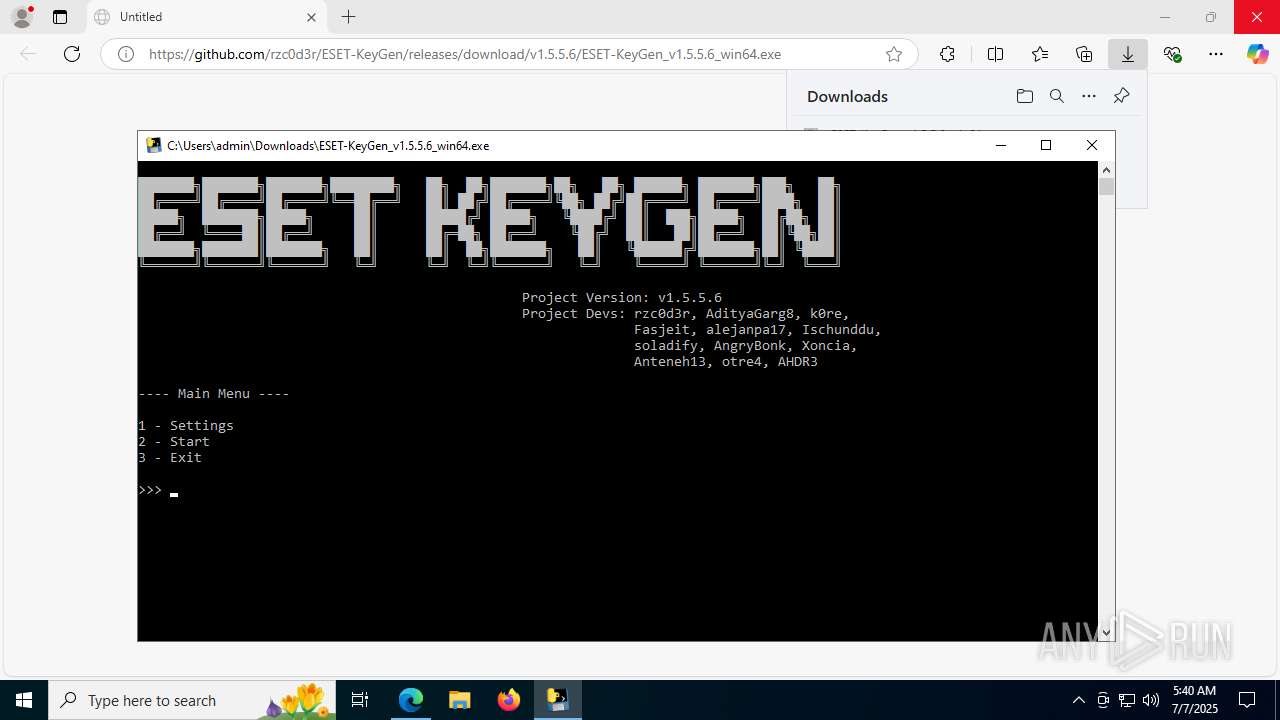
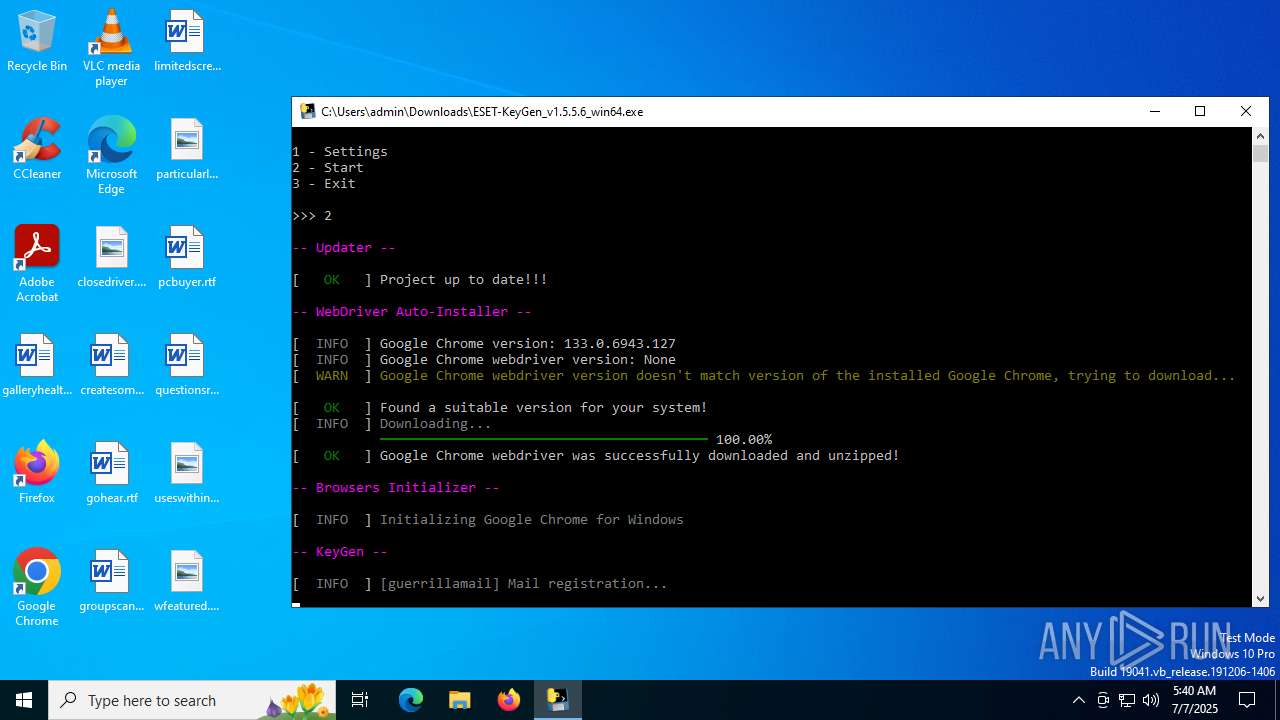
| URL: | https://github.com/rzc0d3r/ESET-KeyGen/releases/download/v1.5.5.6/ESET-KeyGen_v1.5.5.6_win64.exe |
| Full analysis: | https://app.any.run/tasks/8eb70964-fb30-426b-aca2-38177e54ca40 |
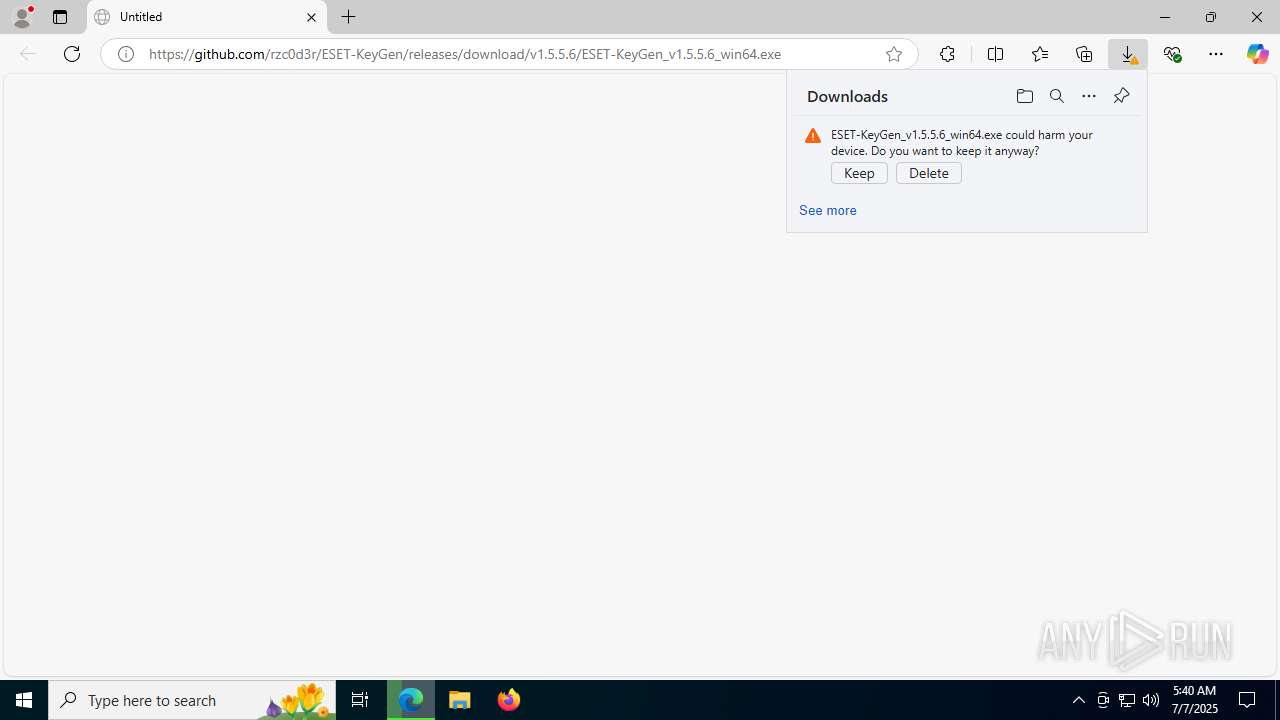
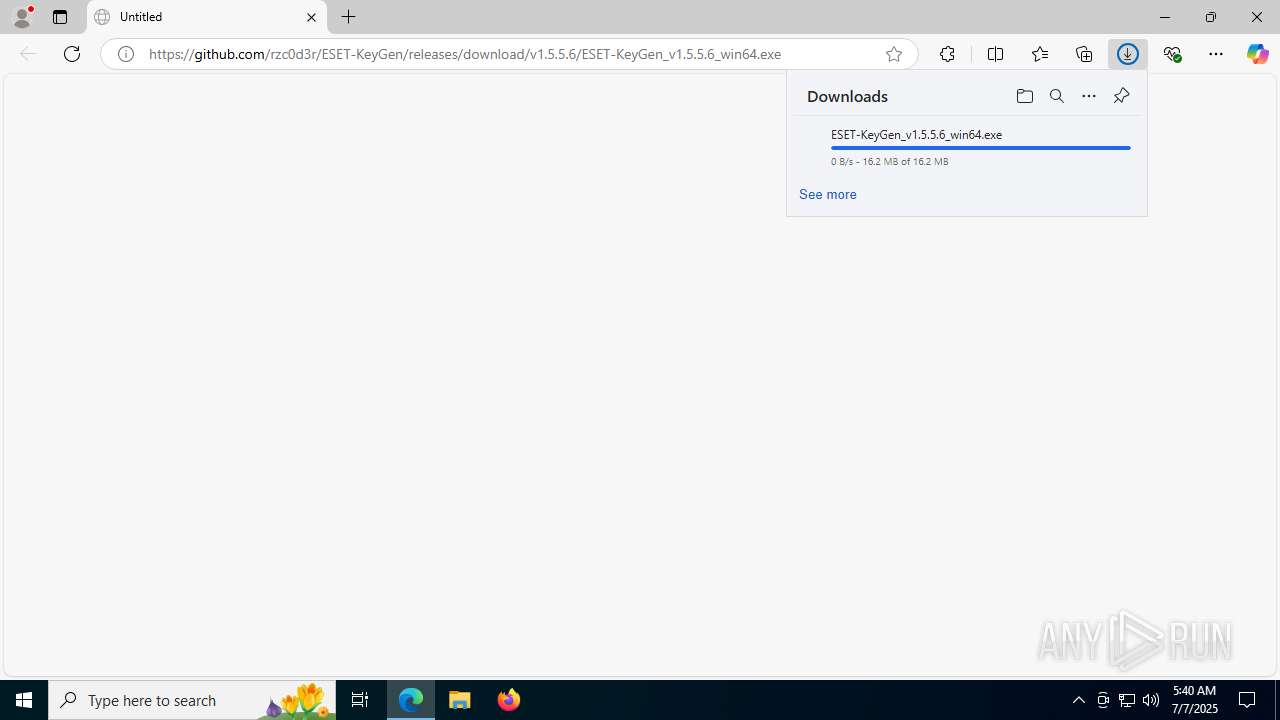
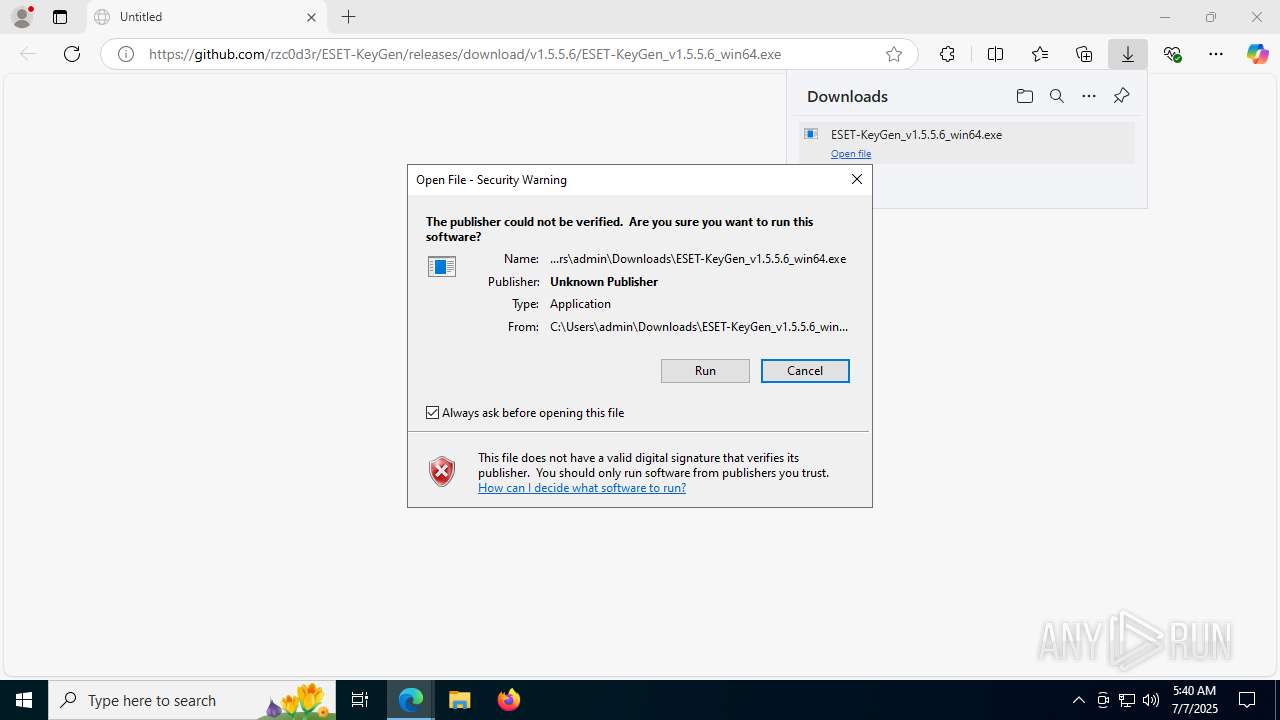
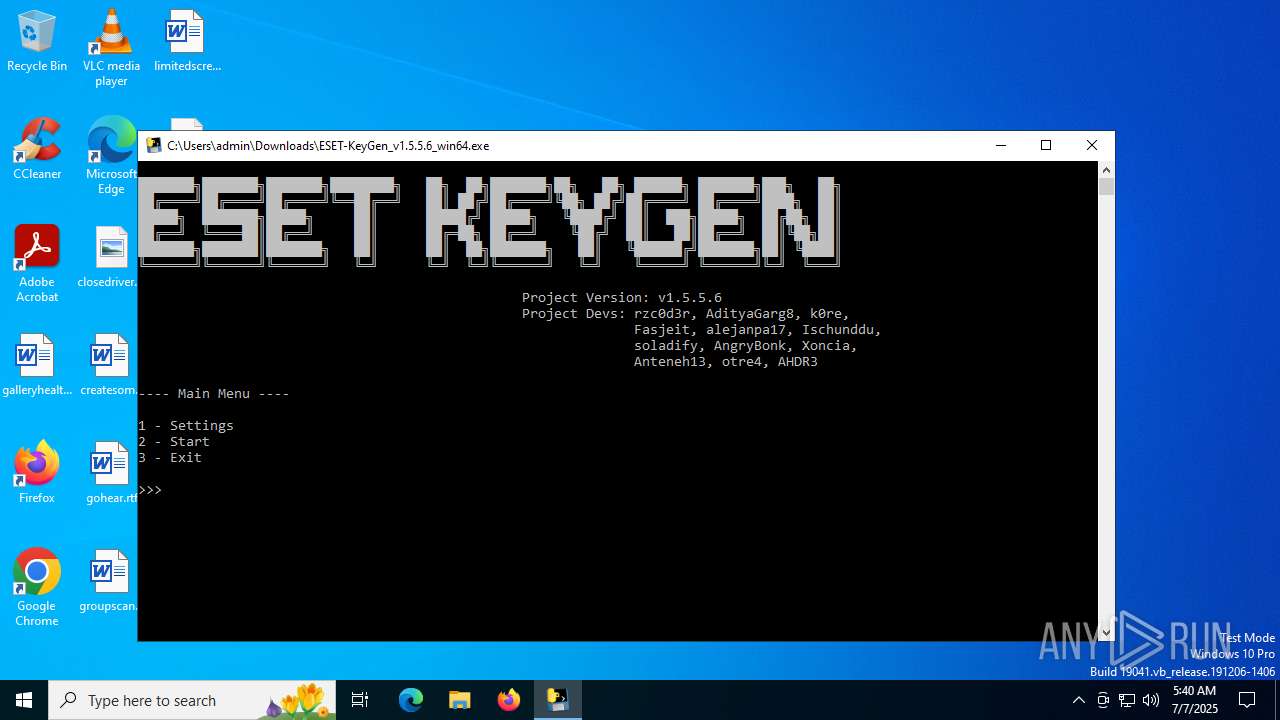
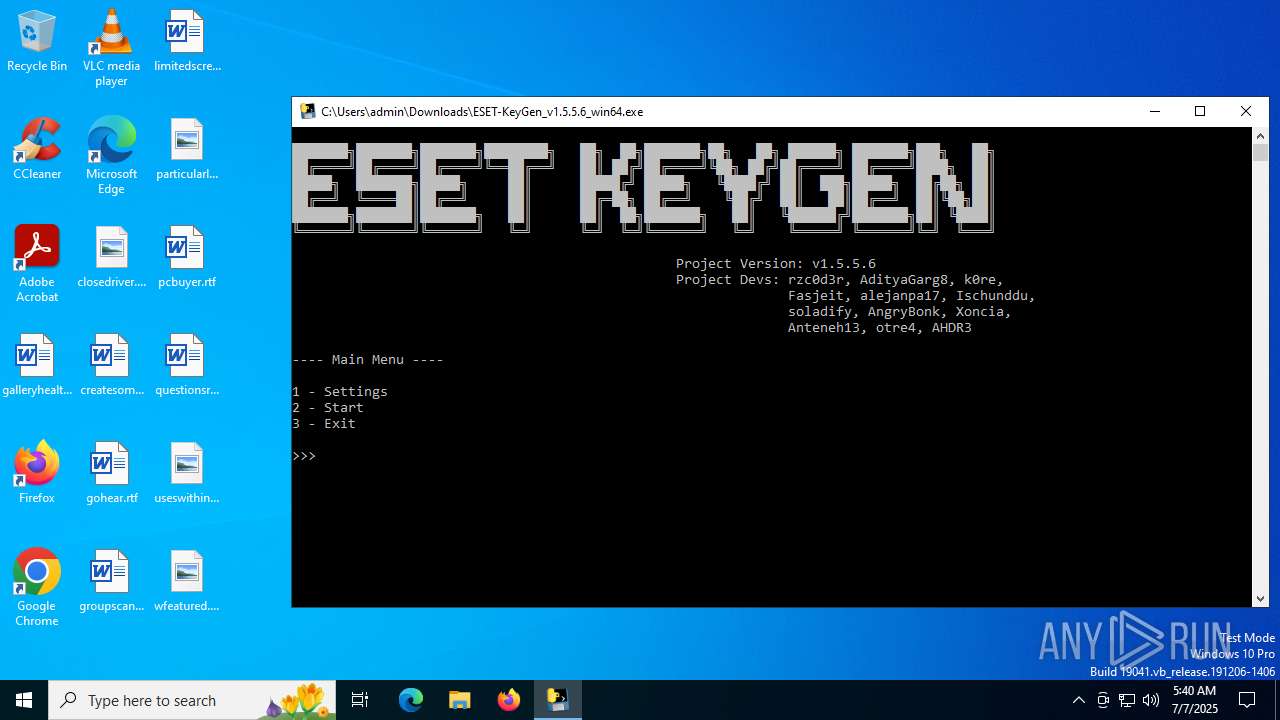
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2025, 05:39:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0CB7281B6F9EB7CDCCF7330E63D658EC |
| SHA1: | C982D1D8CF041C5B944DD745628F96F9571FC415 |
| SHA256: | 89FF38E939DC98900559FB47746B2B6E97DB839E559C81574DBAC6E270A93EAA |
| SSDEEP: | 3:N8tEdnurQKqjLBJMkCmeeGwdjL6TUCeYN:2u4rQX/MseeG06T3eYN |
MALICIOUS
No malicious indicators.SUSPICIOUS
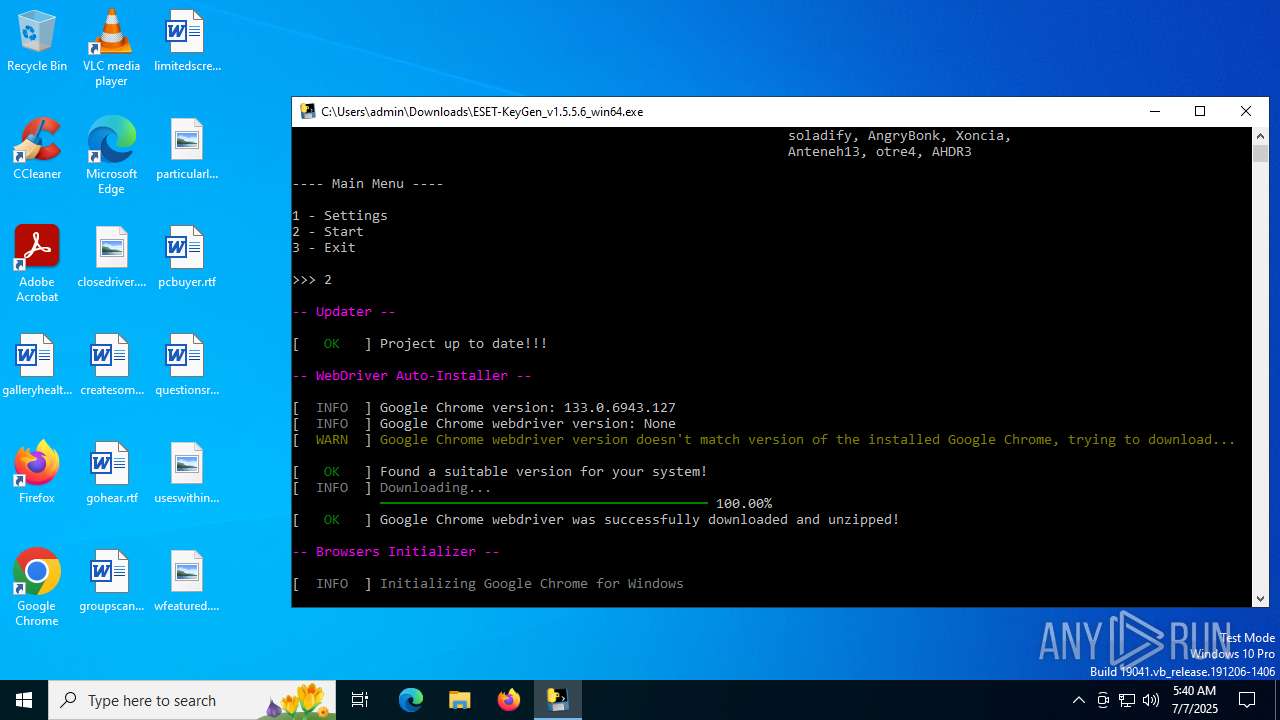
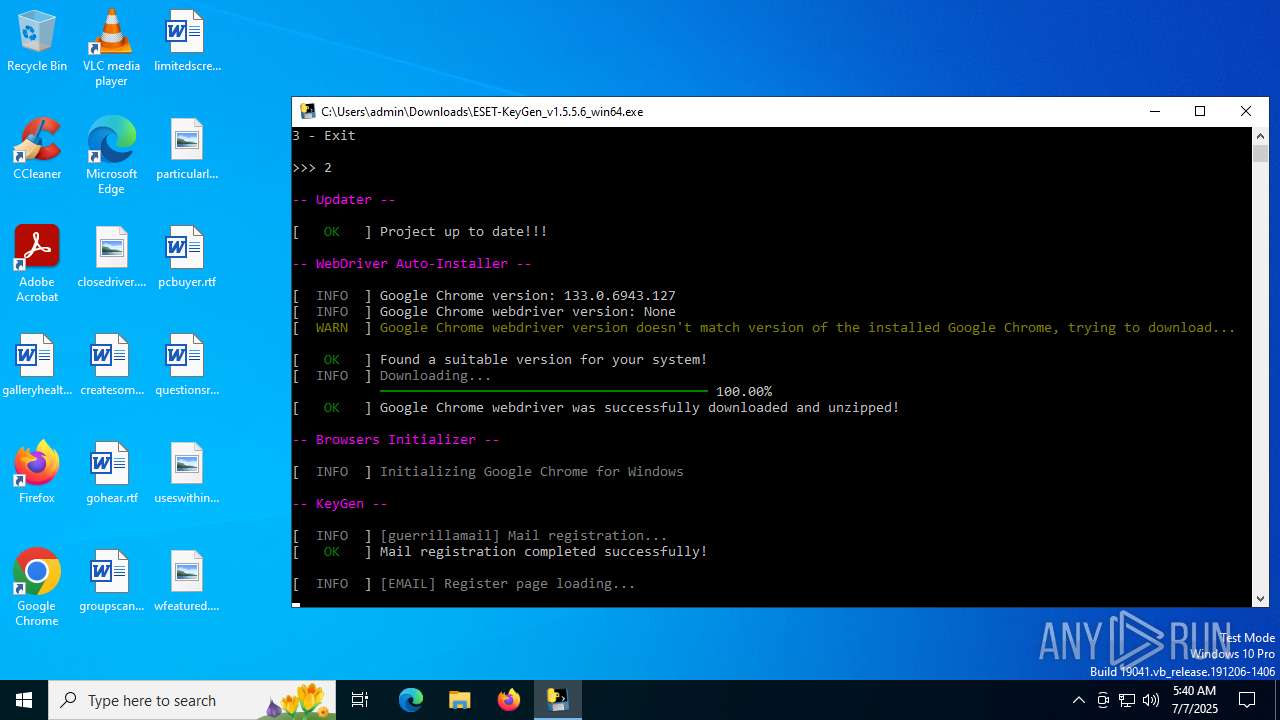
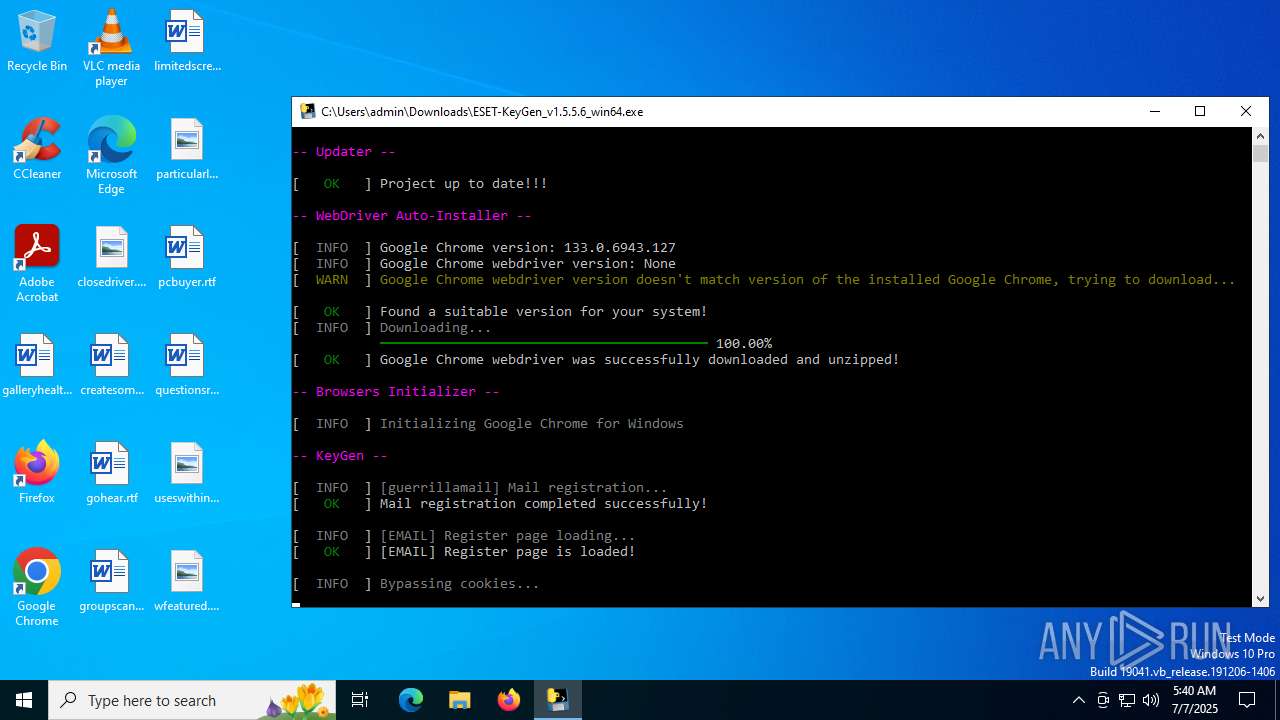
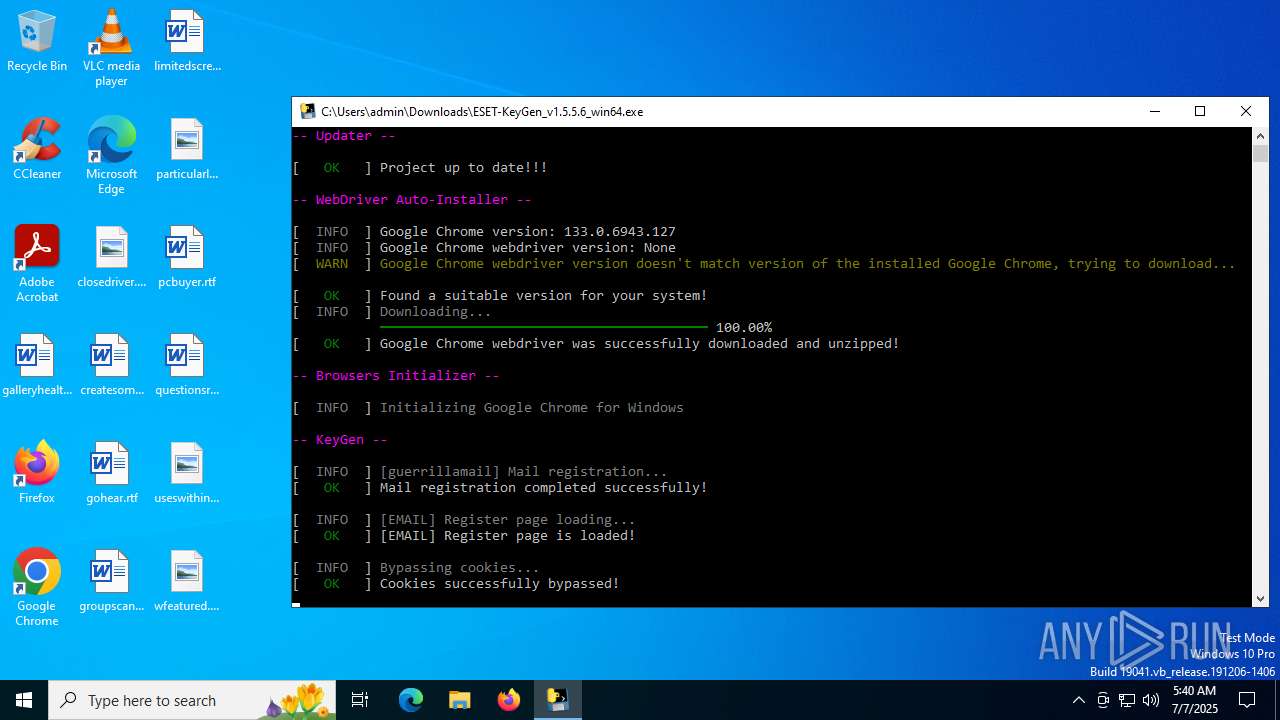
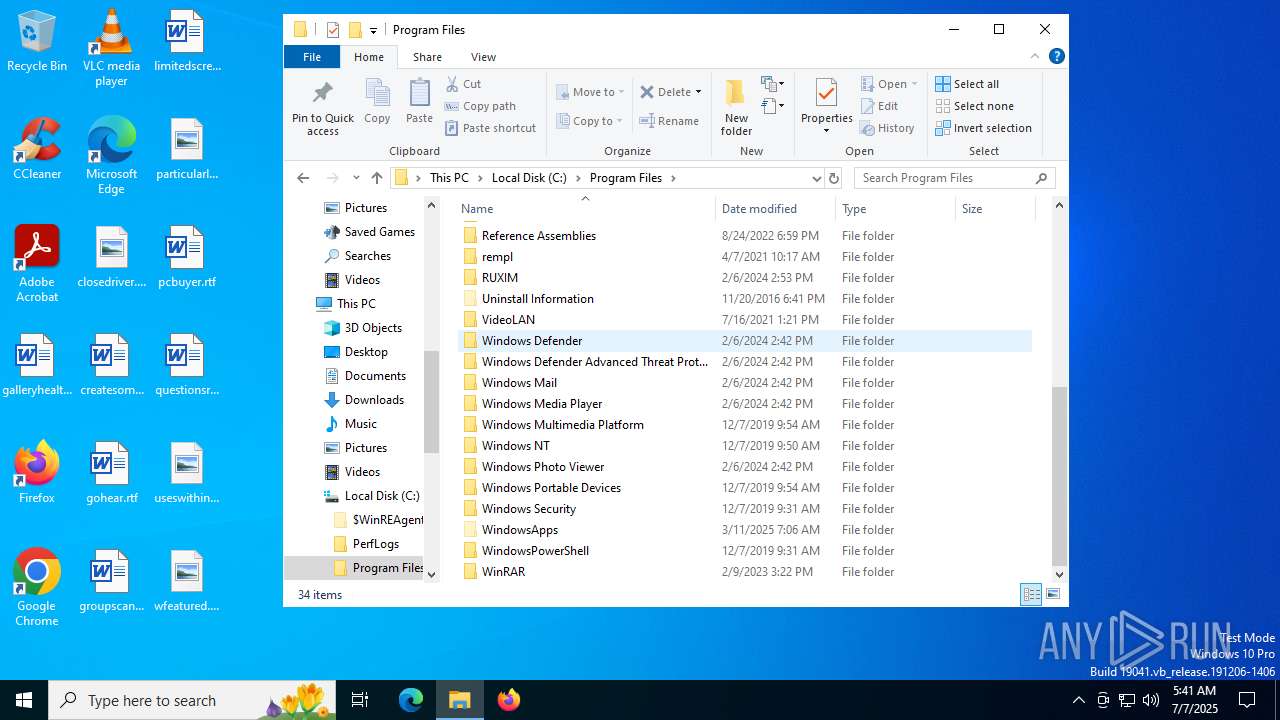
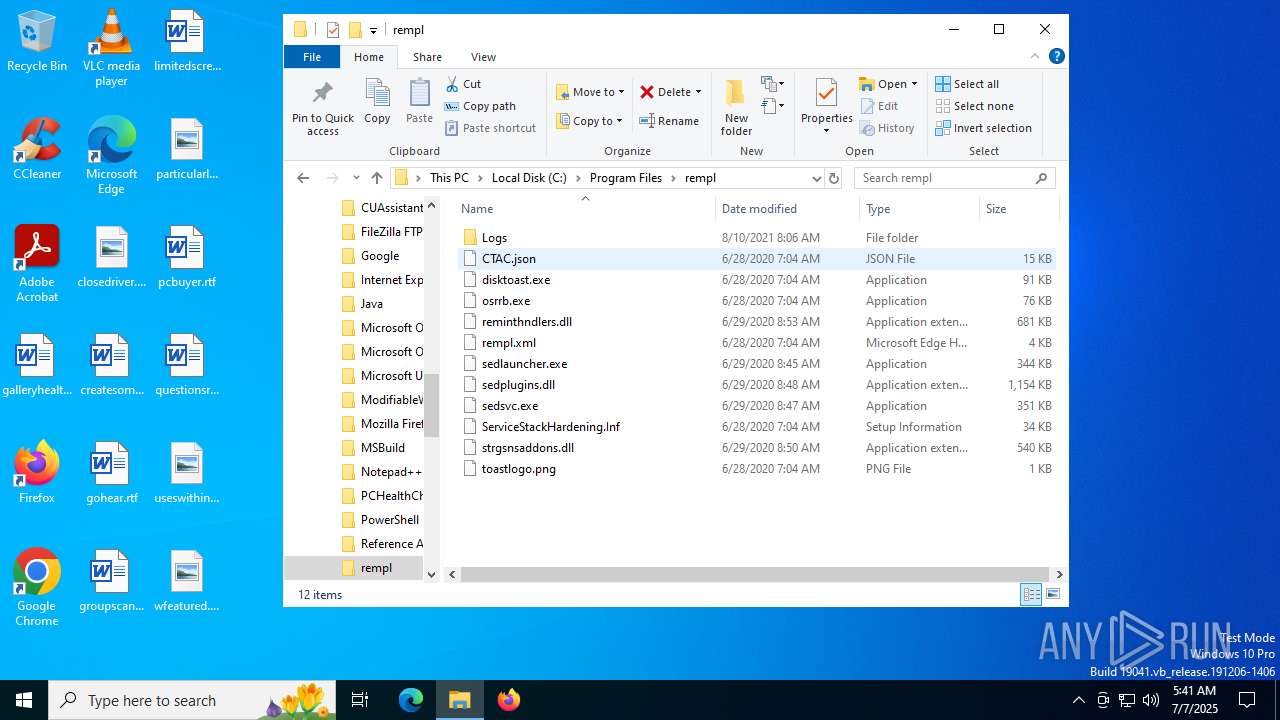
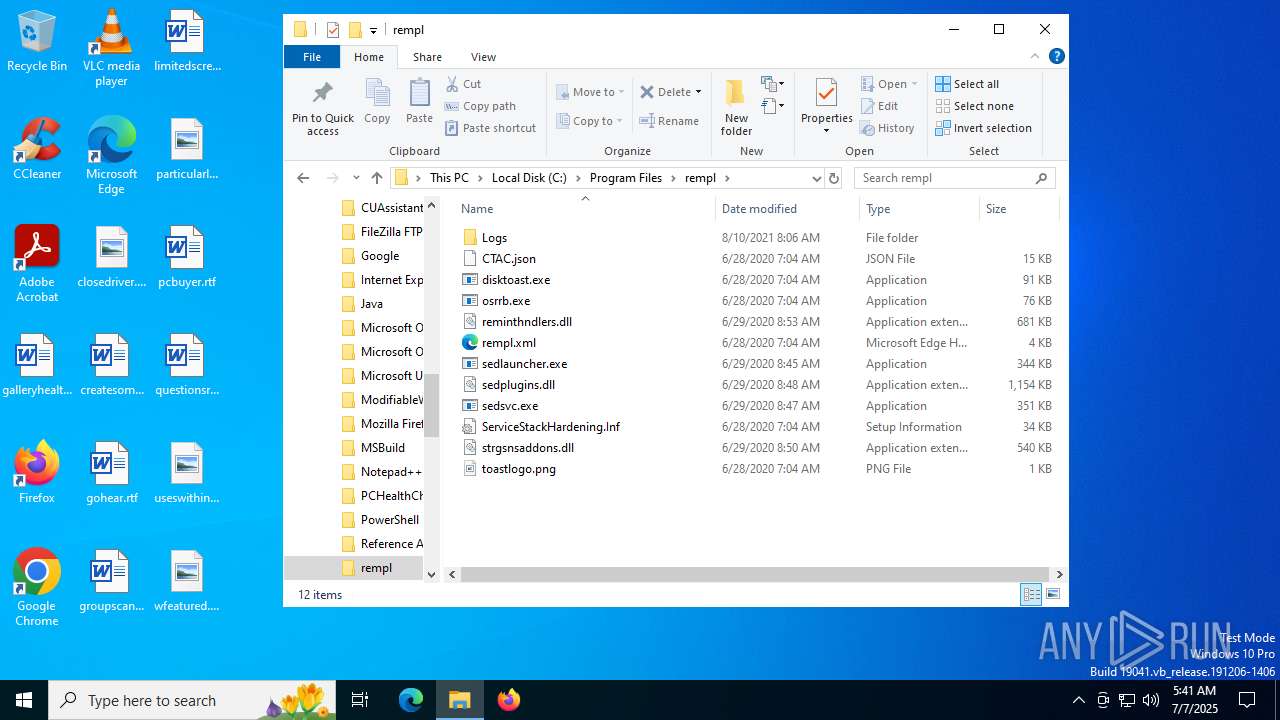
Executable content was dropped or overwritten
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8020)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8084)
The process drops C-runtime libraries
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8020)
Process drops python dynamic module
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8020)
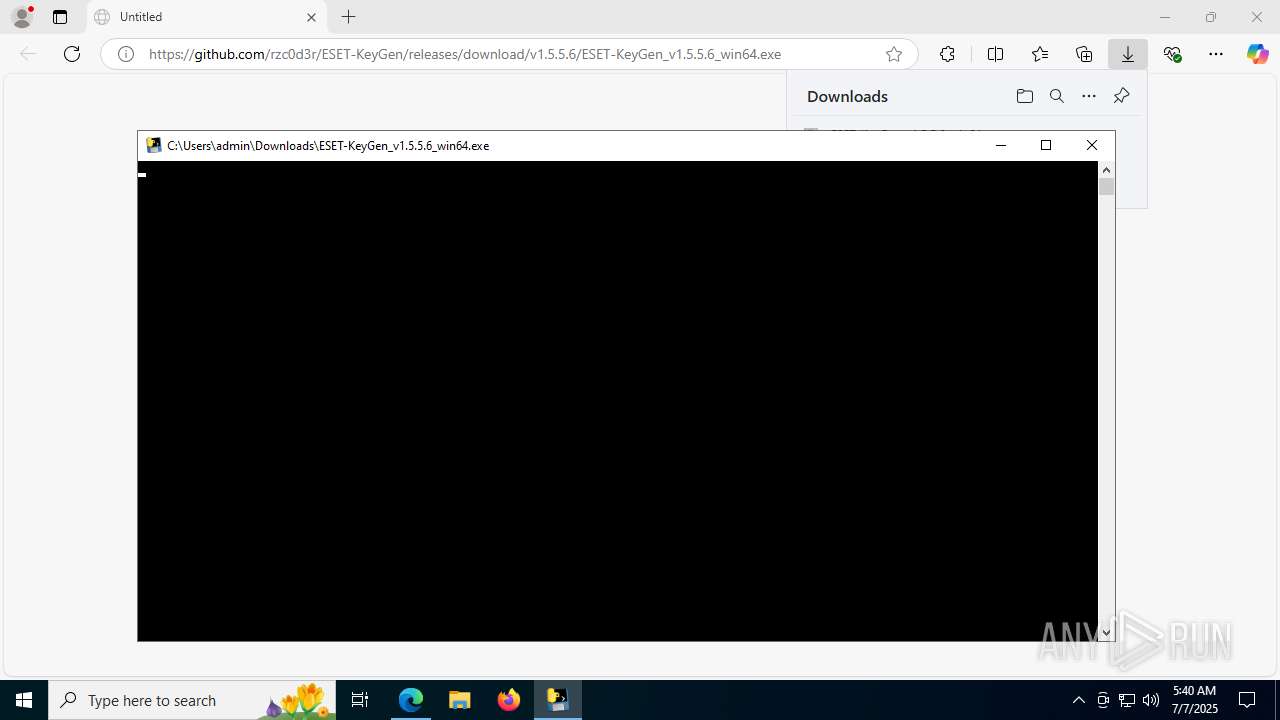
Application launched itself
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8020)
Process drops legitimate windows executable
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8020)
Loads Python modules
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8084)
Starts CMD.EXE for commands execution
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8084)
INFO
Checks supported languages
- identity_helper.exe (PID: 7452)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8020)
- identity_helper.exe (PID: 5436)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8084)
- chromedriver.exe (PID: 6840)
Executable content was dropped or overwritten
- msedge.exe (PID: 2192)
- msedge.exe (PID: 1800)
Application launched itself
- msedge.exe (PID: 1800)
- msedge.exe (PID: 2996)
- chrome.exe (PID: 7212)
Reads the computer name
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8020)
- identity_helper.exe (PID: 7452)
- identity_helper.exe (PID: 5436)
- chromedriver.exe (PID: 6840)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8084)
Reads Environment values
- identity_helper.exe (PID: 7452)
- identity_helper.exe (PID: 5436)
Create files in a temporary directory
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8020)
- chromedriver.exe (PID: 6840)
Drops encrypted JS script (Microsoft Script Encoder)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8084)
PyInstaller has been detected (YARA)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8020)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8084)
The sample compiled with english language support
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8020)
Reads the machine GUID from the registry
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8084)
Checks operating system version
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8084)
Checks proxy server information
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8084)
- slui.exe (PID: 7520)
Reads the software policy settings
- slui.exe (PID: 7520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
215
Monitored processes
73
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 868 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4800,i,15680089109984781589,13920026214062467901,262144 --variations-seed-version --mojo-platform-channel-handle=4824 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 952 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | ESET-KeyGen_v1.5.5.6_win64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 952 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4388,i,15680089109984781589,13920026214062467901,262144 --variations-seed-version --mojo-platform-channel-handle=4888 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir6840_2073762234" --field-trial-handle=5916,i,8065664899498462297,2652296665896581669,262144 --disable-features=PaintHolding --variations-seed-version --log-level=3 --mojo-platform-channel-handle=5620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir6840_2073762234" --field-trial-handle=4836,i,8065664899498462297,2652296665896581669,262144 --disable-features=PaintHolding --variations-seed-version --log-level=3 --mojo-platform-channel-handle=5032 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1700 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2416,i,15626568572407095965,7165095799039791503,262144 --variations-seed-version --mojo-platform-channel-handle=2420 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir6840_2073762234" --field-trial-handle=5760,i,8065664899498462297,2652296665896581669,262144 --disable-features=PaintHolding --variations-seed-version --log-level=3 --mojo-platform-channel-handle=5776 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/rzc0d3r/ESET-KeyGen/releases/download/v1.5.5.6/ESET-KeyGen_v1.5.5.6_win64.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir6840_2073762234" --field-trial-handle=5804,i,8065664899498462297,2652296665896581669,262144 --disable-features=PaintHolding --variations-seed-version --log-level=3 --mojo-platform-channel-handle=5800 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2224,i,15626568572407095965,7165095799039791503,262144 --variations-seed-version --mojo-platform-channel-handle=2660 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
16 353
Read events
16 322
Write events
30
Delete events
1
Modification events
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B643328FE6972F00 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459518 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6F58BE1D-5599-4F86-AECB-8905A79037A9} | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CF63498FE6972F00 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
90
Suspicious files
569
Text files
135
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17598a.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17598a.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF17598a.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1759a9.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1759b8.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
129
DNS requests
136
Threats
83
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2192 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:d5tmF43G4959eiItw9qZGEK6zjk_SLzPBTd9OI4T3jg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7260 | svchost.exe | HEAD | 200 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1751988851&P2=404&P3=2&P4=Q27GvszDAZIxdG%2for6pQwyLuXEpyaT3veKDFliC6sqQE5JFsFsrzVCvi0Q7ajRxnBCcOPP9riA0ez5qyH%2bIntA%3d%3d | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7260 | svchost.exe | GET | 200 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1751988851&P2=404&P3=2&P4=Q27GvszDAZIxdG%2for6pQwyLuXEpyaT3veKDFliC6sqQE5JFsFsrzVCvi0Q7ajRxnBCcOPP9riA0ez5qyH%2bIntA%3d%3d | unknown | — | — | whitelisted |
2552 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7340 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6948 | chrome.exe | GET | 200 | 216.58.212.142:80 | http://clients2.google.com/time/1/current?cup2key=8:wvOkHGAdAw2_A5uEB73kApJujWMNkTJH8QTHM0XTM3U&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7260 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751988835&P2=404&P3=2&P4=fyEHnhFpOP56YM8nST9r%2bCOy8jHLbGO5FExg8AZsL7%2bKlP8ebCjic%2f9RBRVKOAgiMI9itPEpGVO4w1AuMicvXQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5708 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2192 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2192 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2192 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
2192 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2192 | msedge.exe | 104.126.37.169:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6948 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6948 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6948 | chrome.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6948 | chrome.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6948 | chrome.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6948 | chrome.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6948 | chrome.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6948 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6948 | chrome.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6948 | chrome.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\scoped_dir6840_2073762234 directory exists )
|