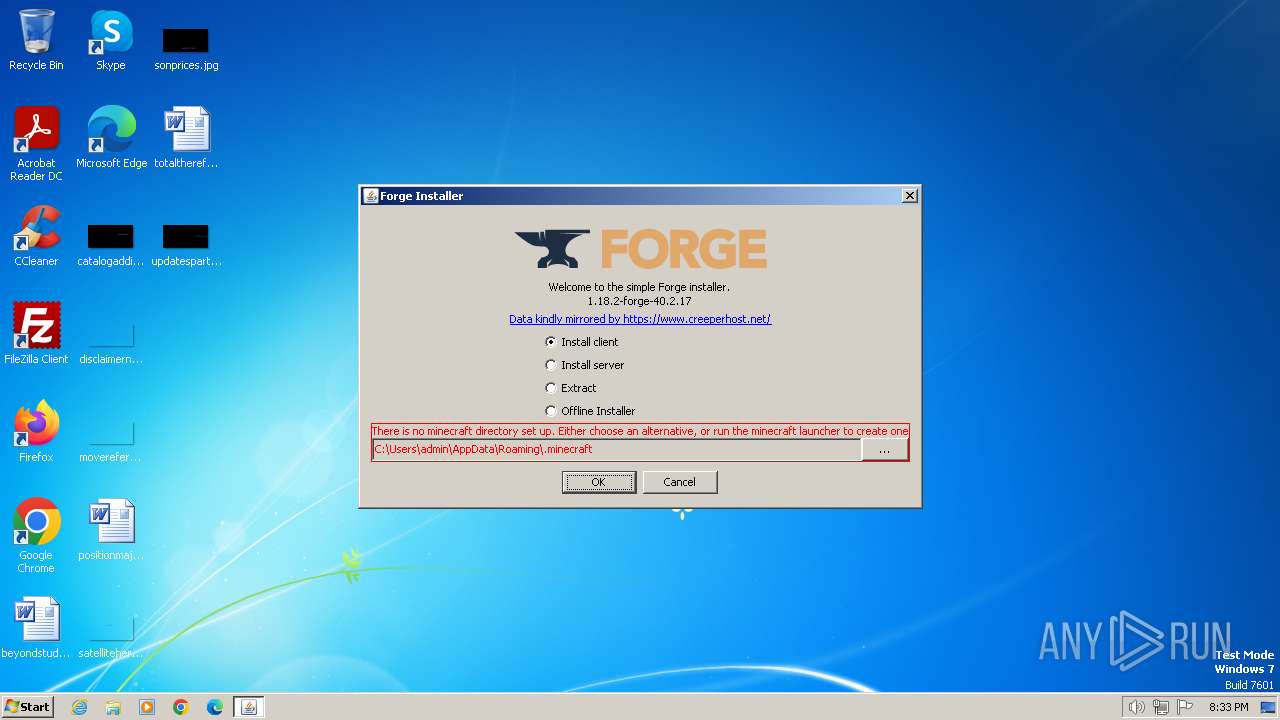
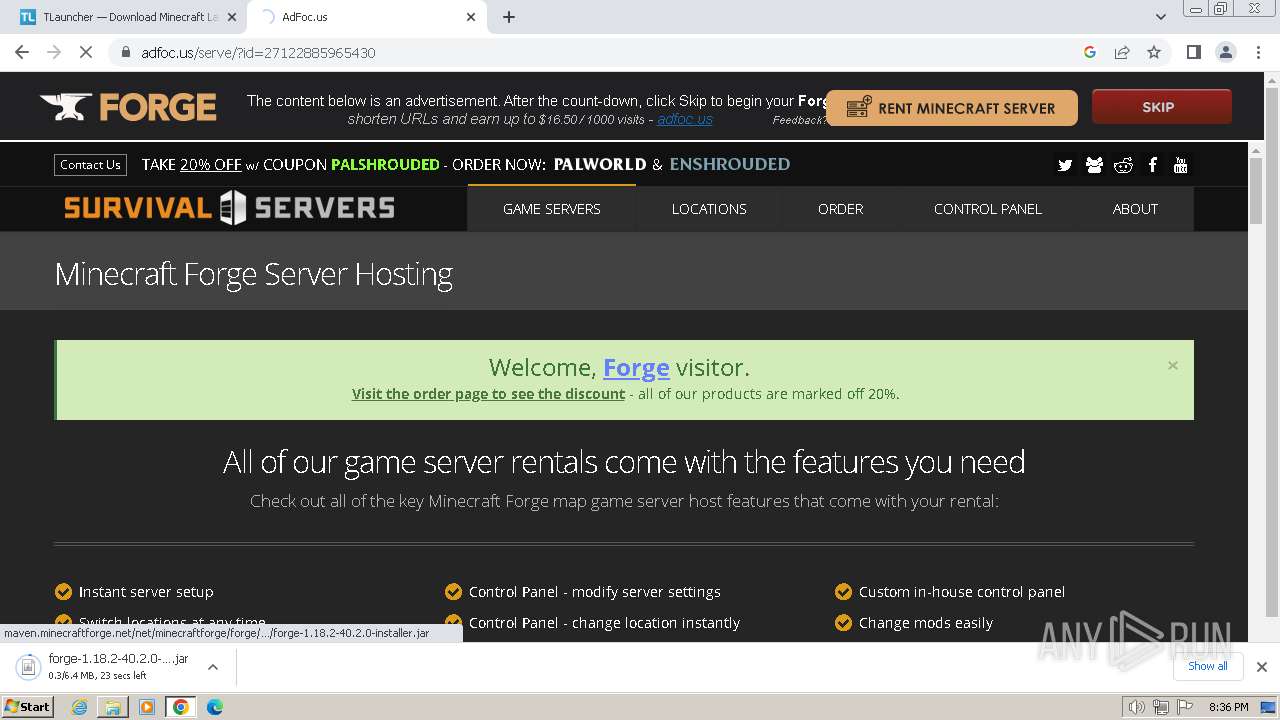
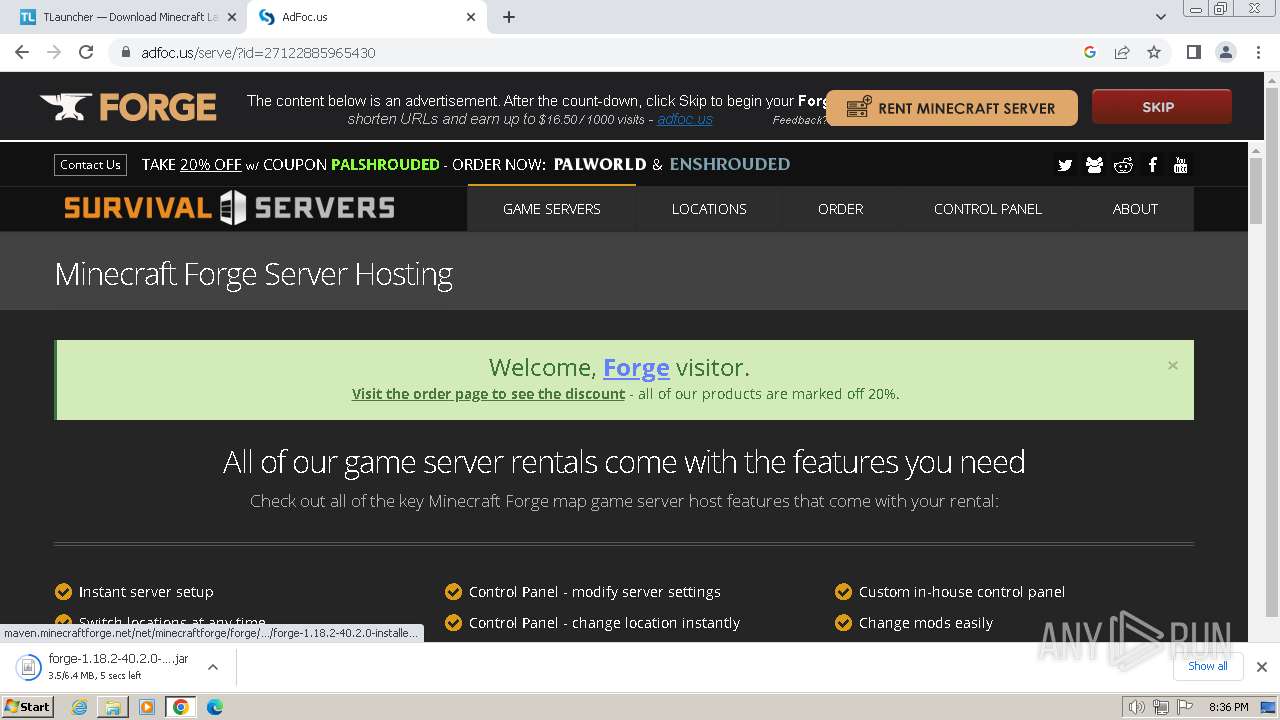
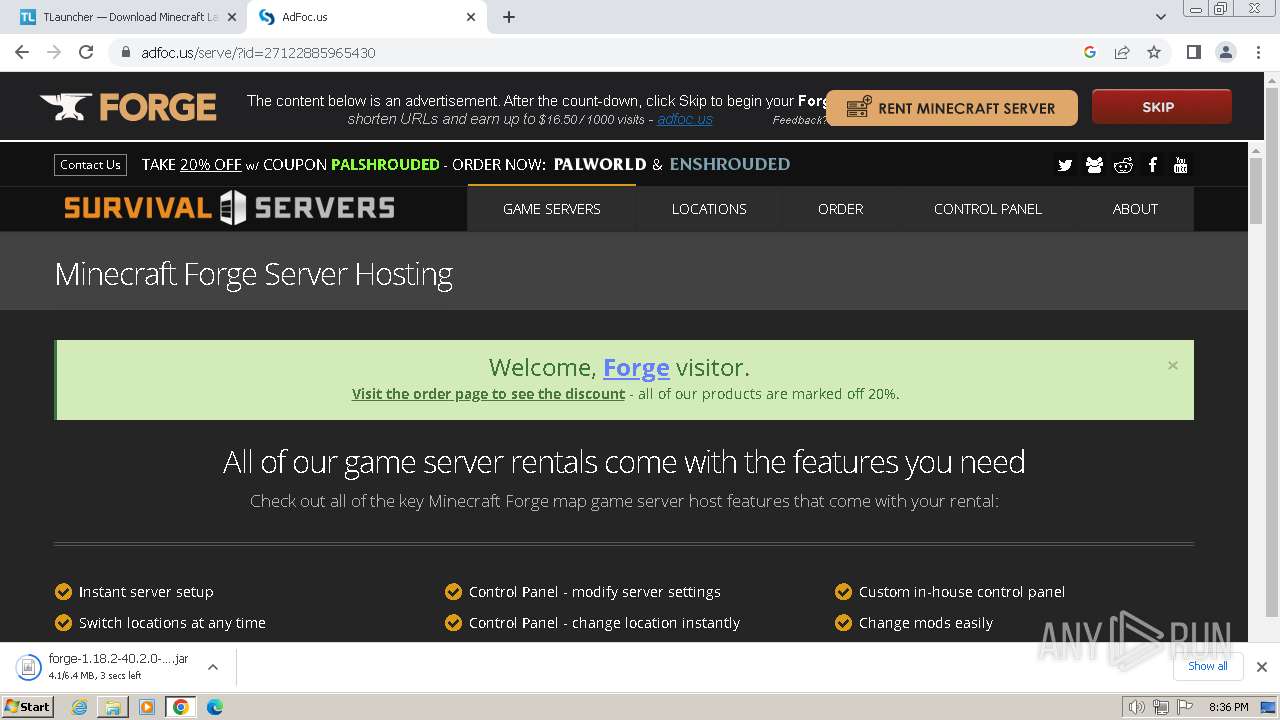
| File name: | forge-1.18.2-40.2.17-installer.jar |
| Full analysis: | https://app.any.run/tasks/2f9089d8-b7dd-4975-8f42-6b63f7e79080 |
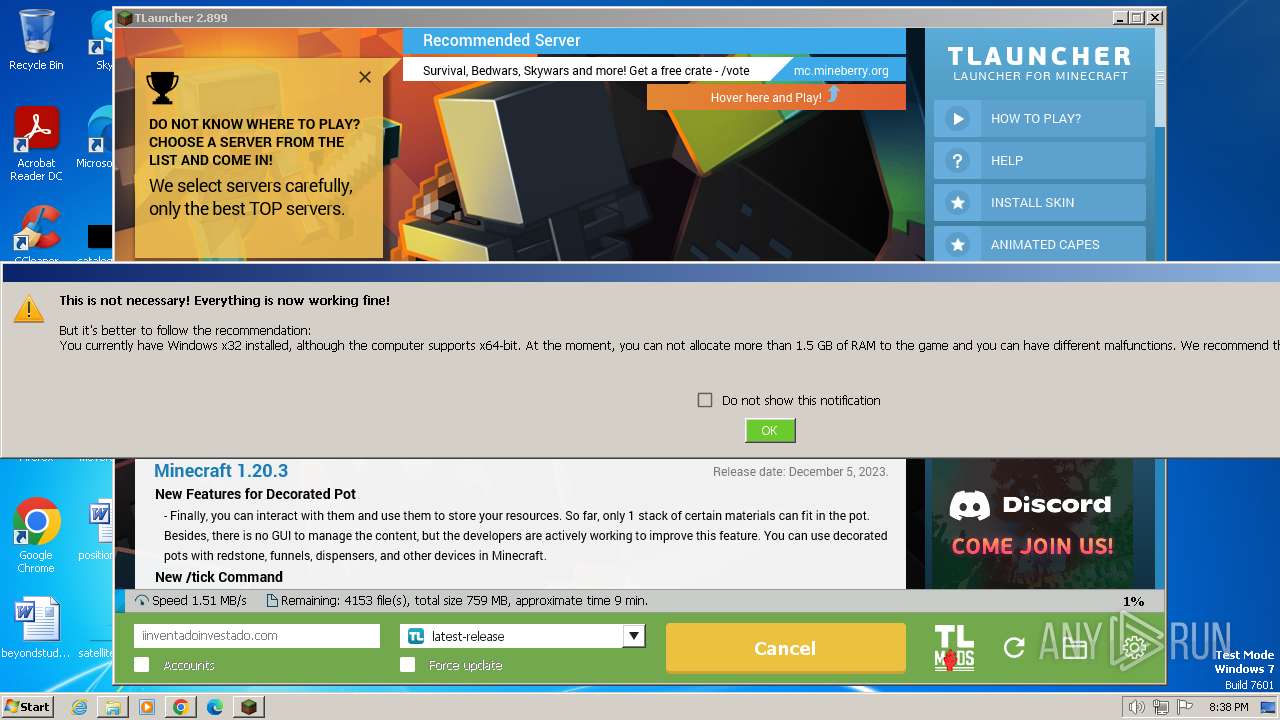
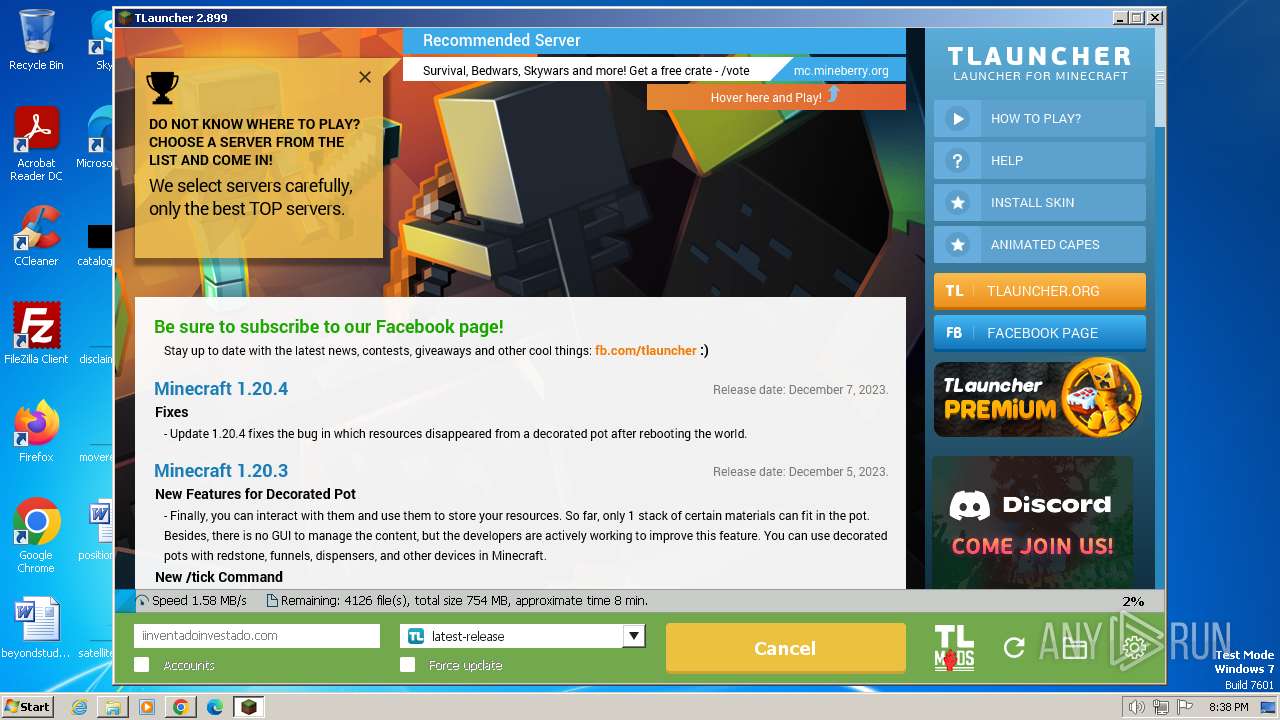
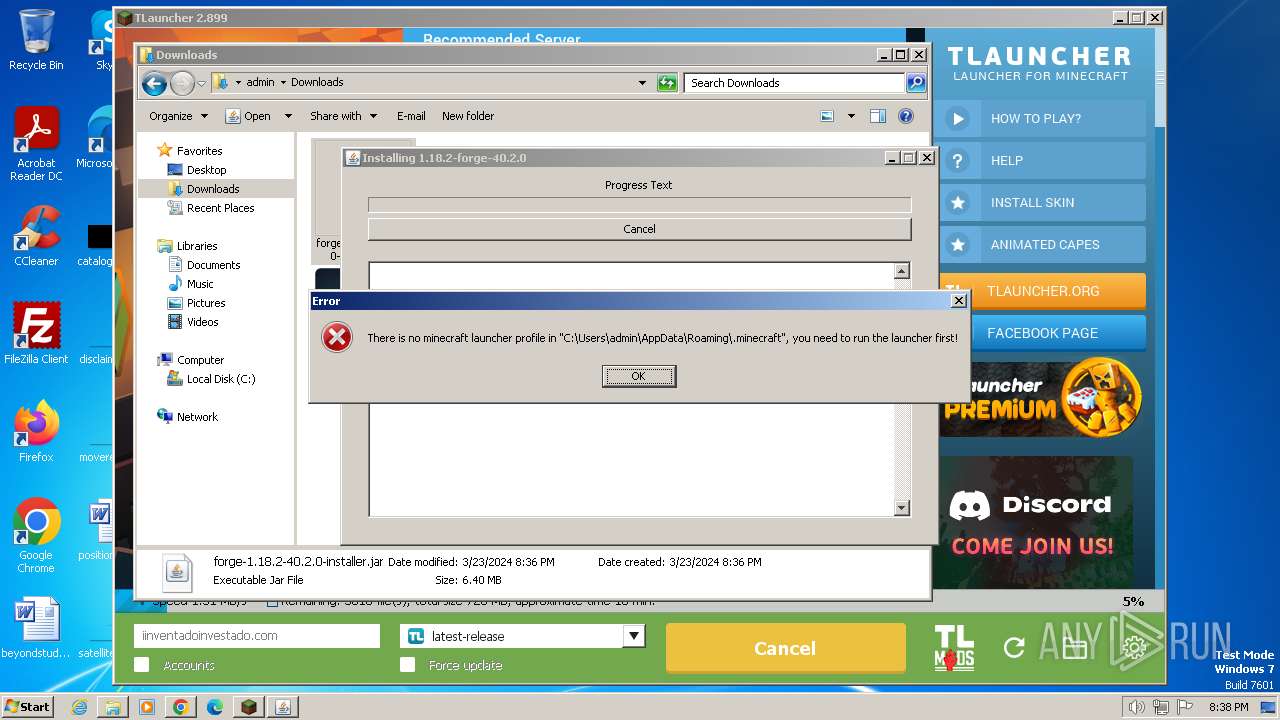
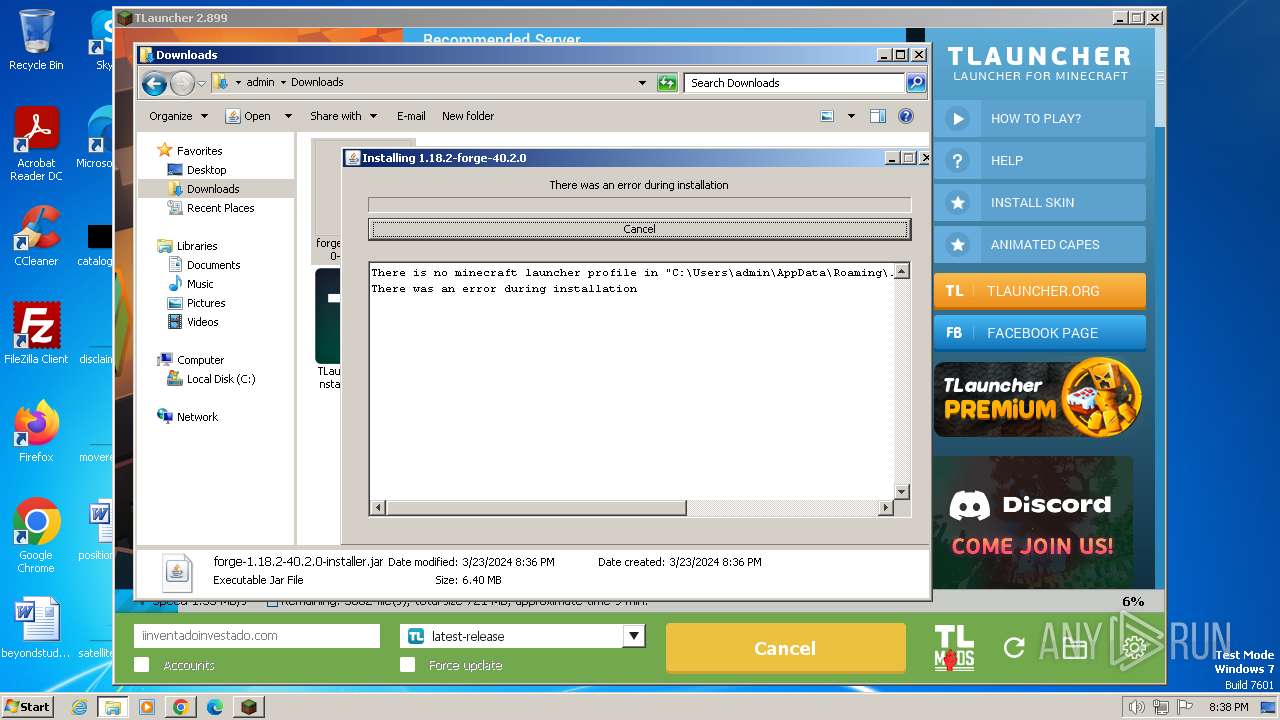
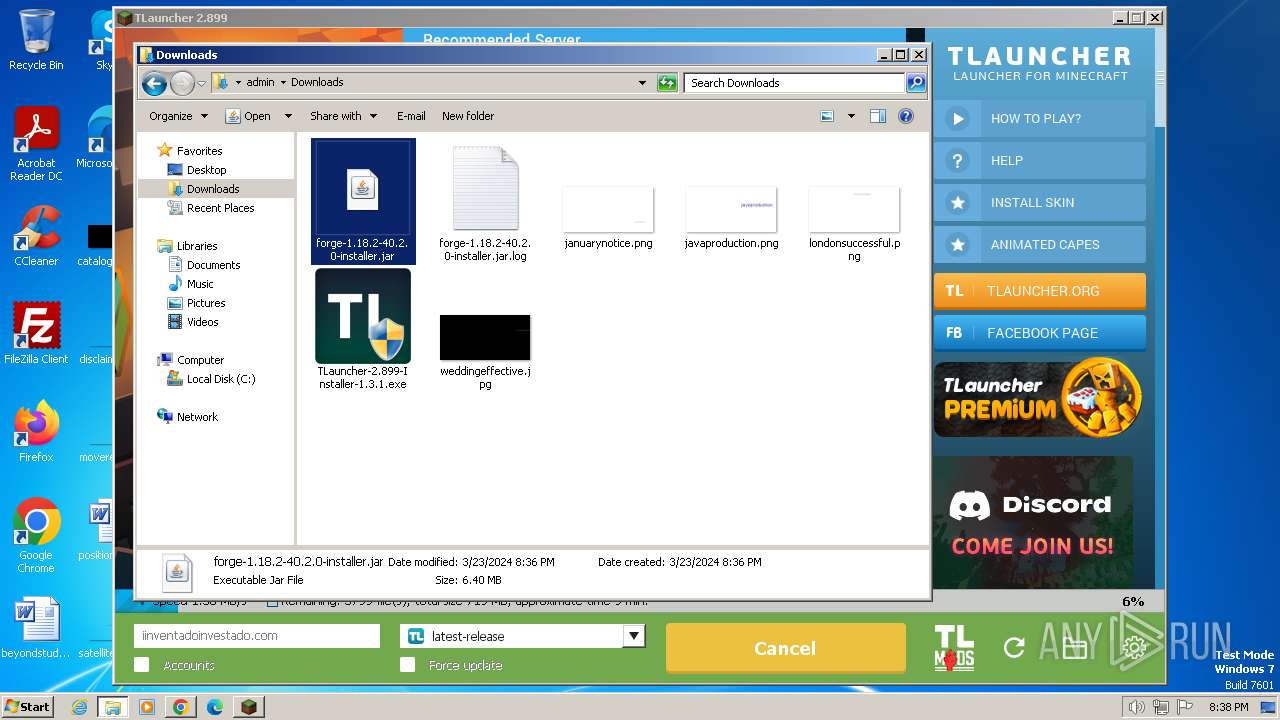
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2024, 20:33:41 |
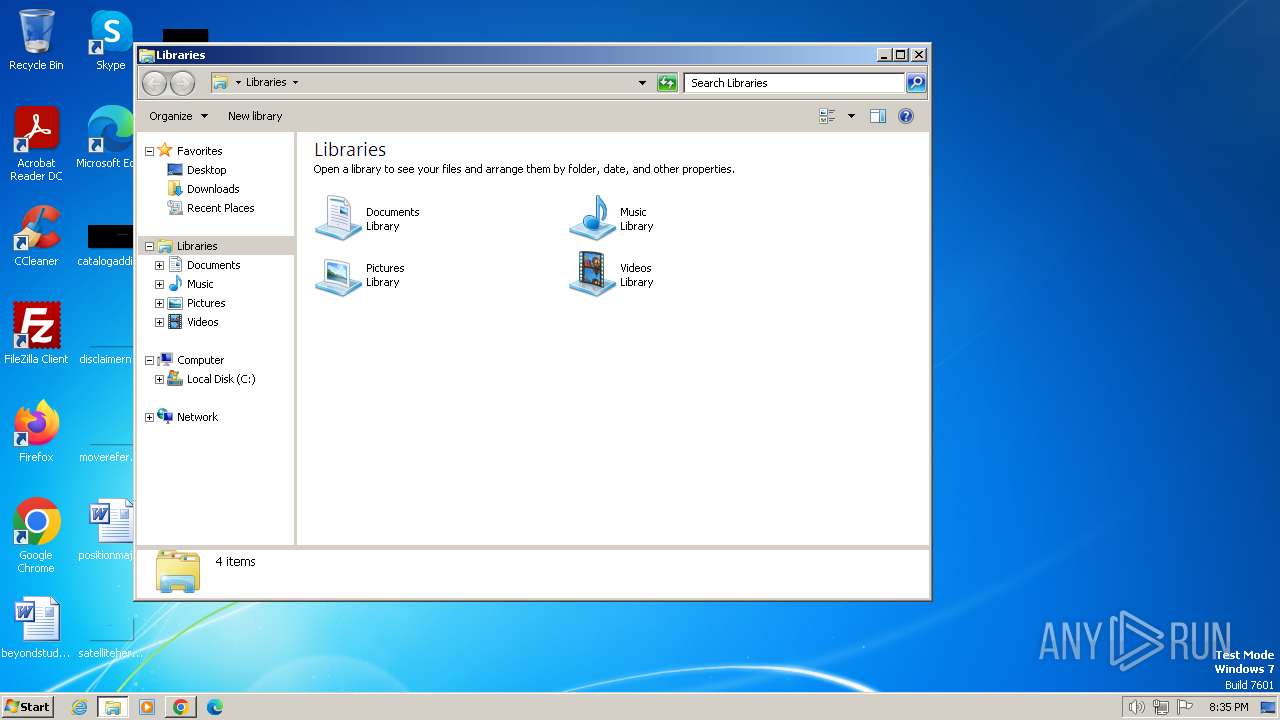
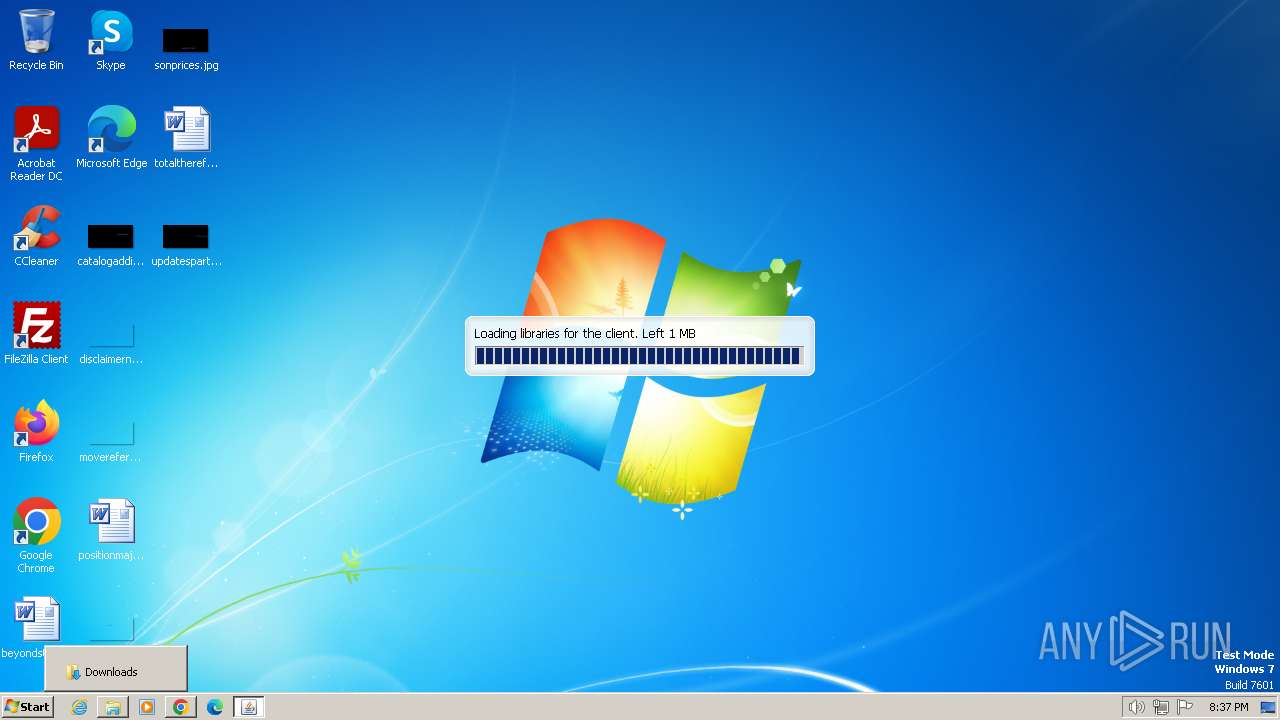
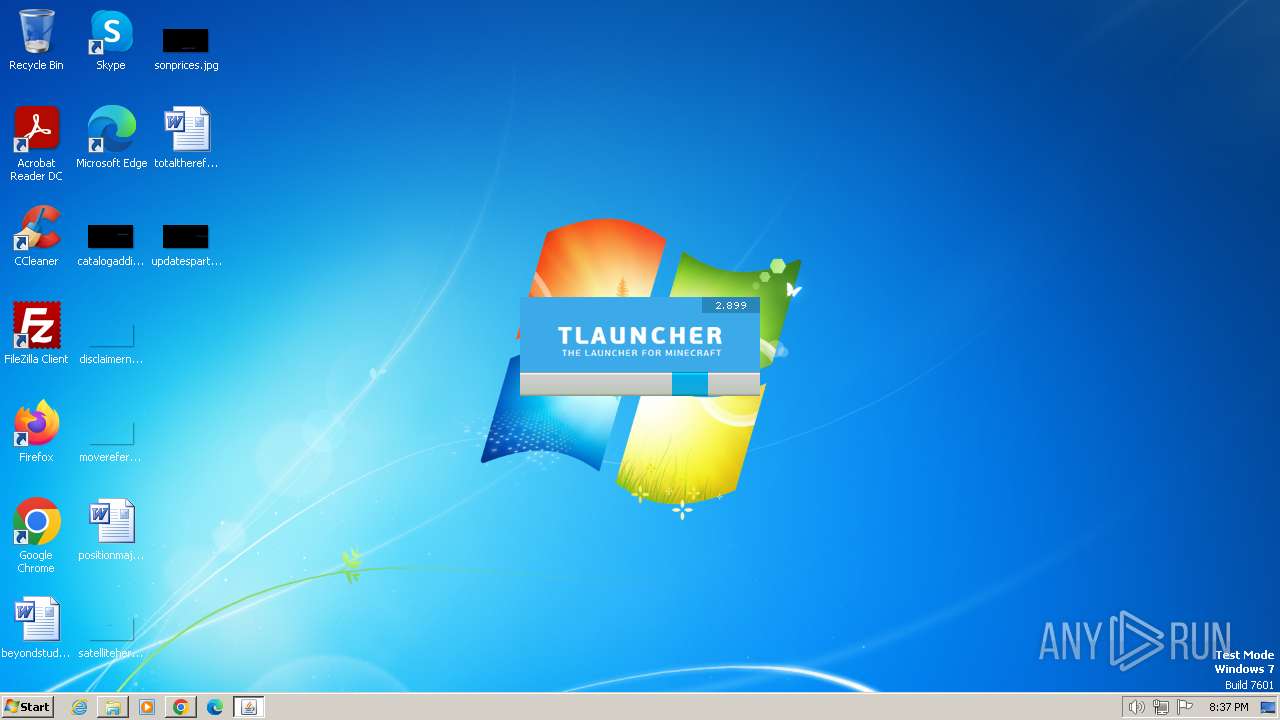
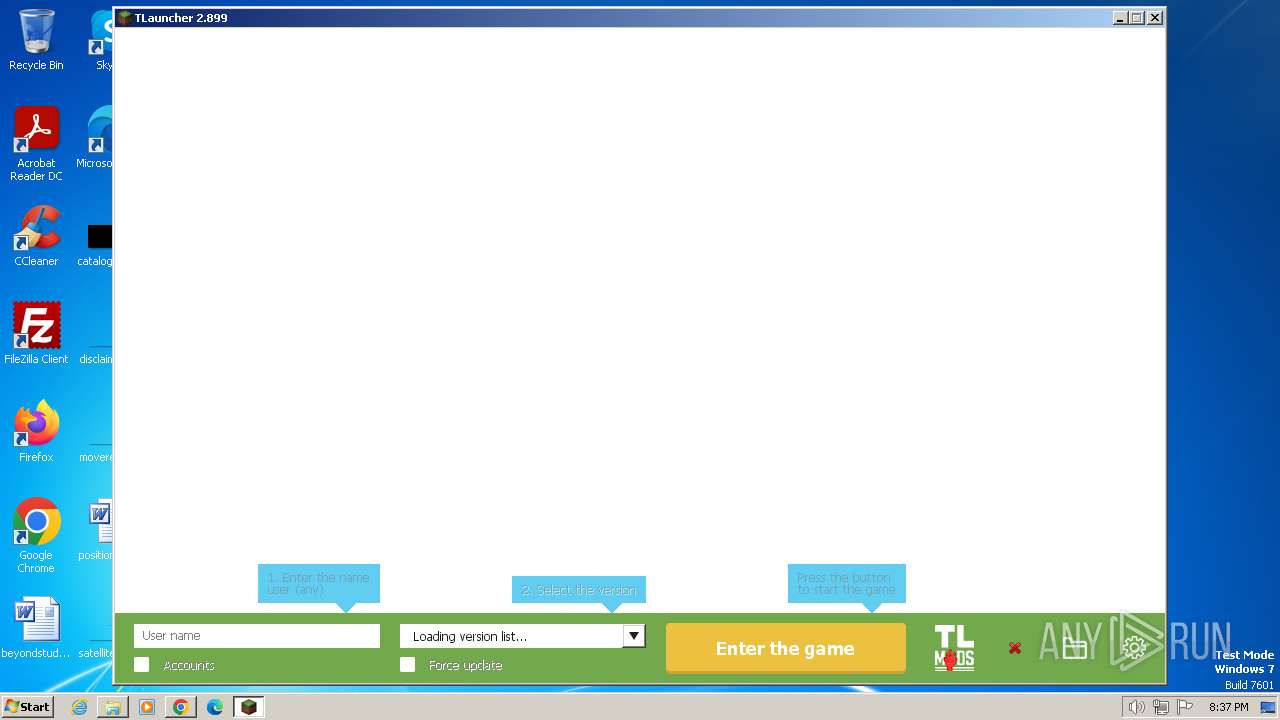
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | 808F55344DDC66E6685EBCC11B5C04C9 |
| SHA1: | DC12B399A682B86AE63F91A458A3B7435696D012 |
| SHA256: | 8991F47EEBAE474DEF502C0660EE6895D2D2524B1A5AB5012A1F6D26C070C3DD |
| SSDEEP: | 98304:0B5XtBpSmX2jBcjdvw8lXPh/pd+SEQ8ROQPJPzx5z1+kbVnvFkwW59nuA6RZ86hh:2OmNC+cMK |
MALICIOUS
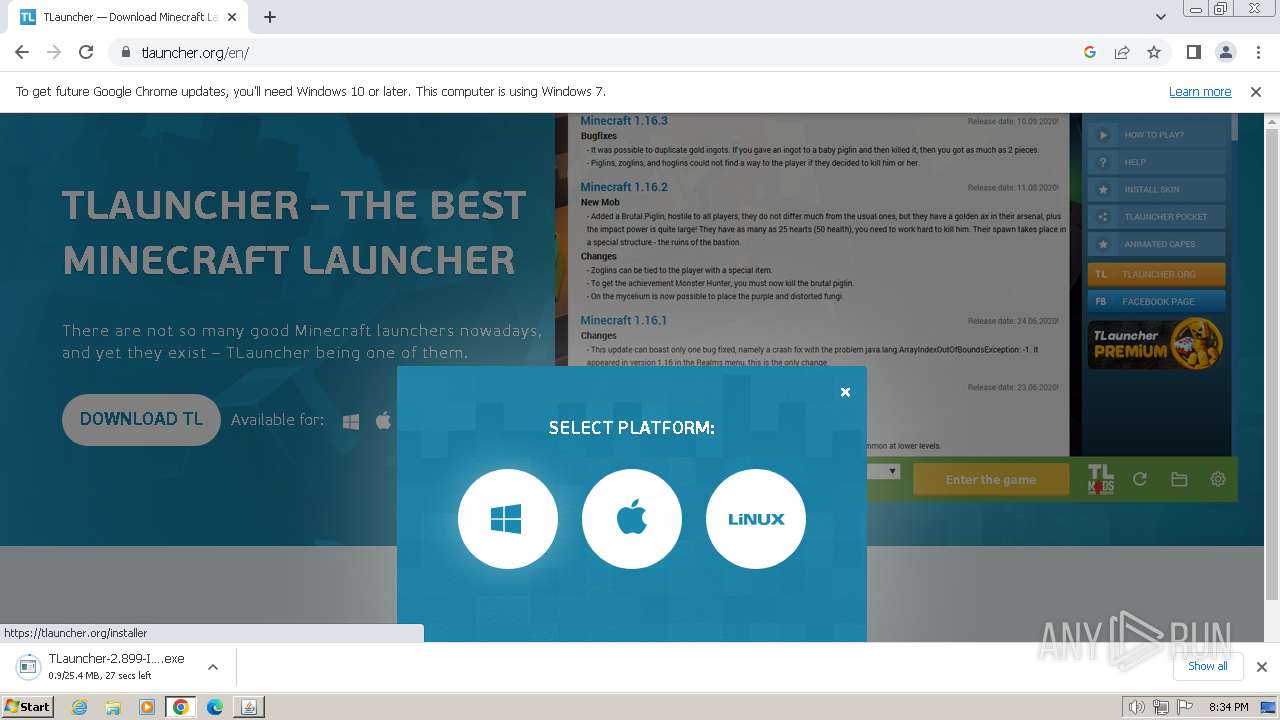
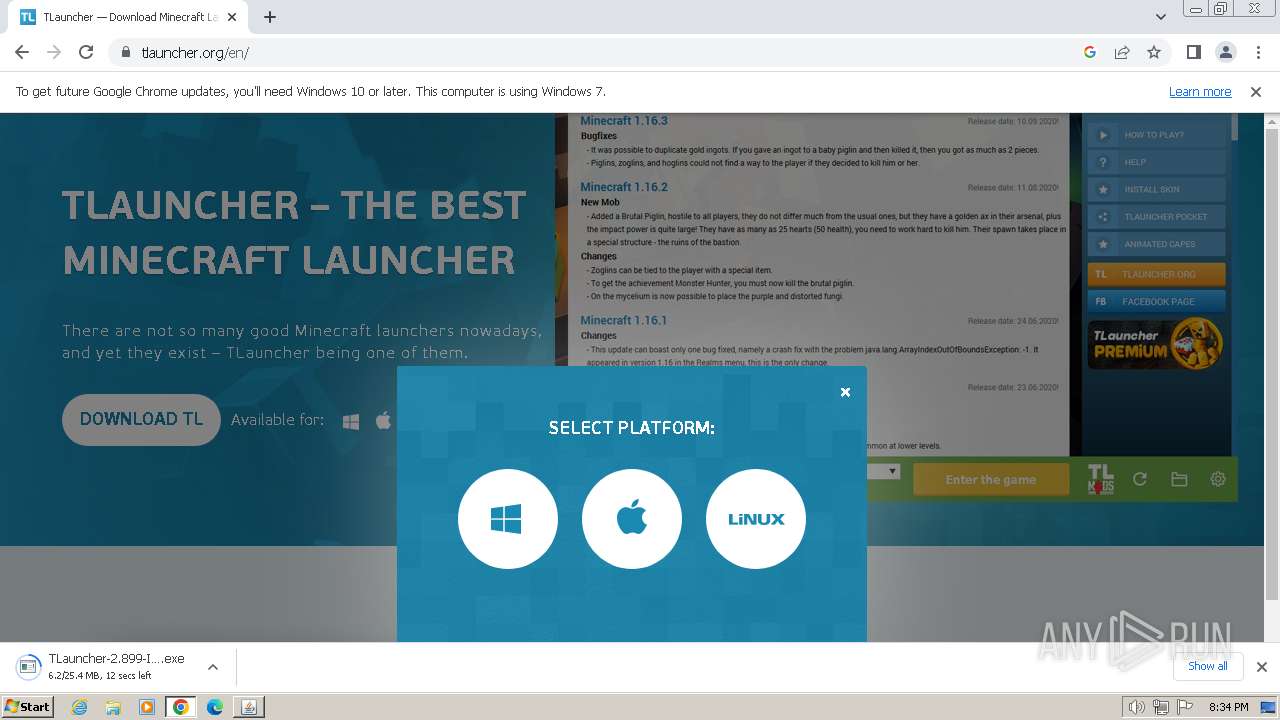
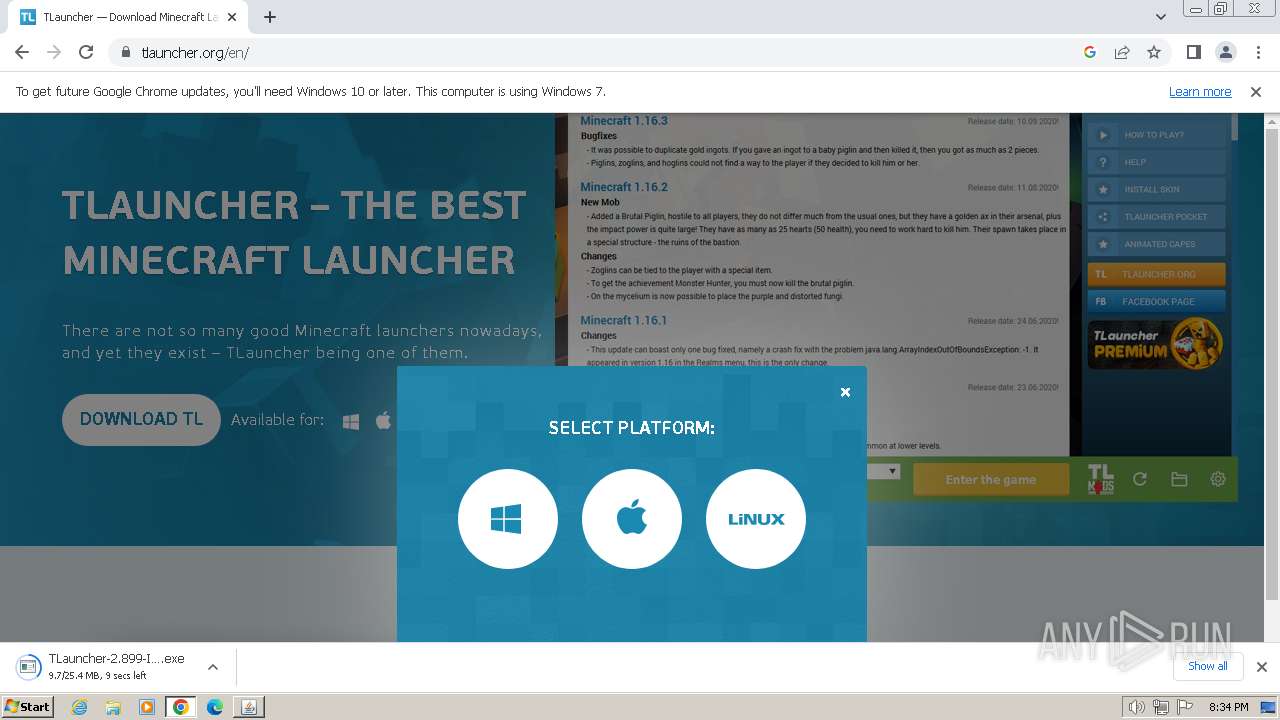
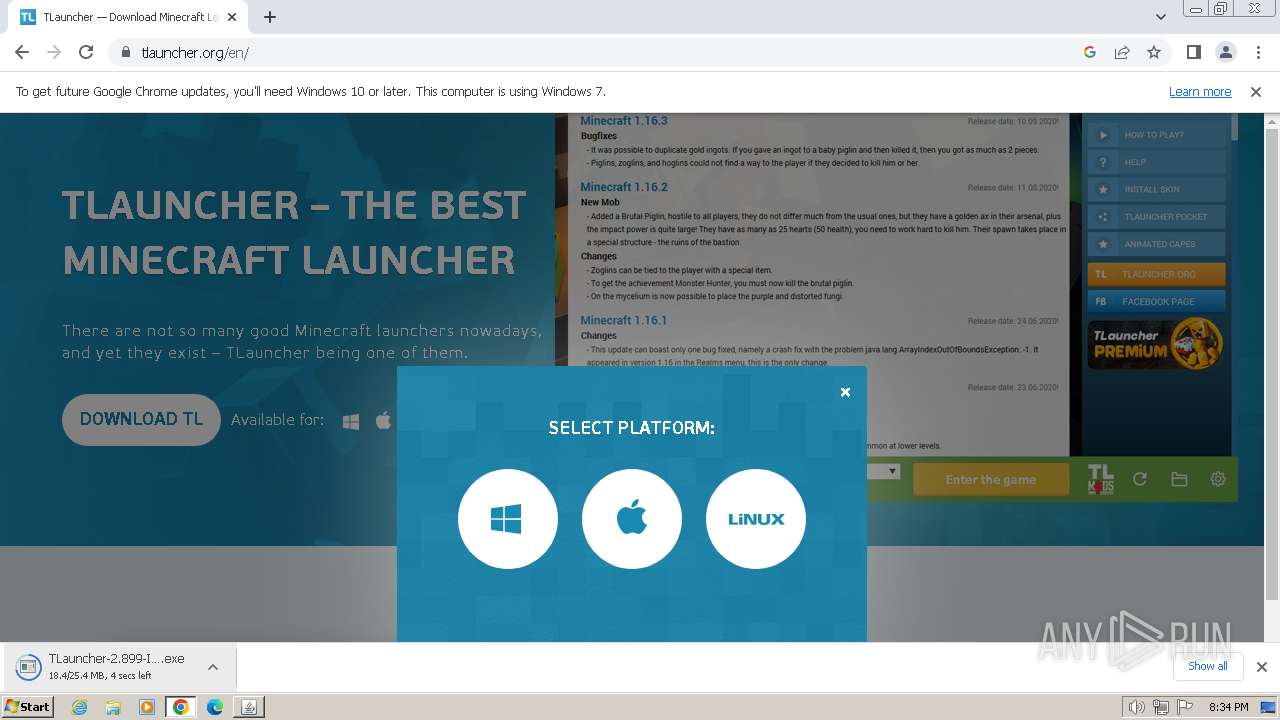
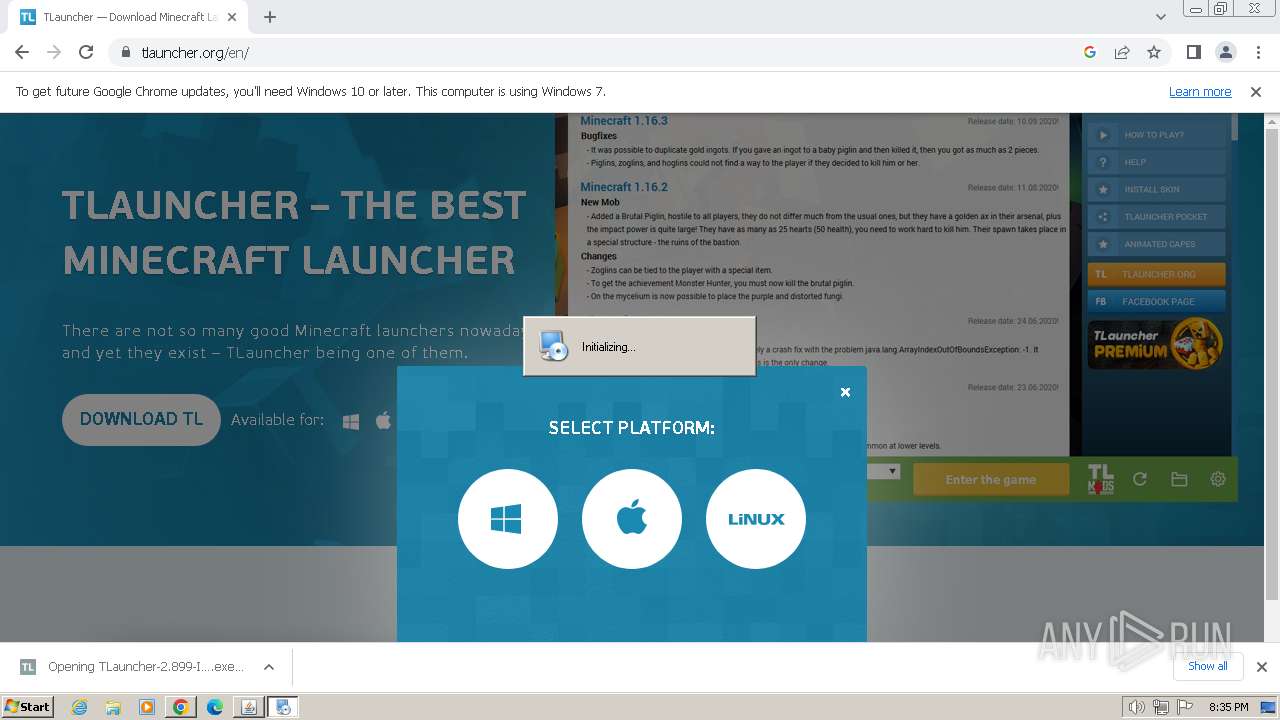
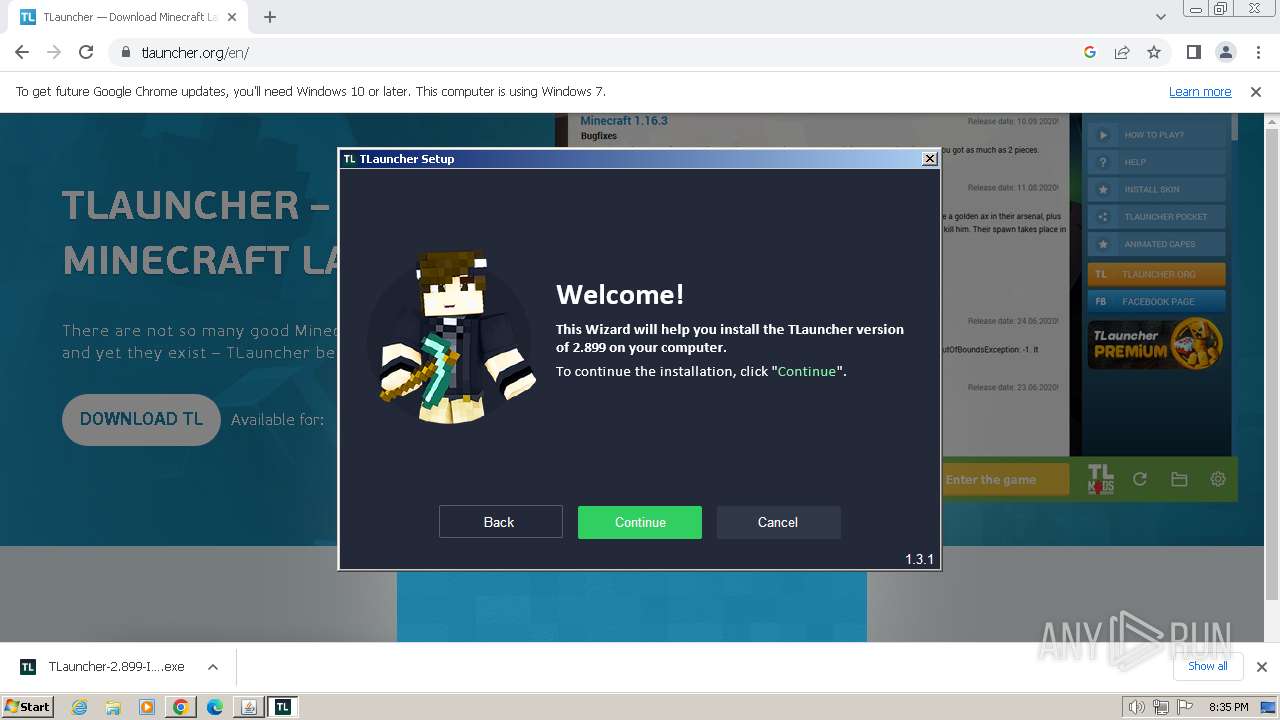
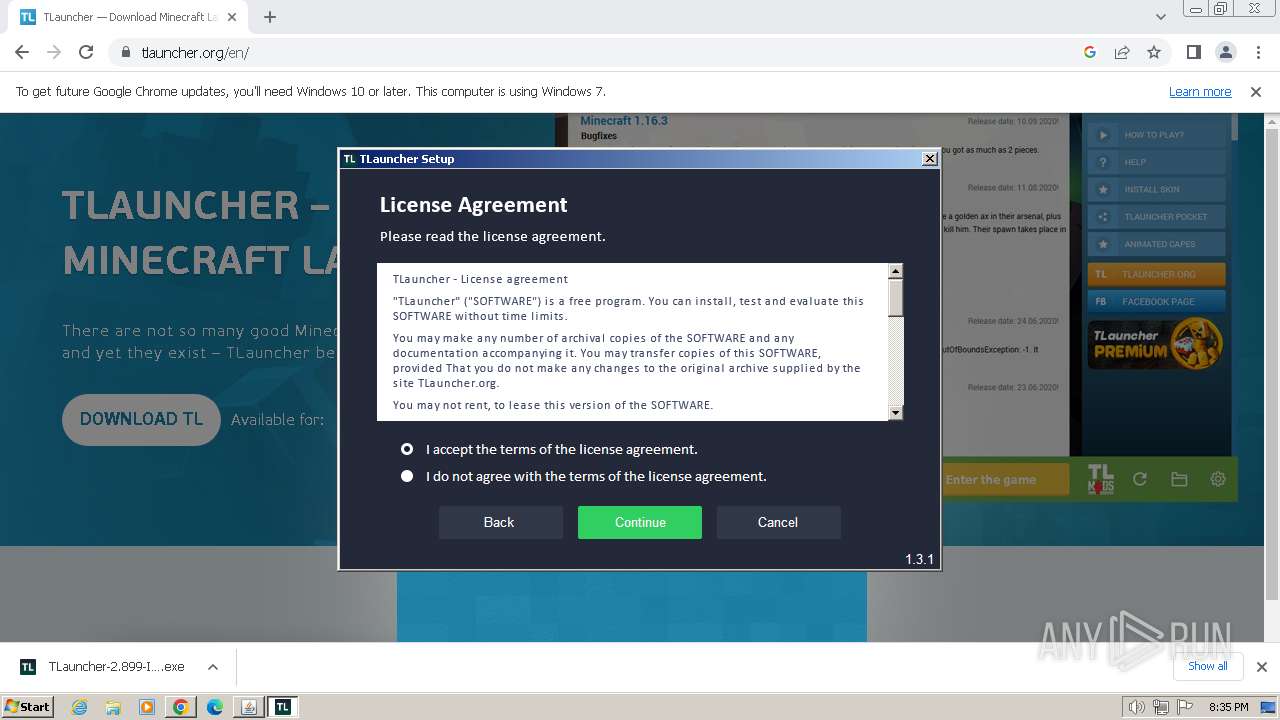
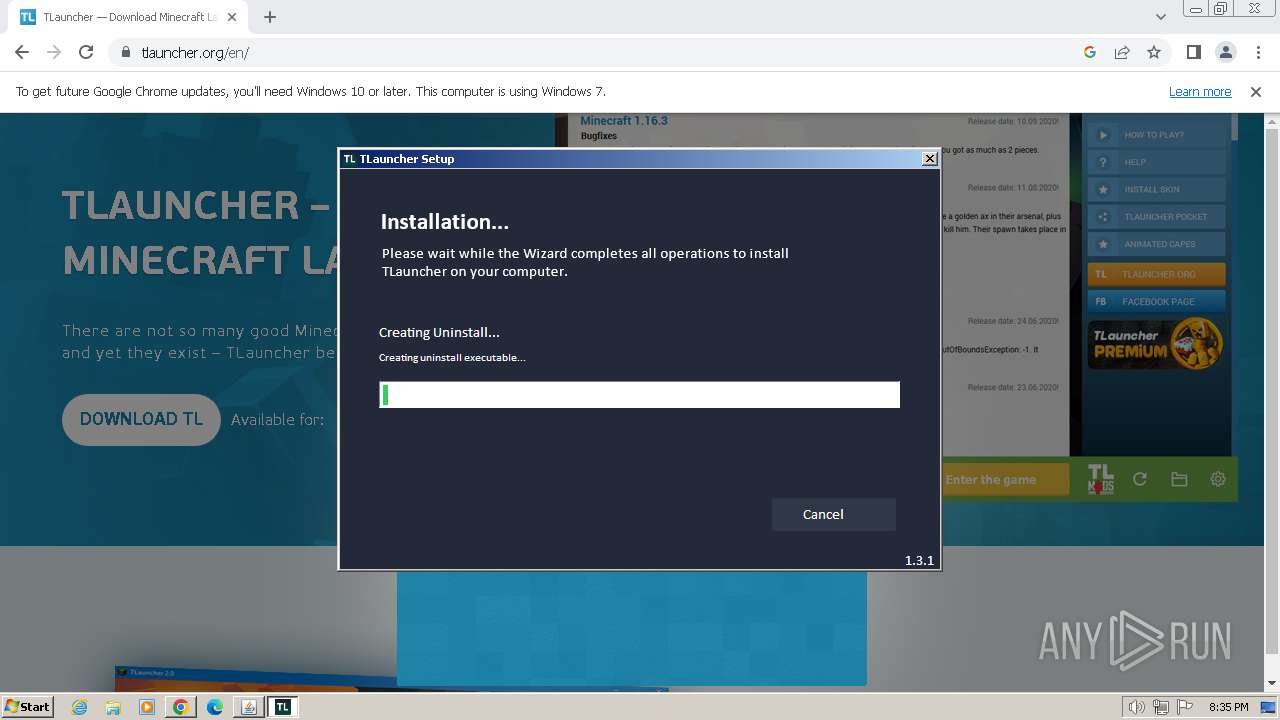
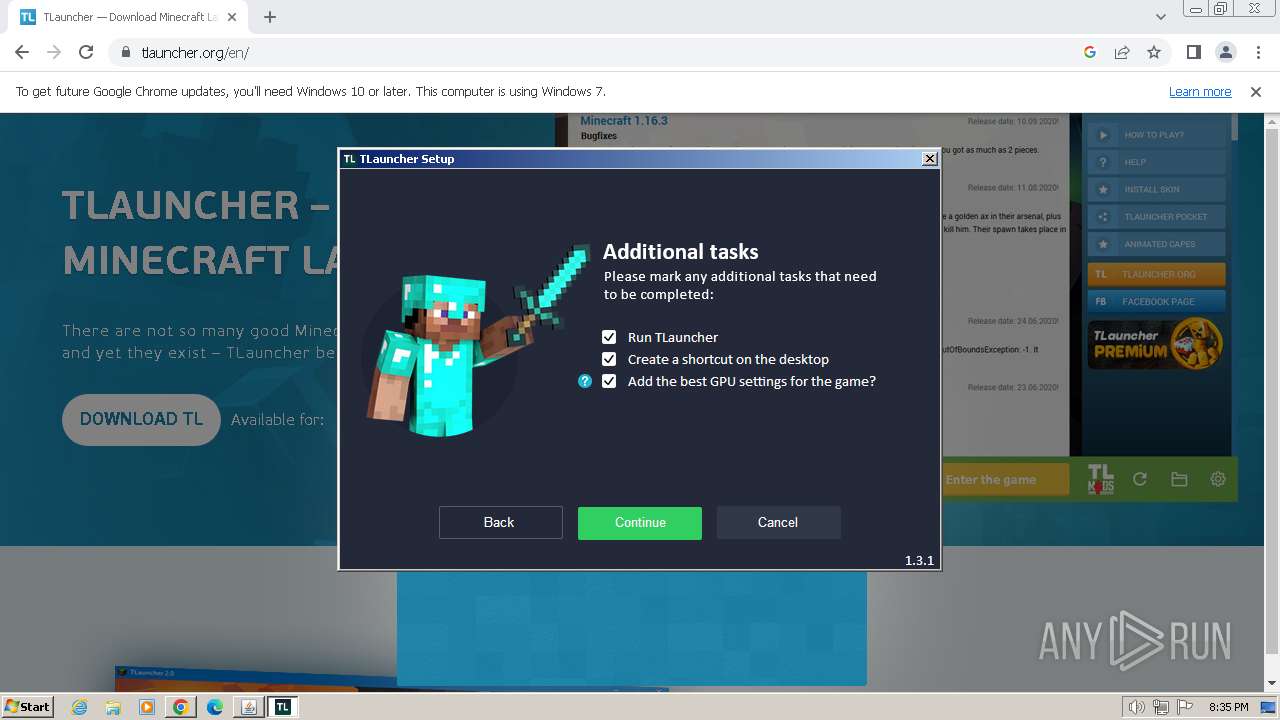
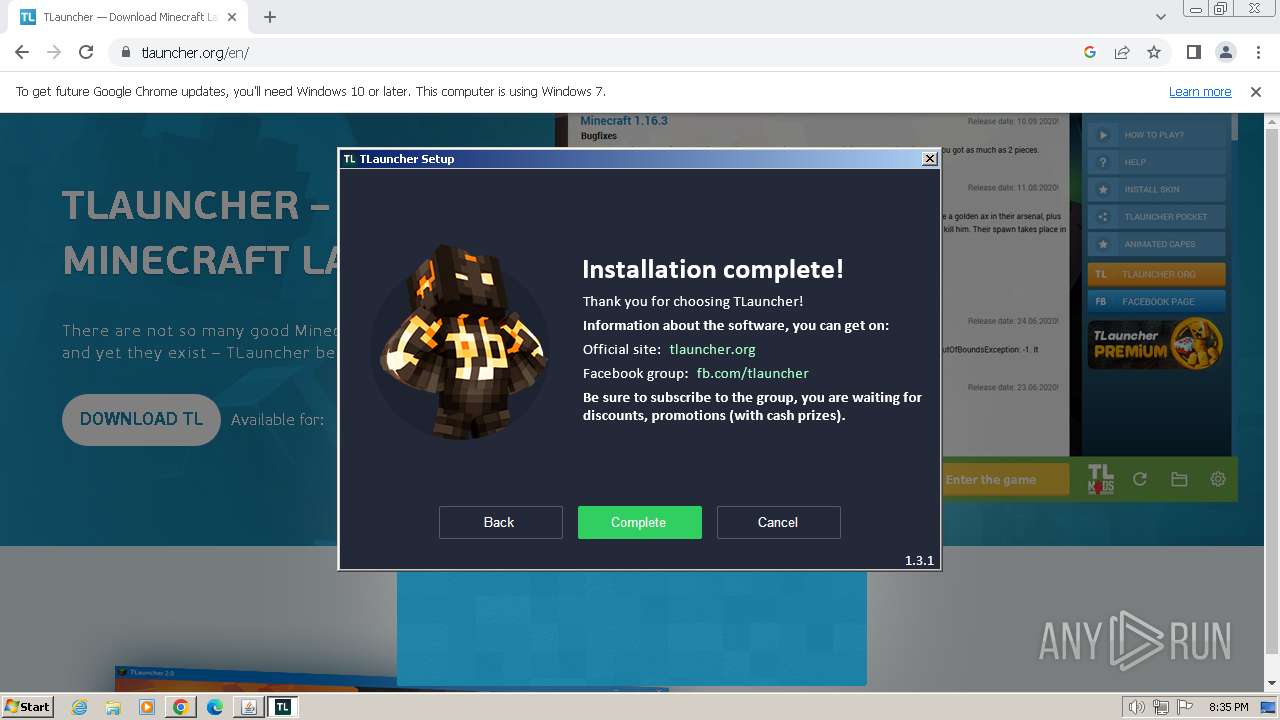
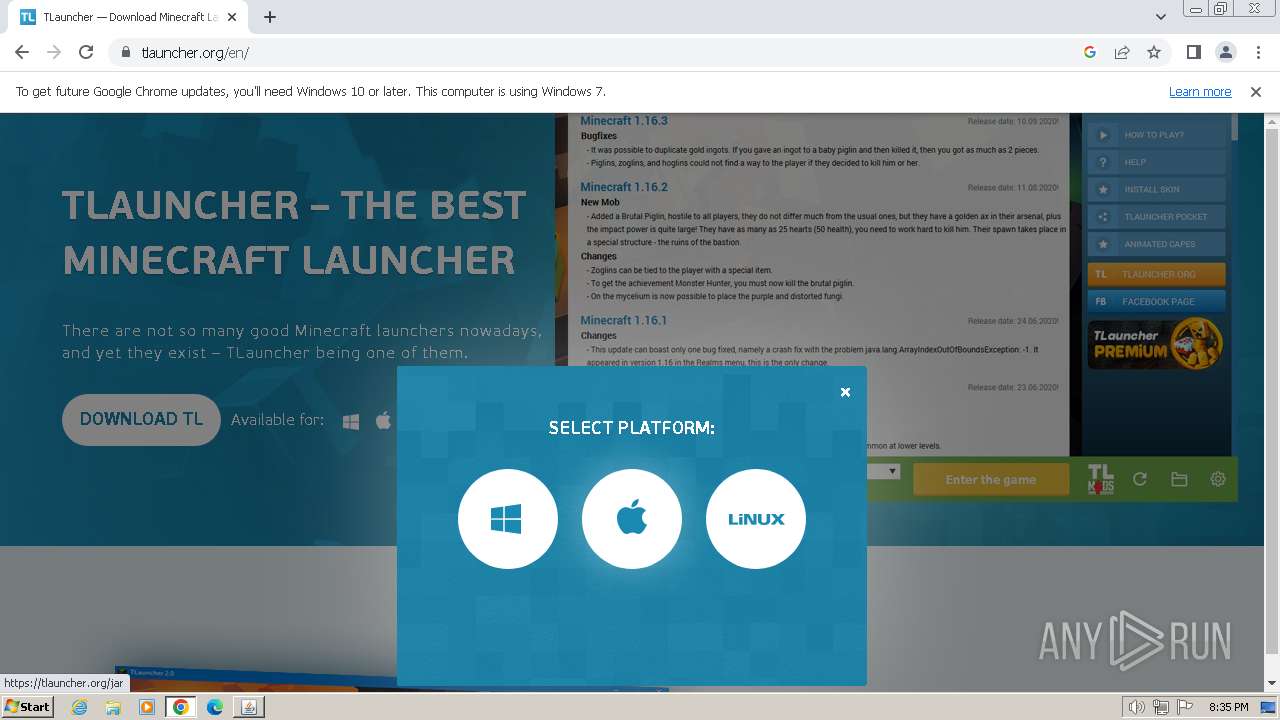
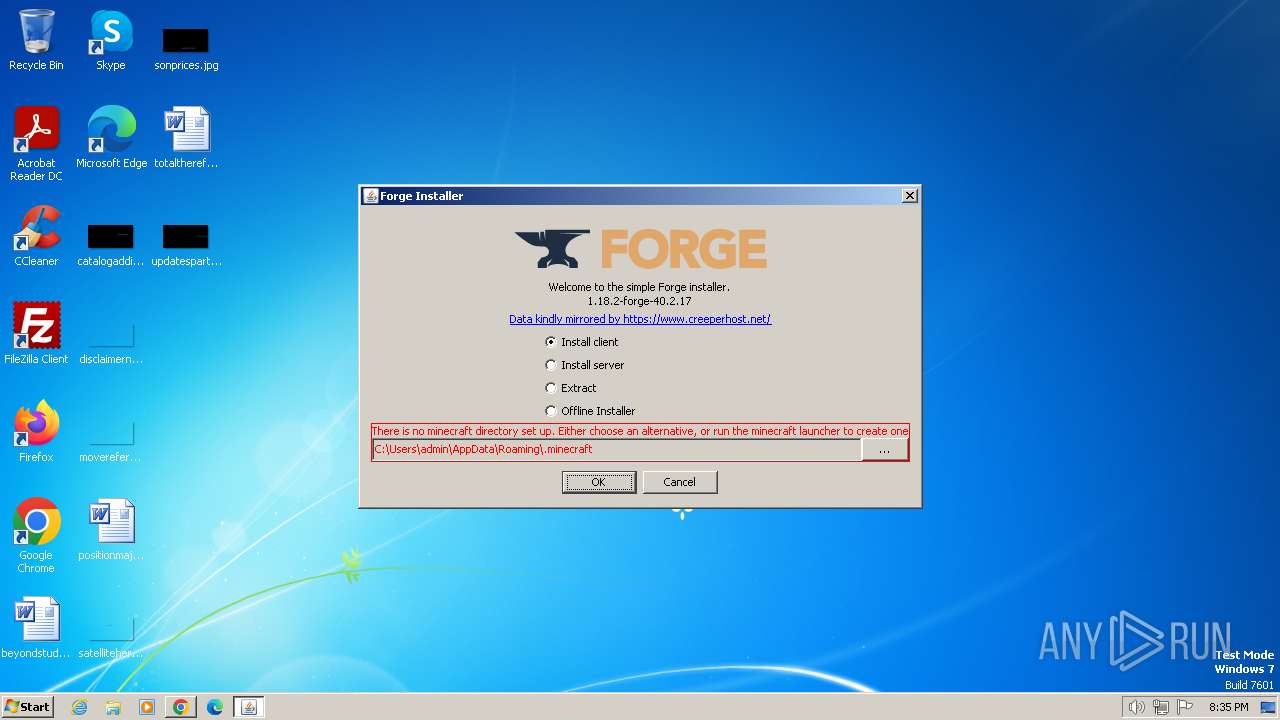
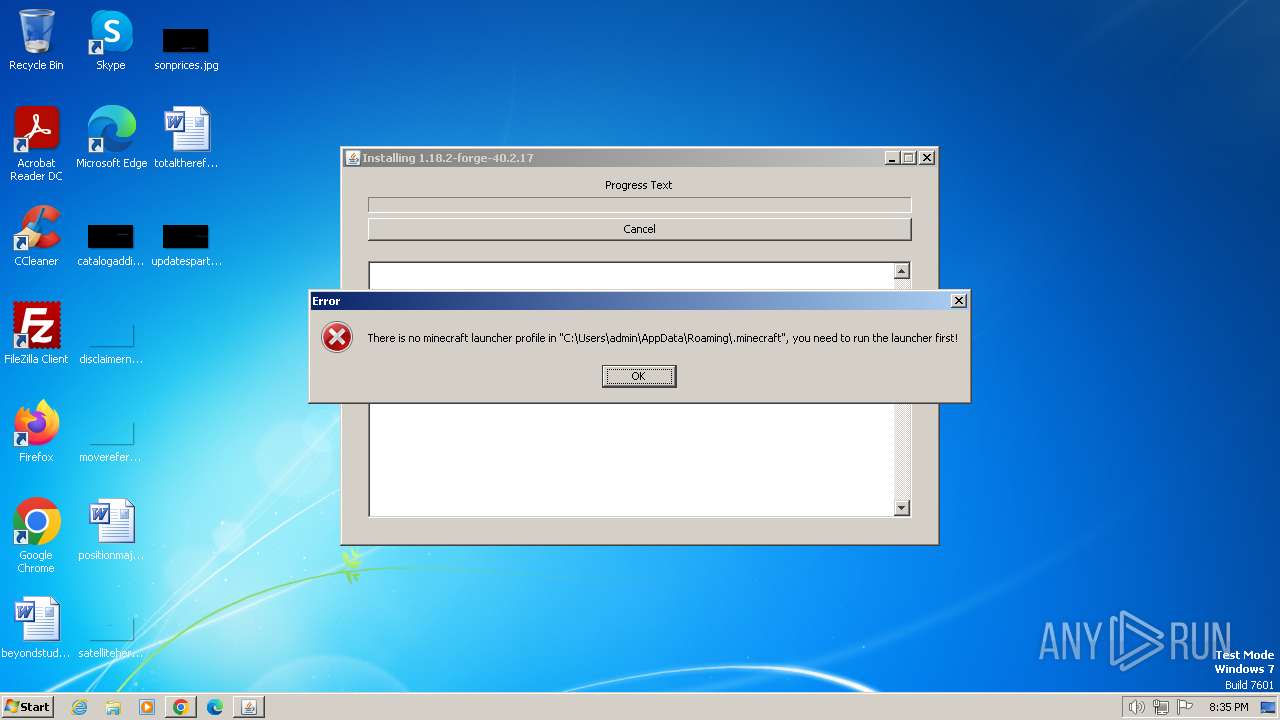
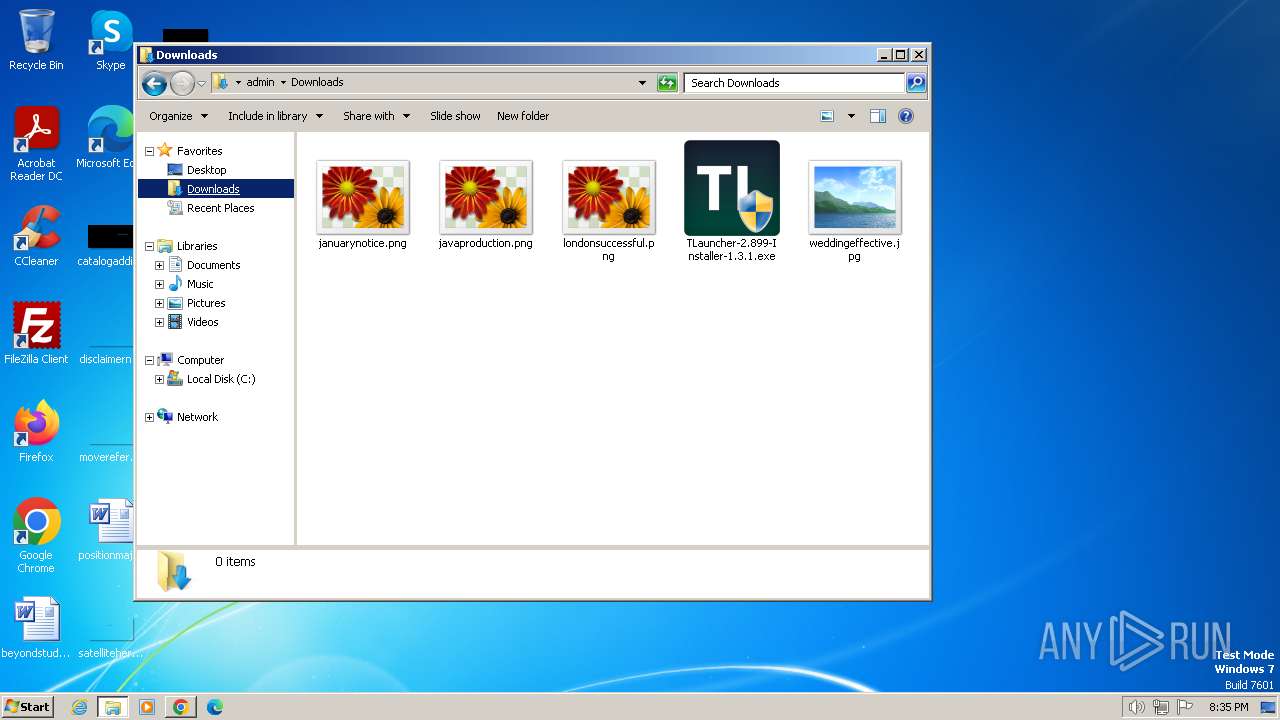
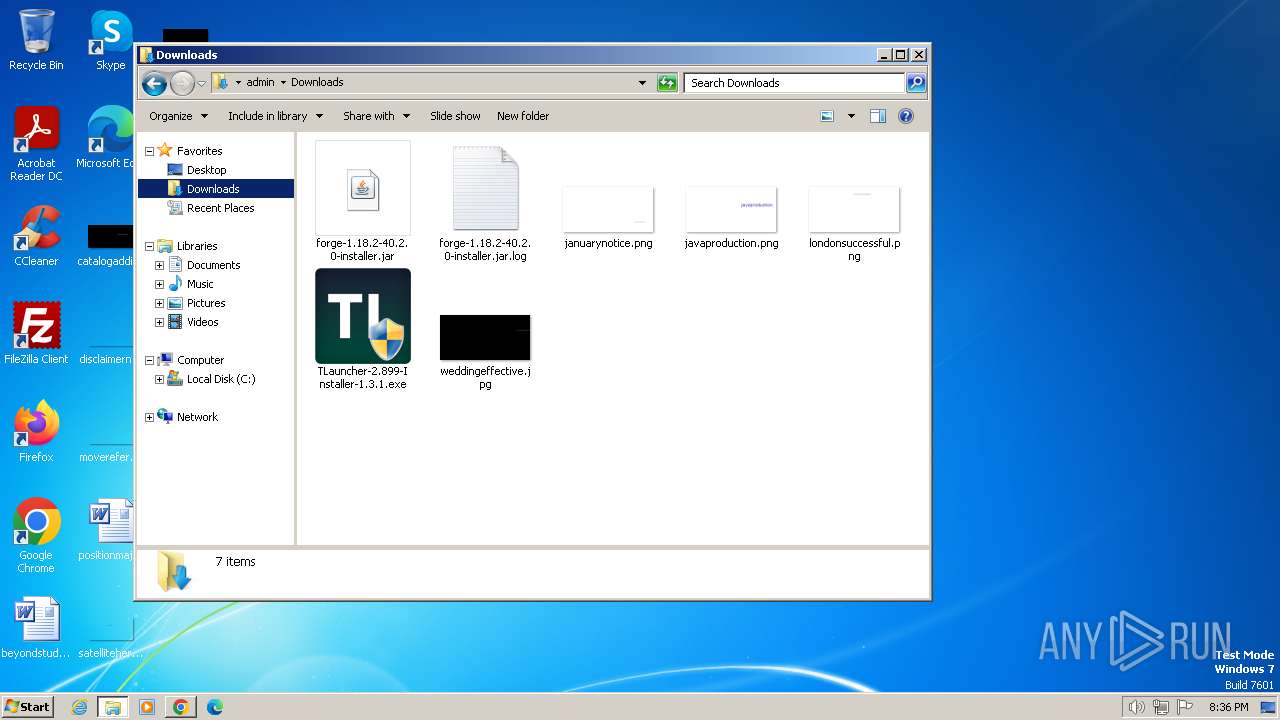
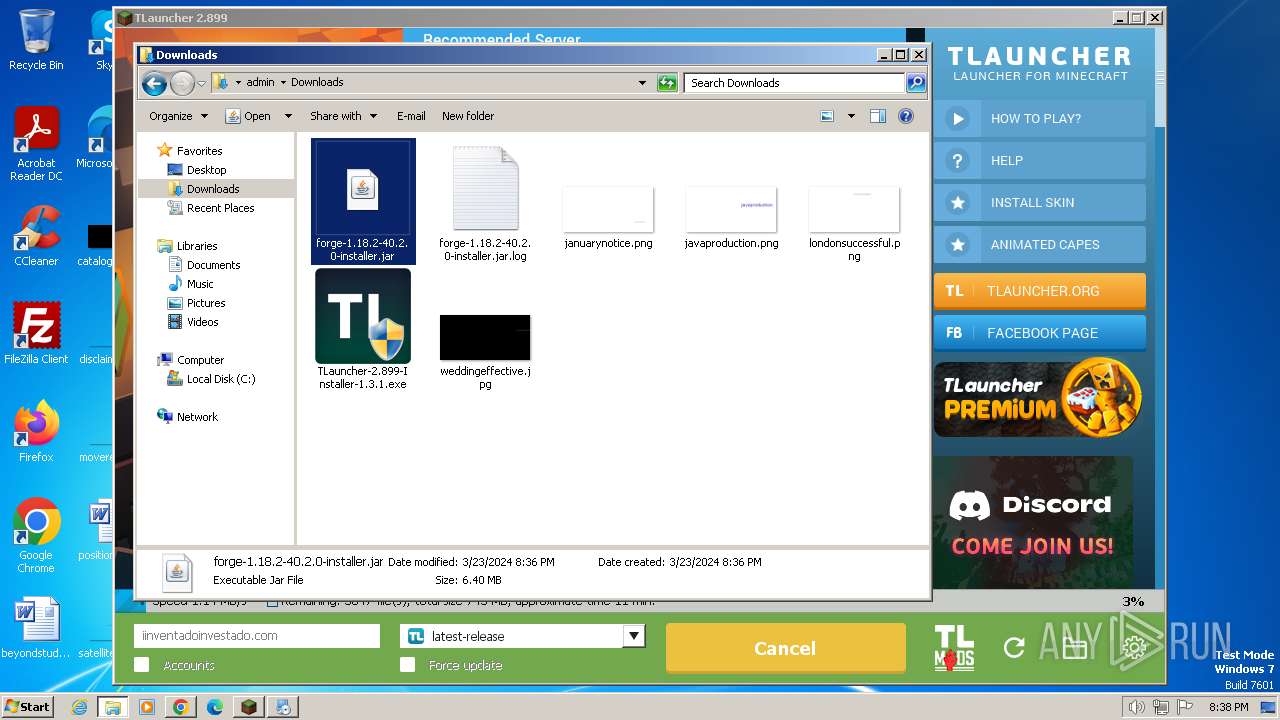
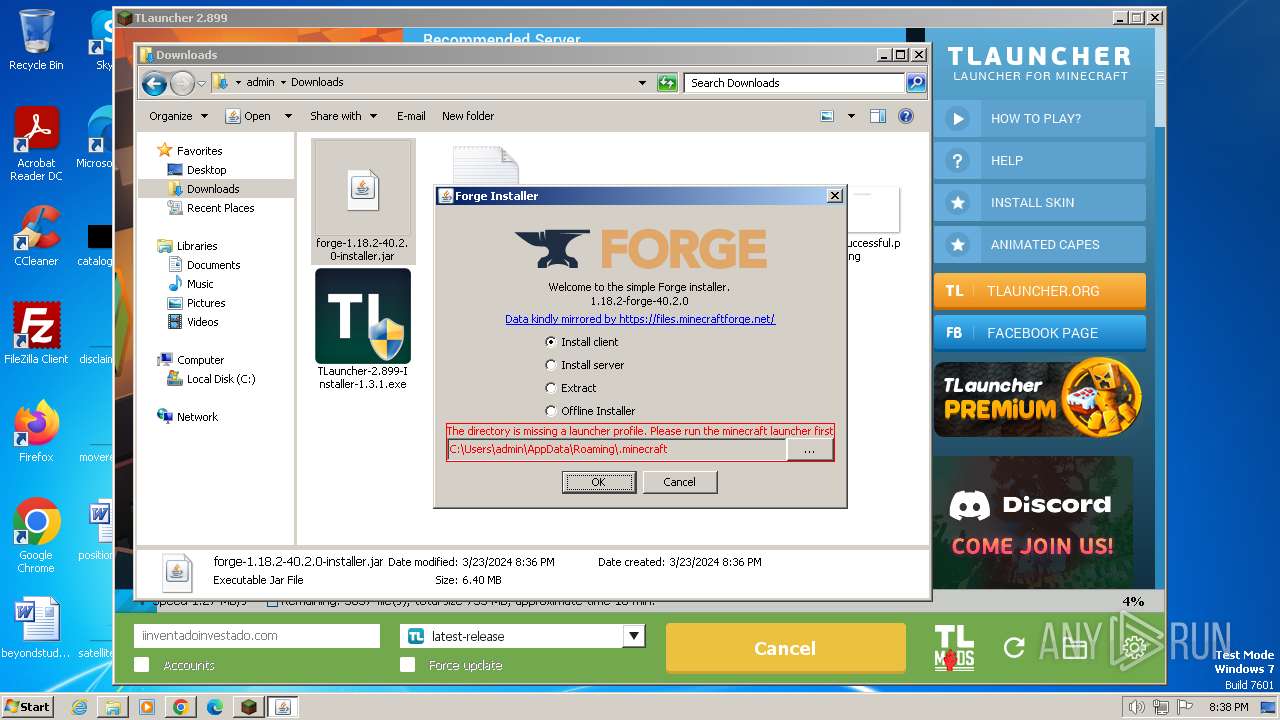
Drops the executable file immediately after the start
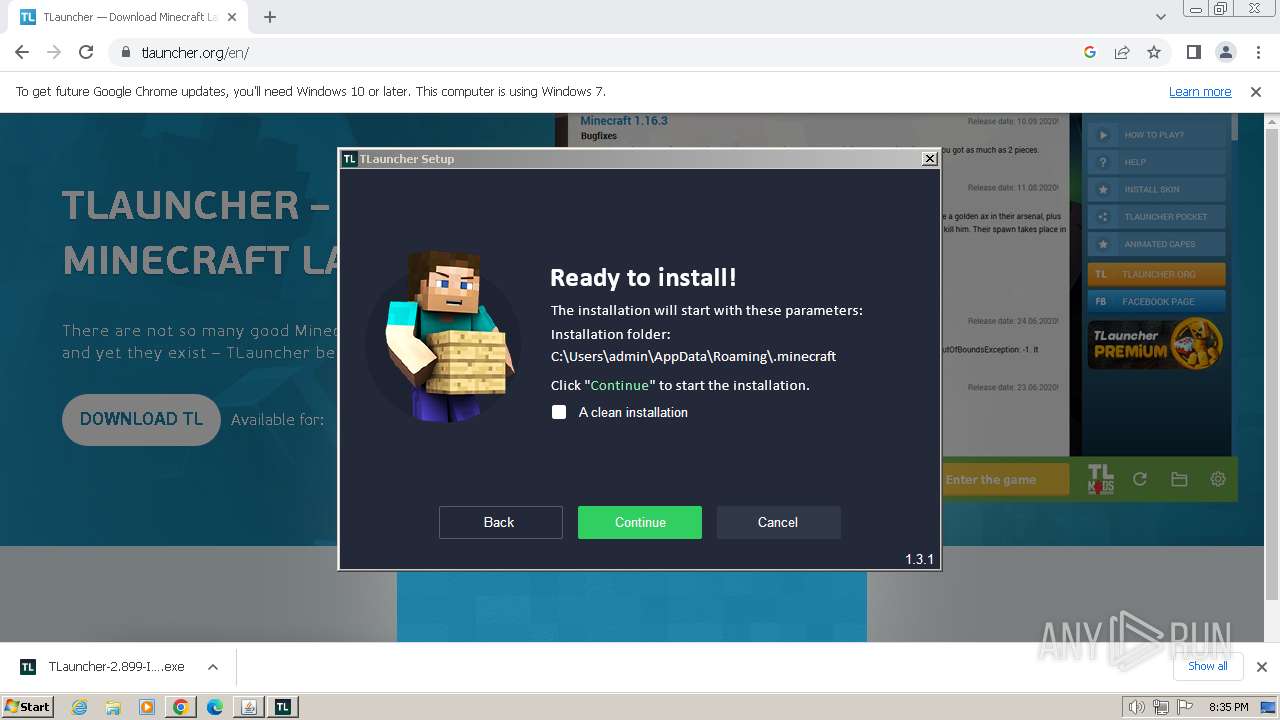
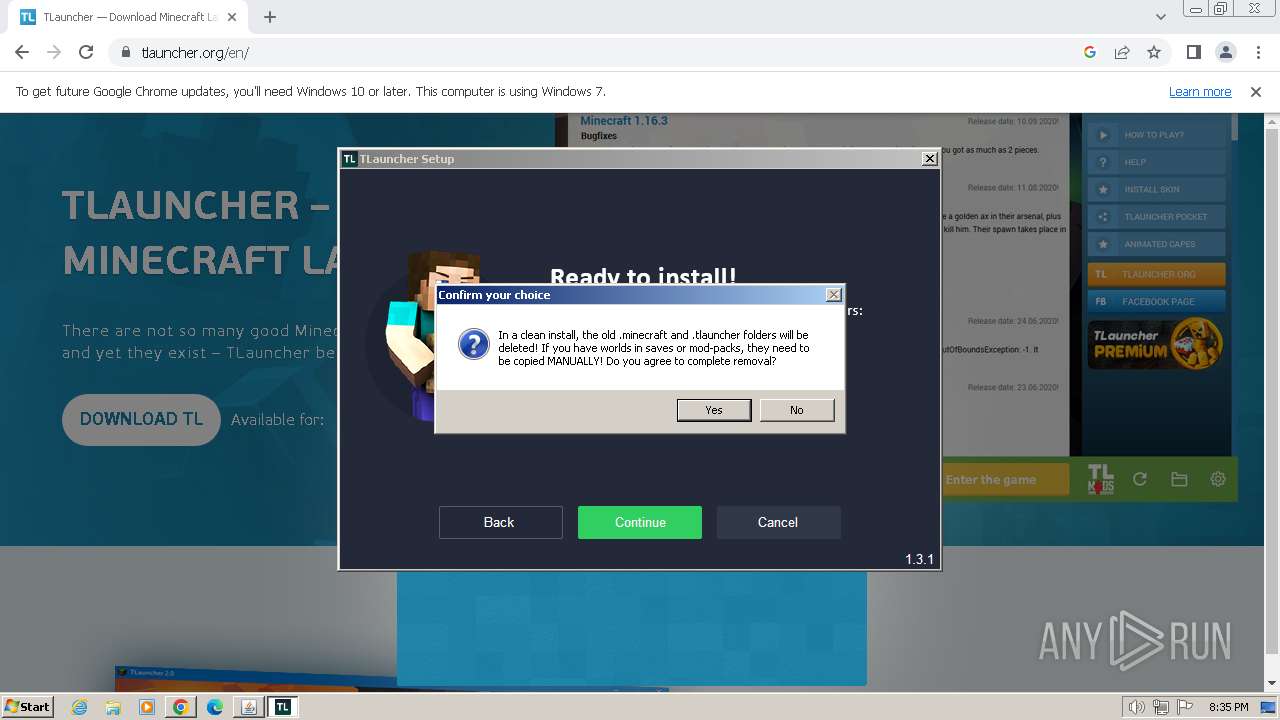
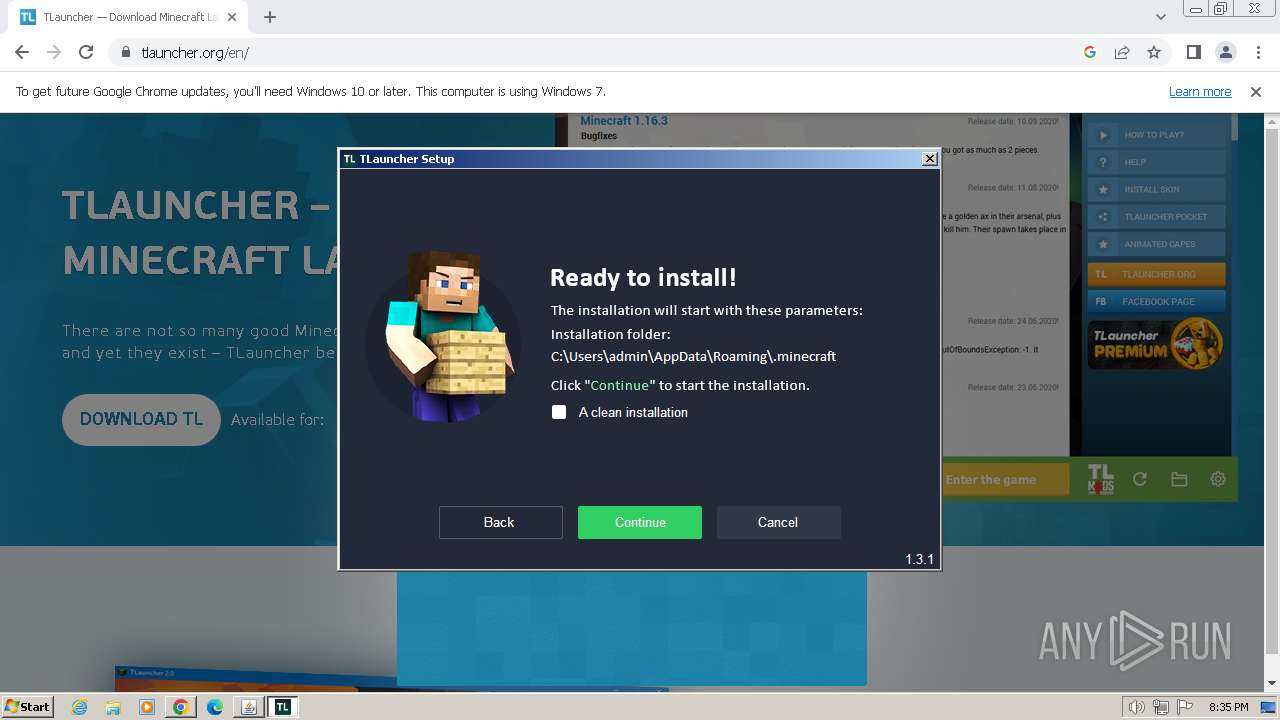
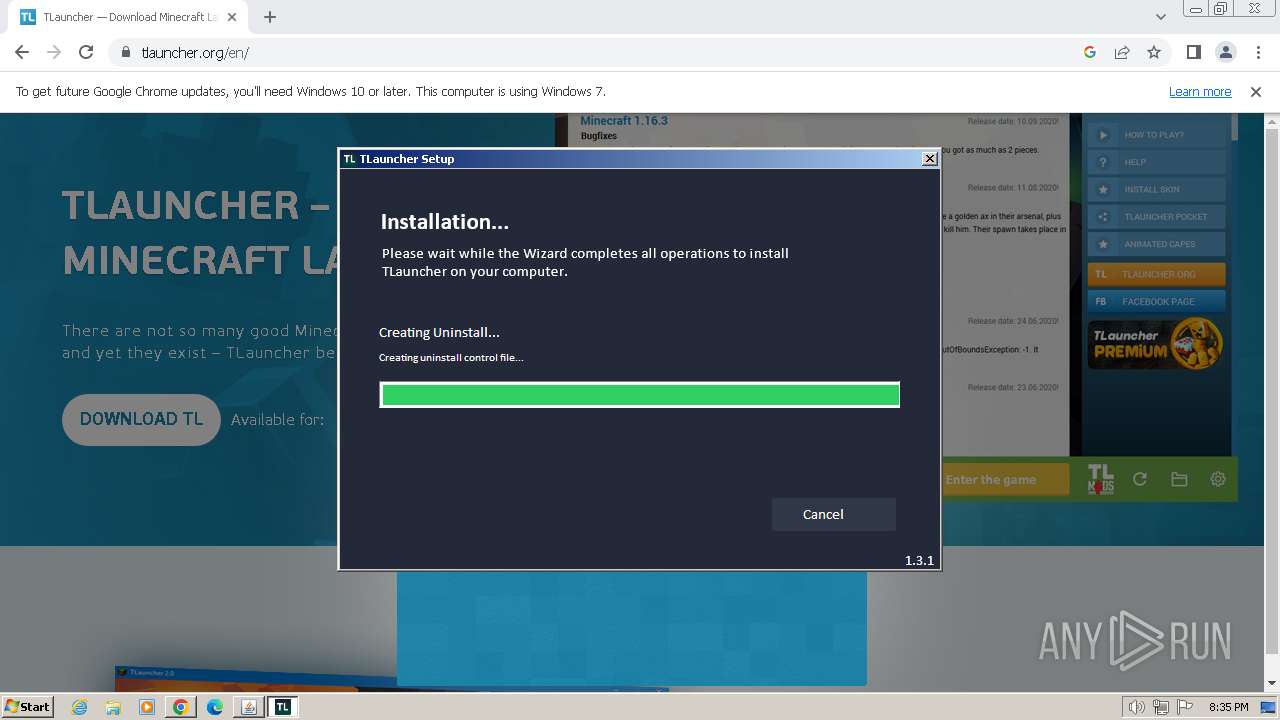
- TLauncher-2.899-Installer-1.3.1.exe (PID: 3652)
- irsetup.exe (PID: 2572)
- BrowserInstaller.exe (PID: 1336)
- javaw.exe (PID: 3096)
- TLauncher-2.899-Installer-1.3.1.exe (PID: 1604)
- irsetup.exe (PID: 3576)
- javaw.exe (PID: 3872)
Actions looks like stealing of personal data
- irsetup.exe (PID: 2572)
- irsetup.exe (PID: 3576)
SUSPICIOUS
Executable content was dropped or overwritten
- TLauncher-2.899-Installer-1.3.1.exe (PID: 3652)
- irsetup.exe (PID: 2572)
- BrowserInstaller.exe (PID: 1336)
- javaw.exe (PID: 3096)
- javaw.exe (PID: 3872)
- TLauncher-2.899-Installer-1.3.1.exe (PID: 1604)
- irsetup.exe (PID: 3576)
Reads security settings of Internet Explorer
- TLauncher-2.899-Installer-1.3.1.exe (PID: 3652)
- irsetup.exe (PID: 2572)
- BrowserInstaller.exe (PID: 1336)
- irsetup.exe (PID: 1864)
- TLauncher-2.899-Installer-1.3.1.exe (PID: 1604)
- irsetup.exe (PID: 3576)
Reads the Internet Settings
- TLauncher-2.899-Installer-1.3.1.exe (PID: 3652)
- irsetup.exe (PID: 2572)
- BrowserInstaller.exe (PID: 1336)
- irsetup.exe (PID: 1864)
- WMIC.exe (PID: 2248)
- WMIC.exe (PID: 3888)
- WMIC.exe (PID: 3112)
- WMIC.exe (PID: 2444)
- TLauncher-2.899-Installer-1.3.1.exe (PID: 1604)
- irsetup.exe (PID: 3576)
Reads settings of System Certificates
- irsetup.exe (PID: 2572)
- irsetup.exe (PID: 1864)
- dxdiag.exe (PID: 1056)
- irsetup.exe (PID: 3576)
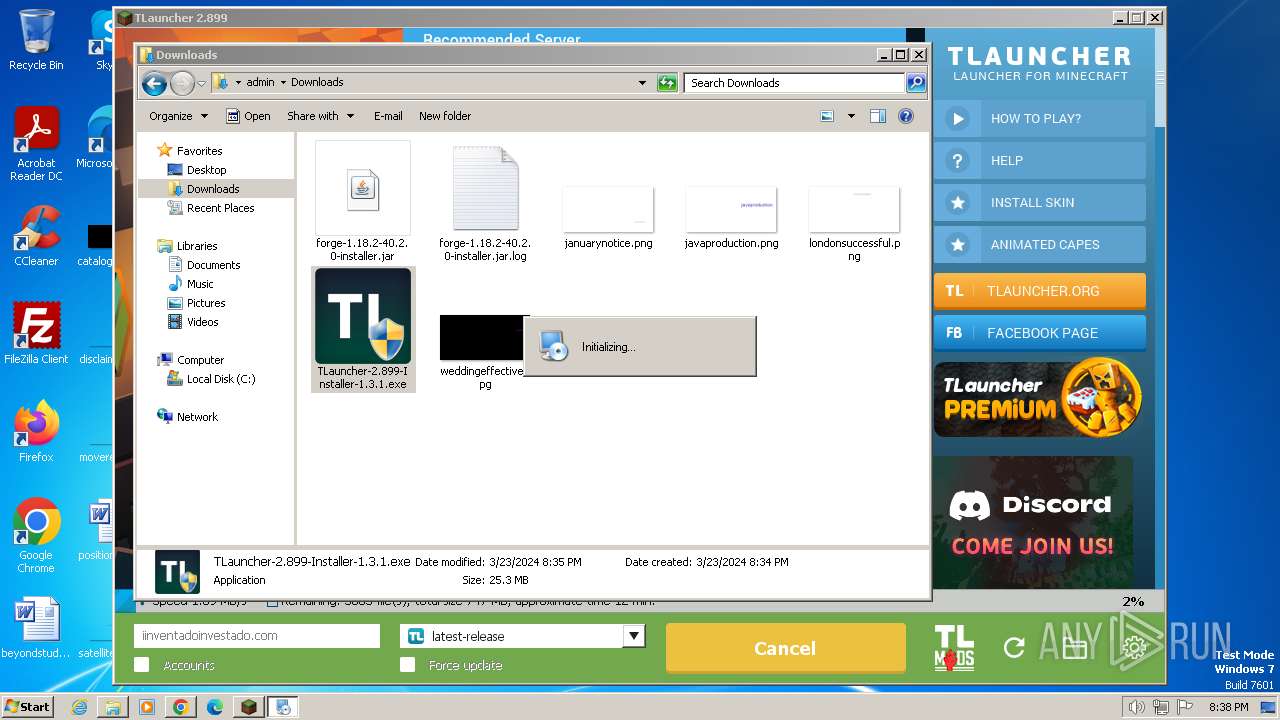
Checks for Java to be installed
- irsetup.exe (PID: 2572)
- TLauncher.exe (PID: 3468)
- irsetup.exe (PID: 3576)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 2572)
- irsetup.exe (PID: 1864)
- irsetup.exe (PID: 3576)
Adds/modifies Windows certificates
- irsetup.exe (PID: 2572)
Checks Windows Trust Settings
- irsetup.exe (PID: 2572)
- irsetup.exe (PID: 1864)
- irsetup.exe (PID: 3576)
Reads Microsoft Outlook installation path
- irsetup.exe (PID: 2572)
- irsetup.exe (PID: 3576)
Creates a software uninstall entry
- irsetup.exe (PID: 2572)
Reads Internet Explorer settings
- irsetup.exe (PID: 2572)
- irsetup.exe (PID: 3576)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 3096)
- javaw.exe (PID: 3872)
Starts application with an unusual extension
- cmd.exe (PID: 3812)
- cmd.exe (PID: 2996)
- cmd.exe (PID: 2020)
- cmd.exe (PID: 3776)
- cmd.exe (PID: 3936)
- cmd.exe (PID: 2752)
- cmd.exe (PID: 2652)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 3812)
- cmd.exe (PID: 2996)
Process drops legitimate windows executable
- javaw.exe (PID: 3096)
- javaw.exe (PID: 3872)
The process drops C-runtime libraries
- javaw.exe (PID: 3096)
- javaw.exe (PID: 3872)
Uses ICACLS.EXE to modify access control lists
- javaw.exe (PID: 3872)
Process requests binary or script from the Internet
- javaw.exe (PID: 3872)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 3776)
Uses WMIC.EXE to obtain quick Fix Engineering (patches) data
- cmd.exe (PID: 2652)
The process creates files with name similar to system file names
- javaw.exe (PID: 3872)
INFO
Checks supported languages
- javaw.exe (PID: 2120)
- TLauncher-2.899-Installer-1.3.1.exe (PID: 3652)
- irsetup.exe (PID: 2572)
- BrowserInstaller.exe (PID: 1336)
- irsetup.exe (PID: 1864)
- javaw.exe (PID: 3836)
- javaw.exe (PID: 3096)
- chcp.com (PID: 2124)
- chcp.com (PID: 2204)
- TLauncher.exe (PID: 3468)
- javaw.exe (PID: 3872)
- chcp.com (PID: 3016)
- chcp.com (PID: 3044)
- chcp.com (PID: 3032)
- chcp.com (PID: 2896)
- TLauncher-2.899-Installer-1.3.1.exe (PID: 1604)
- chcp.com (PID: 1780)
- irsetup.exe (PID: 3576)
- javaw.exe (PID: 2020)
Reads the computer name
- javaw.exe (PID: 2120)
- TLauncher-2.899-Installer-1.3.1.exe (PID: 3652)
- irsetup.exe (PID: 2572)
- BrowserInstaller.exe (PID: 1336)
- irsetup.exe (PID: 1864)
- javaw.exe (PID: 3836)
- javaw.exe (PID: 3096)
- javaw.exe (PID: 3872)
- TLauncher-2.899-Installer-1.3.1.exe (PID: 1604)
- irsetup.exe (PID: 3576)
- javaw.exe (PID: 2020)
Create files in a temporary directory
- javaw.exe (PID: 2120)
- TLauncher-2.899-Installer-1.3.1.exe (PID: 3652)
- irsetup.exe (PID: 2572)
- BrowserInstaller.exe (PID: 1336)
- irsetup.exe (PID: 1864)
- javaw.exe (PID: 3836)
- javaw.exe (PID: 3096)
- javaw.exe (PID: 3872)
- TLauncher-2.899-Installer-1.3.1.exe (PID: 1604)
- javaw.exe (PID: 2020)
- irsetup.exe (PID: 3576)
Reads the machine GUID from the registry
- javaw.exe (PID: 2120)
- irsetup.exe (PID: 2572)
- irsetup.exe (PID: 1864)
- javaw.exe (PID: 3096)
- javaw.exe (PID: 3836)
- javaw.exe (PID: 3872)
- javaw.exe (PID: 2020)
- irsetup.exe (PID: 3576)
Creates files in the program directory
- javaw.exe (PID: 2120)
- irsetup.exe (PID: 2572)
- javaw.exe (PID: 3872)
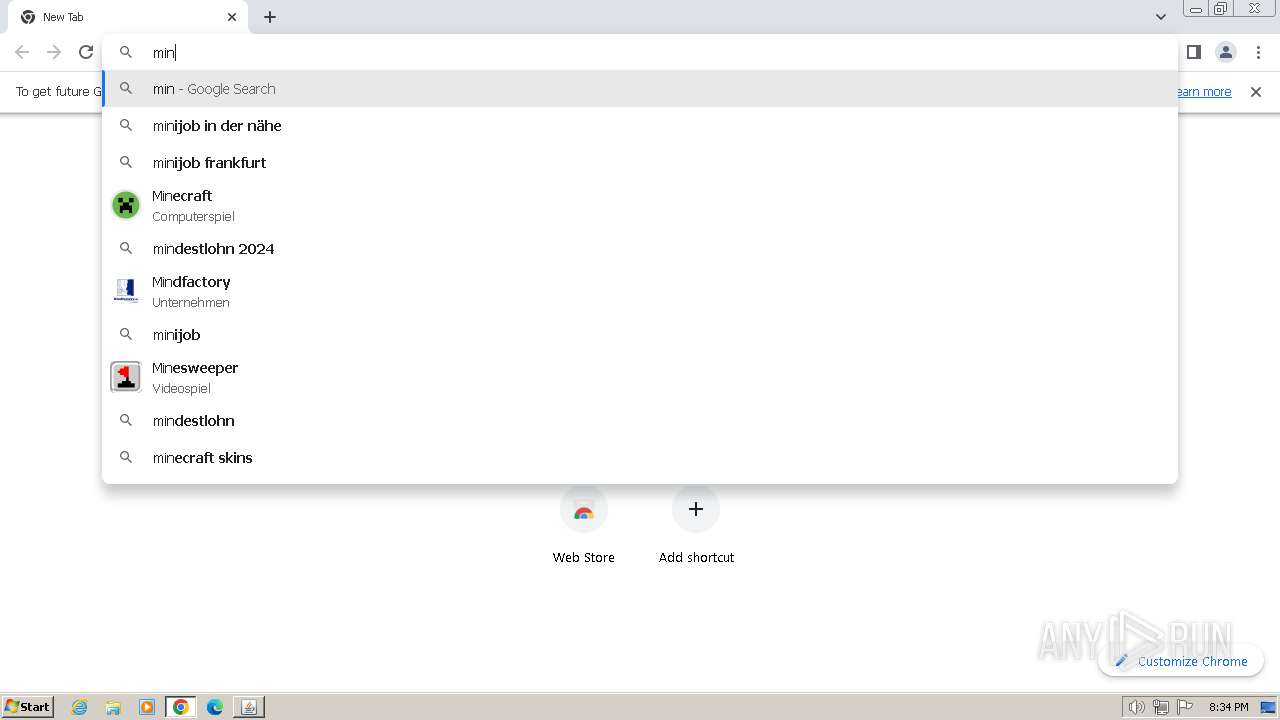
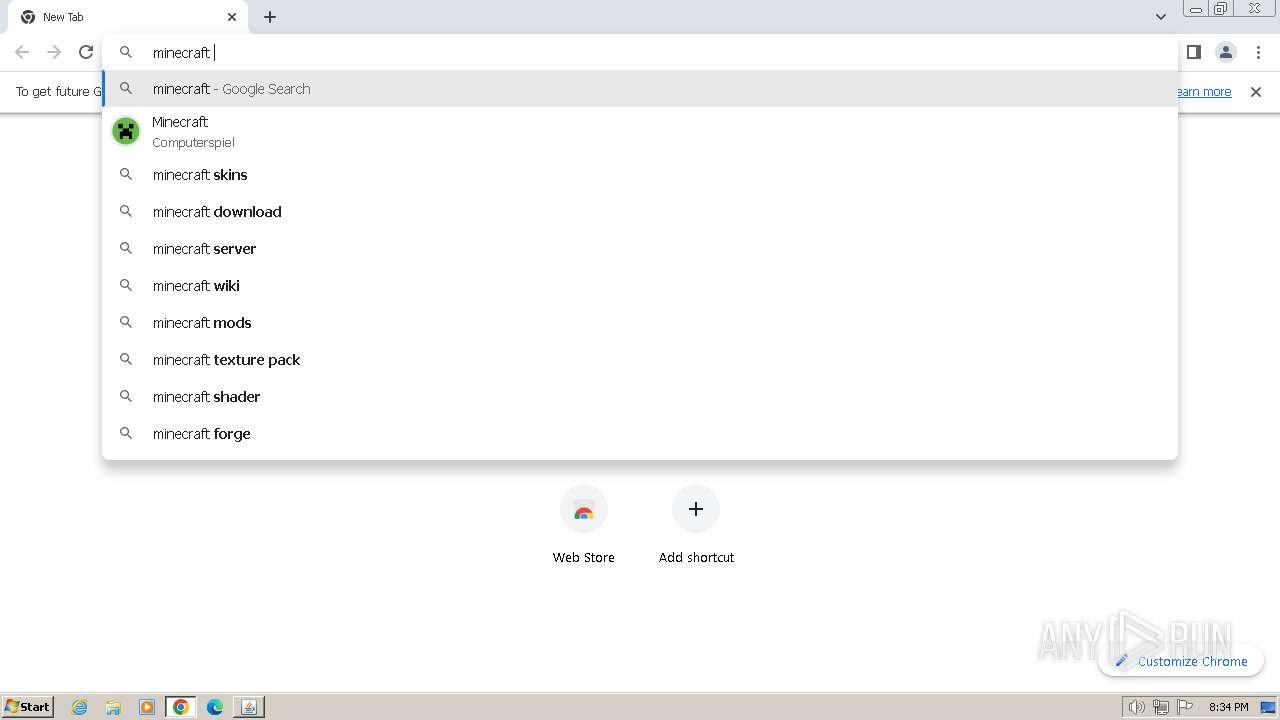
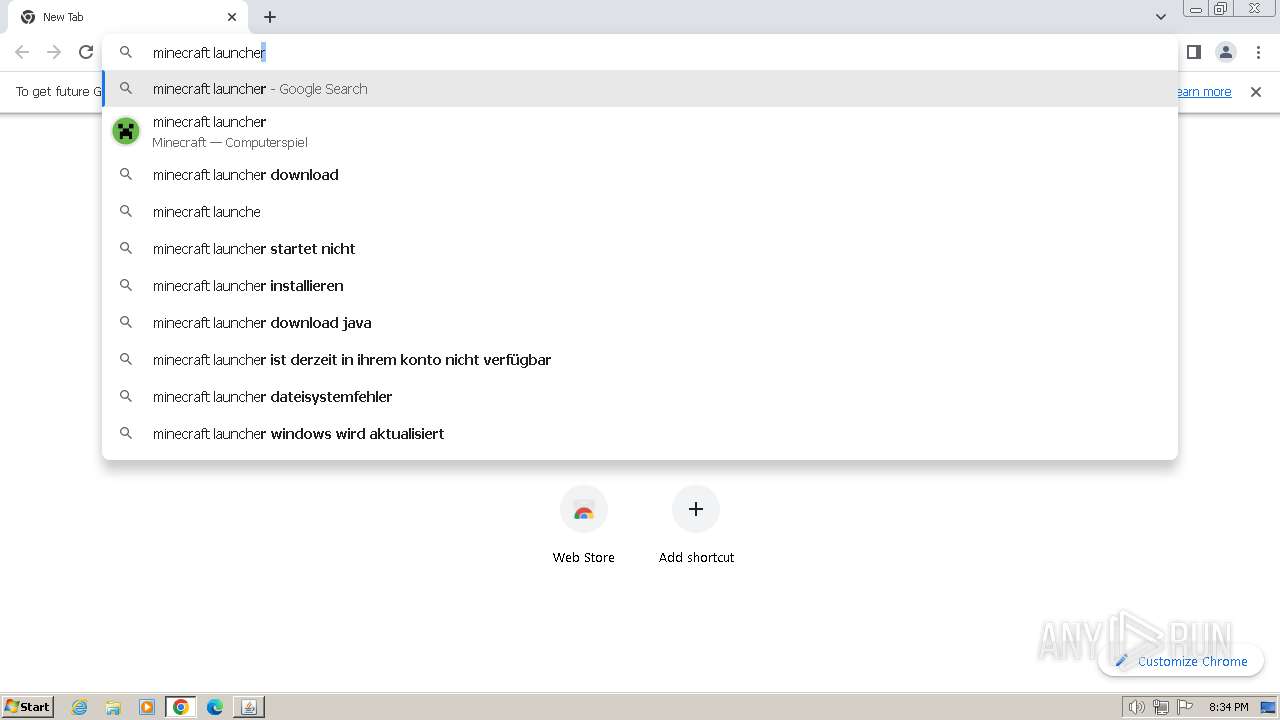
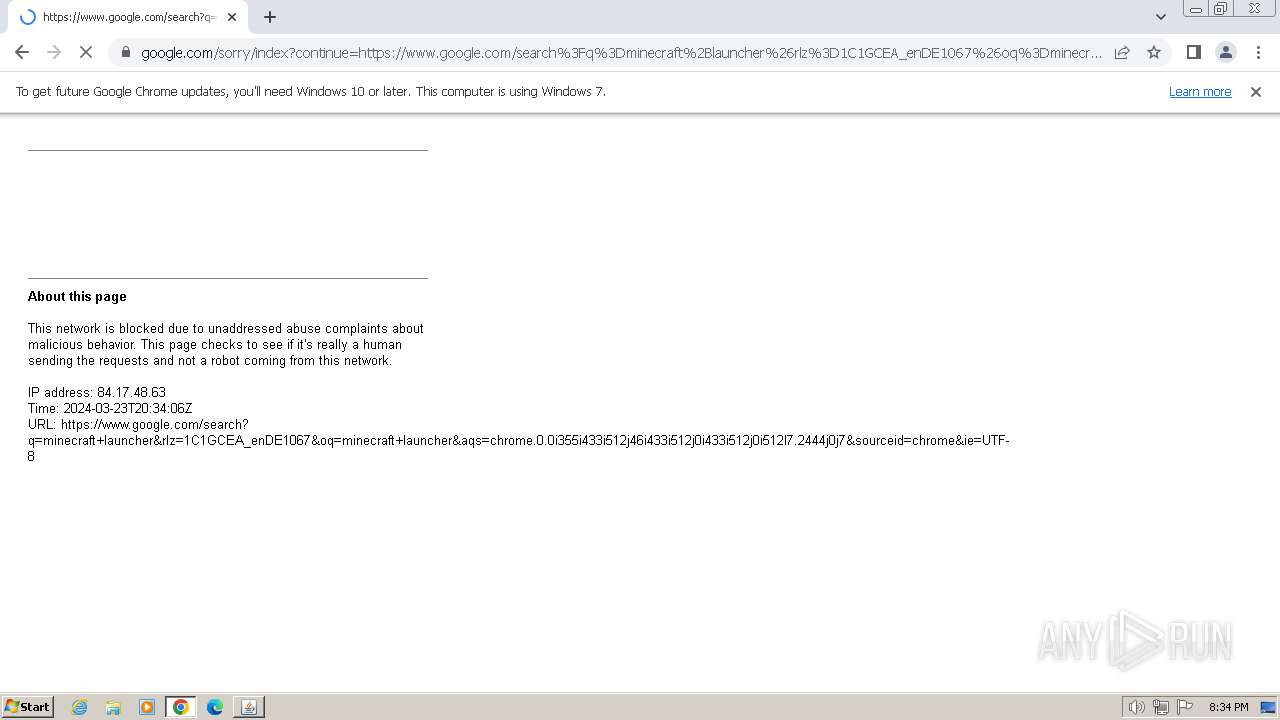
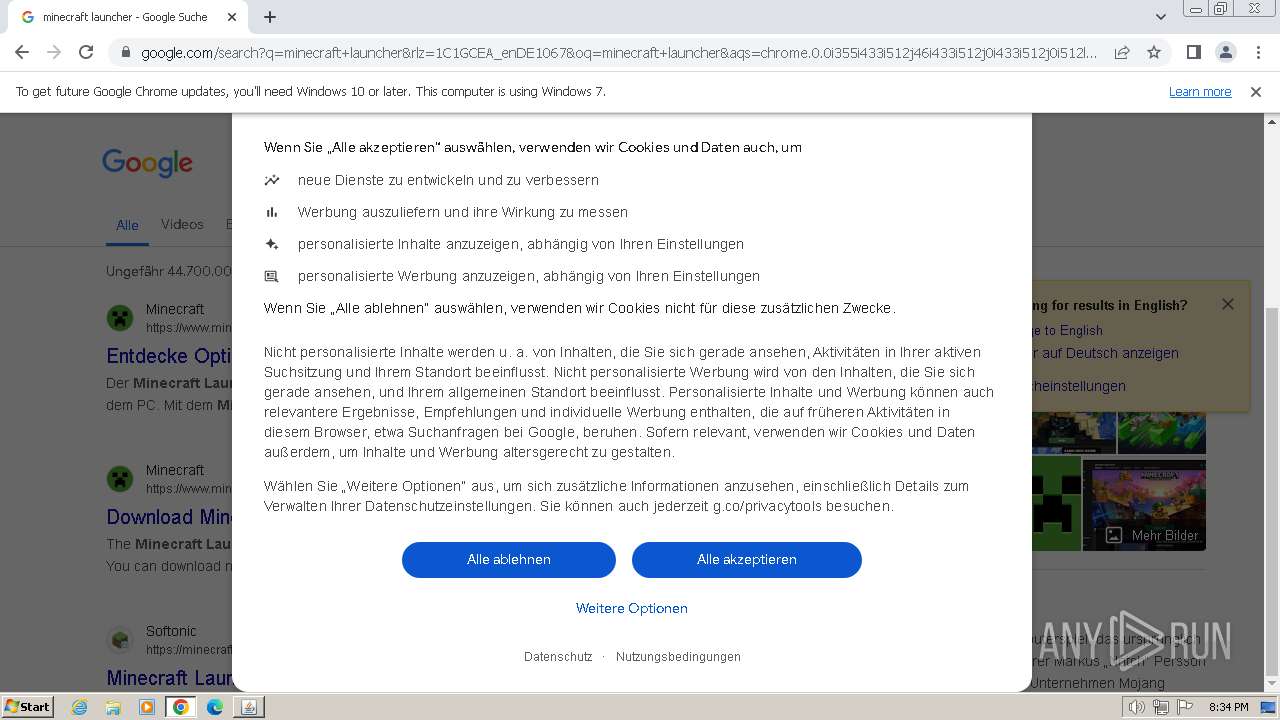
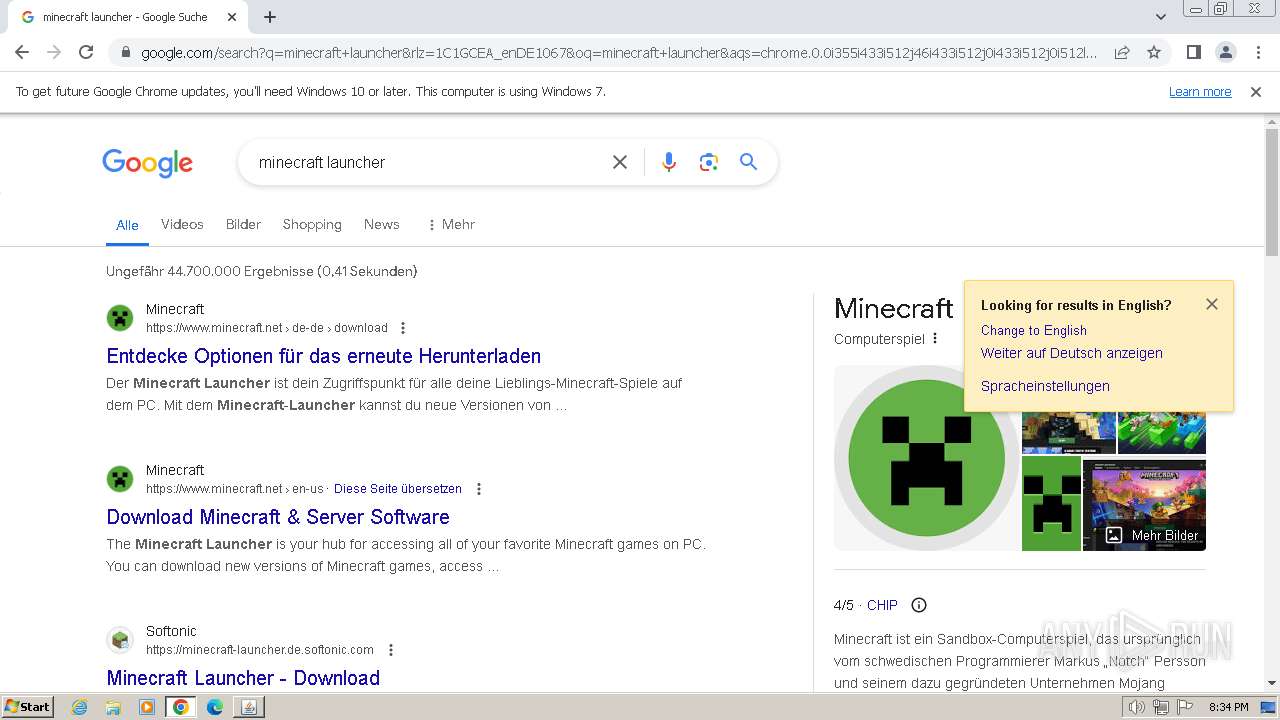
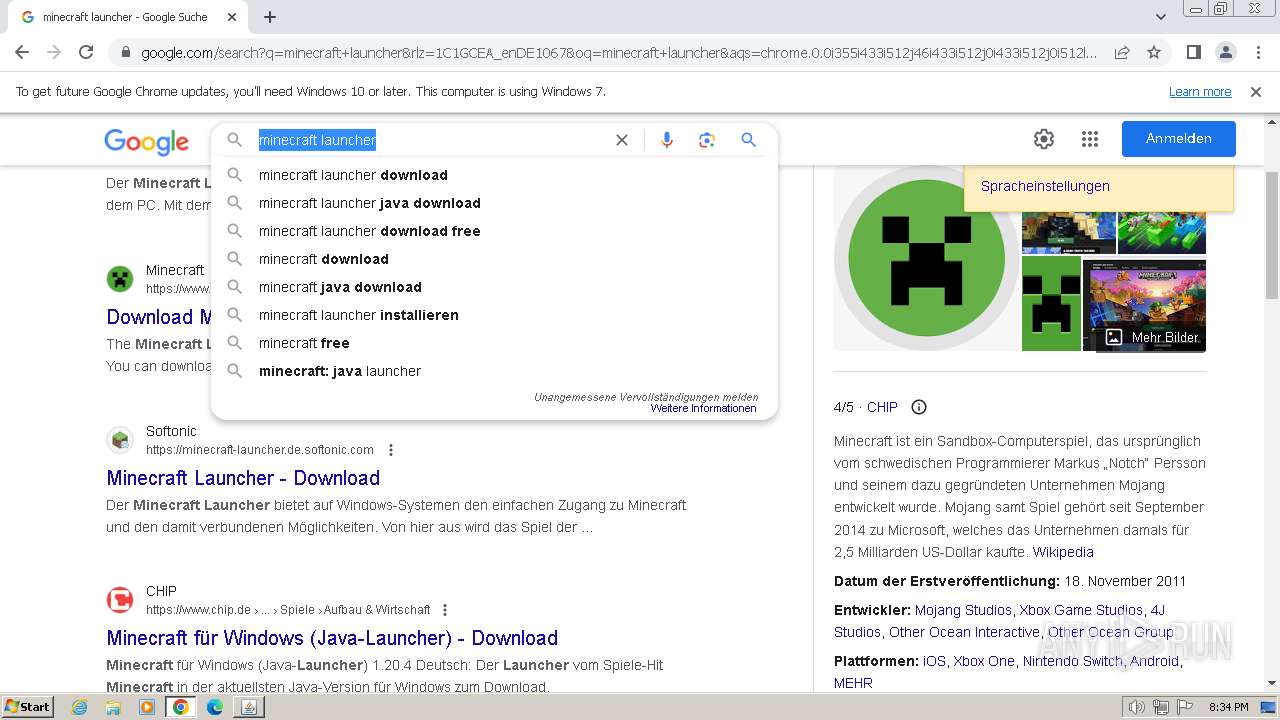
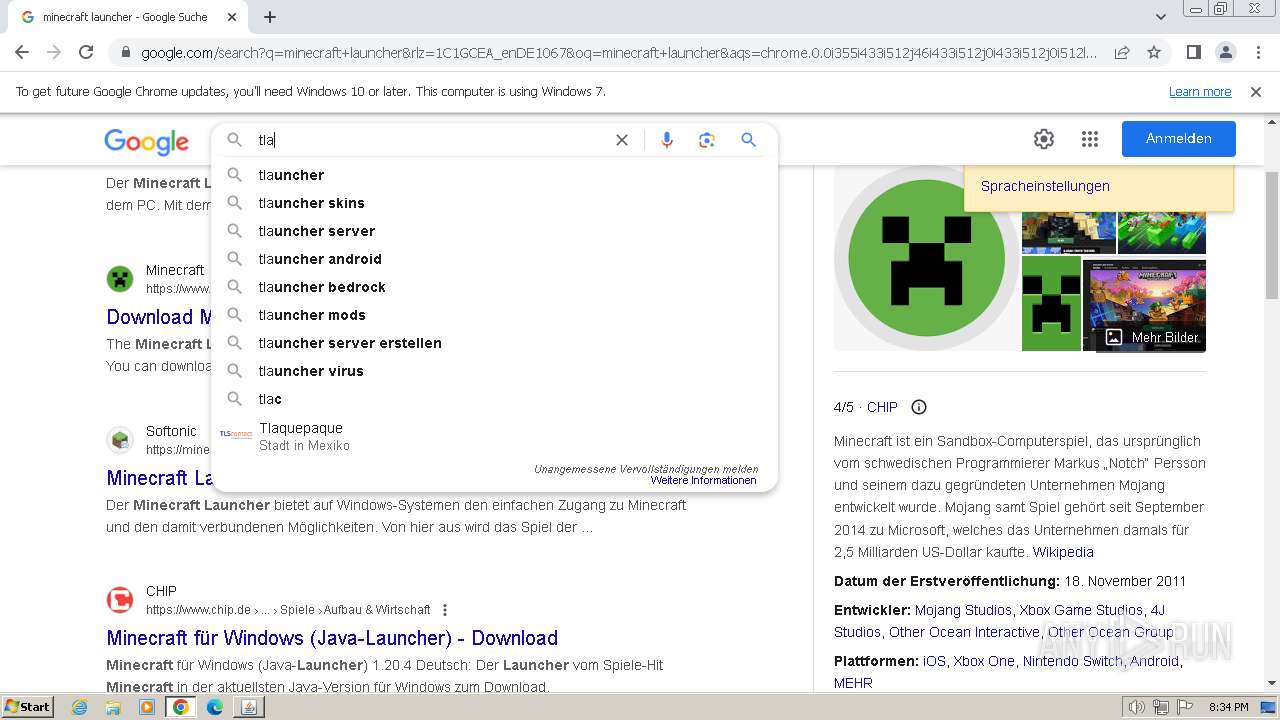
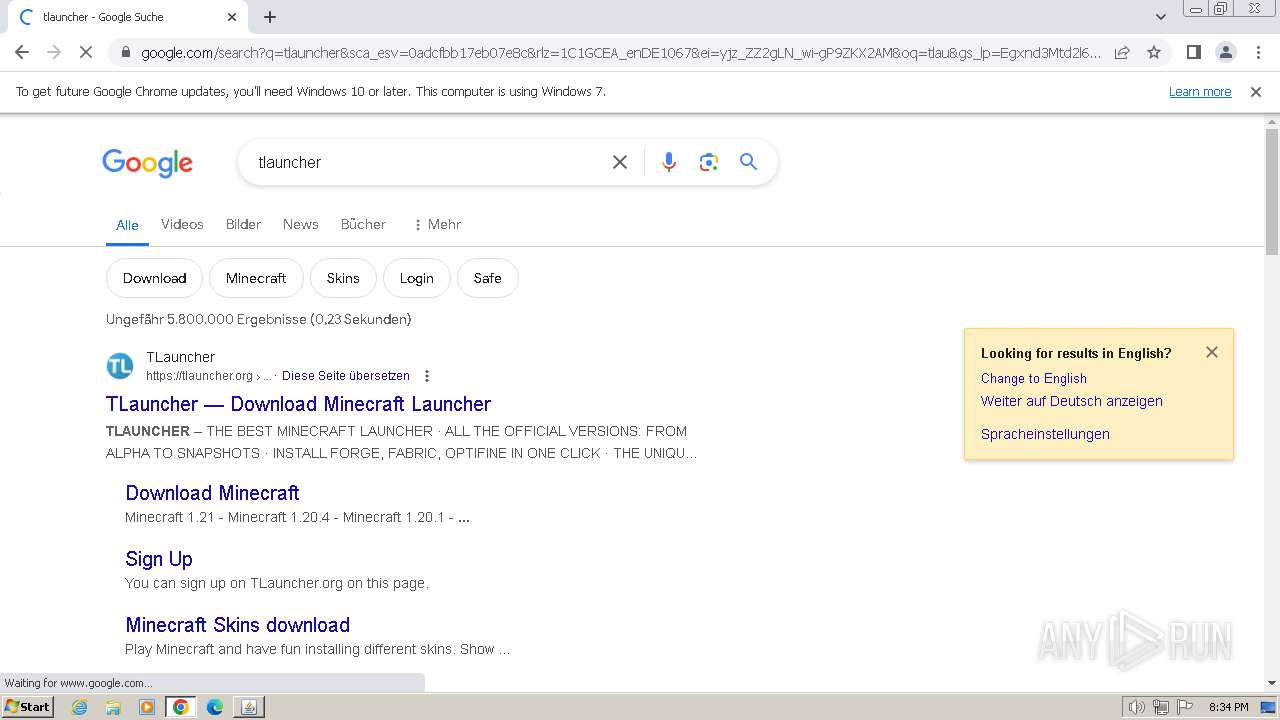
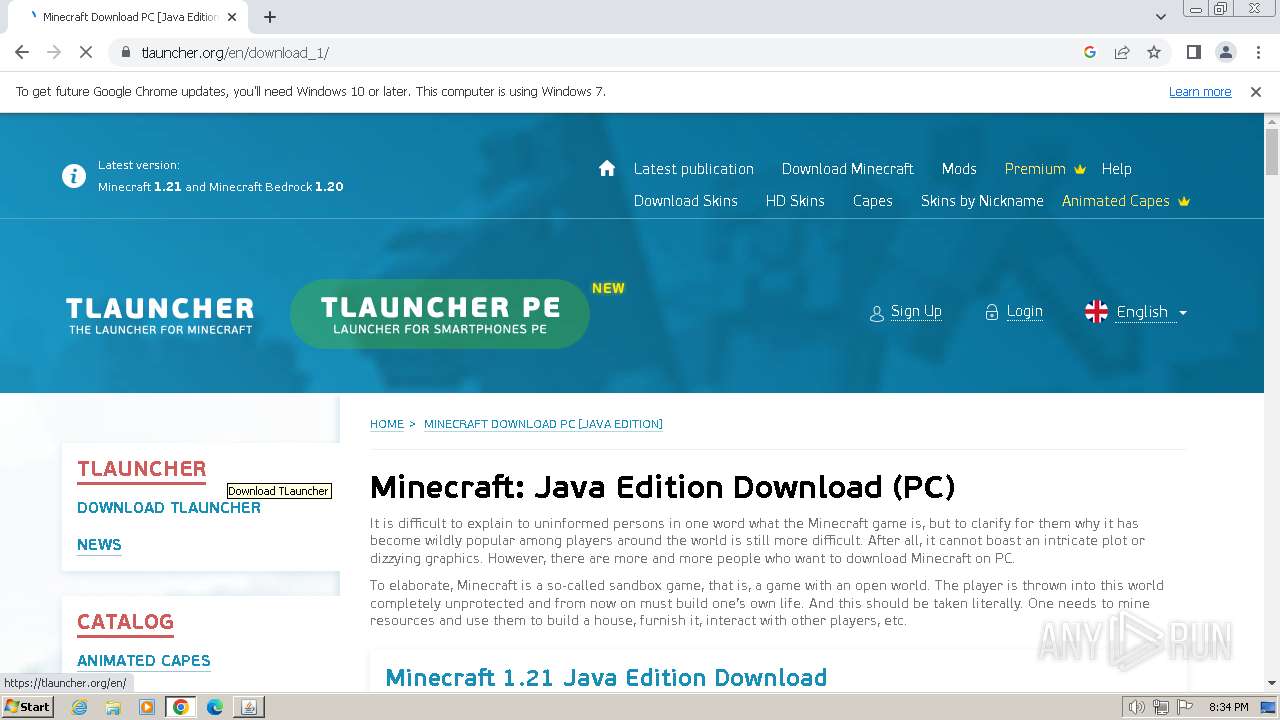
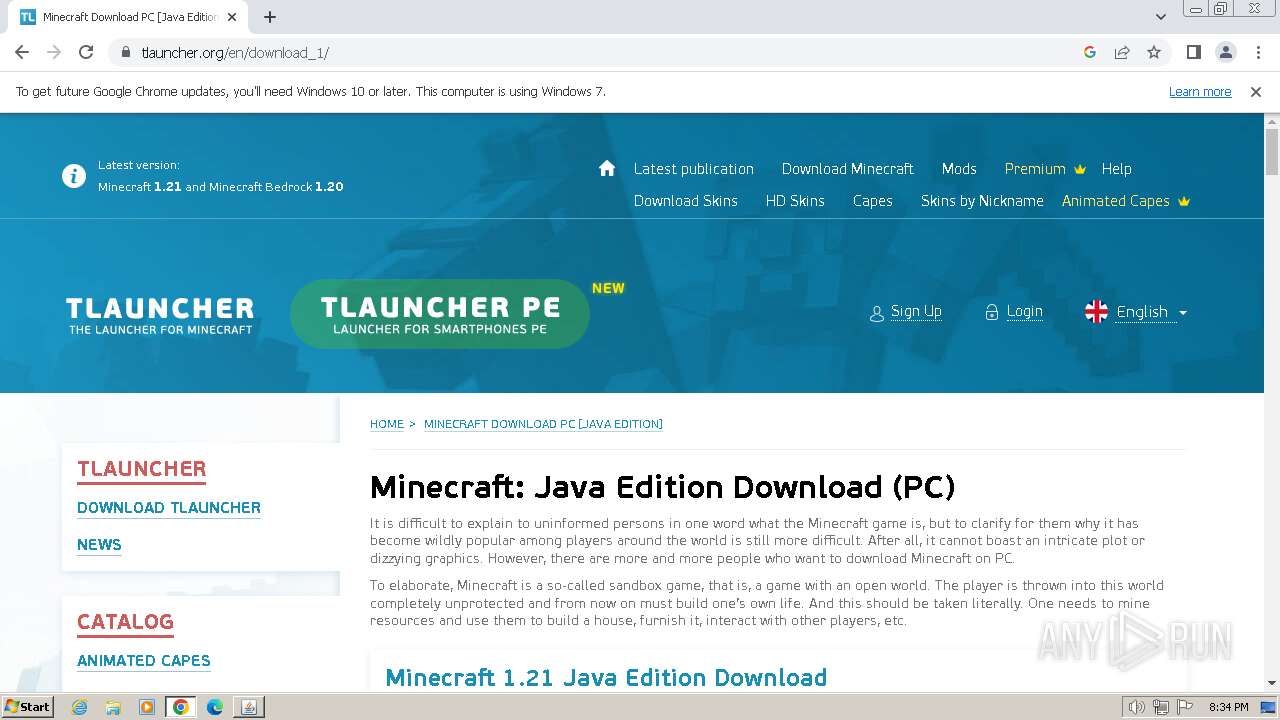
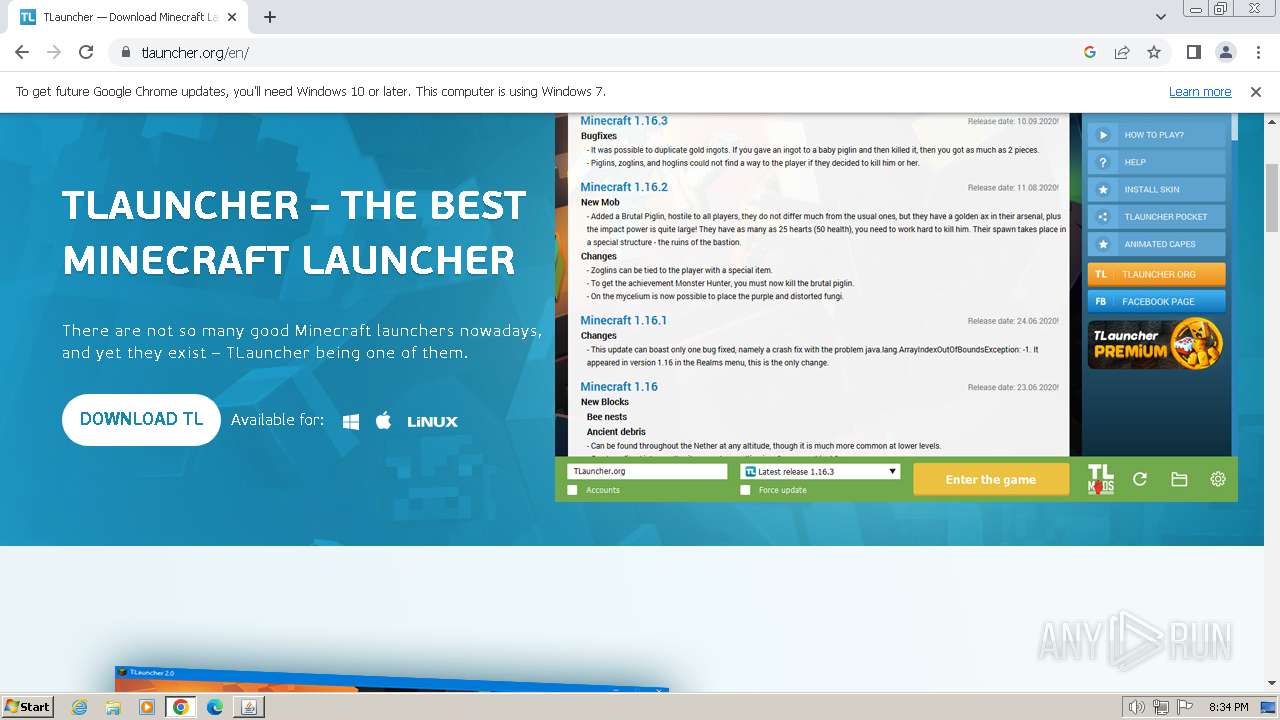
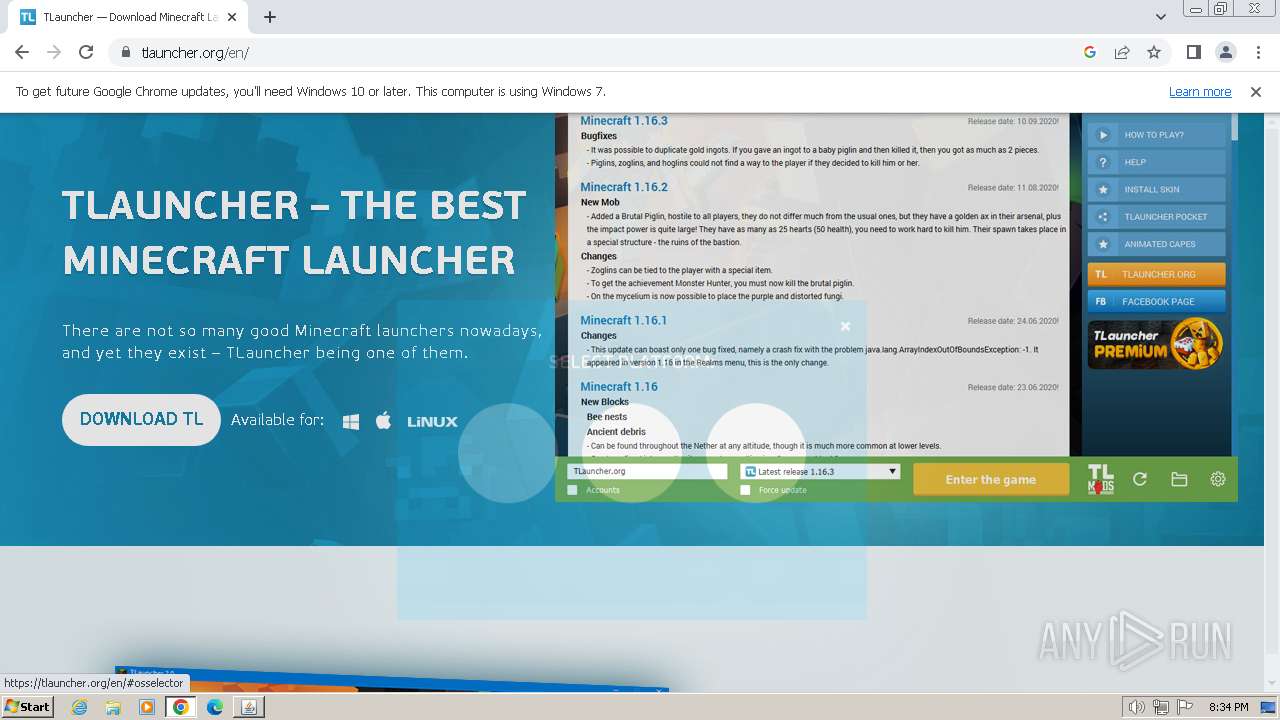
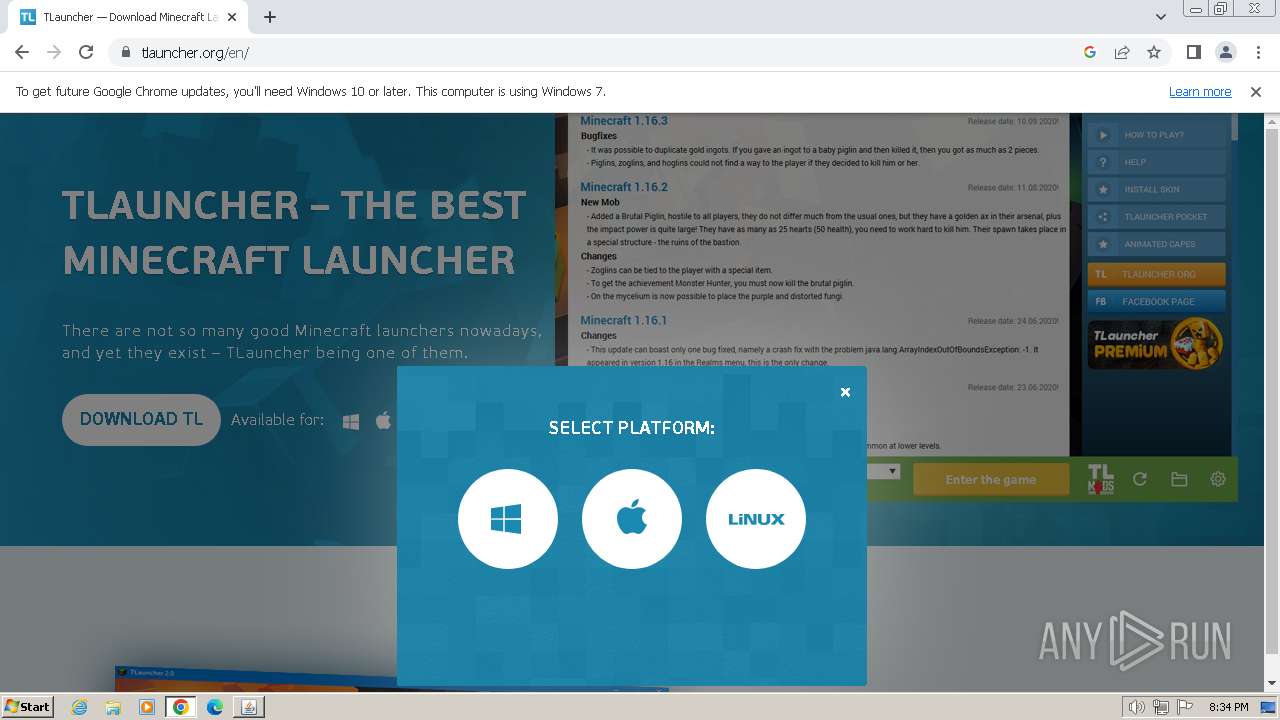
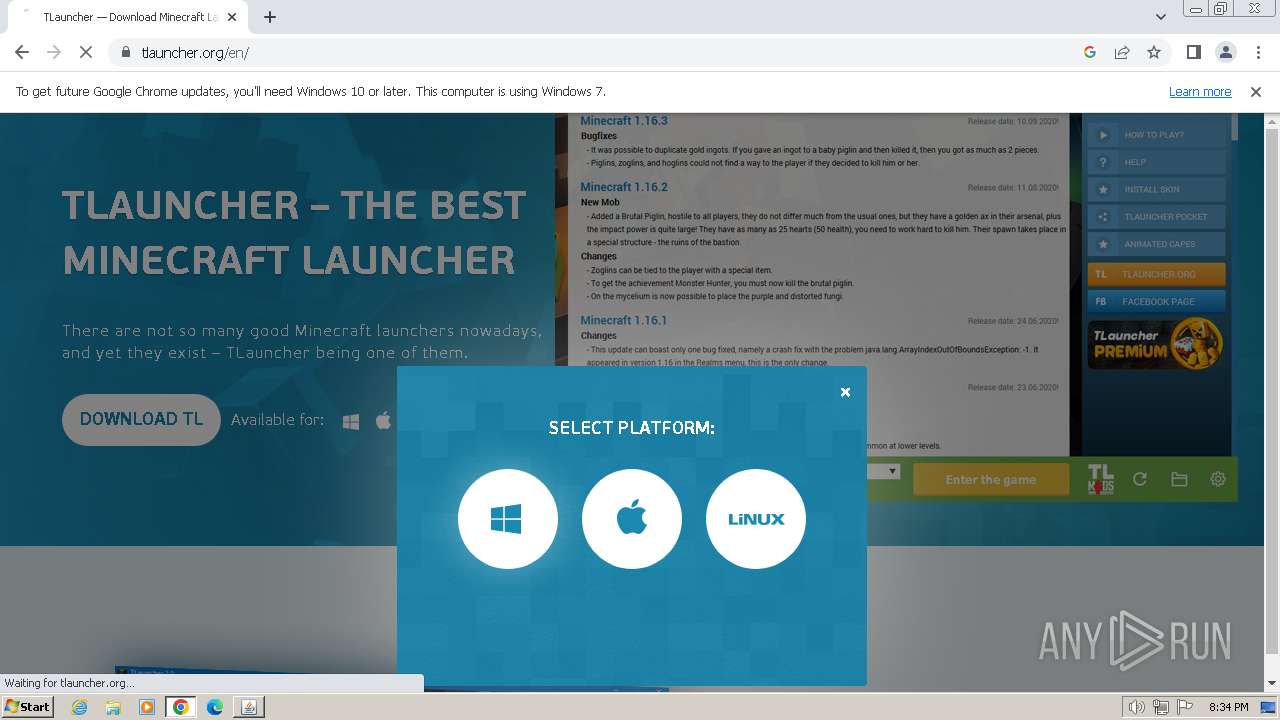
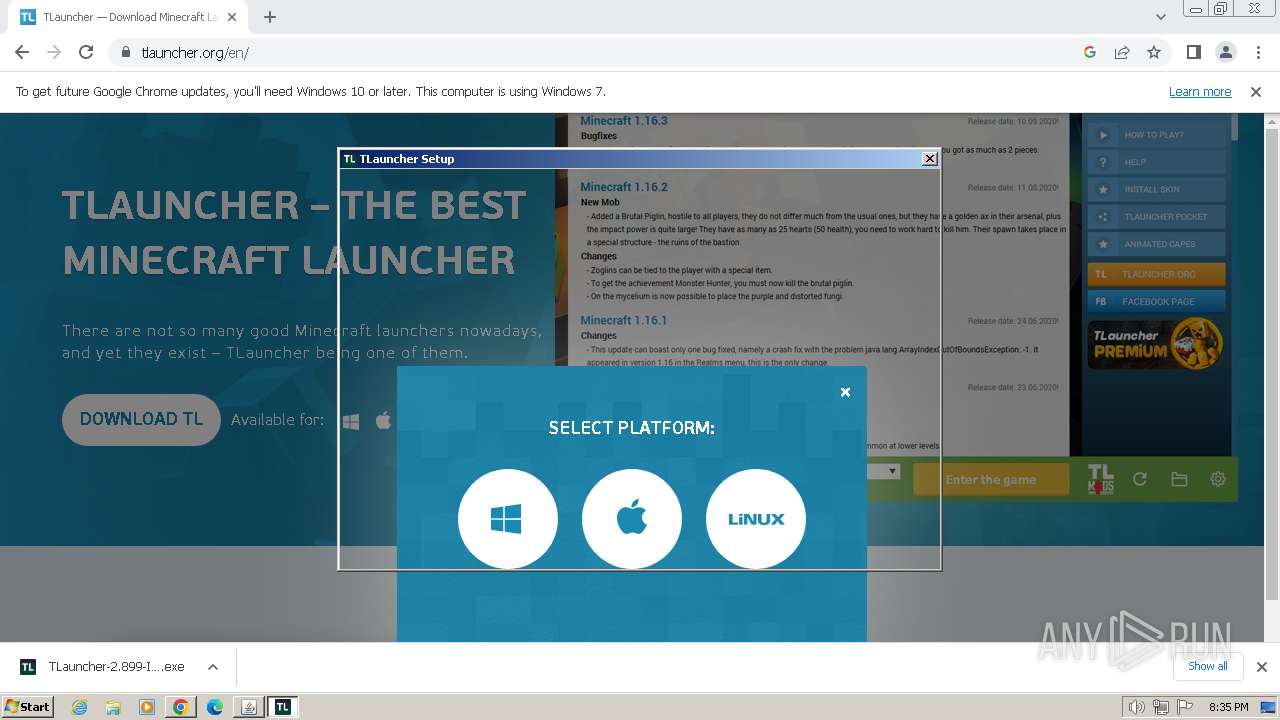
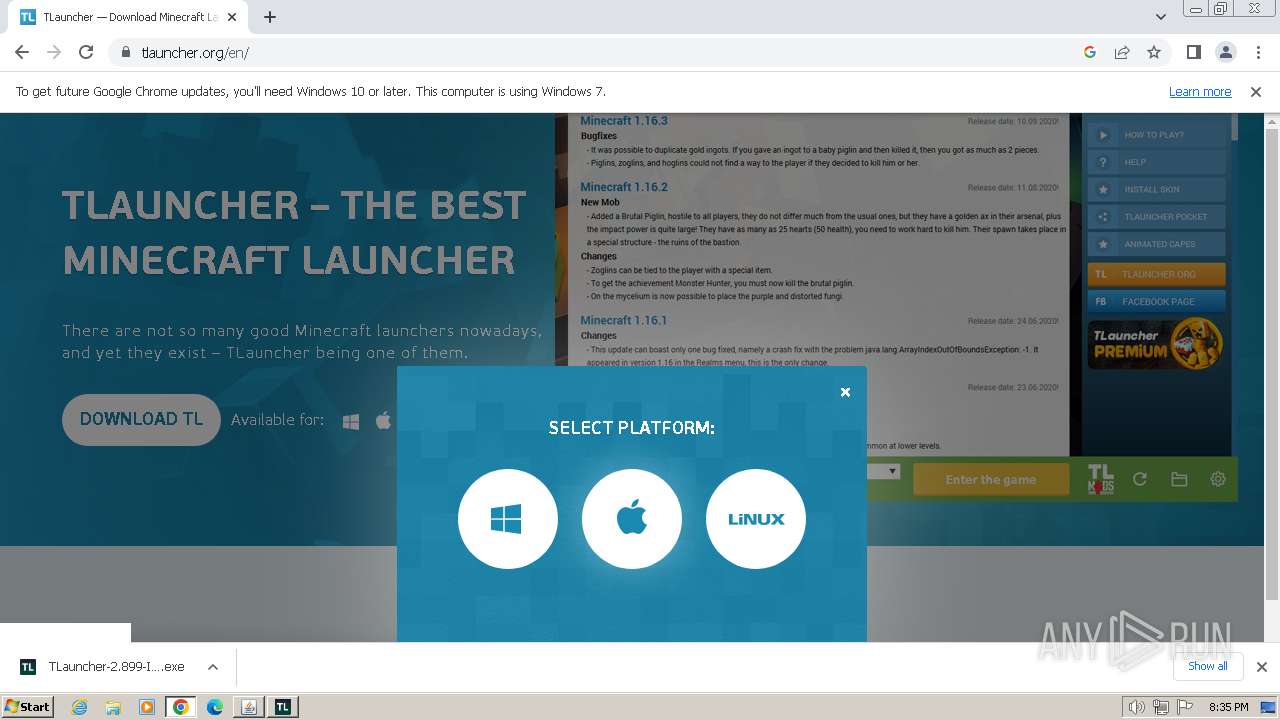
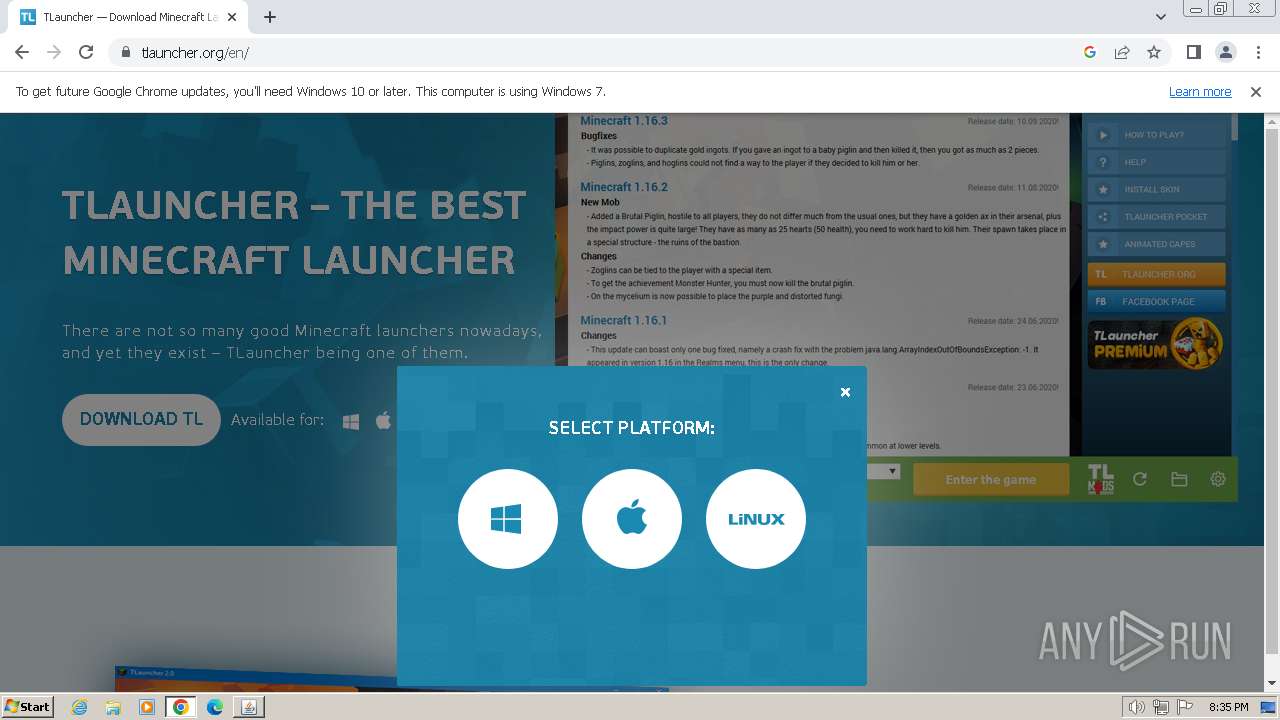
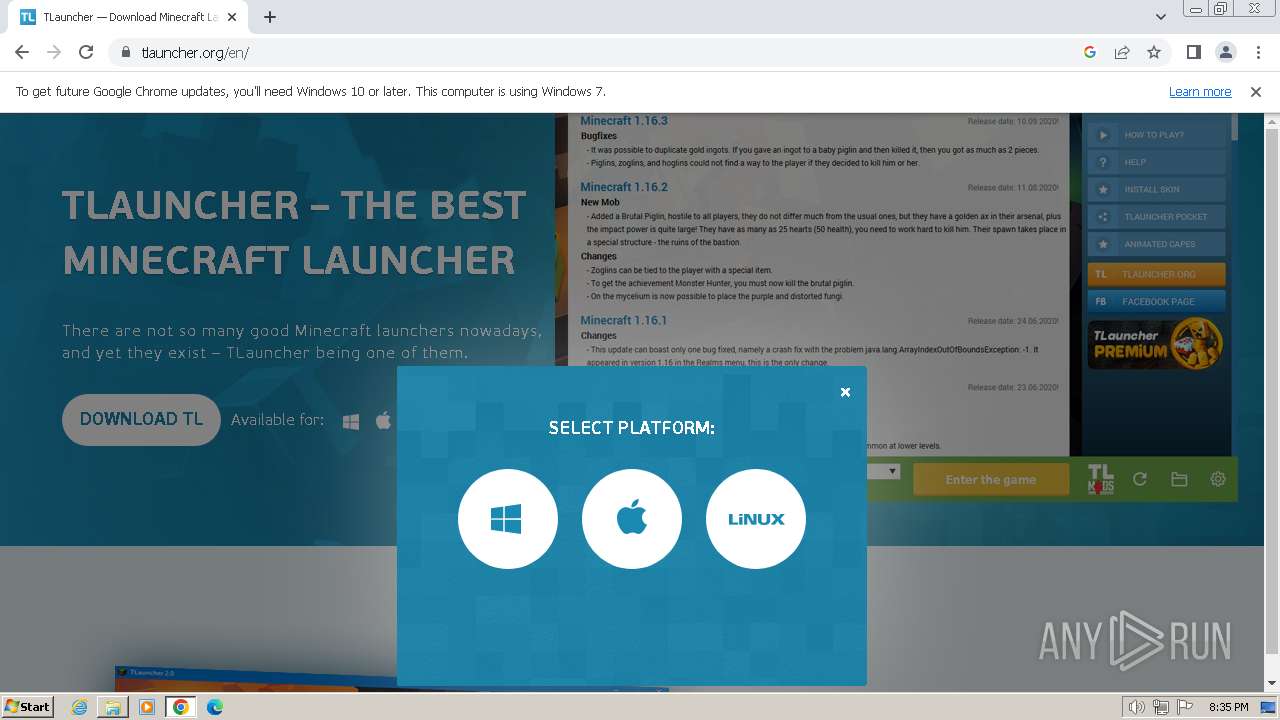
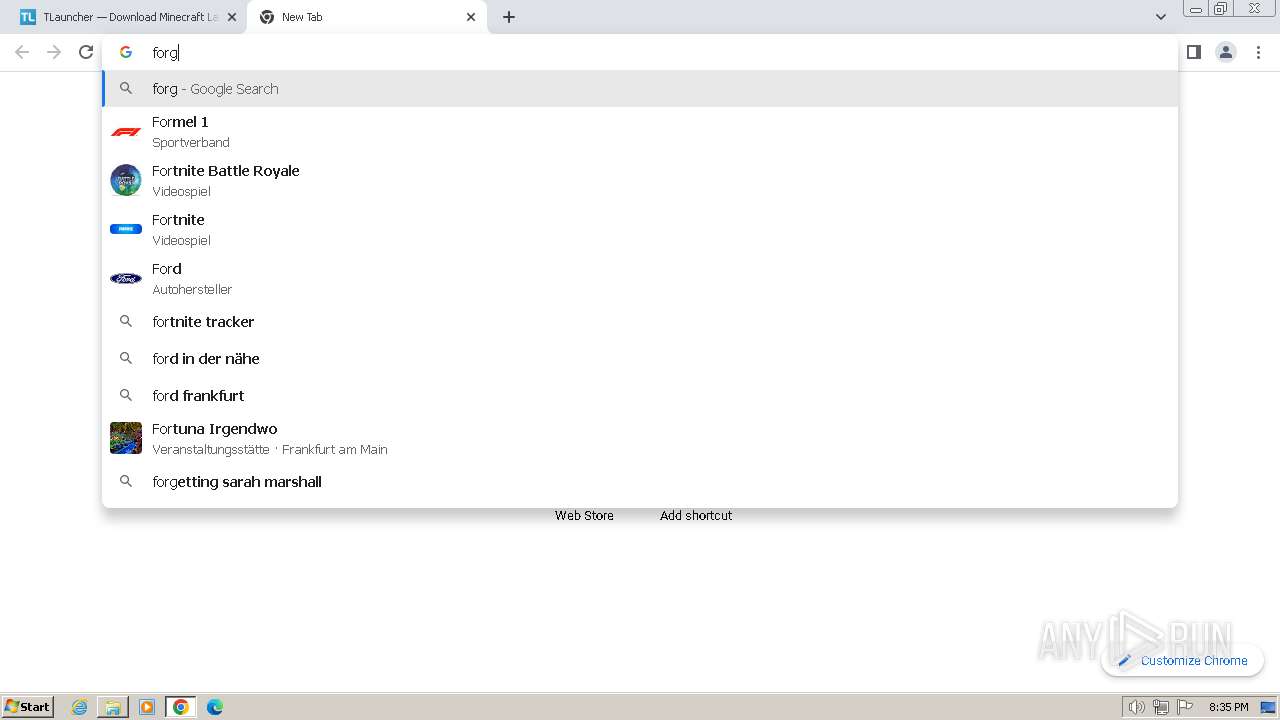
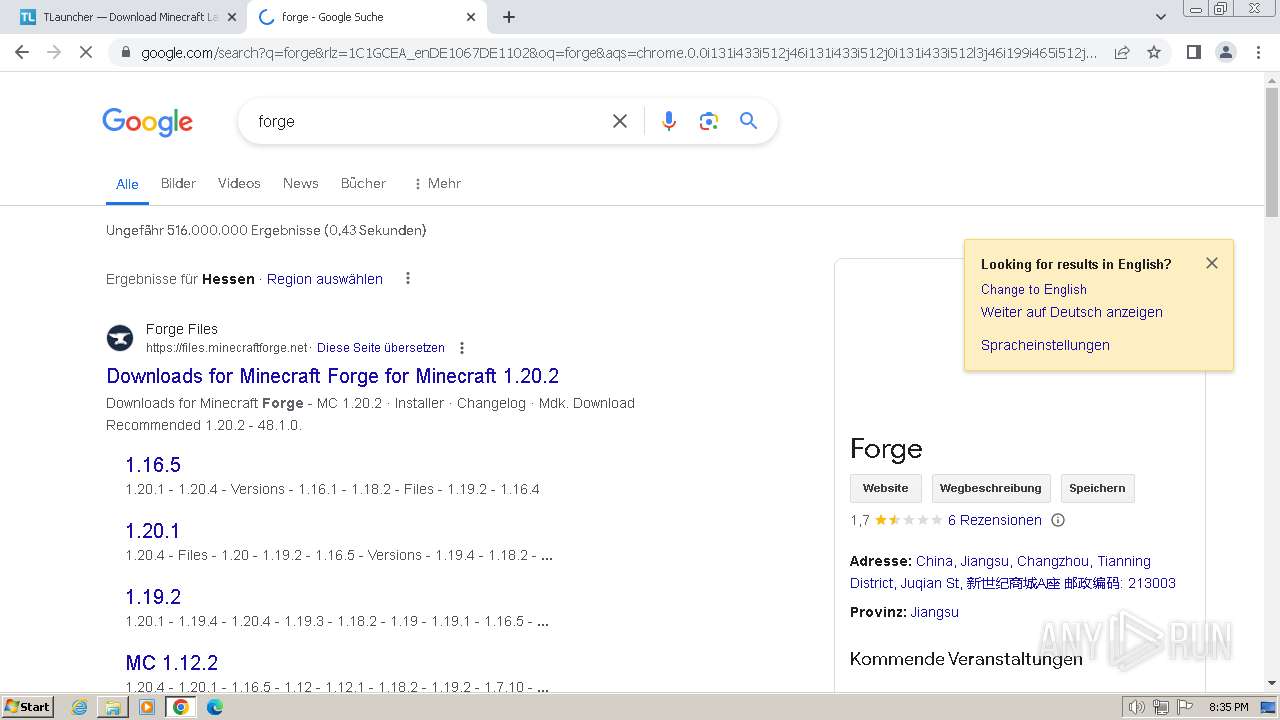
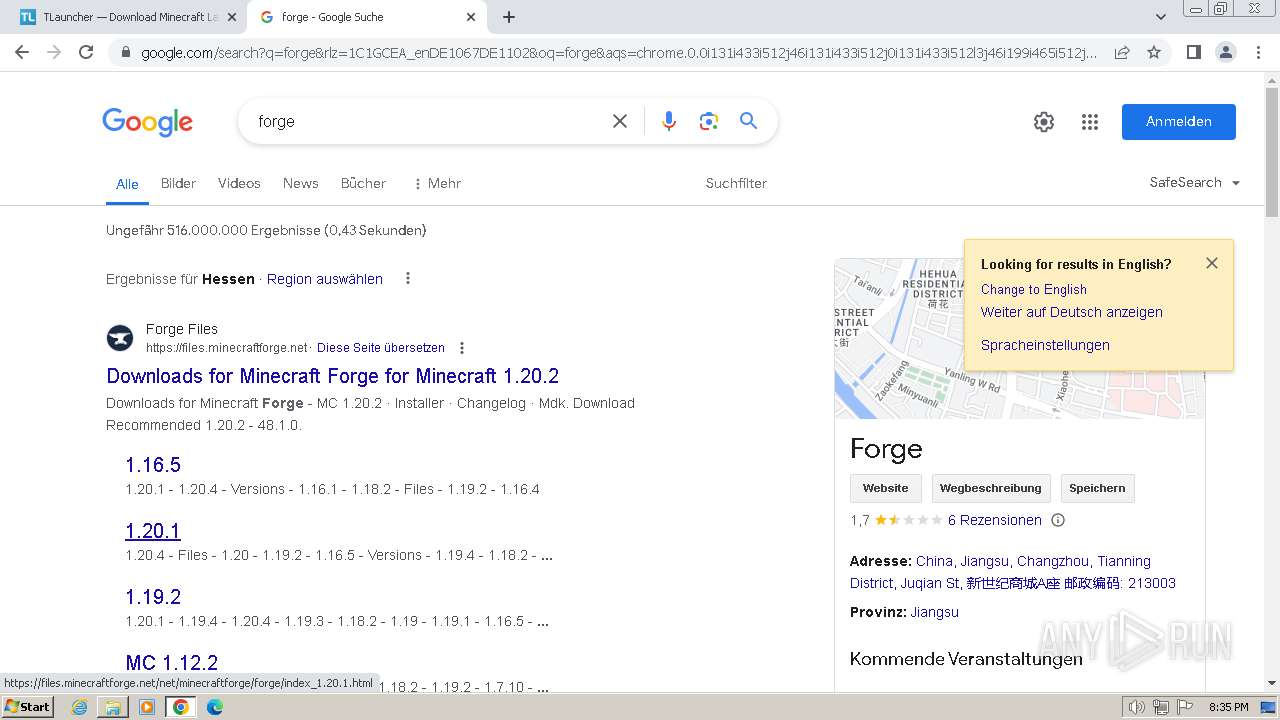
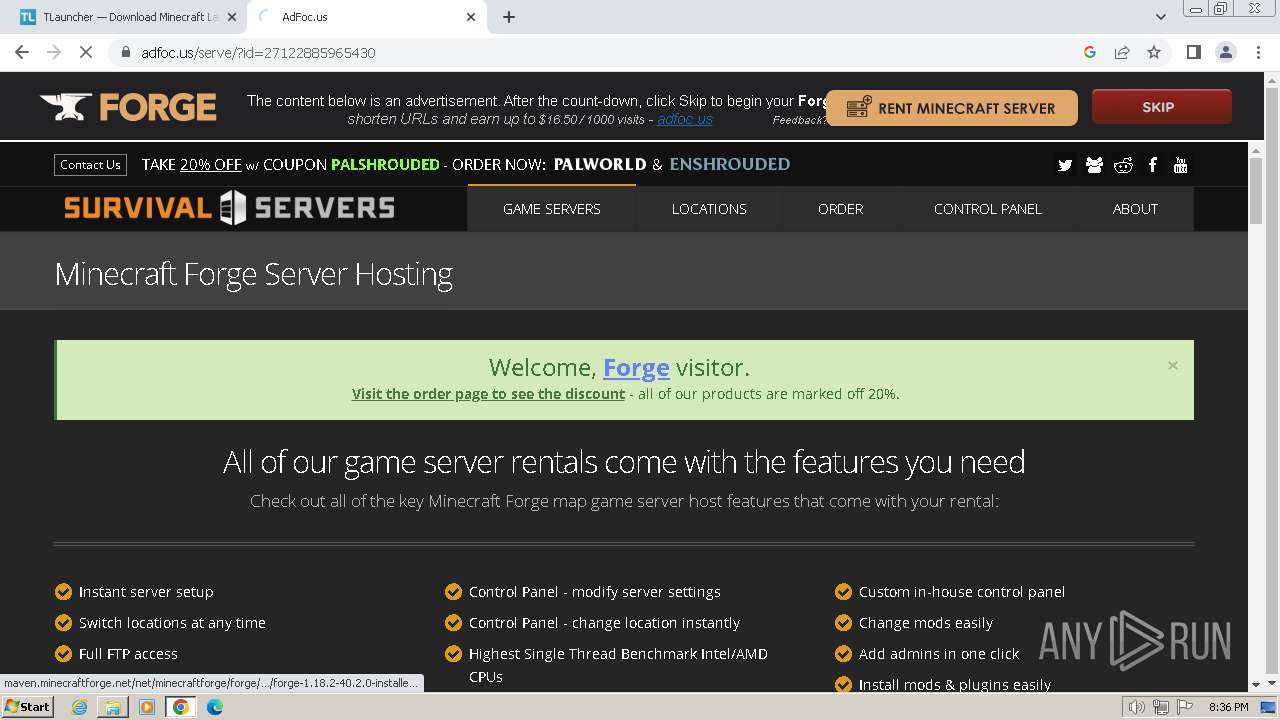
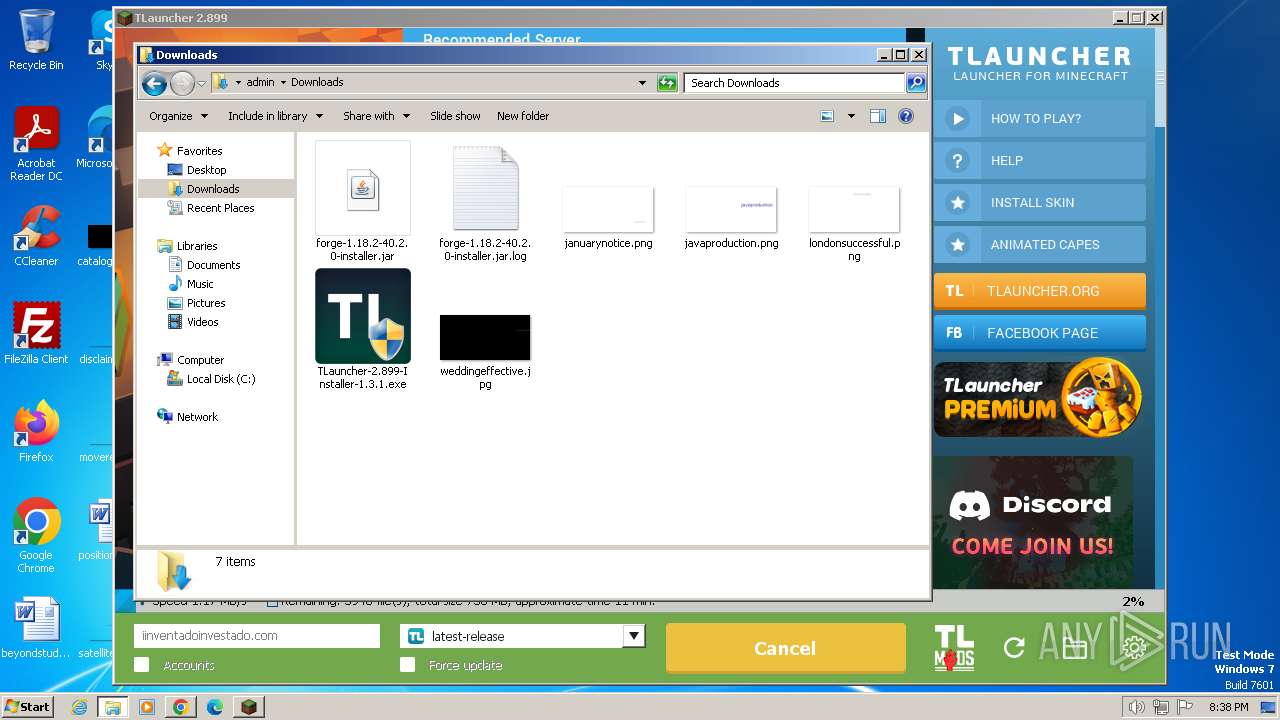
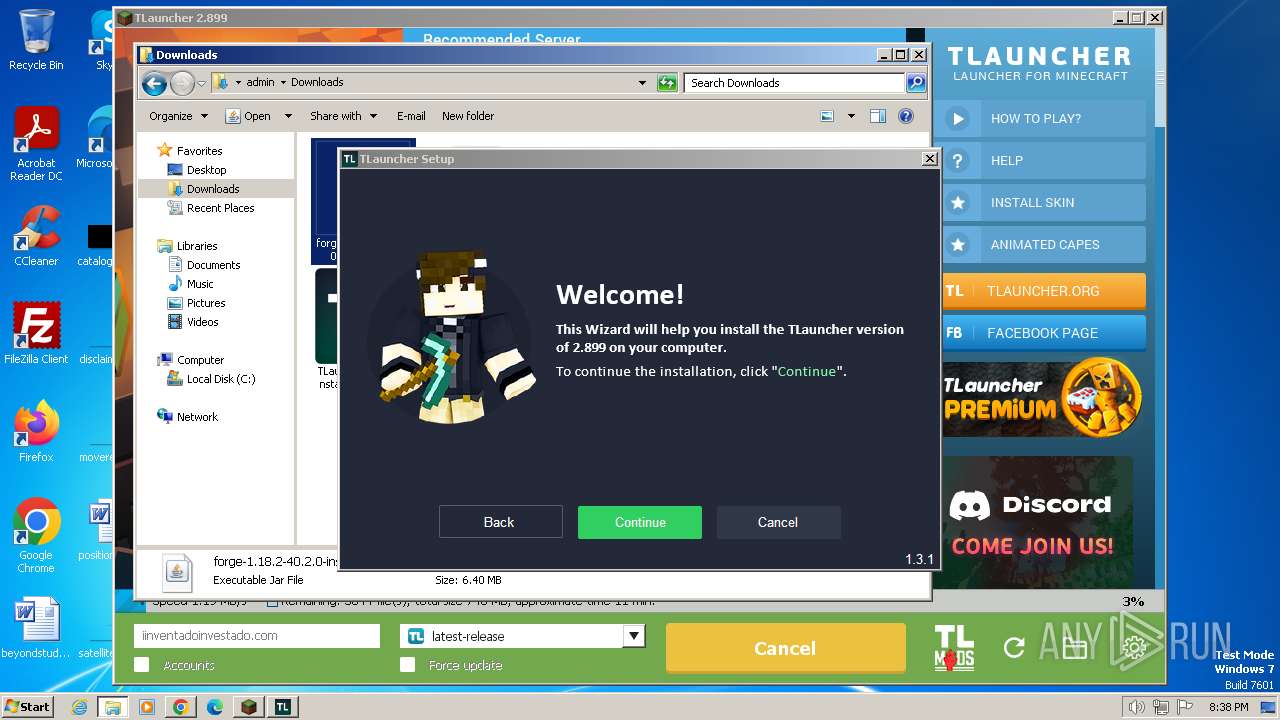
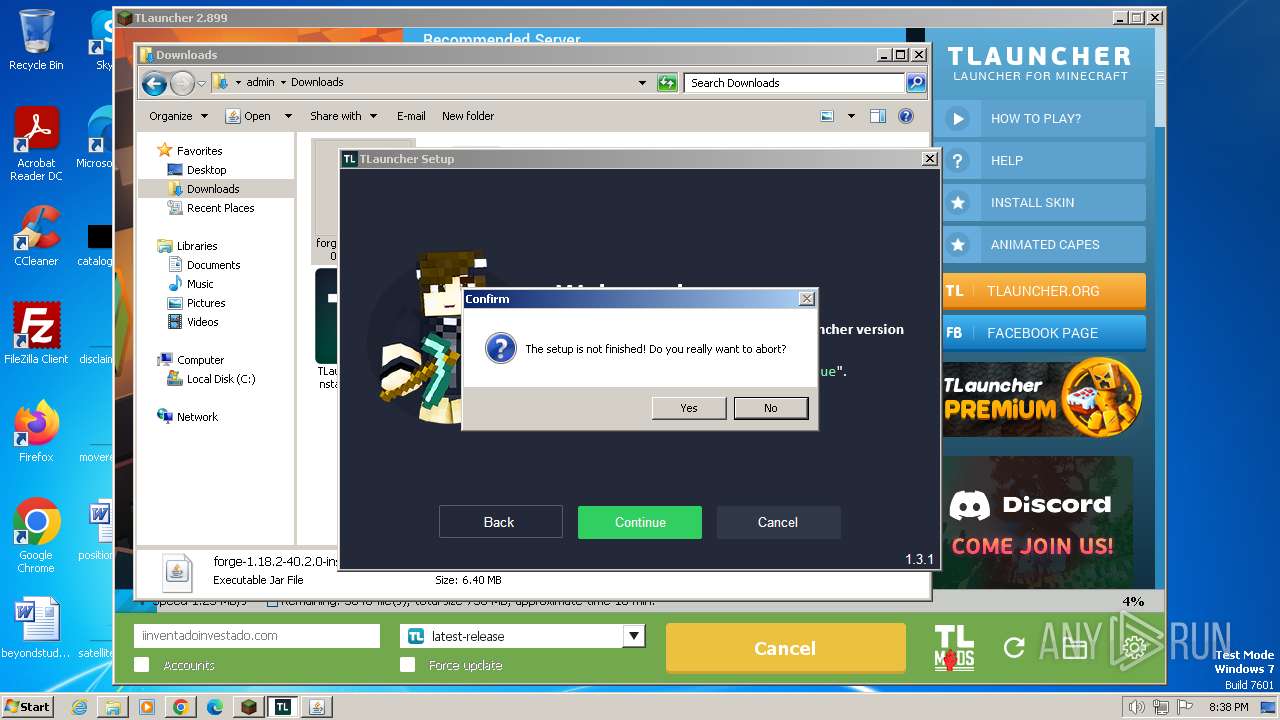
Manual execution by a user
- chrome.exe (PID: 2756)
- explorer.exe (PID: 3468)
- TLauncher.exe (PID: 3468)
- TLauncher-2.899-Installer-1.3.1.exe (PID: 3476)
- TLauncher-2.899-Installer-1.3.1.exe (PID: 1604)
- javaw.exe (PID: 2020)
Executable content was dropped or overwritten
- chrome.exe (PID: 1992)
- chrome.exe (PID: 2756)
- chrome.exe (PID: 1092)
The process uses the downloaded file
- chrome.exe (PID: 2756)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 2368)
Drops the executable file immediately after the start
- chrome.exe (PID: 2756)
- chrome.exe (PID: 1992)
- chrome.exe (PID: 1092)
Checks proxy server information
- irsetup.exe (PID: 2572)
- irsetup.exe (PID: 1864)
- irsetup.exe (PID: 3576)
Reads the software policy settings
- irsetup.exe (PID: 2572)
- irsetup.exe (PID: 1864)
- dxdiag.exe (PID: 1056)
- irsetup.exe (PID: 3576)
Application launched itself
- chrome.exe (PID: 2756)
Creates files or folders in the user directory
- irsetup.exe (PID: 1864)
- irsetup.exe (PID: 2572)
- javaw.exe (PID: 3096)
- javaw.exe (PID: 3872)
Reads security settings of Internet Explorer
- dxdiag.exe (PID: 1056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (54.7) |
|---|---|---|
| .xpi | | | Mozilla Firefox browser extension (30.1) |
| .zip | | | ZIP compressed archive (15) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:12:31 16:21:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2 |
| ZipUncompressedSize: | - |
| ZipFileName: | META-INF/ |
Total processes
167
Monitored processes
99
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=35 --mojo-platform-channel-handle=5704 --field-trial-handle=1176,i,5325482074388634368,3380236758881095040,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1272 --field-trial-handle=1176,i,5325482074388634368,3380236758881095040,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bb28b38,0x6bb28b48,0x6bb28b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2160 --field-trial-handle=1176,i,5325482074388634368,3380236758881095040,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=5668 --field-trial-handle=1176,i,5325482074388634368,3380236758881095040,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --mojo-platform-channel-handle=5540 --field-trial-handle=1176,i,5325482074388634368,3380236758881095040,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --mojo-platform-channel-handle=1144 --field-trial-handle=1176,i,5325482074388634368,3380236758881095040,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1056 | dxdiag /whql:off /t C:\Users\admin\AppData\Roaming\.minecraft\logs\tlauncher\dxdiag.txt | C:\Windows\System32\dxdiag.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft DirectX Diagnostic Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=2368 --field-trial-handle=1176,i,5325482074388634368,3380236758881095040,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4540 --field-trial-handle=1176,i,5325482074388634368,3380236758881095040,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
59 413
Read events
58 814
Write events
532
Delete events
67
Modification events
| (PID) Process: | (2120) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (2756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2756) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
405
Suspicious files
441
Text files
1 991
Unknown types
513
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1844e4.TMP | — | |
MD5:— | SHA256:— | |||
| 2756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 2756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1748ba97-7601-4f88-9dd7-ace21bce53ce.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2120 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio1283066942672512641.tmp | image | |
MD5:7DC8AD1E11C90D7C411EB5994ACCCFFD | SHA256:EB5873B2BDED079AE19DEE03BAC25802AA6D37BCCEDA8ADE48EB0B88225C85E0 | |||
| 2120 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:47C707E67542C5CC6937980A0DF9F62C | SHA256:E3C1D645579A4EB05F26CC579EA8CD633CFDDD05828592BCF370ECC820C62602 | |||
| 2756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF184745.TMP | text | |
MD5:F5B58F0B08202C8D6DE12514994A84BF | SHA256:F5BA8809B6A3920A11CF31E7F6A1DEC46EF4F4339D6158967CCB1405409D1241 | |||
| 2756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 2756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF18488d.TMP | — | |
MD5:— | SHA256:— | |||
| 2756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
444
DNS requests
550
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 5.82 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 10.3 Kb | unknown |
1864 | irsetup.exe | GET | 304 | 2.16.135.41:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?370a7e6f481578e5 | unknown | — | — | unknown |
1864 | irsetup.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | binary | 2.18 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 11.6 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 10.0 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 15.7 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 77.5 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 33.7 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
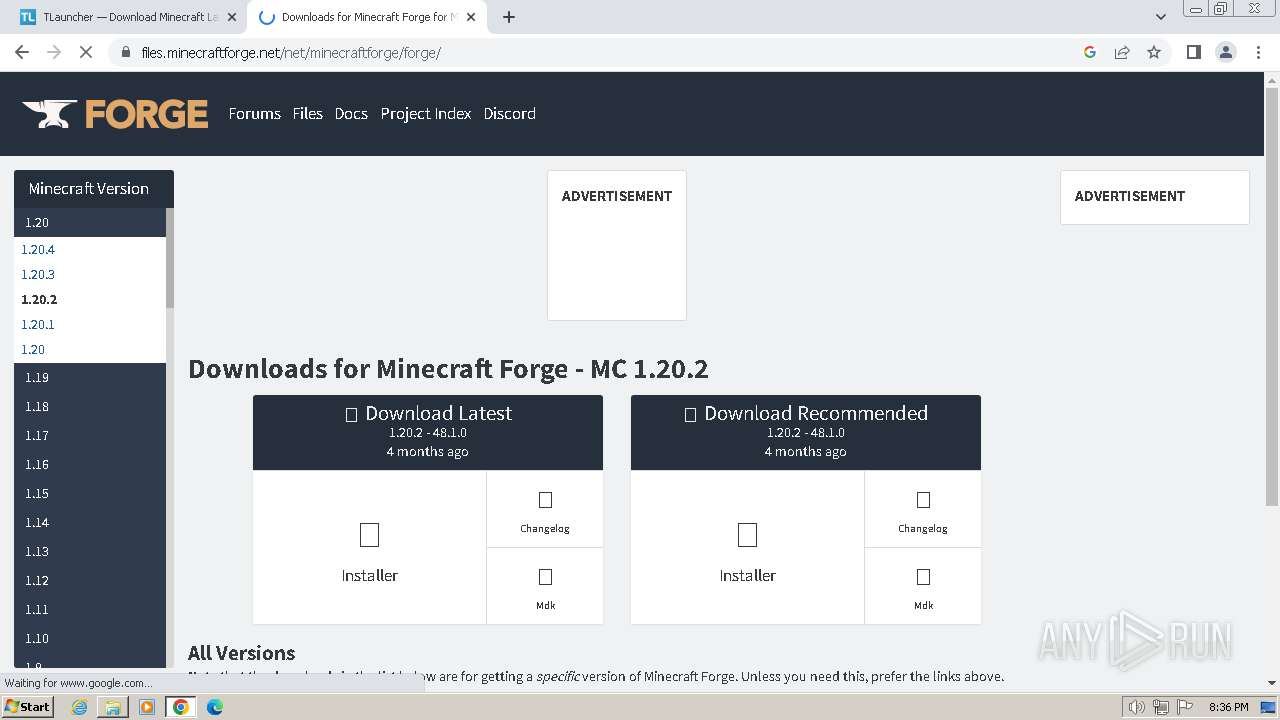
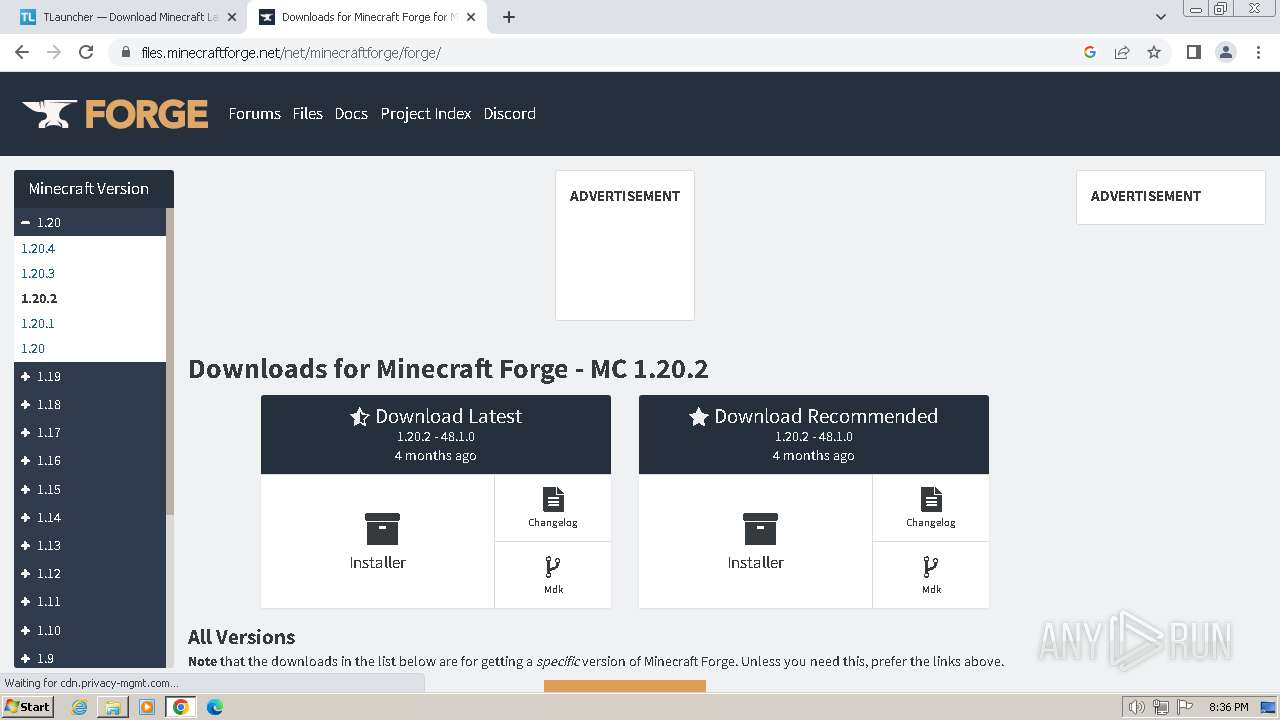
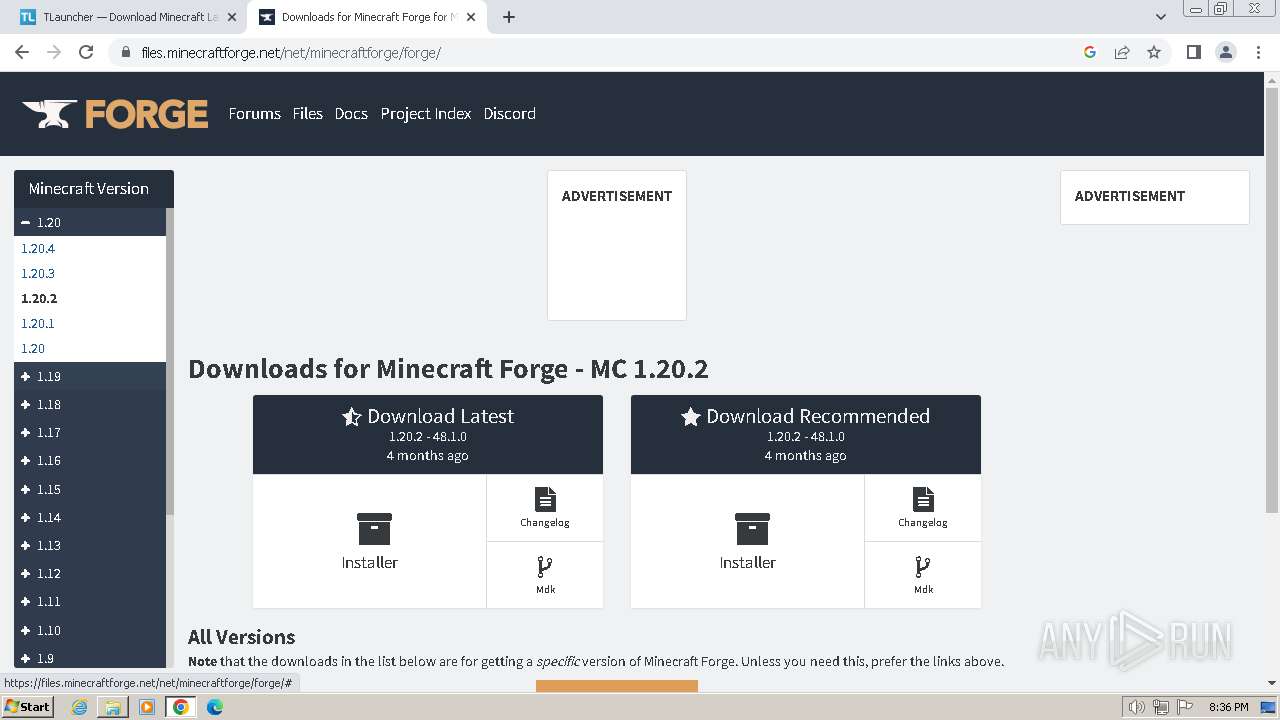
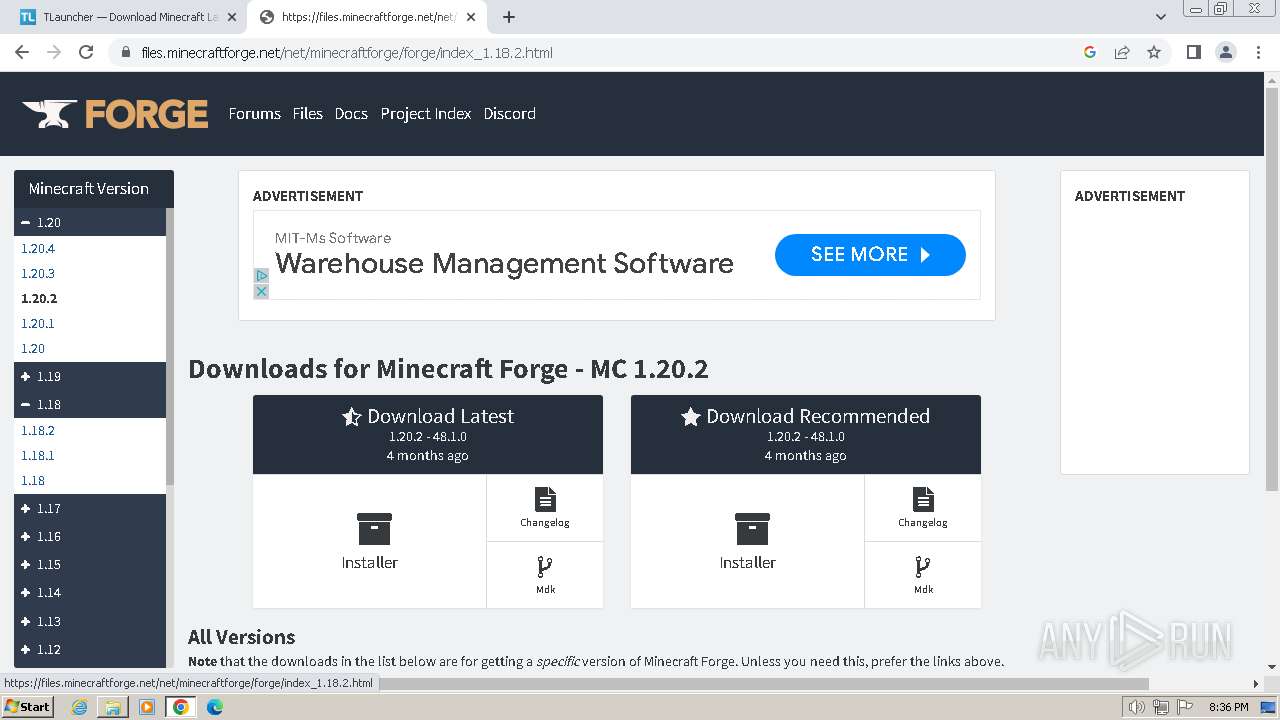
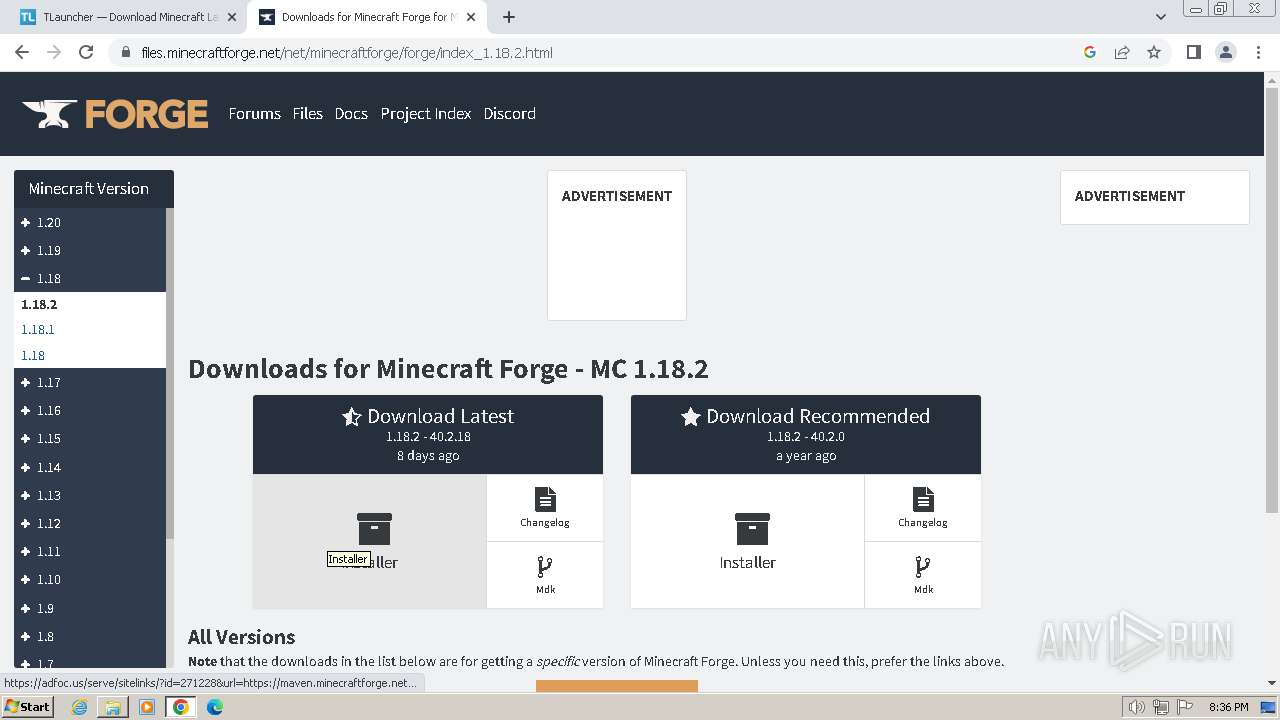
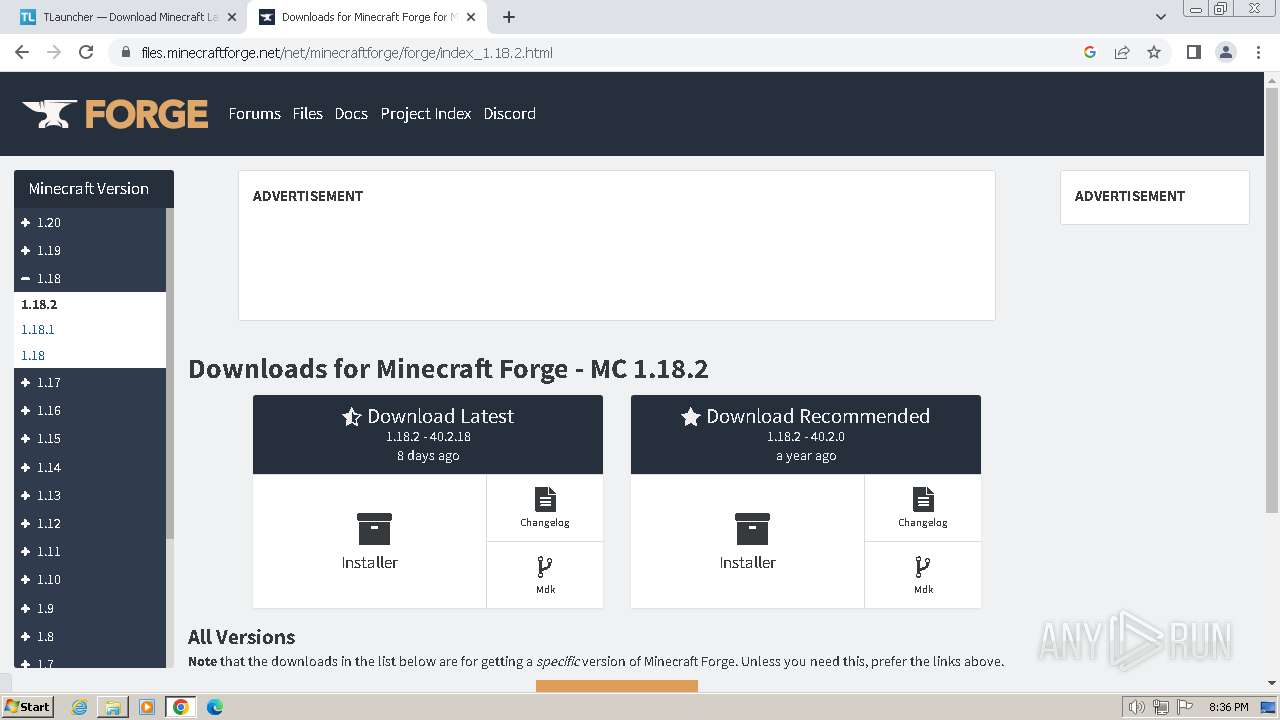
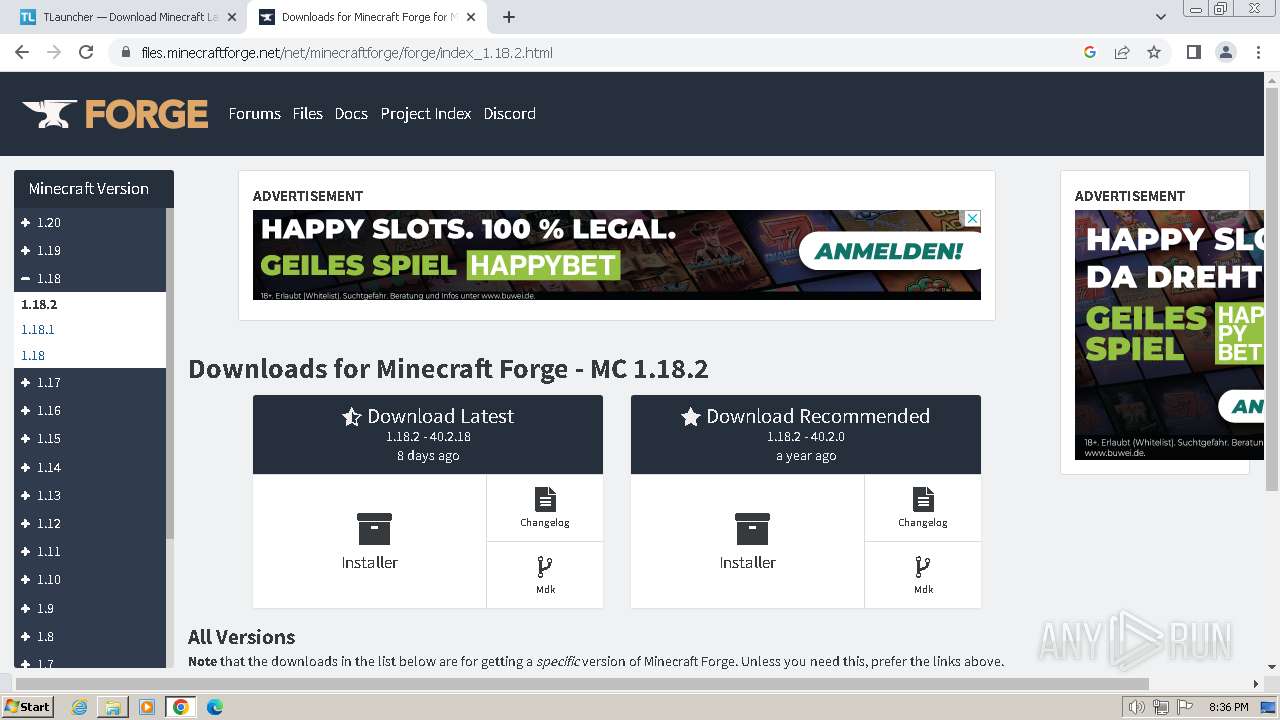
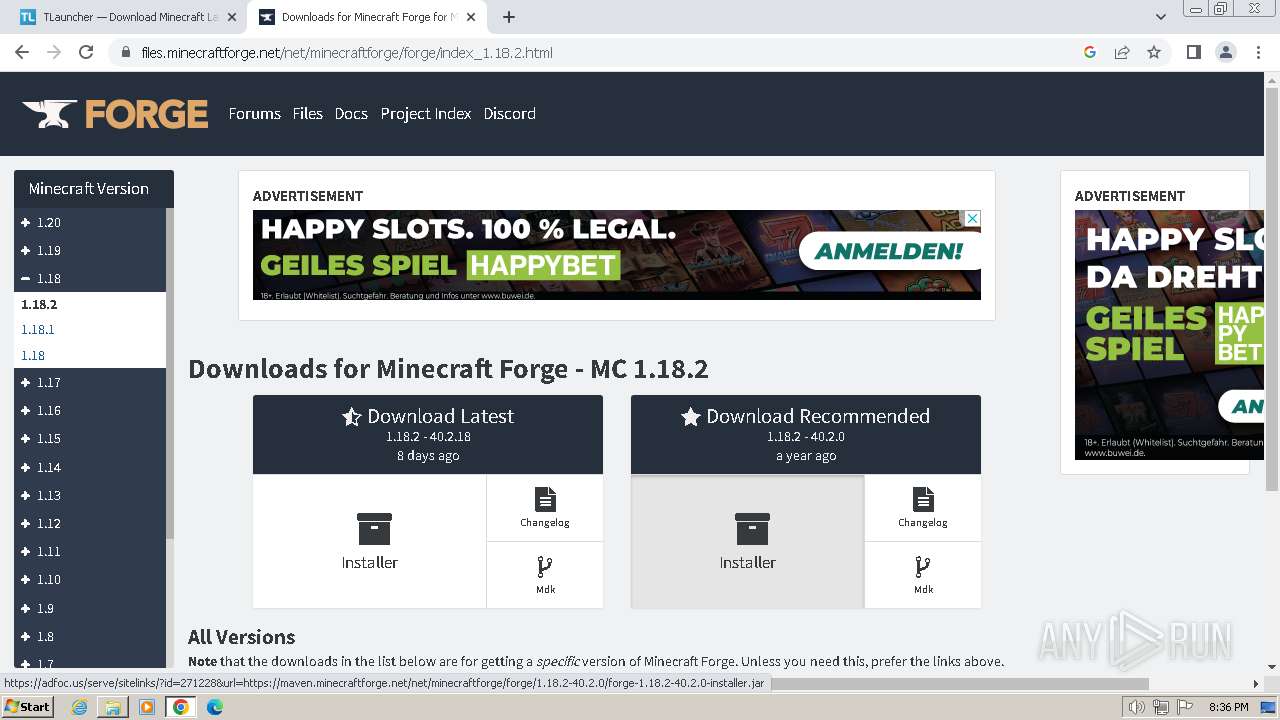
2120 | javaw.exe | 51.79.83.165:443 | files.minecraftforge.net | OVH SAS | CA | unknown |
2120 | javaw.exe | 13.107.246.67:443 | libraries.minecraft.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1992 | chrome.exe | 142.250.181.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2756 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1992 | chrome.exe | 74.125.128.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
1992 | chrome.exe | 142.250.184.228:443 | www.google.com | GOOGLE | US | whitelisted |
1992 | chrome.exe | 142.250.184.238:443 | encrypted-tbn0.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
files.minecraftforge.net |
| unknown |
maven.minecraftforge.net |
| unknown |
libraries.minecraft.net |
| shared |
launchermeta.mojang.com |
| whitelisted |
piston-meta.mojang.com |
| unknown |
sessionserver.mojang.com |
| unknown |
authserver.mojang.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1992 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
1992 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
1992 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
1992 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1992 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1992 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1992 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1992 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1992 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1992 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |