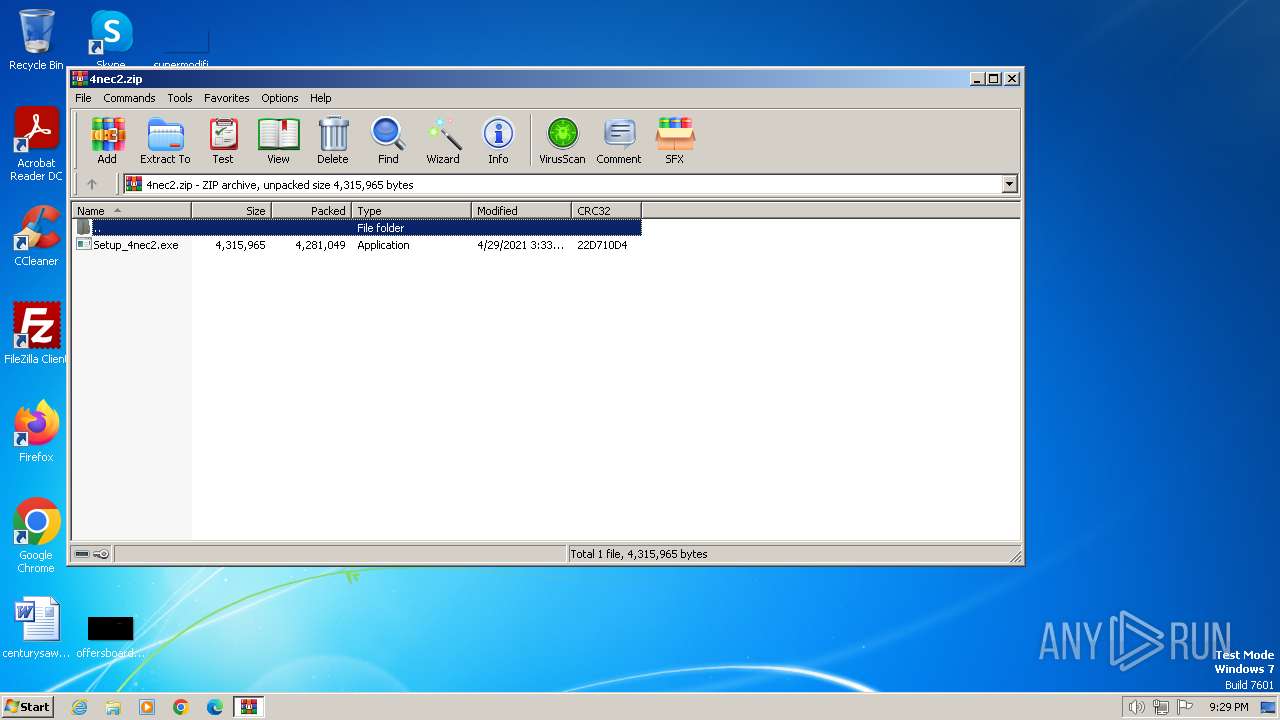
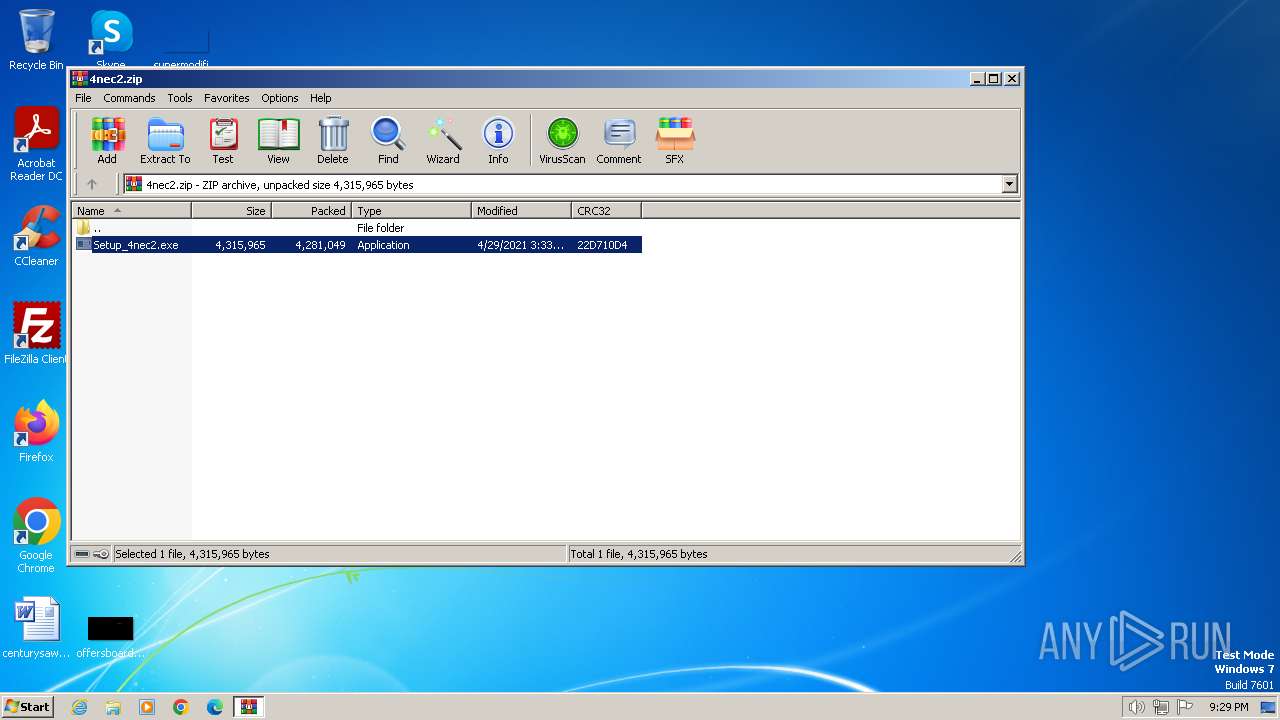
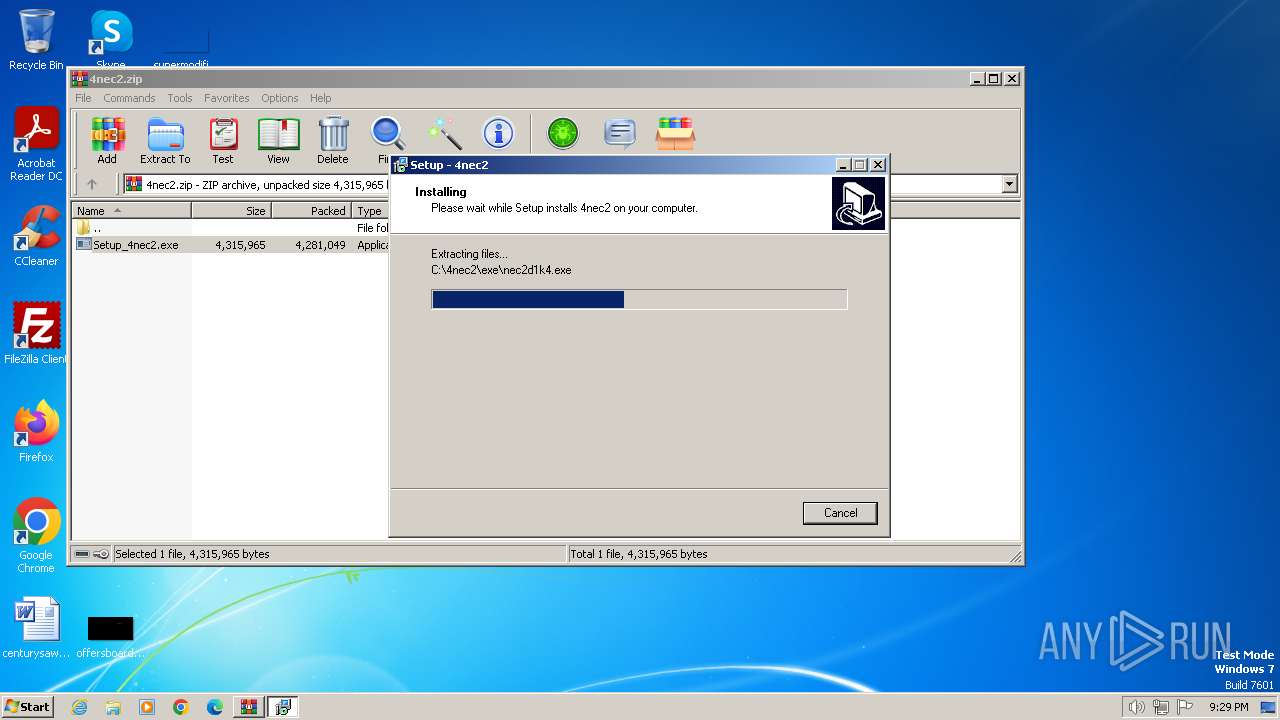
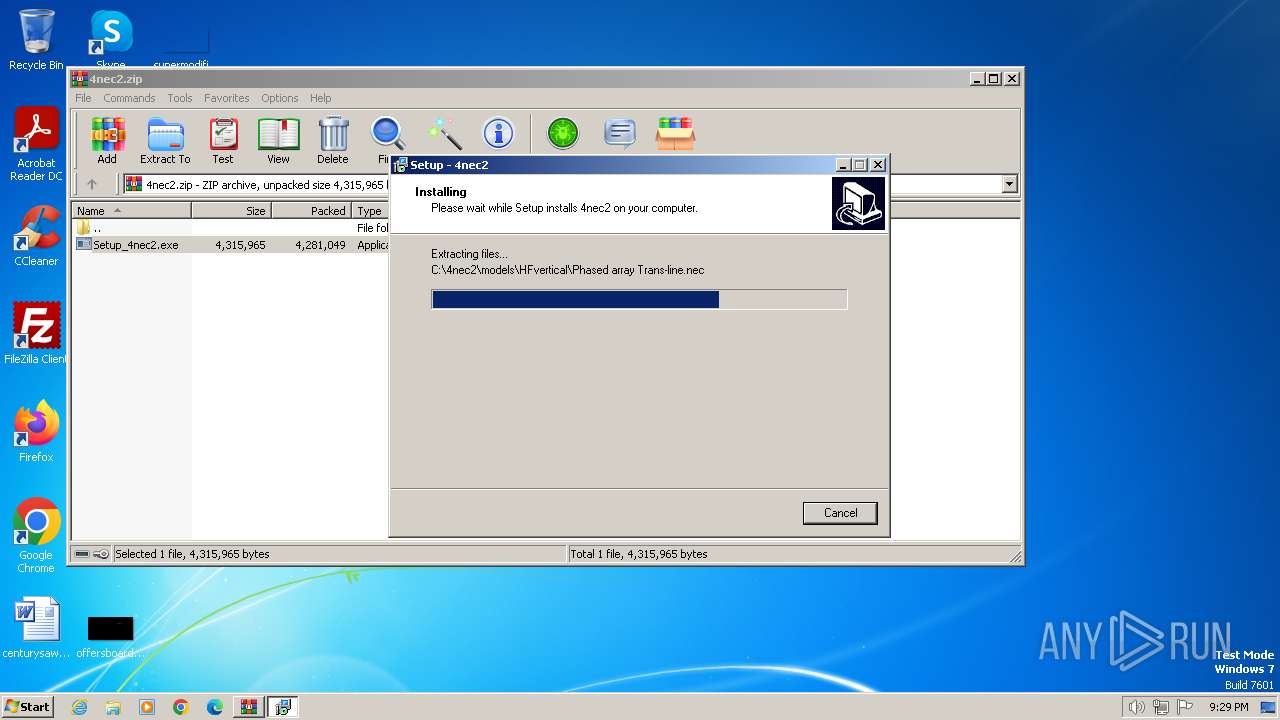
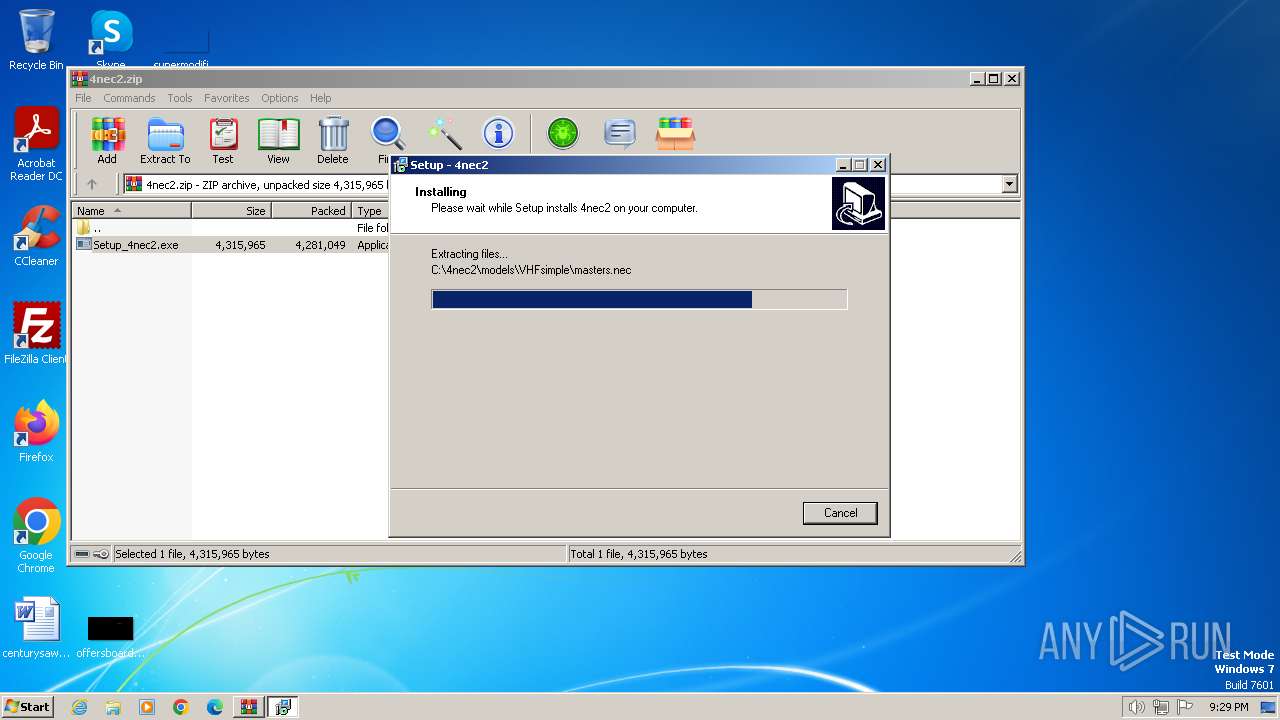
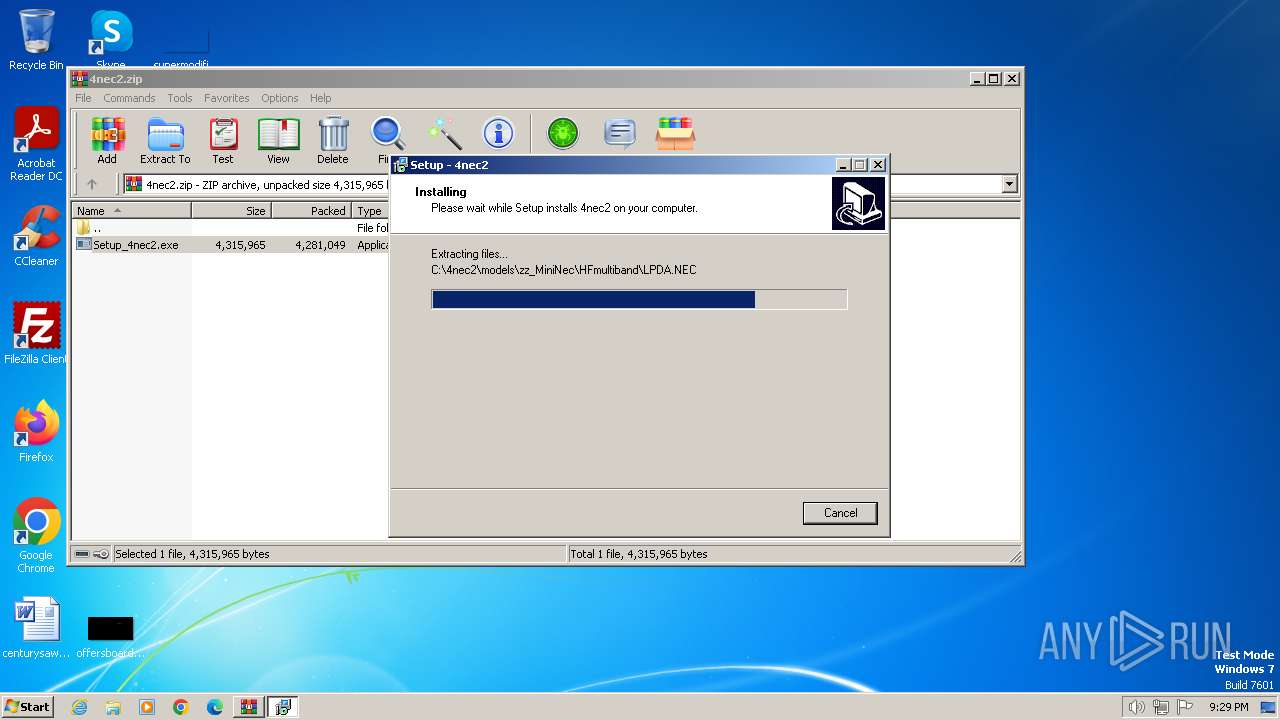
| File name: | 4nec2.zip |
| Full analysis: | https://app.any.run/tasks/64fe2569-28ec-446b-9a12-35ca4254a62e |
| Verdict: | Malicious activity |
| Analysis date: | January 21, 2024, 21:29:00 |
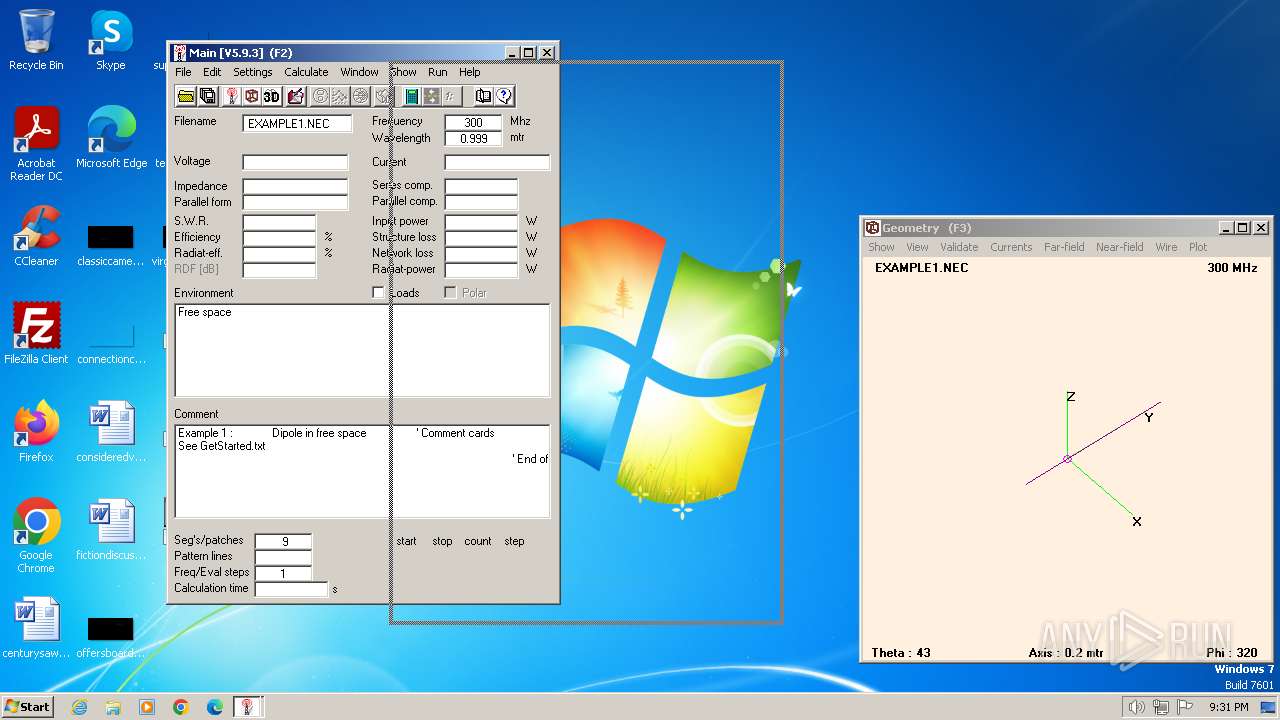
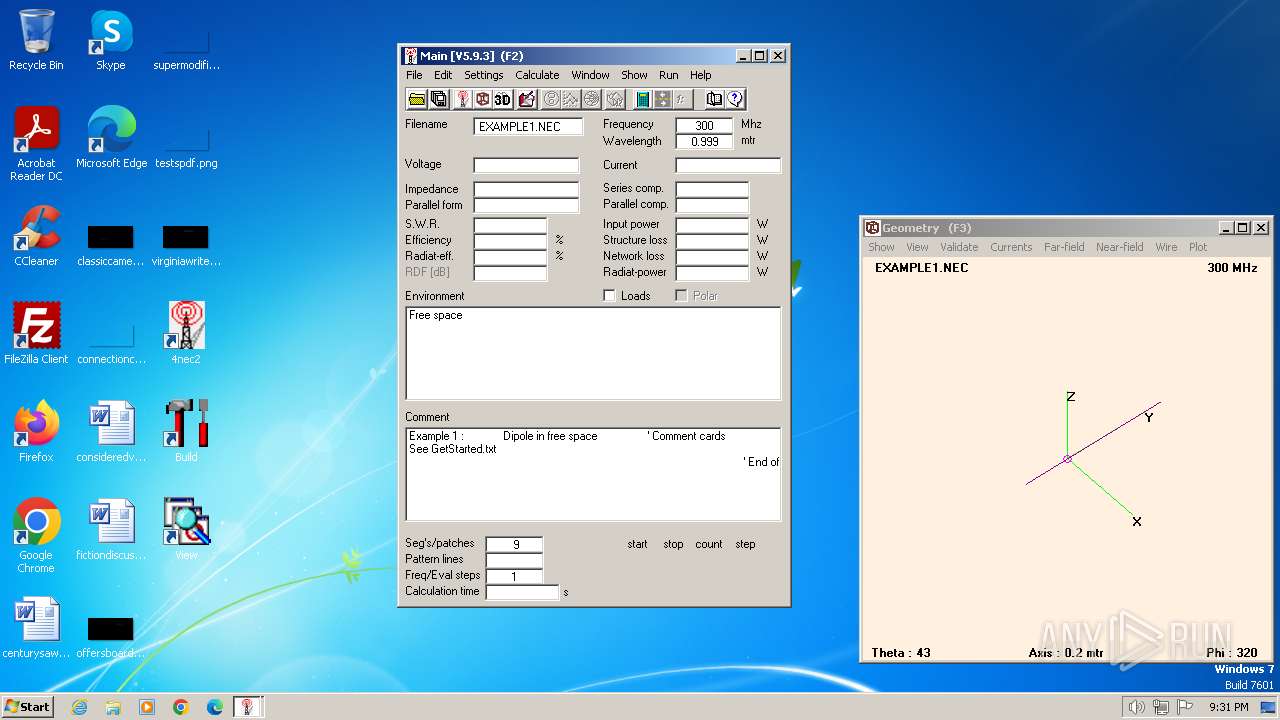
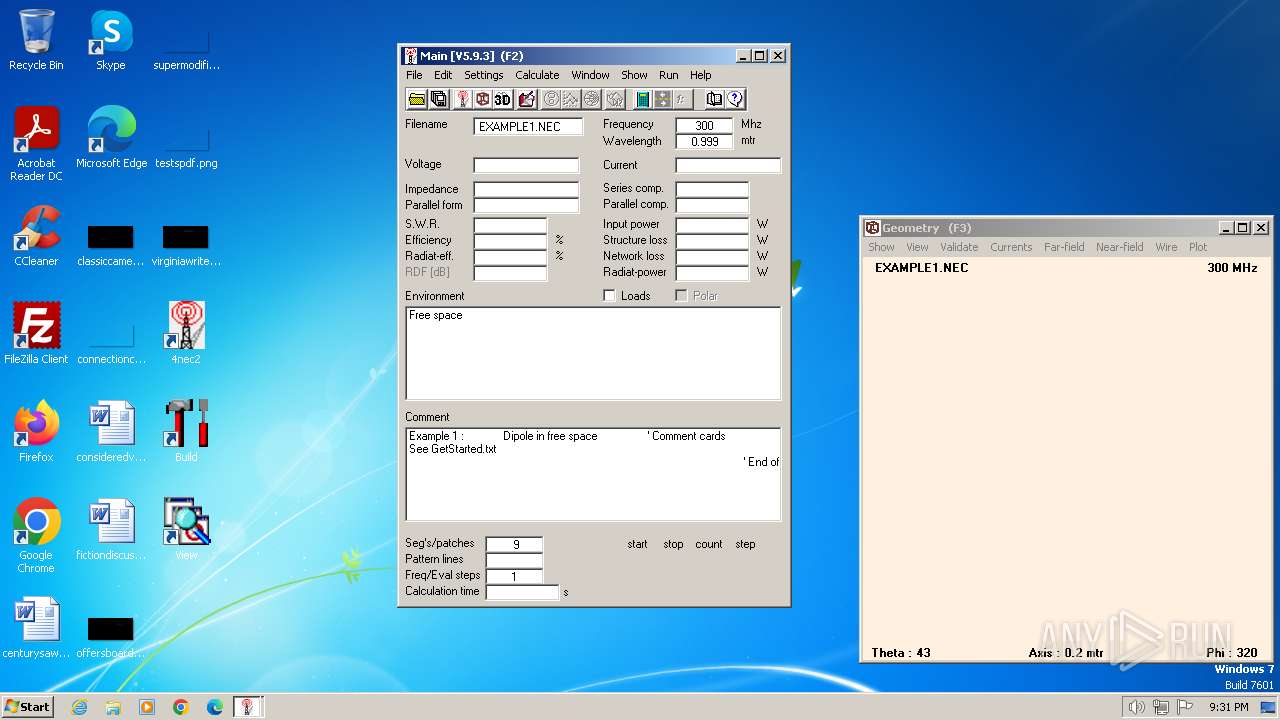
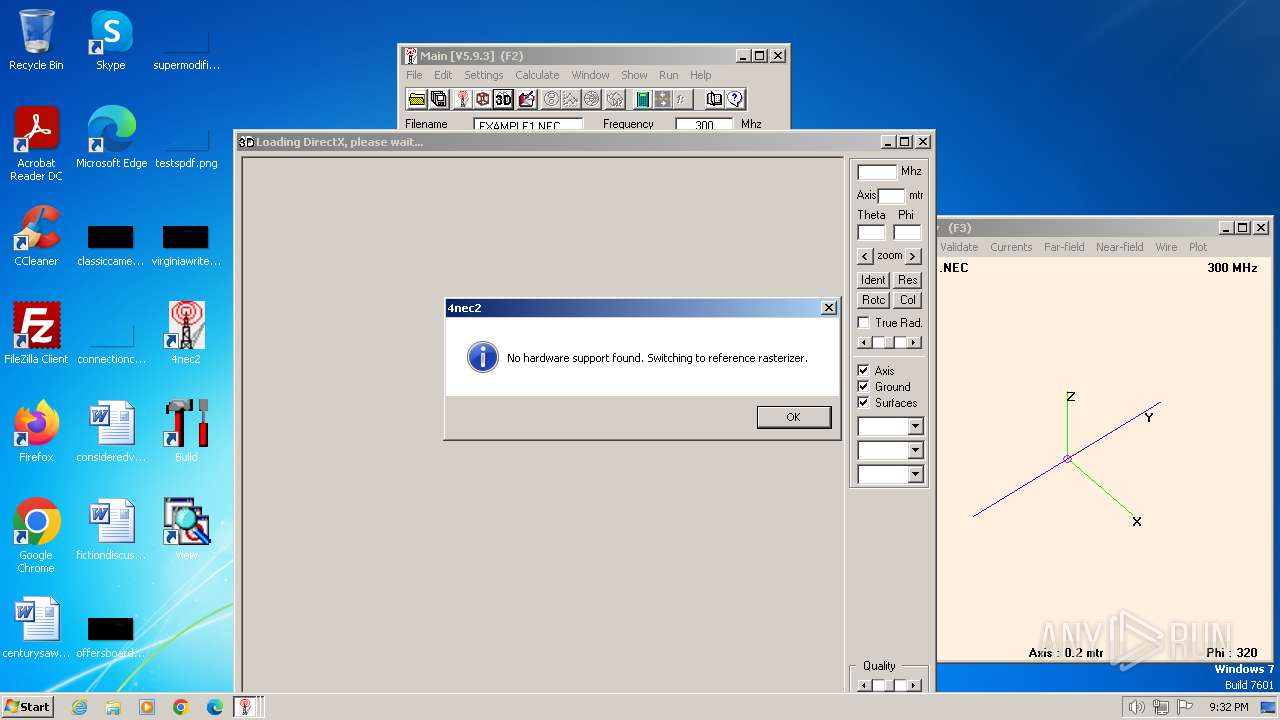
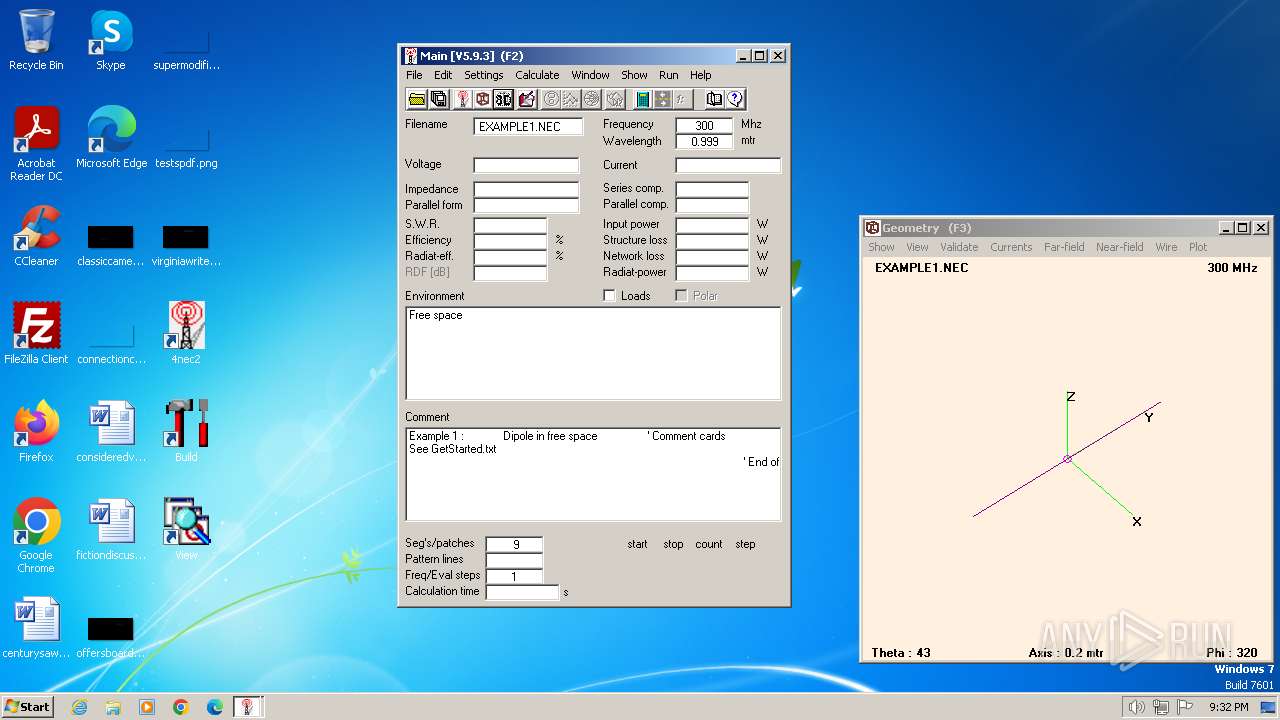
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8AB3E98BDB32A3F05EDC1D04129BFCE0 |
| SHA1: | EC702526323E91F6F50876D50DB9A0ECBB286751 |
| SHA256: | 8A4A1A0397DE8781DCE81D768F5A7DE4BB37D9DD9452B33FD4C4DDCE0A69F5A2 |
| SSDEEP: | 98304:n+YDrVNVm7uiXbJEN8w1rXoZ/43N6frYZkxRITYSE2dMd+G6ESkoufhzmLgJKb+i:N2bQ0rZg |
MALICIOUS
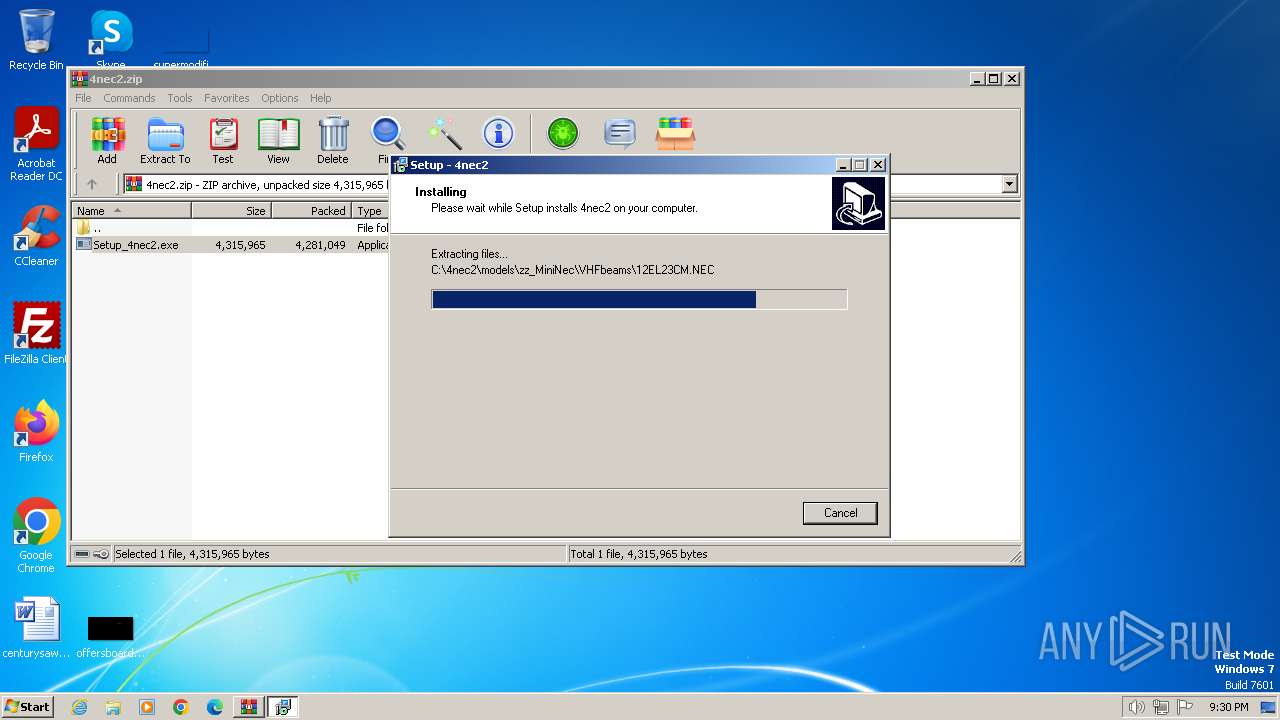
Drops the executable file immediately after the start
- WinRAR.exe (PID: 128)
- Setup_4nec2.exe (PID: 784)
- Setup_4nec2.tmp (PID: 1044)
- Setup_4nec2.exe (PID: 1288)
Creates a writable file in the system directory
- Setup_4nec2.tmp (PID: 1044)
Registers / Runs the DLL via REGSVR32.EXE
- Setup_4nec2.tmp (PID: 1044)
SUSPICIOUS
Executable content was dropped or overwritten
- Setup_4nec2.exe (PID: 1288)
- Setup_4nec2.exe (PID: 784)
- Setup_4nec2.tmp (PID: 1044)
Reads the Windows owner or organization settings
- Setup_4nec2.tmp (PID: 1044)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1816)
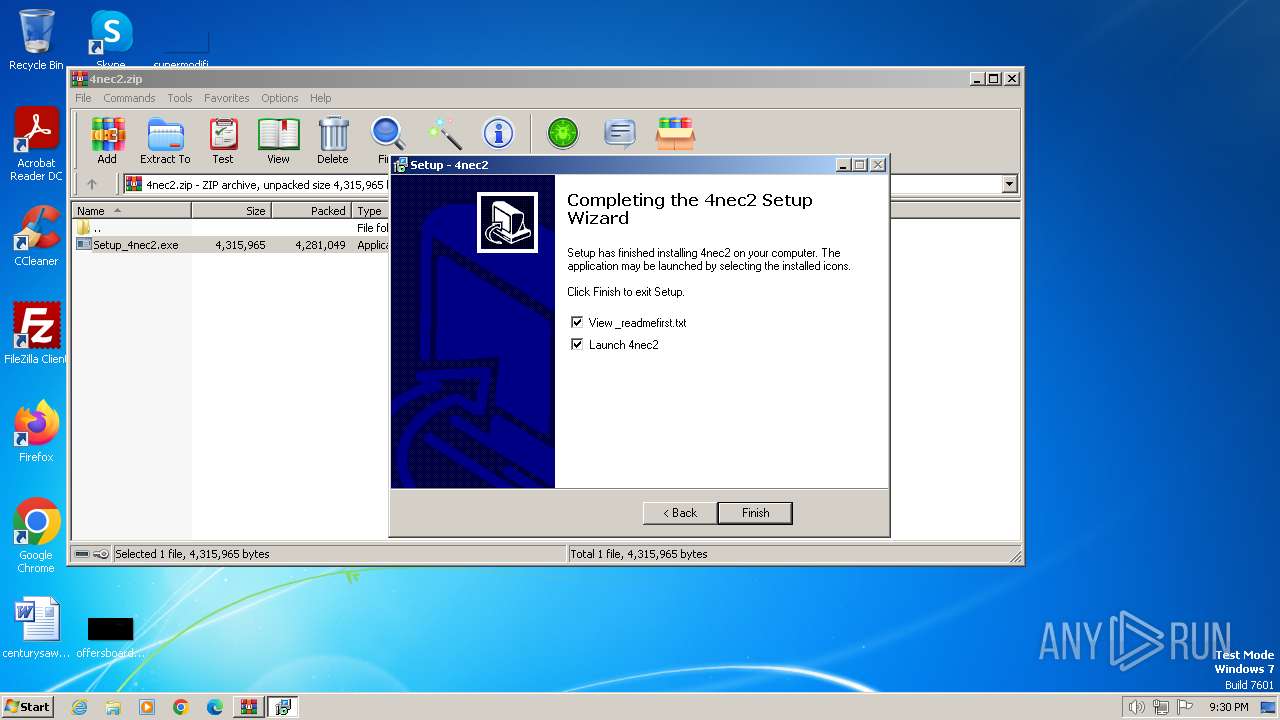
Process drops legitimate windows executable
- Setup_4nec2.tmp (PID: 1044)
Checks Windows Trust Settings
- 4nec2.exe (PID: 2448)
Reads settings of System Certificates
- 4nec2.exe (PID: 2448)
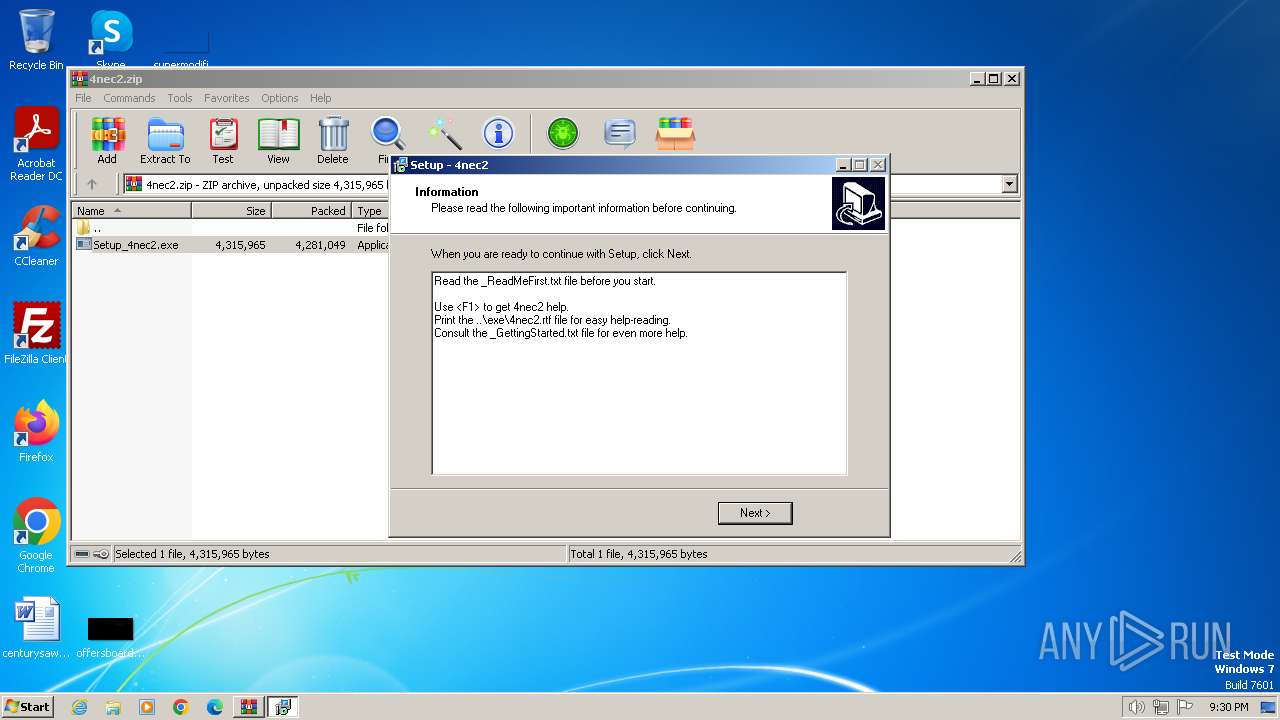
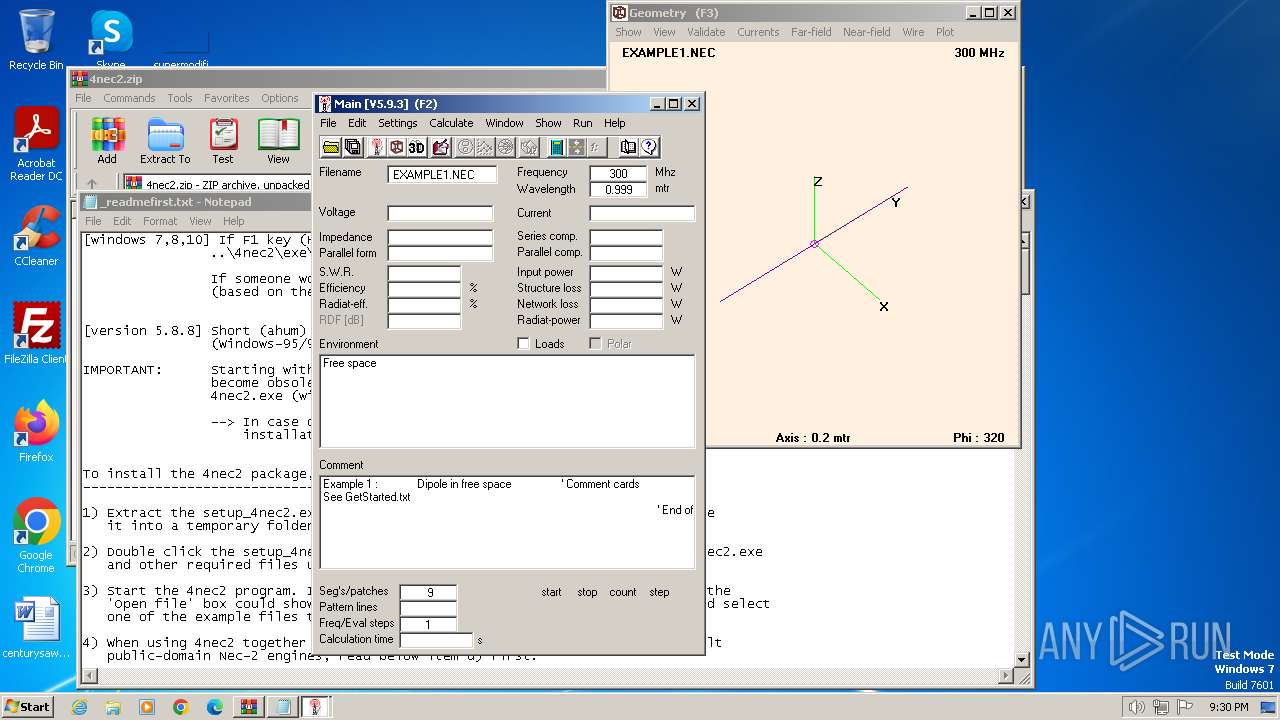
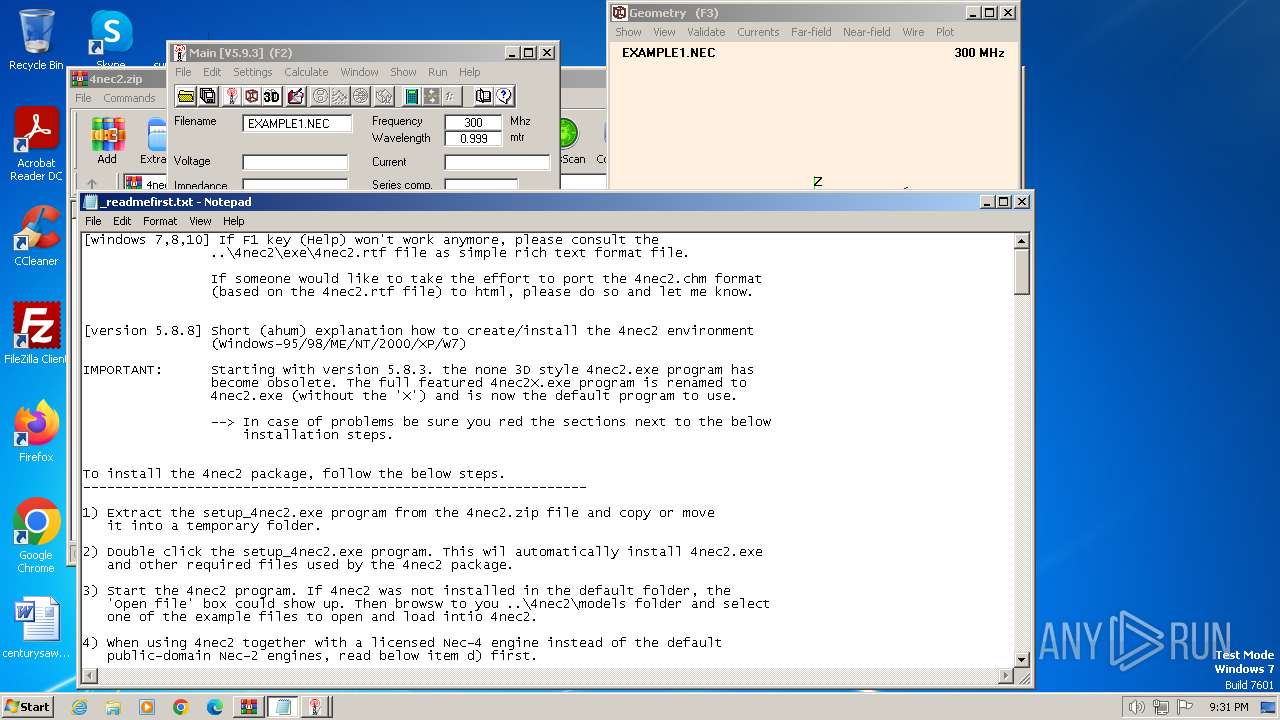
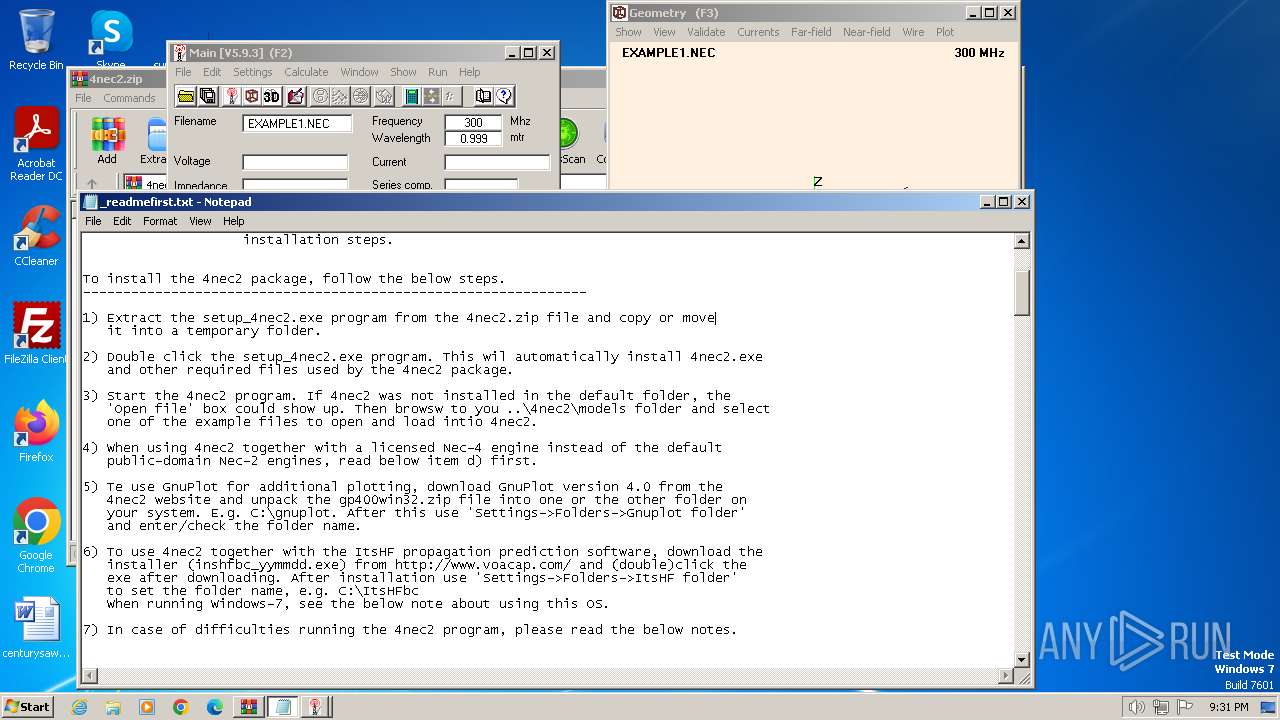
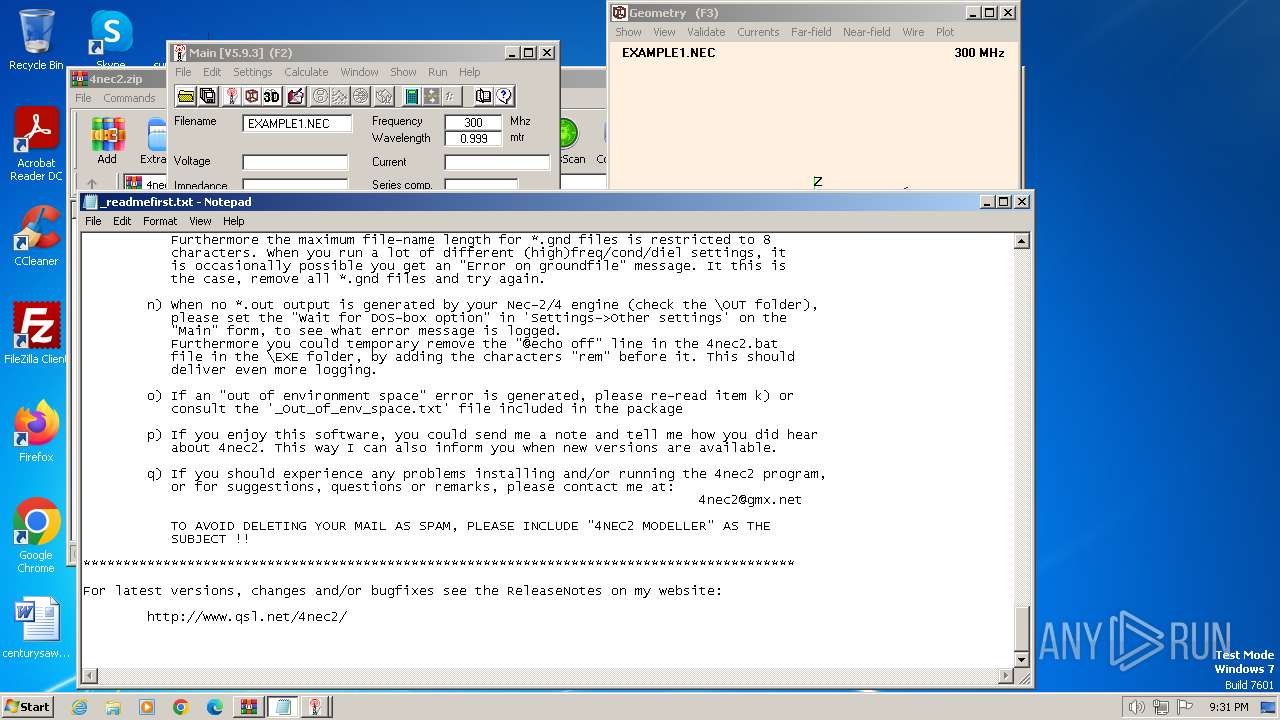
Start notepad (likely ransomware note)
- Setup_4nec2.tmp (PID: 1056)
Reads security settings of Internet Explorer
- 4nec2.exe (PID: 2448)
INFO
Checks supported languages
- Setup_4nec2.exe (PID: 1288)
- Setup_4nec2.exe (PID: 784)
- Setup_4nec2.tmp (PID: 1056)
- 4nec2.exe (PID: 2448)
- Setup_4nec2.tmp (PID: 1044)
Reads the computer name
- Setup_4nec2.tmp (PID: 1056)
- Setup_4nec2.tmp (PID: 1044)
- 4nec2.exe (PID: 2448)
Create files in a temporary directory
- Setup_4nec2.tmp (PID: 1044)
- Setup_4nec2.exe (PID: 1288)
- Setup_4nec2.exe (PID: 784)
- 4nec2.exe (PID: 2448)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 128)
Creates files in the program directory
- Setup_4nec2.tmp (PID: 1044)
Reads the machine GUID from the registry
- 4nec2.exe (PID: 2448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2021:04:29 15:33:46 |
| ZipCRC: | 0x22d710d4 |
| ZipCompressedSize: | 4281049 |
| ZipUncompressedSize: | 4315965 |
| ZipFileName: | Setup_4nec2.exe |
Total processes
53
Monitored processes
12
Malicious processes
6
Suspicious processes
0
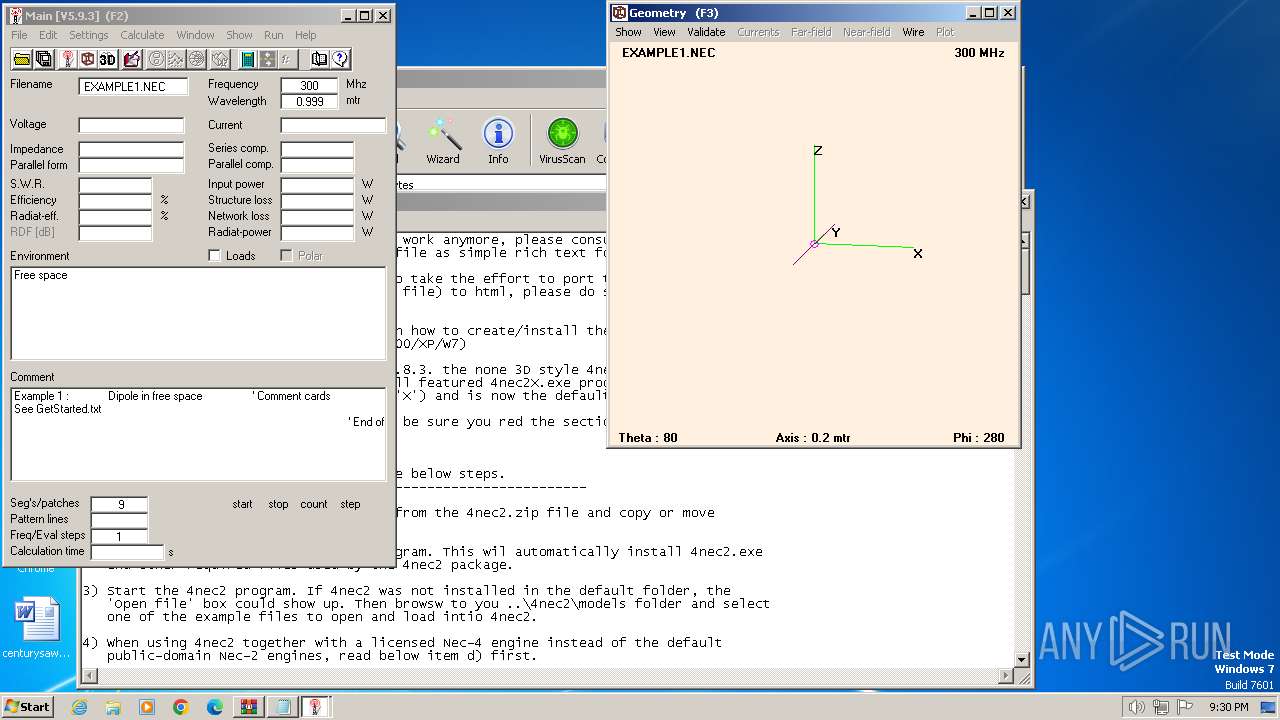
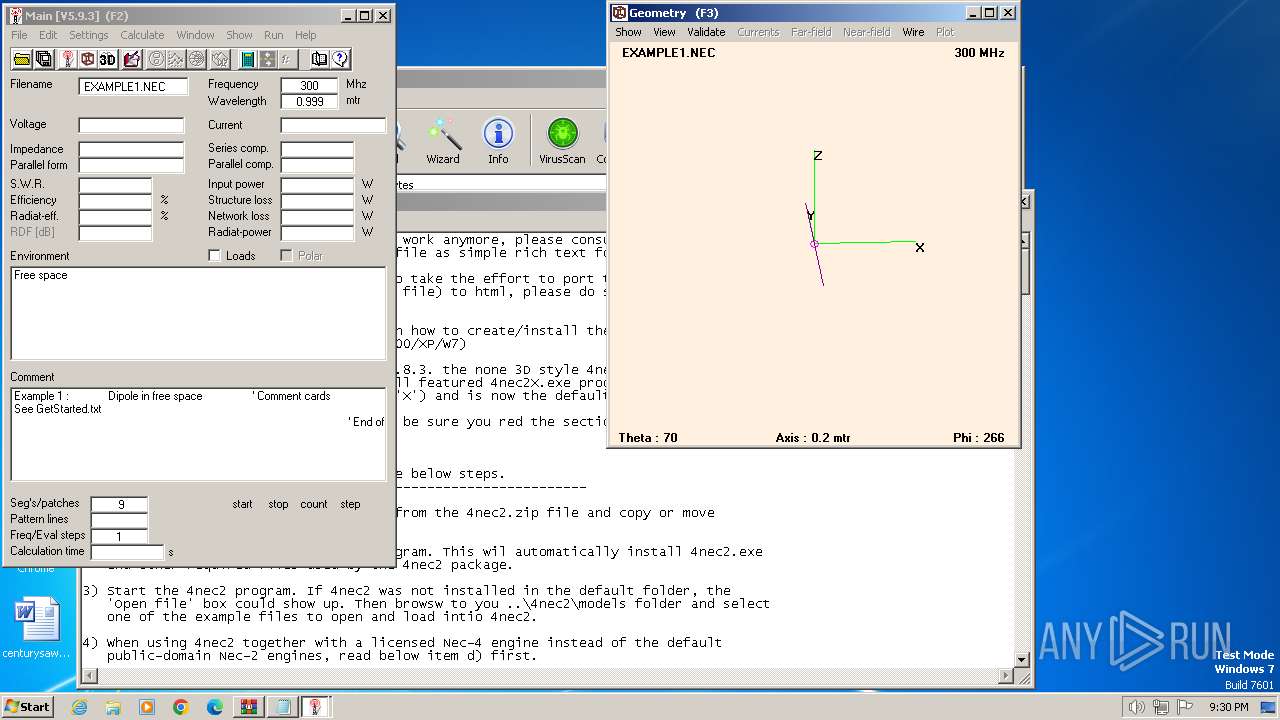
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
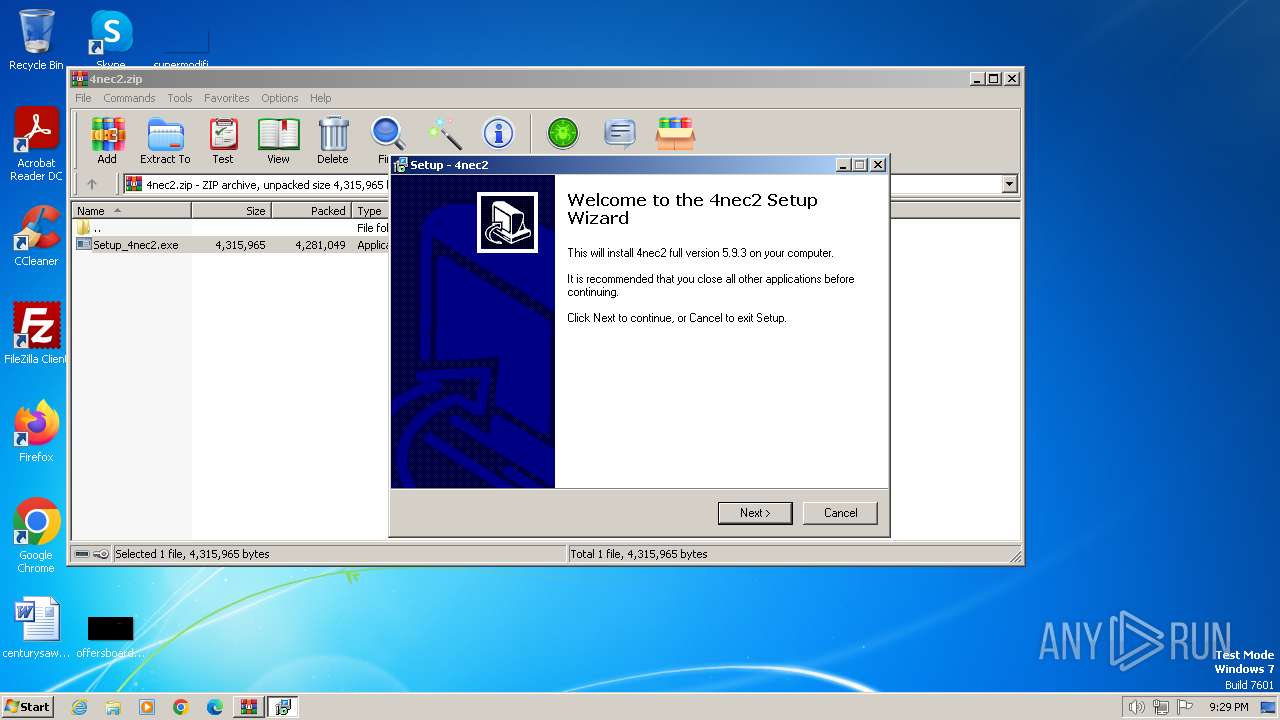
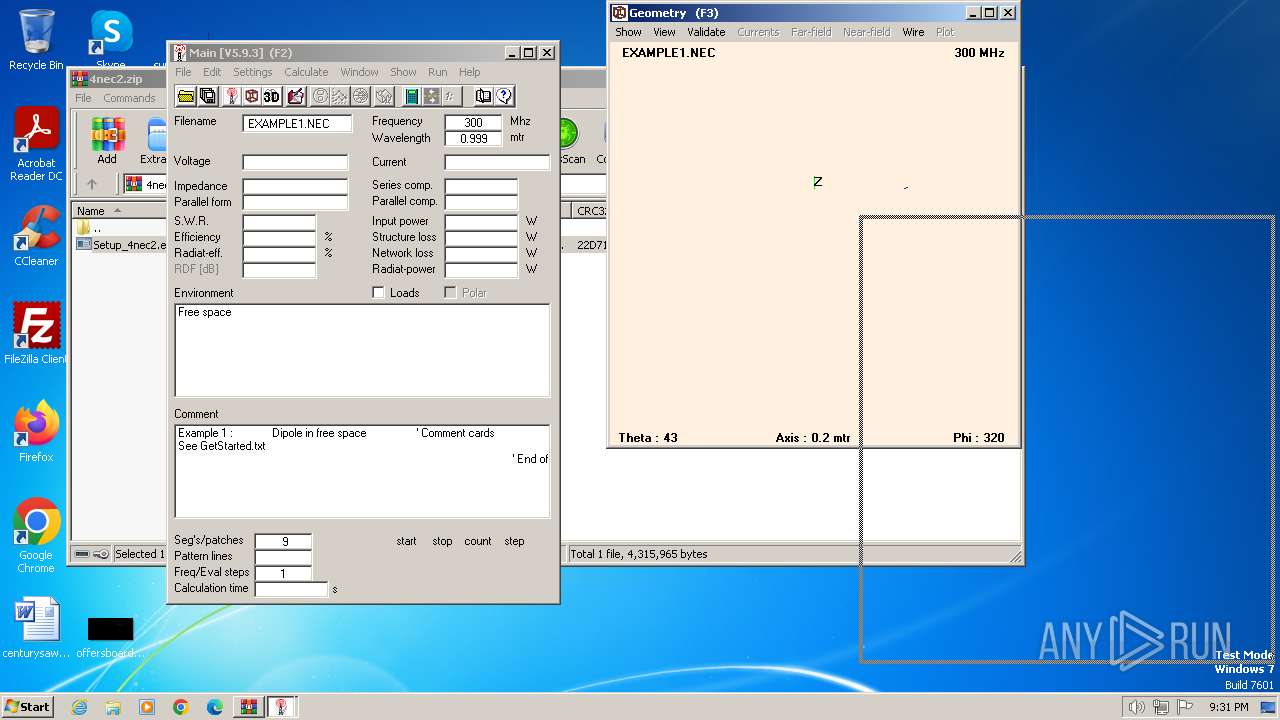
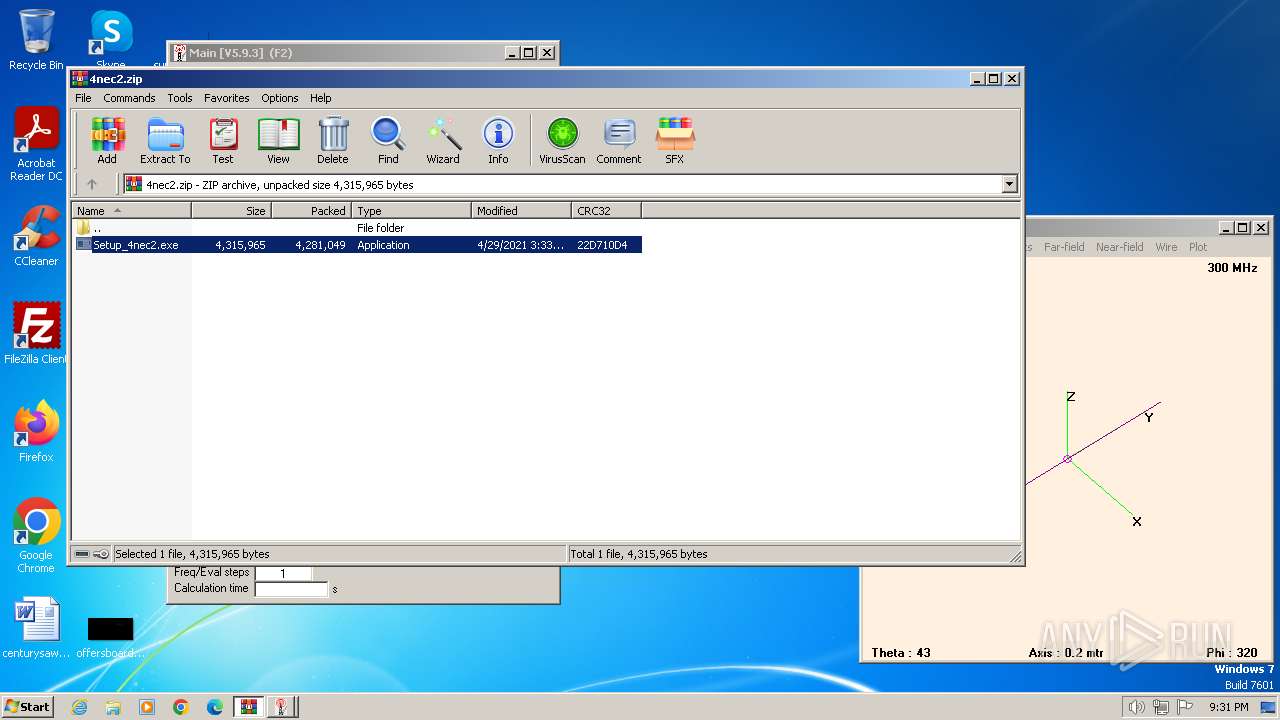
| 128 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\4nec2.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 784 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa128.3533\Setup_4nec2.exe" /SPAWNWND=$3016E /NOTIFYWND=$5018E | C:\Users\admin\AppData\Local\Temp\Rar$EXa128.3533\Setup_4nec2.exe | Setup_4nec2.tmp | ||||||||||||
User: admin Company: 4nec2@gmx.net (Use "4nec2 modeller" as the subject) Integrity Level: HIGH Description: 4nec2 Setup Exit code: 0 Version: Modules
| |||||||||||||||
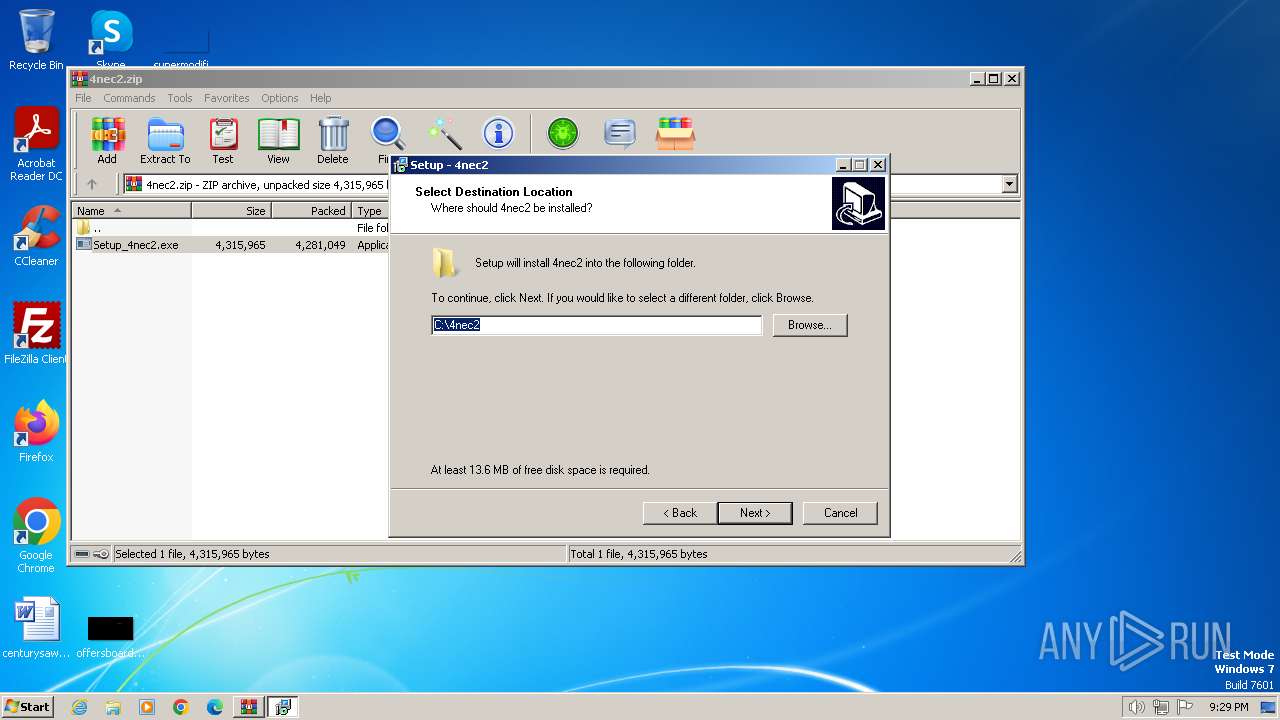
| 1044 | "C:\Users\admin\AppData\Local\Temp\is-P2U5V.tmp\Setup_4nec2.tmp" /SL5="$40170,4052503,54272,C:\Users\admin\AppData\Local\Temp\Rar$EXa128.3533\Setup_4nec2.exe" /SPAWNWND=$3016E /NOTIFYWND=$5018E | C:\Users\admin\AppData\Local\Temp\is-P2U5V.tmp\Setup_4nec2.tmp | Setup_4nec2.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.50.0.0 Modules
| |||||||||||||||
| 1056 | "C:\Users\admin\AppData\Local\Temp\is-9IKHU.tmp\Setup_4nec2.tmp" /SL5="$5018E,4052503,54272,C:\Users\admin\AppData\Local\Temp\Rar$EXa128.3533\Setup_4nec2.exe" | C:\Users\admin\AppData\Local\Temp\is-9IKHU.tmp\Setup_4nec2.tmp | — | Setup_4nec2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.50.0.0 Modules
| |||||||||||||||
| 1288 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa128.3533\Setup_4nec2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa128.3533\Setup_4nec2.exe | WinRAR.exe | ||||||||||||
User: admin Company: 4nec2@gmx.net (Use "4nec2 modeller" as the subject) Integrity Level: MEDIUM Description: 4nec2 Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1784 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\dx8vb.dll" | C:\Windows\System32\regsvr32.exe | — | Setup_4nec2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1808 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\Tabctl32.ocx" | C:\Windows\System32\regsvr32.exe | — | Setup_4nec2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1816 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\Msvbvm60.dll" | C:\Windows\System32\regsvr32.exe | — | Setup_4nec2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1832 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\Msflxgrd.ocx" | C:\Windows\System32\regsvr32.exe | — | Setup_4nec2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
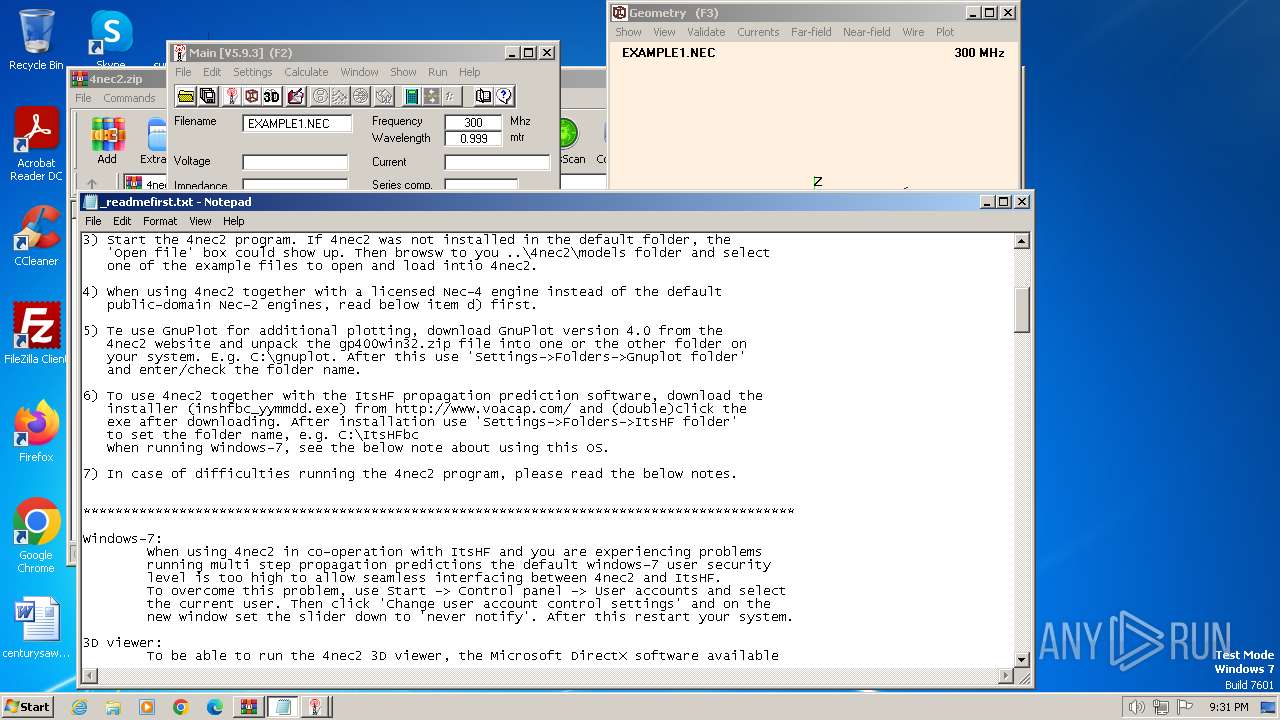
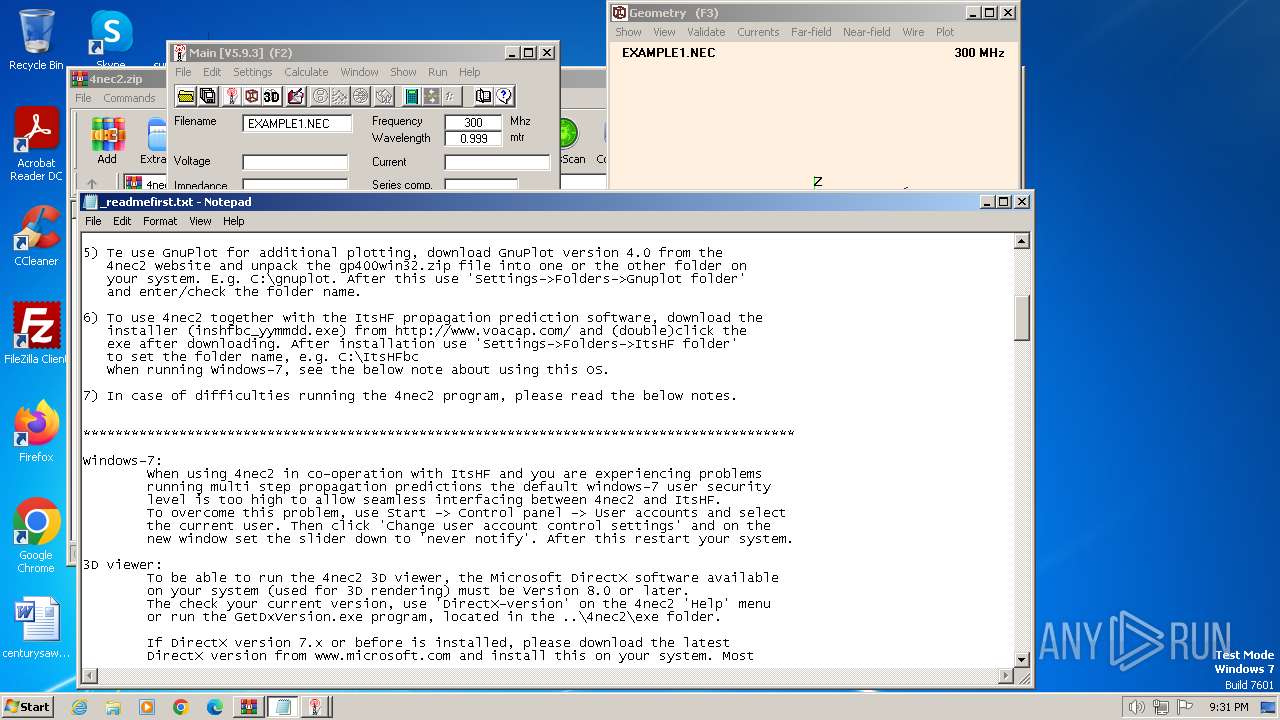
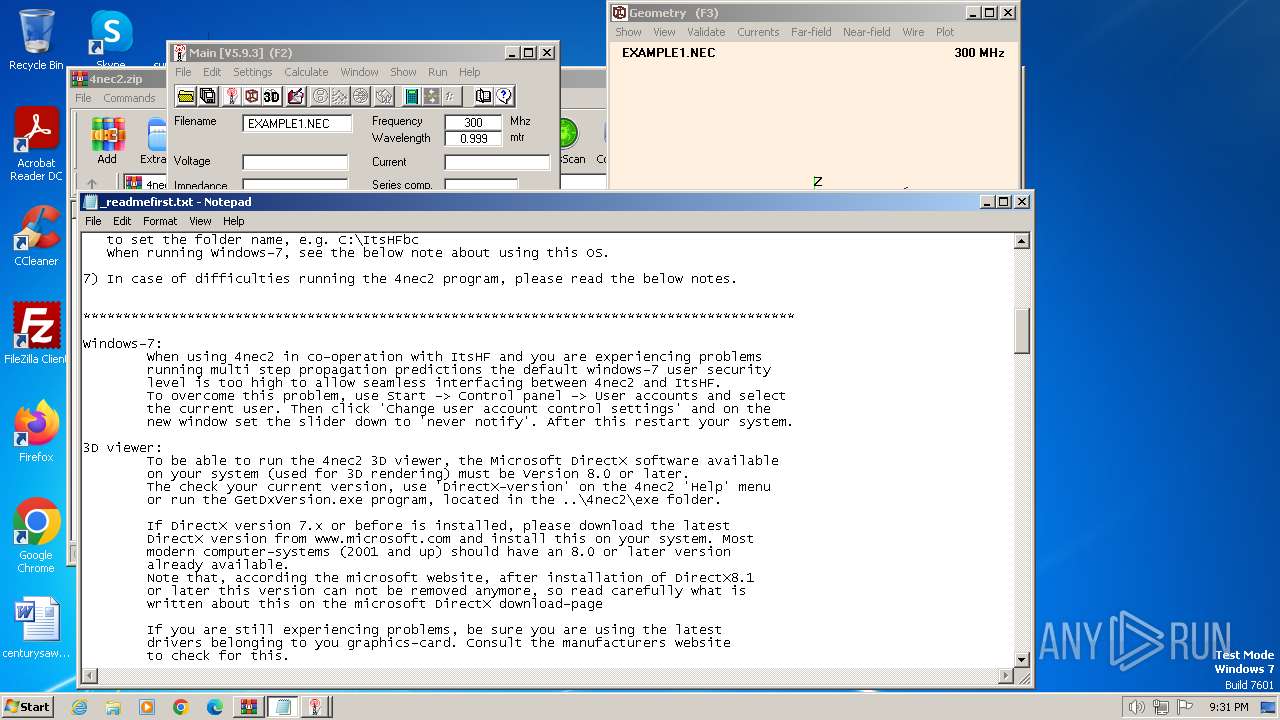
| 2340 | "C:\Windows\system32\NOTEPAD.EXE" C:\4nec2\_readmefirst.txt | C:\Windows\System32\notepad.exe | — | Setup_4nec2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 065
Read events
7 930
Write events
129
Delete events
6
Modification events
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
47
Suspicious files
29
Text files
1 158
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1044 | Setup_4nec2.tmp | C:\4nec2\_readmefirst.txt | ini | |
MD5:33340B778BB8BBCA0BFE68CFE9231914 | SHA256:58757D65BF4E8E5D0D07DBB38C527BEE03F2A667DE88F9C7EBE7ED5E6D2278F7 | |||
| 1044 | Setup_4nec2.tmp | C:\Users\admin\AppData\Local\Temp\is-6HE9B.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 1044 | Setup_4nec2.tmp | C:\4nec2\is-NCHHR.tmp | text | |
MD5:208A3AF8352E14DB32306E4A95FB1406 | SHA256:6A756FCFE40677048091098A302C880C24979AAA1A6416233FCC2F69148C00D7 | |||
| 1044 | Setup_4nec2.tmp | C:\4nec2\is-00E65.tmp | ini | |
MD5:33340B778BB8BBCA0BFE68CFE9231914 | SHA256:58757D65BF4E8E5D0D07DBB38C527BEE03F2A667DE88F9C7EBE7ED5E6D2278F7 | |||
| 1044 | Setup_4nec2.tmp | C:\4nec2\is-QGH1S.tmp | executable | |
MD5:FBA1DE70F5BB8544A9753957F269F897 | SHA256:87931B032A78E11A4DD491E21A66A9F24DF3FFBBEF61B5672BFE286E3903953B | |||
| 1044 | Setup_4nec2.tmp | C:\4nec2\unins000.exe | executable | |
MD5:FBA1DE70F5BB8544A9753957F269F897 | SHA256:87931B032A78E11A4DD491E21A66A9F24DF3FFBBEF61B5672BFE286E3903953B | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa128.3533\Setup_4nec2.exe | executable | |
MD5:D9C1CB4AB1777143F9C81C993C9CD64B | SHA256:7DE2860311D0FF1F764F38CC20ED27CBB9F68F7BF2145AFD97736268FA9E5BAD | |||
| 1044 | Setup_4nec2.tmp | C:\4nec2\_Info.txt | text | |
MD5:7B261CD7A69AE1202BC8AAAA91ADDCD9 | SHA256:2E89E62367C5F240EACA316002067C1232FF70A3AFE8B7AAFCC20AAD3166D289 | |||
| 1044 | Setup_4nec2.tmp | C:\4nec2\is-AJ8BN.tmp | text | |
MD5:B844164FAD30916854B95FC433772D19 | SHA256:37C311824E81821CB2C5D68C6692C37BA64F5AEFF6793DD3C9E1ACD902DFF7A3 | |||
| 1044 | Setup_4nec2.tmp | C:\4nec2\is-7VKHM.tmp | text | |
MD5:5708F56F2AEE9D5AF652EF754C1A695B | SHA256:E8AA45B87EF665E097048232B5697324D6CAB206B70B7BE14A2D313060EFE4C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |