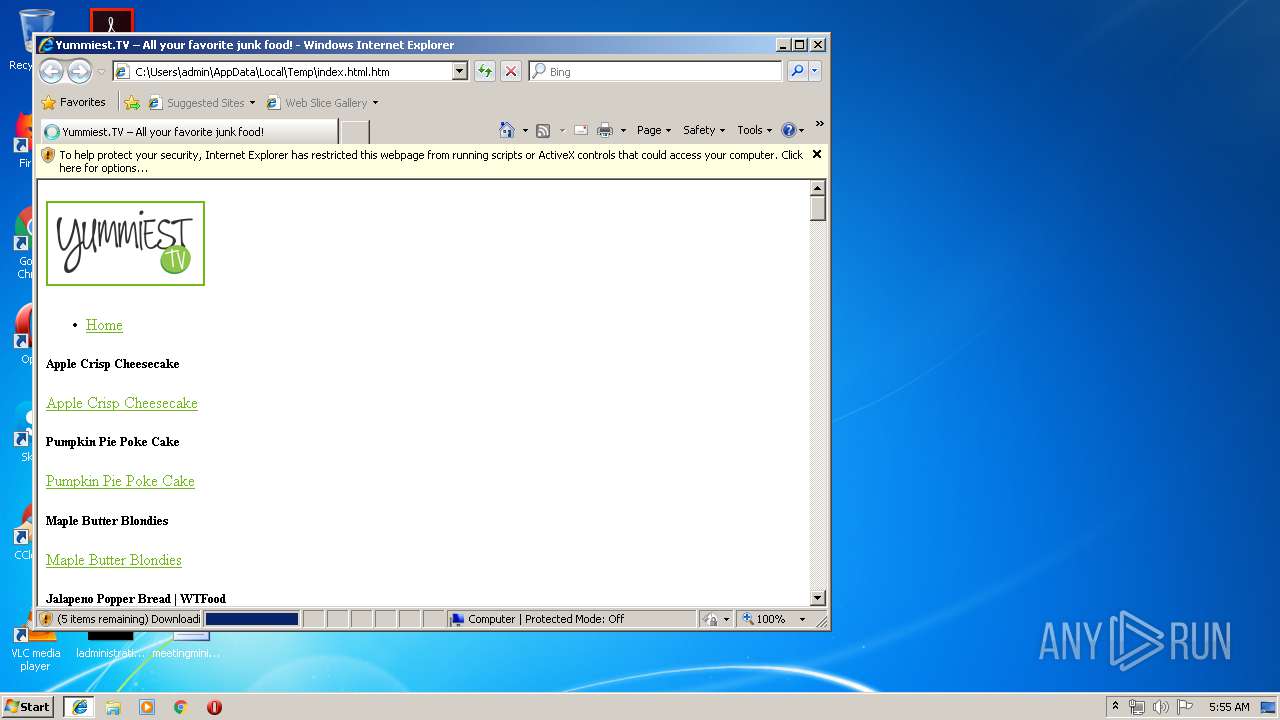
| download: | index.html |
| Full analysis: | https://app.any.run/tasks/ccb5c418-c96a-4693-a4f5-ad67212400b9 |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2019, 04:54:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 81730A0403C7542DF69166FB8CD36AA0 |
| SHA1: | 66EF77AFB688FFDAC4282349426A154039C2568B |
| SHA256: | 8A0E3C746B6D79CA0F9EEA992A07BB909038CC90B4A8454AFFE4B613E18F1F1E |
| SSDEEP: | 768:ctIXjnVeaHpaz5fKvG5jdjRYNIpBdrFqtYRHd+hMF1IoqAhYvBMjDM9xS0wz1Nac:cGXjnV/JalS+tZmyv9wux8Gv/qAhYvBI |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
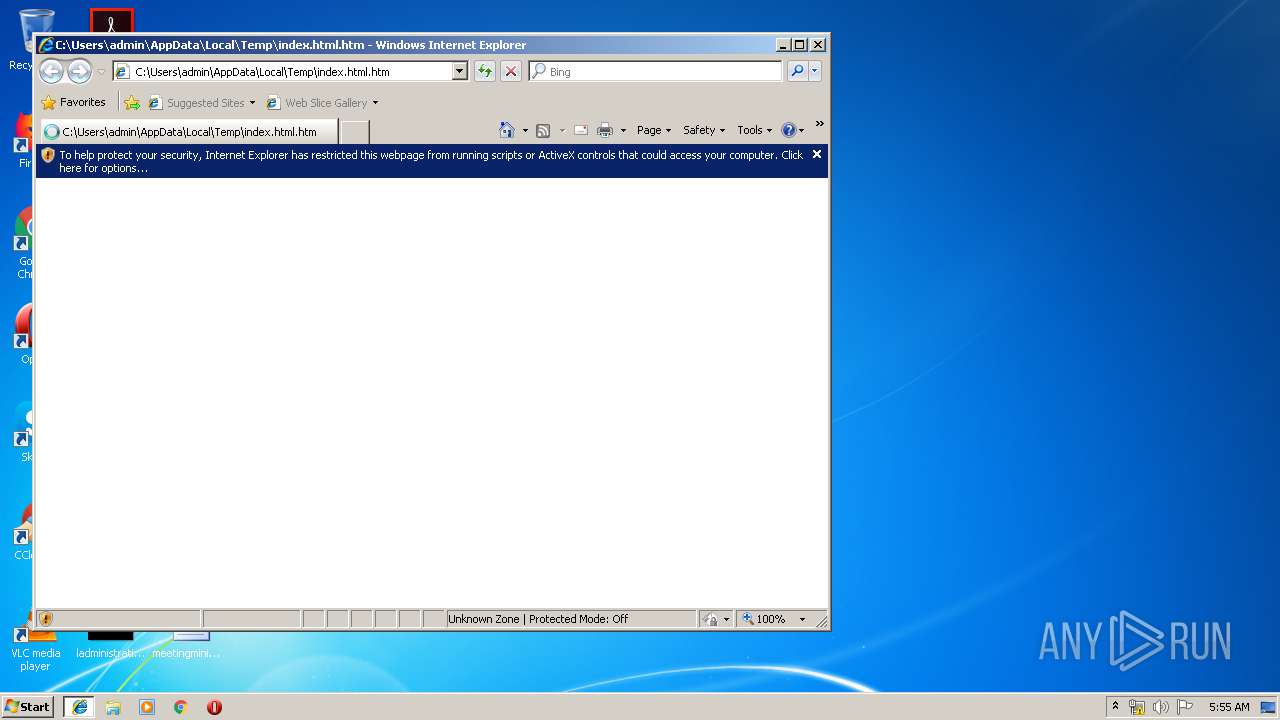
Application launched itself
- iexplore.exe (PID: 3532)
Reads internet explorer settings
- iexplore.exe (PID: 3304)
Changes internet zones settings
- iexplore.exe (PID: 3532)
Reads Internet Cache Settings
- iexplore.exe (PID: 3304)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3304)
Changes settings of System certificates
- iexplore.exe (PID: 3304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| viewport: | width=device-width, initial-scale=1 |
|---|---|
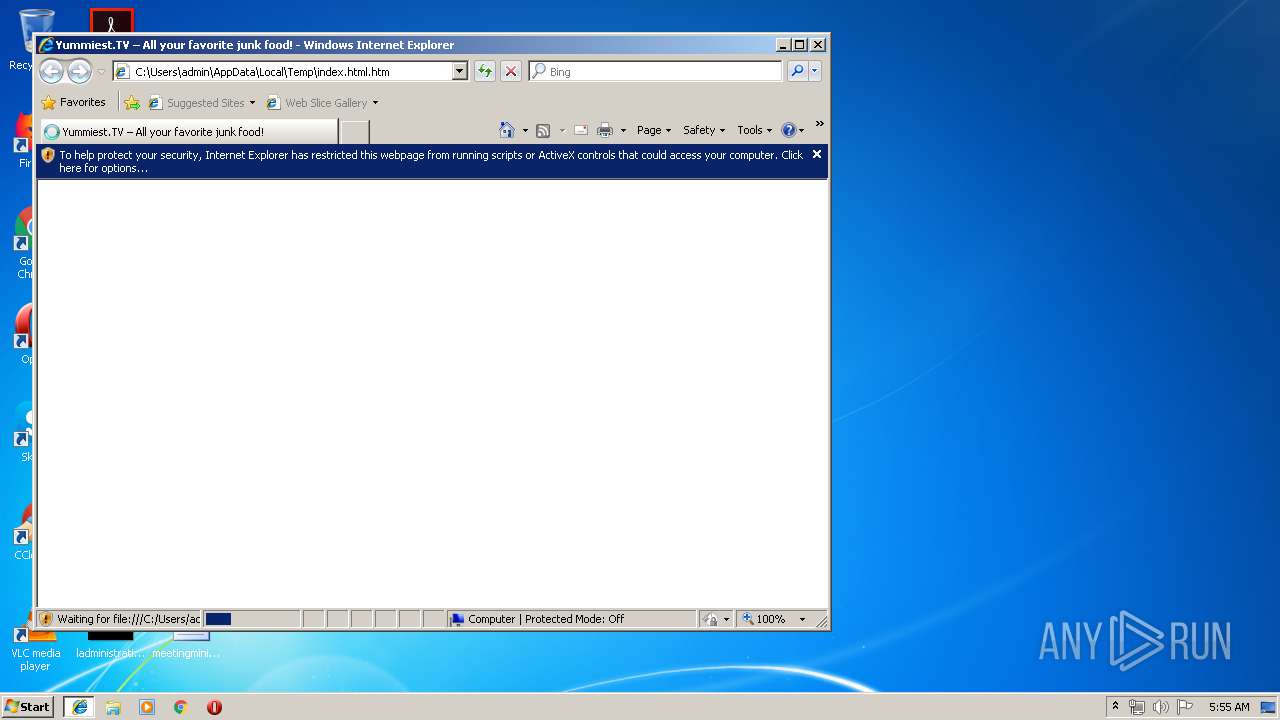
| Title: | Yummiest.TV – All your favorite junk food! |
| Robots: | noindex,follow |
| Generator: | WordPress 4.8.2 |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3304 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3532 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3532 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
383
Read events
299
Write events
79
Delete events
5
Modification events
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {EBAEC3AF-8FF2-11E9-A09E-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307060000001000040037000C003202 | |||
Executable files
0
Suspicious files
0
Text files
26
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\js[1] | text | |
MD5:— | SHA256:— | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\clDWED2b_normal[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\0_q3k2gcmy[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\0_m6bhowx0[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\Nsb_GQi__normal[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\video-lib[1].js | text | |
MD5:— | SHA256:— | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\yummiest.tv-logo-1-e150661667326911[1].png | image | |
MD5:— | SHA256:— | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\Y3fBPnw-_normal[1].jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
18
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3304 | iexplore.exe | GET | 200 | 52.219.116.65:80 | http://vpimg.s3-us-west-1.amazonaws.com/wp-content/uploads/2019/06/15084509/0_1fnyuid0.jpeg | US | image | 173 Kb | shared |
3304 | iexplore.exe | GET | 200 | 52.219.116.65:80 | http://vpimg.s3-us-west-1.amazonaws.com/wp-content/uploads/2019/06/15084507/0_m6bhowx0.jpeg | US | image | 164 Kb | shared |
3304 | iexplore.exe | GET | 200 | 52.219.116.65:80 | http://vpimg.s3-us-west-1.amazonaws.com/wp-content/uploads/2019/06/15084502/0_gewkv2go.jpeg | US | image | 138 Kb | shared |
3304 | iexplore.exe | GET | 200 | 52.219.116.65:80 | http://vpimg.s3-us-west-1.amazonaws.com/wp-content/uploads/2019/06/15084505/0_q3k2gcmy.jpeg | US | image | 147 Kb | shared |
3304 | iexplore.exe | GET | 200 | 52.219.116.65:80 | http://vpimg.s3-us-west-1.amazonaws.com/wp-content/uploads/2019/06/15084514/0_bm08ug69.jpeg | US | image | 57.3 Kb | shared |
3304 | iexplore.exe | GET | 200 | 52.219.116.65:80 | http://vpimg.s3-us-west-1.amazonaws.com/wp-content/uploads/2019/06/15084504/0_8y8wq0q6.jpeg | US | image | 143 Kb | shared |
3304 | iexplore.exe | GET | 200 | 52.219.116.65:80 | http://vpimg.s3-us-west-1.amazonaws.com/wp-content/uploads/2019/06/15084508/0_tmlgeq3k.jpeg | US | image | 158 Kb | shared |
3304 | iexplore.exe | GET | 200 | 52.219.116.65:80 | http://vpimg.s3-us-west-1.amazonaws.com/wp-content/uploads/2019/06/15084510/0_jgpbrktb.jpeg | US | image | 126 Kb | shared |
3304 | iexplore.exe | GET | 200 | 52.219.116.65:80 | http://vpimg.s3-us-west-1.amazonaws.com/wp-content/uploads/2019/06/15084516/0_969v6jjg.jpeg | US | image | 65.2 Kb | shared |
3304 | iexplore.exe | GET | 200 | 52.219.116.65:80 | http://vpimg.s3-us-west-1.amazonaws.com/wp-content/uploads/2019/06/15084518/0_6rhvlvpo.jpeg | US | image | 137 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3304 | iexplore.exe | 52.219.24.177:443 | s3-us-west-1.amazonaws.com | Amazon.com, Inc. | US | unknown |
3532 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4 | System | 172.217.23.138:445 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3304 | iexplore.exe | 216.58.207.72:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3304 | iexplore.exe | 93.184.220.70:443 | pbs.twimg.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3304 | iexplore.exe | 52.219.116.65:80 | vpimg.s3-us-west-1.amazonaws.com | — | US | shared |
— | — | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3304 | iexplore.exe | 192.229.233.25:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4 | System | 172.217.23.138:139 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s3-us-west-1.amazonaws.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
platform.twitter.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
vpimg.s3-us-west-1.amazonaws.com |
| shared |
pbs.twimg.com |
| whitelisted |