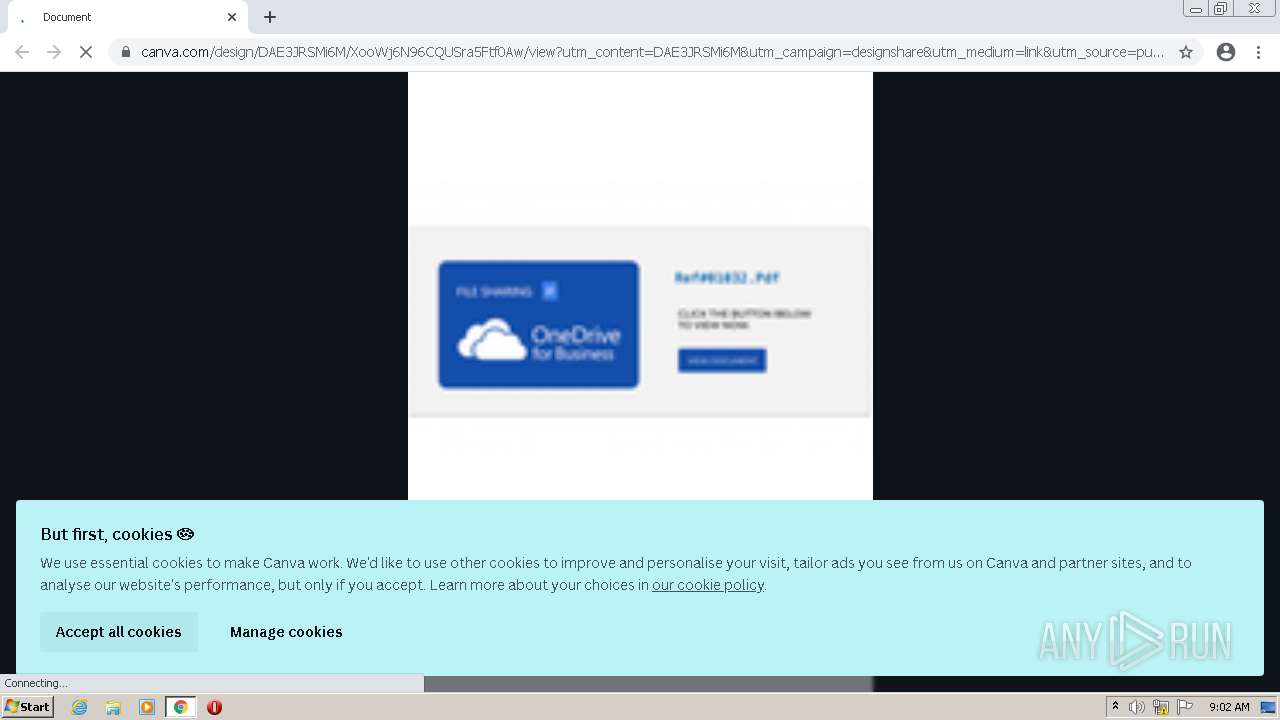
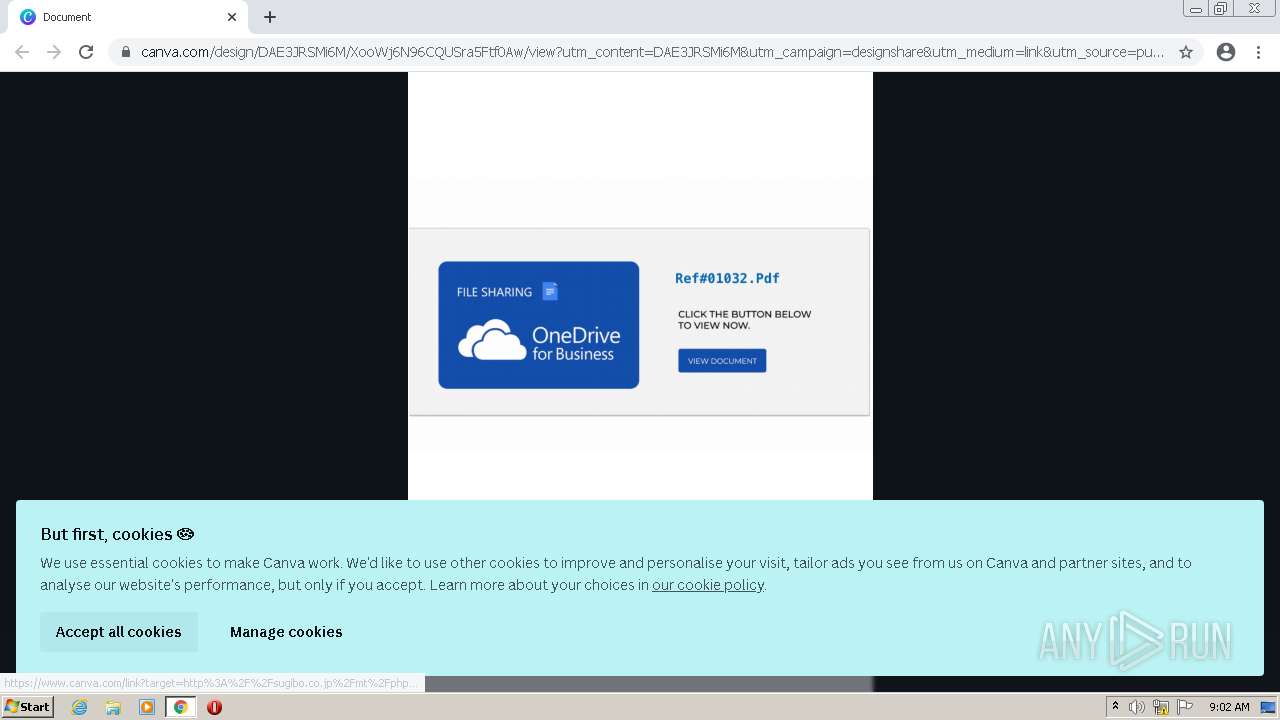
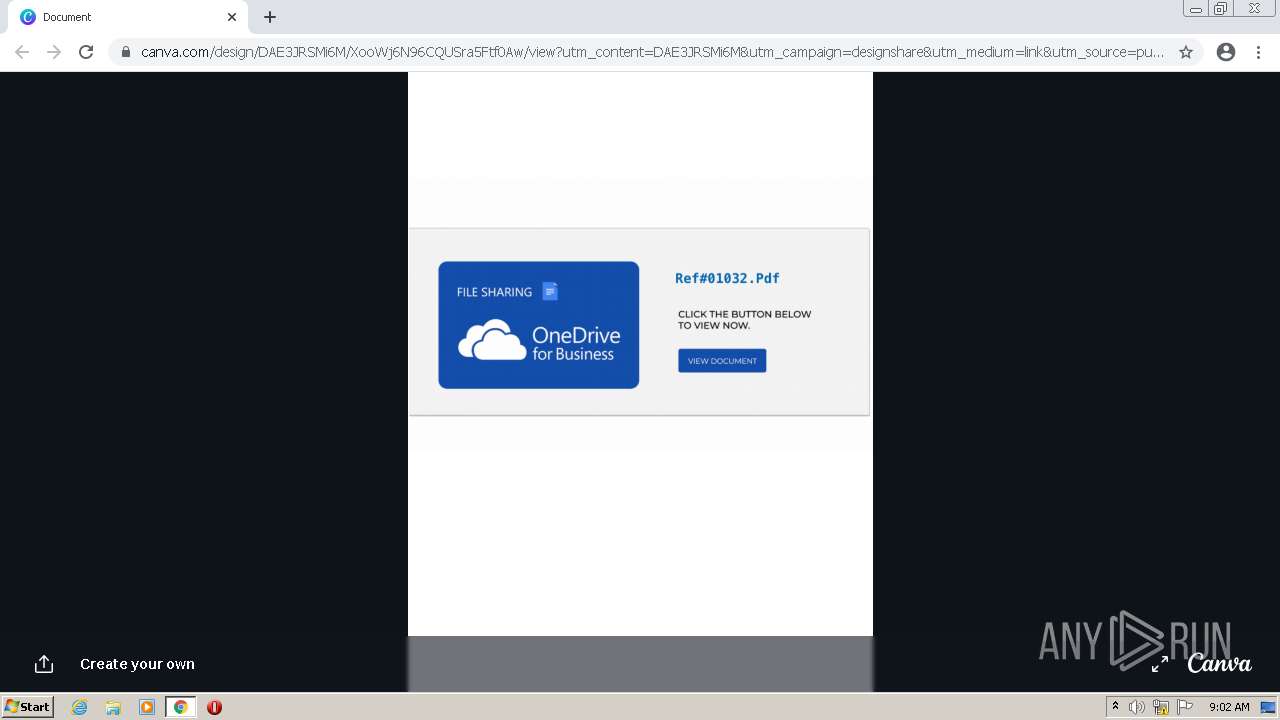
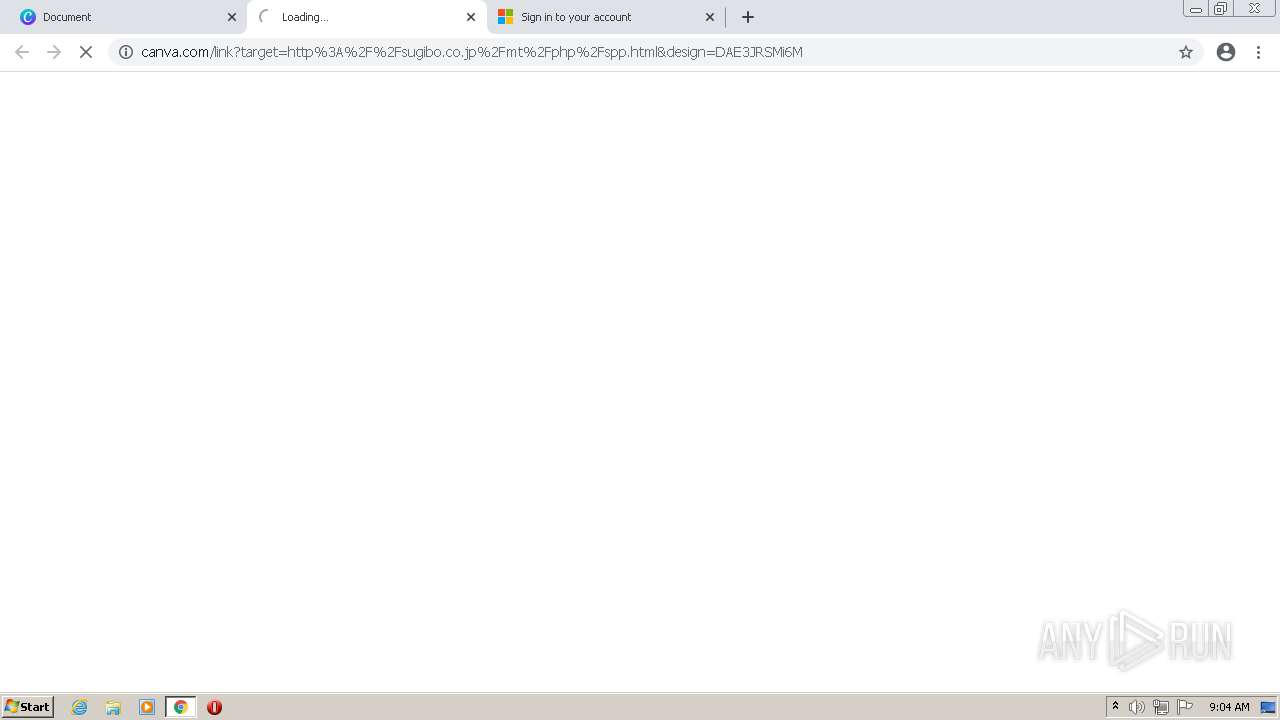
| URL: | https://www.canva.com/design/DAE3JRSMi6M/XooWj6N96CQUSra5Ftf0Aw/view?utm_content=DAE3JRSMi6M&utm_campaign=designshare&utm_medium=link&utm_source=publishsharelink |
| Full analysis: | https://app.any.run/tasks/fe10d692-9500-4bec-86ec-cba4ad4bda2d |
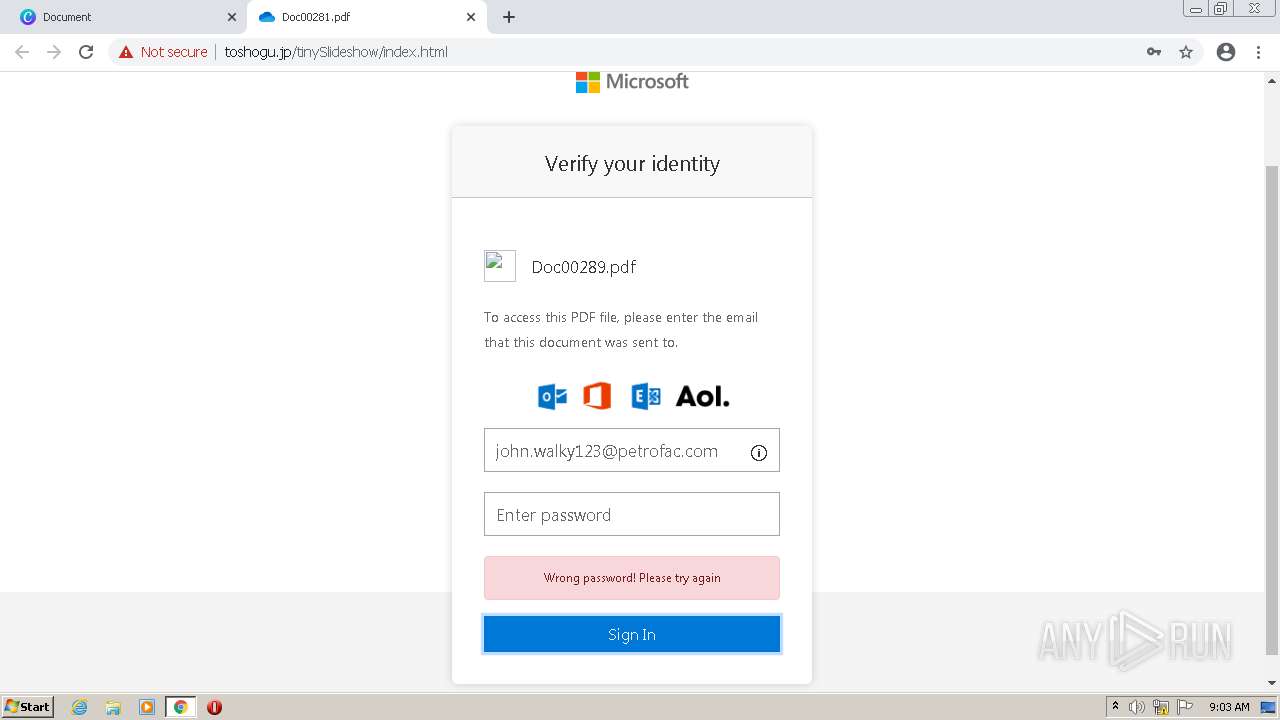
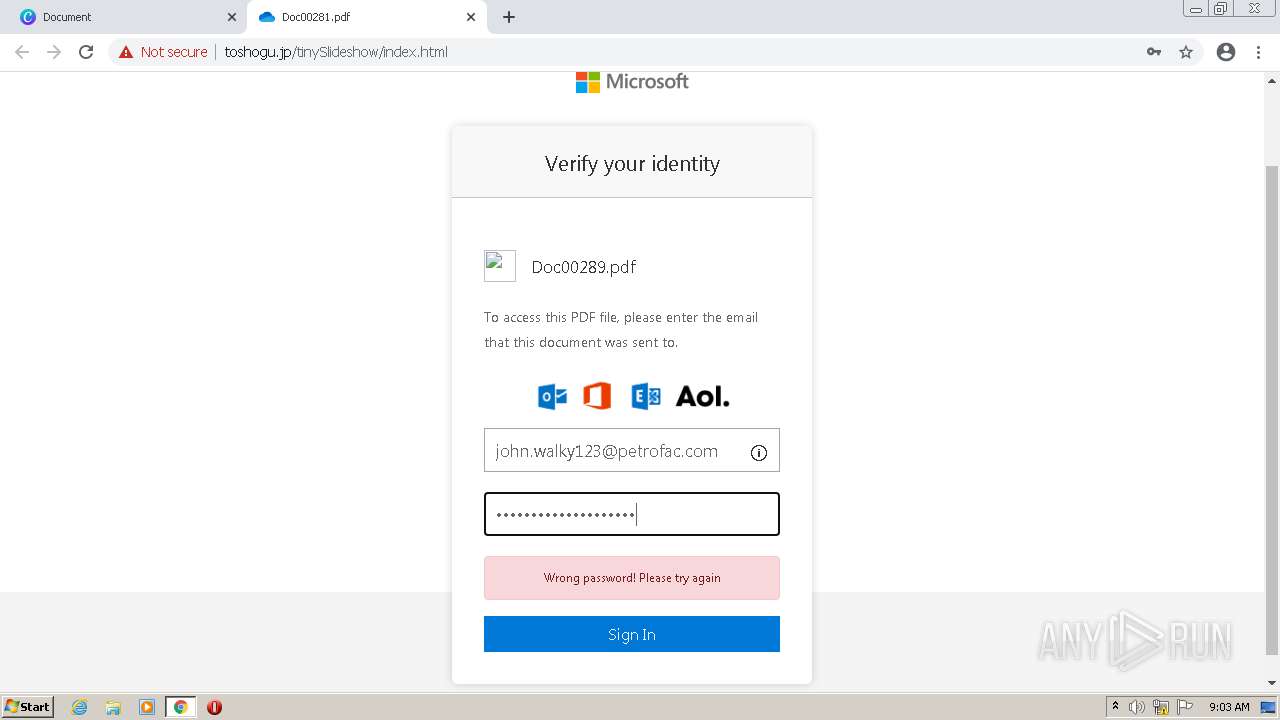
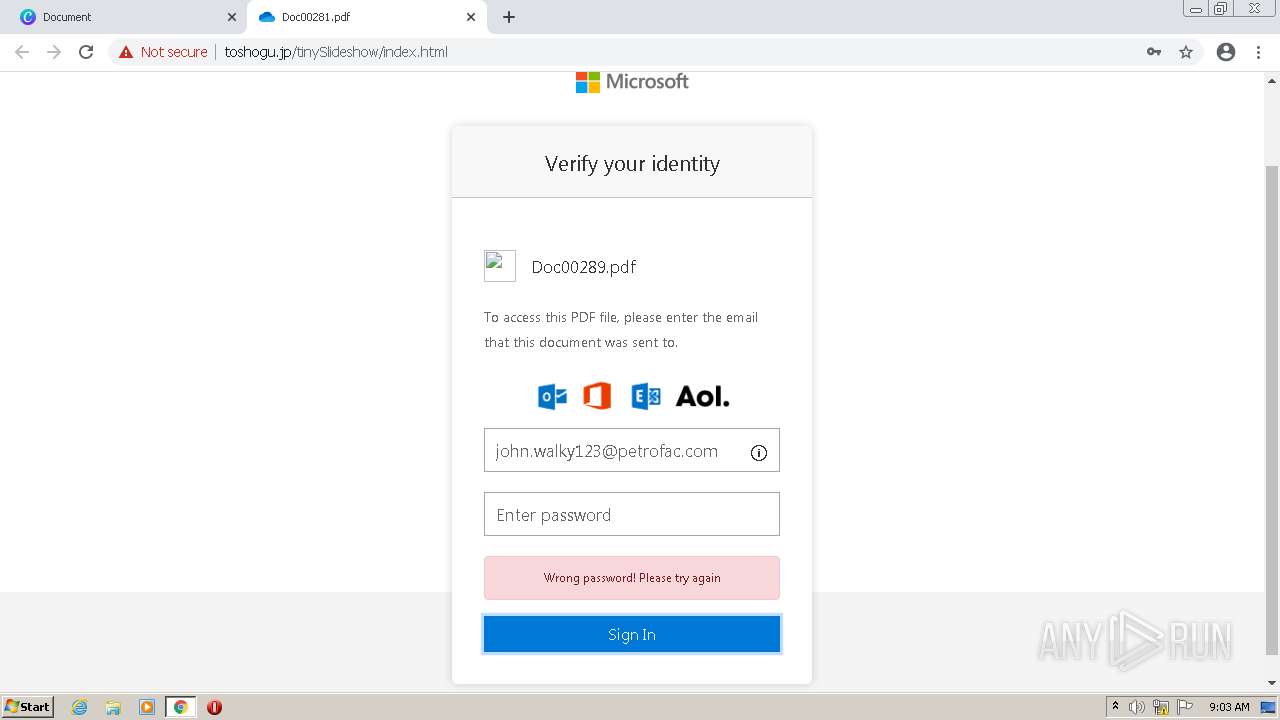
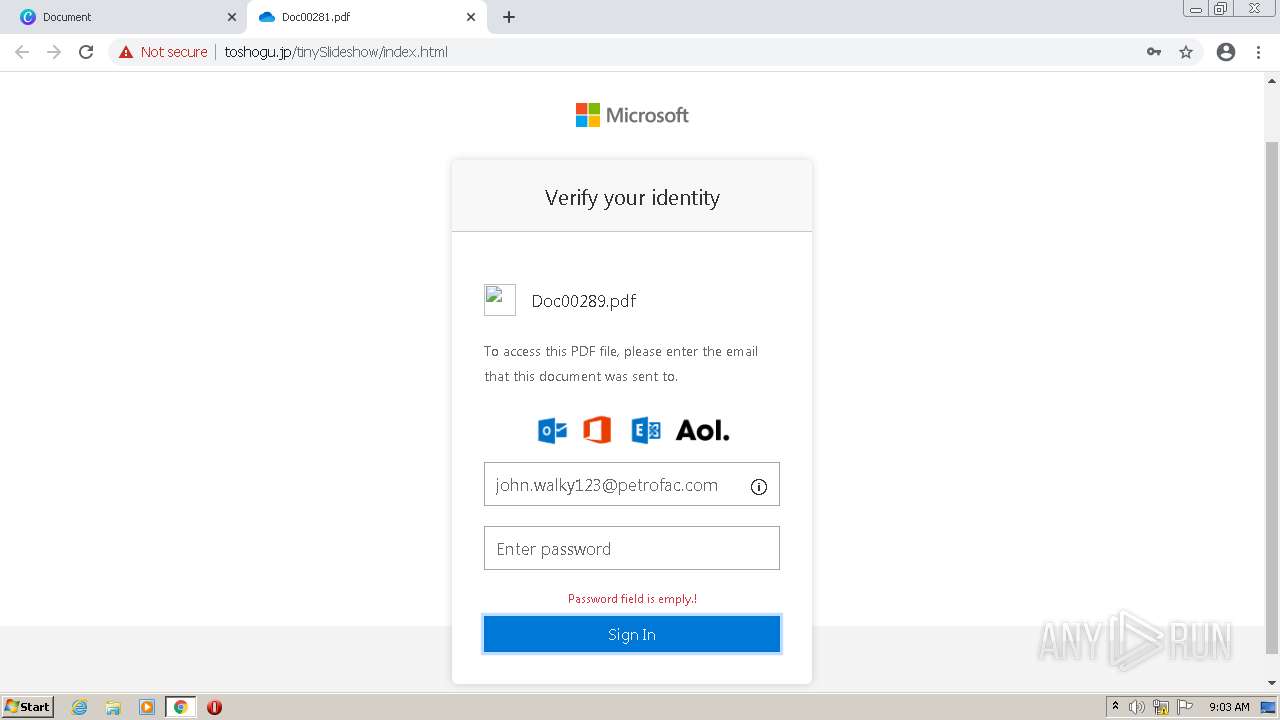
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2022, 09:02:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6E3F4C14A49D7D23398E922780C5744E |
| SHA1: | F00C90186C7528ECC0BF7784029FED1B311DC651 |
| SHA256: | 8A10025DF00A82330610AF8697157A9A38AB13AF75DEAF3B0967D15742742814 |
| SSDEEP: | 3:N8DSLHTiAWDkkOXEVSIMqhGAL+6vEkQHTomAGN/MRI6jRIYzbKQWa0V:2OLN/qBXDElcmtN/MRIHMWZV |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- chrome.exe (PID: 3636)
- chrome.exe (PID: 432)
- chrome.exe (PID: 372)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 892)
- chrome.exe (PID: 1472)
- chrome.exe (PID: 360)
- chrome.exe (PID: 1840)
- chrome.exe (PID: 2044)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 2232)
- chrome.exe (PID: 1860)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 2264)
- chrome.exe (PID: 2120)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 2028)
- chrome.exe (PID: 3904)
- chrome.exe (PID: 2864)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 3876)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 3264)
Reads the computer name
- chrome.exe (PID: 3636)
- chrome.exe (PID: 432)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 892)
- chrome.exe (PID: 2044)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 1860)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 2028)
Application launched itself
- chrome.exe (PID: 3636)
Reads the hosts file
- chrome.exe (PID: 3636)
- chrome.exe (PID: 432)
Reads settings of System Certificates
- chrome.exe (PID: 432)
Reads the date of Windows installation
- chrome.exe (PID: 2616)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2128 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1032,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1328 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1856 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3612 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3180 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2988 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1036 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3576 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
8 767
Read events
8 662
Write events
100
Delete events
5
Modification events
| (PID) Process: | (3636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3636) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
944
Text files
122
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61FA48AD-E34.pma | — | |
MD5:— | SHA256:— | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6663c135-6d13-49e9-904e-c646273bc247.tmp | text | |
MD5:— | SHA256:— | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF12c9ef.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 4048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF12cb09.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
99
DNS requests
53
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
872 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adko7cb7py3mfr6ojtw37dv4sioa_2770/jflookgnkcckhobaglndicnbbgbonegd_2770_all_jqirjt3kiw2cbws7eaqlt6re3q.crx3 | US | — | — | whitelisted |
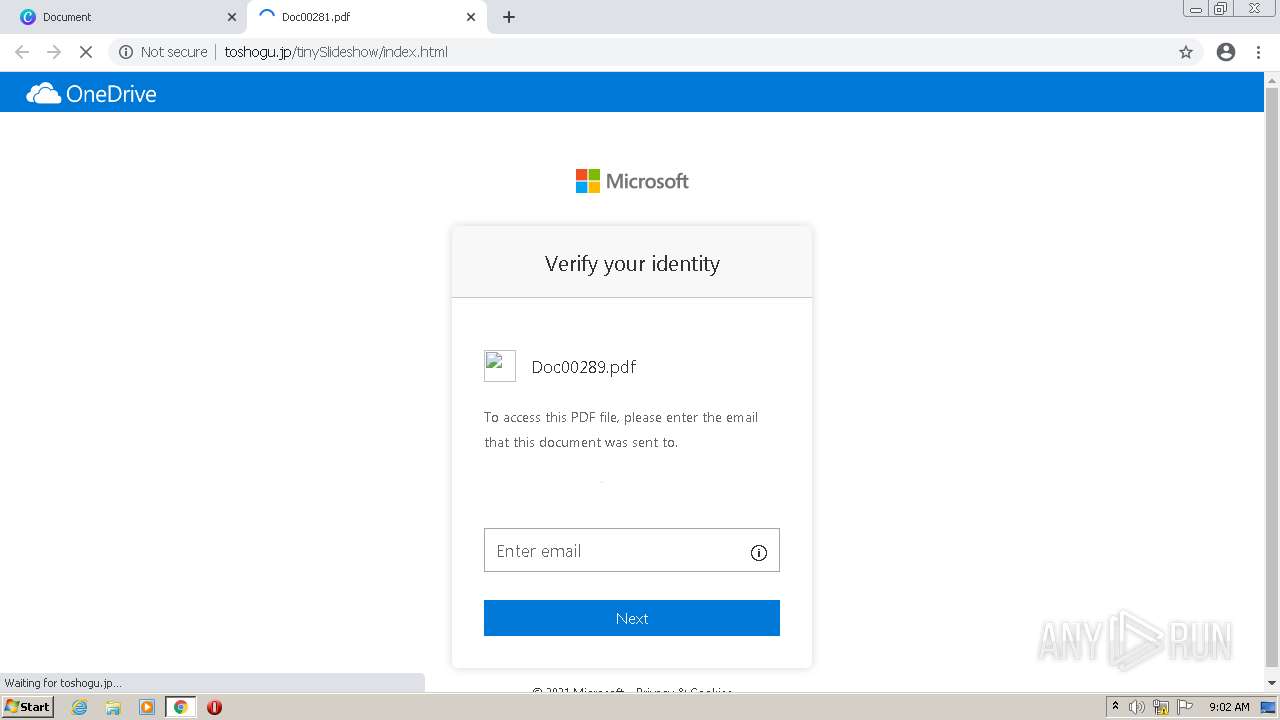
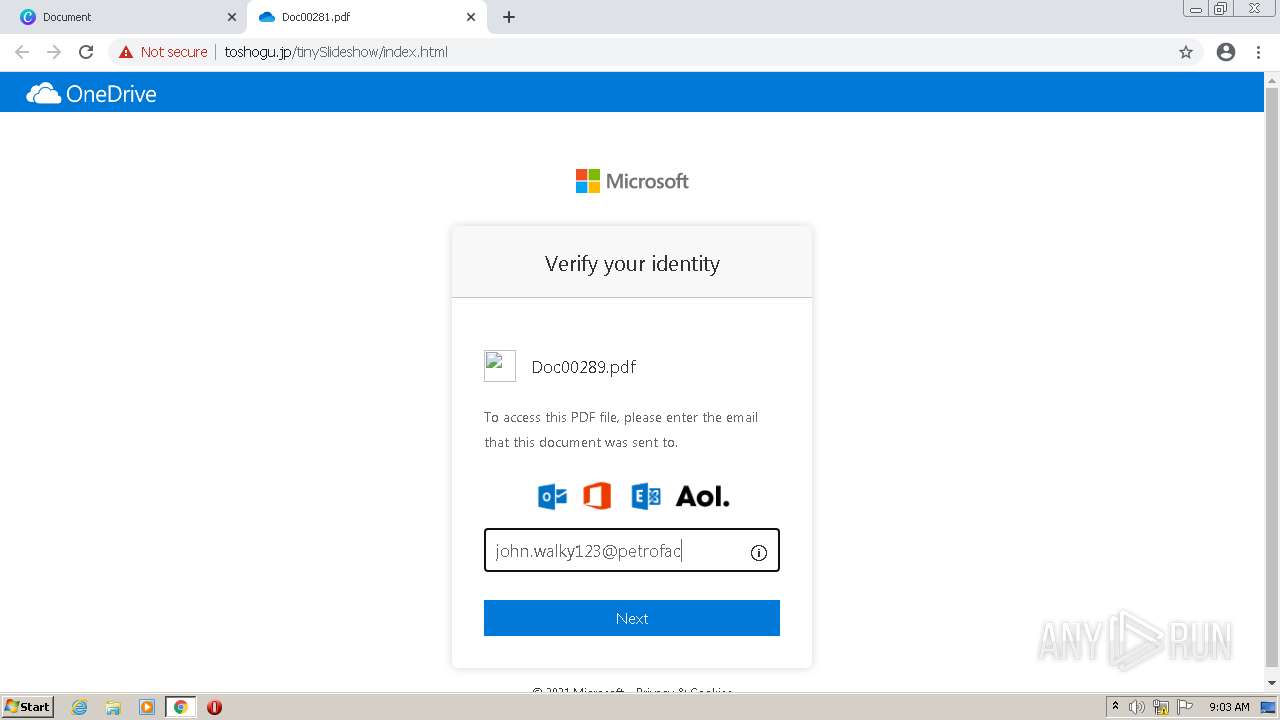
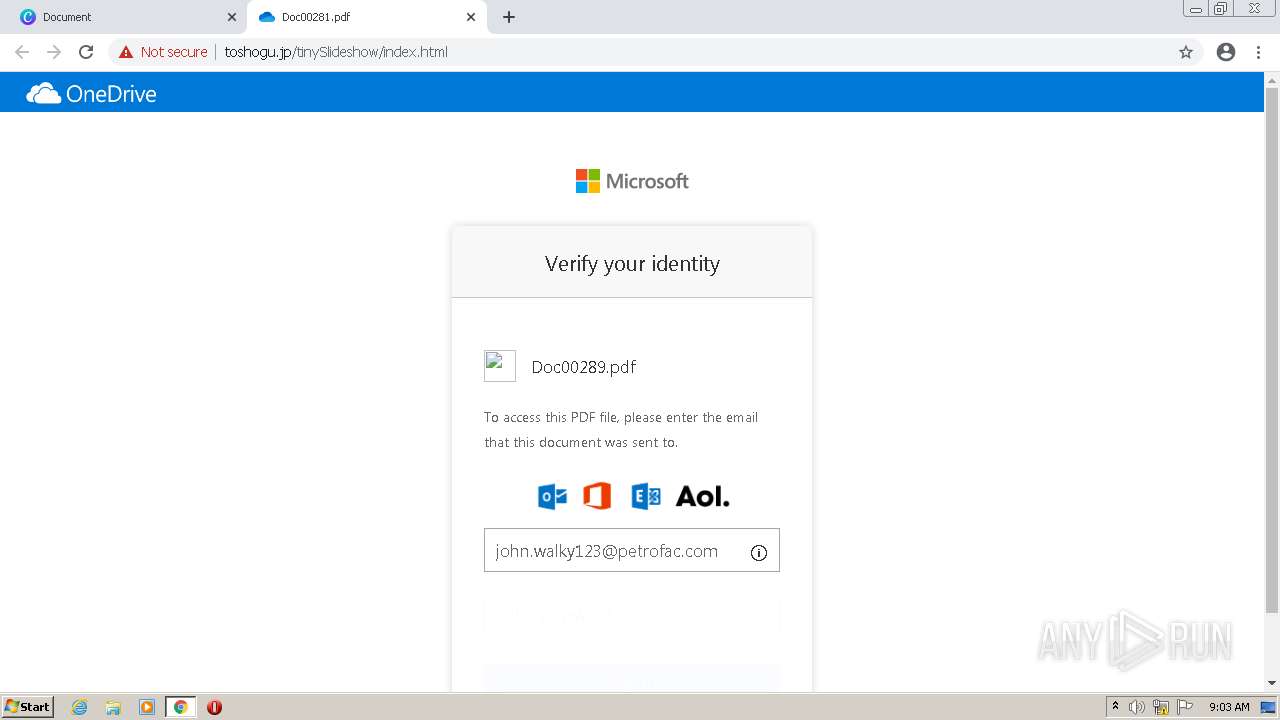
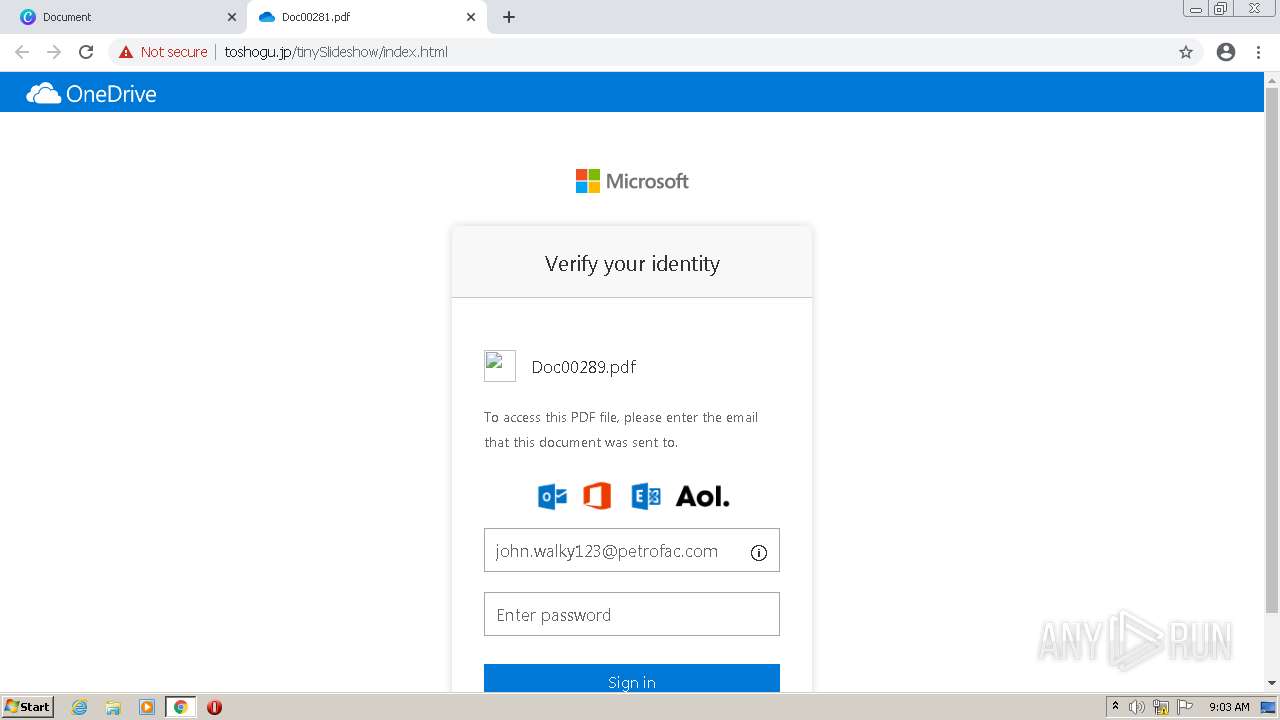
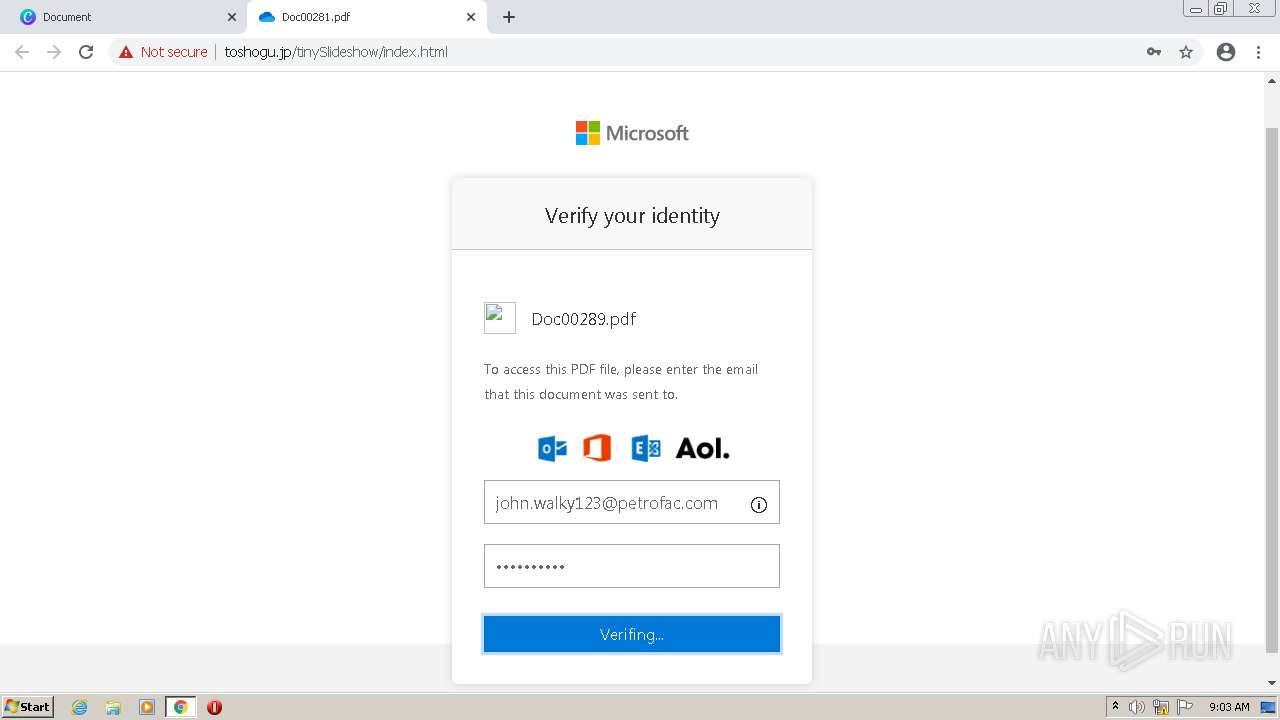
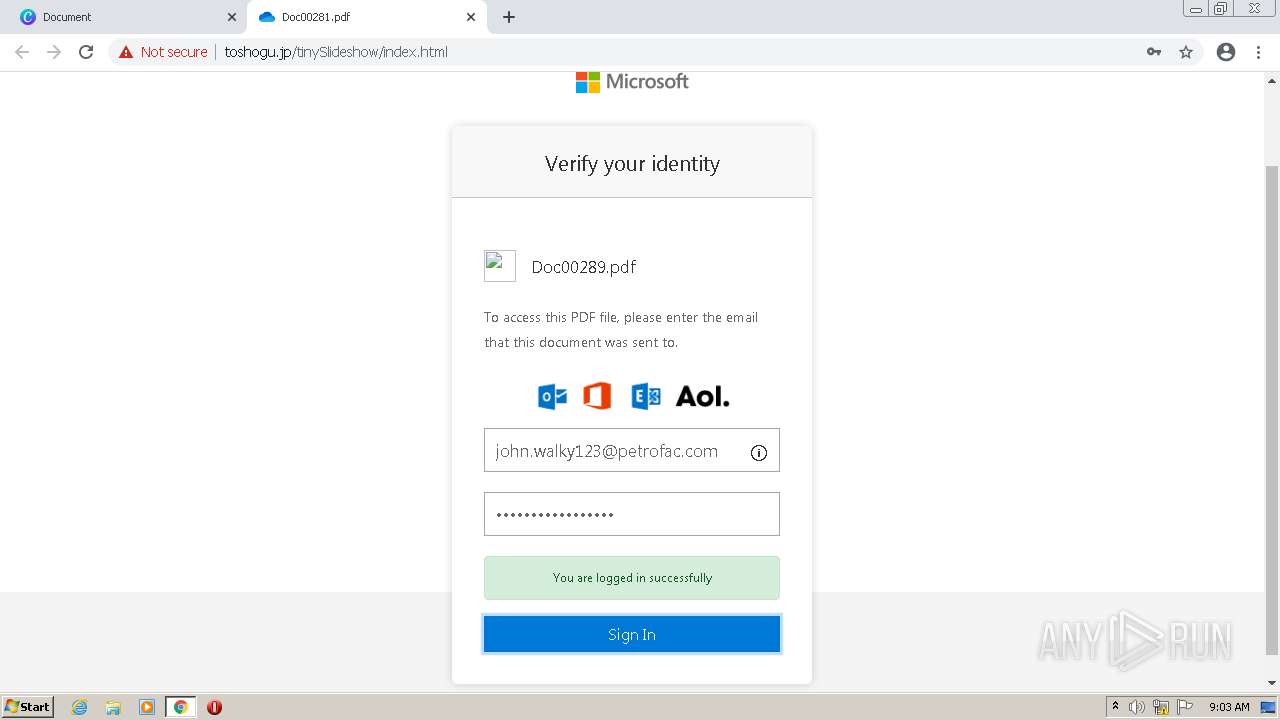
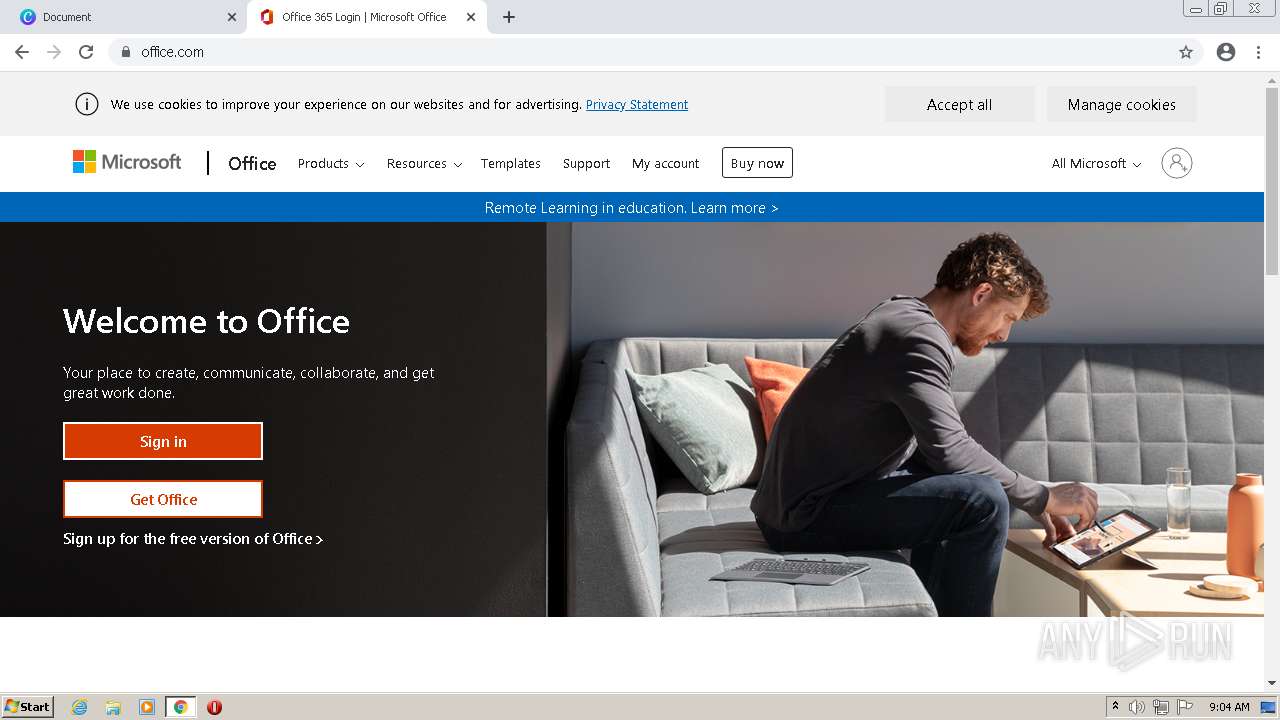
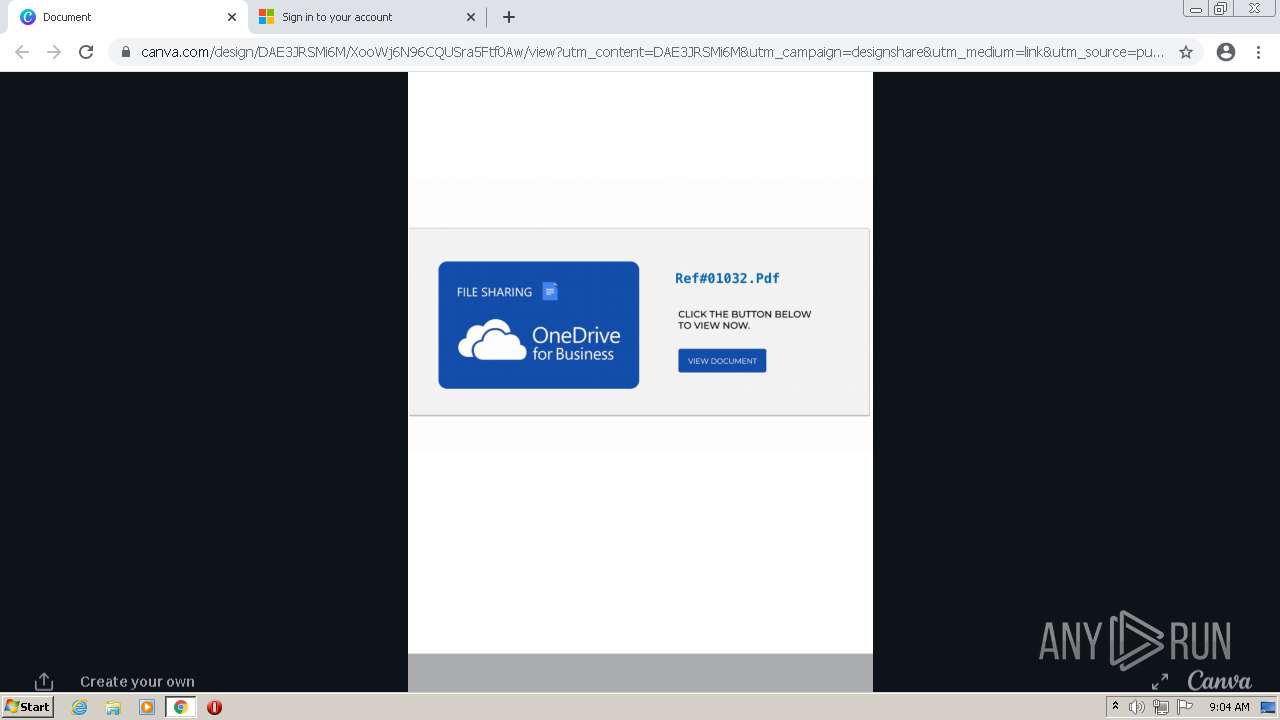
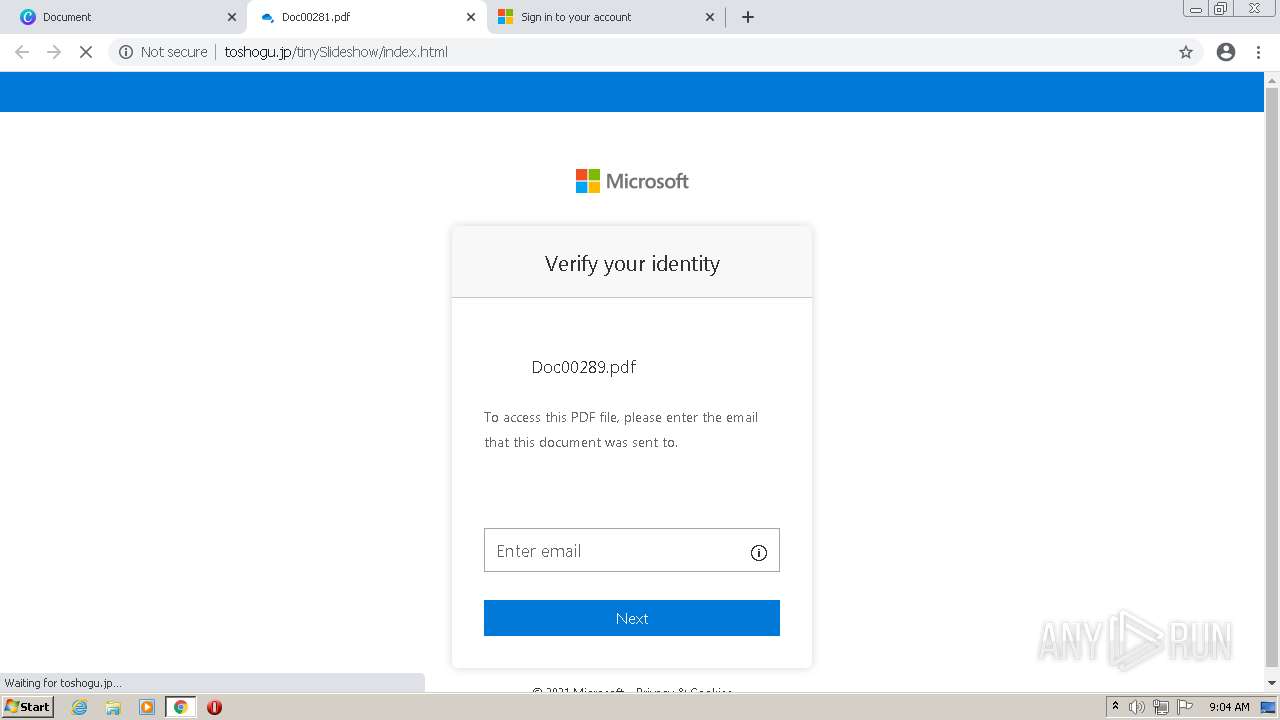
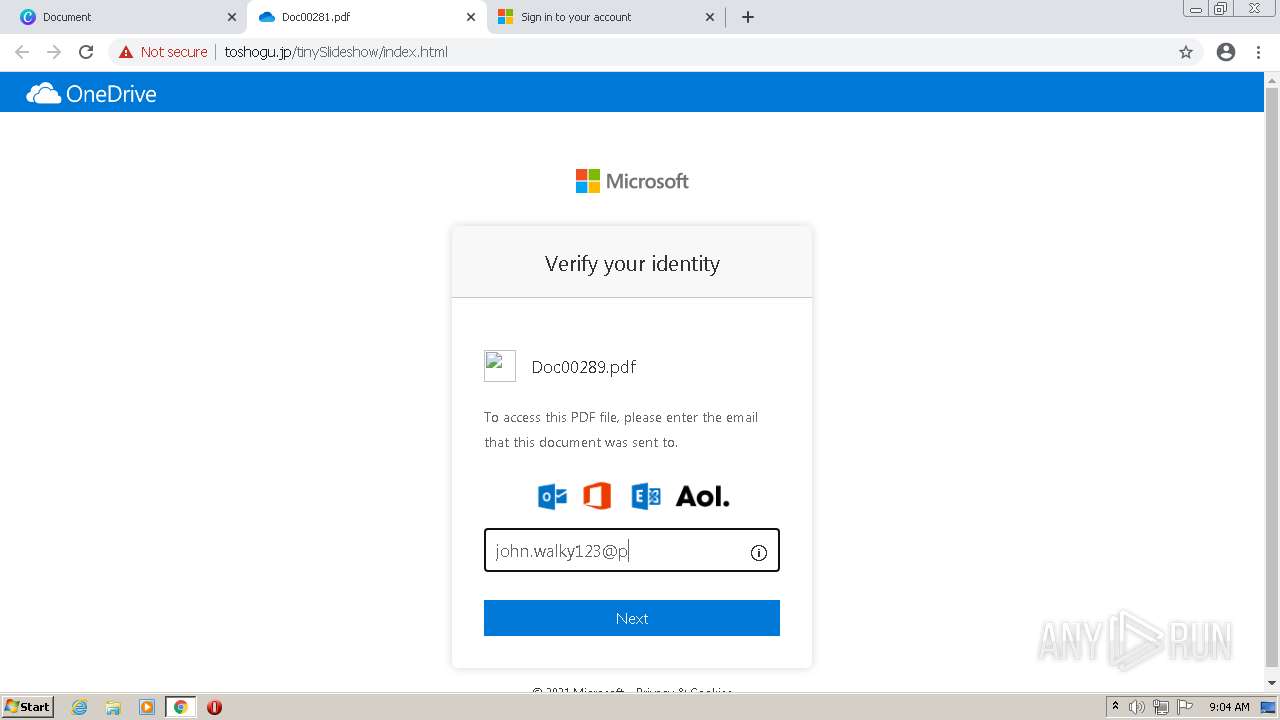
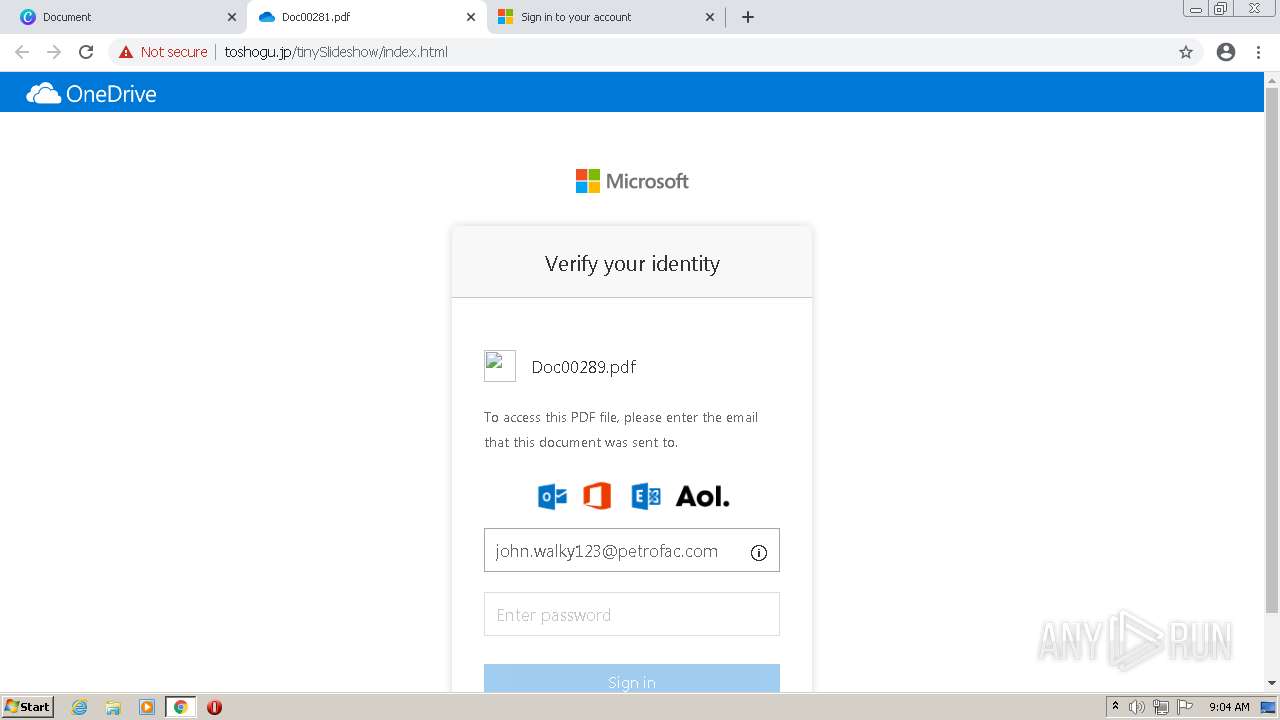
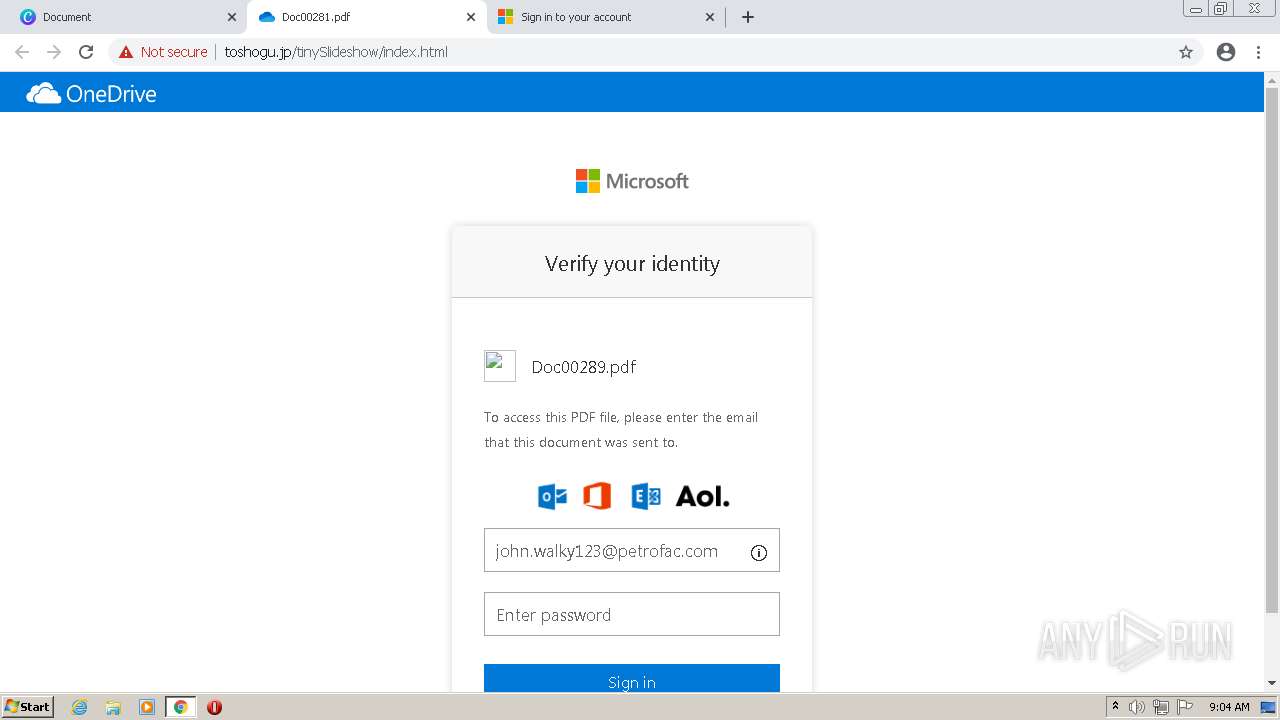
432 | chrome.exe | GET | 200 | 153.122.141.78:80 | http://toshogu.jp/tinySlideshow/index.html | JP | html | 27.4 Kb | suspicious |
432 | chrome.exe | GET | 404 | 153.122.141.78:80 | http://toshogu.jp/tinySlideshow/.png | JP | html | 295 b | suspicious |
432 | chrome.exe | GET | 404 | 153.122.141.78:80 | http://toshogu.jp/tinySlideshow/p.png | JP | html | 295 b | suspicious |
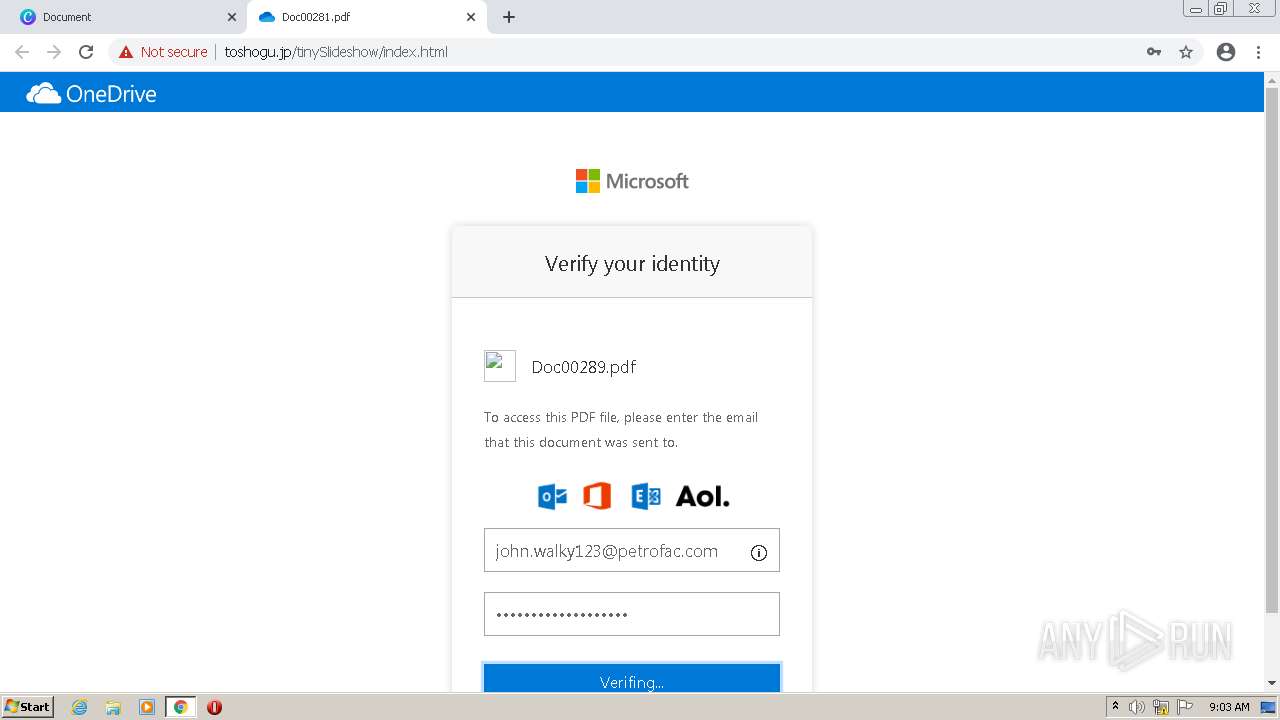
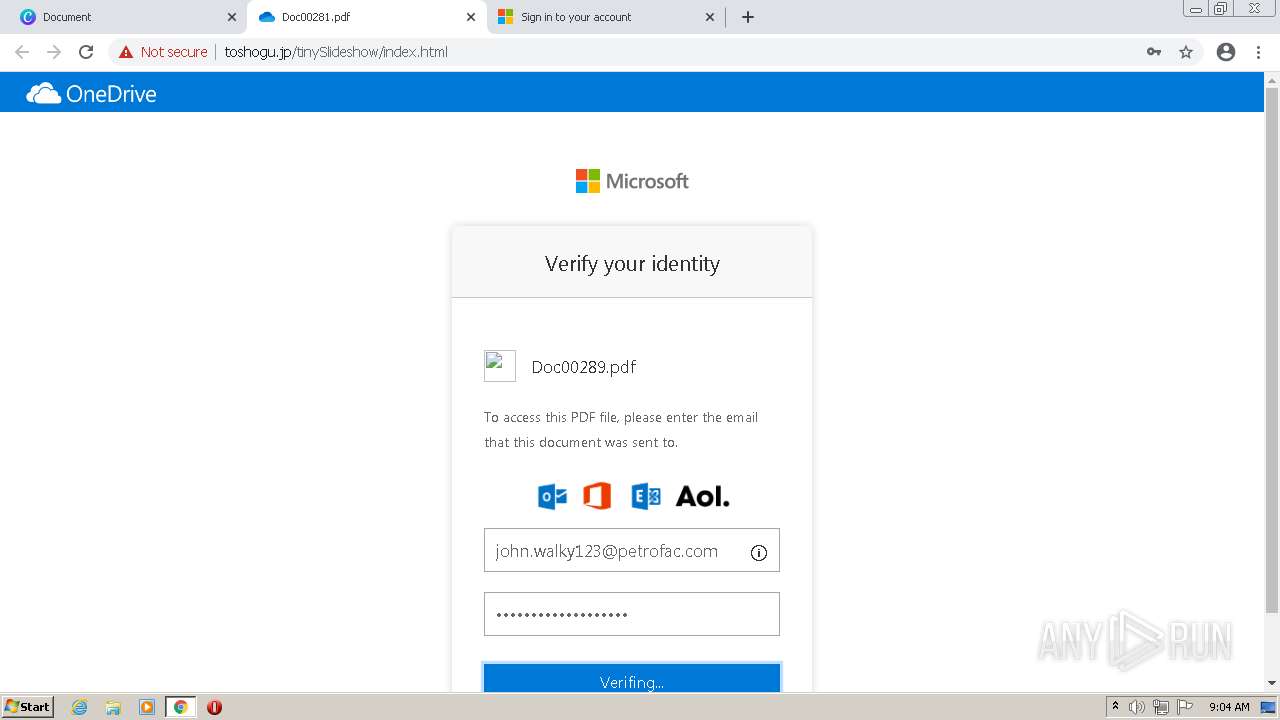
432 | chrome.exe | POST | 200 | 153.122.141.78:80 | http://toshogu.jp/tinySlideshow/next.php | JP | binary | 90 b | suspicious |
432 | chrome.exe | POST | 200 | 153.122.141.78:80 | http://toshogu.jp/tinySlideshow/next.php | JP | binary | 90 b | suspicious |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adko7cb7py3mfr6ojtw37dv4sioa_2770/jflookgnkcckhobaglndicnbbgbonegd_2770_all_jqirjt3kiw2cbws7eaqlt6re3q.crx3 | US | binary | 444 b | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adko7cb7py3mfr6ojtw37dv4sioa_2770/jflookgnkcckhobaglndicnbbgbonegd_2770_all_jqirjt3kiw2cbws7eaqlt6re3q.crx3 | US | binary | 5.66 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 22.5 Kb | whitelisted |
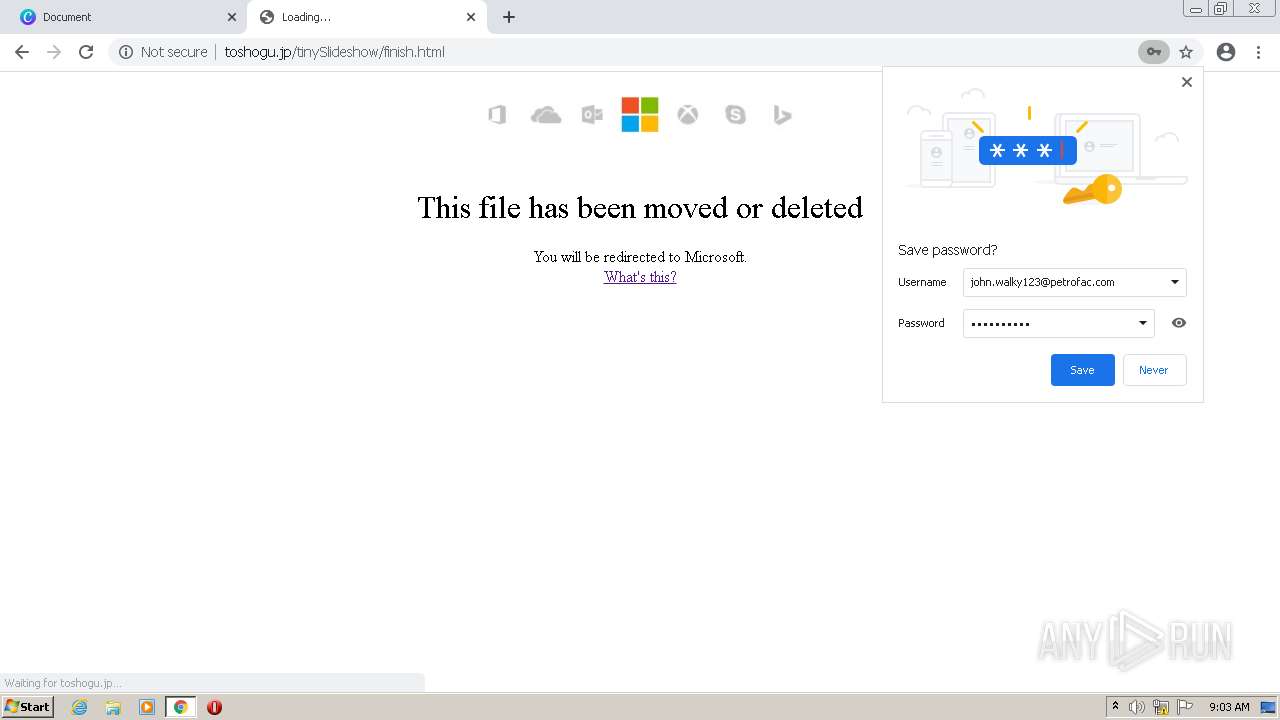
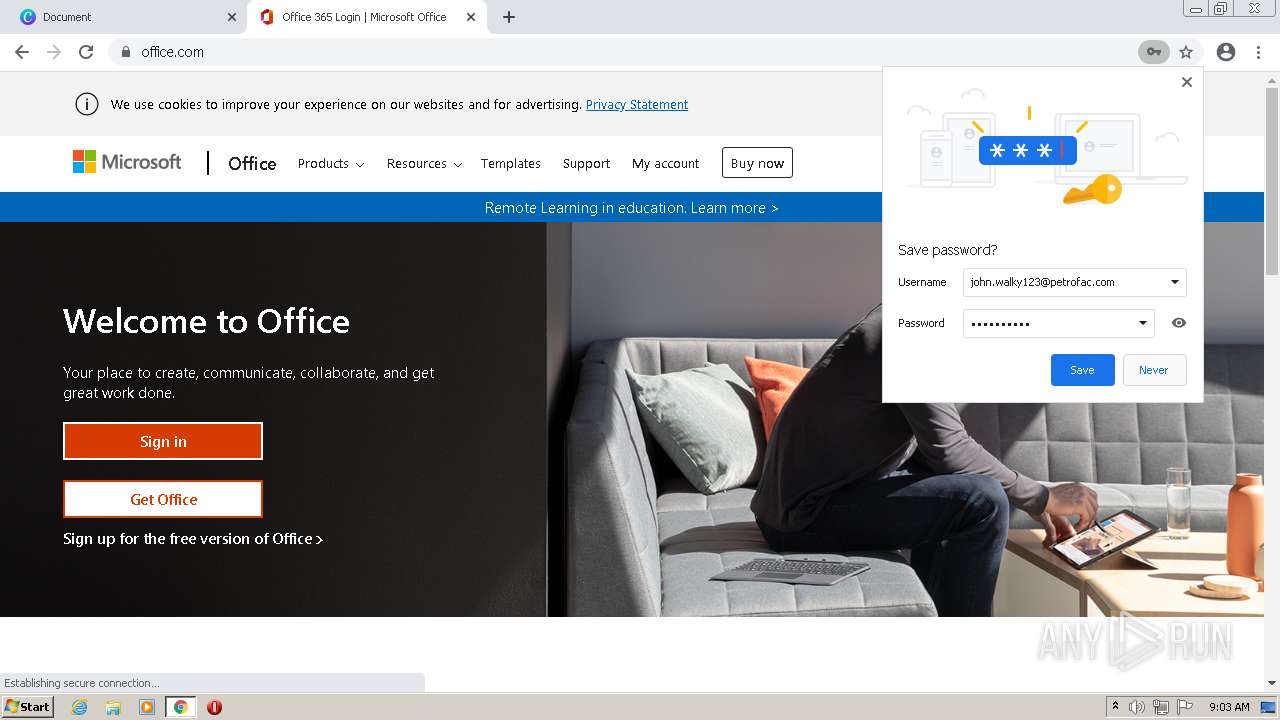
432 | chrome.exe | GET | 200 | 153.122.141.78:80 | http://toshogu.jp/tinySlideshow/finish.html | JP | html | 5.43 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
432 | chrome.exe | 216.58.212.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
432 | chrome.exe | 142.250.185.237:443 | accounts.google.com | Google Inc. | US | suspicious |
432 | chrome.exe | 35.188.42.15:443 | — | Google Inc. | US | whitelisted |
432 | chrome.exe | 104.17.115.17:443 | www.canva.com | Cloudflare Inc | US | unknown |
432 | chrome.exe | 104.16.95.65:443 | static.cloudflareinsights.com | Cloudflare Inc | US | shared |
432 | chrome.exe | 142.250.181.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
432 | chrome.exe | 151.101.193.208:443 | sdk.iad-01.braze.com | Fastly | US | unknown |
432 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
432 | chrome.exe | 153.122.141.78:80 | toshogu.jp | GMO CLOUD K.K. | JP | suspicious |
432 | chrome.exe | 153.122.141.223:80 | sugibo.co.jp | GMO CLOUD K.K. | JP | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.canva.com |
| whitelisted |
static.canva.com |
| whitelisted |
sentry.io |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
font-public.canva.com |
| whitelisted |
media-private.canva.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
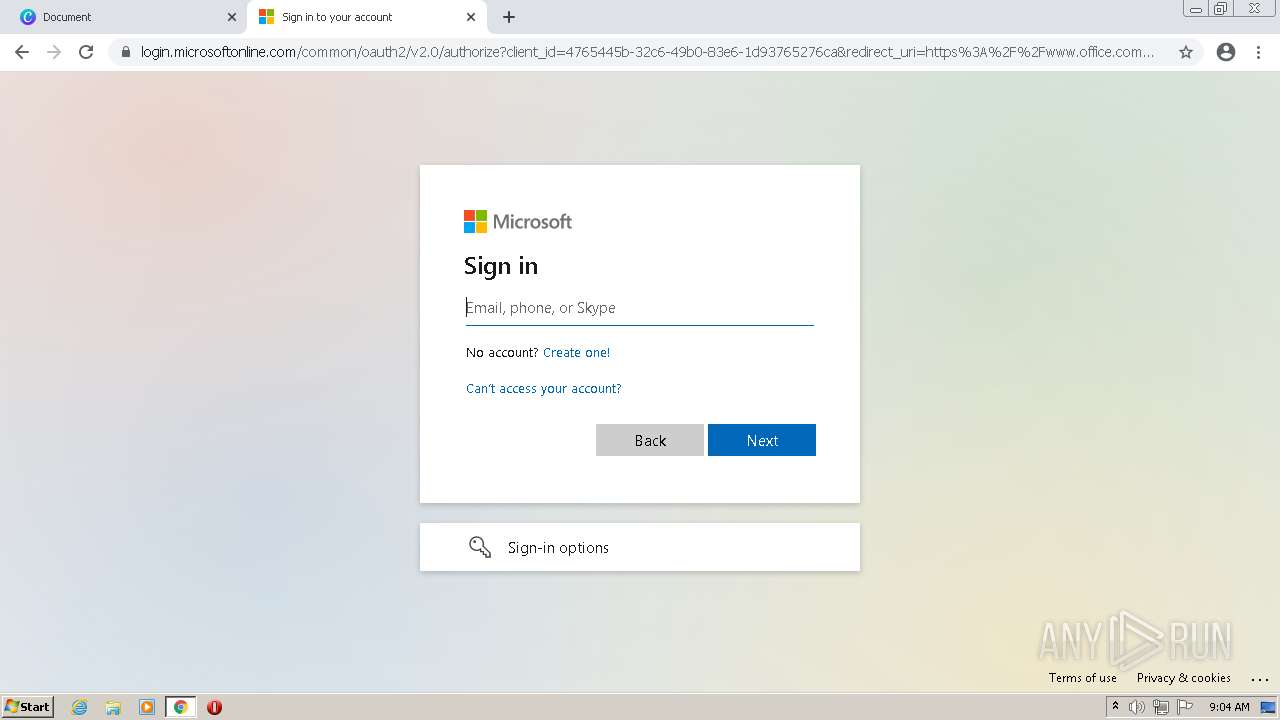
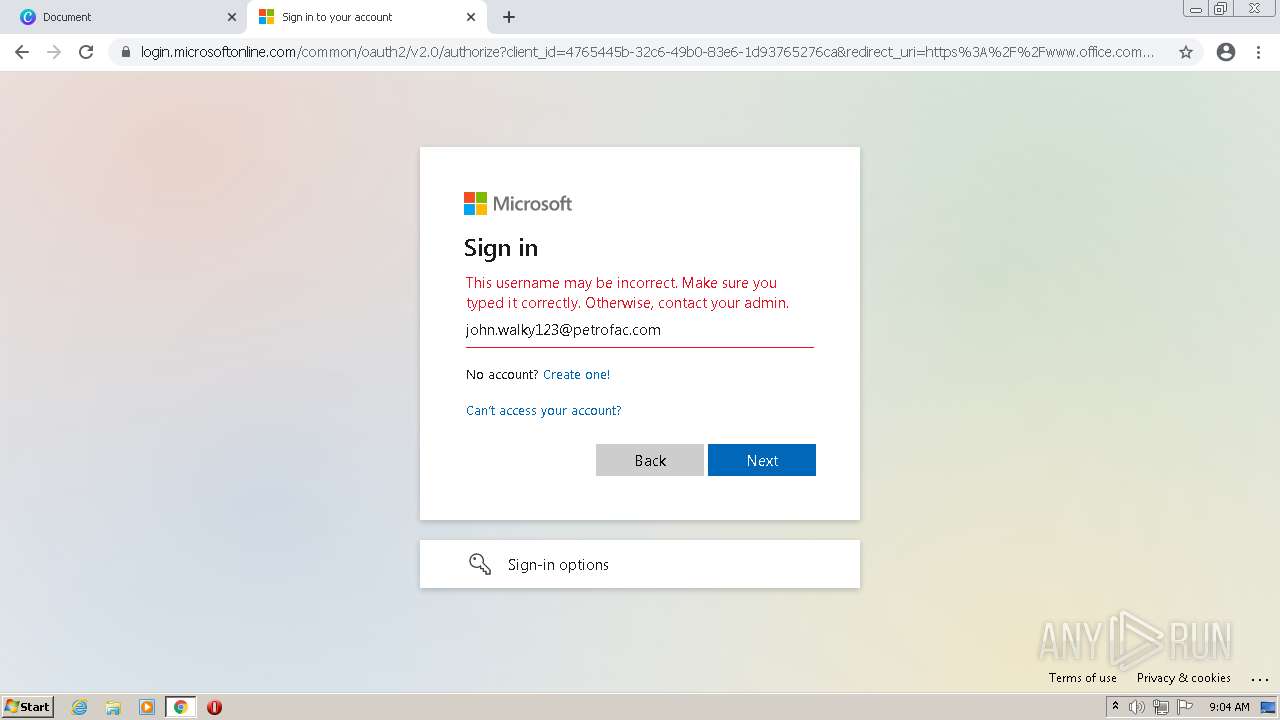
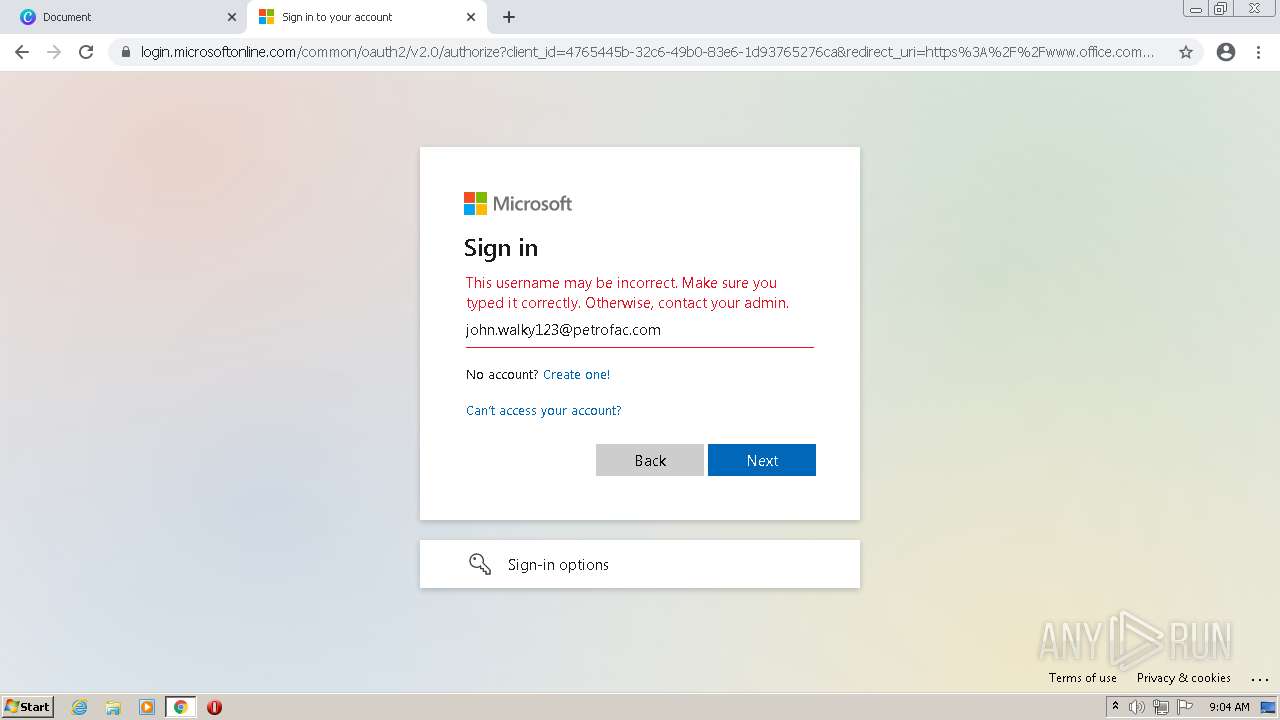
432 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Generic Multibrand NewInjection Phishing Landing Template |
432 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Generic Multibrand NewInjection Phishing Landing Template |
432 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Generic Multibrand NewInjection Phishing Landing Template |
432 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Generic Multibrand NewInjection Phishing Landing Template |
4 ETPRO signatures available at the full report