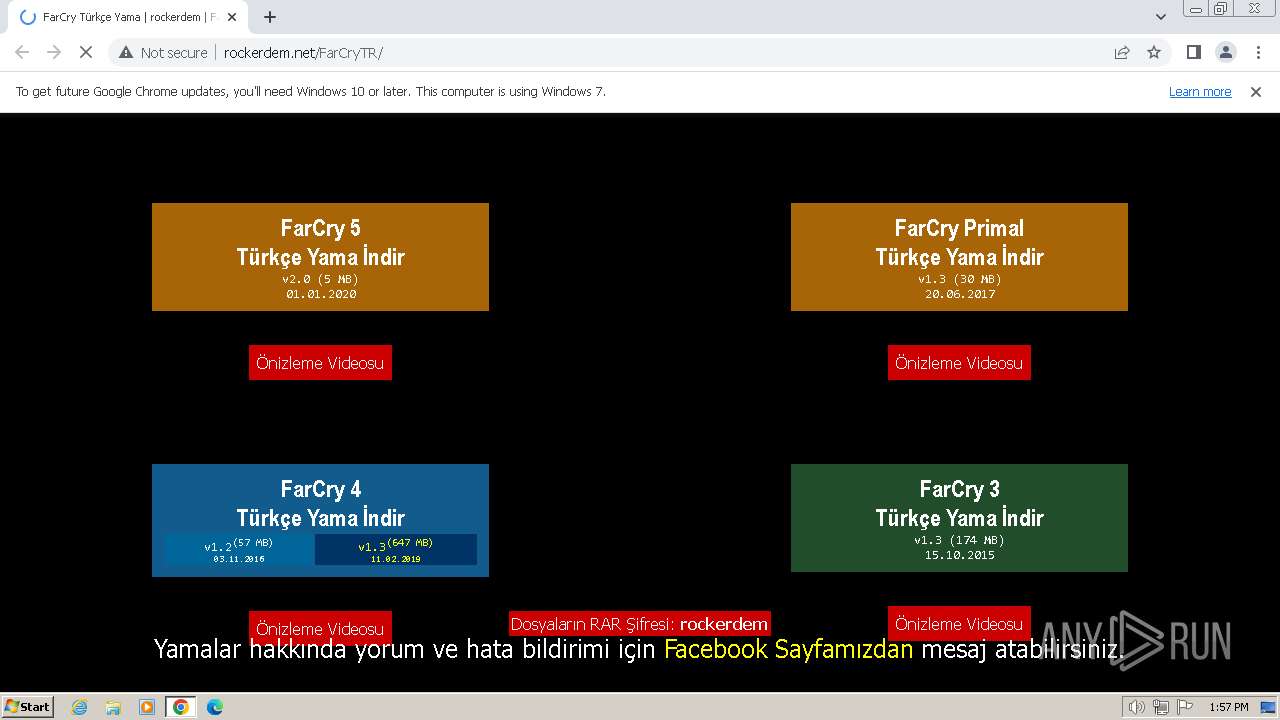
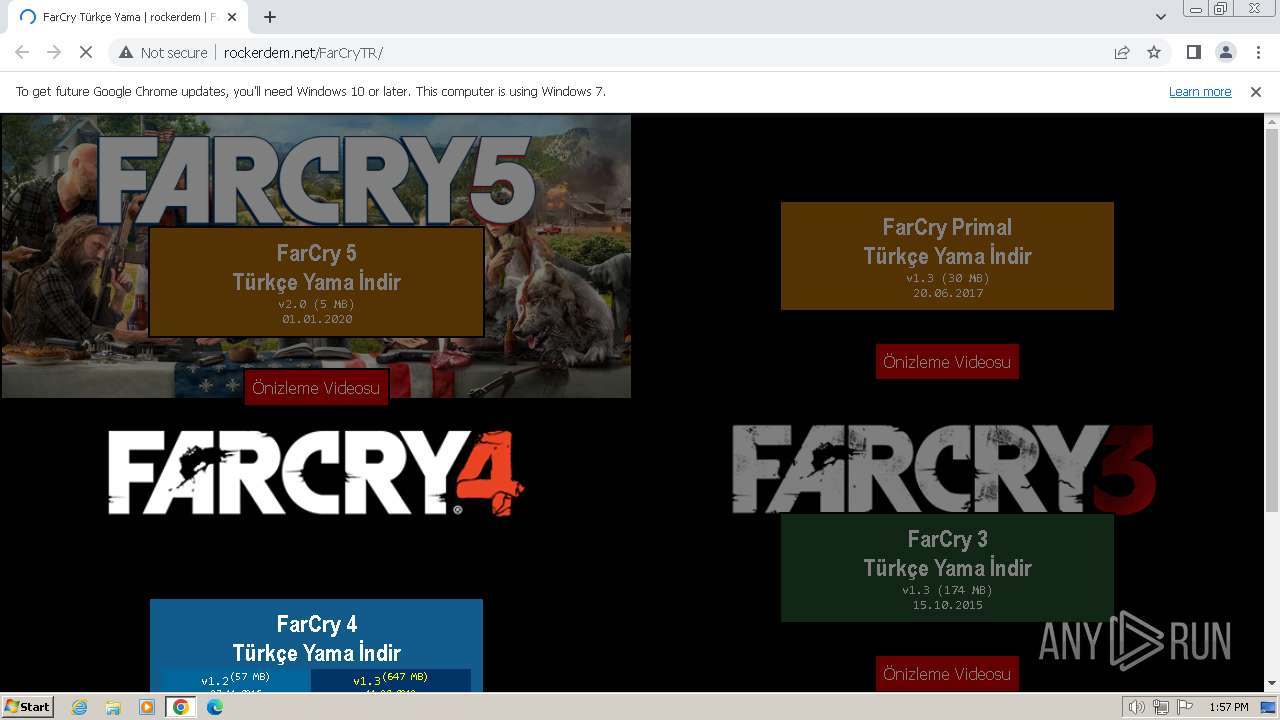
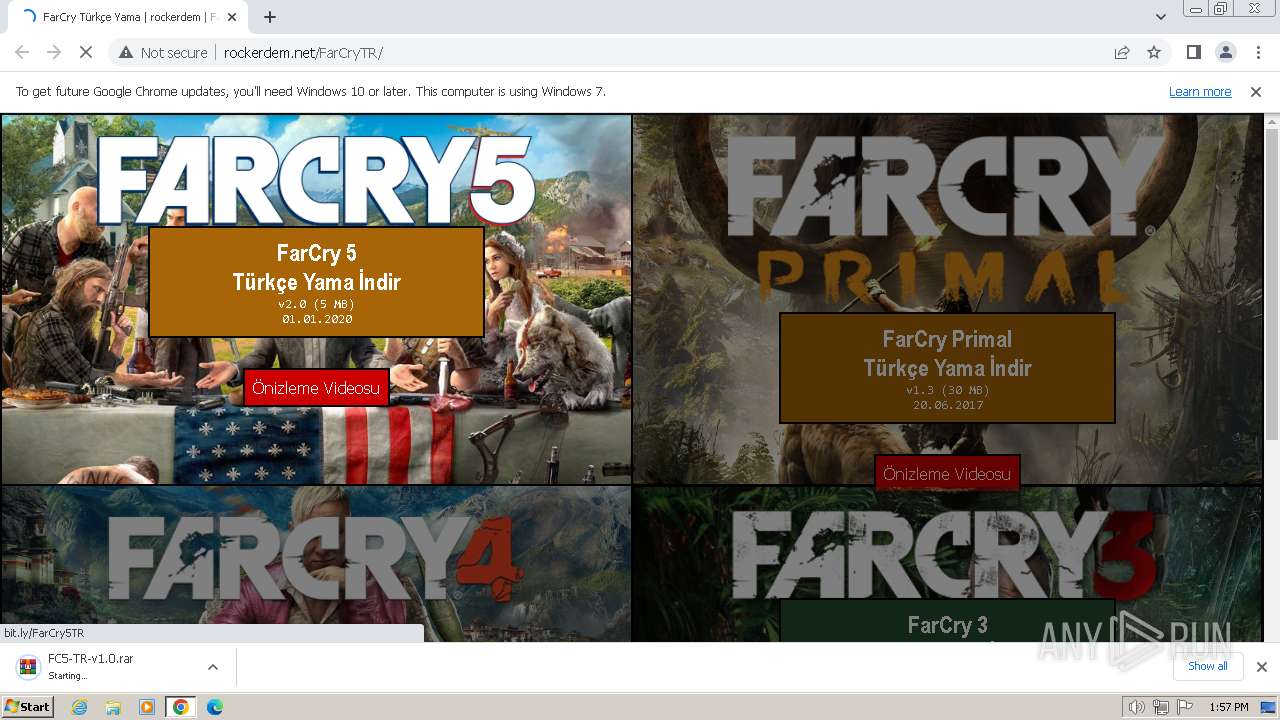
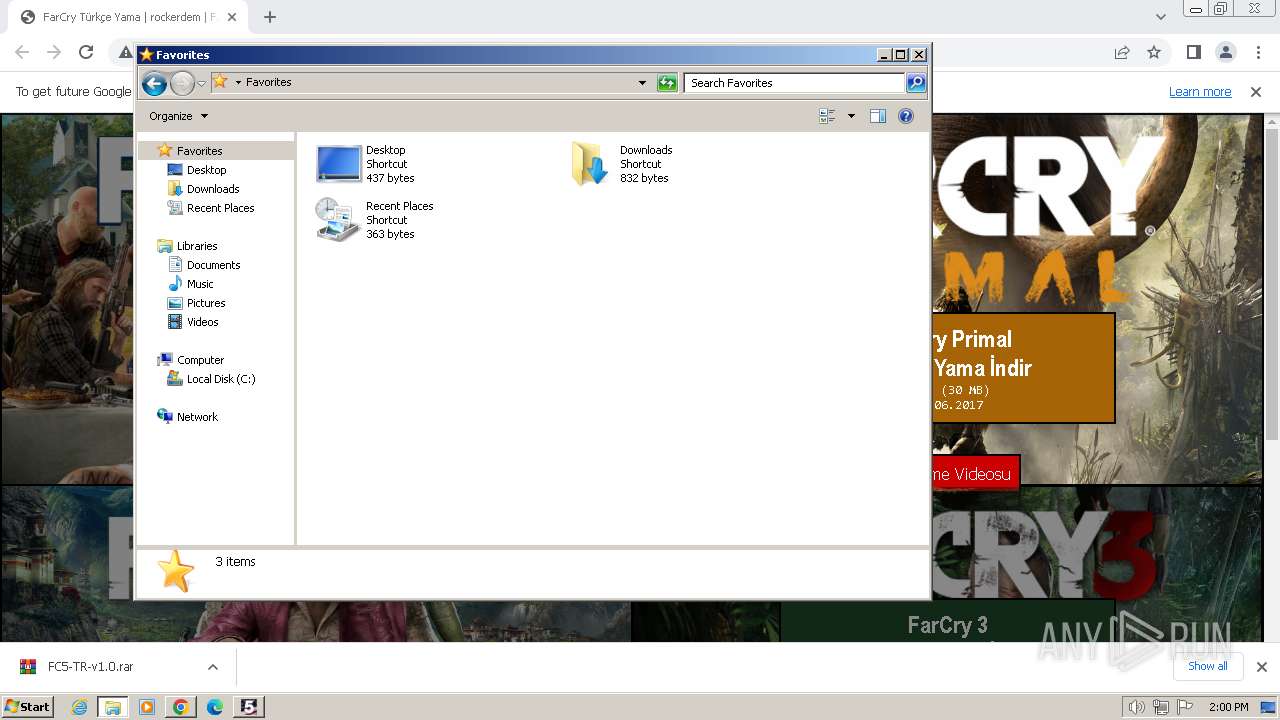
| URL: | http://rockerdem.net/FarCryTR/ |
| Full analysis: | https://app.any.run/tasks/b72b0f22-1afa-4a9b-9562-4eb8cfdc3302 |
| Verdict: | Malicious activity |
| Analysis date: | March 05, 2024, 13:57:30 |
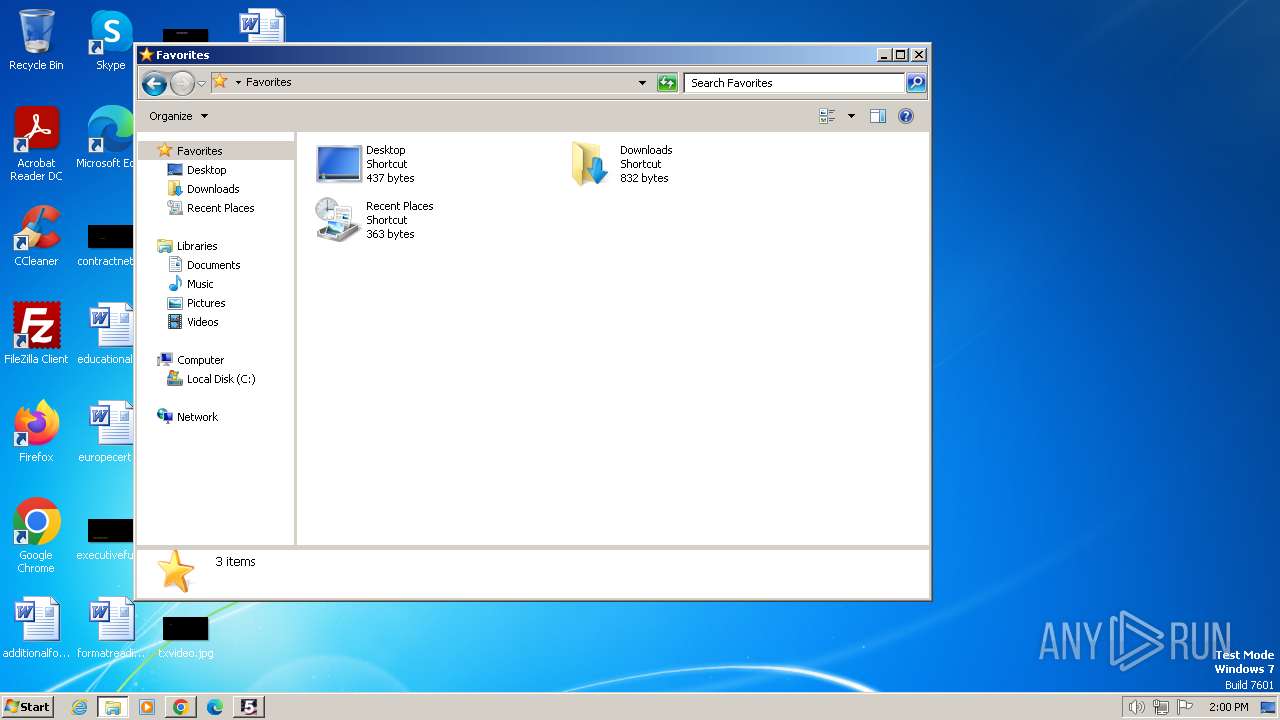
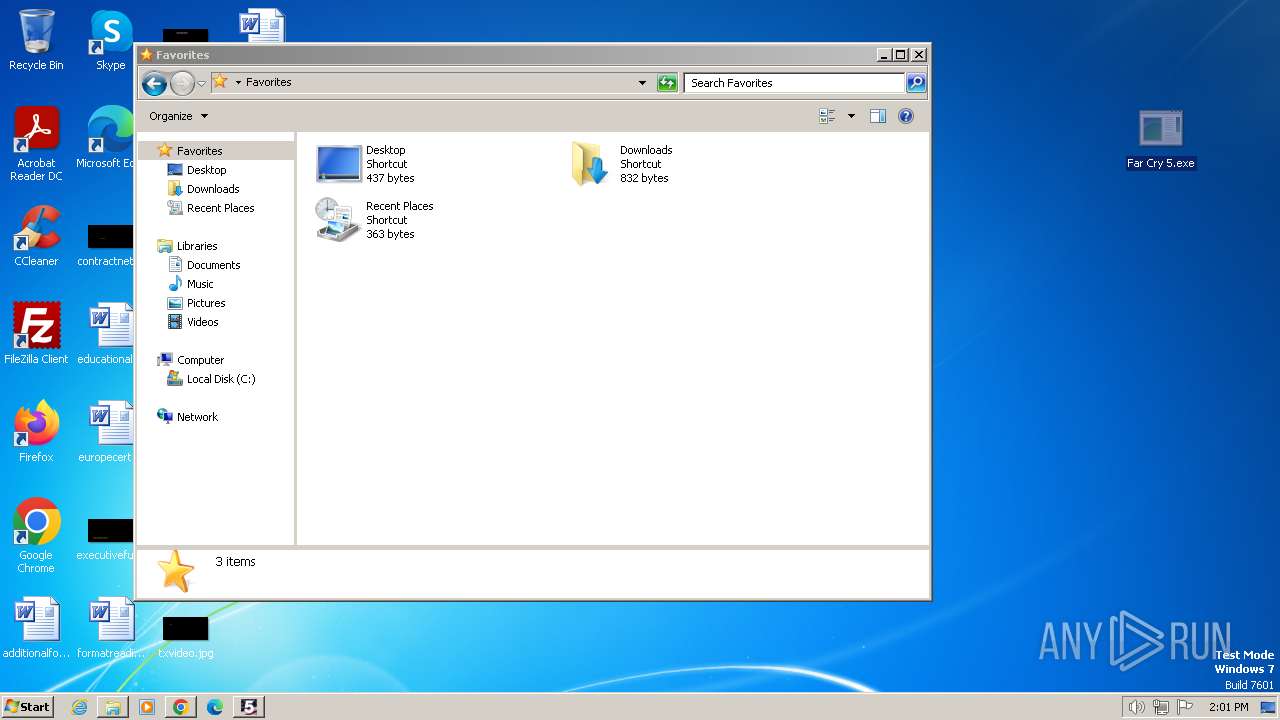
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 035A18D0DDFF5B26CEEBAC7C49F2AFF9 |
| SHA1: | D59B706941E6071F22614CEE508955CFE62286E6 |
| SHA256: | 89A9FC284D30191B26CEE13F52DD75CA6D8DE3085E17E7A49551A3064A9800A9 |
| SSDEEP: | 3:N1KMBjjEXy:CMOXy |
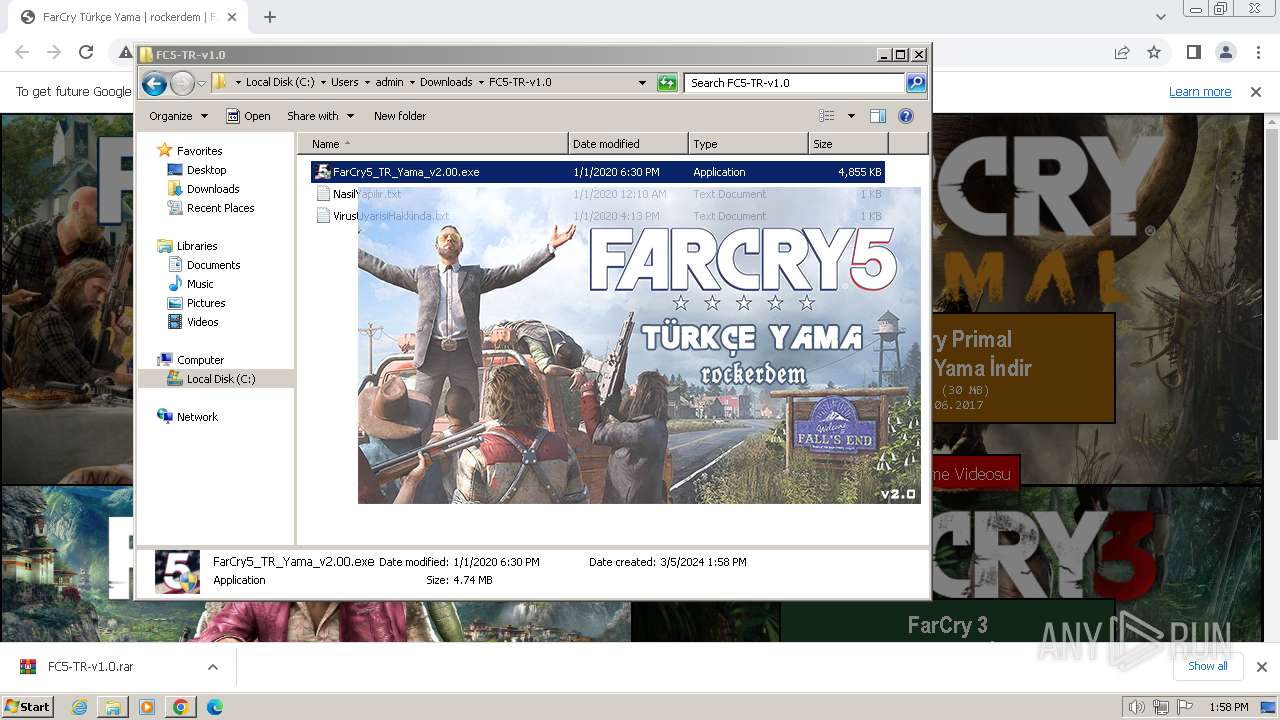
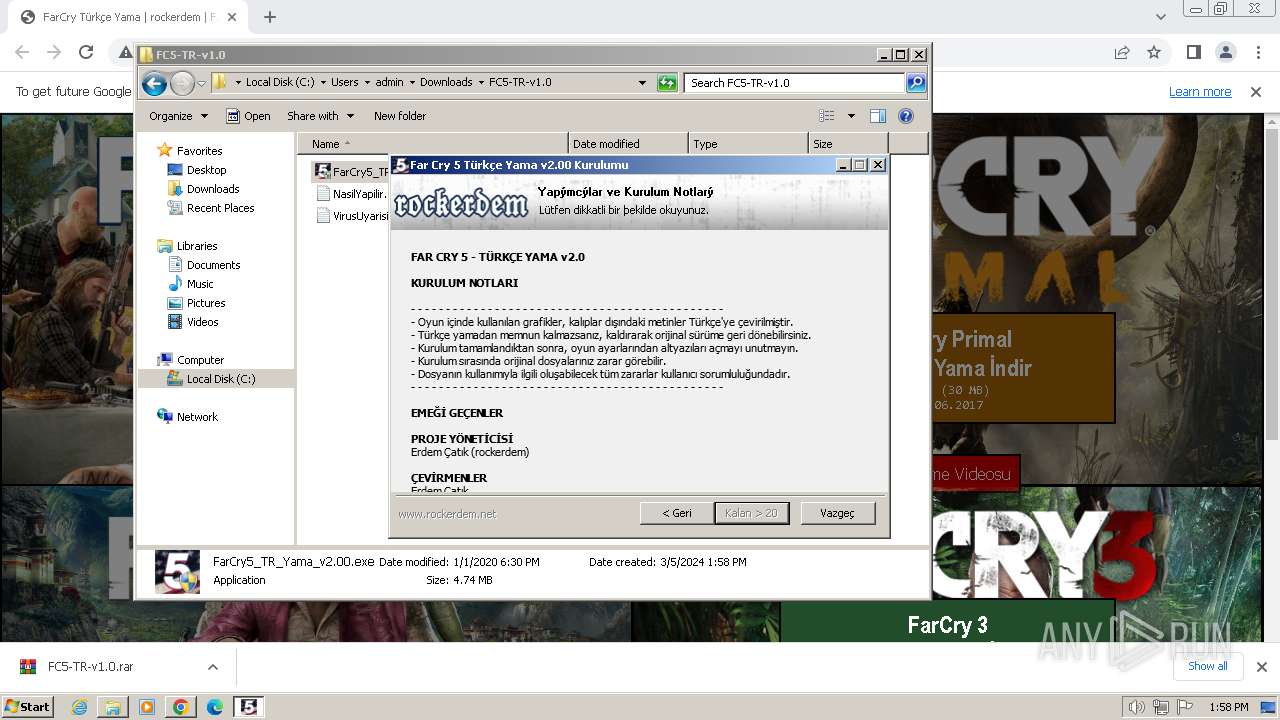
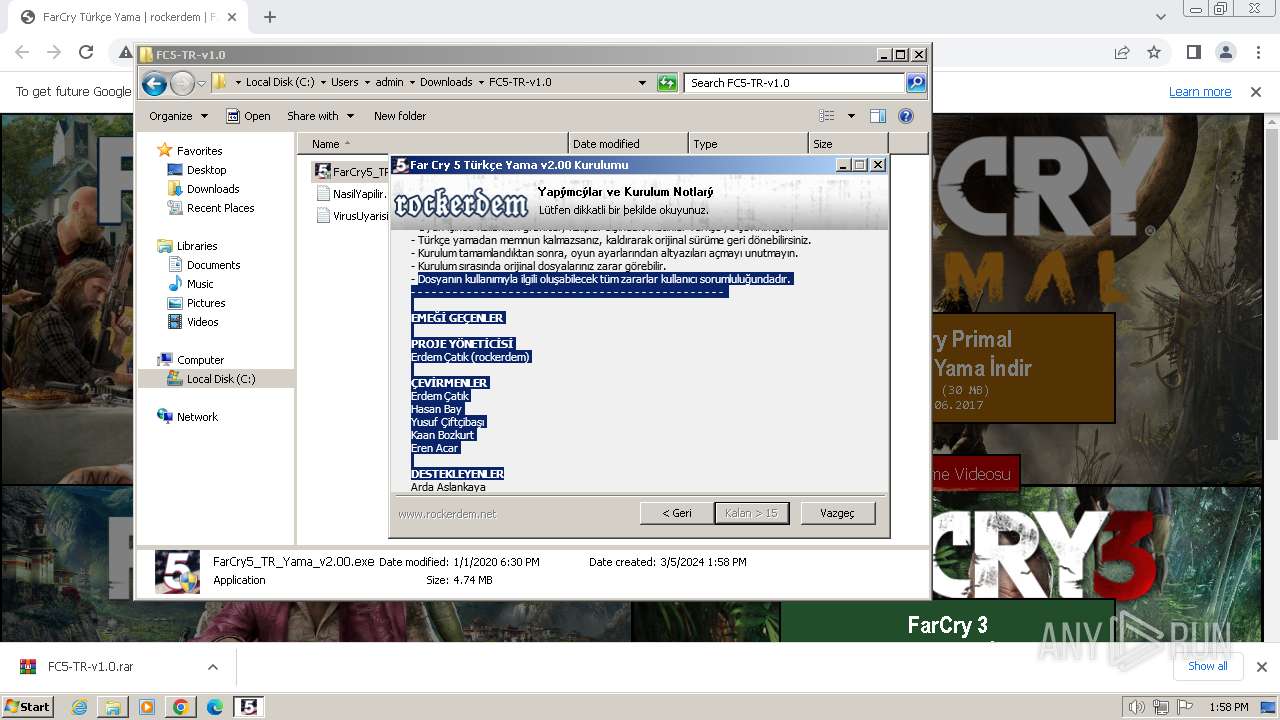
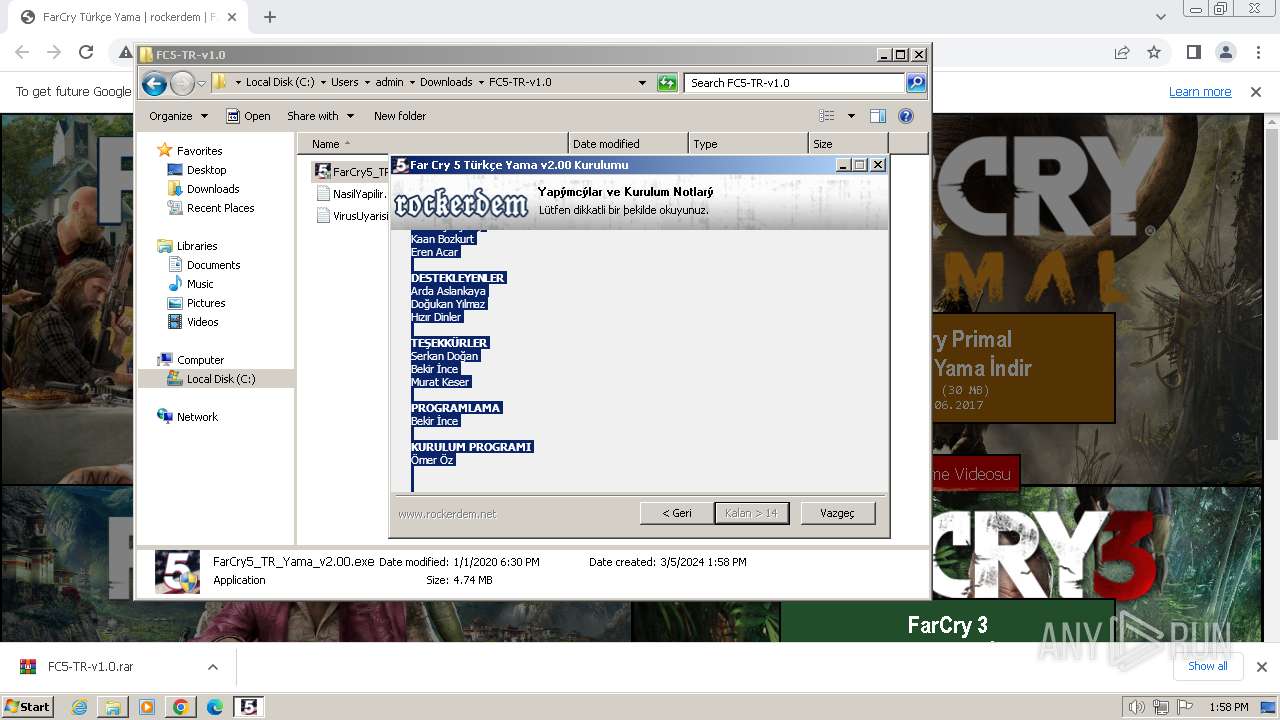
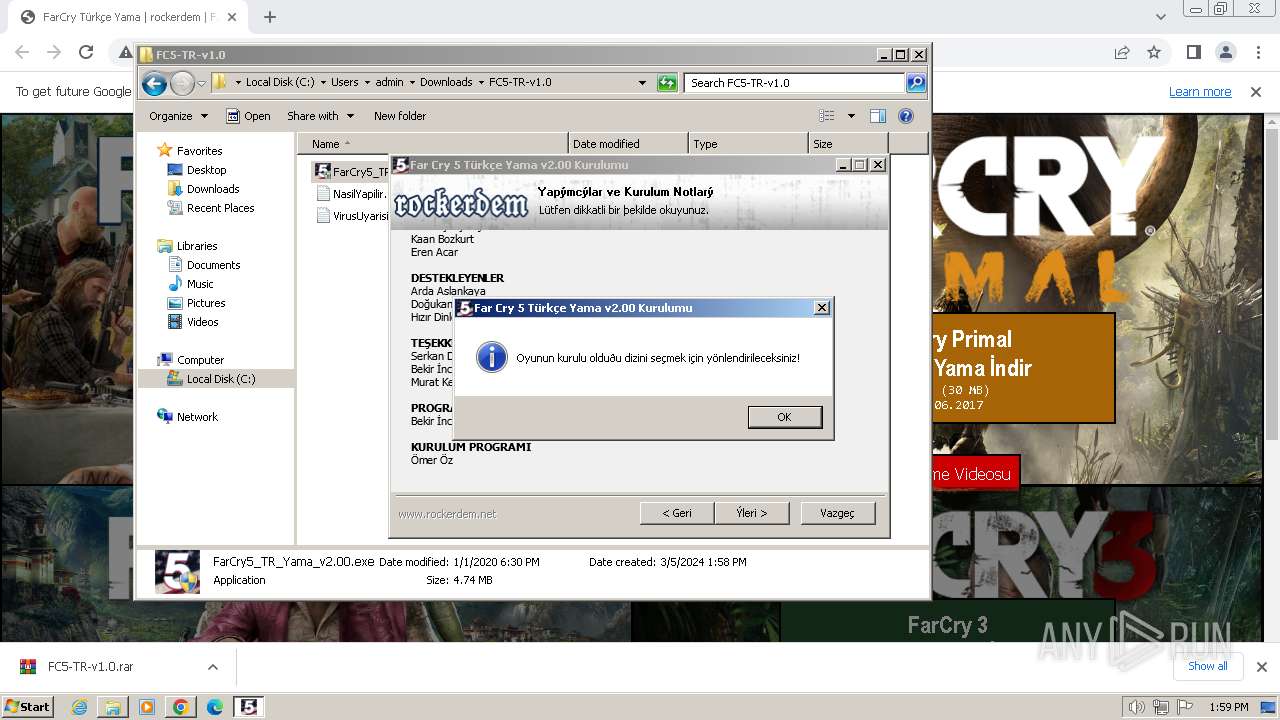
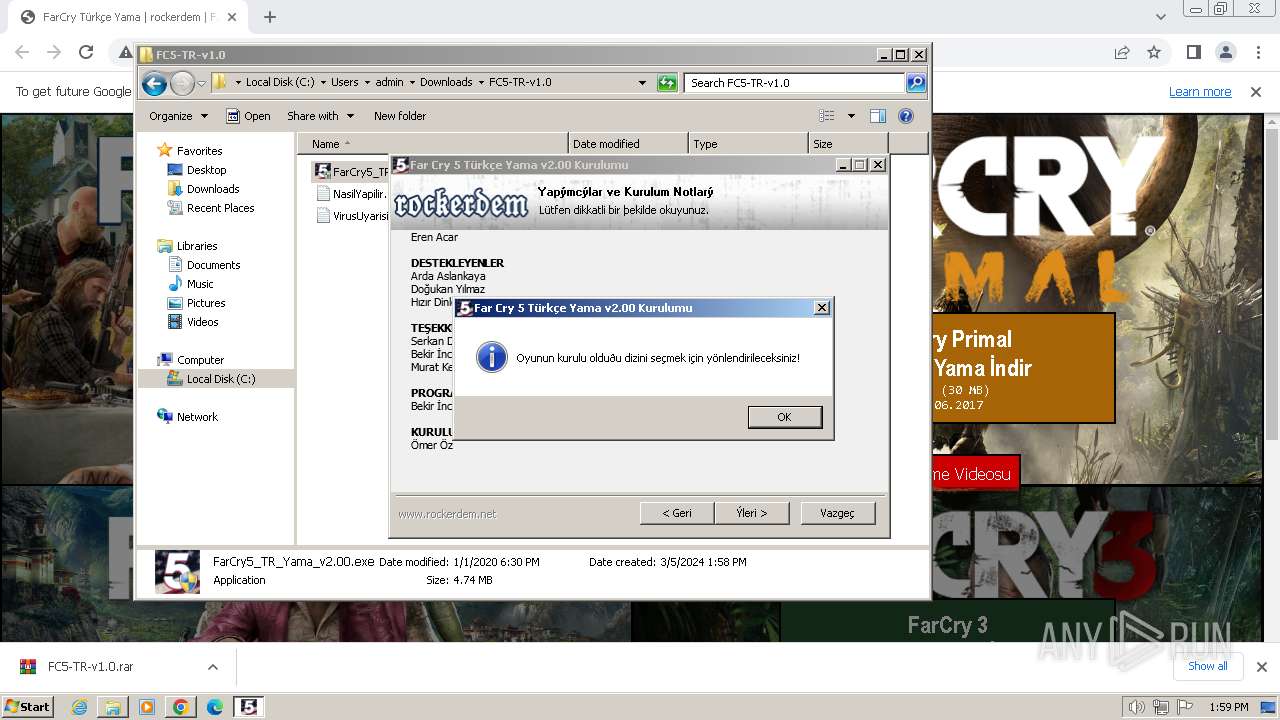
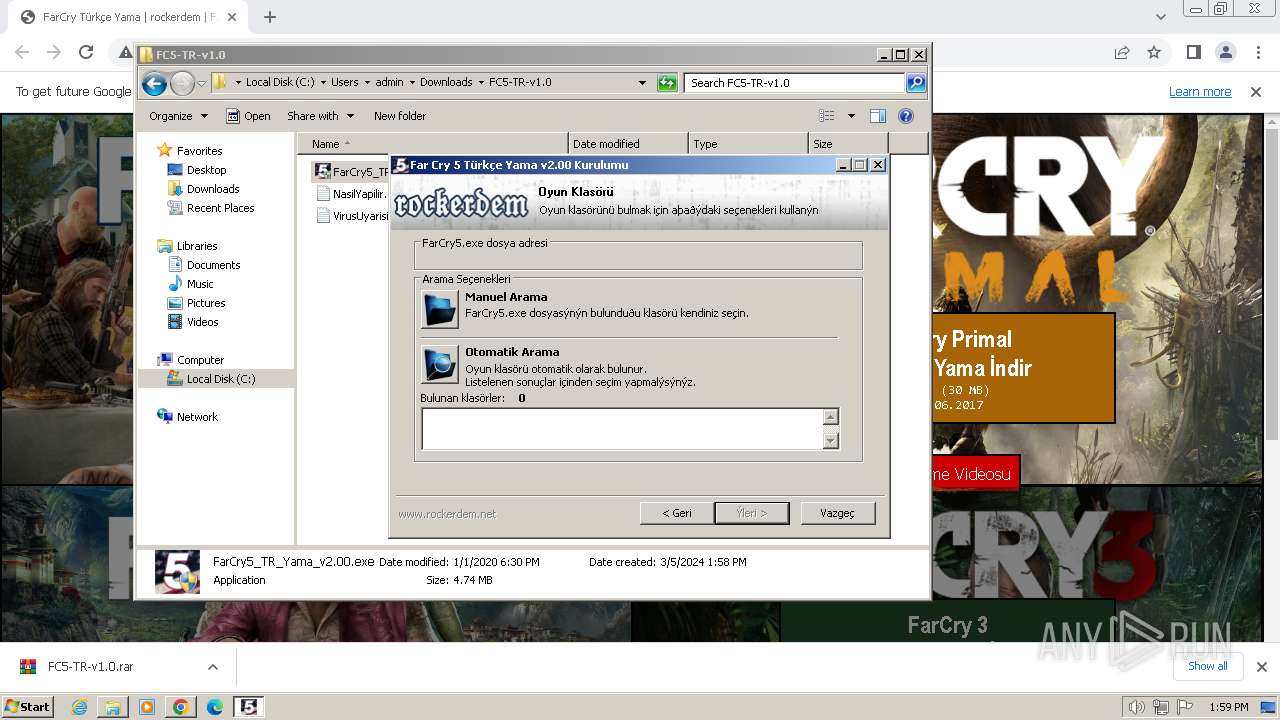
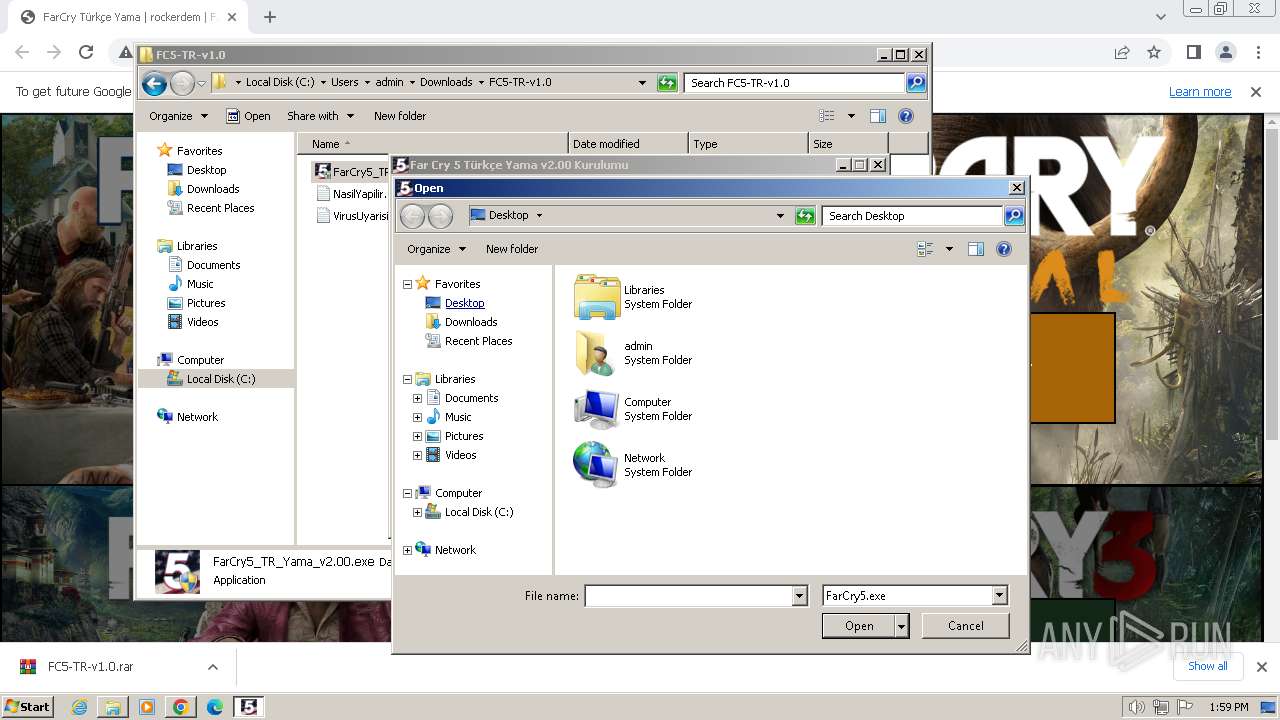
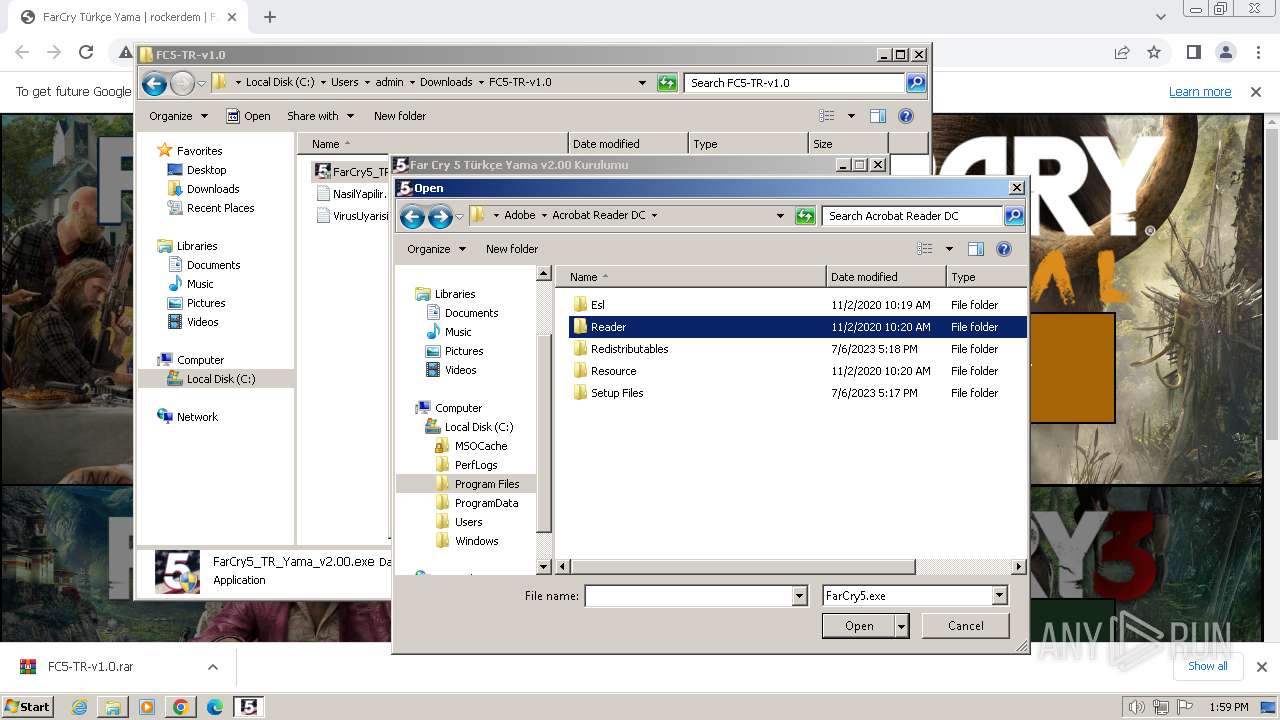
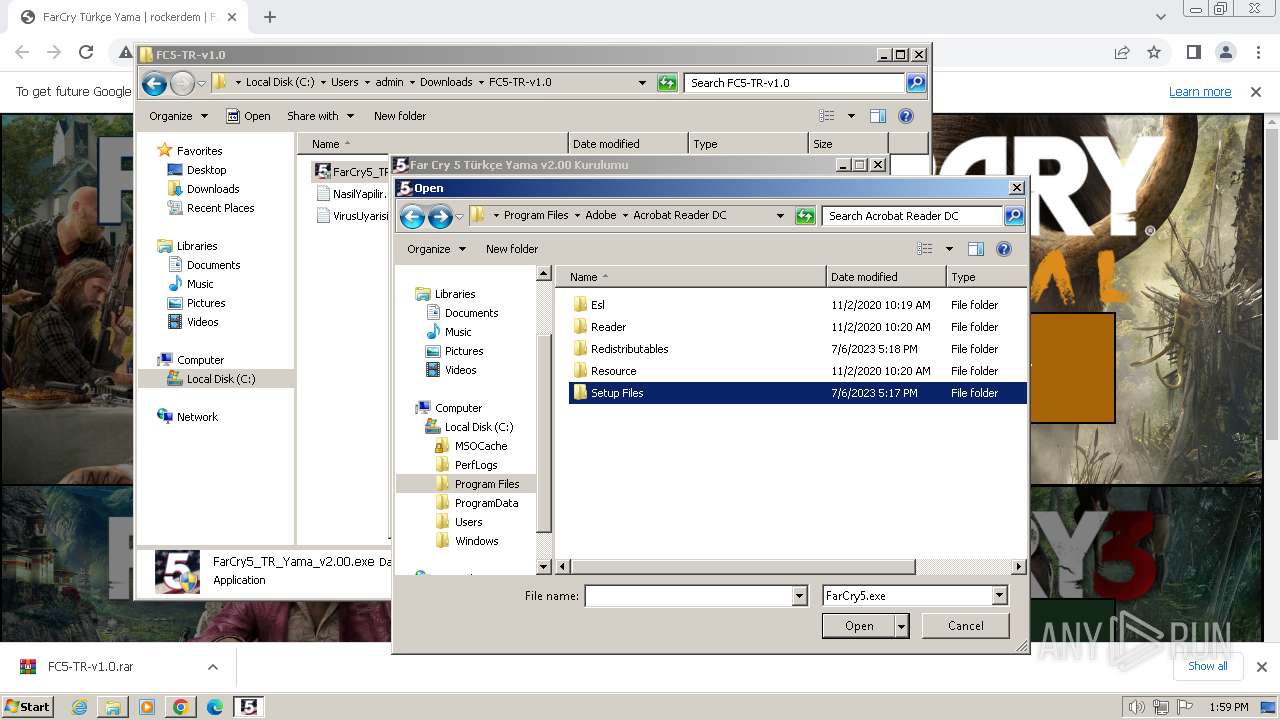
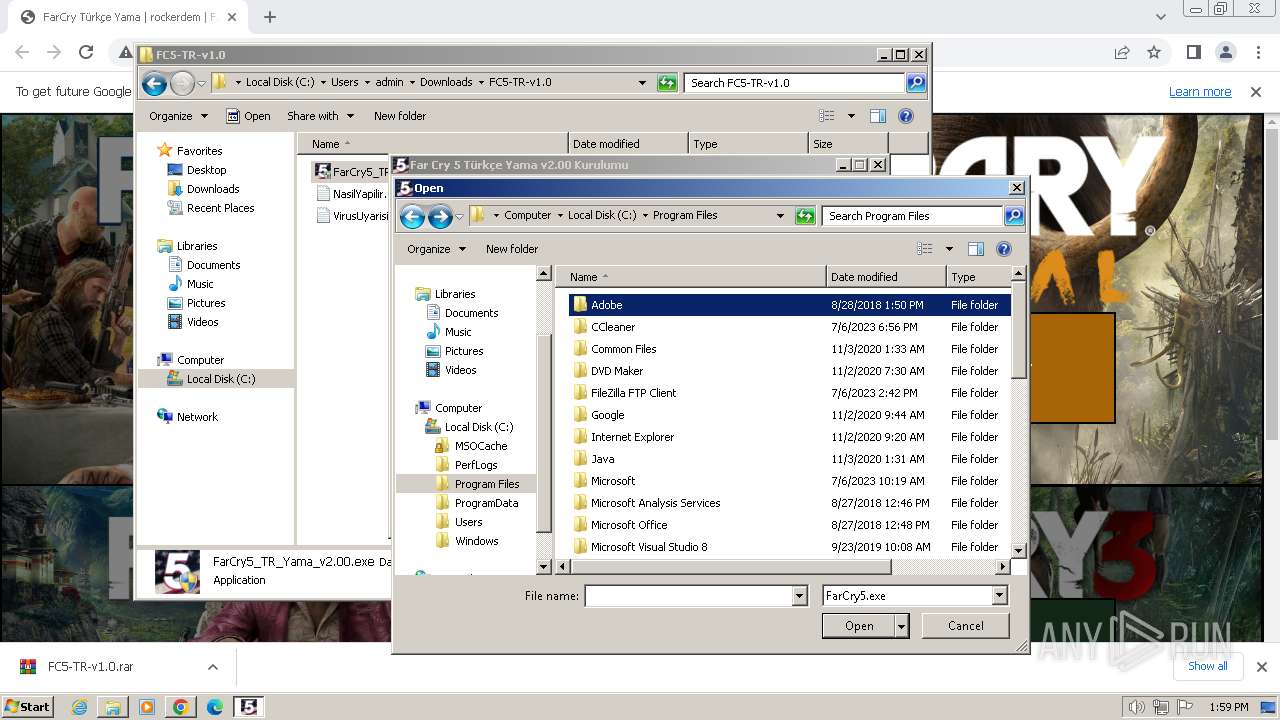
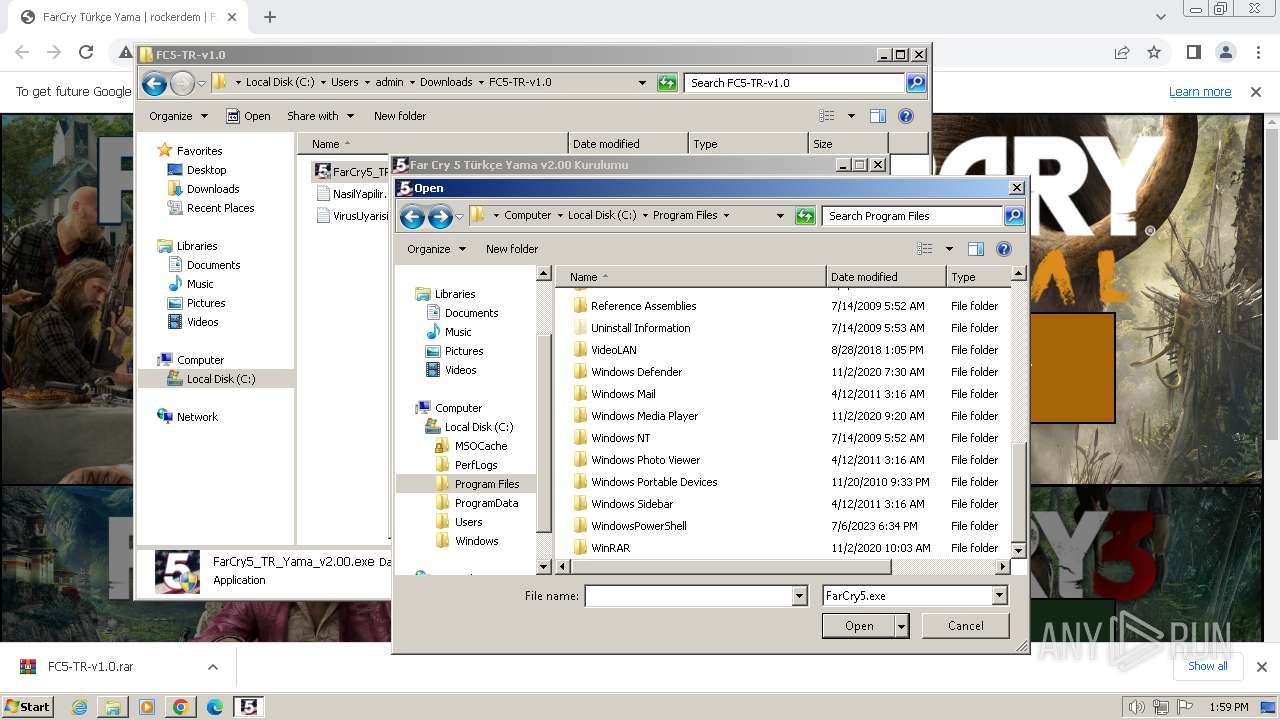
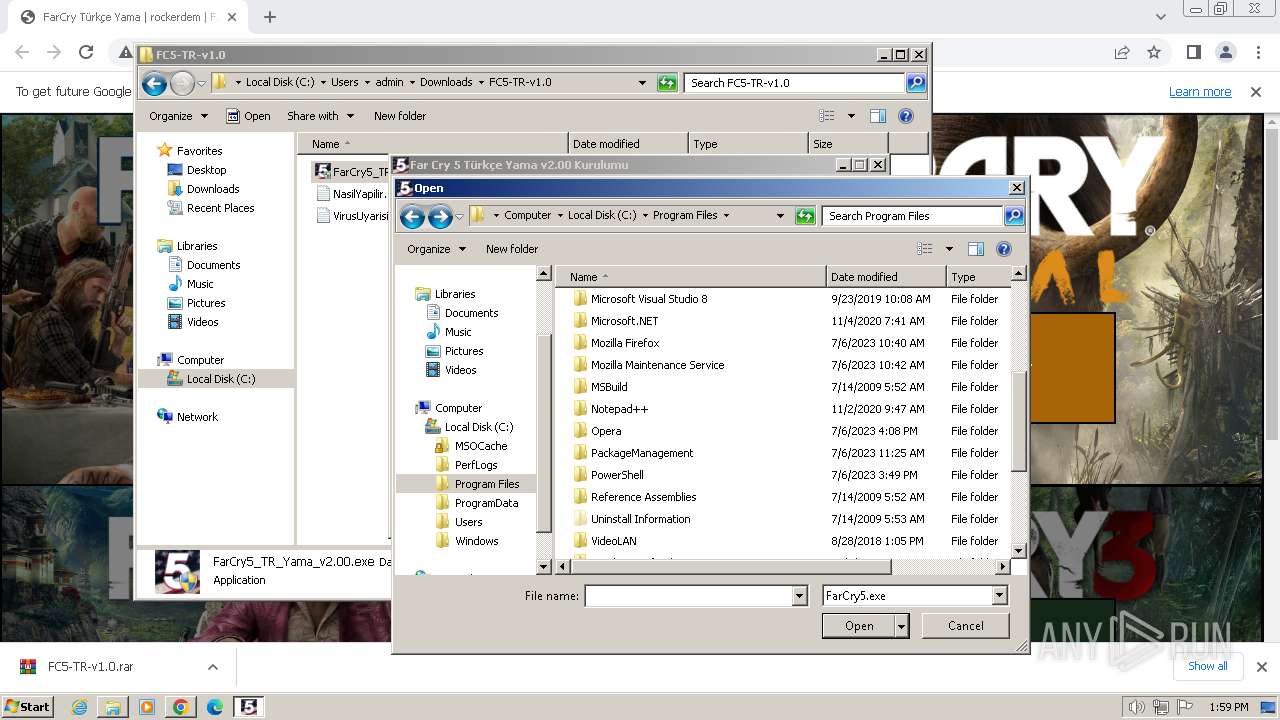
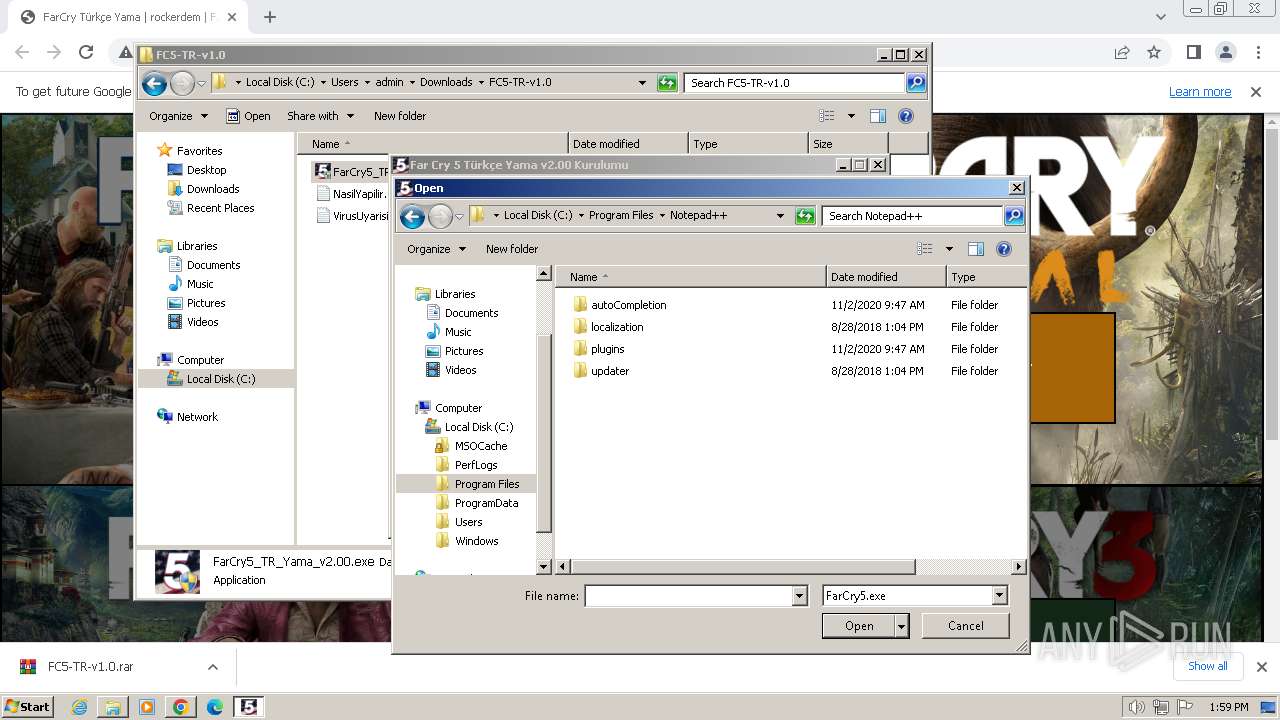
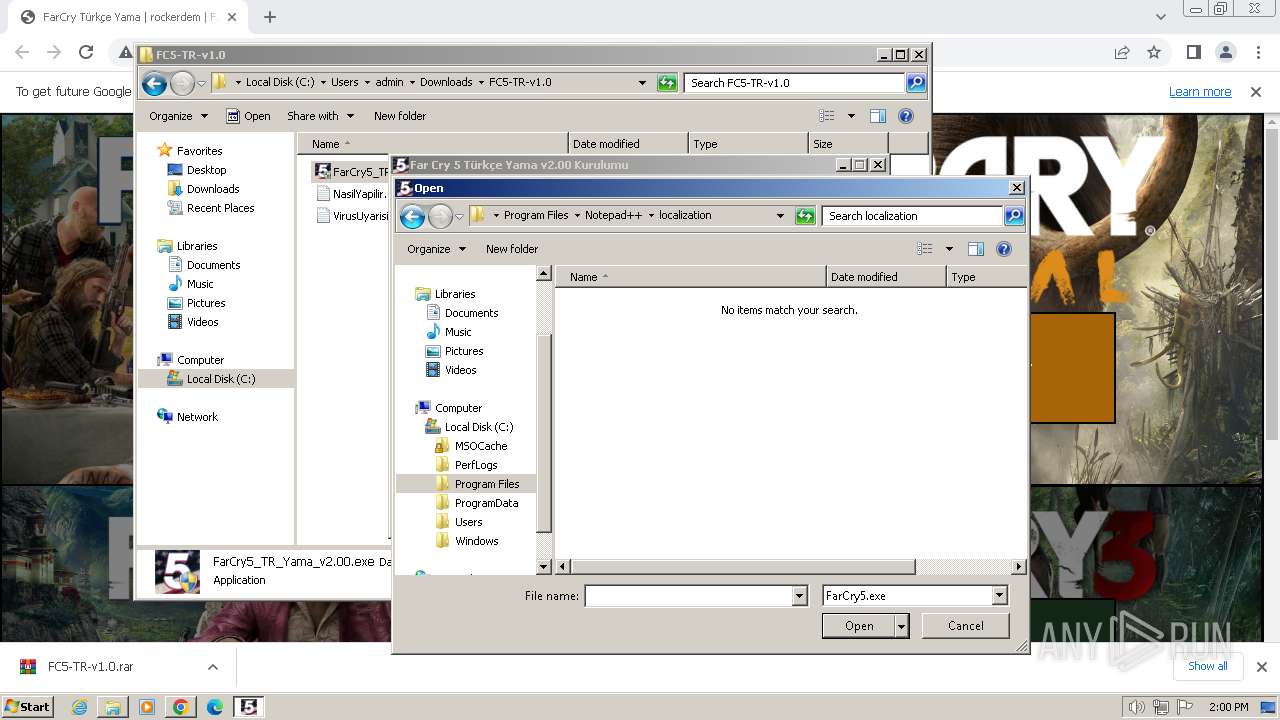
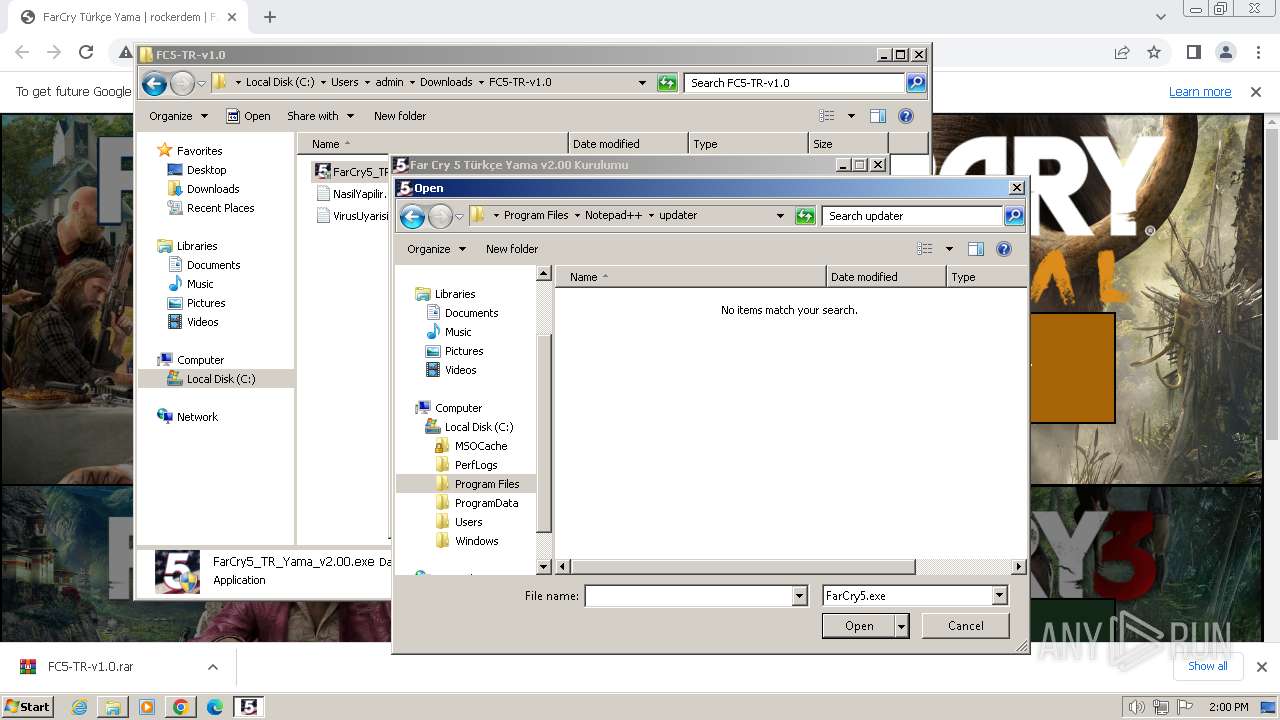
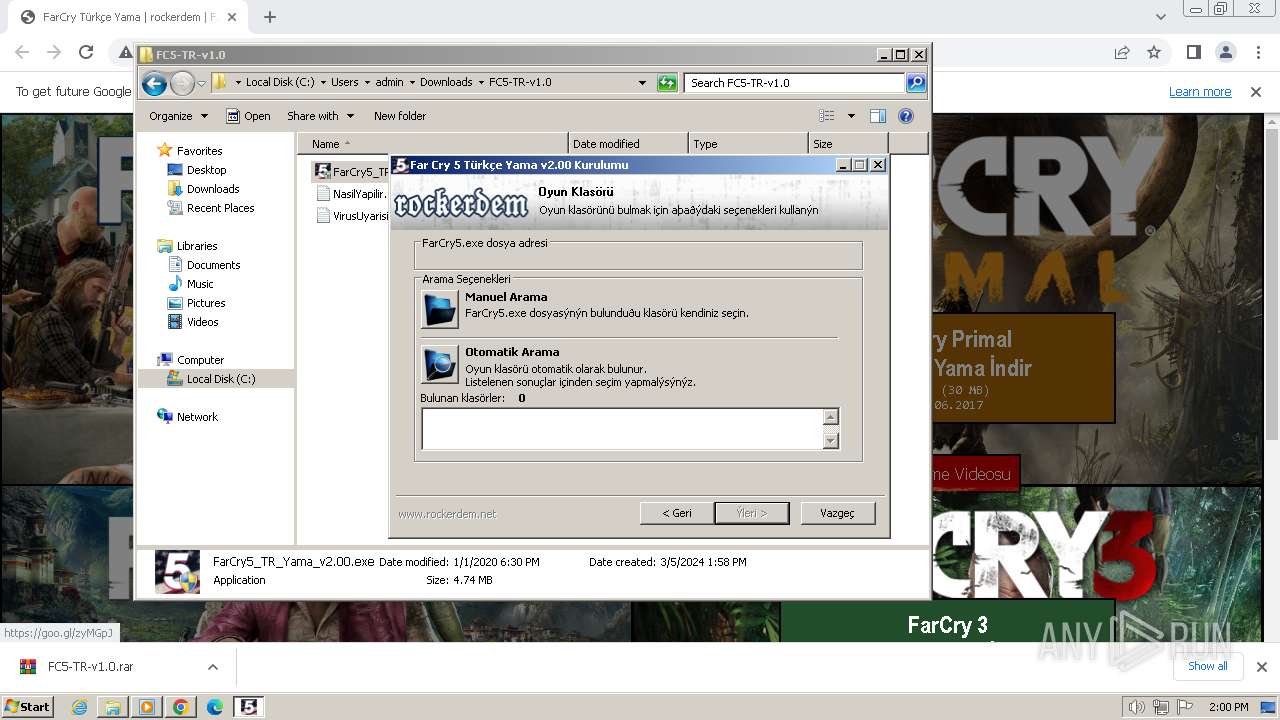
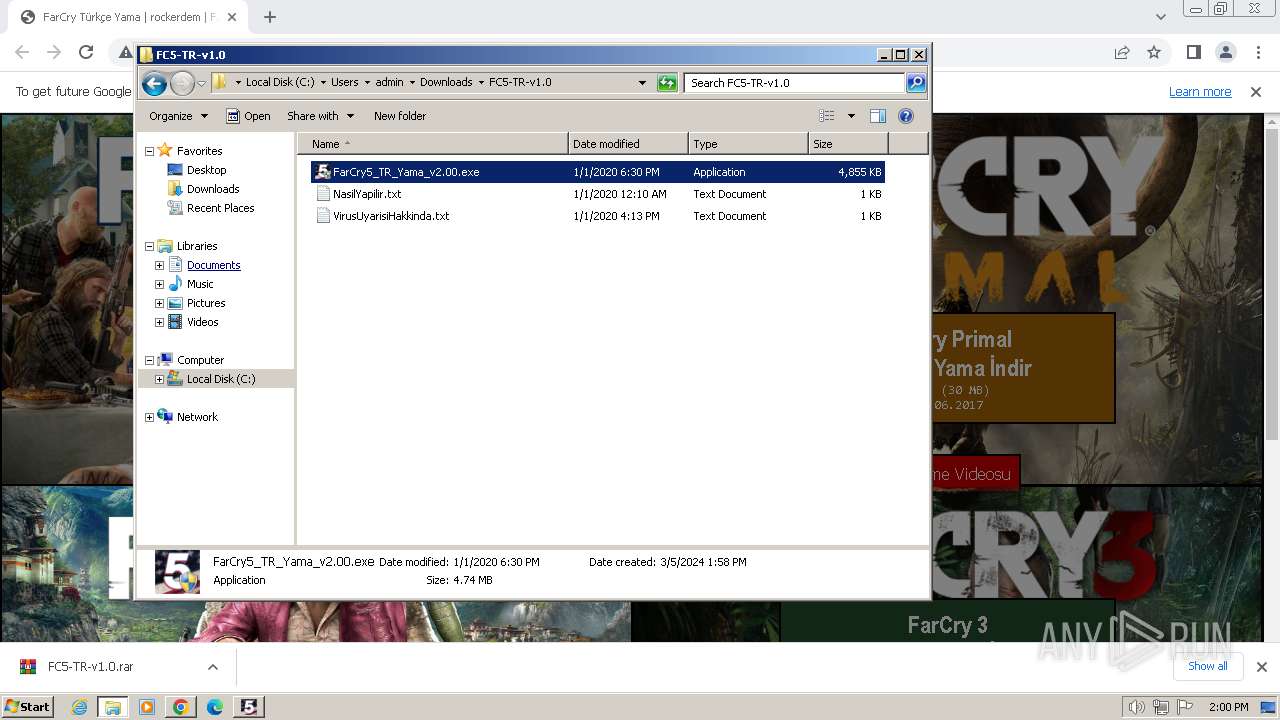
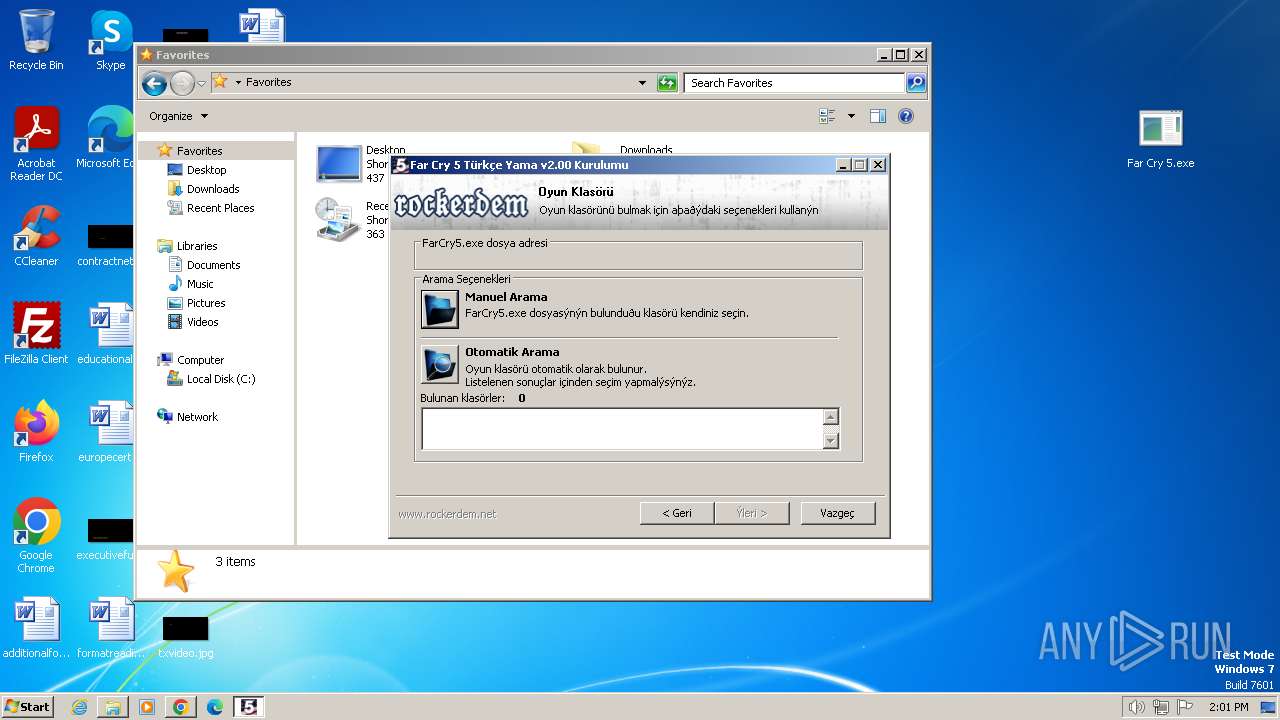
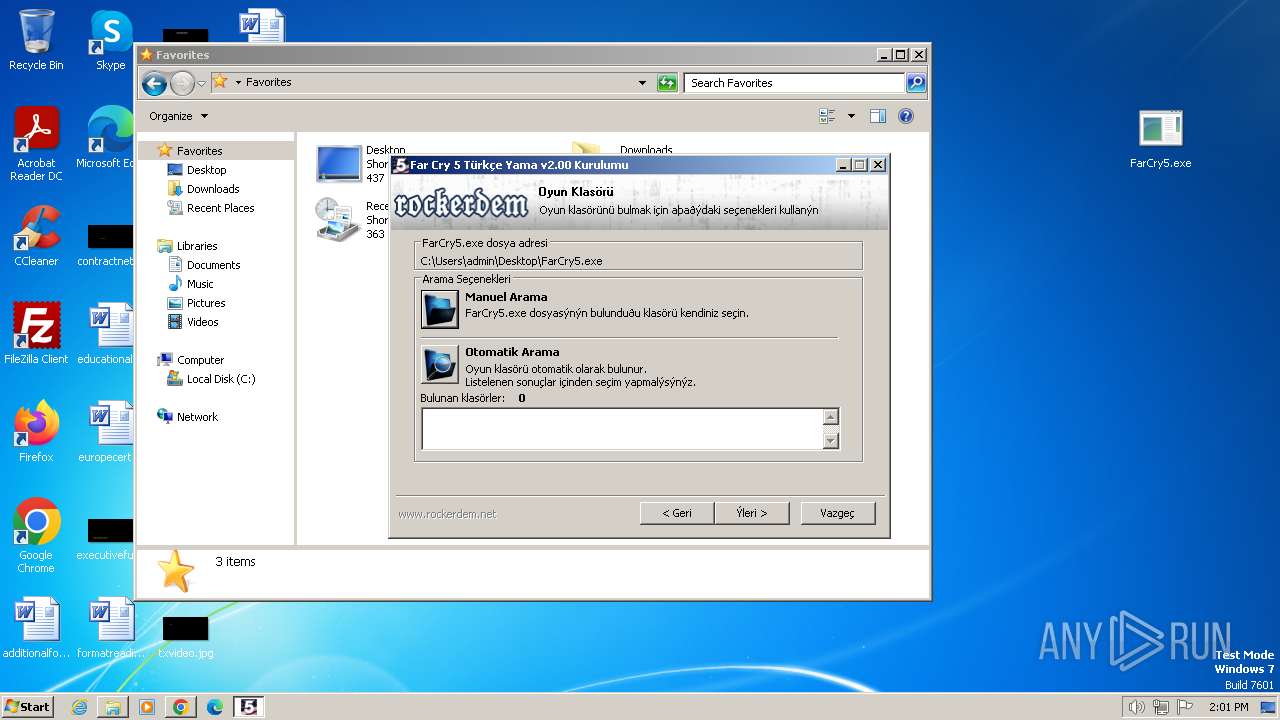
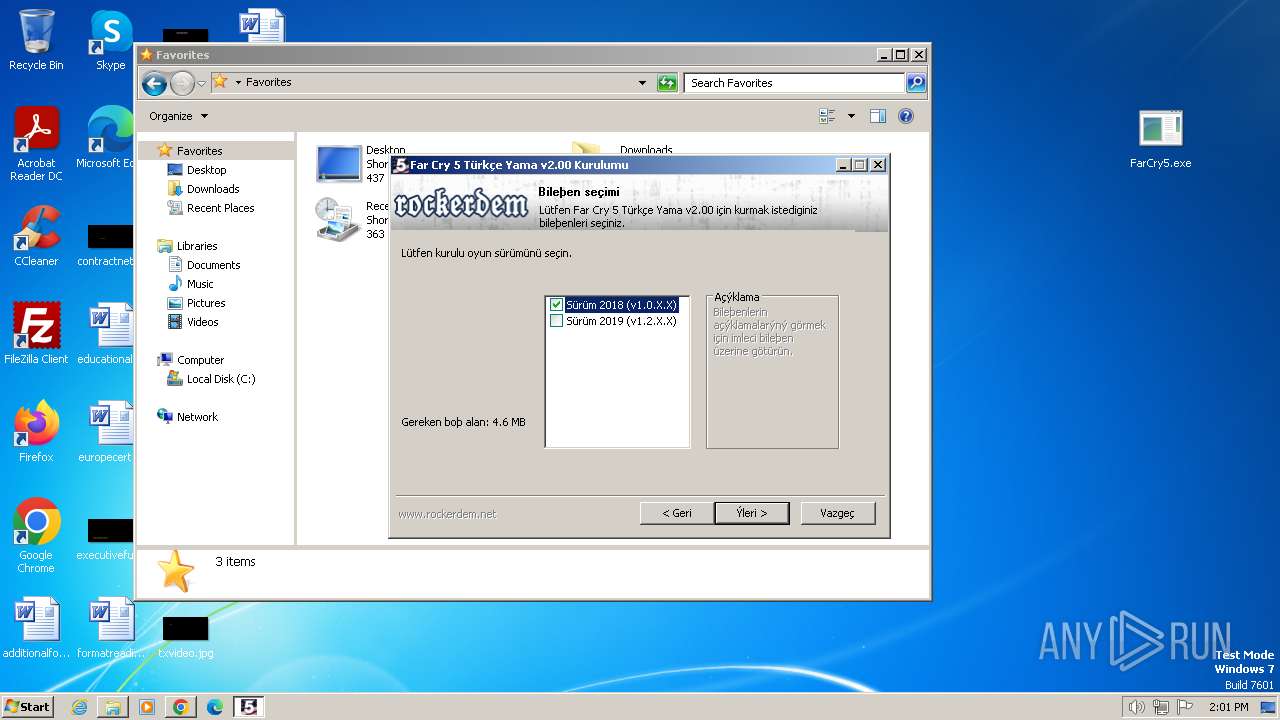
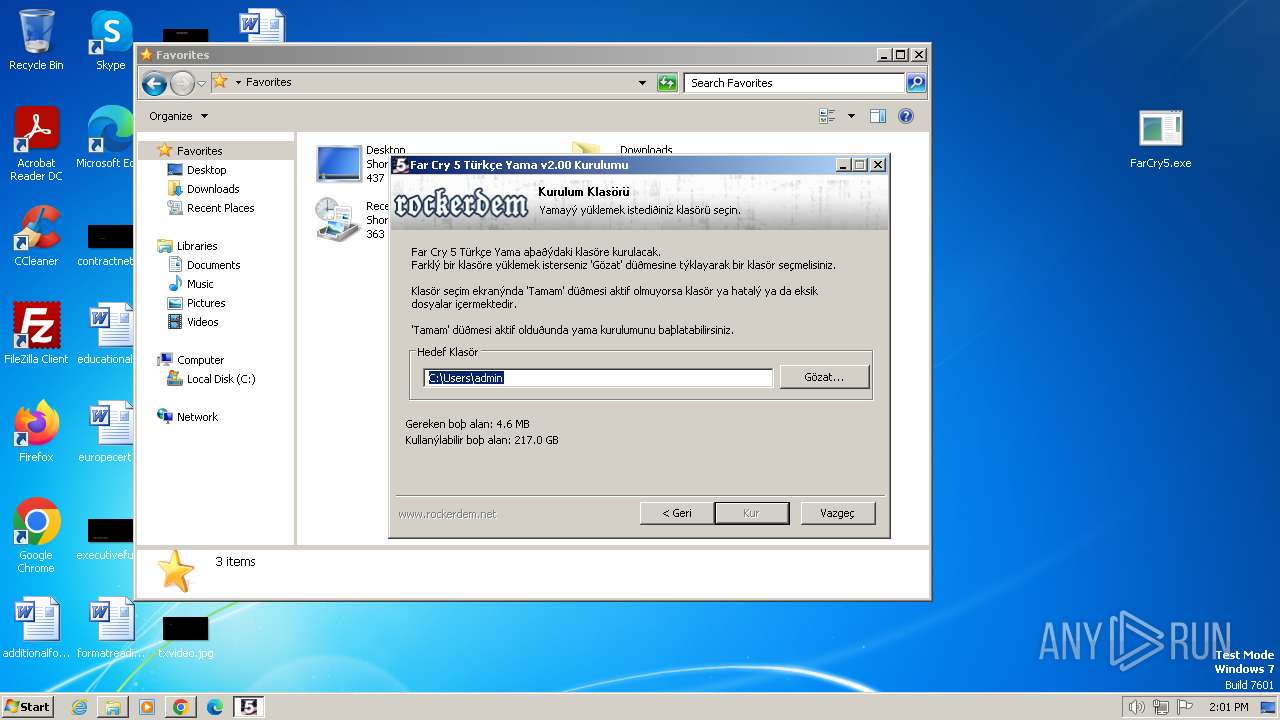
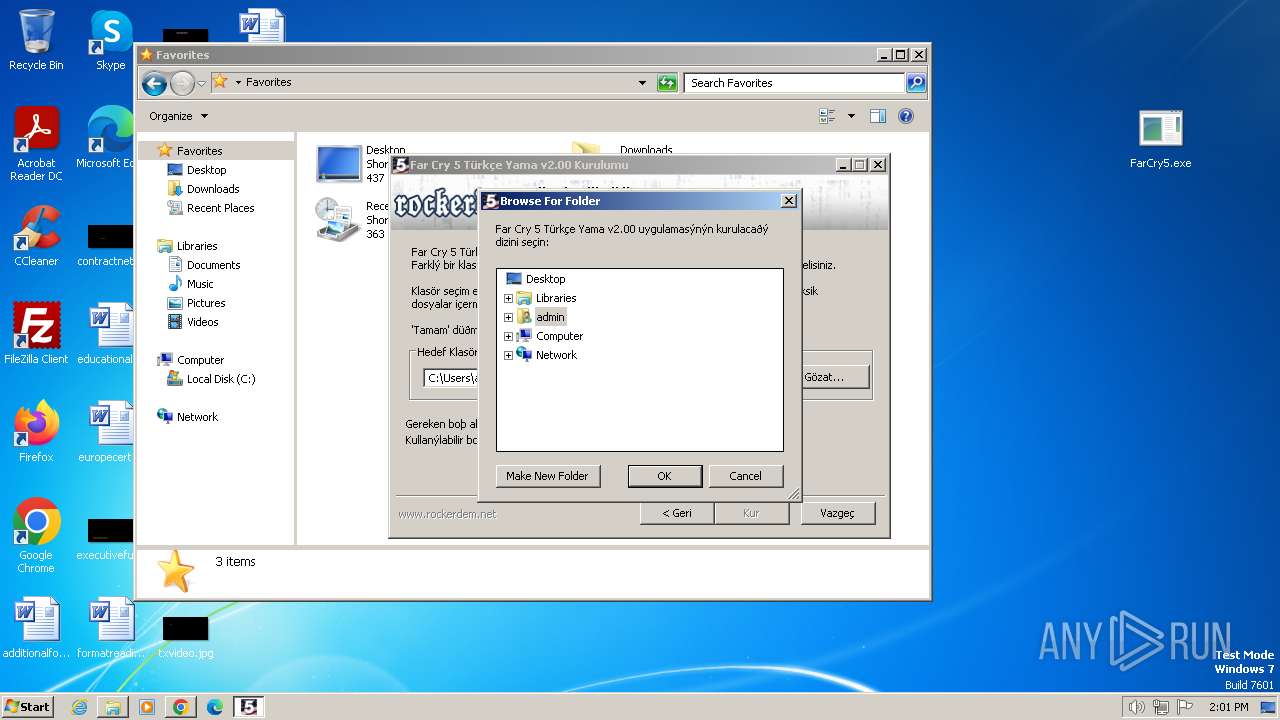
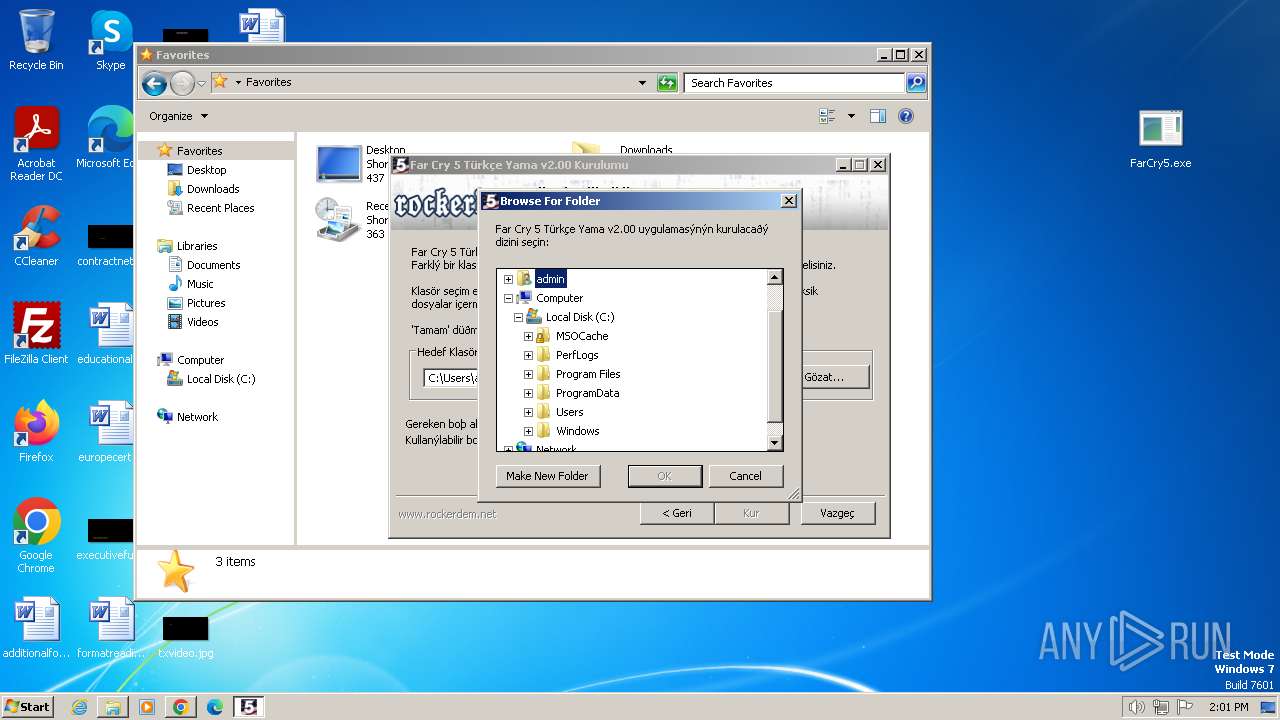
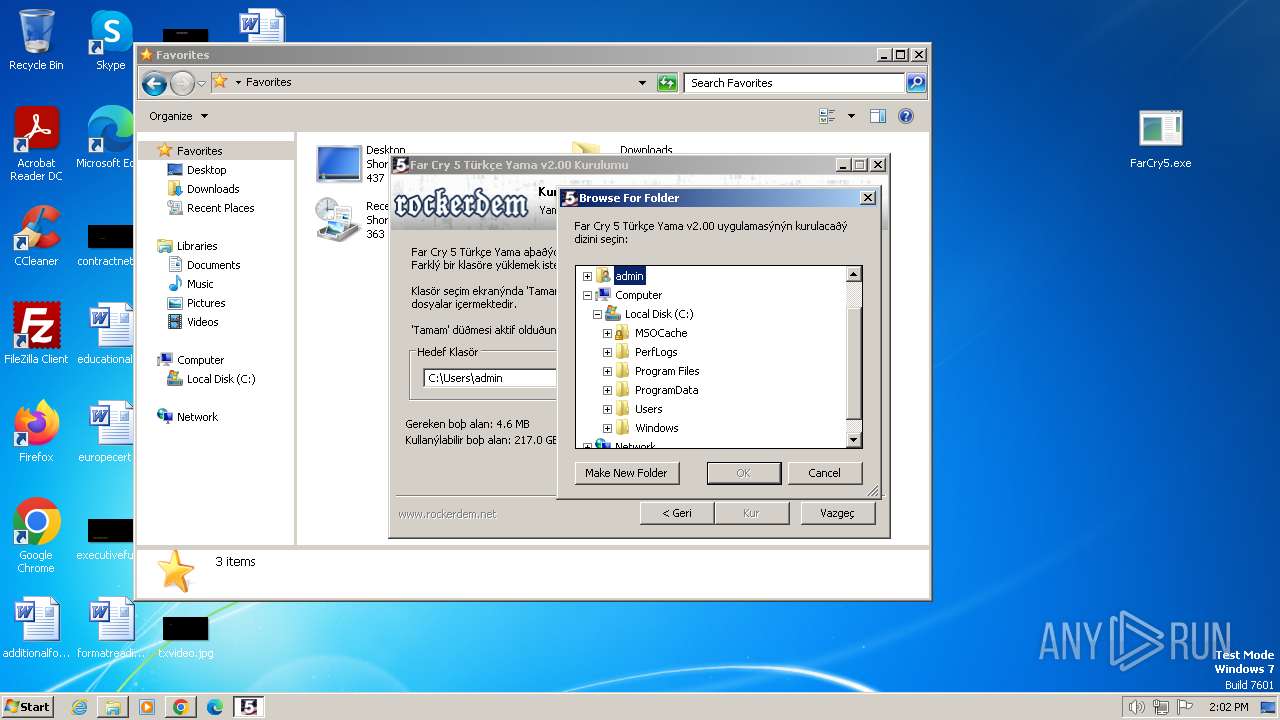
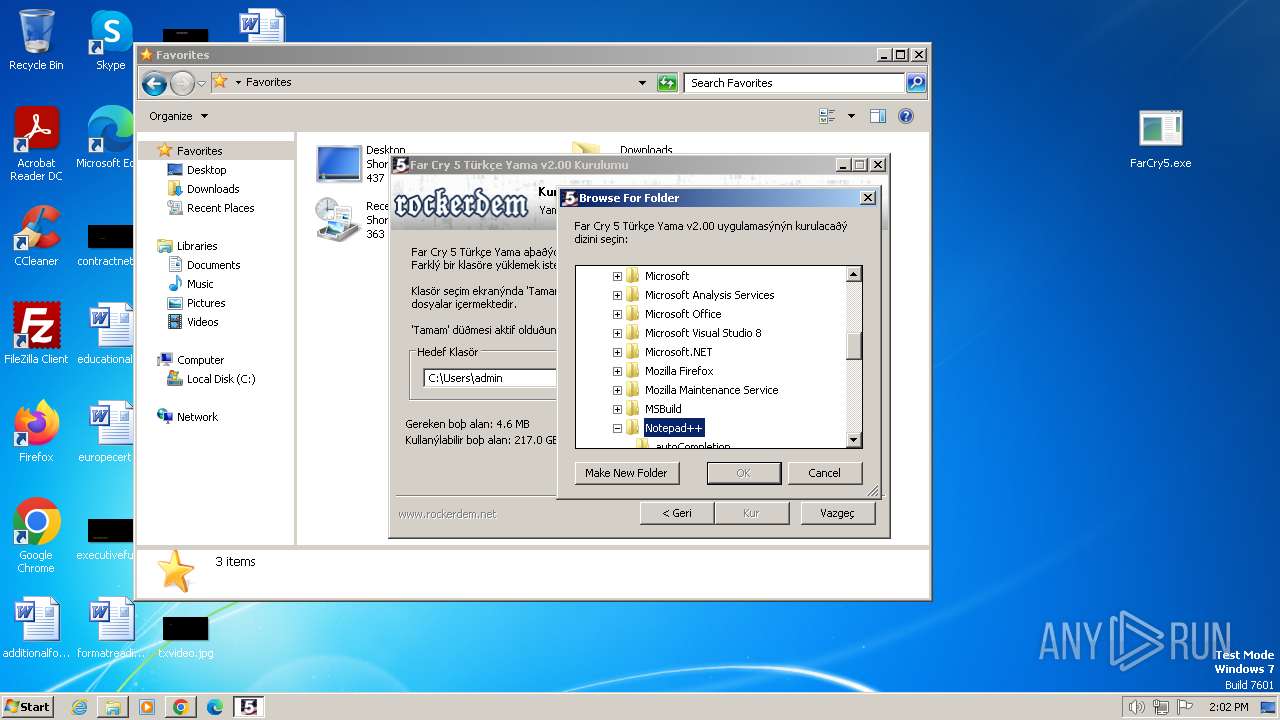
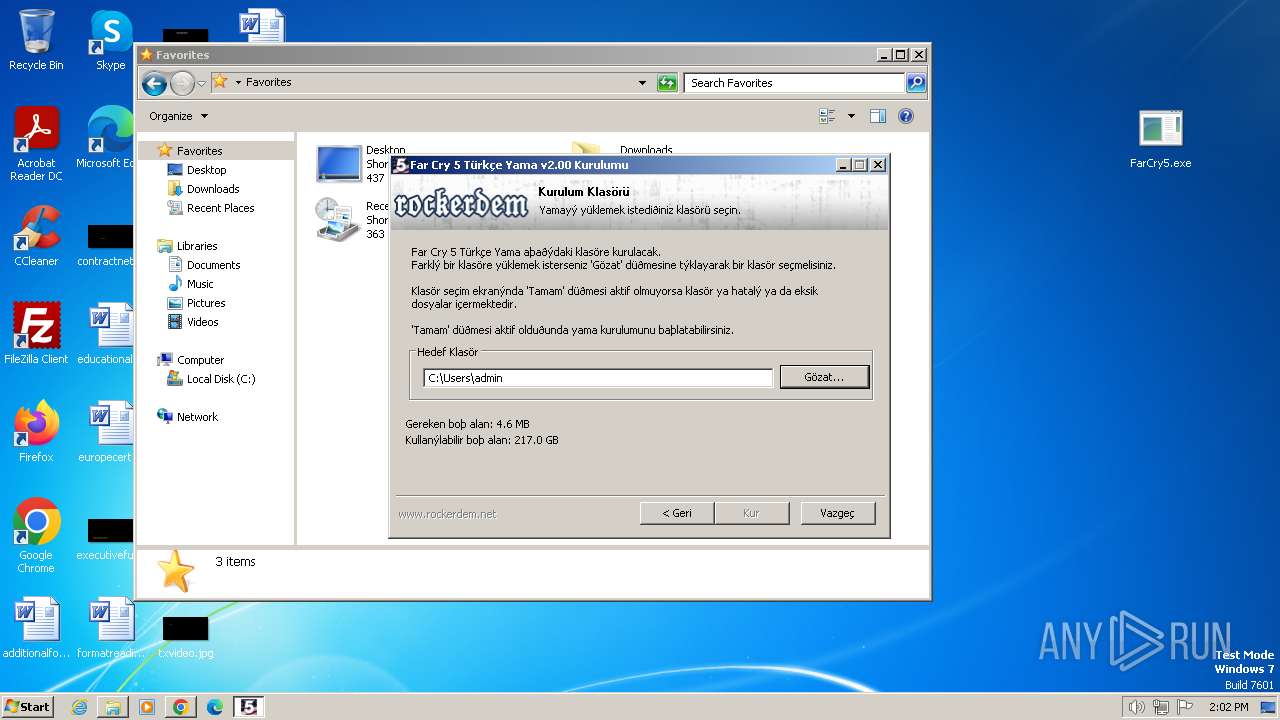
MALICIOUS
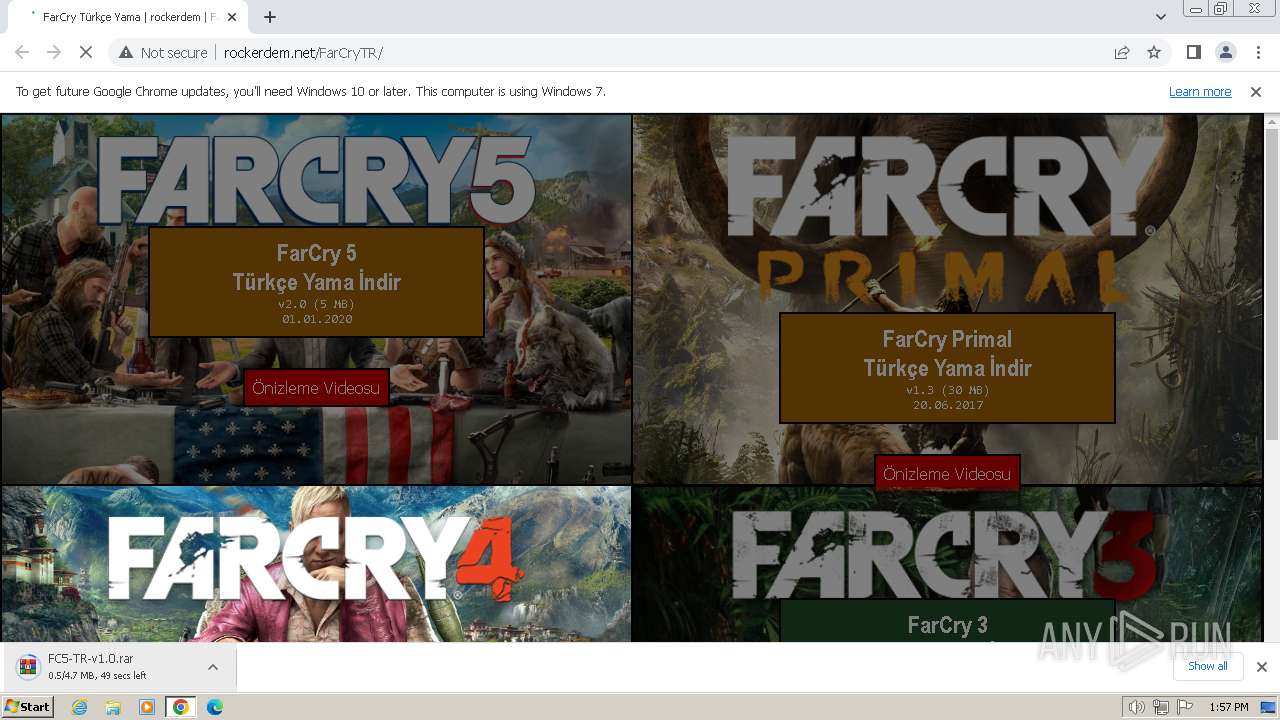
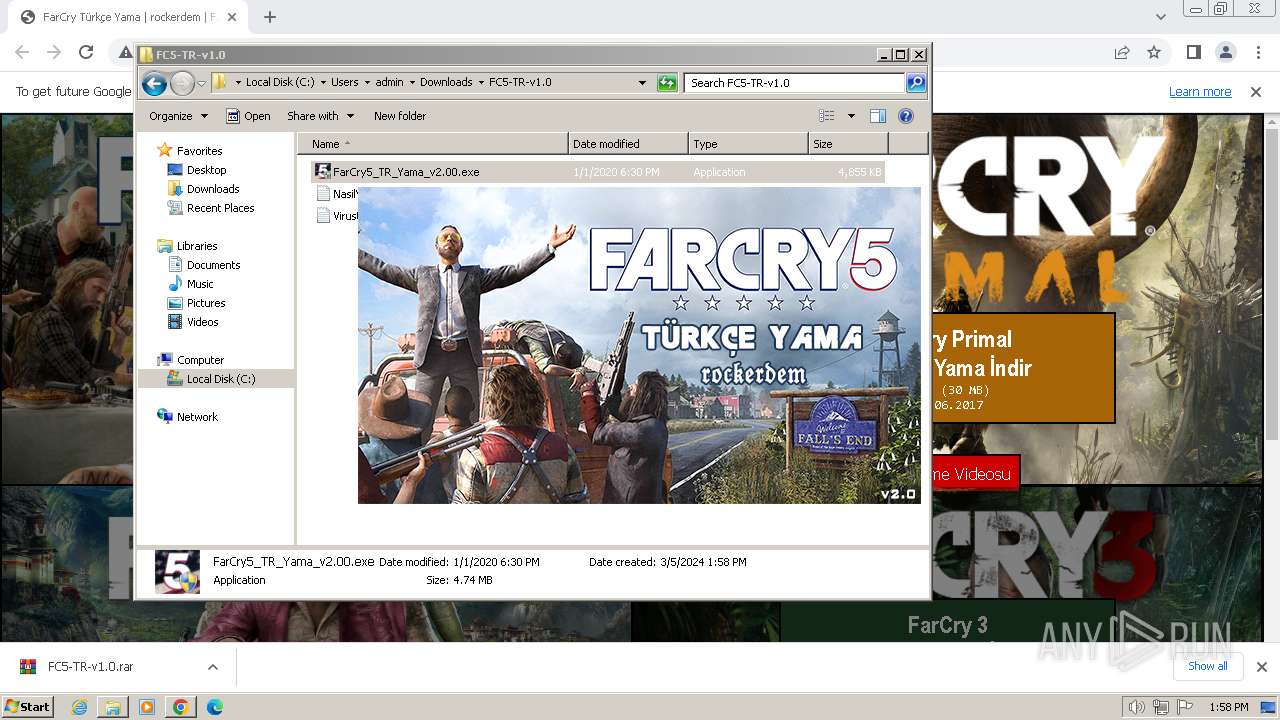
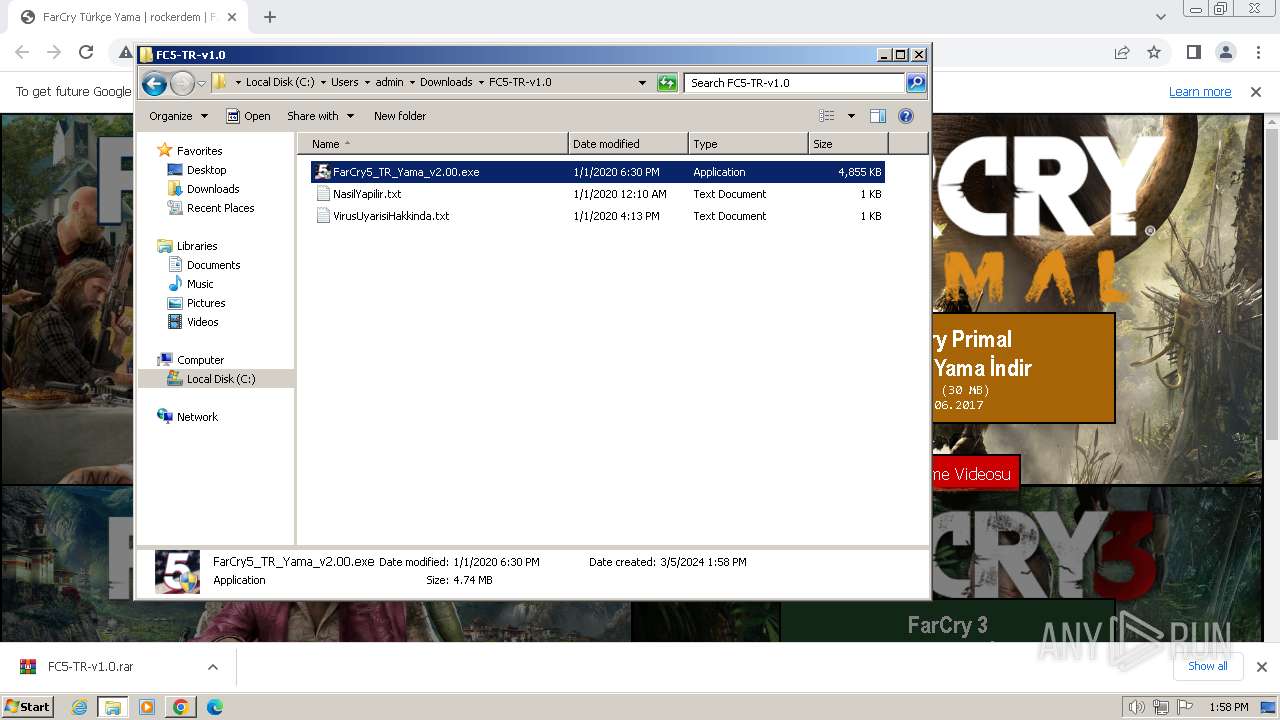
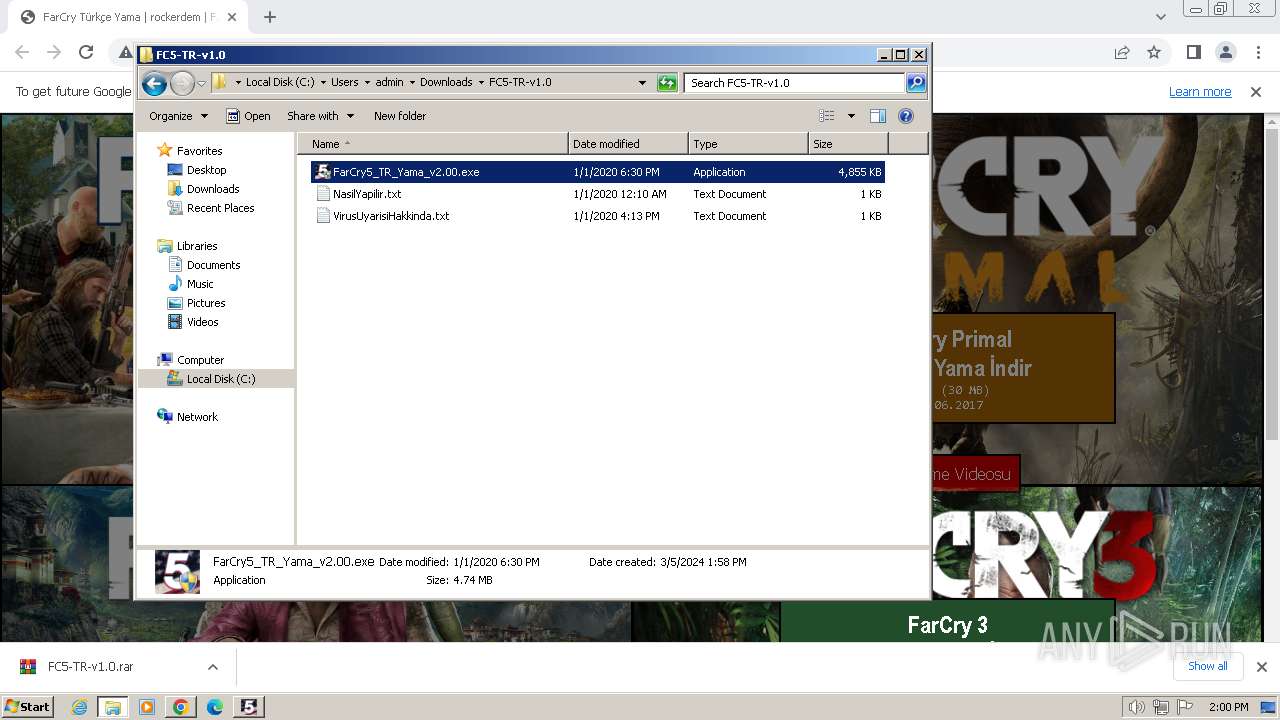
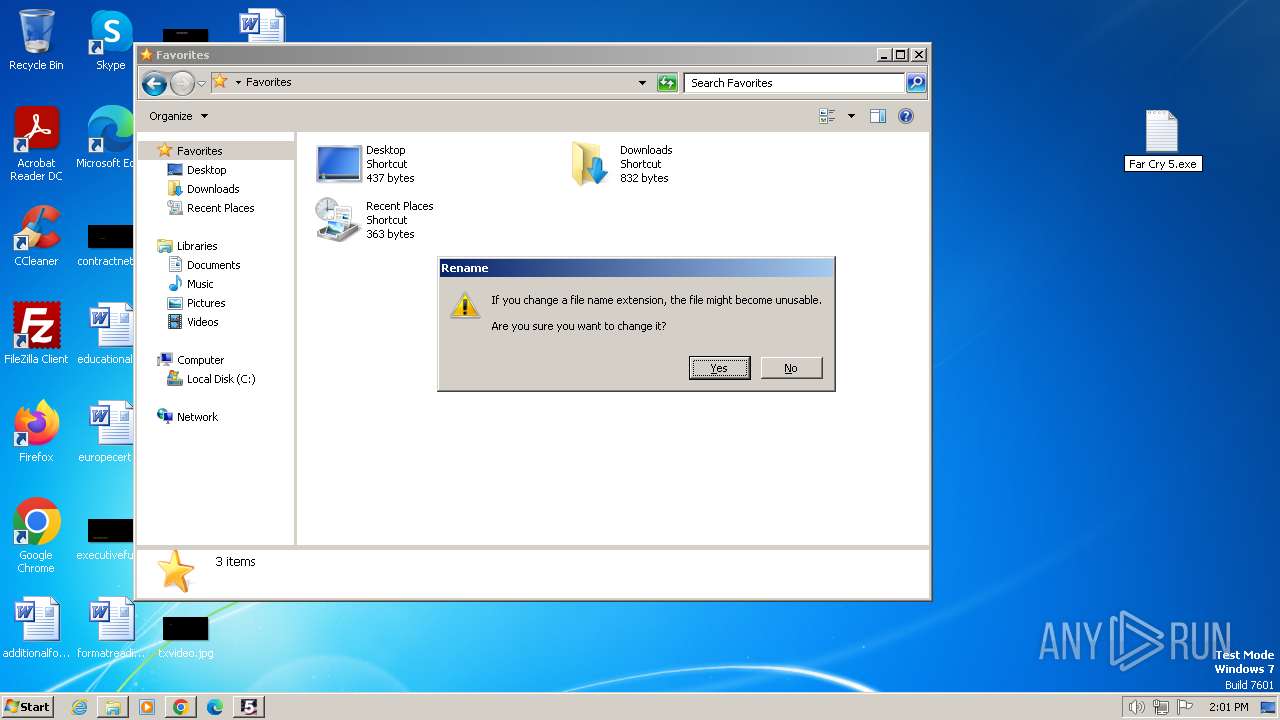
Drops the executable file immediately after the start
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
SUSPICIOUS
Executable content was dropped or overwritten
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
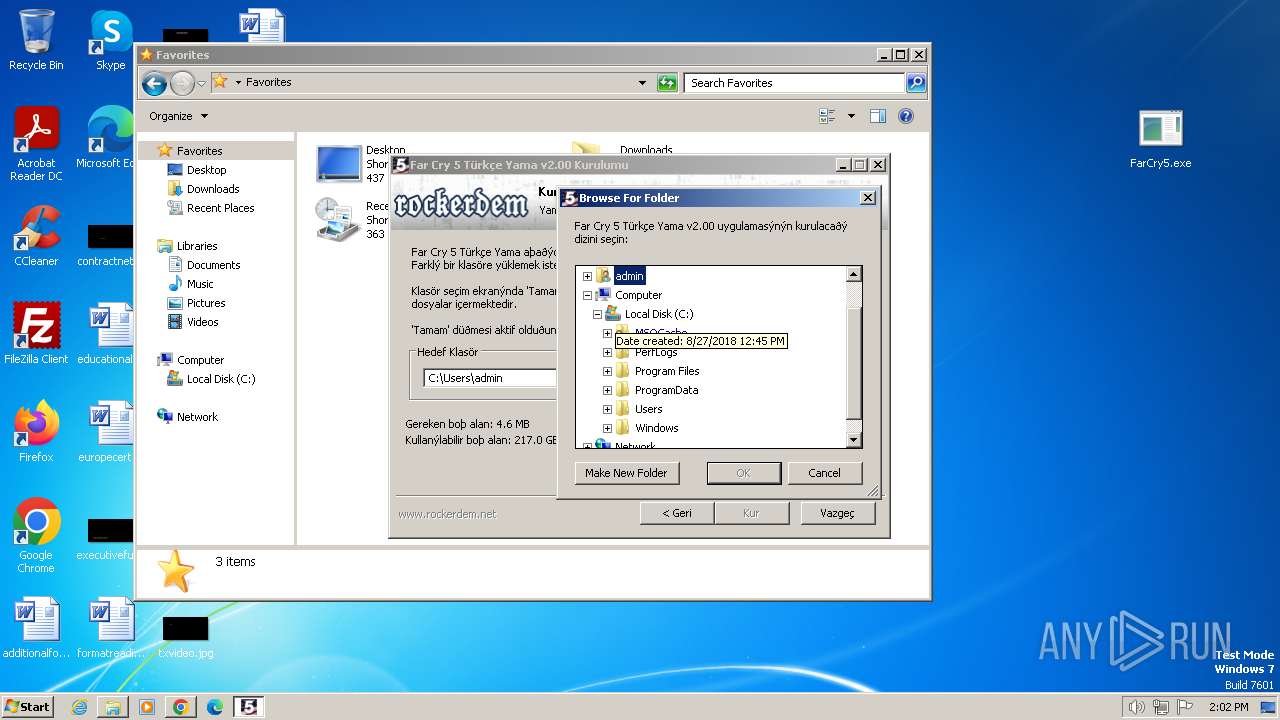
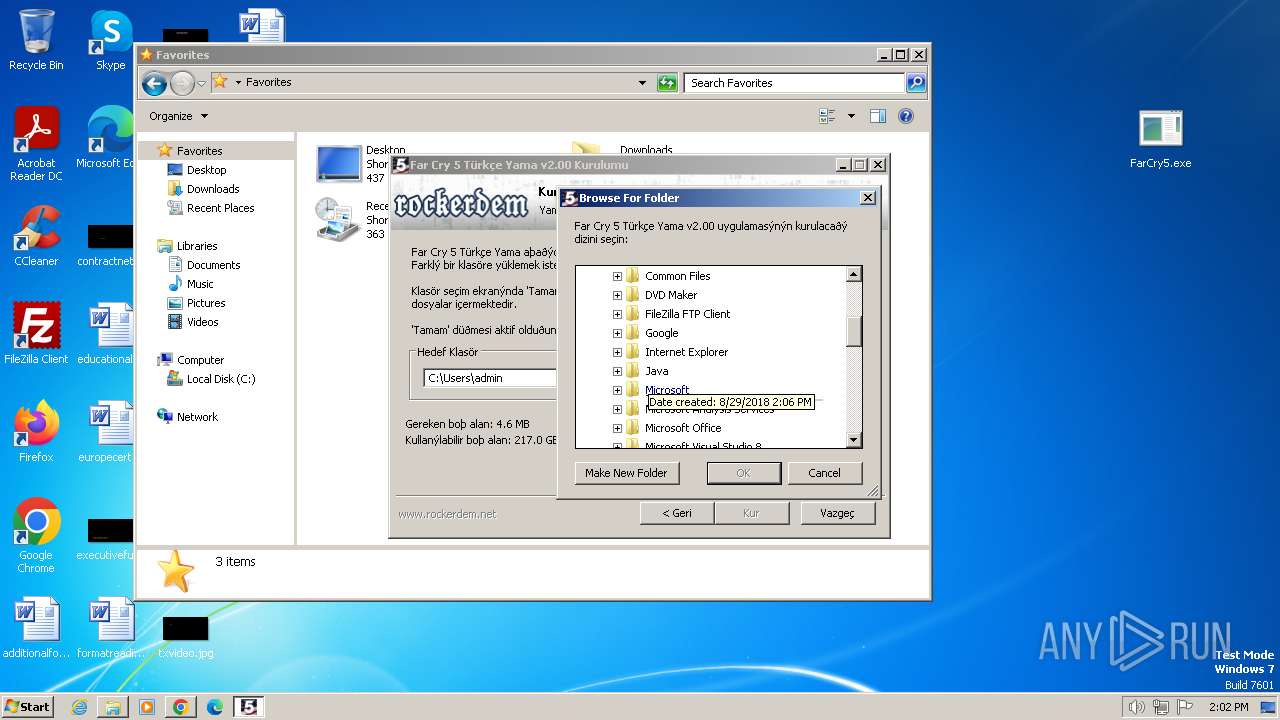
Reads the Internet Settings
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
Reads security settings of Internet Explorer
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
Reads Microsoft Outlook installation path
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
Reads Internet Explorer settings
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
Malware-specific behavior (creating "System.dll" in Temp)
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
The process creates files with name similar to system file names
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
INFO
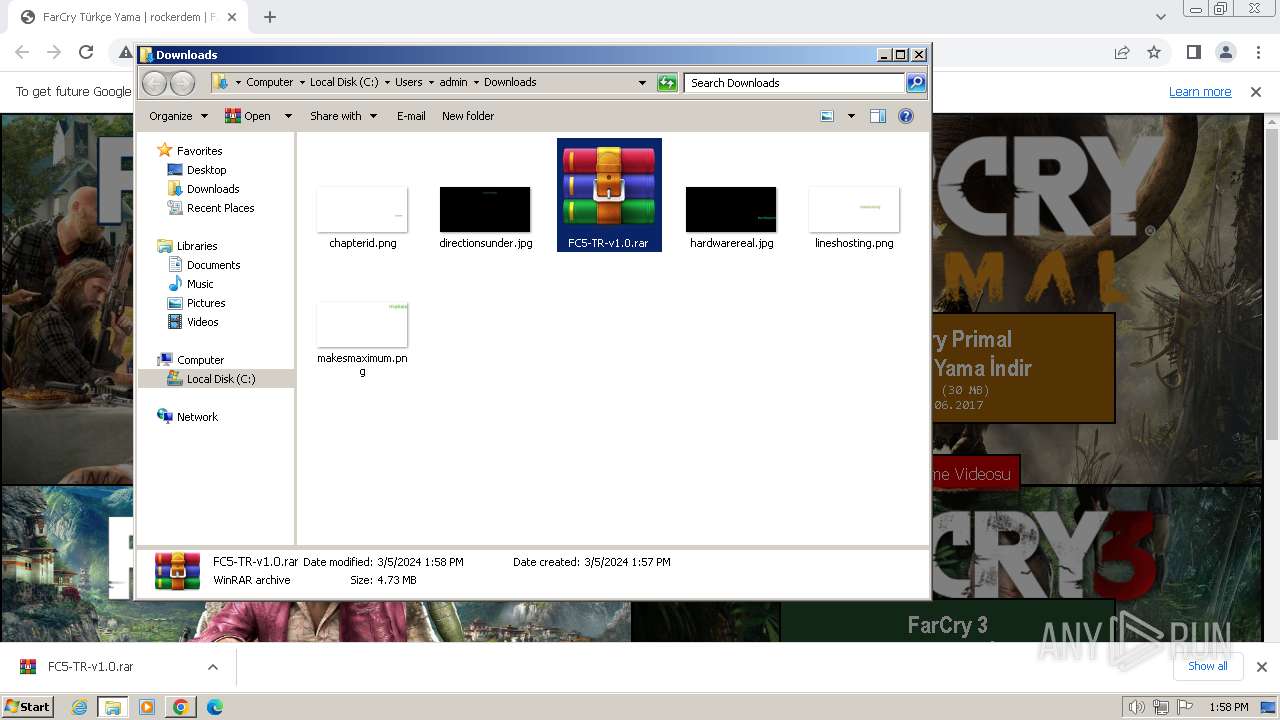
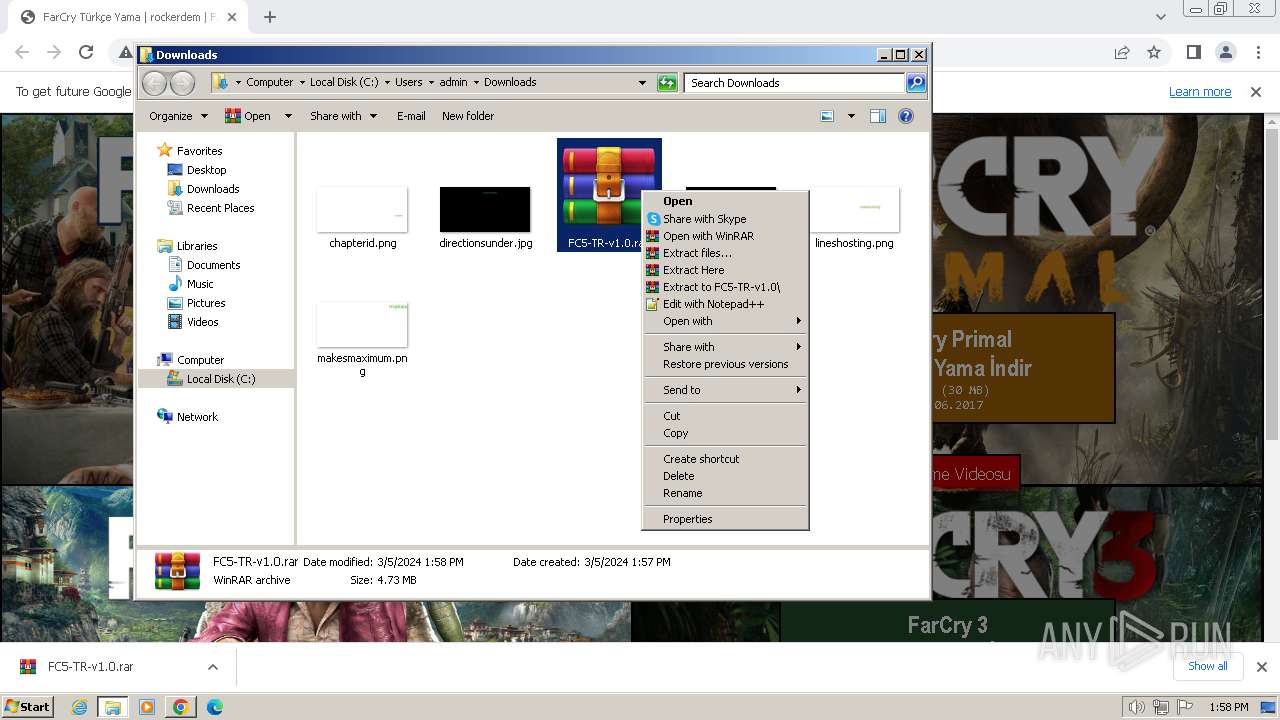
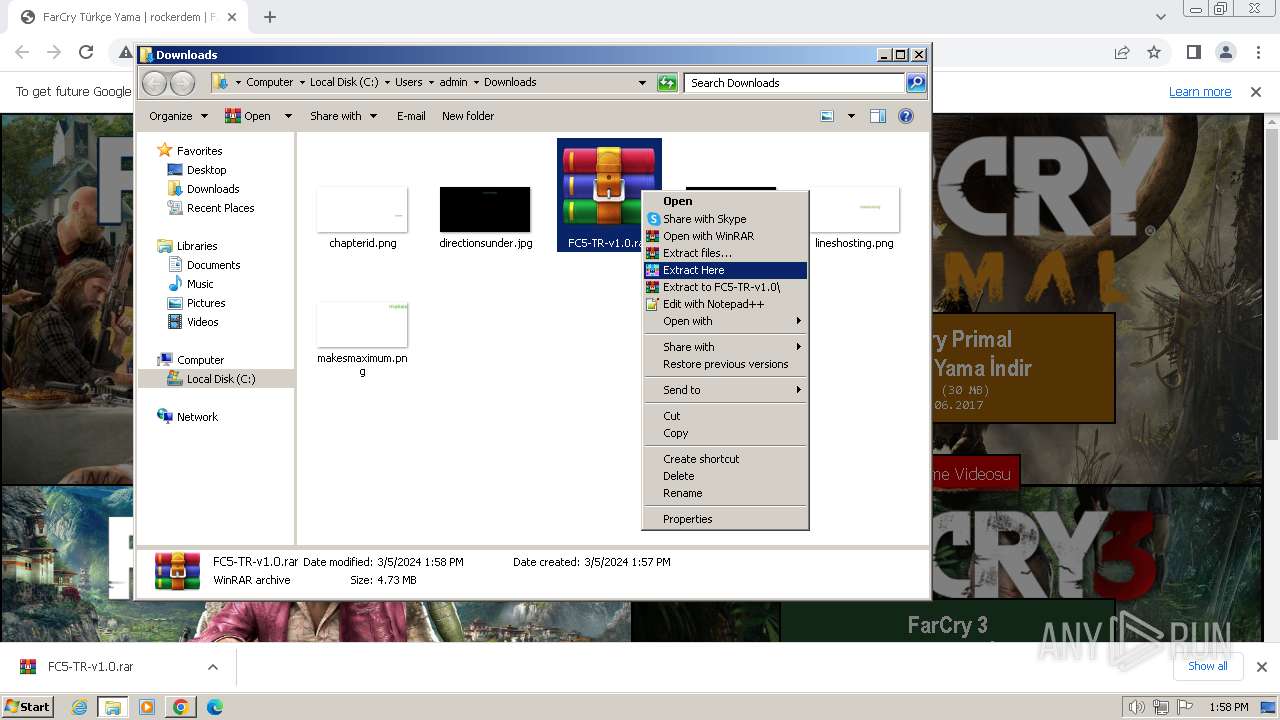
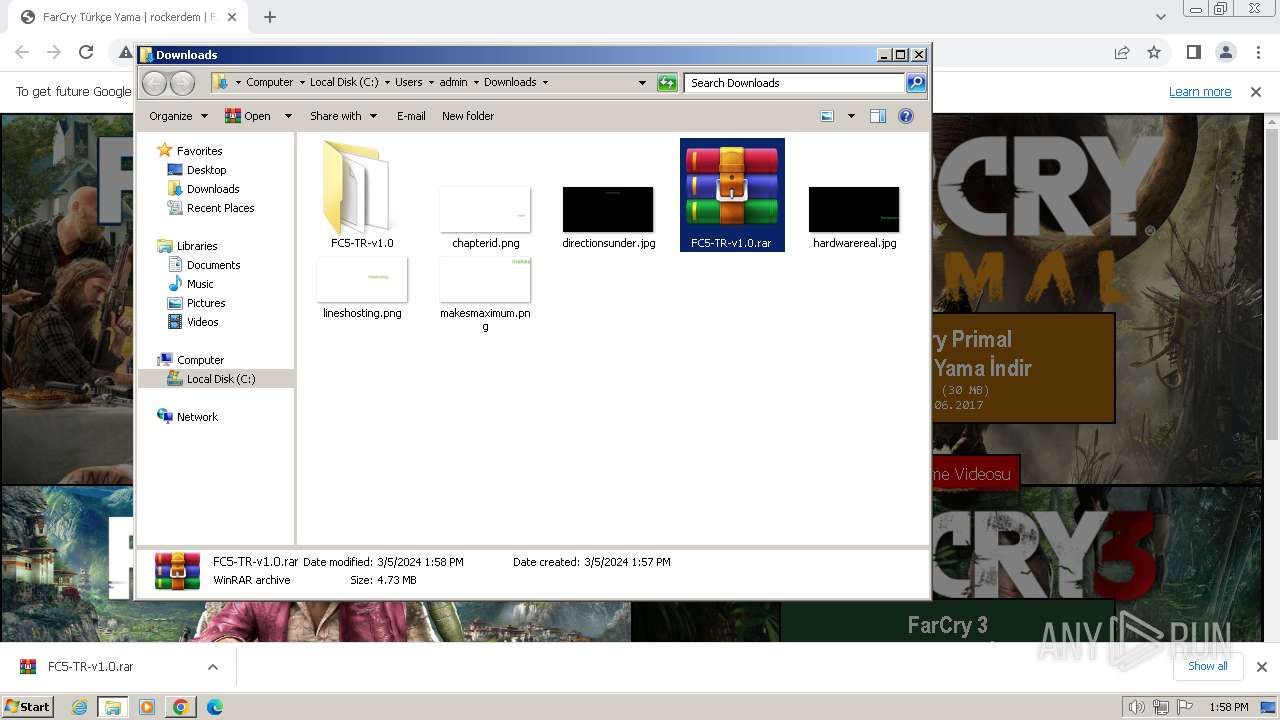
The process uses the downloaded file
- chrome.exe (PID: 2336)
- WinRAR.exe (PID: 764)
Reads the computer name
- wmpnscfg.exe (PID: 2472)
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 764)
Reads the machine GUID from the registry
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
Checks proxy server information
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
Checks supported languages
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
- wmpnscfg.exe (PID: 2472)
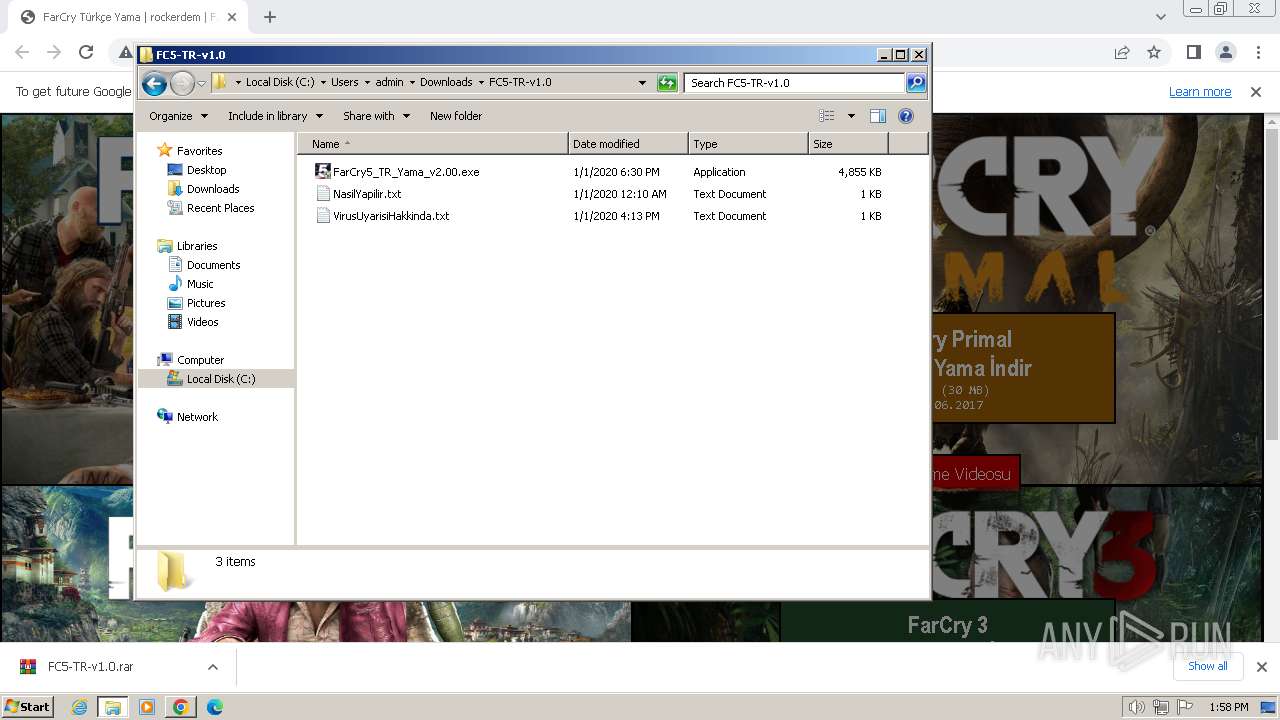
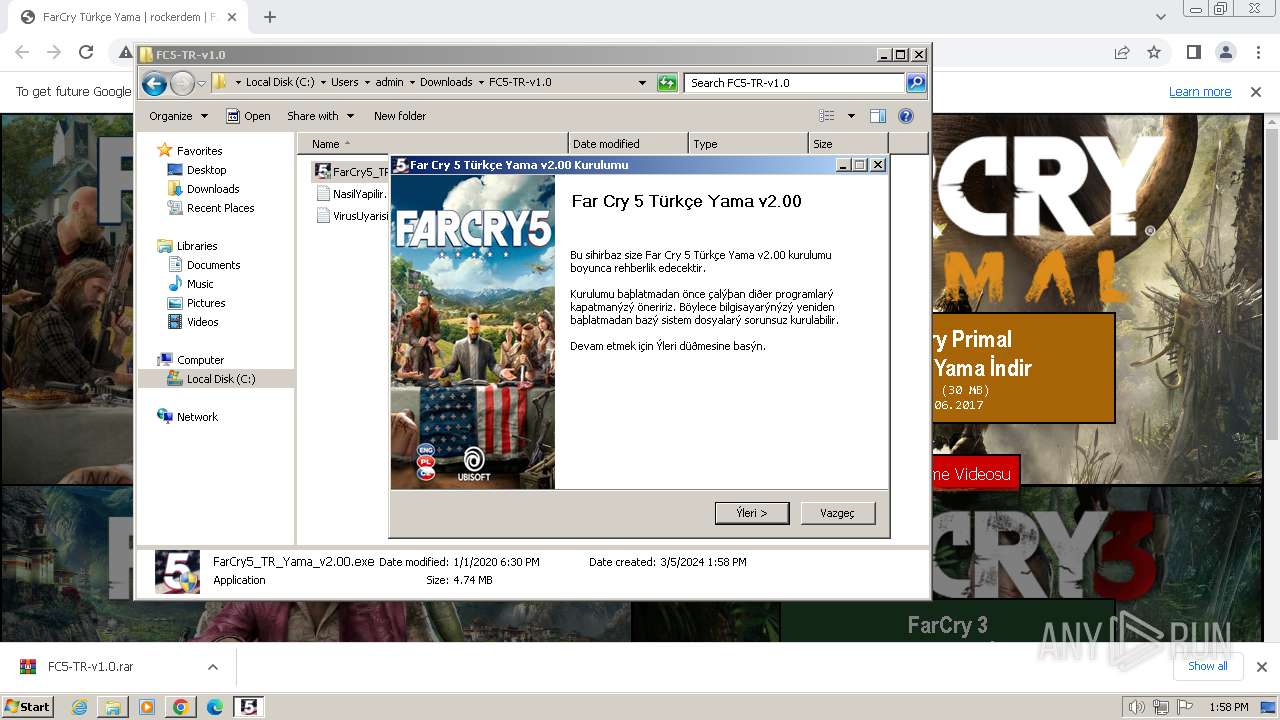
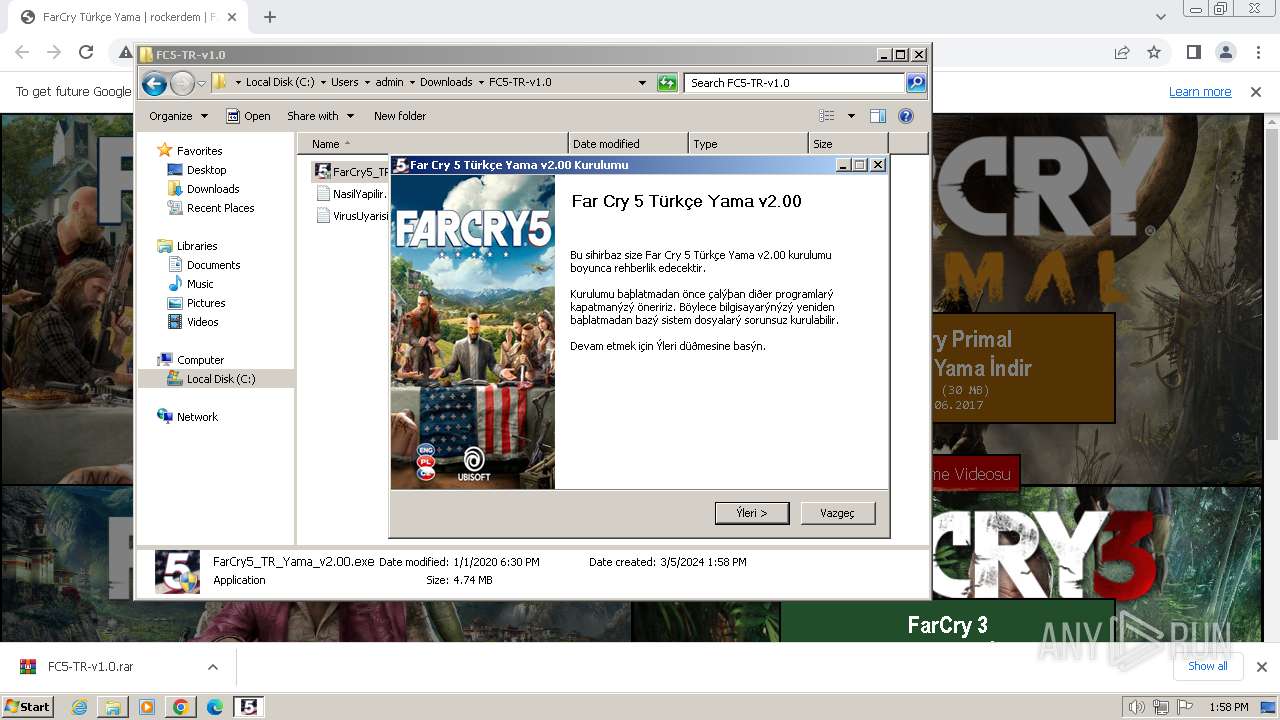
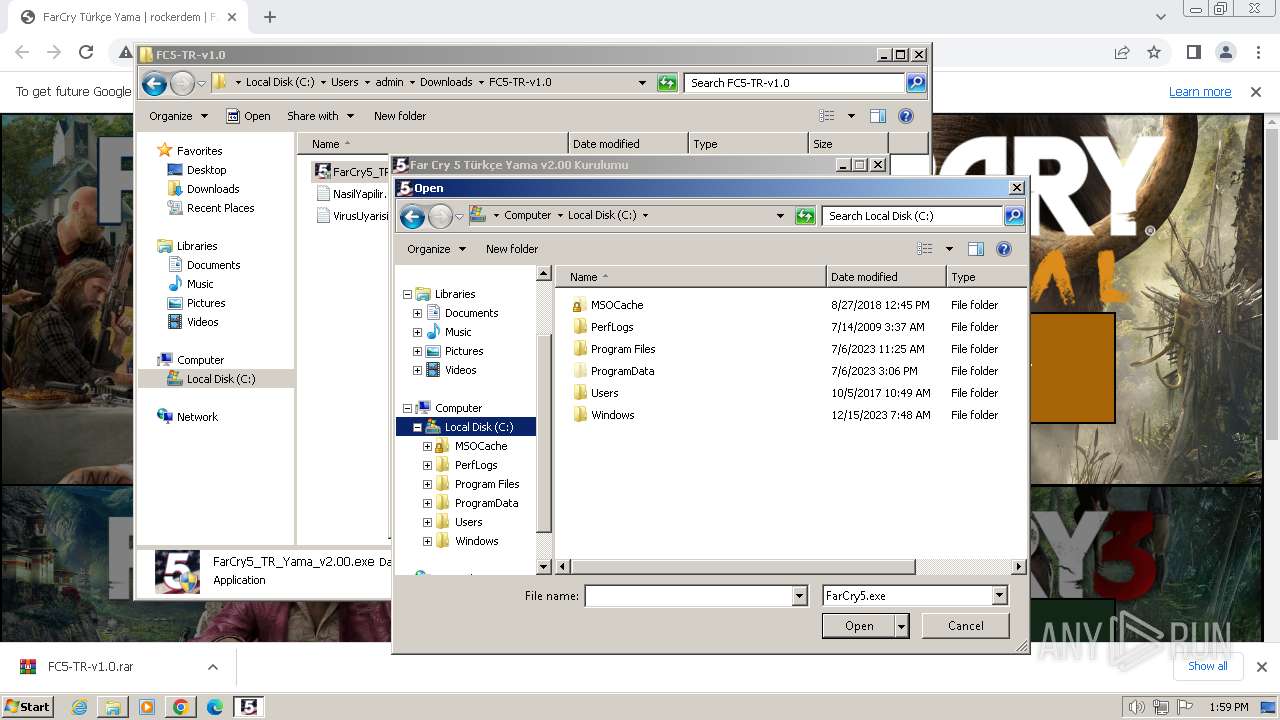
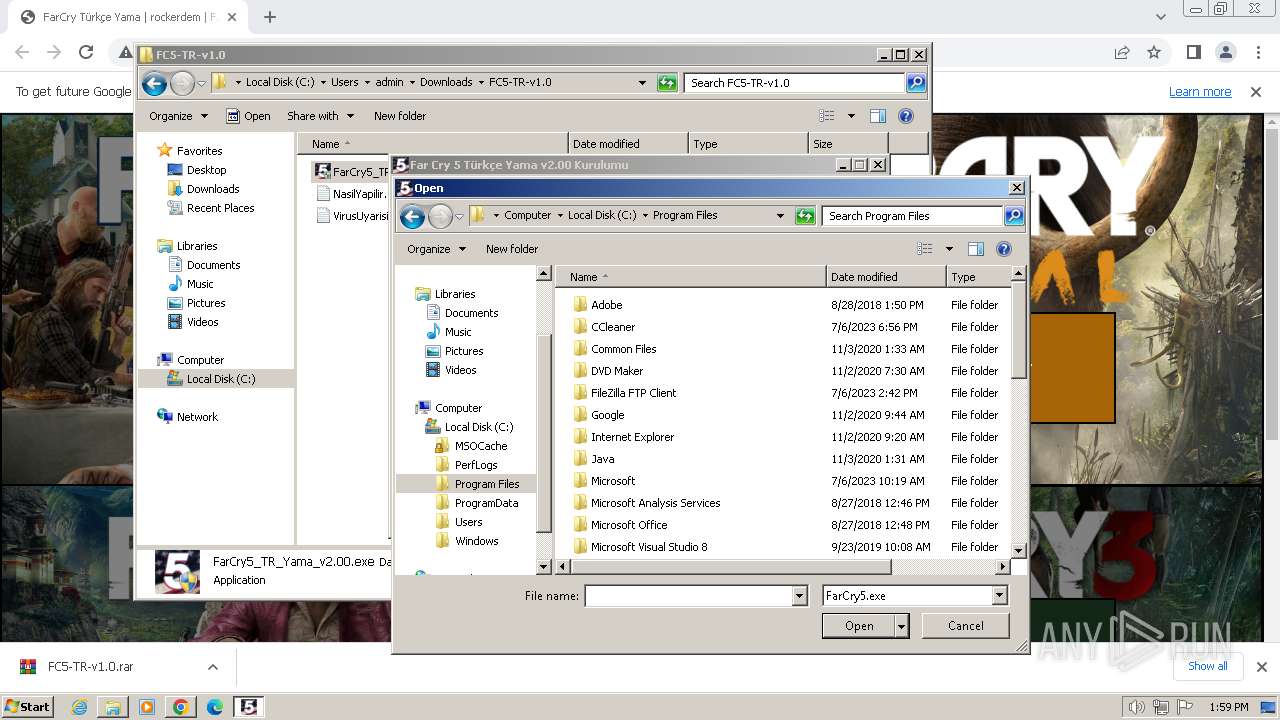
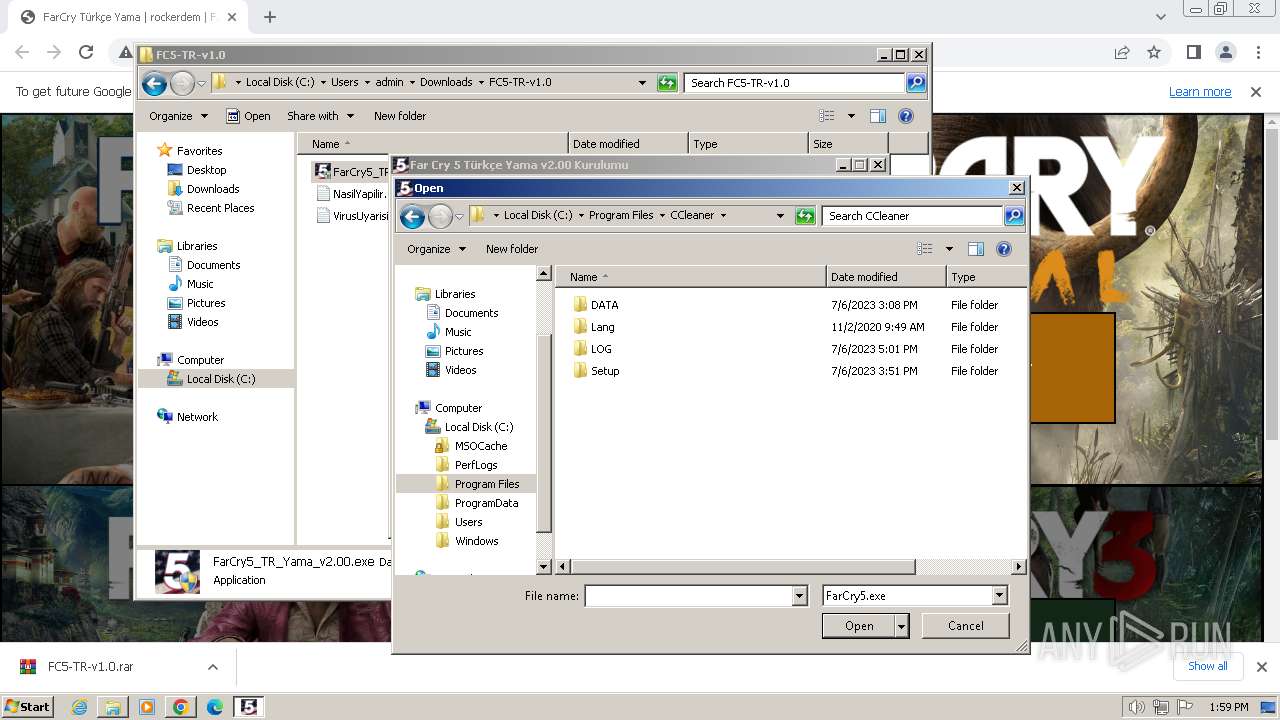
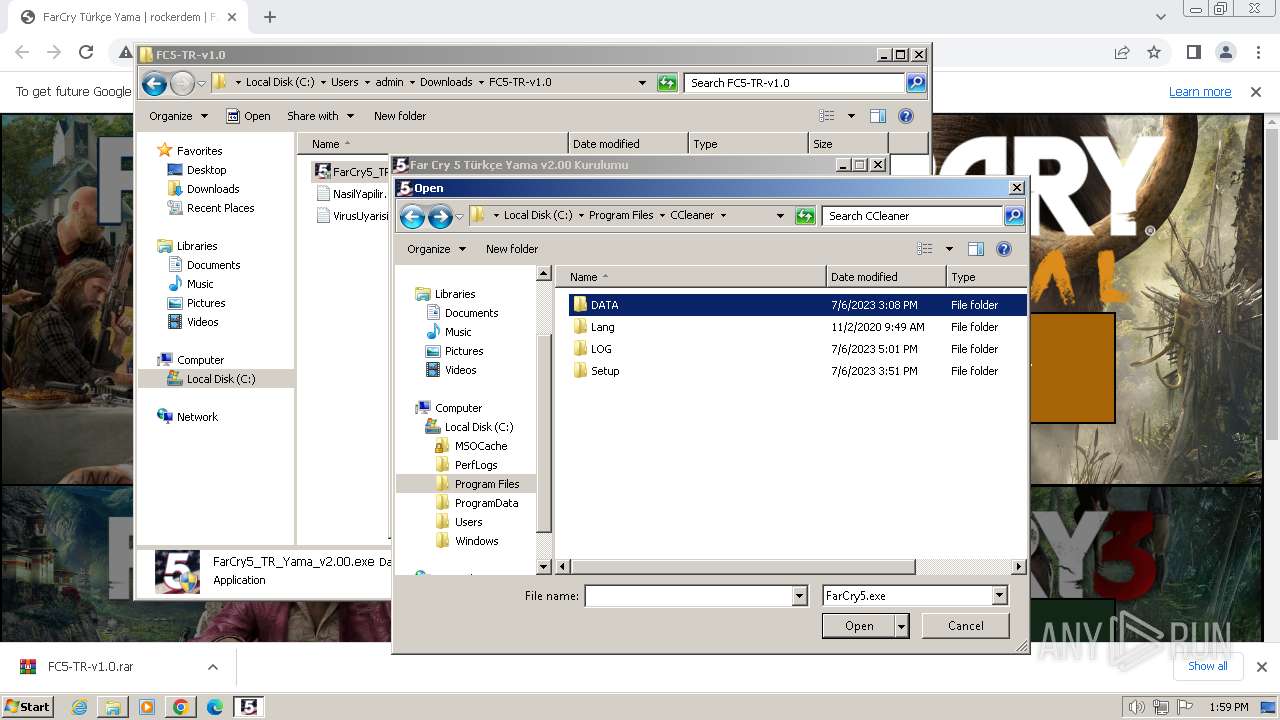
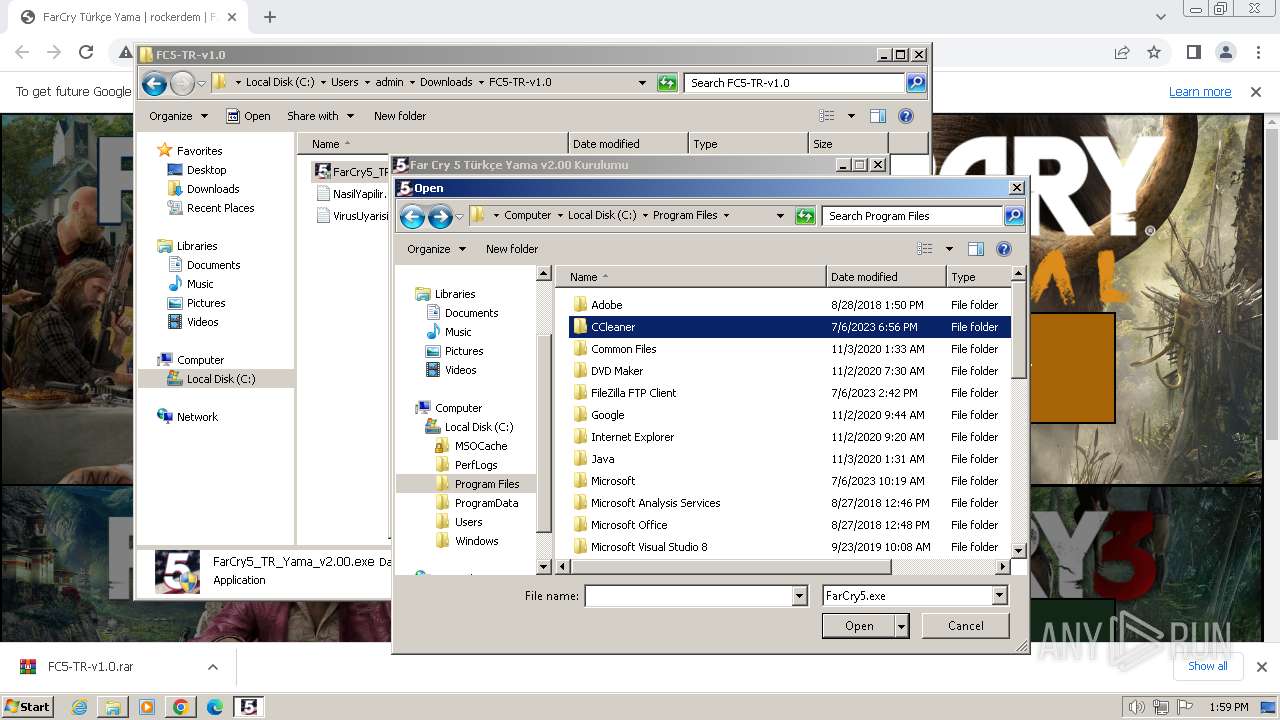
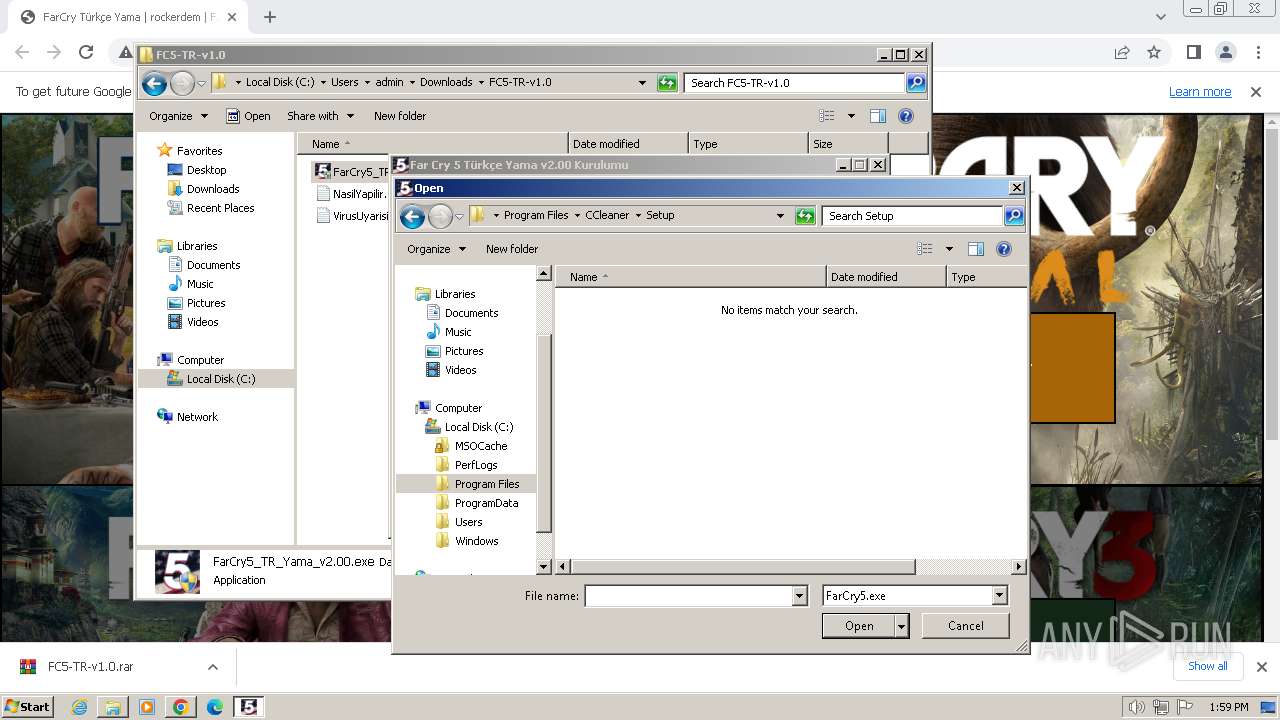
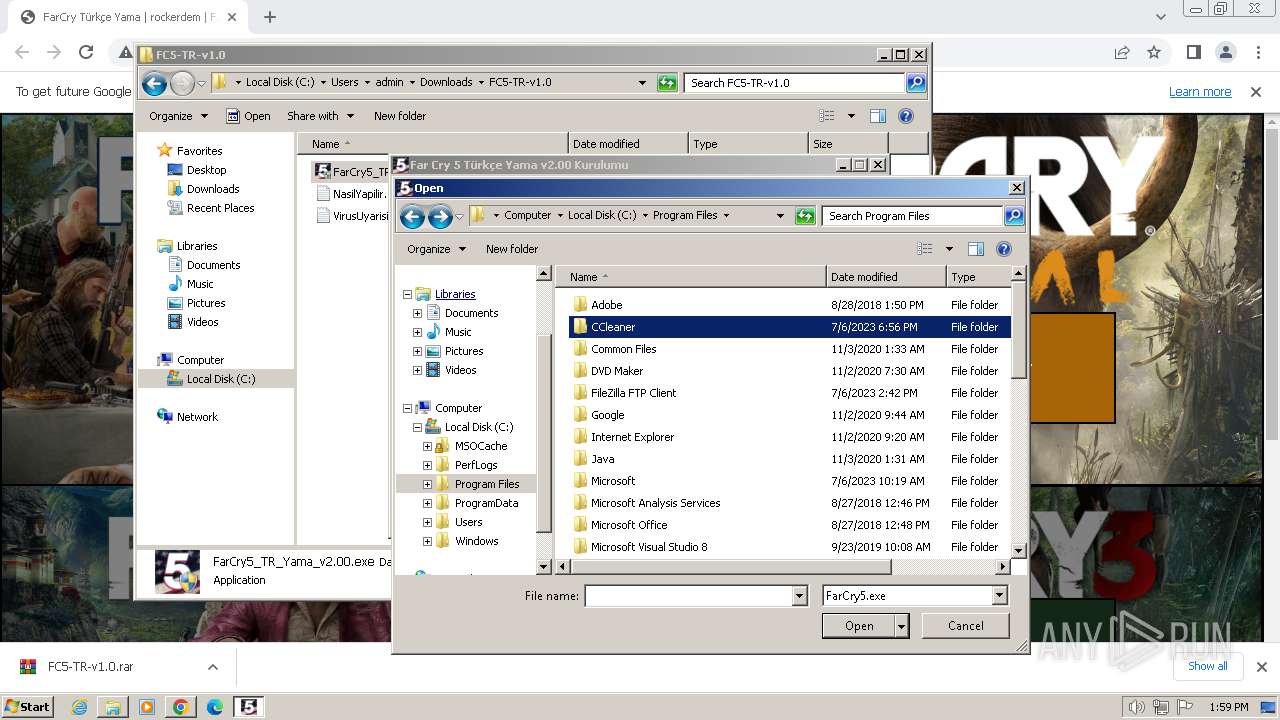
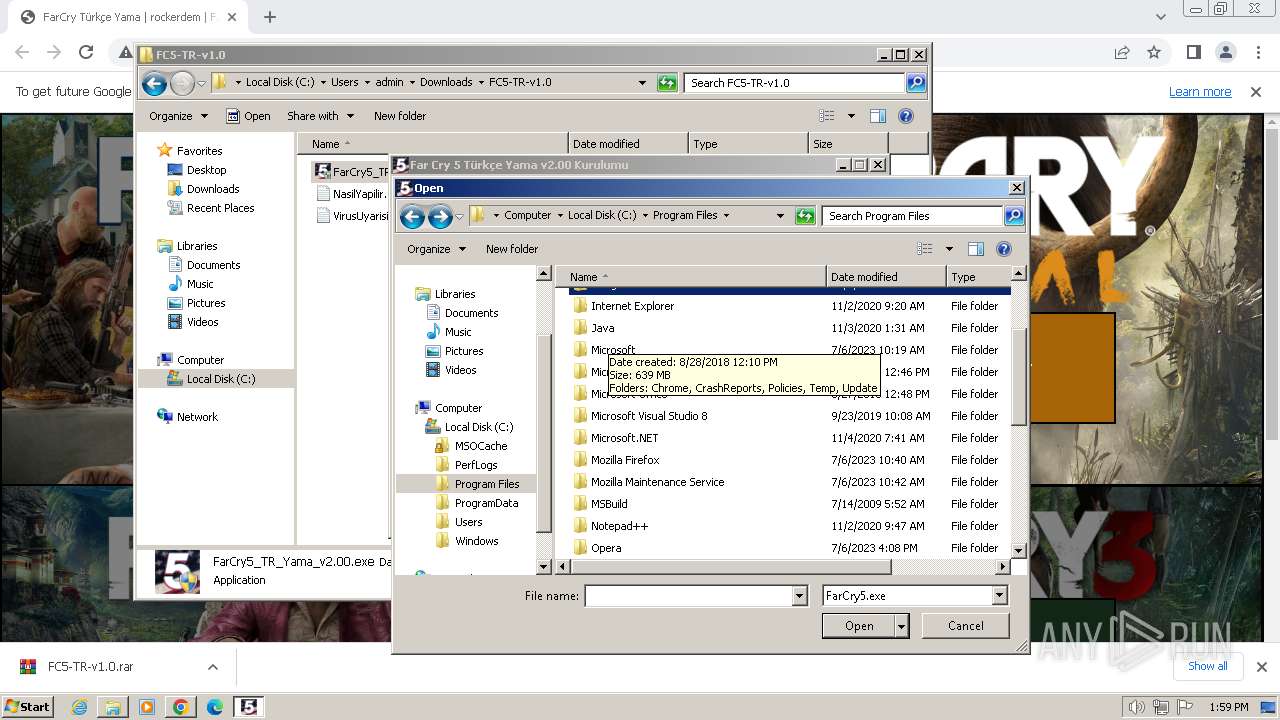
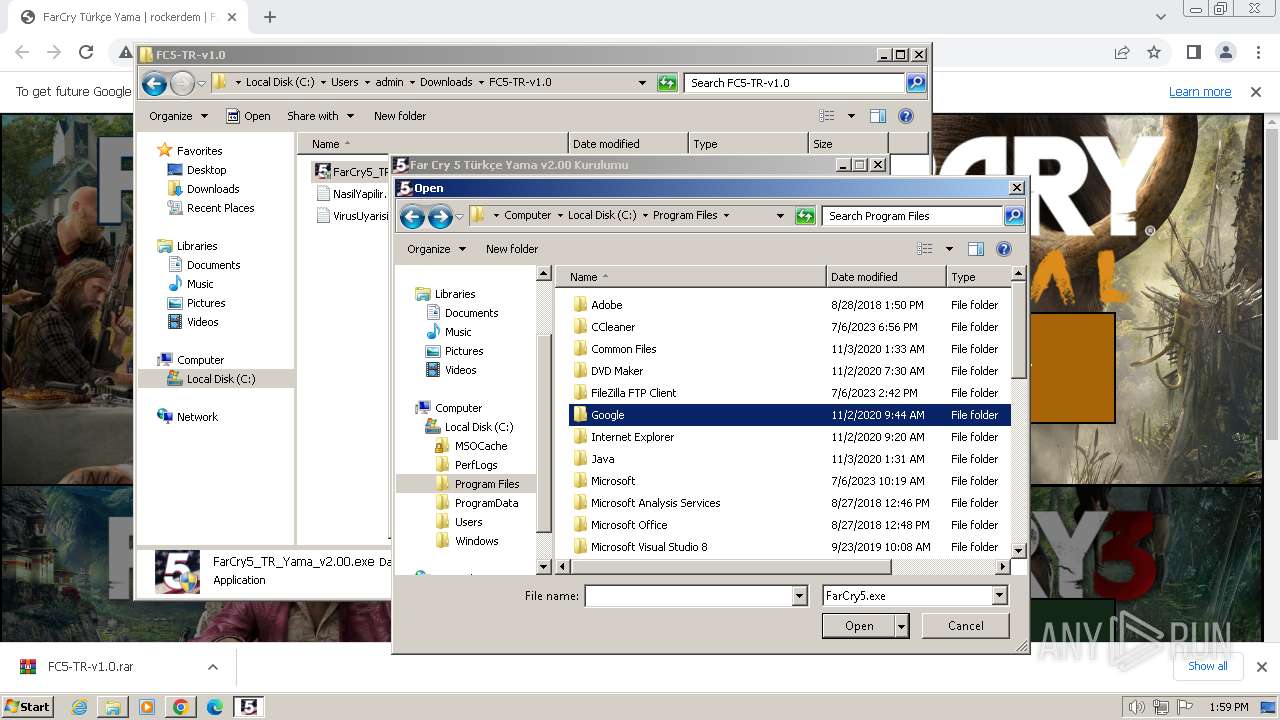
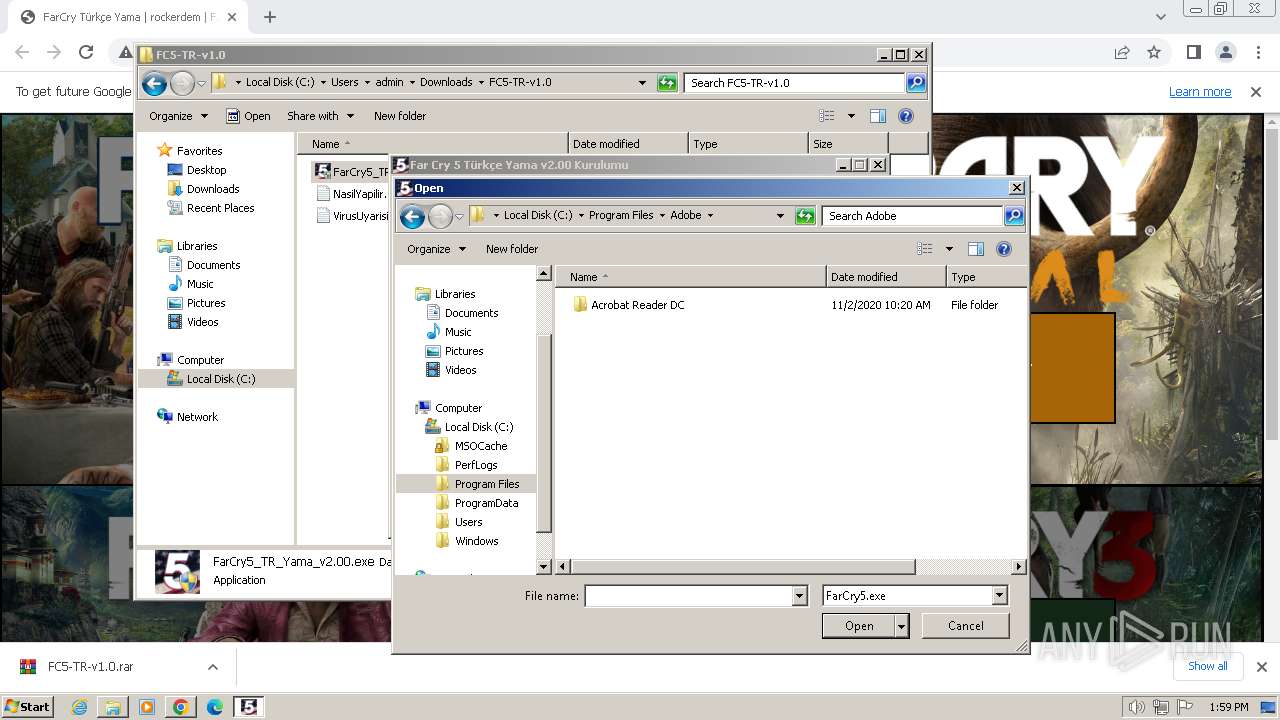
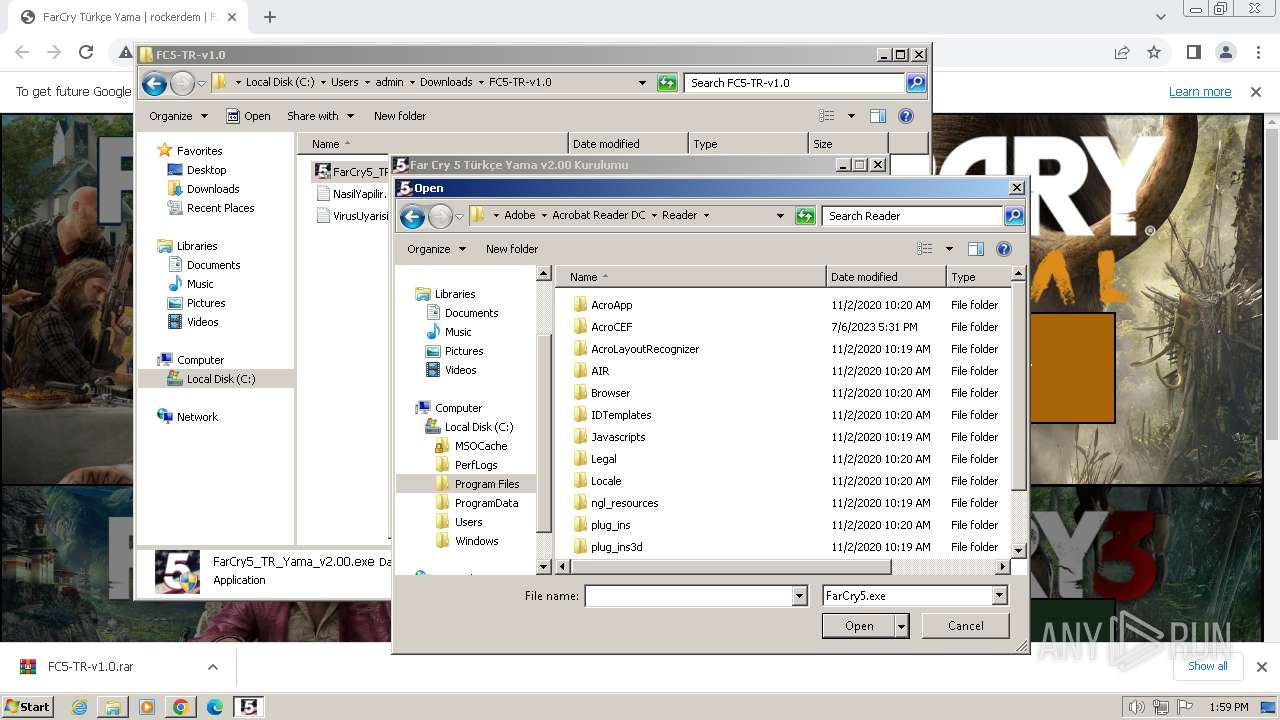
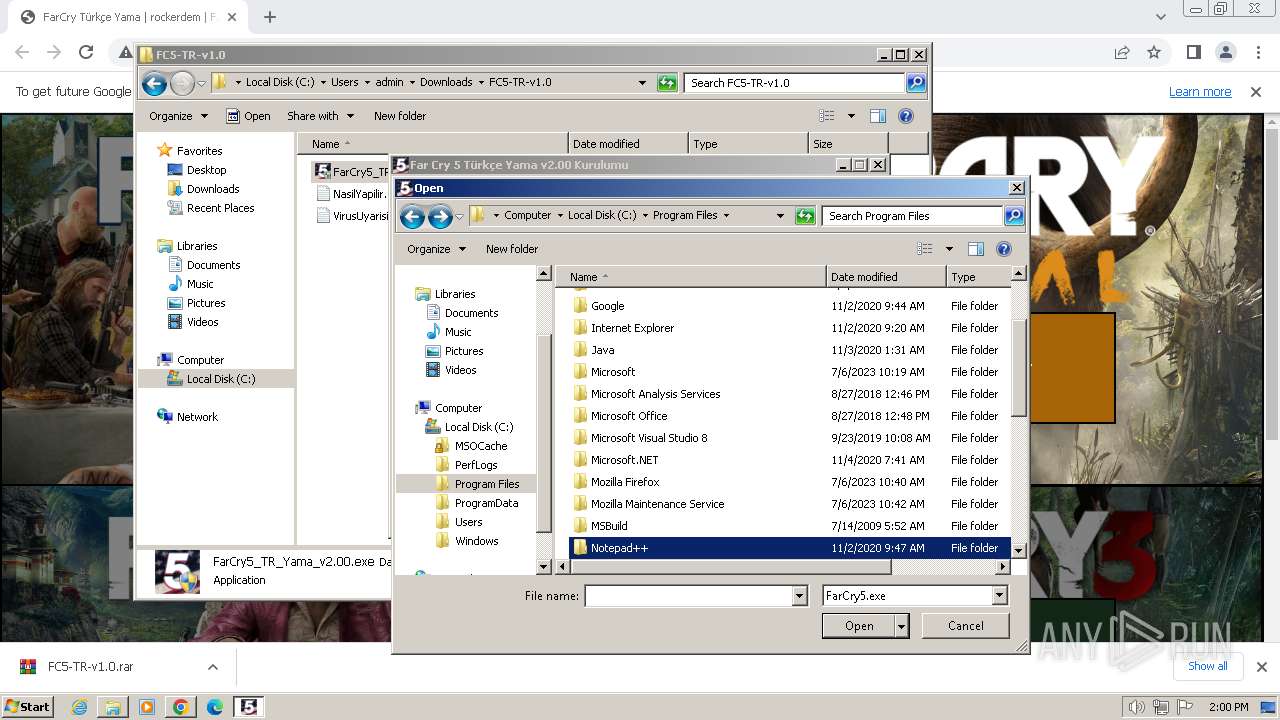
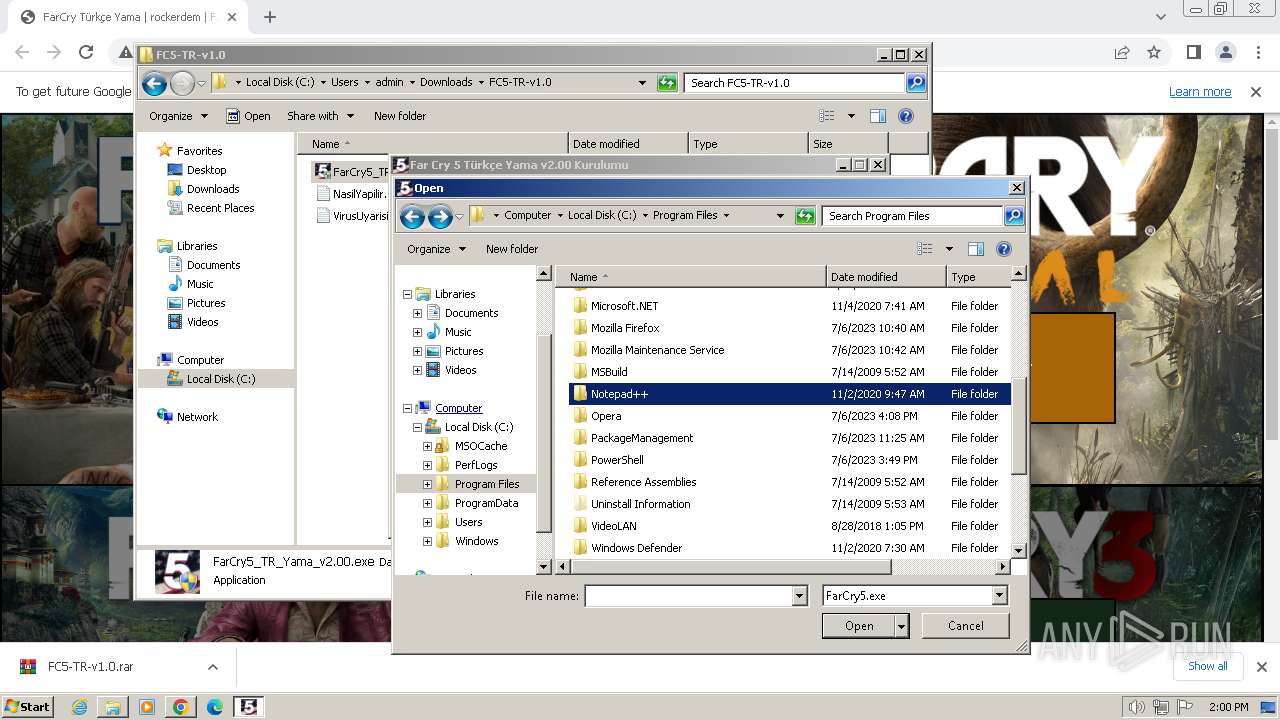
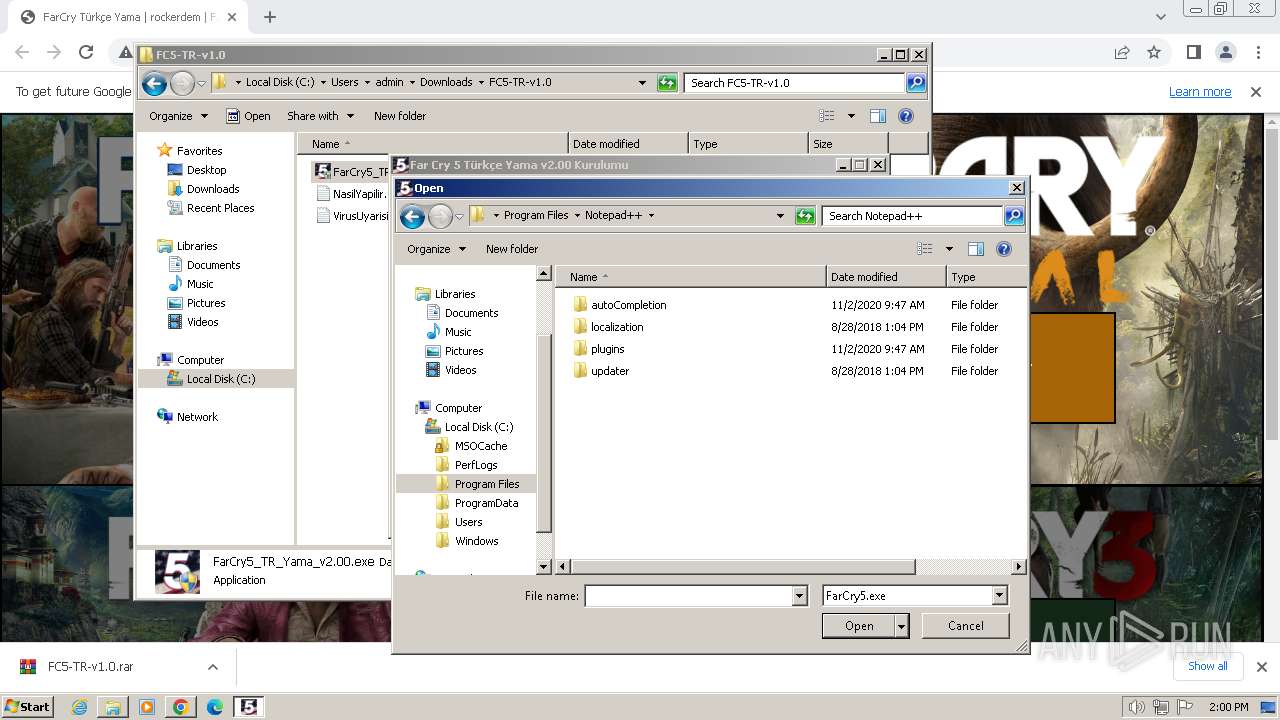
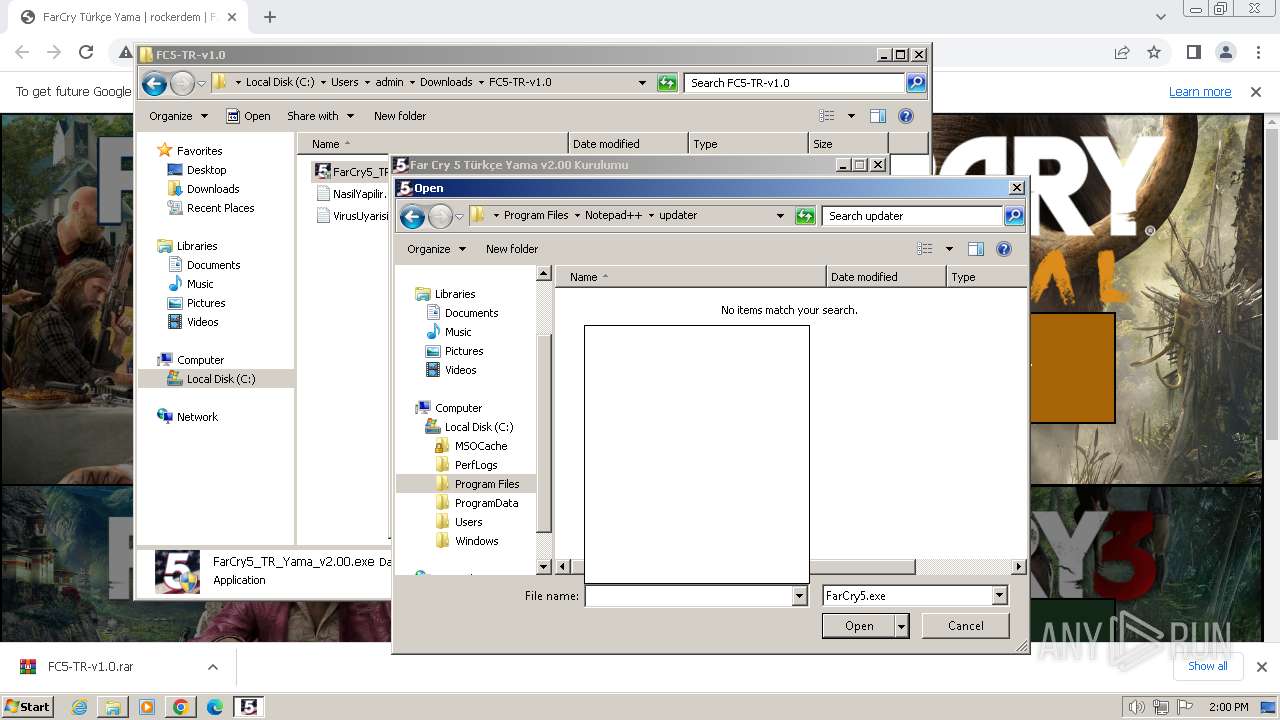
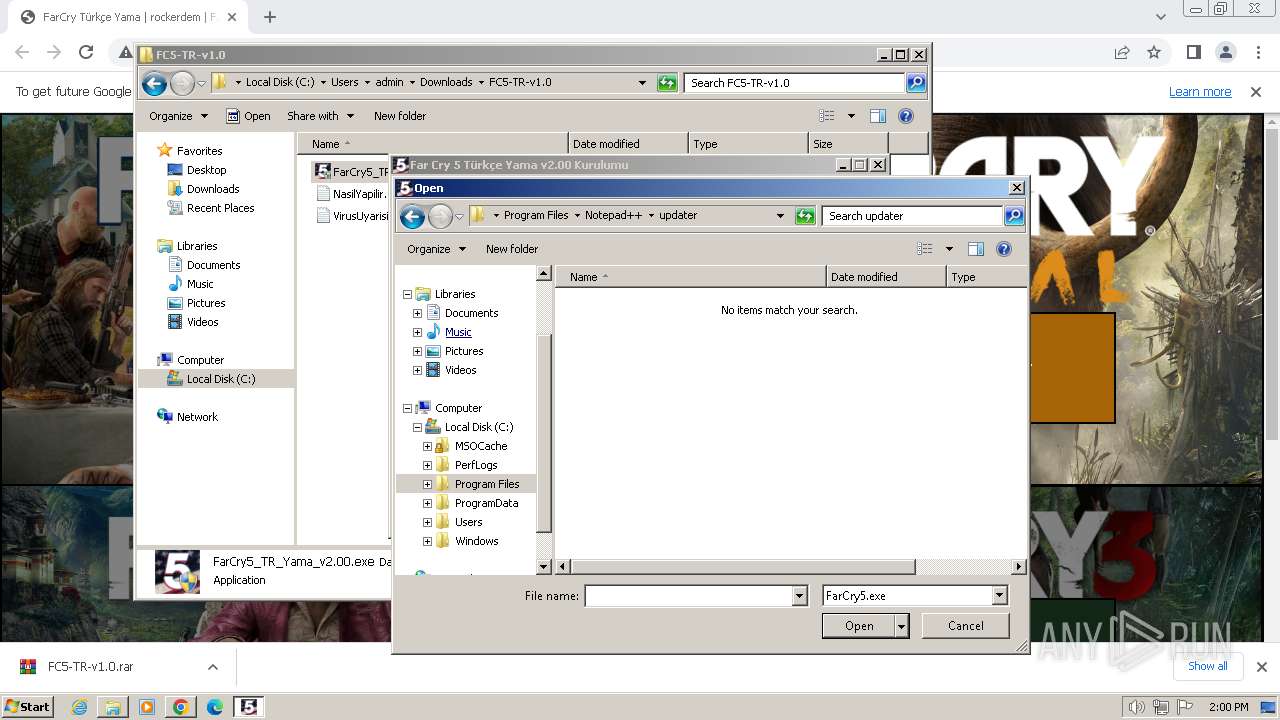
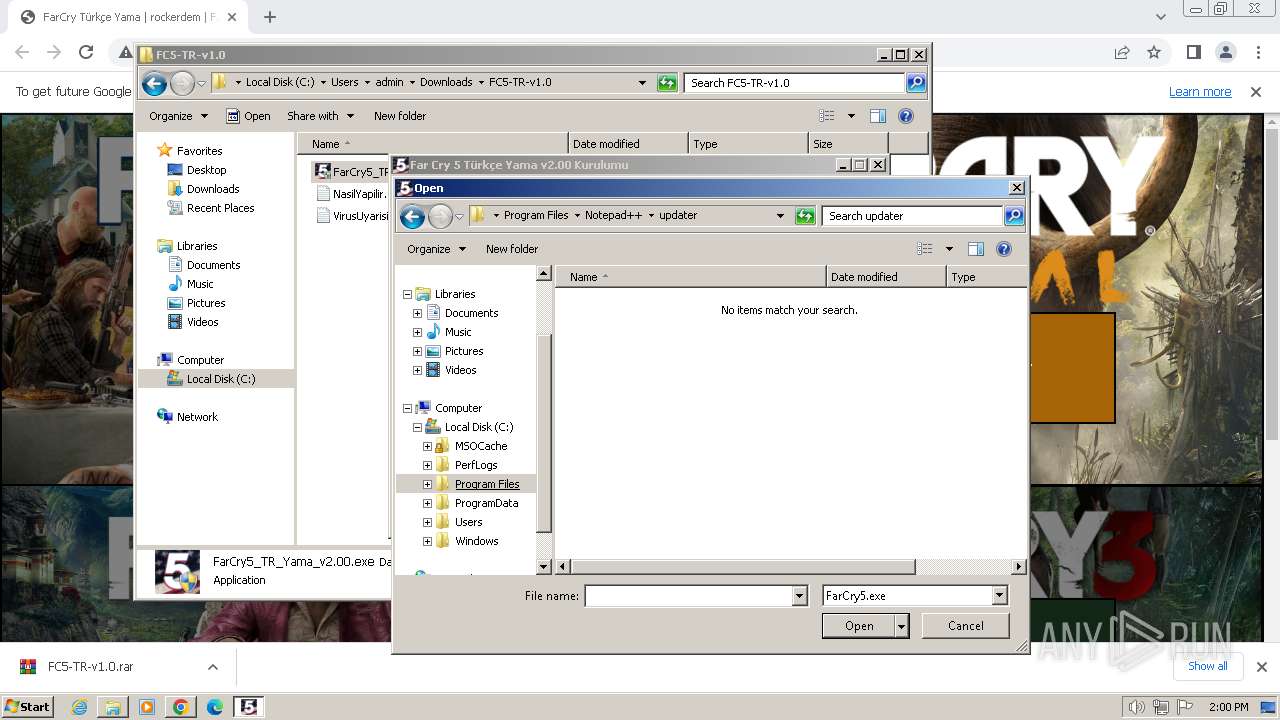
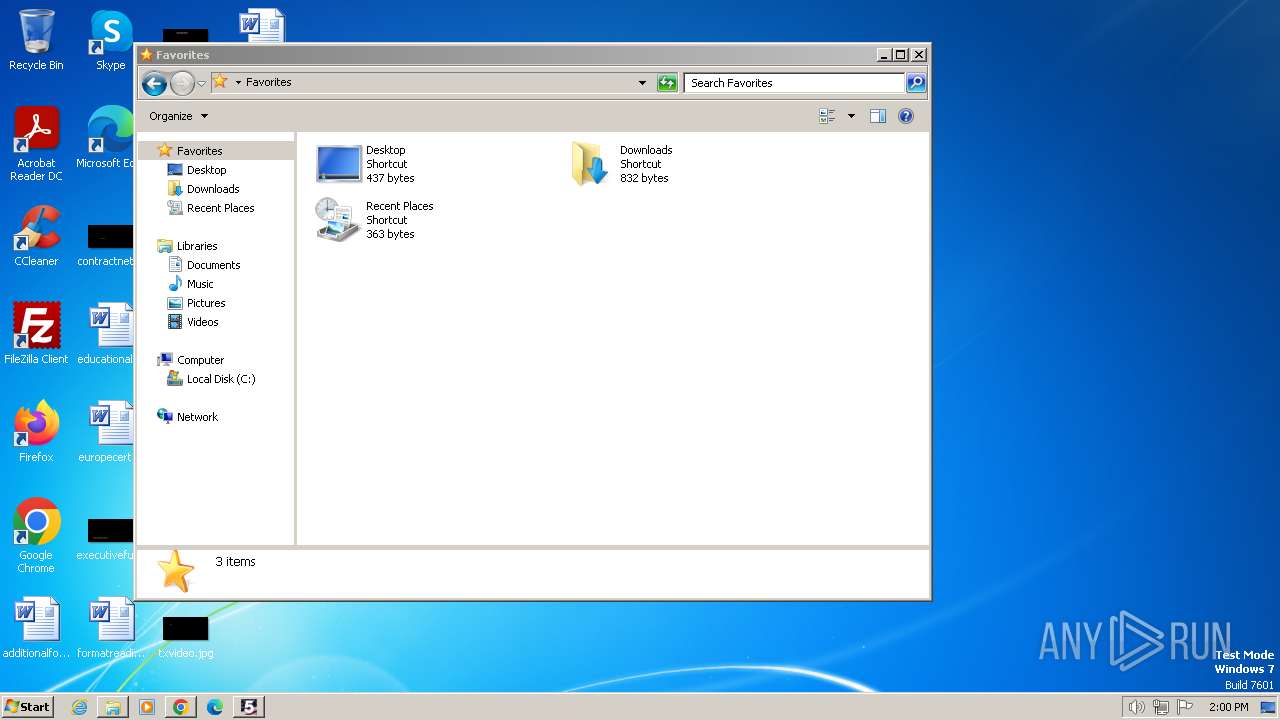
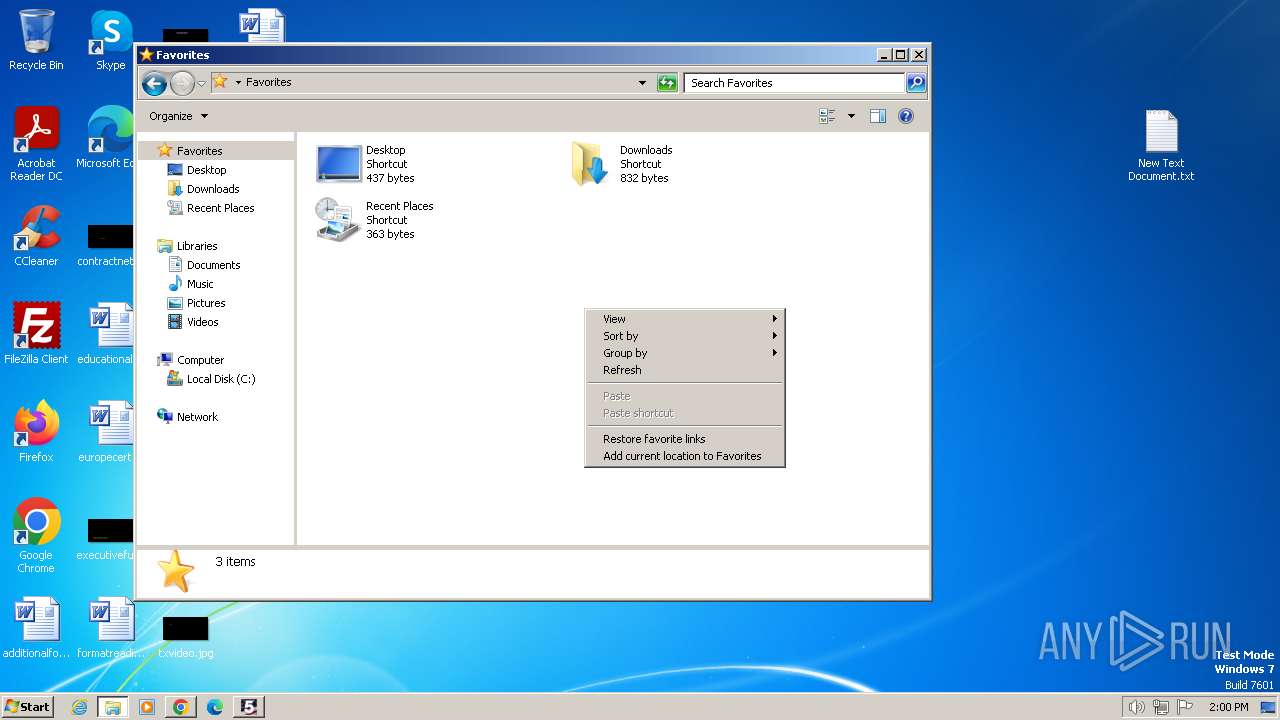
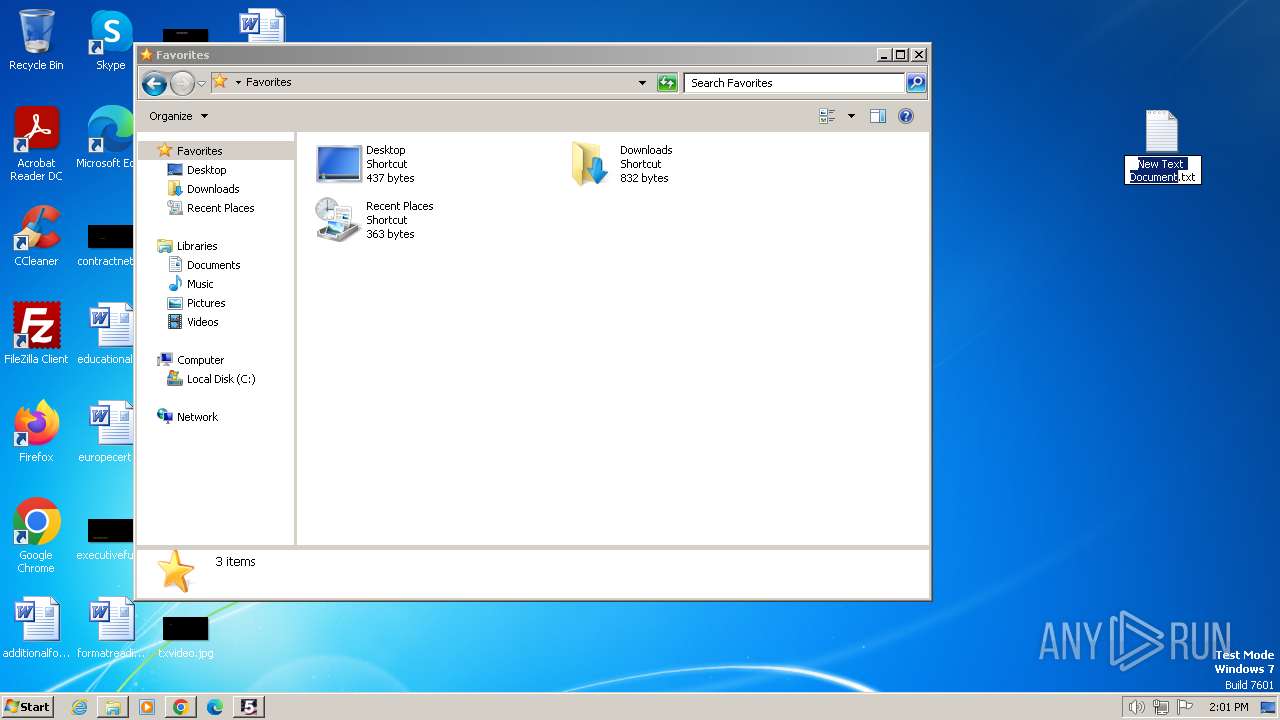
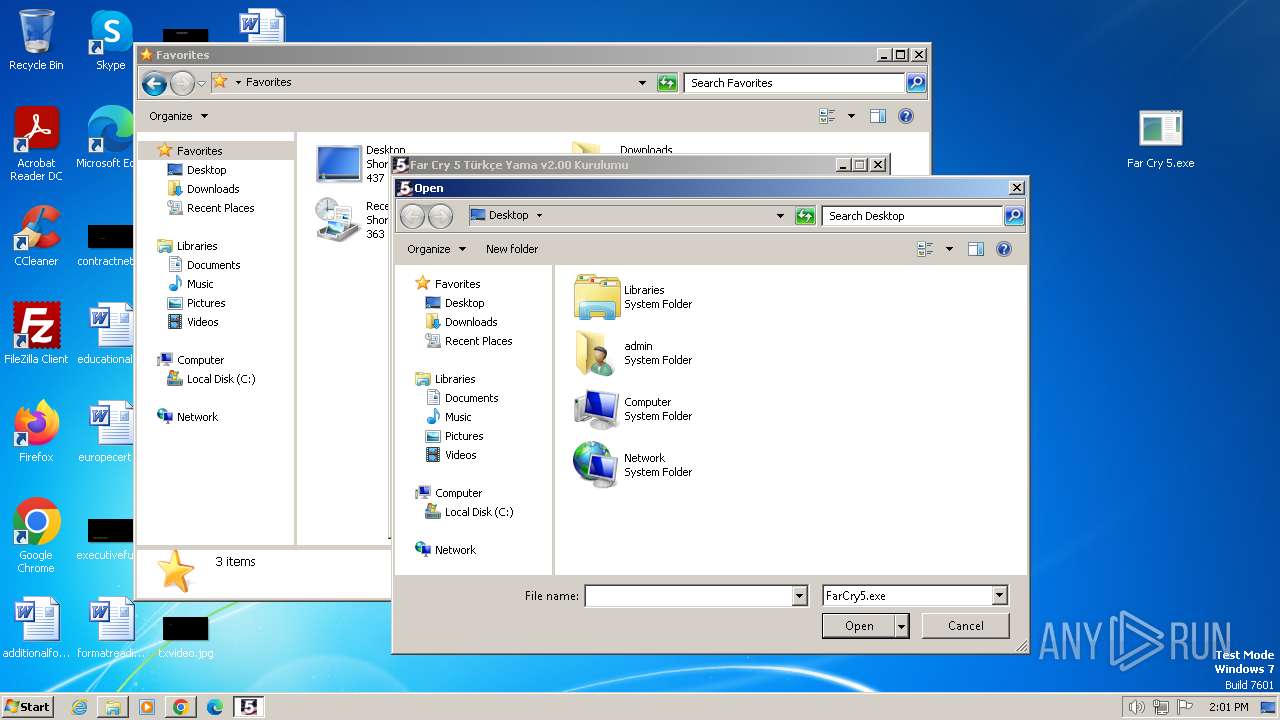
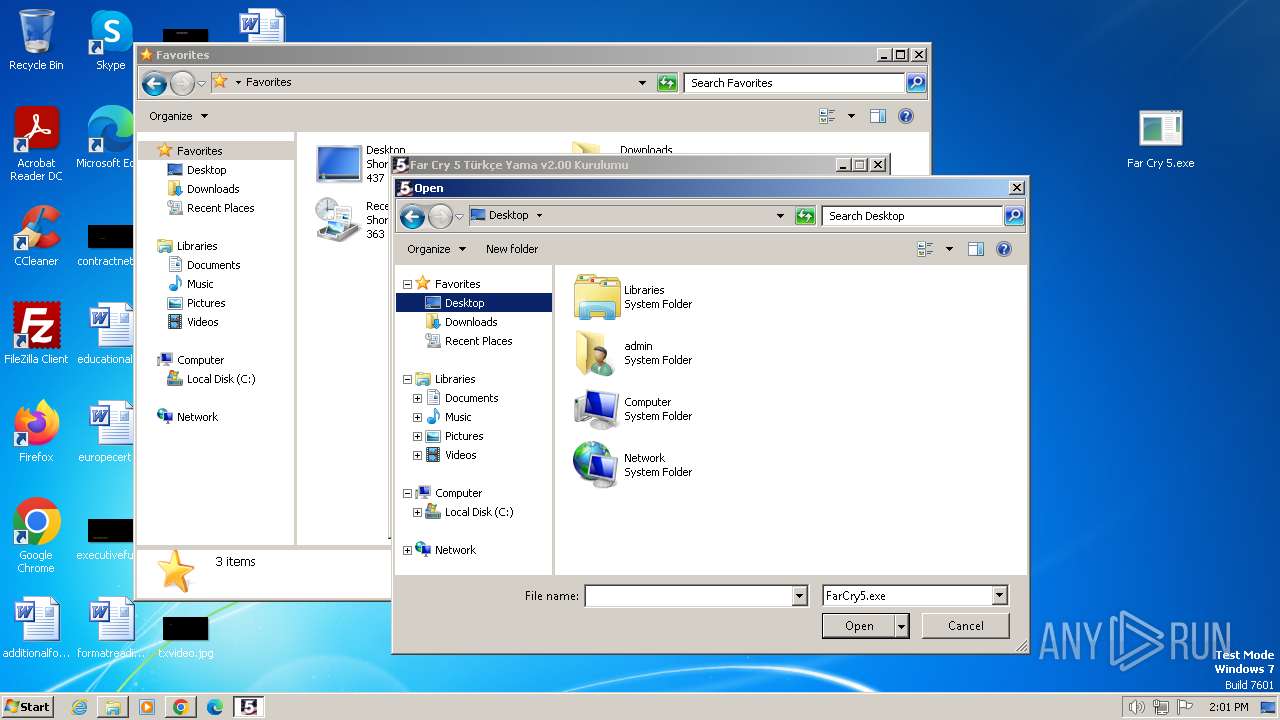
Manual execution by a user
- FarCry5_TR_Yama_v2.00.exe (PID: 2748)
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
- WinRAR.exe (PID: 764)
Create files in a temporary directory
- FarCry5_TR_Yama_v2.00.exe (PID: 3900)
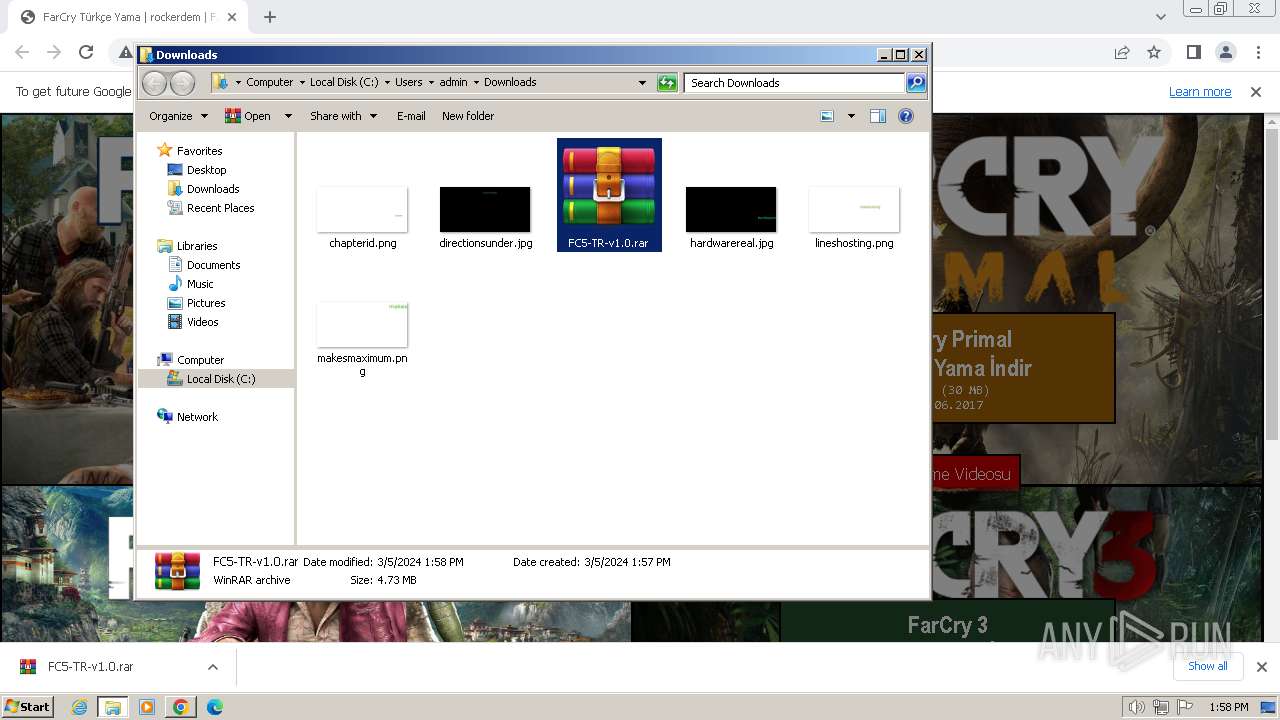
Executable content was dropped or overwritten
- WinRAR.exe (PID: 764)
Application launched itself
- chrome.exe (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
19
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3476 --field-trial-handle=1172,i,5804333041968641534,8941490774512339025,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
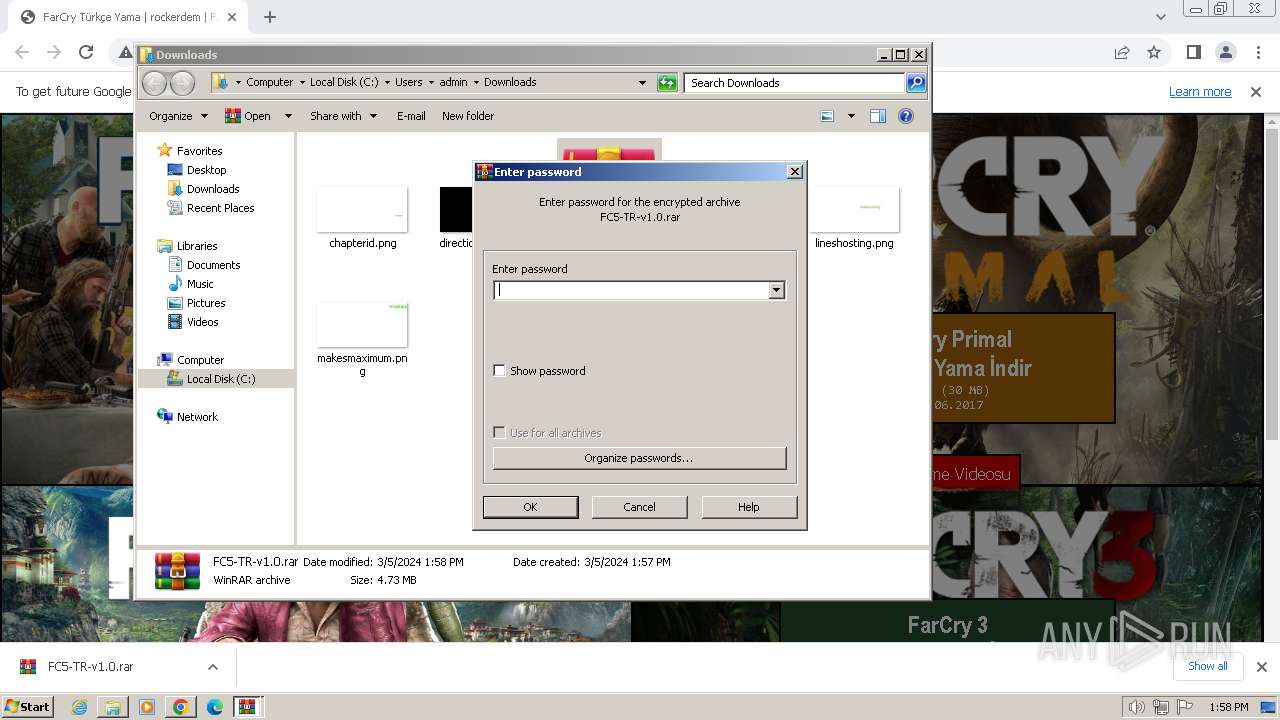
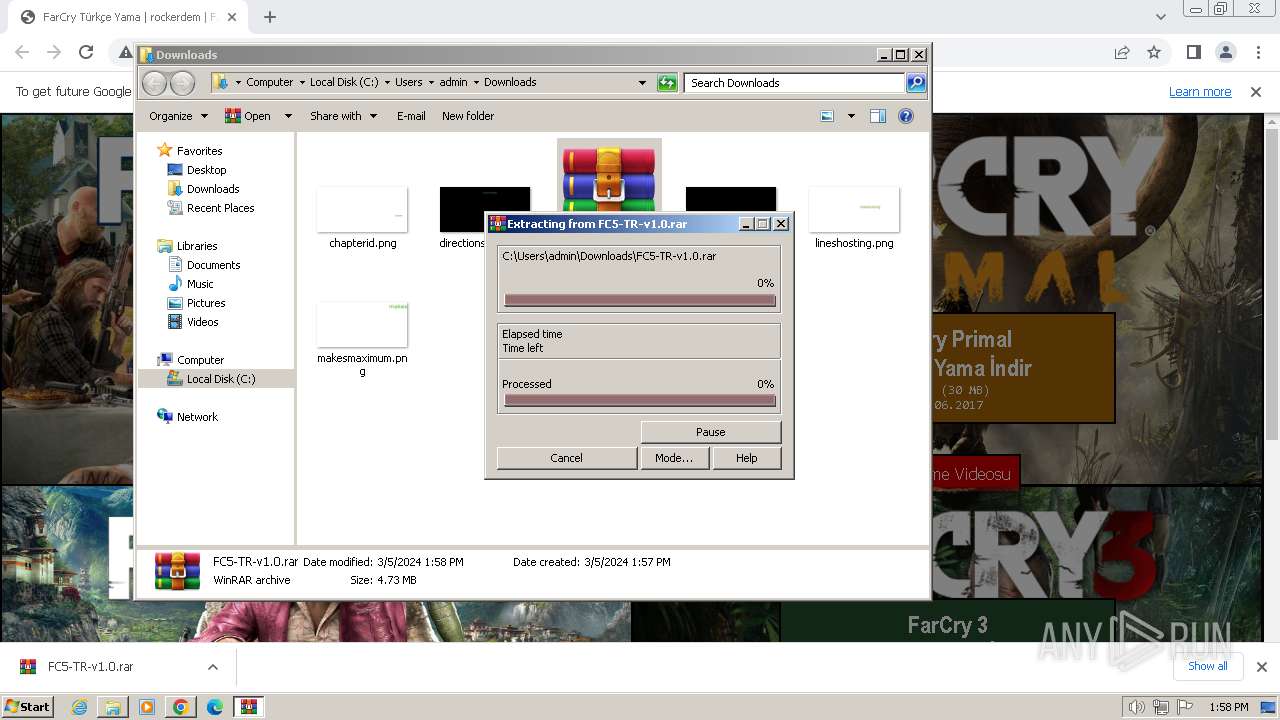
| 764 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\FC5-TR-v1.0.rar" C:\Users\admin\Downloads\FC5-TR-v1.0\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1360 --field-trial-handle=1172,i,5804333041968641534,8941490774512339025,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3640 --field-trial-handle=1172,i,5804333041968641534,8941490774512339025,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=3332 --field-trial-handle=1172,i,5804333041968641534,8941490774512339025,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3700 --field-trial-handle=1172,i,5804333041968641534,8941490774512339025,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3688 --field-trial-handle=1172,i,5804333041968641534,8941490774512339025,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1520 --field-trial-handle=1172,i,5804333041968641534,8941490774512339025,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1236 --field-trial-handle=1172,i,5804333041968641534,8941490774512339025,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
23 897
Read events
23 028
Write events
820
Delete events
49
Modification events
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
7
Suspicious files
12
Text files
45
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17fcaf.TMP | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8439ca62-0d38-40ea-a451-c5639cd93fc7.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17fcbf.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF180385.TMP | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF181c8b.TMP | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
30
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1040 | chrome.exe | GET | 200 | 178.210.174.35:80 | http://rockerdem.net/FarCryTR/ | unknown | html | 9.94 Kb | unknown |
1040 | chrome.exe | GET | 200 | 178.210.174.35:80 | http://rockerdem.net/FarCryTR/inc/jquery.js | unknown | text | 90.9 Kb | unknown |
1040 | chrome.exe | GET | 200 | 178.210.174.35:80 | http://rockerdem.net/FarCryTR/fc5.png | unknown | image | 62.3 Kb | unknown |
1040 | chrome.exe | GET | 200 | 178.210.174.35:80 | http://rockerdem.net/FarCryTR/fc4.png | unknown | image | 31.3 Kb | unknown |
1040 | chrome.exe | GET | 200 | 178.210.174.35:80 | http://rockerdem.net/FarCryTR/fcp.png | unknown | image | 22.8 Kb | unknown |
1040 | chrome.exe | GET | 200 | 178.210.174.35:80 | http://rockerdem.net/FarCryTR/fc3.png | unknown | image | 42.6 Kb | unknown |
1040 | chrome.exe | GET | 200 | 178.210.174.35:80 | http://rockerdem.net/FarCryTR/abc/r.png | unknown | image | 1.81 Kb | unknown |
1040 | chrome.exe | GET | 200 | 178.210.174.35:80 | http://rockerdem.net/FarCryTR/abc/o.png | unknown | image | 1.77 Kb | unknown |
1040 | chrome.exe | GET | 200 | 178.210.174.35:80 | http://rockerdem.net/FarCryTR/abc/c.png | unknown | image | 1.84 Kb | unknown |
1040 | chrome.exe | GET | 200 | 178.210.174.35:80 | http://rockerdem.net/FarCryTR/abc/k.png | unknown | image | 2.04 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3652 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1040 | chrome.exe | 74.125.128.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
1040 | chrome.exe | 178.210.174.35:80 | rockerdem.net | PremierDC Veri Merkezi Anonim Sirketi | TR | unknown |
1040 | chrome.exe | 142.250.186.78:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
1040 | chrome.exe | 142.250.184.200:443 | www.googletagmanager.com | GOOGLE | US | unknown |
1040 | chrome.exe | 216.239.34.36:443 | region1.google-analytics.com | GOOGLE | US | unknown |
1040 | chrome.exe | 142.250.186.132:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
rockerdem.net |
| unknown |
www.google-analytics.com |
| whitelisted |
bit.ly |
| shared |
goo.gl |
| shared |
voidu.com |
| whitelisted |
www.facebook.com |
| whitelisted |
www.youtube.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
region1.google-analytics.com |
| whitelisted |