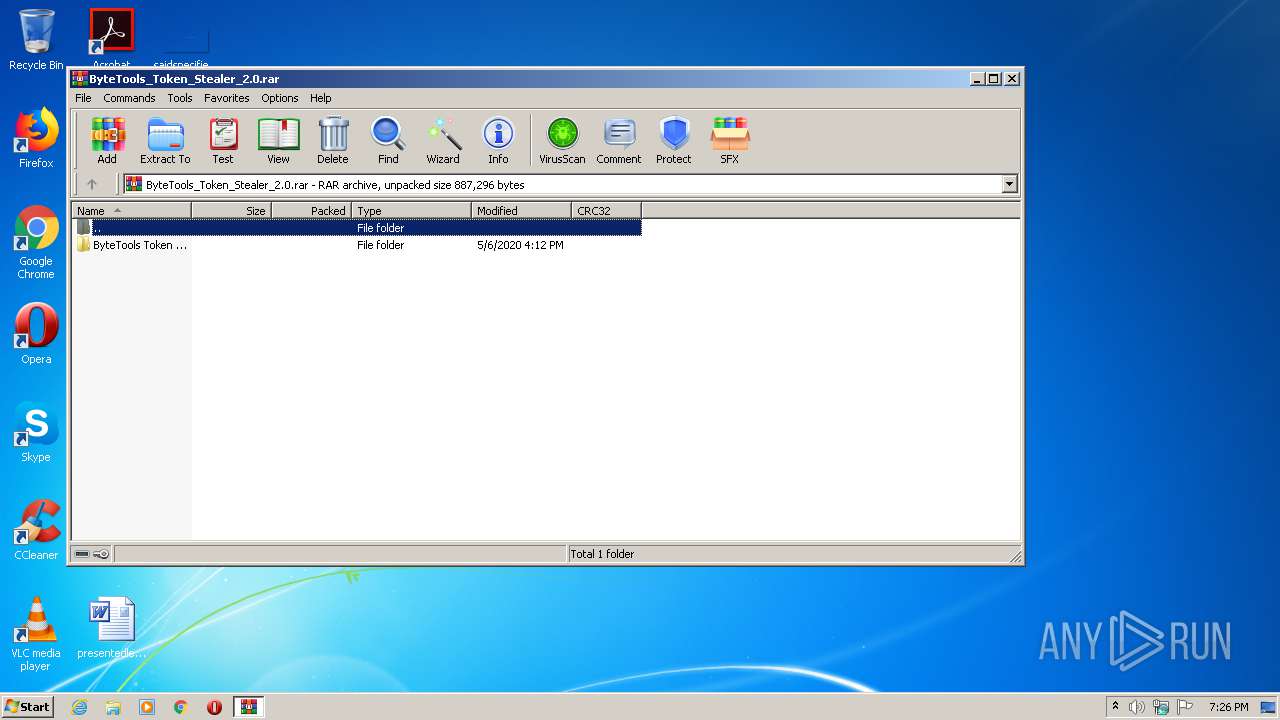
| download: | ByteTools_Token_Stealer_2.0.rar |
| Full analysis: | https://app.any.run/tasks/ab106b24-ba2f-4af0-8e1b-815f8e091122 |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2020, 18:25:56 |
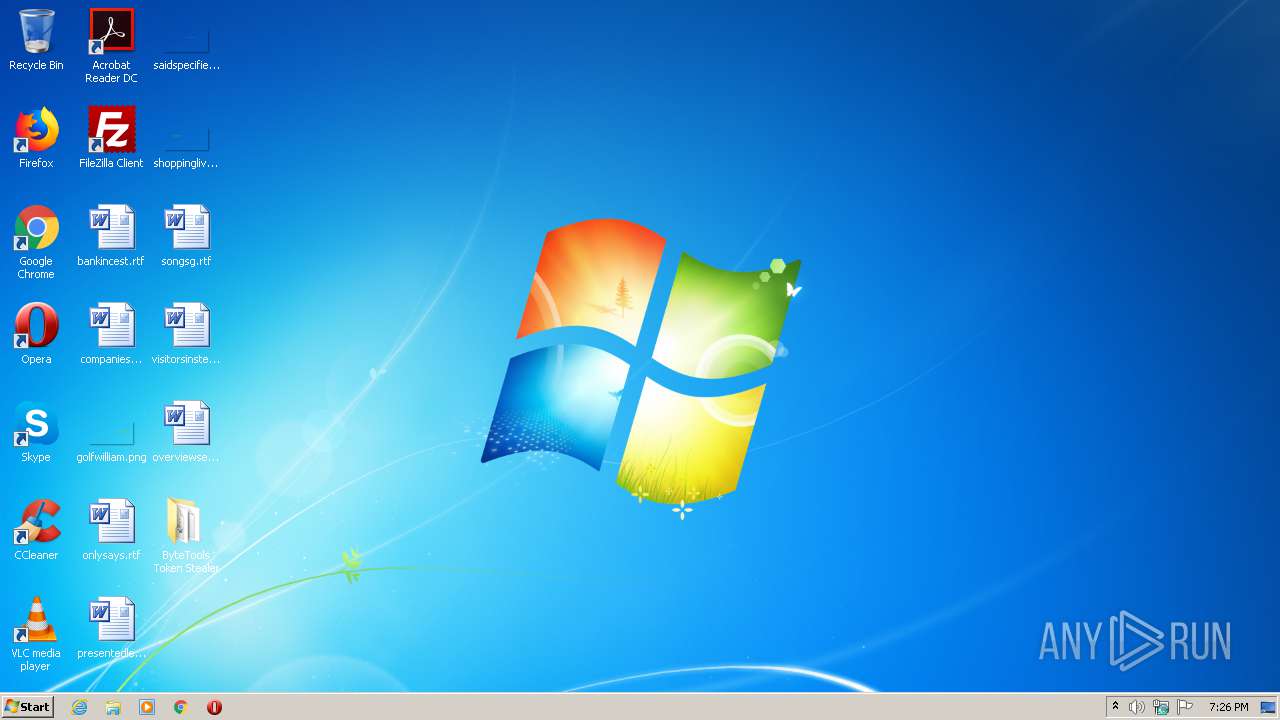
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 11F286C8156367251F953EAF9E82E049 |
| SHA1: | F70E4D513085399910CB7F288A580EE14847987F |
| SHA256: | 89D9A8552BC75F5E6A07807D4C3C555F105E9D0C404AA2B85BD6602BAB8B2D48 |
| SSDEEP: | 6144:WhbKDq38qM7cVZ4/teL6cWcAf+RzjO0UElr/:WhNsyK/te+cWLo20U4r |
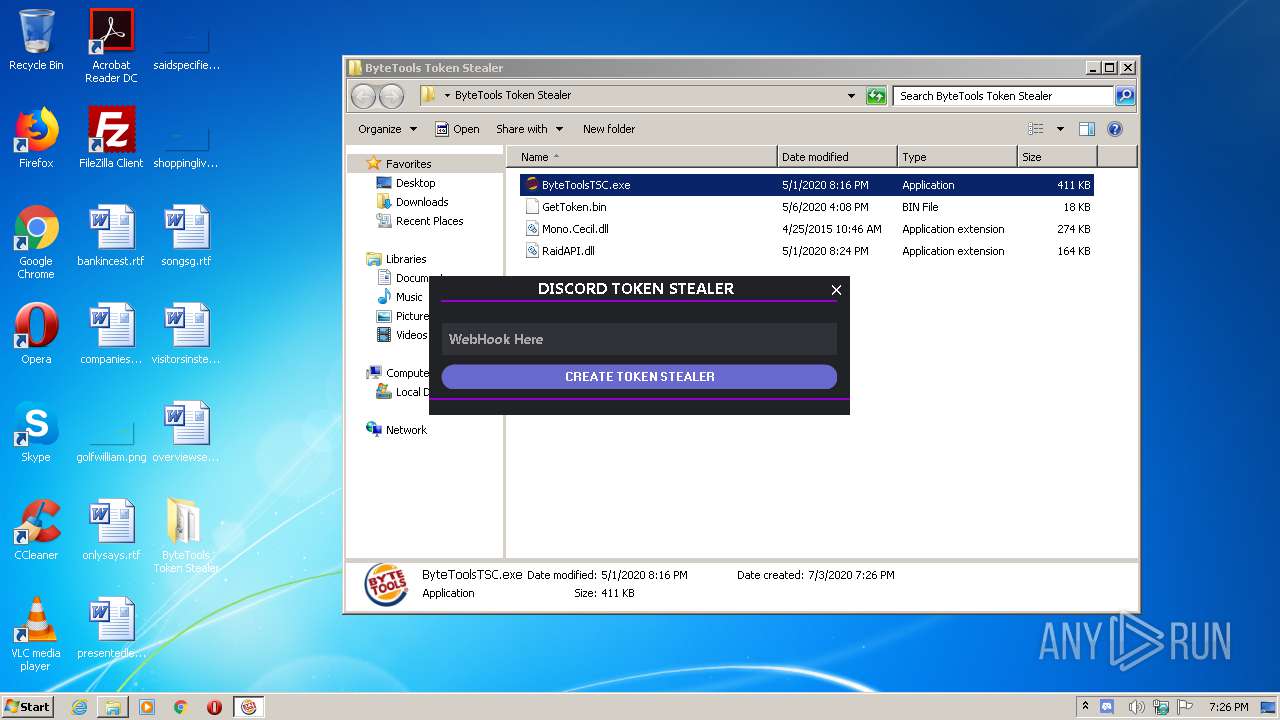
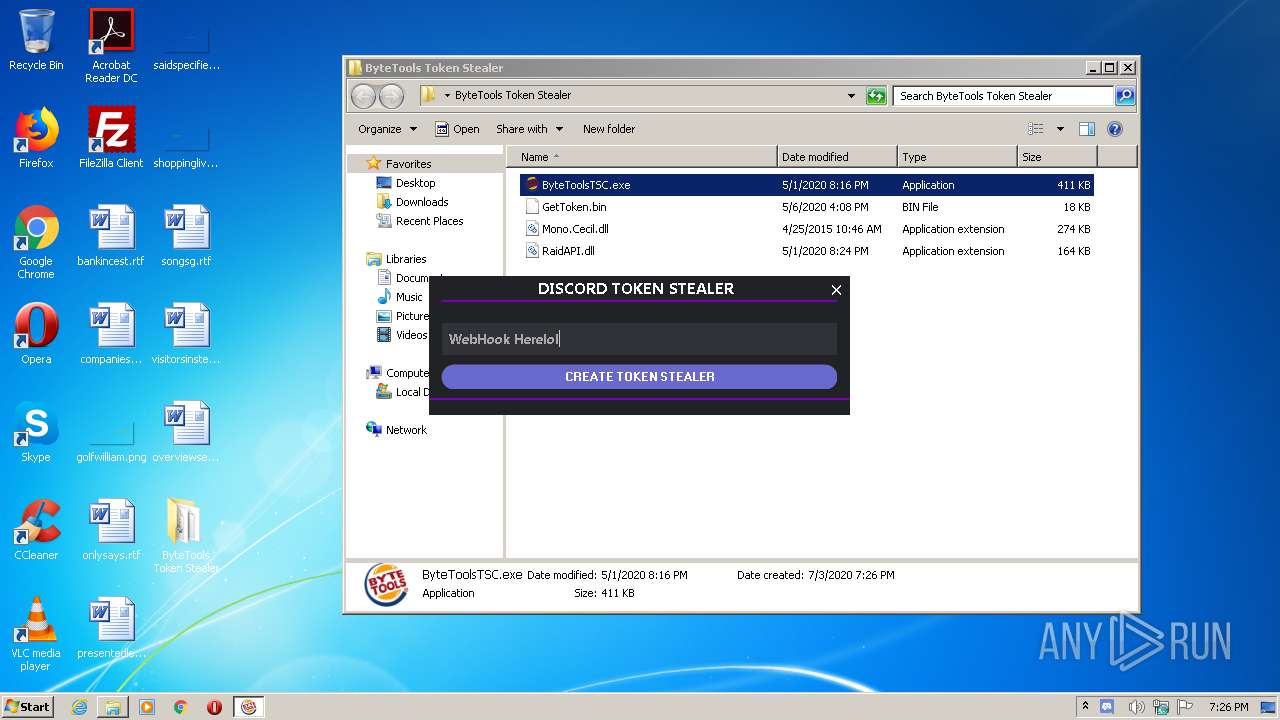
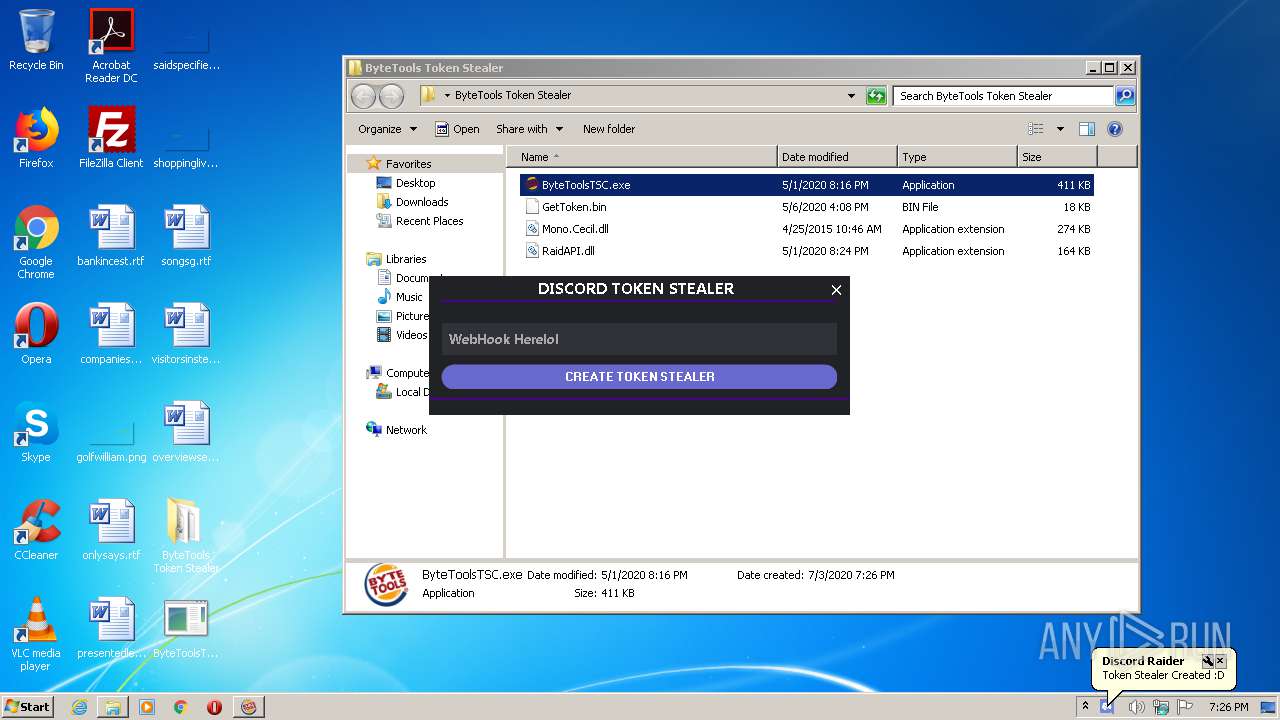
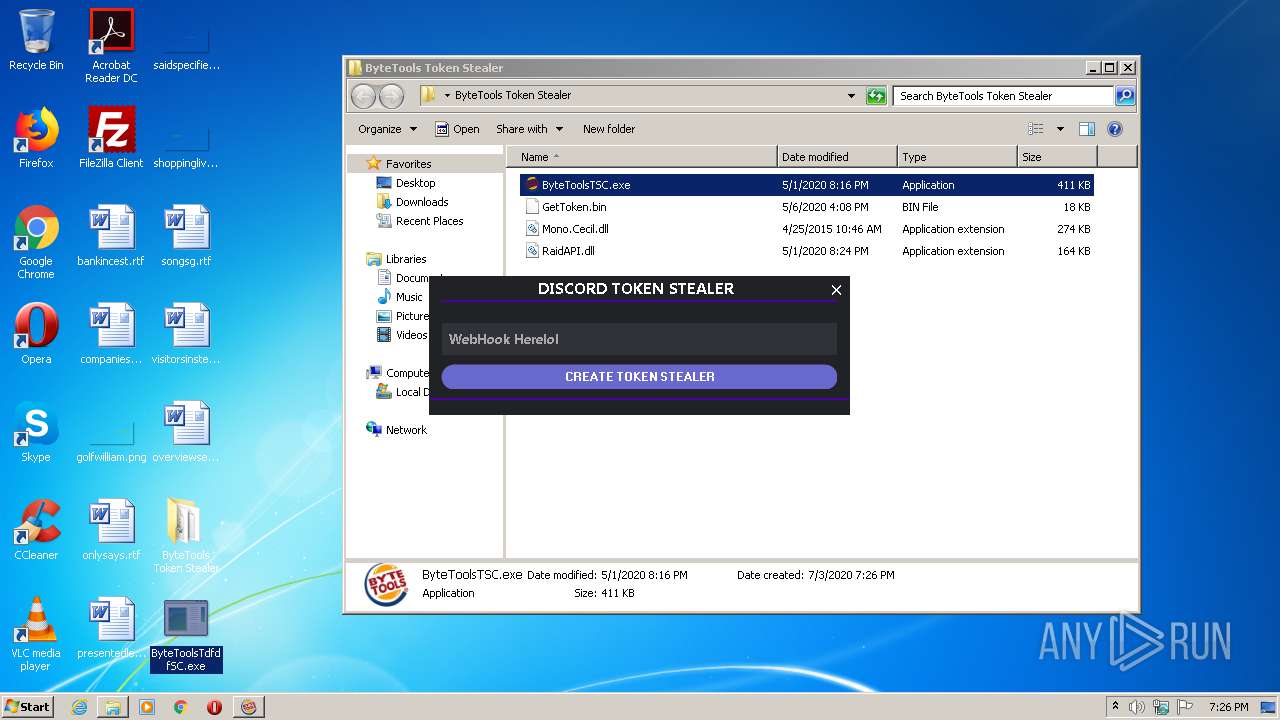
MALICIOUS
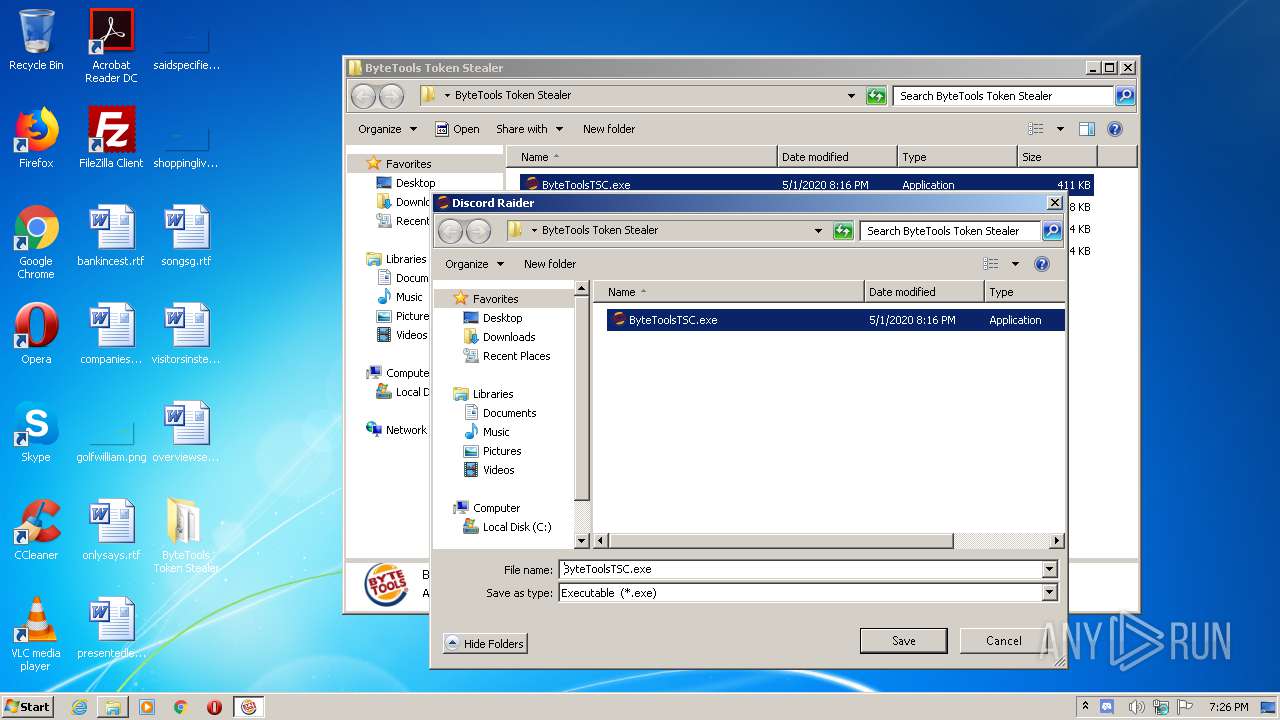
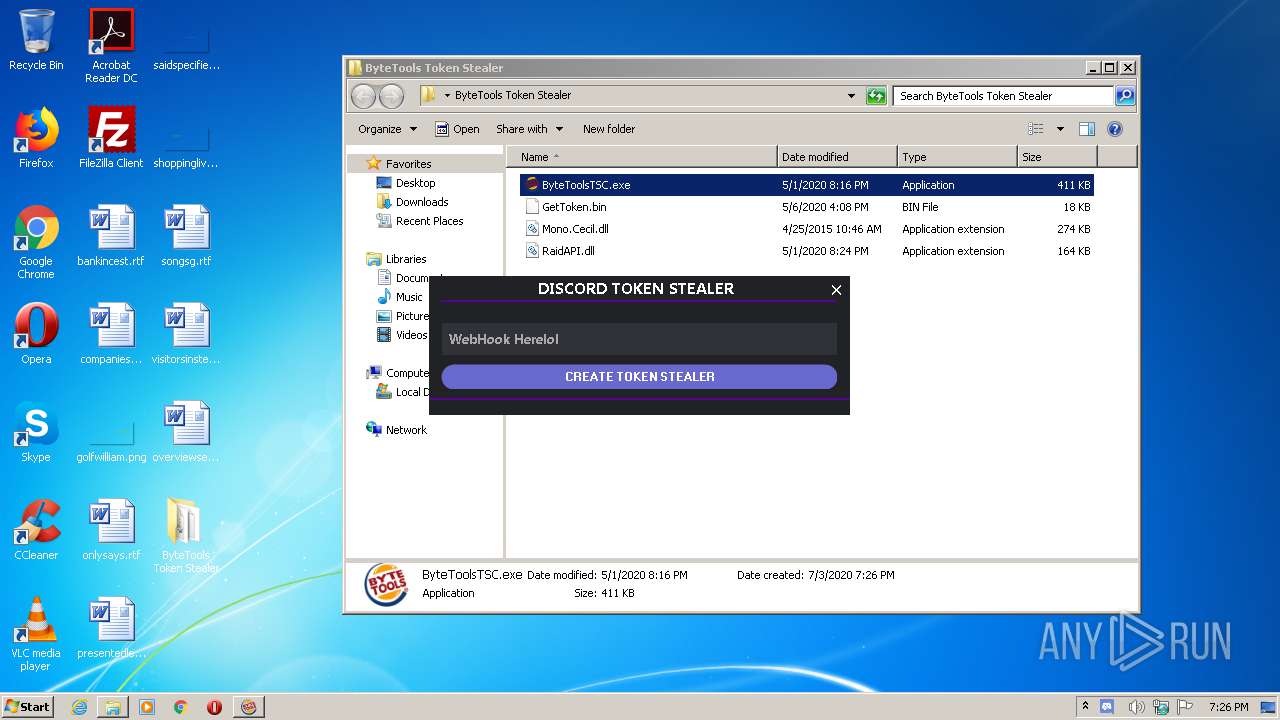
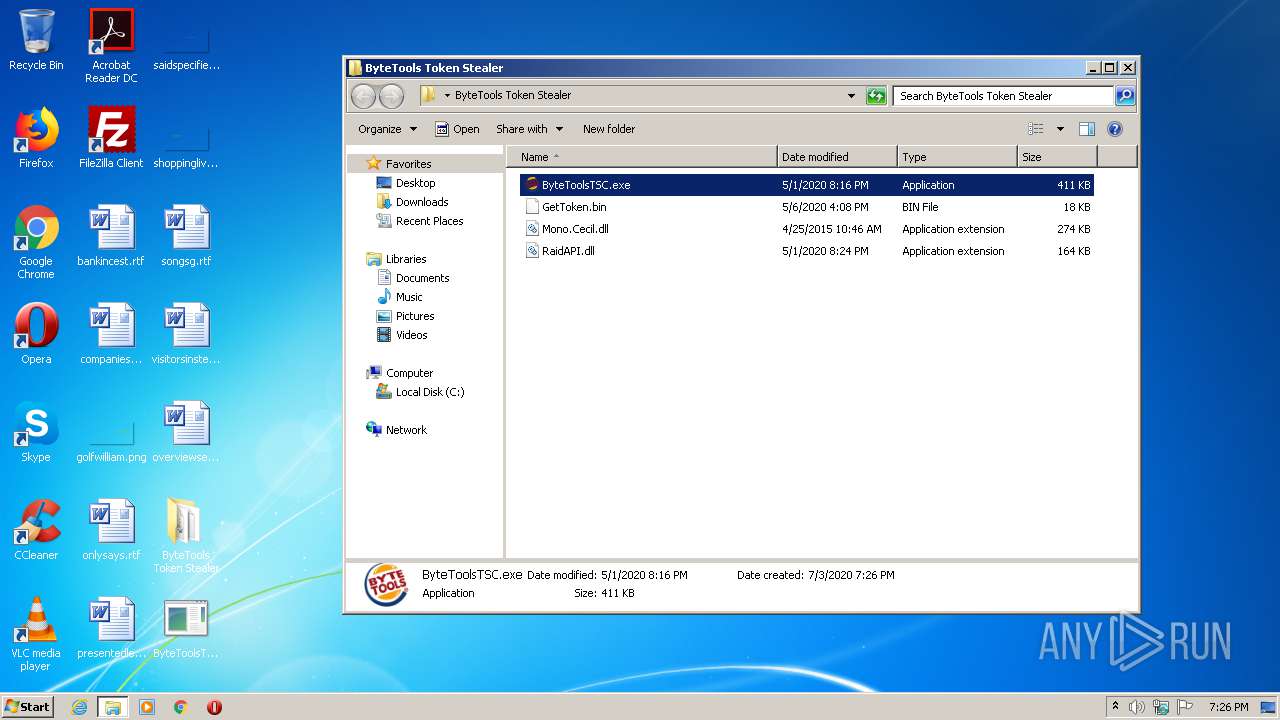
Loads dropped or rewritten executable
- ByteToolsTSC.exe (PID: 3044)
- SearchProtocolHost.exe (PID: 284)
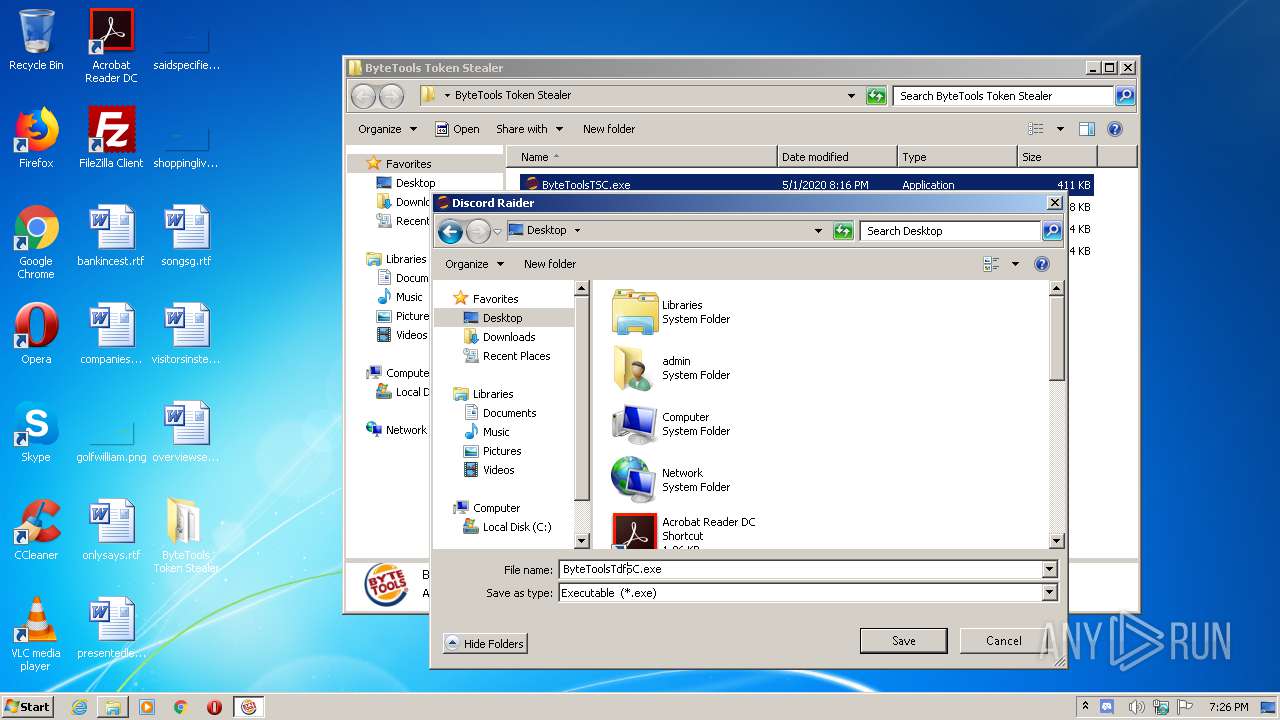
Application was dropped or rewritten from another process
- ByteToolsTSC.exe (PID: 3044)
- ByteToolsTdfdfSC.exe (PID: 2872)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2884)
- ByteToolsTSC.exe (PID: 3044)
INFO
Manual execution by user
- ByteToolsTSC.exe (PID: 3044)
- ByteToolsTdfdfSC.exe (PID: 2872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2872 | "C:\Users\admin\Desktop\ByteToolsTdfdfSC.exe" | C:\Users\admin\Desktop\ByteToolsTdfdfSC.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: StealerBin Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
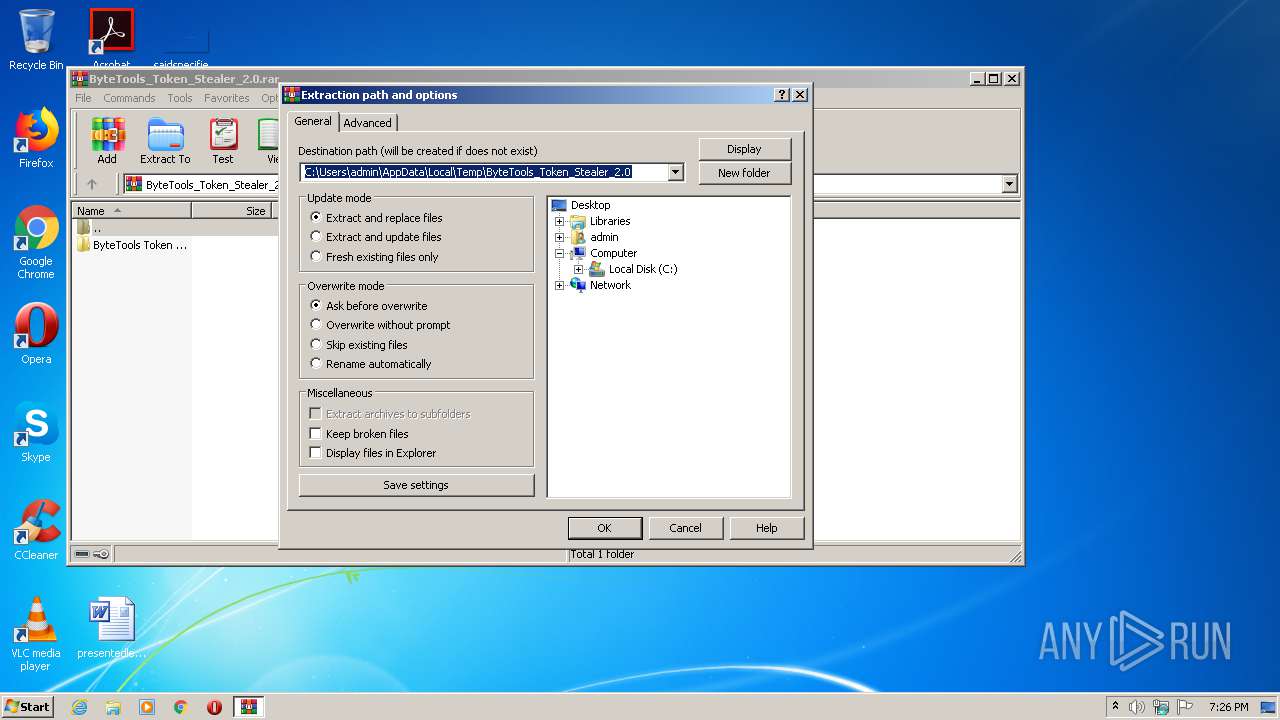
| 2884 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ByteTools_Token_Stealer_2.0.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3044 | "C:\Users\admin\Desktop\ByteTools Token Stealer\ByteToolsTSC.exe" | C:\Users\admin\Desktop\ByteTools Token Stealer\ByteToolsTSC.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ByteToolsTSC Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 385
Read events
1 290
Write events
92
Delete events
3
Modification events
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ByteTools_Token_Stealer_2.0.rar | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
5
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3044 | ByteToolsTSC.exe | C:\Users\admin\Desktop\ByteToolsTdfdfSC.exe | executable | |
MD5:— | SHA256:— | |||
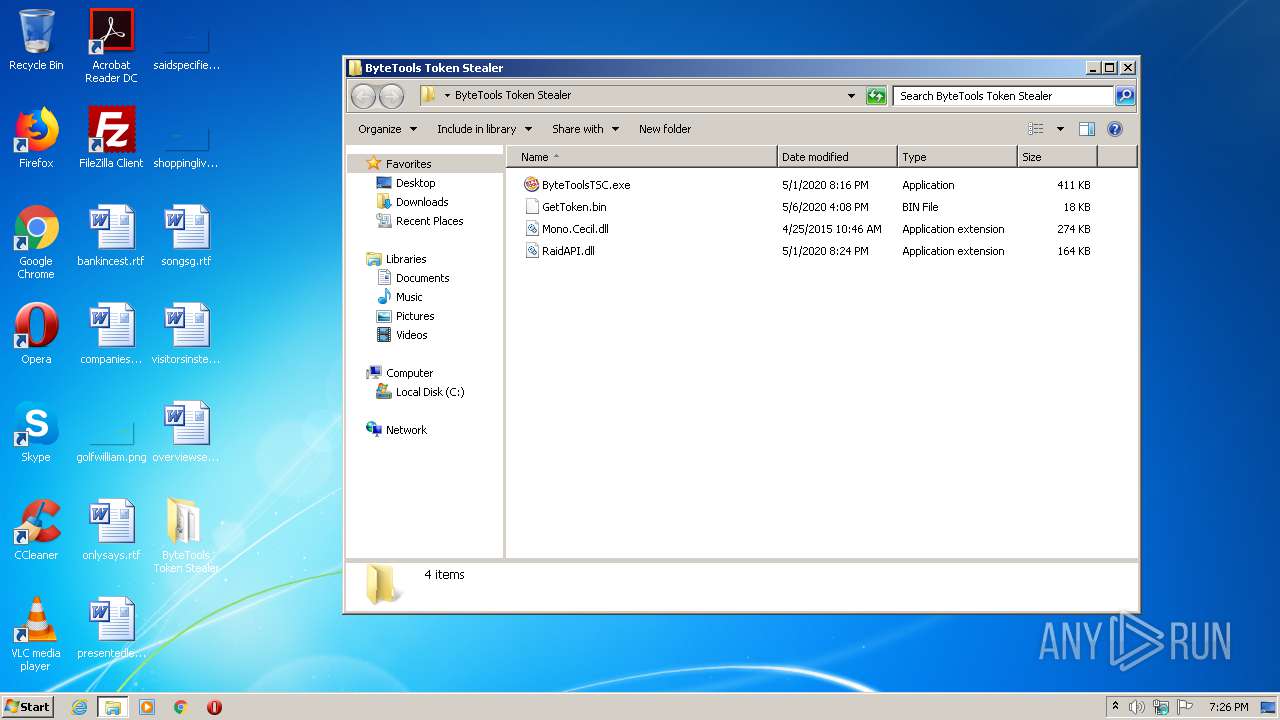
| 2884 | WinRAR.exe | C:\Users\admin\Desktop\ByteTools Token Stealer\GetToken.bin | executable | |
MD5:B45CB38EFE2408EC5B32725F514B31DC | SHA256:4D3AE75FABD5FBE0AADE8DF6C545B419832862895C80C88811BC55FE6DDD939A | |||
| 2884 | WinRAR.exe | C:\Users\admin\Desktop\ByteTools Token Stealer\Mono.Cecil.dll | executable | |
MD5:F494762FCCE61F0C294BED88D1B5F3A9 | SHA256:A3444DD5C83EEBEA15A807E4932AD4127EF33DC7C7C2D799F30DED930E1E1A74 | |||
| 2884 | WinRAR.exe | C:\Users\admin\Desktop\ByteTools Token Stealer\RaidAPI.dll | executable | |
MD5:476A01D97977D0BFD9512B287CAA8763 | SHA256:CC39B4BF0C717F2AF67D20F477F0A82A59C6CE96403E4DFDB1D95BF9F1D14C51 | |||
| 2884 | WinRAR.exe | C:\Users\admin\Desktop\ByteTools Token Stealer\ByteToolsTSC.exe | executable | |
MD5:E4AE361933BC32F469186C48CF2CE472 | SHA256:0E51BA0690515B3F95BBBB0EC17186448AA5CB6DC73FEF2BBF0E7DA335A5599E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report