| File name: | procdot.exe |
| Full analysis: | https://app.any.run/tasks/8c229eec-e855-4328-a980-0ac94ad0cc40 |
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2023, 17:26:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7CA52F911BF8CA022EB62CB1A4647D45 |
| SHA1: | 2F4D632C9E3CFEA382B1D6855F907D02B8E8C6B7 |
| SHA256: | 89BCF0F72D37215487DB5871641F140F6519956C64B22BEE1DB59F6B4368D464 |
| SSDEEP: | 98304:PB0xgvq2syG4+UqBAUZLCll+ezqUlLm3O+cGFL1upG:p0xOsq+/Vul+eTLm+LGF5u |
MALICIOUS
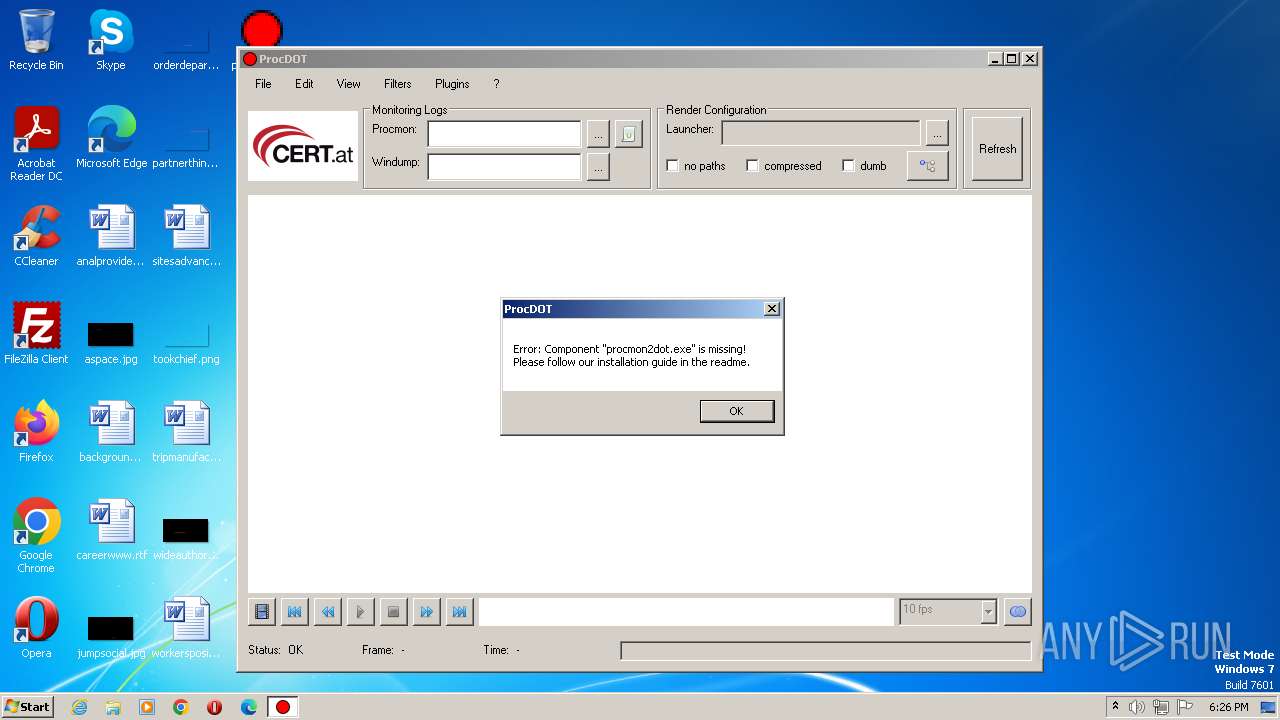
Loads dropped or rewritten executable
- procdot.exe (PID: 772)
- procdot.exe (PID: 3392)
SUSPICIOUS
Reads the Internet Settings
- procdot.exe (PID: 772)
Executable content was dropped or overwritten
- procdot.exe (PID: 772)
- procdot.exe (PID: 3392)
INFO
Create files in a temporary directory
- procdot.exe (PID: 772)
- procdot.exe (PID: 3392)
Checks supported languages
- procdot.exe (PID: 772)
- procdot.exe (PID: 3392)
Reads the computer name
- procdot.exe (PID: 772)
- procdot.exe (PID: 3392)
The process checks LSA protection
- procdot.exe (PID: 772)
- procdot.exe (PID: 3392)
Manual execution by a user
- procdot.exe (PID: 3392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| Website: | http://www.procdot.com |
|---|---|
| Email: | chrisu@procdot.com |
| LegalCopyright: | Copyright by nic.at / Written by Christian Wojner |
| OriginalFileName: | procdot.exe |
| InternalName: | ProcDOT |
| FileDescription: | ProcDOT - Visual Malware Analysis |
| FileVersion: | 1.2 |
| ProductVersion: | 1.2 |
| ProductName: | ProcDOT |
| CompanyName: | CERT.at |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Unknown (0) |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.2.0.0 |
| FileVersionNumber: | 1.2.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4442624 |
| CodeSize: | 1379840 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2017:11:30 14:25:29+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Nov-2017 14:25:29 |
| Detected languages: |
|
| CompanyName: | CERT.at |
| ProductName: | ProcDOT |
| ProductVersion: | 1.2 |
| FileVersion: | 1.2 |
| FileDescription: | ProcDOT - Visual Malware Analysis |
| InternalName: | ProcDOT |
| OriginalFilename: | procdot.exe |
| LegalCopyright: | Copyright by nic.at / Written by Christian Wojner |
| Email: | chrisu@procdot.com |
| Website: | http://www.procdot.com |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Nov-2017 14:25:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x00074FFF | 0x00075000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.84771 |
.text | 0x00076000 | 0x000DBDA0 | 0x000DBE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58558 |
.rdata | 0x00152000 | 0x00027EB4 | 0x00028000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.45454 |
.data | 0x0017A000 | 0x00413AE4 | 0x0040E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.16174 |
.rsrc | 0x0058E000 | 0x00000C84 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.88859 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.872 | 863 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
OLEAUT32.DLL |
SHELL32.DLL |
USER32.DLL |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 772 | "C:\Users\admin\Desktop\procdot.exe" | C:\Users\admin\Desktop\procdot.exe | explorer.exe | ||||||||||||
User: admin Company: CERT.at Integrity Level: MEDIUM Description: ProcDOT - Visual Malware Analysis Exit code: 0 Version: 1.2 Modules
| |||||||||||||||
| 3392 | "C:\Users\admin\Desktop\procdot.exe" | C:\Users\admin\Desktop\procdot.exe | explorer.exe | ||||||||||||
User: admin Company: CERT.at Integrity Level: MEDIUM Description: ProcDOT - Visual Malware Analysis Exit code: 0 Version: 1.2 Modules
| |||||||||||||||
Total events
127
Read events
127
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 772 | procdot.exe | C:\Users\admin\AppData\Local\Temp\wojner.pbi.procdot\PBTEMP.772.52.dll | executable | |
MD5:A5FBBEF842A3DC9990FEF994477A44A8 | SHA256:3FFE354B183E2C450768F44B8003F67C194A2FBAE0687304E28E4E5AC6872E1C | |||
| 3392 | procdot.exe | C:\Users\admin\AppData\Local\Temp\wojner.pbi.procdot\PBTEMP.3392.62479.dll | executable | |
MD5:A5FBBEF842A3DC9990FEF994477A44A8 | SHA256:3FFE354B183E2C450768F44B8003F67C194A2FBAE0687304E28E4E5AC6872E1C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |