| URL: | http://www.wincore.ru/programs/7540-powerrun-zapuskaem-programmy-s-vysochayshimi-privilegiyami.html |
| Full analysis: | https://app.any.run/tasks/ca979f36-2a68-4a10-8a0c-87516376881d |
| Verdict: | Malicious activity |
| Analysis date: | December 24, 2024, 08:37:51 |
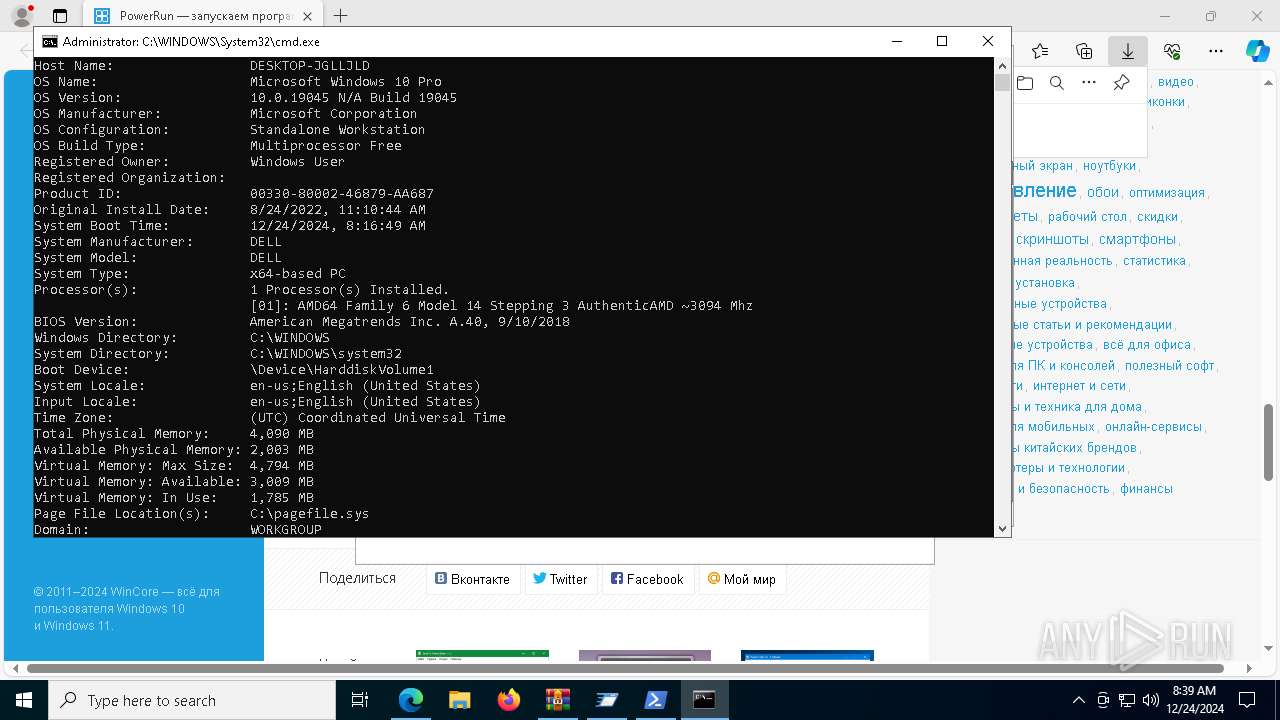
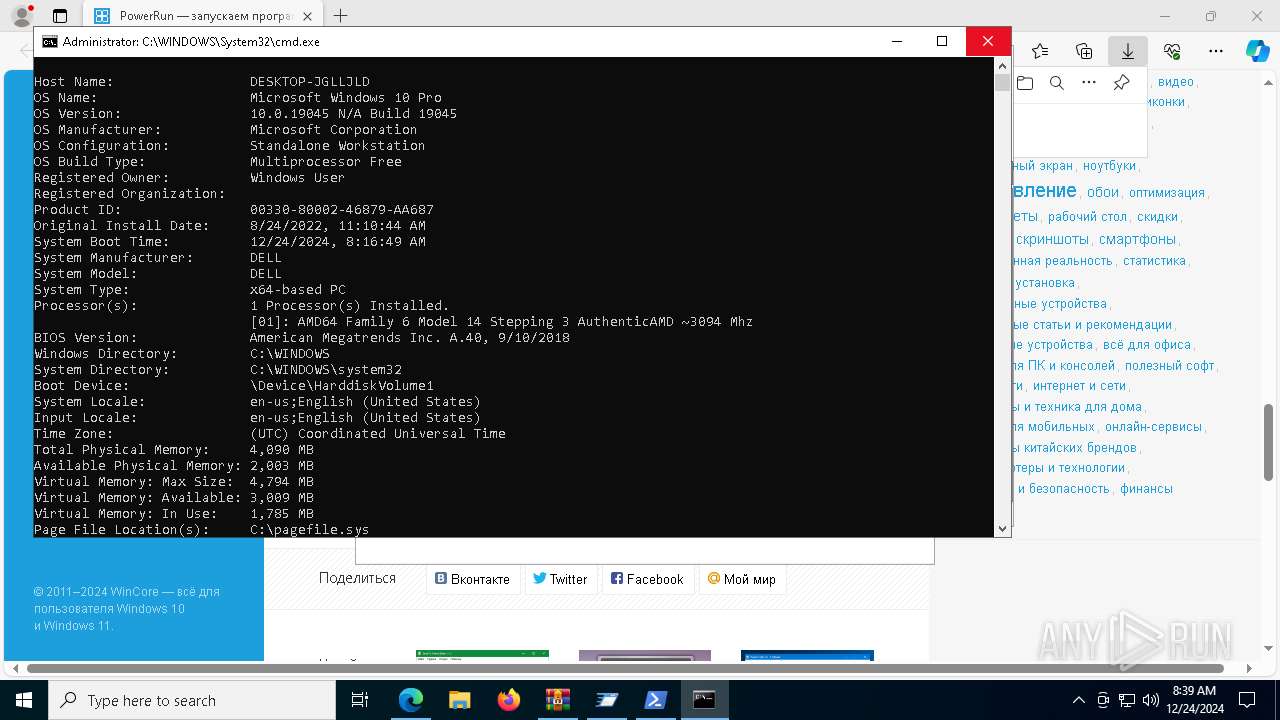
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6FEDA0D55F4D5BEBA4AEC59E6133E0E1 |
| SHA1: | 76955FAD29EC6A78301852D063DC6DD09EB454F3 |
| SHA256: | 89BAB0C00AA74D4BBE4D67AD7EF535BCB1E3187773FA4A6CF8F06FD4AB839256 |
| SSDEEP: | 3:N1KJS4huhWKIVJyuI4r+XKCUIIccTcNfedUGIKNG:Cc46WjXyJaCRIZcNfwjNQ |
MALICIOUS
Executing a file with an untrusted certificate
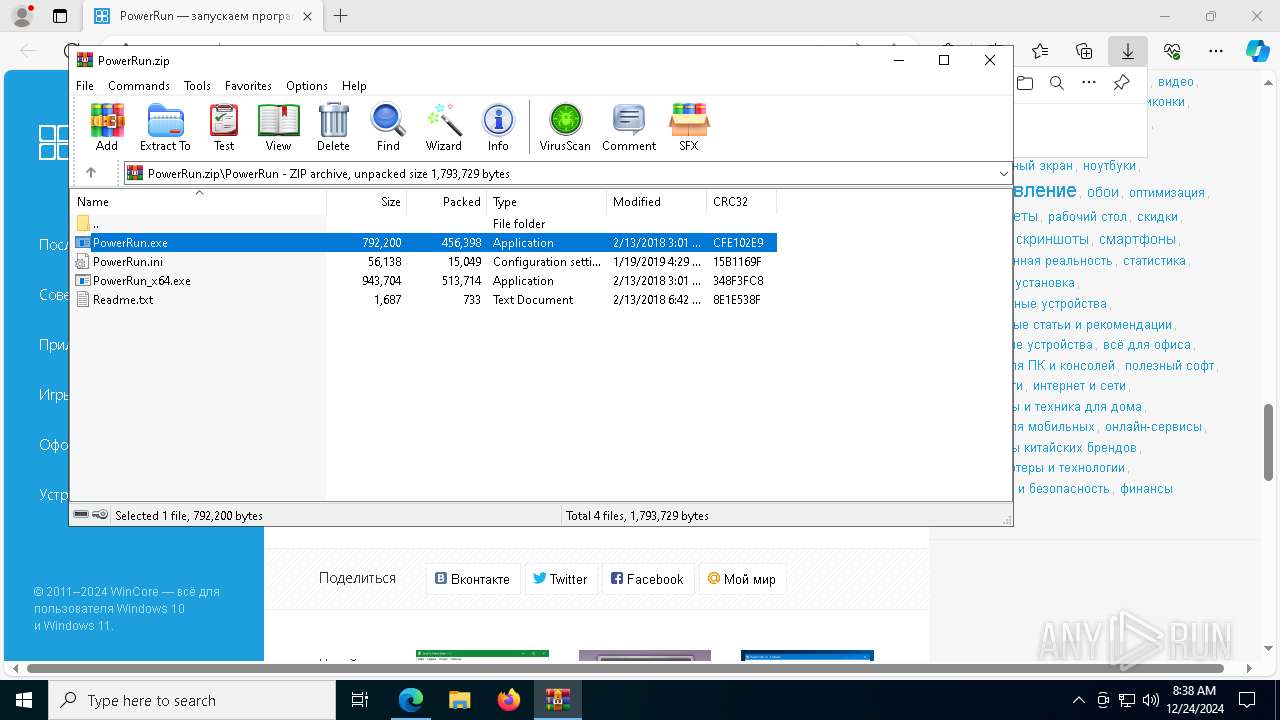
- PowerRun.exe (PID: 5588)
SUSPICIOUS
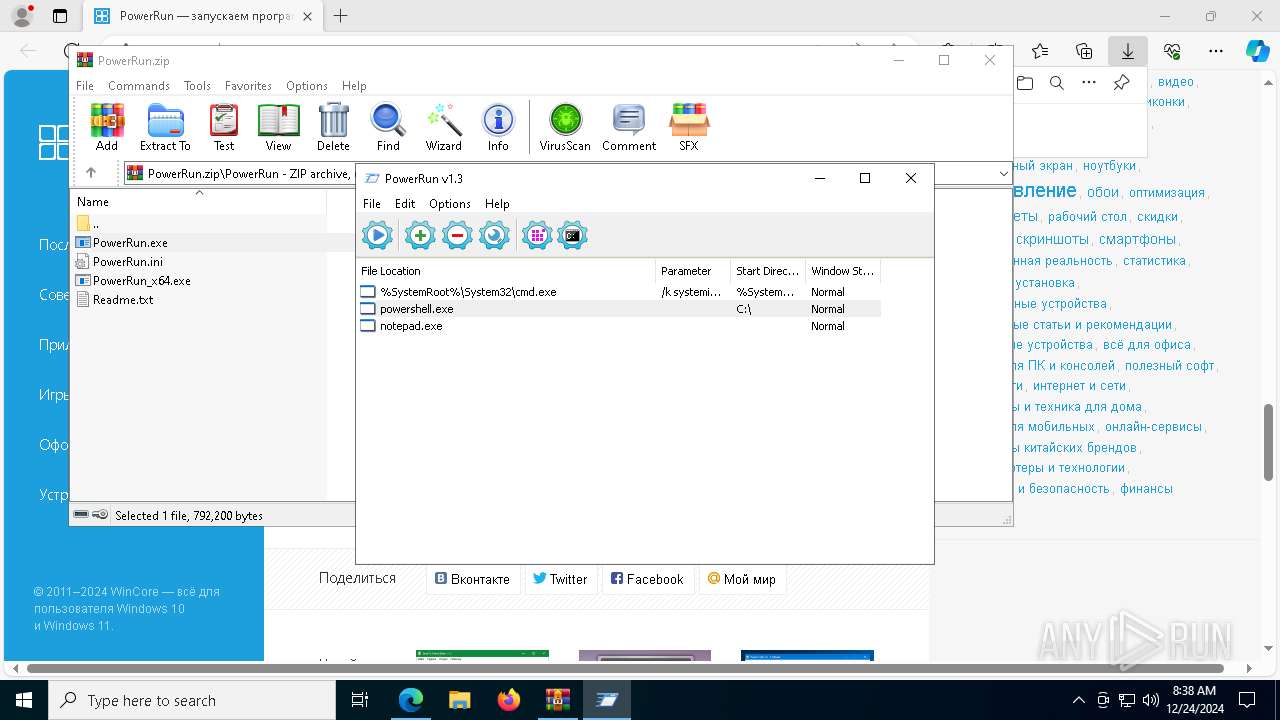
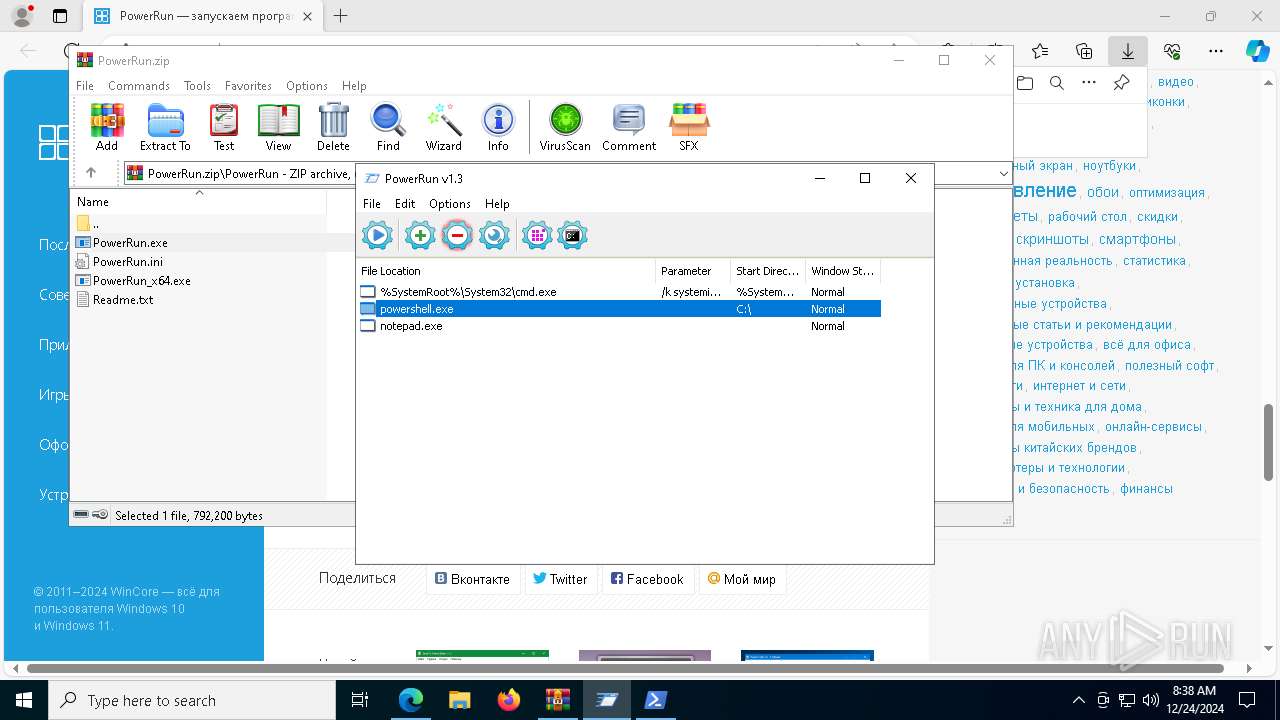
Application launched itself
- PowerRun.exe (PID: 7548)
- PowerRun.exe (PID: 7468)
- PowerRun.exe (PID: 7408)
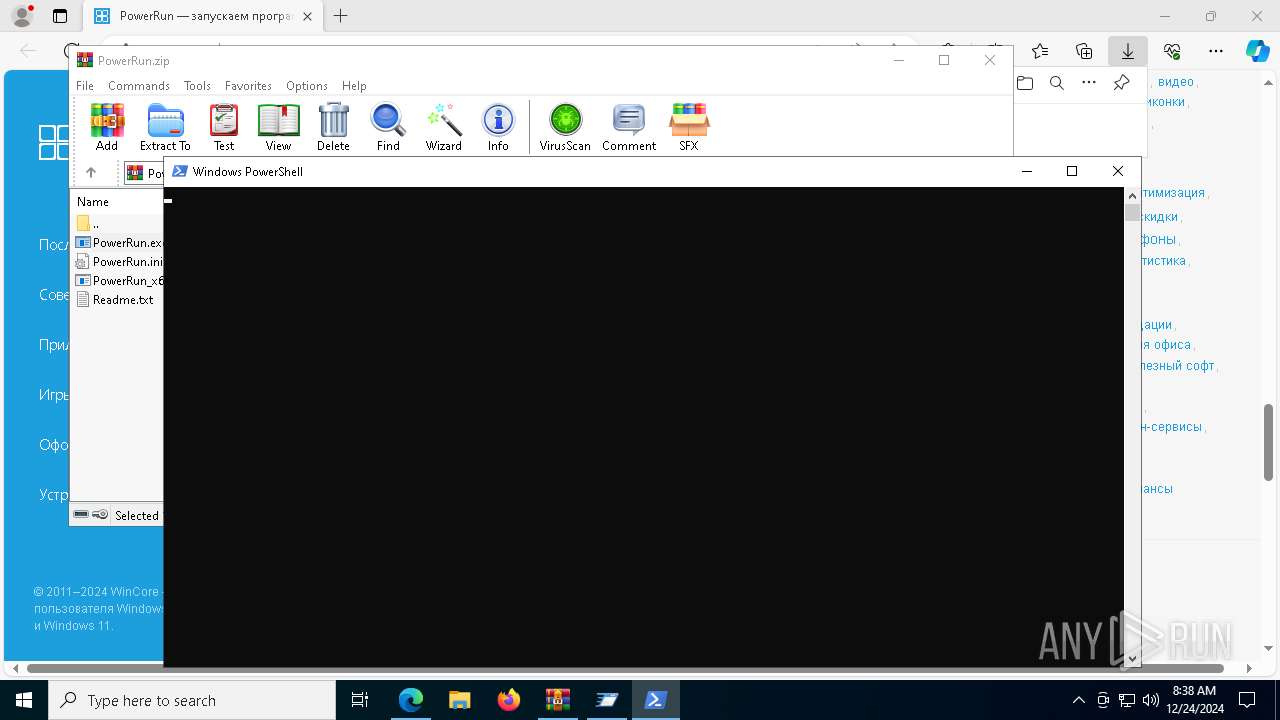
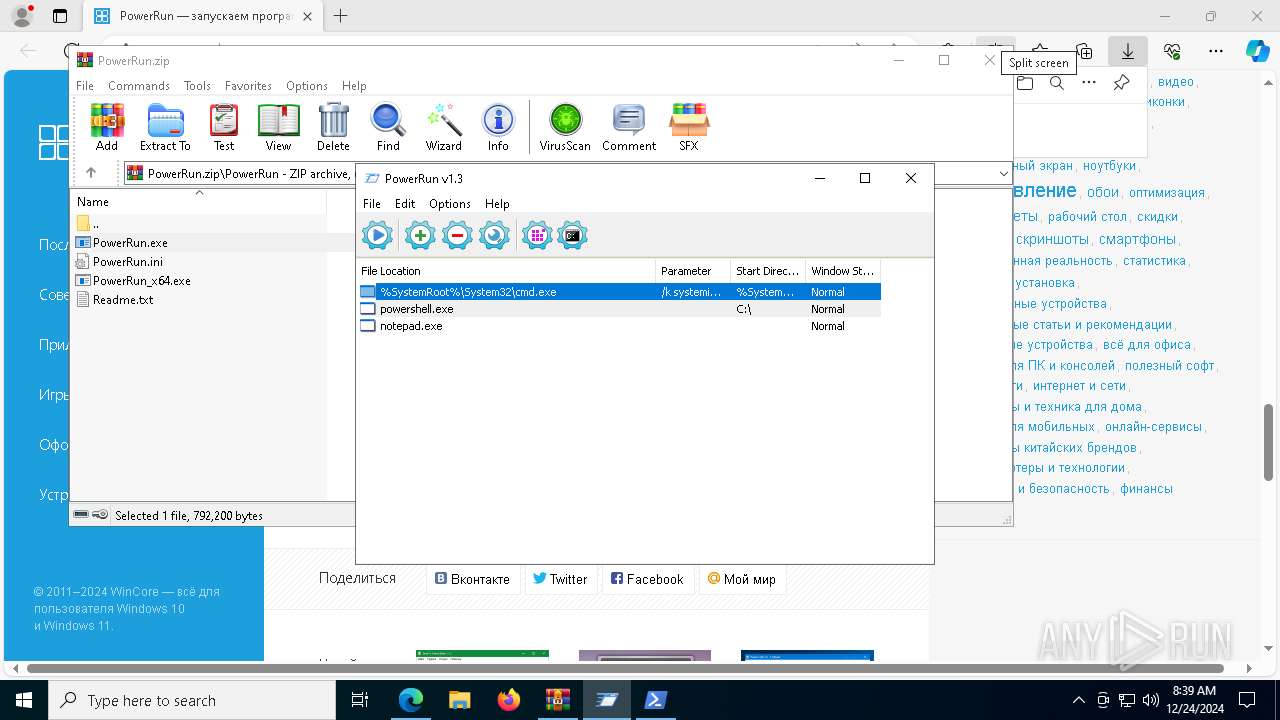
Starts POWERSHELL.EXE for commands execution
- PowerRun.exe (PID: 4444)
Reads security settings of Internet Explorer
- PowerRun.exe (PID: 4444)
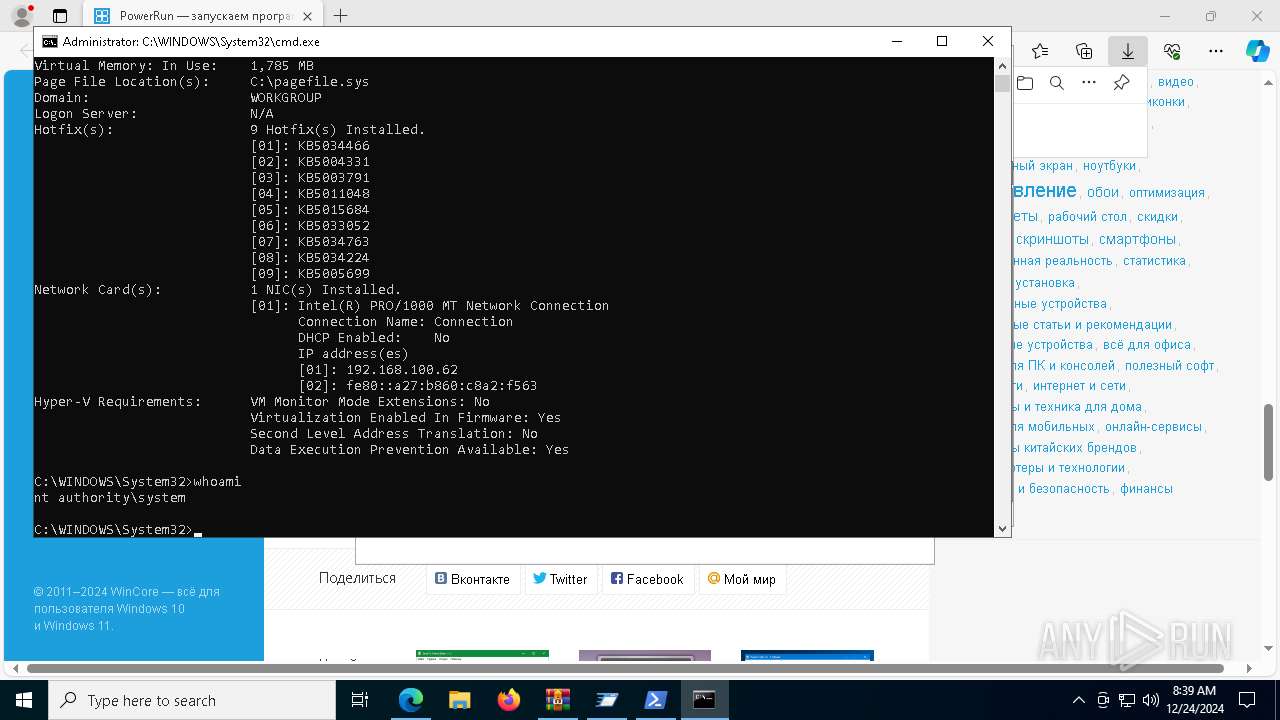
Identifying current user with WHOAMI command
- cmd.exe (PID: 5720)
- powershell.exe (PID: 1488)
Starts CMD.EXE for commands execution
- PowerRun.exe (PID: 4444)
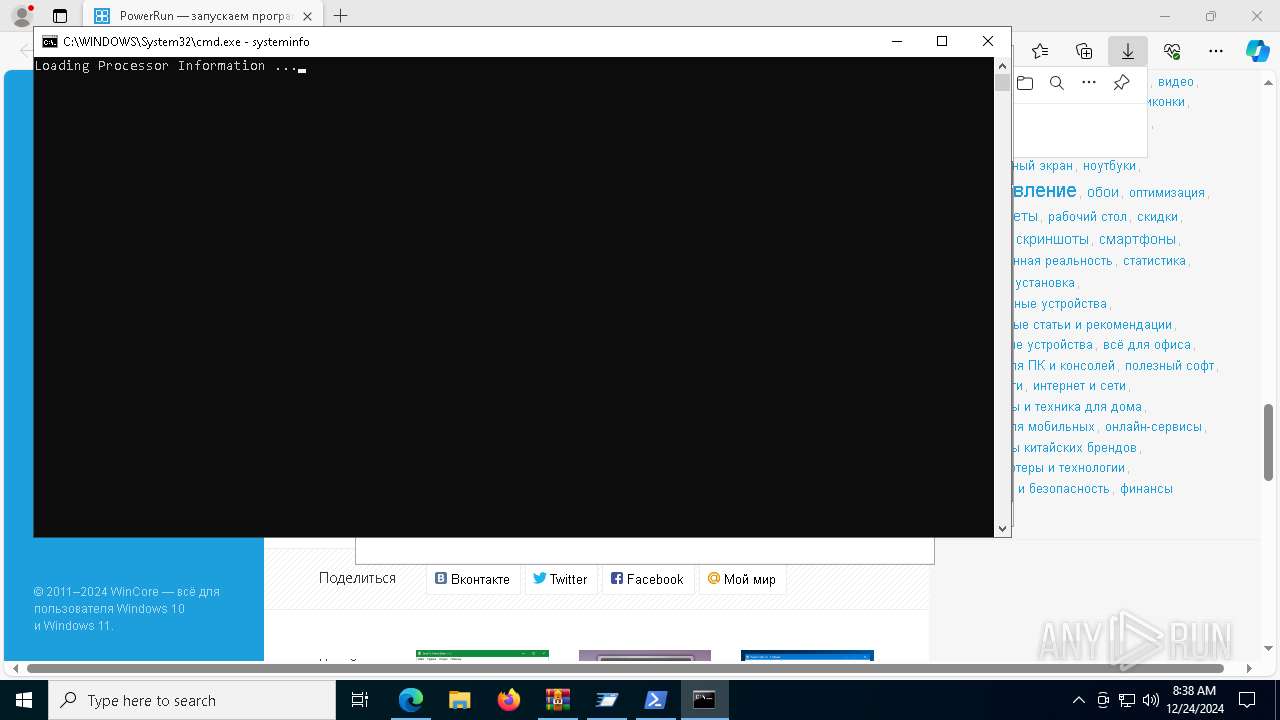
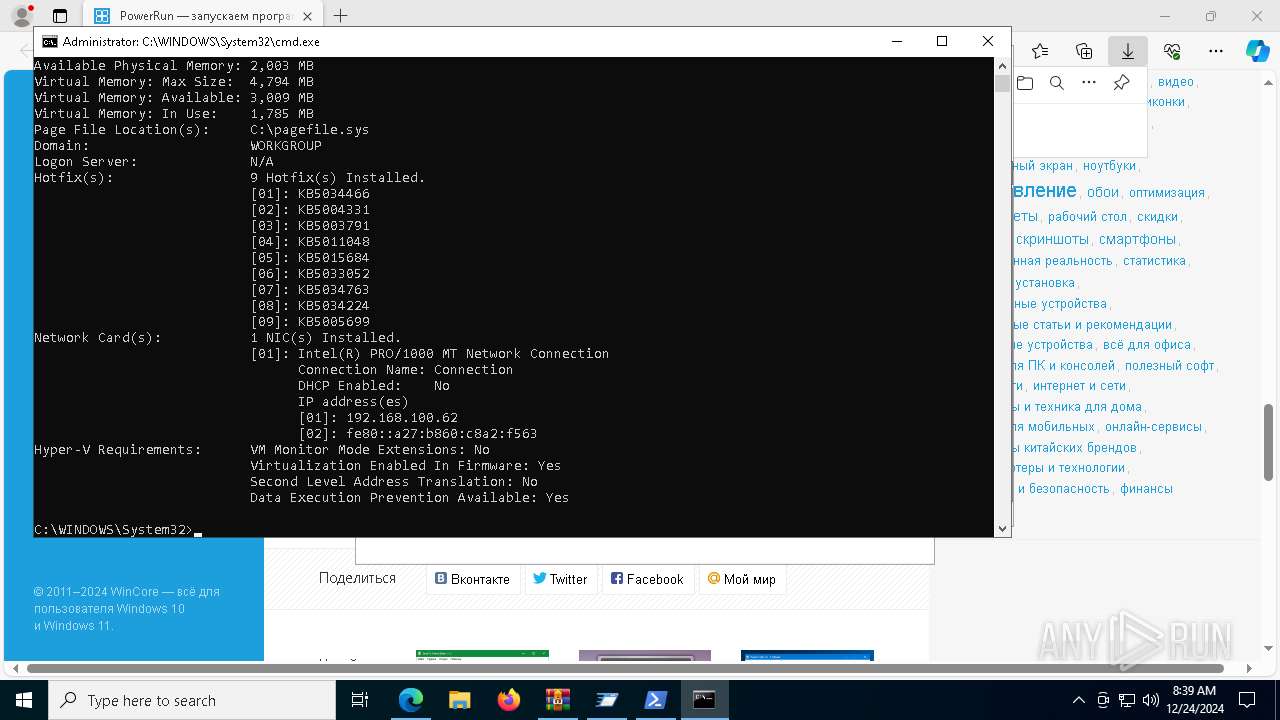
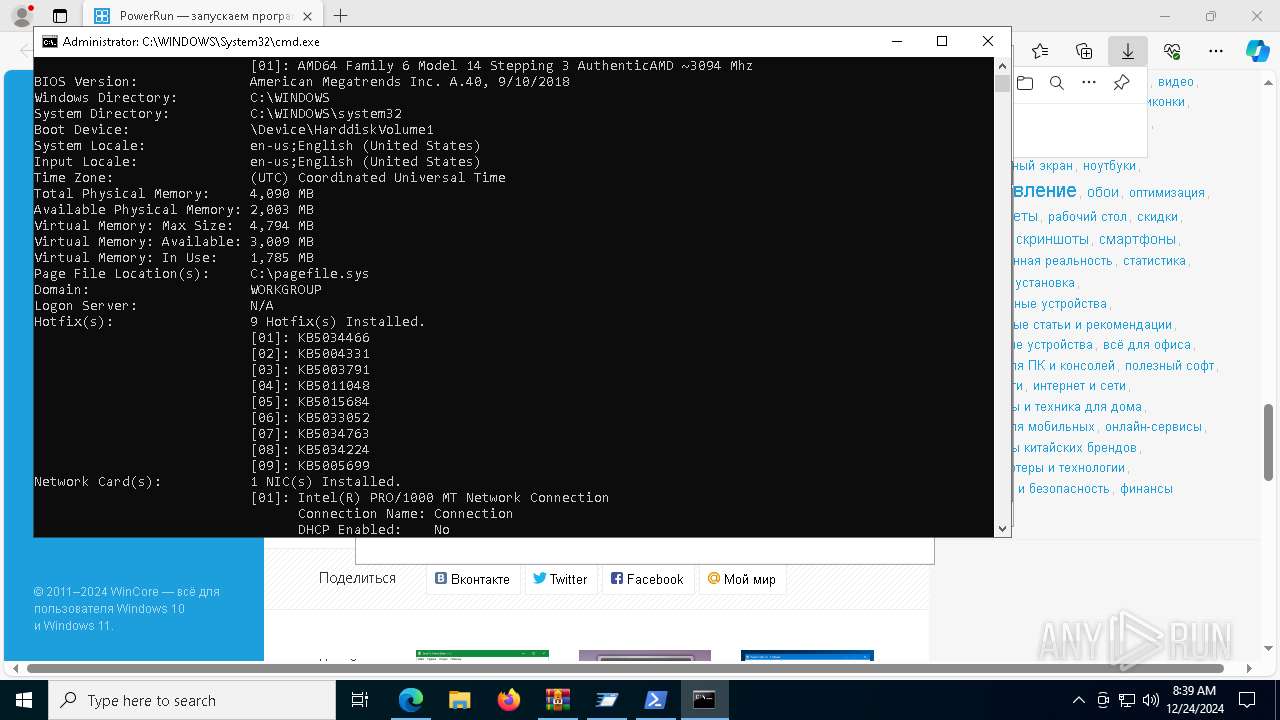
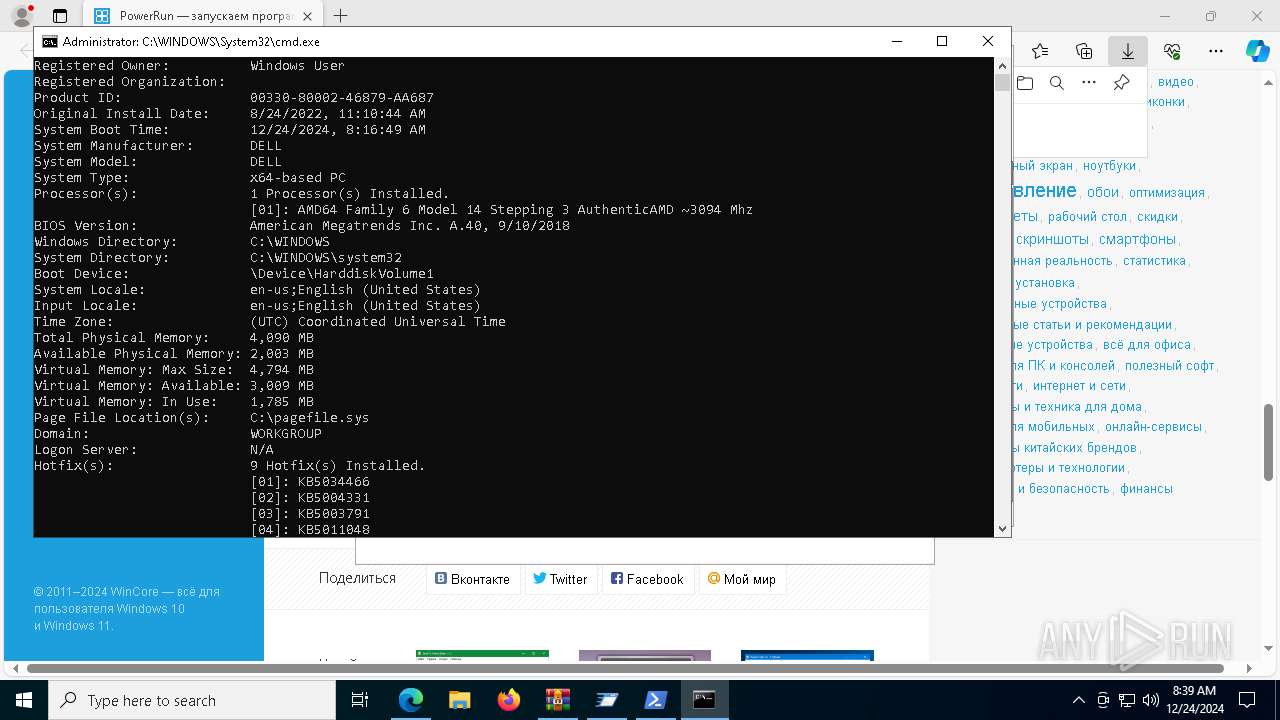
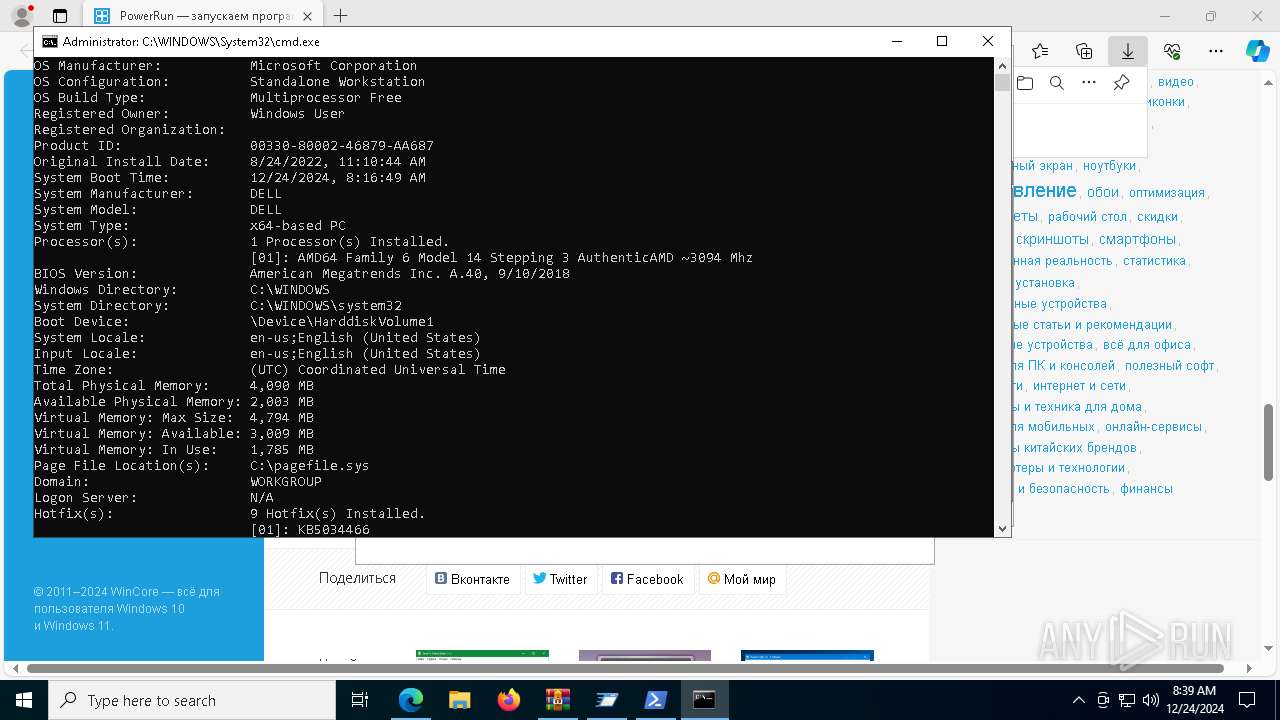
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 5720)
INFO
Checks supported languages
- identity_helper.exe (PID: 8076)
- PowerRun.exe (PID: 7468)
- PowerRun.exe (PID: 7548)
- PowerRun.exe (PID: 4444)
- PowerRun.exe (PID: 7408)
The sample compiled with english language support
- msedge.exe (PID: 6656)
- msedge.exe (PID: 6272)
- WinRAR.exe (PID: 7192)
Reads Environment values
- identity_helper.exe (PID: 8076)
Reads the computer name
- identity_helper.exe (PID: 8076)
- PowerRun.exe (PID: 7548)
- PowerRun.exe (PID: 4444)
- PowerRun.exe (PID: 7408)
Reads mouse settings
- PowerRun.exe (PID: 7468)
- PowerRun.exe (PID: 4444)
- PowerRun.exe (PID: 7408)
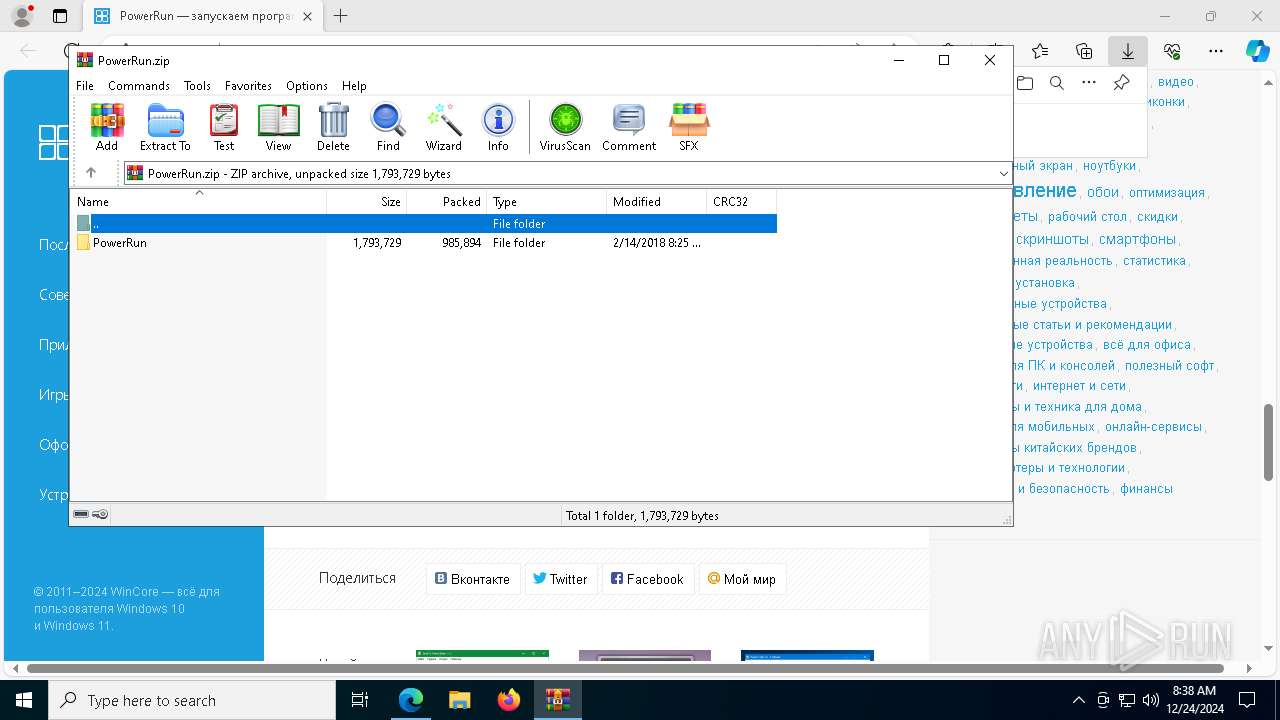
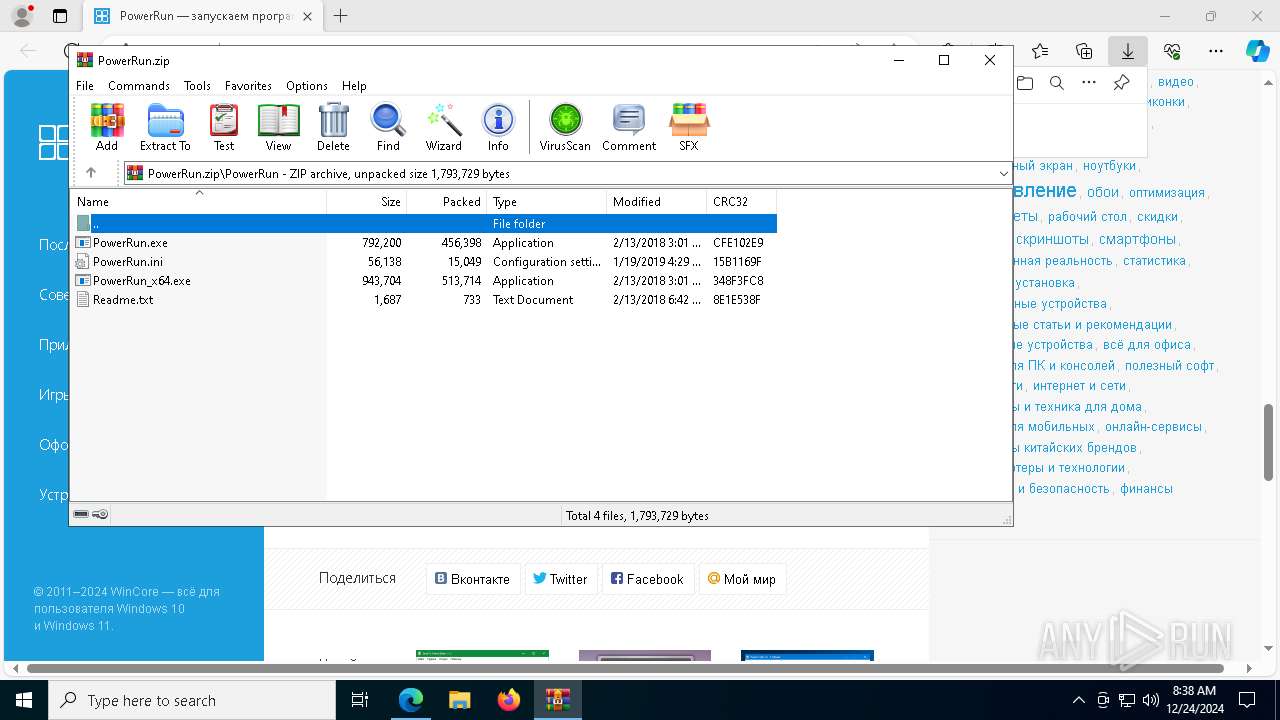
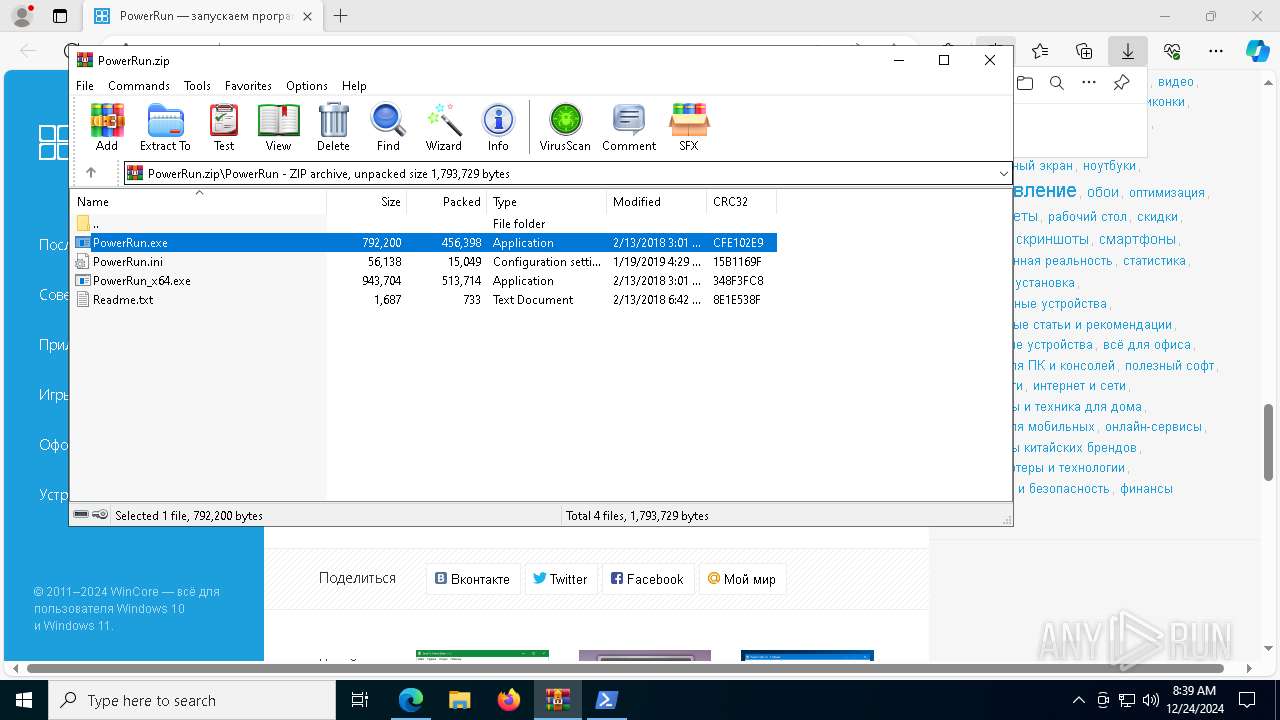
The process uses the downloaded file
- msedge.exe (PID: 5236)
- WinRAR.exe (PID: 7192)
- msedge.exe (PID: 6272)
- PowerRun.exe (PID: 4444)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7192)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6272)
Create files in a temporary directory
- PowerRun.exe (PID: 7468)
- PowerRun.exe (PID: 7548)
Application launched itself
- msedge.exe (PID: 6272)
Checks current location (POWERSHELL)
- powershell.exe (PID: 1488)
The process uses AutoIt
- PowerRun.exe (PID: 7468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
187
Monitored processes
54
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | PowerRun.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --mojo-platform-channel-handle=7160 --field-trial-handle=2400,i,10090347704202822305,5213086361222834797,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3436 | "C:\WINDOWS\system32\whoami.exe" | C:\Windows\System32\whoami.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: whoami - displays logged on user information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4444 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7192.32337\PowerRun\PowerRun.exe" /TI/ /P:197242 | C:\Users\admin\AppData\Local\Temp\Rar$EXa7192.32337\PowerRun\PowerRun.exe | — | PowerRun.exe | |||||||||||
User: SYSTEM Company: www.sordum.org Integrity Level: SYSTEM Description: PowerRun Exit code: 0 Version: 1.3.0.0 Modules
| |||||||||||||||
| 4668 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.wincore.ru/programs/7540-powerrun-zapuskaem-programmy-s-vysochayshimi-privilegiyami.html" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1348 --field-trial-handle=2400,i,10090347704202822305,5213086361222834797,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6428 --field-trial-handle=2400,i,10090347704202822305,5213086361222834797,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5588 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7192.32337\PowerRun\PowerRun.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7192.32337\PowerRun\PowerRun.exe | — | WinRAR.exe | |||||||||||
User: admin Company: www.sordum.org Integrity Level: MEDIUM Description: PowerRun Exit code: 3221226540 Version: 1.3.0.0 Modules
| |||||||||||||||
Total events
18 111
Read events
18 060
Write events
51
Delete events
0
Modification events
| (PID) Process: | (4668) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4668) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4668) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4668) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4668) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4668) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
4
Suspicious files
278
Text files
87
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1355c4.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1355d4.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1355d4.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1355e3.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1355e3.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
85
TCP/UDP connections
129
DNS requests
140
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
440 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
440 | svchost.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6656 | msedge.exe | GET | 200 | 46.36.222.191:80 | http://www.wincore.ru/programs/7540-powerrun-zapuskaem-programmy-s-vysochayshimi-privilegiyami.html | unknown | — | — | whitelisted |
6656 | msedge.exe | GET | 200 | 46.36.222.191:80 | http://www.wincore.ru/engine/classes/js/jquery.js | unknown | — | — | whitelisted |
6656 | msedge.exe | GET | 200 | 46.36.222.191:80 | http://www.wincore.ru/engine/classes/js/jqueryui.js | unknown | — | — | whitelisted |
6656 | msedge.exe | GET | 200 | 46.36.222.191:80 | http://www.wincore.ru/templates/wincorenew/style/engine.css | unknown | — | — | whitelisted |
6656 | msedge.exe | GET | 200 | 46.36.222.191:80 | http://www.wincore.ru/templates/wincorenew/style/bootstrap.css | unknown | — | — | whitelisted |
6656 | msedge.exe | GET | 200 | 46.36.222.191:80 | http://www.wincore.ru/templates/wincorenew/style/main.css | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
440 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
440 | svchost.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 23.212.110.162:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6656 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.wincore.ru |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
config.edge.skype.com |
| whitelisted |