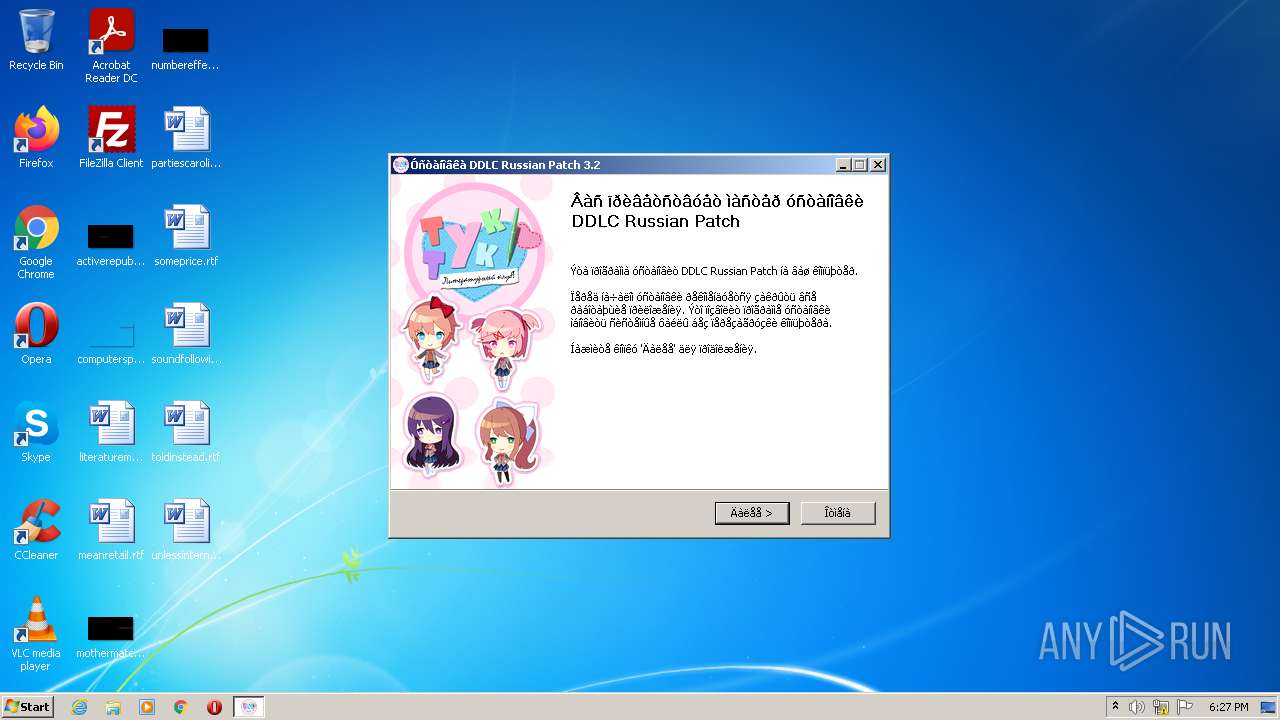
| File name: | DDLC_russian_patch_3.2.exe |
| Full analysis: | https://app.any.run/tasks/d4b50ed1-e0ad-4069-91f6-befdede43bfb |
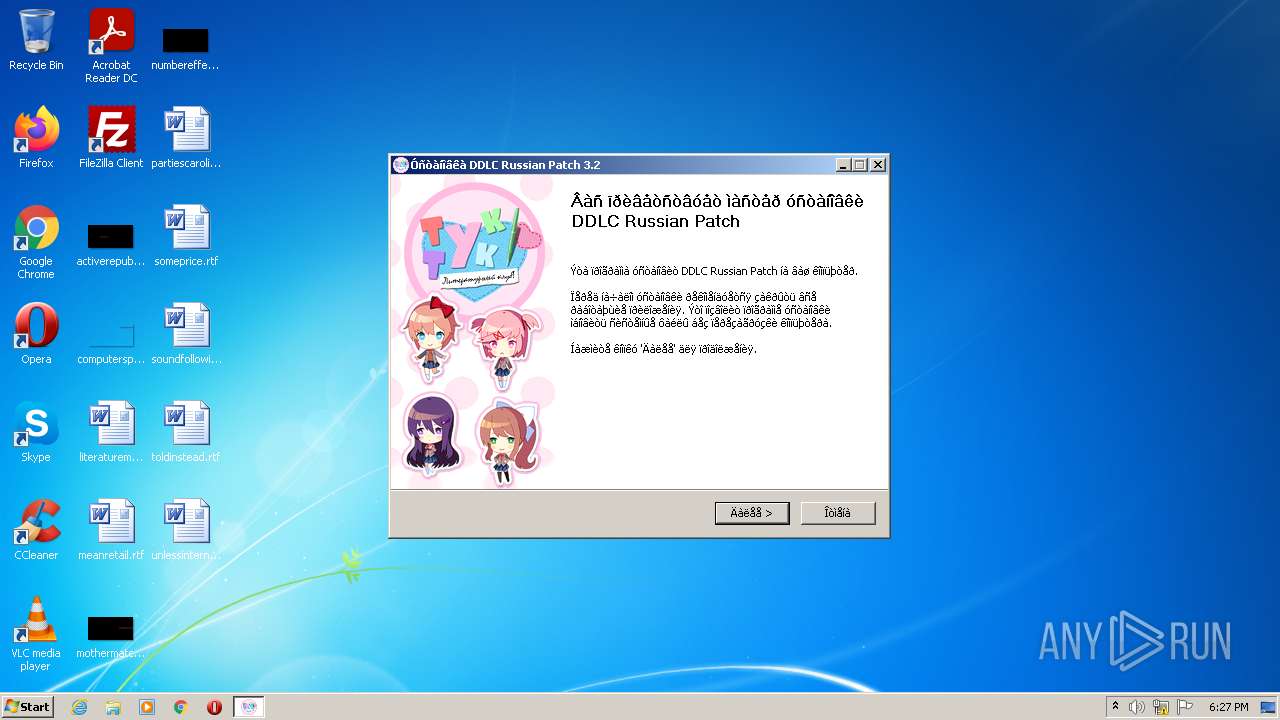
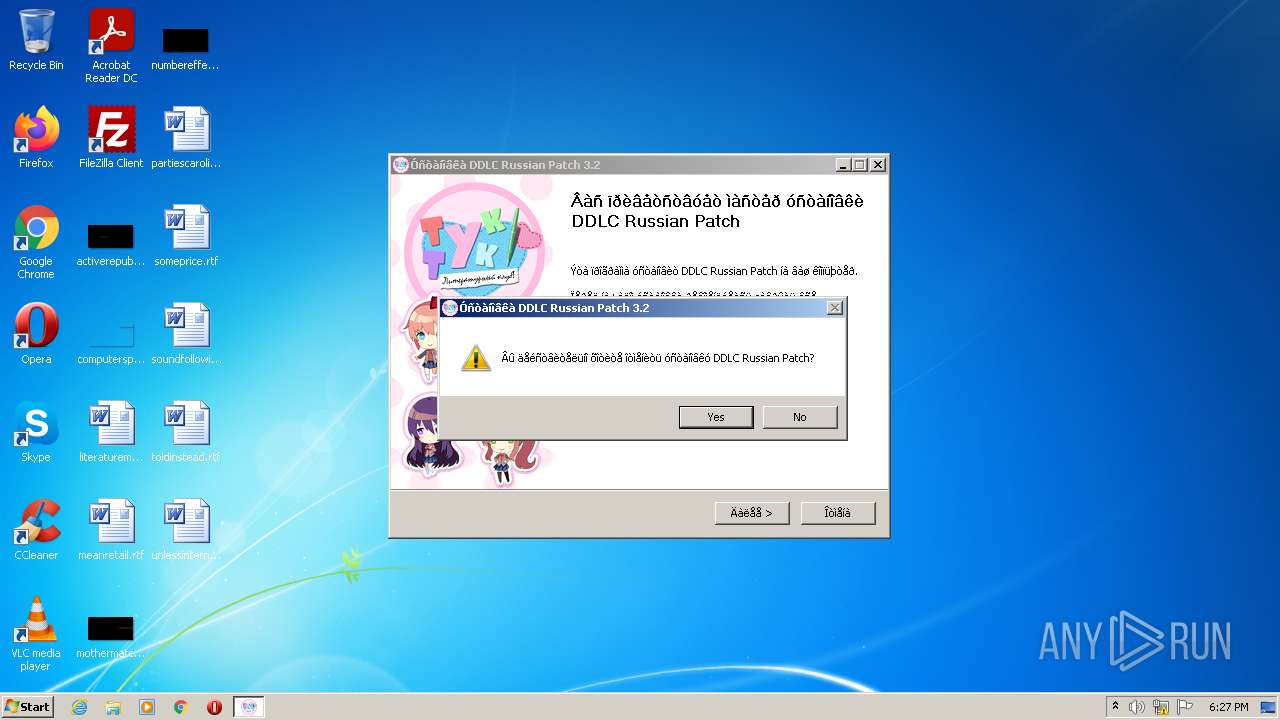
| Verdict: | Malicious activity |
| Analysis date: | August 28, 2022, 17:26:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | BC7900B11EE151EBE0933A8207E681BD |
| SHA1: | EDBD986032C3BB78B780AA8148CB2EDF41B013C5 |
| SHA256: | 8A30778288D5C28CFCFDC8811153B9EF192DA7E65F6614432D37E1898CD8B7A3 |
| SSDEEP: | 393216:cSkBm0j0rABzrVuIn/9lexAZjUY6kQZKptwk8tg/:cJBYIn/9lATY6lZfO |
MALICIOUS
Loads dropped or rewritten executable
- DDLC_russian_patch_3.2.exe (PID: 4020)
Drops executable file immediately after starts
- DDLC_russian_patch_3.2.exe (PID: 4020)
SUSPICIOUS
Reads the computer name
- DDLC_russian_patch_3.2.exe (PID: 4020)
Checks supported languages
- DDLC_russian_patch_3.2.exe (PID: 4020)
Executable content was dropped or overwritten
- DDLC_russian_patch_3.2.exe (PID: 4020)
Drops a file with a compile date too recent
- DDLC_russian_patch_3.2.exe (PID: 4020)
INFO
Checks supported languages
- explorer.exe (PID: 2984)
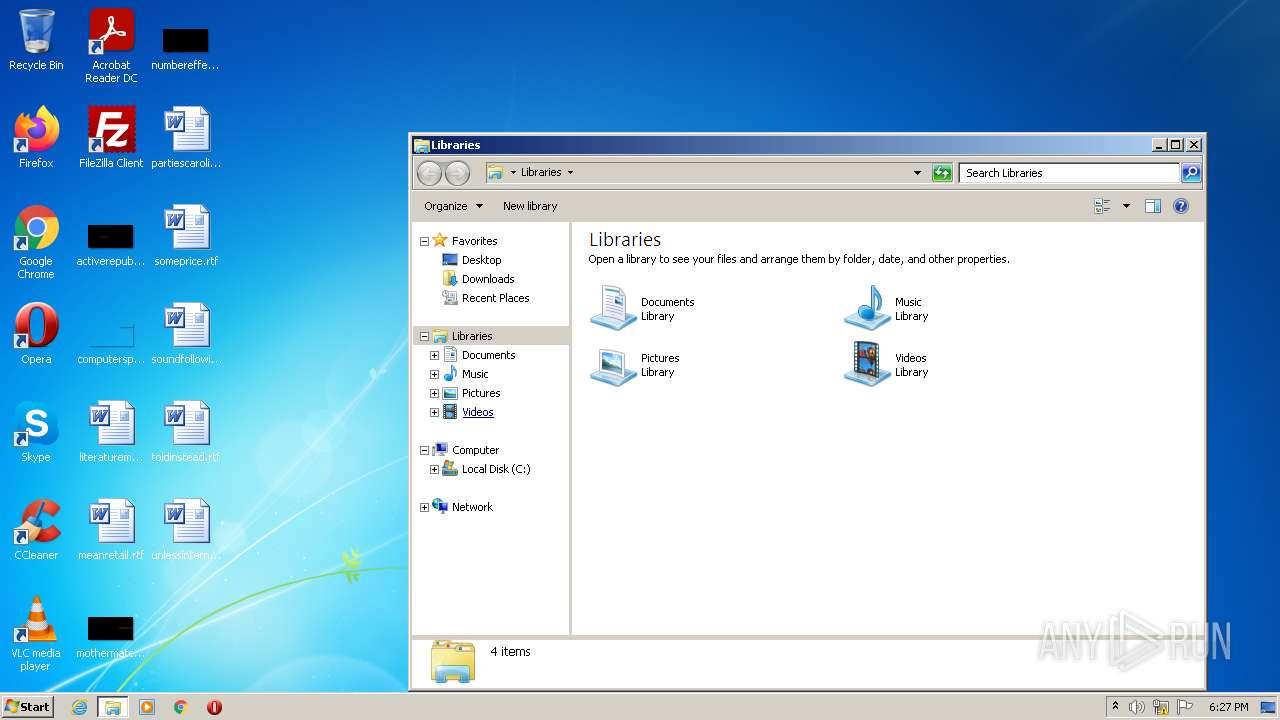
Manual execution by user
- explorer.exe (PID: 2984)
Reads the computer name
- explorer.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2017-Aug-01 00:33:55 |
| Detected languages: |
|
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 216 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 5 |
| TimeDateStamp: | 2017-Aug-01 00:33:55 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 24636 | 25088 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39362 |
.rdata | 32768 | 4680 | 5120 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04426 |
.data | 40960 | 108600 | 1024 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22313 |
.ndata | 151552 | 36864 | 0 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.rsrc | 188416 | 12680 | 12800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.08221 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.68843 | 9640 | UNKNOWN | English - United States | RT_ICON |
103 | 2.56193 | 288 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
103 (#2) | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
1 (#2) | 5.2901 | 1072 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2984 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3380 | "C:\Users\admin\AppData\Local\Temp\DDLC_russian_patch_3.2.exe" | C:\Users\admin\AppData\Local\Temp\DDLC_russian_patch_3.2.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4020 | "C:\Users\admin\AppData\Local\Temp\DDLC_russian_patch_3.2.exe" | C:\Users\admin\AppData\Local\Temp\DDLC_russian_patch_3.2.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
Total events
1 081
Read events
1 072
Write events
9
Delete events
0
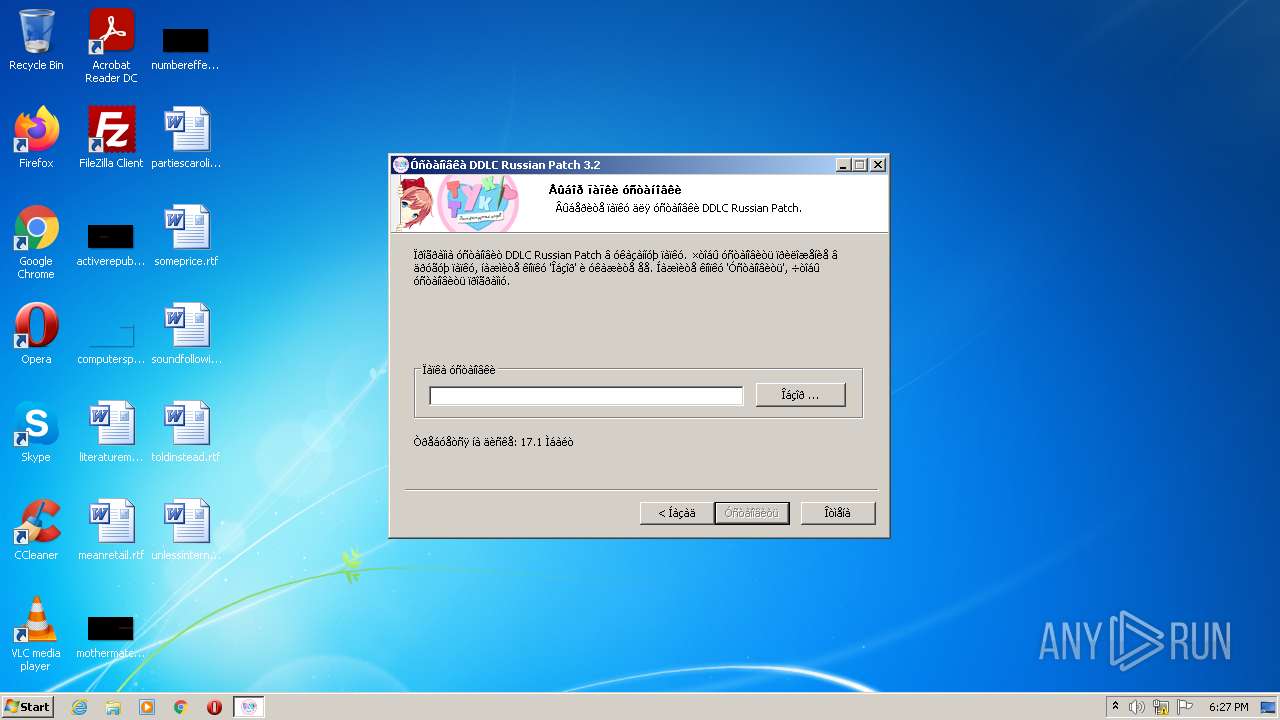
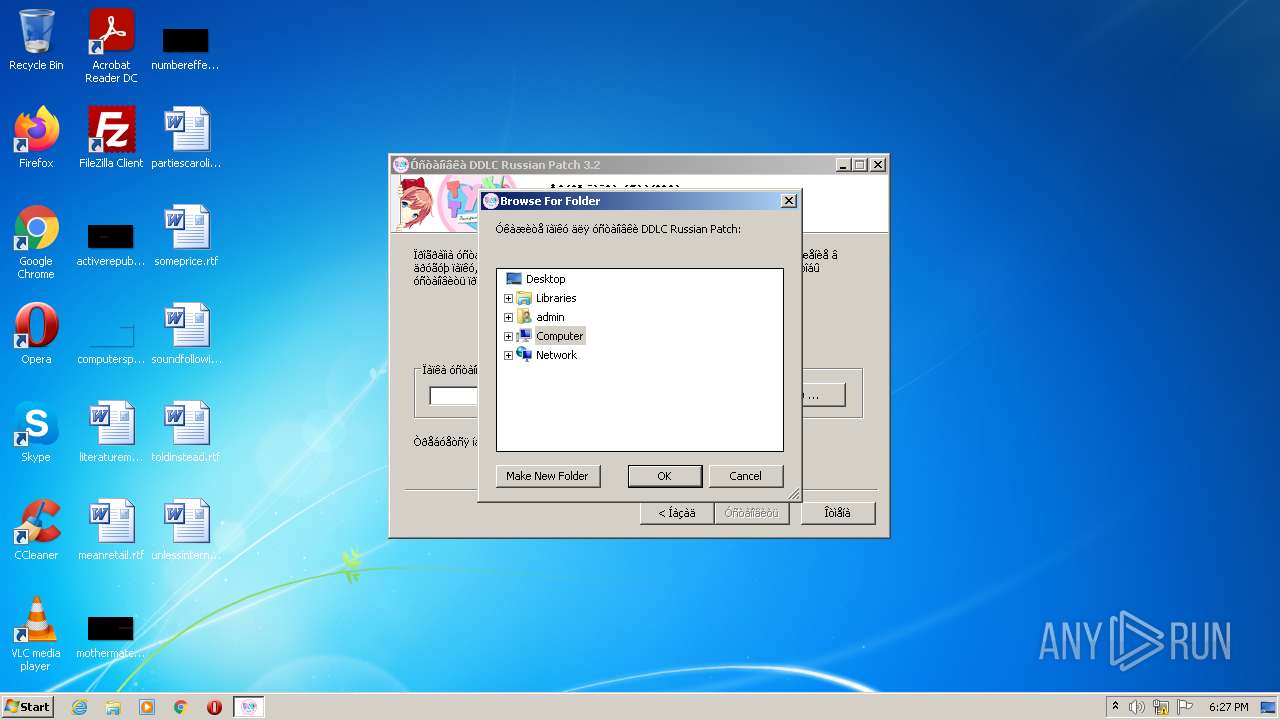
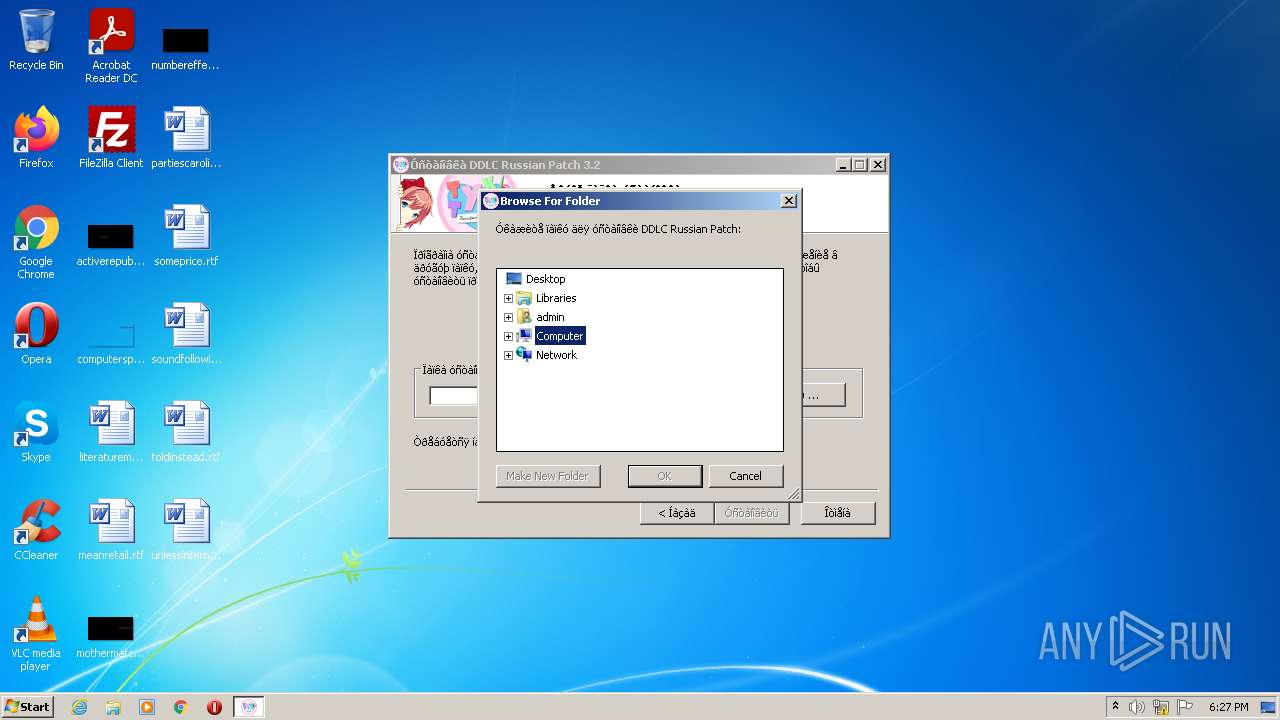
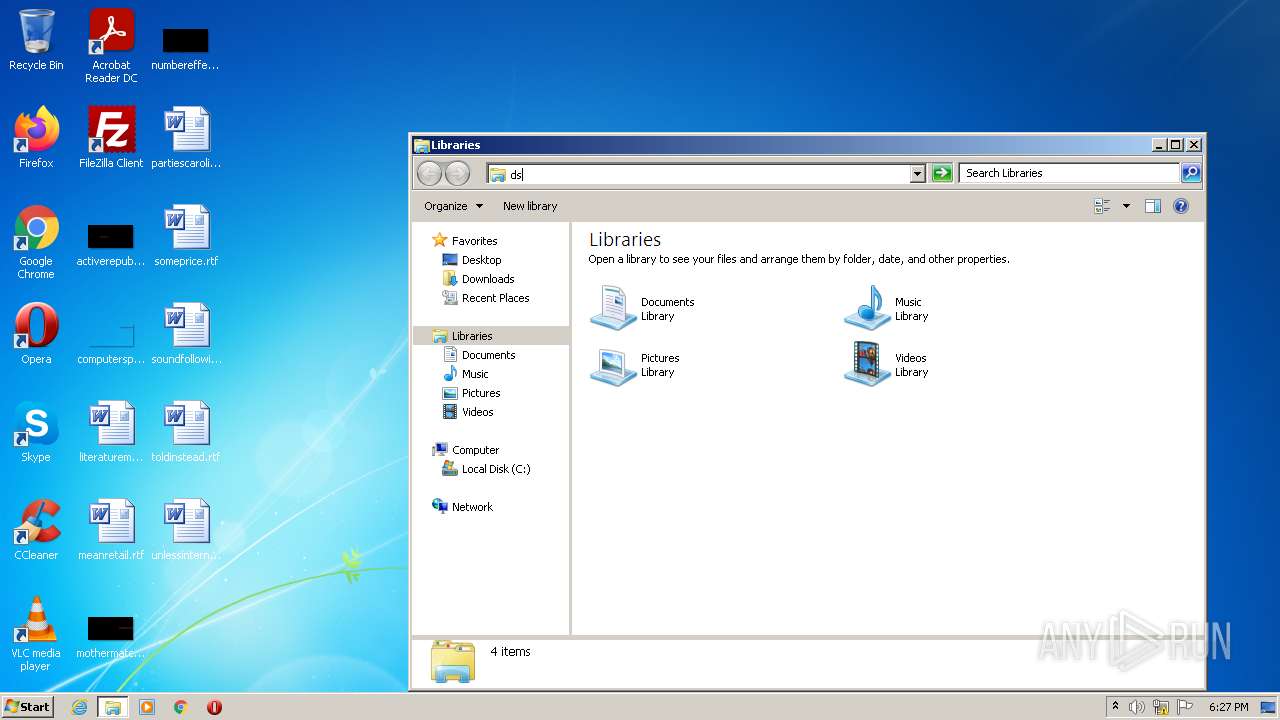
Modification events
| (PID) Process: | (4020) DDLC_russian_patch_3.2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4020) DDLC_russian_patch_3.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (4020) DDLC_russian_patch_3.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
Executable files
1
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
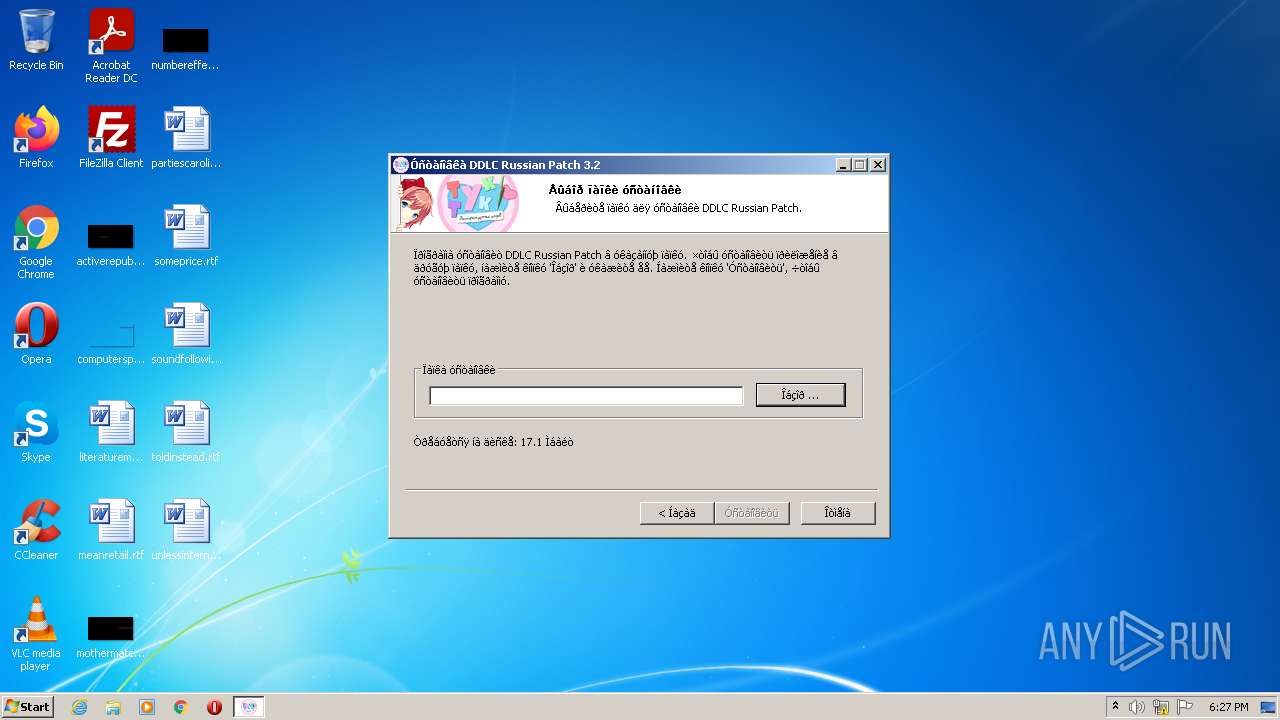
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4020 | DDLC_russian_patch_3.2.exe | C:\Users\admin\AppData\Local\Temp\nsy6DD1.tmp | binary | |
MD5:— | SHA256:— | |||
| 4020 | DDLC_russian_patch_3.2.exe | C:\Users\admin\AppData\Local\Temp\nsy6DD2.tmp\modern-wizard.bmp | image | |
MD5:301964FF73628DF4758131C20CB53671 | SHA256:D0A7F9675FB4D8682BEE2D6DB14C9B3989C65B44C626AC7F41BE7531311DE87B | |||
| 4020 | DDLC_russian_patch_3.2.exe | C:\Users\admin\AppData\Local\Temp\nsy6DD2.tmp\InstallOptions.dll | executable | |
MD5:20F3184EFE7EDDDFEF3325EFC25D12A5 | SHA256:0E014352B64ABC431D97460D79757CBAFBF6BA997C08B608C294E1F582AF269A | |||
| 4020 | DDLC_russian_patch_3.2.exe | C:\Users\admin\AppData\Local\Temp\nsy6DD2.tmp\modern-header.bmp | image | |
MD5:D39EA663D3FB91C0BAD278CFE905B3C8 | SHA256:6C17E96D99A39D33651105CE69C674EAE910BC1CF2CBC27508ADC74C4F58140E | |||
| 4020 | DDLC_russian_patch_3.2.exe | C:\Users\admin\AppData\Local\Temp\nsy6DD2.tmp\ioSpecial.ini | ini | |
MD5:E2D5070BC28DB1AC745613689FF86067 | SHA256:D95AED234F932A1C48A2B1B0D98C60CA31F962310C03158E2884AB4DDD3EA1E0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report