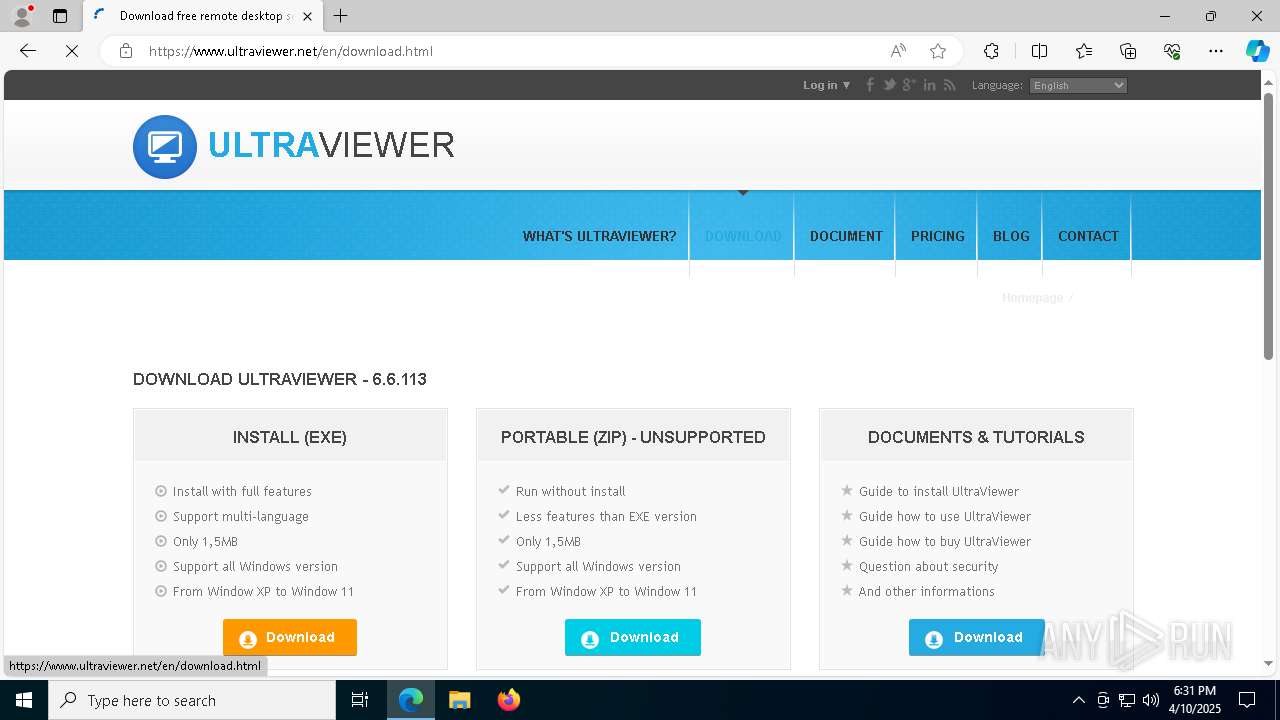
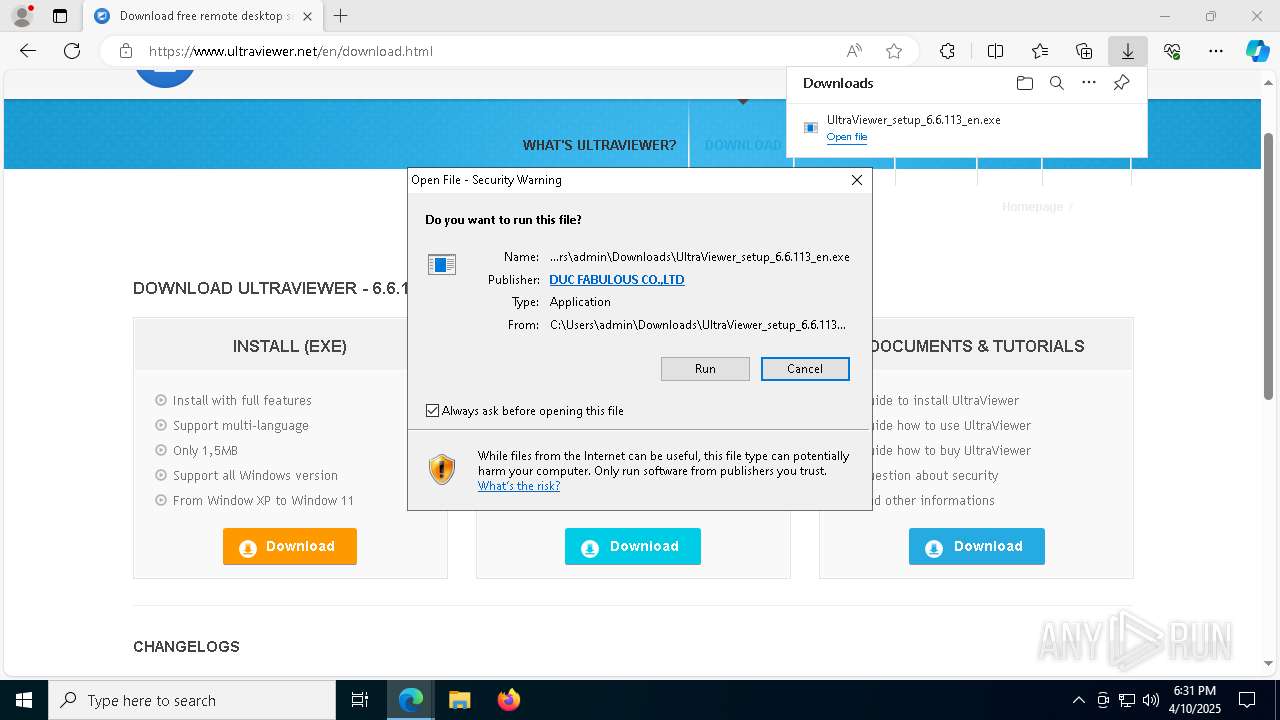
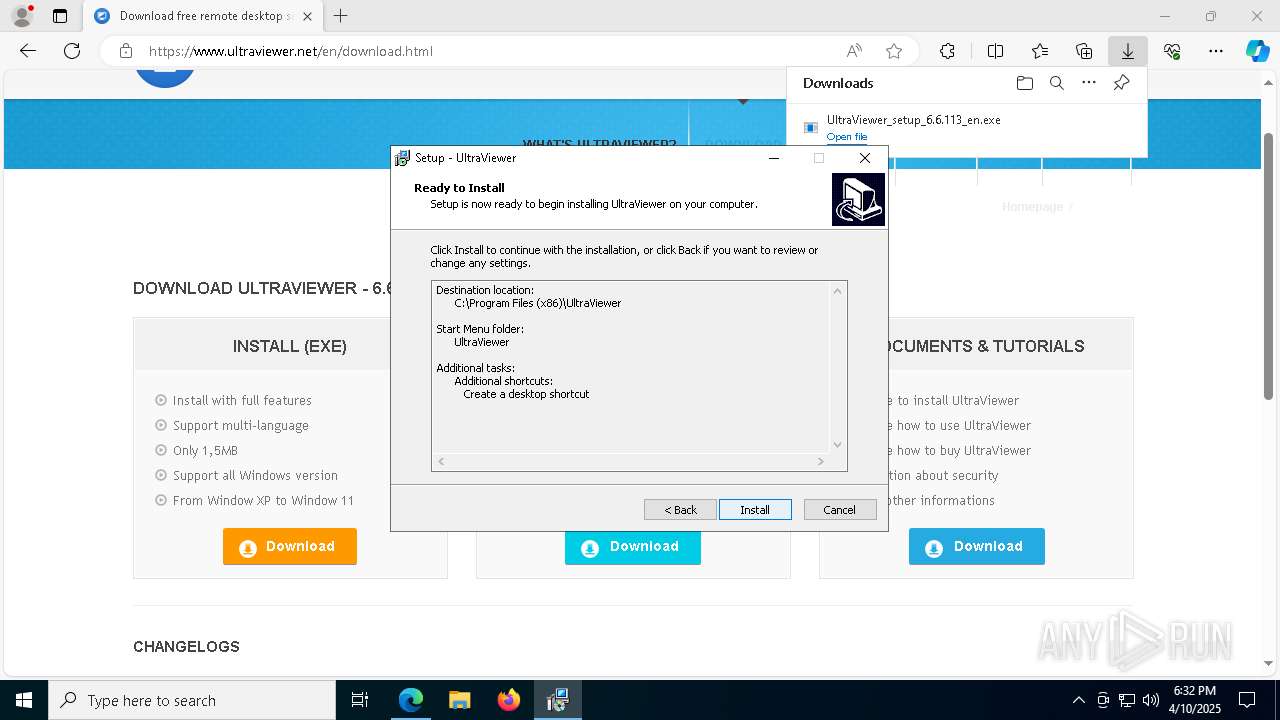
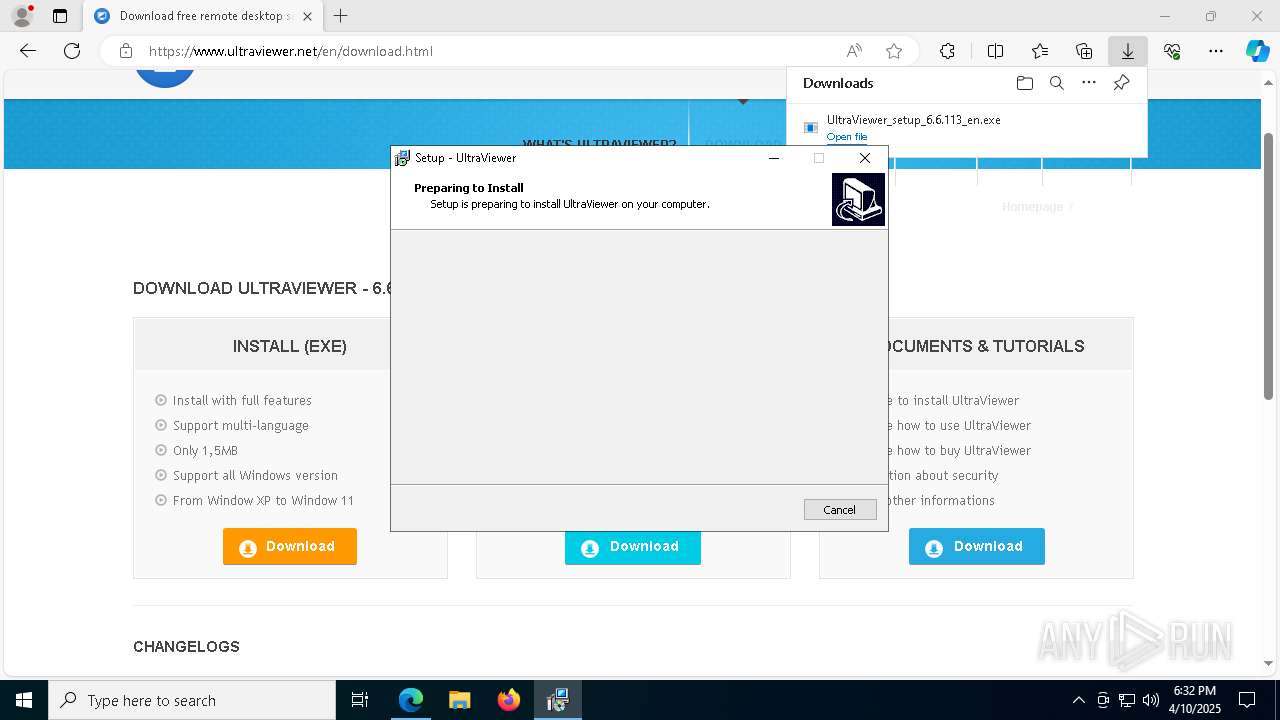
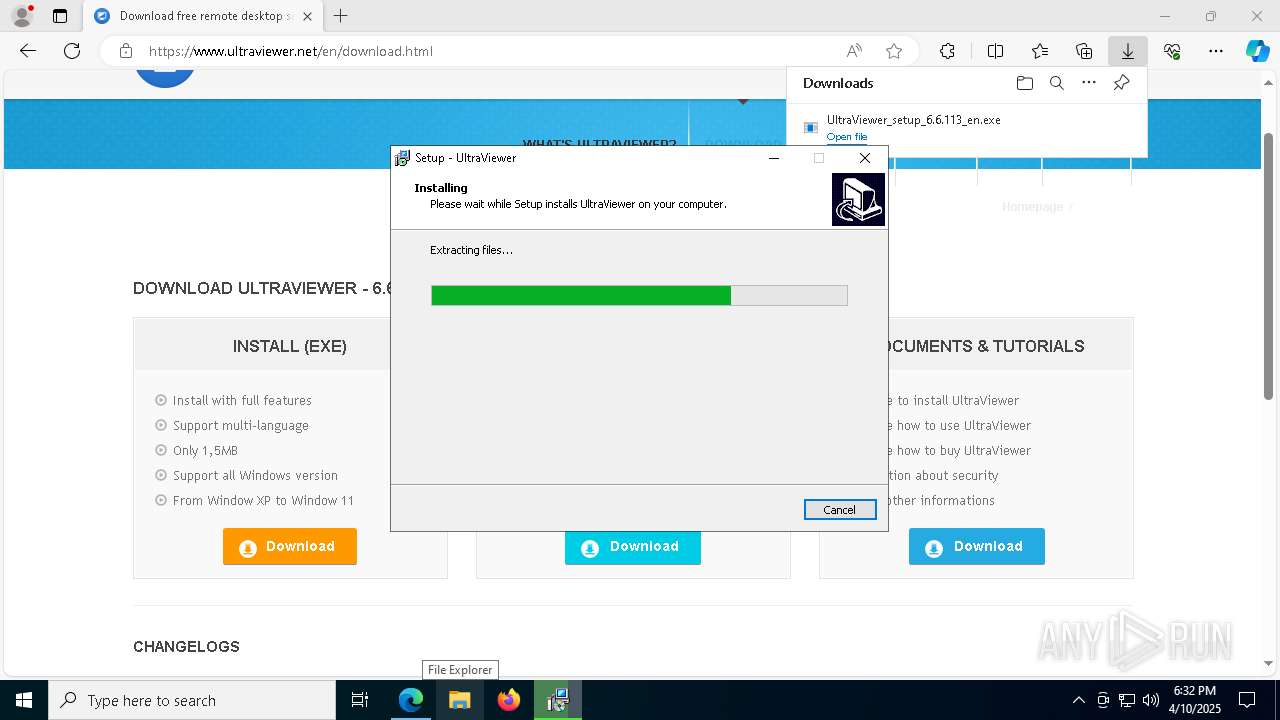
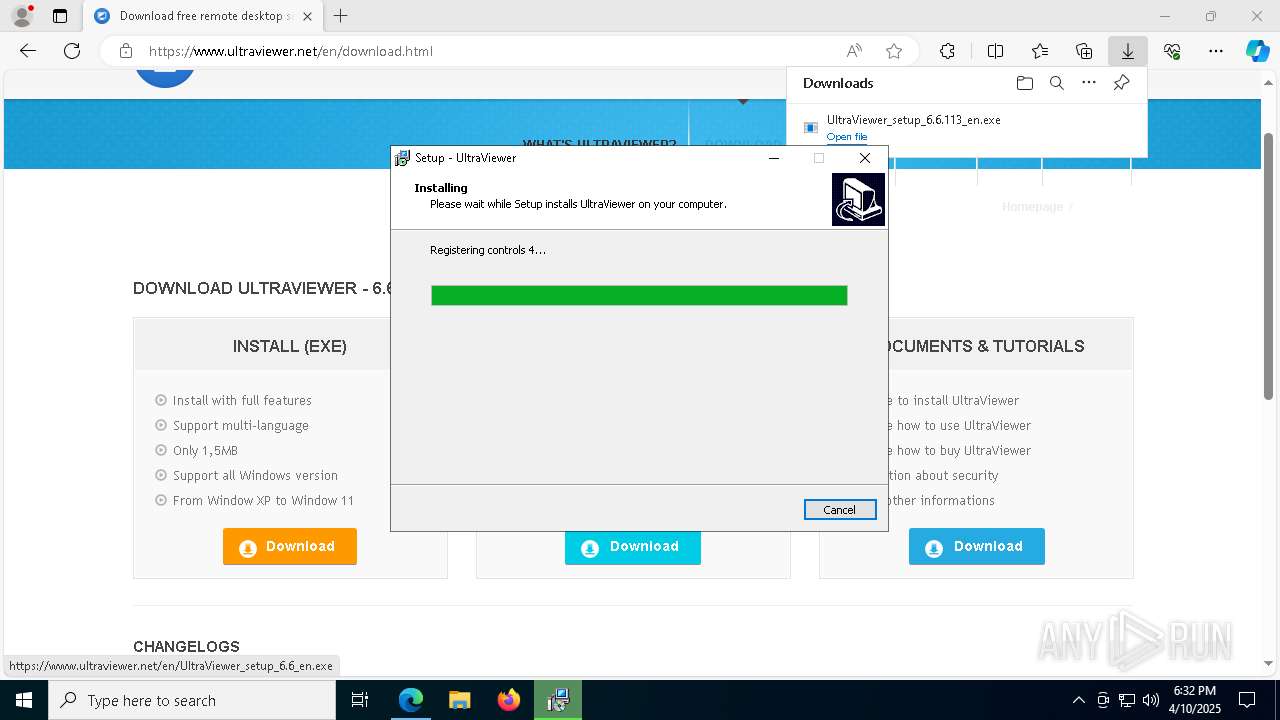
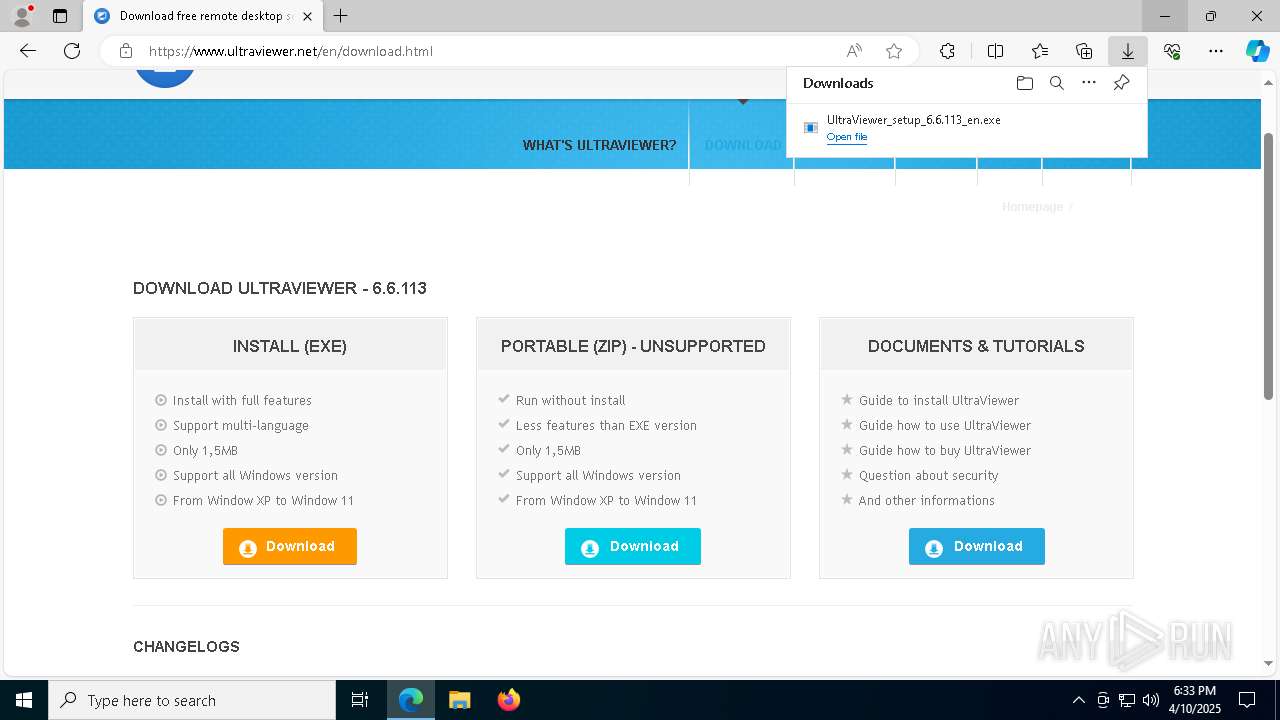
| URL: | https://www.ultraviewer.net |
| Full analysis: | https://app.any.run/tasks/364723cb-742b-4c67-ae4e-4099adff5151 |
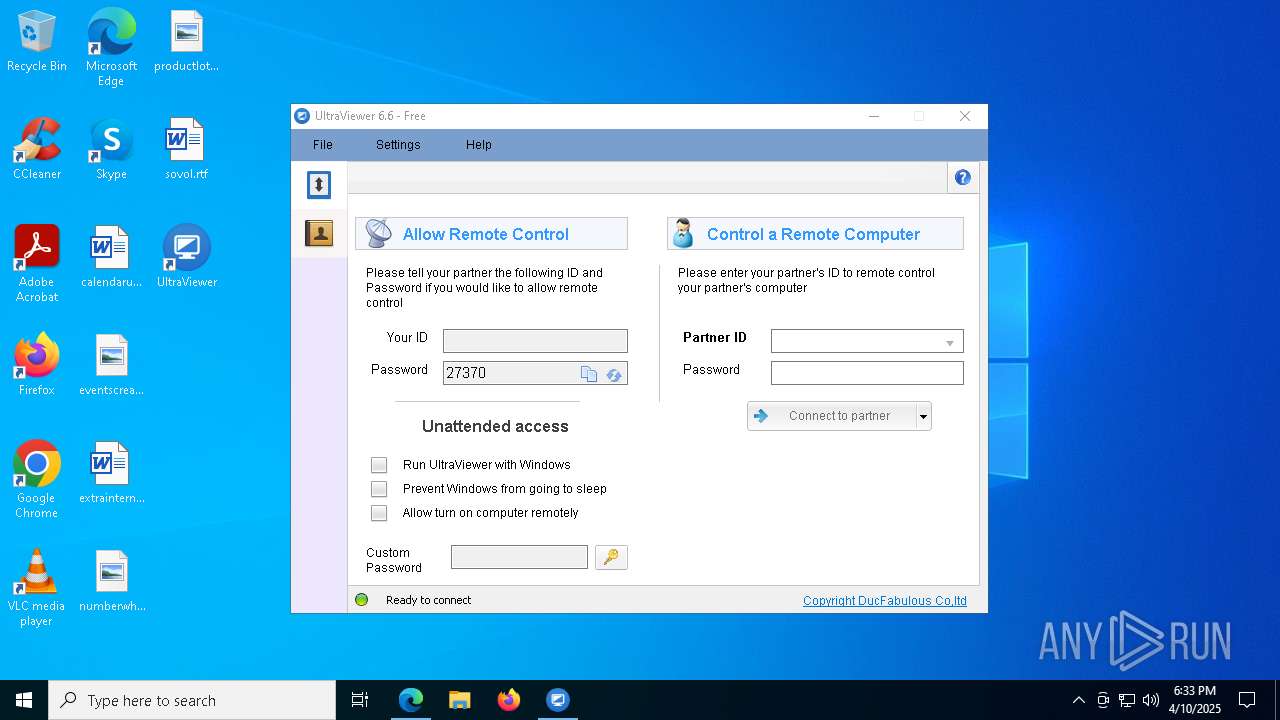
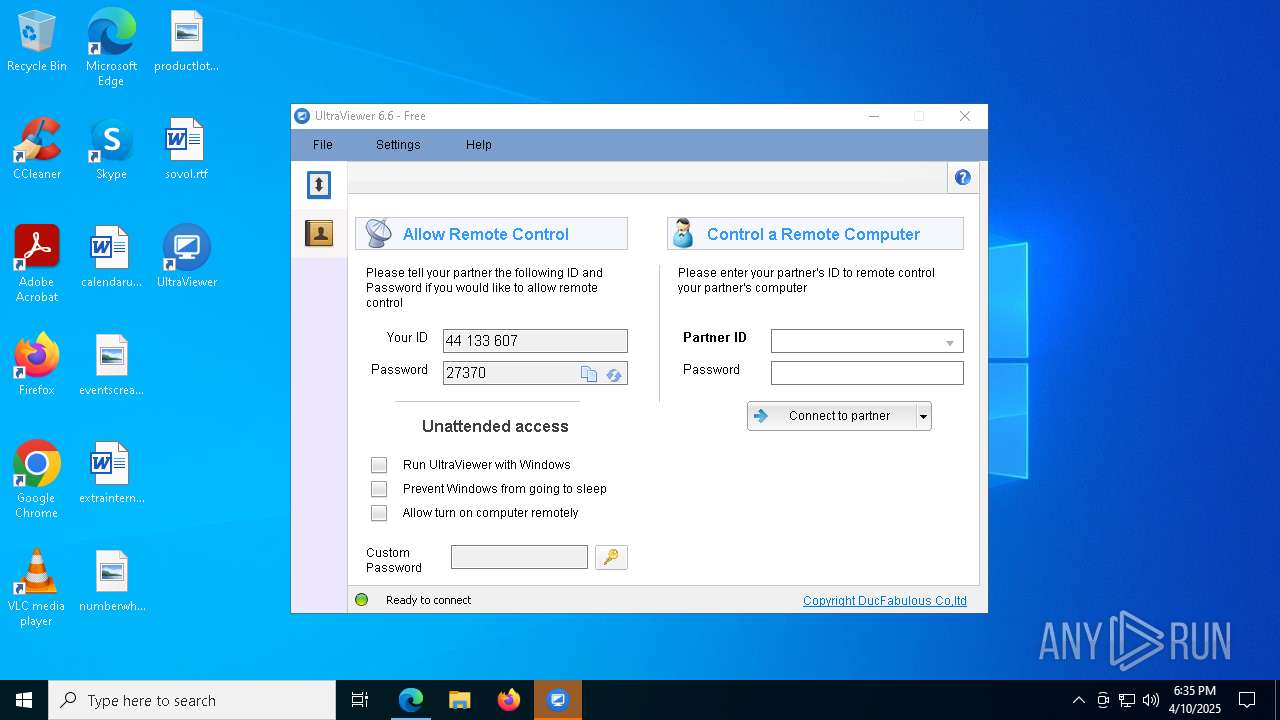
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2025, 18:31:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C0AFC4F460B3758512C22B54454C0451 |
| SHA1: | 92B887807B9EF0F5A4B6106ABCADE1EC8D52C2DA |
| SHA256: | 8A4D30FF0AB5B4BA1E442A0DC8A980B25E2A216EB35A00506D1FCD9E313164B3 |
| SSDEEP: | 3:N8DSLjBzv0:2OL1w |
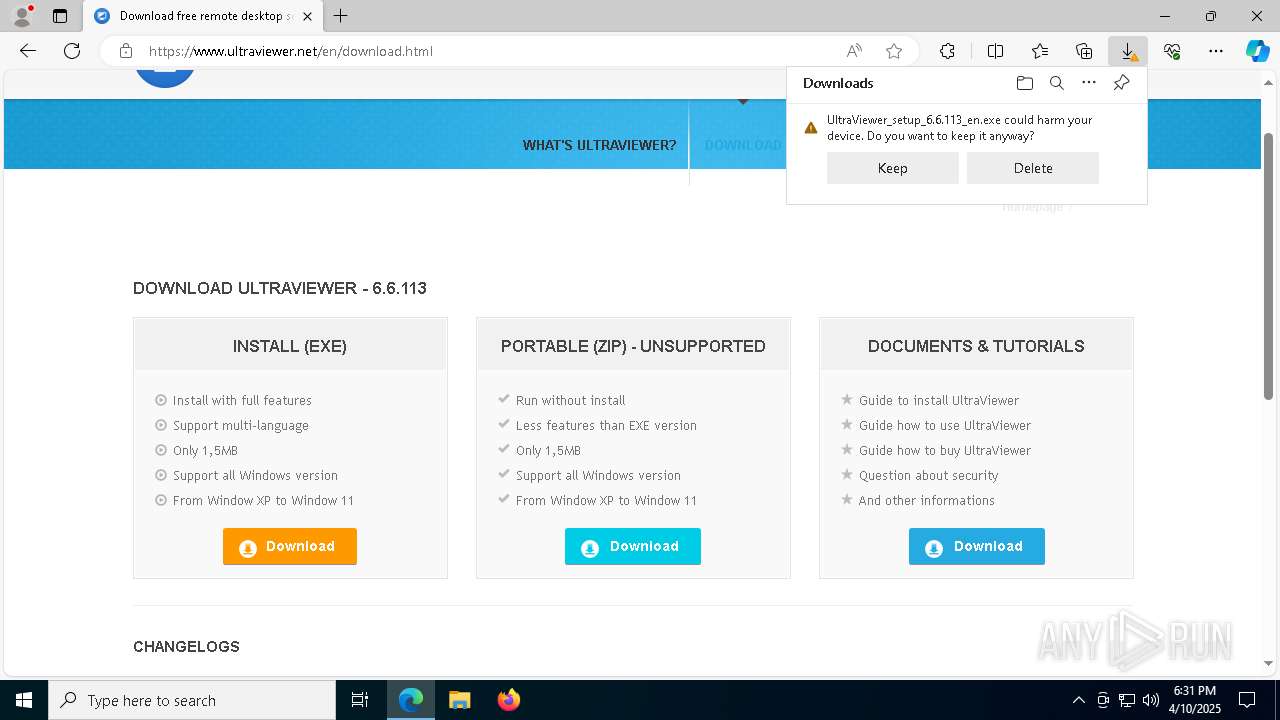
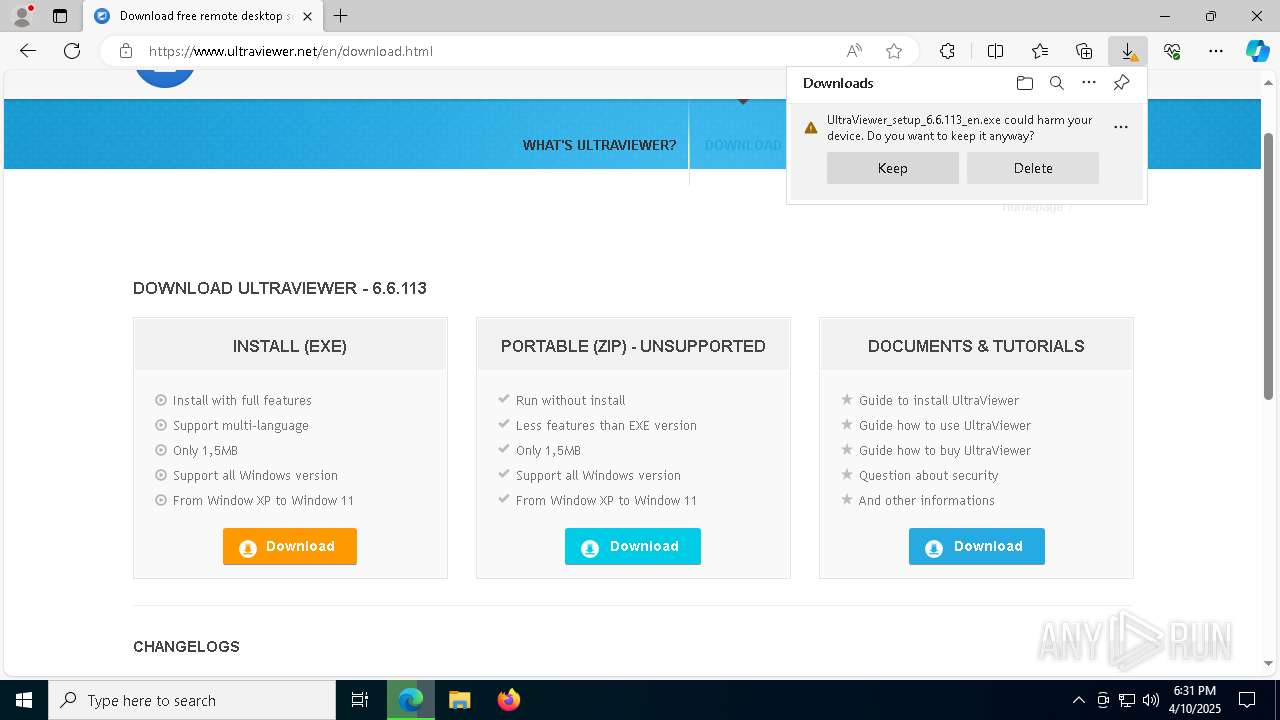
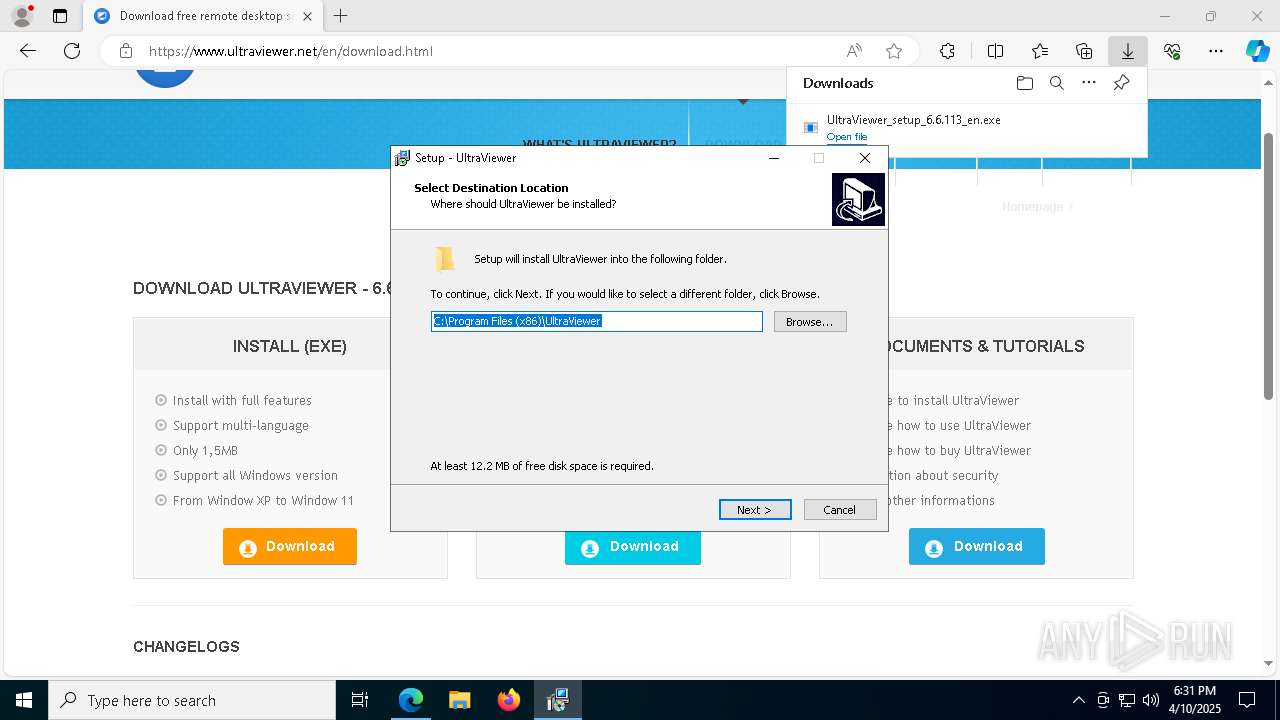
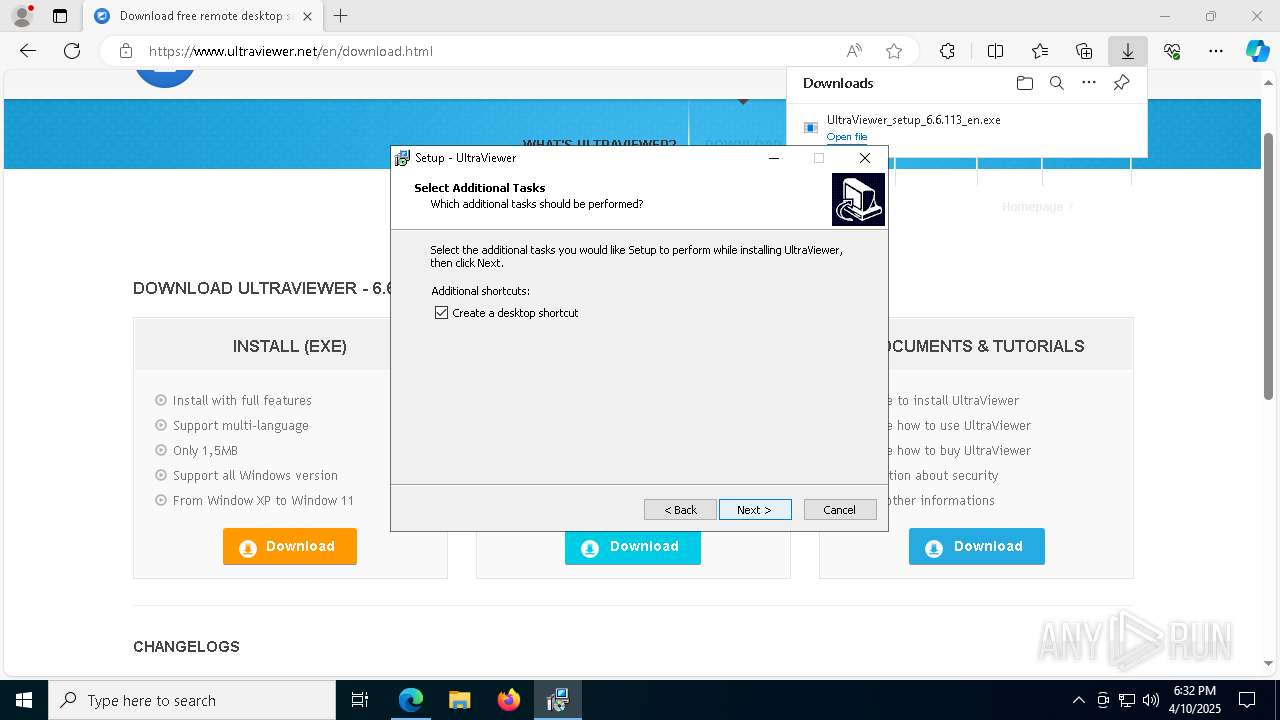
MALICIOUS
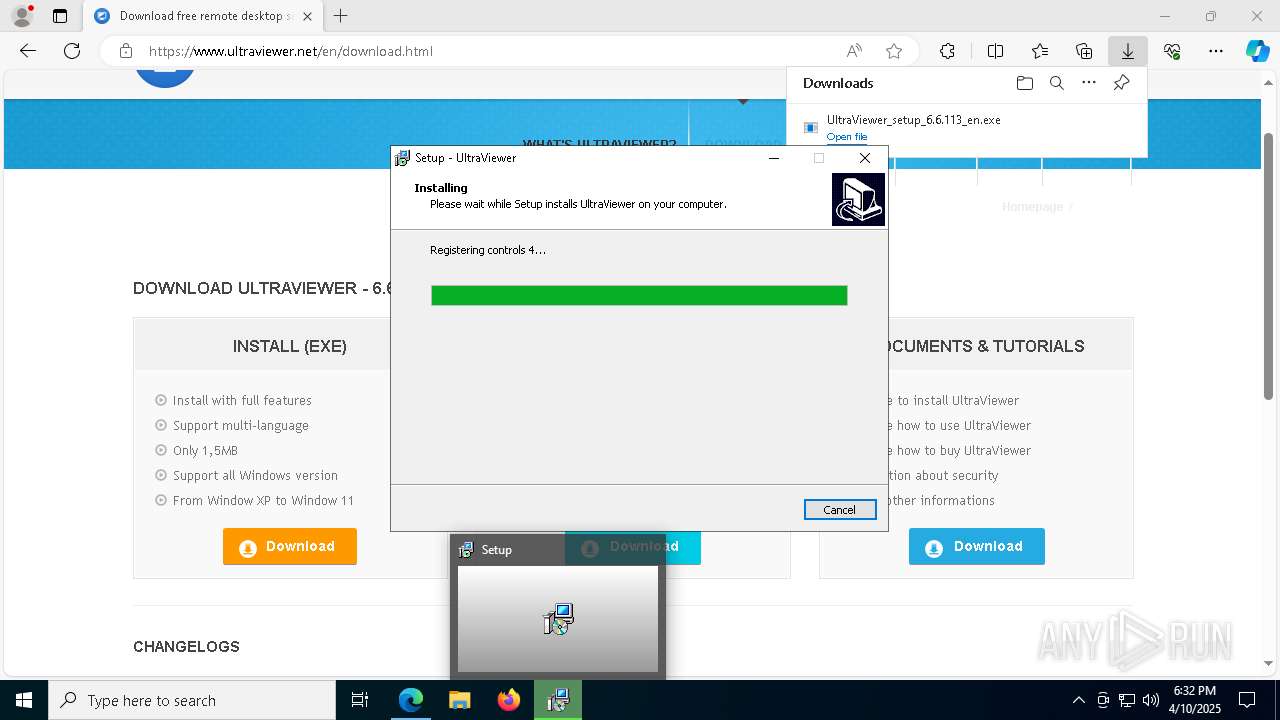
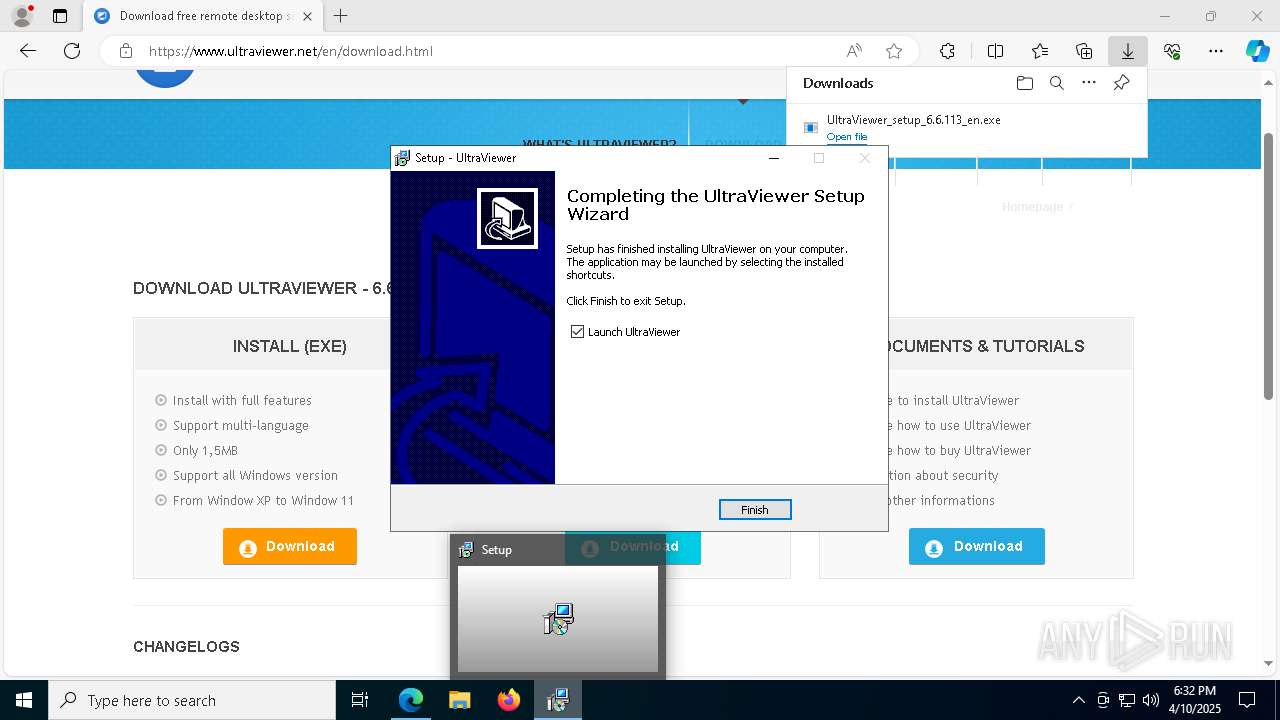
Executing a file with an untrusted certificate
- UltraViewer_setup_6.6.113_en.exe (PID: 864)
- UltraViewer_setup_6.6.113_en.exe (PID: 6388)
- UltraViewer_Desktop.exe (PID: 7908)
- UltraViewer_Desktop.exe (PID: 7424)
- UltraViewer_Service.exe (PID: 6828)
- UltraViewer_Desktop.exe (PID: 4108)
- UltraViewer_Desktop.exe (PID: 3016)
- UltraViewer_Desktop.exe (PID: 1540)
- UltraViewer_Desktop.exe (PID: 5868)
- UltraViewer_Desktop.exe (PID: 7764)
Starts NET.EXE for service management
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
- net.exe (PID: 5376)
- net.exe (PID: 1676)
SUSPICIOUS
Executable content was dropped or overwritten
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
- UltraViewer_setup_6.6.113_en.exe (PID: 864)
- UltraViewer_setup_6.6.113_en.exe (PID: 6388)
Reads the Windows owner or organization settings
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
Reads security settings of Internet Explorer
- UltraViewer_setup_6.6.113_en.tmp (PID: 5084)
- RegAsm.exe (PID: 7476)
- UltraViewer_Desktop.exe (PID: 7908)
- RegAsm.exe (PID: 6036)
- UltraViewer_Service.exe (PID: 6828)
- UltraViewer_Desktop.exe (PID: 3016)
- UltraViewer_Desktop.exe (PID: 5868)
Windows service management via SC.EXE
- sc.exe (PID: 6264)
Process drops legitimate windows executable
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
There is functionality for taking screenshot (YARA)
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
- UltraViewer_Desktop.exe (PID: 3016)
- UltraViewer_Desktop.exe (PID: 5868)
Uses TASKKILL.EXE to kill process
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
Reads Microsoft Outlook installation path
- UltraViewer_Desktop.exe (PID: 7908)
- UltraViewer_Desktop.exe (PID: 3016)
- UltraViewer_Desktop.exe (PID: 5868)
Reads Internet Explorer settings
- UltraViewer_Desktop.exe (PID: 7908)
- UltraViewer_Desktop.exe (PID: 5868)
- UltraViewer_Desktop.exe (PID: 3016)
Creates/Modifies COM task schedule object
- RegAsm.exe (PID: 6036)
- RegAsm.exe (PID: 7476)
Restarts service on failure
- sc.exe (PID: 6572)
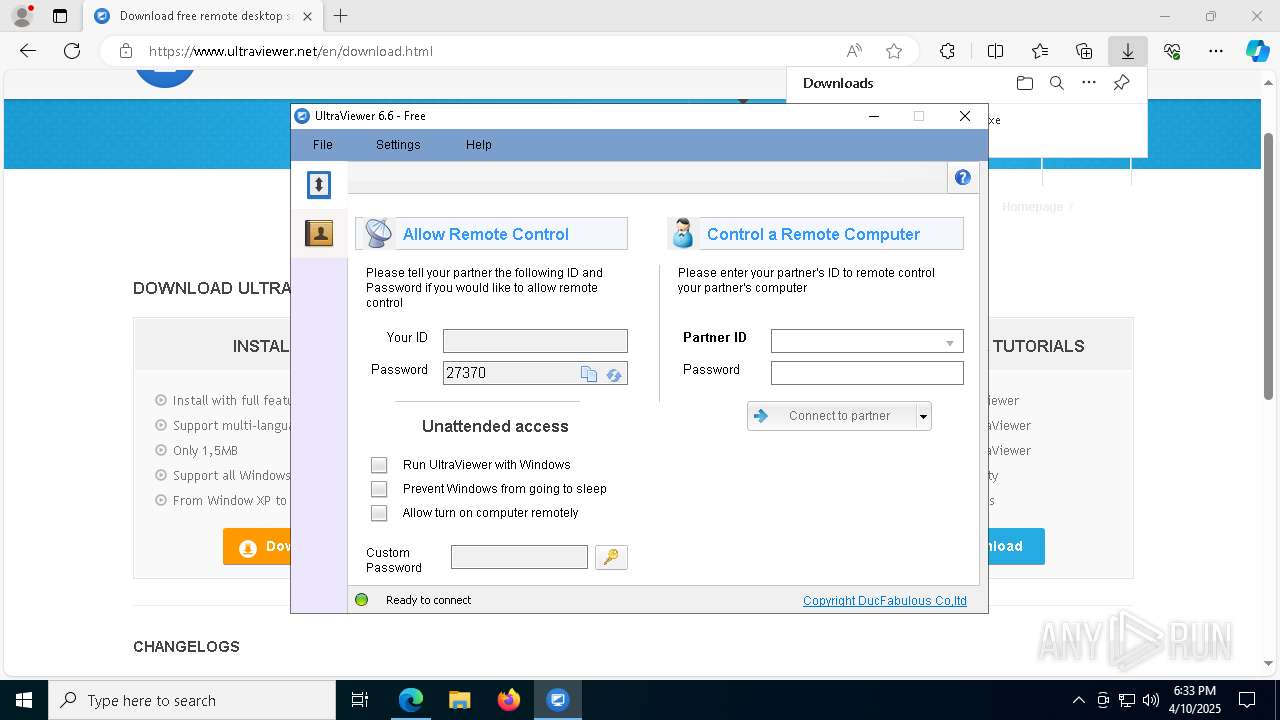
Executes as Windows Service
- UltraViewer_Service.exe (PID: 6828)
Starts CMD.EXE for commands execution
- UltraViewer_Desktop.exe (PID: 3016)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 444)
Executing commands from a ".bat" file
- UltraViewer_Desktop.exe (PID: 3016)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 5048)
- msedge.exe (PID: 7352)
- msedge.exe (PID: 728)
Application launched itself
- msedge.exe (PID: 5048)
Reads Environment values
- identity_helper.exe (PID: 4120)
Checks supported languages
- identity_helper.exe (PID: 4120)
- UltraViewer_setup_6.6.113_en.exe (PID: 864)
- UVUninstallHelper.exe (PID: 4464)
- UltraViewer_setup_6.6.113_en.tmp (PID: 5084)
- UltraViewer_setup_6.6.113_en.exe (PID: 6388)
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
- UltraViewer_Desktop.exe (PID: 7908)
- RegAsm.exe (PID: 7476)
- RegAsm.exe (PID: 6036)
- UltraViewer_Desktop.exe (PID: 7424)
- UltraViewer_Desktop.exe (PID: 4108)
- UltraViewer_Service.exe (PID: 6828)
- RegAsm.exe (PID: 5232)
- RegAsm.exe (PID: 2552)
- UltraViewer_Desktop.exe (PID: 3016)
- RegAsm.exe (PID: 4620)
- UltraViewer_Desktop.exe (PID: 1540)
- uv_x64.exe (PID: 5136)
- uv_x64.exe (PID: 1812)
- UltraViewer_Desktop.exe (PID: 7764)
- UltraViewer_Desktop.exe (PID: 5868)
Reads the computer name
- identity_helper.exe (PID: 4120)
- UVUninstallHelper.exe (PID: 4464)
- UltraViewer_setup_6.6.113_en.tmp (PID: 5084)
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
- RegAsm.exe (PID: 7476)
- UltraViewer_Desktop.exe (PID: 7908)
- RegAsm.exe (PID: 6036)
- UltraViewer_Desktop.exe (PID: 7424)
- UltraViewer_Service.exe (PID: 6828)
- UltraViewer_Desktop.exe (PID: 4108)
- RegAsm.exe (PID: 5232)
- RegAsm.exe (PID: 2552)
- RegAsm.exe (PID: 4620)
- UltraViewer_Desktop.exe (PID: 1540)
- UltraViewer_Desktop.exe (PID: 3016)
- uv_x64.exe (PID: 5136)
- UltraViewer_Desktop.exe (PID: 5868)
- UltraViewer_Desktop.exe (PID: 7764)
- uv_x64.exe (PID: 1812)
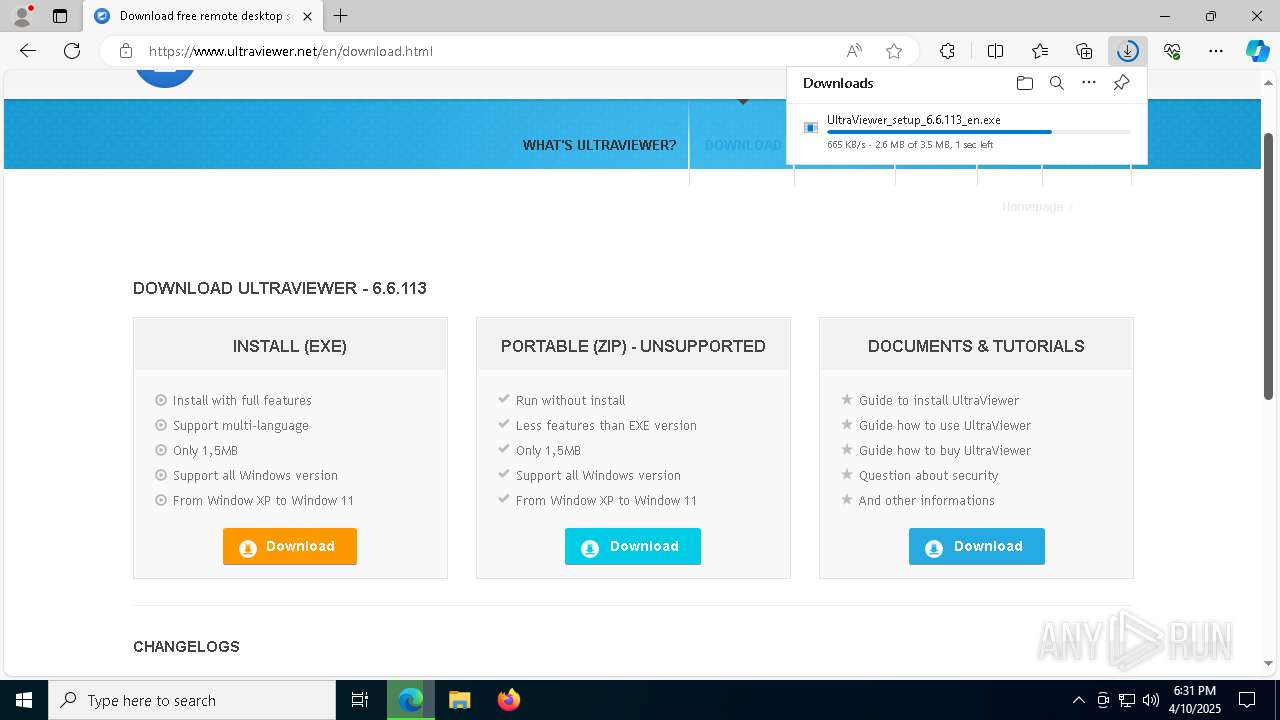
Autorun file from Downloads
- msedge.exe (PID: 5964)
- msedge.exe (PID: 5048)
Create files in a temporary directory
- UltraViewer_setup_6.6.113_en.exe (PID: 864)
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
- UltraViewer_setup_6.6.113_en.exe (PID: 6388)
- UltraViewer_Desktop.exe (PID: 7908)
- UltraViewer_Desktop.exe (PID: 3016)
- UltraViewer_Desktop.exe (PID: 5868)
Process checks computer location settings
- UltraViewer_setup_6.6.113_en.tmp (PID: 5084)
The sample compiled with english language support
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
- msedge.exe (PID: 728)
Compiled with Borland Delphi (YARA)
- UltraViewer_setup_6.6.113_en.exe (PID: 864)
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
- UltraViewer_setup_6.6.113_en.exe (PID: 6388)
- UltraViewer_setup_6.6.113_en.tmp (PID: 5084)
Detects InnoSetup installer (YARA)
- UltraViewer_setup_6.6.113_en.exe (PID: 864)
- UltraViewer_setup_6.6.113_en.tmp (PID: 5084)
- UltraViewer_setup_6.6.113_en.exe (PID: 6388)
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
UPX packer has been detected
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
- UltraViewer_Desktop.exe (PID: 3016)
- UltraViewer_Desktop.exe (PID: 5868)
Confuser has been detected (YARA)
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
ULTRAVIEWER has been detected
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
- RegAsm.exe (PID: 7476)
- UltraViewer_Desktop.exe (PID: 7908)
- RegAsm.exe (PID: 6036)
- UltraViewer_Desktop.exe (PID: 7424)
- conhost.exe (PID: 3332)
- UltraViewer_Service.exe (PID: 6828)
- UltraViewer_Desktop.exe (PID: 4108)
- RegAsm.exe (PID: 5232)
- RegAsm.exe (PID: 2552)
- UltraViewer_Desktop.exe (PID: 3016)
- UltraViewer_setup_6.6.113_en.tmp (PID: 5084)
- RegAsm.exe (PID: 4620)
- UltraViewer_Desktop.exe (PID: 1540)
- conhost.exe (PID: 7588)
- uv_x64.exe (PID: 5136)
- msedge.exe (PID: 4652)
- msedge.exe (PID: 5048)
- conhost.exe (PID: 2148)
- UltraViewer_Desktop.exe (PID: 5868)
- UltraViewer_Desktop.exe (PID: 7764)
- uv_x64.exe (PID: 1812)
- cmd.exe (PID: 444)
- conhost.exe (PID: 4428)
Creates files in the program directory
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
- RegAsm.exe (PID: 7476)
- RegAsm.exe (PID: 6036)
- UltraViewer_Service.exe (PID: 6828)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 7476)
- UltraViewer_Desktop.exe (PID: 7908)
- RegAsm.exe (PID: 6036)
- UltraViewer_Desktop.exe (PID: 7424)
- UltraViewer_Service.exe (PID: 6828)
- UltraViewer_Desktop.exe (PID: 3016)
- UltraViewer_Desktop.exe (PID: 1540)
- uv_x64.exe (PID: 5136)
- UltraViewer_Desktop.exe (PID: 5868)
- UltraViewer_Desktop.exe (PID: 7764)
- uv_x64.exe (PID: 1812)
Reads the software policy settings
- slui.exe (PID: 7900)
- UltraViewer_Service.exe (PID: 6828)
- slui.exe (PID: 5972)
- uv_x64.exe (PID: 5136)
- uv_x64.exe (PID: 1812)
Checks proxy server information
- UltraViewer_Desktop.exe (PID: 7908)
- slui.exe (PID: 5972)
- UltraViewer_Desktop.exe (PID: 3016)
- UltraViewer_Desktop.exe (PID: 5868)
Creates a software uninstall entry
- UltraViewer_setup_6.6.113_en.tmp (PID: 7520)
Disables trace logs
- UltraViewer_Service.exe (PID: 6828)
- UltraViewer_Desktop.exe (PID: 3016)
- UltraViewer_Desktop.exe (PID: 5868)
Creates files or folders in the user directory
- UltraViewer_Desktop.exe (PID: 3016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
643
Monitored processes
499
Malicious processes
11
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "taskkill.exe" /f /im "UltraViewer_Service.exe" | C:\Windows\SysWOW64\taskkill.exe | — | UltraViewer_setup_6.6.113_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5628 --field-trial-handle=2352,i,16311175707761640722,11631020651667413133,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | C:\WINDOWS\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\UltraViewer_Restart.bat | C:\Windows\SysWOW64\cmd.exe | — | UltraViewer_Desktop.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | RegAsm.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5744 --field-trial-handle=2352,i,16311175707761640722,11631020651667413133,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "taskkill.exe" /f /im "UltraViewer_Desktop.exe" | C:\Windows\SysWOW64\taskkill.exe | — | UltraViewer_setup_6.6.113_en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
51 842
Read events
50 273
Write events
1 567
Delete events
2
Modification events
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3B94A21307912F00 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CF2CAB1307912F00 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328396 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {98F24249-621D-4E49-B566-7E82EB242A5C} | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328396 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8CF12C67-F605-4593-A44F-7C5740D18143} | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328396 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {68B69F0C-B338-416A-8AF6-F5357F0E6C54} | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328396 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C06D92FC-173F-4E96-8B78-20B01A3139CB} | |||
Executable files
60
Suspicious files
578
Text files
276
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b131.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b131.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b131.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b141.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b150.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
93
DNS requests
96
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.21.245.180:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1072 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1744543544&P2=404&P3=2&P4=NP7d6X3ShMxnDGHzYhyRUiwRExBv2QtoegzDAaJg5GvsJHNelvr9IArlmSoNF8CKzZI2qwDTbM1uWwWdSTFR%2bQ%3d%3d | unknown | — | — | whitelisted |
1072 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1744694410&P2=404&P3=2&P4=Nyi2j5dUpWyjcP%2flv4X4jbk5TbXrzuSy%2fNZa71i6bs6F7wtJh9paFs0oTqXpmQct1ImPpBsUL4epxeGp9%2b0iOA%3d%3d | unknown | — | — | whitelisted |
1072 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1744543544&P2=404&P3=2&P4=NP7d6X3ShMxnDGHzYhyRUiwRExBv2QtoegzDAaJg5GvsJHNelvr9IArlmSoNF8CKzZI2qwDTbM1uWwWdSTFR%2bQ%3d%3d | unknown | — | — | whitelisted |
2568 | SIHClient.exe | GET | 200 | 23.222.86.92:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5048 | msedge.exe | GET | 200 | 18.173.205.113:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQg3SSkKA74hABkhmlBtJTz8w3hlAQU%2BWC71OPVNPa49QaAJadz20ZpqJ4CEEJLalPOx2YUHCpjsaUcQQQ%3D | unknown | — | — | whitelisted |
1072 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744547148&P2=404&P3=2&P4=A%2f%2faMUFfEiwX8VxQZpUYdGqhaPrbTW%2fveQAY3H6DnkcWtR7Qktmk7YVd9lXv8Q%2b4Hiv24oX0PauqkUoU0ynuNw%3d%3d | unknown | — | — | whitelisted |
5048 | msedge.exe | GET | 200 | 18.173.205.113:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSoEwb5tith0jIBy9frSyNGB1lsAAQUNr1J%2FzEs669qQP6ZwBbtuvxI3V8CEG3S4xc5lfUb%2BsHZ%2B0yyAME%3D | unknown | — | — | whitelisted |
1072 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744547148&P2=404&P3=2&P4=A%2f%2faMUFfEiwX8VxQZpUYdGqhaPrbTW%2fveQAY3H6DnkcWtR7Qktmk7YVd9lXv8Q%2b4Hiv24oX0PauqkUoU0ynuNw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5404 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5048 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7352 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7352 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7352 | msedge.exe | 13.107.253.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7352 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.ultraviewer.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |