| File name: | uploads_faeac3a0-9e5d-4a89-bb82-f99827cd5cef.eml |
| Full analysis: | https://app.any.run/tasks/fe0ebed0-3f16-4768-afcb-81af36fcd456 |
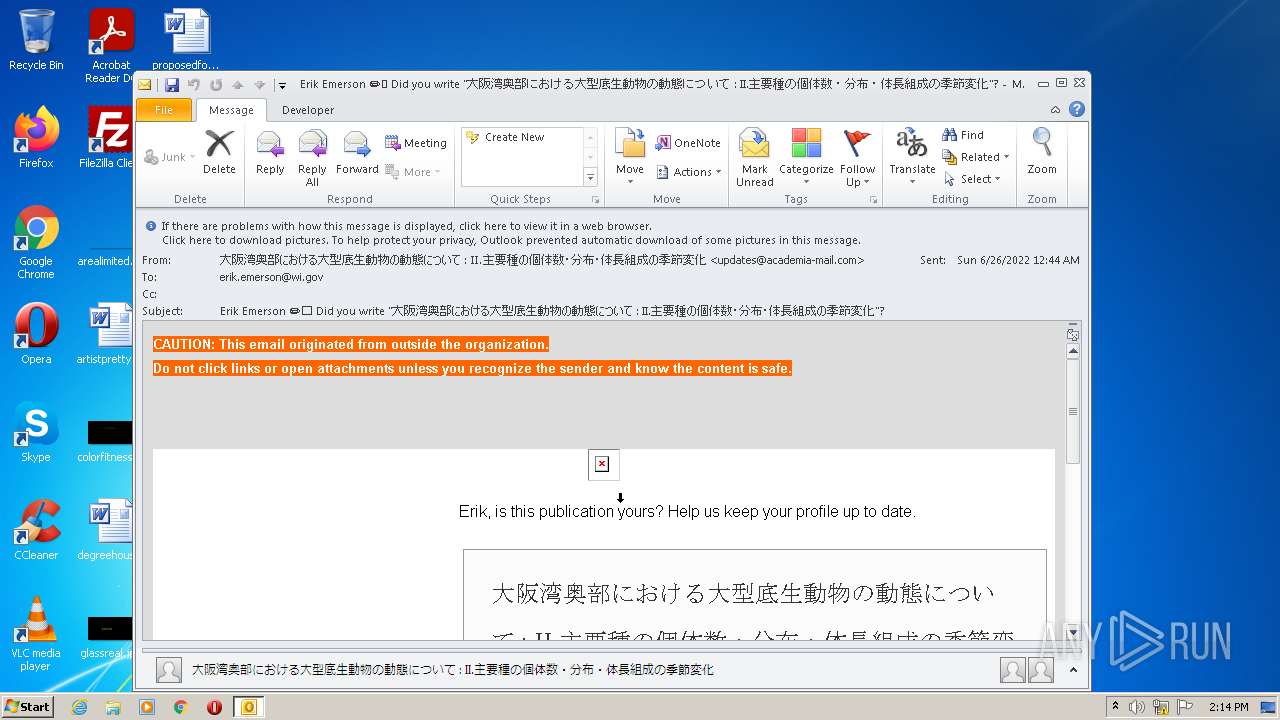
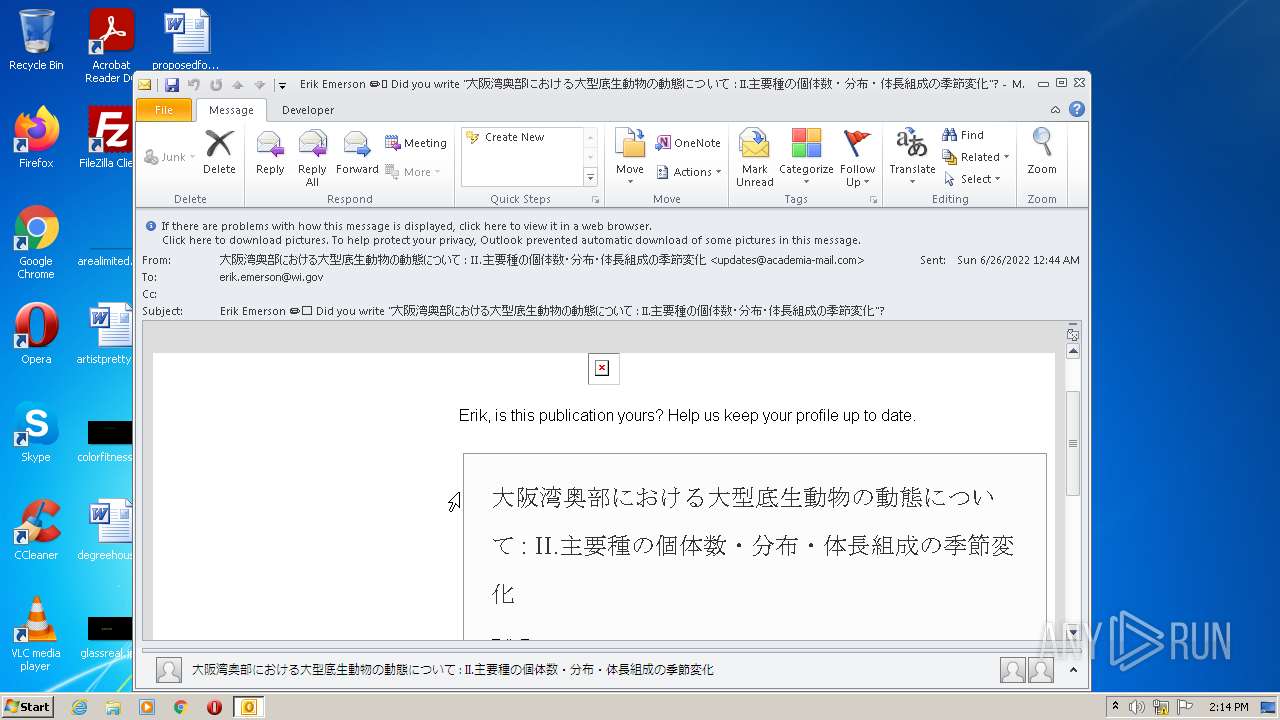
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 13:14:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 107635CB38A224366252FB7BAD0A144D |
| SHA1: | 722B2E324CA36F38E58CDB9870A3307BEEE10002 |
| SHA256: | 8A58ED5DE4A2AE2A393FD3C58AC43B2418F41F62B79079B39B8AED8A62EBE058 |
| SSDEEP: | 1536:swCIU0p+z9CwDzlMZqx5PwNB7l5Sa2nqFHnNCnQjJF98rIgLqsAiNDJiVqGiRWi8:IyI07l5N2qFHnNCnQjJnw1HMjN |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2508)
Reads the computer name
- OUTLOOK.EXE (PID: 2508)
Searches for installed software
- OUTLOOK.EXE (PID: 2508)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2508)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3152)
Checks supported languages
- OUTLOOK.EXE (PID: 2508)
INFO
Reads the computer name
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 3152)
Application launched itself
- iexplore.exe (PID: 3728)
Reads settings of System Certificates
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 3152)
Checks supported languages
- iexplore.exe (PID: 3152)
- iexplore.exe (PID: 3728)
Reads internet explorer settings
- iexplore.exe (PID: 3152)
Changes internet zones settings
- iexplore.exe (PID: 3728)
Checks Windows Trust Settings
- iexplore.exe (PID: 3152)
- iexplore.exe (PID: 3728)
Creates files in the user directory
- iexplore.exe (PID: 3152)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3728)
Changes settings of System certificates
- iexplore.exe (PID: 3728)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2508 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\uploads_faeac3a0-9e5d-4a89-bb82-f99827cd5cef.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3152 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3728 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
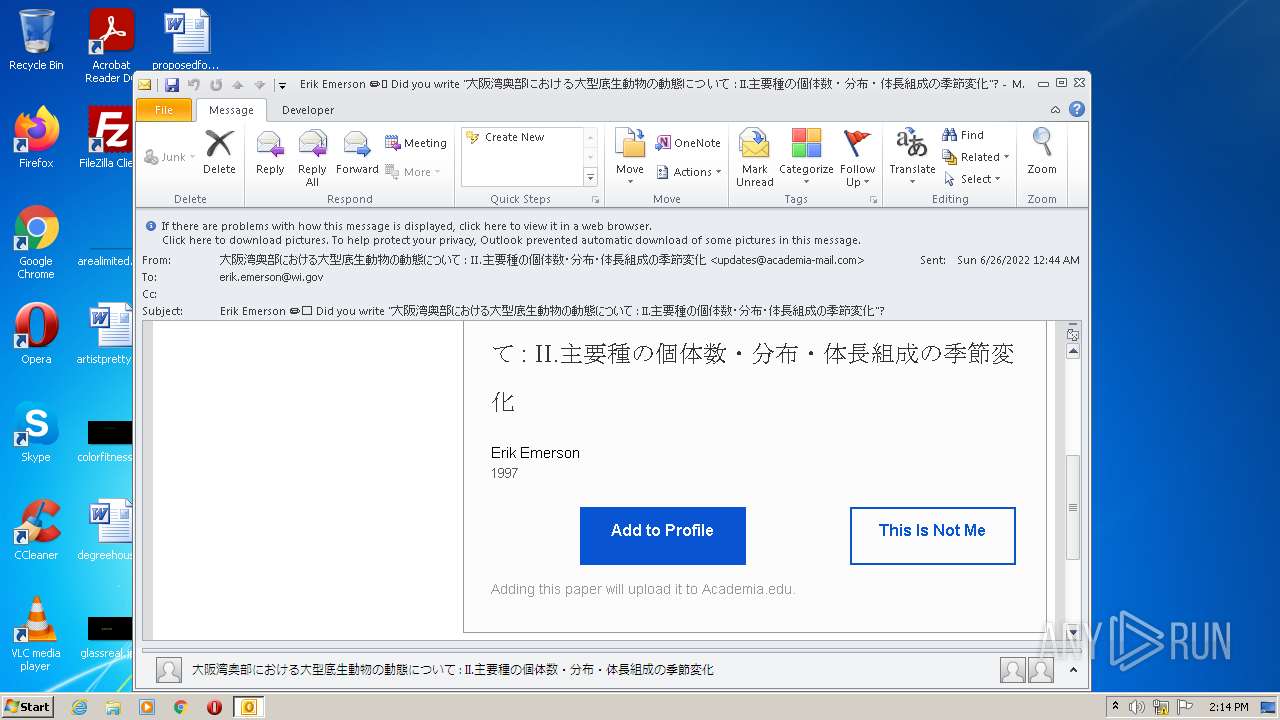
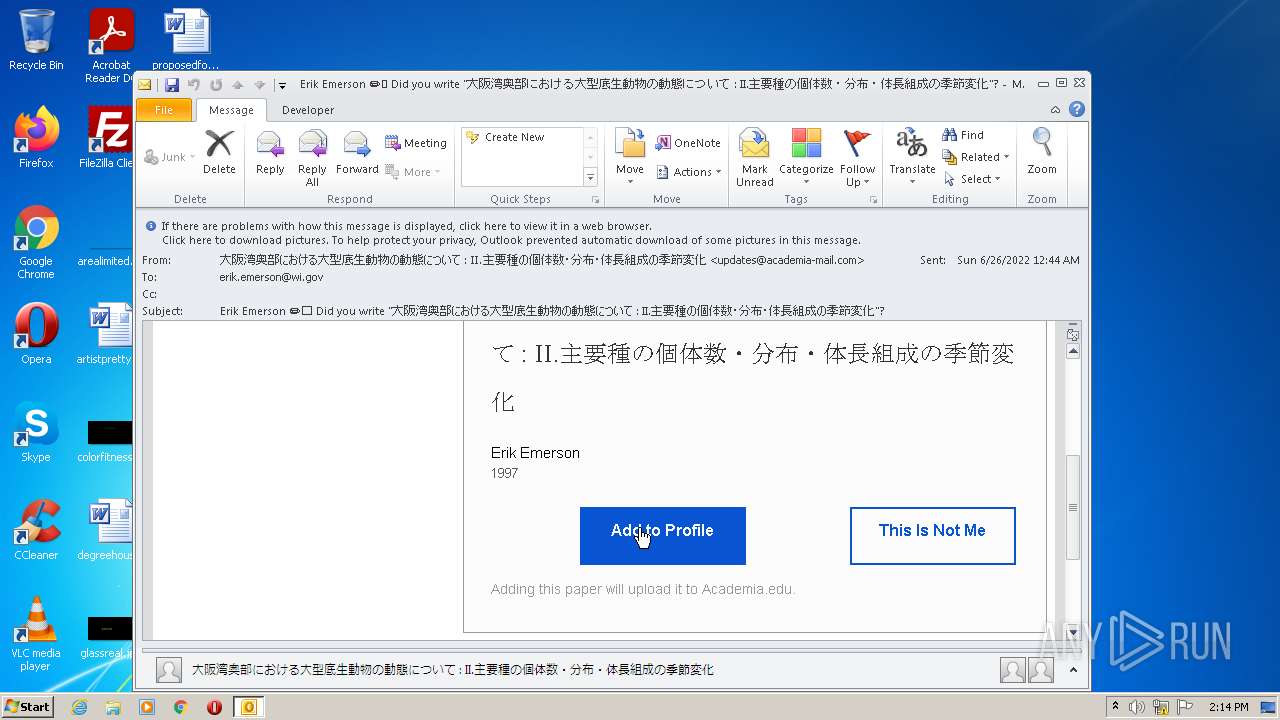
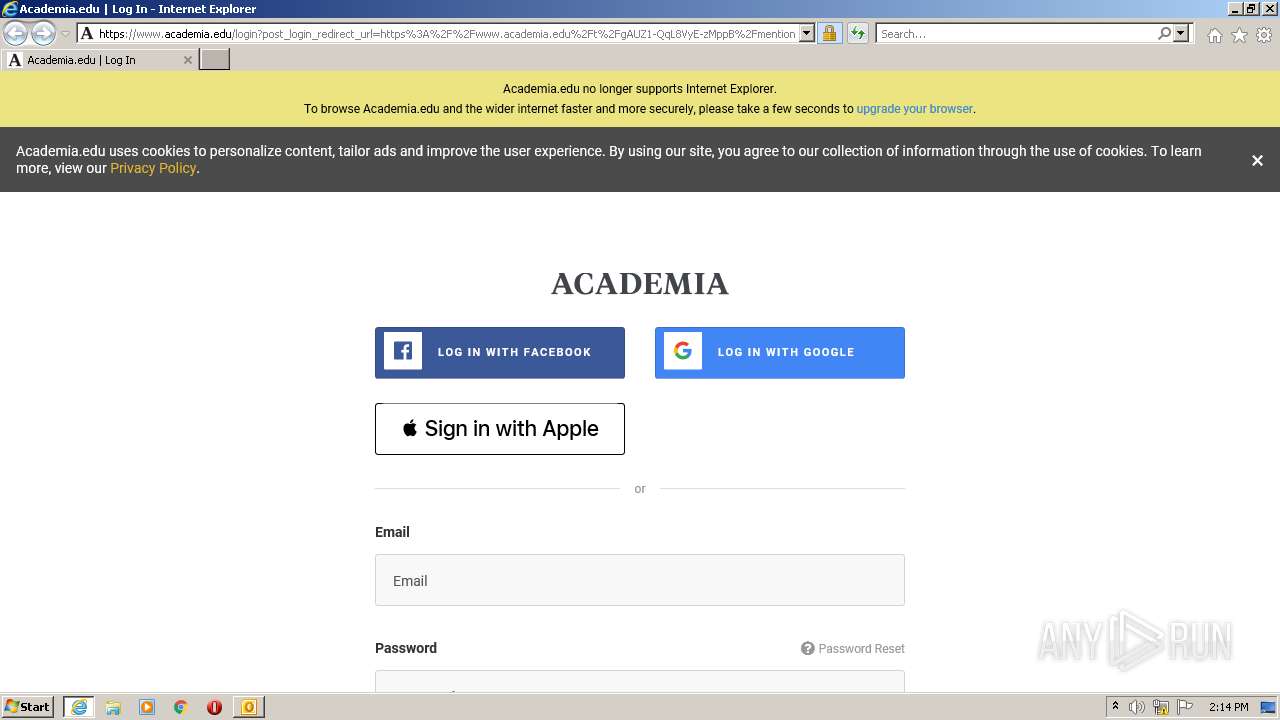
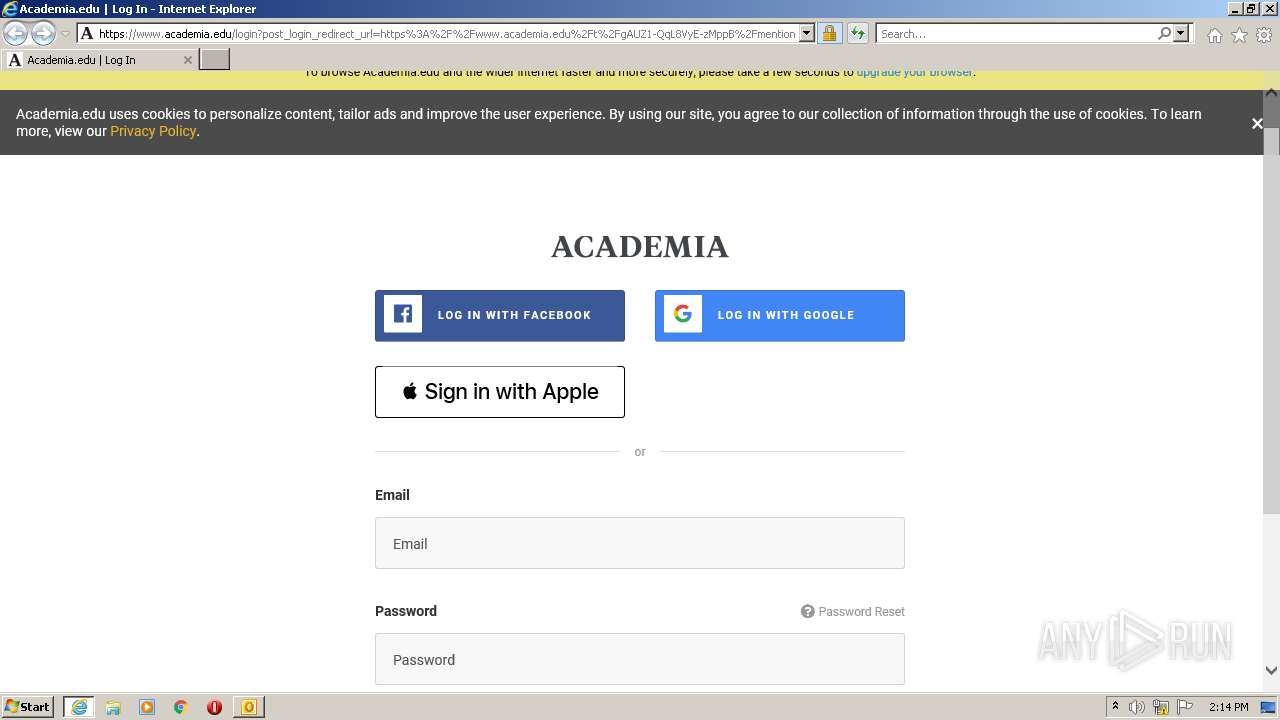
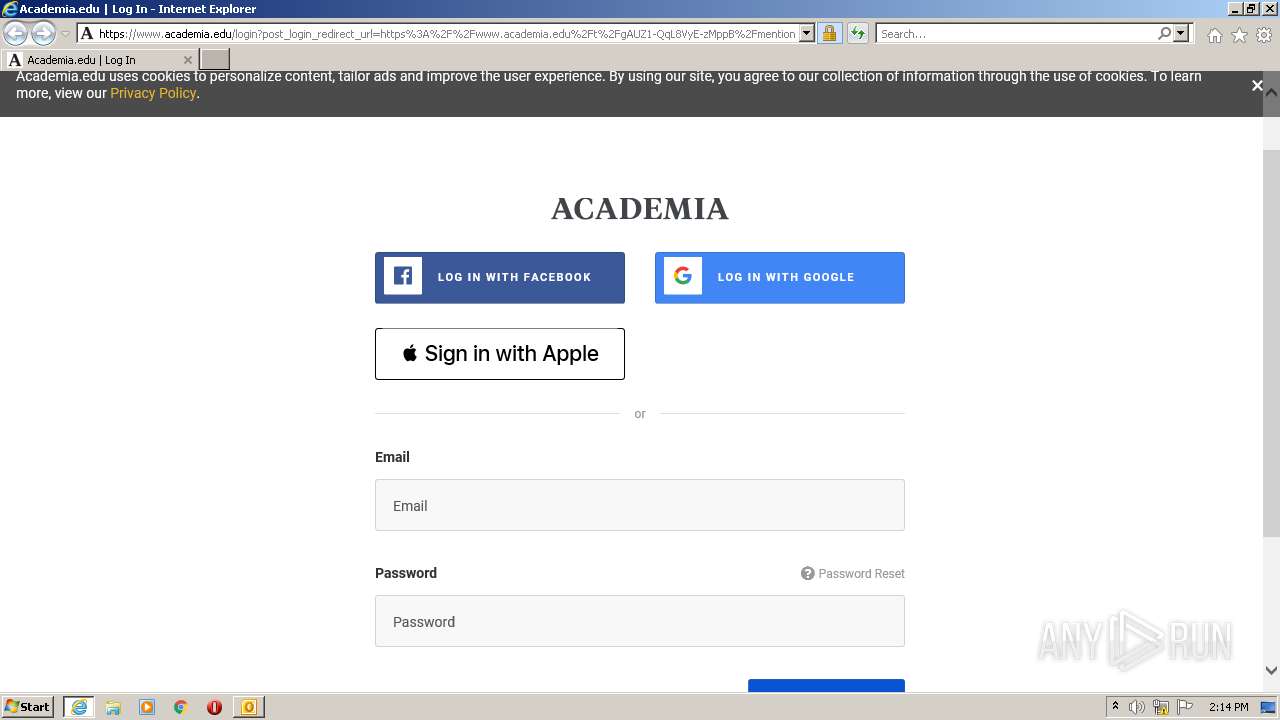
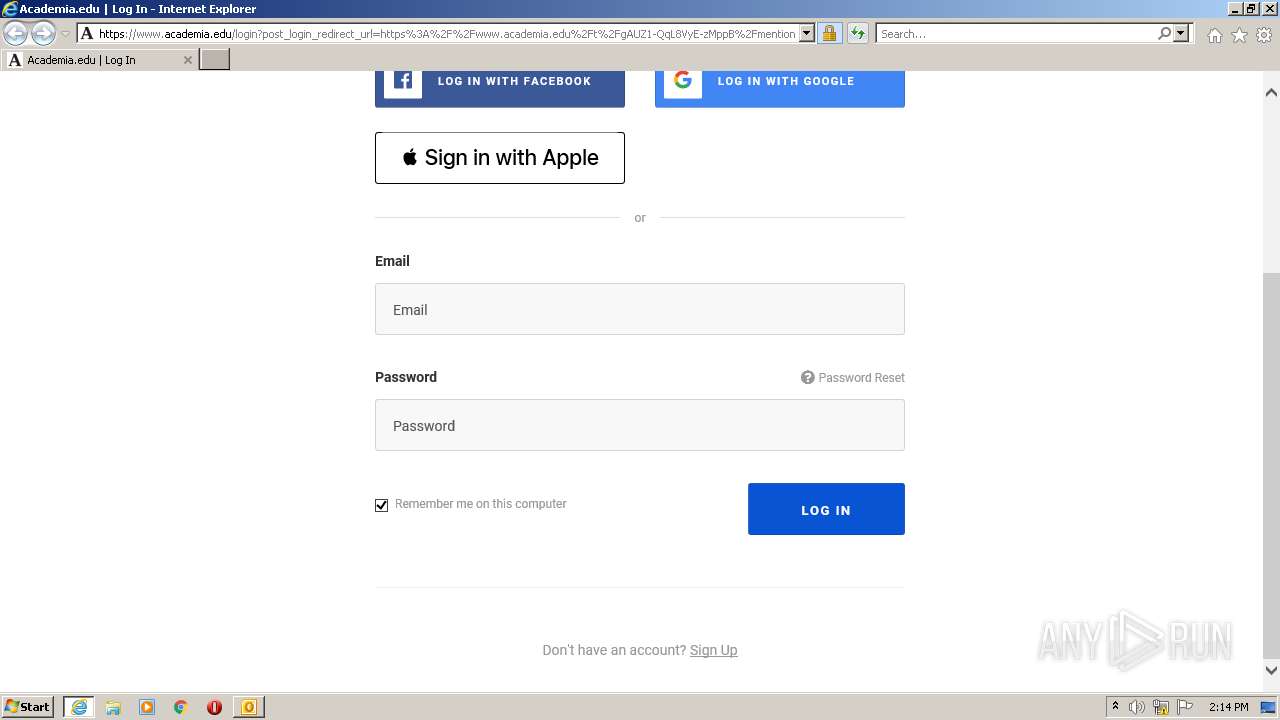
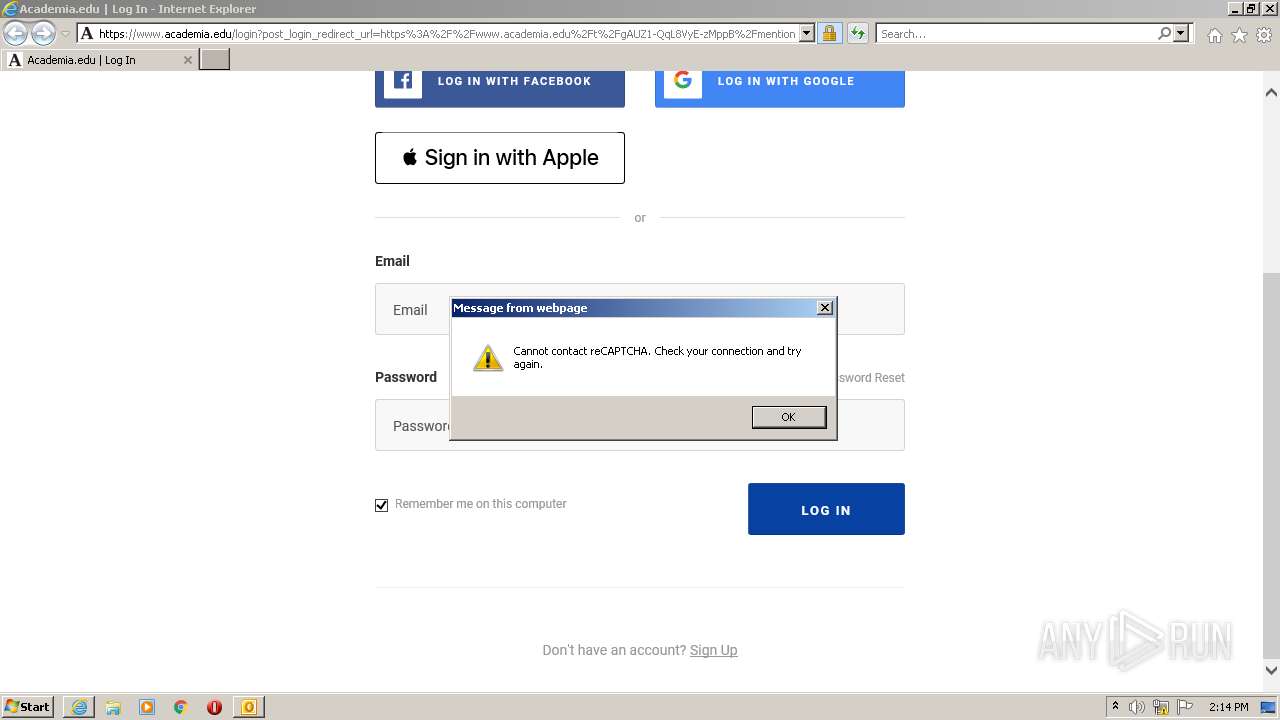
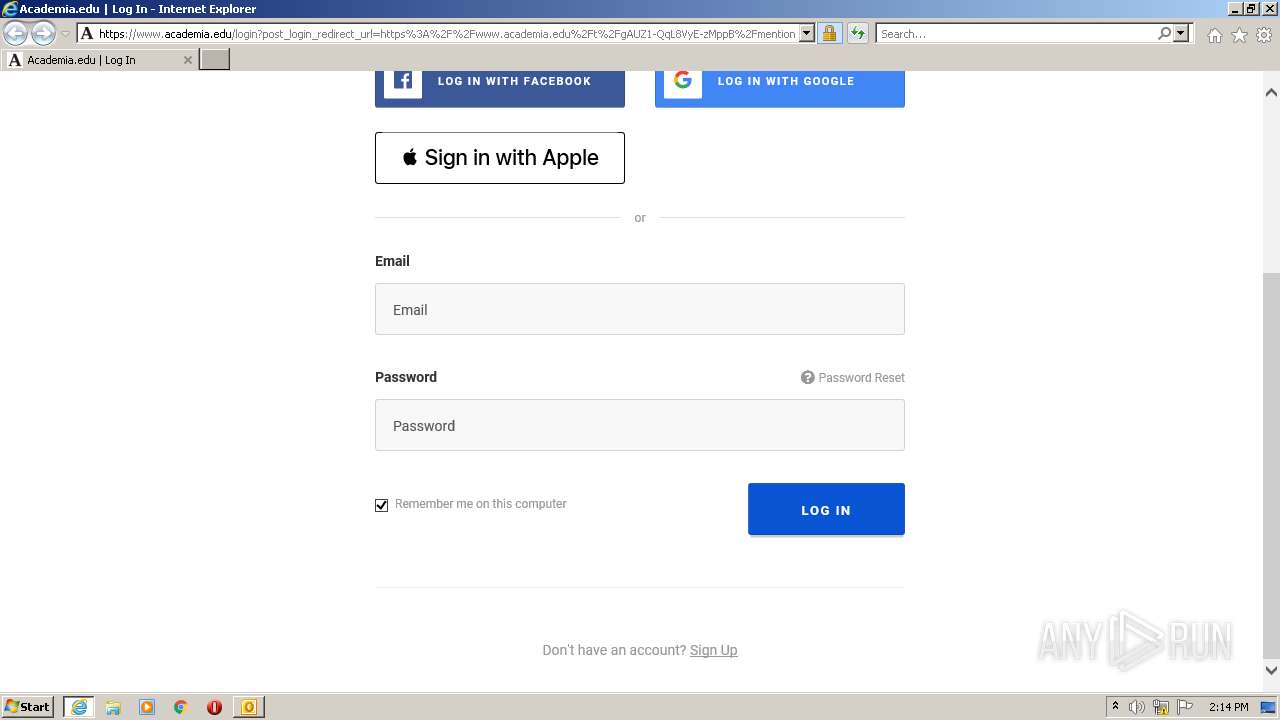
| 3728 | "C:\Program Files\Internet Explorer\iexplore.exe" https://secure-web.cisco.com/1utMBsLbyV_M-h8aojpUmrVWDxiGqO0wqlzwT5TIdNDc8m0qRy1ONQENaNbHvMIFkKj32CGnlx68fNnHxyP5ZtYHRH172pCB-l7PgL6zgLG5hTDc0IzPoUaDdftav8--kxn8tn4j8uKcT2t1z8ZUhw30H_nZMm71AYwlmA5U3HT_Q7dlgBH1Da1U-b7r-SYXfvbFYkbLtBZCenpnDpK7hfFFF16_uJSQ5WY2ClVy7uhrLzWSJomXUkQxcti5tKLPKx0Z8vZzJMqEoWUP1mF_idLIPZasHJ4HGZR6nZBK4Xv6MjPyCVjd6I6GtgWiRklqiqc8tHpXnWs-FaaP0Yl2wkQ/https%3A%2F%2Fwww.academia.edu%2Fkeypass%2FVDlJdkhwV2J2bnQvMFZVUmtMeHlxQ2Z4RU1PL2dTWmJIUXFKWlNxVGc2Zz0tLWtXYllMQngyc3NaM2dhVW4zQTlmaVE9PQ%3D%3D--caee63d0ec9c6d59aa15de11f10721760bfdc343%2Ft%2FgAUZ1-QqL8VyE-zMppB%2Fmentions%2Fclaim_papers%2Fclaim%3Fpaper_id%3D580488196 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
22 511
Read events
21 757
Write events
730
Delete events
24
Modification events
| (PID) Process: | (2508) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2508) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2508) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2508) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2508) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2508) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2508) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2508) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2508) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2508) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
28
Text files
59
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2508 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR5A4C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2508 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2508 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2508 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2508 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{64D4F336-C899-4007-A395-8A8AF8C1261B}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 2508 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_F3E2F4966884444BB6257E72ED8C0D50.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
| 2508 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_6AB572A7B6FB7345830F401E27E3CE39.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 2508 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_107963688EA810478306D5DA2DAB7A10.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6CFED4E1A8866BE87BE17622BFB4D726_FBADB8F7FD7B56EE191ACF24A8989D94 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
92
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3152 | iexplore.exe | GET | — | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC4AQFyTCvCchJ%2FC984V1eJ | US | — | — | whitelisted |
3152 | iexplore.exe | GET | — | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEAT%2FrubUb6nOEpcsoEFY3SI%3D | US | — | — | whitelisted |
2508 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3152 | iexplore.exe | GET | — | 18.66.242.58:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | — | — | shared |
3152 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDHcc6QGVhwAwqBwrQ6ks05 | US | der | 472 b | whitelisted |
3152 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3152 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDHcc6QGVhwAwqBwrQ6ks05 | US | der | 471 b | whitelisted |
3152 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCfB0sRdF8W%2FBIjdfpYeZPw | US | der | 472 b | whitelisted |
3152 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3152 | iexplore.exe | GET | 200 | 192.35.177.23:80 | http://commercial.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTQfEOioPd4%2FtCA3%2FhgDklRXB0FwgQU7UQZwNPwBovupHu%2BQucmVMiONnYCEEABbvsKIFz66%2BGPcdc6u3g%3D | US | der | 1.63 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2508 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3152 | iexplore.exe | 146.112.255.69:443 | secure-web.cisco.com | OpenDNS, LLC | — | suspicious |
3152 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3152 | iexplore.exe | 192.35.177.23:80 | commercial.ocsp.identrust.com | IdenTrust | US | unknown |
3728 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3152 | iexplore.exe | 52.222.236.49:443 | www.academia.edu | Amazon.com, Inc. | US | suspicious |
3152 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | — | US | suspicious |
3152 | iexplore.exe | 13.32.121.21:443 | sb.scorecardresearch.com | Amazon.com, Inc. | US | suspicious |
3152 | iexplore.exe | 104.92.101.166:443 | appleid.cdn-apple.com | Akamai Technologies, Inc. | NL | unknown |
3152 | iexplore.exe | 142.250.184.227:443 | recaptcha.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
secure-web.cisco.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
commercial.ocsp.identrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.academia.edu |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |