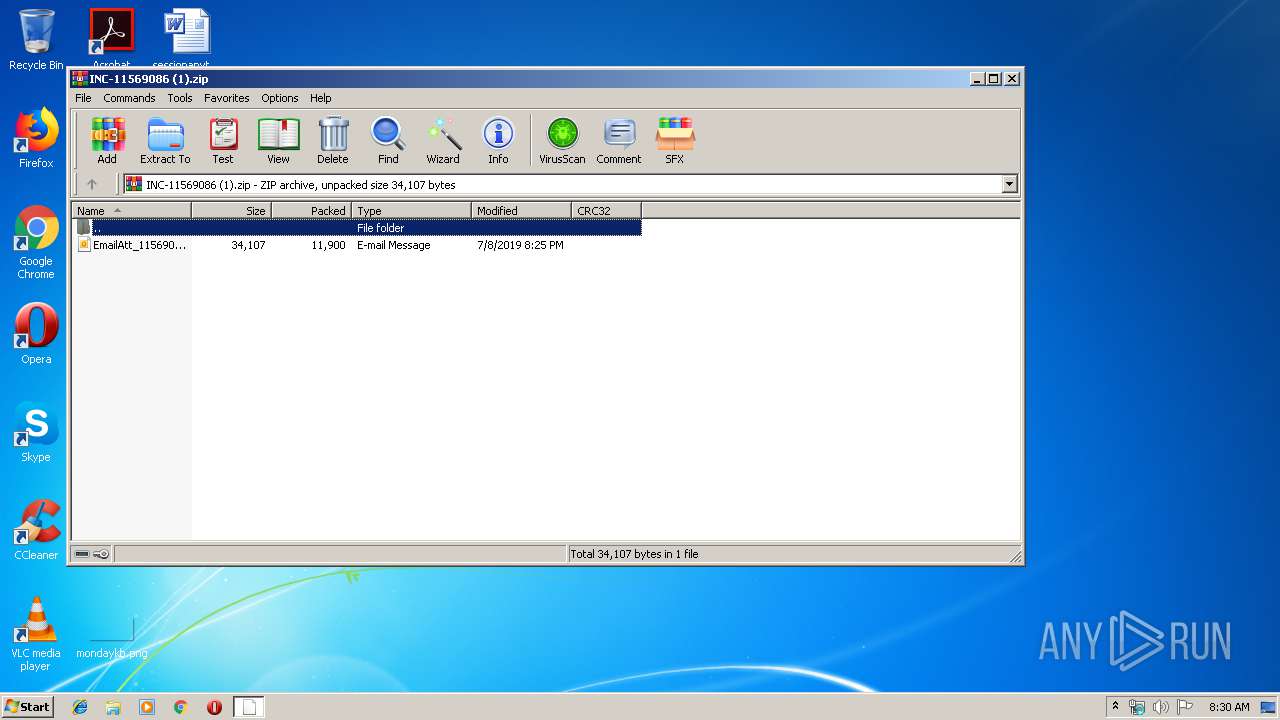
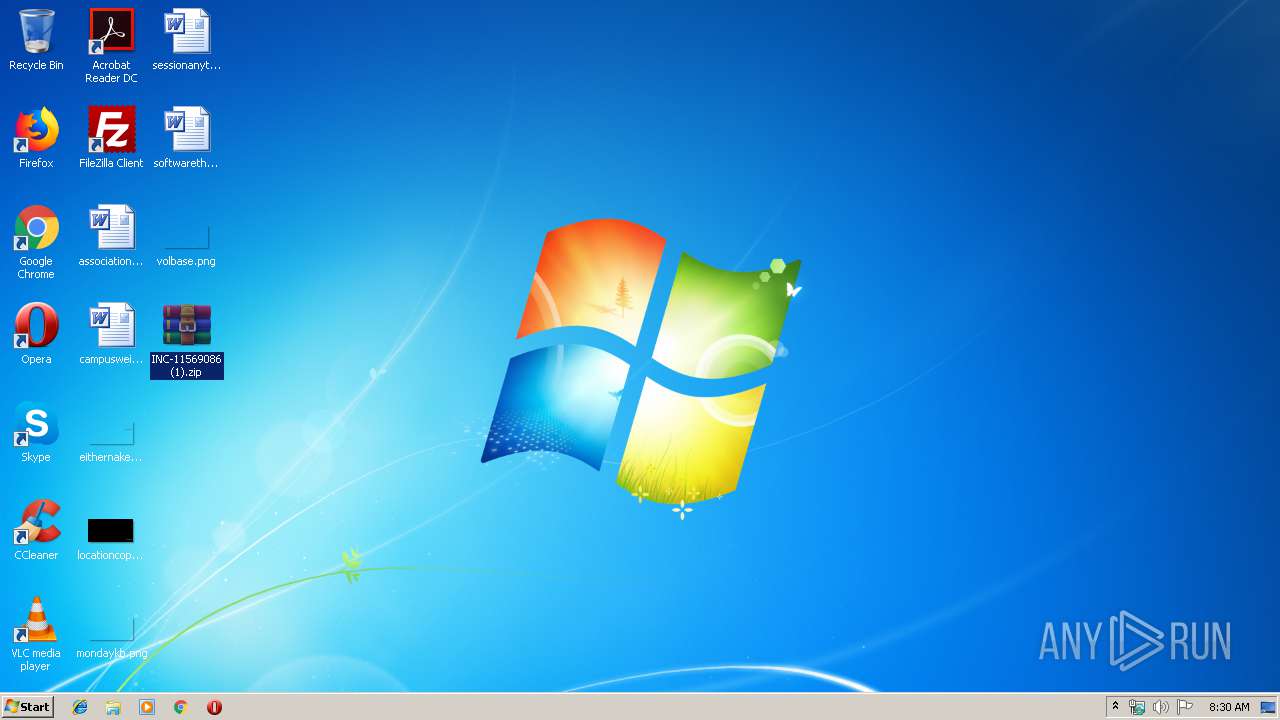
| File name: | INC-11569086 (1).zip |
| Full analysis: | https://app.any.run/tasks/5b2f58c7-7575-4ca9-ab51-e86501790bab |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 07:30:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | CFEE2848580F91B09D8BC325AB3F4BFC |
| SHA1: | 26CB3C79D3D9F113A4E50CD14D675B482A3CEAFE |
| SHA256: | 8A1E1E5D78F753E1153FDFB57C022EFBA3DCAE6EA1655F18FAD485137A35928F |
| SSDEEP: | 192:B/efeXCjwgJaVmKq0klVyfb0EiIWKw1zGgBpwzNPsPwfaRjBXeL7dx3FsYWg:B2kngyi7yWWuUJsMKjBX2qU |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2612)
Application launched itself
- OUTLOOK.EXE (PID: 2612)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2612)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3092)
INFO
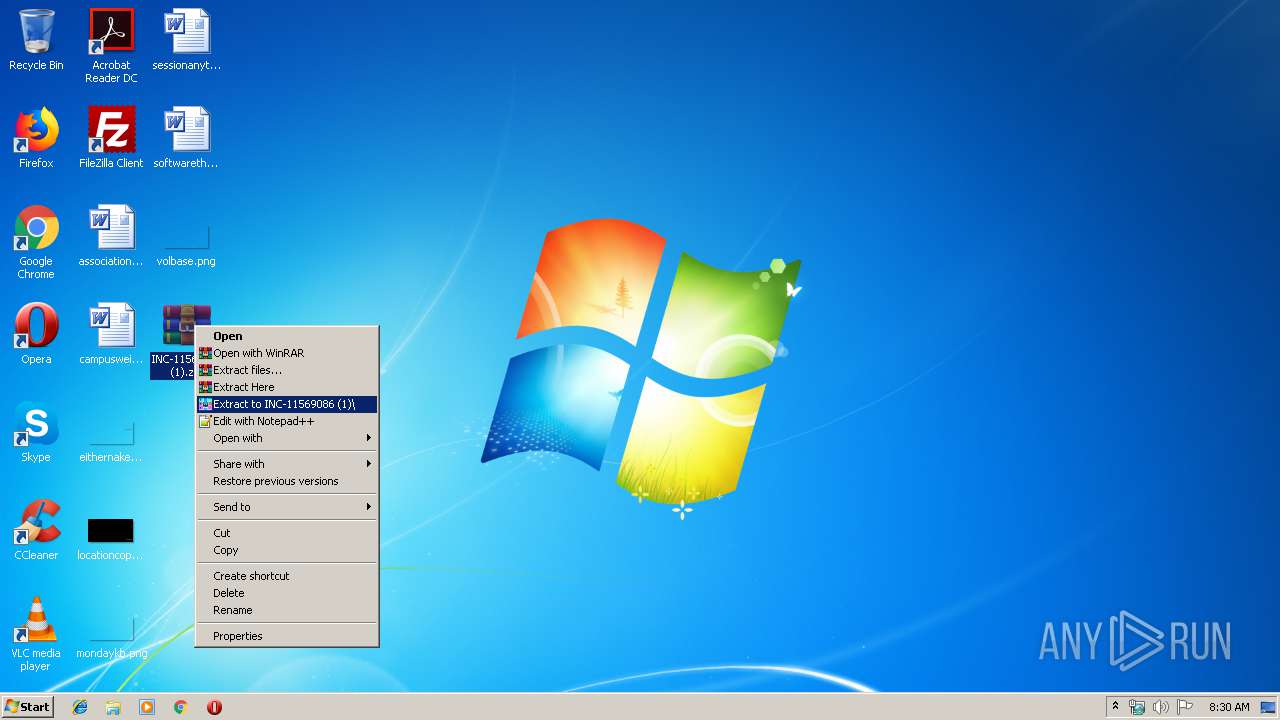
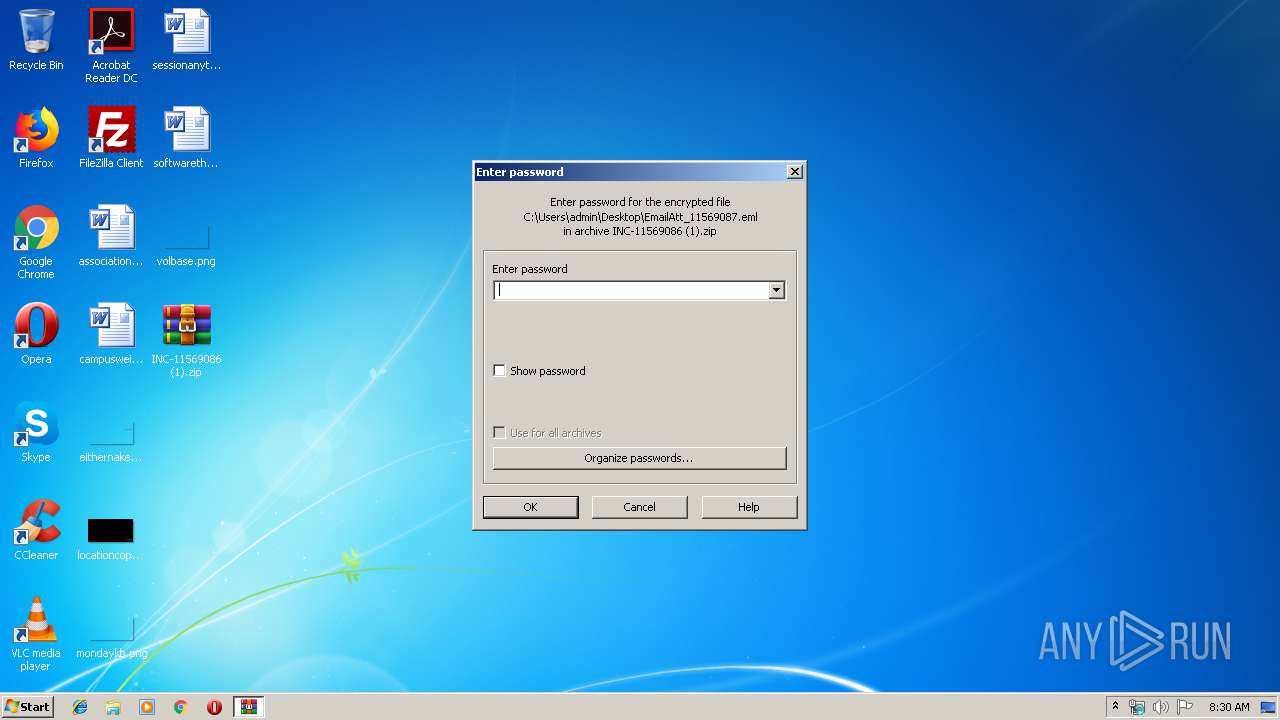
Manual execution by user
- WinRAR.exe (PID: 2068)
- OUTLOOK.EXE (PID: 2612)
- chrome.exe (PID: 3092)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2612)
- OUTLOOK.EXE (PID: 2456)
Application launched itself
- chrome.exe (PID: 3092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2019:07:08 15:25:06 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 11900 |
| ZipUncompressedSize: | 34107 |
| ZipFileName: | EmailAtt_11569087.eml |
Total processes
71
Monitored processes
33
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,4592074597370561415,5102032156157836407,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17389015509684976295 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\INC-11569086 (1).zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3100 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
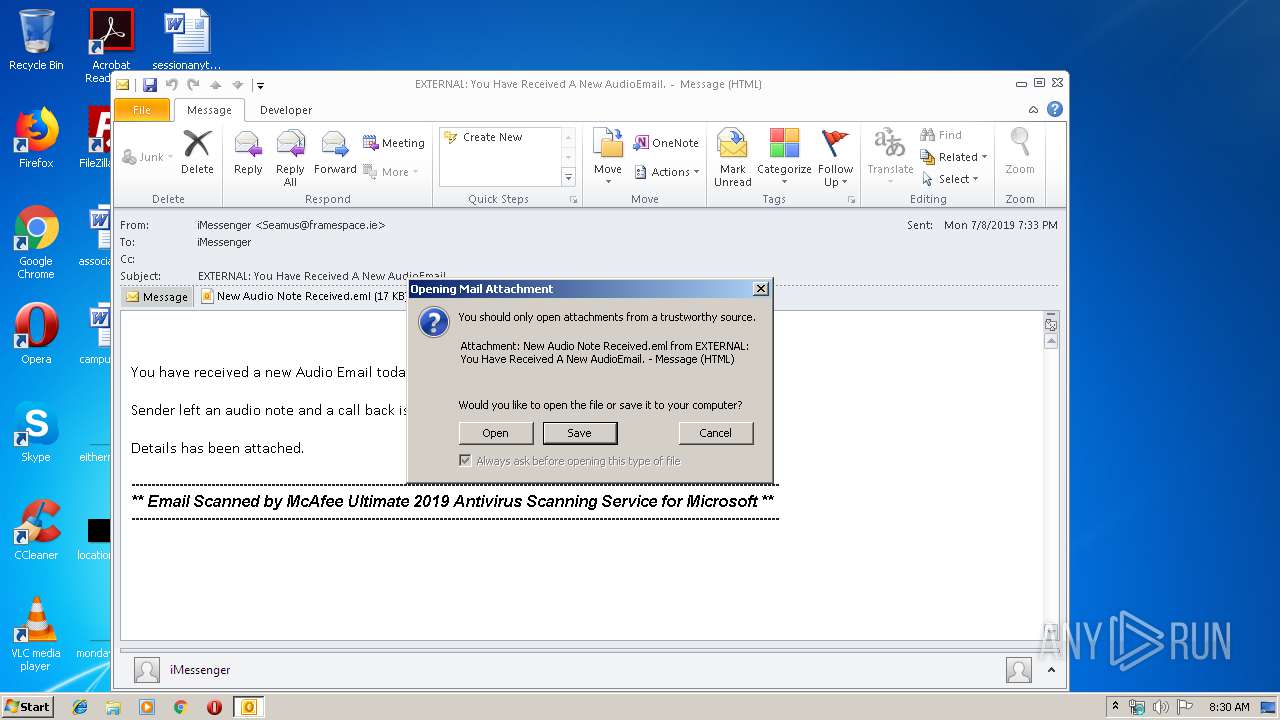
| 2456 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\OG13IZK2\New Audio Note Received.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,4592074597370561415,5102032156157836407,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3394429809421031582 --mojo-platform-channel-handle=2724 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2612 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\Desktop\EmailAtt_11569087.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,4592074597370561415,5102032156157836407,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12241518731024998795 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,4592074597370561415,5102032156157836407,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11932182470554041063 --mojo-platform-channel-handle=4132 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,4592074597370561415,5102032156157836407,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11533110381018044098 --mojo-platform-channel-handle=3372 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,4592074597370561415,5102032156157836407,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9874156570196623545 --mojo-platform-channel-handle=3344 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 122
Read events
1 609
Write events
488
Delete events
25
Modification events
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\INC-11569086 (1).zip | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
164
Text files
197
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2612 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR2B62.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2612 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\OG13IZK2\New Audio Note Received (2).eml\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2456 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR4042.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2612 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
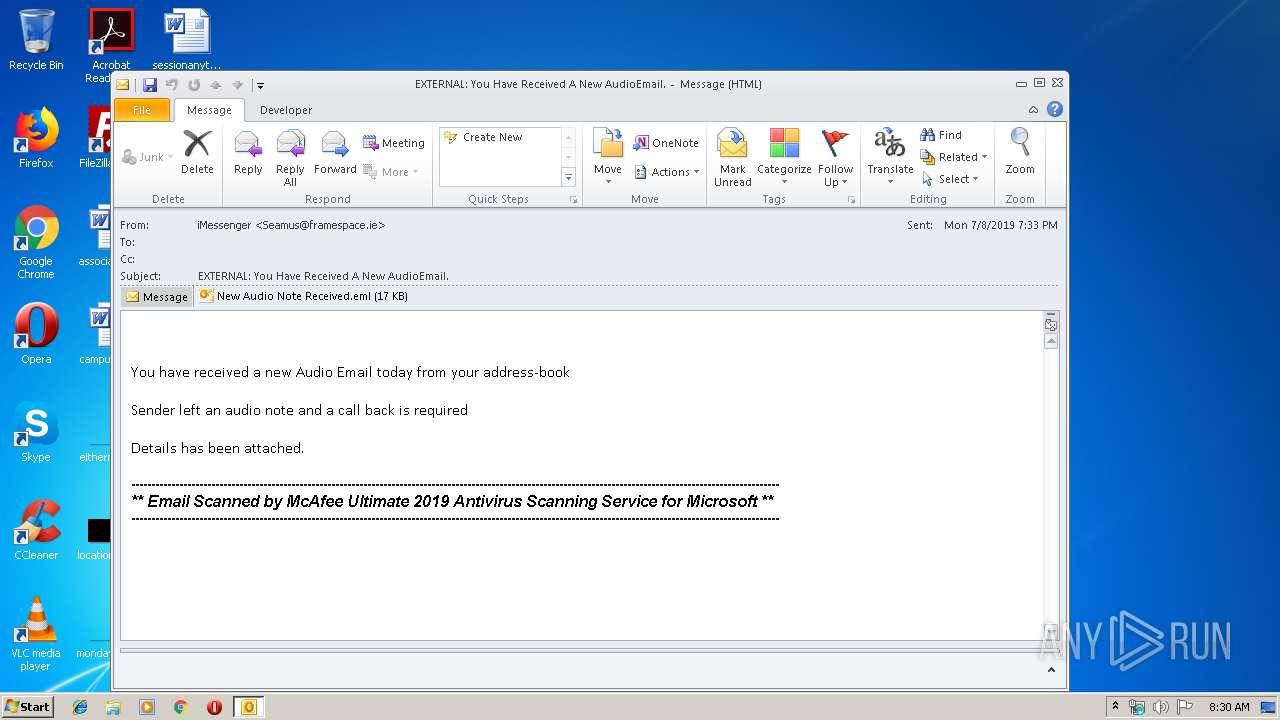
| 2068 | WinRAR.exe | C:\Users\admin\Desktop\EmailAtt_11569087.eml | eml | |
MD5:— | SHA256:— | |||
| 2612 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF115c36.TMP | text | |
MD5:— | SHA256:— | |||
| 2612 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\OG13IZK2\New Audio Note Received.eml | eml | |
MD5:— | SHA256:— | |||
| 2612 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\OG13IZK2\New Audio Note Received (2).eml | eml | |
MD5:— | SHA256:— | |||
| 3092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
67
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
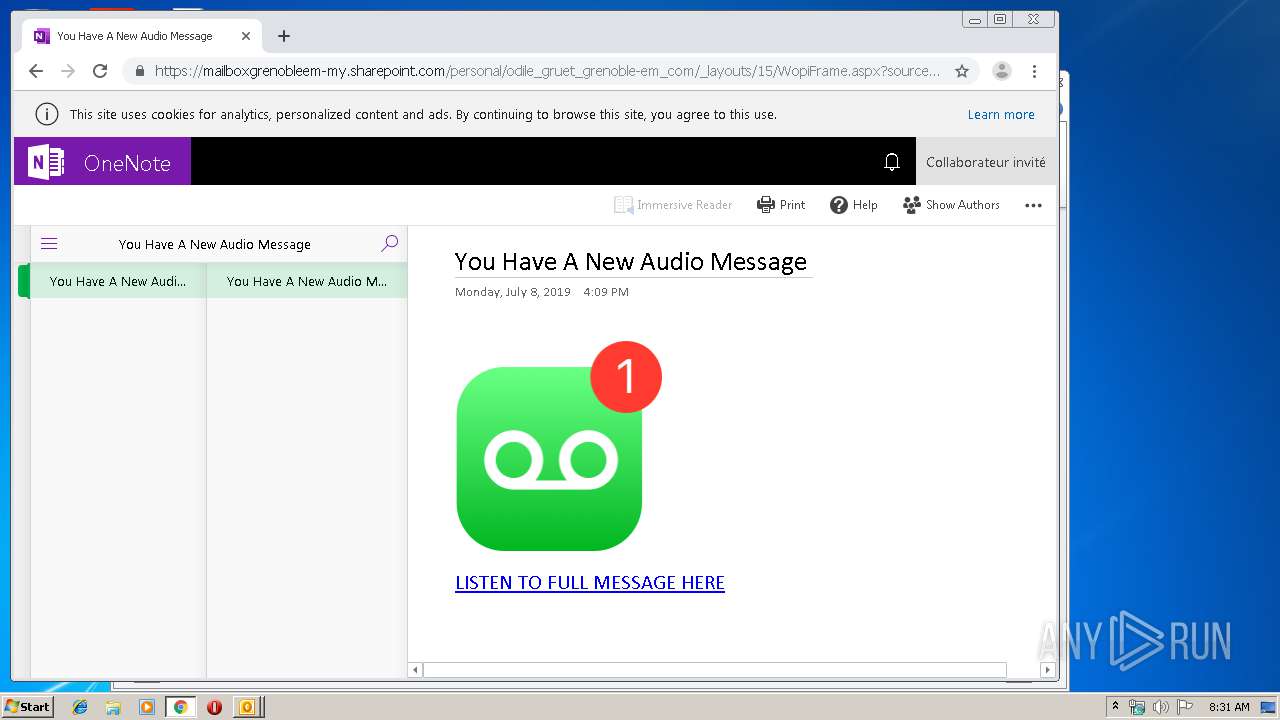
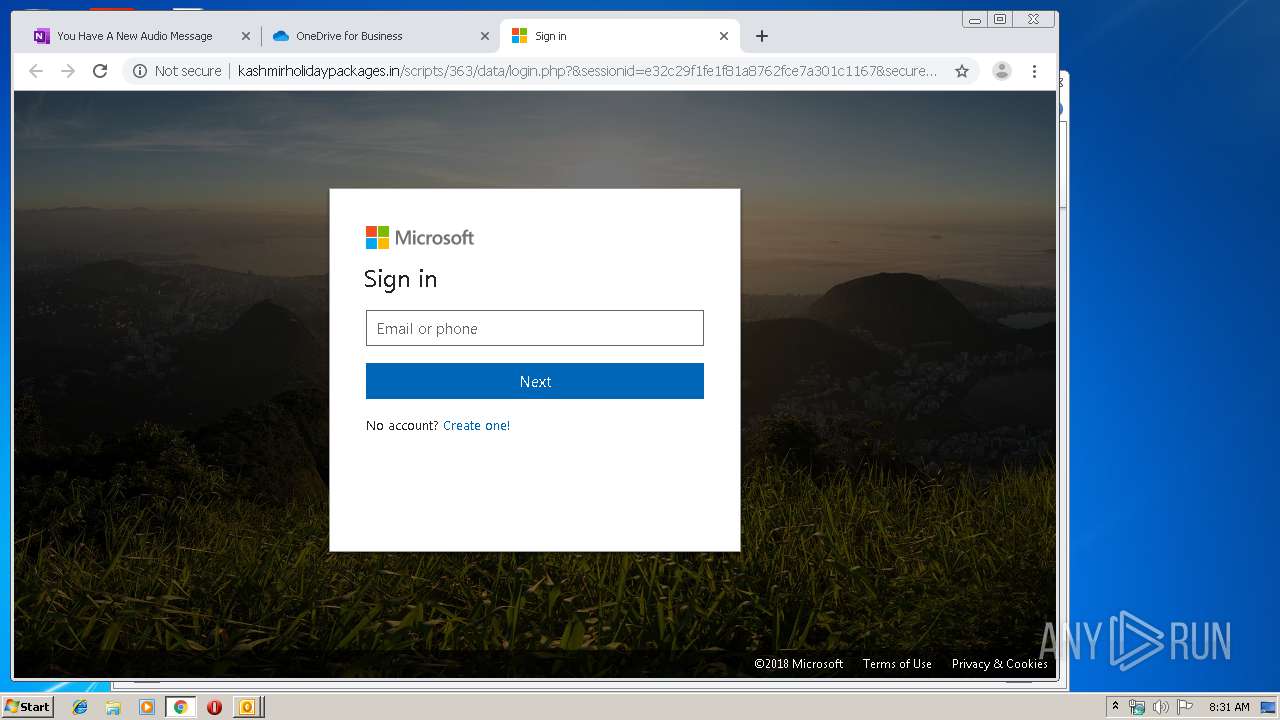
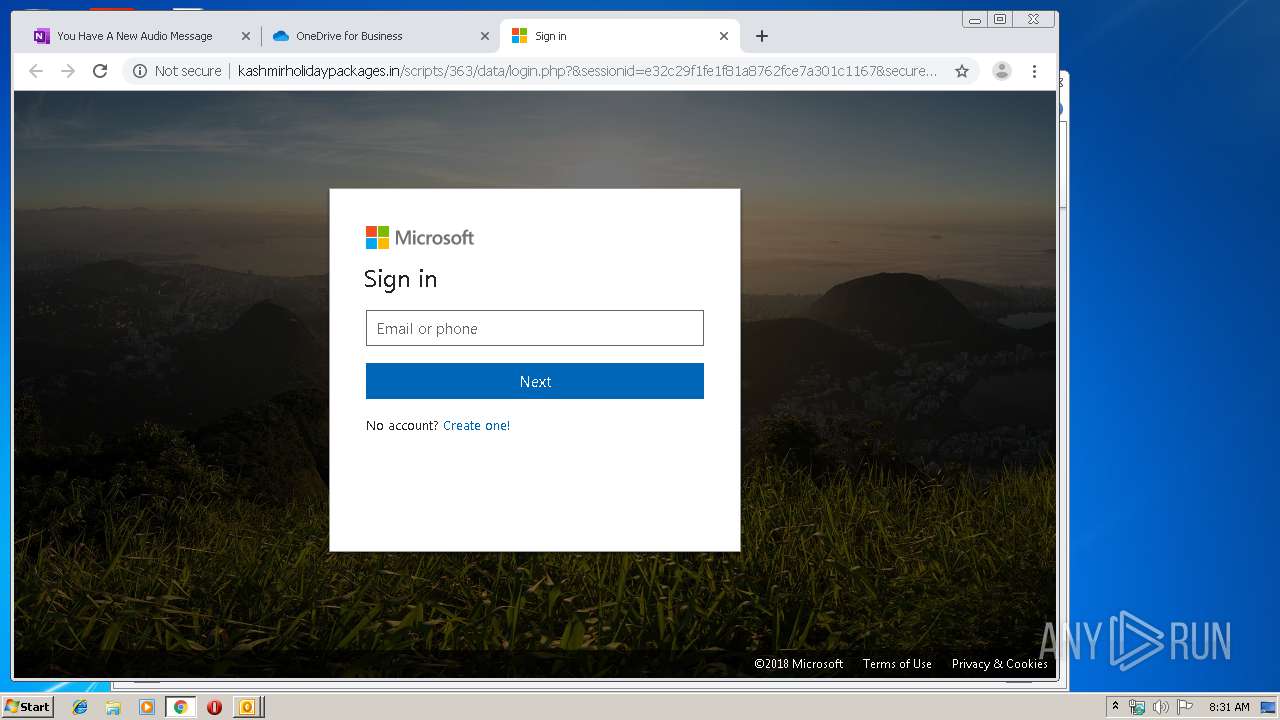
3064 | chrome.exe | GET | 200 | 54.36.166.181:80 | http://kashmirholidaypackages.in/scripts/363/data/outlook_files/Converged1033.css | FR | text | 16.3 Kb | malicious |
3064 | chrome.exe | GET | 200 | 54.36.166.181:80 | http://kashmirholidaypackages.in/scripts/363/data/outlook_files/modal.js | FR | text | 2.46 Kb | malicious |
3064 | chrome.exe | GET | 200 | 54.36.166.181:80 | http://kashmirholidaypackages.in/scripts/363/data/login.php?&sessionid=e32c29f1fe1f81a8762fce7a301c1167&securessl=true | FR | html | 3.14 Kb | malicious |
2612 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3064 | chrome.exe | GET | 200 | 54.36.166.181:80 | http://kashmirholidaypackages.in/scripts/363/data/outlook_files/favicon.ico | FR | image | 16.7 Kb | malicious |
3064 | chrome.exe | GET | 200 | 54.36.166.181:80 | http://kashmirholidaypackages.in/scripts/363/data/outlook_files/microsoft_logo.svg | FR | image | 1.40 Kb | malicious |
3064 | chrome.exe | GET | 200 | 54.36.166.181:80 | http://kashmirholidaypackages.in/scripts/363/data/outlook_files/0.jpg | FR | image | 291 Kb | malicious |
3064 | chrome.exe | GET | 200 | 54.36.166.181:80 | http://kashmirholidaypackages.in/scripts/363/data/outlook_files/0-small.jpg | FR | image | 1.00 Kb | malicious |
3064 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 521 b | whitelisted |
3064 | chrome.exe | GET | 302 | 54.36.166.181:80 | http://kashmirholidaypackages.in/scripts/363/data/ | FR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3064 | chrome.exe | 172.217.23.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3064 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3064 | chrome.exe | 172.217.21.206:443 | apis.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3064 | chrome.exe | 172.217.16.131:443 | www.google.com.ua | Google Inc. | US | whitelisted |
— | — | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2612 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
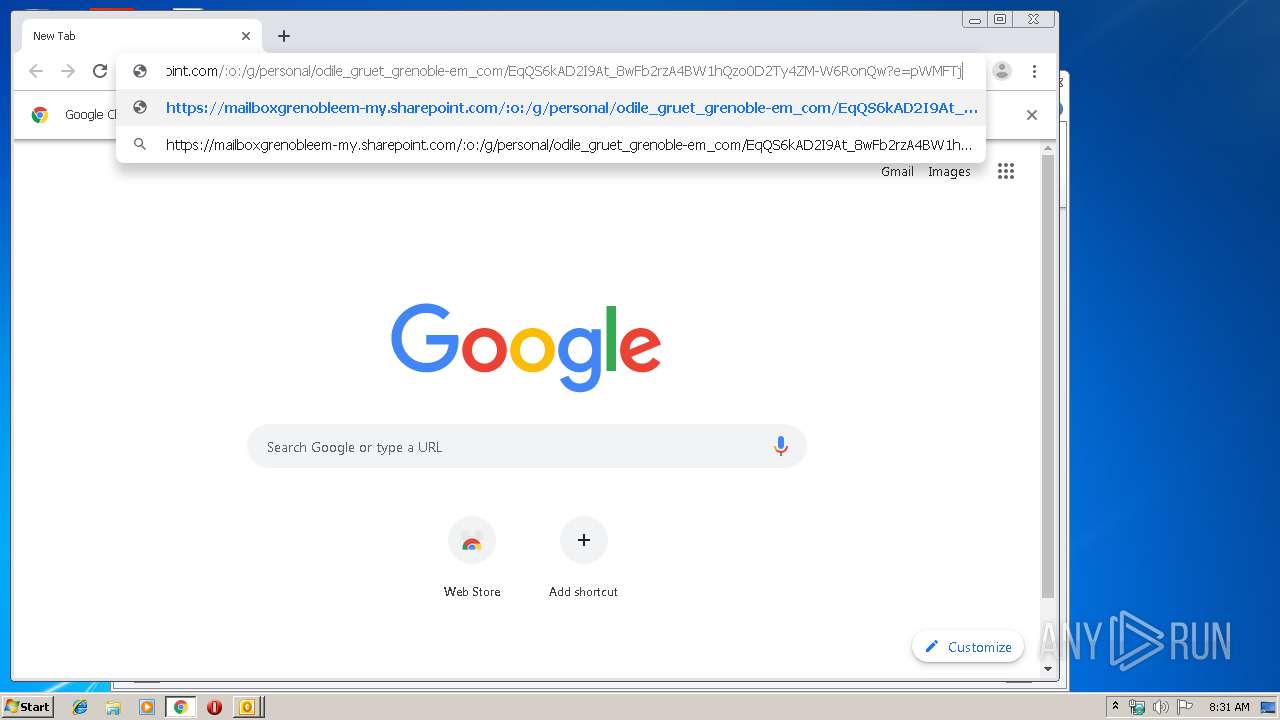
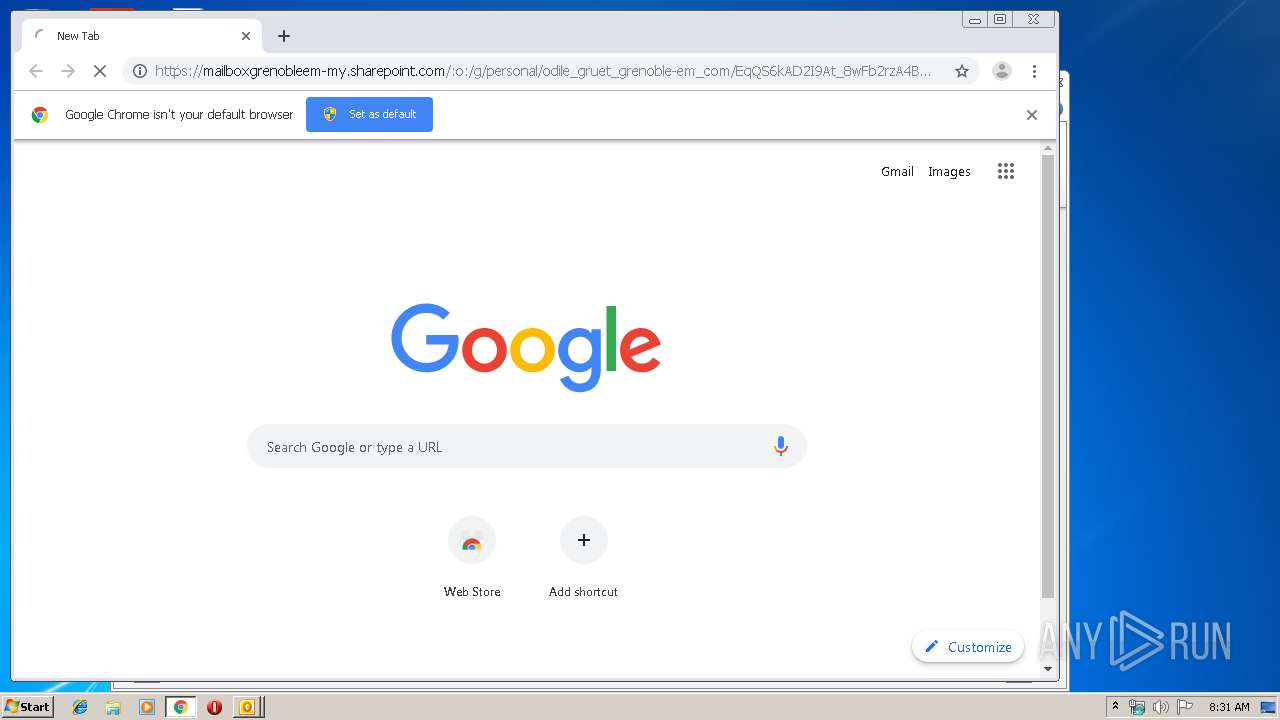
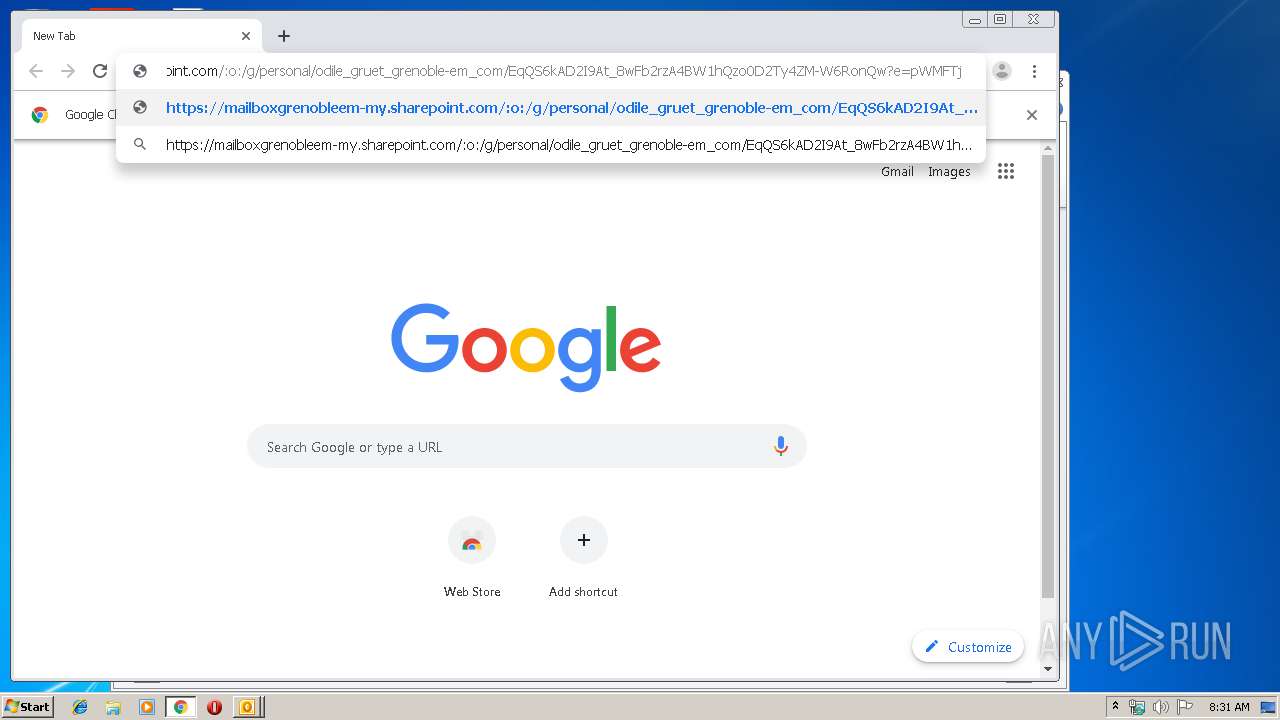
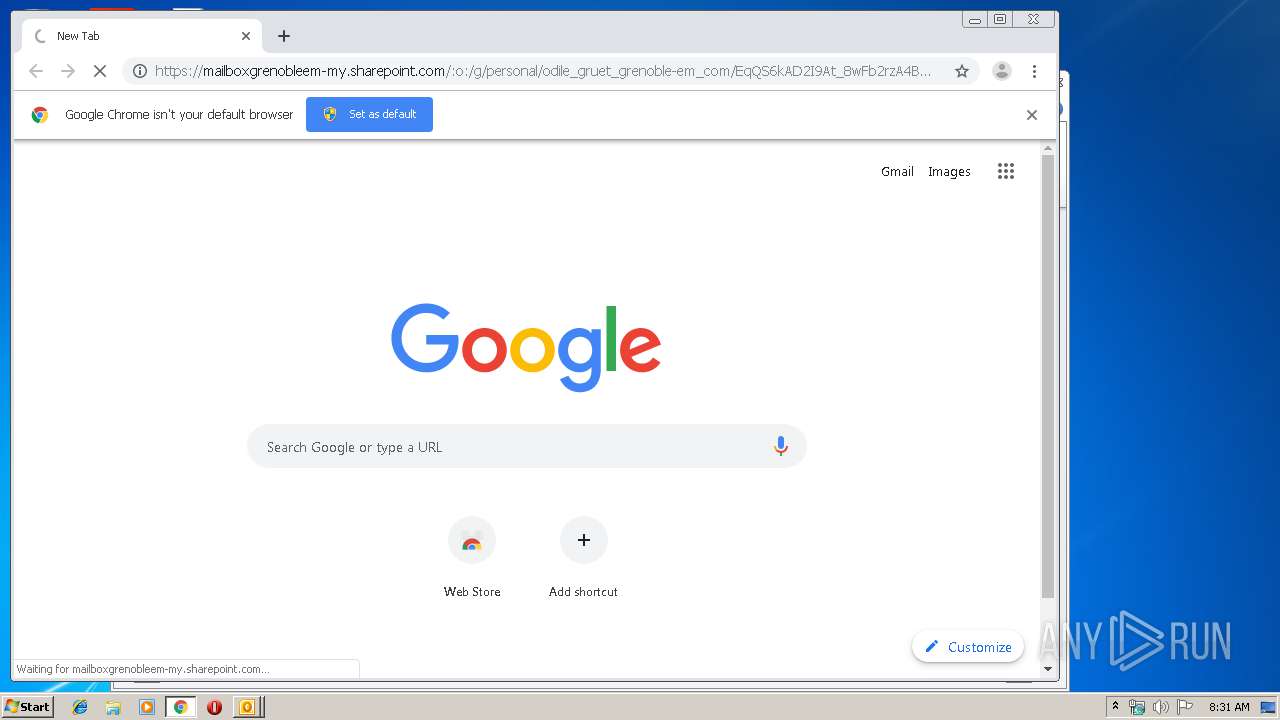
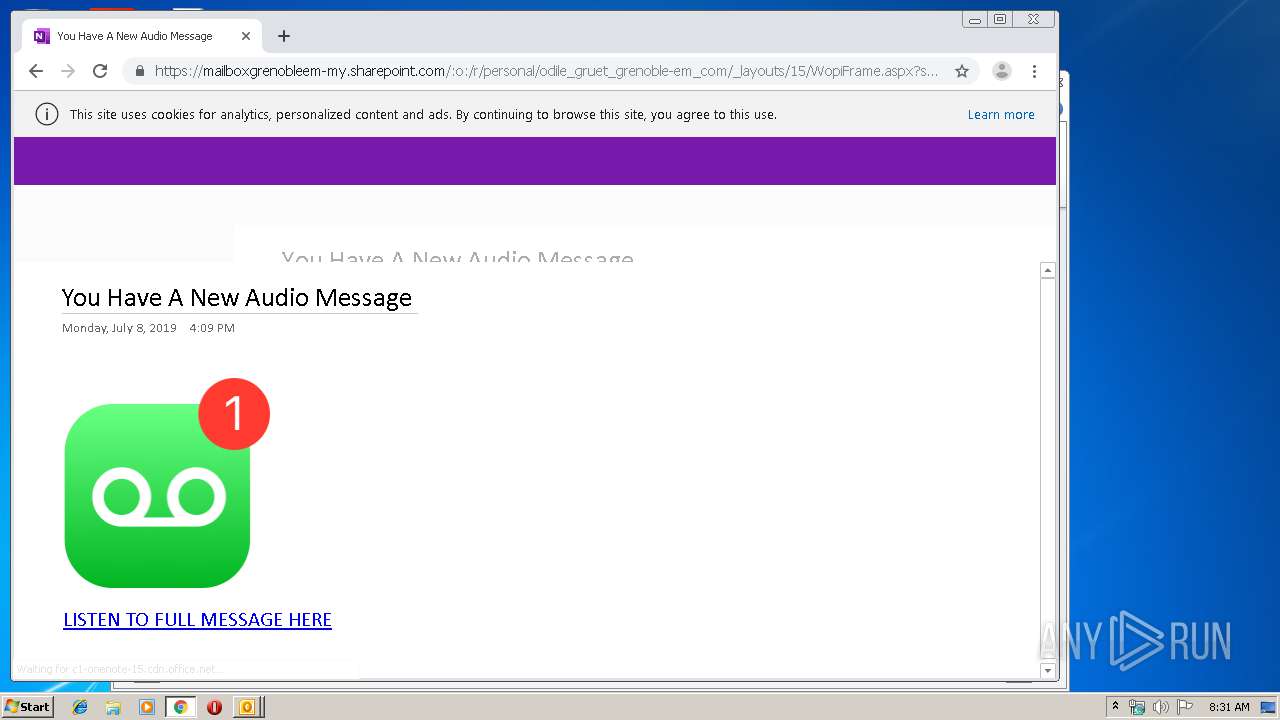
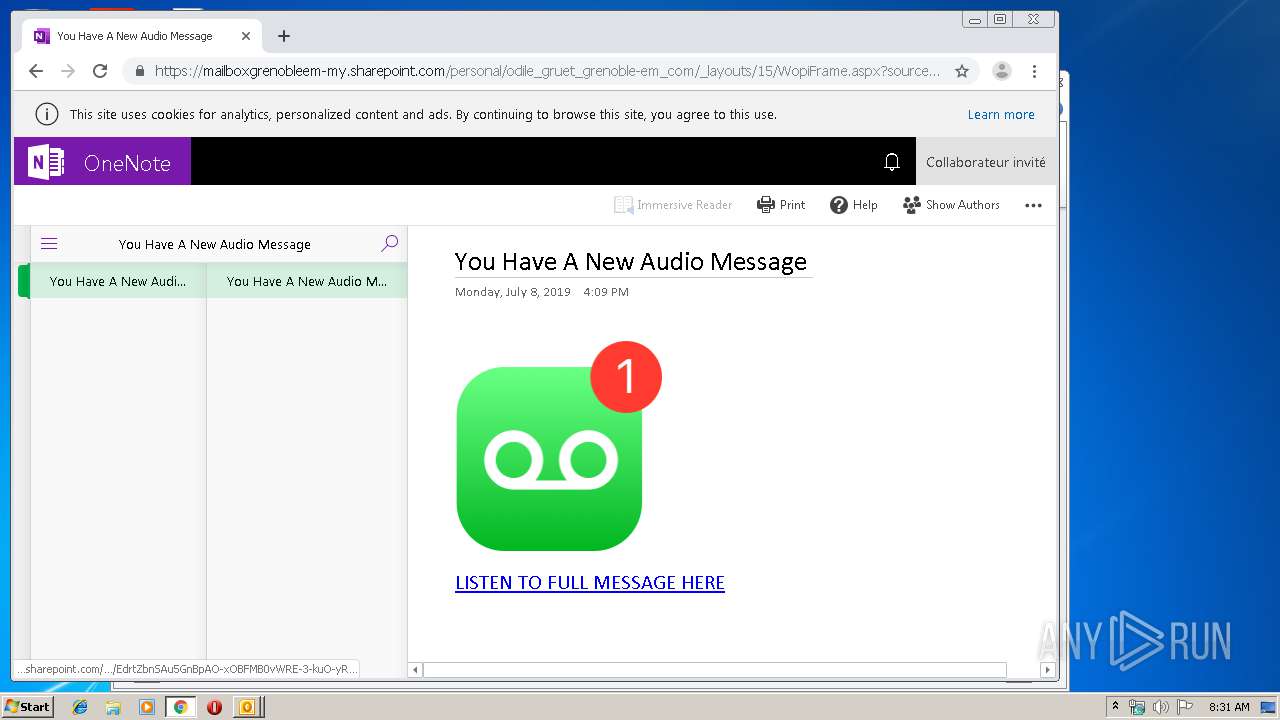
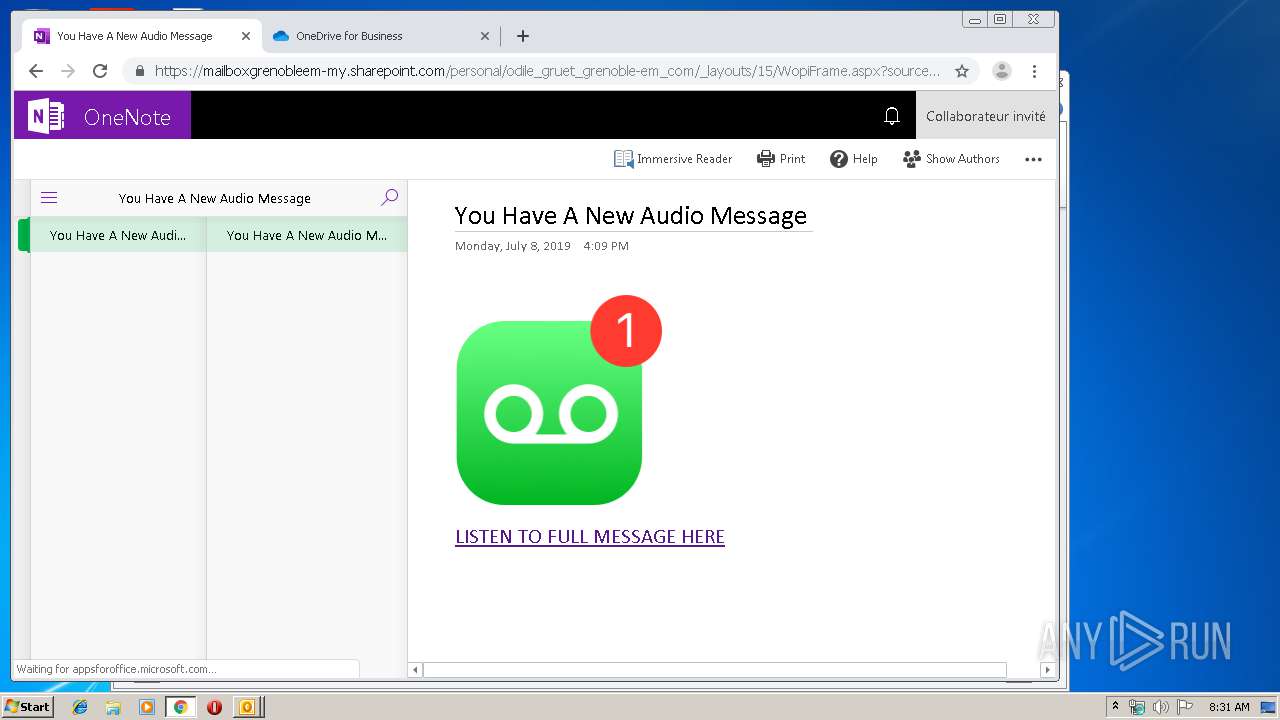
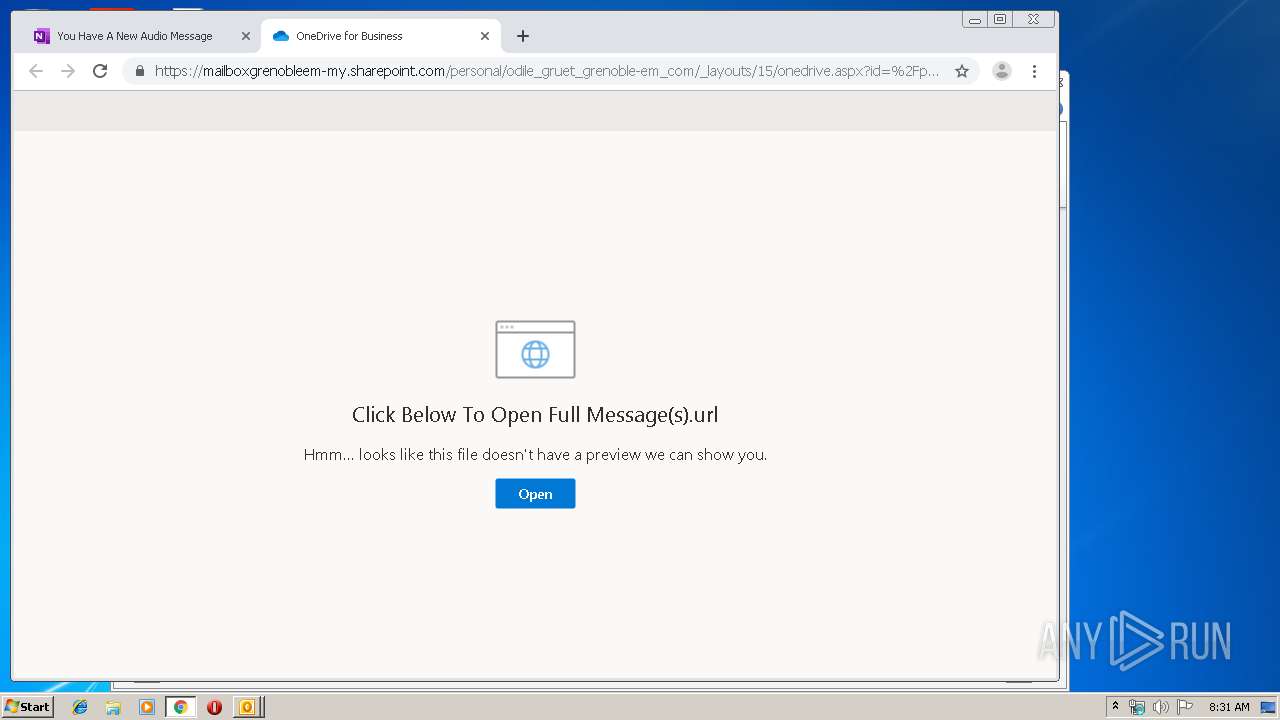
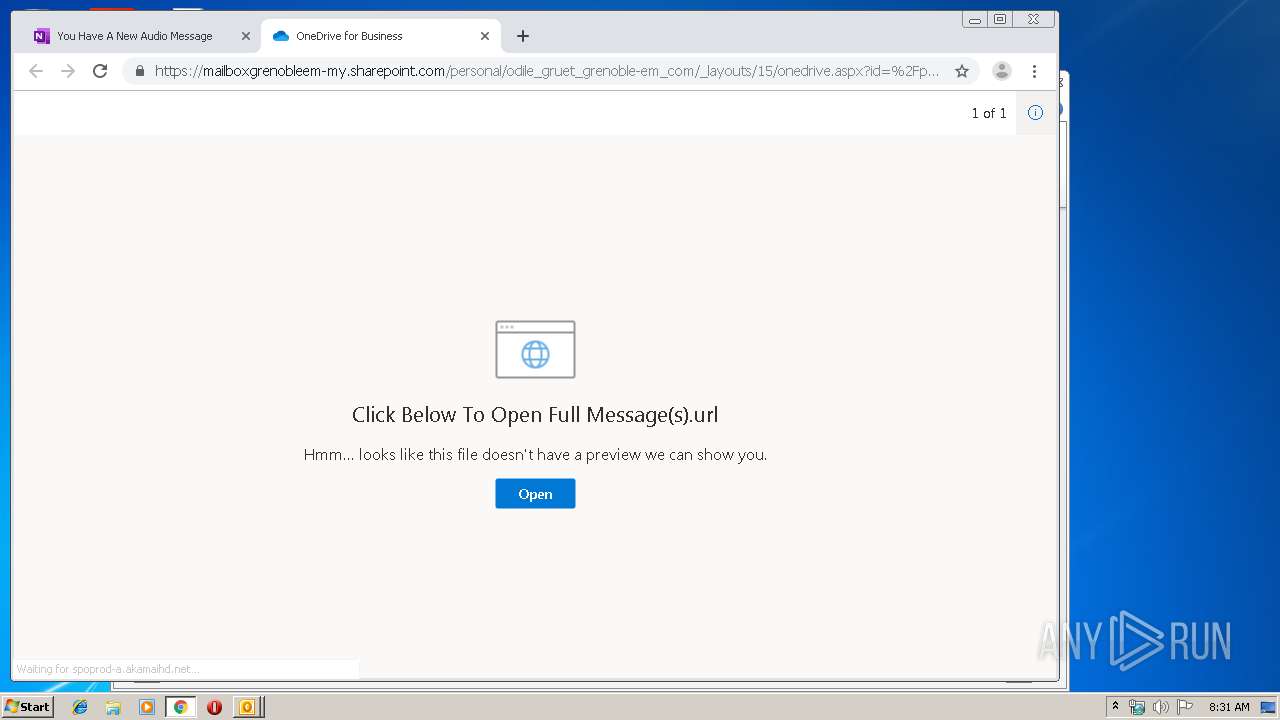
3064 | chrome.exe | 13.107.136.9:443 | mailboxgrenobleem-my.sharepoint.com | Microsoft Corporation | US | whitelisted |
3064 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
3064 | chrome.exe | 172.217.18.14:443 | ogs.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
mailboxgrenobleem-my.sharepoint.com |
| suspicious |
www.google.com |
| malicious |