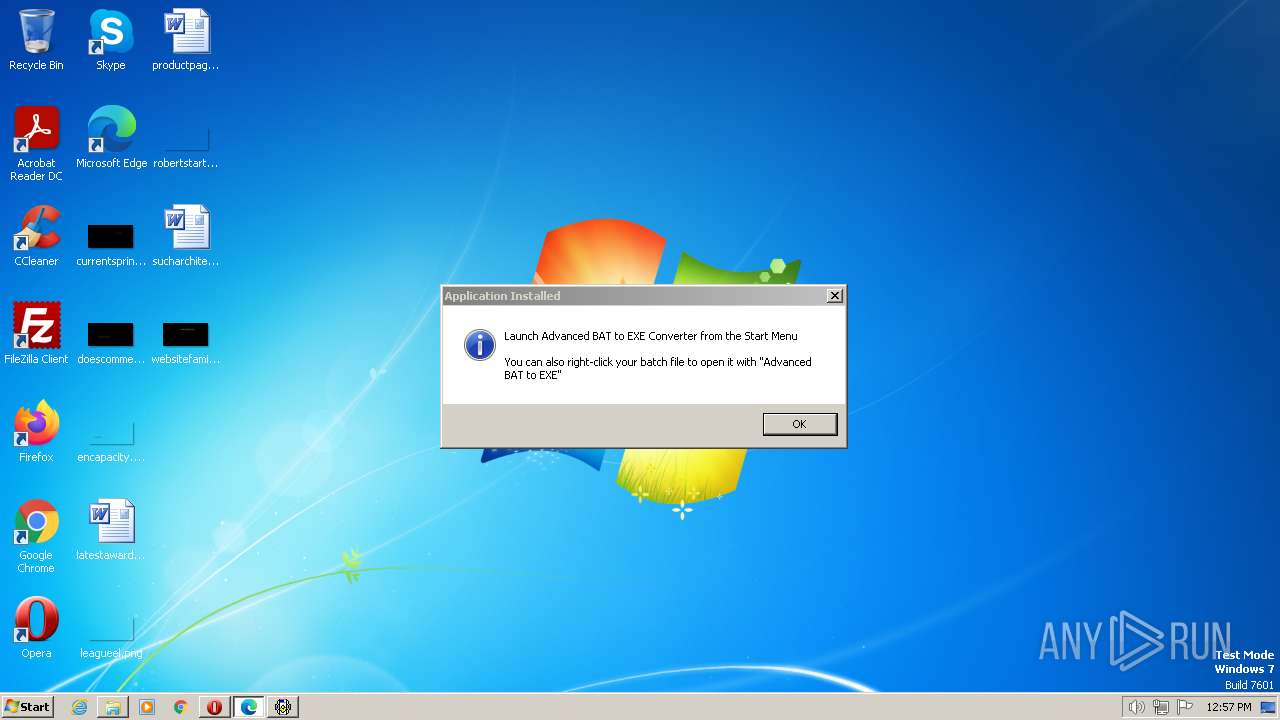
Manual execution by a user
- explorer.exe (PID: 4036)
- opera.exe (PID: 952)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 856)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 2868)
- aB2Econv.exe (PID: 3664)
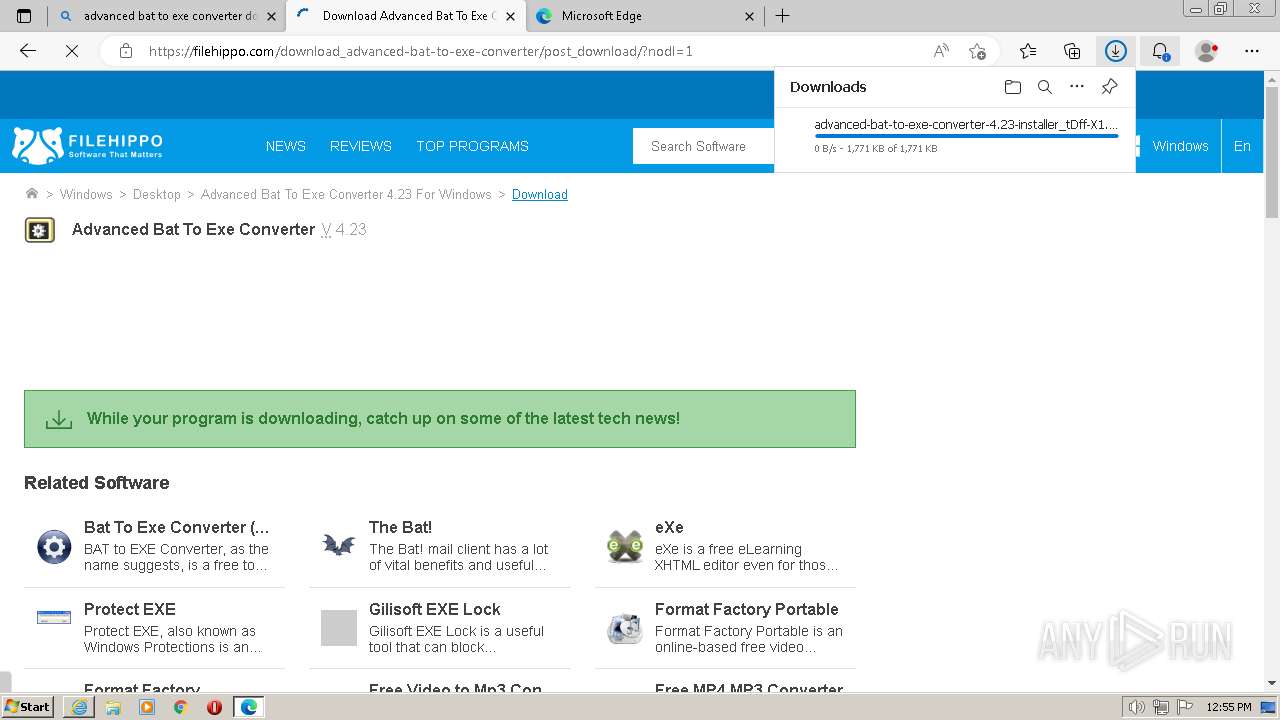
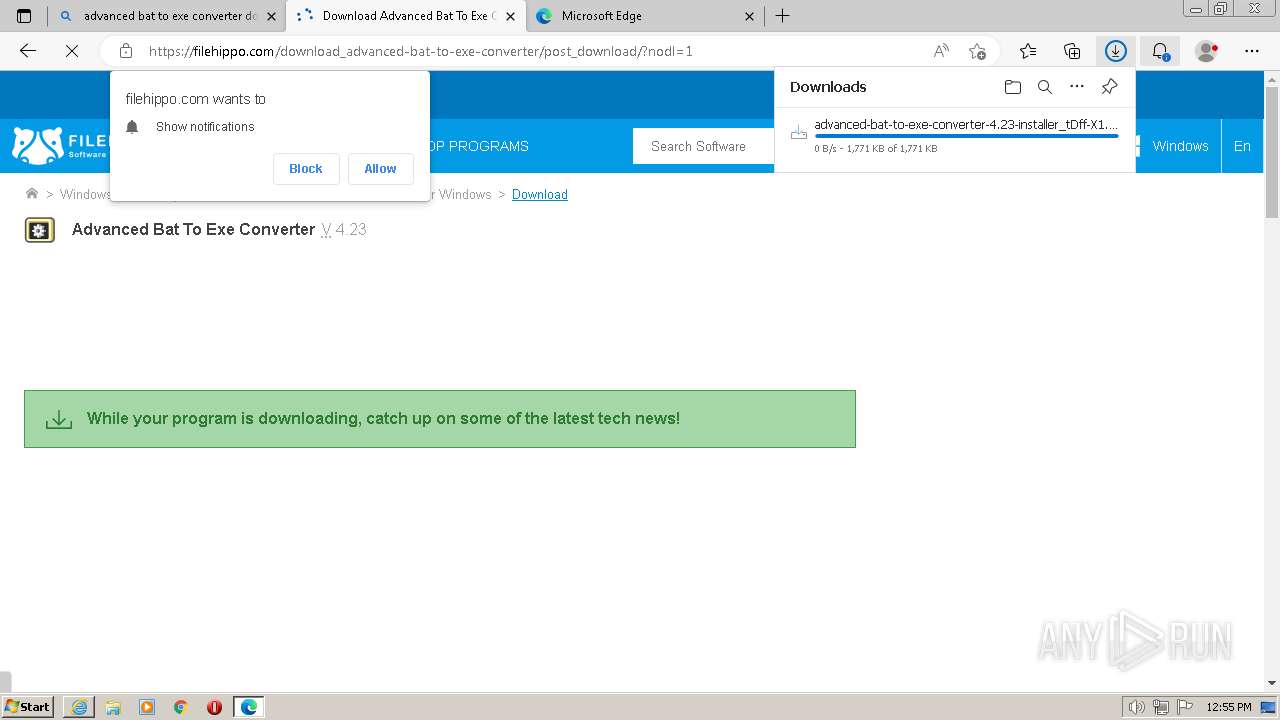
Create files in a temporary directory
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 856)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 3028)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3788)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 4036)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe (PID: 2868)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 1188)
- advanced-bat-to-exe-converter-4.23-installer.exe (PID: 680)
- setupinf.exe (PID: 3740)
- aB2Econv.exe (PID: 3664)
Application was dropped or rewritten from another process
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 2952)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3788)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3556)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 1188)
The process uses the downloaded file
- msedge.exe (PID: 1580)
Reads the machine GUID from the registry
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 3788)
- advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp (PID: 1188)
- saBSI.exe (PID: 2984)
- setupinf.exe (PID: 3740)
- aB2Econv.exe (PID: 3664)
Creates files in the program directory
- saBSI.exe (PID: 2984)
- advanced-bat-to-exe-converter-4.23-installer.exe (PID: 680)
Creates files or folders in the user directory
- advanced-bat-to-exe-converter-4.23-installer.exe (PID: 680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
144
Monitored processes
95
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --first-renderer-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2420 --field-trial-handle=1216,i,8607904822743172121,4343649401682983710,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 312 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3492 --field-trial-handle=1216,i,8607904822743172121,4343649401682983710,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 528 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2108 --field-trial-handle=1216,i,8607904822743172121,4343649401682983710,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 632 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3700 --field-trial-handle=1276,i,9666411208683906154,16429138658214644922,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
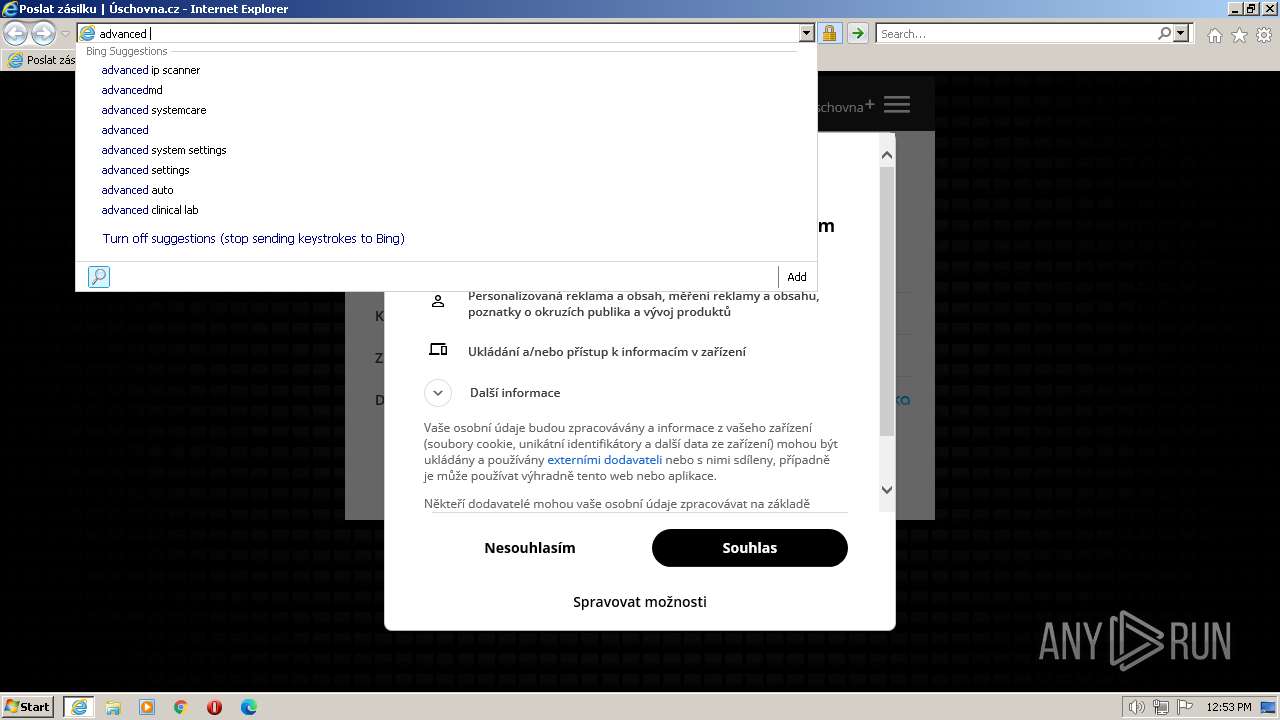
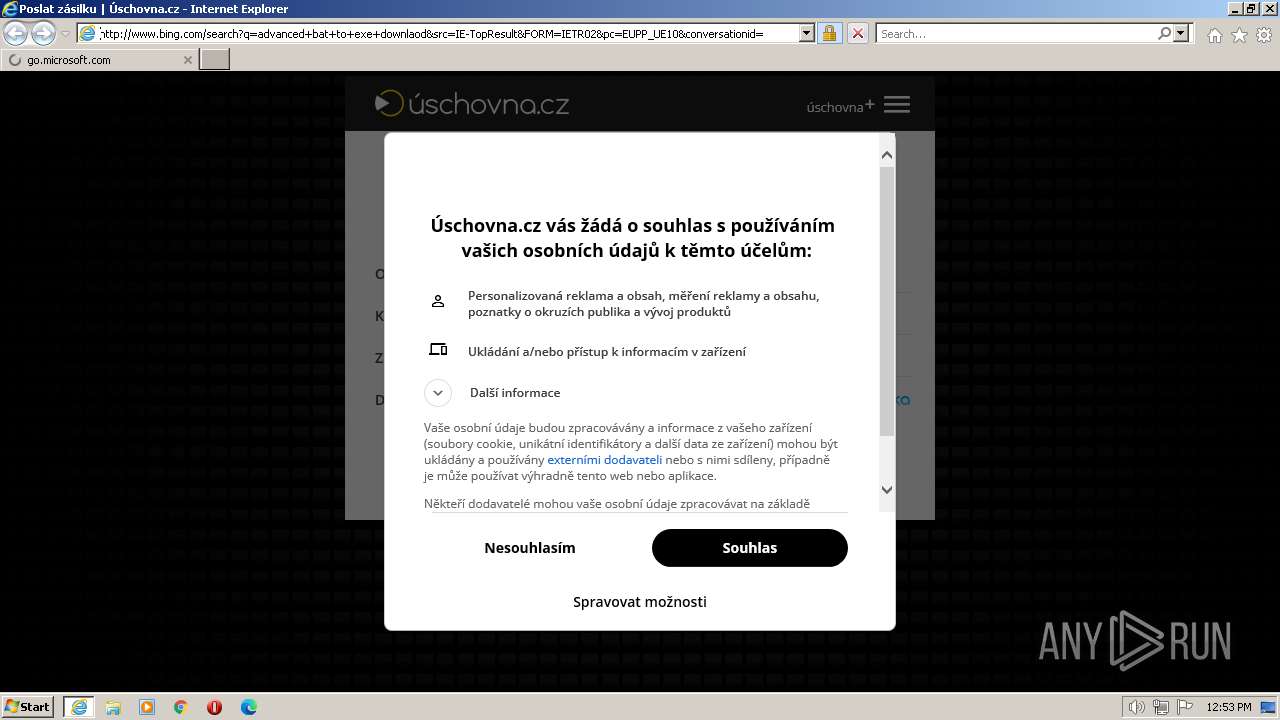
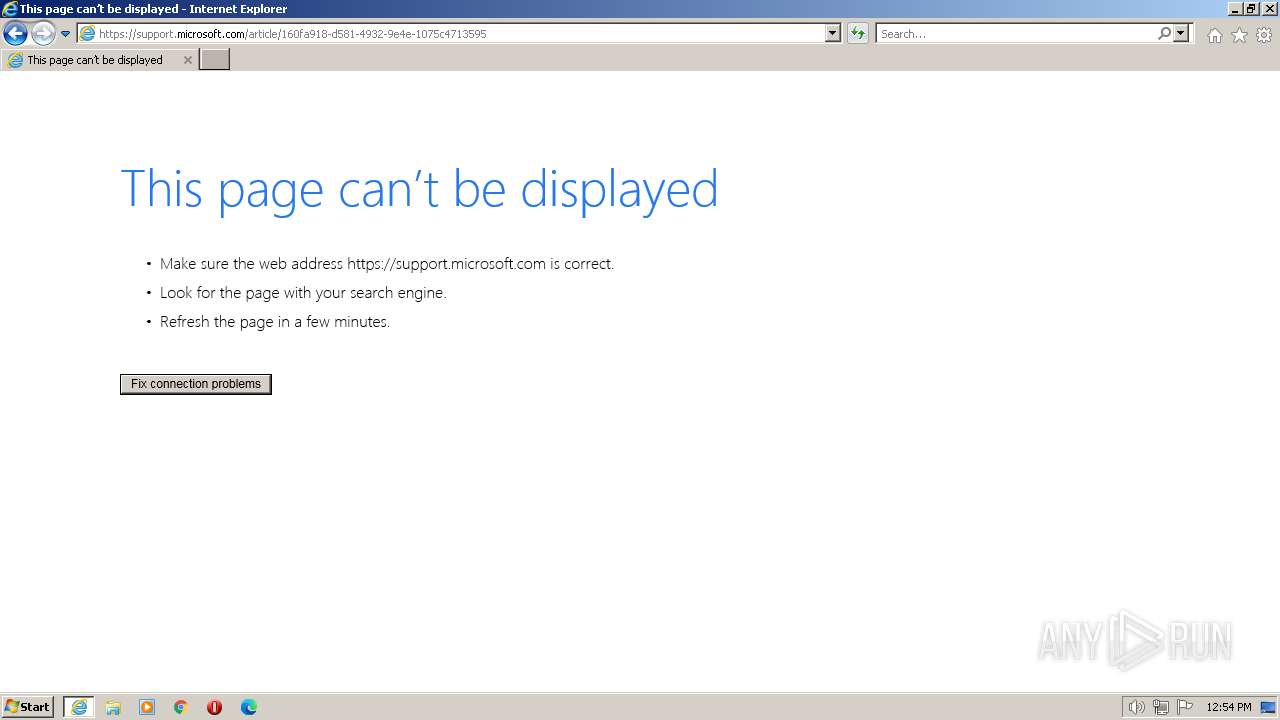
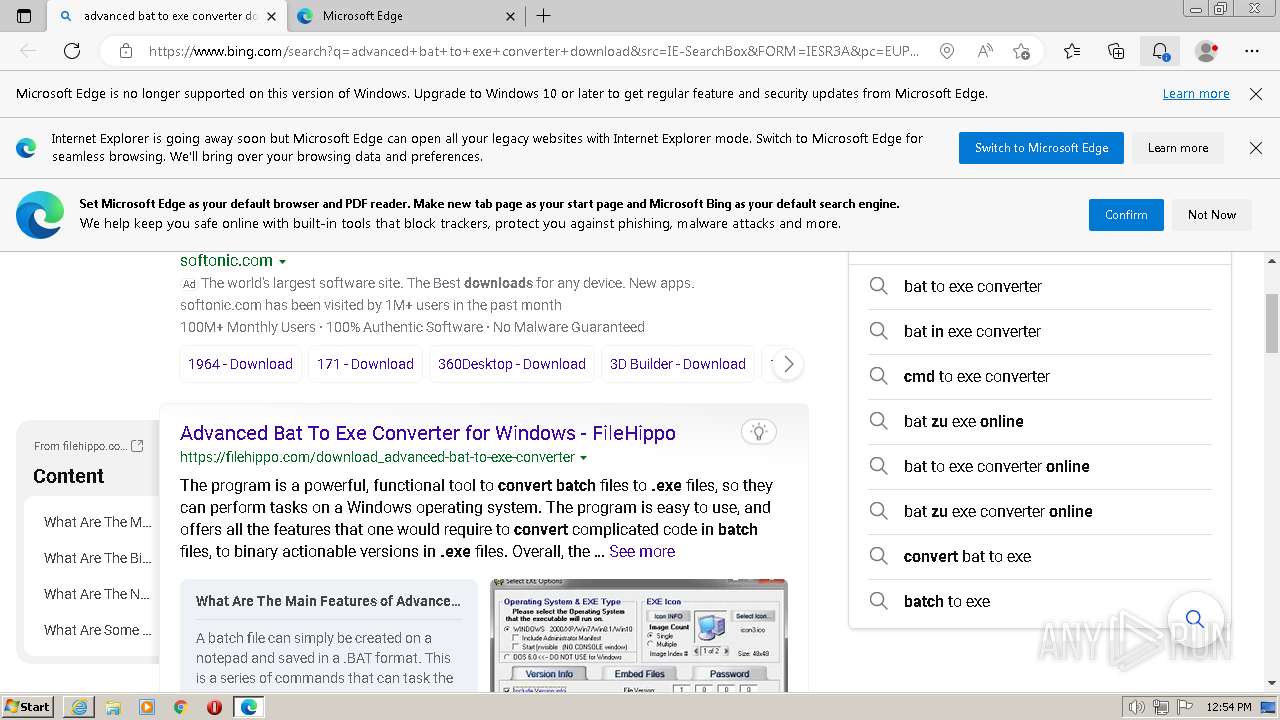
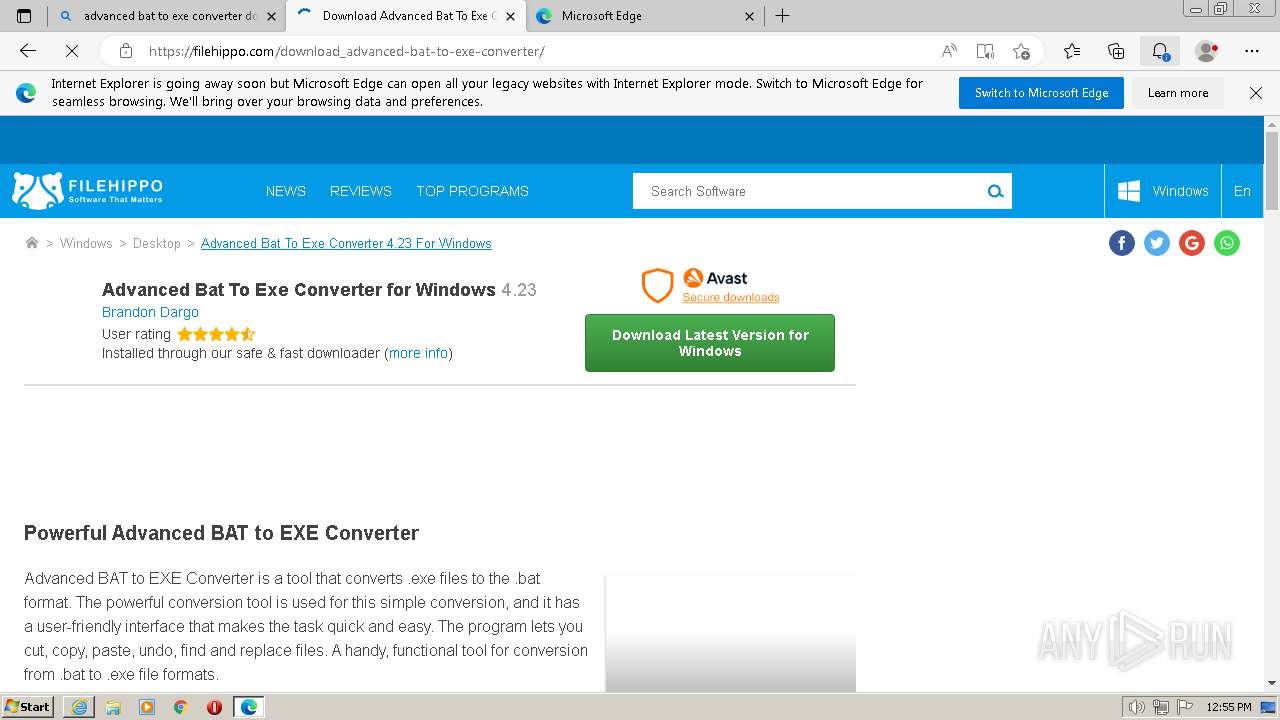
| 632 | "C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\BHO\ie_to_edge_stub.exe" --from-ie-to-edge=1 --customer-type=1 -- "http://www.bing.com/search?q=advanced+bat+to+exe+converter+download&src=IE-SearchBox&FORM=IESR3A&pc=EUPP_UE10" | C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\BHO\ie_to_edge_stub.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: IEToEdge BHO Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
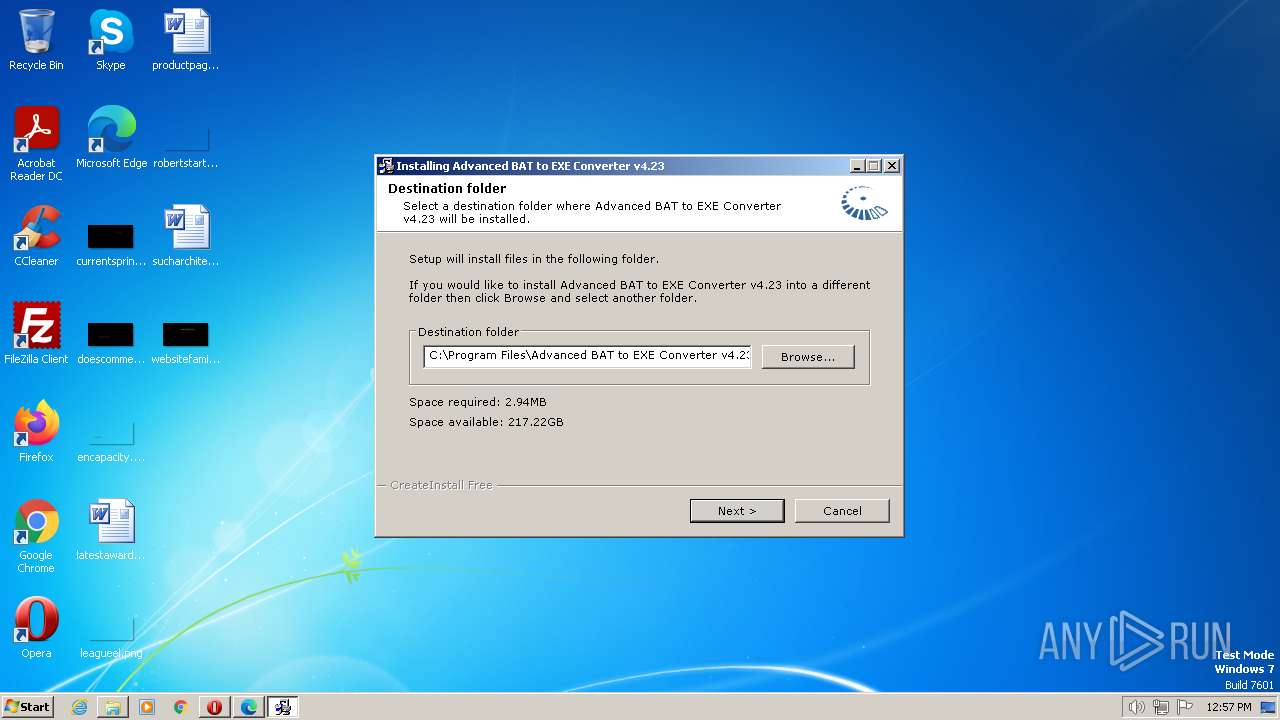
| 680 | "C:\Users\admin\Downloads\advanced-bat-to-exe-converter-4.23-installer.exe" | C:\Users\admin\Downloads\advanced-bat-to-exe-converter-4.23-installer.exe | advanced-bat-to-exe-converter-4.23-installer_tDff-X1.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=46 --mojo-platform-channel-handle=6416 --field-trial-handle=1216,i,8607904822743172121,4343649401682983710,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\BHO\ie_to_edge_stub.exe" --create-cache-container=0 | C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\BHO\ie_to_edge_stub.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: IEToEdge BHO Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
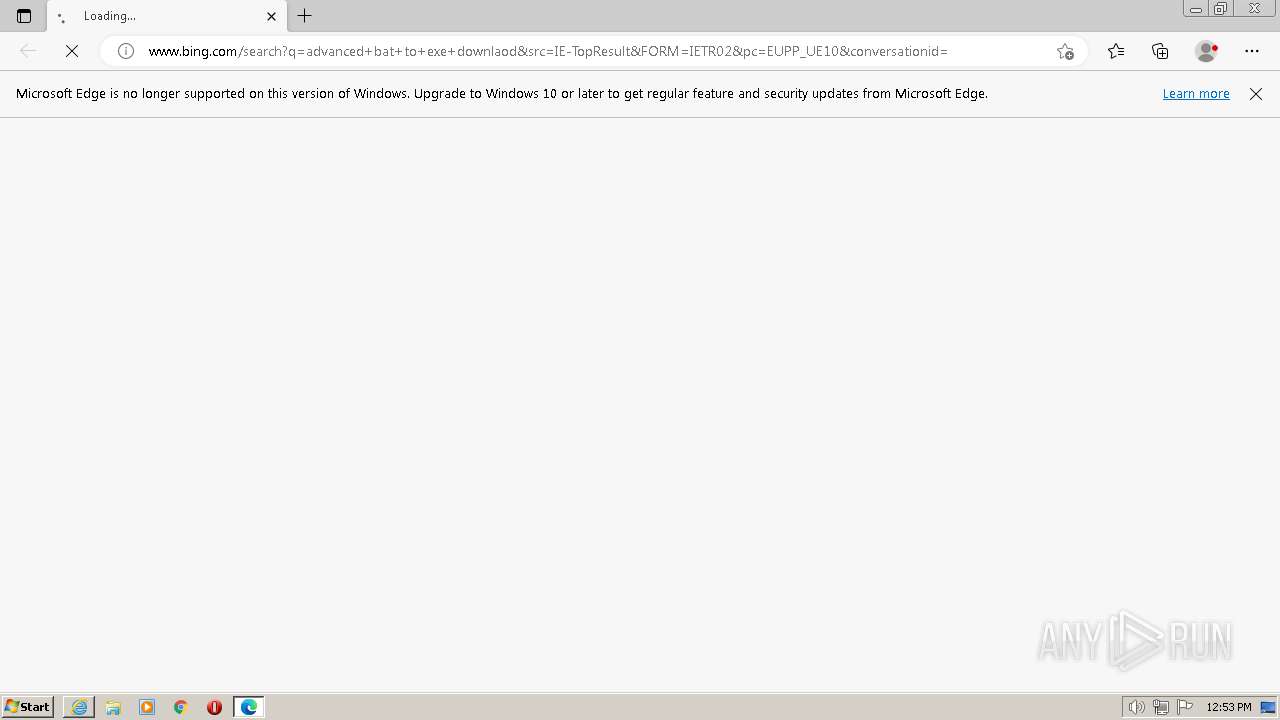
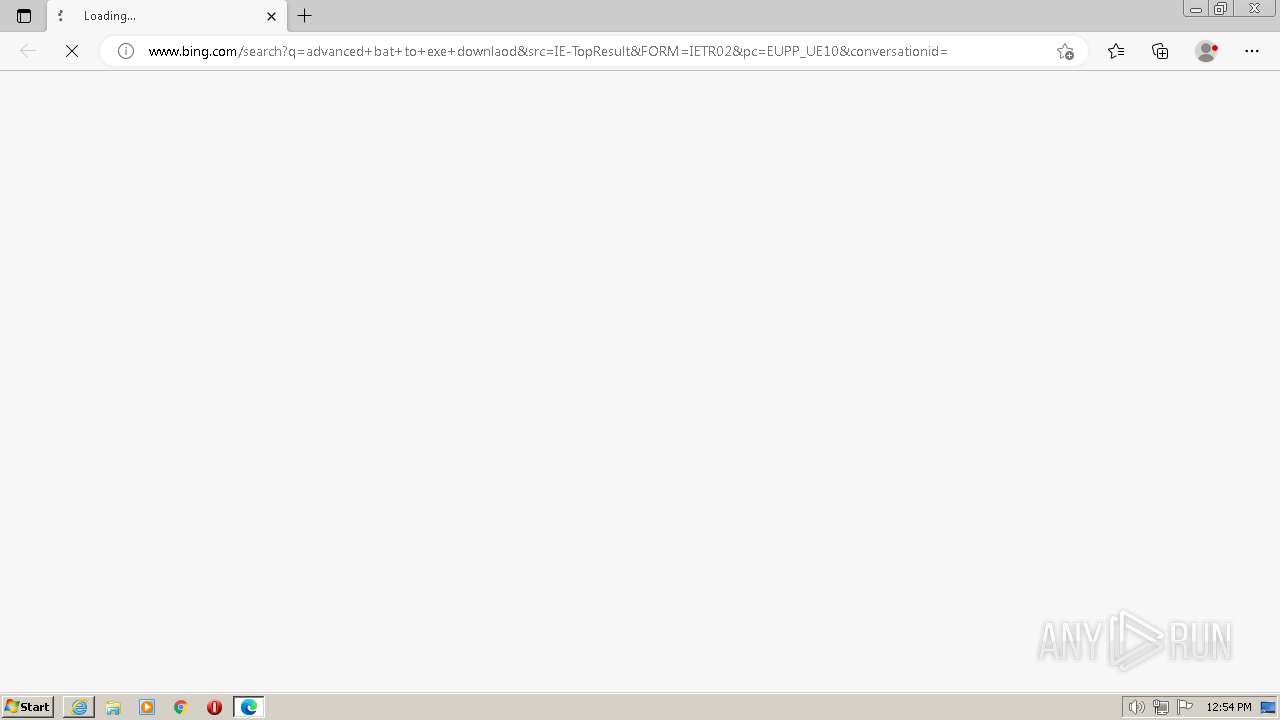
| 856 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=1 --customer-type=1 --single-argument http://www.bing.com/search?q=advanced+bat+to+exe+downlaod&src=IE-TopResult&FORM=IETR02&pc=EUPP_UE10&conversationid= | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | ie_to_edge_stub.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 856 | "C:\Users\admin\Downloads\advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe" | C:\Users\admin\Downloads\advanced-bat-to-exe-converter-4.23-installer_tDff-X1.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Capturāl Lmk Exit code: 0 Version: 8.7.2431 Modules
| |||||||||||||||
Total events
52 370
Read events
51 962
Write events
374
Delete events
34
Modification events
| (PID) Process: | (1132) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1132) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1132) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1132) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1132) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1132) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1132) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1132) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1132) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1132) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
43
Suspicious files
431
Text files
383
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3624 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_E503B048B745DFA14B81FCFC68D6DECE | binary | |
MD5:4B06DACAF8952FFC3B9FA4E3BB5CA0C1 | SHA256:E1475FEBA31C134FB2943EEE6A729B1E1E17A3FAB6795B233736F16E4608535E | |||
| 3624 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2AA.tmp | compressed | |
MD5:3AC860860707BAAF32469FA7CC7C0192 | SHA256:D015145D551ECD14916270EFAD773BBC9FD57FAD2228D2C24559F696C961D904 | |||
| 3624 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2AB.tmp | binary | |
MD5:4FF65AD929CD9A367680E0E5B1C08166 | SHA256:C8733C93CC5AAF5CA206D06AF22EE8DBDEC764FB5085019A6A9181FEB9DFDEE6 | |||
| 3624 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35DE96AFE0979FFB7BAF5CA67005FBB0 | binary | |
MD5:1835D7465199C79B8CC660C067A27CBD | SHA256:84BCB190B0F1D2CEA1B6860A94B6BB4E6898DC6F088626E7C76399E7ACCD8F96 | |||
| 3624 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\35DE96AFE0979FFB7BAF5CA67005FBB0 | binary | |
MD5:A963CBA1E39BA47CFEE6C5F4E185553E | SHA256:C15B0F9976F5382A614A9DC7B508093199875E5ECFB1527D0AAB52AE5FBE6335 | |||
| 2084 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma | binary | |
MD5:886E82F2CA62ECCCE64601B30592078A | SHA256:E5E13D53601100FF3D6BB71514CBCCC4C73FE9B7EF5E930100E644187B42948E | |||
| 2756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:A2B913D3BC9B6344C76B056712064197 | SHA256:CC7E7F39A2B36FFD7D6EC45A4AA70BFB8DBEBC58EEB784D08218B0036D3AD564 | |||
| 3624 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_E503B048B745DFA14B81FCFC68D6DECE | binary | |
MD5:274BA5EBBD2E26FE78F4E55CB92F5E7E | SHA256:A4CA1BCF63409C34EF2C4CBCEE26AF26171B7C197231948251B94A6D05B988AE | |||
| 3624 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\v1[1].xml | xml | |
MD5:DB1AADD13ECD5B5FA97119B7B5000D85 | SHA256:4BF5F613A25A5D431C32870C9402F3476263193307DFB6A7B9A31ADA831E50E7 | |||
| 3624 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_D46D6FA25B74360E1349F9015B5CCE53 | binary | |
MD5:A0B9878C8F0FF9932B8B0E57BE3B75AC | SHA256:4BCD3852BD5B1723950BDDB55AB1AE71EFE00804699BDF2127CA4E40DFD966C6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
405
DNS requests
309
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3624 | iexplore.exe | GET | — | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECyP1HvZSJrzEIqeU6yEBFk%3D | US | — | — | whitelisted |
3624 | iexplore.exe | GET | 200 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?913fd89c2bb75413 | US | compressed | 4.70 Kb | whitelisted |
3624 | iexplore.exe | GET | 200 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?470891137287efc4 | US | compressed | 62.3 Kb | whitelisted |
3624 | iexplore.exe | GET | 200 | 23.215.61.11:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRLbx4j3nHwwbhyb9y5PRiZkA%3D%3D | GB | binary | 503 b | shared |
3624 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | binary | 471 b | whitelisted |
3624 | iexplore.exe | GET | 200 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a079bccc846085c6 | US | compressed | 4.70 Kb | whitelisted |
3624 | iexplore.exe | GET | 200 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c85132eb457c74c7 | US | compressed | 4.70 Kb | whitelisted |
3624 | iexplore.exe | GET | 200 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b8d8ffc7f83be446 | US | compressed | 4.70 Kb | whitelisted |
3624 | iexplore.exe | GET | 200 | 104.84.250.230:80 | http://x1.c.lencr.org/ | US | binary | 717 b | whitelisted |
3624 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3624 | iexplore.exe | 8.238.30.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3624 | iexplore.exe | 88.221.179.76:443 | go.microsoft.com | AKAMAI-AS | GB | suspicious |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3388 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3624 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3624 | iexplore.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3624 | iexplore.exe | 172.217.18.2:443 | www.googleadservices.com | GOOGLE | US | whitelisted |
3624 | iexplore.exe | 104.84.250.230:80 | x1.c.lencr.org | AKAMAI-AS | GB | unknown |
3624 | iexplore.exe | 85.239.227.189:443 | cdn-static.tiscali.cz | CASABLANCA INT a.s. | CZ | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
cdn.performax.cz |
| unknown |
cms.tiscali.cz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3744 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
Process | Message |
|---|---|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-PAR6K.tmp\component0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-PAR6K.tmp\component0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-PAR6K.tmp\component0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-PAR6K.tmp\component0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-PAR6K.tmp\component0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-PAR6K.tmp\component0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|