| File name: | 084d9db2736619891e99f16b615dd050N.exe |
| Full analysis: | https://app.any.run/tasks/6be223a1-742c-4f3d-837a-9bd3882abe1c |
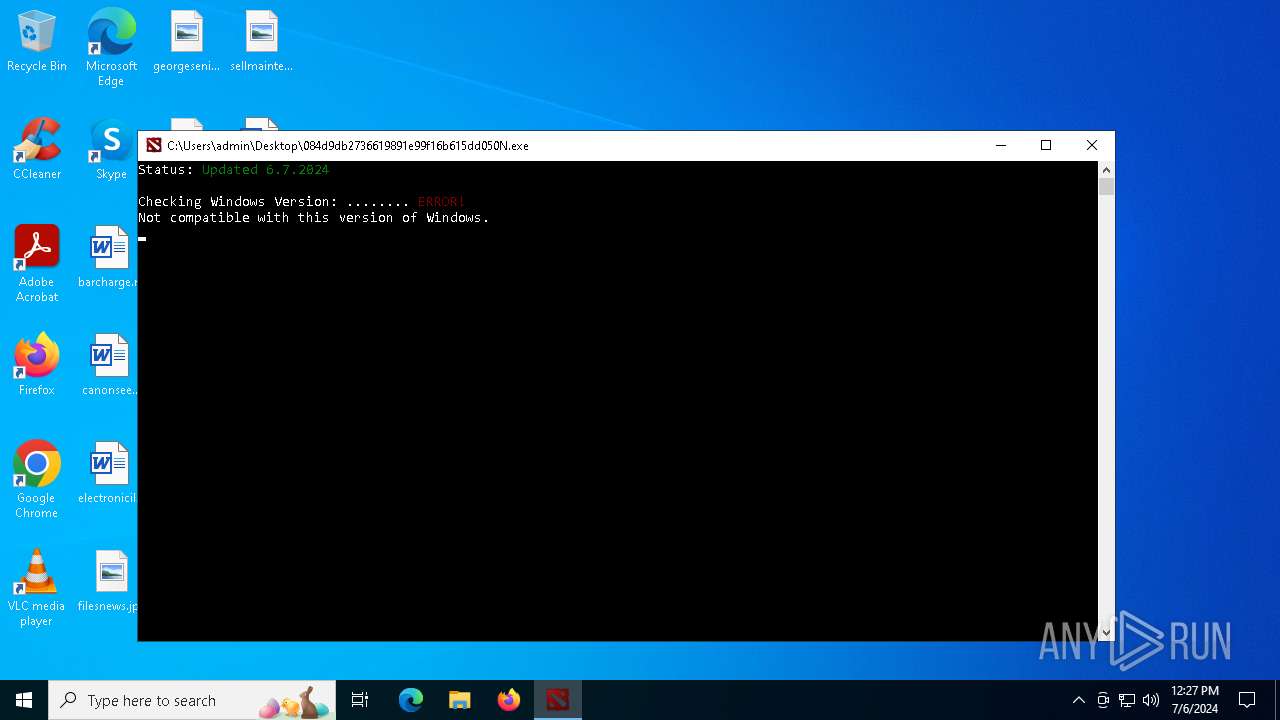
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2024, 12:26:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 084D9DB2736619891E99F16B615DD050 |
| SHA1: | F33EF6963EC3EE0712A366711EE4AEF5B6A55F24 |
| SHA256: | 89DBA9C97B5D68063A51C8FE1049D8E12FB349CBDC6102CBF1EC3976381964C8 |
| SSDEEP: | 98304:3+NZWrp1hgbd2oHt6D1c4qnu3WUm2i2t3hZL072QxDrFPMB81jnxv3rYl4n4IEKO:/3j |
MALICIOUS
Drops the executable file immediately after the start
- 084d9db2736619891e99f16b615dd050N.exe (PID: 4764)
SUSPICIOUS
Executes application which crashes
- 084d9db2736619891e99f16b615dd050N.exe (PID: 4764)
- 084d9db2736619891e99f16b615dd050N.exe (PID: 5004)
Reads security settings of Internet Explorer
- 084d9db2736619891e99f16b615dd050N.exe (PID: 5004)
Checks Windows Trust Settings
- 084d9db2736619891e99f16b615dd050N.exe (PID: 5004)
Executable content was dropped or overwritten
- 084d9db2736619891e99f16b615dd050N.exe (PID: 4764)
INFO
Checks supported languages
- 084d9db2736619891e99f16b615dd050N.exe (PID: 4764)
- 084d9db2736619891e99f16b615dd050N.exe (PID: 5004)
Creates files in the program directory
- 084d9db2736619891e99f16b615dd050N.exe (PID: 5004)
Creates files or folders in the user directory
- WerFault.exe (PID: 2268)
- WerFault.exe (PID: 5816)
- WerFault.exe (PID: 4840)
- WerFault.exe (PID: 1188)
- WerFault.exe (PID: 240)
- WerFault.exe (PID: 3188)
- WerFault.exe (PID: 5504)
- WerFault.exe (PID: 3840)
- WerFault.exe (PID: 740)
- WerFault.exe (PID: 4800)
- WerFault.exe (PID: 2716)
Reads the computer name
- 084d9db2736619891e99f16b615dd050N.exe (PID: 5004)
Checks proxy server information
- 084d9db2736619891e99f16b615dd050N.exe (PID: 5004)
Reads the machine GUID from the registry
- 084d9db2736619891e99f16b615dd050N.exe (PID: 5004)
Reads the software policy settings
- 084d9db2736619891e99f16b615dd050N.exe (PID: 5004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1971:05:16 00:00:00+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 3.4 |
| CodeSize: | 83008 |
| InitializedDataSize: | 816128 |
| UninitializedDataSize: | 10212 |
| EntryPoint: | 0x153e0 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Total processes
148
Monitored processes
15
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5004 -s 832 | C:\Windows\SysWOW64\WerFault.exe | — | 084d9db2736619891e99f16b615dd050N.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 740 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5004 -s 1536 | C:\Windows\SysWOW64\WerFault.exe | — | 084d9db2736619891e99f16b615dd050N.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1004 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 084d9db2736619891e99f16b615dd050N.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5004 -s 724 | C:\Windows\SysWOW64\WerFault.exe | — | 084d9db2736619891e99f16b615dd050N.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 4764 -s 388 | C:\Windows\SysWOW64\WerFault.exe | — | 084d9db2736619891e99f16b615dd050N.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2416 | "C:\Users\admin\Desktop\084d9db2736619891e99f16b615dd050N.exe" | C:\Users\admin\Desktop\084d9db2736619891e99f16b615dd050N.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2716 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5004 -s 1144 | C:\Windows\SysWOW64\WerFault.exe | — | 084d9db2736619891e99f16b615dd050N.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3188 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5004 -s 724 | C:\Windows\SysWOW64\WerFault.exe | — | 084d9db2736619891e99f16b615dd050N.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3840 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5004 -s 1460 | C:\Windows\SysWOW64\WerFault.exe | — | 084d9db2736619891e99f16b615dd050N.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4764 | "C:\Users\admin\Desktop\084d9db2736619891e99f16b615dd050N.exe" | C:\Users\admin\Desktop\084d9db2736619891e99f16b615dd050N.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
26 241
Read events
26 164
Write events
44
Delete events
33
Modification events
| (PID) Process: | (2268) WerFault.exe | Key: | \REGISTRY\A\{01832d3a-9f77-b384-b71a-61d57f9581b7}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (2268) WerFault.exe | Key: | \REGISTRY\A\{01832d3a-9f77-b384-b71a-61d57f9581b7}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5816) WerFault.exe | Key: | \REGISTRY\A\{bb962d2e-7061-1002-6f38-2c4c18d11110}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (5816) WerFault.exe | Key: | \REGISTRY\A\{bb962d2e-7061-1002-6f38-2c4c18d11110}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4840) WerFault.exe | Key: | \REGISTRY\A\{66d97b13-60a7-ced6-b4ab-ec326108afa2}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (4840) WerFault.exe | Key: | \REGISTRY\A\{66d97b13-60a7-ced6-b4ab-ec326108afa2}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1188) WerFault.exe | Key: | \REGISTRY\A\{66d97b13-60a7-ced6-b4ab-ec326108afa2}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (1188) WerFault.exe | Key: | \REGISTRY\A\{66d97b13-60a7-ced6-b4ab-ec326108afa2}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3188) WerFault.exe | Key: | \REGISTRY\A\{66d97b13-60a7-ced6-b4ab-ec326108afa2}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (3188) WerFault.exe | Key: | \REGISTRY\A\{66d97b13-60a7-ced6-b4ab-ec326108afa2}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
2
Suspicious files
4
Text files
22
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2268 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_084d9db273661989_12b59fae99827a9294aaac4797493ecb4fbfdeac_e8d65991_49c575ac-41fb-432b-806a-5a6c157bfe46\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5816 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_084d9db273661989_12b59fae99827a9294aaac4797493ecb4fbfdeac_e8d65991_45c7f73b-a7d9-485d-b8b5-9a968d74cd1f\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4840 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_084d9db273661989_8ce13d66dc60478d745a4d6f8ca0dc64271e8bb_e8d65991_8060bcd9-d360-4412-af4d-48a05a47af37\Report.wer | — | |
MD5:— | SHA256:— | |||
| 1188 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_084d9db273661989_8ce13d66dc60478d745a4d6f8ca0dc64271e8bb_e8d65991_6ac71a51-8e16-43dd-a3c3-864eb6012668\Report.wer | — | |
MD5:— | SHA256:— | |||
| 2268 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER70.tmp.dmp | dmp | |
MD5:67957286F234DE7F5CD7070DC7B5314F | SHA256:C192B007051415D45C78EA1AC76B88C05DCB140D12DB0799480DEE24B646311A | |||
| 2268 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER17A.tmp.WERInternalMetadata.xml | xml | |
MD5:65B94335194AEE845F7AC4EA631313F6 | SHA256:B9225CE3159050A04601BAF567A1EB1583BE98E88B8D8556C76E55271A70FAF5 | |||
| 5816 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\084d9db2736619891e99f16b615dd050N.exe.5004.dmp | dmp | |
MD5:09F17CDE79C1780AE8EFB18F31C7214D | SHA256:4C6135C799BEF9907FC6BD469201F28502E1D6748C8FEC764C002D3BB69E8479 | |||
| 3188 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_084d9db273661989_8ce13d66dc60478d745a4d6f8ca0dc64271e8bb_e8d65991_a180cc9c-f62c-4190-9b74-983db36960bd\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5816 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER467.tmp.dmp | dmp | |
MD5:62B7D11D178EAA1915550A75BE90BEDE | SHA256:659A64C5AD1A04D438355BCCA7E0EA28F68BE61DFD1694AB2B71D8389B106E08 | |||
| 2268 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER1AA.tmp.xml | xml | |
MD5:BEC005A45E5146D669DCAC9D2FAE9CAE | SHA256:524EE0BB19DCD7FB26B46379FBDF8B0EF5DAA09FC93EB22E8C4B7E2A672F7864 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
24
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2248 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2124 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
2248 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
4752 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
4752 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2124 | RUXIMICS.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
— | — | GET | 404 | 104.20.4.235:443 | https://pastebin.com/raw/AqndxJKK | unknown | html | 474 b | unknown |
— | — | POST | 200 | 13.69.116.107:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4752 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2124 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2248 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2248 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4752 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
2124 | RUXIMICS.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
2124 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
2248 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
pastebin.com |
| shared |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |