| File name: | MrT.exe |
| Full analysis: | https://app.any.run/tasks/213c1368-431b-4da3-9fa5-62f7e381356d |
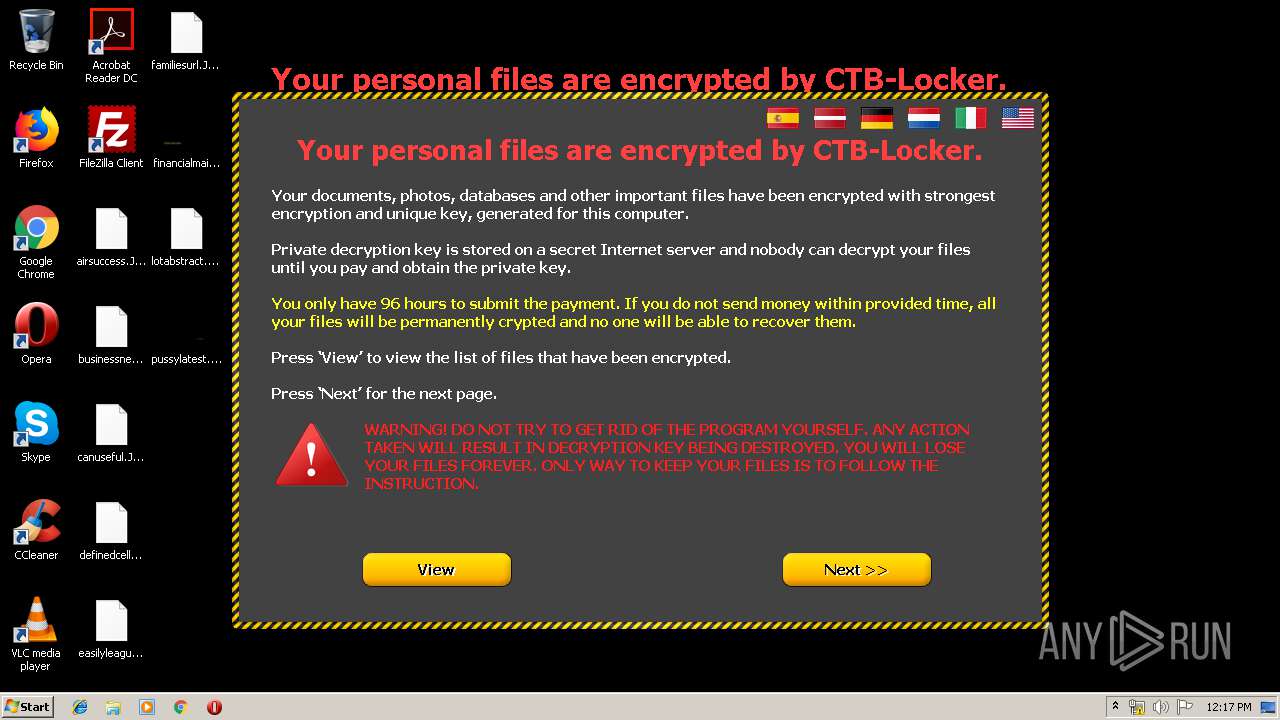
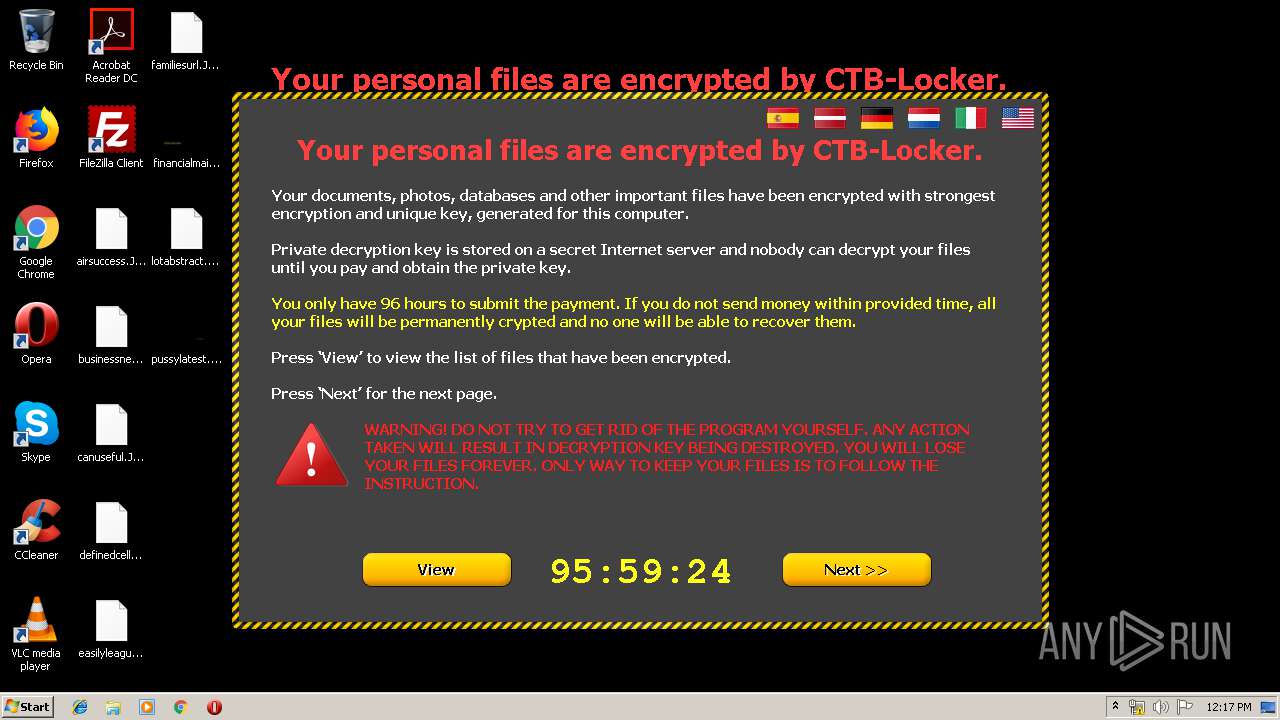
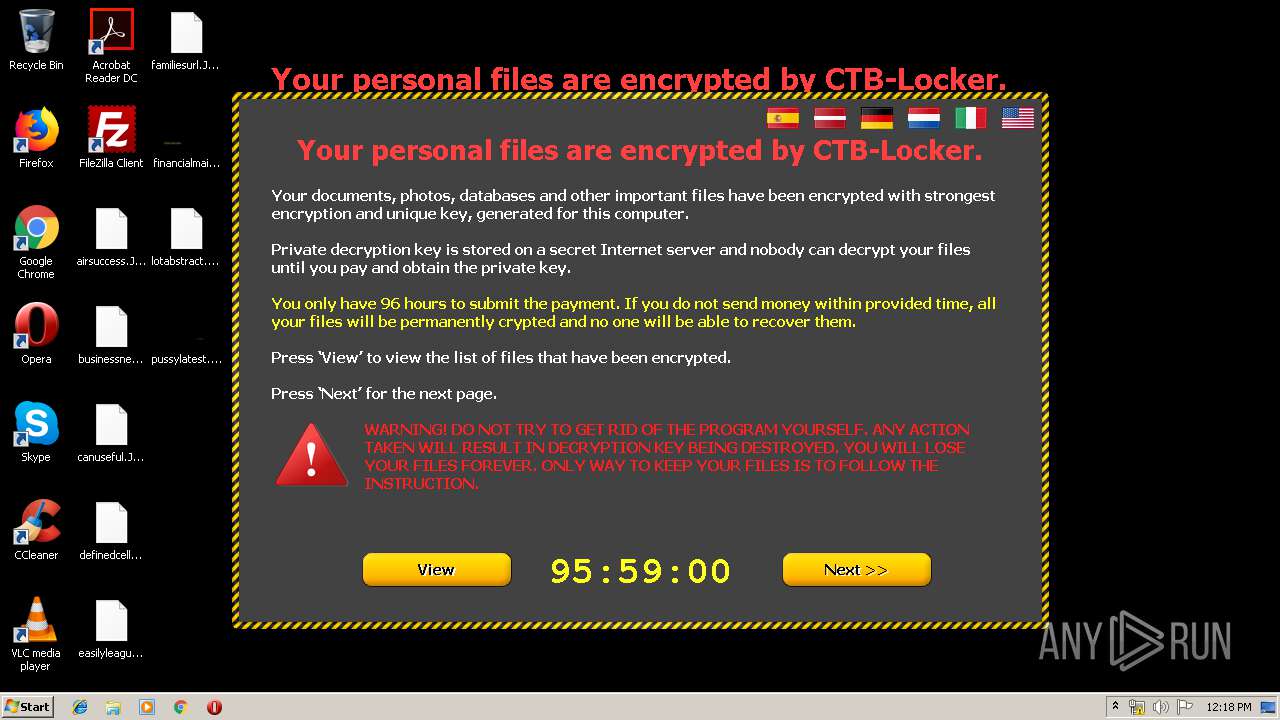
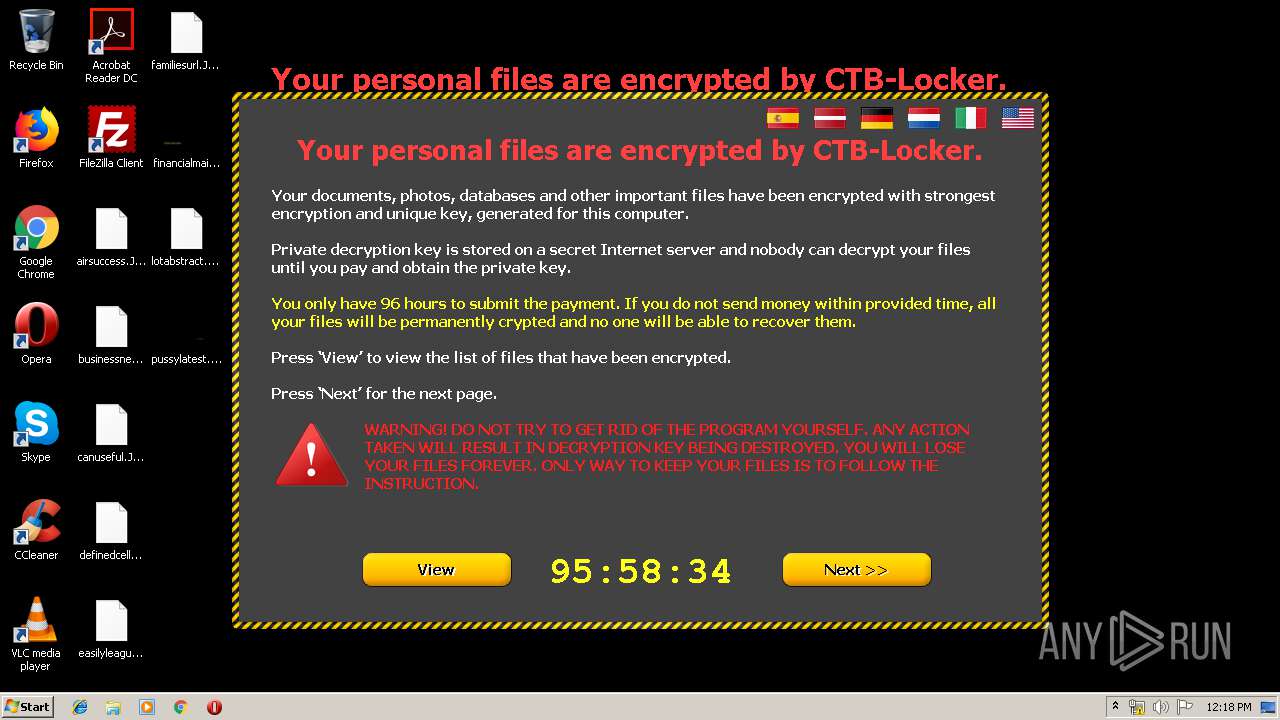
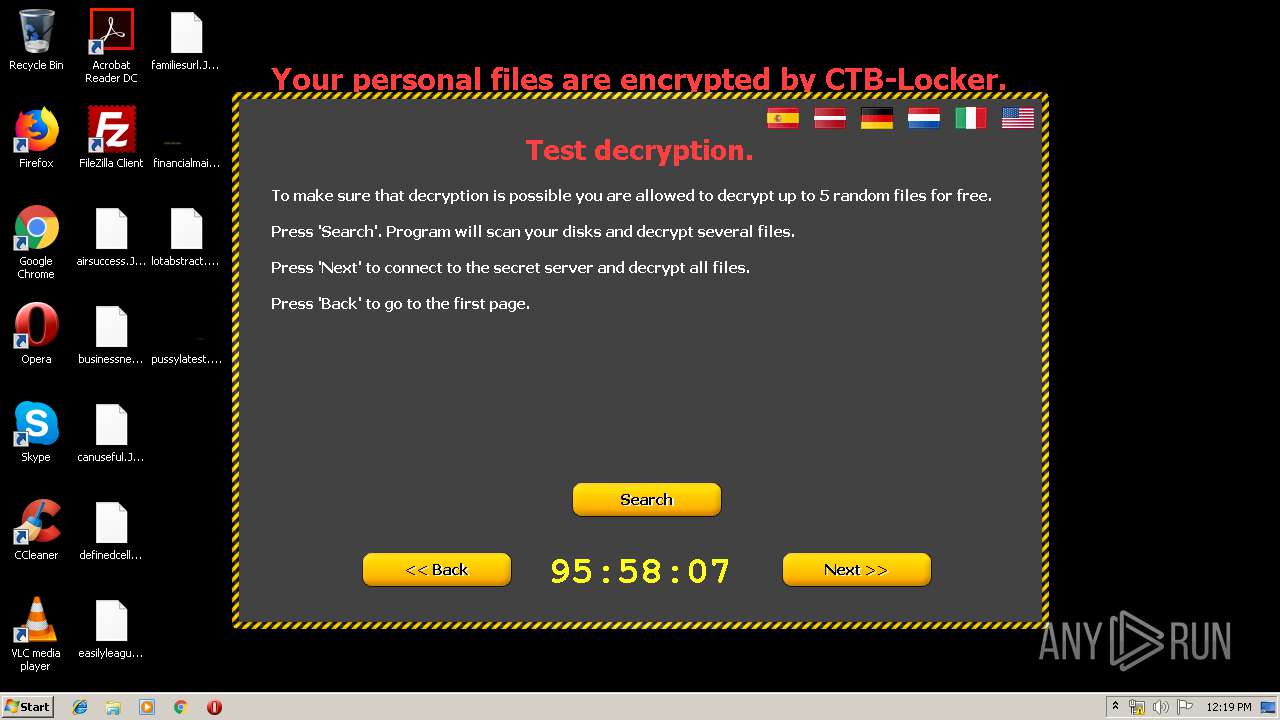
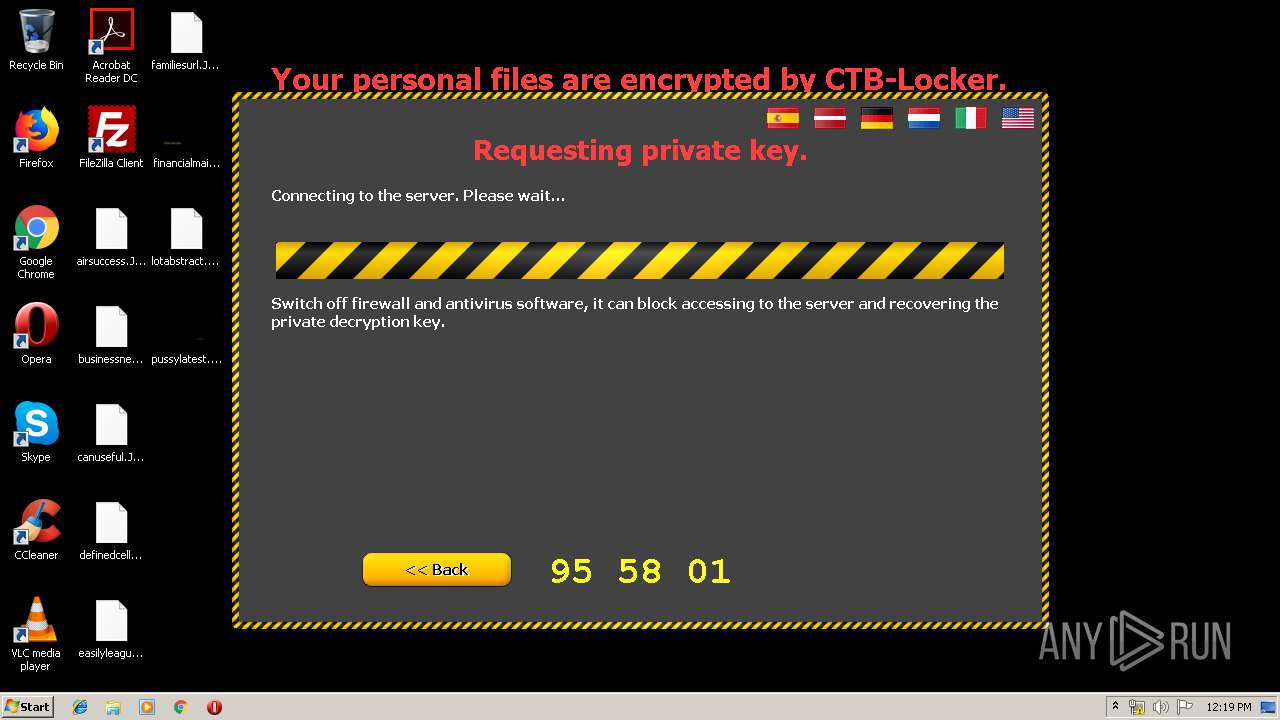
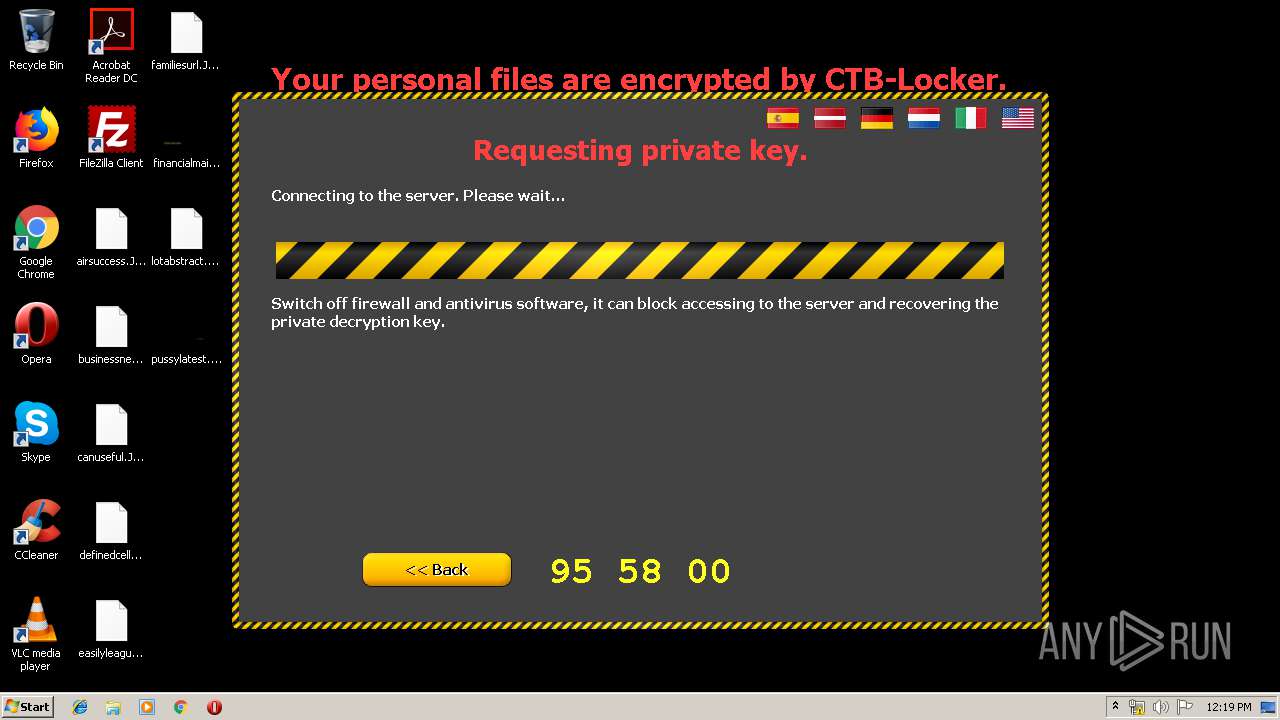
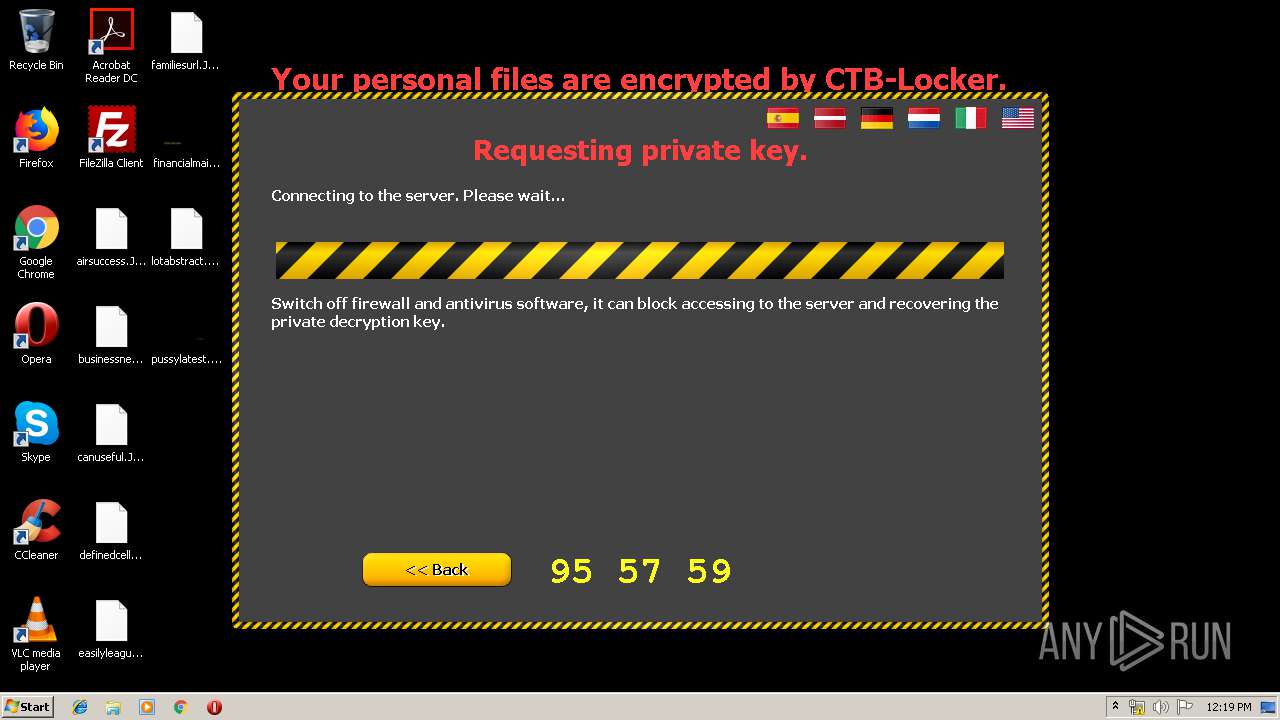
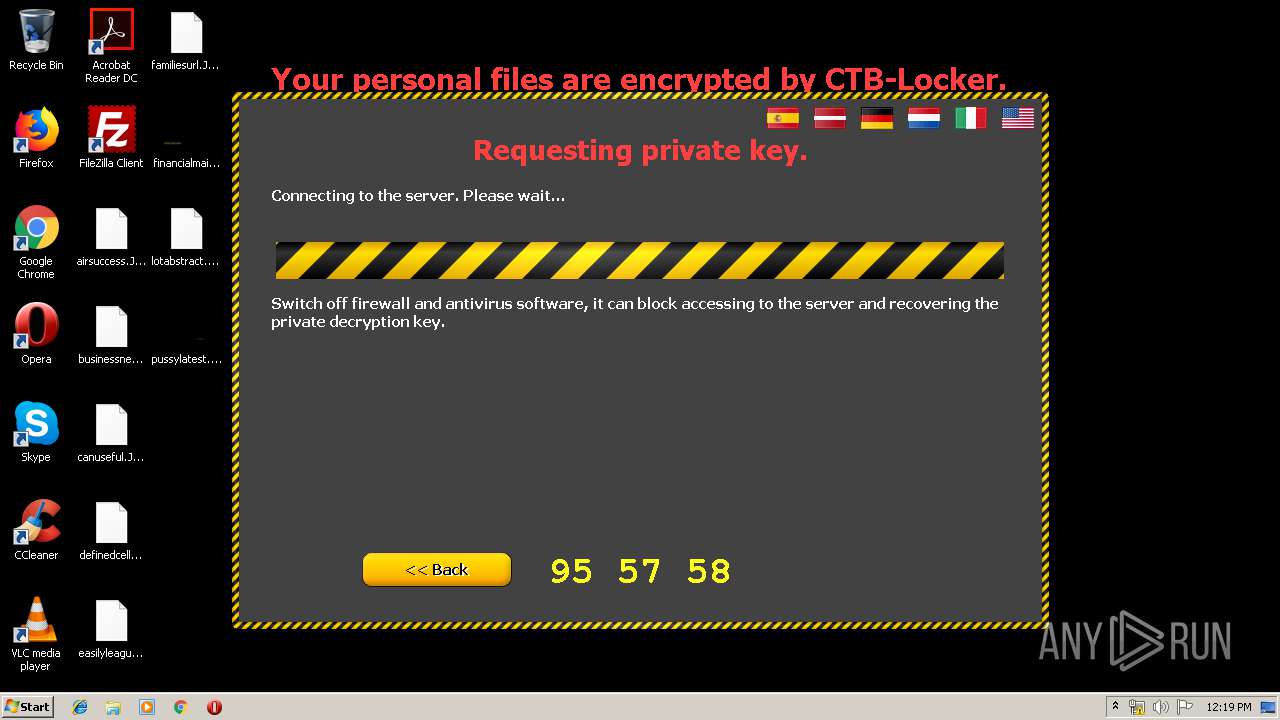
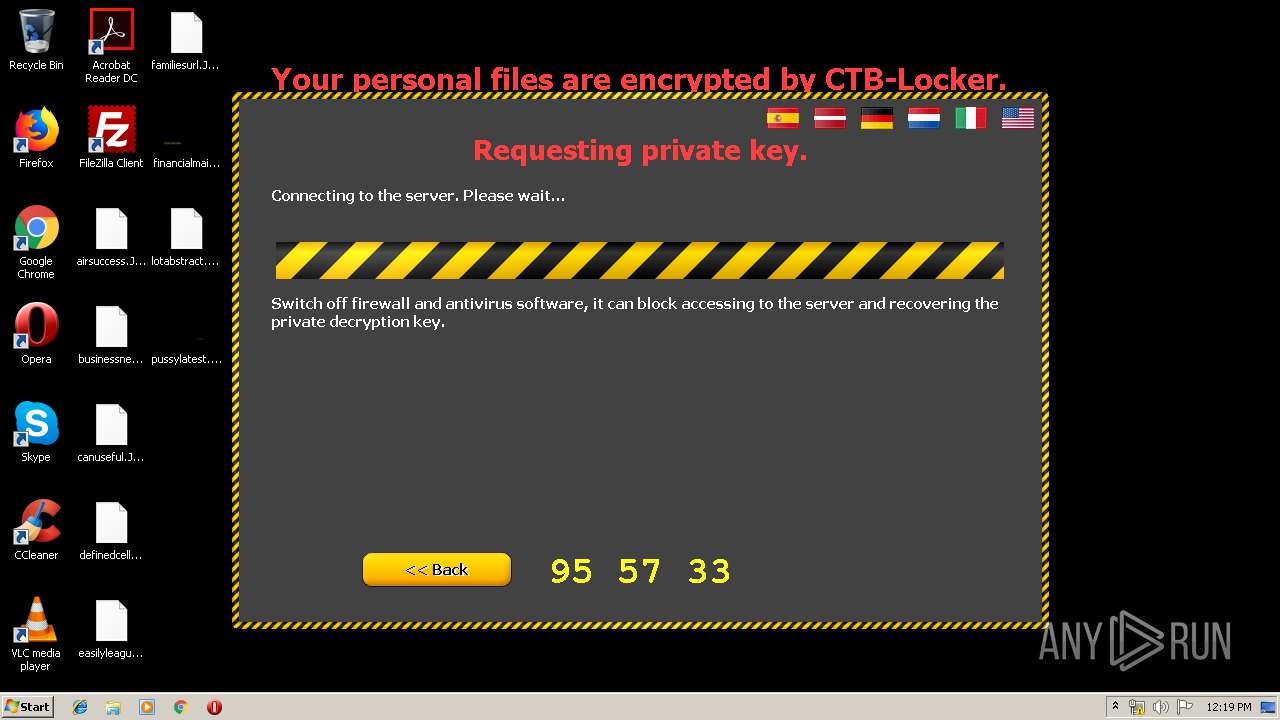
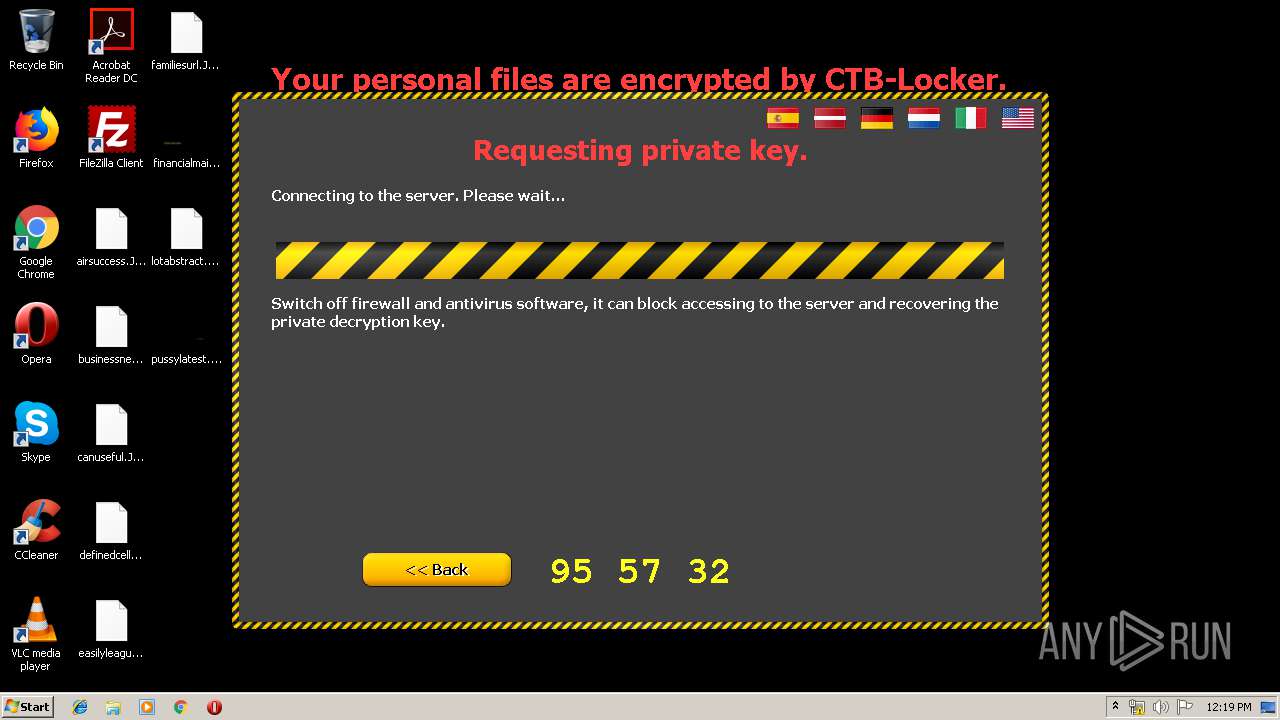
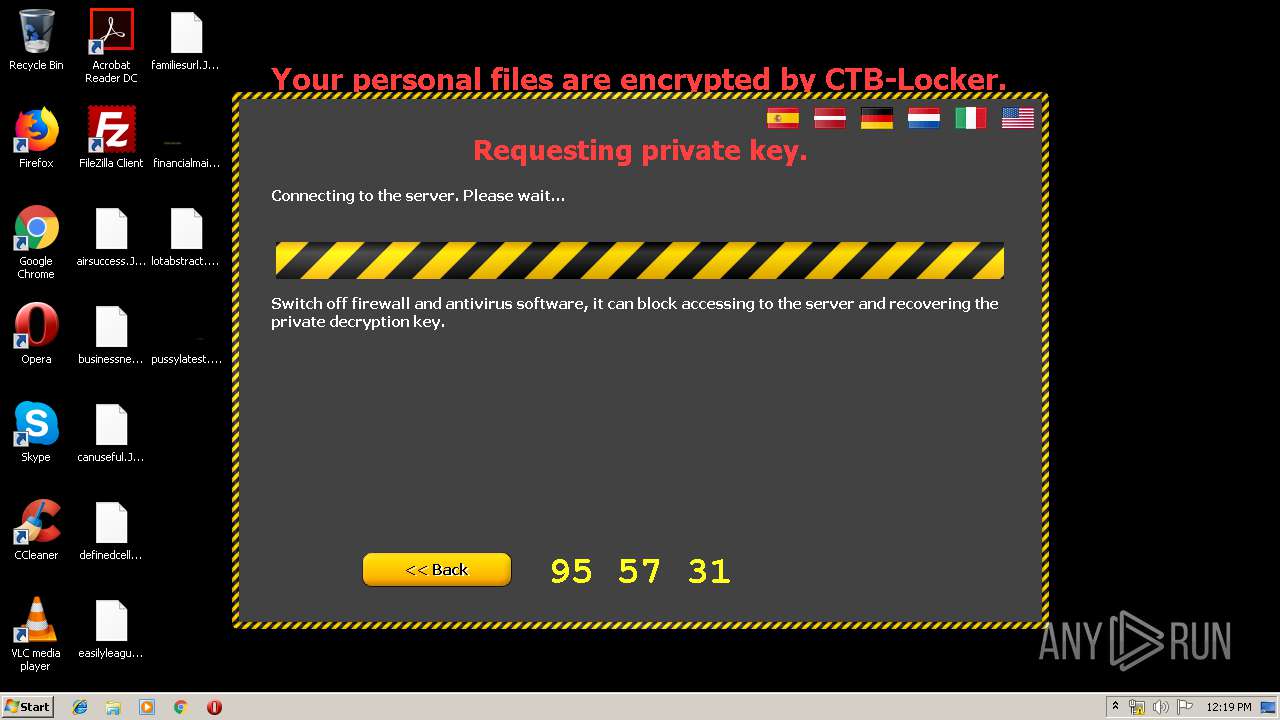
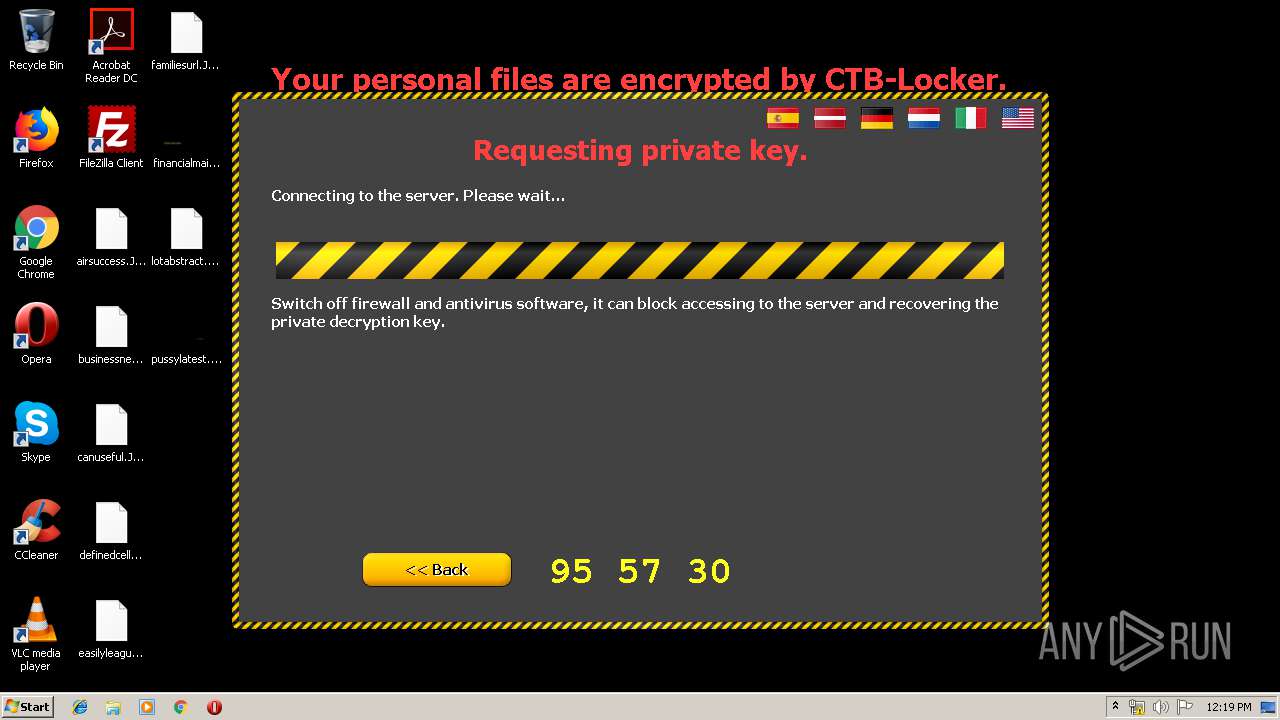
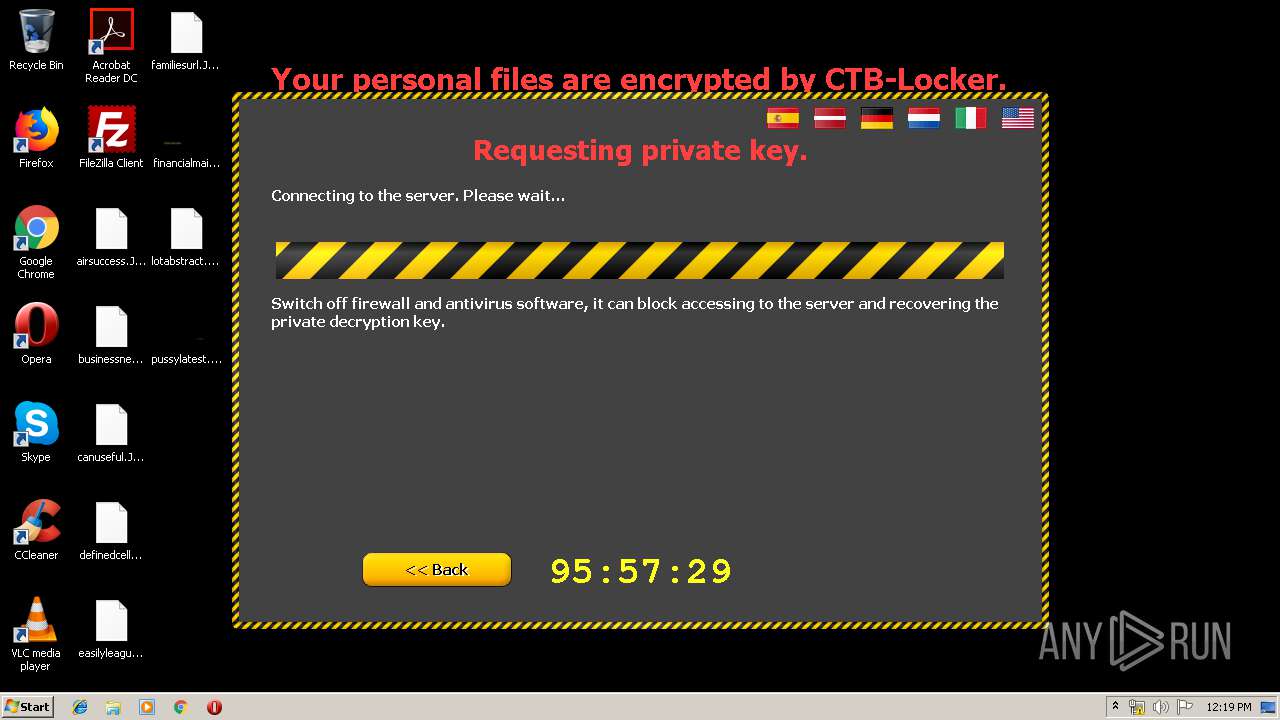
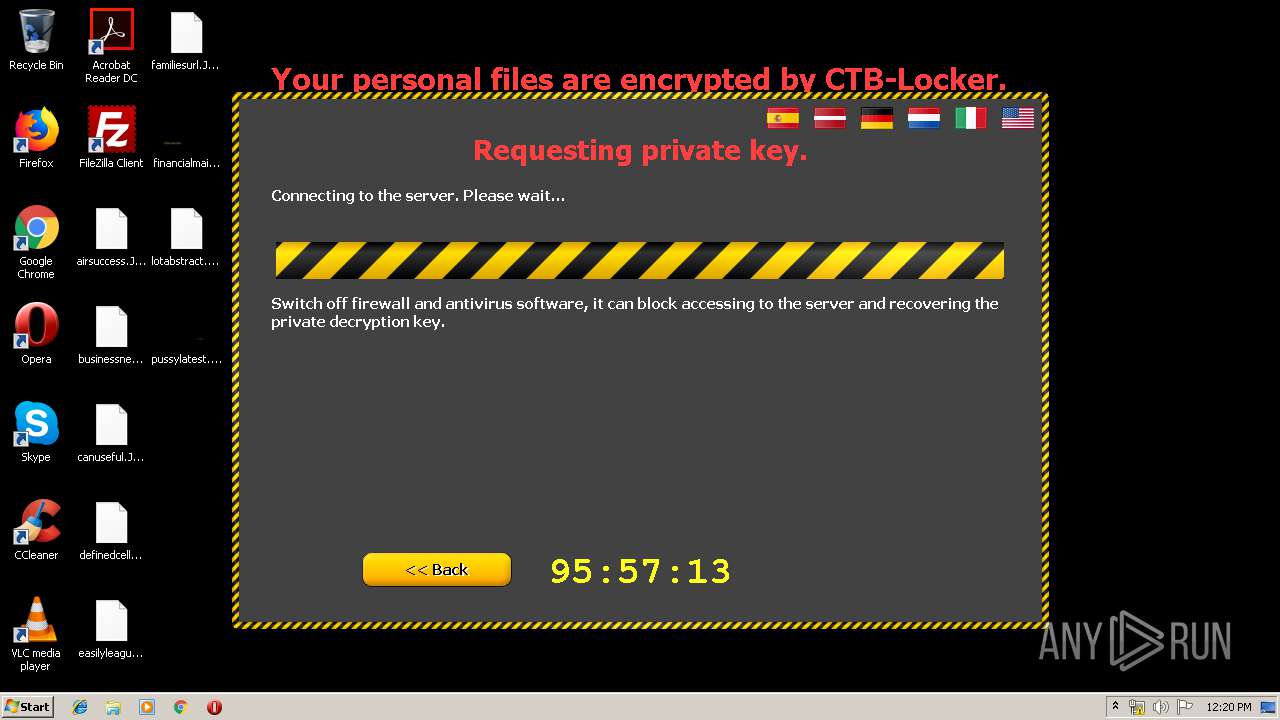
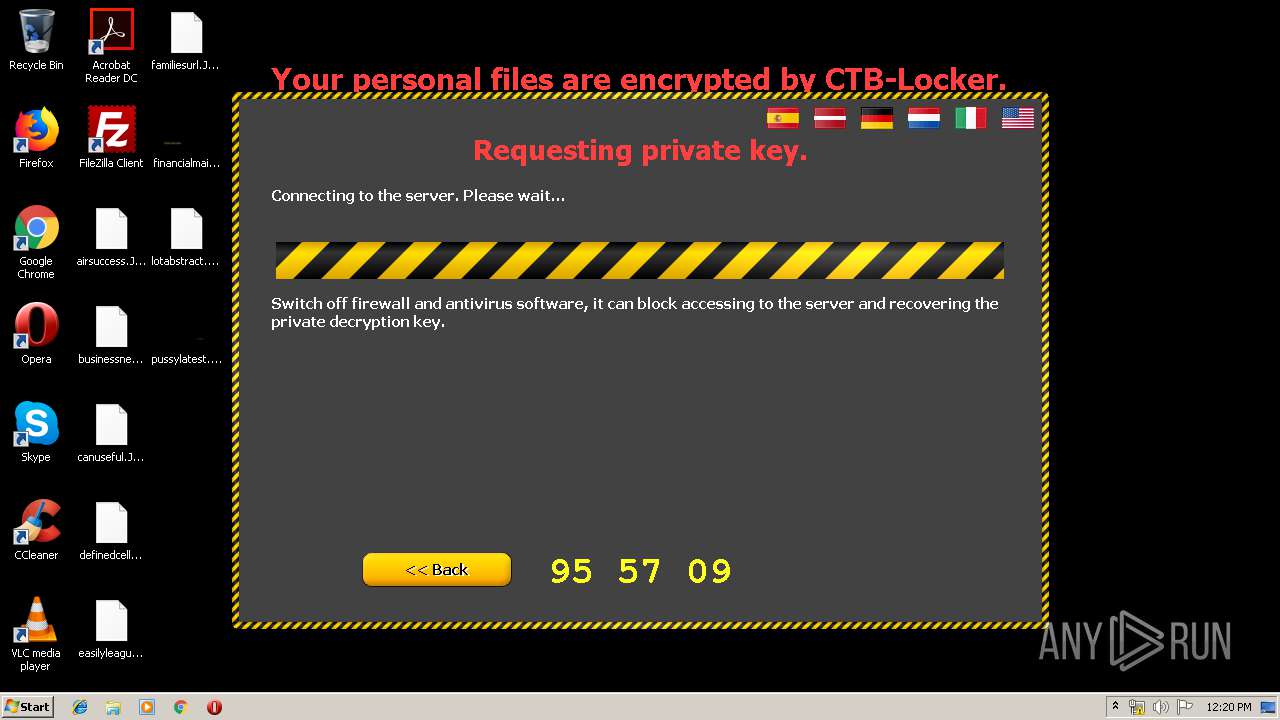
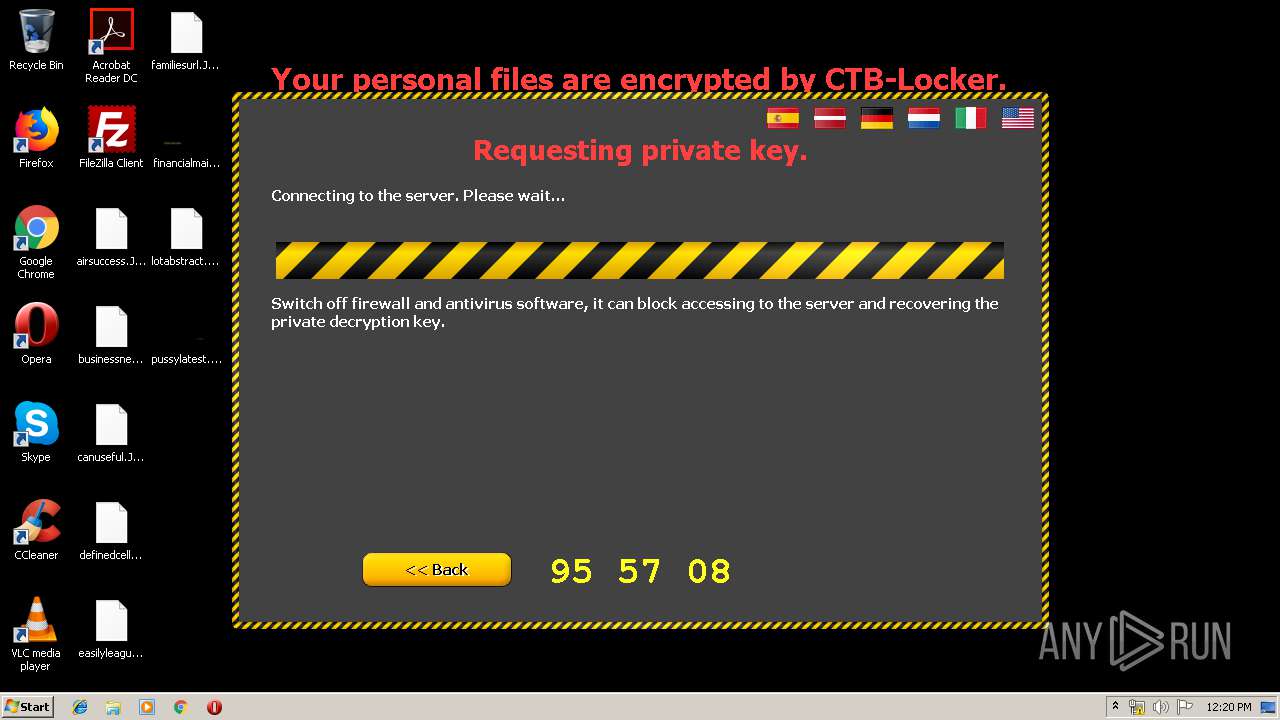
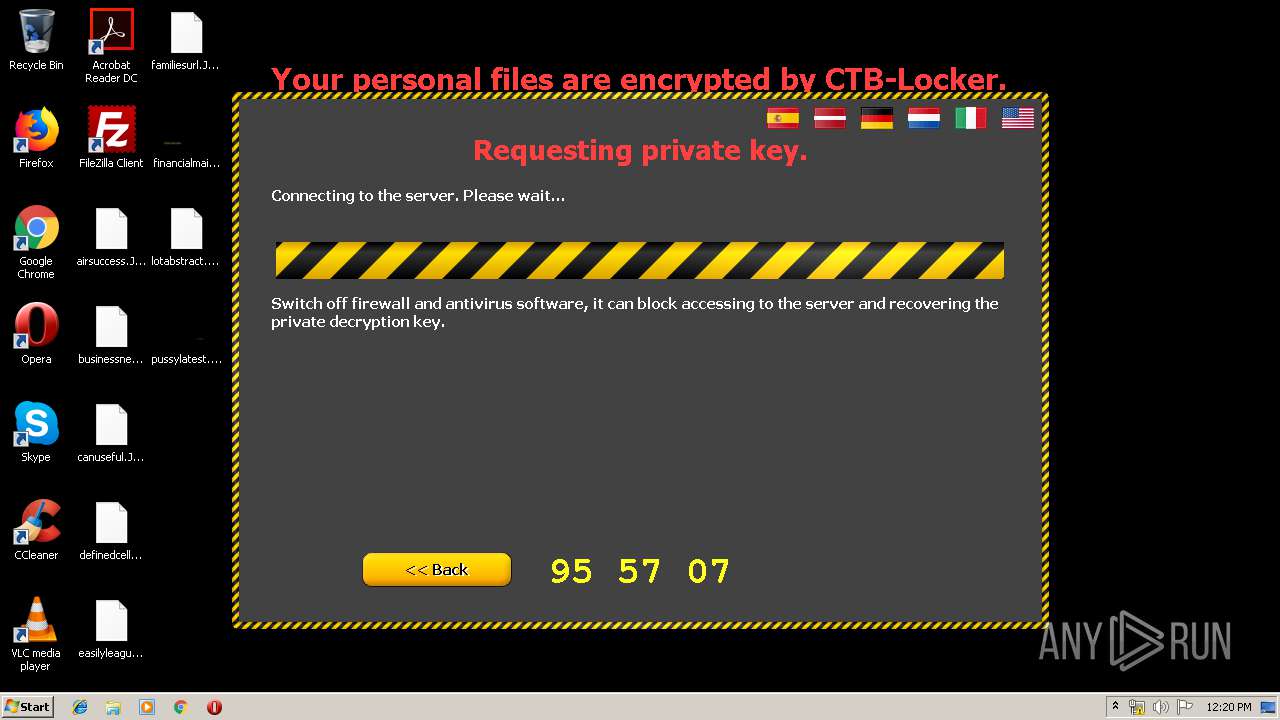
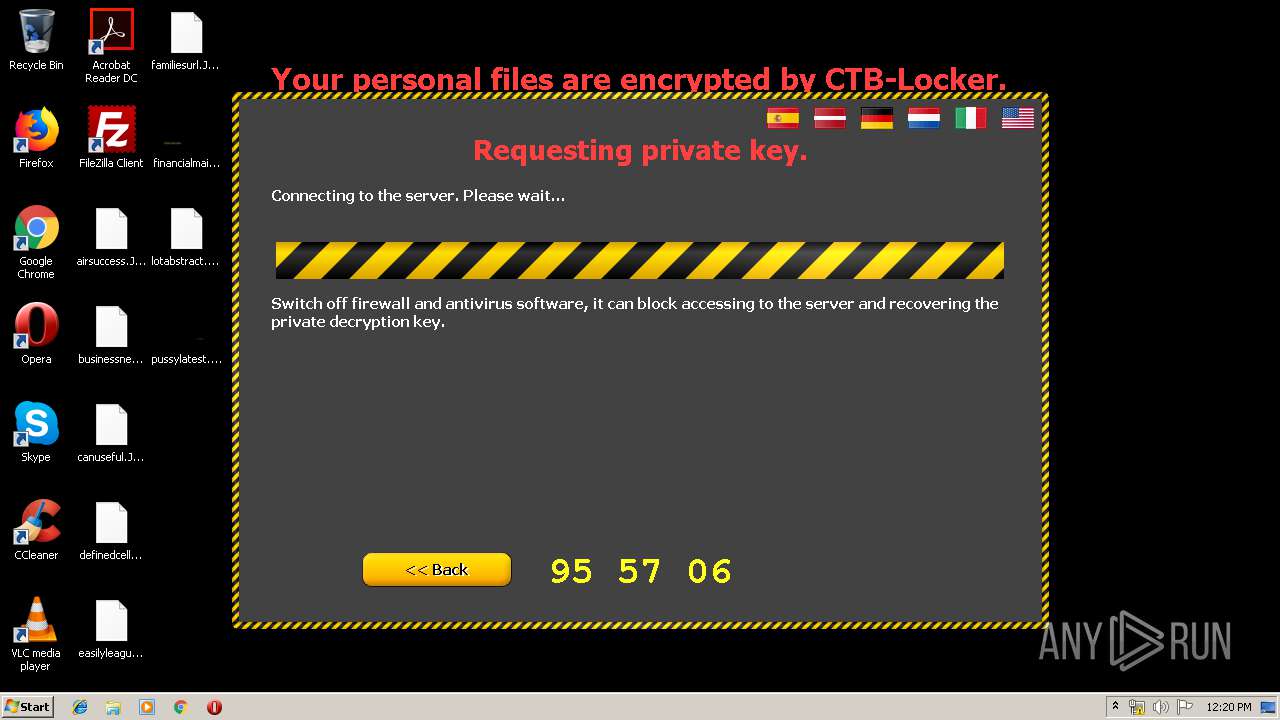
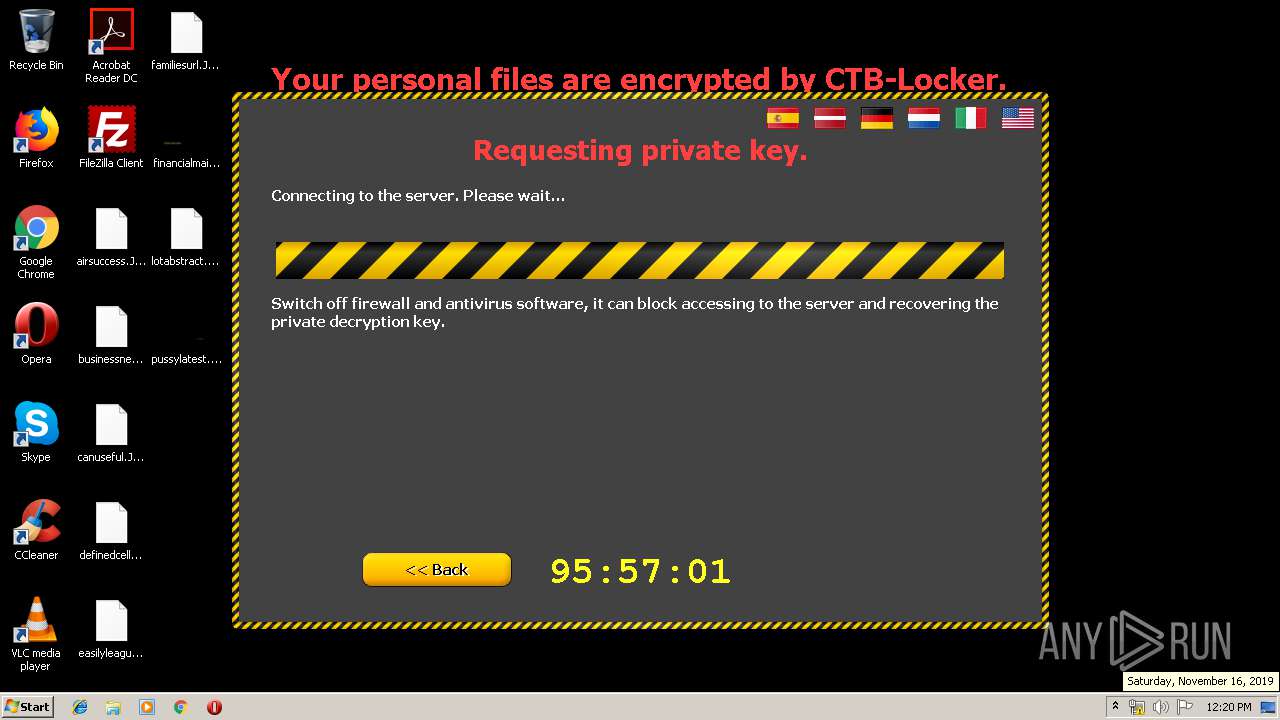
| Verdict: | Malicious activity |
| Threats: | Trojans are a group of malicious programs distinguished by their ability to masquerade as benign software. Depending on their type, trojans possess a variety of capabilities, ranging from maintaining full remote control over the victim’s machine to stealing data and files, as well as dropping other malware. At the same time, the main functionality of each trojan family can differ significantly depending on its type. The most common trojan infection chain starts with a phishing email. |
| Analysis date: | November 16, 2019, 12:16:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 521BD488A5DE44D84E9D145D3EB8A238 |
| SHA1: | A9086094BA2EAA8DC6FF046788CCD441136AD692 |
| SHA256: | 8A128F5122D32A4D6780644A13D3AC81CD85895CA025C5FB6E8BB12E94AA5F94 |
| SSDEEP: | 12288:Eq24RXH8L52vF+k9/WUqWb+6GqOwGhPcb/ruGe/2DUrkVH1:WmX8L5xk9+f6GqpGRcPuGQmPVH |
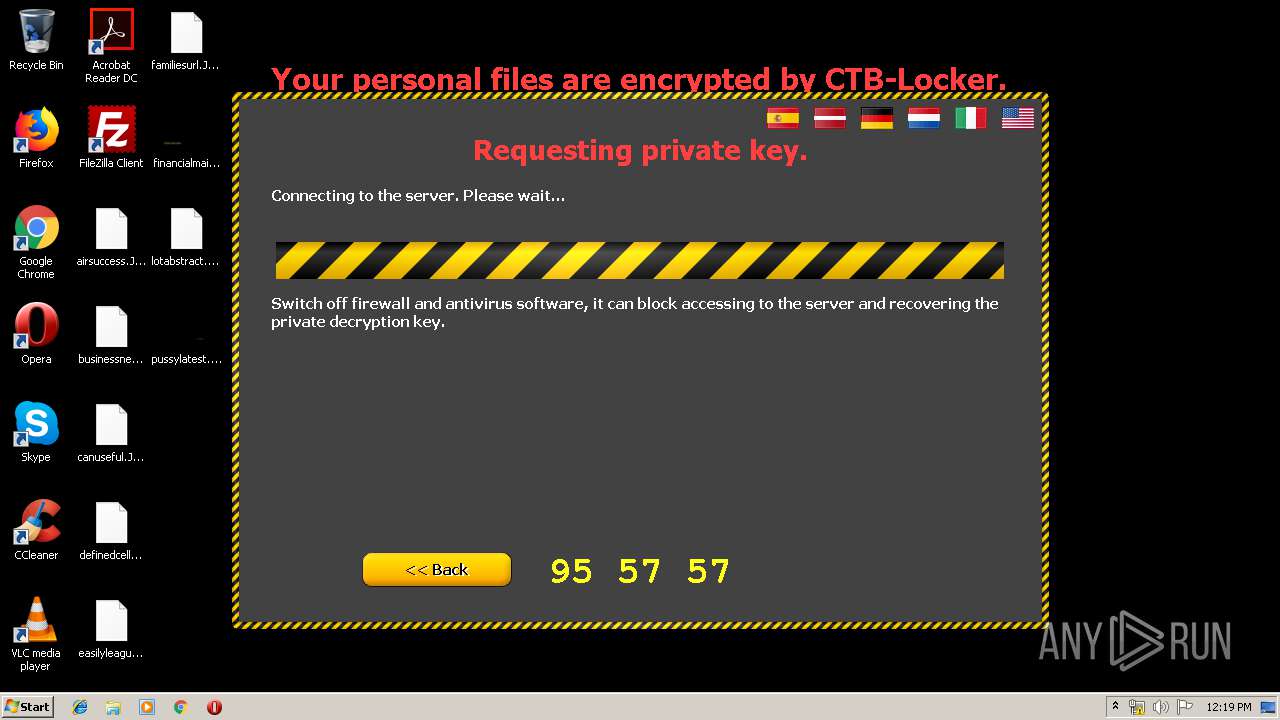
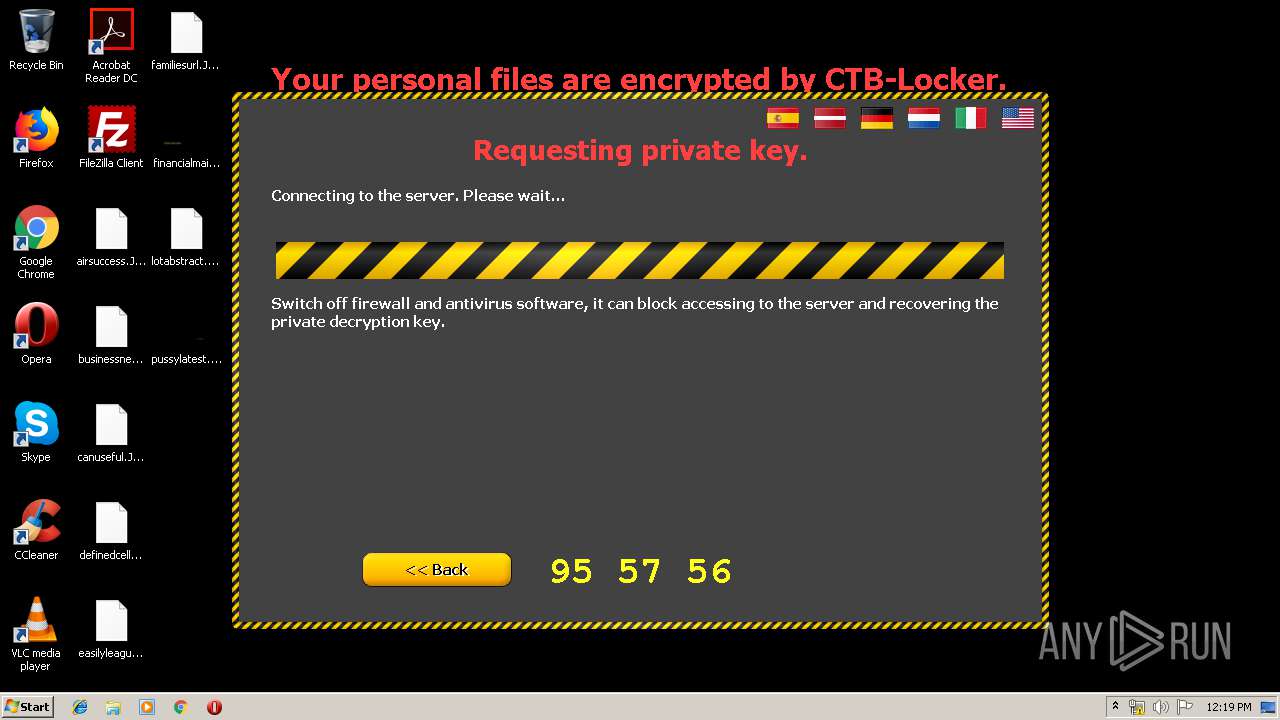
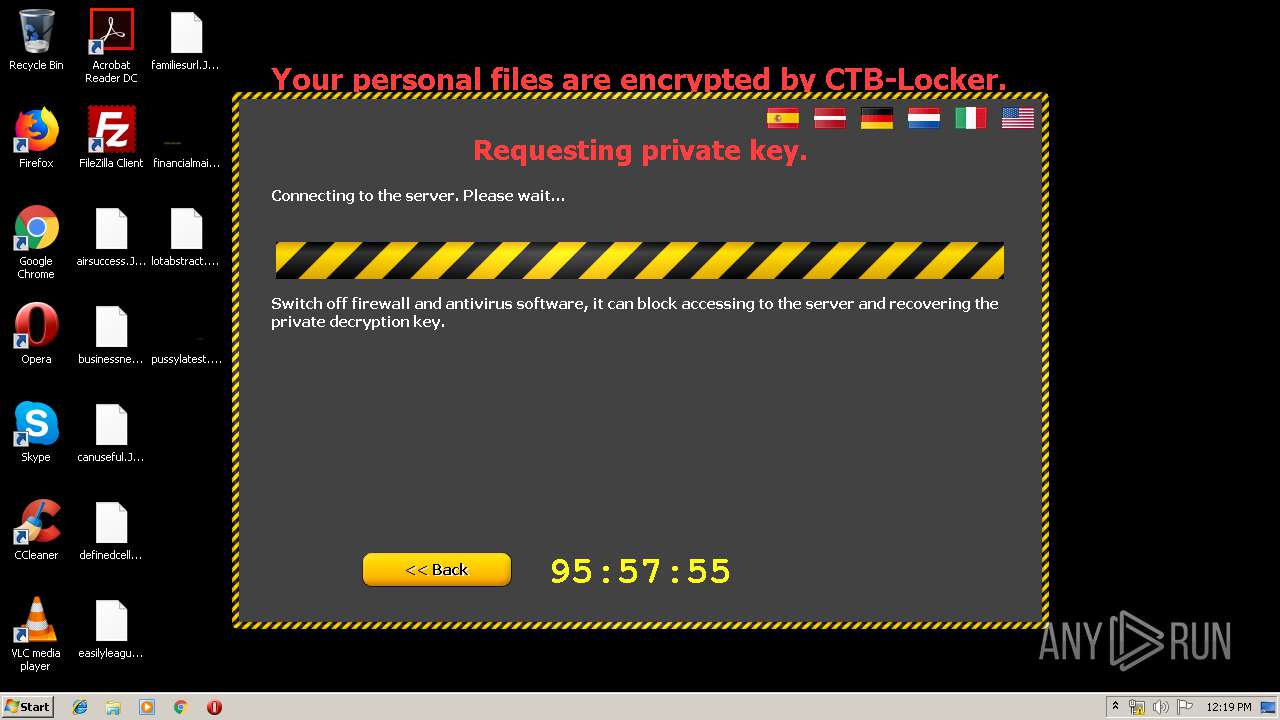
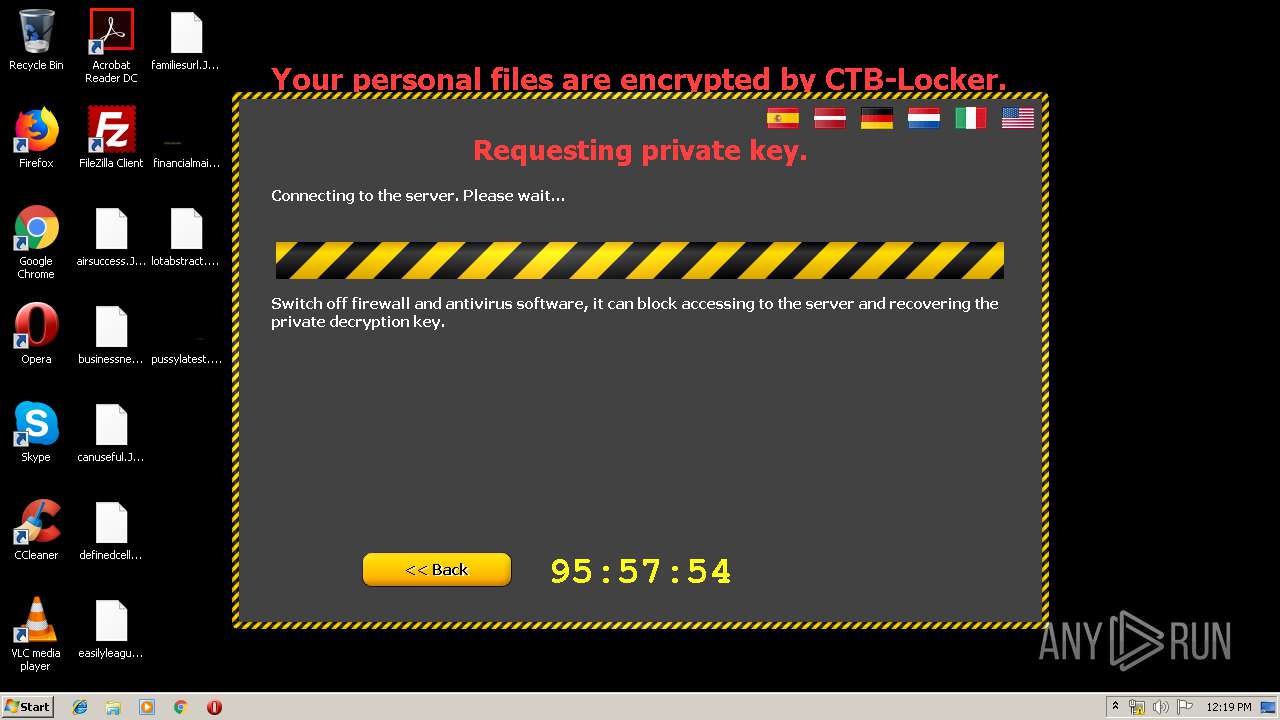
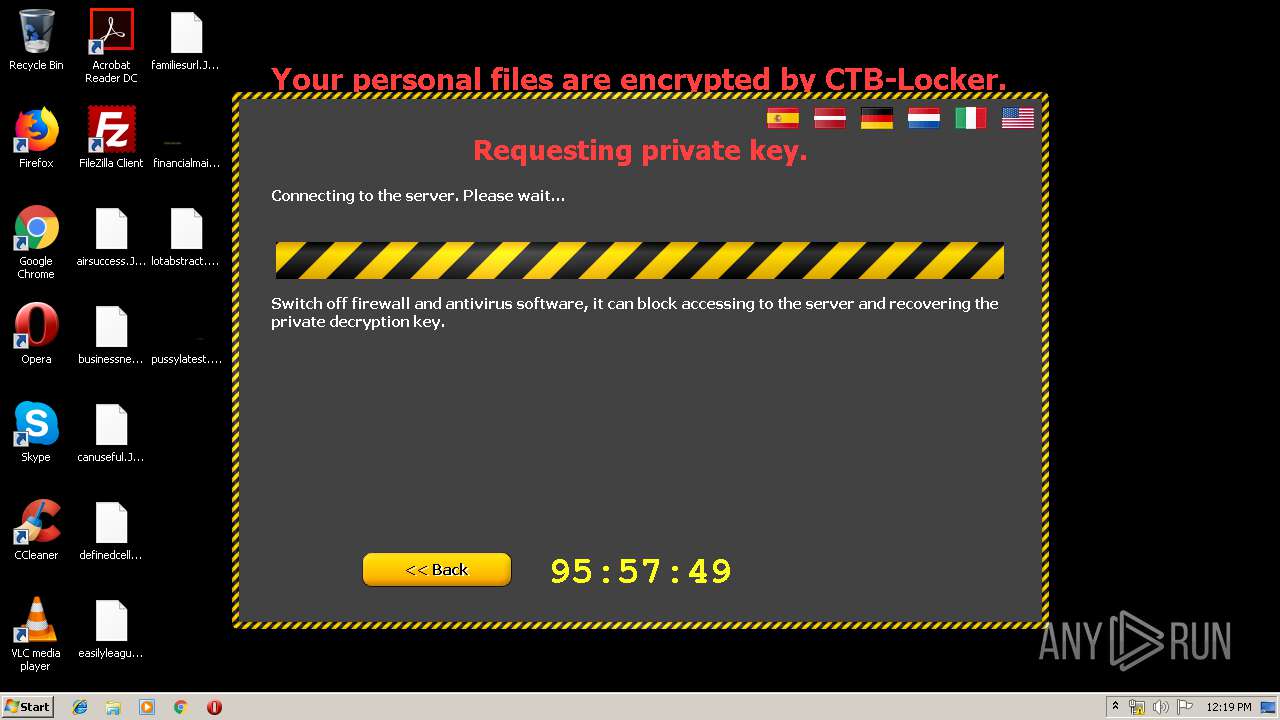
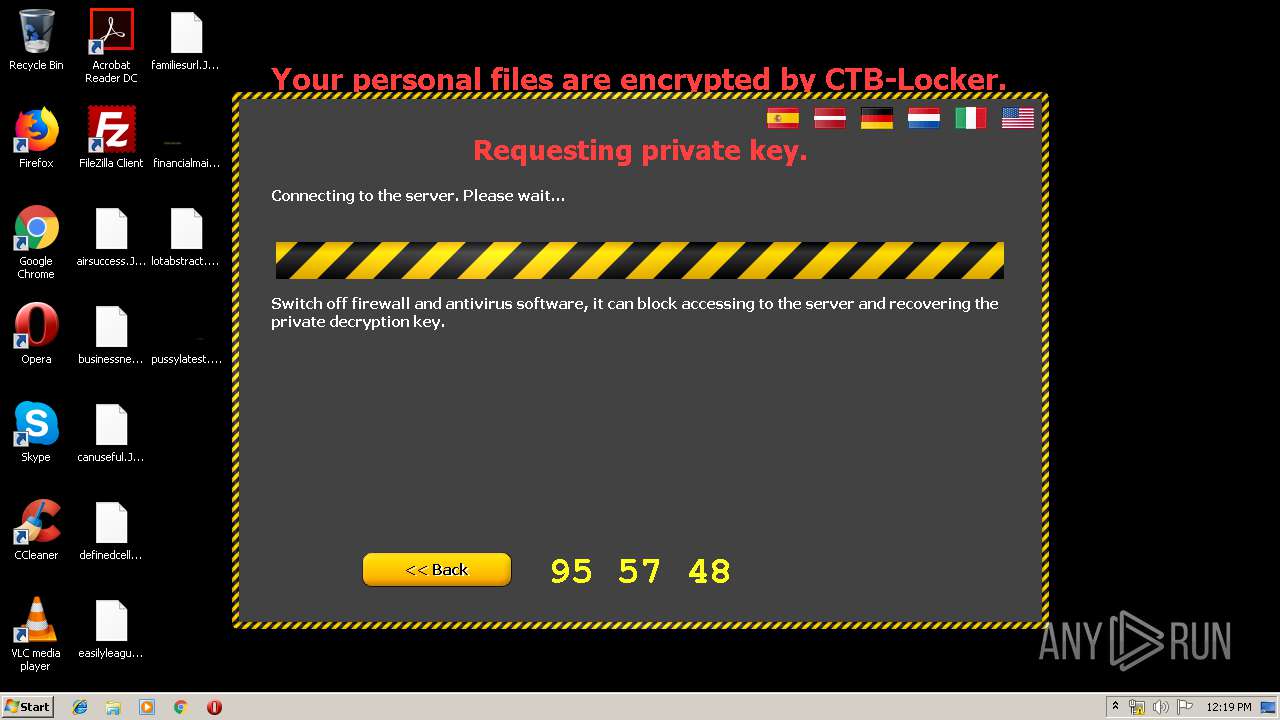
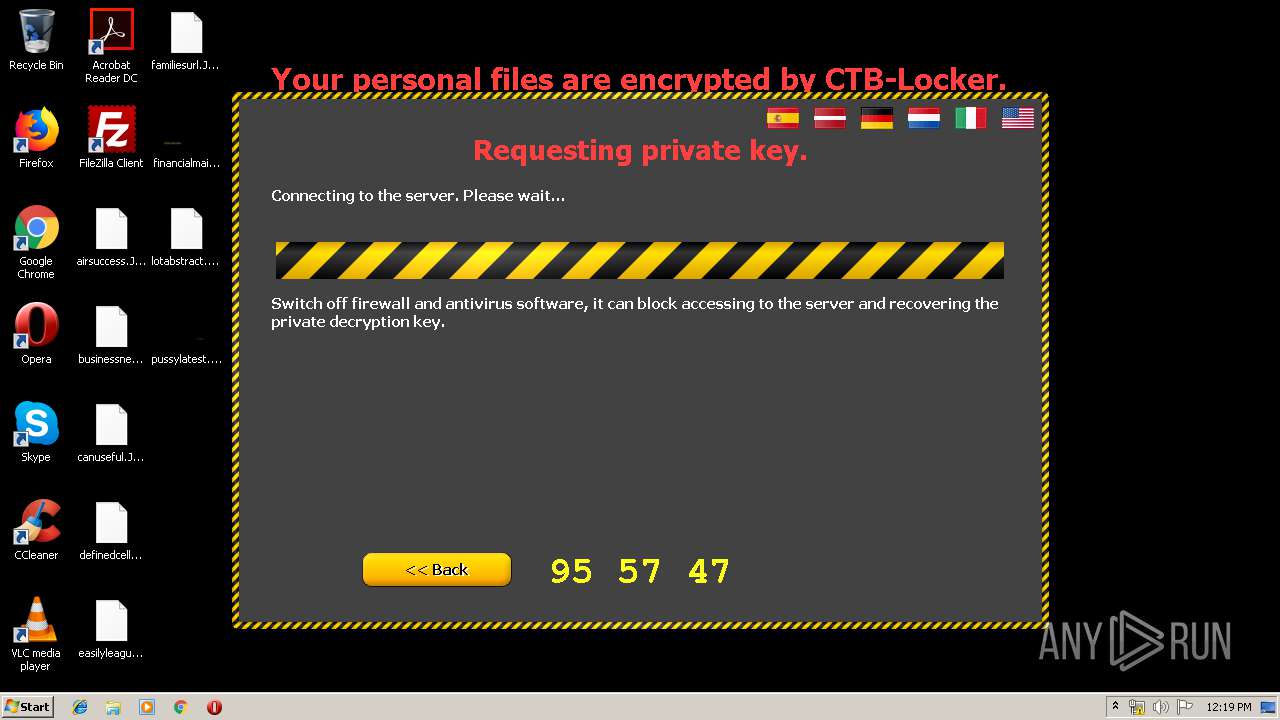
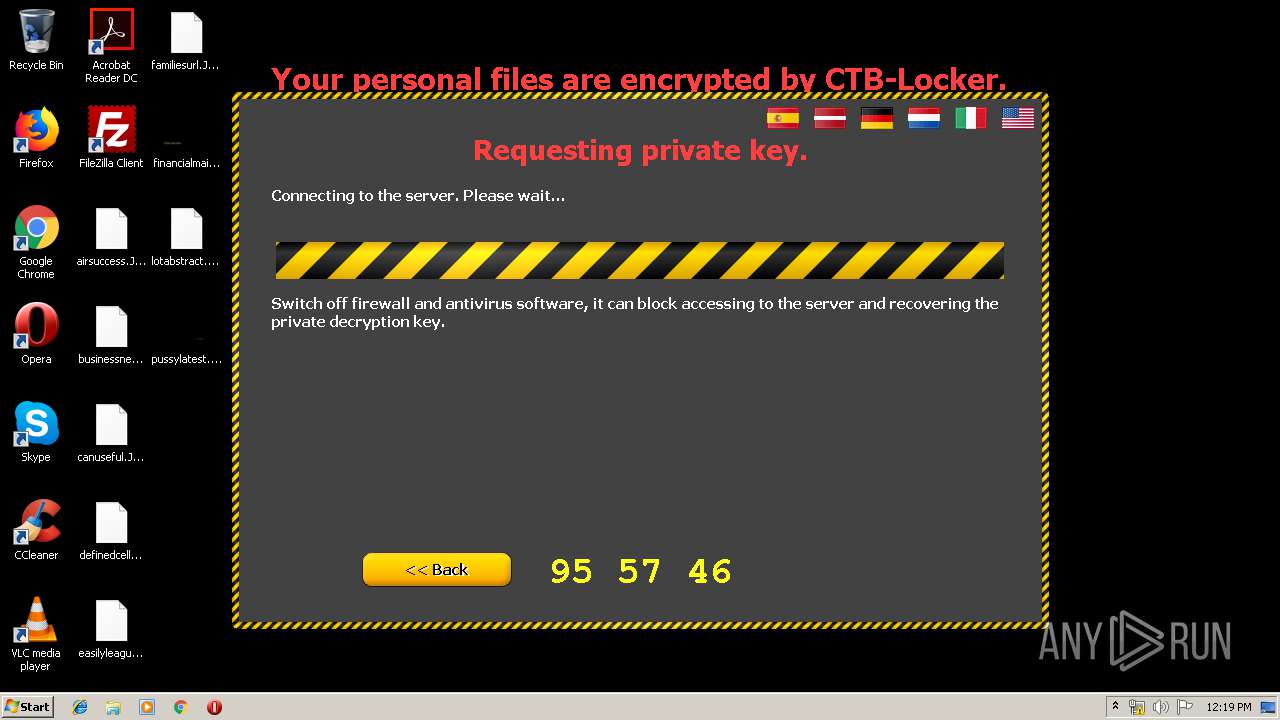
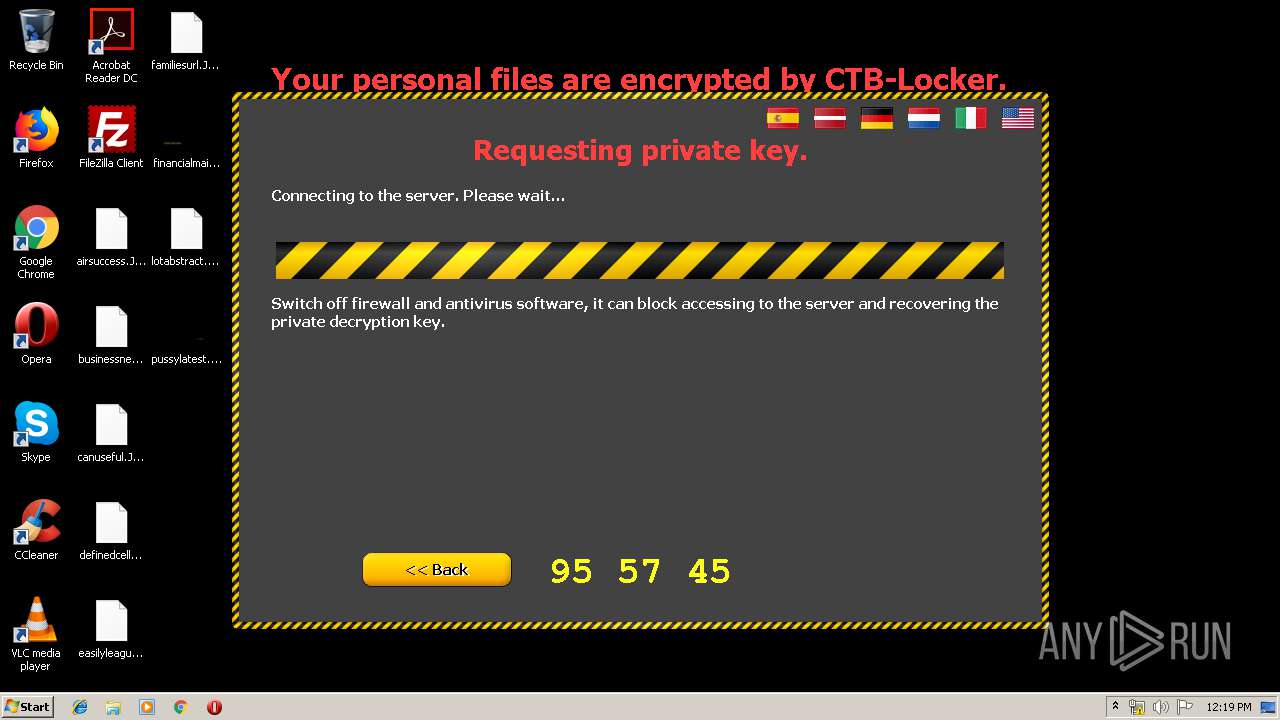
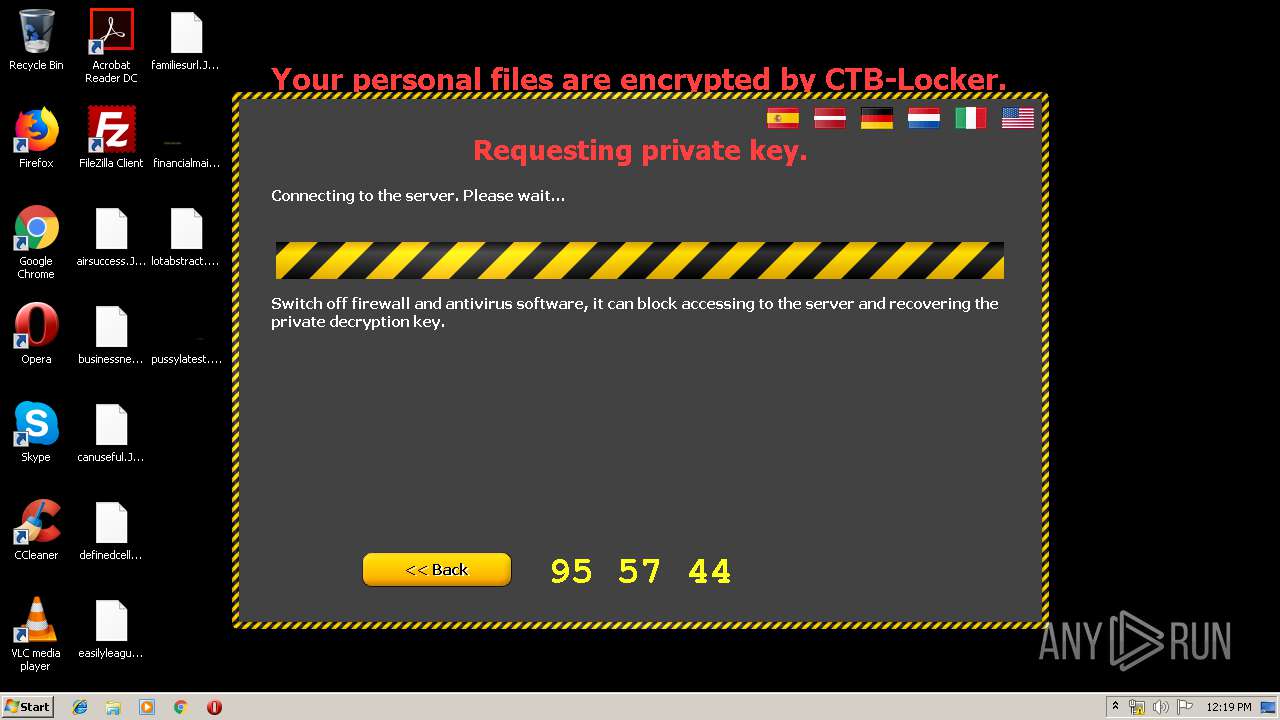
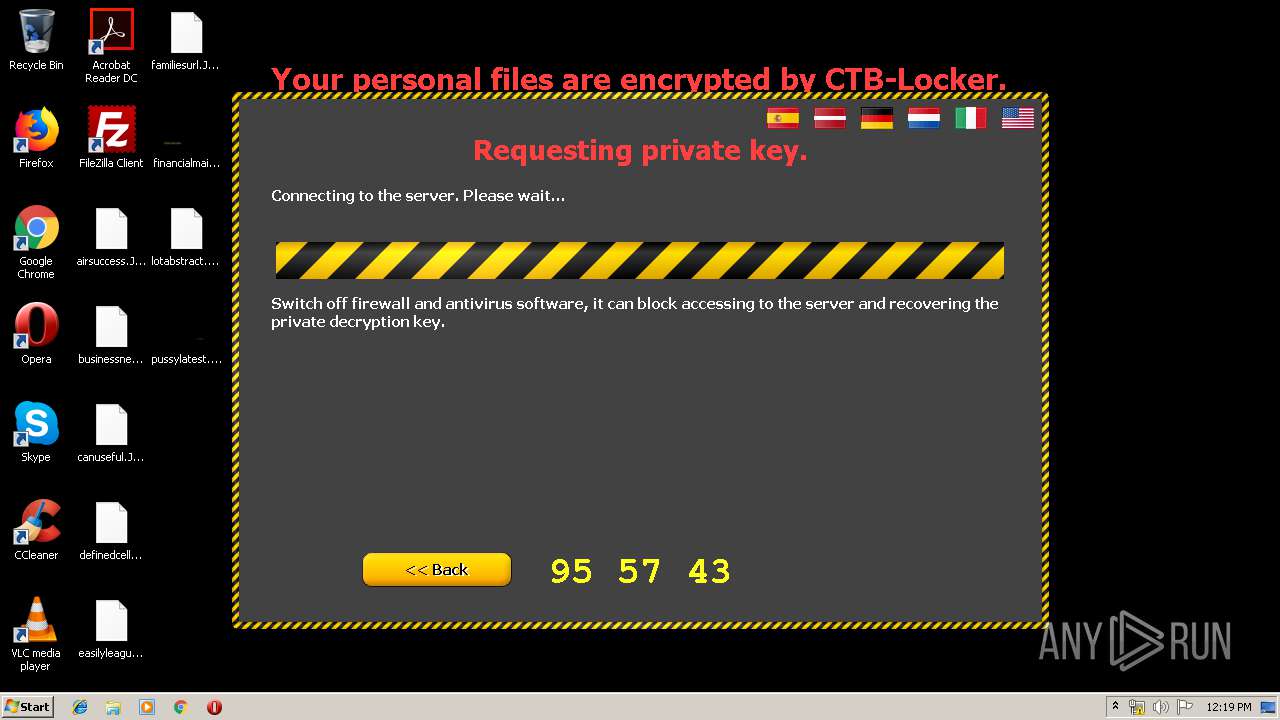
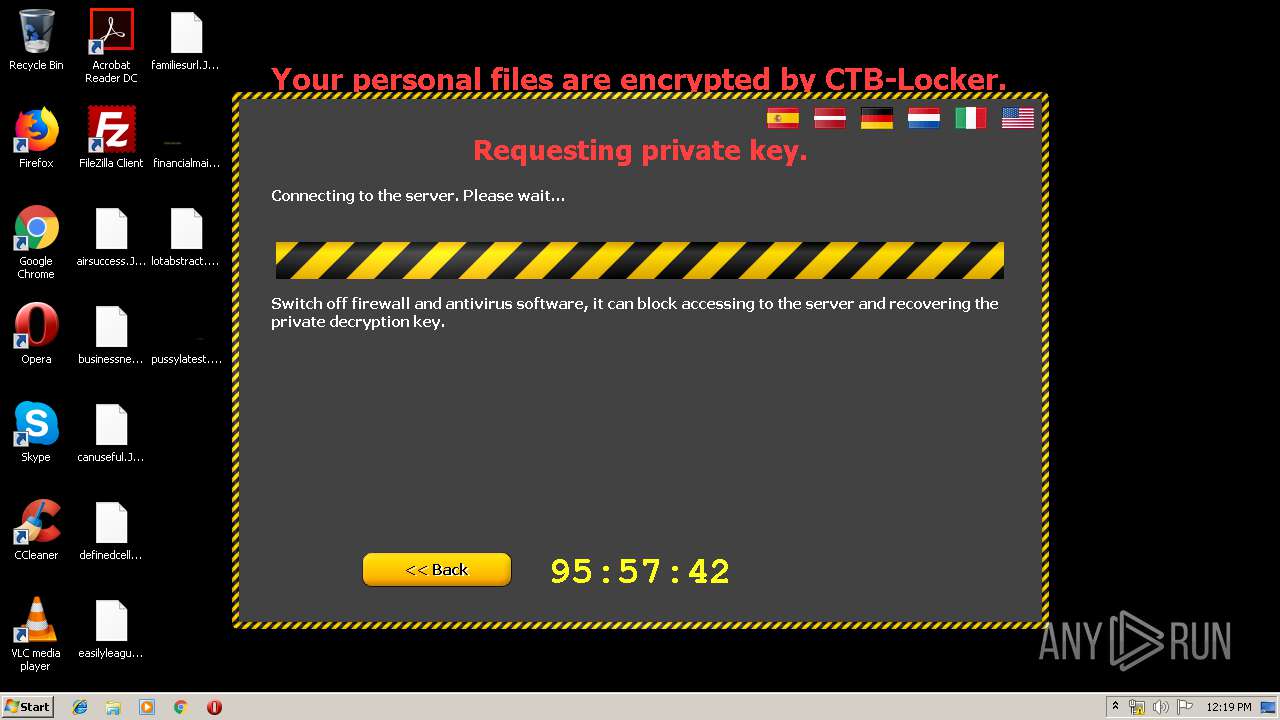
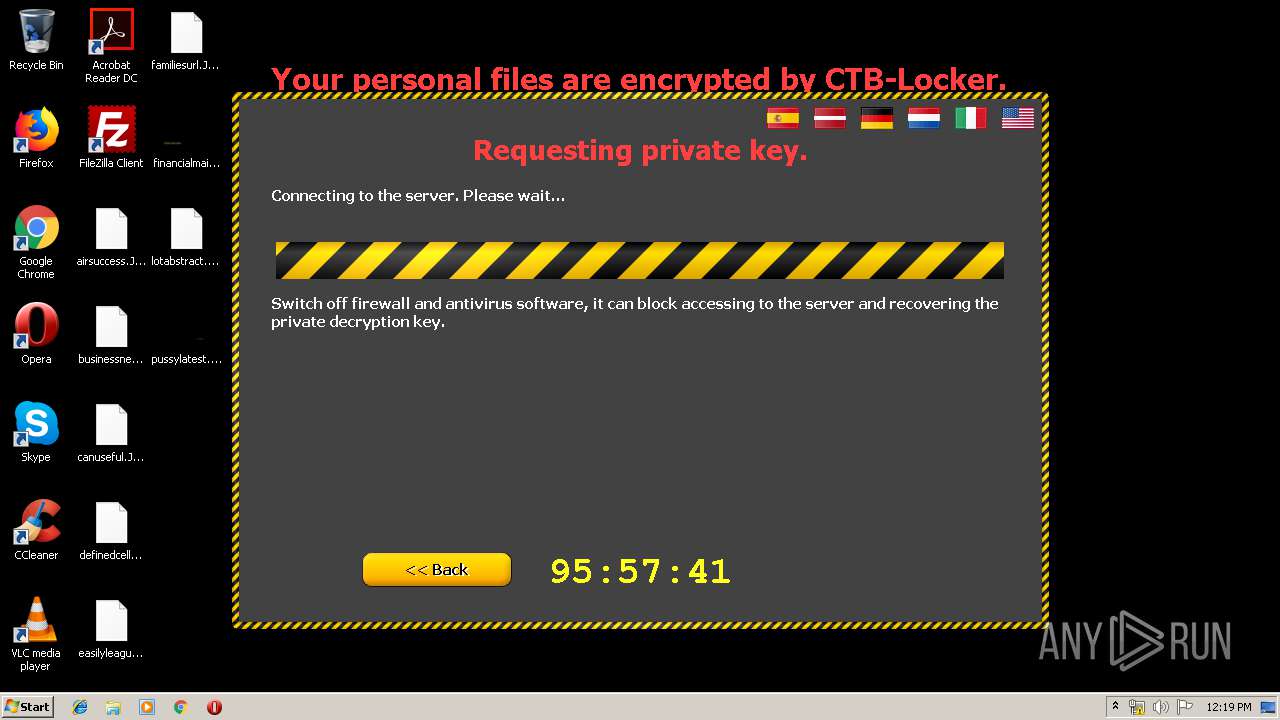
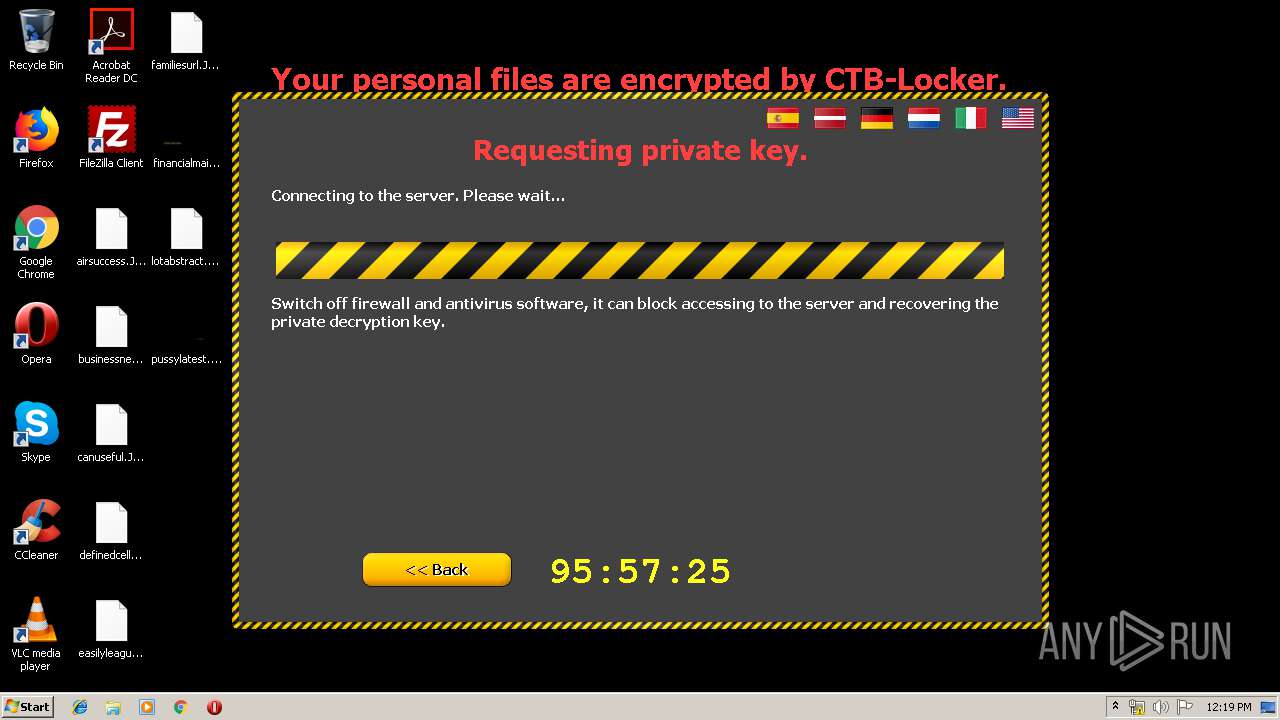
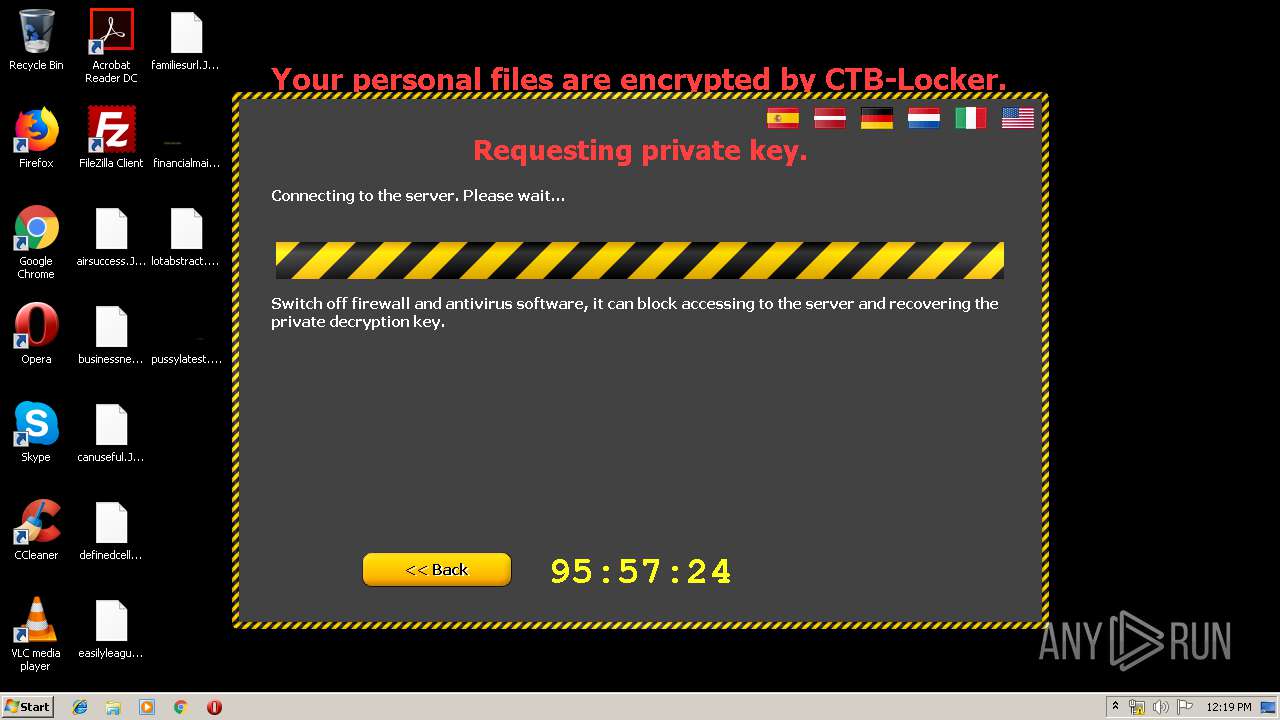
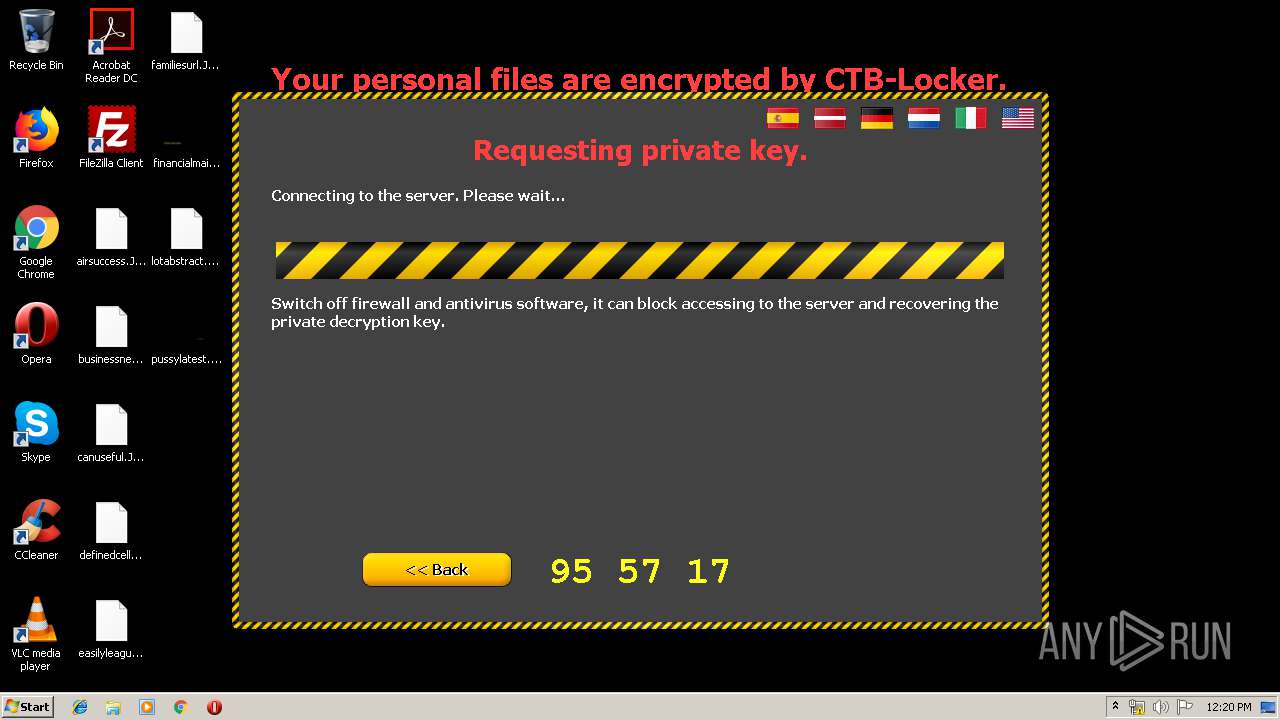
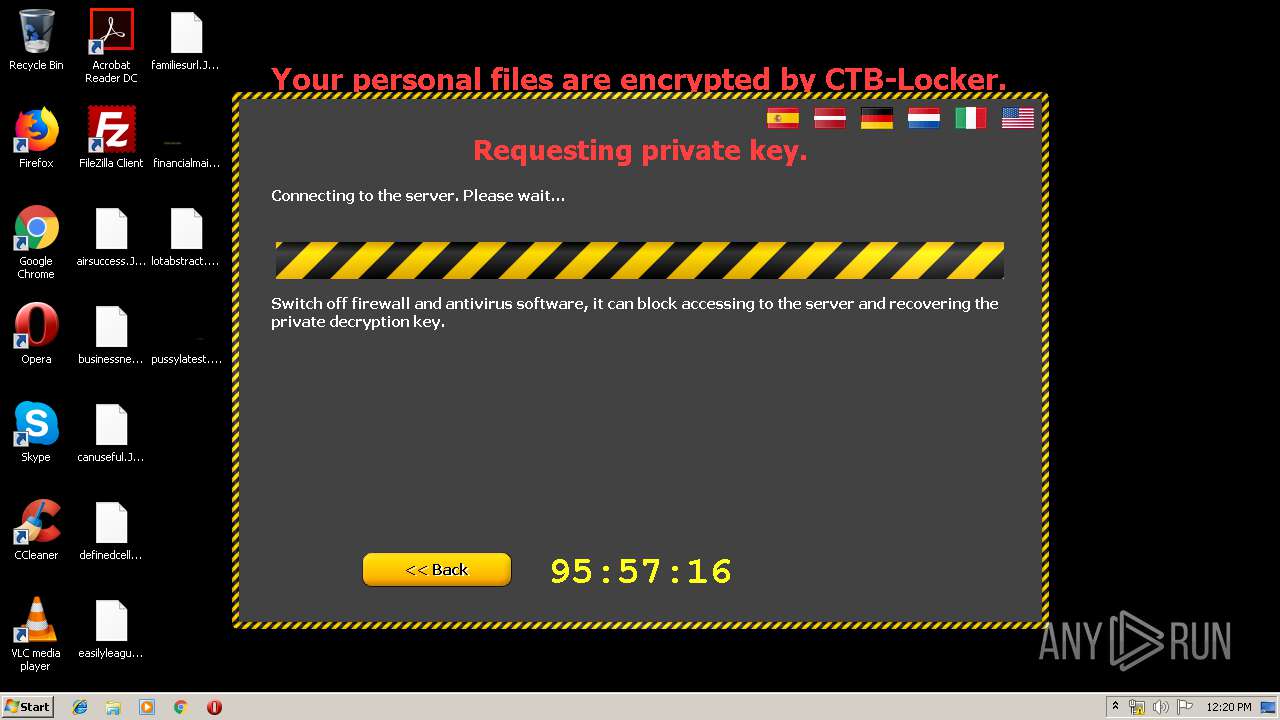
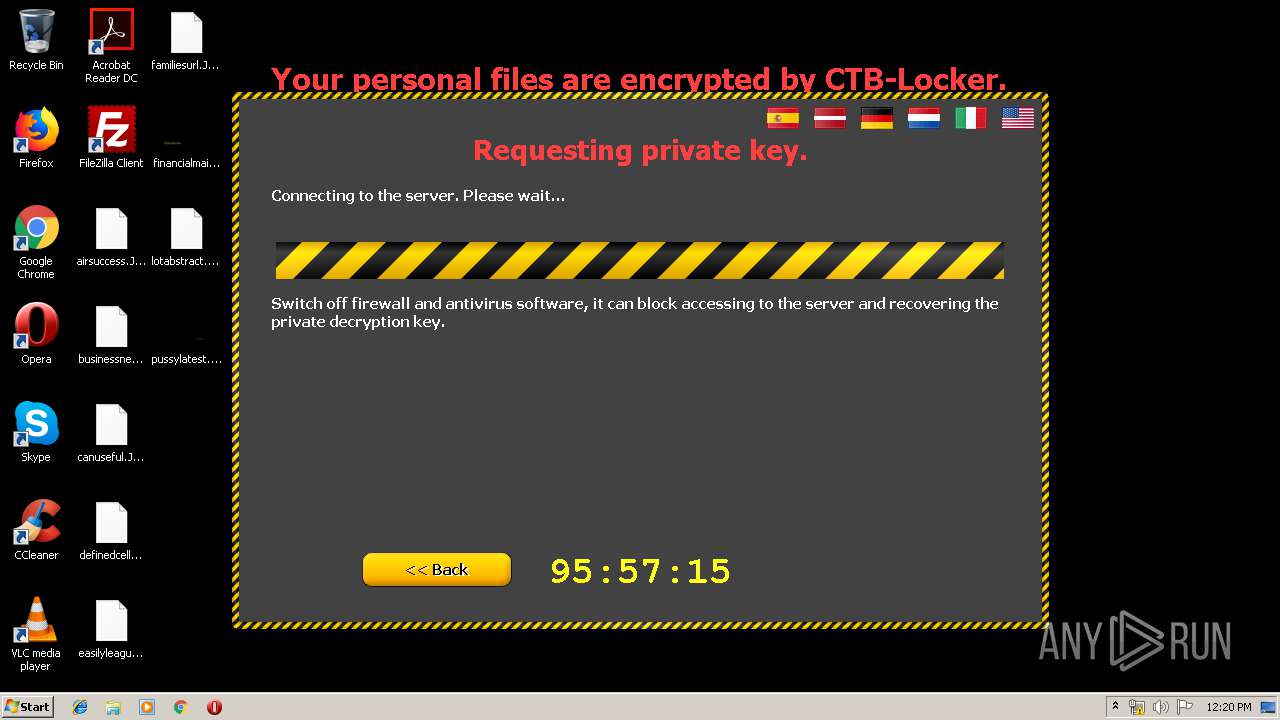
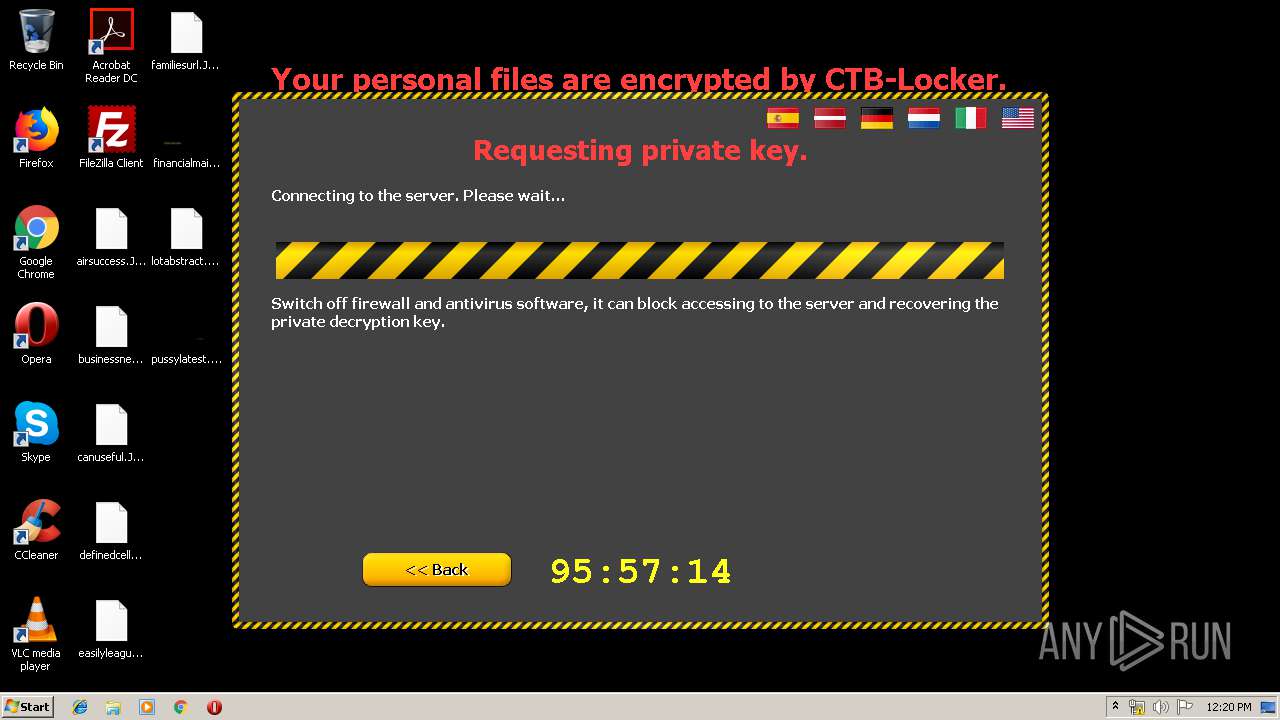
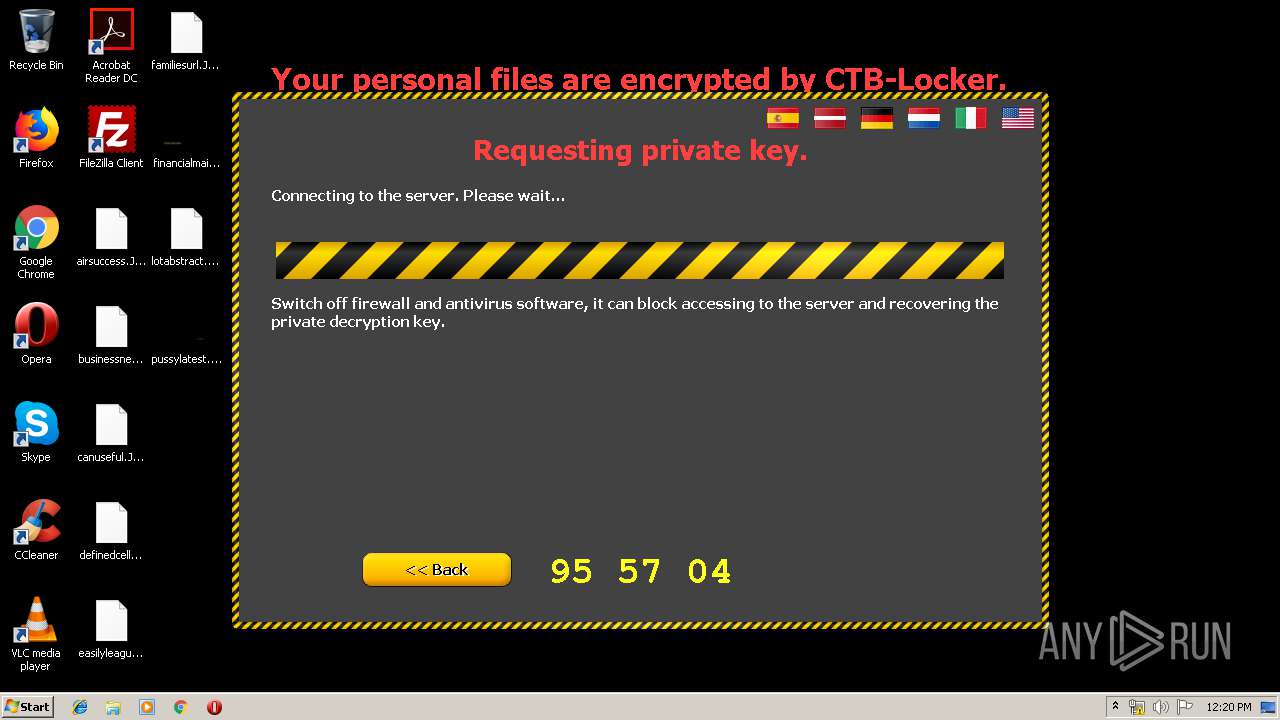
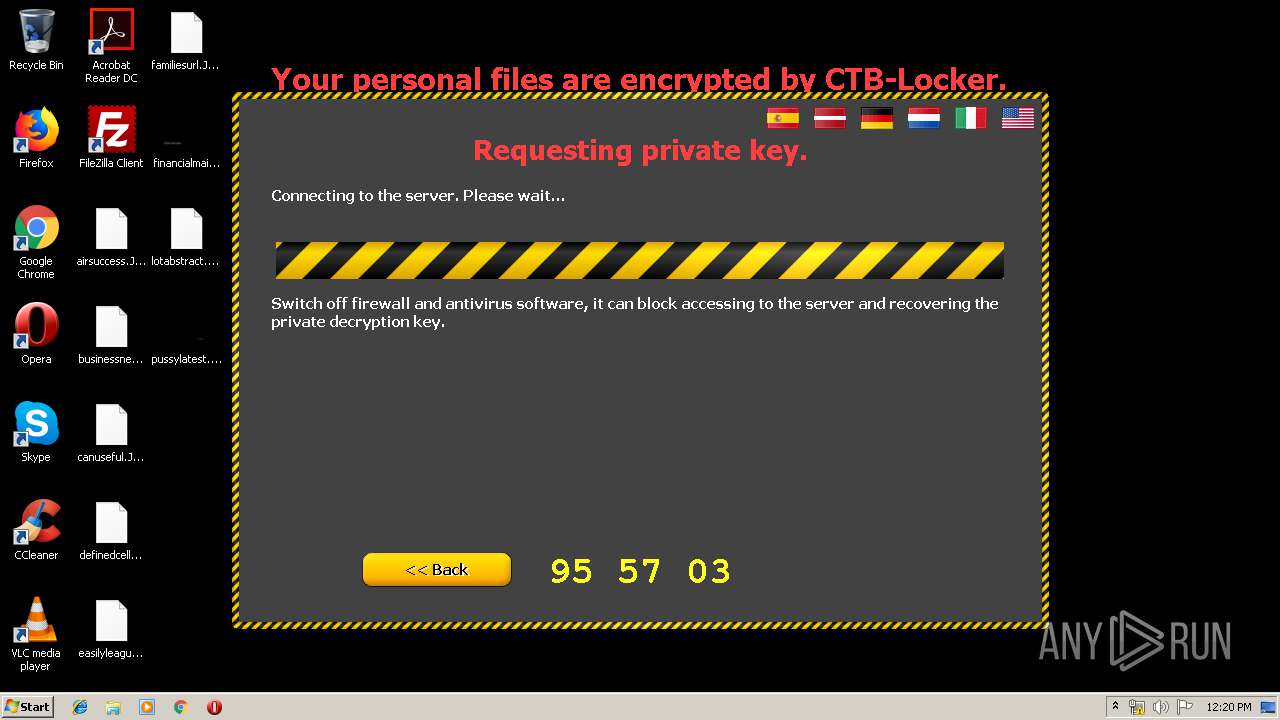
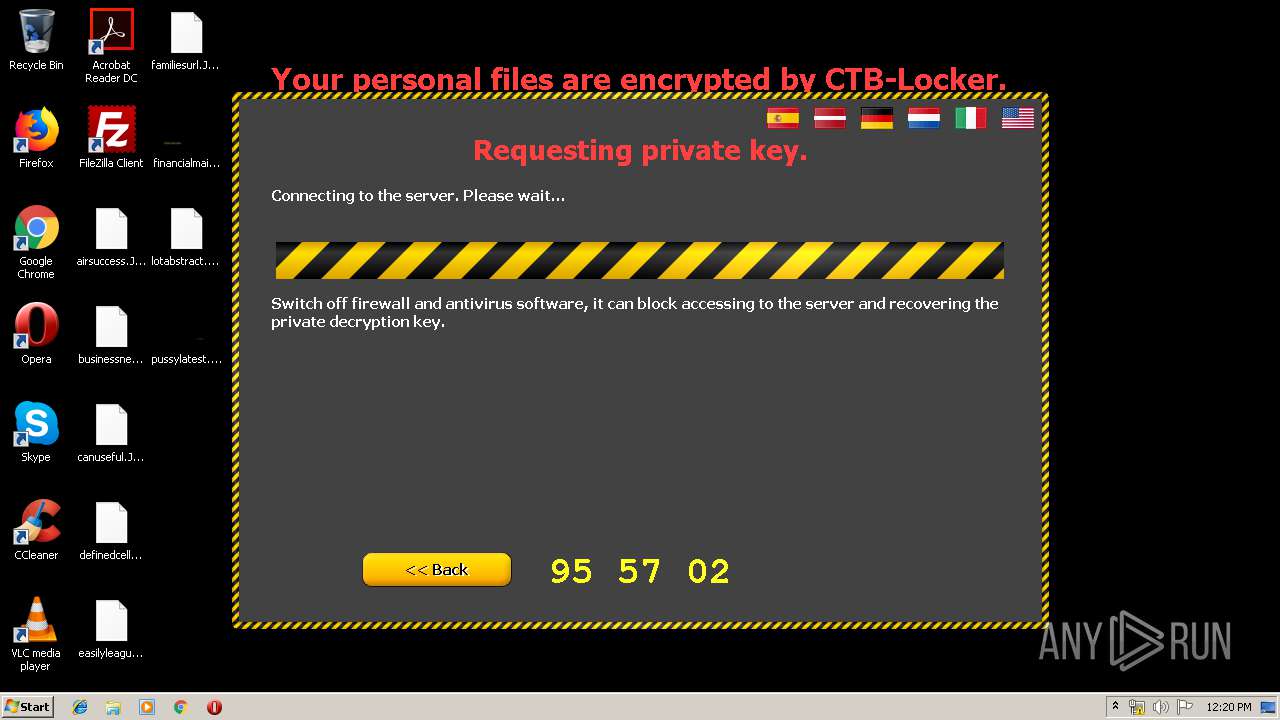
MALICIOUS
Loads the Task Scheduler COM API
- MrT.exe (PID: 2580)
Application was injected by another process
- explorer.exe (PID: 352)
Runs injected code in another process
- ourkble.exe (PID: 1244)
SUSPICIOUS
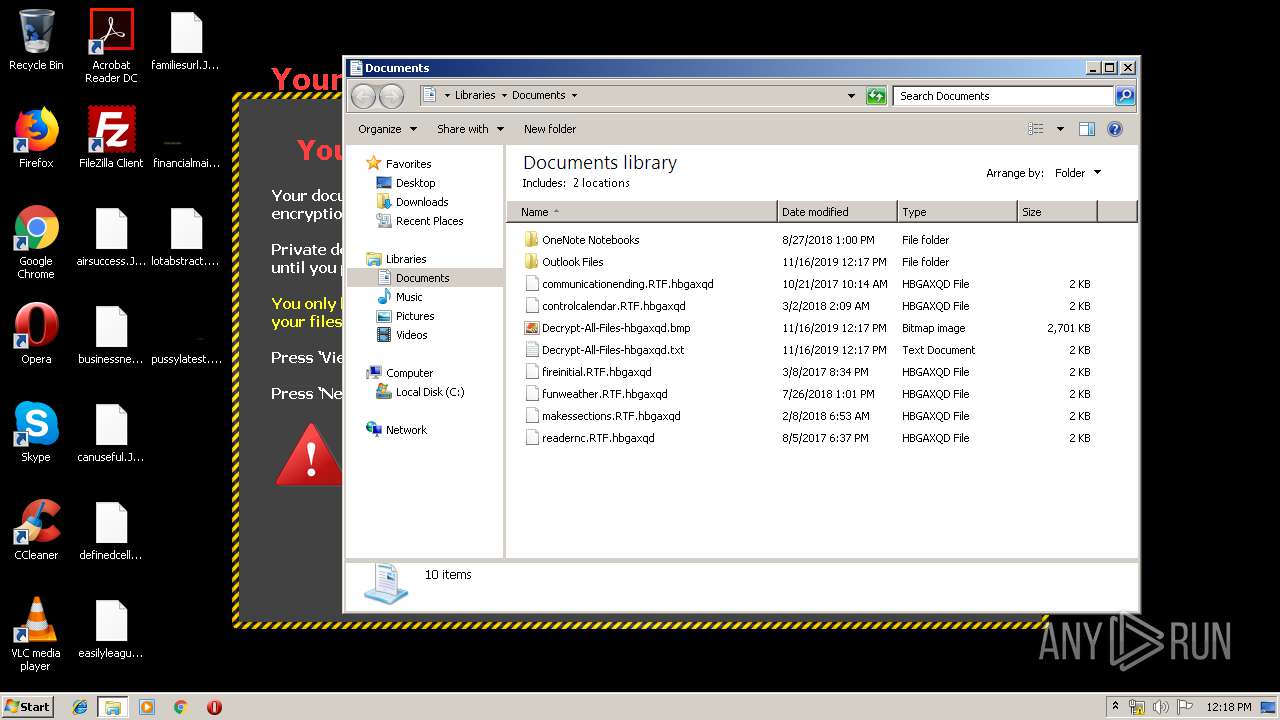
Executable content was dropped or overwritten
- MrT.exe (PID: 2580)
Executed via Task Scheduler
- ourkble.exe (PID: 1244)
Creates files in the program directory
- ourkble.exe (PID: 1244)
Reads internet explorer settings
- ourkble.exe (PID: 1244)
Reads Internet Cache Settings
- explorer.exe (PID: 352)
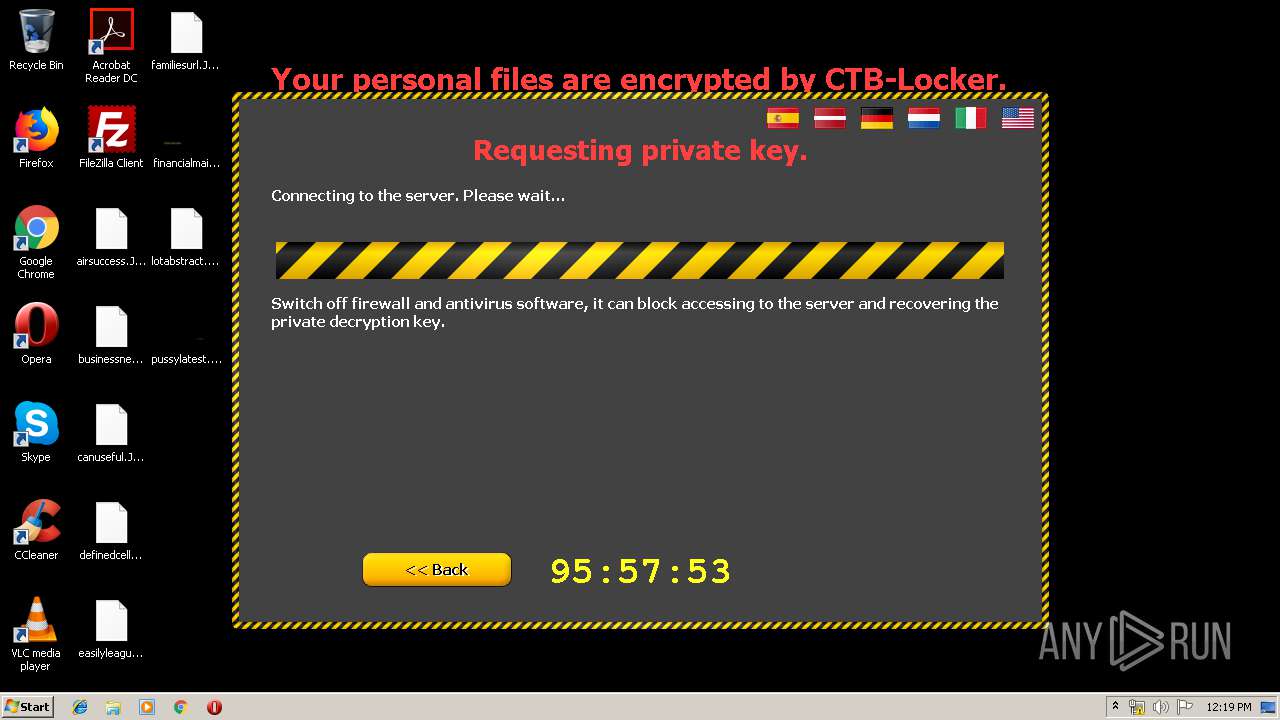
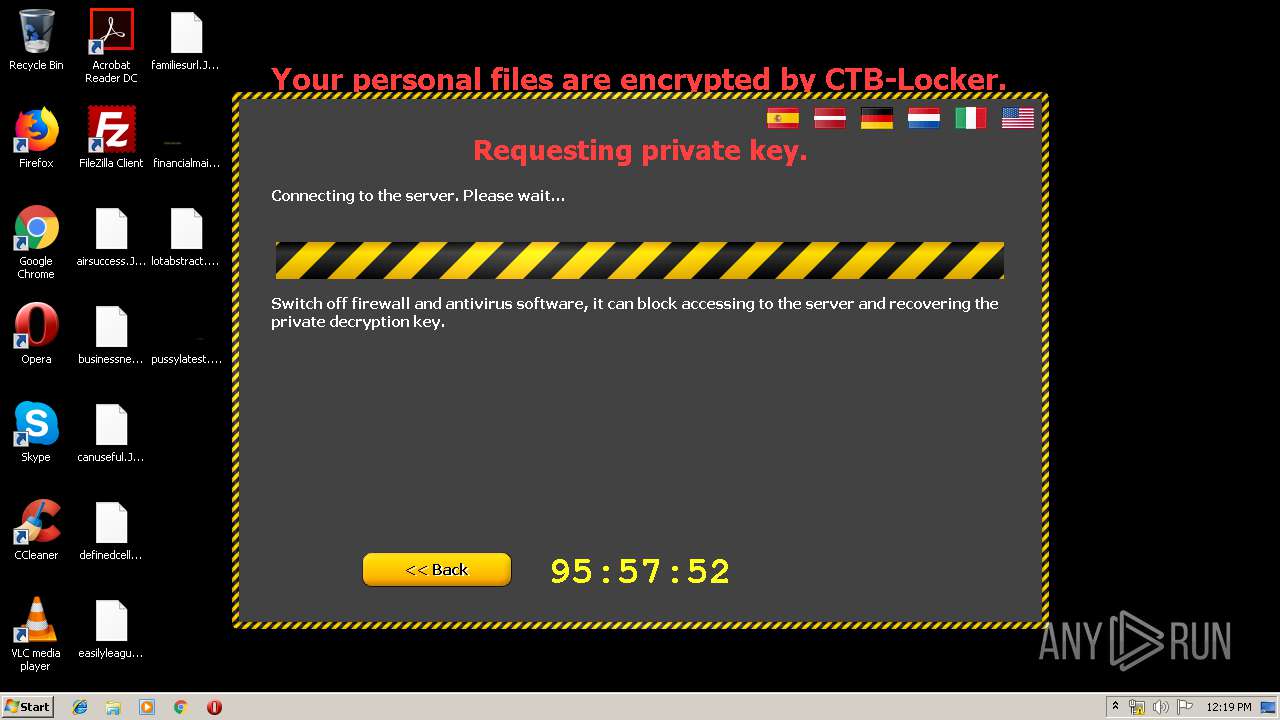
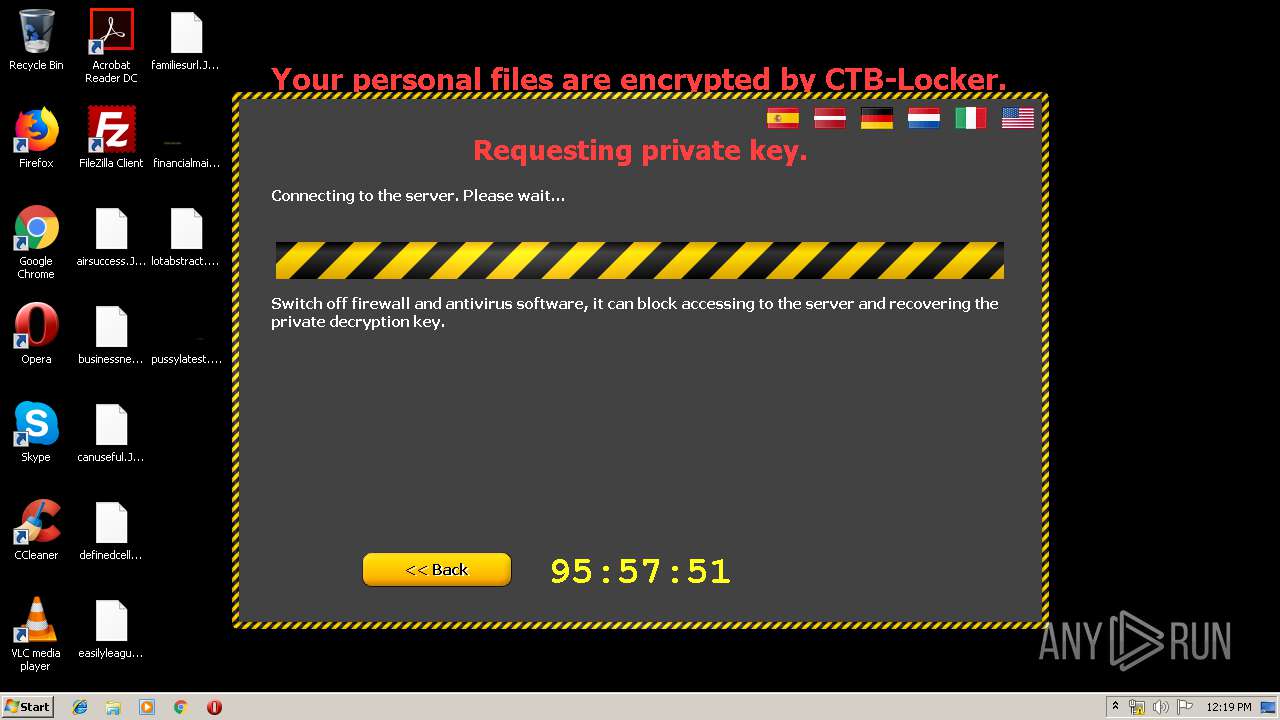
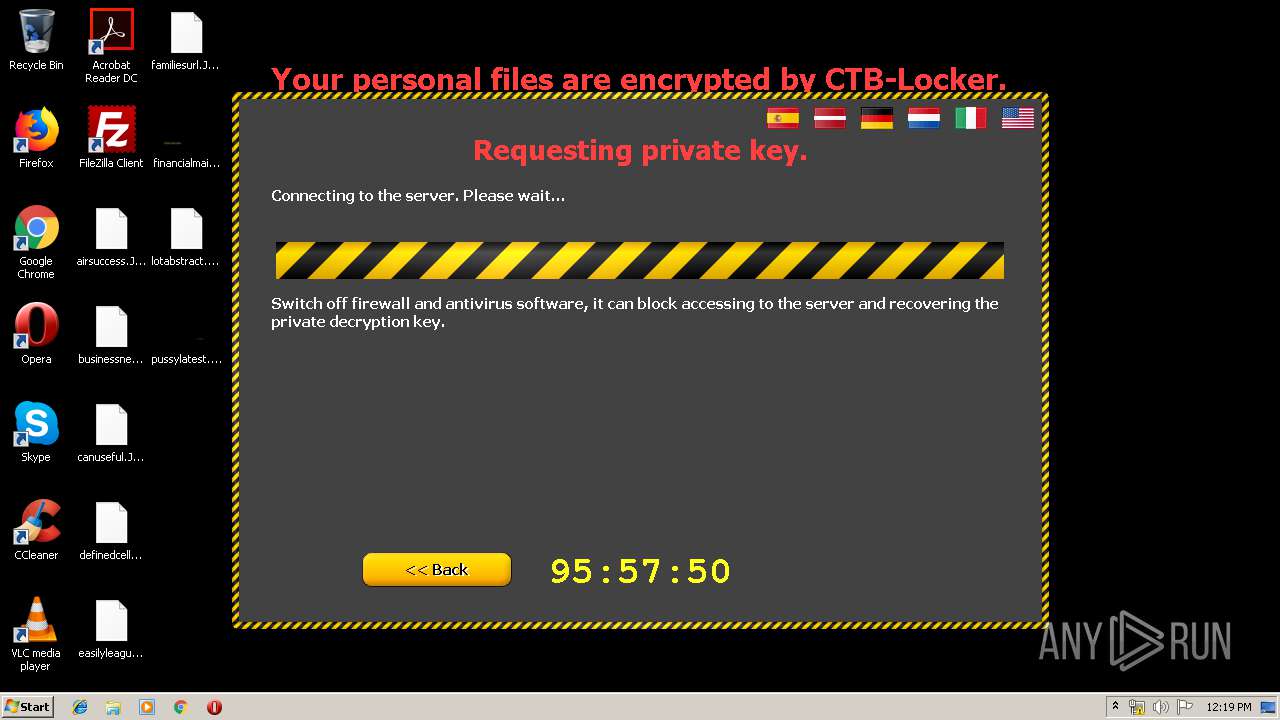
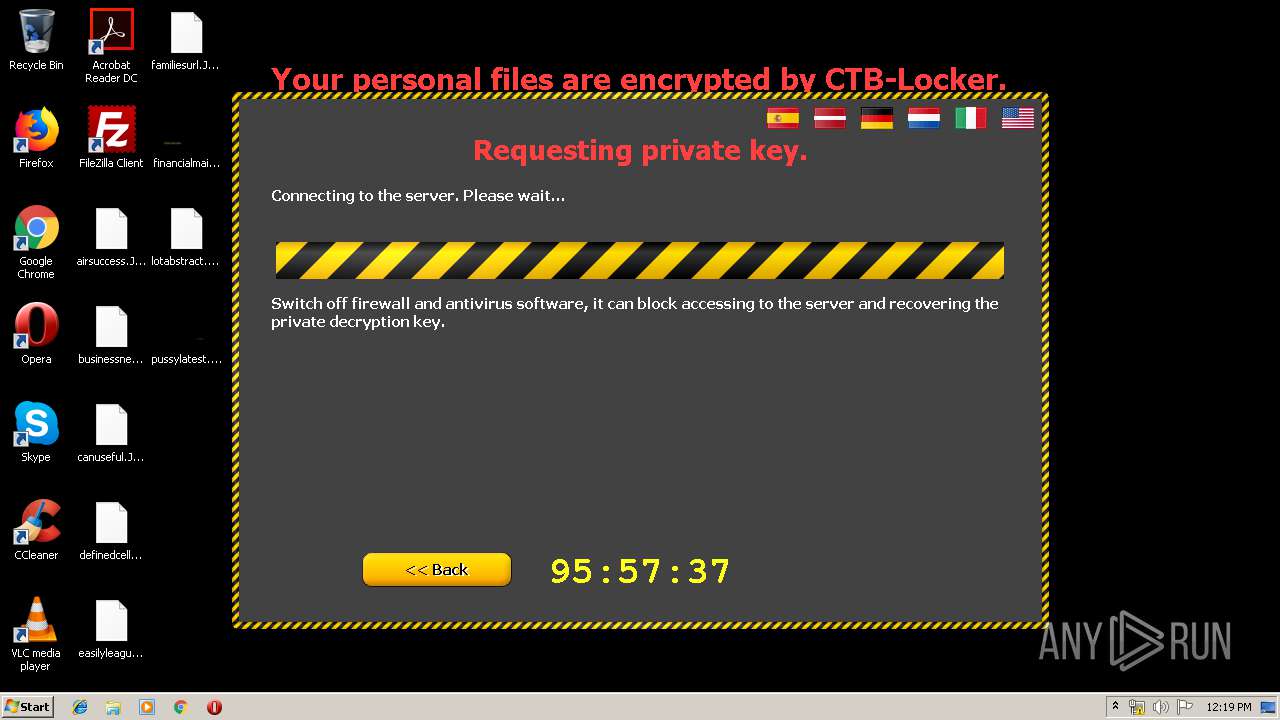
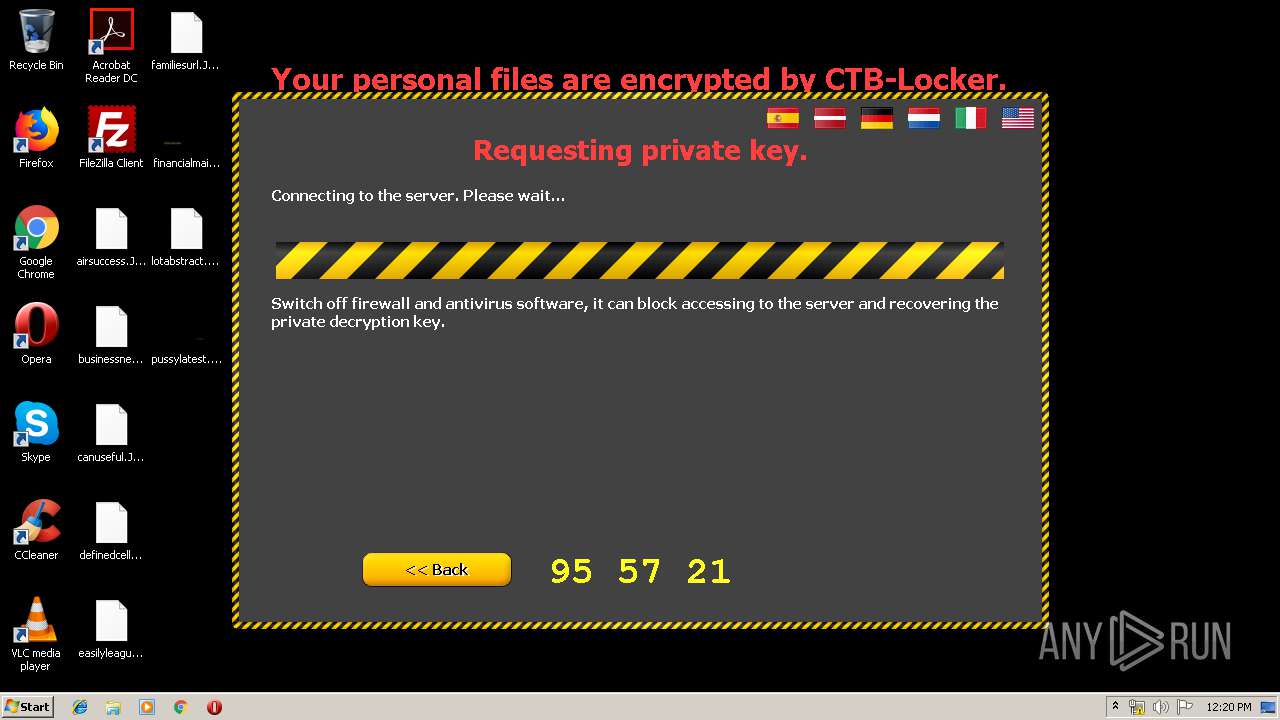
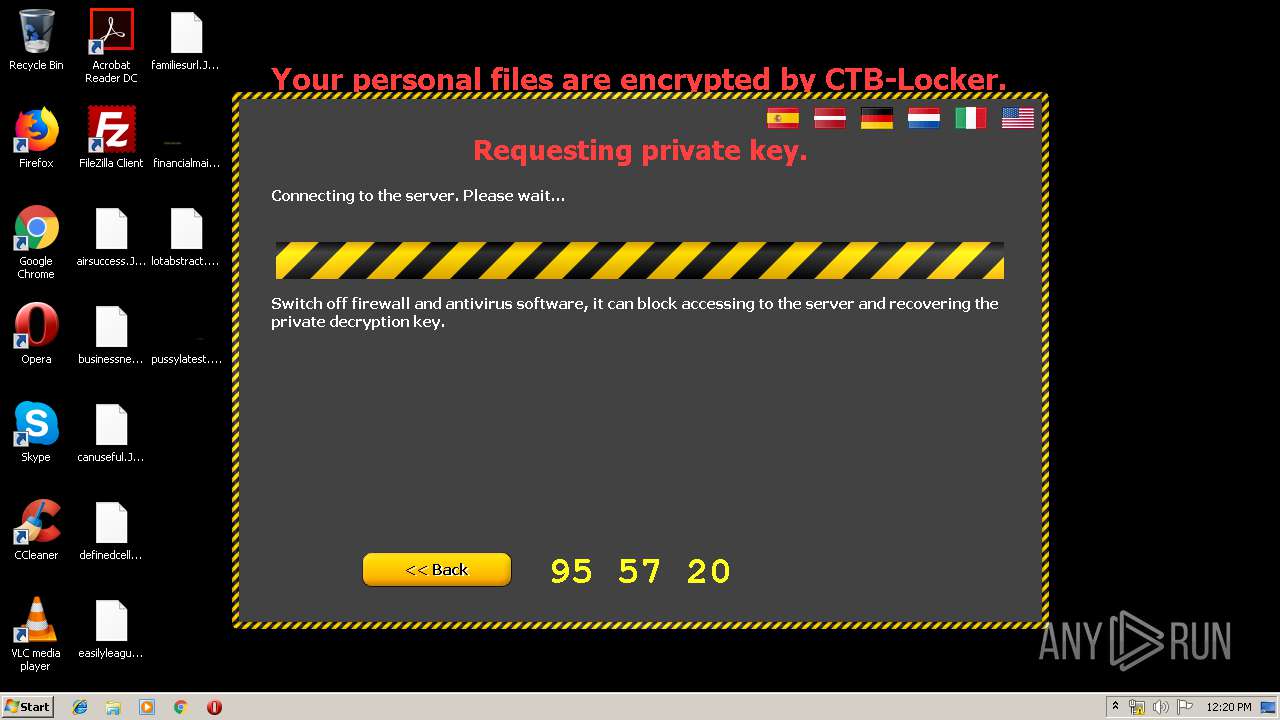
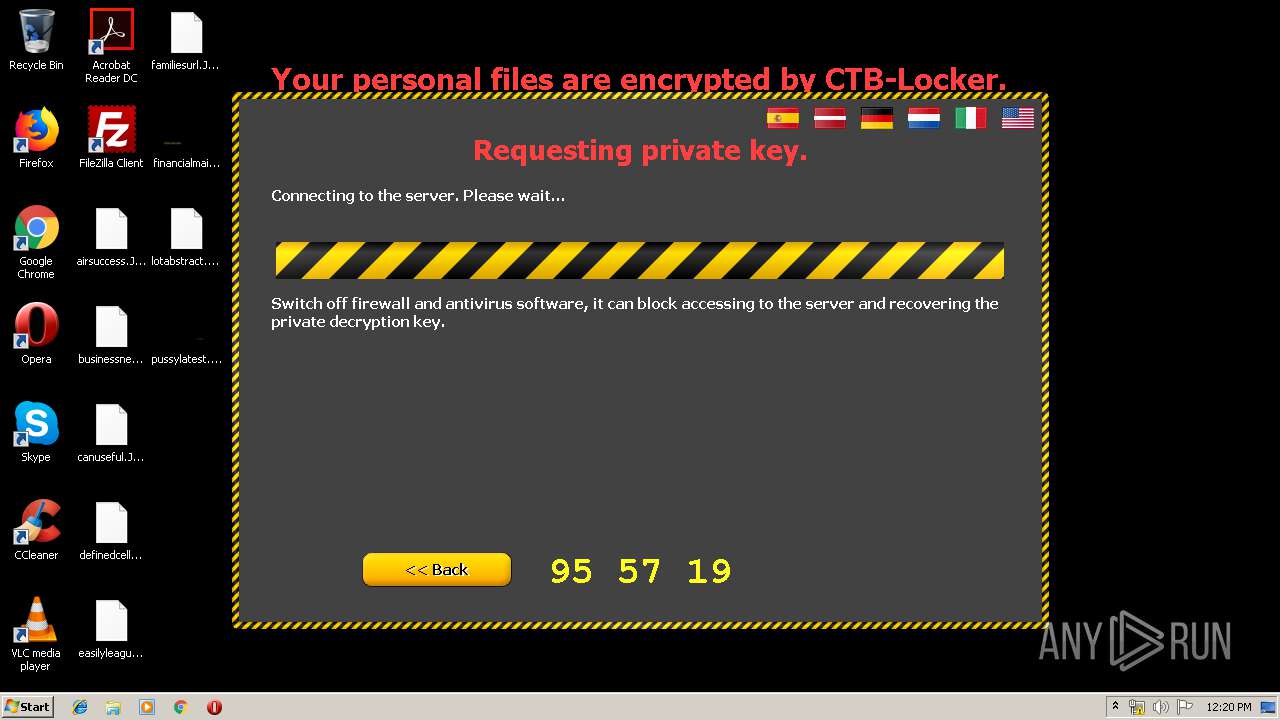
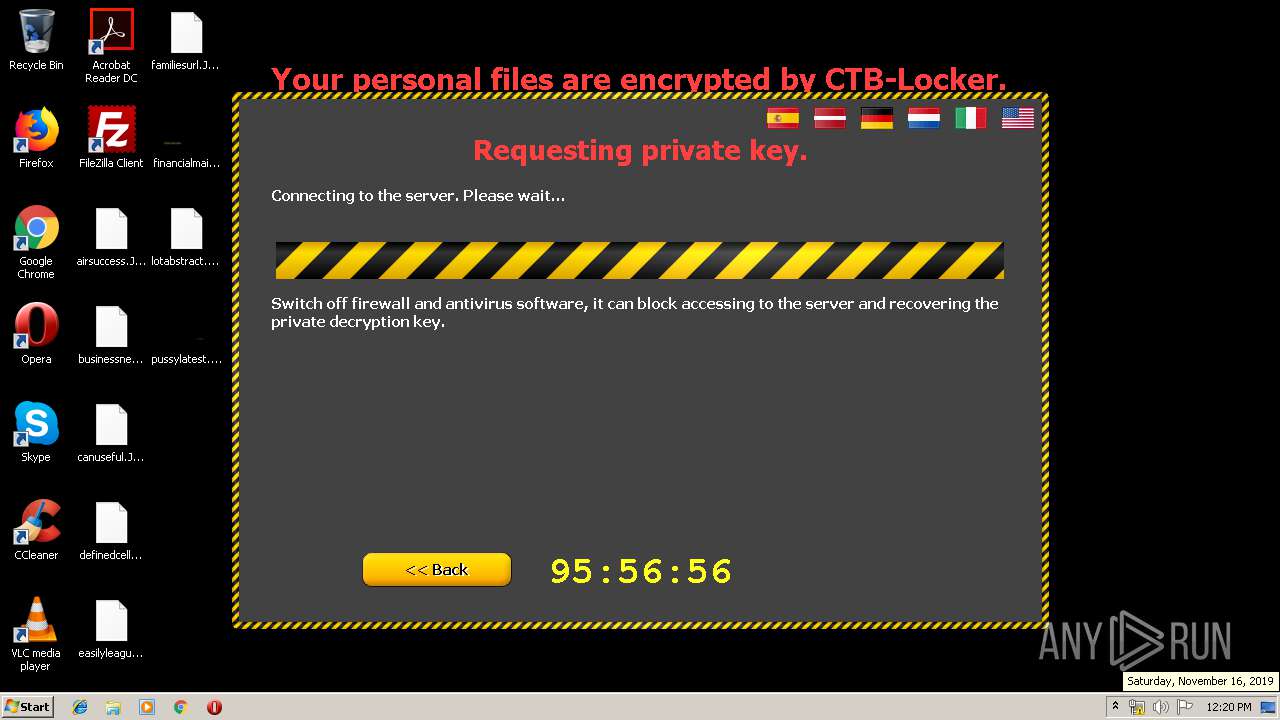
Changes the desktop background image
- ourkble.exe (PID: 1244)
INFO
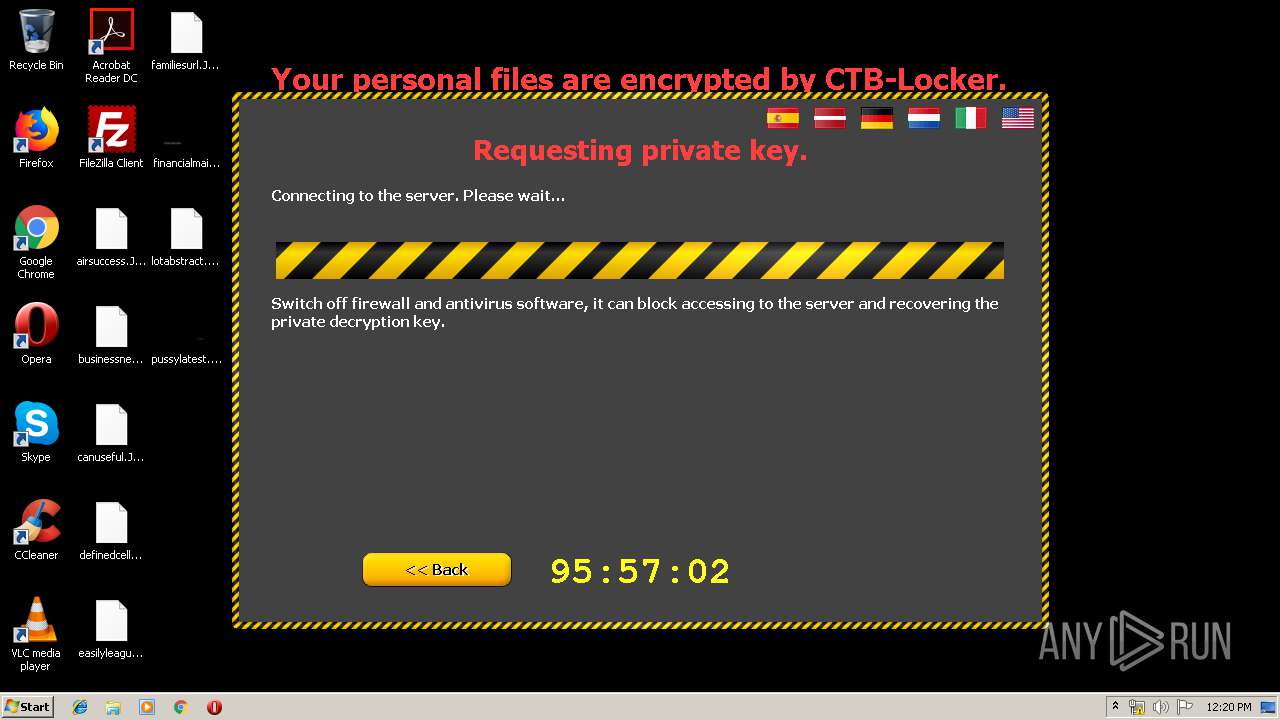
Dropped object may contain TOR URL's
- ourkble.exe (PID: 1244)
Dropped object may contain URL to Tor Browser
- ourkble.exe (PID: 1244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .scr | | | Windows screen saver (46.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (23.3) |
| .exe | | | Win32 Executable (generic) (15.9) |
| .exe | | | Generic Win/DOS Executable (7.1) |
| .exe | | | DOS Executable Generic (7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:25 20:44:19+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7 |
| CodeSize: | 24064 |
| InitializedDataSize: | 694784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x52ae |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Oct-2012 18:44:19 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Oct-2012 18:44:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005D53 | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.73476 |
.data | 0x00007000 | 0x000009FB | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.66459 |
.rsrc | 0x00008000 | 0x000A8ED9 | 0x000A9000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.97246 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.82595 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 5.388 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.95559 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.92736 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
512 | 2.45205 | 70 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHLWAPI.dll |
WTSAPI32.dll |
modemui.dll |
msimg32.dll |
nddeapi.dll |
user32.dll |
Total processes
35
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1244 | C:\Users\admin\AppData\Local\Temp\ourkble.exe | C:\Users\admin\AppData\Local\Temp\ourkble.exe | taskeng.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2580 | "C:\Users\admin\AppData\Local\Temp\MrT.exe" | C:\Users\admin\AppData\Local\Temp\MrT.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 413
Read events
1 332
Write events
80
Delete events
1
Modification events
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ApplicationDestinations |
| Operation: | write | Name: | MaxEntries |
Value: 15 | |||
| (PID) Process: | (1244) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1244) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1244) ourkble.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | TileWallpaper |
Value: 0 | |||
| (PID) Process: | (1244) ourkble.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | WallpaperStyle |
Value: 0 | |||
| (PID) Process: | (1244) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019111620191117 |
| Operation: | write | Name: | CachePath |
Value: %USERPROFILE%\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019111620191117 | |||
| (PID) Process: | (1244) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019111620191117 |
| Operation: | write | Name: | CachePrefix |
Value: :2019111620191117: | |||
| (PID) Process: | (1244) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019111620191117 |
| Operation: | write | Name: | CacheLimit |
Value: 8192 | |||
| (PID) Process: | (1244) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019111620191117 |
| Operation: | write | Name: | CacheOptions |
Value: 11 | |||
Executable files
1
Suspicious files
121
Text files
9
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1244 | ourkble.exe | C:\Users\admin\AppData\Local\Temp\lemjruda.tmp | — | |
MD5:— | SHA256:— | |||
| 1244 | ourkble.exe | C:\Users\admin\AppData\Local\Temp\lecanoda.tmp | — | |
MD5:— | SHA256:— | |||
| 1244 | ourkble.exe | C:\Users\admin\AppData\Local\Temp\lwzymoda.tmp | — | |
MD5:— | SHA256:— | |||
| 1244 | ourkble.exe | C:\Users\admin\AppData\Local\Temp\leivanda.tmp | — | |
MD5:— | SHA256:— | |||
| 1244 | ourkble.exe | C:\Users\admin\AppData\Local\Temp\lspazmda.tmp | — | |
MD5:— | SHA256:— | |||
| 1244 | ourkble.exe | C:\Users\admin\AppData\Local\Temp\lyyuanda.tmp | — | |
MD5:— | SHA256:— | |||
| 1244 | ourkble.exe | C:\Users\admin\AppData\Local\Temp\leqdfnda.tmp | — | |
MD5:— | SHA256:— | |||
| 1244 | ourkble.exe | C:\Users\admin\AppData\Local\Temp\lqyazmda.tmp | — | |
MD5:— | SHA256:— | |||
| 1244 | ourkble.exe | C:\Users\admin\AppData\Local\Temp\lwfanoda.tmp | — | |
MD5:— | SHA256:— | |||
| 1244 | ourkble.exe | C:\Users\admin\AppData\Local\Temp\lgxfrmda.tmp | — | |
MD5:— | SHA256:— | |||
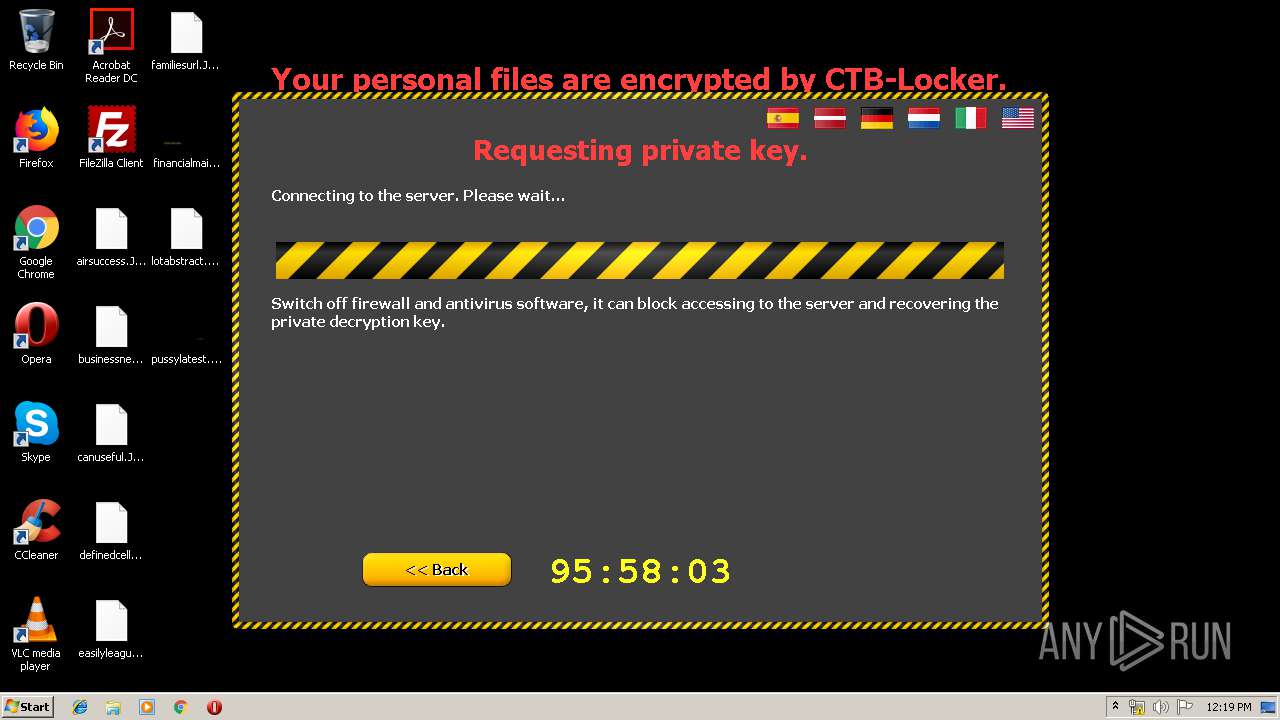
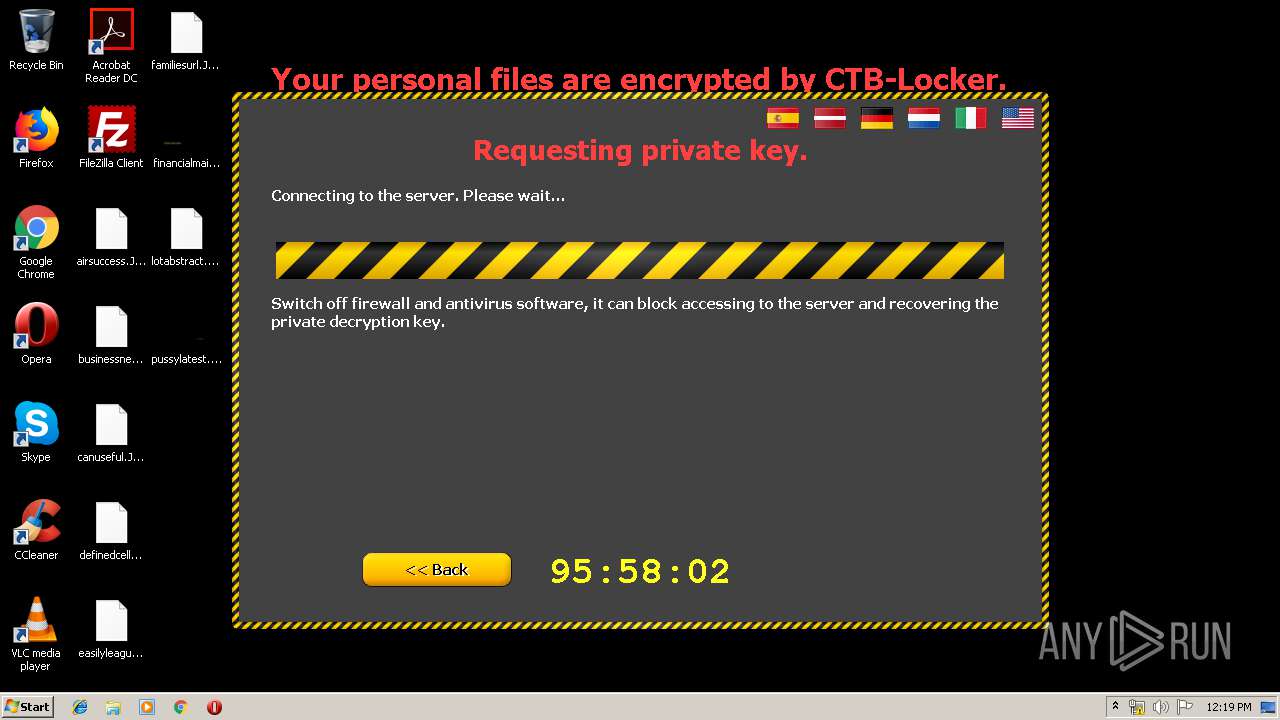
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
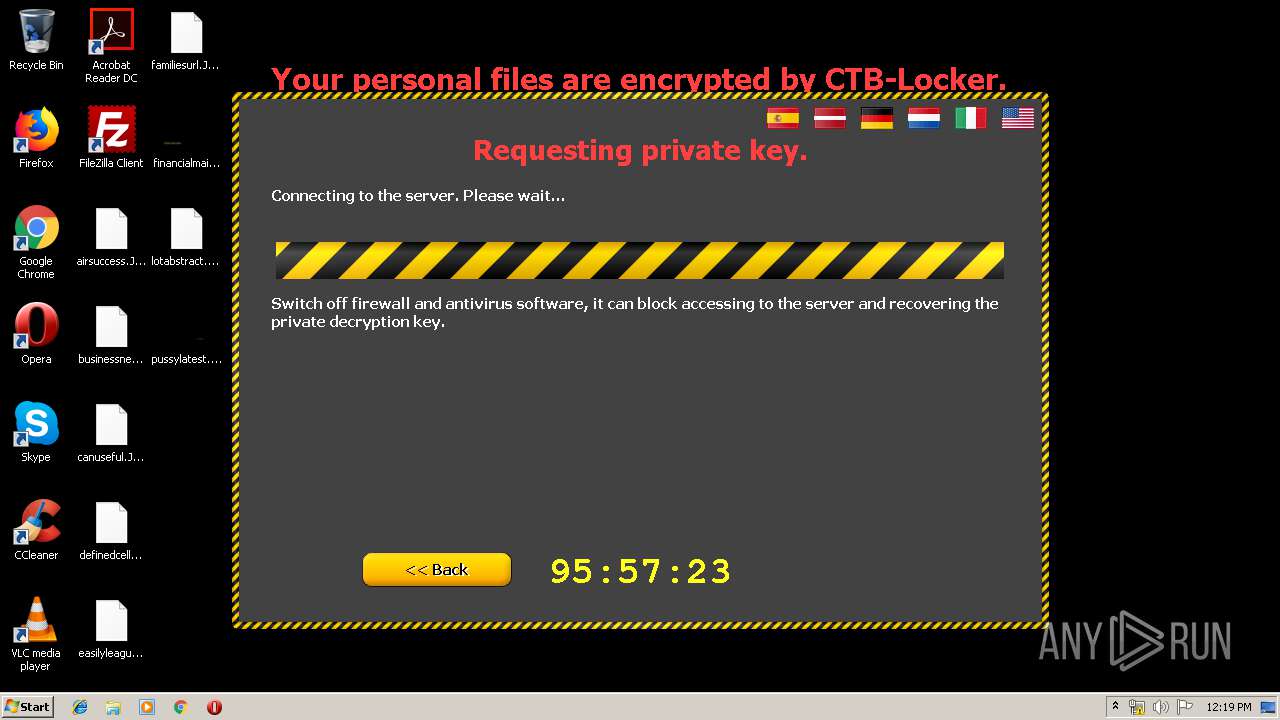
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1244 | ourkble.exe | 212.112.245.170:443 | — | QSC AG | DE | unknown |
1244 | ourkble.exe | 103.198.0.111:443 | dpaqjri6tinnqleh.tor2web.org | Hosting Services, Inc. | SG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip.telize.com |
| unknown |
dpaqjri6tinnqleh.tor2web.org |
| malicious |
Threats
1 ETPRO signatures available at the full report